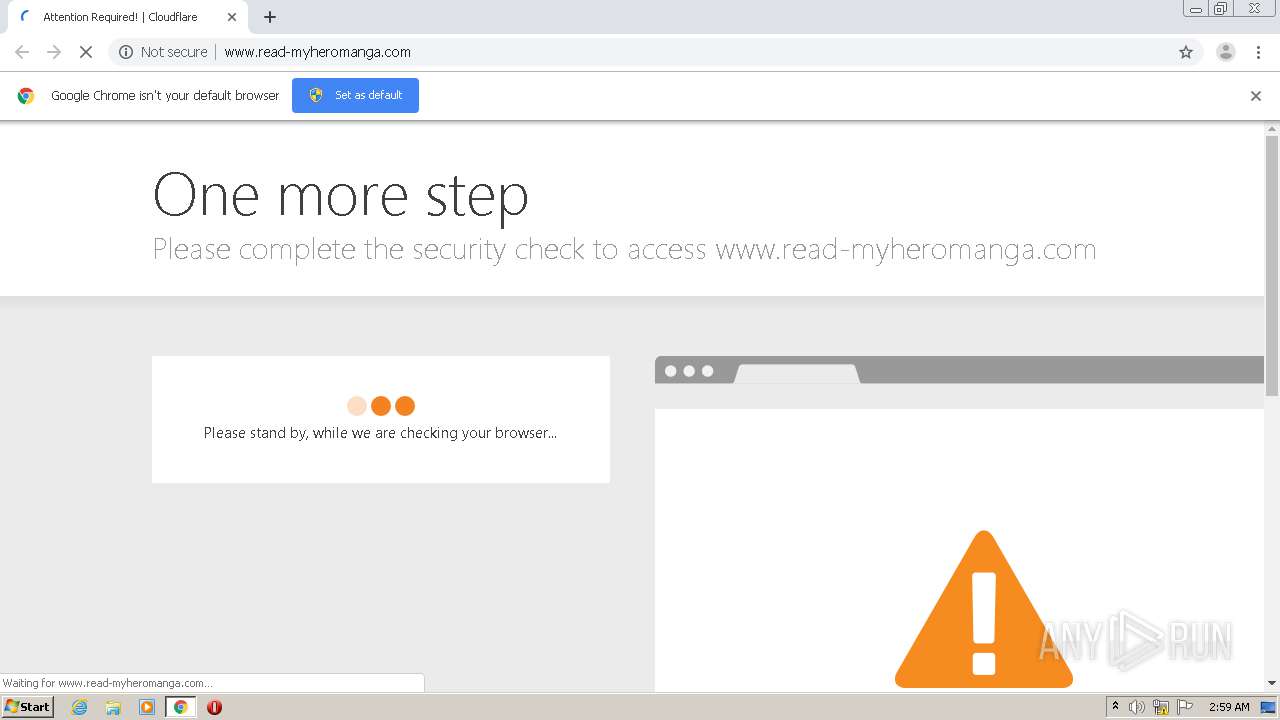
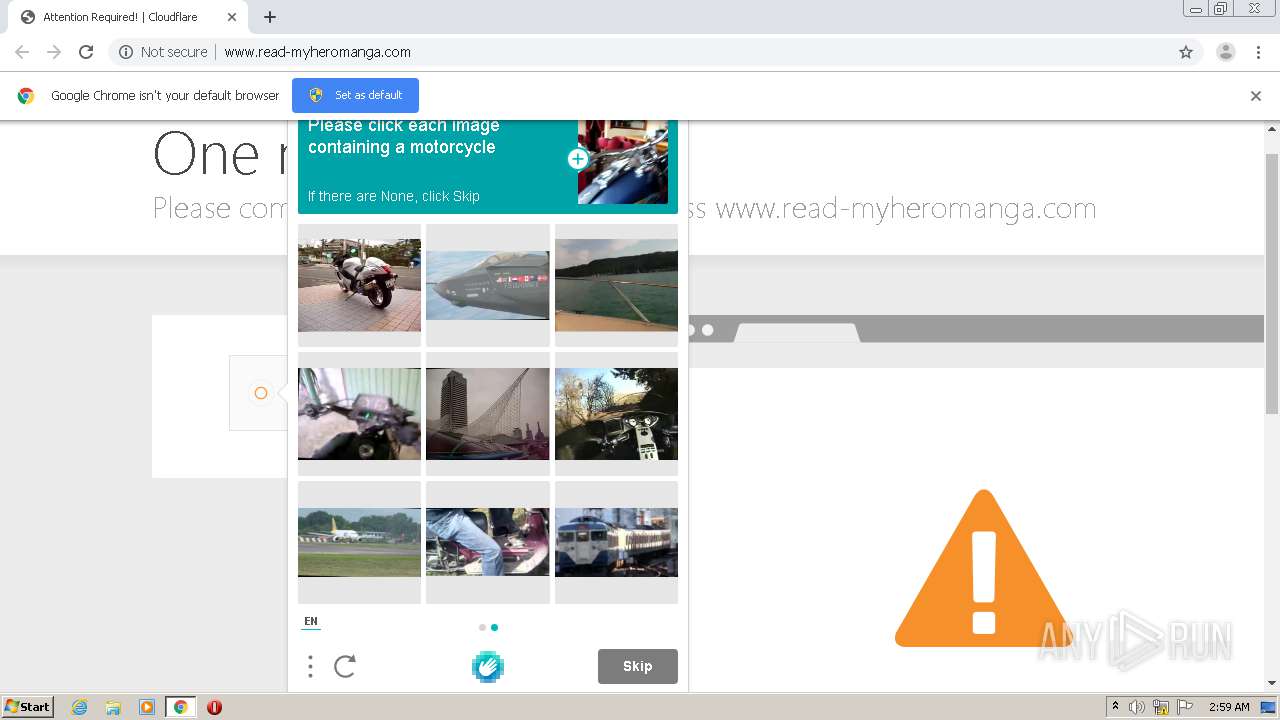
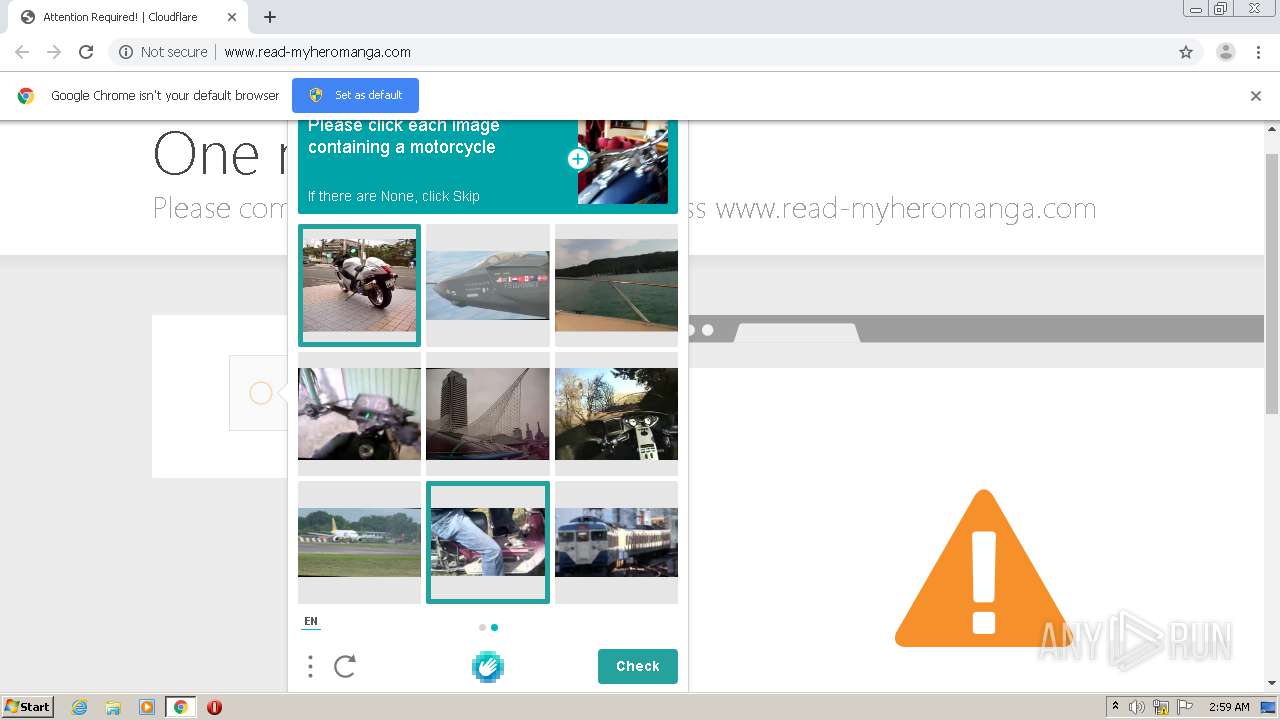
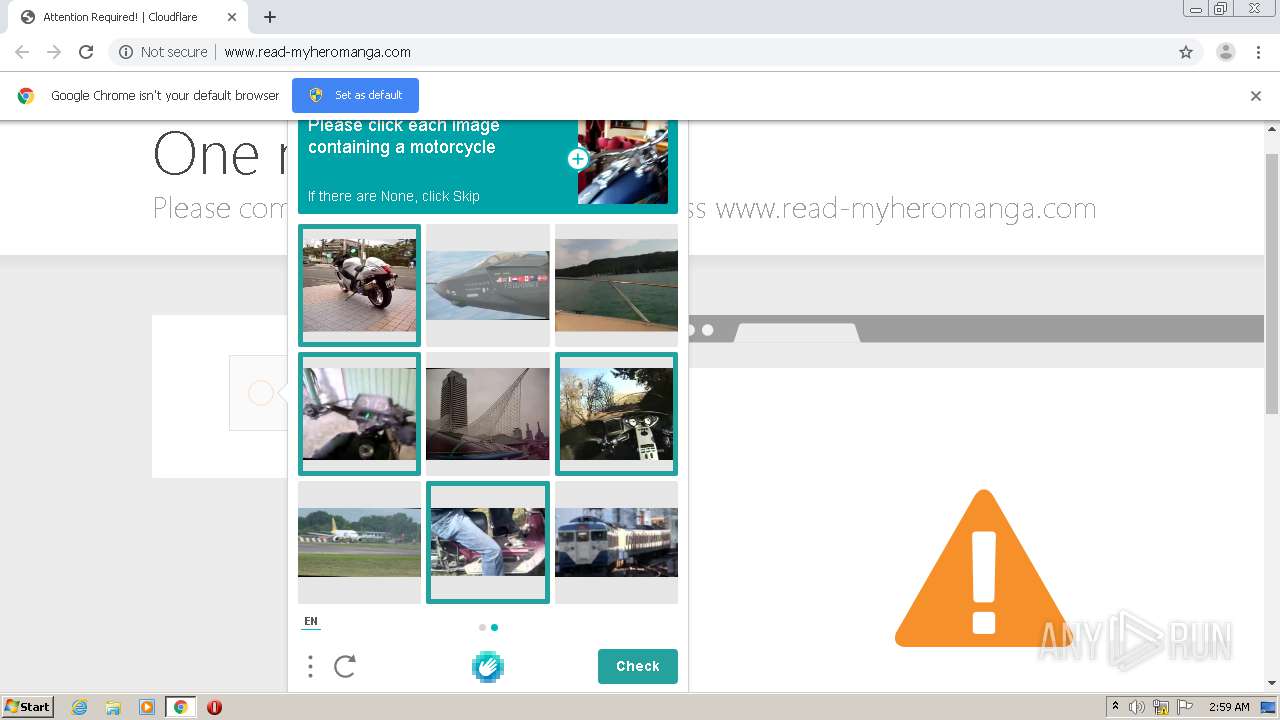
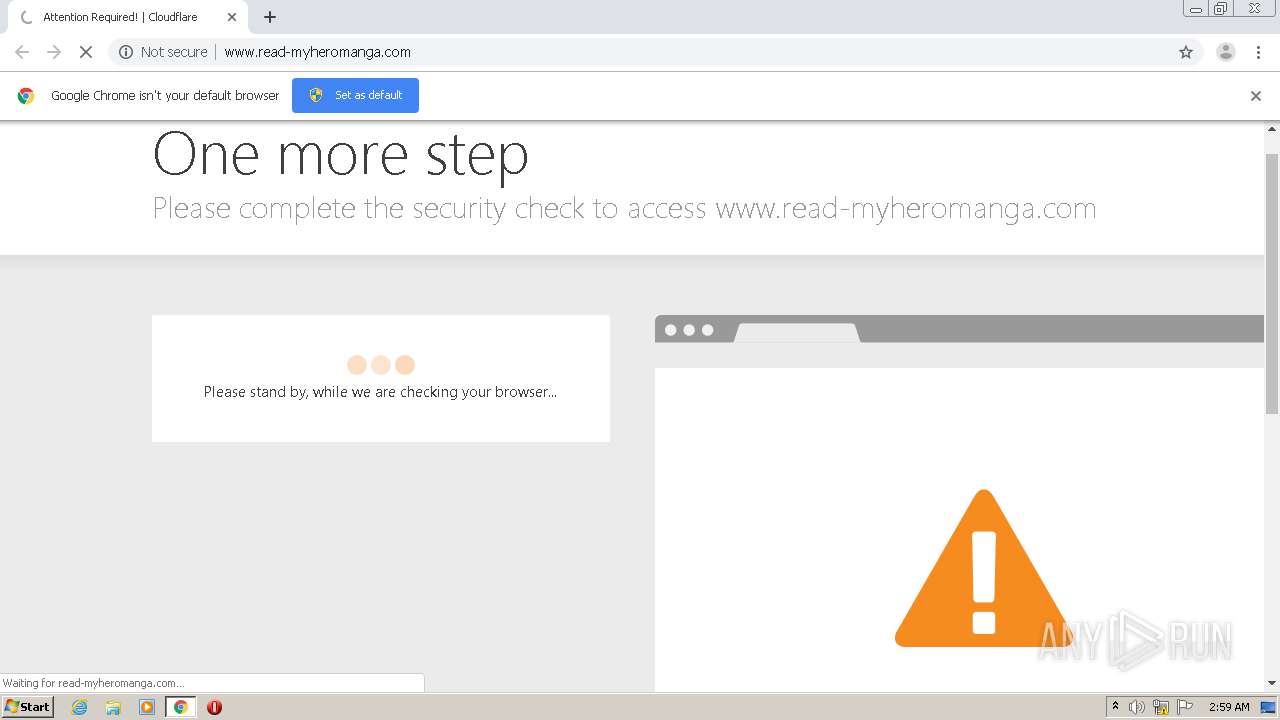
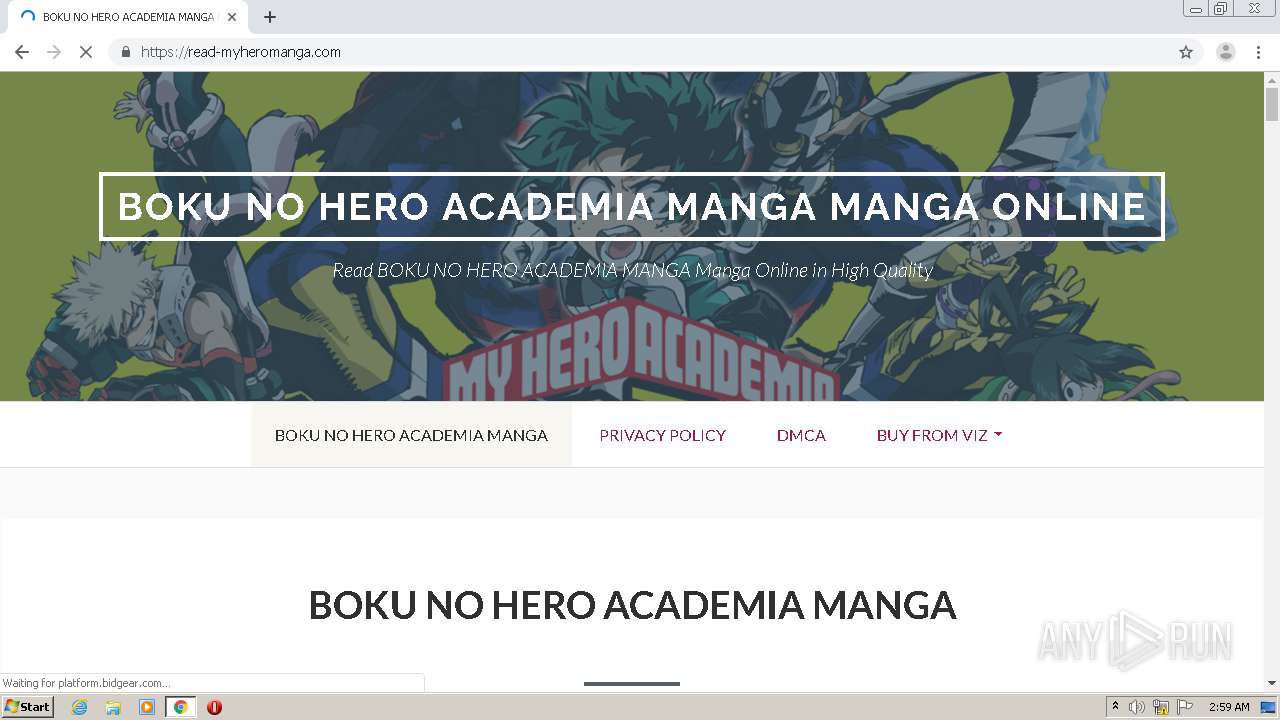
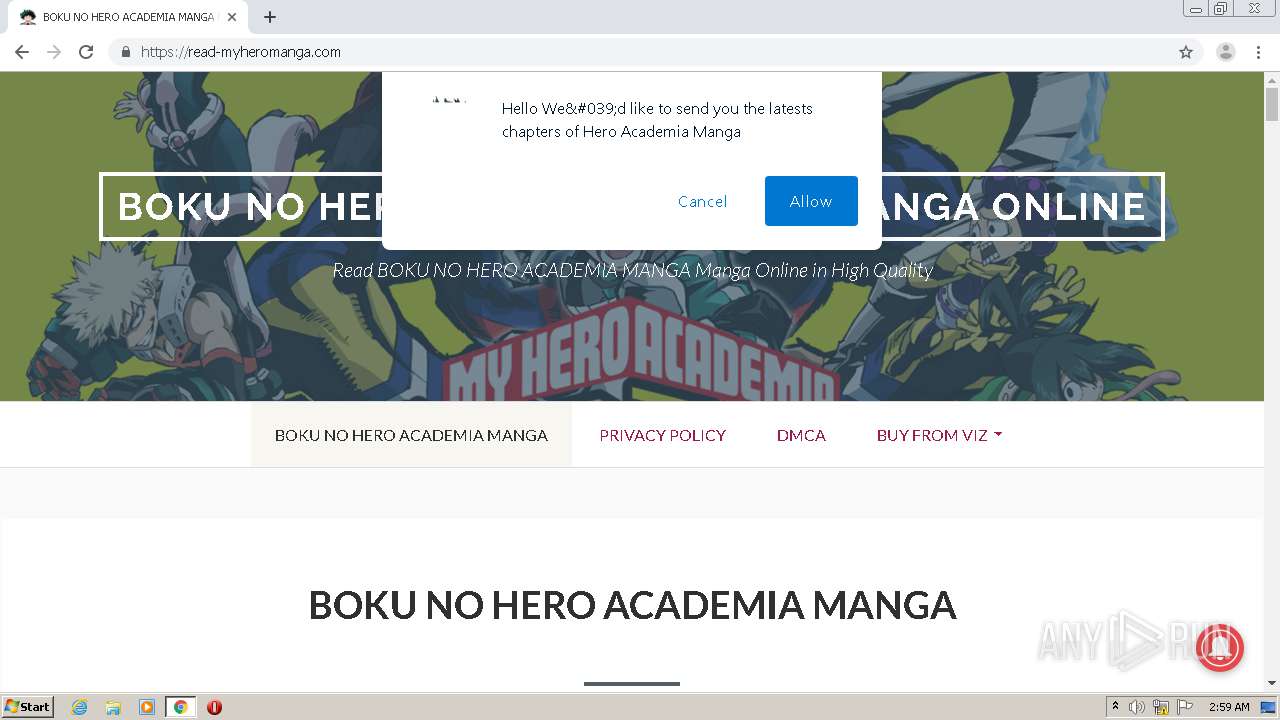
| URL: | http://www.read-myheromanga.com |
| Full analysis: | https://app.any.run/tasks/0990bbf9-414d-4165-8d90-b808545655f4 |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 02:58:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AF0F124ABAB9A0770D85956F01FE942C |
| SHA1: | 5D2C54B564BD4E59314EE40A7ED129125A986BCA |
| SHA256: | E648A6766CB6724F59BBDD3EAC962513E5F2E1ABF9D5D24AF0DC6E8B2AB95E7C |
| SSDEEP: | 3:N1KJS4QoWkeZI:Cc4Q/kiI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops a file with a compile date too recent
- chrome.exe (PID: 1168)
INFO
Reads the hosts file
- chrome.exe (PID: 1700)
- chrome.exe (PID: 1168)
Application launched itself
- chrome.exe (PID: 1168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
12
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://www.read-myheromanga.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4167830258203466410 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5863196136686764131 --mojo-platform-channel-handle=1404 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1536833659696099015 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14017008155035029811 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1540 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2260332909690171875 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6cc4a9d0,0x6cc4a9e0,0x6cc4a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14994052832516272259 --mojo-platform-channel-handle=2420 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,16360920075182319709,9993600982492634187,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2666115575838876945 --mojo-platform-channel-handle=3752 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
582
Read events
529
Write events
50
Delete events
3
Modification events
| (PID) Process: | (1168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1168-13251178742921375 |
Value: 259 | |||
| (PID) Process: | (1168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1168) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
34
Text files
79
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC45FF7-490.pma | — | |
MD5:— | SHA256:— | |||
| 1168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0a993b26-2444-4e6e-8397-777f234591fa.tmp | — | |
MD5:— | SHA256:— | |||
| 1168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF127855.TMP | text | |
MD5:— | SHA256:— | |||
| 1168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1277e7.TMP | text | |
MD5:— | SHA256:— | |||
| 1168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF127ab6.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
39
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1700 | chrome.exe | GET | 200 | 104.28.1.194:80 | http://www.read-myheromanga.com/cdn-cgi/styles/cf.errors.css | US | text | 4.32 Kb | shared |
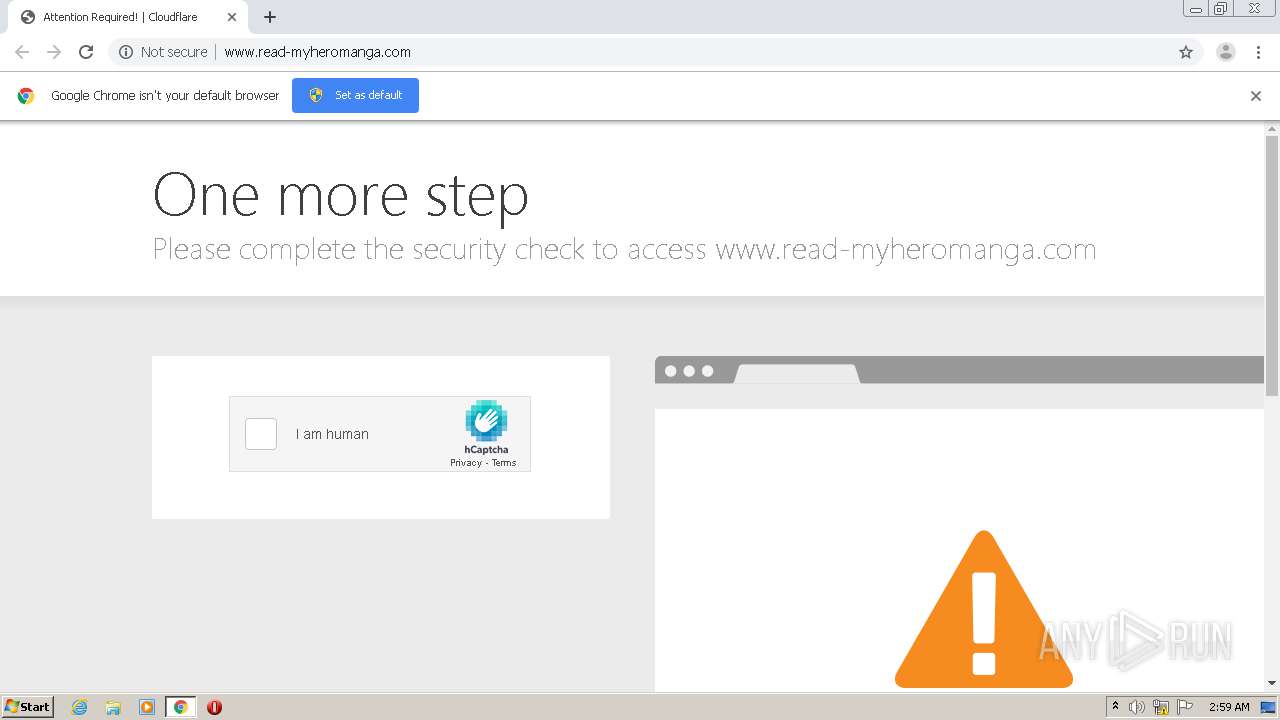
1700 | chrome.exe | GET | 200 | 104.28.1.194:80 | http://www.read-myheromanga.com/cdn-cgi/challenge-platform/h/g/orchestrate/captcha/v1 | US | text | 13.5 Kb | shared |
1700 | chrome.exe | GET | 301 | 104.28.1.194:80 | http://www.read-myheromanga.com/favicon.ico | US | html | 252 b | shared |
1700 | chrome.exe | GET | 403 | 104.28.1.194:80 | http://www.read-myheromanga.com/ | US | html | 5.25 Kb | shared |
1700 | chrome.exe | POST | 200 | 104.28.1.194:80 | http://www.read-myheromanga.com/cdn-cgi/challenge-platform/h/g/generate/ov1/0.9062973758848704:1606704104:5e5b7ef7627bce9beca99624485aab472ccc1e3d550162c1534bff47c941266f/5fa14f791b22162a/53d75b3eb63ae96 | US | binary | 1.87 Kb | shared |
1700 | chrome.exe | POST | 200 | 104.28.1.194:80 | http://www.read-myheromanga.com/cdn-cgi/challenge-platform/h/g/generate/ov1/0.9062973758848704:1606704104:5e5b7ef7627bce9beca99624485aab472ccc1e3d550162c1534bff47c941266f/5fa14f791b22162a/53d75b3eb63ae96 | US | binary | 6.89 Kb | shared |
1700 | chrome.exe | POST | 200 | 104.28.1.194:80 | http://www.read-myheromanga.com/cdn-cgi/challenge-platform/h/g/generate/ov1/0.9062973758848704:1606704104:5e5b7ef7627bce9beca99624485aab472ccc1e3d550162c1534bff47c941266f/5fa14f791b22162a/53d75b3eb63ae96 | US | binary | 1.09 Kb | shared |
1700 | chrome.exe | POST | 301 | 104.28.1.194:80 | http://www.read-myheromanga.com/?__cf_chl_captcha_tk__=44e900d4cfbd6aadb6575a5dc5e6774d24942e5c-1606705145-0-ASoN8wNtMKk-hqKBdy1Bb-BwxBtgUV8U2DYmNmTB8r7V8mMM58fevNB_wgqtDujwOZ2bMihjER4ER5VpqE3mWfPwPM7ej1U0p4HlqpBZyFlZBc5dKtH8JmQT9i-YkqHCGZVGdKb49yKBW3EloJK8W-571GN5mGMyMpJaEWa0oOTKyjDCC0XAPFq2Pdy1pQ2cEHDPiiJw-cWne2mZTXfdhgiOfY_N6uBVHxAM0e-Y19guA0QIQNQ7qmG0NxsUH9jW8ysVuNQd3HsNOgBx7cIT3tDON5lTYocx2G7-ZI0SD_Fg3lmGCUa-pjHUlJUGIxqwndUph-jUBnIgk85SUiLtJvtSmMdDLDa7PuDQSW6b37CcP5h6ya_0T9KWUwAI9XttThcpfwxoK9oLFetd-jpV-g-zCBE_O-2JXnfrmOWWMx5uN2jPv2o0dmlmCUXL2M_TNBOaQJ1GasIJ4Sp5cDBEIYhQ-G1JDMCoTtwuJ75vj6Cu8yVbxCfwJQPZ_rXul77LOkG7T9ohfE2ahmaSLIaVzNS7A1bHjiXuN86TCMc9JP31 | US | html | 241 b | shared |
1700 | chrome.exe | GET | 200 | 104.28.1.194:80 | http://www.read-myheromanga.com/cdn-cgi/images/trace/captcha/nojs/h/transparent.gif?ray=5fa14f791b22162a | US | image | 42 b | shared |
1700 | chrome.exe | GET | 200 | 104.28.1.194:80 | http://www.read-myheromanga.com/cdn-cgi/images/cf-no-screenshot-warn.png | US | image | 2.53 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.28.1.194:80 | www.read-myheromanga.com | Cloudflare Inc | US | shared |
1700 | chrome.exe | 104.28.1.194:80 | www.read-myheromanga.com | Cloudflare Inc | US | shared |
1700 | chrome.exe | 104.28.1.194:443 | www.read-myheromanga.com | Cloudflare Inc | US | shared |
1700 | chrome.exe | 172.217.18.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 172.67.174.68:443 | read-myheromanga.com | — | US | unknown |
1700 | chrome.exe | 172.217.18.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 216.58.204.136:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 216.58.213.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1700 | chrome.exe | 35.190.55.95:443 | www.onclickperformance.com | Google Inc. | US | unknown |
1700 | chrome.exe | 172.67.74.36:443 | platform.bidgear.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.read-myheromanga.com |
| unknown |
accounts.google.com |
| shared |
chrome.google.com |
| whitelisted |
purpleisp.net |
| malicious |
www.cloudflare.com |
| whitelisted |
hcaptcha.com |
| whitelisted |
assets.hcaptcha.com |
| whitelisted |
clients1.google.com |
| whitelisted |
read-myheromanga.com |
| unknown |
ssl.gstatic.com |
| whitelisted |