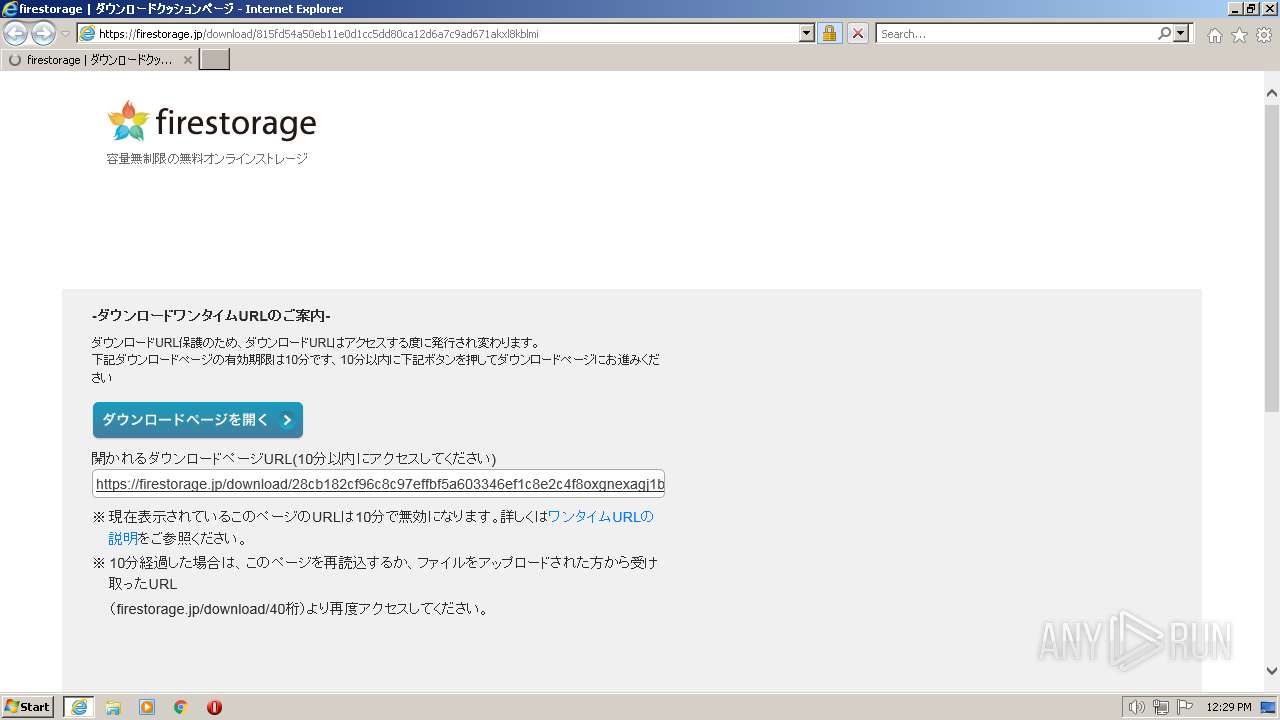
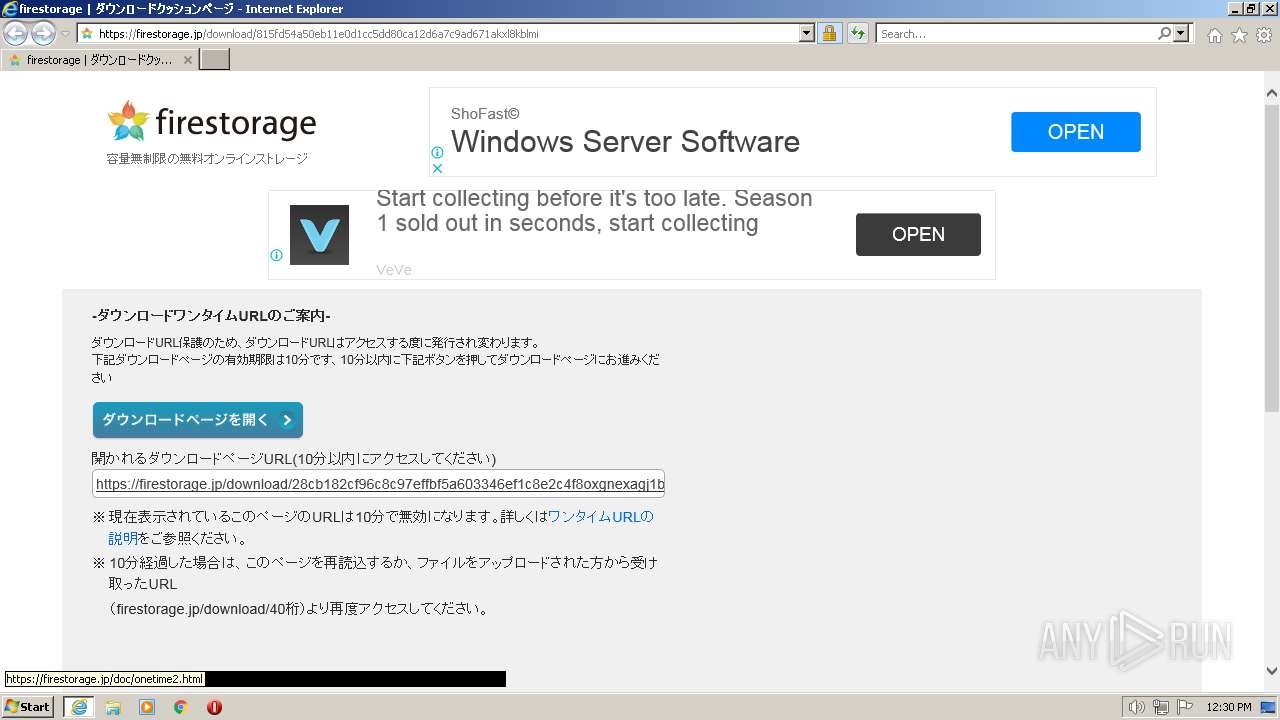
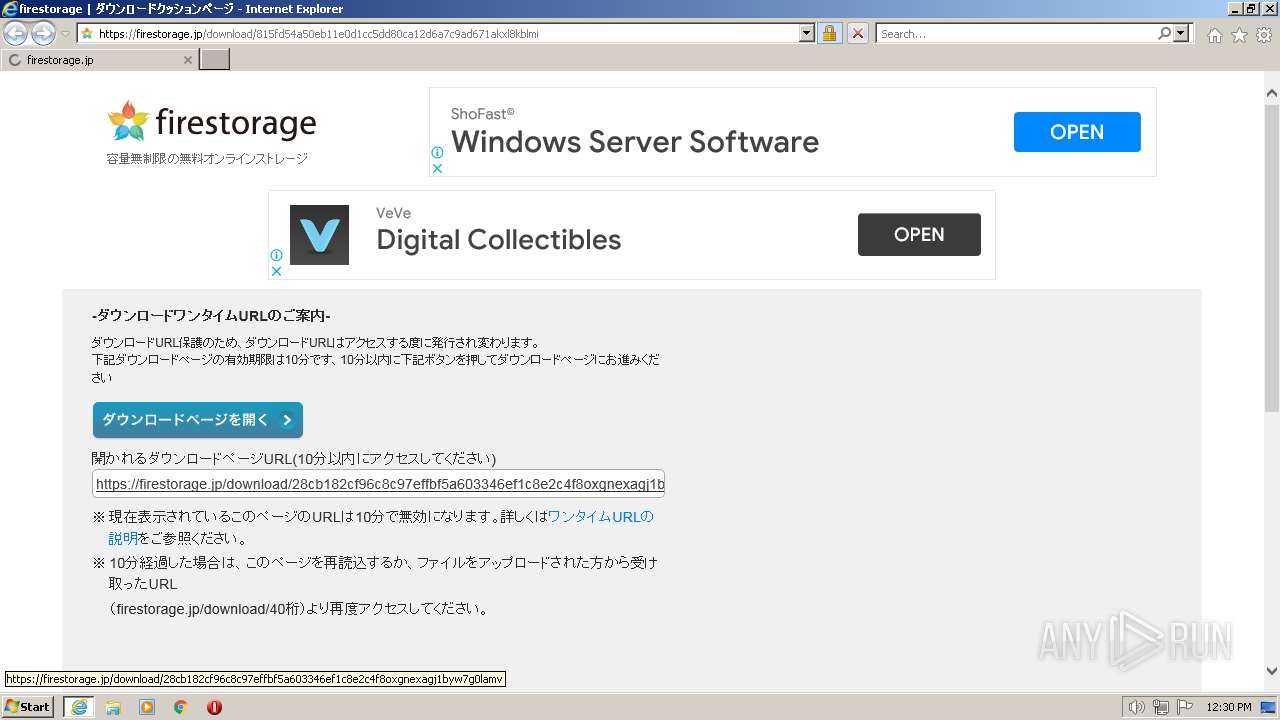
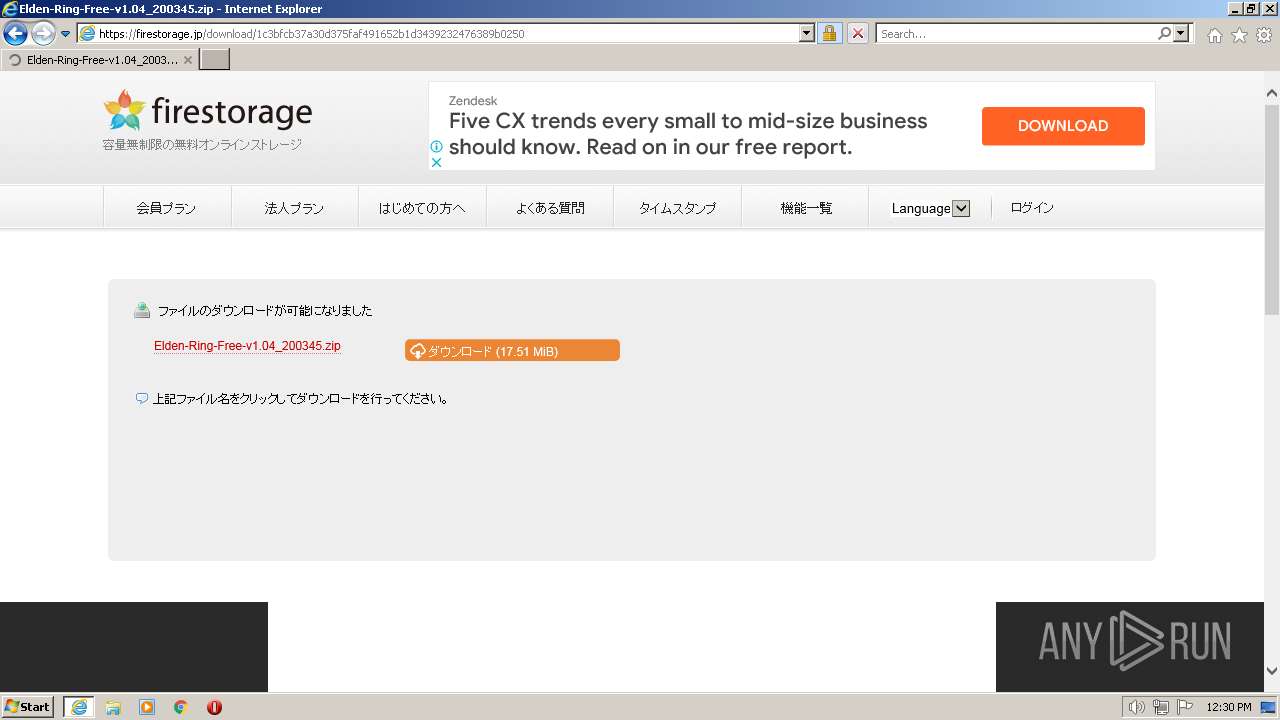
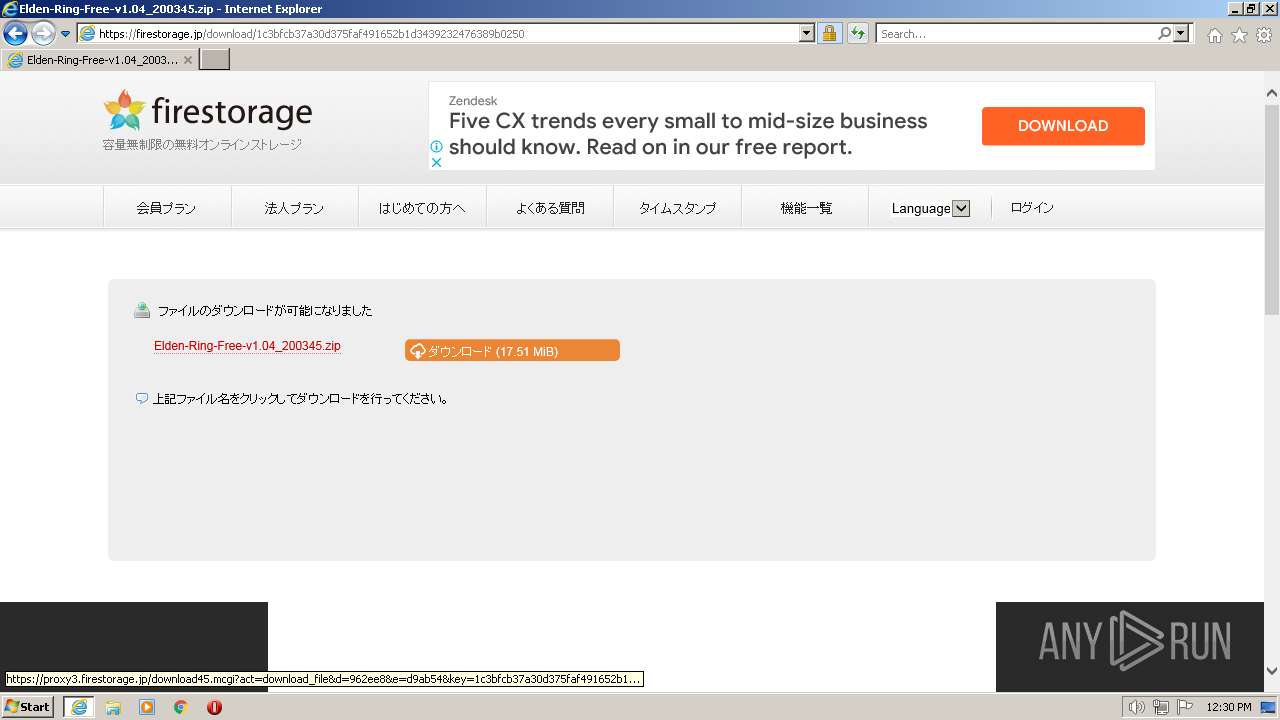
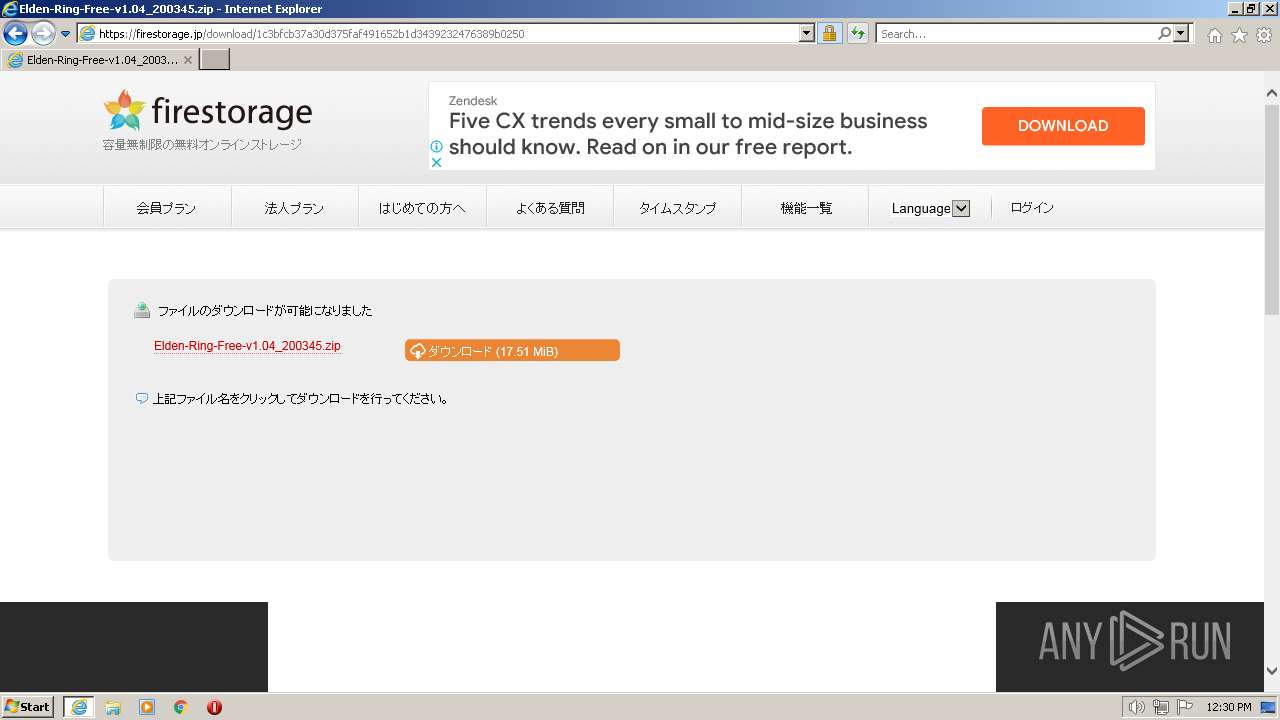
| URL: | https://firestorage.jp/download/baf7d646cdb4a71f5a2f1e8290500818423dd0e5 |
| Full analysis: | https://app.any.run/tasks/f08bda03-d0fe-4a2f-bdb7-9079ccbb9756 |
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2023, 12:29:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E7EAB4D766747423AD92C61102AE64D8 |
| SHA1: | 7A272229DD0283F6D13F8DFB48A3EBF5F847CD89 |
| SHA256: | E60B6125BCFADADD6CED091756872C167385F971BE8A0A78C21EDA75EF79BA19 |
| SSDEEP: | 3:N8dW2P9kK0KxxUFTjMVQtAQn:2PxdMAQn |
MALICIOUS
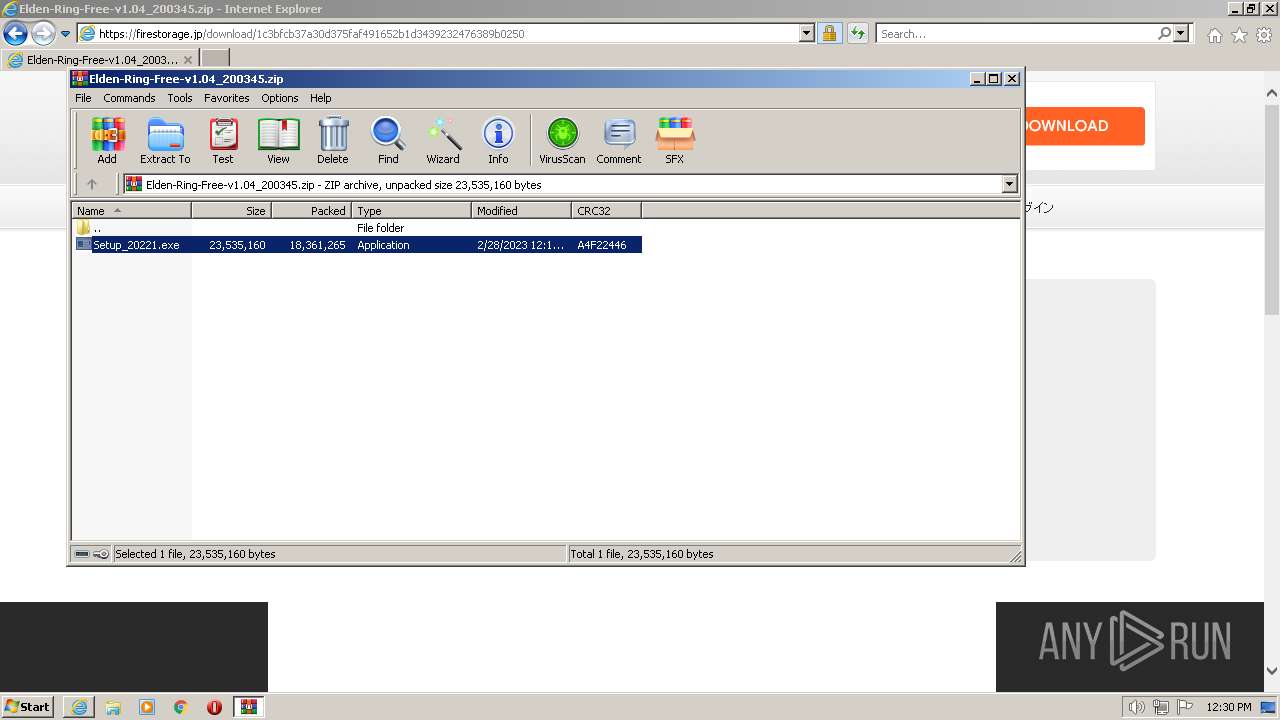
Application was dropped or rewritten from another process
- Setup_20221.exe (PID: 2268)
Drops the executable file immediately after the start
- Setup_20221.exe (PID: 2268)
SUSPICIOUS
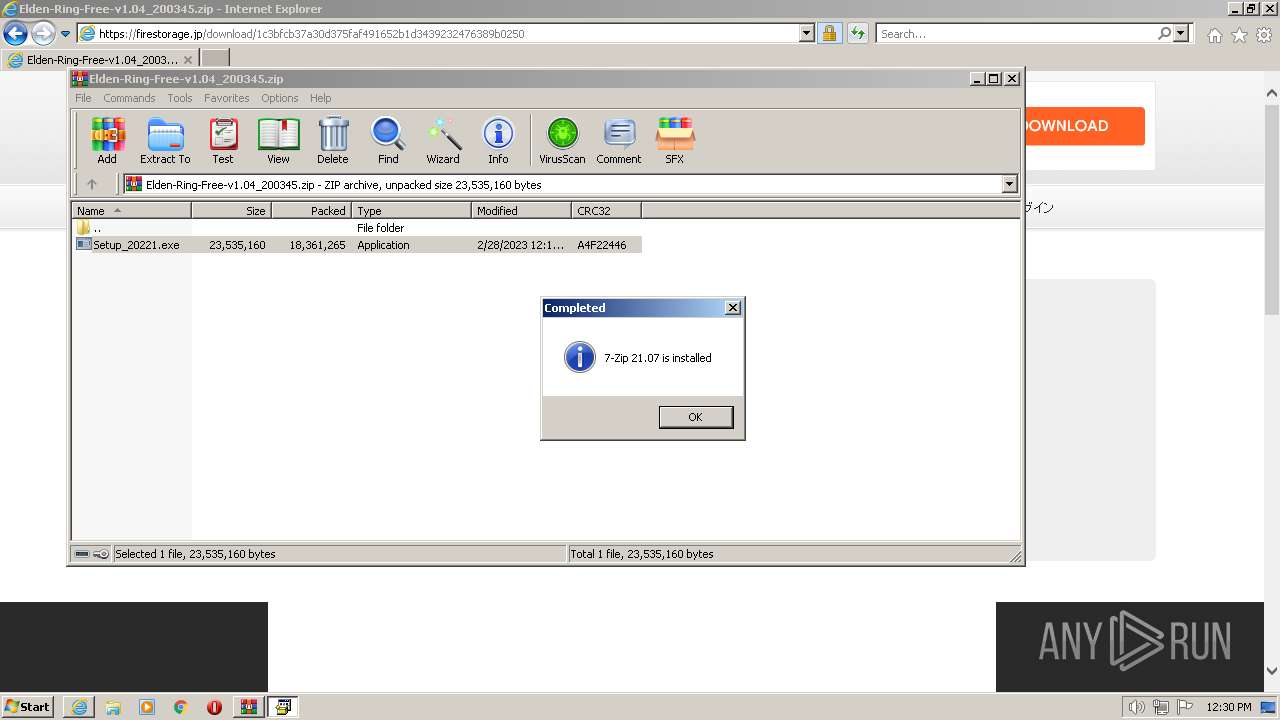
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 3896)
- Setup_20221.exe (PID: 2268)
Executable content was dropped or overwritten
- Setup_20221.exe (PID: 2268)
Reads the Internet Settings
- Setup_20221.exe (PID: 2268)
Creates/Modifies COM task schedule object
- Setup_20221.exe (PID: 2268)
INFO
Application launched itself
- iexplore.exe (PID: 3492)
Create files in a temporary directory
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 3436)
The process uses the downloaded file
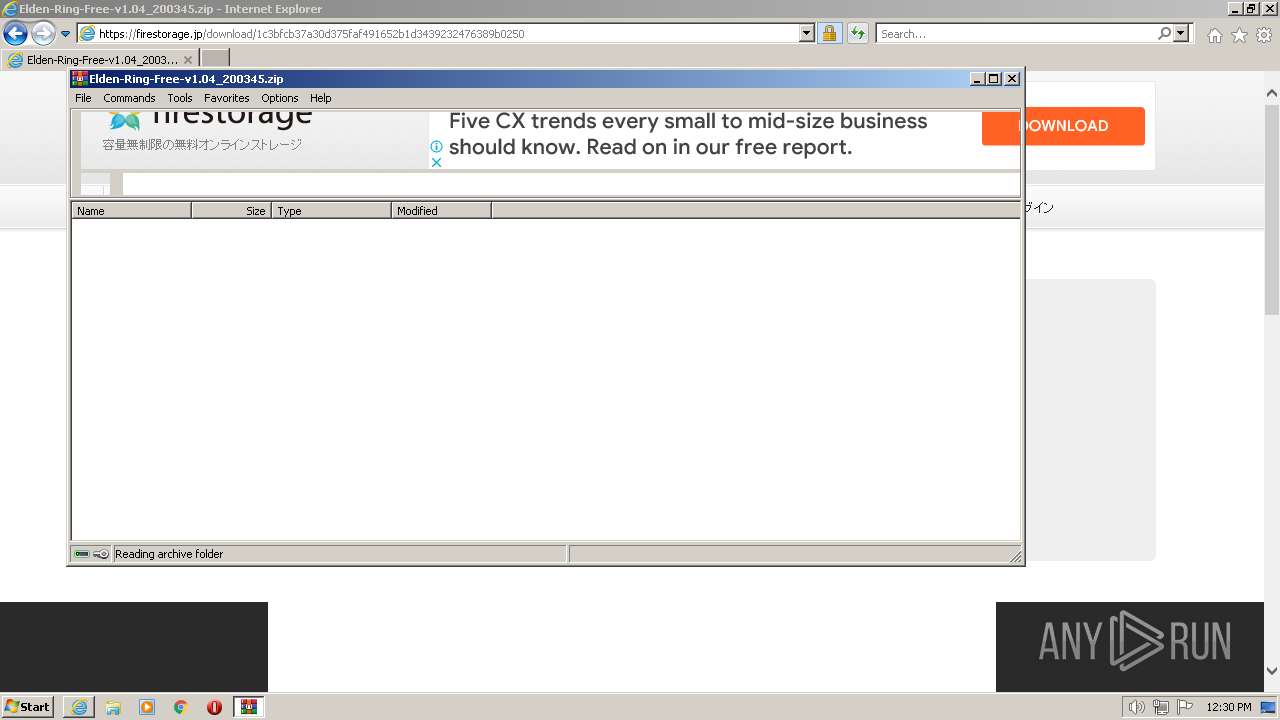
- WinRAR.exe (PID: 3896)
- iexplore.exe (PID: 3492)
Checks supported languages
- Setup_20221.exe (PID: 2268)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3896)
Reads the computer name
- Setup_20221.exe (PID: 2268)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3896)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3492)
The process checks LSA protection
- Setup_20221.exe (PID: 2268)
Creates files or folders in the user directory
- Setup_20221.exe (PID: 2268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
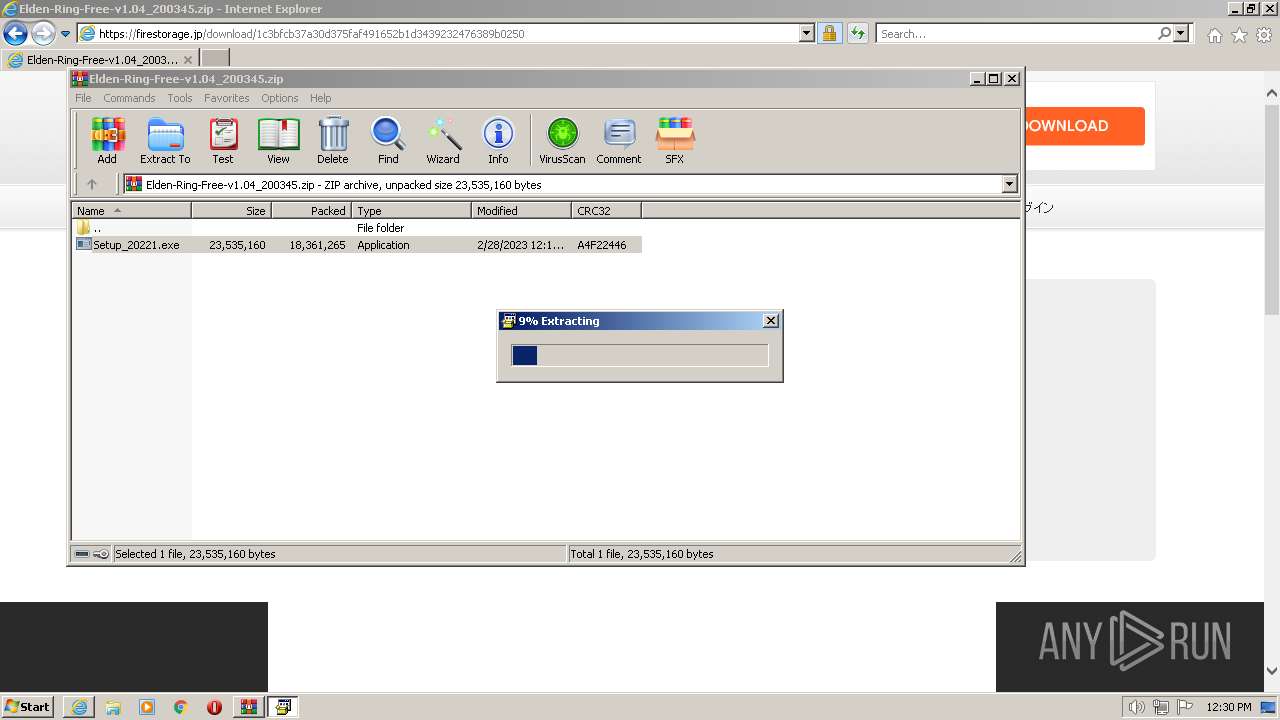
| 2268 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3896.41655\Setup_20221.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3896.41655\Setup_20221.exe | WinRAR.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z Setup SFX Exit code: 0 Version: 21.07 Modules
| |||||||||||||||
| 3436 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3492 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
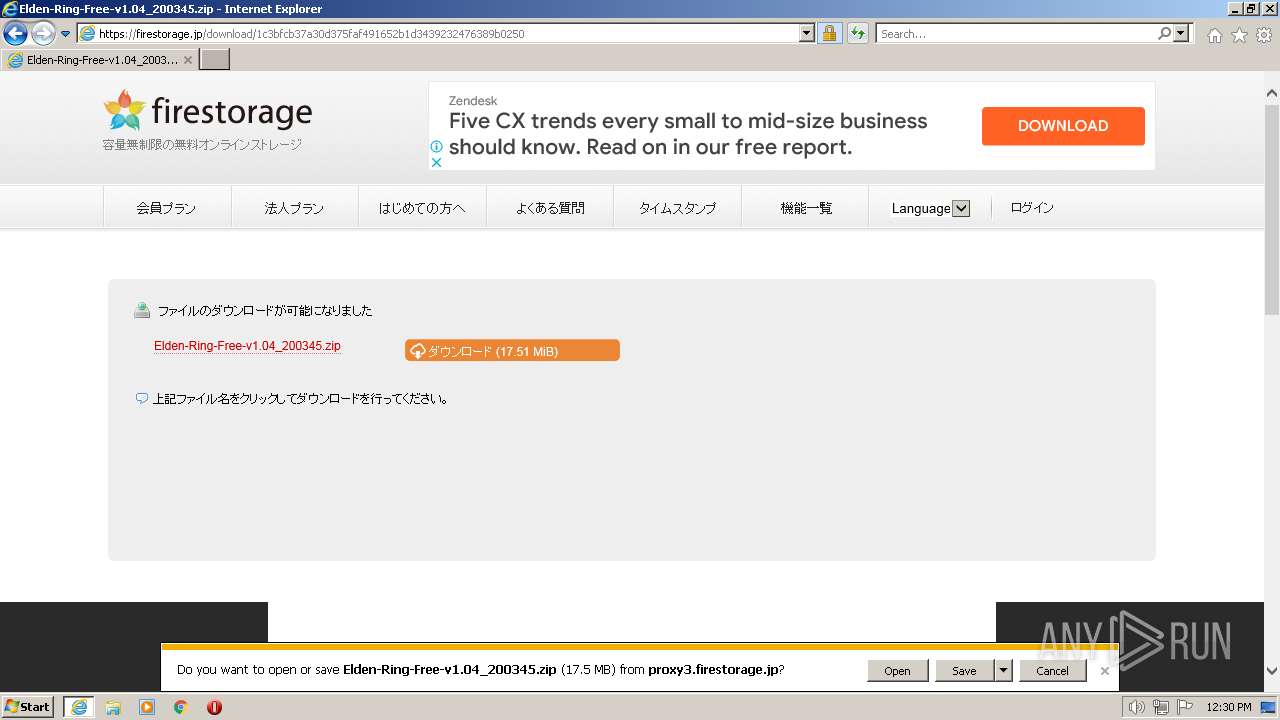
| 3492 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://firestorage.jp/download/baf7d646cdb4a71f5a2f1e8290500818423dd0e5" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
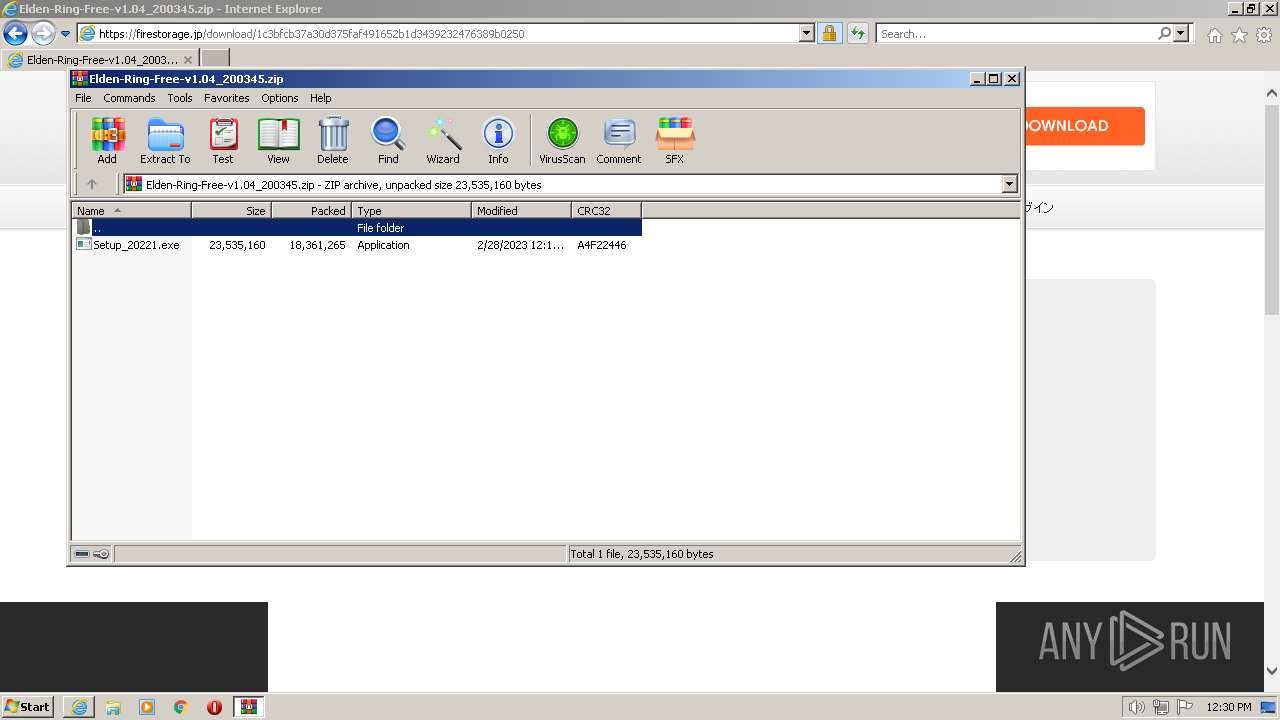
| 3896 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\Elden-Ring-Free-v1.04_200345.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
63 206
Read events
62 792
Write events
406
Delete events
8
Modification events
| (PID) Process: | (3492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31017840 | |||
| (PID) Process: | (3492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31017840 | |||
| (PID) Process: | (3492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3492) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
20
Suspicious files
154
Text files
610
Unknown types
150
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7A0F0ECE678D5EB632844D0A8018B79A_F65BA7EC0DECB8BA3142C5446DA23C74 | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\13886C091EC5C0D7486A78E314A2ED81_2672E234A655F603D9576AEF22D78824 | der | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7A0F0ECE678D5EB632844D0A8018B79A_F65BA7EC0DECB8BA3142C5446DA23C74 | der | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\13886C091EC5C0D7486A78E314A2ED81_2672E234A655F603D9576AEF22D78824 | binary | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
70
TCP/UDP connections
205
DNS requests
84
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3436 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDz6f%2FI8VdjcwrWnyPUY376 | US | der | 472 b | whitelisted |
3492 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAoFmyX1Sz2HlMxmMUd1OKM%3D | US | der | 471 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 153.127.216.172:80 | http://ssocsp.cybertrust.ne.jp/OcspServer/MFUwUzBRME8wTTAJBgUrDgMCGgUABBSdAxQrs2W5NWr2QA%2Fa%2BIVB2osTTQQUYqfS2t6FtpLxhbz26JWddaD6Th8CFFZya0oRnbT%2Fpb2BRtFDlyB0AF6v | JP | der | 1.44 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECCaJyxaKKxMCob%2B%2Fr17VBA%3D | US | der | 471 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDHezjC8R8IIEj%2BqoymGAUY%3D | US | der | 471 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQlOydjtpho0%2Bholo77zGjGxETUEQQU8JyF%2FaKffY%2FJaLvV1IlNHb7TkP8CEArLULkHOtSeUURv%2FC27c8s%3D | US | der | 727 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCEqUTOx23pPwqy5En6Xuzs | US | der | 472 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDsbu%2F%2BvFy5Mwq12LDuuFcZ | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3436 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3436 | iexplore.exe | 125.100.137.179:443 | — | ARTERIA Networks Corporation | JP | unknown |
3492 | iexplore.exe | 92.123.104.52:443 | www.bing.com | Akamai International B.V. | DE | suspicious |
3492 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3492 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3436 | iexplore.exe | 193.108.153.21:80 | scrootca2.ocsp.secomtrust.net | Akamai International B.V. | DE | suspicious |
3436 | iexplore.exe | 153.127.216.172:80 | ssocsp.cybertrust.ne.jp | SAKURA Internet Inc. | JP | unknown |
3436 | iexplore.exe | 124.32.142.105:443 | posh.firestorage.jp | ARTERIA Networks Corporation | JP | unknown |
3436 | iexplore.exe | 142.250.186.42:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3436 | iexplore.exe | 142.250.185.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
scrootca2.ocsp.secomtrust.net |
| whitelisted |
ssocsp.cybertrust.ne.jp |
| whitelisted |
posh.firestorage.jp |
| unknown |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
sakura1.firestorage.jp |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3436 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3436 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |