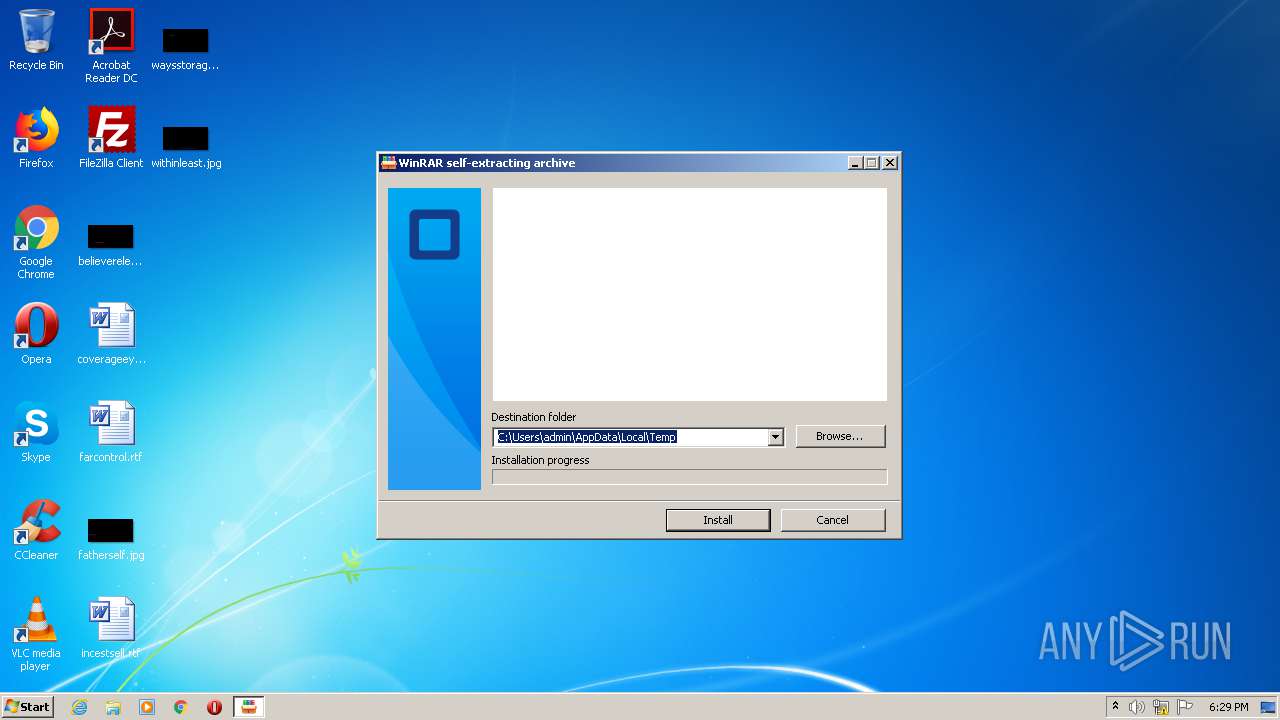
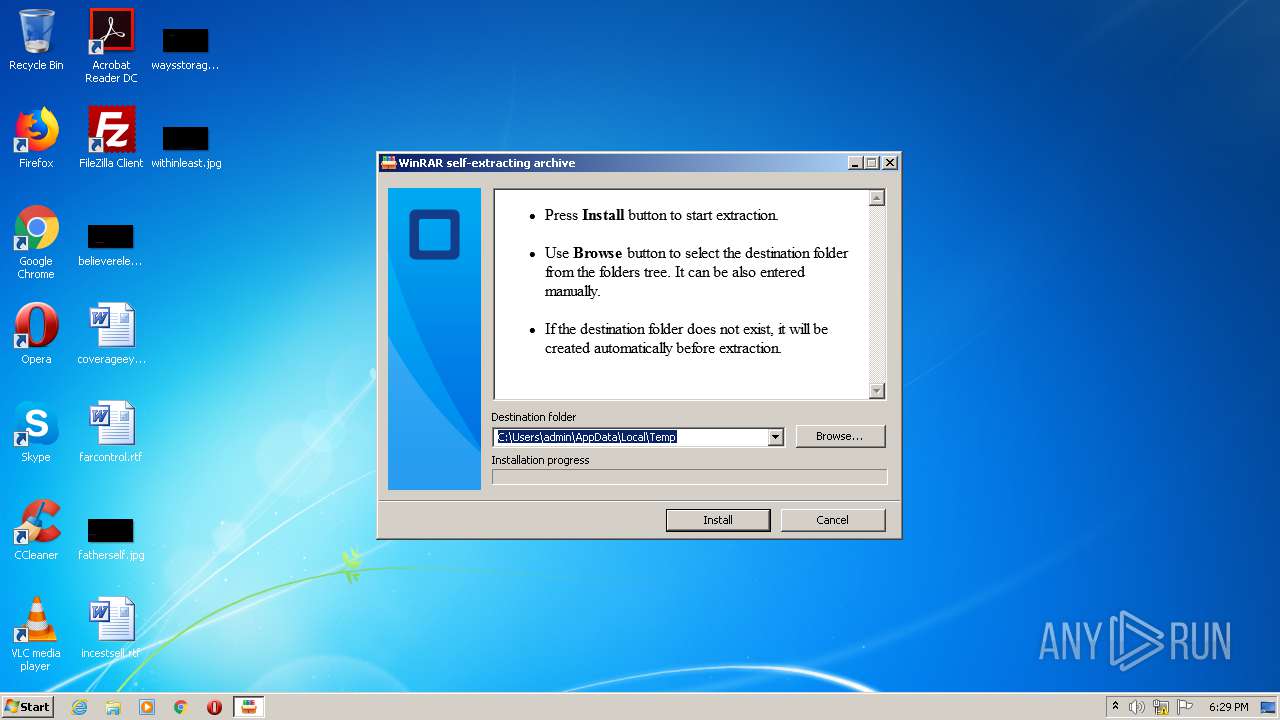
| File name: | Case13Data.exe |
| Full analysis: | https://app.any.run/tasks/1d447d27-2eef-4dde-8100-d28a59093fa5 |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2020, 17:29:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F0A539667910635F010A4108834D78C9 |
| SHA1: | 78863A457B26DDF057B9A95A2288E1261B35515A |
| SHA256: | E617E4588958ECB78ECC3CFD88C974C72F22901D0E716AF6C690CC3494684040 |
| SSDEEP: | 12288:0Qnk3GDYKGcblwtX+t4Y8Hmsg3nO/QqM3AqQQ:IAOcZwXY6msg3nO/HzqQQ |
MALICIOUS
Loads dropped or rewritten executable
- AcroRd32.exe (PID: 3932)
- AcroRd32.exe (PID: 2892)
Changes the autorun value in the registry
- AcroRd32.exe (PID: 3932)
Application was dropped or rewritten from another process
- AcroRd32.exe (PID: 3932)
- AcroRd32.exe (PID: 2892)
SUSPICIOUS
Creates files in the program directory
- AcroRd32.exe (PID: 3932)
Reads Internet Cache Settings
- Case13Data.exe (PID: 2848)
Reads internet explorer settings
- Case13Data.exe (PID: 2848)
Executable content was dropped or overwritten
- Case13Data.exe (PID: 2848)
- AcroRd32.exe (PID: 3932)
Starts itself from another location
- AcroRd32.exe (PID: 3932)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:26 11:02:47+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 198144 |
| InitializedDataSize: | 254464 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e1f9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Mar-2020 10:02:47 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 26-Mar-2020 10:02:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00030581 | 0x00030600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70021 |
.rdata | 0x00032000 | 0x0000A332 | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23888 |
.data | 0x0003D000 | 0x000238B0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.83994 |
.gfids | 0x00061000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12166 |
.rsrc | 0x00062000 | 0x0000DFD0 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.63693 |
.reloc | 0x00070000 | 0x0000210C | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.61039 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.11236 | 440 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2848 | "C:\Users\admin\AppData\Local\Temp\Case13Data.exe" | C:\Users\admin\AppData\Local\Temp\Case13Data.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2892 | C:\ProgramData\AcroRd32cWP\AcroRd32.exe 449 | C:\ProgramData\AcroRd32cWP\AcroRd32.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe CEF Helper Exit code: 0 Version: 3.9.0.327 Modules
| |||||||||||||||
| 3932 | "C:\Users\admin\AppData\Local\Temp\AcroRd32.exe" | C:\Users\admin\AppData\Local\Temp\AcroRd32.exe | Case13Data.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe CEF Helper Exit code: 0 Version: 3.9.0.327 Modules
| |||||||||||||||
Total events
415
Read events
406
Write events
9
Delete events
0
Modification events
| (PID) Process: | (2848) Case13Data.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2848) Case13Data.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2848) Case13Data.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2848) Case13Data.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2848) Case13Data.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3932) AcroRd32.exe | Key: | HKEY_CLASSES_ROOT\ms-pu |
| Operation: | write | Name: | CLSID |
Value: 33003400430034003100380032003600430033003600410032004400350041000000 | |||
| (PID) Process: | (3932) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | AcroRd32cWP |
Value: "C:\ProgramData\AcroRd32cWP\AcroRd32.exe" 449 | |||
Executable files
4
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
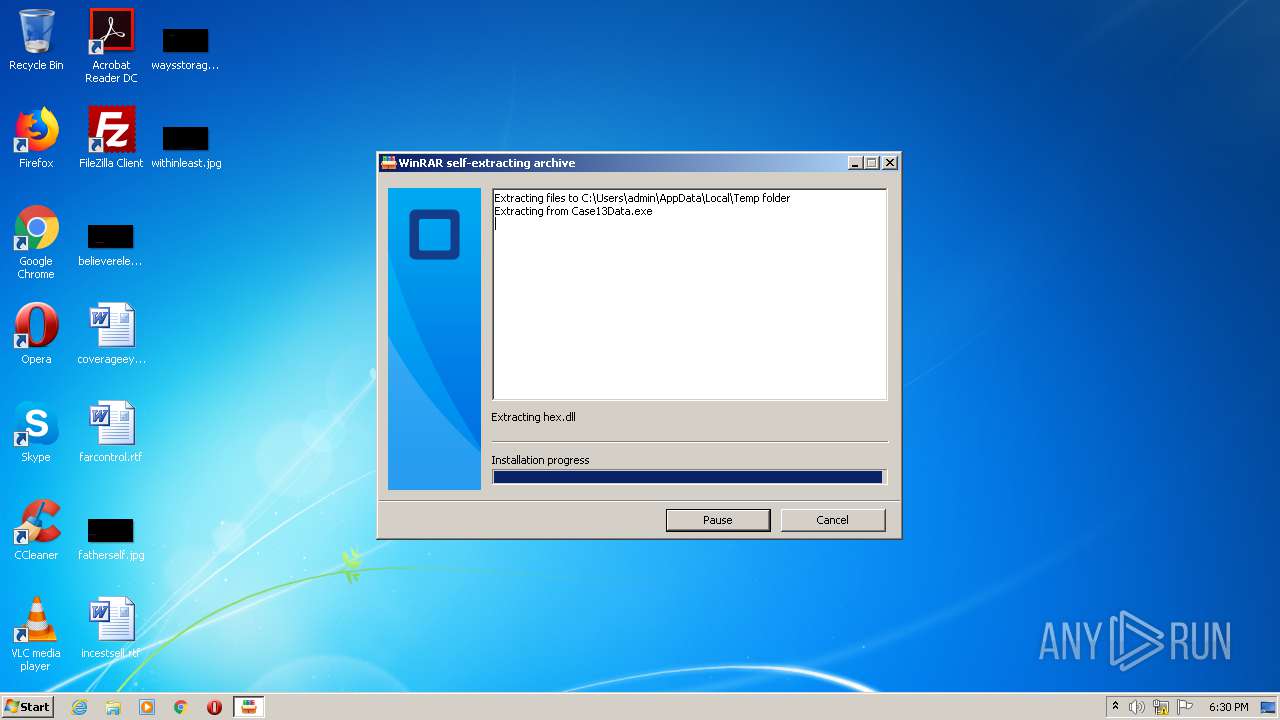
| 3932 | AcroRd32.exe | C:\ProgramData\AcroRd32cWP\hex.dll | executable | |
MD5:C33D3D6970DBB19062AE09505A6EB376 | SHA256:5BF291FD726770A7C3E60192BE74B960FE34C4733C4E0E770202E8E8F85CBD02 | |||
| 2848 | Case13Data.exe | C:\Users\admin\AppData\Local\Temp\hex.dll | executable | |
MD5:C33D3D6970DBB19062AE09505A6EB376 | SHA256:5BF291FD726770A7C3E60192BE74B960FE34C4733C4E0E770202E8E8F85CBD02 | |||
| 3932 | AcroRd32.exe | C:\ProgramData\AcroRd32cWP\AcroRd32.exe | executable | |
MD5:C70D8DCE46B4551133ECC58AED84BF0E | SHA256:0459E62C5444896D5BE404C559C834BA455FA5CAE1689C70FC8C61BC15468681 | |||
| 3932 | AcroRd32.exe | C:\ProgramData\AcroRd32cWP\adobeupdate.dat | binary | |
MD5:38BAABDDFFB1D732A05FFA2C70331E21 | SHA256:F0F2FF31B869FDB9F2EF67BFB0CC7840F098A37B6B21E6EB4983134448E3D208 | |||
| 2848 | Case13Data.exe | C:\Users\admin\AppData\Local\Temp\AcroRd32.exe | executable | |
MD5:C70D8DCE46B4551133ECC58AED84BF0E | SHA256:0459E62C5444896D5BE404C559C834BA455FA5CAE1689C70FC8C61BC15468681 | |||
| 2848 | Case13Data.exe | C:\Users\admin\AppData\Local\Temp\adobeupdate.dat | binary | |
MD5:38BAABDDFFB1D732A05FFA2C70331E21 | SHA256:F0F2FF31B869FDB9F2EF67BFB0CC7840F098A37B6B21E6EB4983134448E3D208 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | AcroRd32.exe | 42.99.117.95:443 | — | — | HK | unknown |
2892 | AcroRd32.exe | 42.99.117.95:8080 | — | — | HK | unknown |
2892 | AcroRd32.exe | 72.52.179.175:8000 | news.169mt.com | Liquid Web, L.L.C | US | malicious |
— | — | 42.99.117.95:443 | — | — | HK | unknown |
2892 | AcroRd32.exe | 72.52.179.175:8090 | news.169mt.com | Liquid Web, L.L.C | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
news.169mt.com |
| malicious |