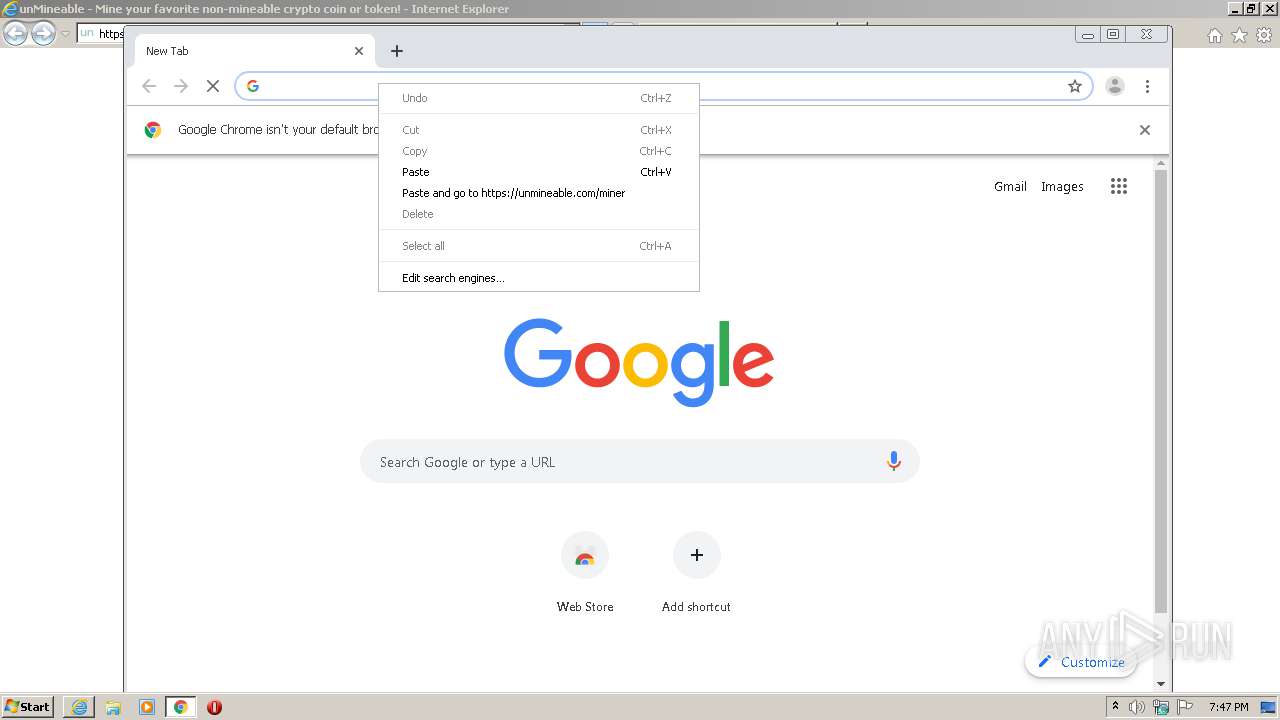
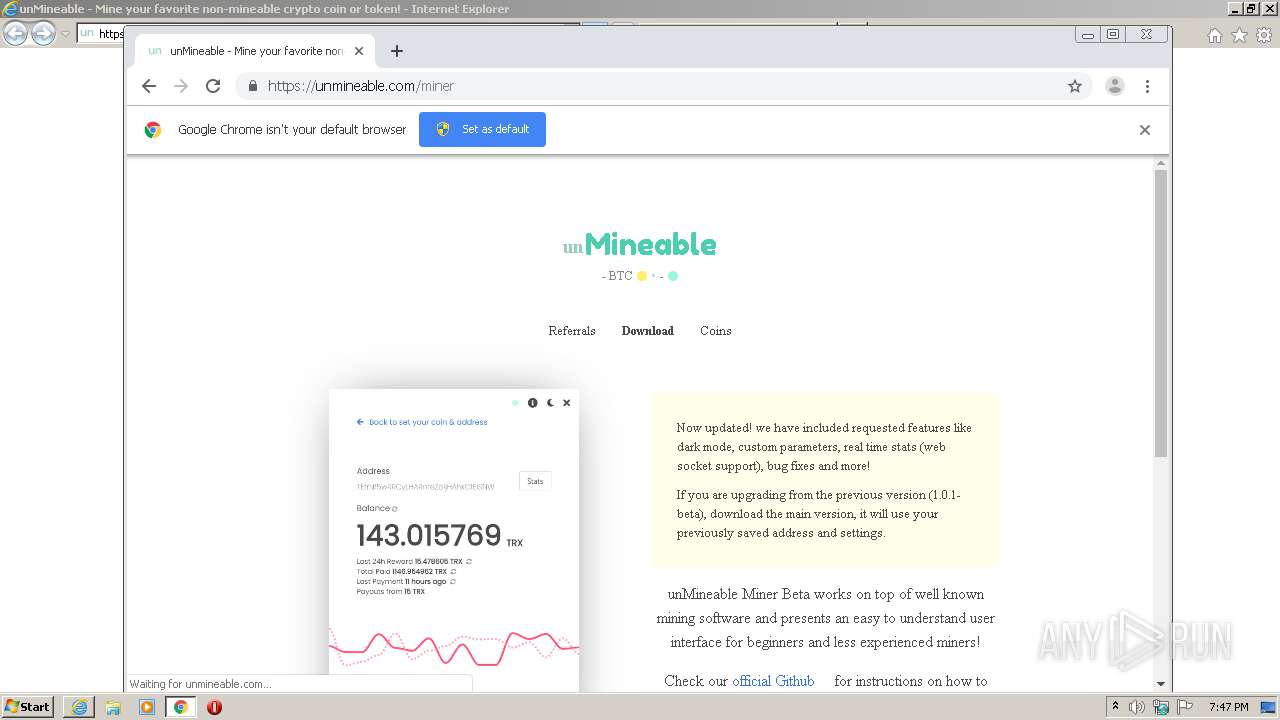
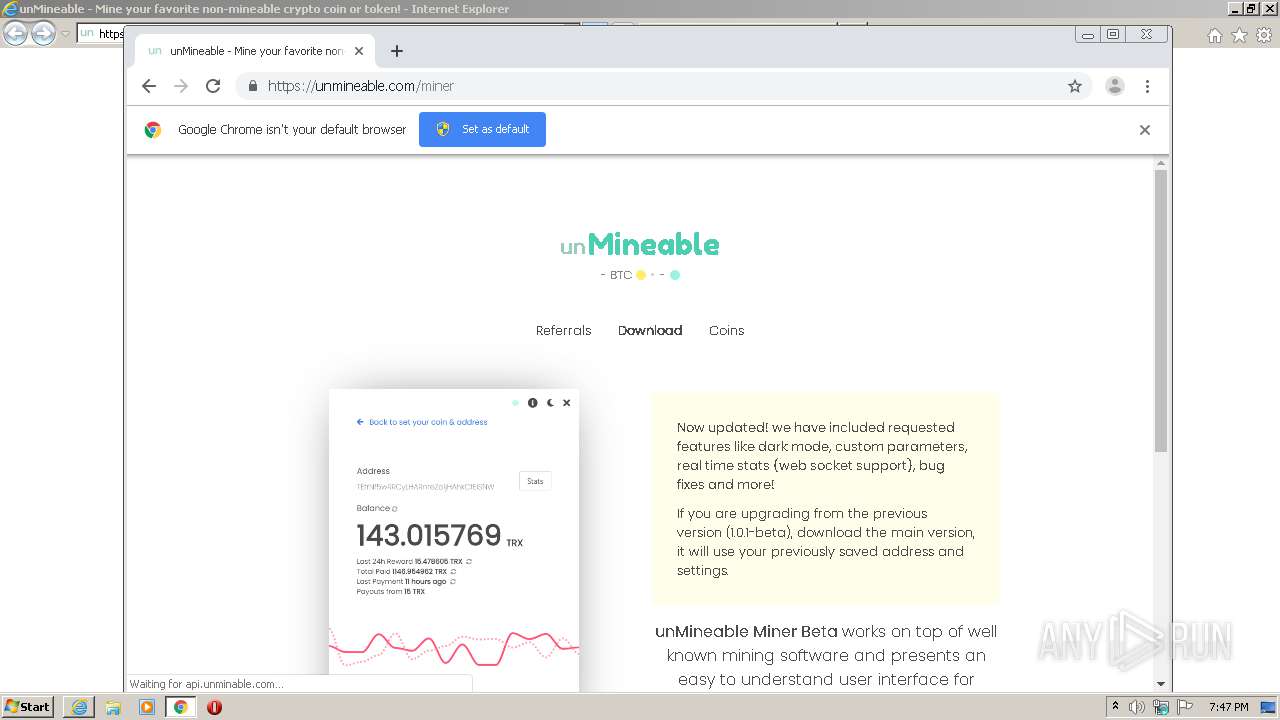
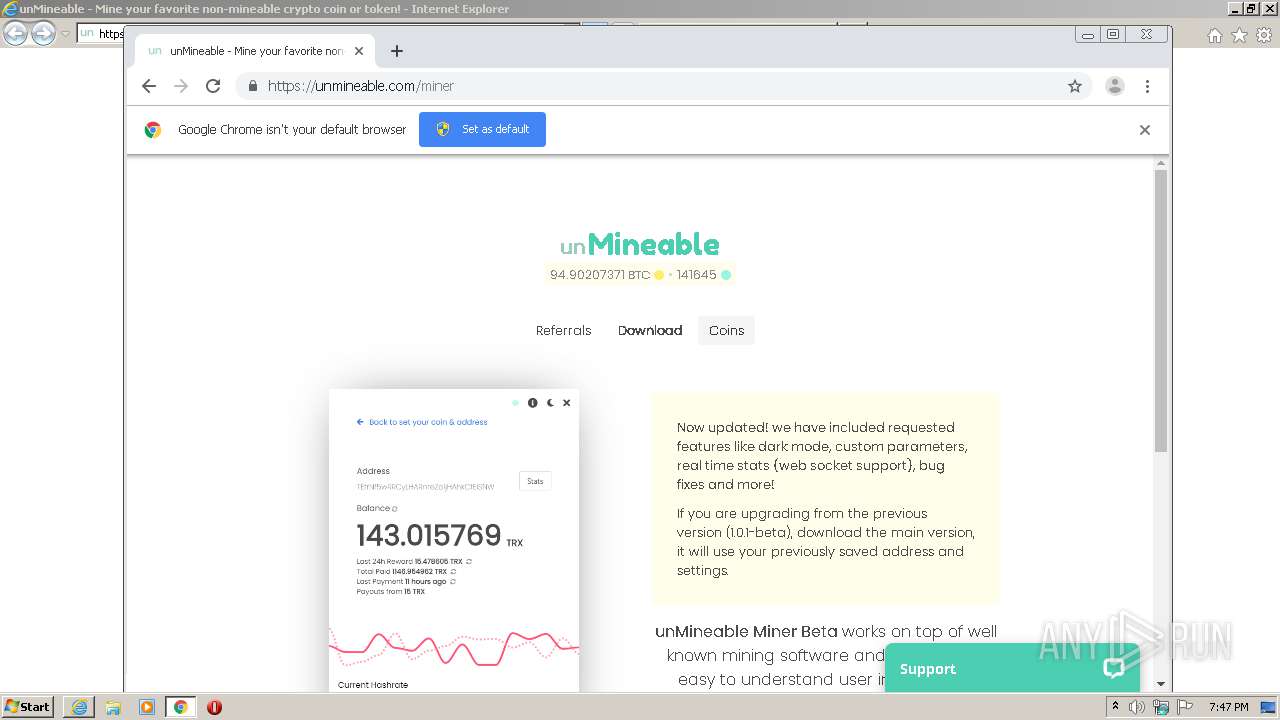
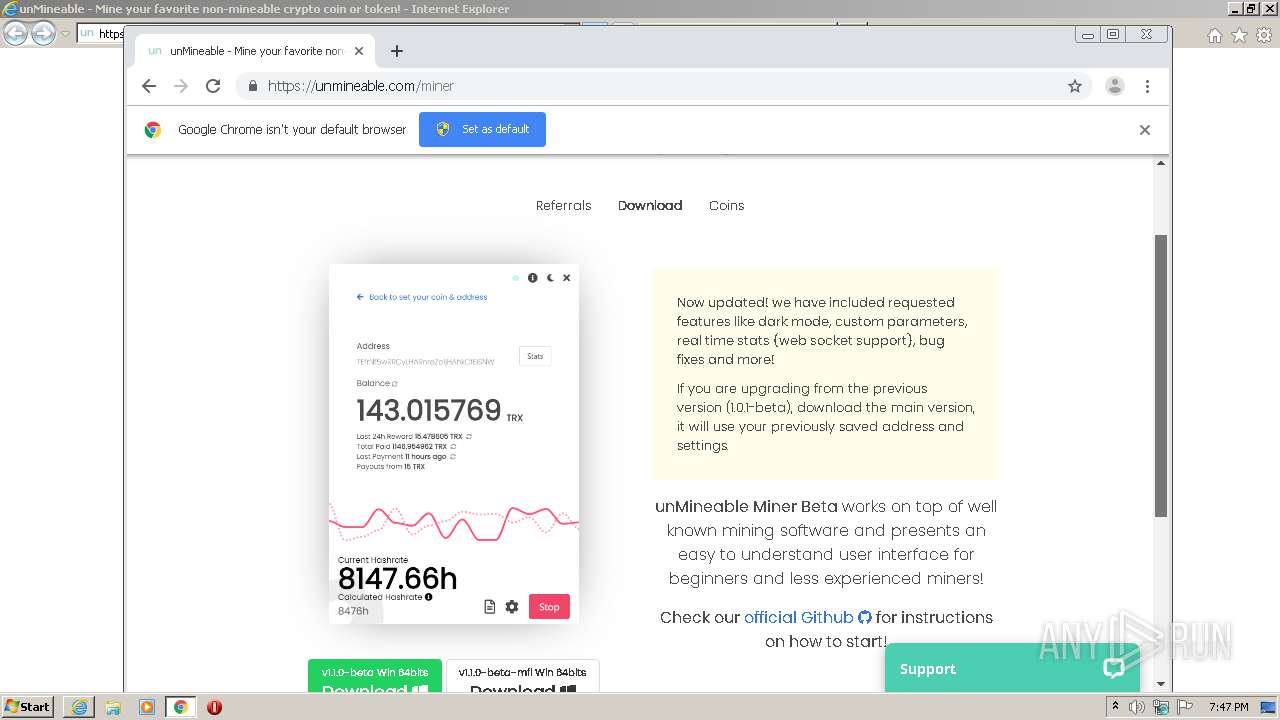
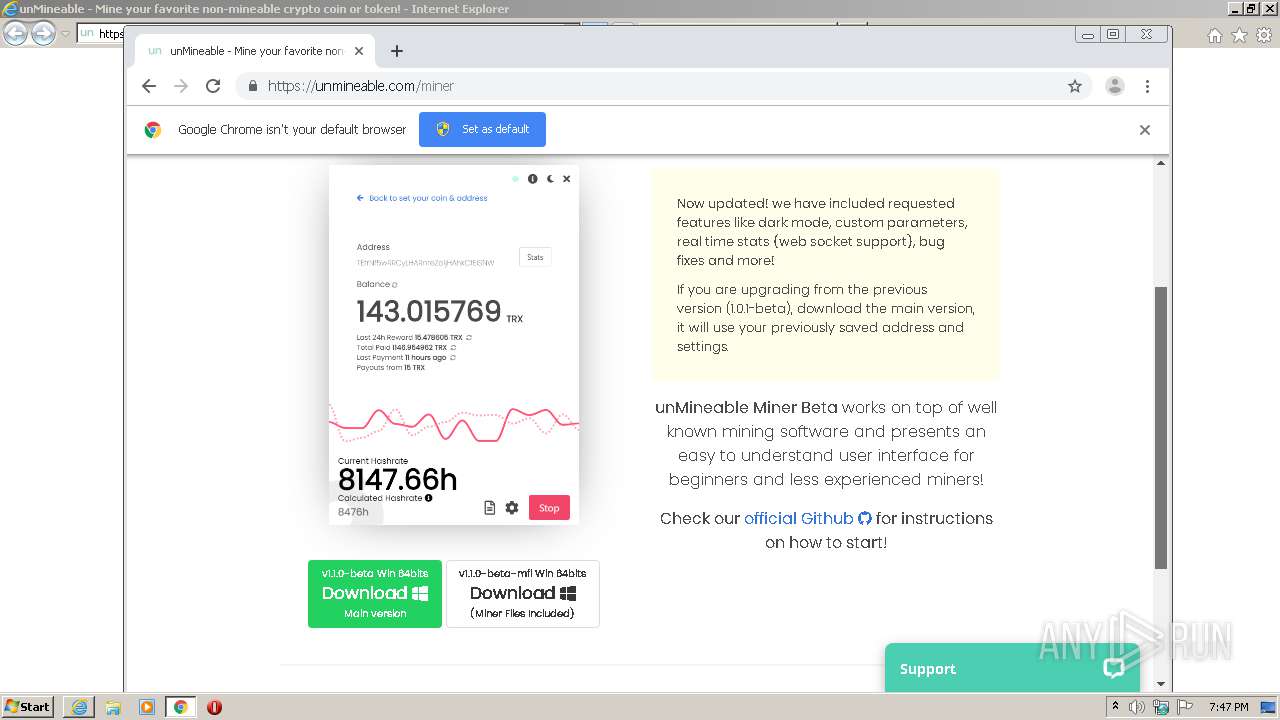
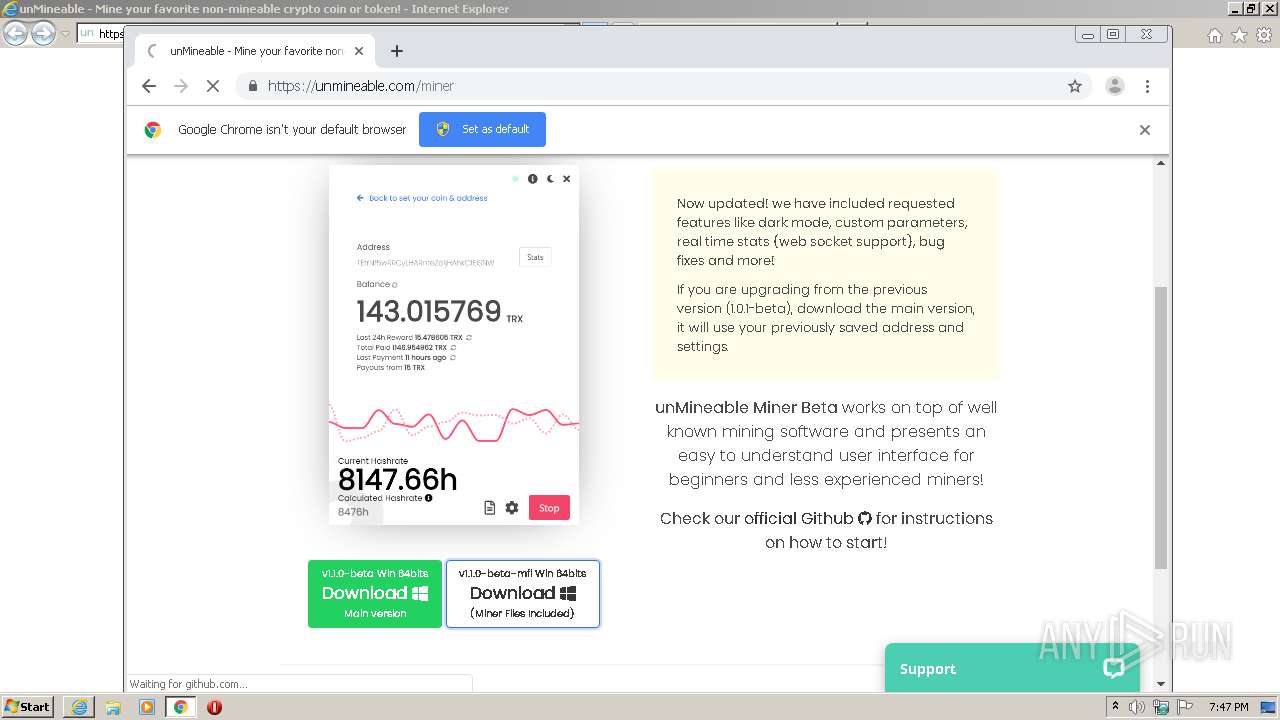
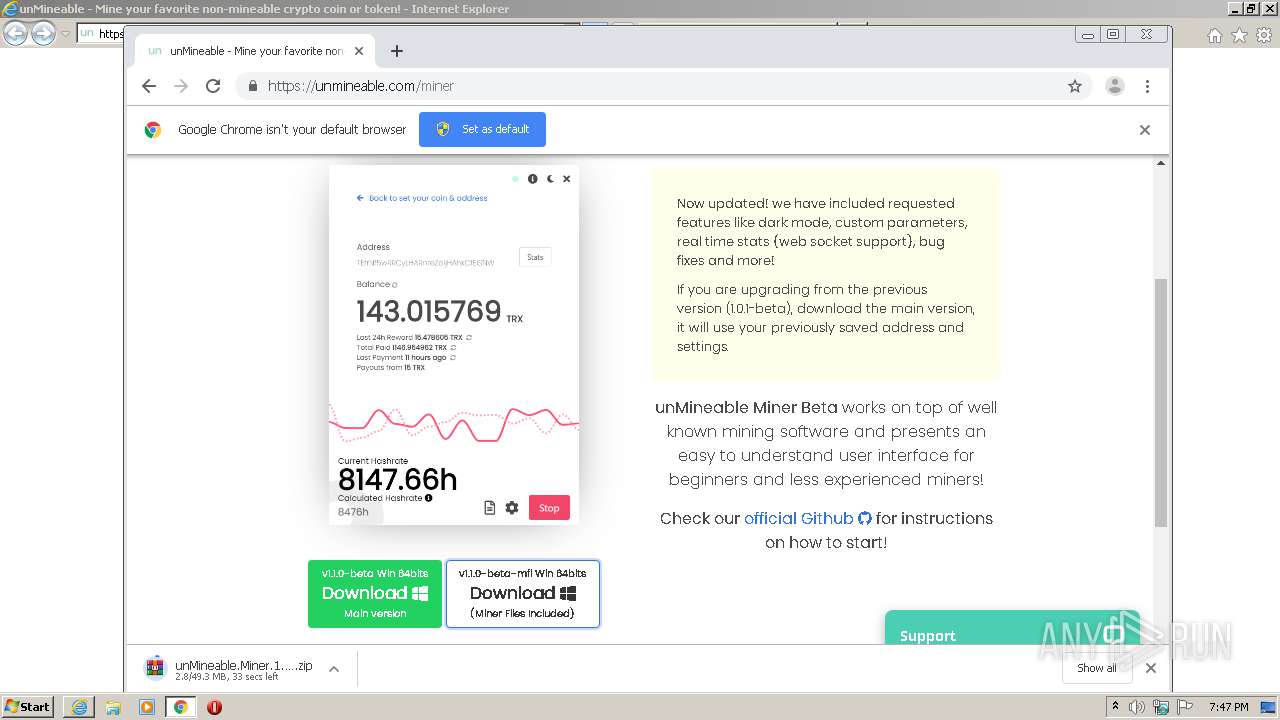
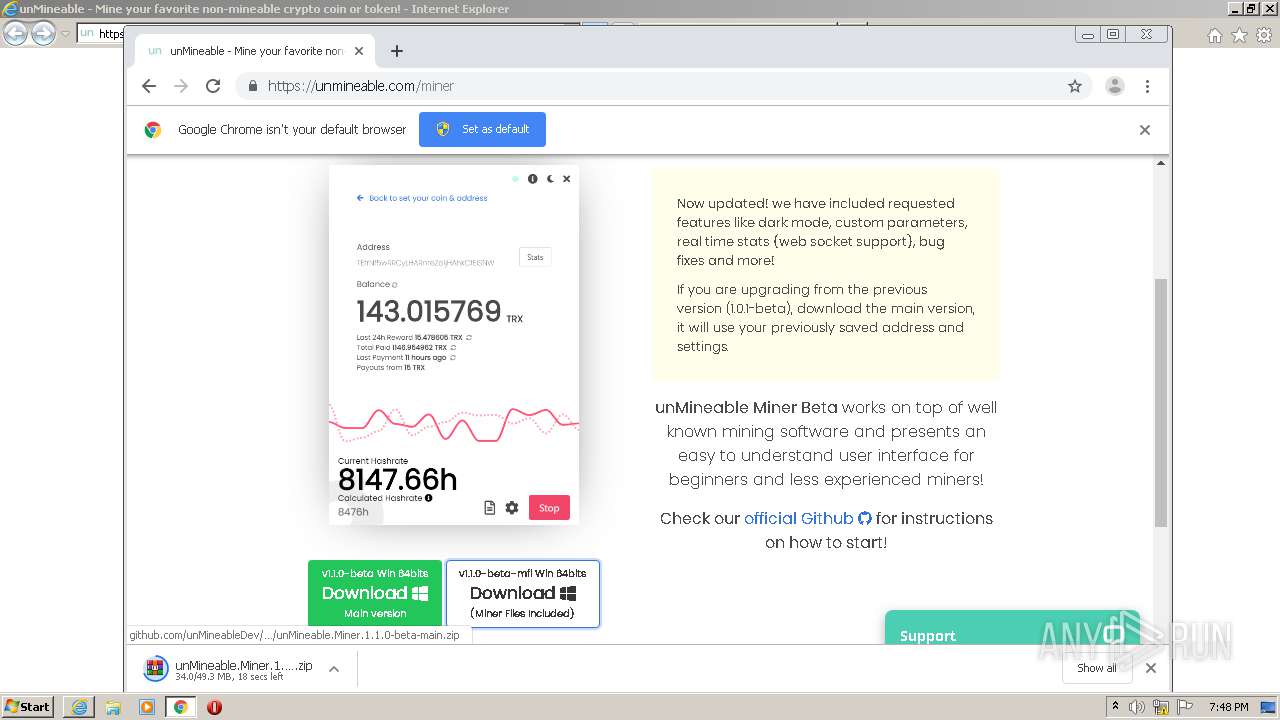
| URL: | https://unmineable.com/miner |
| Full analysis: | https://app.any.run/tasks/77aa1185-a6aa-4042-b179-6feb18da70fd |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2021, 18:46:27 |
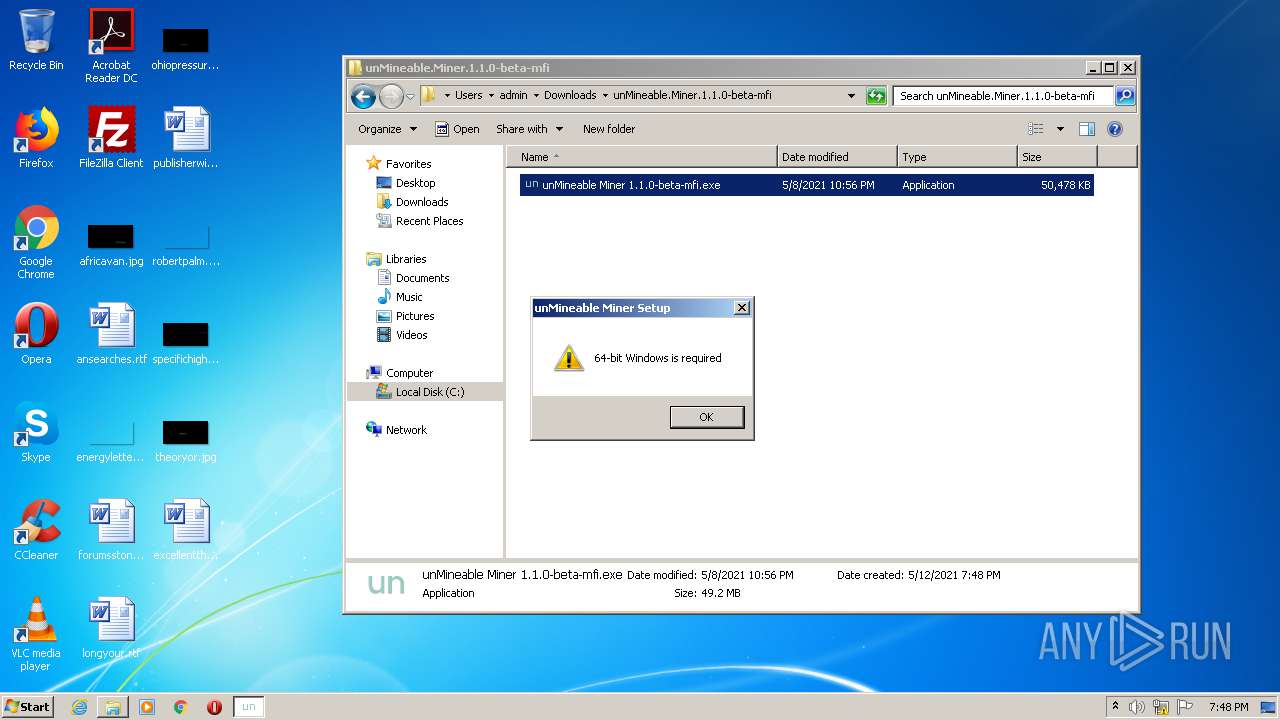
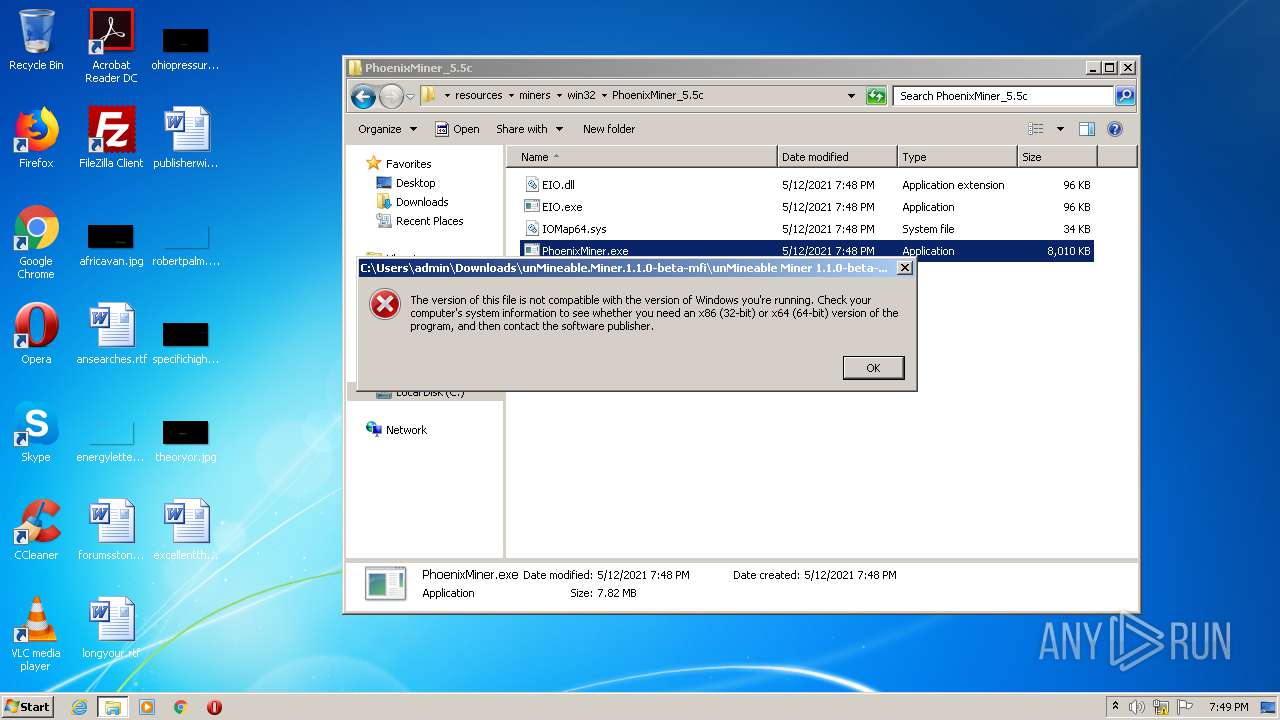
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A06C116B4798E3061F6A16590582CCDE |
| SHA1: | F266B06EE585561C6F2DA66391B006A707C5897D |
| SHA256: | E633C2345AB7BAE33E0C4E0F4E26F55154FDF138A9C334402772F588188F9A0C |
| SSDEEP: | 3:N8xKAifz:2Vqz |
MALICIOUS
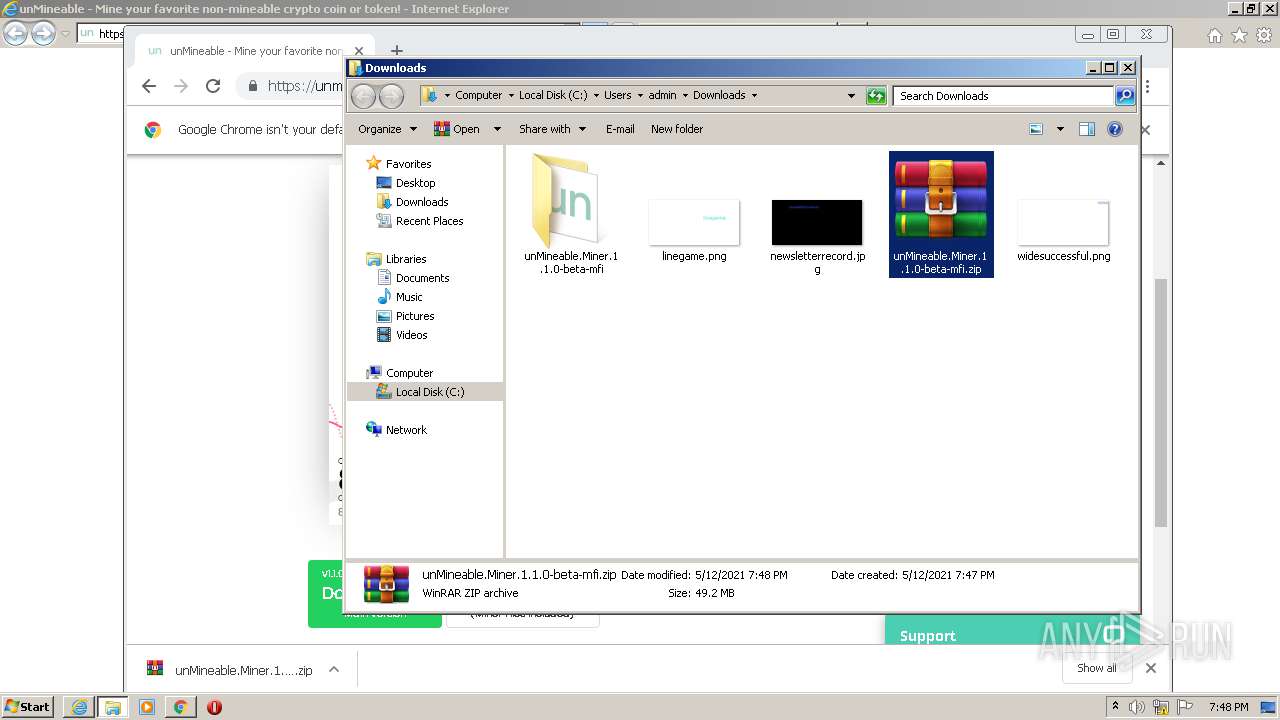
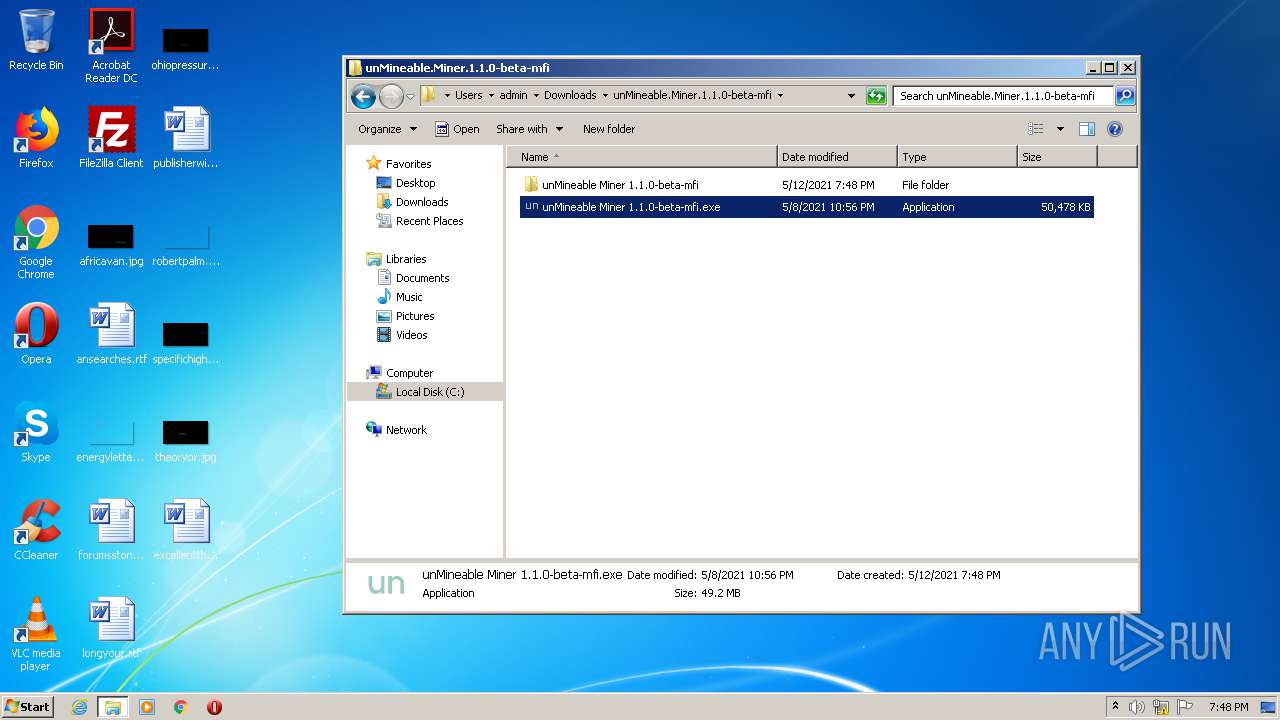
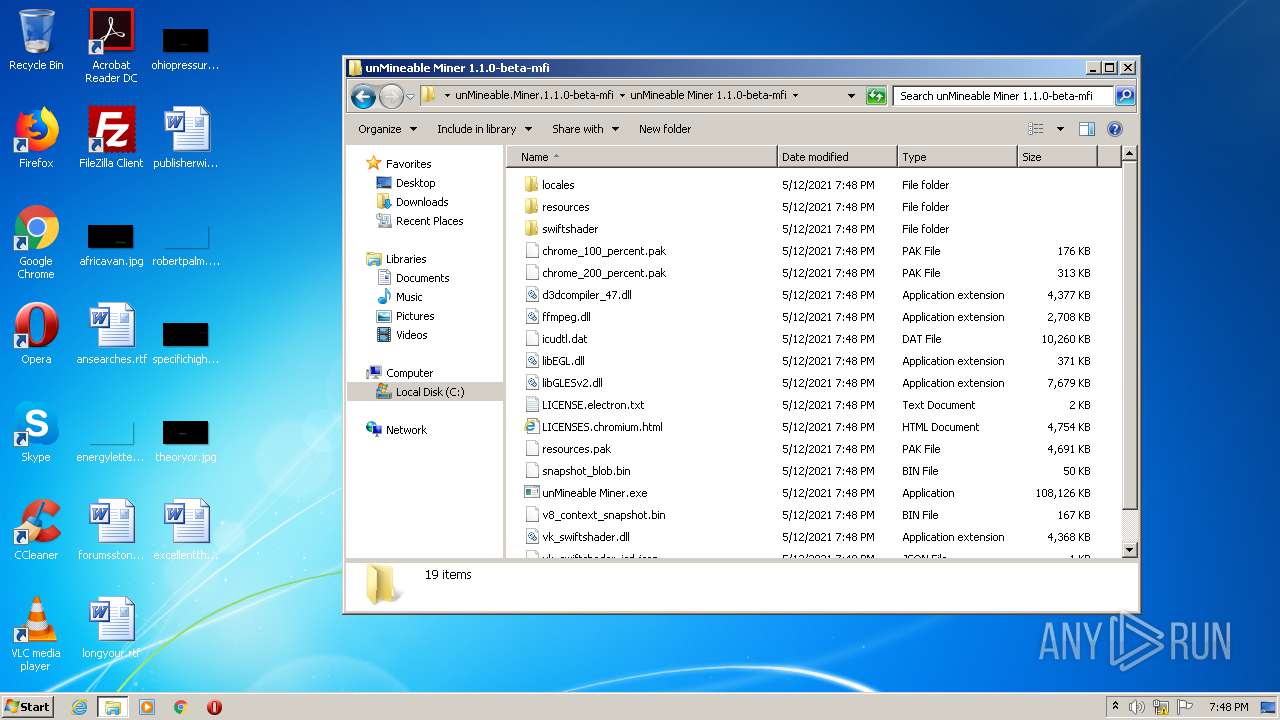
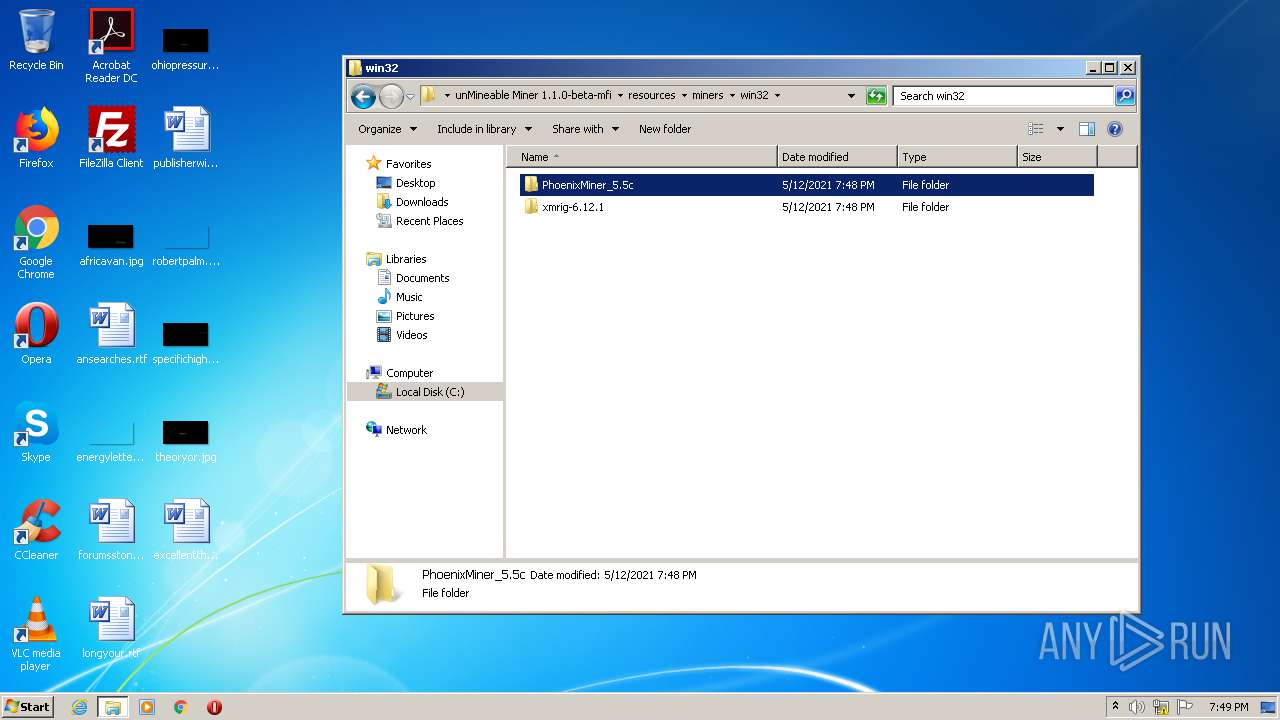
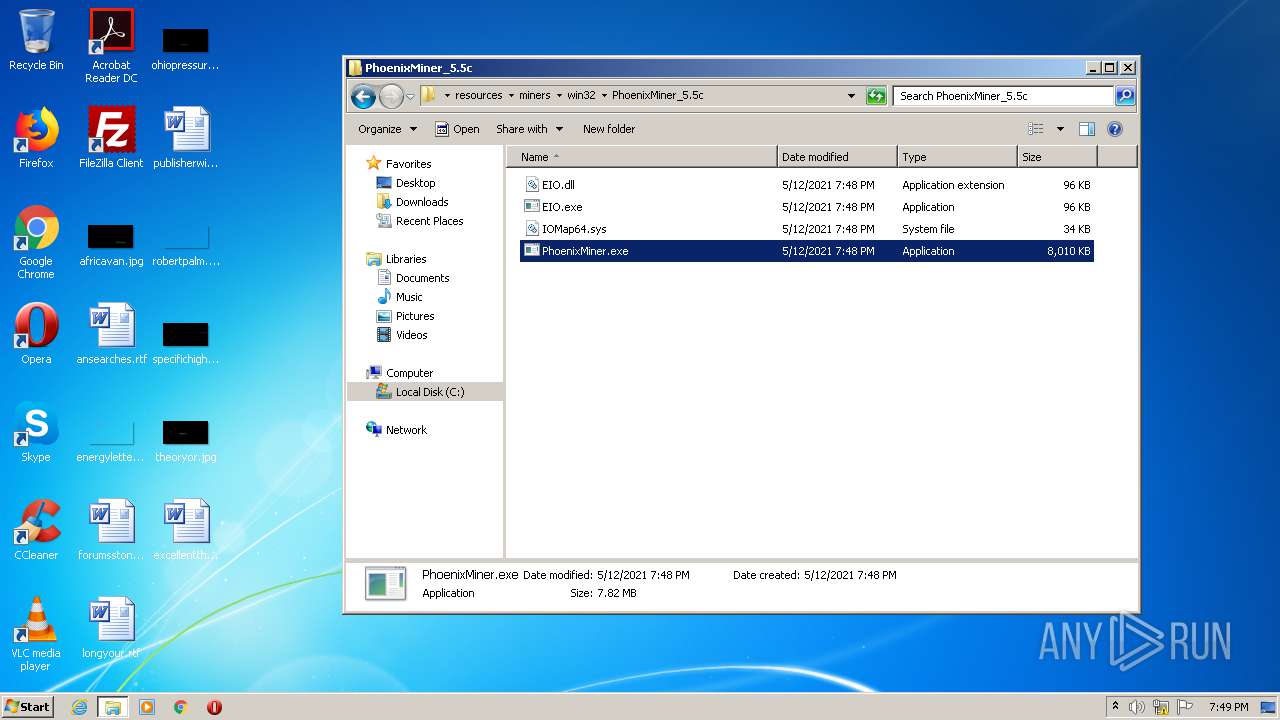
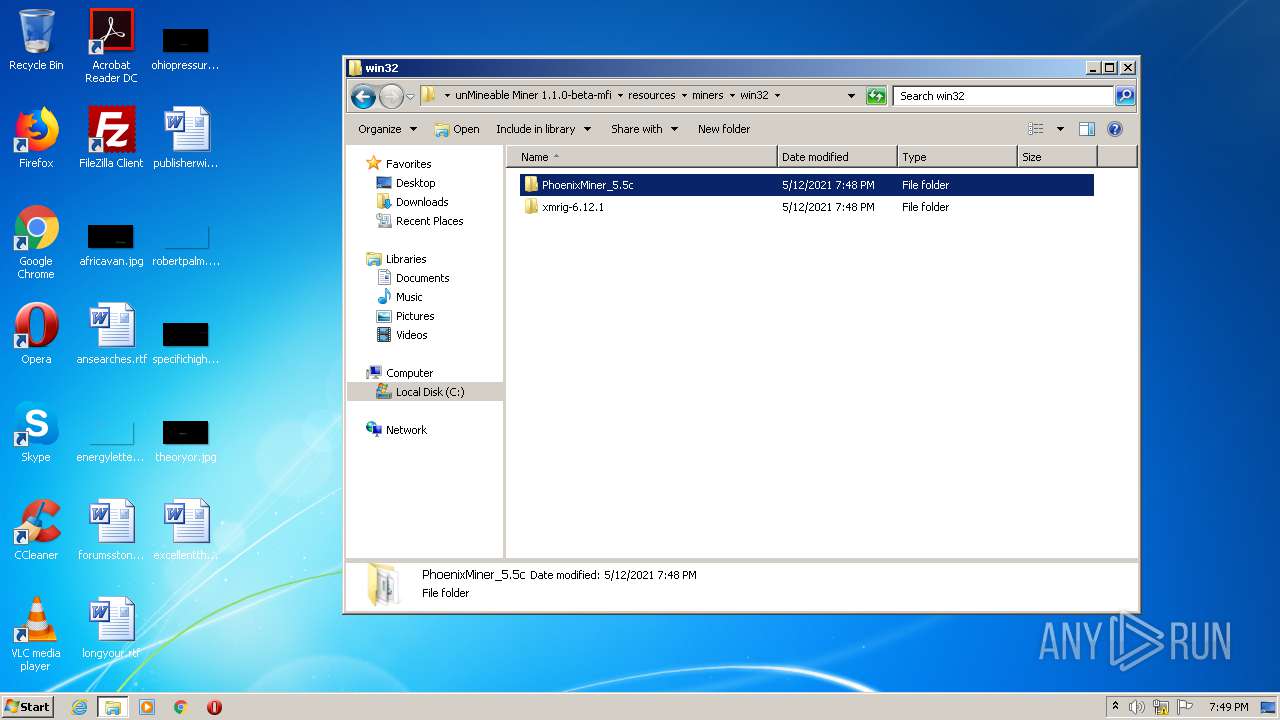
Drops executable file immediately after starts
- unMineable Miner 1.1.0-beta-mfi.exe (PID: 3104)
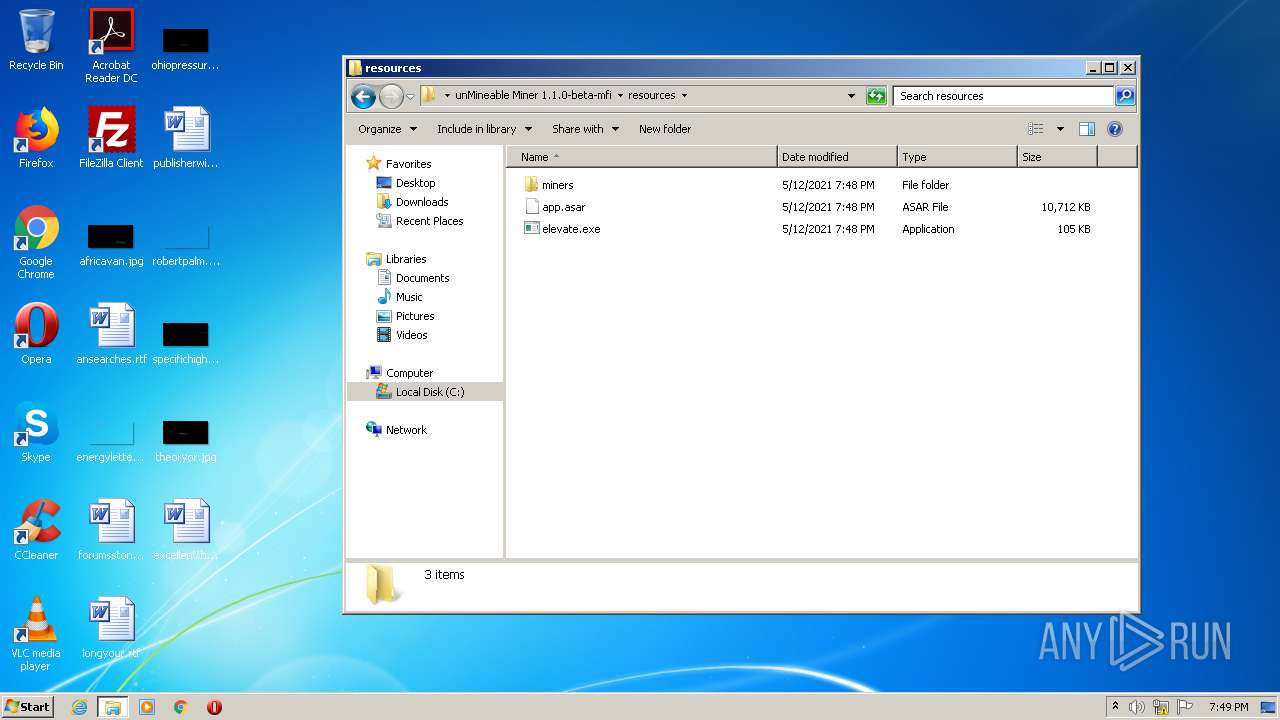
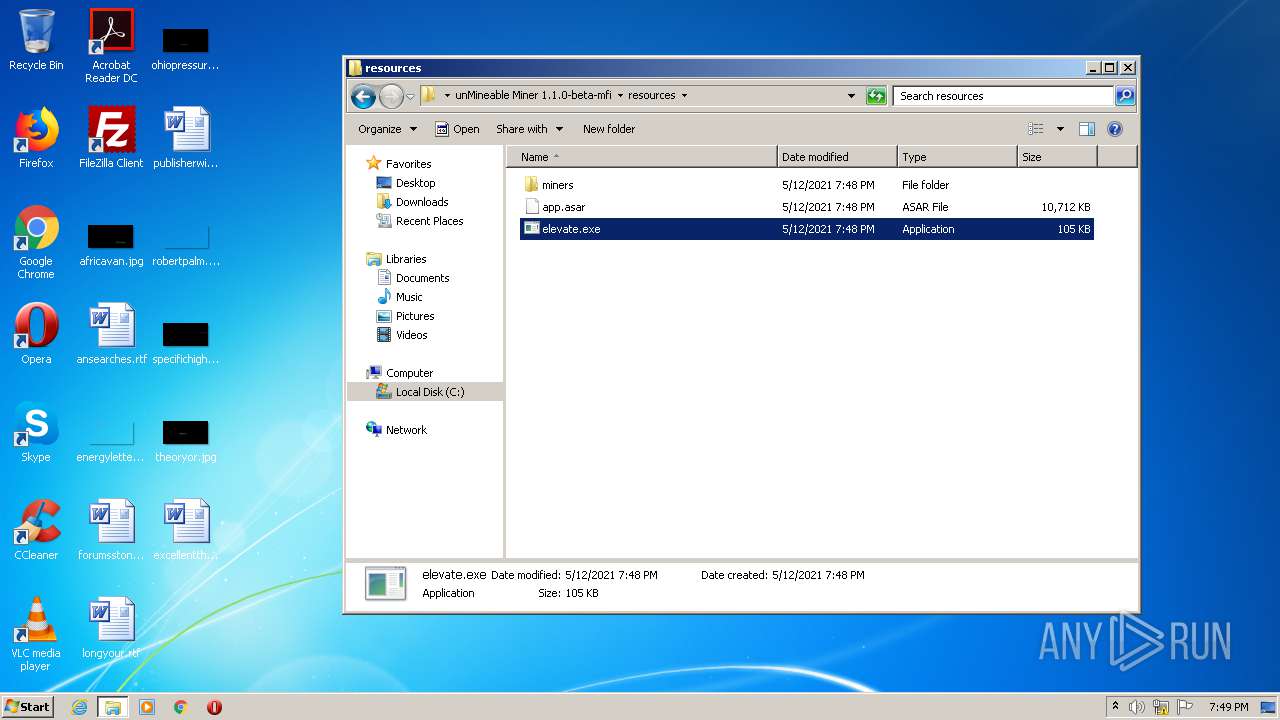
Application was dropped or rewritten from another process
- elevate.exe (PID: 1500)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2636)
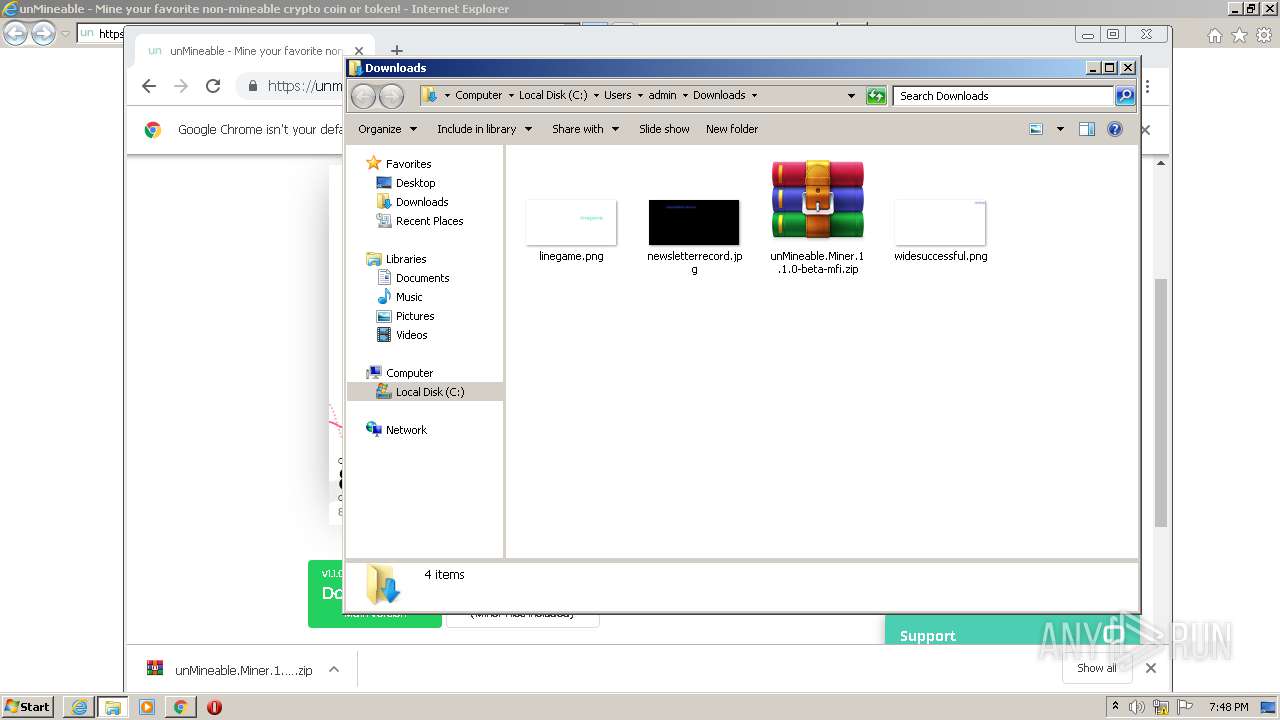
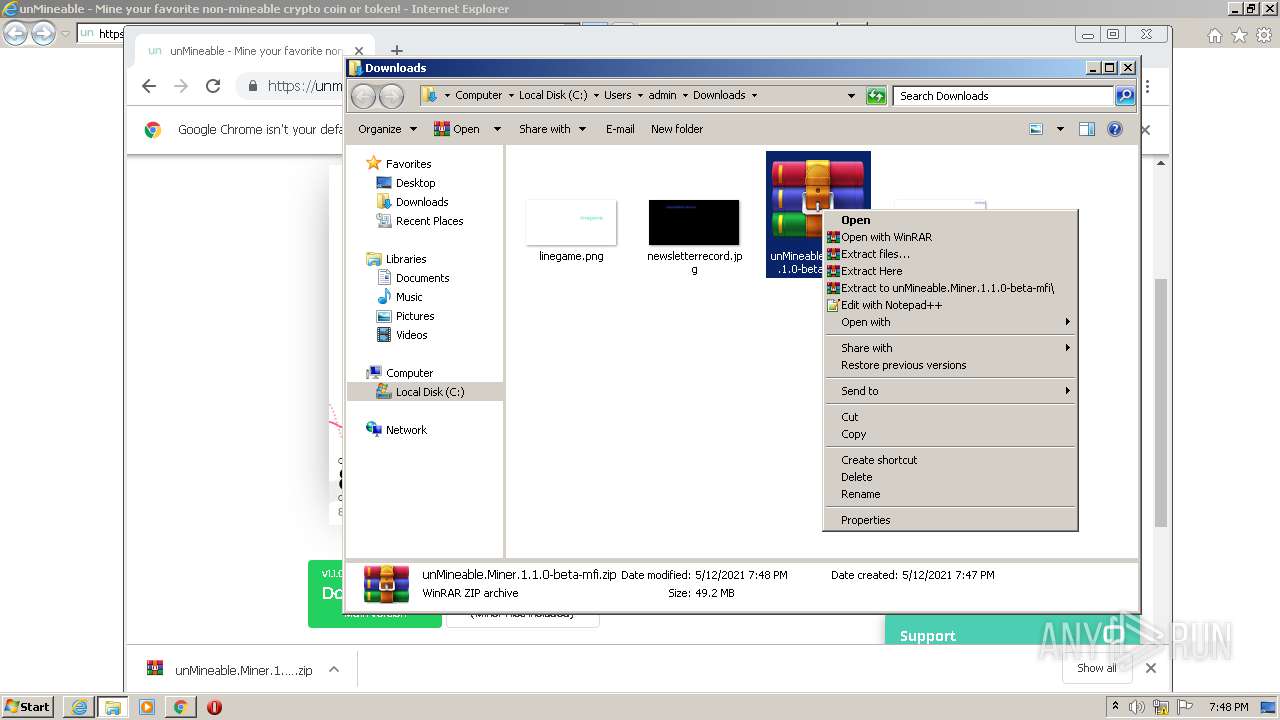
Drops a file with too old compile date
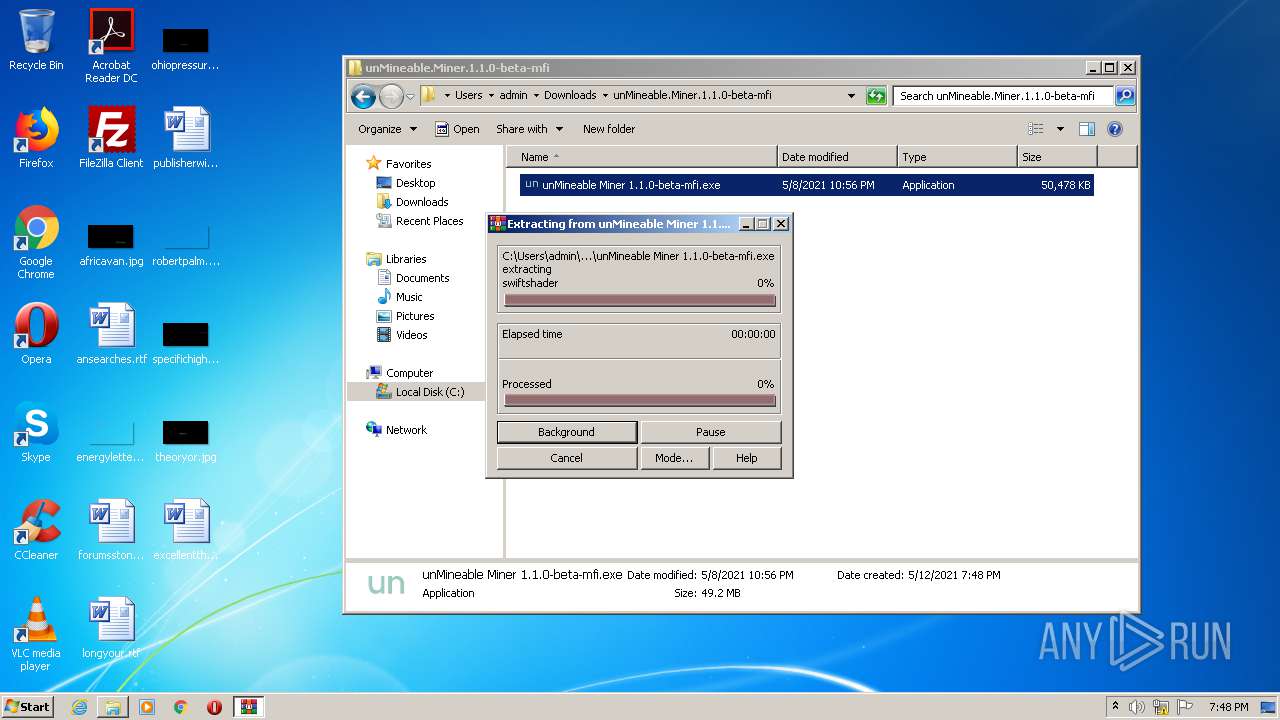
- WinRAR.exe (PID: 3336)
Executable content was dropped or overwritten
- unMineable Miner 1.1.0-beta-mfi.exe (PID: 3104)
- WinRAR.exe (PID: 3336)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3336)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3336)
INFO
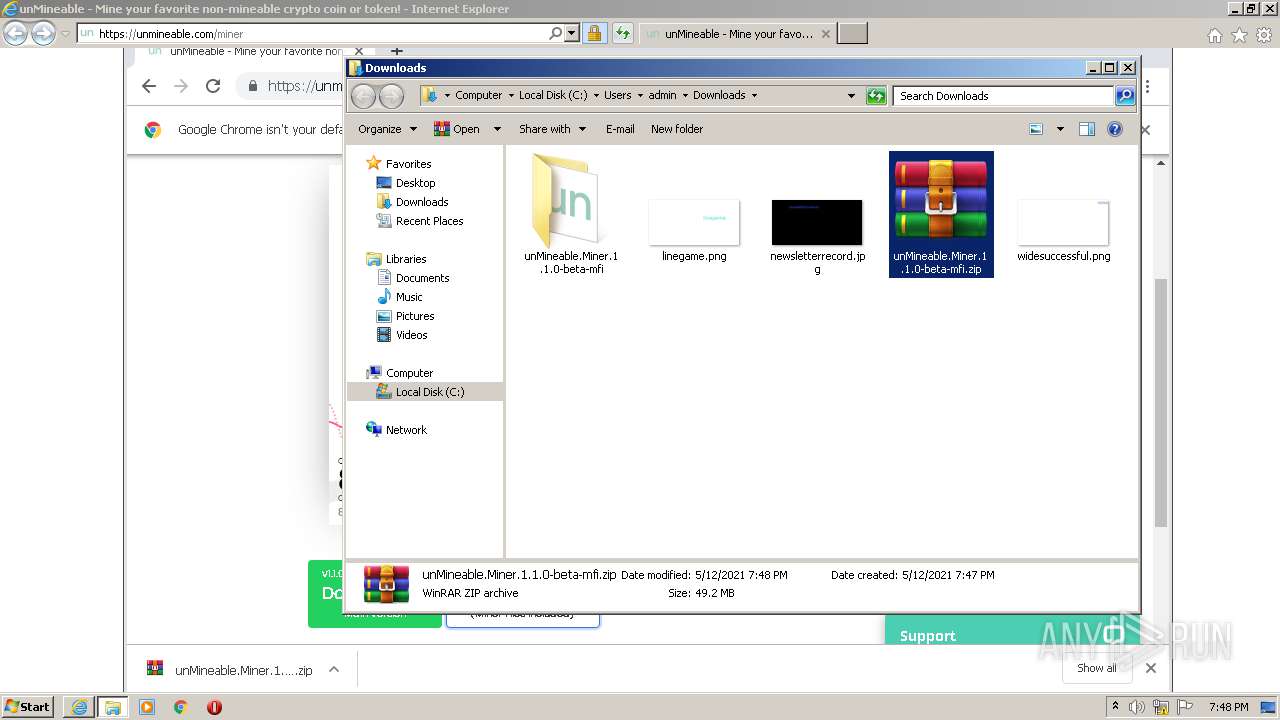
Changes internet zones settings
- iexplore.exe (PID: 3500)
Reads settings of System Certificates
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 3500)
Application launched itself
- iexplore.exe (PID: 3500)
- chrome.exe (PID: 2636)
Changes settings of System certificates
- iexplore.exe (PID: 3500)
Reads the hosts file
- chrome.exe (PID: 2636)
- chrome.exe (PID: 1788)
Creates files in the user directory
- iexplore.exe (PID: 3500)
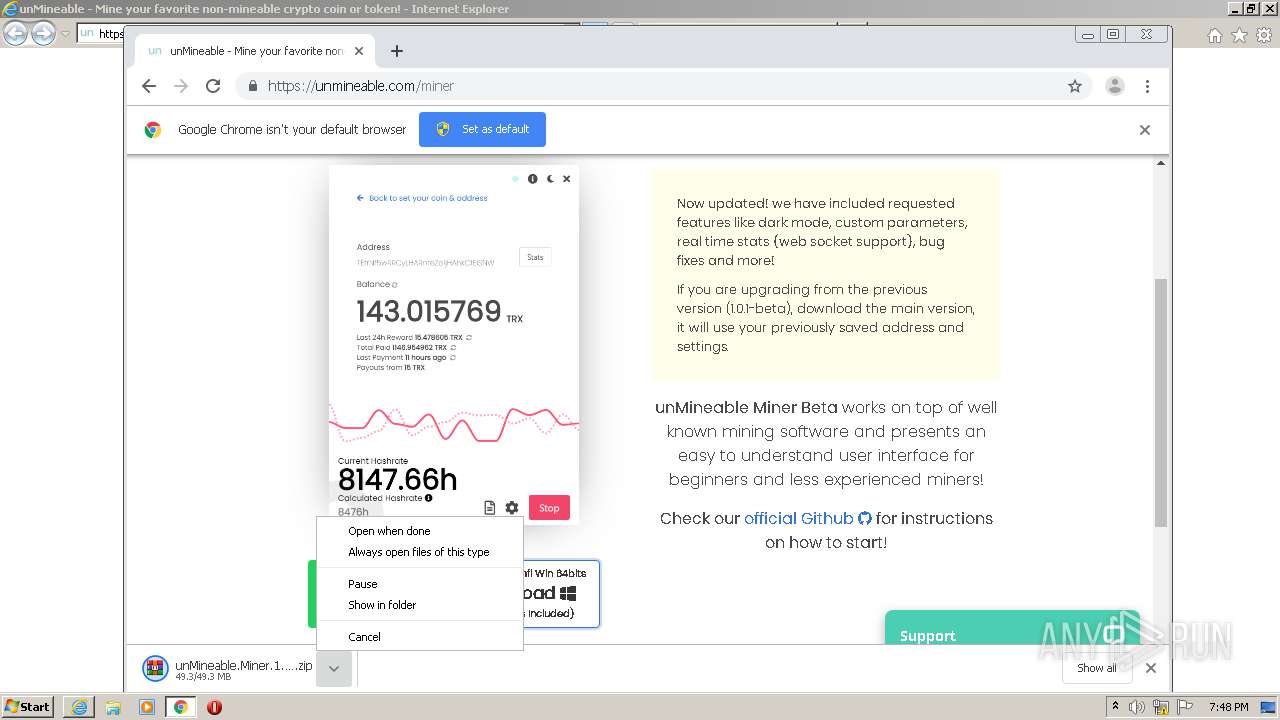
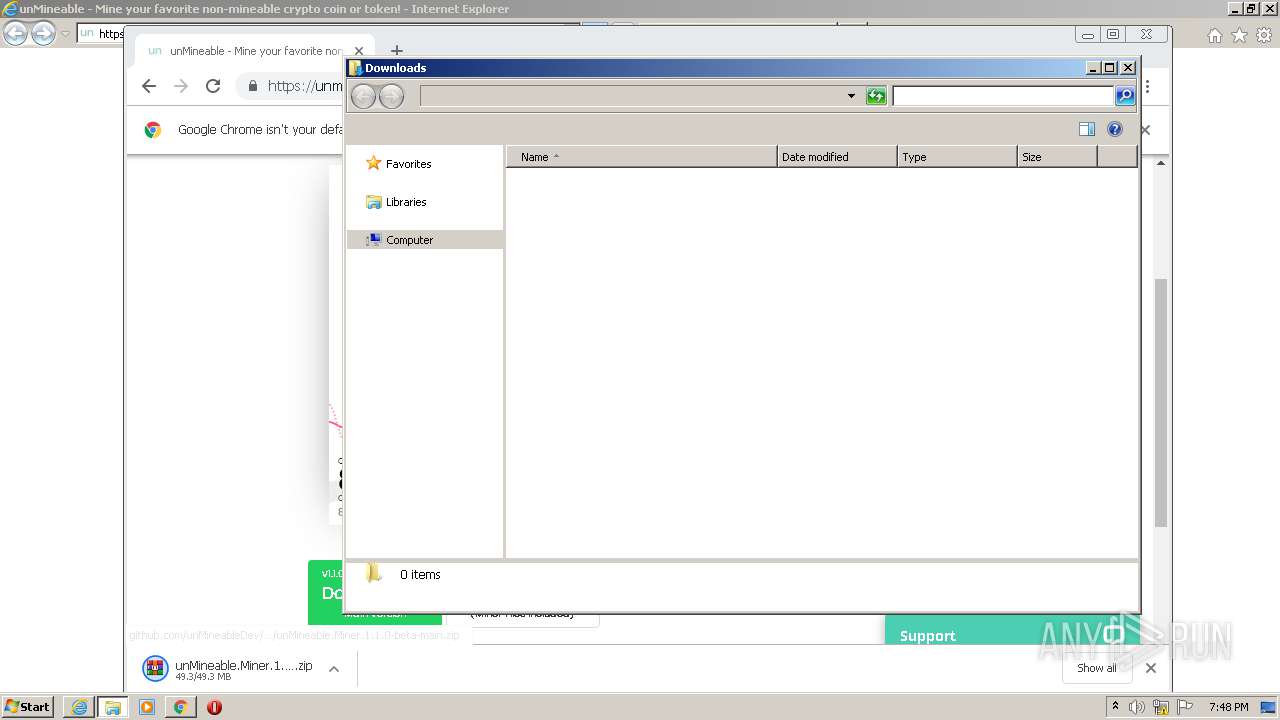
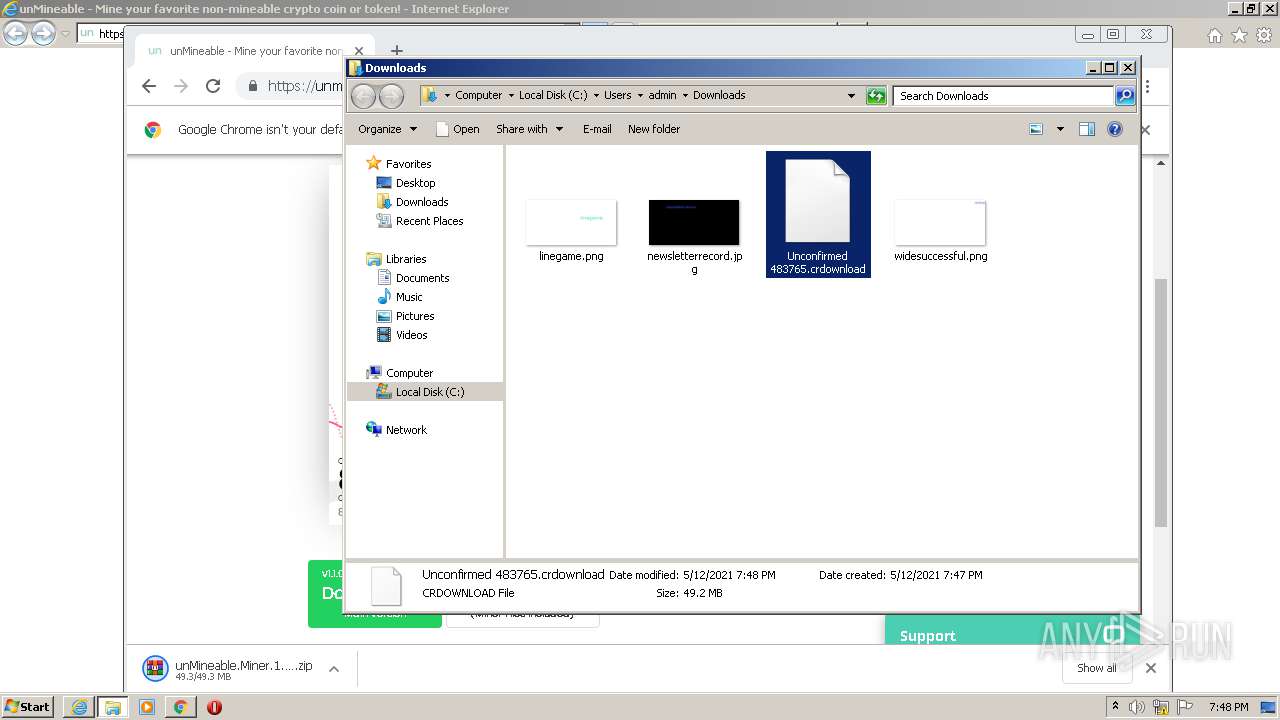
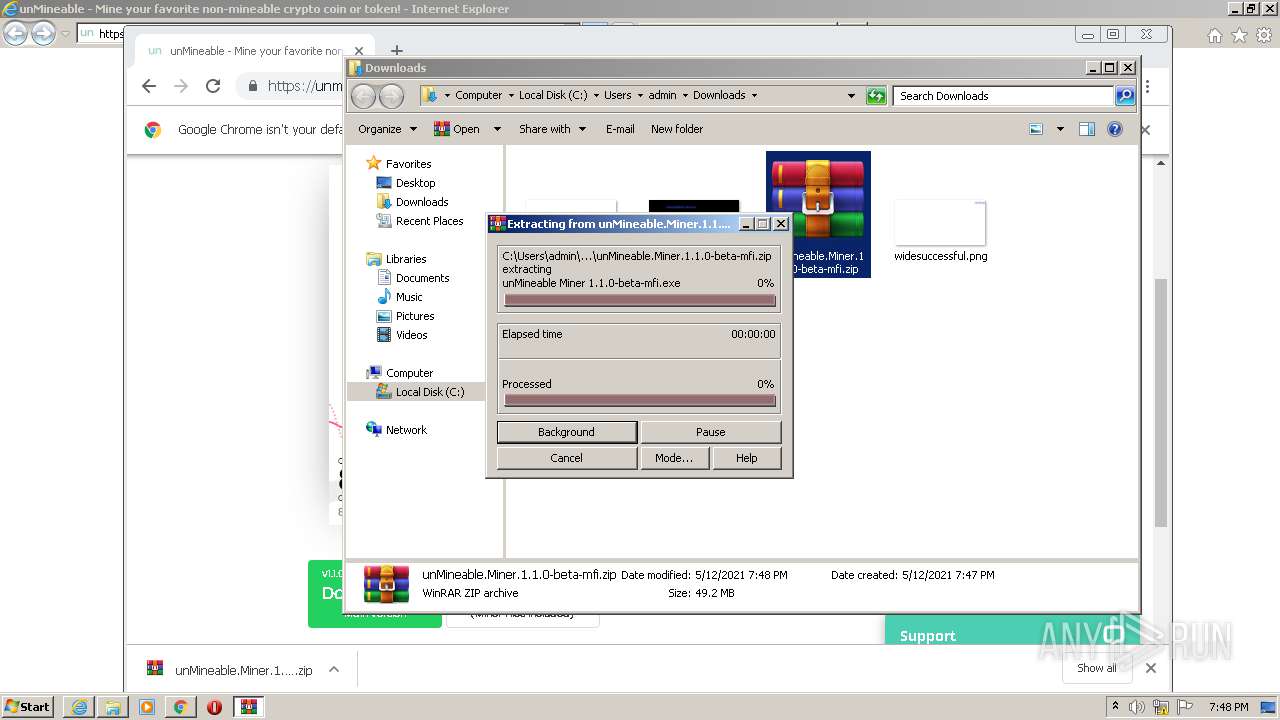
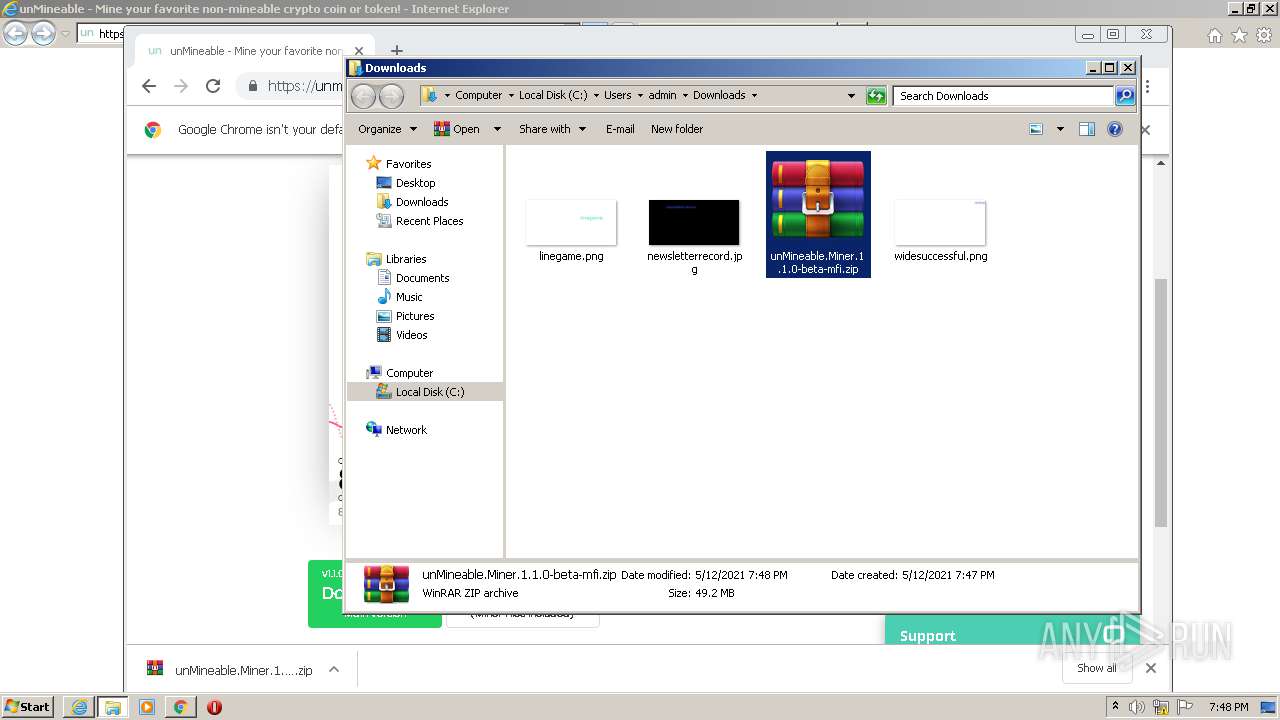
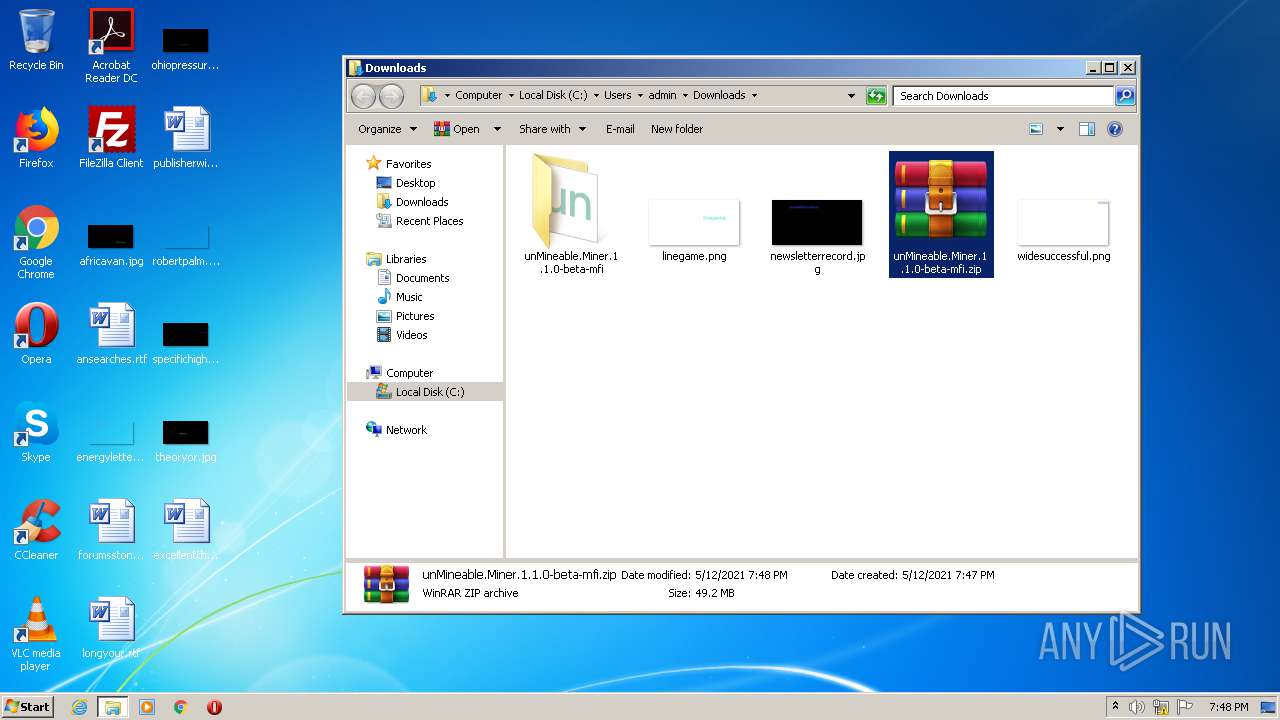
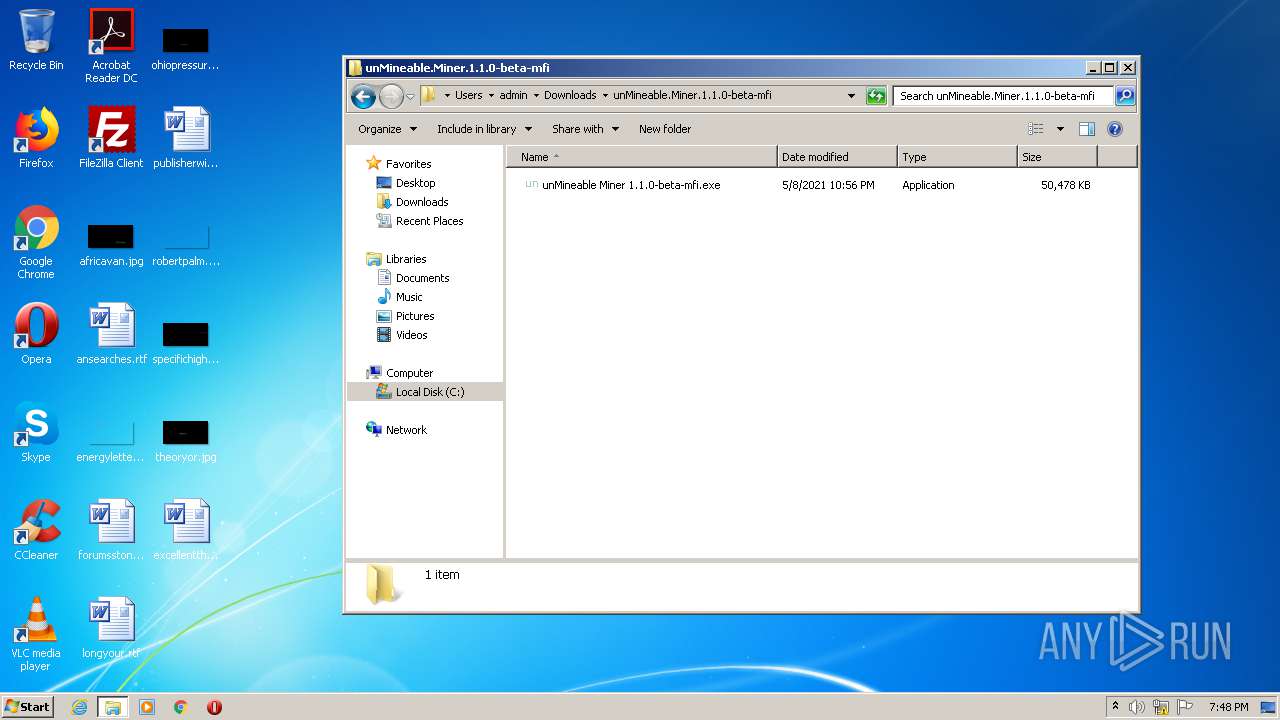
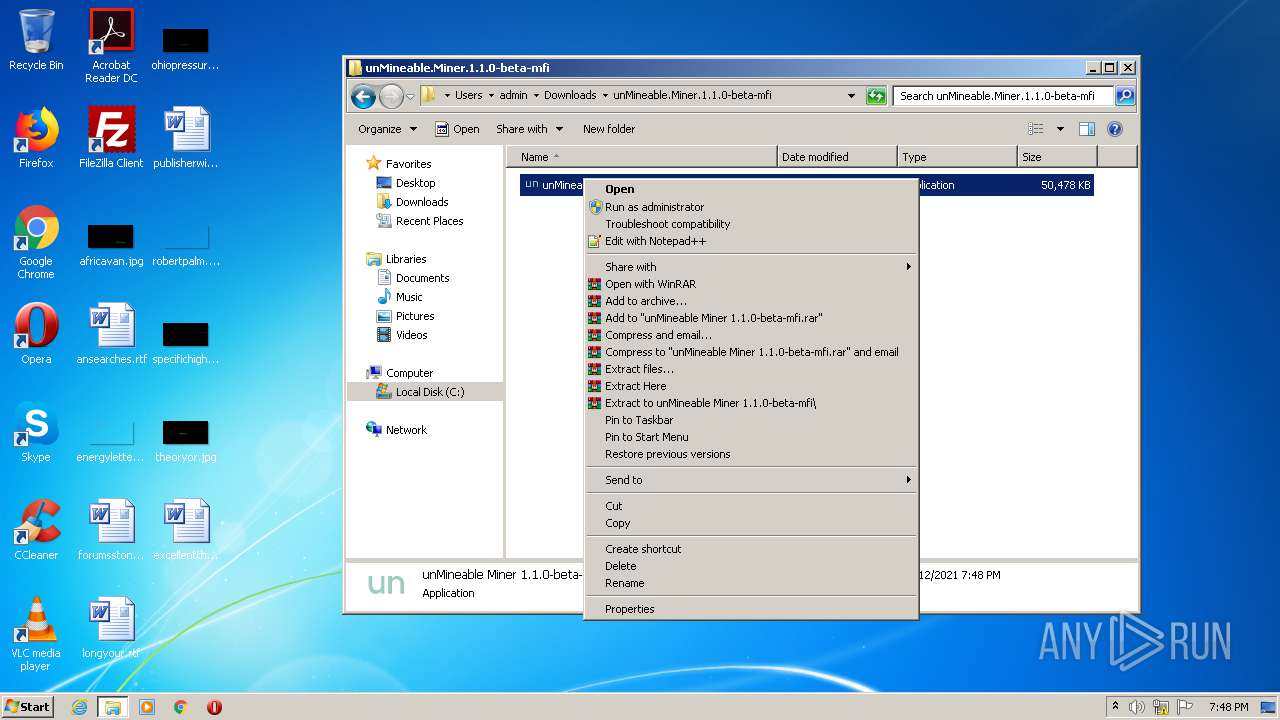
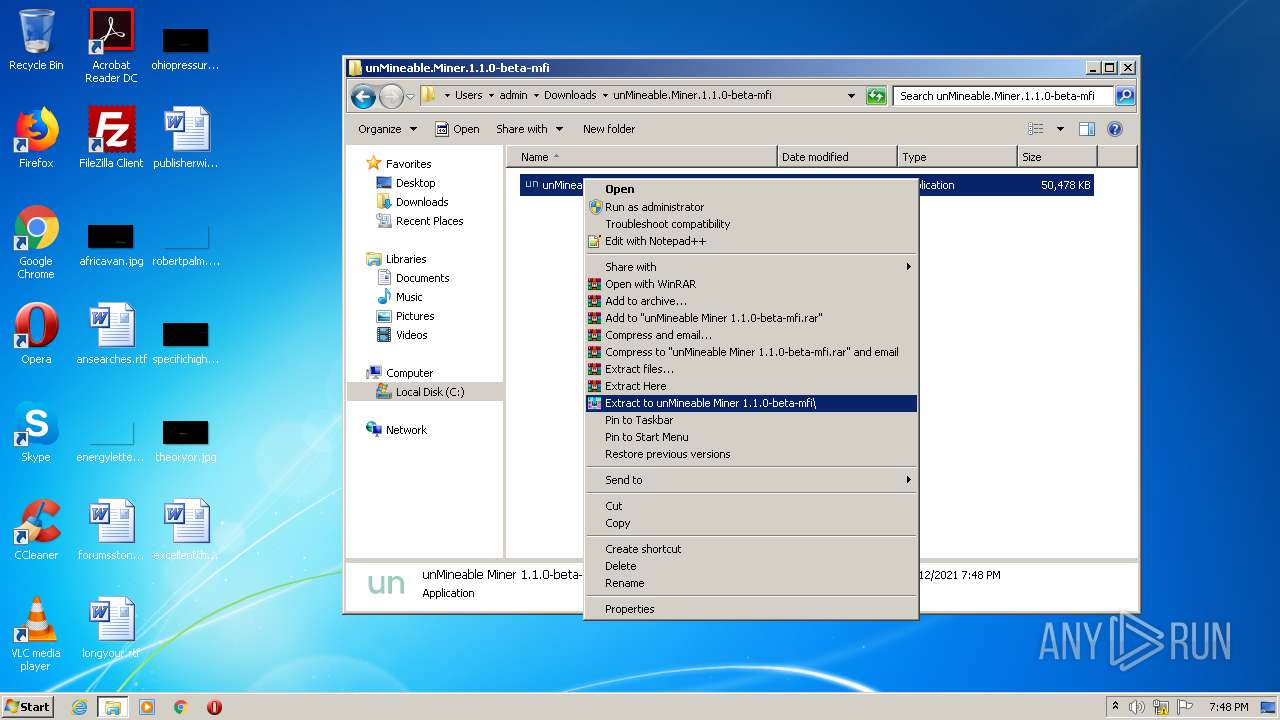
Manual execution by user
- WinRAR.exe (PID: 3568)
- WinRAR.exe (PID: 3336)
- unMineable Miner 1.1.0-beta-mfi.exe (PID: 3104)
- chrome.exe (PID: 2636)
- elevate.exe (PID: 1500)
Reads internet explorer settings
- iexplore.exe (PID: 2332)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
42
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14510878166758426122,921576701130013190,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6586341966676869075 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14510878166758426122,921576701130013190,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1010172029420591586 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1324 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14510878166758426122,921576701130013190,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14266142468627224408 --mojo-platform-channel-handle=3932 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14510878166758426122,921576701130013190,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2427859417896514698 --mojo-platform-channel-handle=3392 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14510878166758426122,921576701130013190,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13669350024562926148 --mojo-platform-channel-handle=4148 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1500 | "C:\Users\admin\Downloads\unMineable.Miner.1.1.0-beta-mfi\unMineable Miner 1.1.0-beta-mfi\resources\elevate.exe" | C:\Users\admin\Downloads\unMineable.Miner.1.1.0-beta-mfi\unMineable Miner 1.1.0-beta-mfi\resources\elevate.exe | — | explorer.exe | |||||||||||
User: admin Company: Johannes Passing Integrity Level: MEDIUM Description: Elevate Exit code: 0 Version: 1, 0, 0, 2894 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14510878166758426122,921576701130013190,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15376480030269818558 --mojo-platform-channel-handle=3072 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14510878166758426122,921576701130013190,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15633491625506414141 --mojo-platform-channel-handle=3440 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14510878166758426122,921576701130013190,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7797738761144911524 --mojo-platform-channel-handle=1636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14510878166758426122,921576701130013190,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10727113435918215133 --mojo-platform-channel-handle=3884 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 125
Read events
1 885
Write events
231
Delete events
9
Modification events
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 924988308 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30885727 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3500) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
16
Suspicious files
132
Text files
370
Unknown types
100
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabBA06.tmp | — | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabBA05.tmp | — | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarBA08.tmp | — | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarBA07.tmp | — | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\404[1].js | text | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\miner[1].htm | html | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\referrals[1].js | text | |
MD5:— | SHA256:— | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\layout[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
107
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.49 Kb | whitelisted |
2332 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2332 | iexplore.exe | GET | 200 | 151.101.194.133:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.41 Kb | whitelisted |
2332 | iexplore.exe | GET | 200 | 172.217.19.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBaL4OfTp%2BeHAwAAAADL91k%3D | US | der | 471 b | whitelisted |
2332 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2332 | iexplore.exe | GET | 200 | 172.217.19.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDDhar4btqgzgUAAAAAh7wW | US | der | 472 b | whitelisted |
2332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.49 Kb | whitelisted |
2332 | iexplore.exe | GET | 200 | 172.217.19.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBaL4OfTp%2BeHAwAAAADL91k%3D | US | der | 471 b | whitelisted |
2332 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2332 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2332 | iexplore.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2332 | iexplore.exe | 184.86.103.208:443 | api.livechatinc.com | Akamai Technologies, Inc. | US | suspicious |
2332 | iexplore.exe | 139.59.196.11:443 | api.unminable.com | Digital Ocean, Inc. | GB | unknown |
2332 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2332 | iexplore.exe | 184.86.103.203:443 | api.livechatinc.com | Akamai Technologies, Inc. | US | suspicious |
3500 | iexplore.exe | 172.67.69.49:443 | unmineable.com | — | US | unknown |
2332 | iexplore.exe | 172.67.69.49:443 | unmineable.com | — | US | unknown |
2332 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3500 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2332 | iexplore.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
unmineable.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |