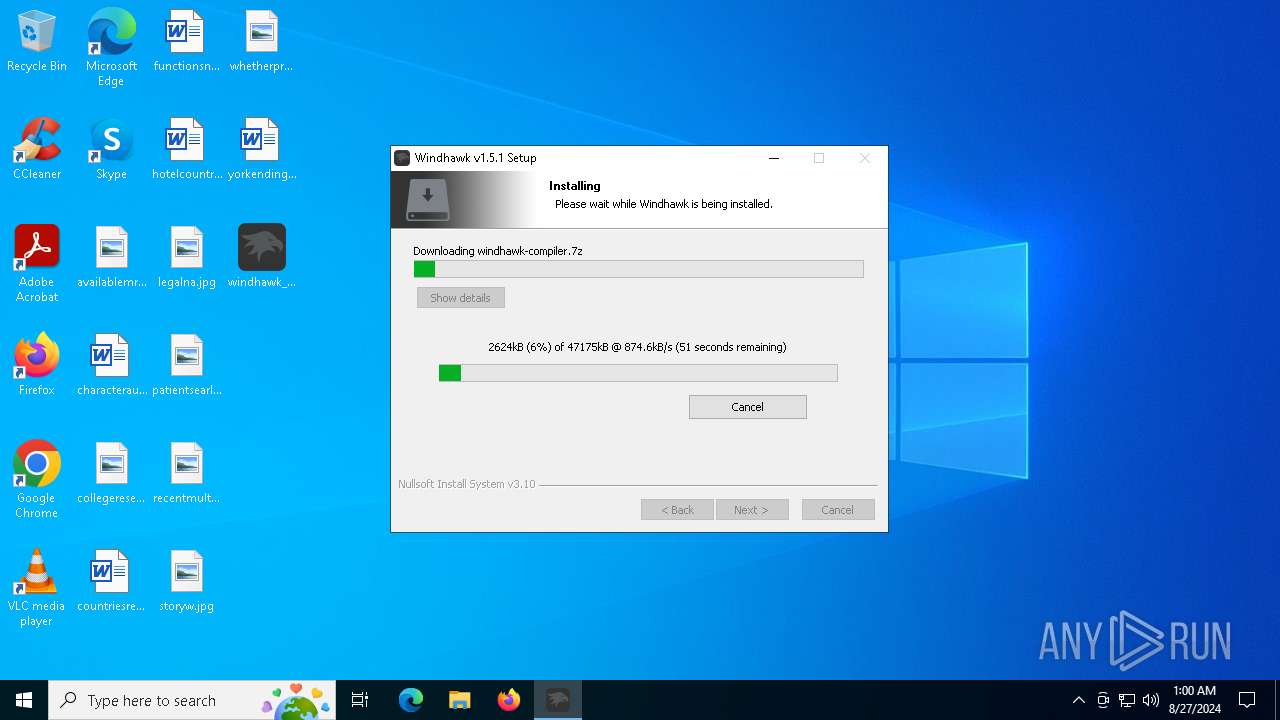
| File name: | windhawk_setup.exe |
| Full analysis: | https://app.any.run/tasks/de041eba-f84e-42dc-9d0e-b120d56b1bfa |
| Verdict: | Malicious activity |
| Analysis date: | August 27, 2024, 00:59:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D634FCD62241A93EFD88315091CCED44 |
| SHA1: | F1BAAD89DA31BF3F63D07E9CB1517E371101DDE1 |
| SHA256: | E60928DEE71B11866A826BC474A72B928327D1378EA80319819217CEBCD53B2A |
| SSDEEP: | 98304:xNTiJgw8einZCXrJMorrJ/dAjo39ZjqlQuA7GY5nbr4XZmNd/uWN2OM15OeD2q4m:IomYSkJ324+A |
MALICIOUS
No malicious indicators.SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- windhawk_setup.exe (PID: 6152)
- windhawk_setup.exe (PID: 4292)
Drops the executable file immediately after the start
- windhawk_setup.exe (PID: 6152)
- windhawk_setup.exe (PID: 4292)
Executable content was dropped or overwritten
- windhawk_setup.exe (PID: 6152)
- windhawk_setup.exe (PID: 4292)
The process creates files with name similar to system file names
- windhawk_setup.exe (PID: 6152)
- windhawk_setup.exe (PID: 4292)
Reads security settings of Internet Explorer
- windhawk_setup.exe (PID: 6152)
- windhawk_setup.exe (PID: 4292)
Reads the date of Windows installation
- windhawk_setup.exe (PID: 6152)
Application launched itself
- windhawk_setup.exe (PID: 6152)
Checks Windows Trust Settings
- windhawk_setup.exe (PID: 4292)
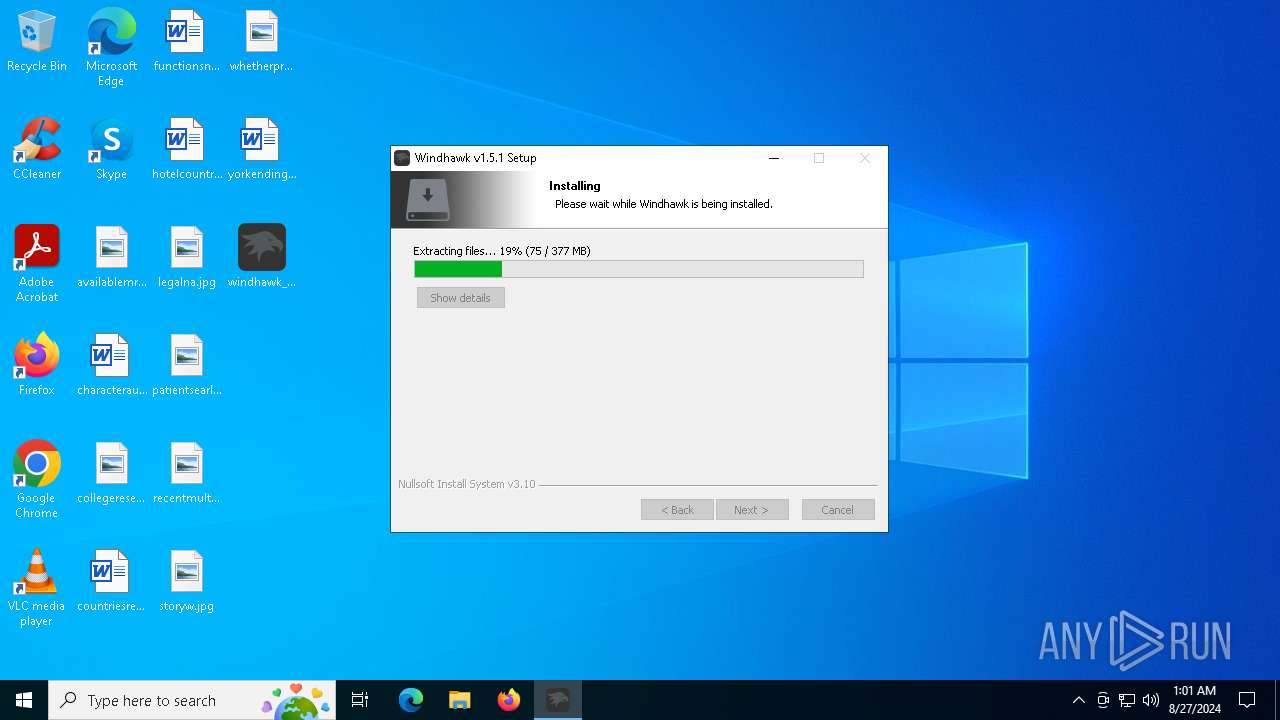
Drops 7-zip archiver for unpacking
- windhawk_setup.exe (PID: 4292)
INFO
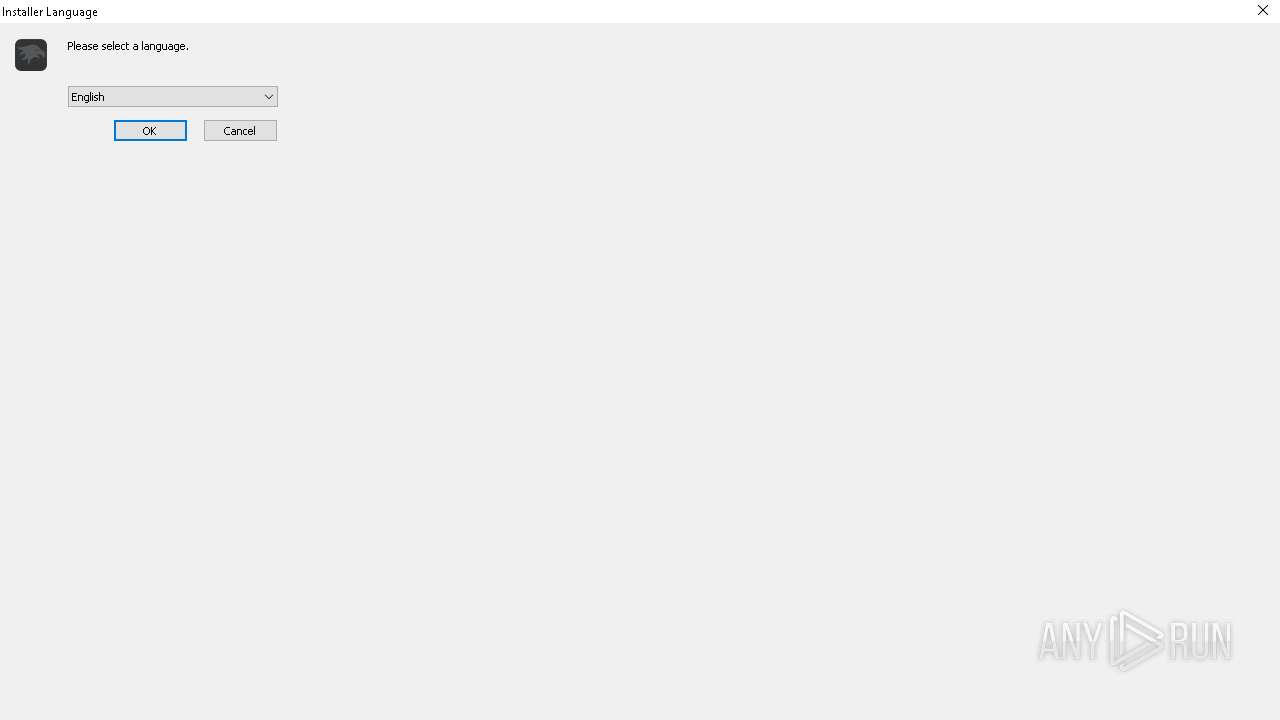
Checks supported languages
- windhawk_setup.exe (PID: 6152)
- windhawk_setup.exe (PID: 4292)
Create files in a temporary directory
- windhawk_setup.exe (PID: 6152)
- windhawk_setup.exe (PID: 4292)
Reads the computer name
- windhawk_setup.exe (PID: 6152)
- windhawk_setup.exe (PID: 4292)
Process checks computer location settings
- windhawk_setup.exe (PID: 6152)
Checks proxy server information
- windhawk_setup.exe (PID: 4292)
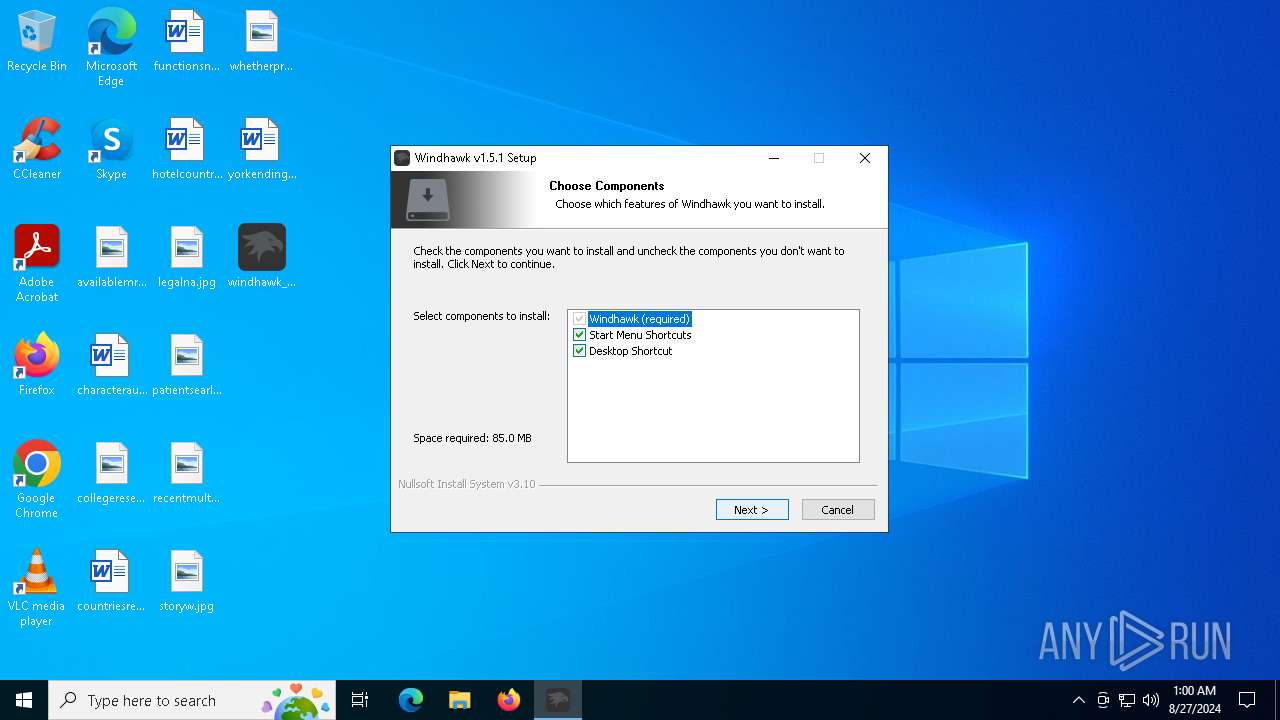
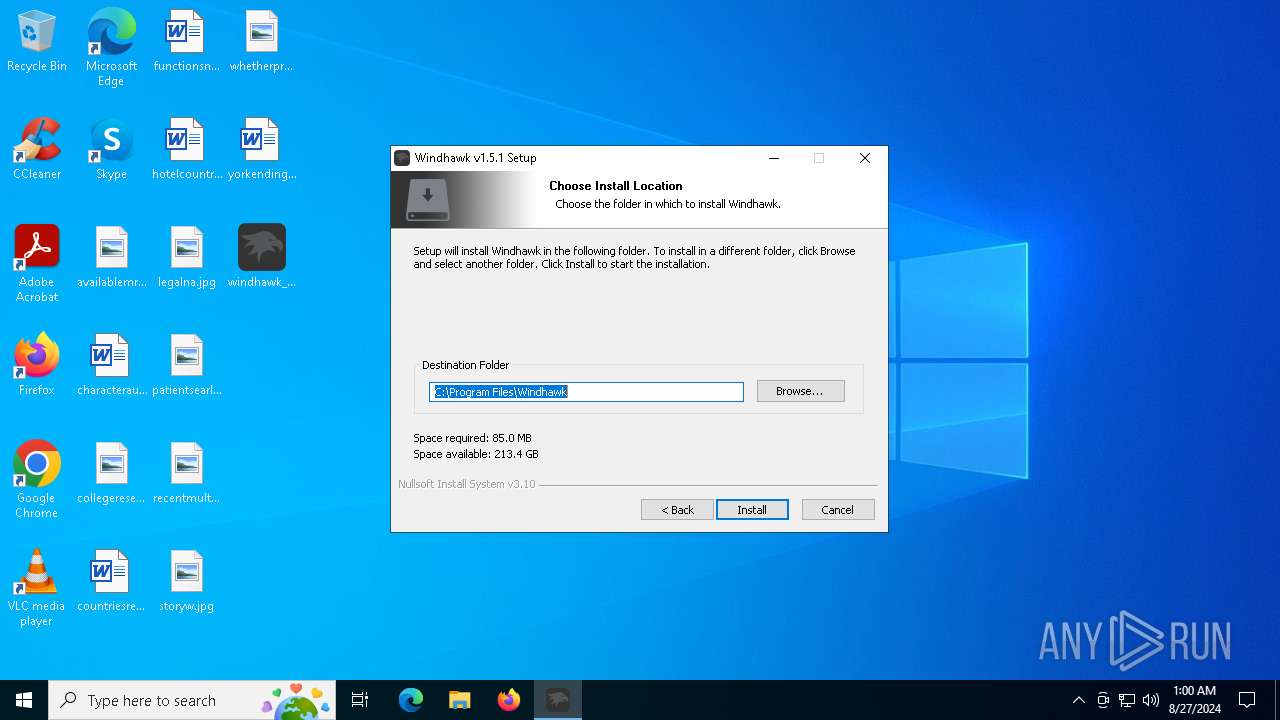
Creates files in the program directory
- windhawk_setup.exe (PID: 4292)
Reads the machine GUID from the registry
- windhawk_setup.exe (PID: 4292)
Creates files or folders in the user directory
- windhawk_setup.exe (PID: 4292)
Reads the software policy settings
- windhawk_setup.exe (PID: 4292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:30 16:55:19+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 139776 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3665 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
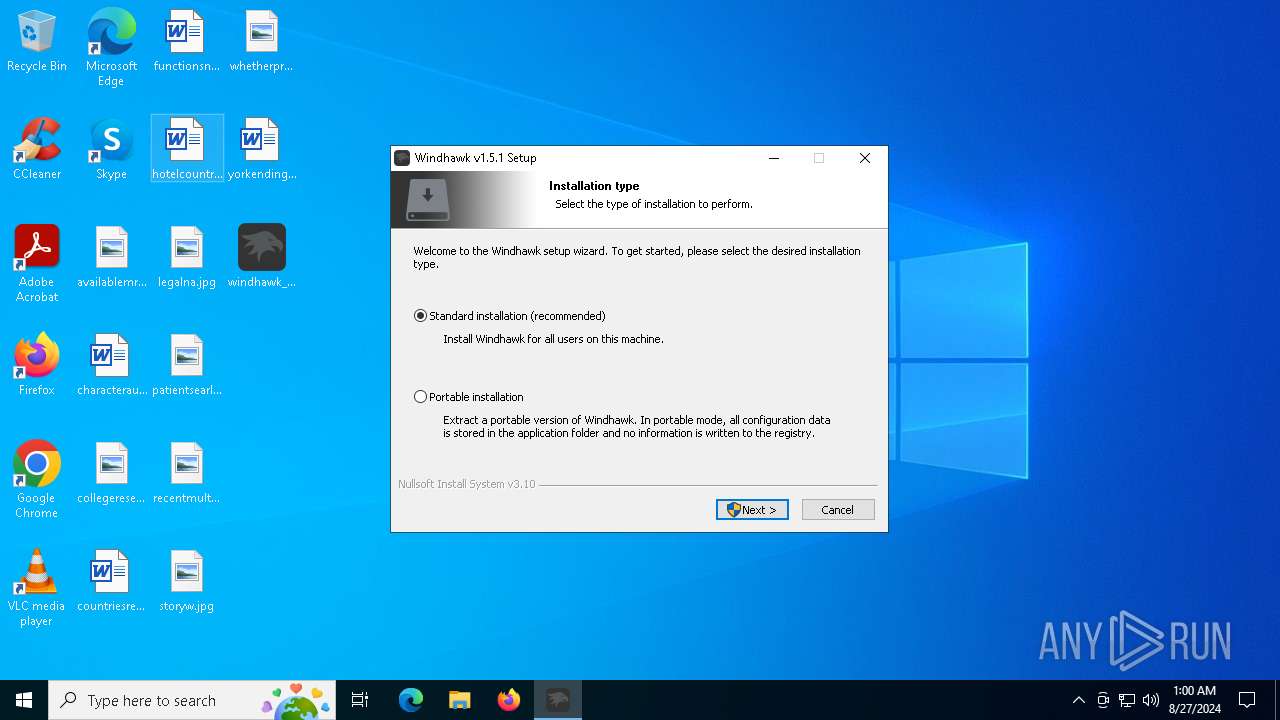
| FileVersionNumber: | 1.5.1.0 |
| ProductVersionNumber: | 1.5.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Ramen Software |
| FileDescription: | Windhawk |
| FileVersion: | 1.5.1 |
| LegalCopyright: | https://windhawk.net/ |
| ProductName: | Windhawk |
| ProductVersion: | 1.5.1 |
Total processes
124
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4292 | "C:\Users\admin\Desktop\windhawk_setup.exe" /STANDARD /LANG=1033 | C:\Users\admin\Desktop\windhawk_setup.exe | windhawk_setup.exe | ||||||||||||
User: admin Company: Ramen Software Integrity Level: HIGH Description: Windhawk Version: 1.5.1 Modules
| |||||||||||||||
| 6152 | "C:\Users\admin\Desktop\windhawk_setup.exe" | C:\Users\admin\Desktop\windhawk_setup.exe | explorer.exe | ||||||||||||
User: admin Company: Ramen Software Integrity Level: MEDIUM Description: Windhawk Exit code: 0 Version: 1.5.1 Modules
| |||||||||||||||
Total events
4 504
Read events
4 485
Write events
19
Delete events
0
Modification events
| (PID) Process: | (6152) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6152) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6152) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6152) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4292) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4292) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4292) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4292) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4292) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4292) windhawk_setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
6
Suspicious files
180
Text files
1 354
Unknown types
307
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4292 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\windhawk-compiler-1.5[1].7z | — | |
MD5:— | SHA256:— | |||
| 4292 | windhawk_setup.exe | C:\Program Files\Windhawk\Compiler\windhawk-compiler.7z | — | |
MD5:— | SHA256:— | |||
| 4292 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nstC7BF.tmp\System.dll | executable | |
MD5:192639861E3DC2DC5C08BB8F8C7260D5 | SHA256:23D618A0293C78CE00F7C6E6DD8B8923621DA7DD1F63A070163EF4C0EC3033D6 | |||
| 4292 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nstC7BF.tmp\modern-header.bmp | image | |
MD5:DA5C5013B5FEABD247AC98460D5F4077 | SHA256:42023BAF6AB9CC3DAF47FBEBE76B78C6B22C560A863B557BEFEF4A68304928A5 | |||
| 4292 | windhawk_setup.exe | C:\Program Files\Windhawk\Compiler\i686-w64-mingw32\lib\crt2.o | binary | |
MD5:69277114423DC0C9EE65F767A9608651 | SHA256:083D8E22B323216AD6B99B2518F407DFFE2BDE0985F654B730A6B58C6AC7D1A7 | |||
| 6152 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nsiAC95.tmp | binary | |
MD5:C473624C9F4EE79B0E1D490D1B0FB4EB | SHA256:7DC1894111DE0E1A5A21BF6EBB95045343B23852B44EE240A496C0AD6A86D537 | |||
| 4292 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nstC7BF.tmp\INetC.dll | executable | |
MD5:40D7ECA32B2F4D29DB98715DD45BFAC5 | SHA256:85E03805F90F72257DD41BFDAA186237218BBB0EC410AD3B6576A88EA11DCCB9 | |||
| 4292 | windhawk_setup.exe | C:\Program Files\Windhawk\Compiler\i686-w64-mingw32\lib\crt1.o | binary | |
MD5:69277114423DC0C9EE65F767A9608651 | SHA256:083D8E22B323216AD6B99B2518F407DFFE2BDE0985F654B730A6B58C6AC7D1A7 | |||
| 4292 | windhawk_setup.exe | C:\Program Files\Windhawk\Compiler\i686-w64-mingw32\lib\crt1u.o | binary | |
MD5:92C573C1C1E459F284699665B3E6577D | SHA256:C23E258715337AE35295078CBC5D33E98EE47B229E6DF0FDEC12847A6AAA79E2 | |||
| 4292 | windhawk_setup.exe | C:\Users\admin\AppData\Local\Temp\nstC7BF.tmp\modern-wizard.bmp | image | |
MD5:566514B5802E326406DF34C35877484F | SHA256:4653F410DCB67A35E280BDEF7D563EF8F5788E72A05D472419F9E864AF563984 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
17
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 302 | 140.82.121.4:443 | https://github.com/ramensoftware/windhawk-dependencies/releases/download/v1.5/windhawk-compiler-1.5.7z | unknown | — | — | unknown |
— | — | GET | 302 | 104.21.74.253:443 | https://ramensoftware.com/downloads/windhawk-compiler-1.5.7z | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6052 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
6400 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6052 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4324 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4292 | windhawk_setup.exe | 104.21.74.253:443 | ramensoftware.com | CLOUDFLARENET | — | suspicious |
4292 | windhawk_setup.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ramensoftware.com |
| unknown |
github.com |
| shared |
objects.githubusercontent.com |
| shared |