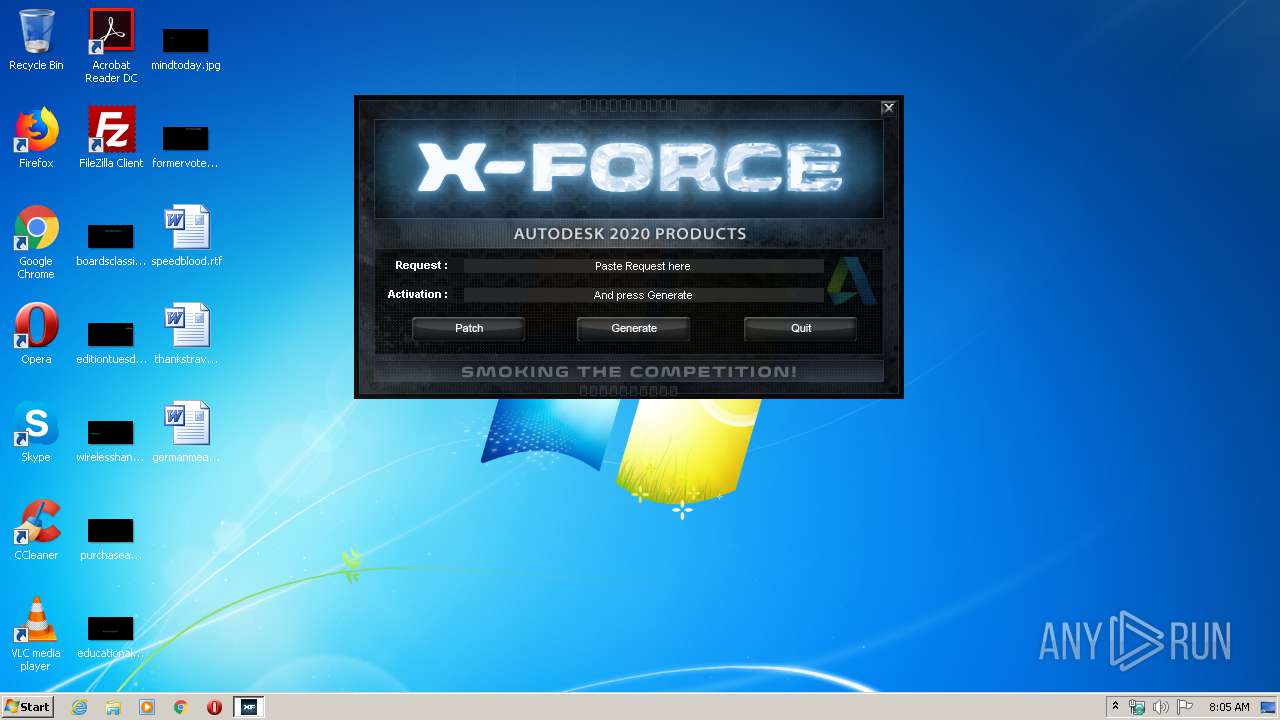
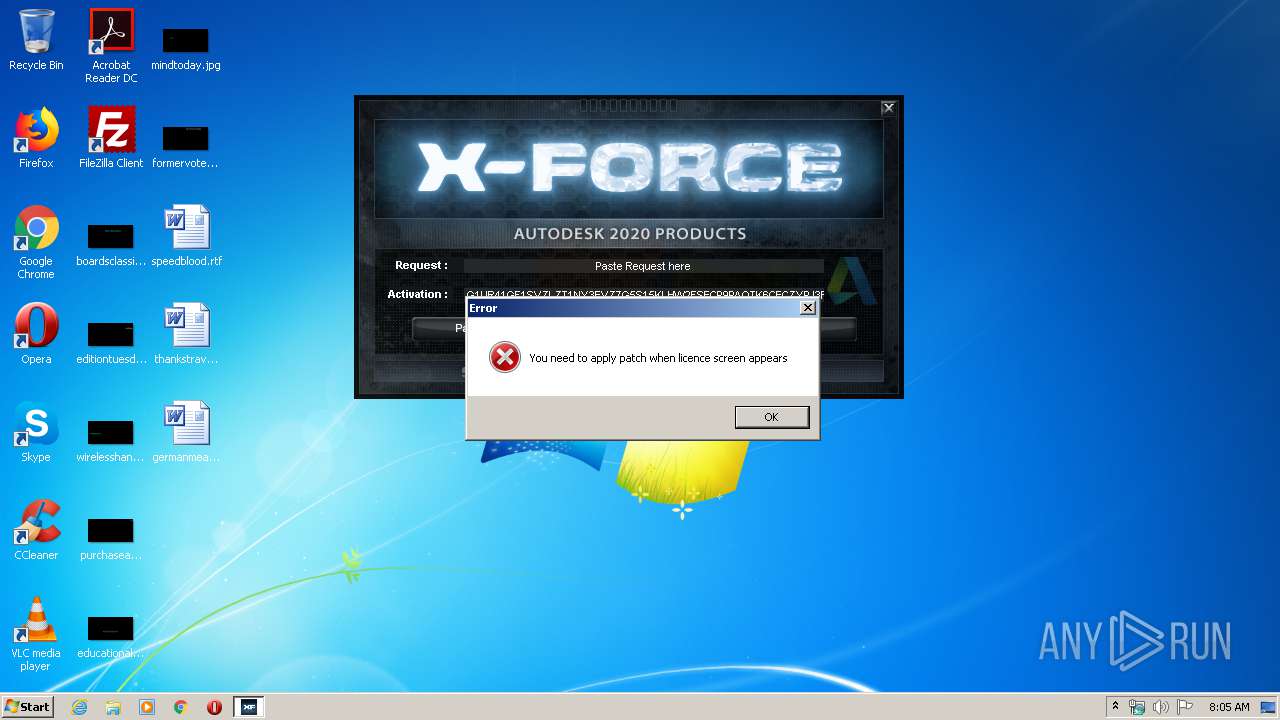
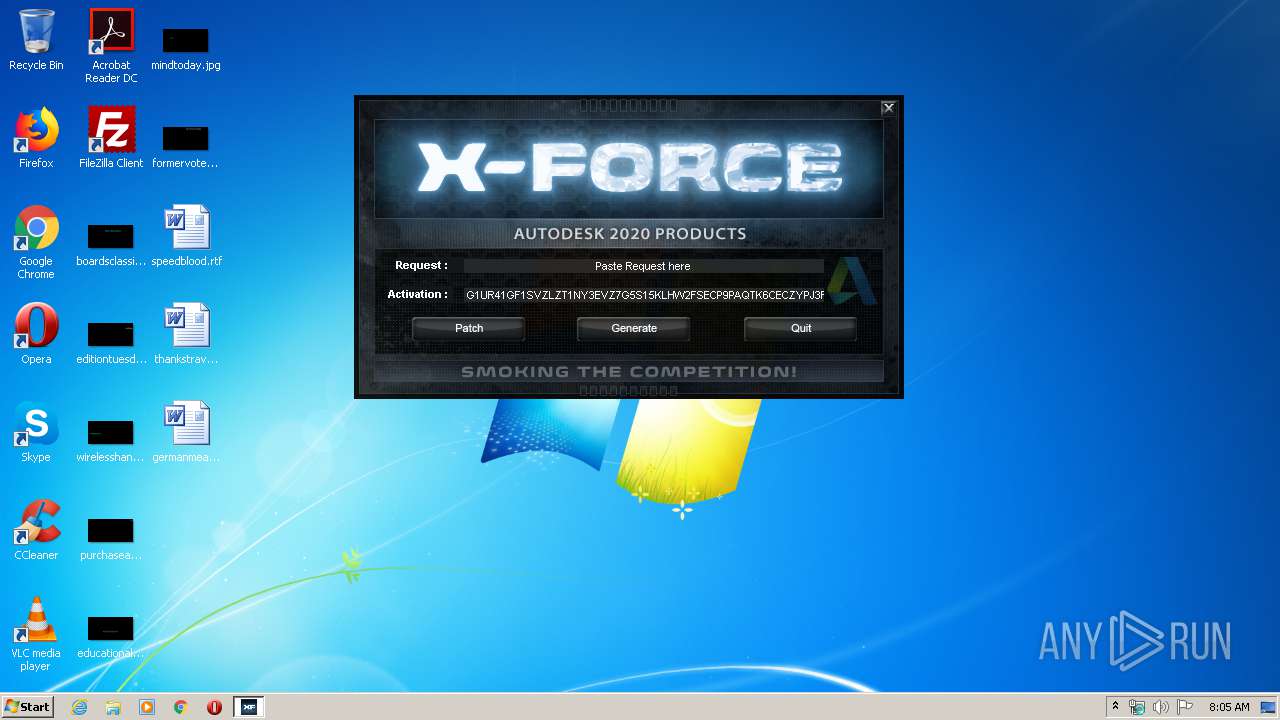
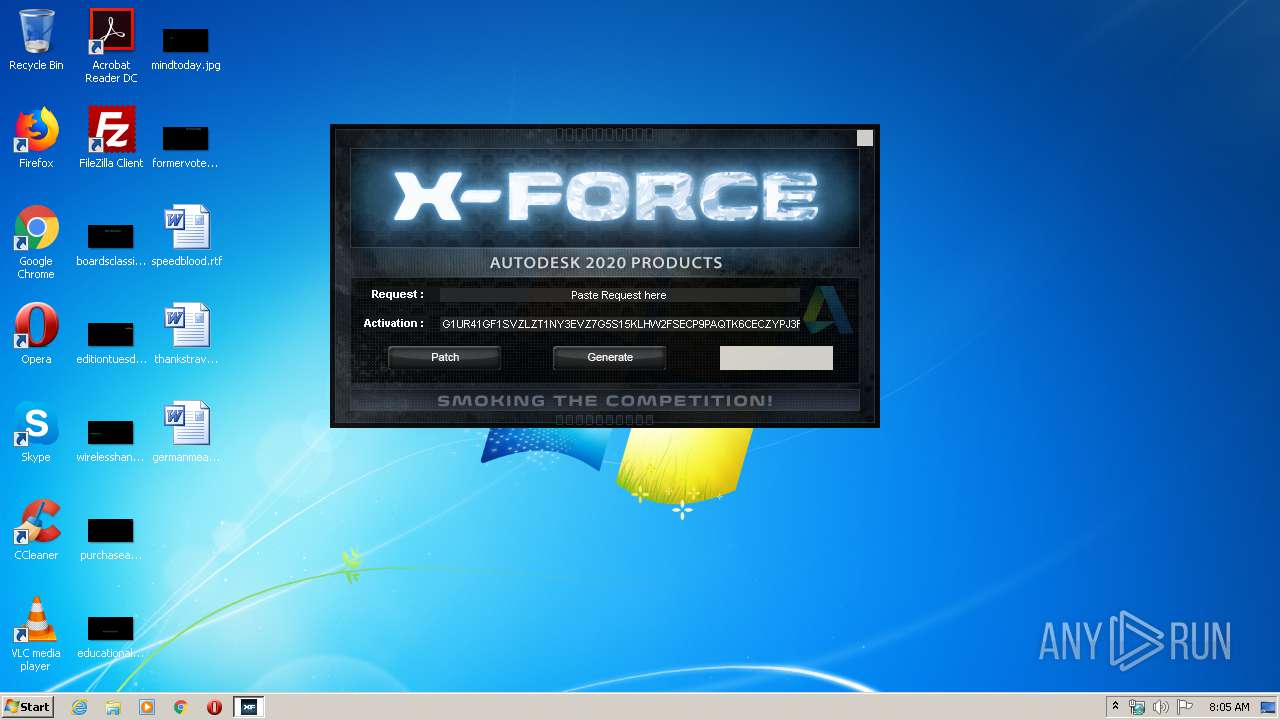
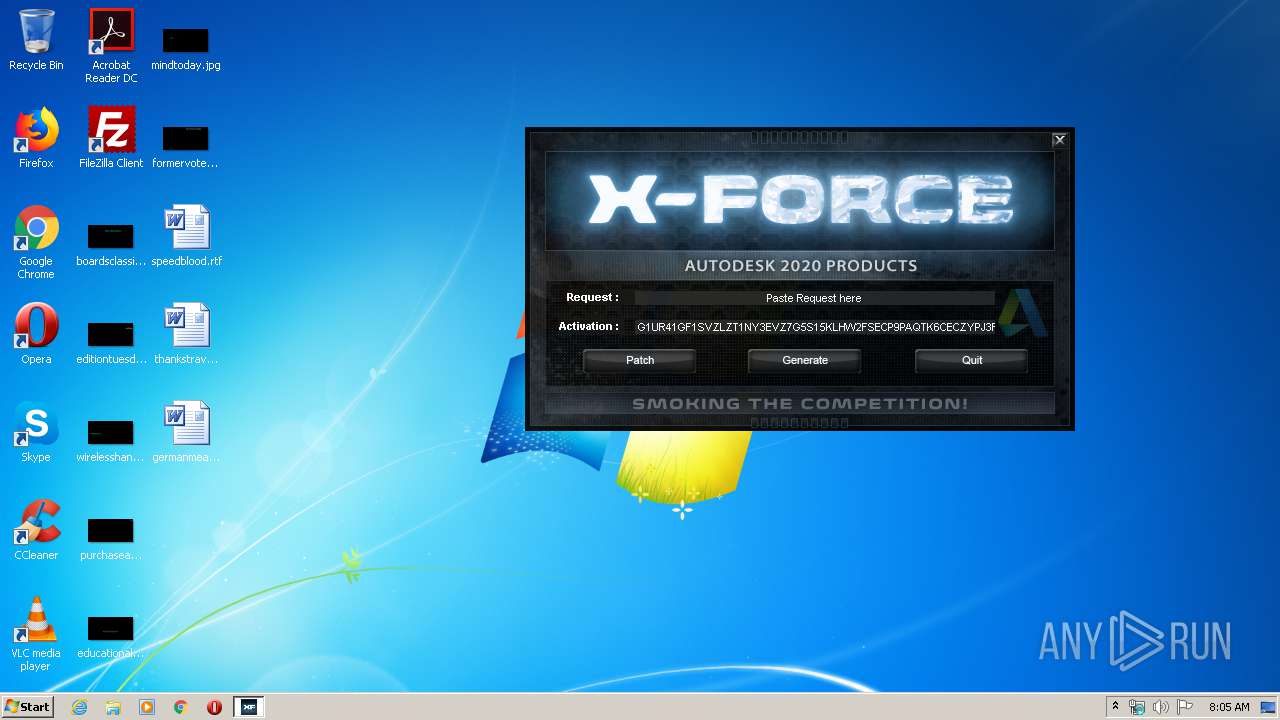
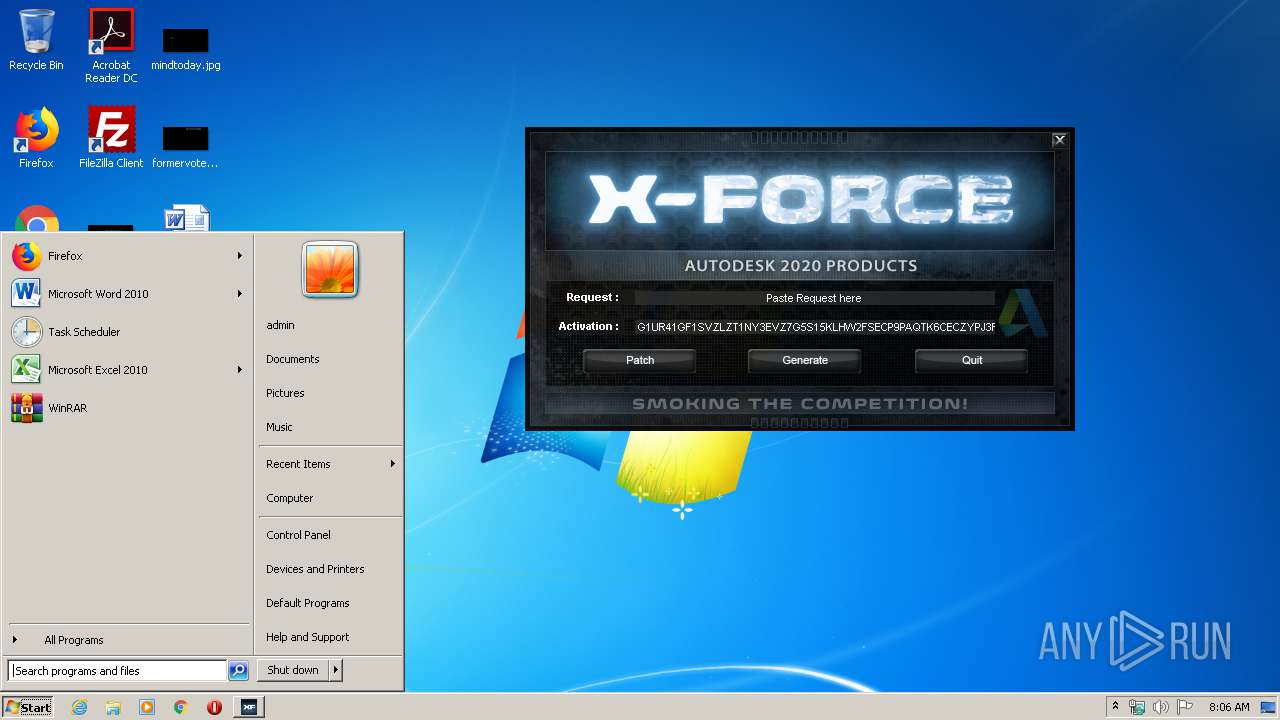
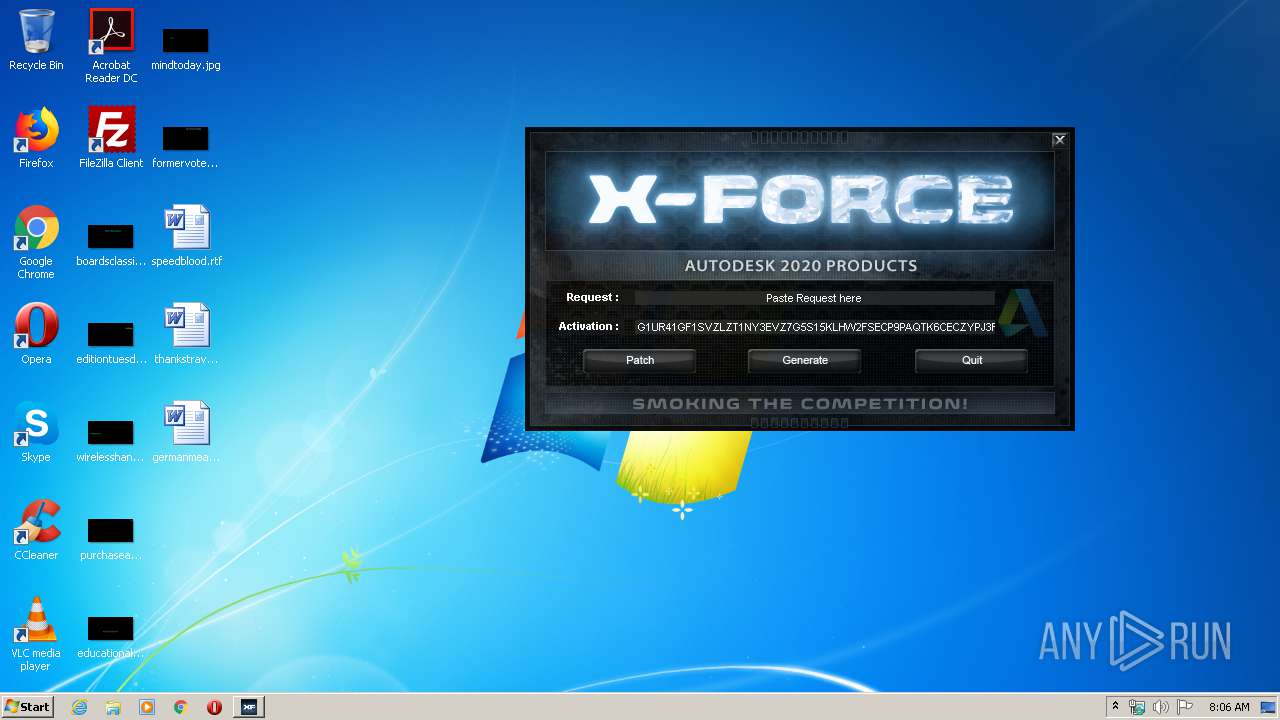
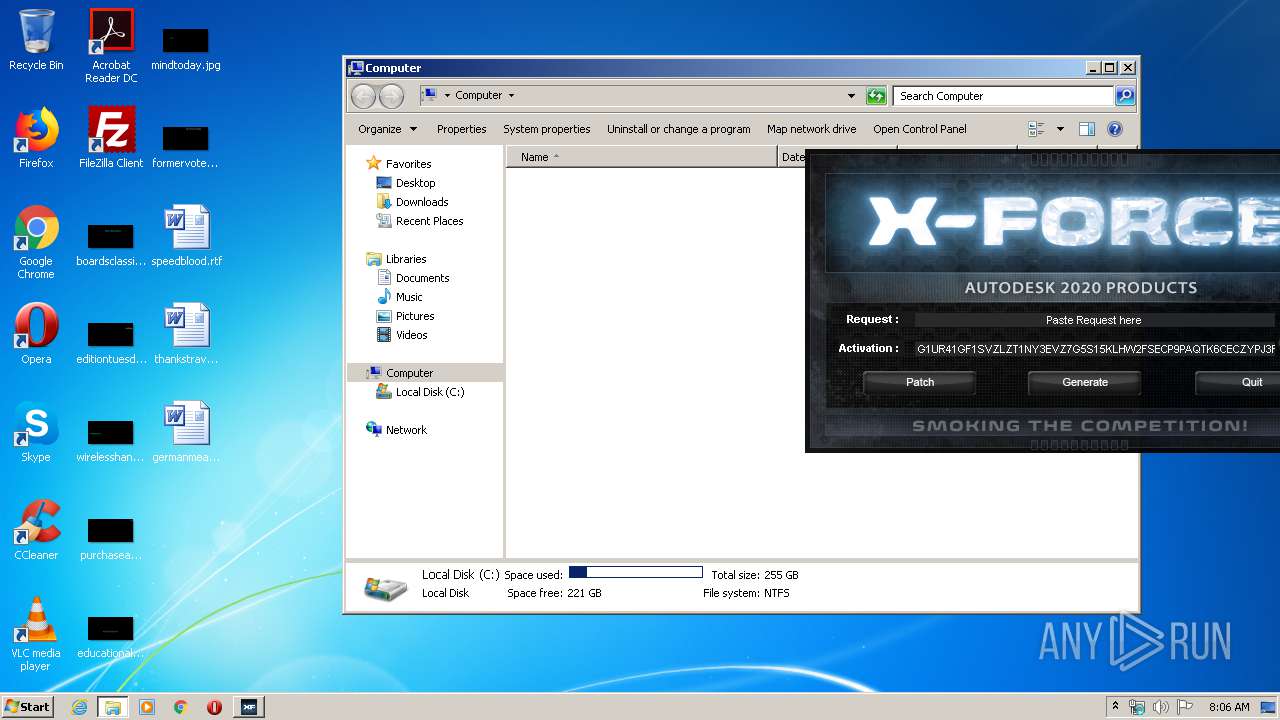
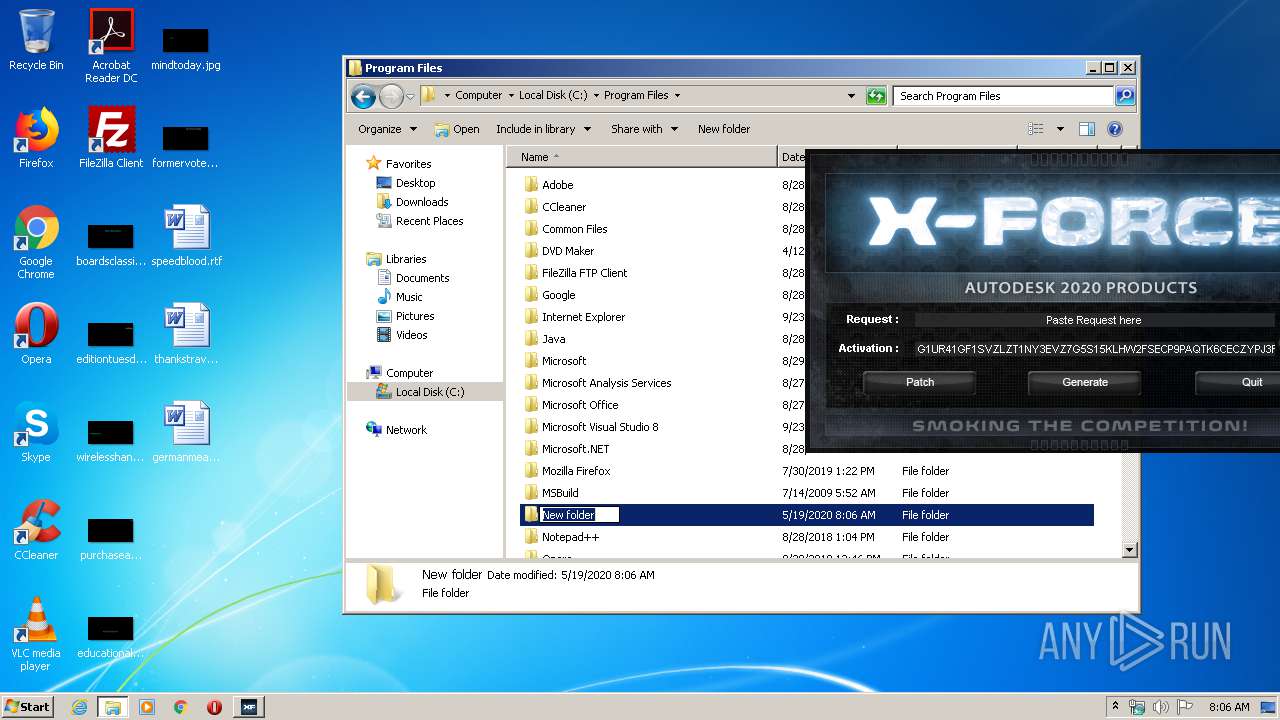
| File name: | xf-adesk20.exe |
| Full analysis: | https://app.any.run/tasks/afc35756-009b-4e3a-b2bc-d332a7f0741c |
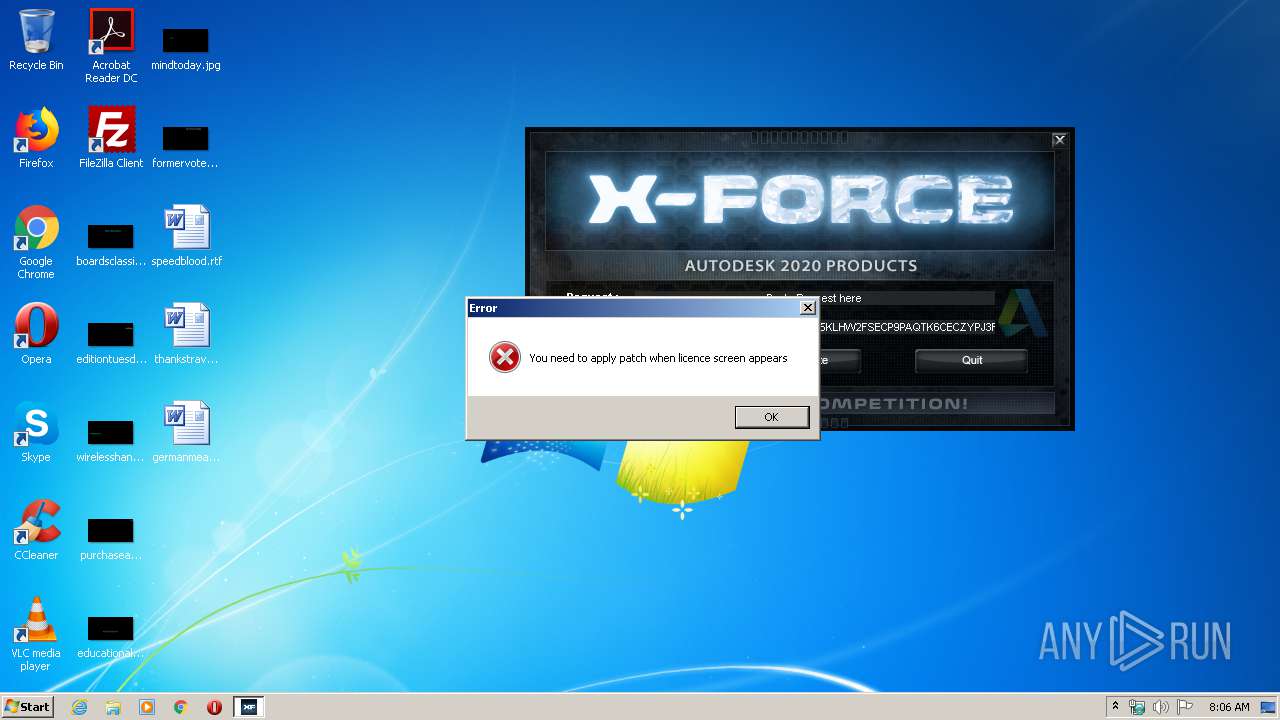
| Verdict: | Suspicious activity |
| Analysis date: | May 19, 2020, 07:05:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 706939C469346BEF9B84C822ABCF7B31 |
| SHA1: | BC87860064ECD909C9F9569B1FCE0785DB06ECC7 |
| SHA256: | E64FDD9DD992EFCEB24951C882B3DCCE36D9EE22C09EEA4E3AF8ECEDF4D65BF9 |
| SSDEEP: | 12288:e4sTwc9jjjml1Mp2gnl9F0aqDGJVkA7gvx2wZWe6woS:eVTdNHKMognTF0vGAAu2w |
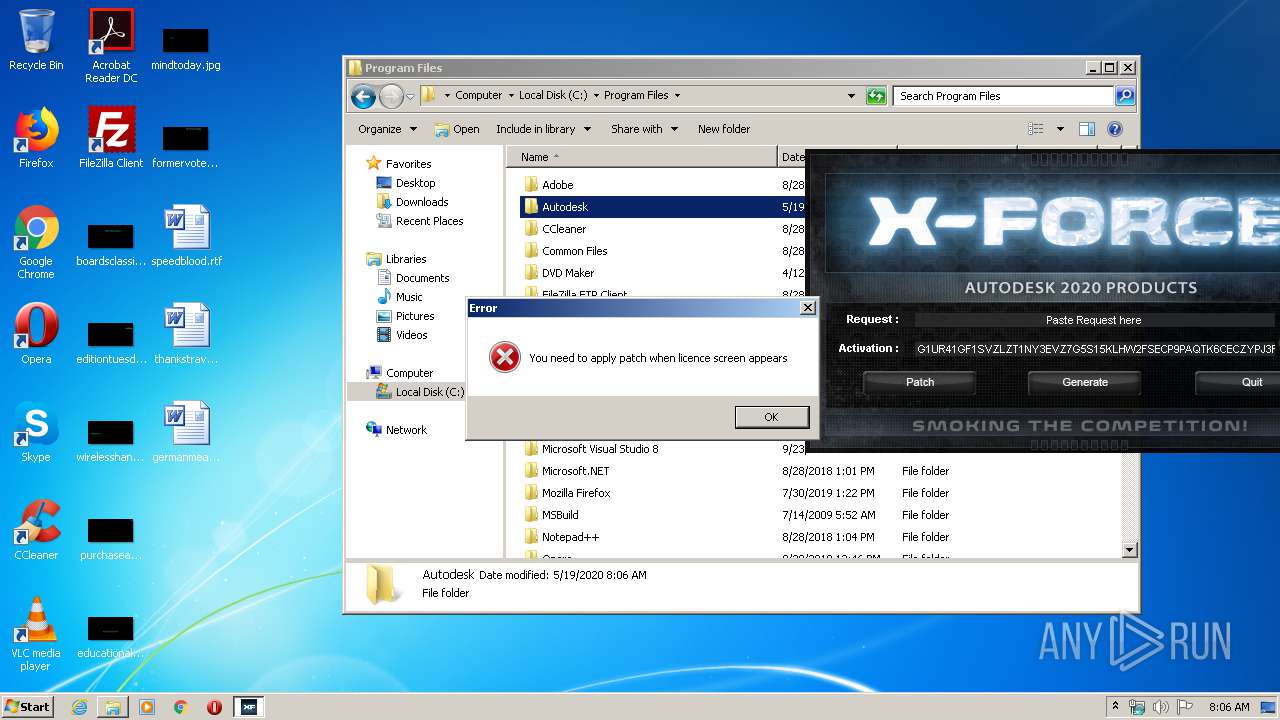
MALICIOUS
Actions looks like stealing of personal data
- DllHost.exe (PID: 3528)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 3528)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:30 22:07:04+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.14 |
| CodeSize: | 589824 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | 1695744 |
| EntryPoint: | 0x22dce0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Mar-2019 21:07:04 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 30-Mar-2019 21:07:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0019E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0019F000 | 0x00090000 | 0x0008FA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9994 |
.rsrc | 0x0022F000 | 0x00003000 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.85886 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.93643 | 8500 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 7.20777 | 276 | UNKNOWN | UNKNOWN | RT_DIALOG |
102 | 7.99878 | 159102 | UNKNOWN | UNKNOWN | RT_BITMAP |
103 | 1.91924 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
105 | 7.94189 | 3848 | UNKNOWN | UNKNOWN | RT_BITMAP |
106 | 7.94849 | 3846 | UNKNOWN | UNKNOWN | RT_BITMAP |
107 | 7.95423 | 3848 | UNKNOWN | UNKNOWN | RT_BITMAP |
108 | 7.95035 | 3846 | UNKNOWN | UNKNOWN | RT_BITMAP |
111 | 7.69867 | 750 | UNKNOWN | UNKNOWN | RT_BITMAP |
112 | 7.76129 | 854 | UNKNOWN | UNKNOWN | RT_BITMAP |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
WINMM.dll |
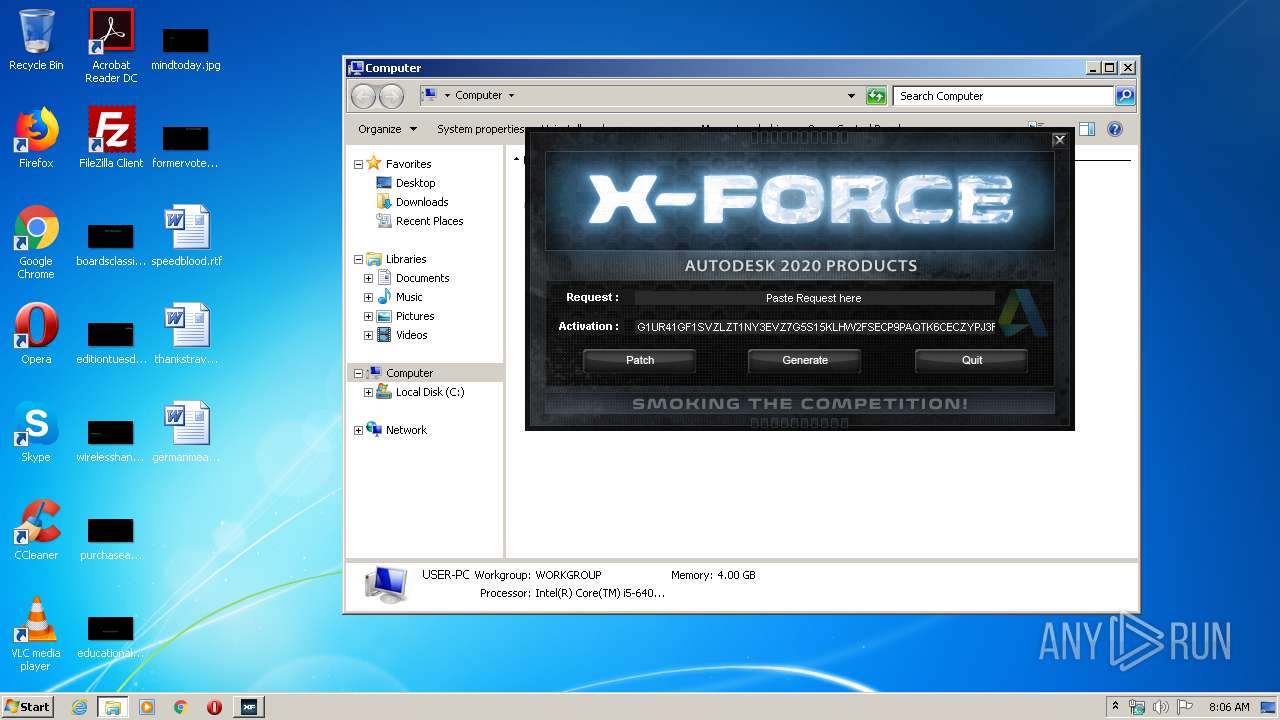
Total processes
44
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1848 | "C:\Users\admin\AppData\Local\Temp\xf-adesk20.exe" | C:\Users\admin\AppData\Local\Temp\xf-adesk20.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3528 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
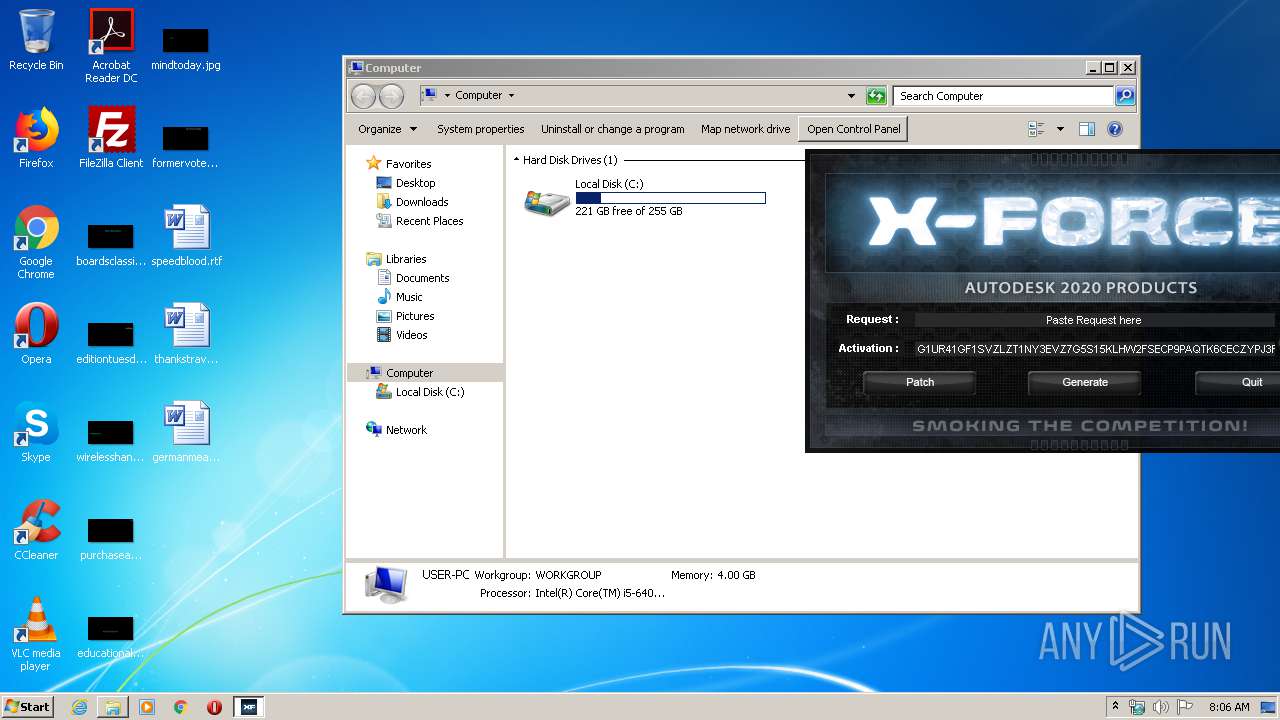
Total events
315
Read events
315
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
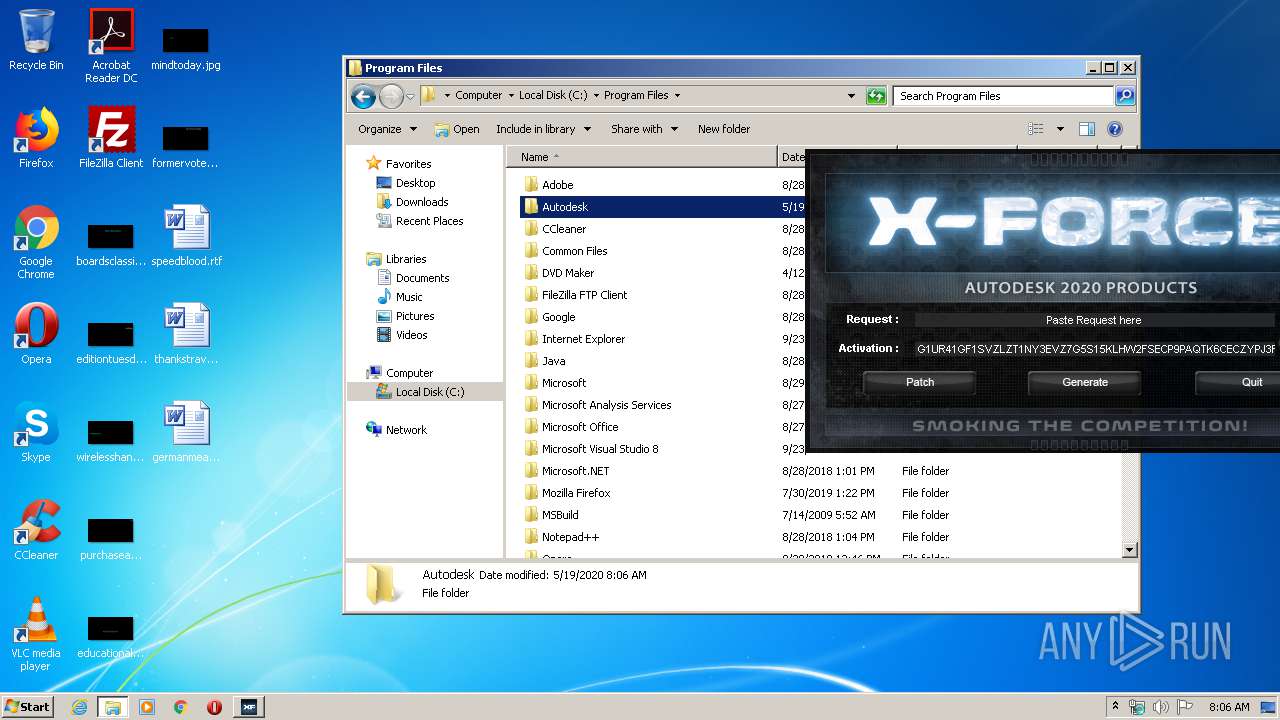
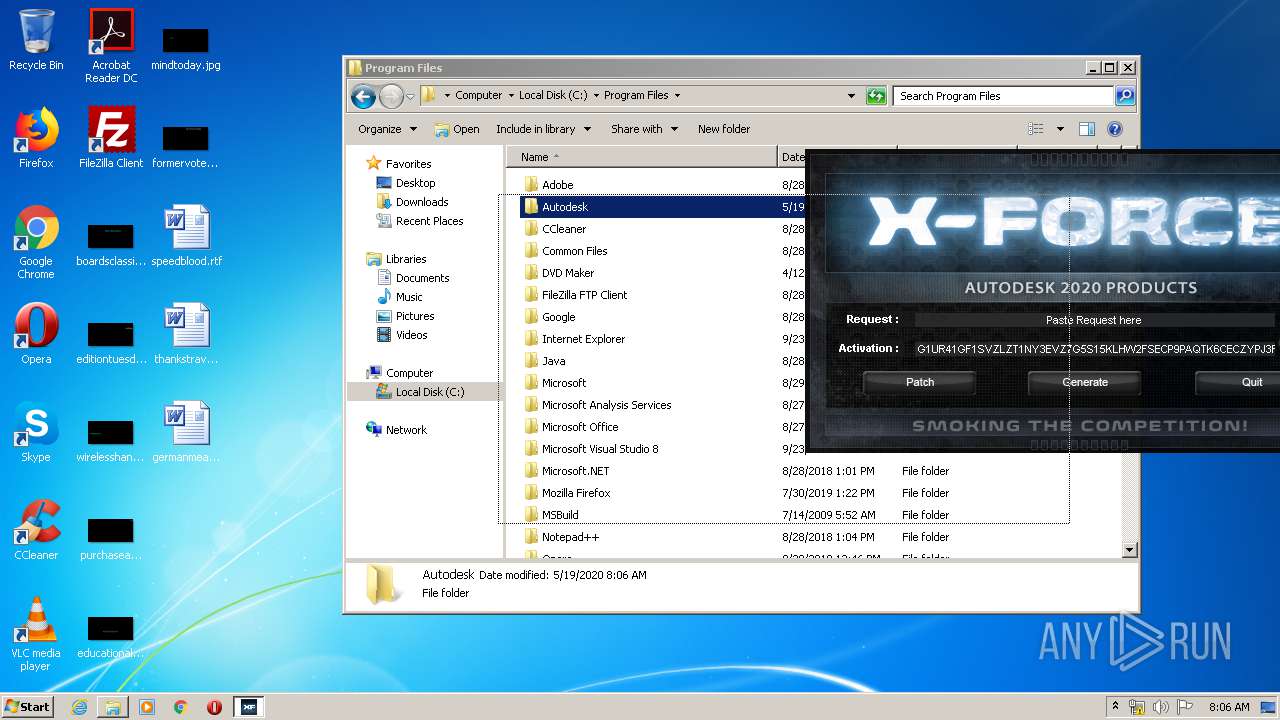
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
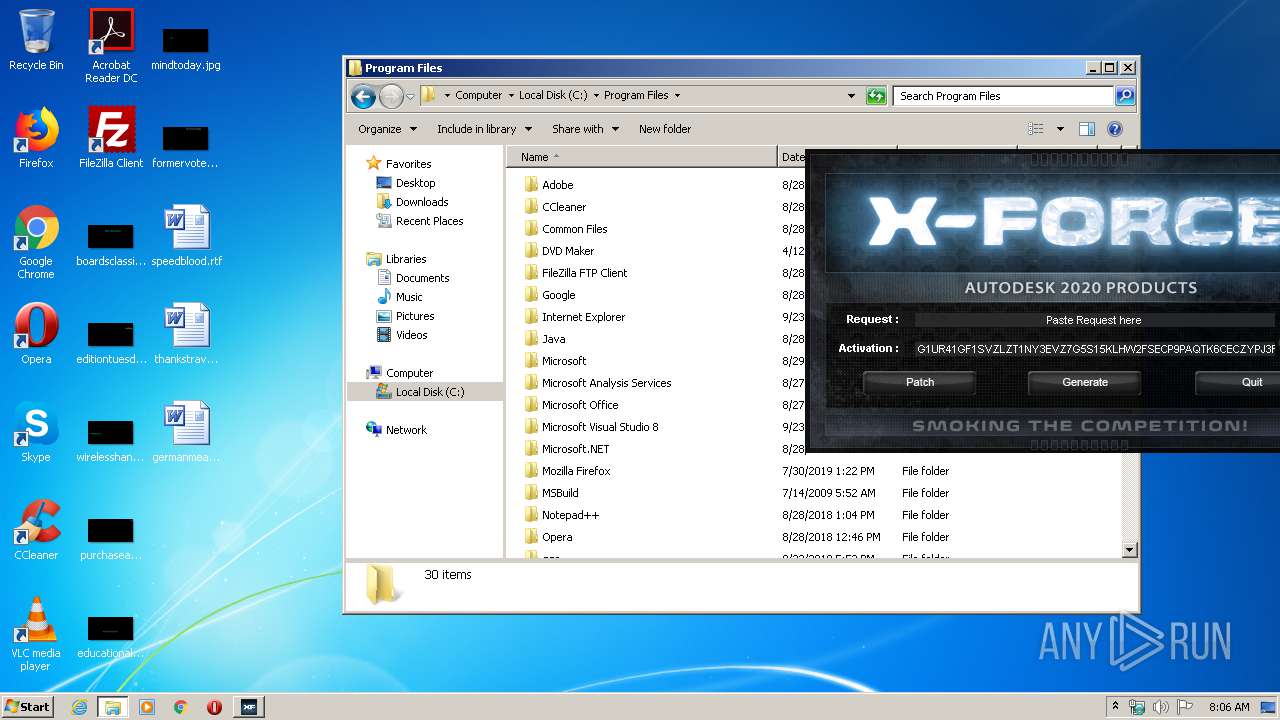
| 3528 | DllHost.exe | C:\Program Files\Autodesk | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report