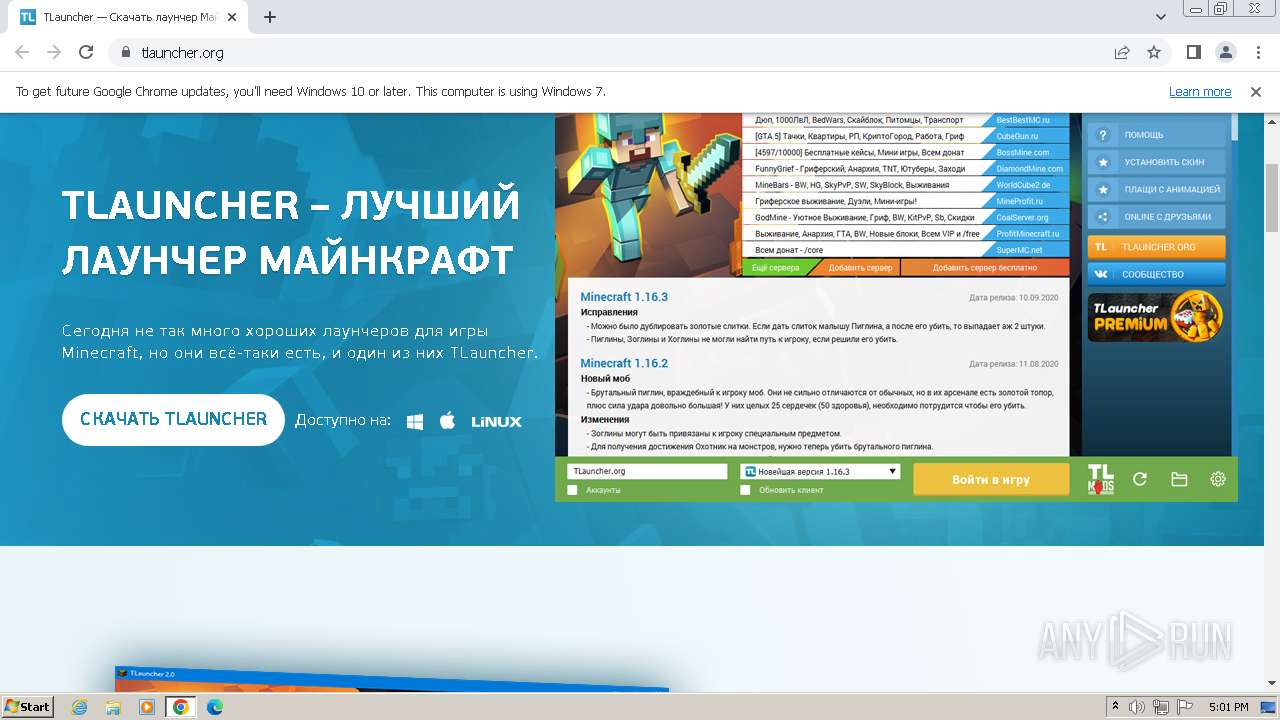
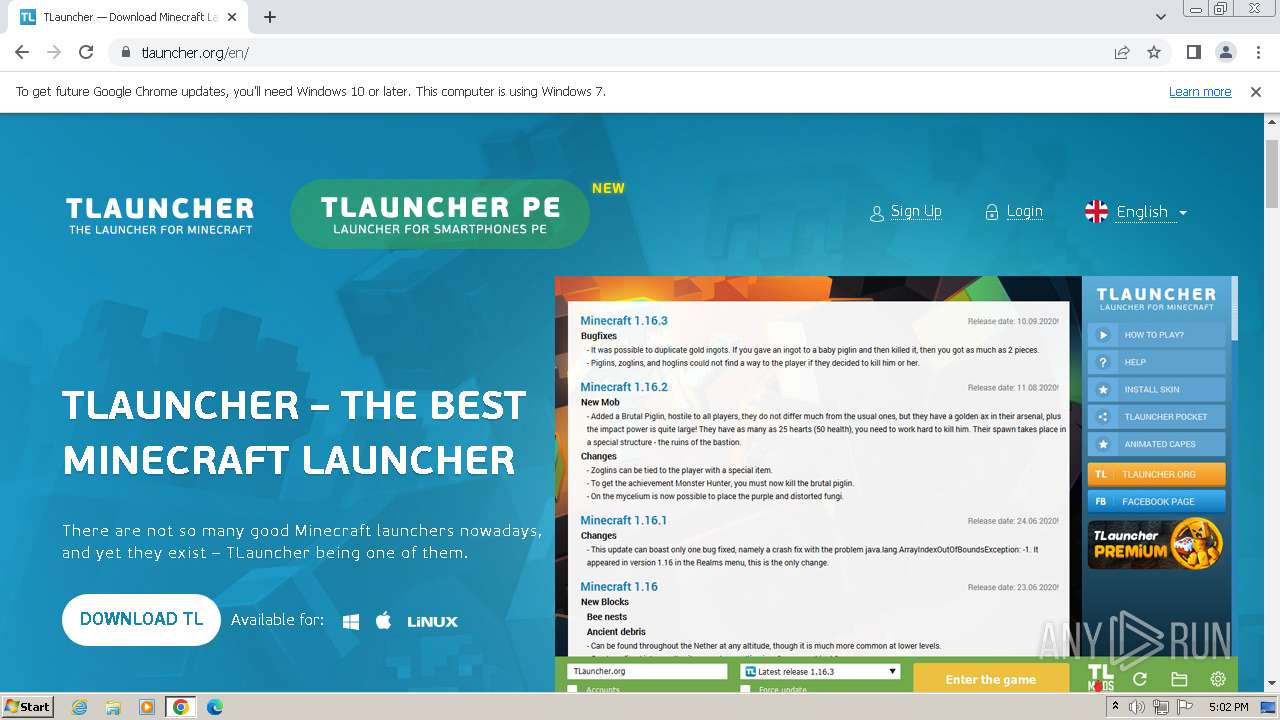
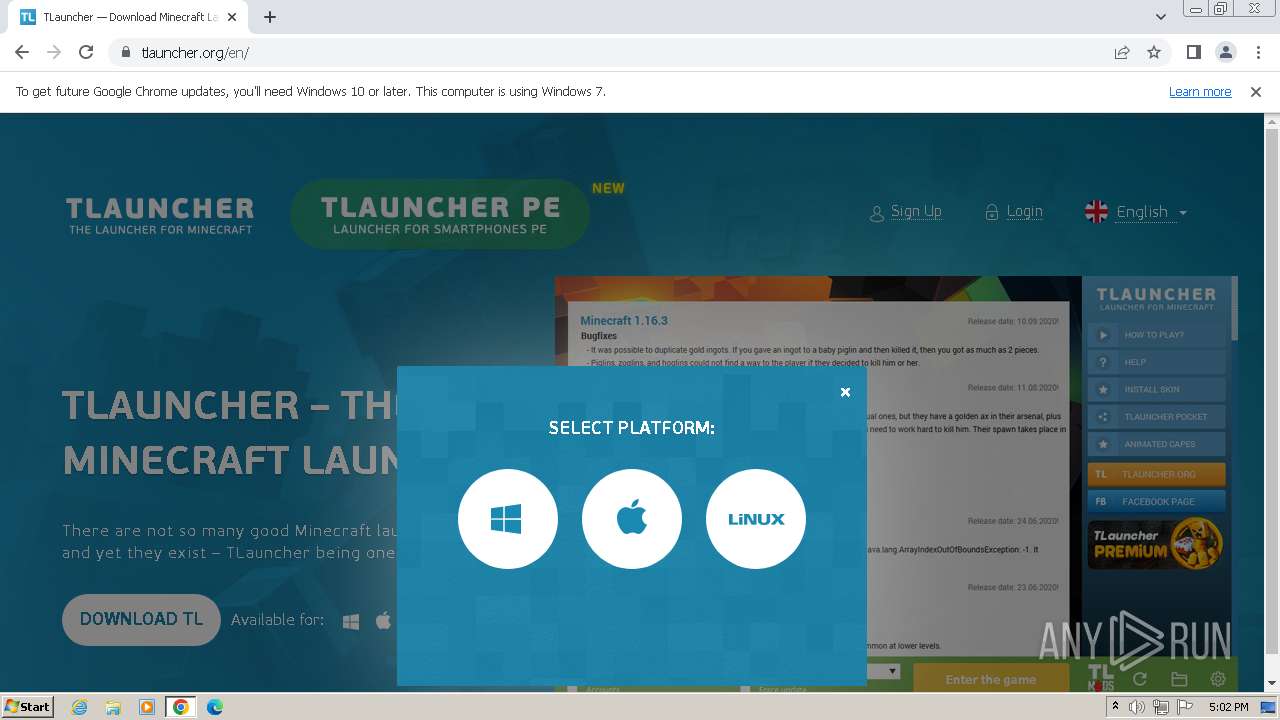
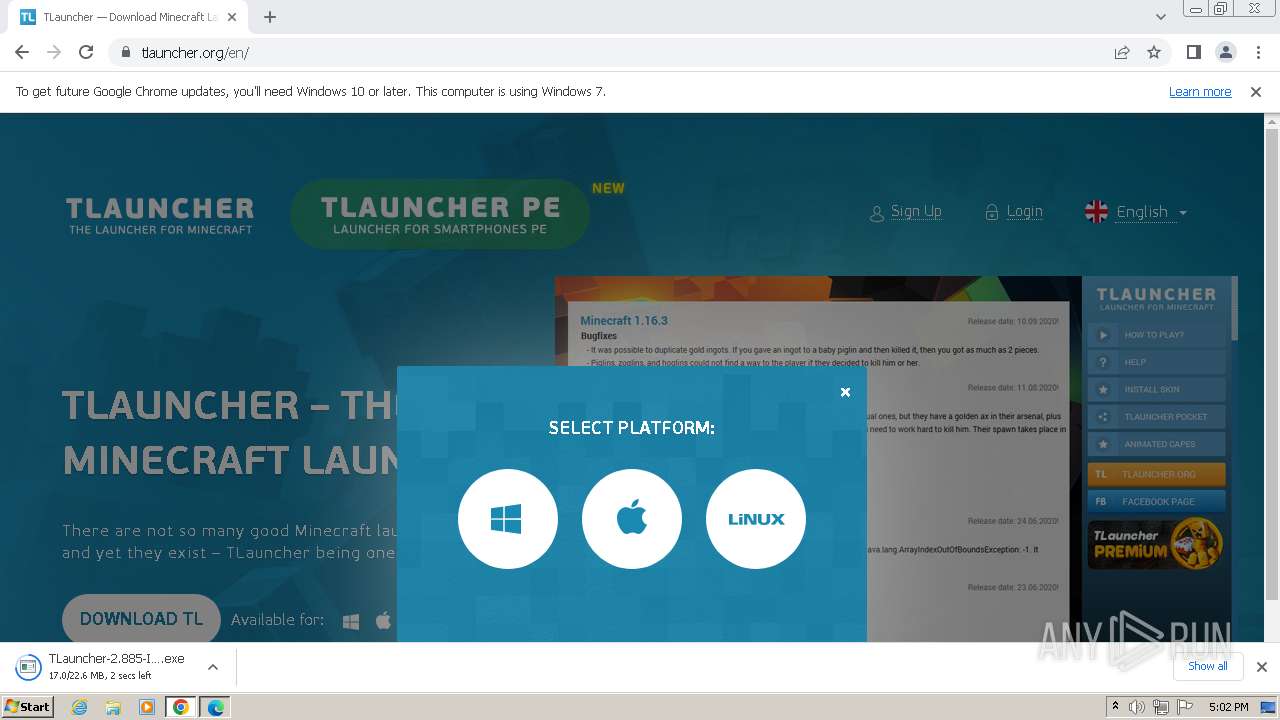
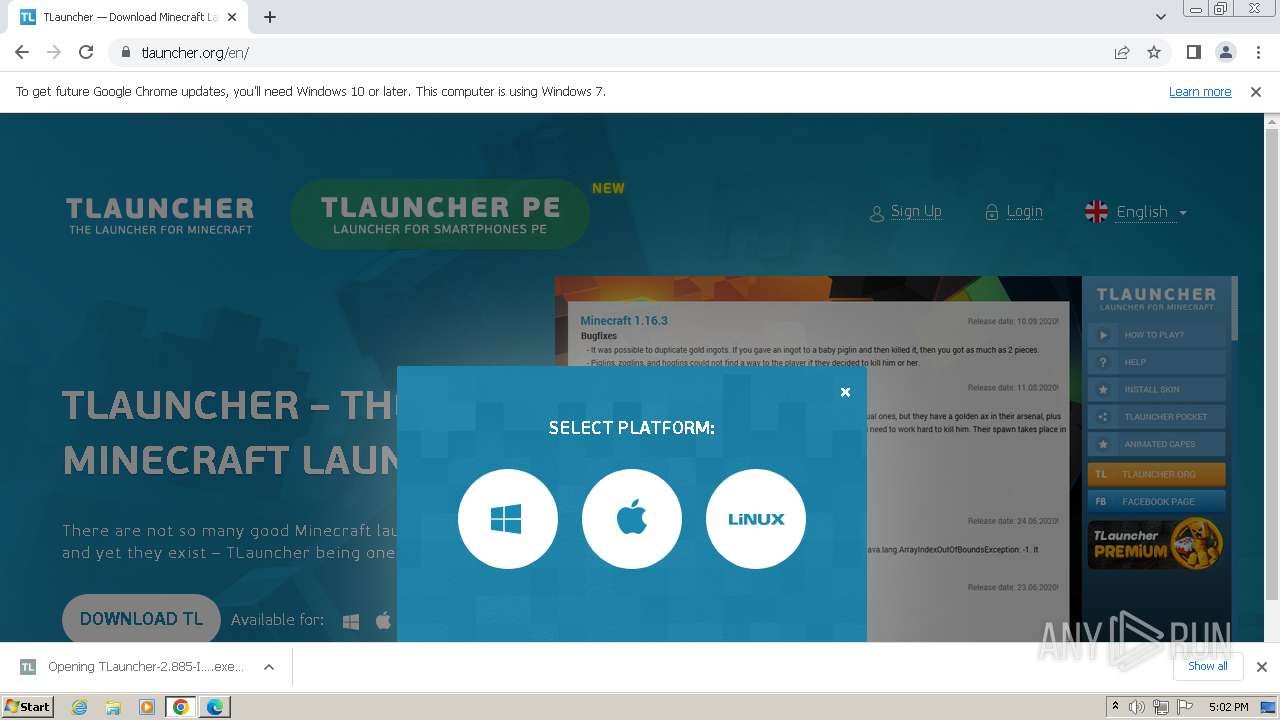
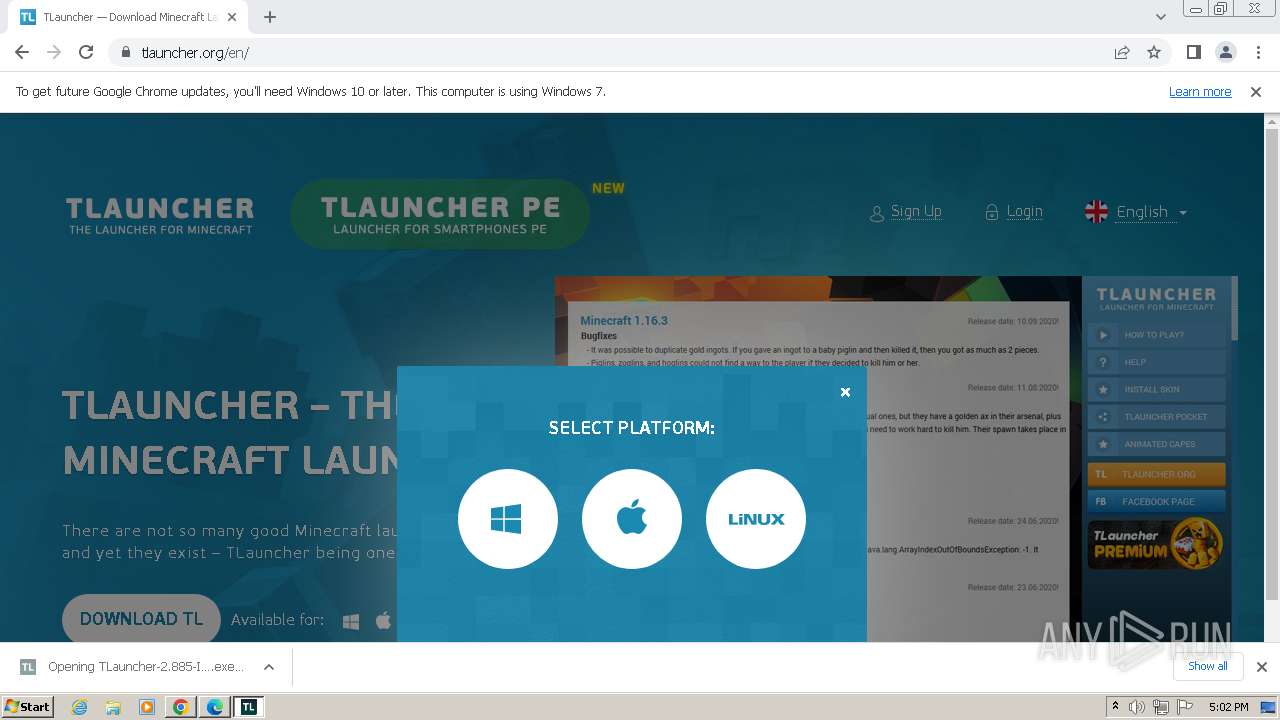
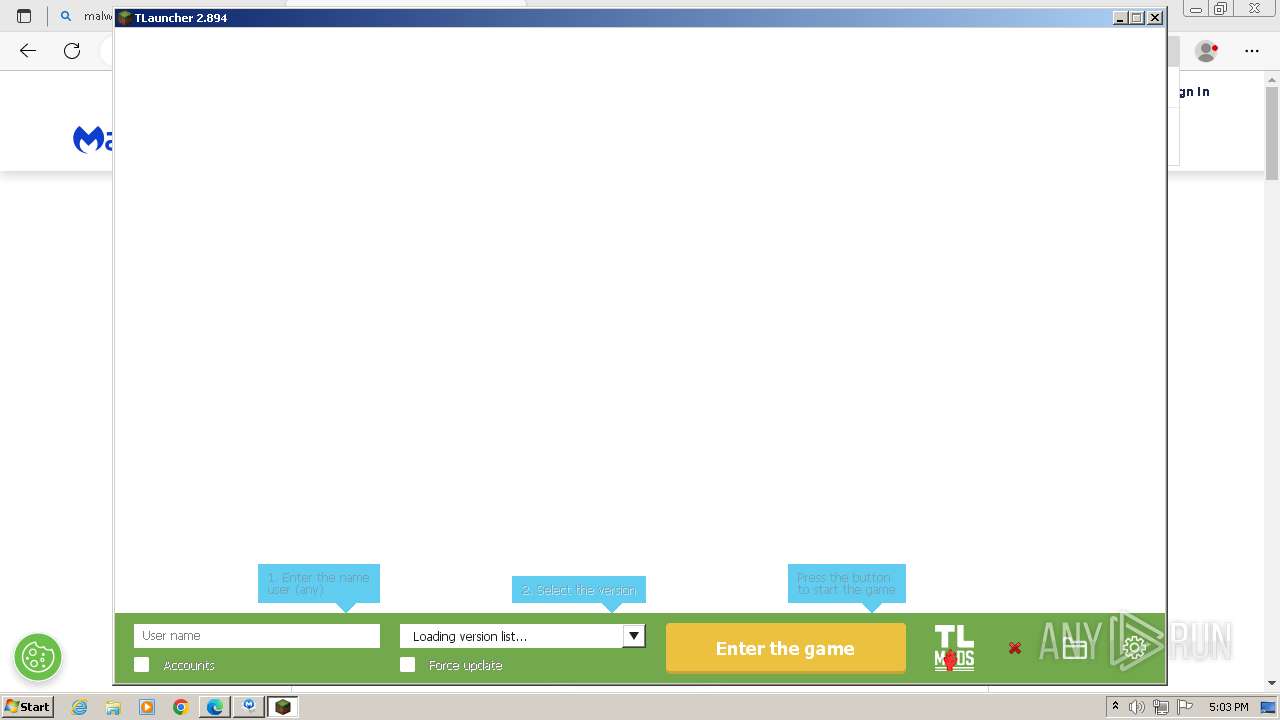
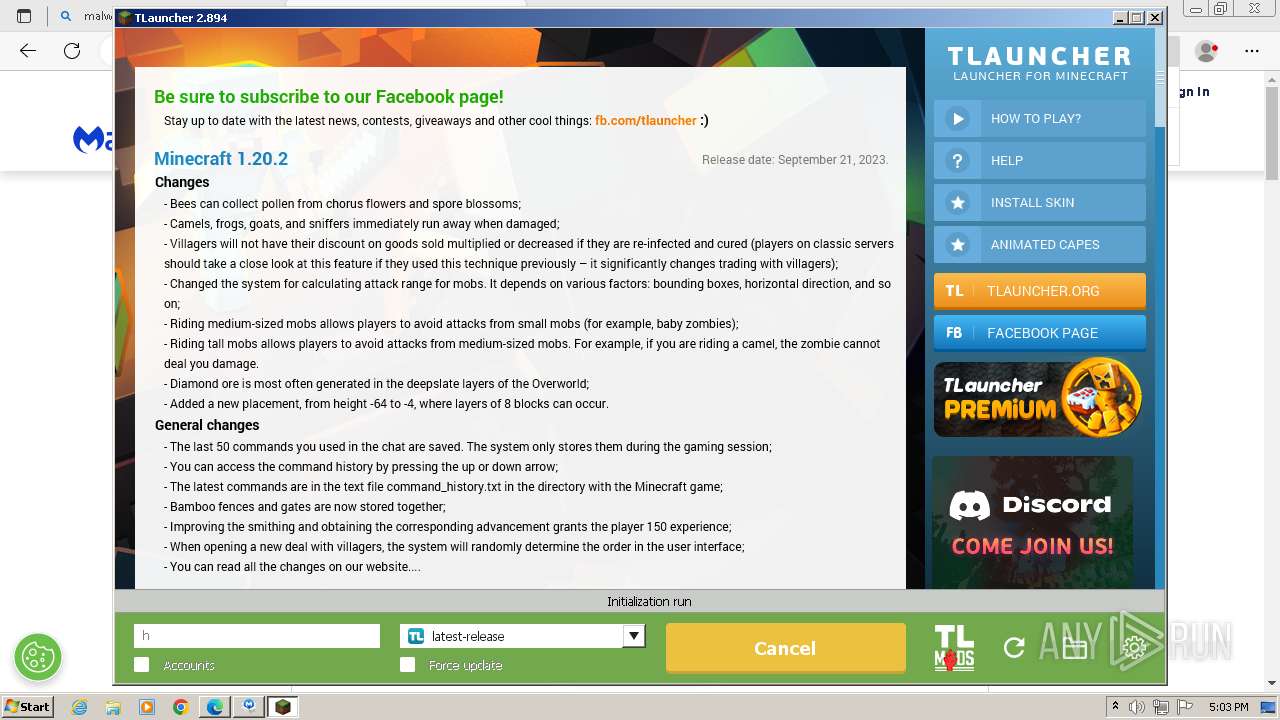
| URL: | tlauncher.org |
| Full analysis: | https://app.any.run/tasks/6f1b516b-45fc-4dee-8c2a-6b4597b3a672 |
| Verdict: | Malicious activity |
| Analysis date: | October 21, 2023, 16:01:40 |
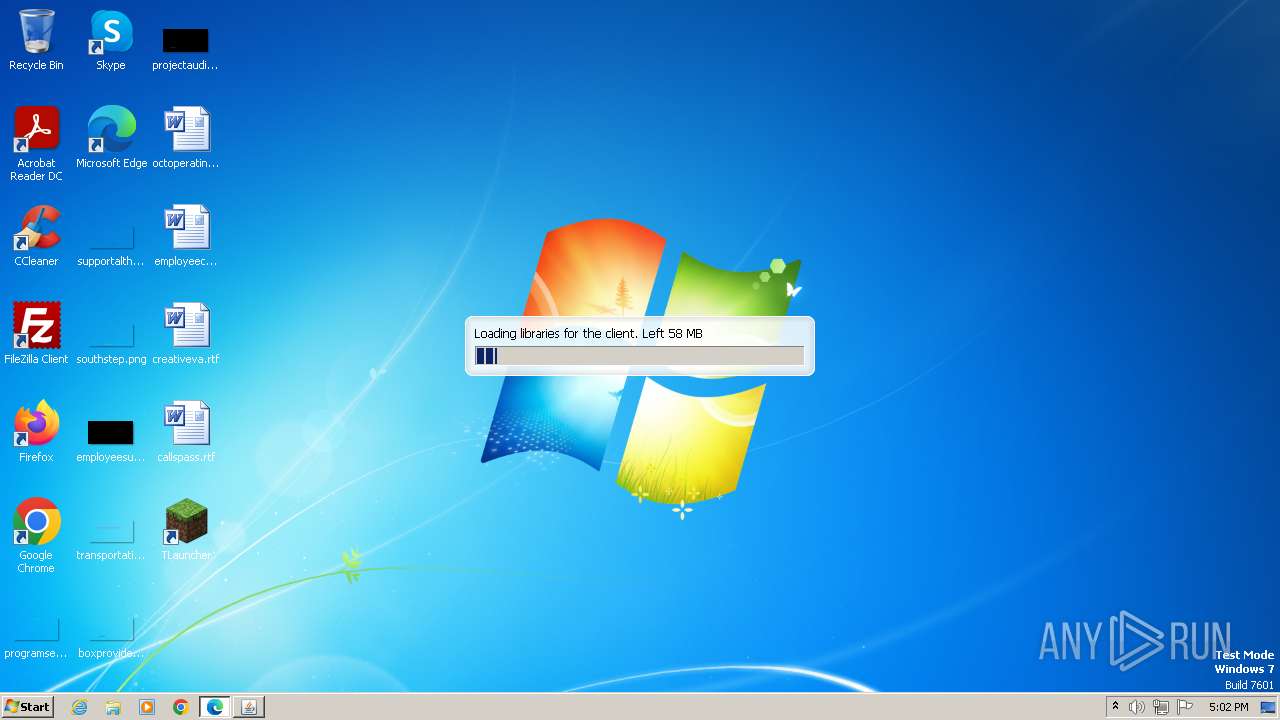
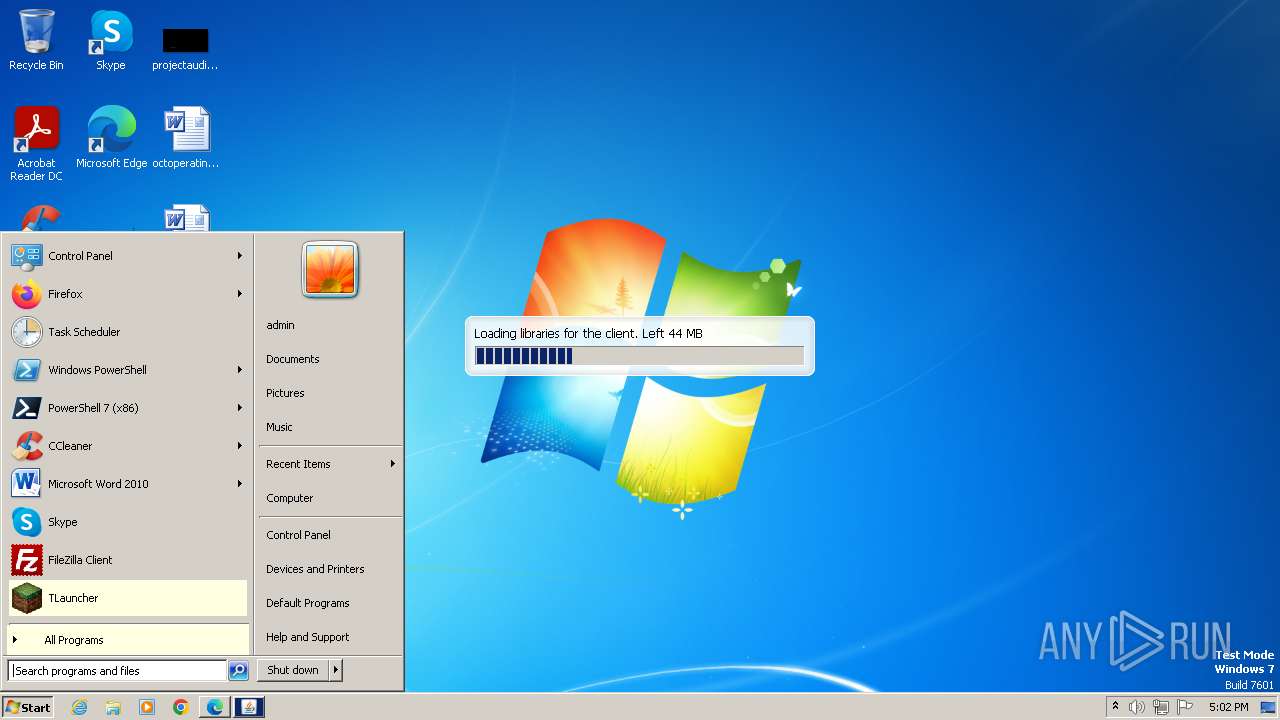
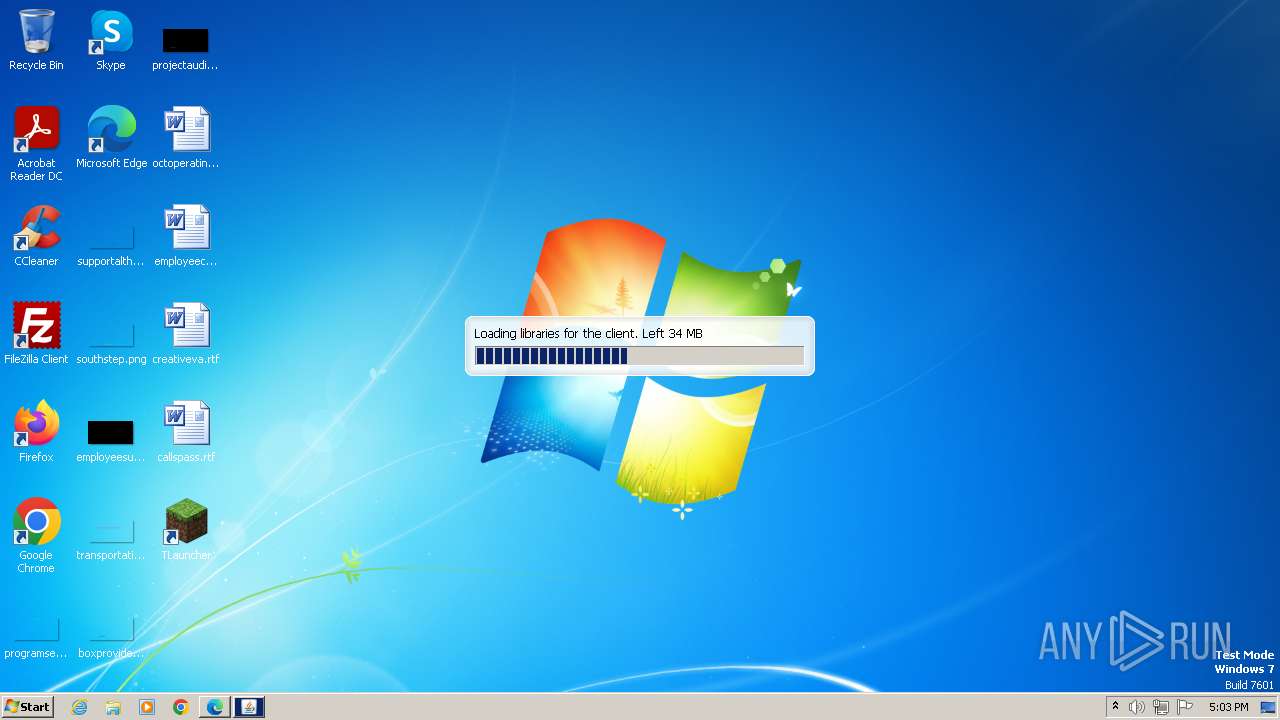
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BBC528DE5026EBFE34500509055792B9 |
| SHA1: | 324E368D43A346BFF3E4F386C408F103C5D41619 |
| SHA256: | E604DB46499A4CFC1BACC72E3A25C8A0E2C87ED2ED9A1BDE6B963A27FDD64916 |
| SSDEEP: | 3:ceLuS:ce6S |
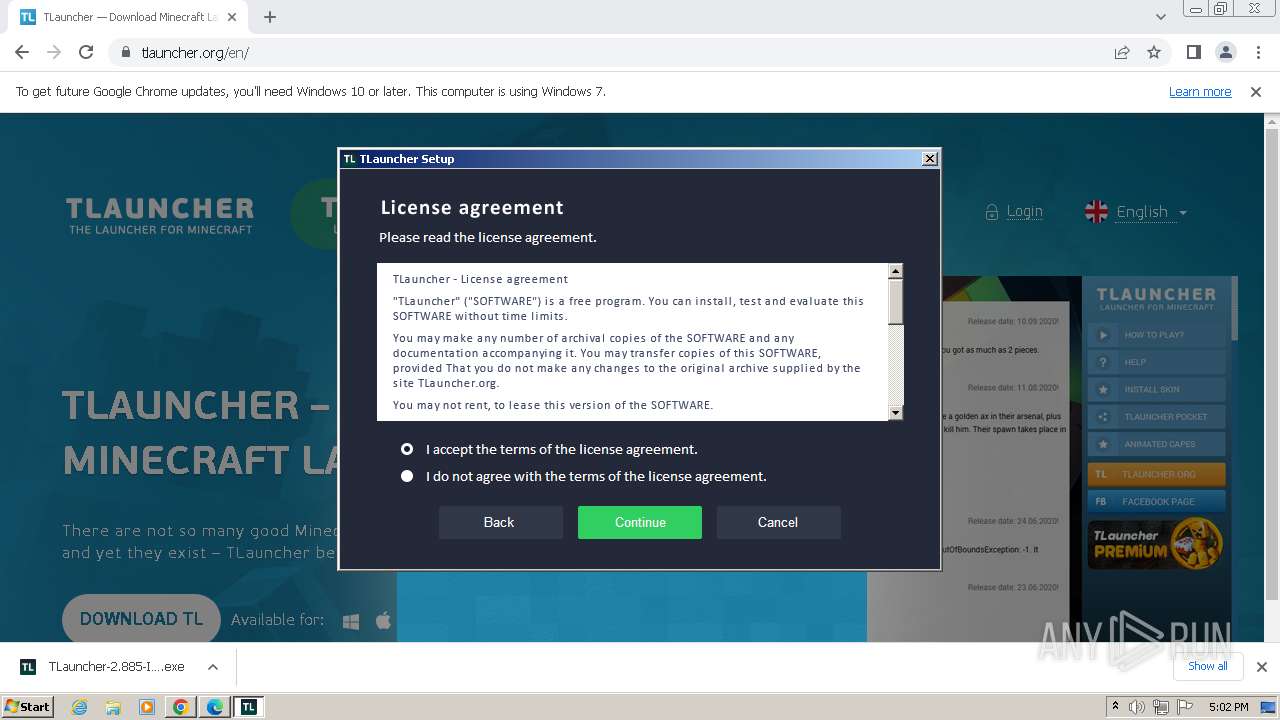
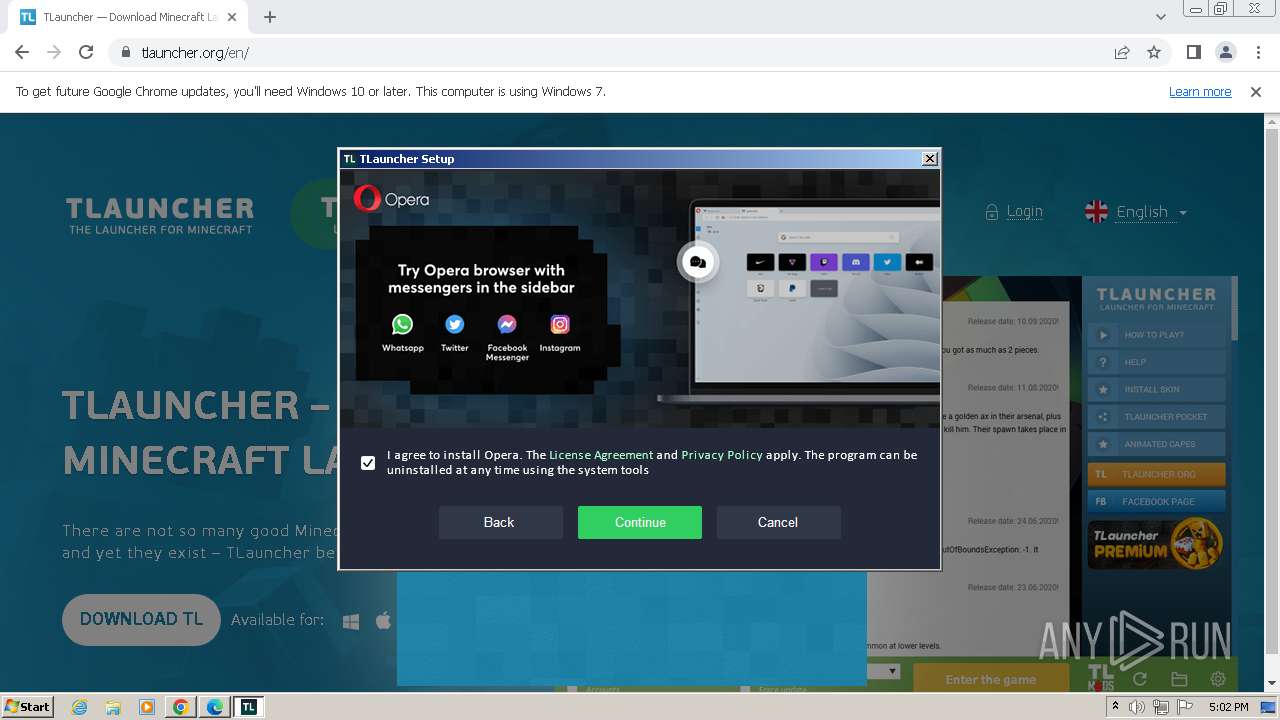
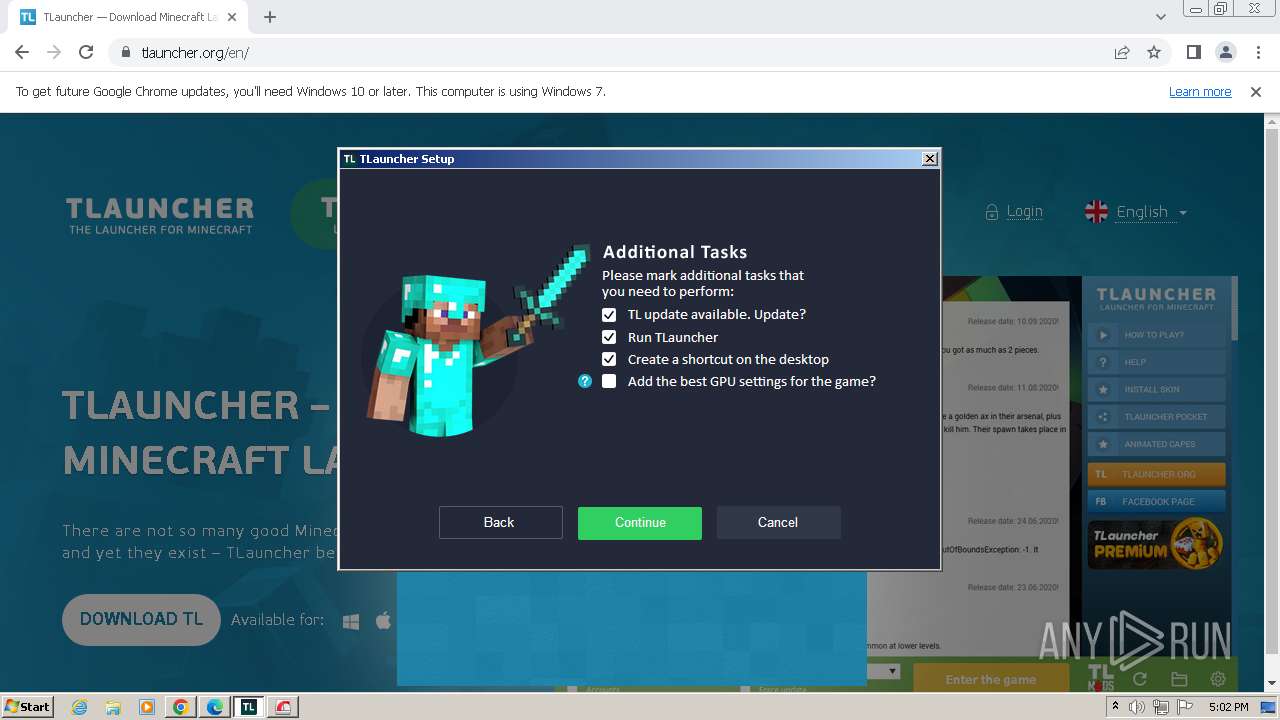
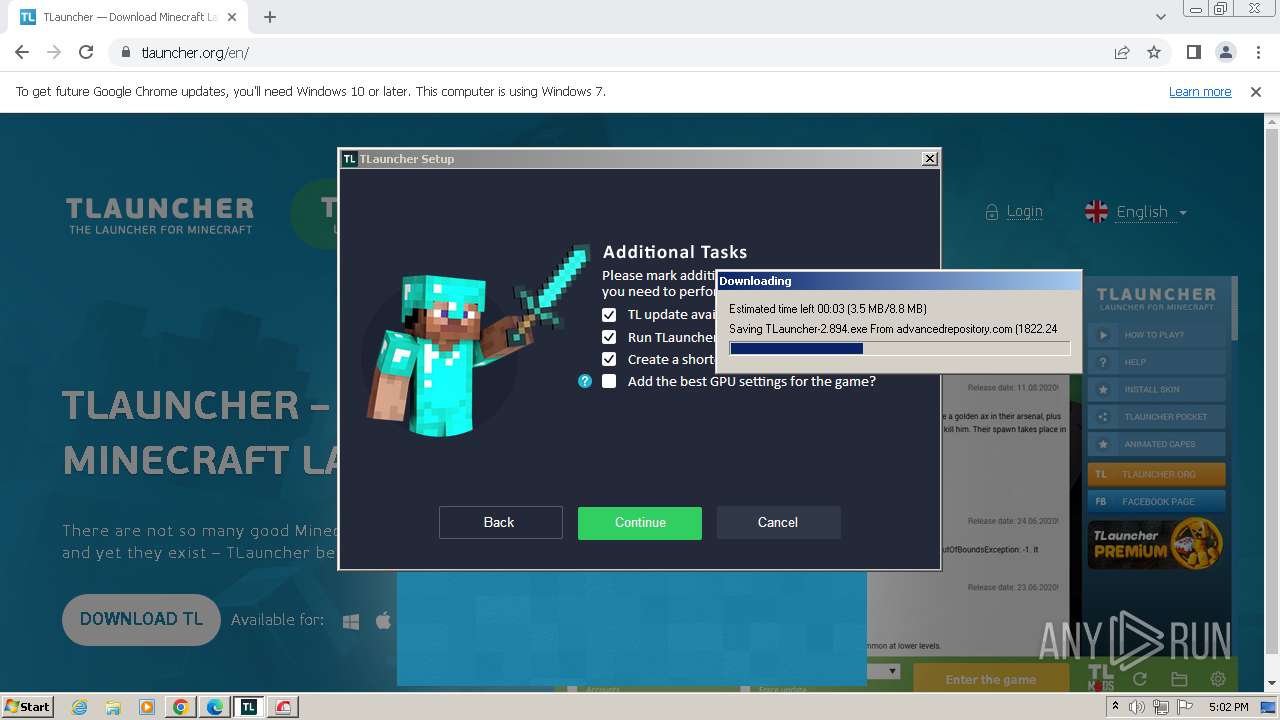
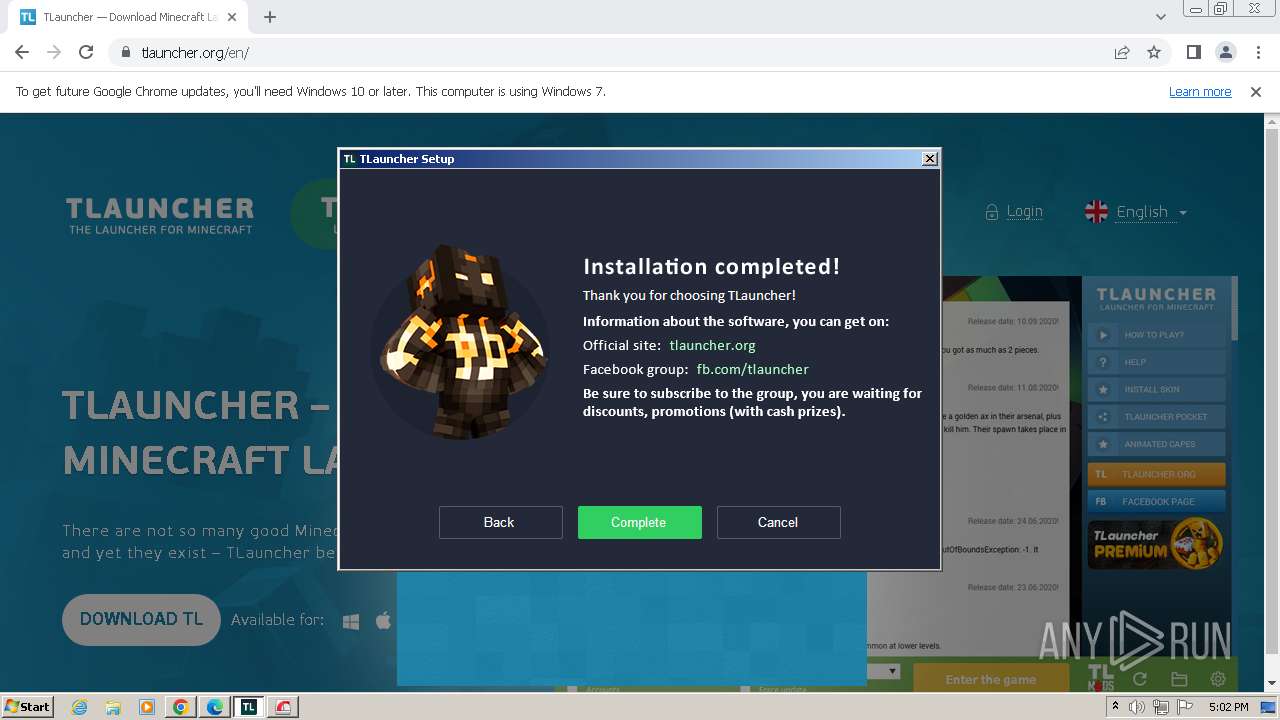
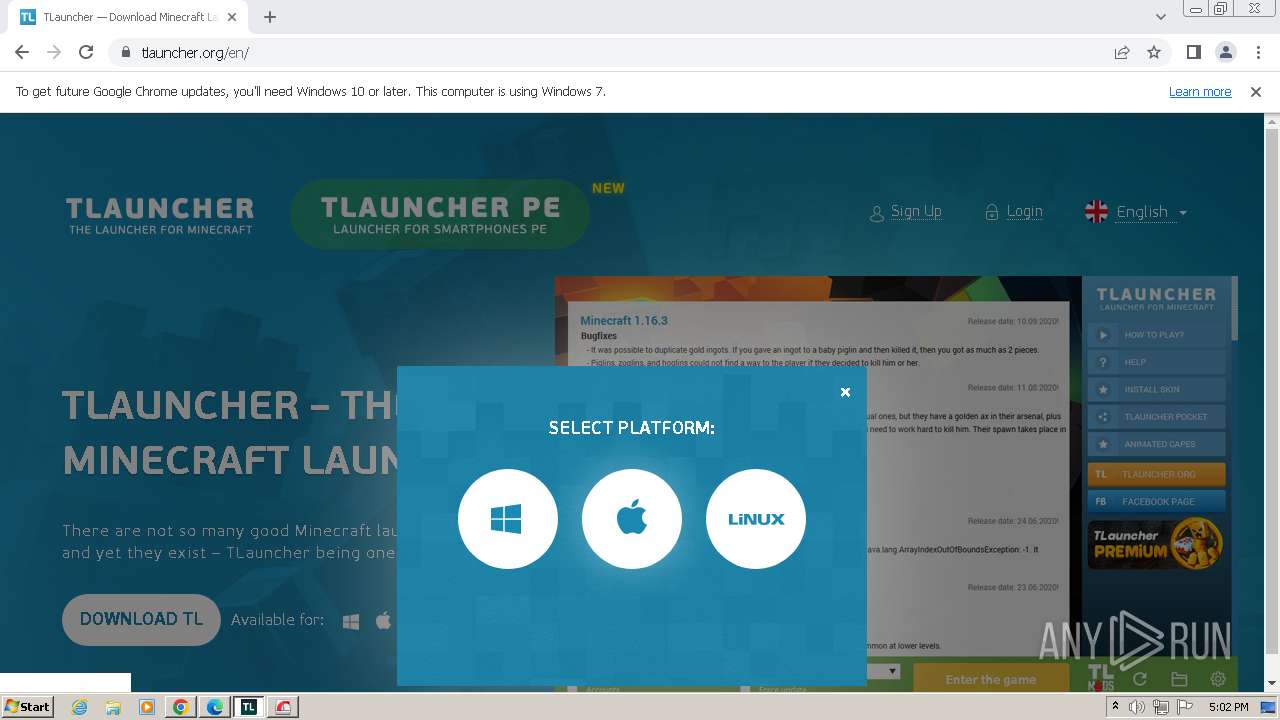
MALICIOUS
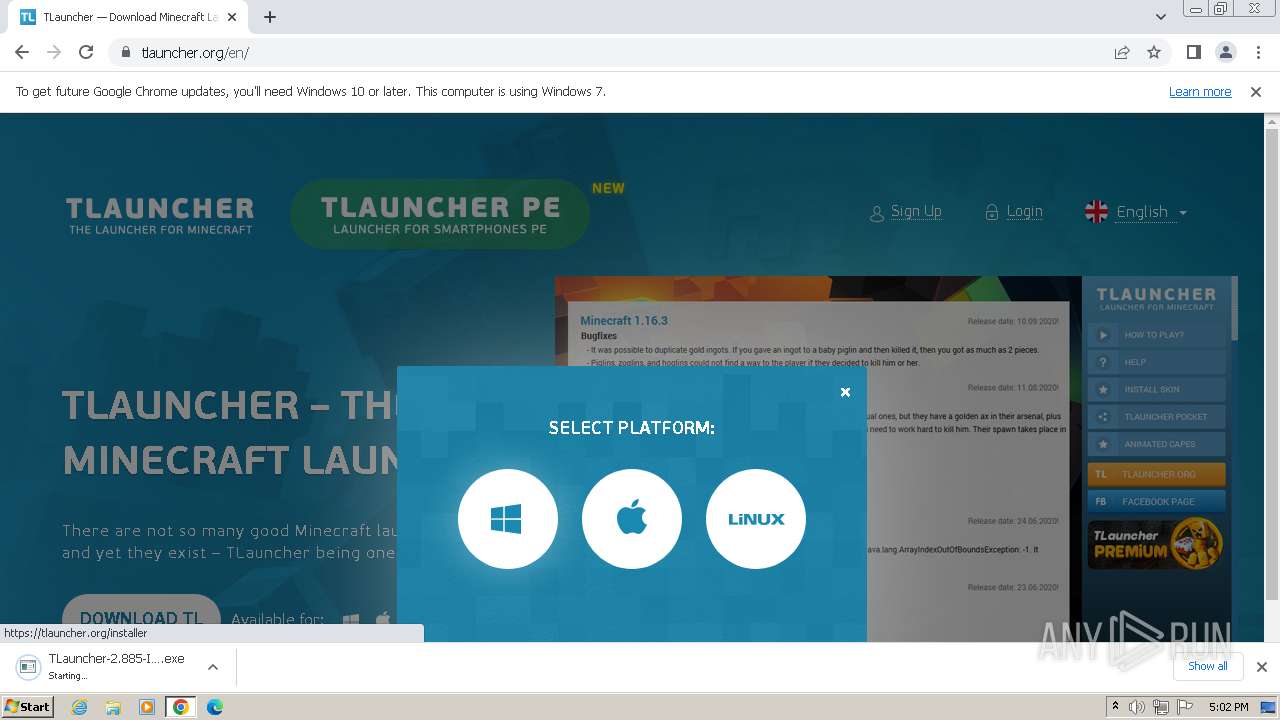
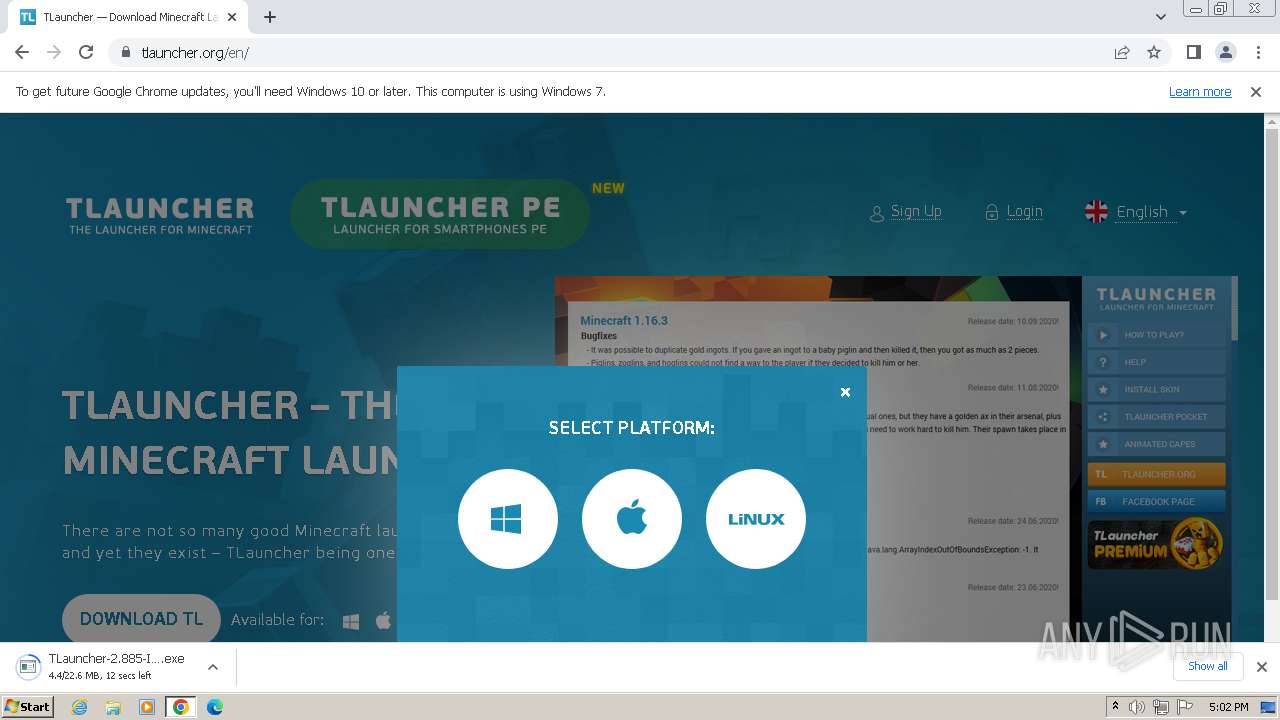
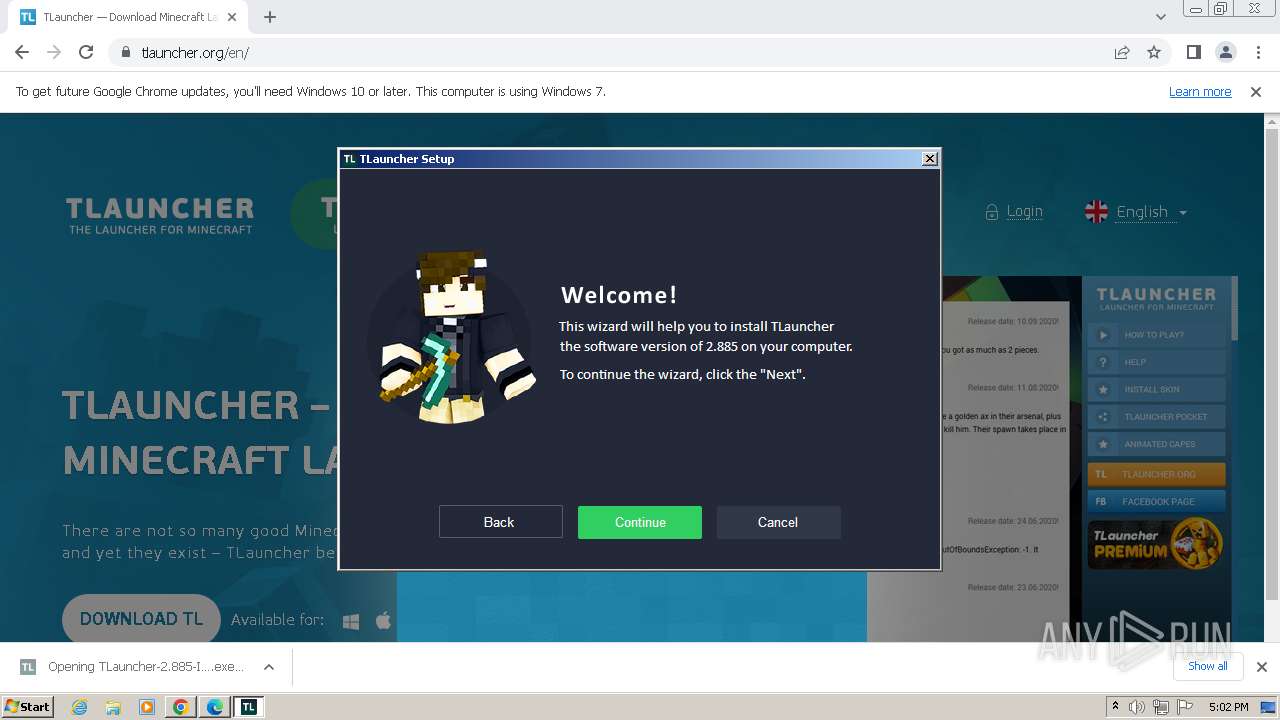
Application was dropped or rewritten from another process
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3772)
- TLauncher-2.885-Installer-1.1.3.exe (PID: 2184)
- irsetup.exe (PID: 3068)
- BrowserInstaller.exe (PID: 3872)
- irsetup.exe (PID: 3640)
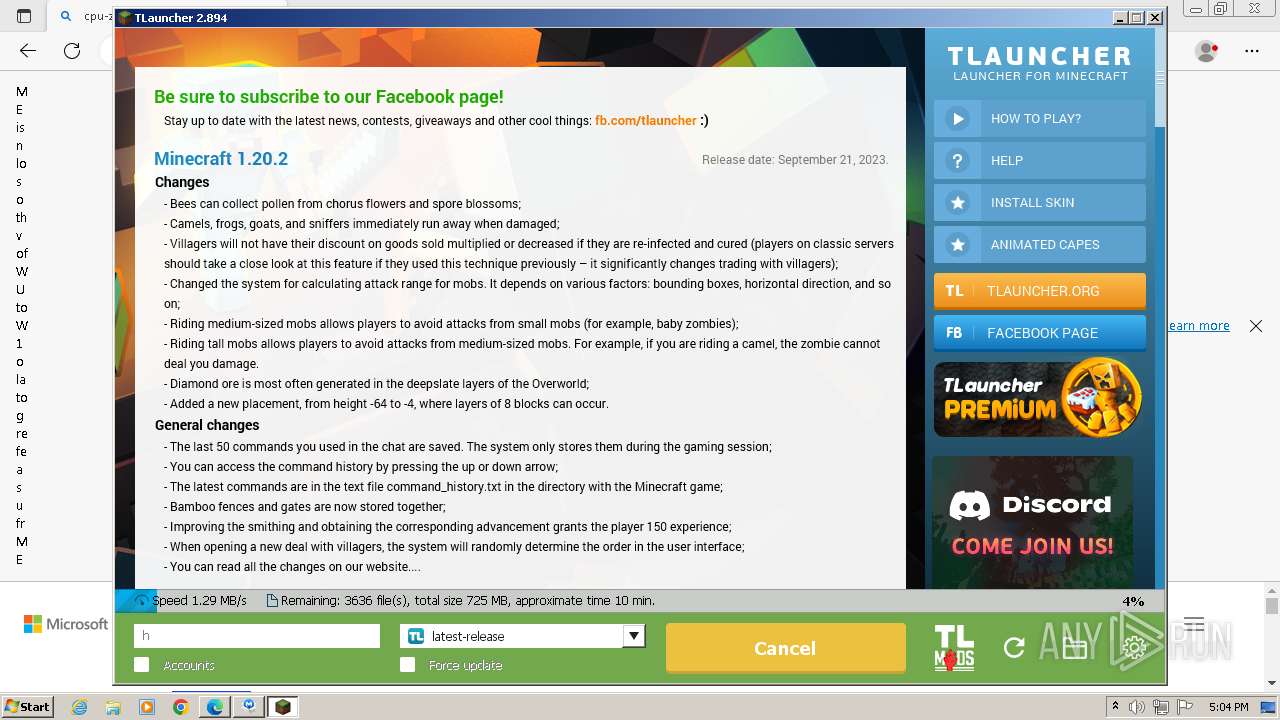
- TLauncher.exe (PID: 2080)
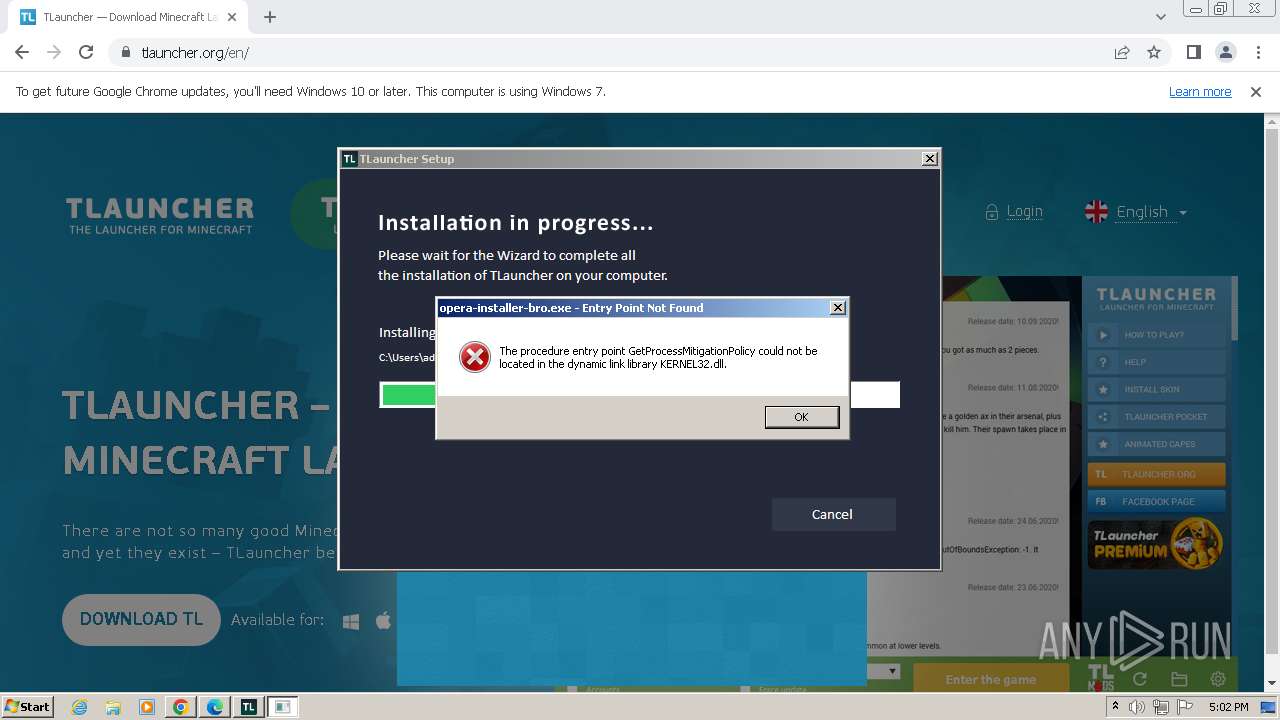
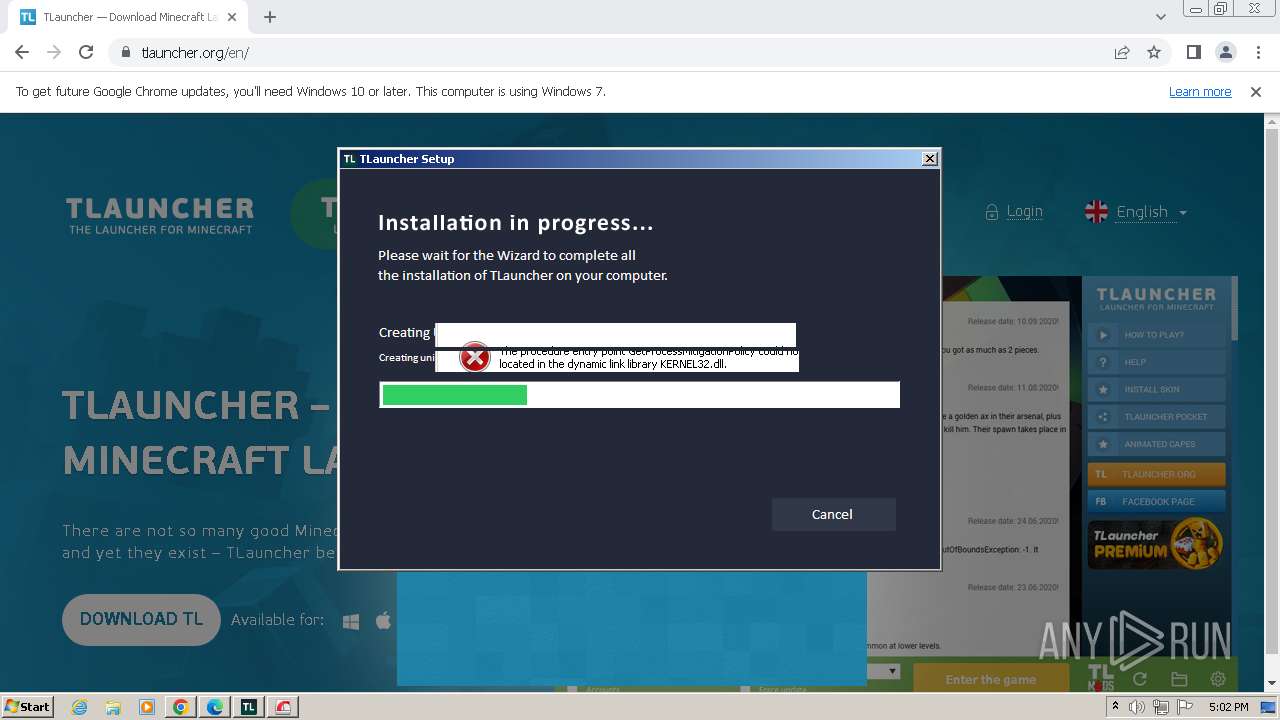
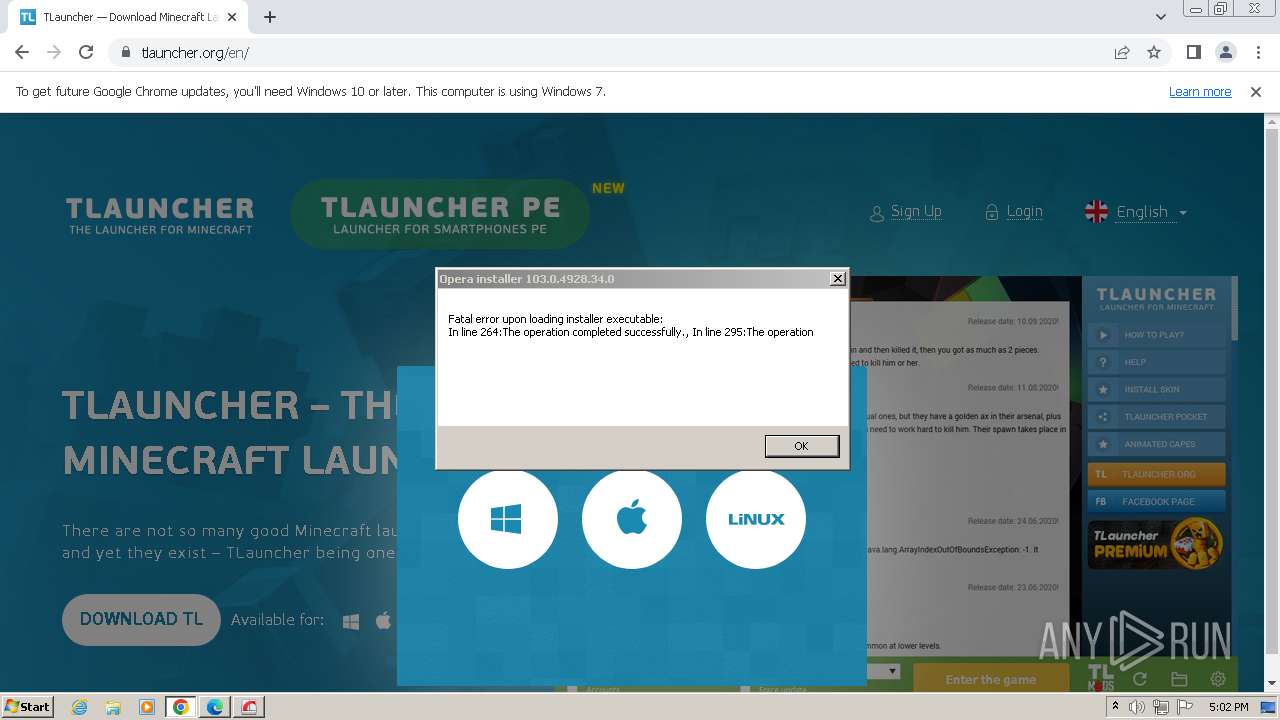
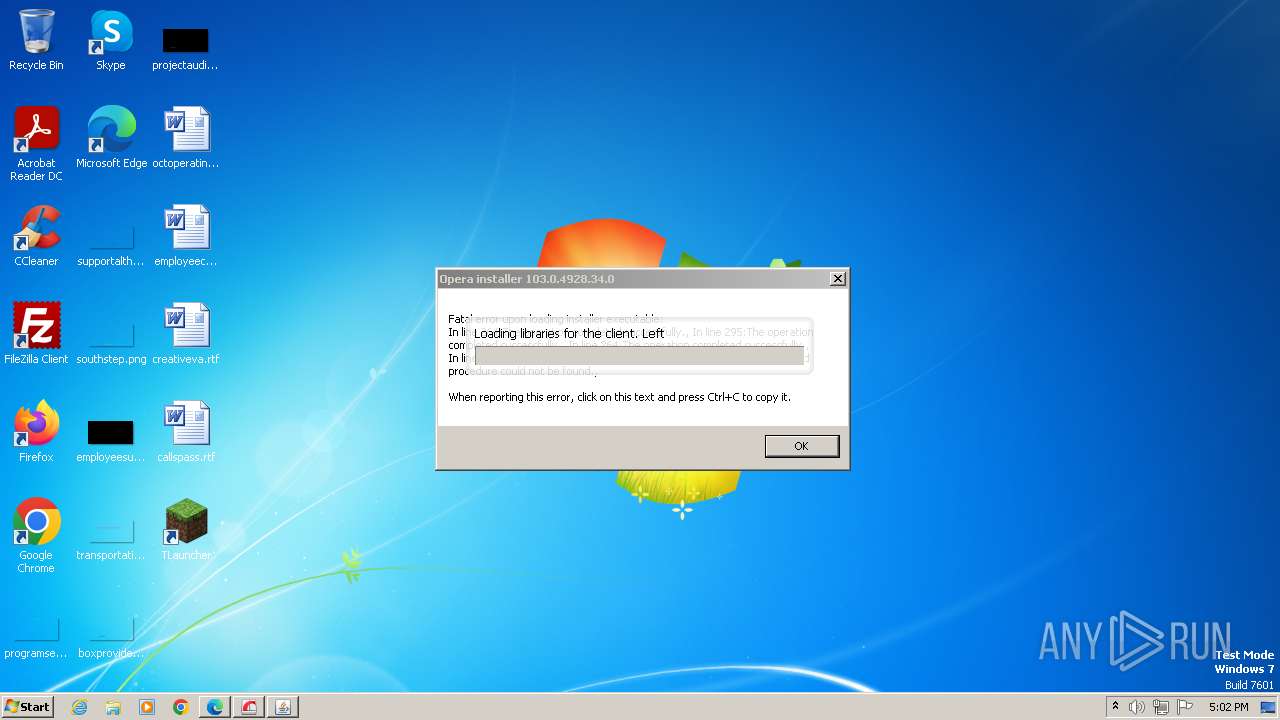
- opera-installer-bro.exe (PID: 4036)
- javaw.exe (PID: 3384)
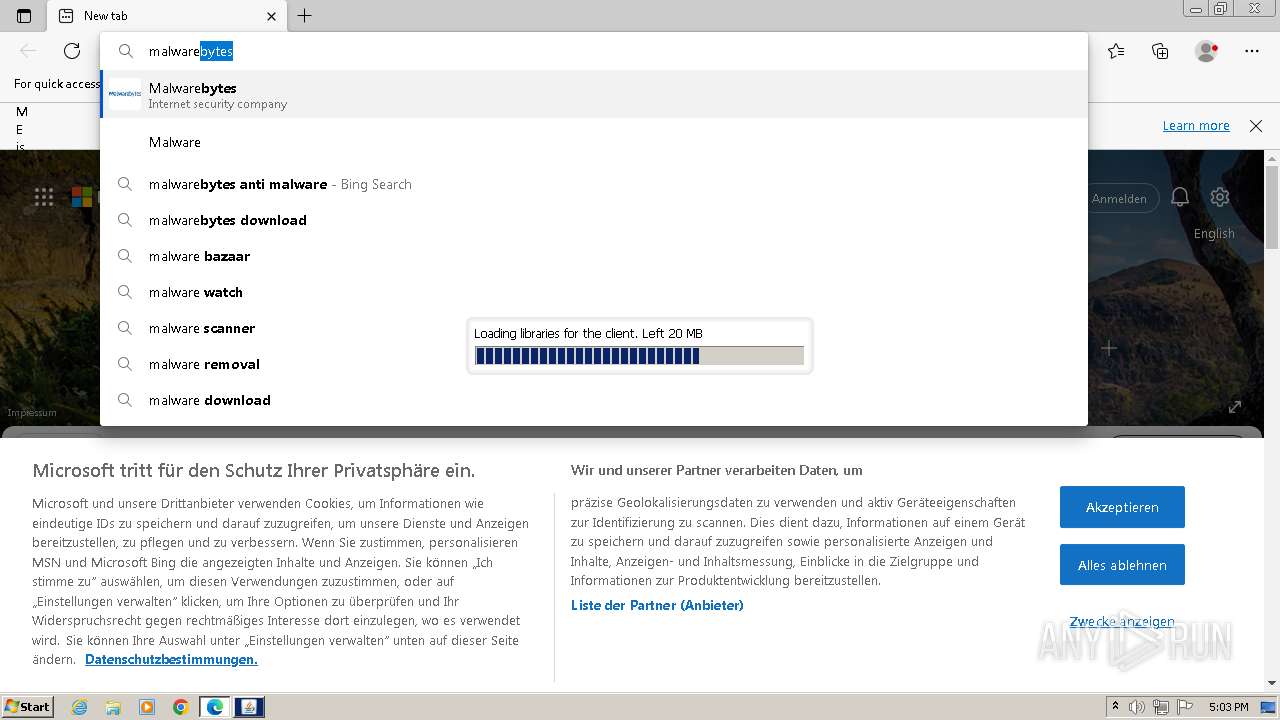
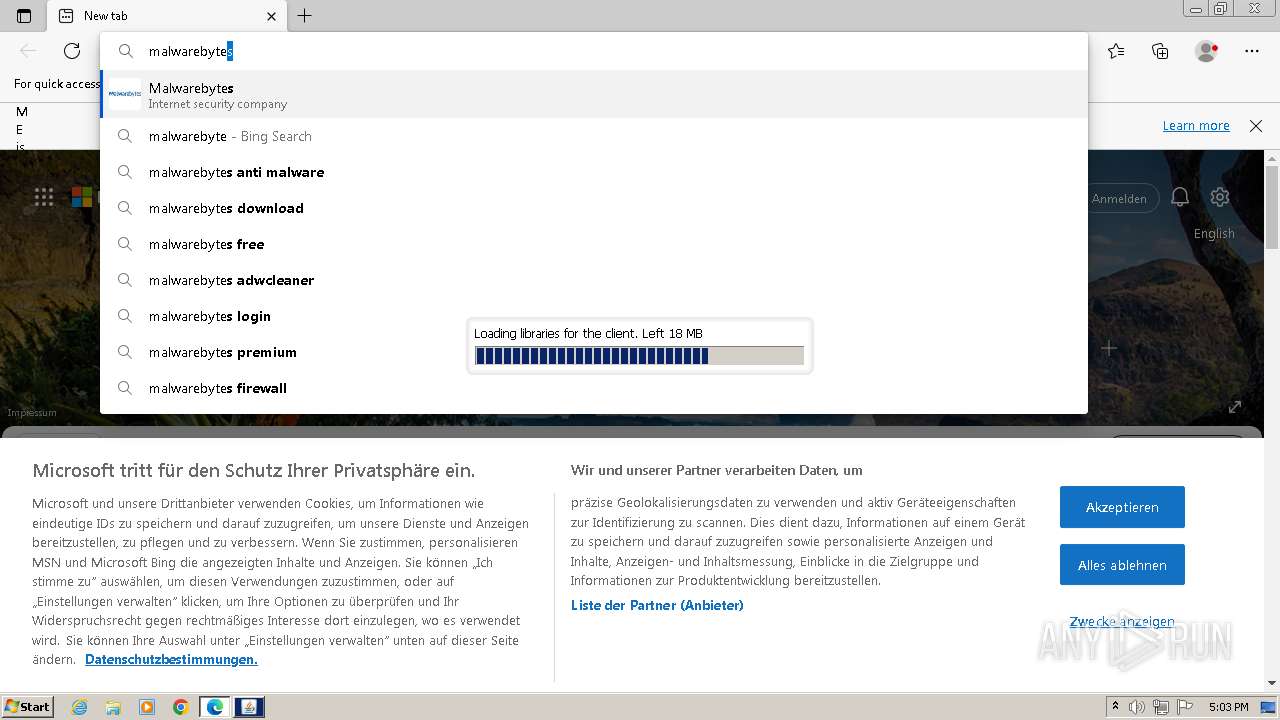
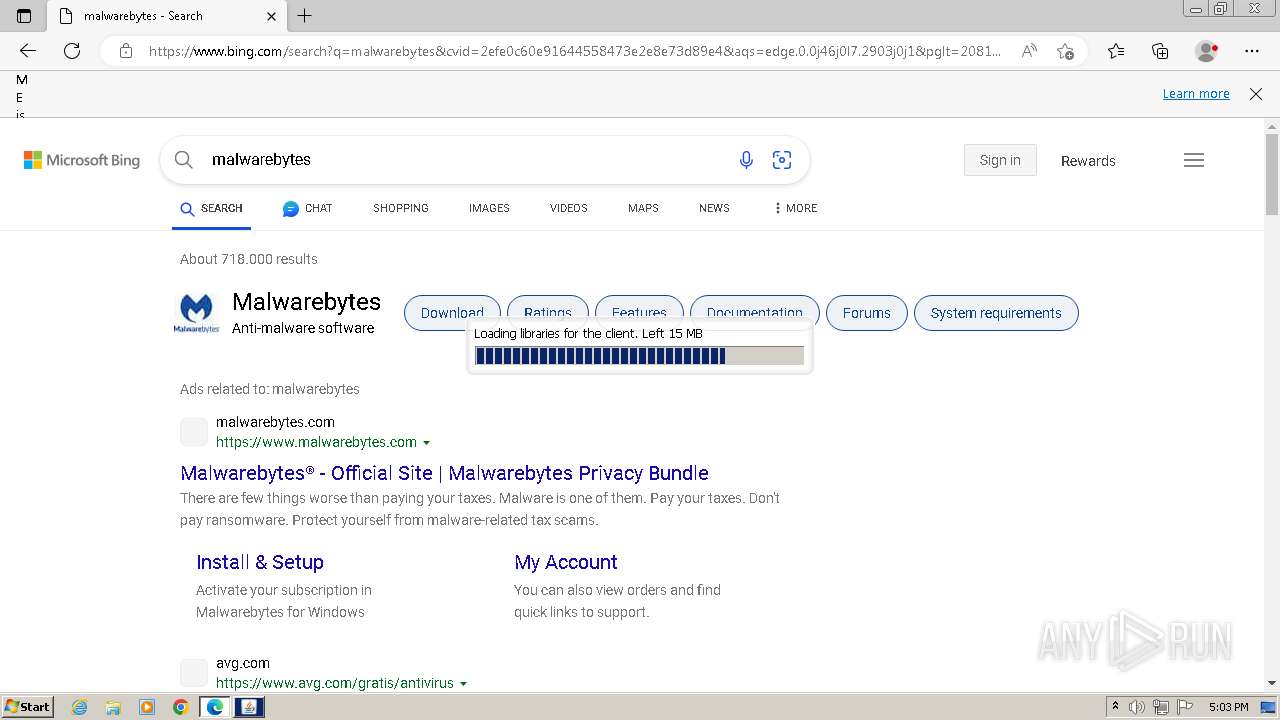
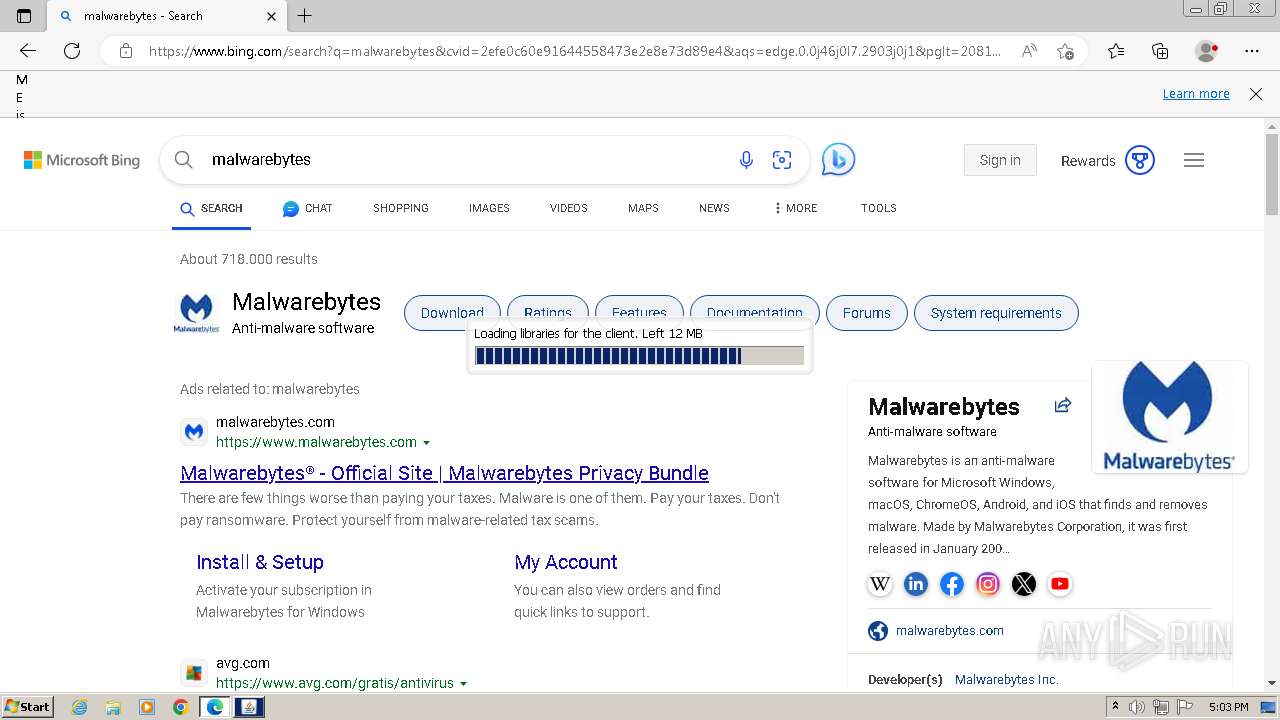
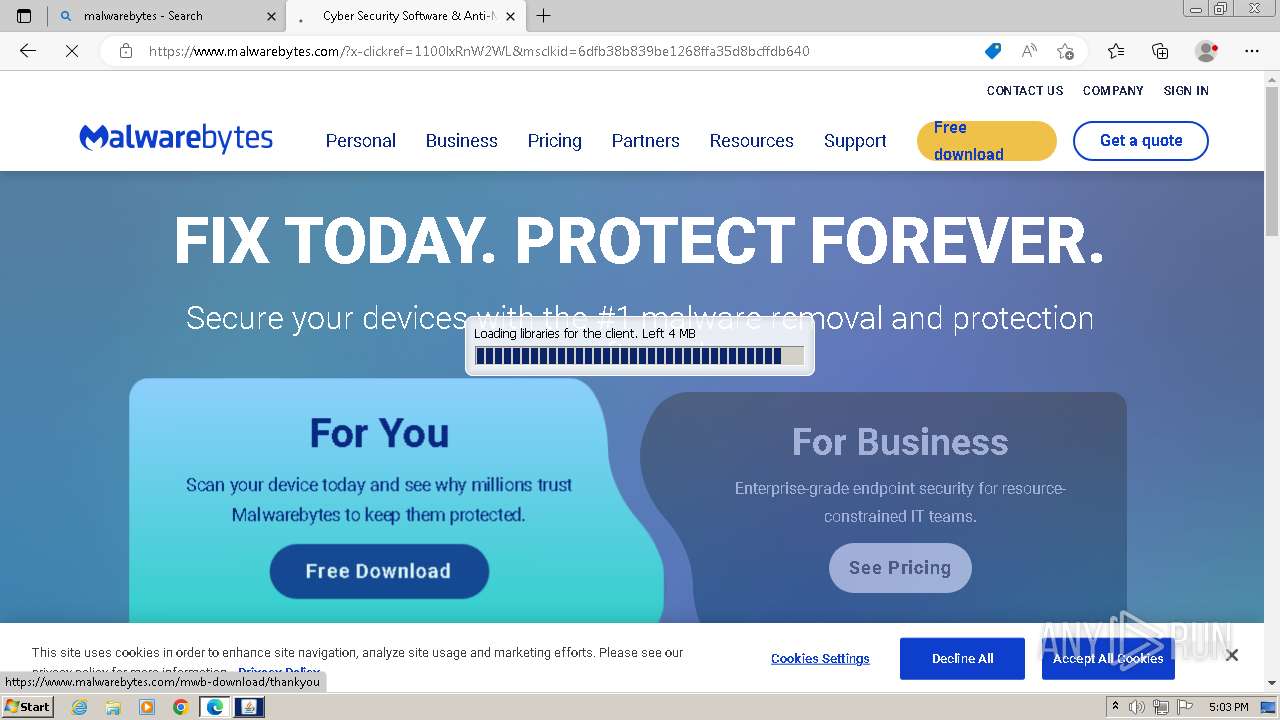
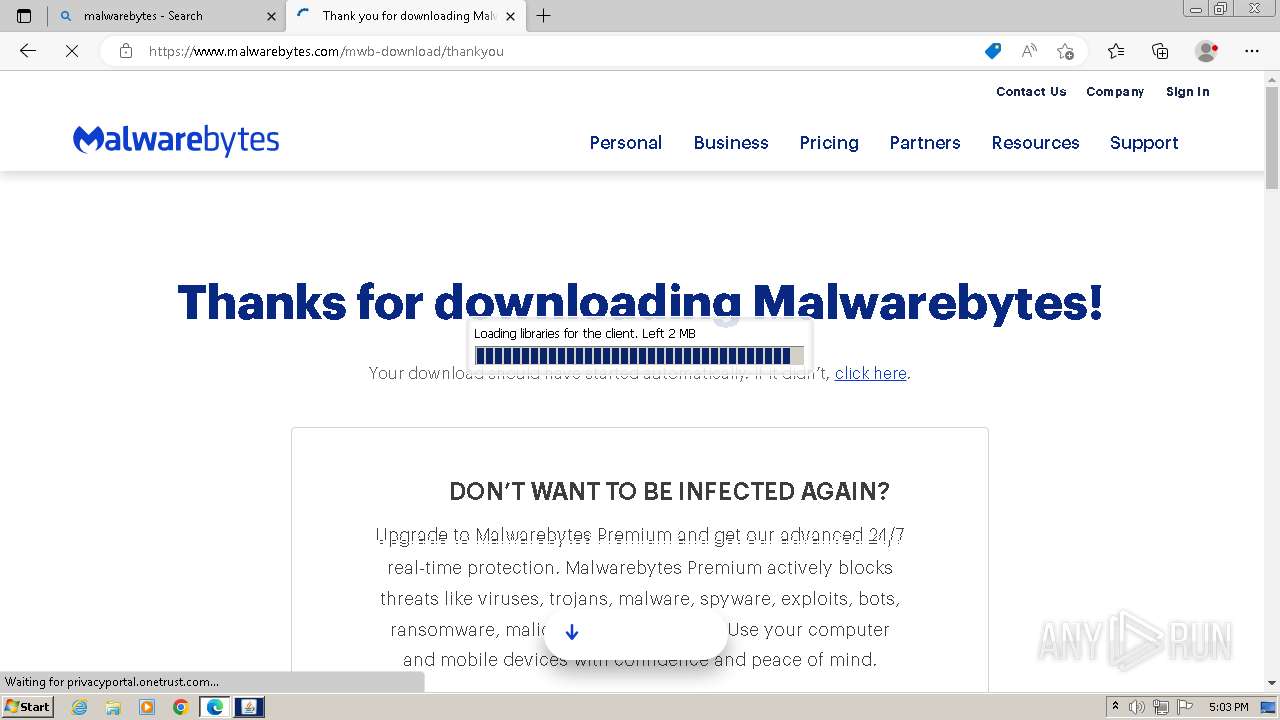
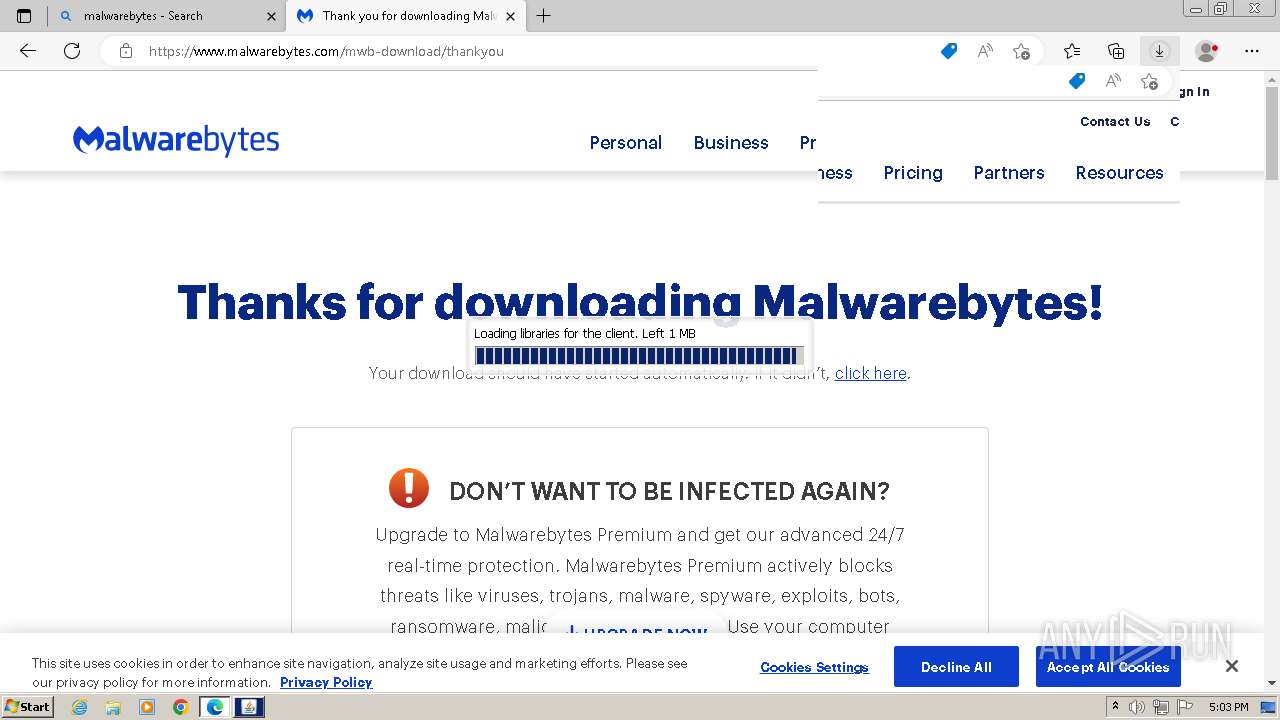
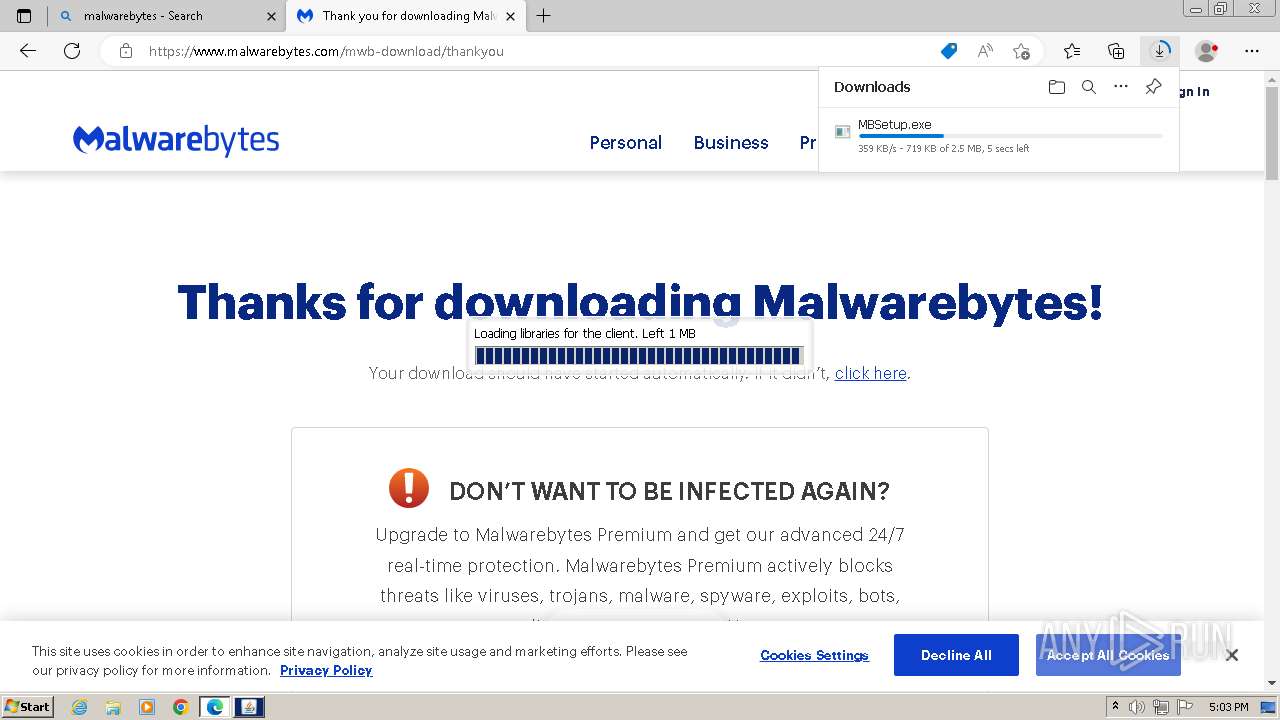
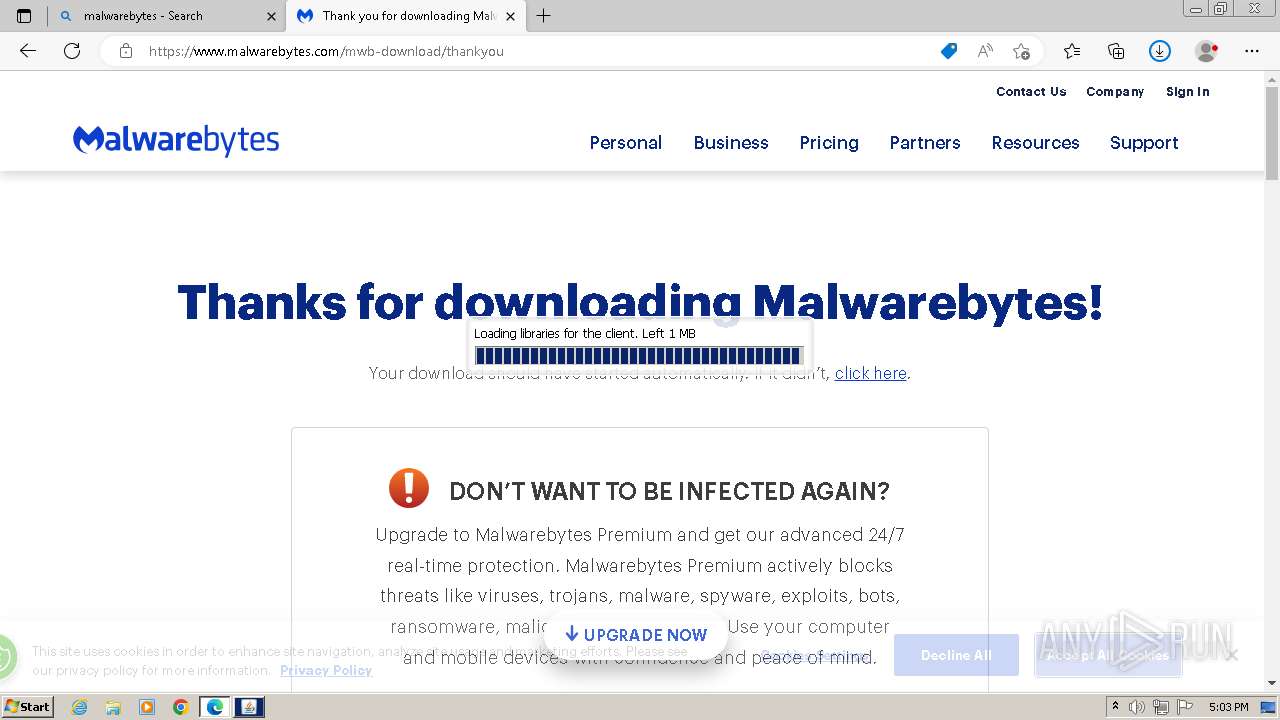
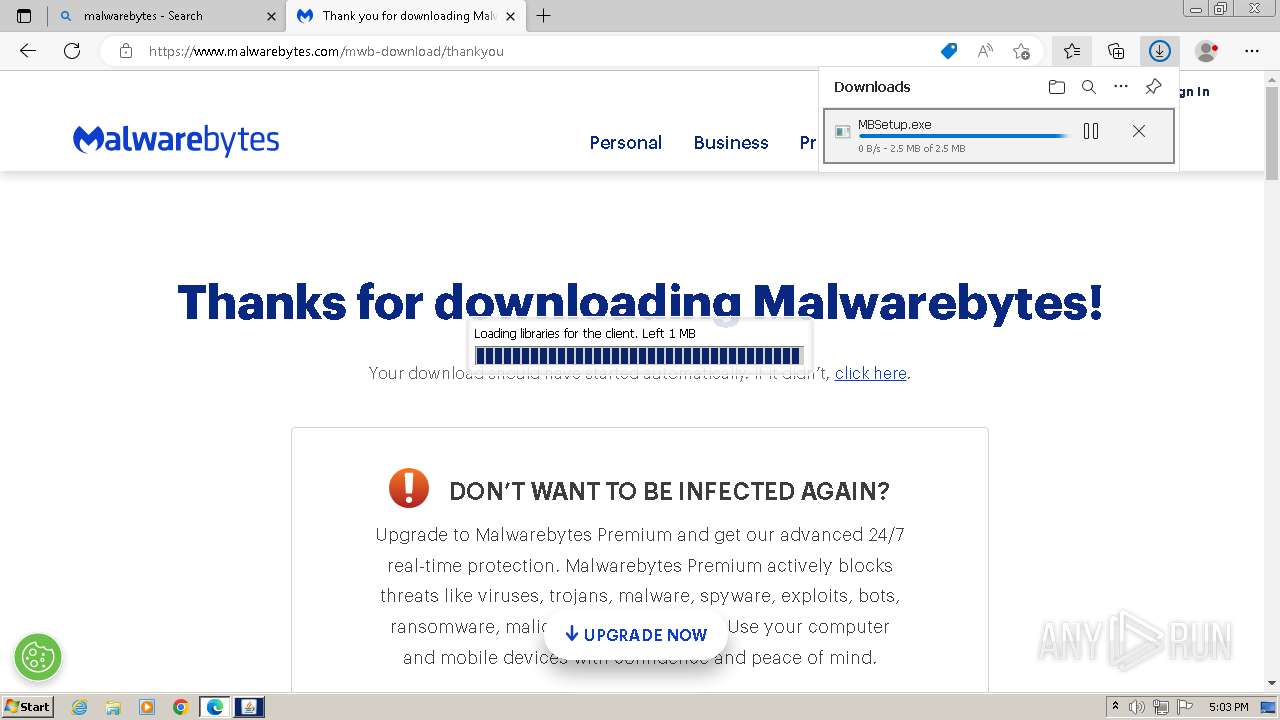
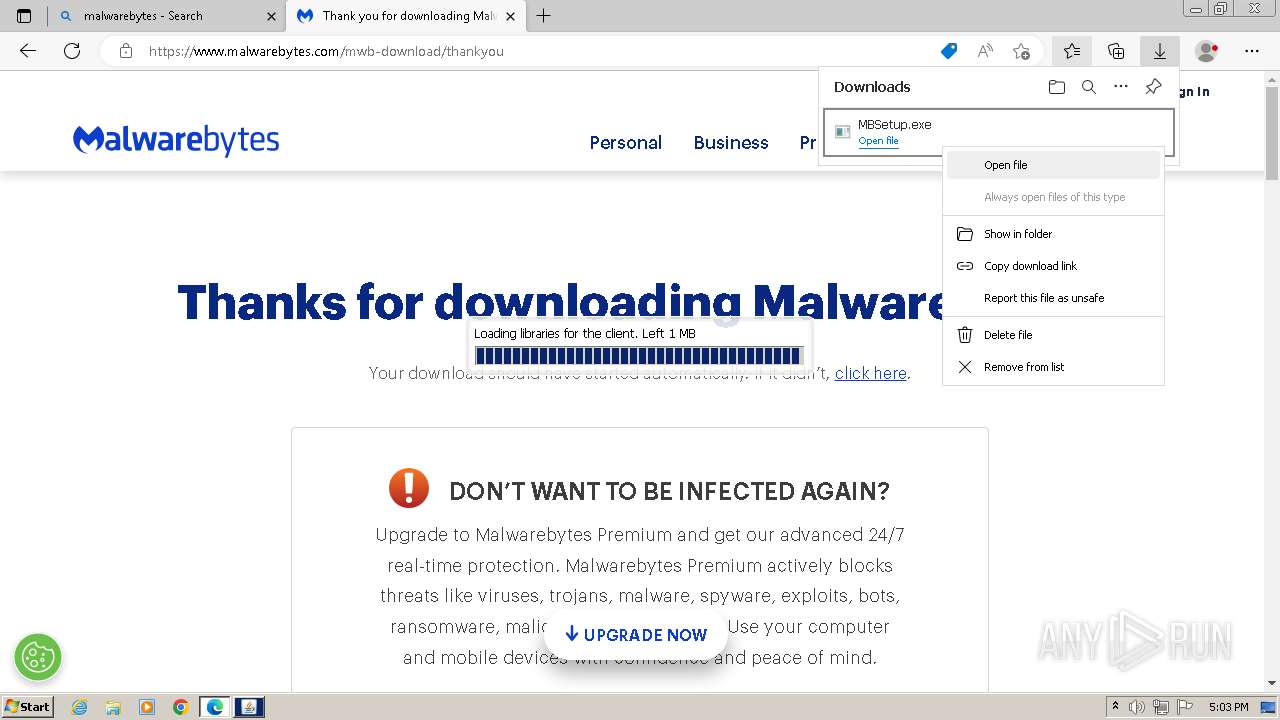
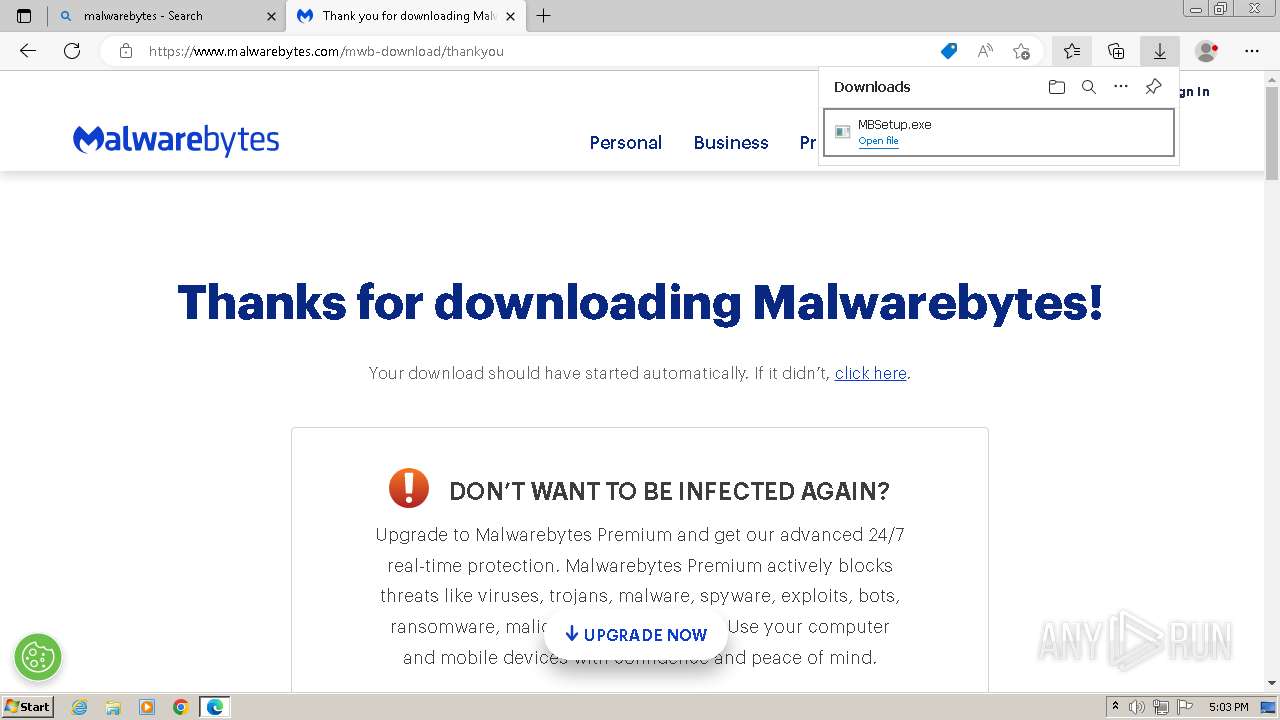
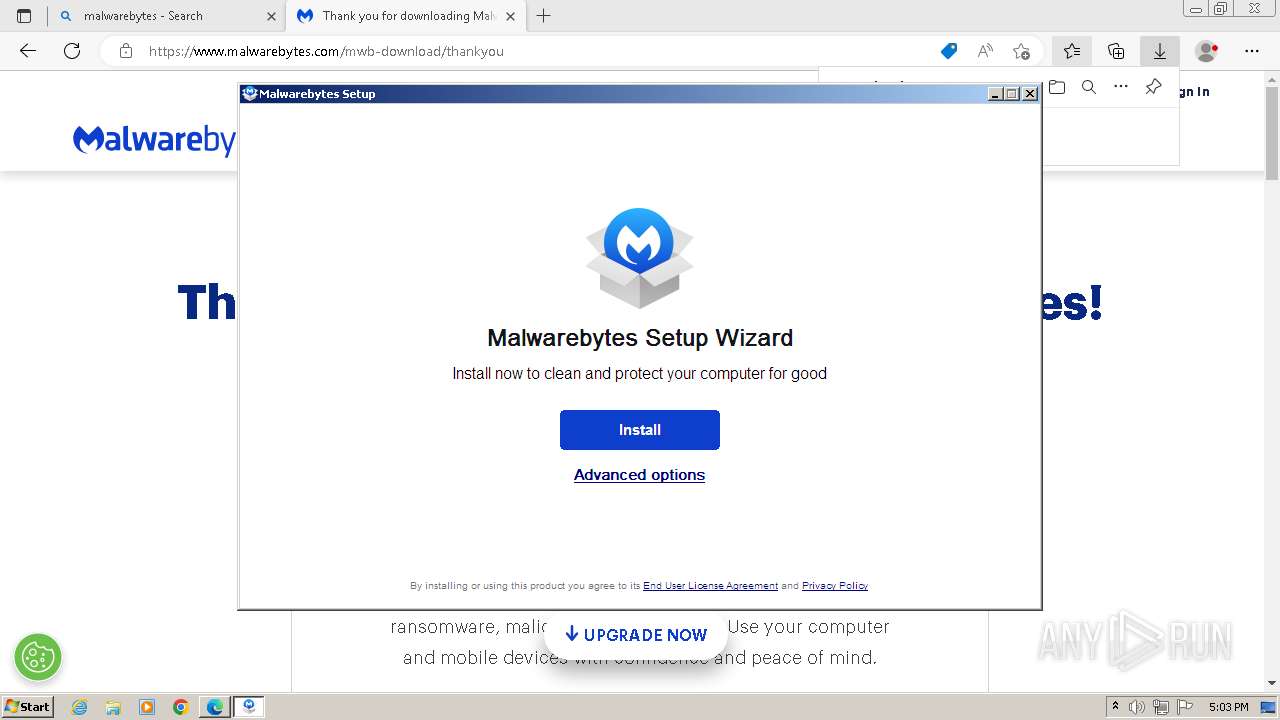
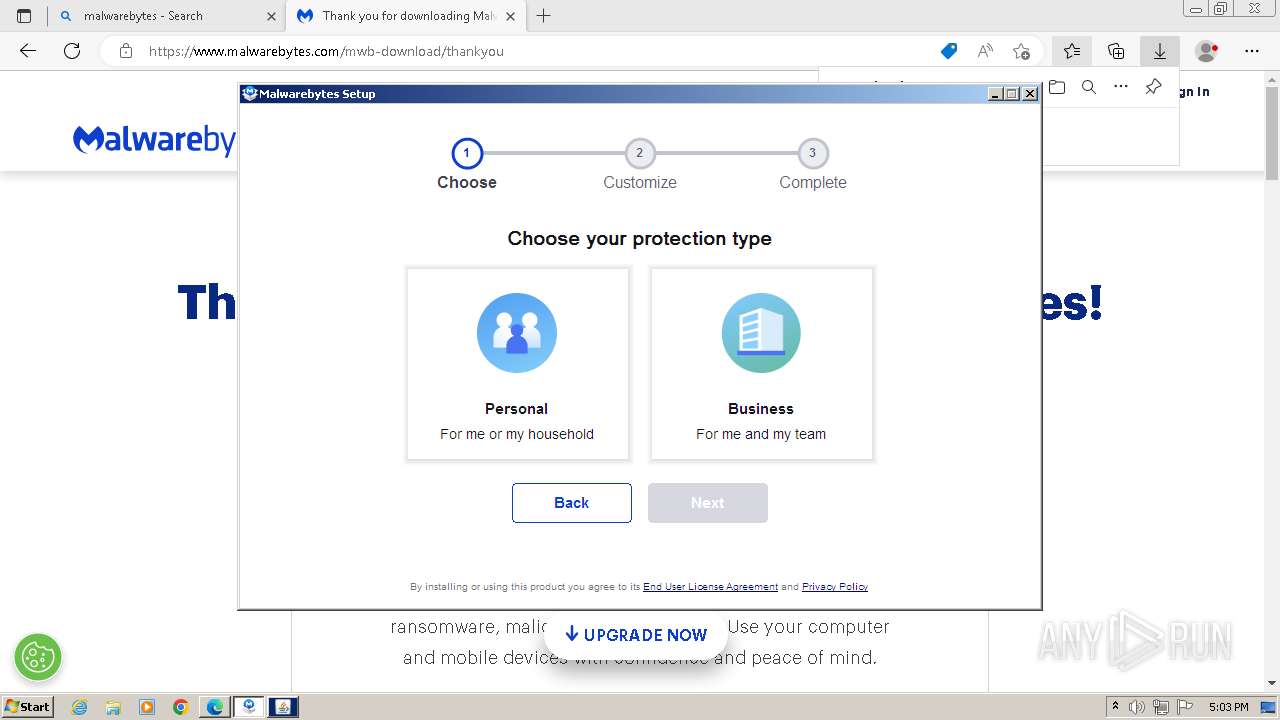
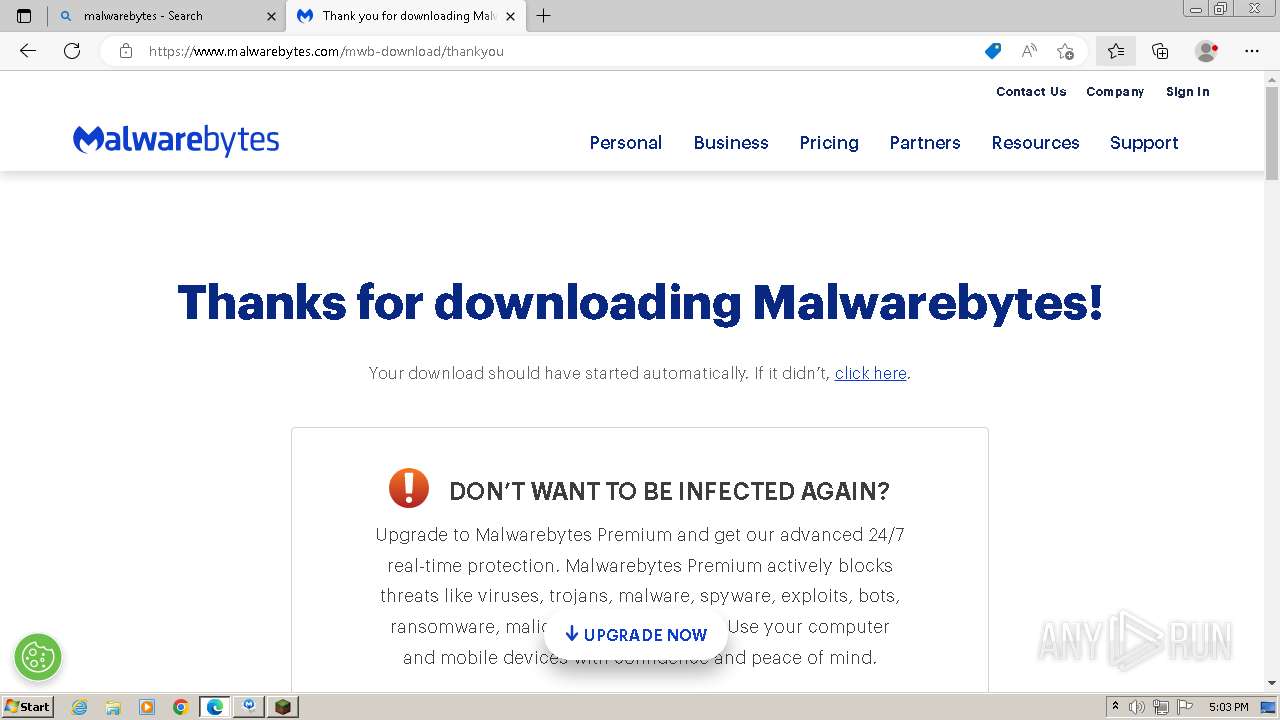
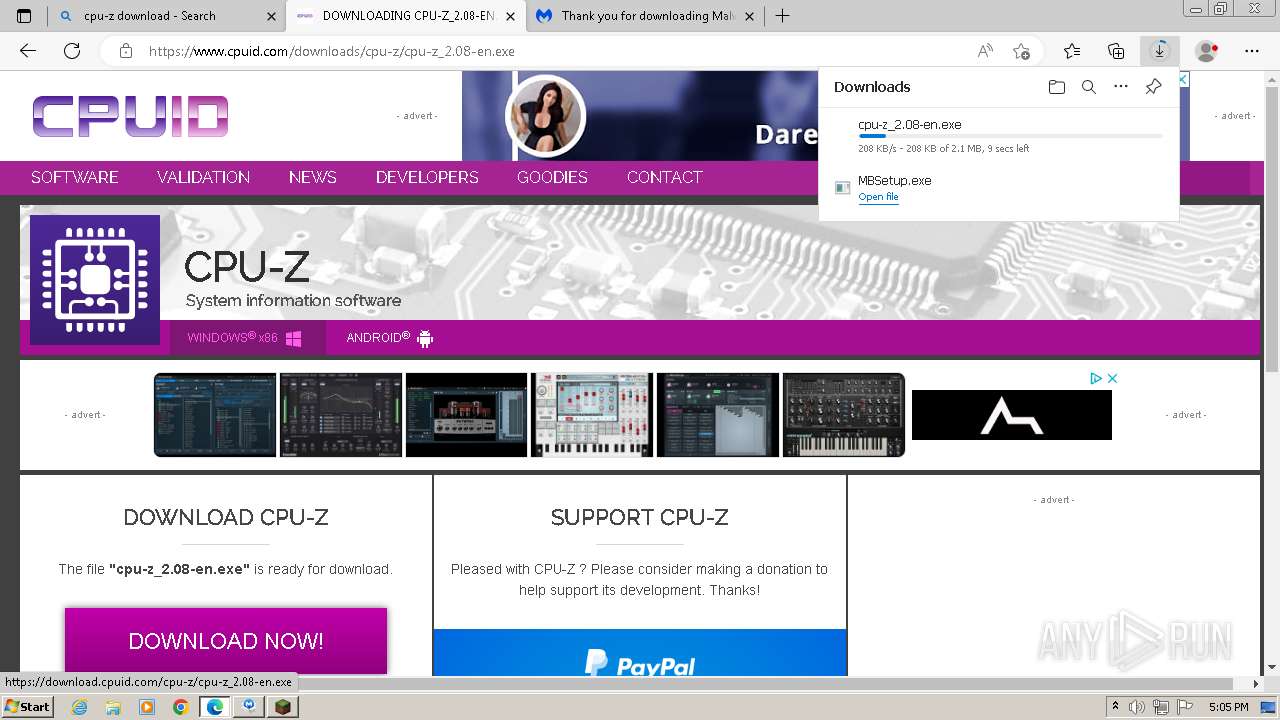
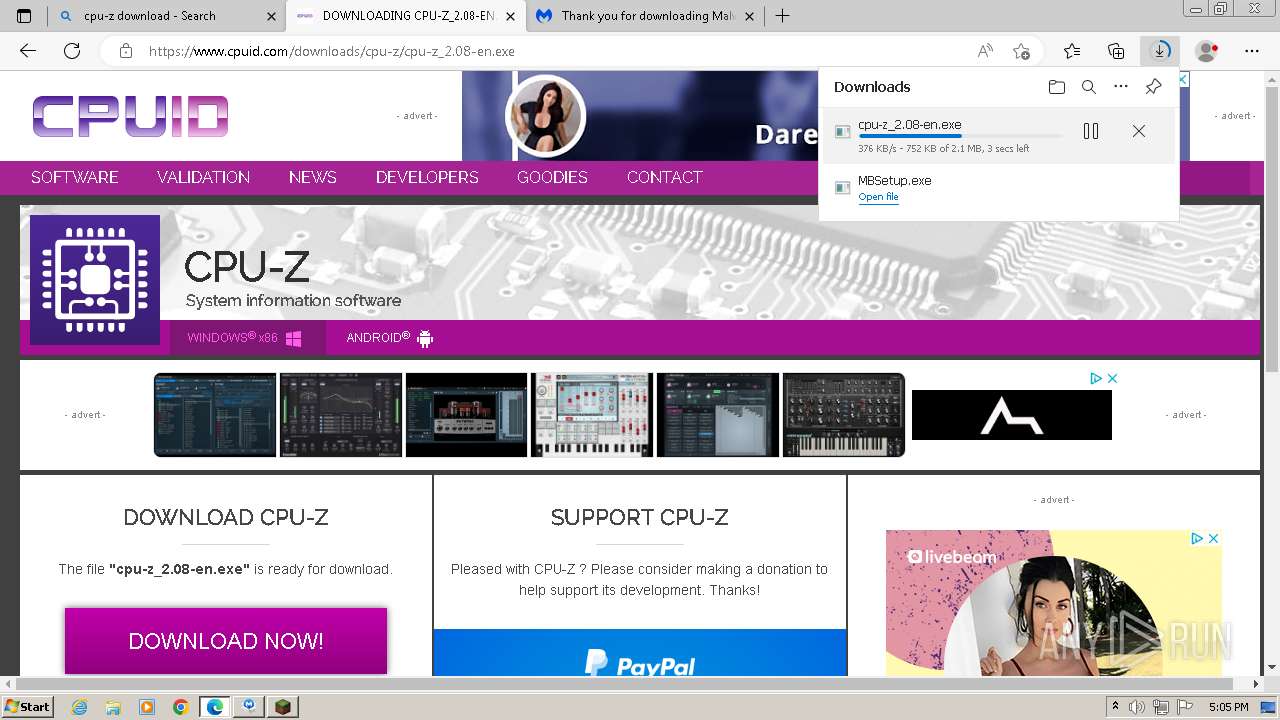
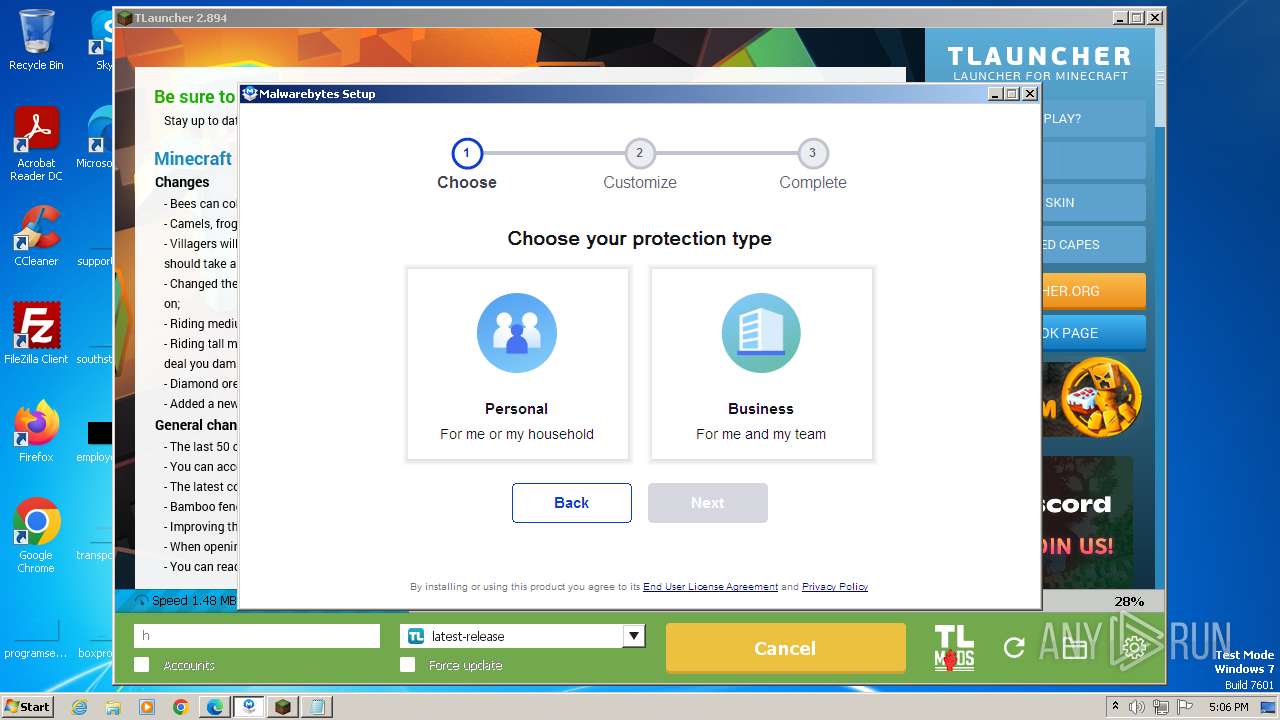
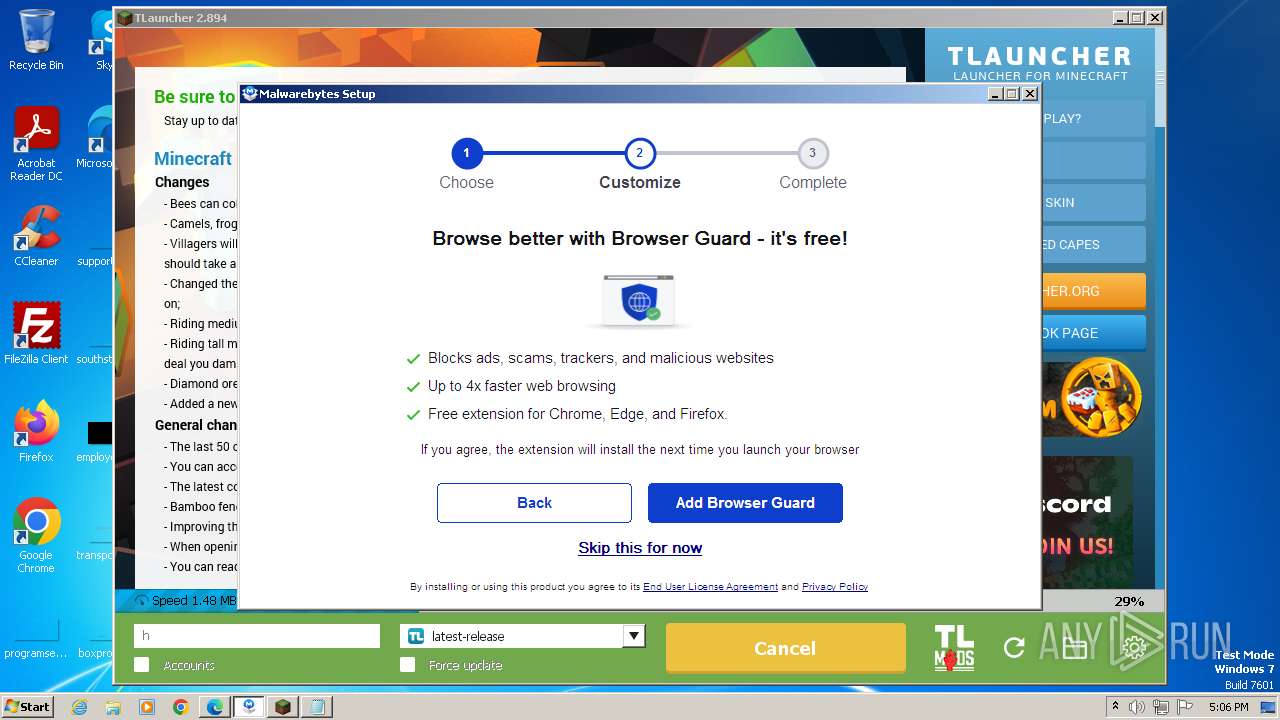
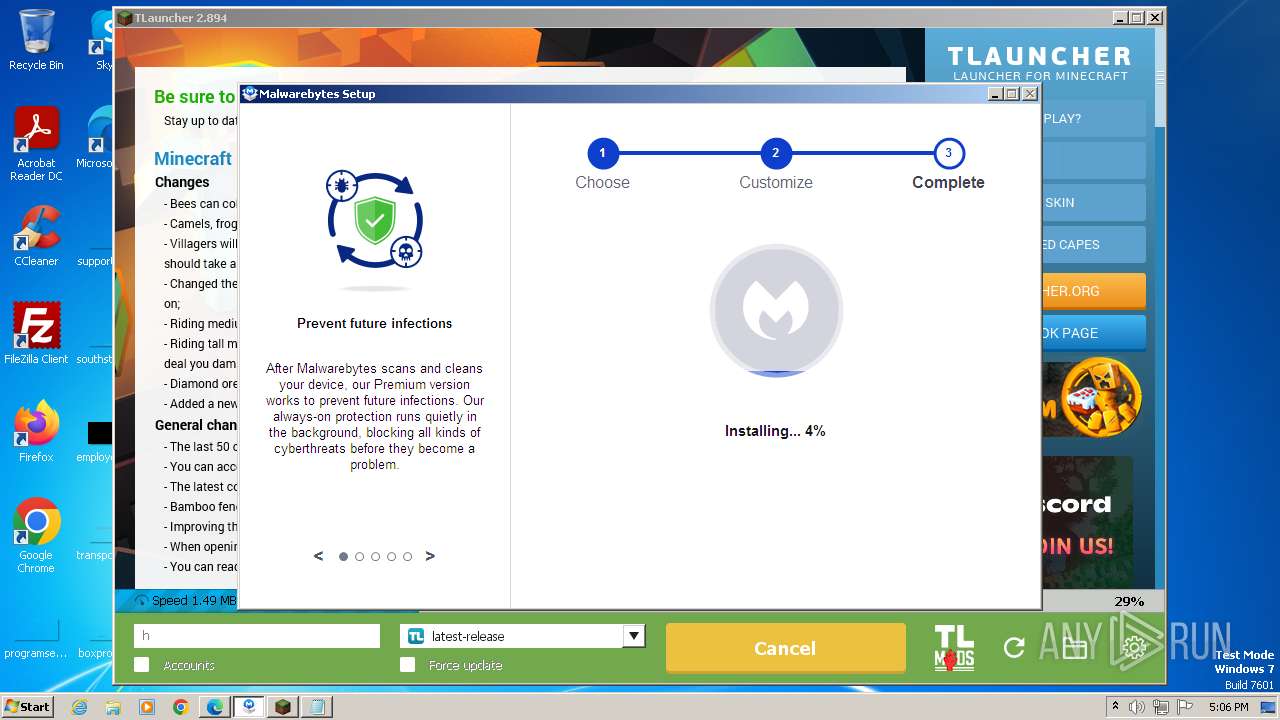
- MBSetup.exe (PID: 460)
- MBSetup.exe (PID: 1240)
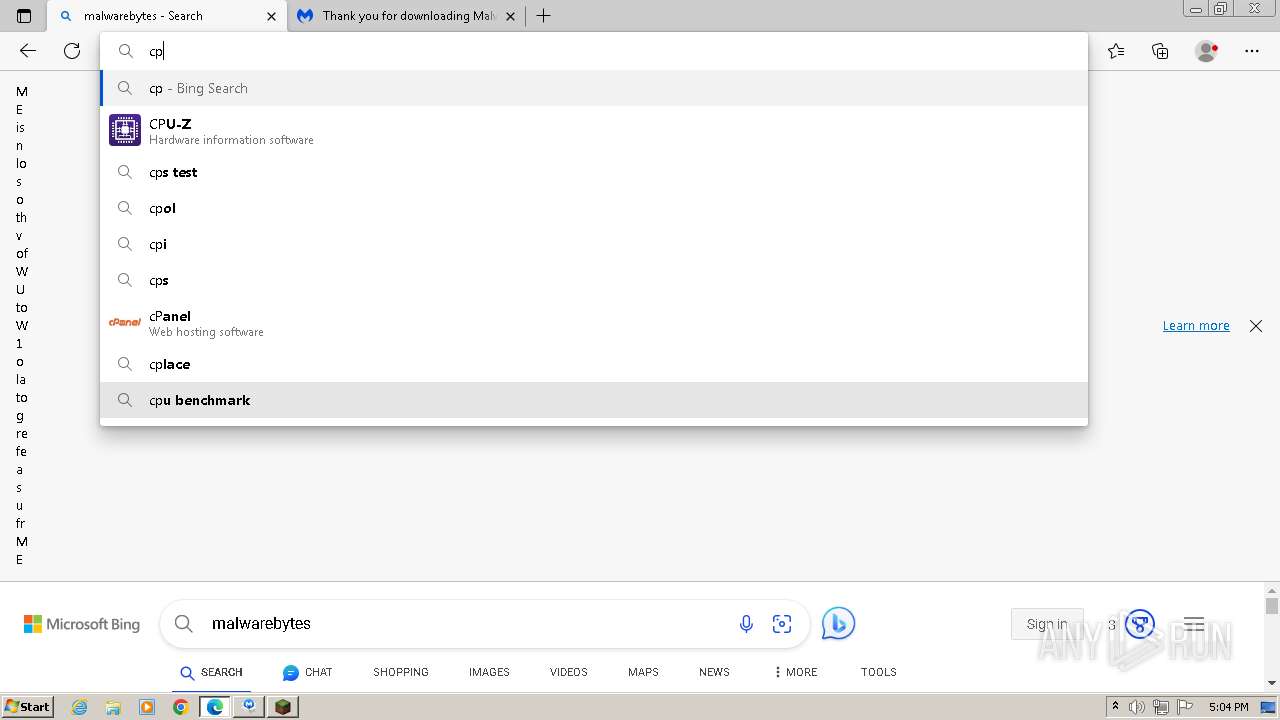
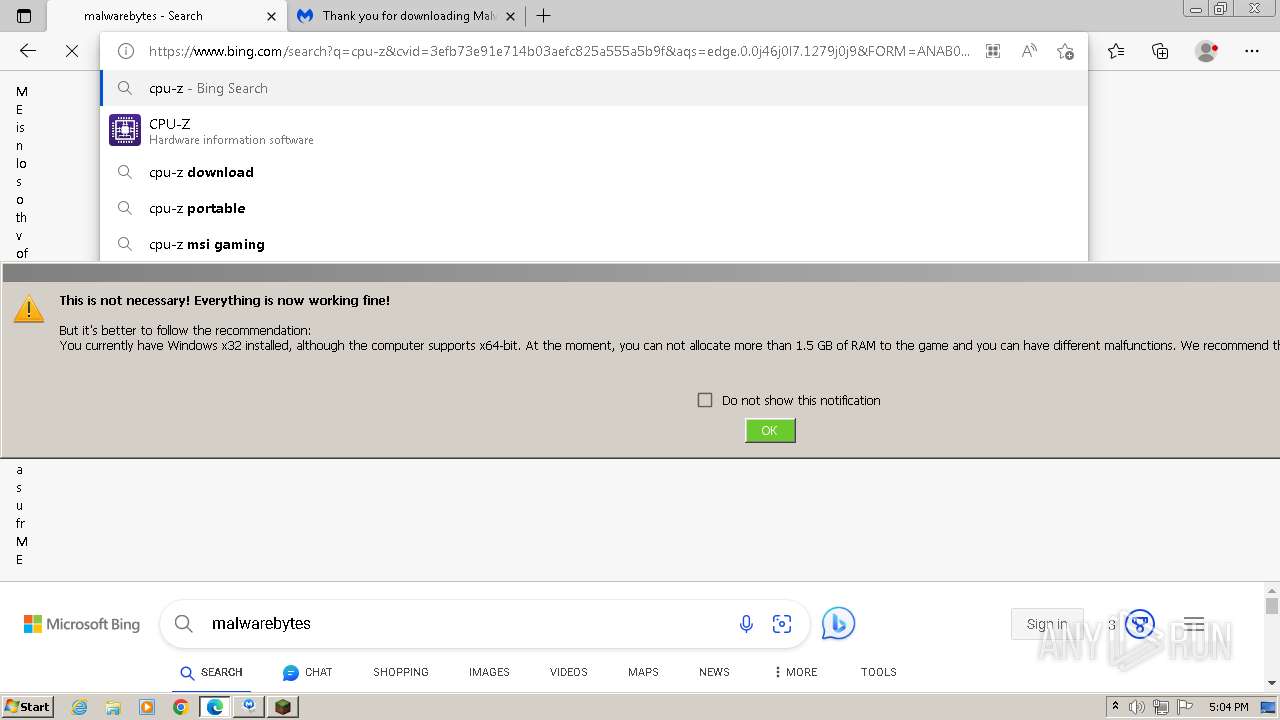
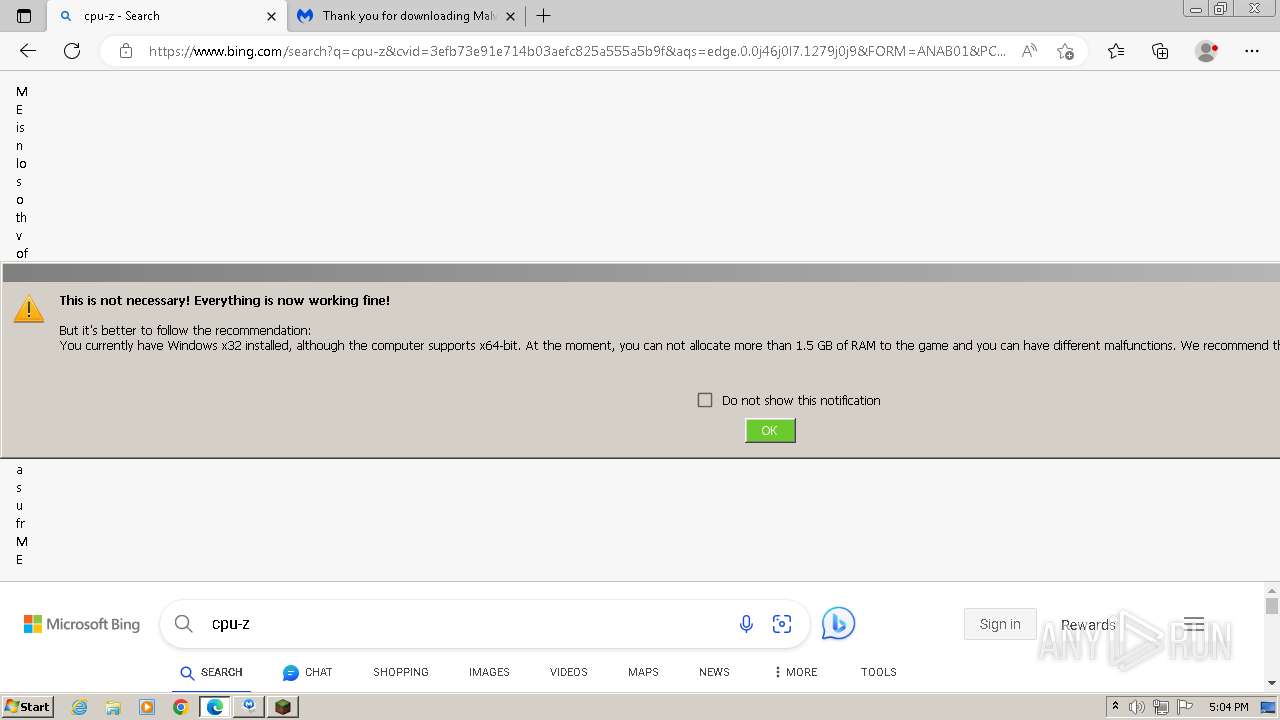
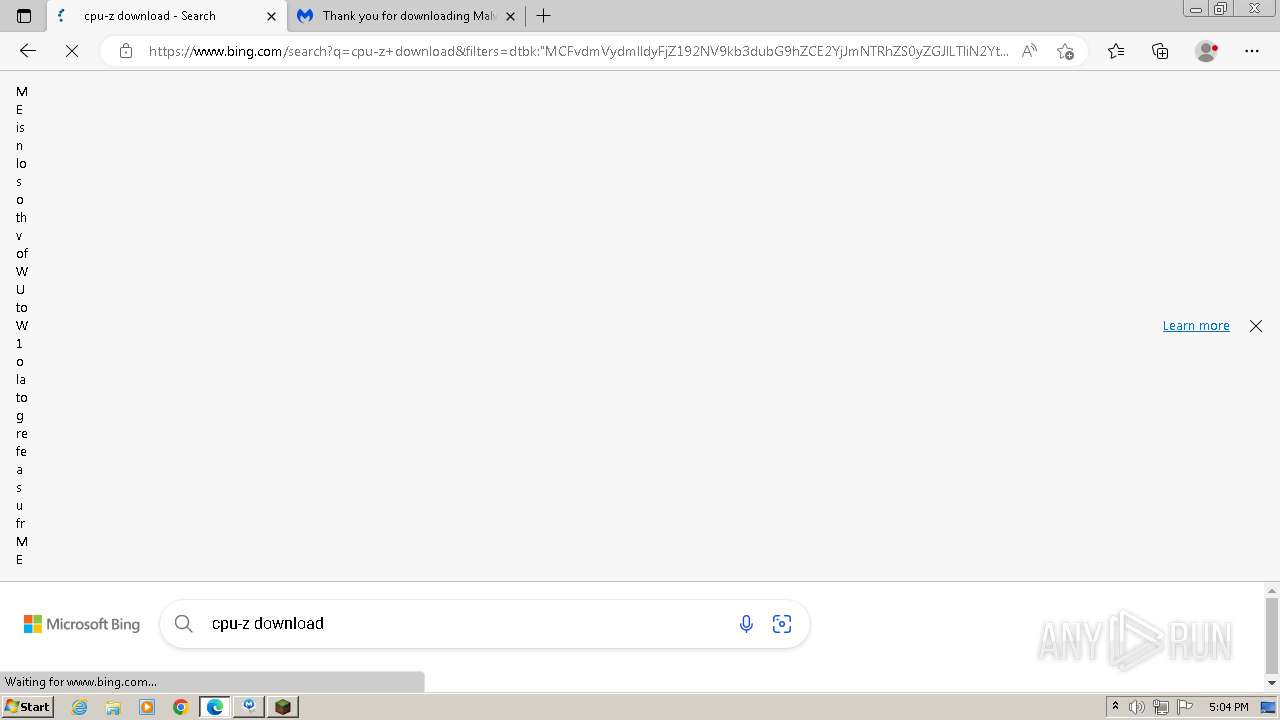
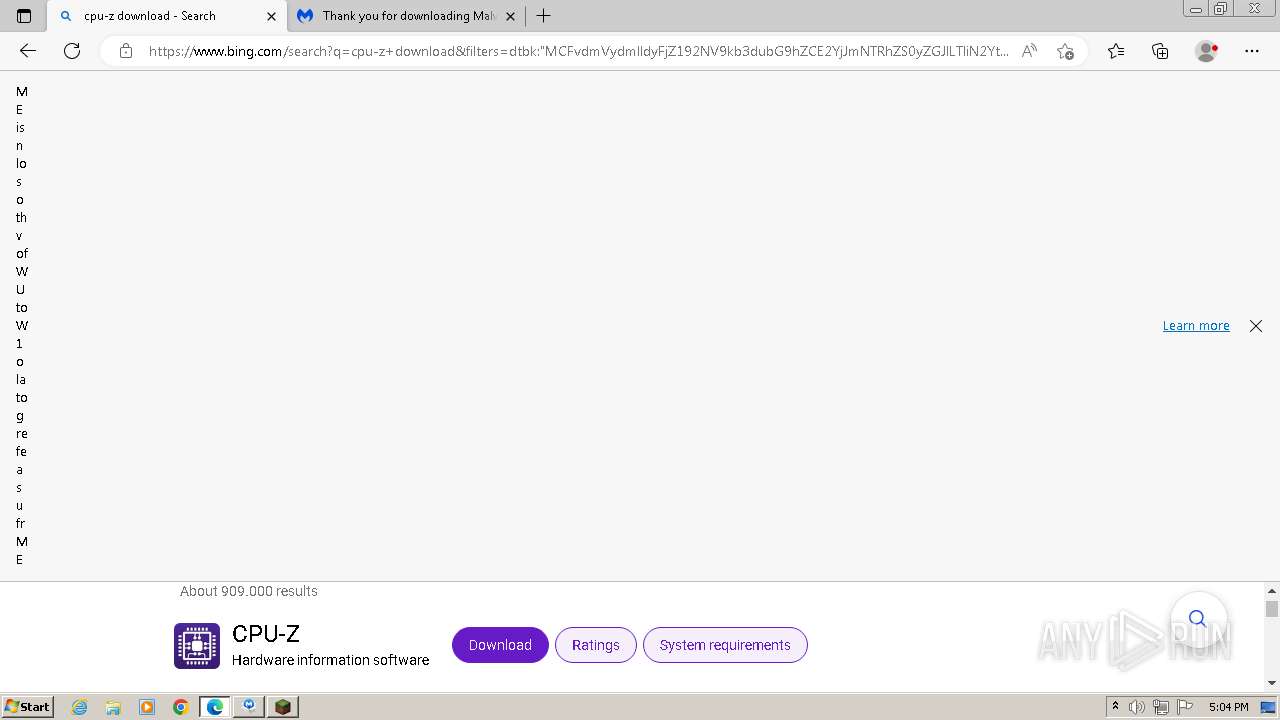
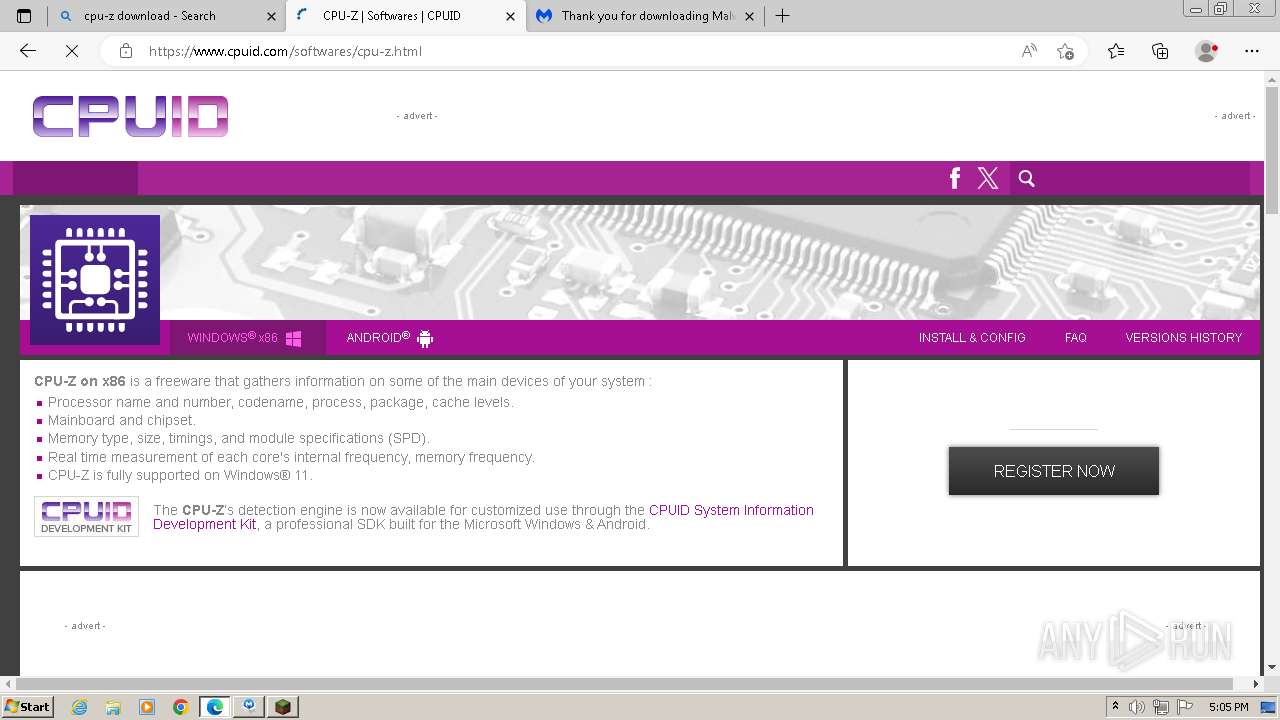
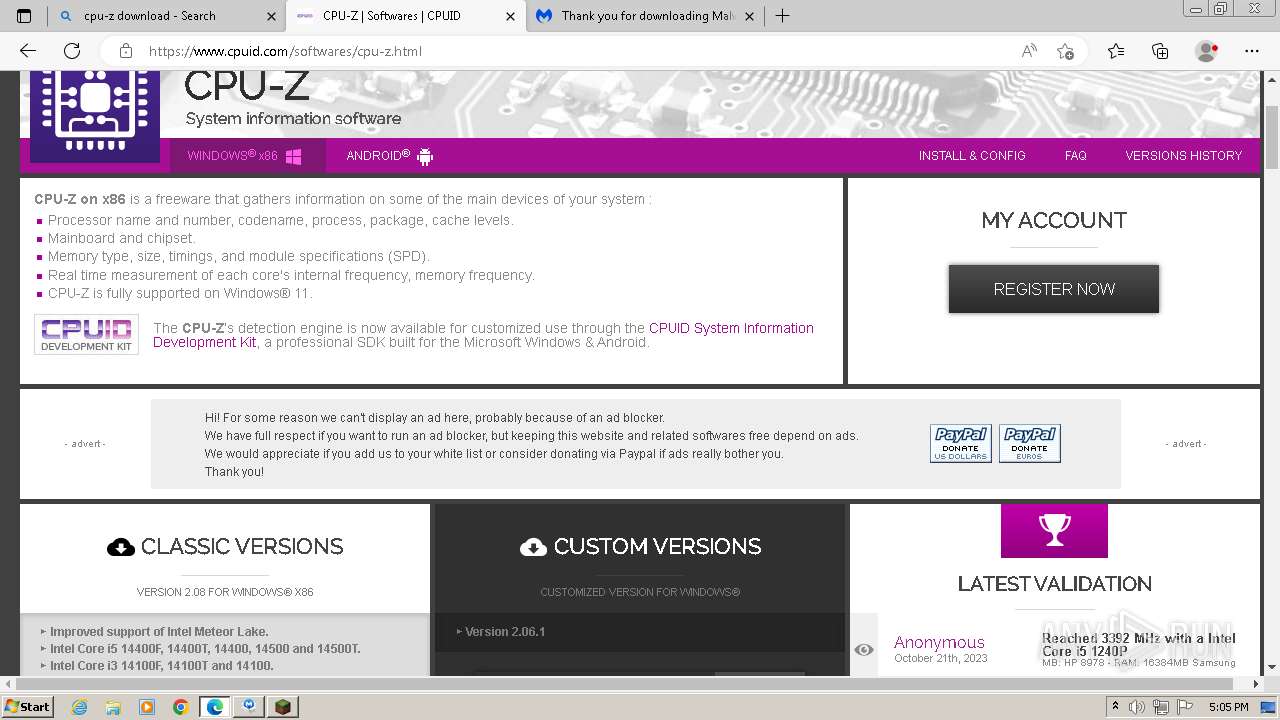
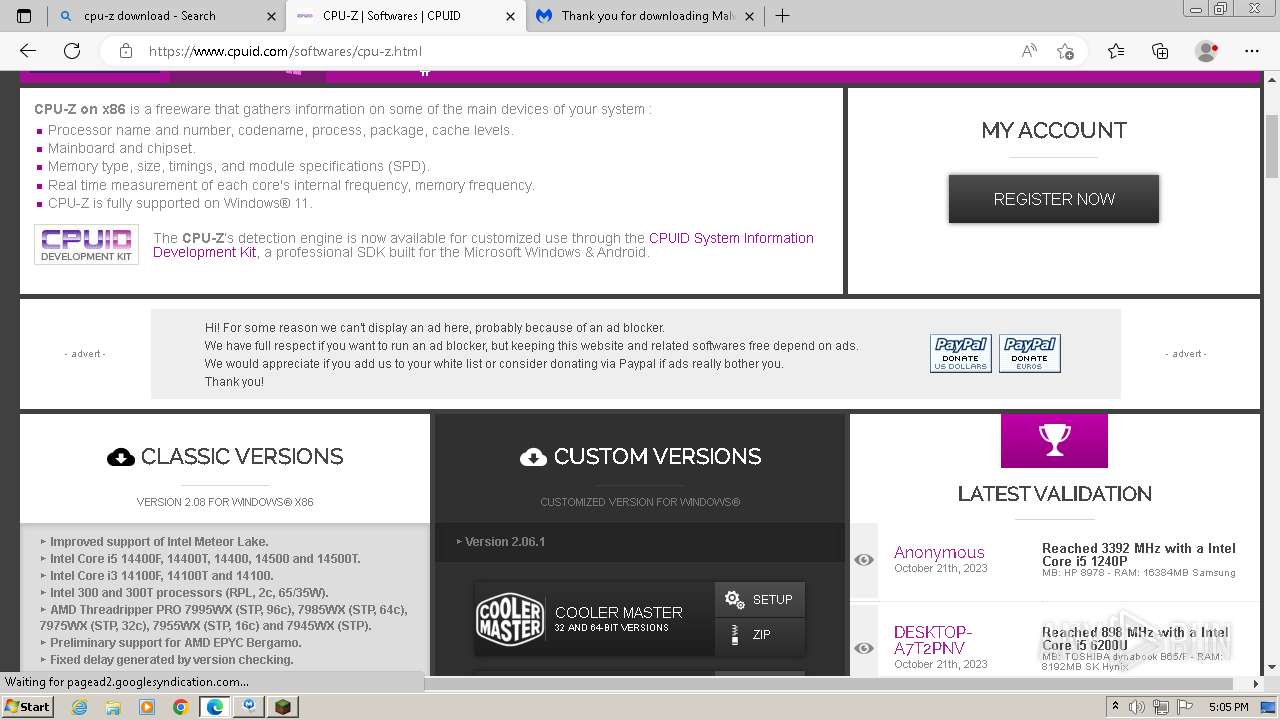
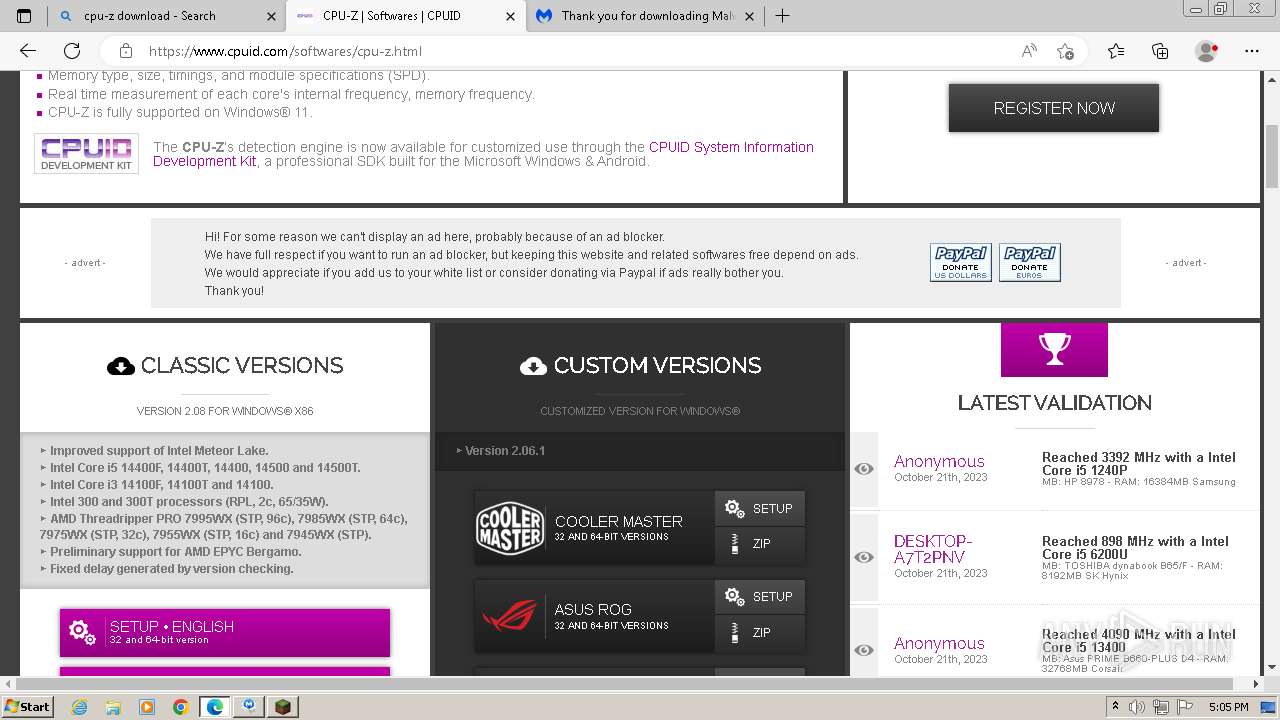
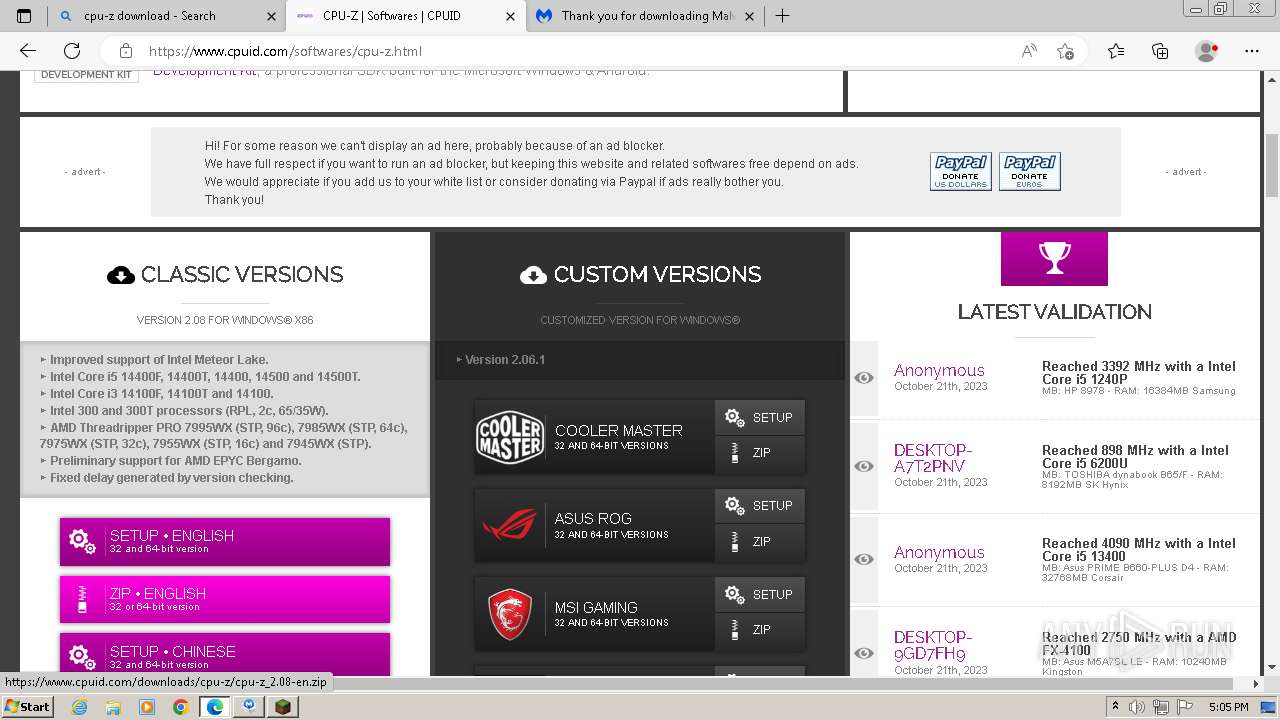
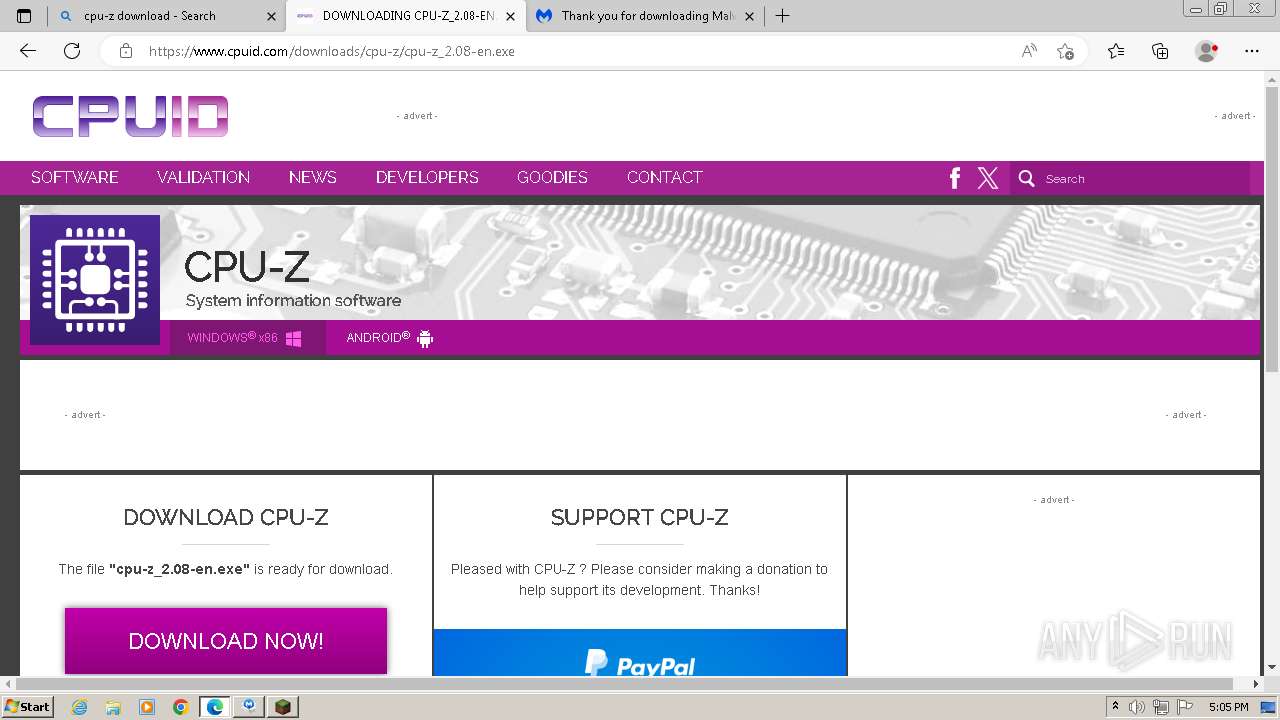
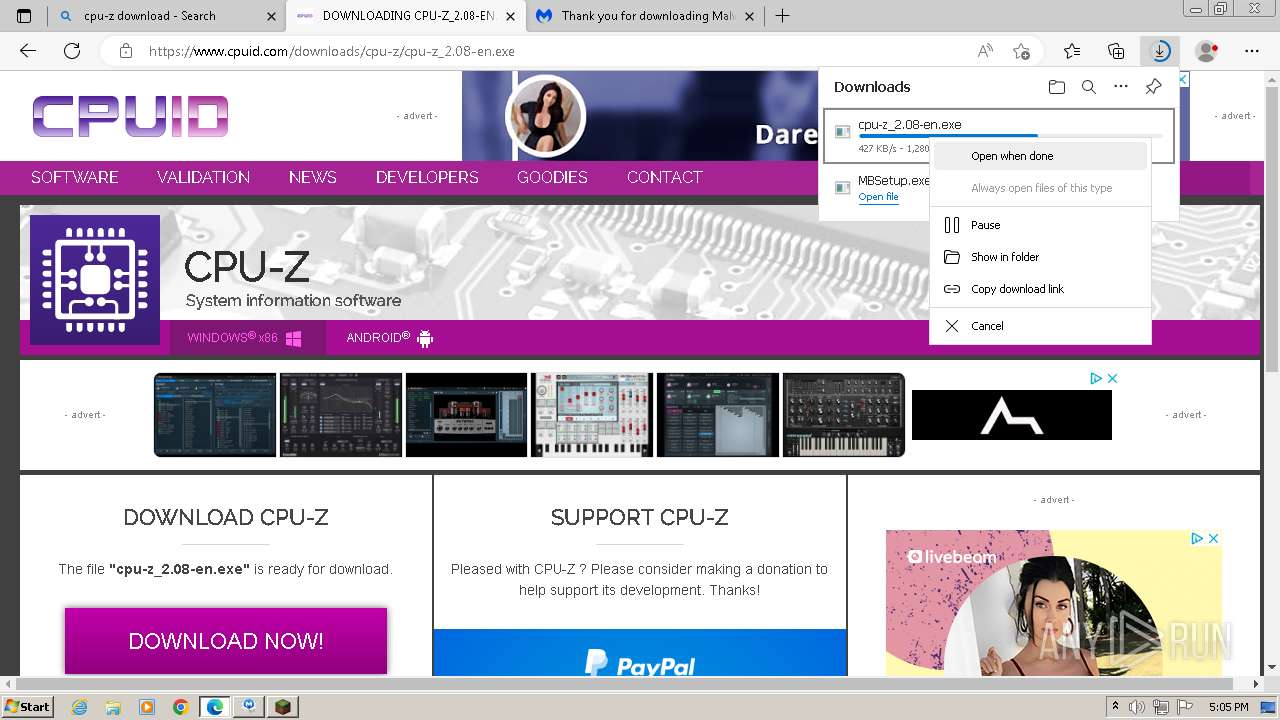
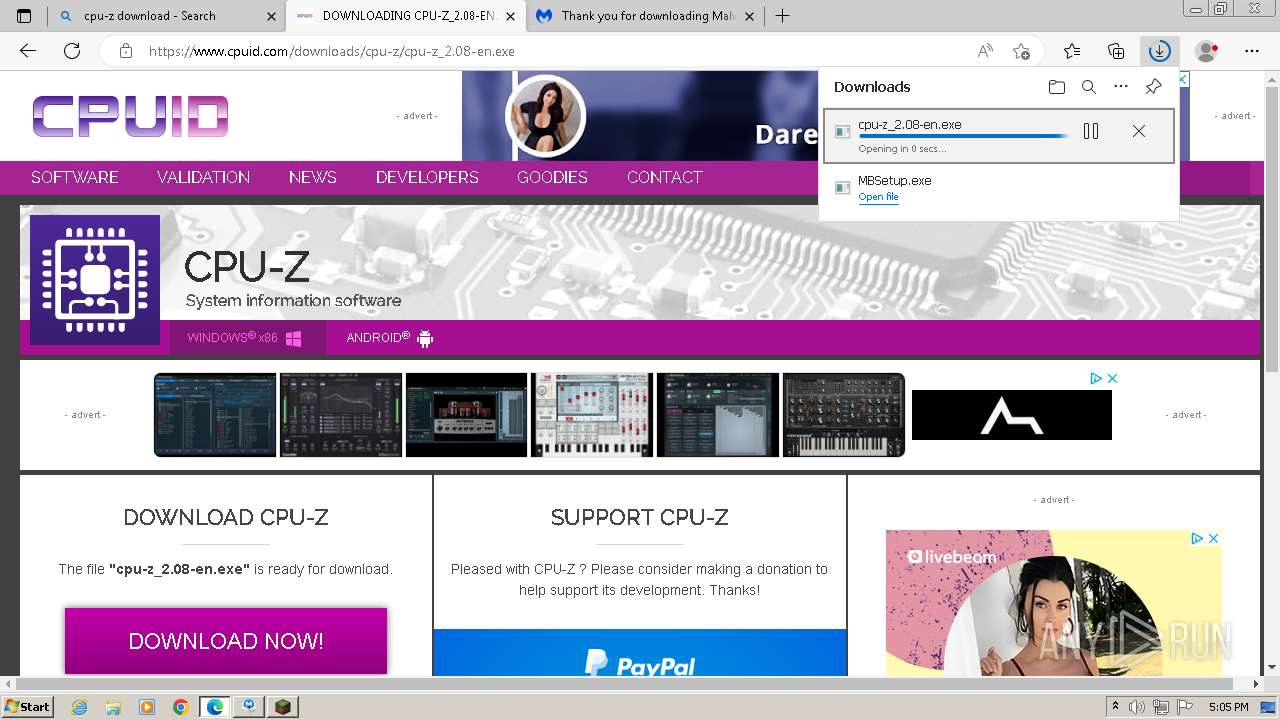
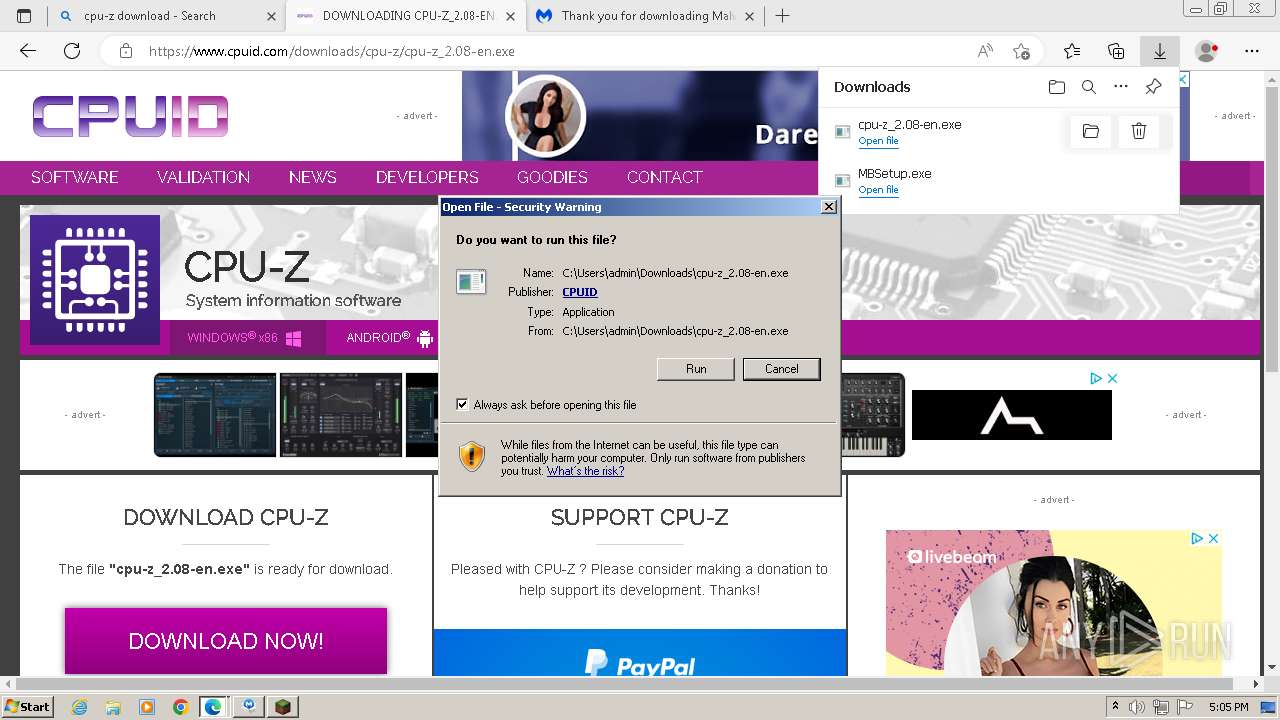
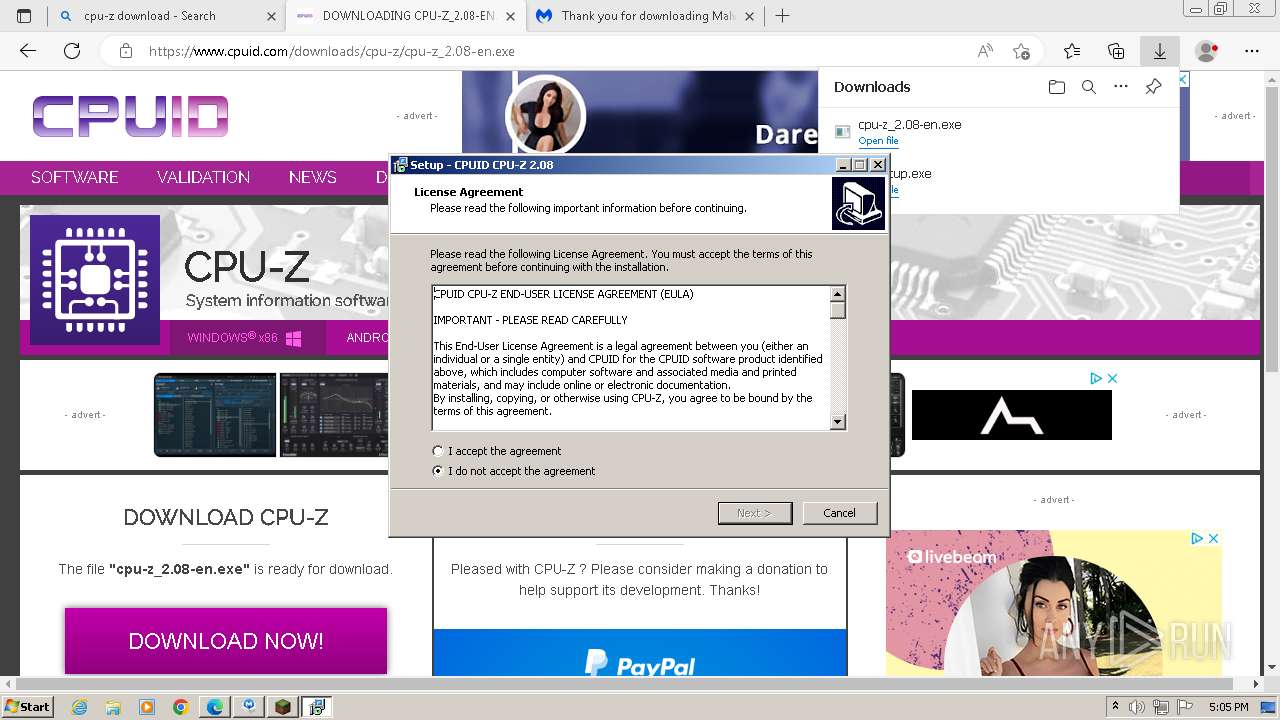
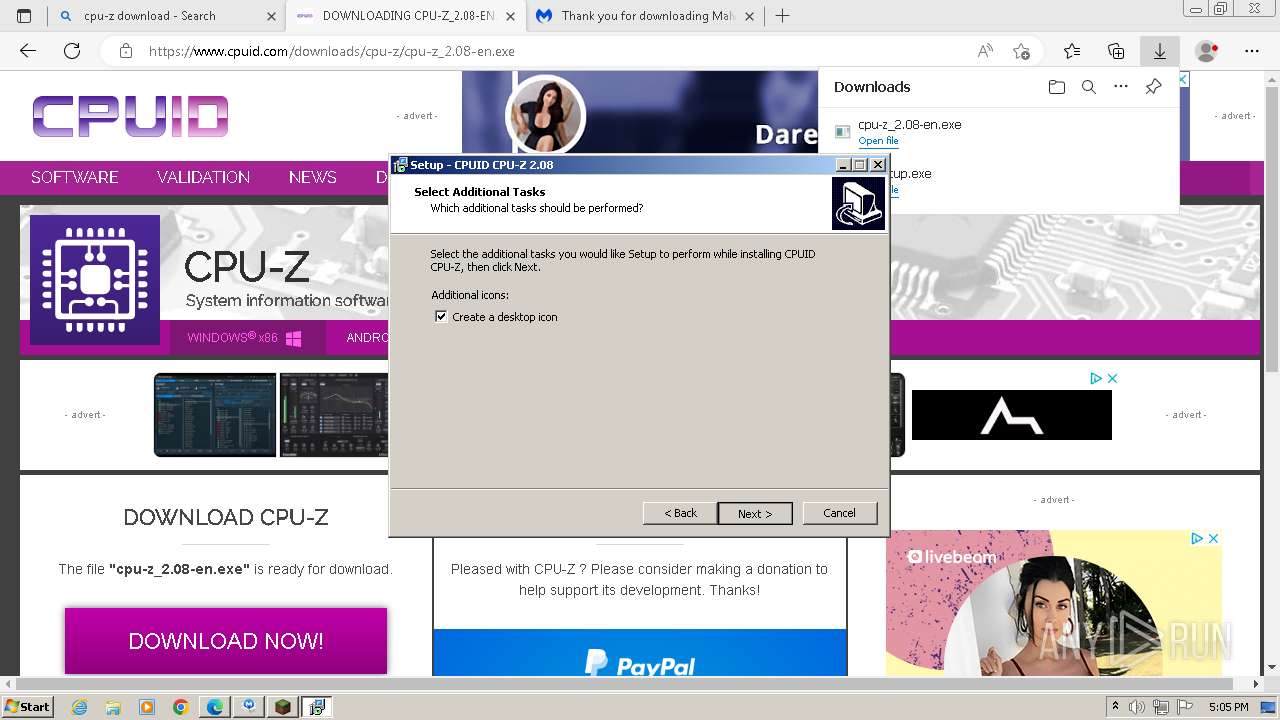
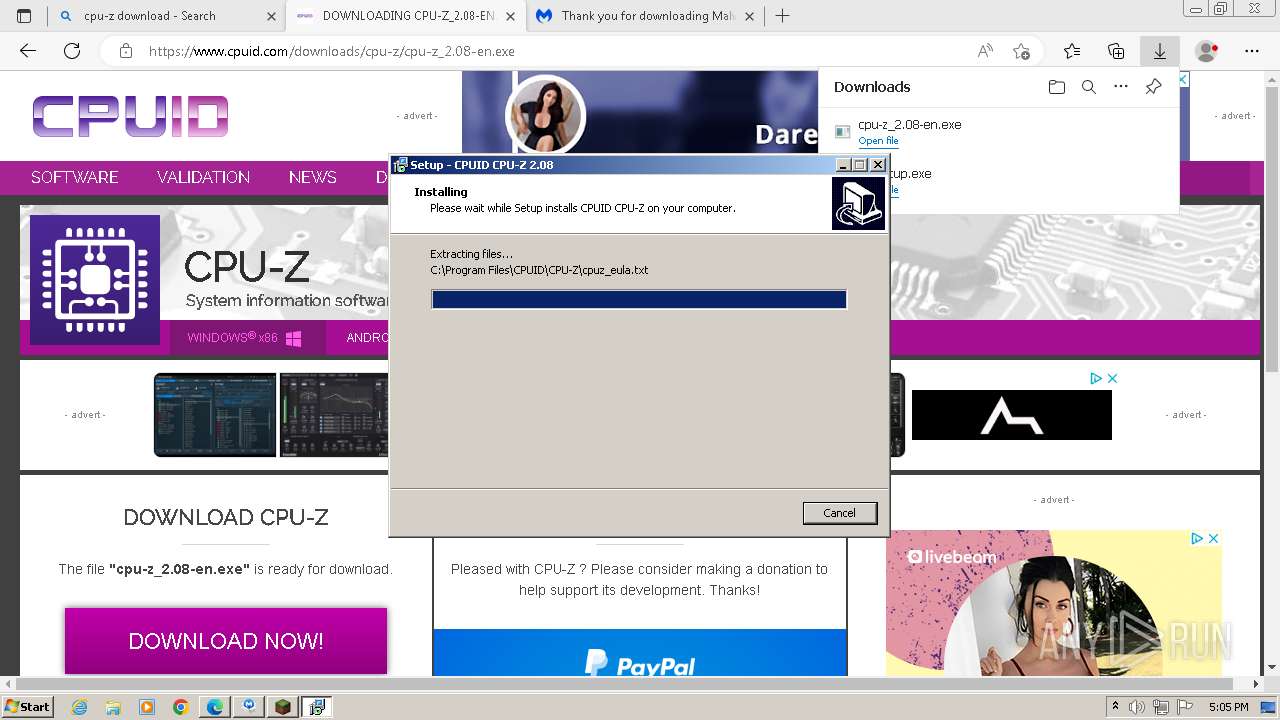
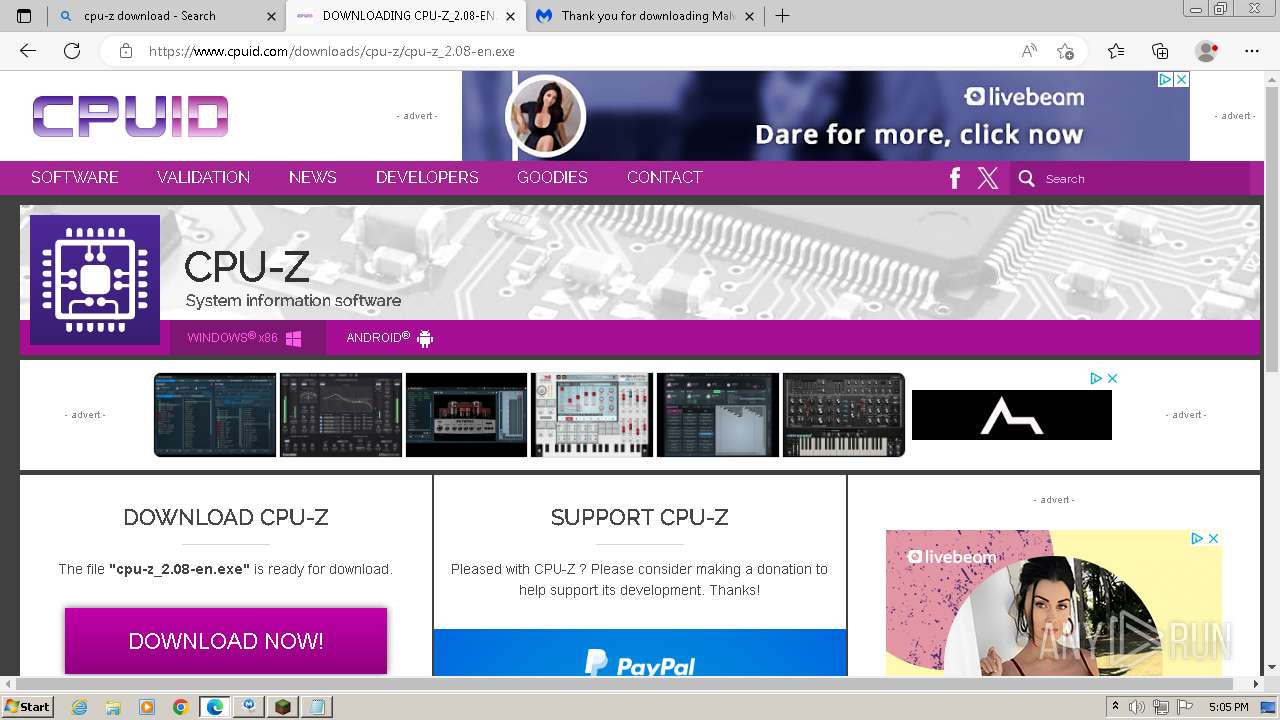
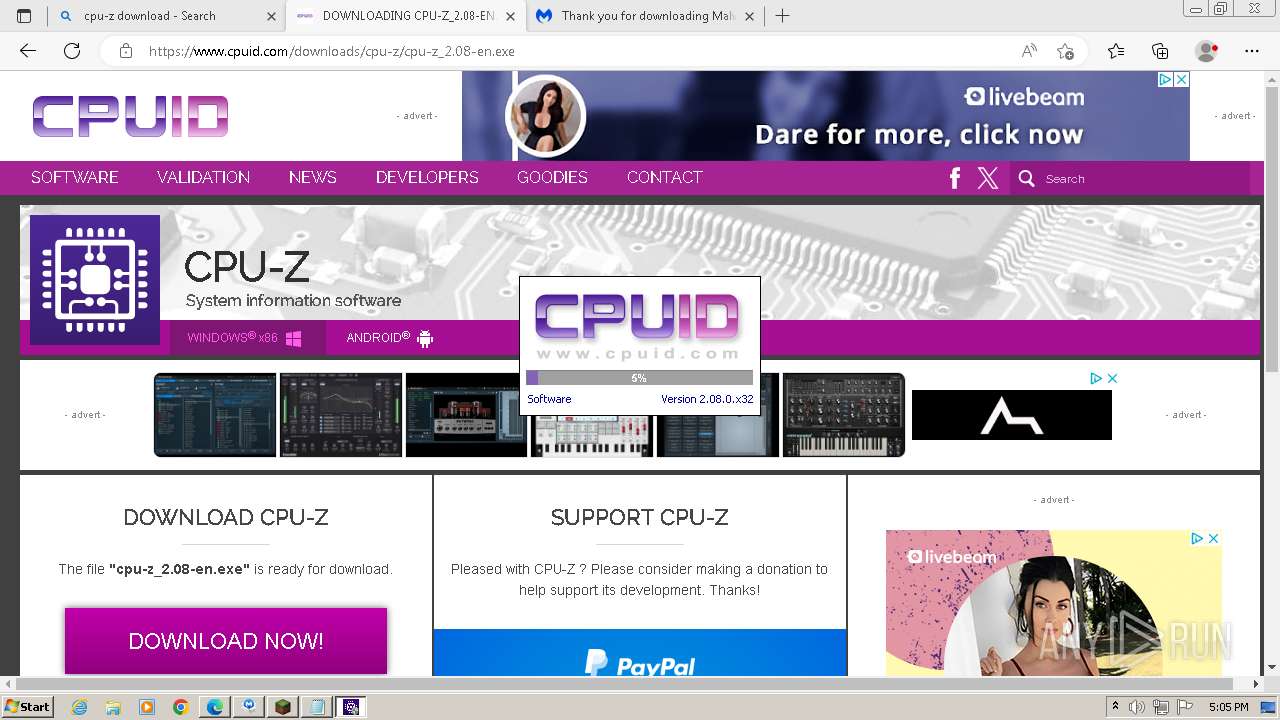
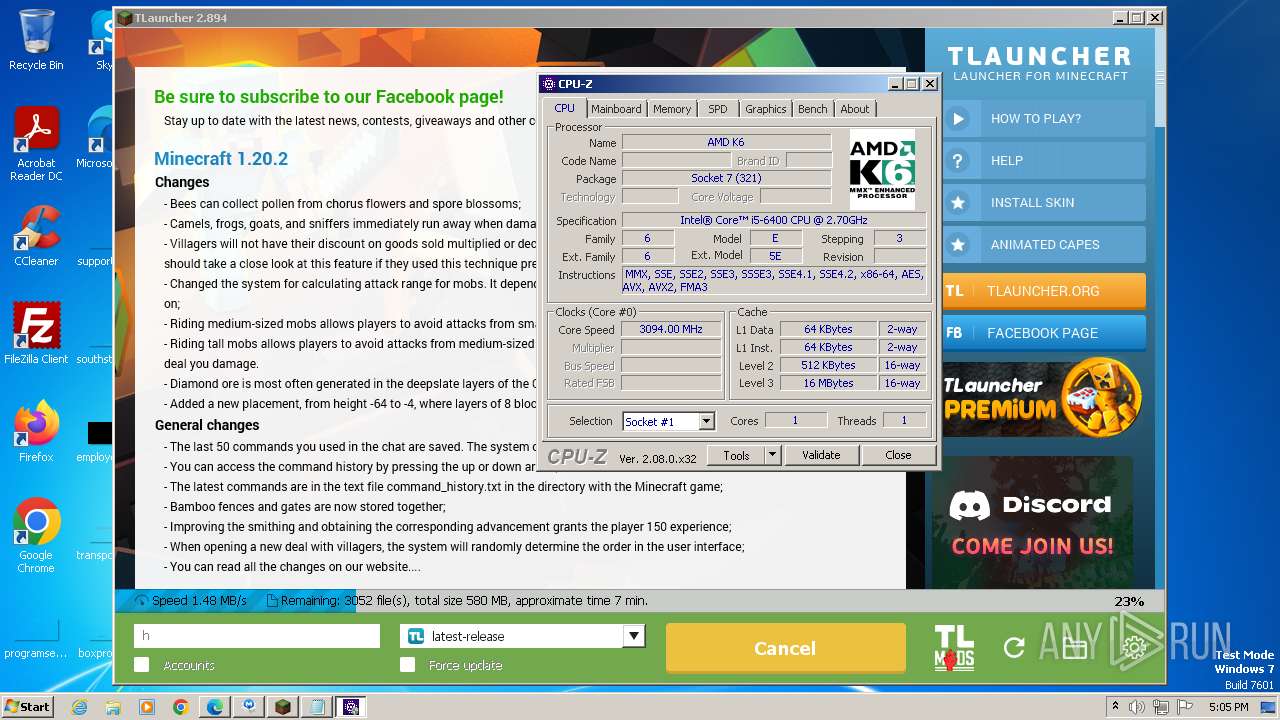
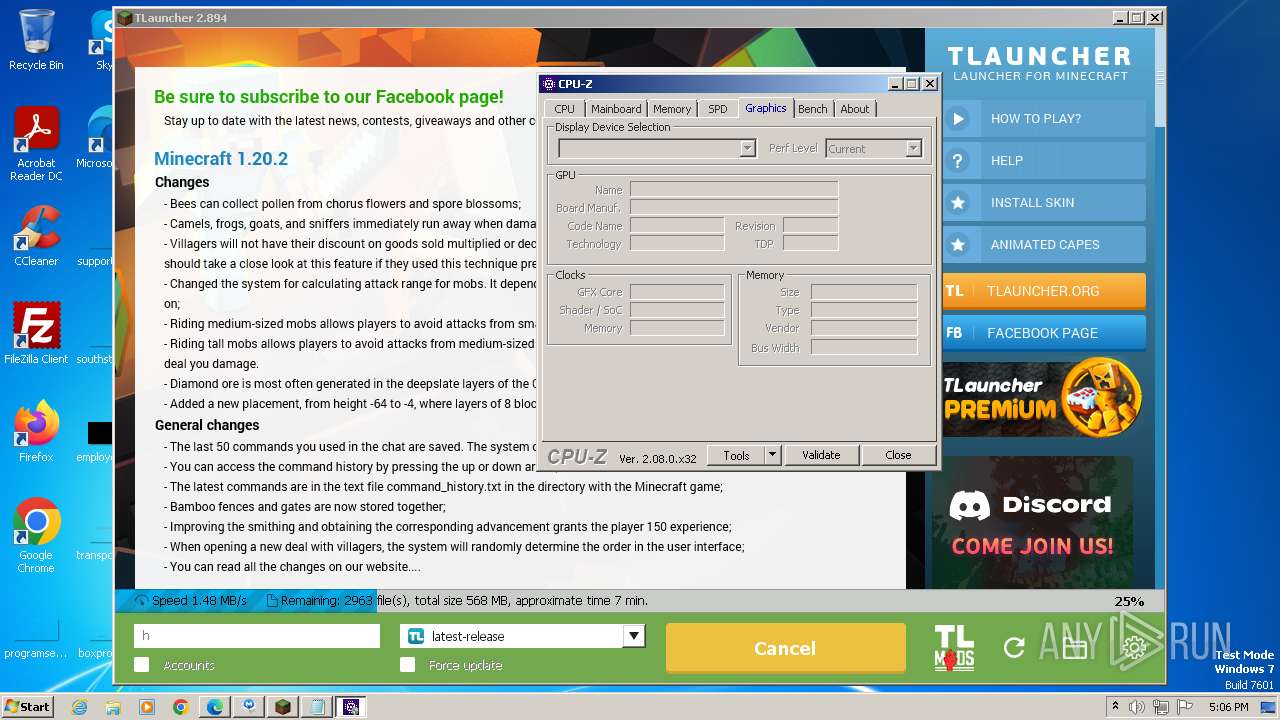
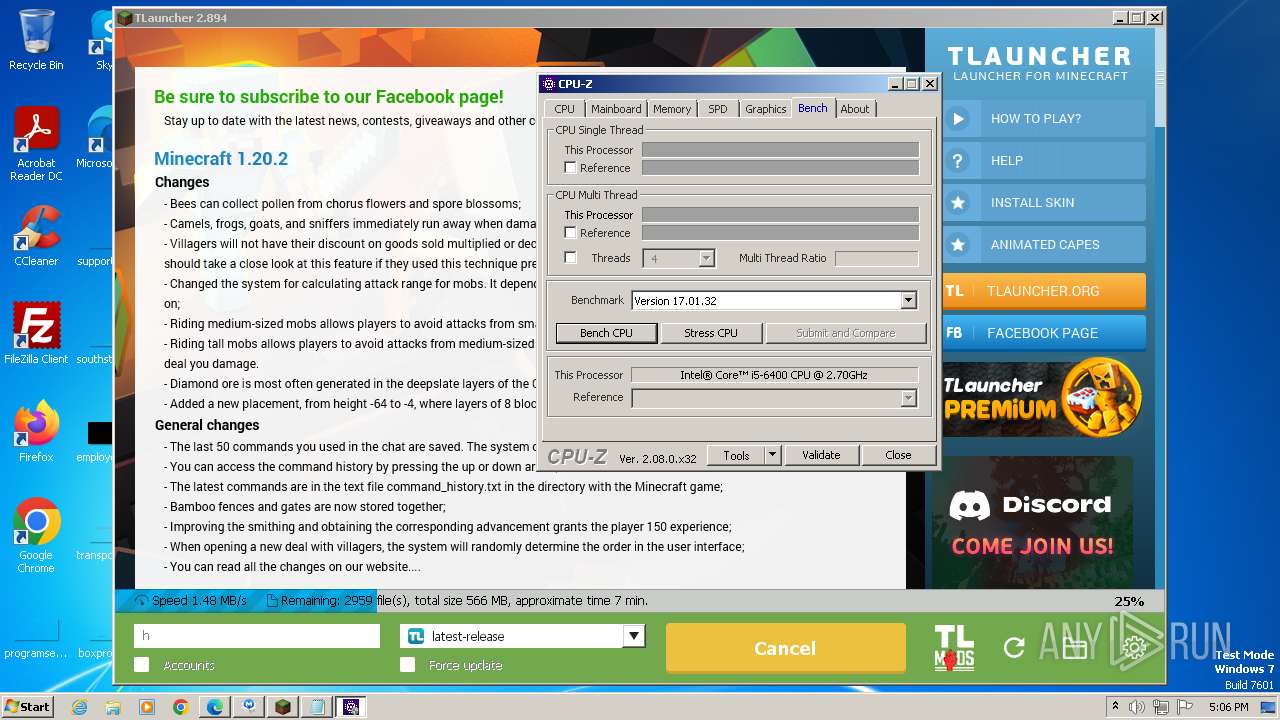
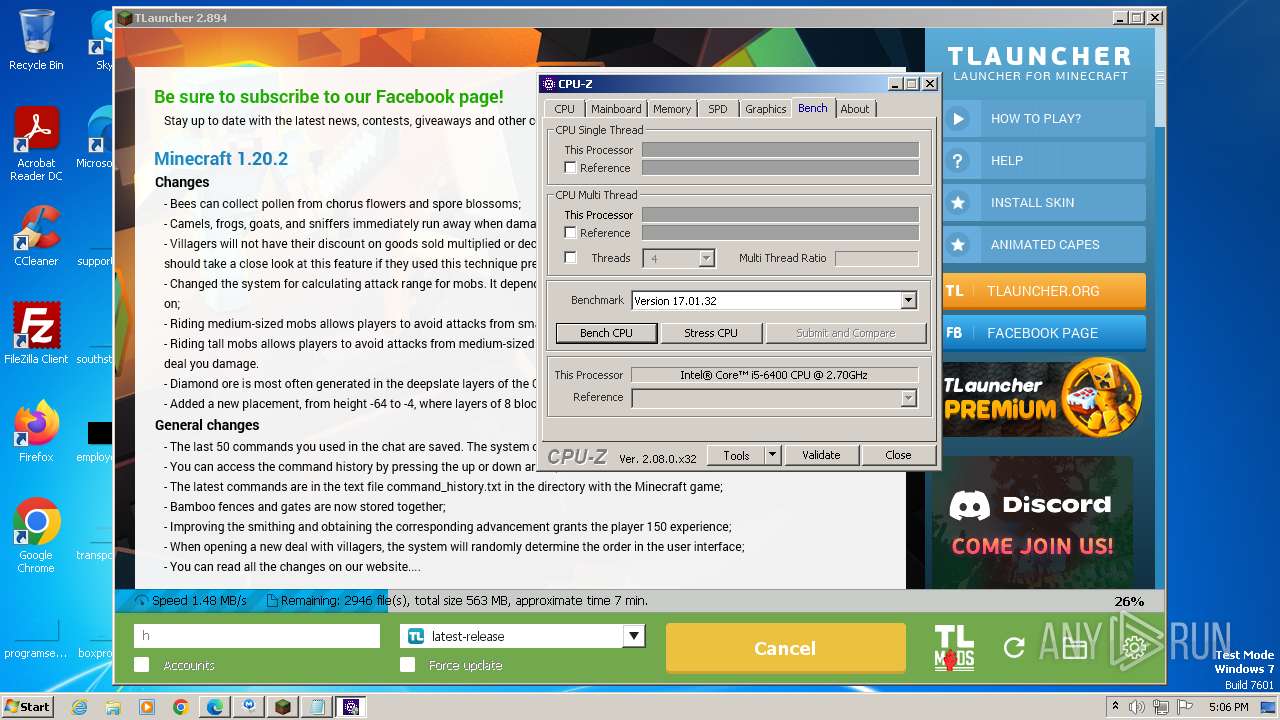
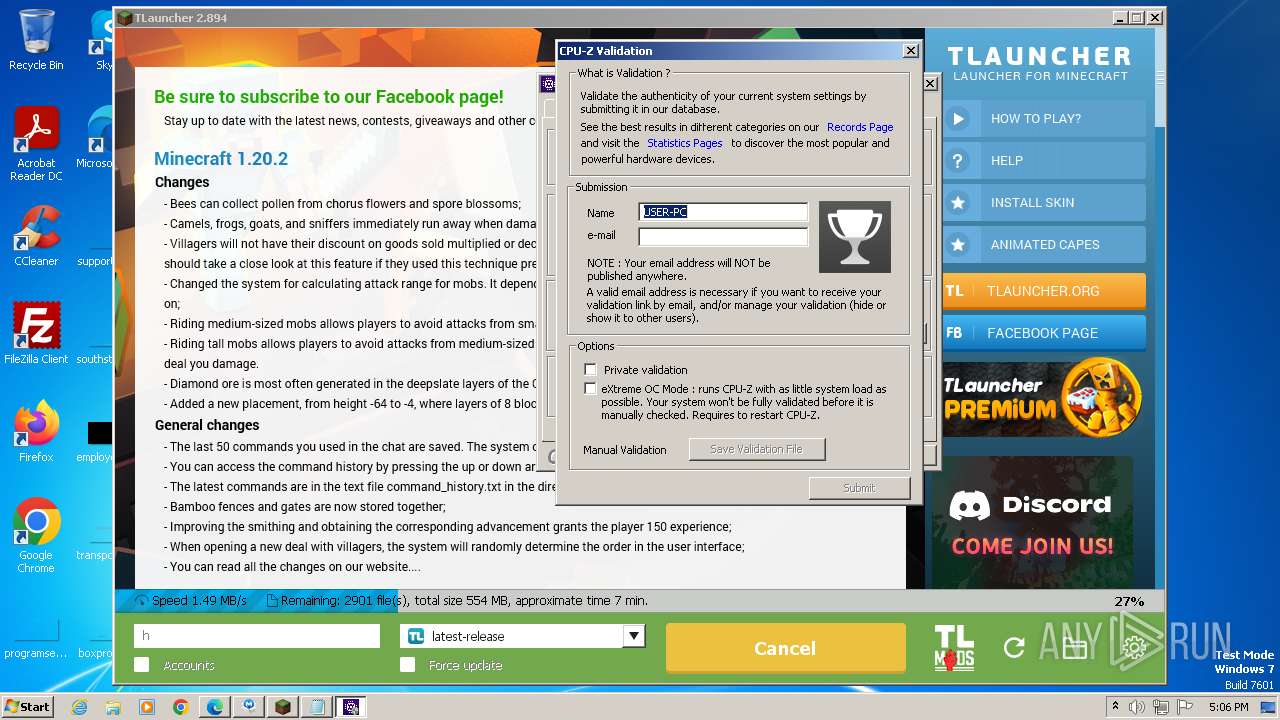
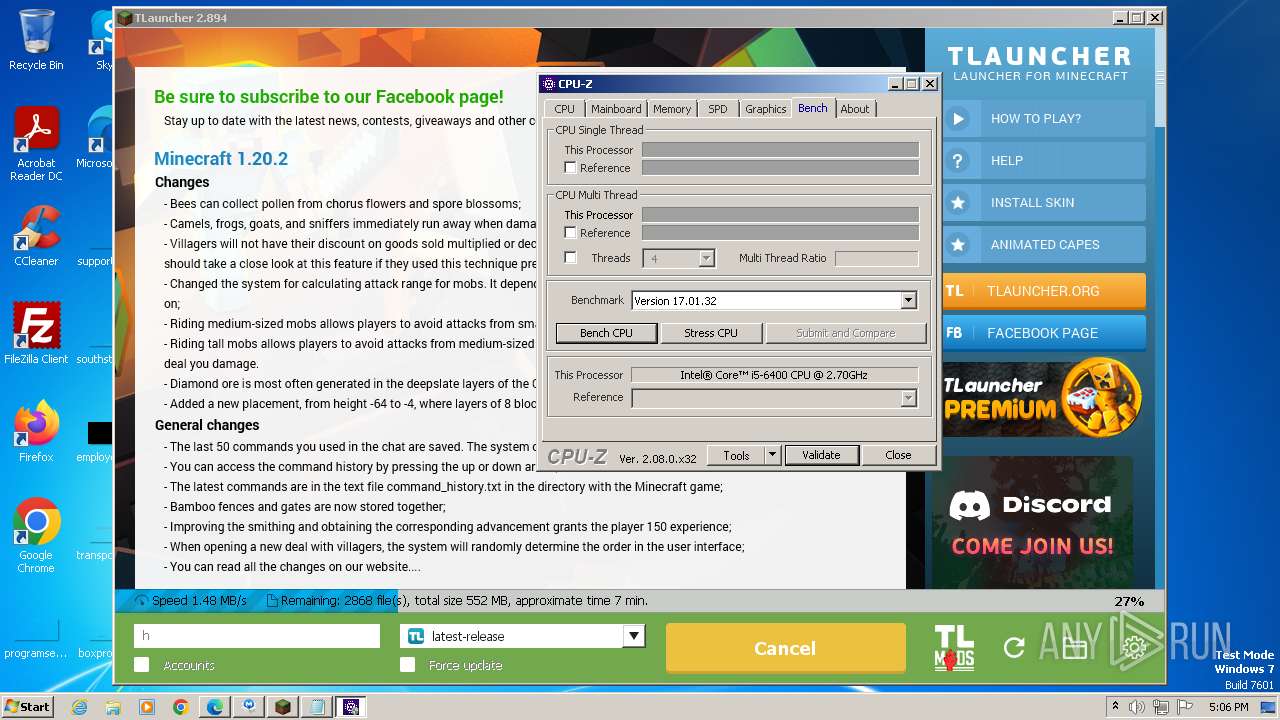
- cpu-z_2.08-en.exe (PID: 3520)
- cpu-z_2.08-en.exe (PID: 2564)
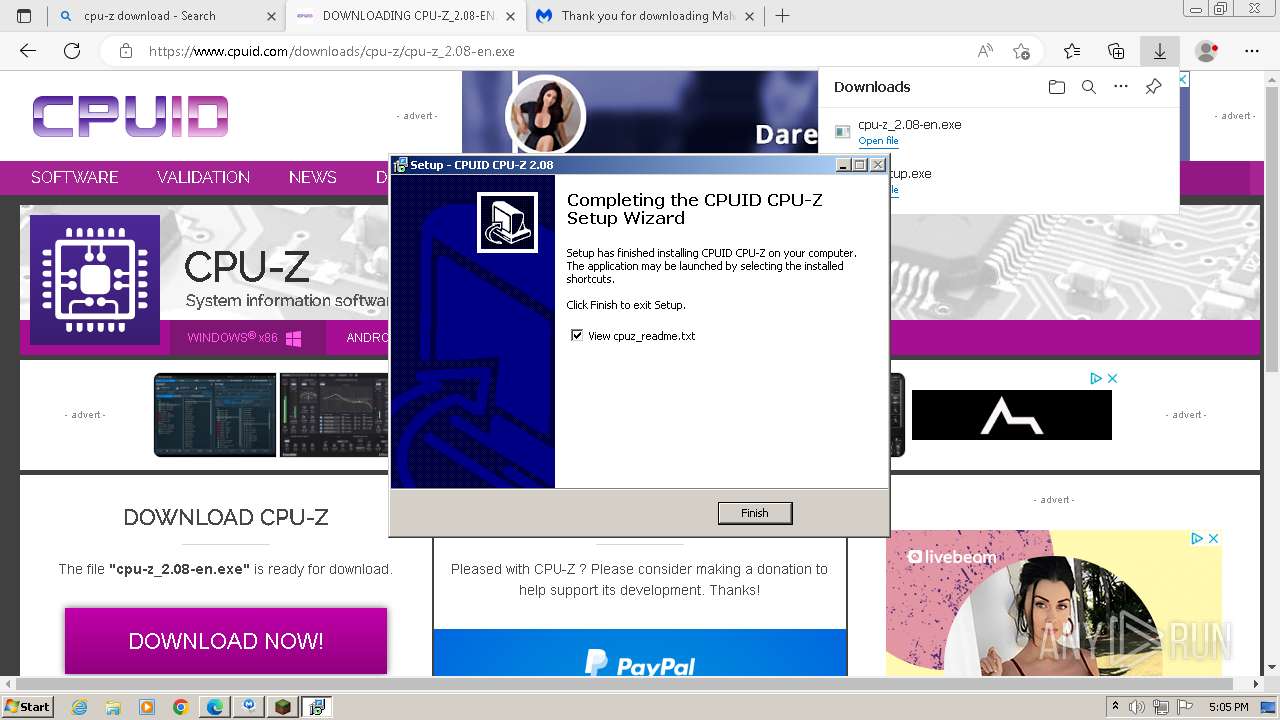
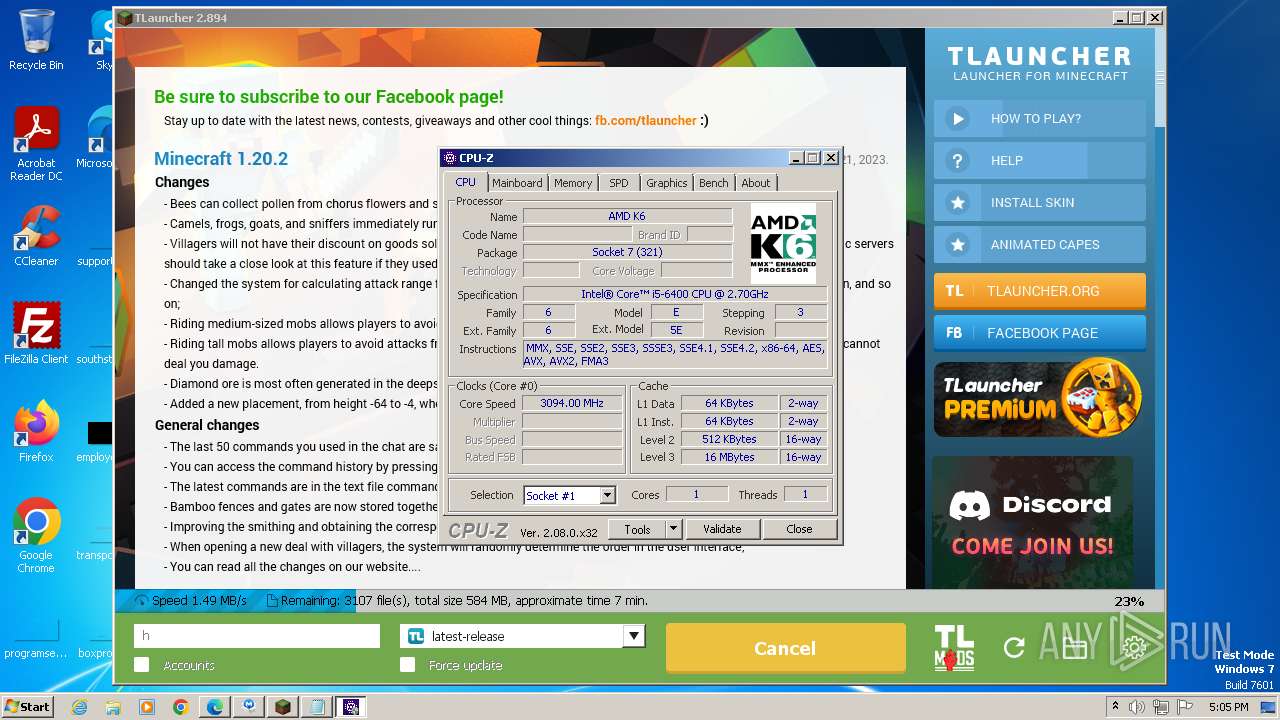
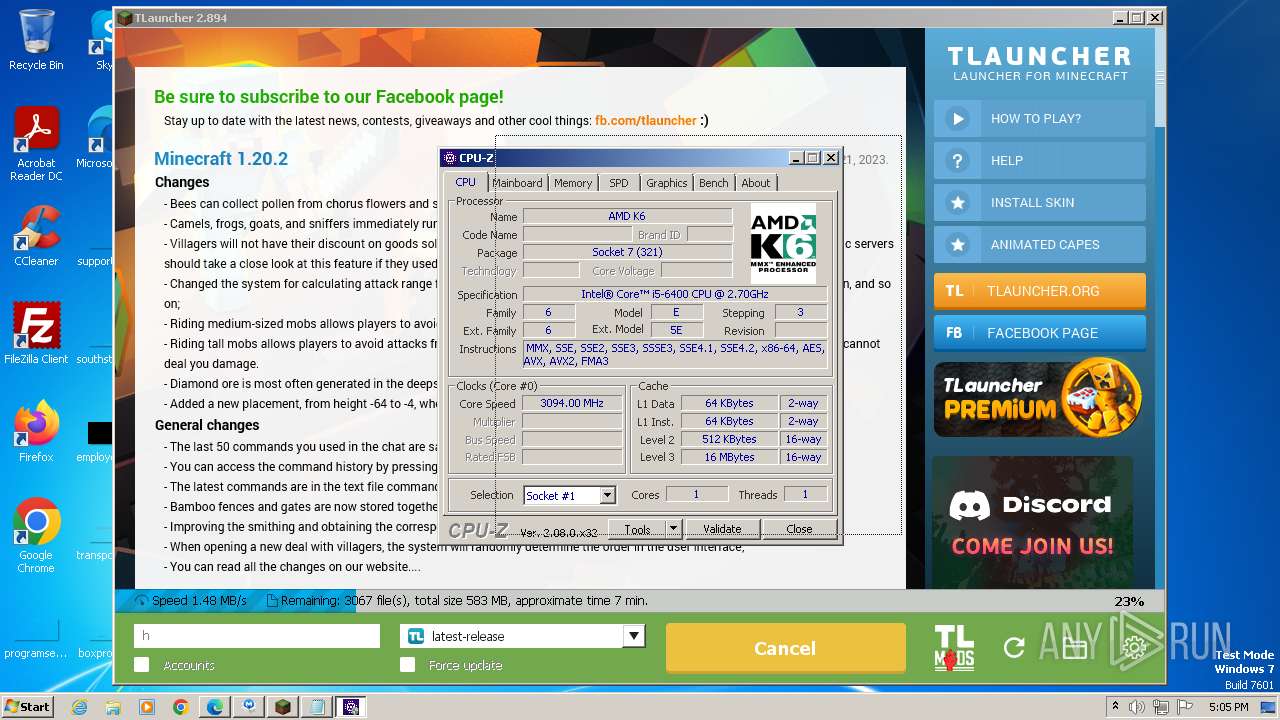
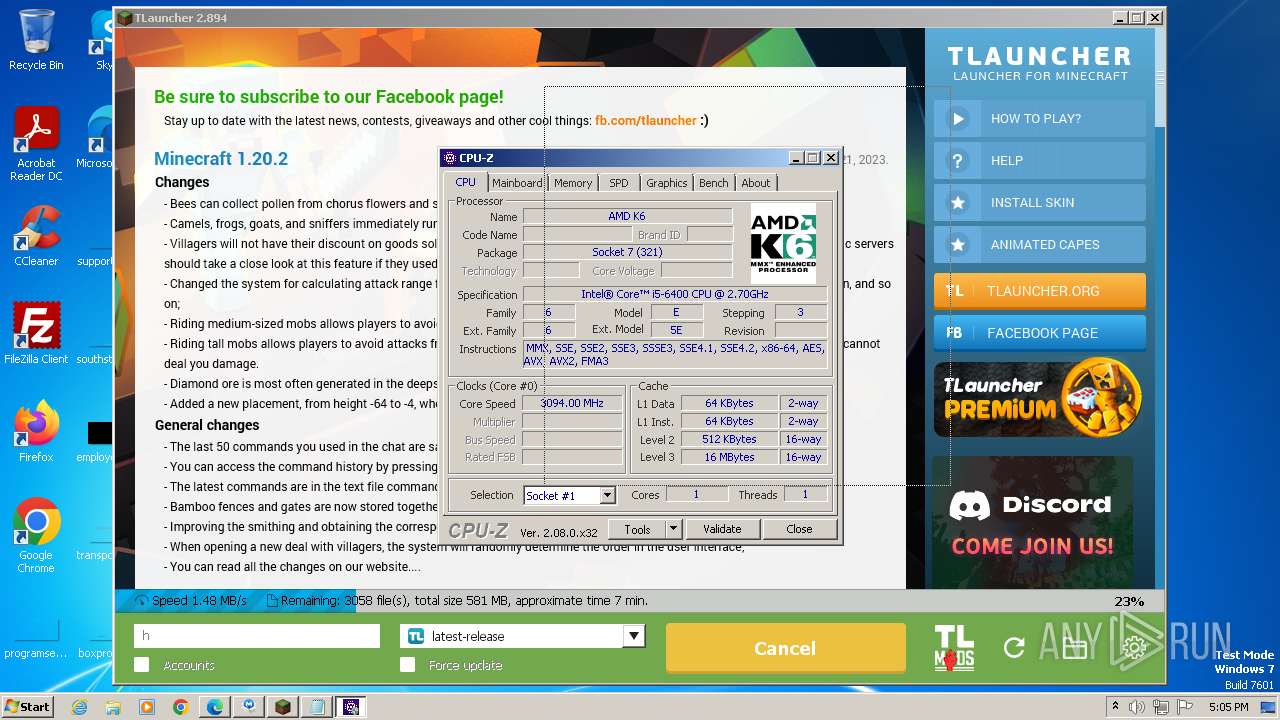
- cpuz.exe (PID: 2052)
- cpuz.exe (PID: 1560)
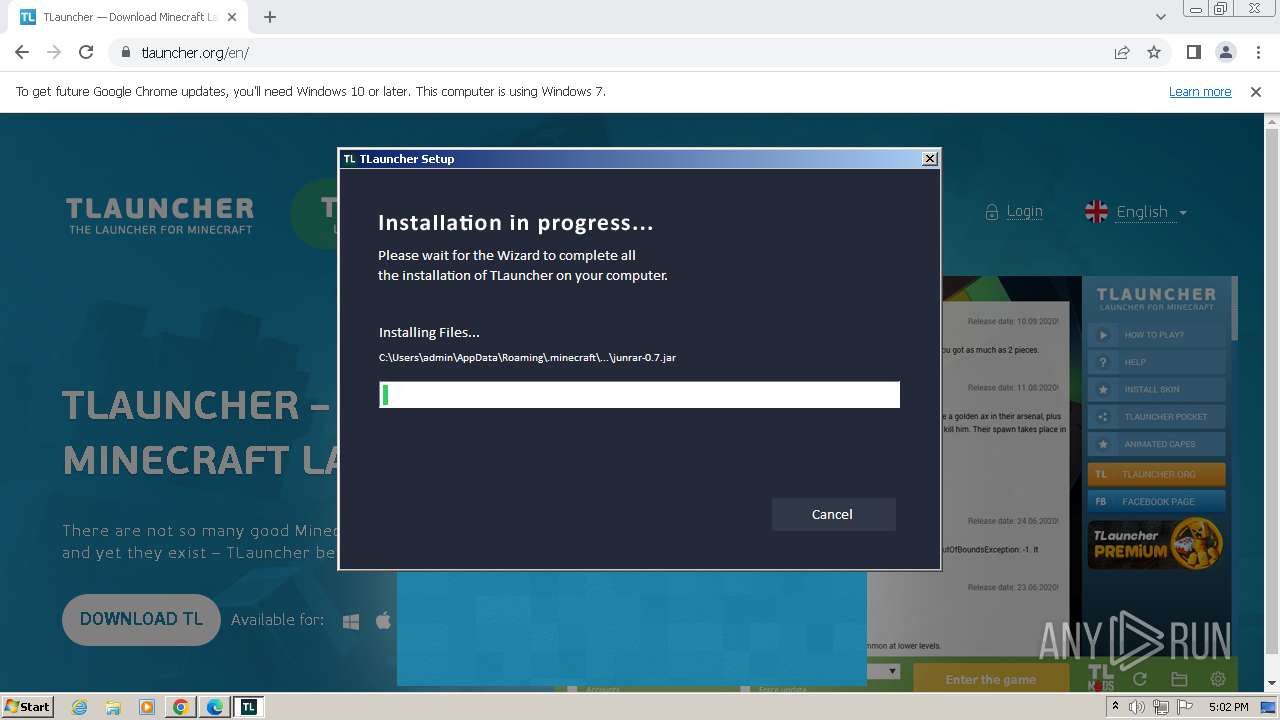
Drops the executable file immediately after the start
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3772)
- irsetup.exe (PID: 3068)
- irsetup.exe (PID: 3640)
- BrowserInstaller.exe (PID: 3872)
- opera-installer-bro.exe (PID: 4036)
- javaw.exe (PID: 280)
- cpu-z_2.08-en.exe (PID: 2564)
- cpu-z_2.08-en.tmp (PID: 1620)
- cpu-z_2.08-en.exe (PID: 3520)
- javaw.exe (PID: 3384)
- cpuz.exe (PID: 2052)
Loads dropped or rewritten executable
- irsetup.exe (PID: 3068)
- irsetup.exe (PID: 3640)
- opera-installer-bro.exe (PID: 4036)
- javaw.exe (PID: 280)
- javaw.exe (PID: 3384)
Actions looks like stealing of personal data
- irsetup.exe (PID: 3068)
- MBSetup.exe (PID: 1240)
Creates a writable file the system directory
- MBSetup.exe (PID: 1240)
SUSPICIOUS
Reads the Internet Settings
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3772)
- irsetup.exe (PID: 3068)
- irsetup.exe (PID: 3640)
- BrowserInstaller.exe (PID: 3872)
- WMIC.exe (PID: 444)
- WMIC.exe (PID: 2212)
- WMIC.exe (PID: 1040)
- WMIC.exe (PID: 3812)
- cpuz.exe (PID: 2052)
- MBSetup.exe (PID: 1240)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 3068)
- irsetup.exe (PID: 3640)
- cpu-z_2.08-en.tmp (PID: 1620)
Checks for Java to be installed
- irsetup.exe (PID: 3068)
- TLauncher.exe (PID: 2080)
Reads Internet Explorer settings
- irsetup.exe (PID: 3068)
Reads settings of System Certificates
- irsetup.exe (PID: 3068)
- irsetup.exe (PID: 3640)
- MBSetup.exe (PID: 1240)
- dxdiag.exe (PID: 2724)
- cpuz.exe (PID: 2052)
Reads security settings of Internet Explorer
- irsetup.exe (PID: 3068)
- irsetup.exe (PID: 3640)
- cpuz.exe (PID: 2052)
Checks Windows Trust Settings
- irsetup.exe (PID: 3068)
- irsetup.exe (PID: 3640)
- cpuz.exe (PID: 2052)
Reads Microsoft Outlook installation path
- irsetup.exe (PID: 3068)
Adds/modifies Windows certificates
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3772)
- msedge.exe (PID: 3388)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 280)
- javaw.exe (PID: 3384)
Starts application with an unusual extension
- cmd.exe (PID: 1560)
- cmd.exe (PID: 2412)
- cmd.exe (PID: 3344)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 2560)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 3748)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 1560)
- cmd.exe (PID: 2412)
Process requests binary or script from the Internet
- javaw.exe (PID: 280)
- javaw.exe (PID: 3384)
Process drops legitimate windows executable
- javaw.exe (PID: 280)
- javaw.exe (PID: 3384)
Uses ICACLS.EXE to modify access control lists
- javaw.exe (PID: 3384)
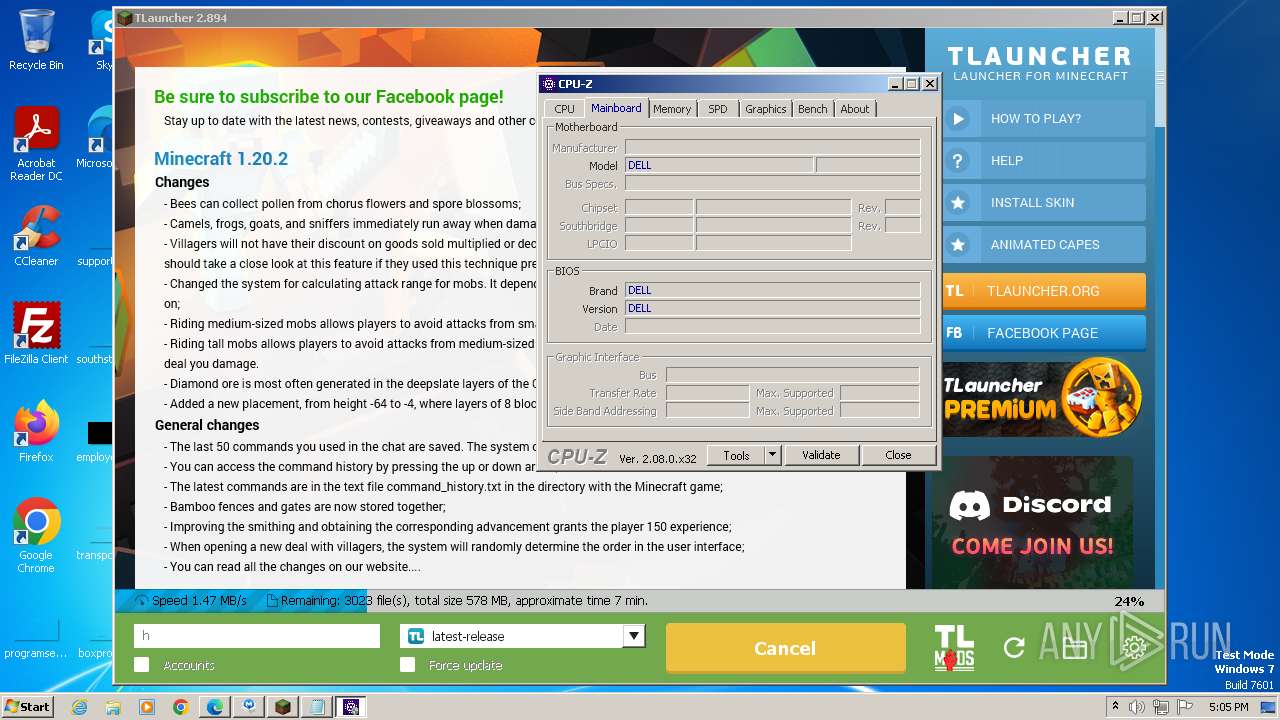
Reads the BIOS version
- MBSetup.exe (PID: 1240)
The process drops C-runtime libraries
- javaw.exe (PID: 280)
- javaw.exe (PID: 3384)
Searches for installed software
- MBSetup.exe (PID: 1240)
Creates files in the driver directory
- MBSetup.exe (PID: 1240)
Uses WMIC.EXE to obtain quick Fix Engineering (patches) data
- cmd.exe (PID: 3240)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 2560)
The process creates files with name similar to system file names
- javaw.exe (PID: 3384)
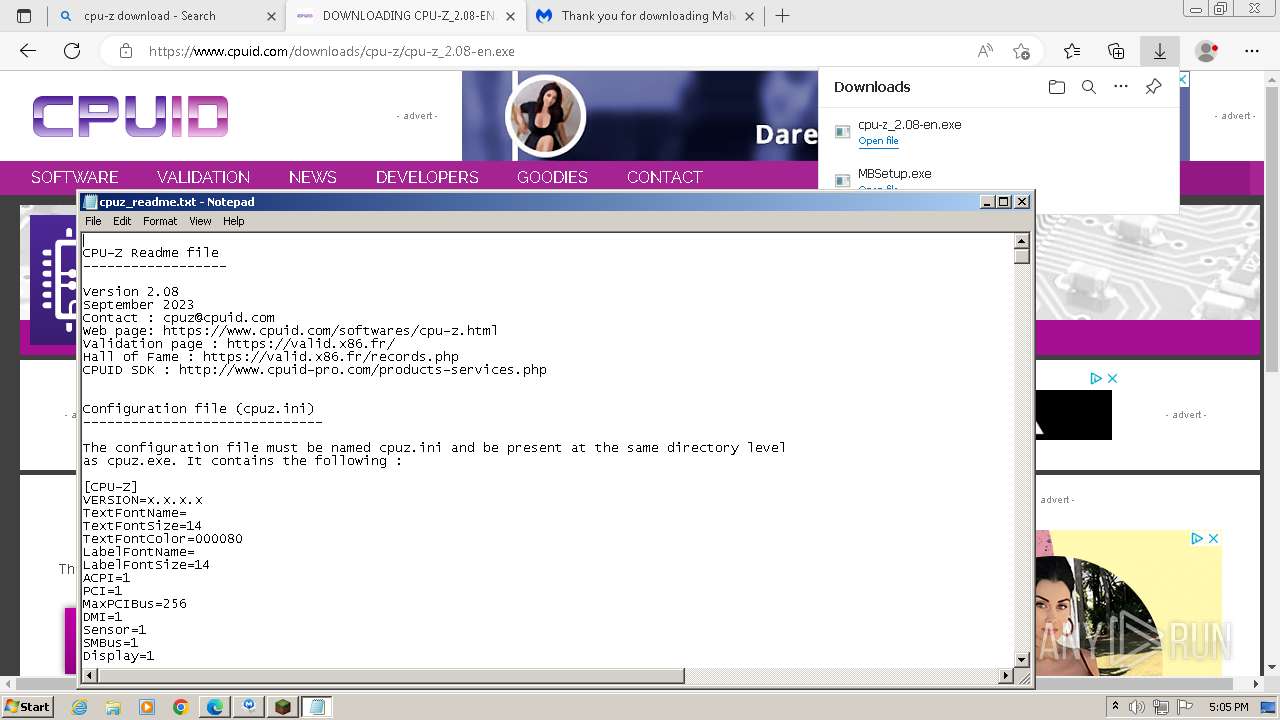
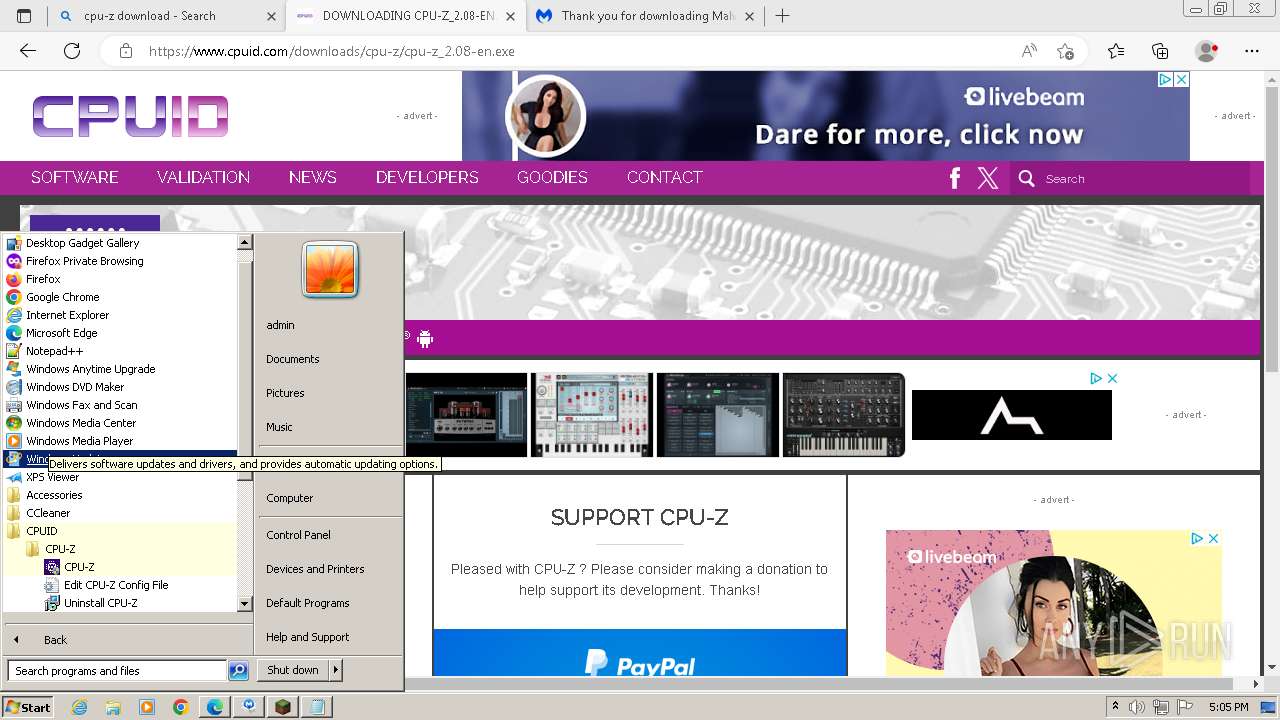
Start notepad (likely ransomware note)
- cpu-z_2.08-en.tmp (PID: 820)
The process verifies whether the antivirus software is installed
- MBSetup.exe (PID: 1240)
Drops a system driver (possible attempt to evade defenses)
- cpuz.exe (PID: 2052)
INFO
The process uses the downloaded file
- chrome.exe (PID: 1928)
- chrome.exe (PID: 4000)
- chrome.exe (PID: 3552)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 3612)
- msedge.exe (PID: 2520)
- msedge.exe (PID: 3388)
- msedge.exe (PID: 3776)
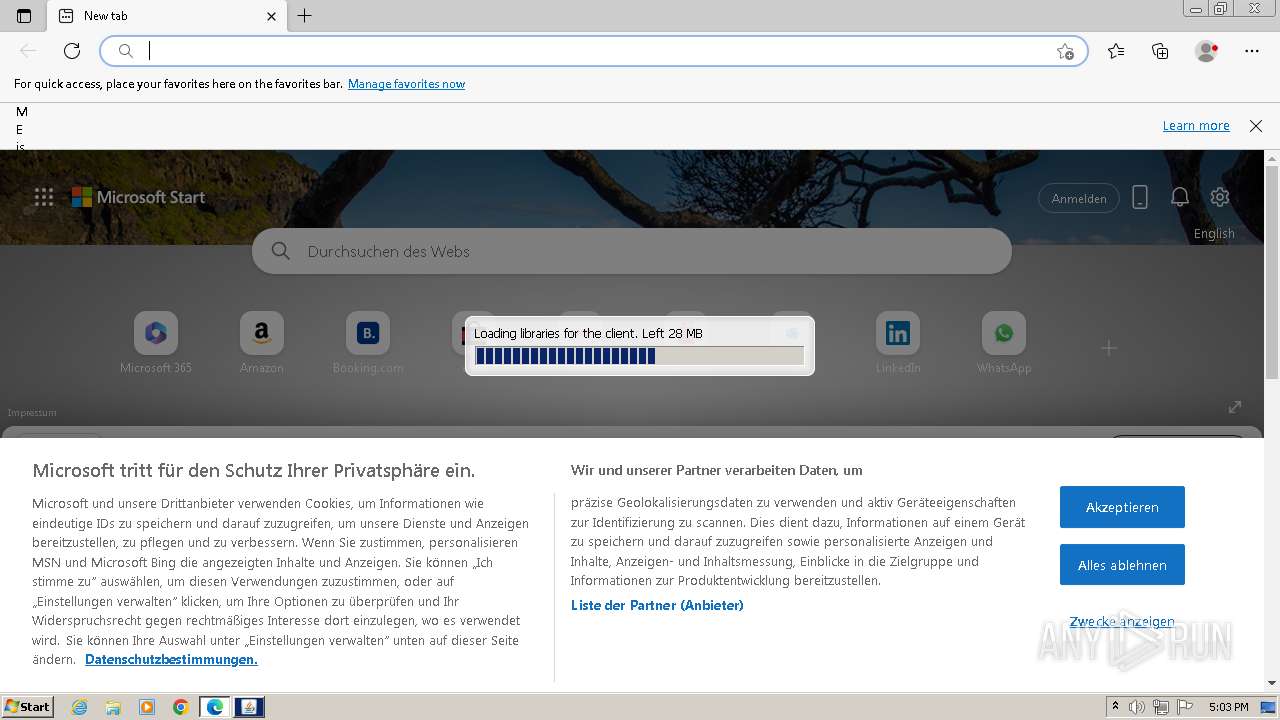
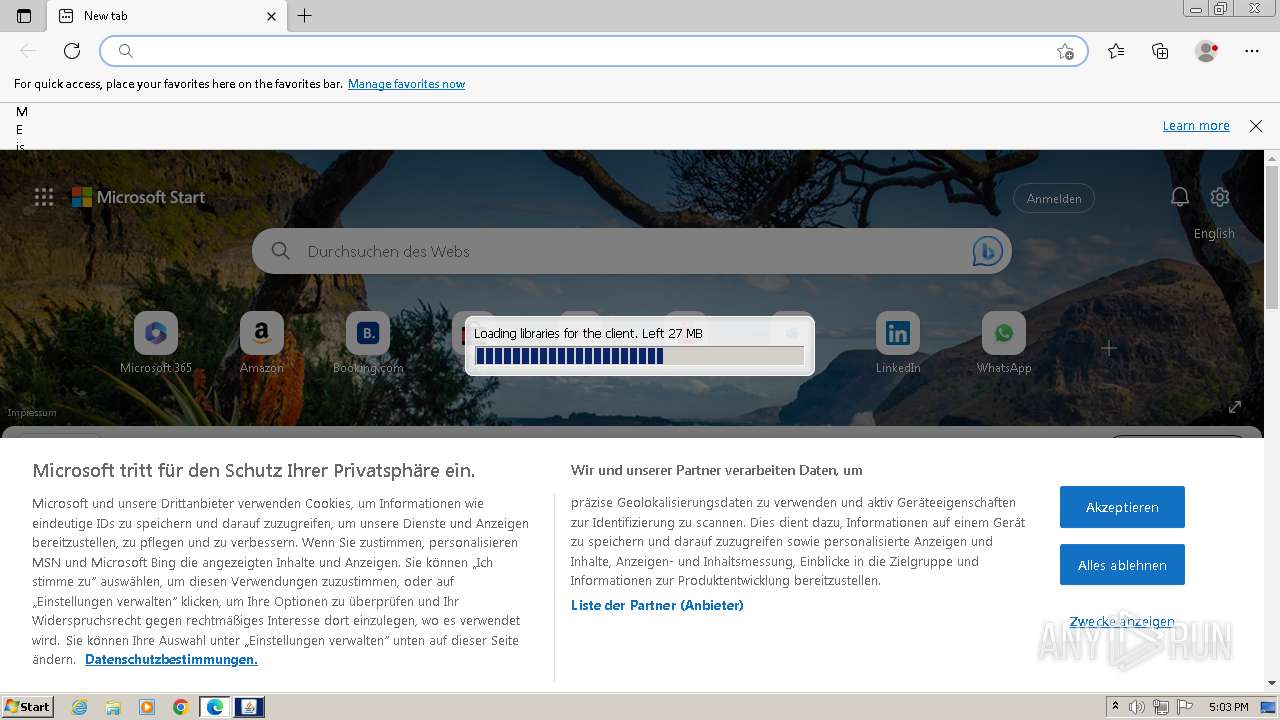
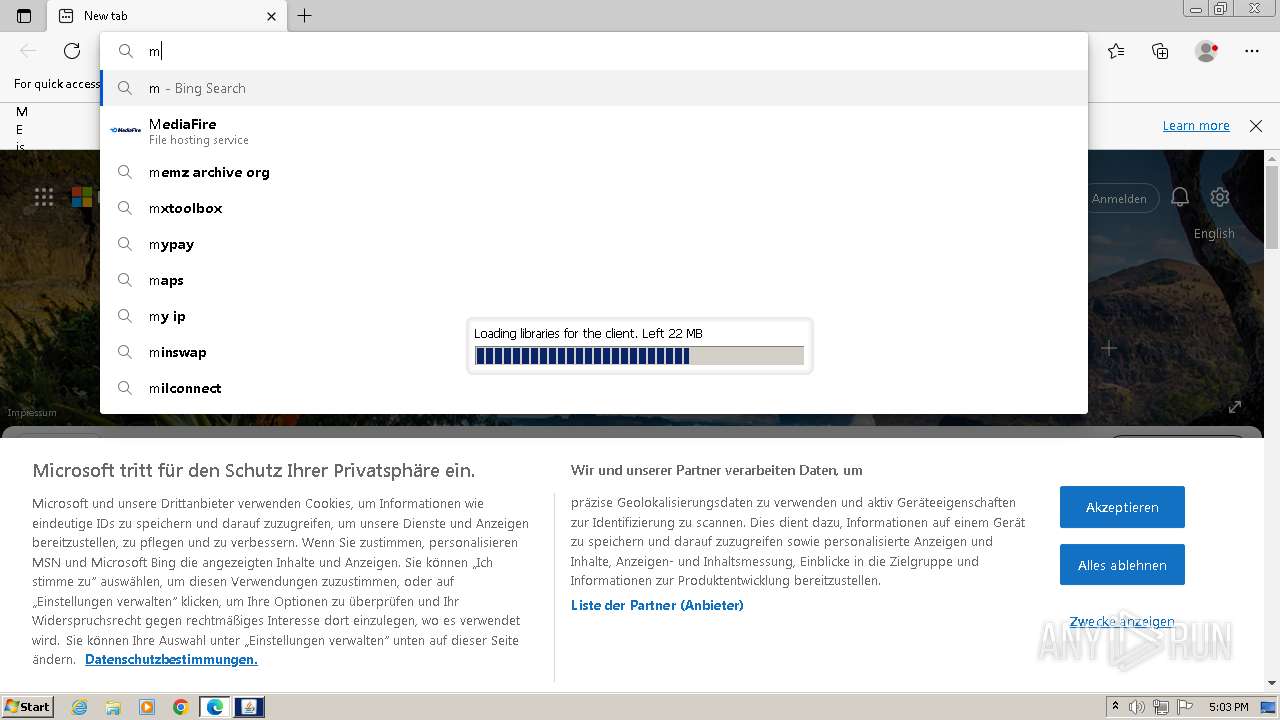
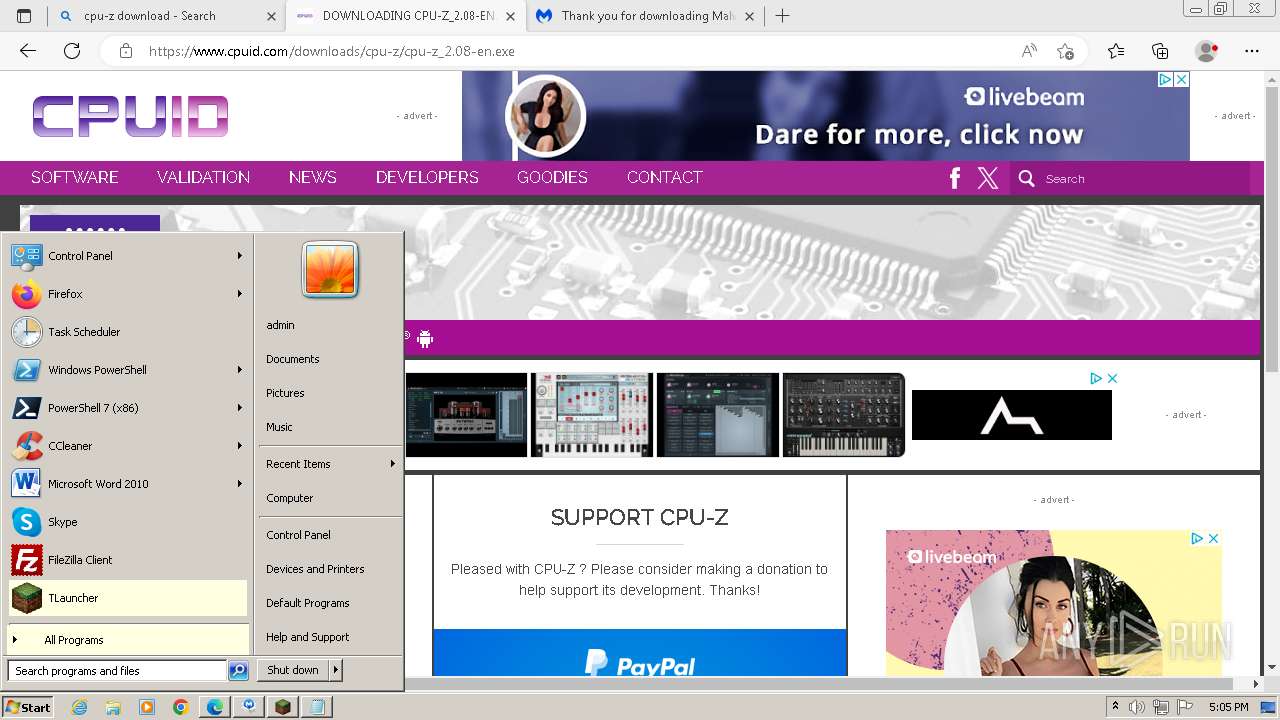
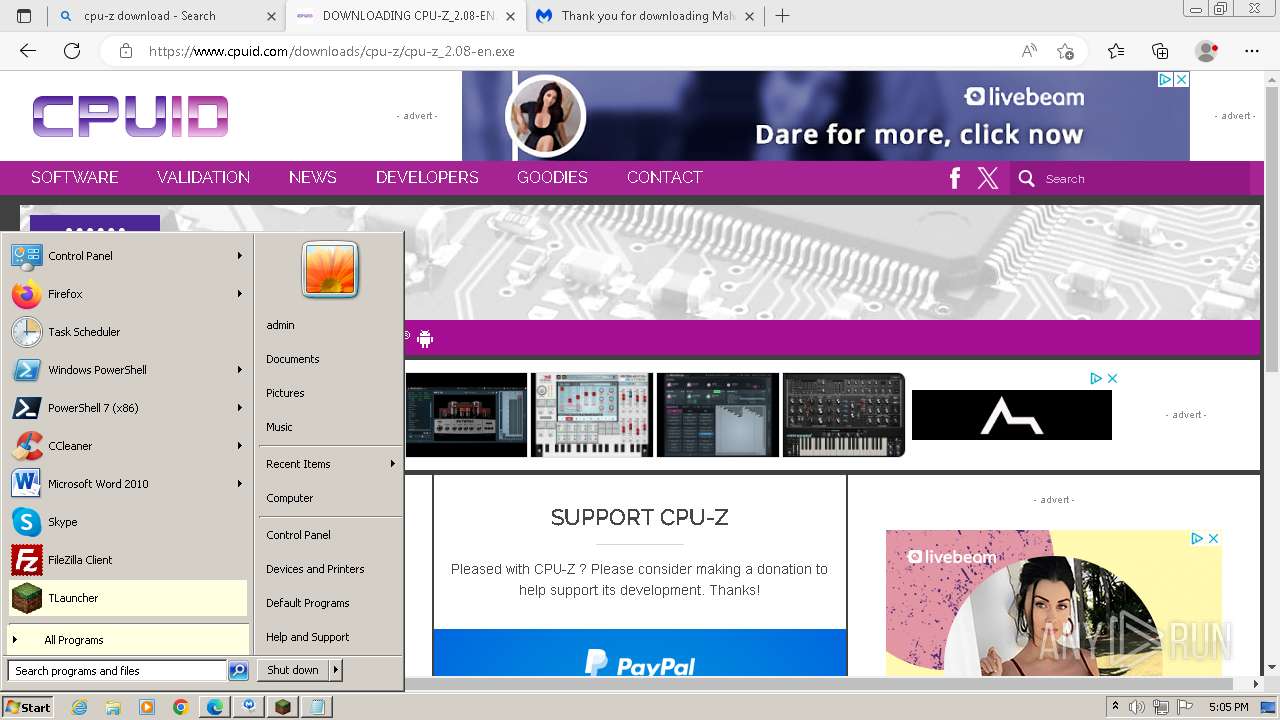
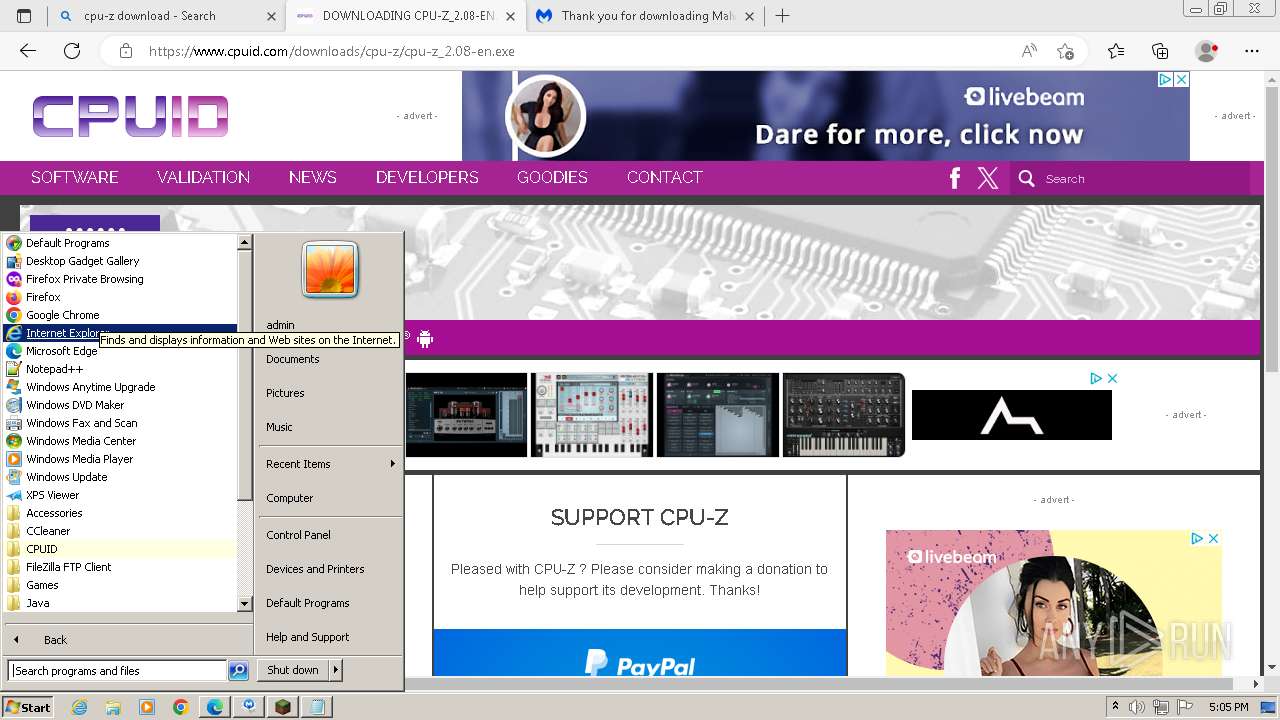
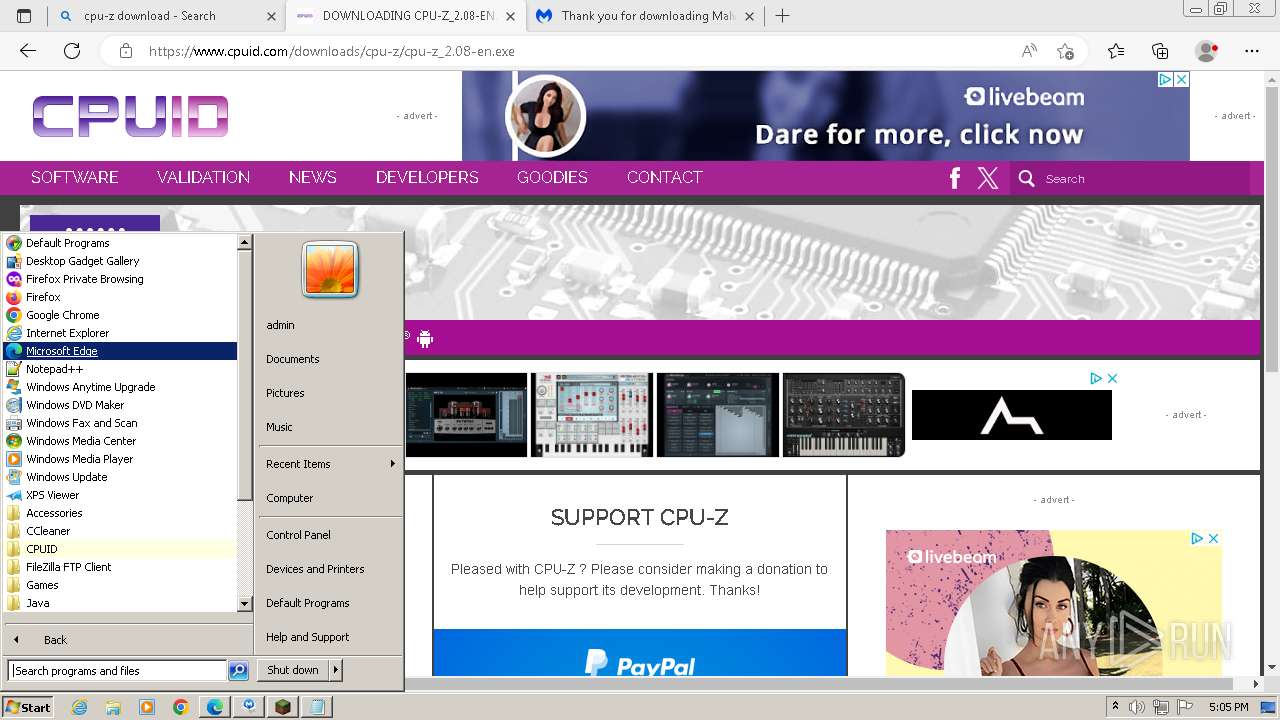
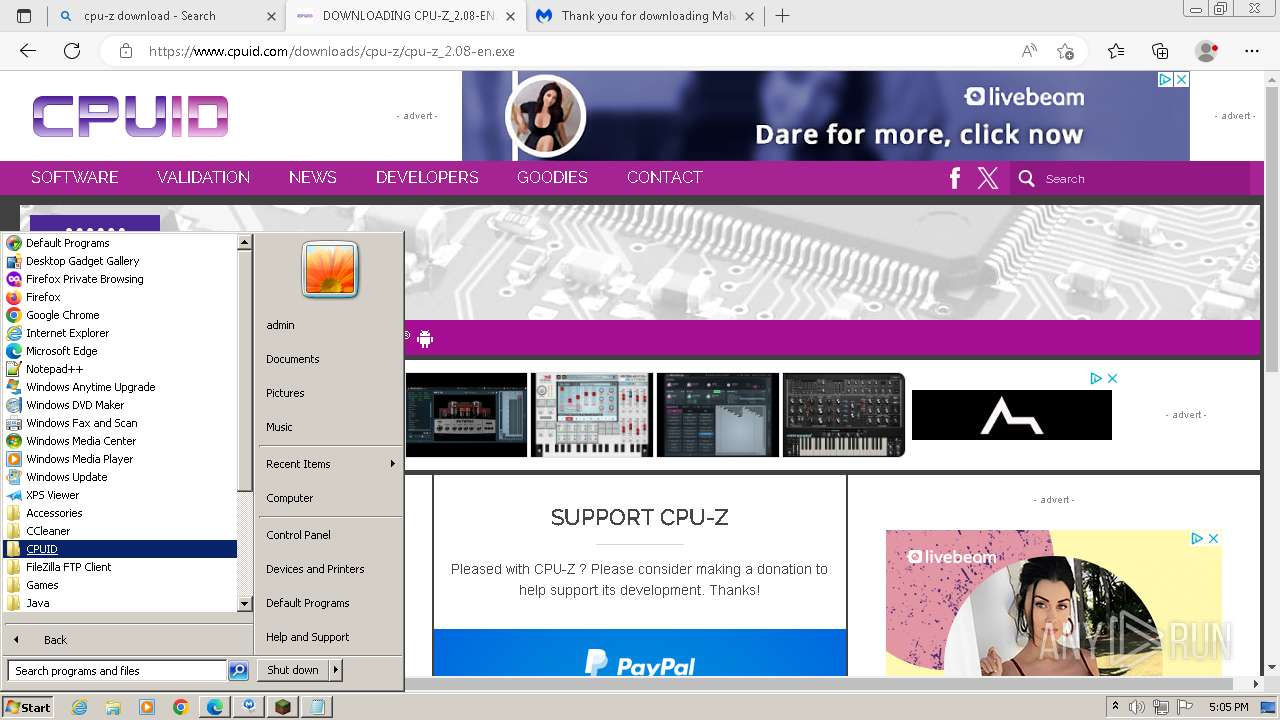
Manual execution by a user
- msedge.exe (PID: 3388)
- cpuz.exe (PID: 1560)
- cpuz.exe (PID: 2052)
Application launched itself
- chrome.exe (PID: 3628)
- msedge.exe (PID: 3388)
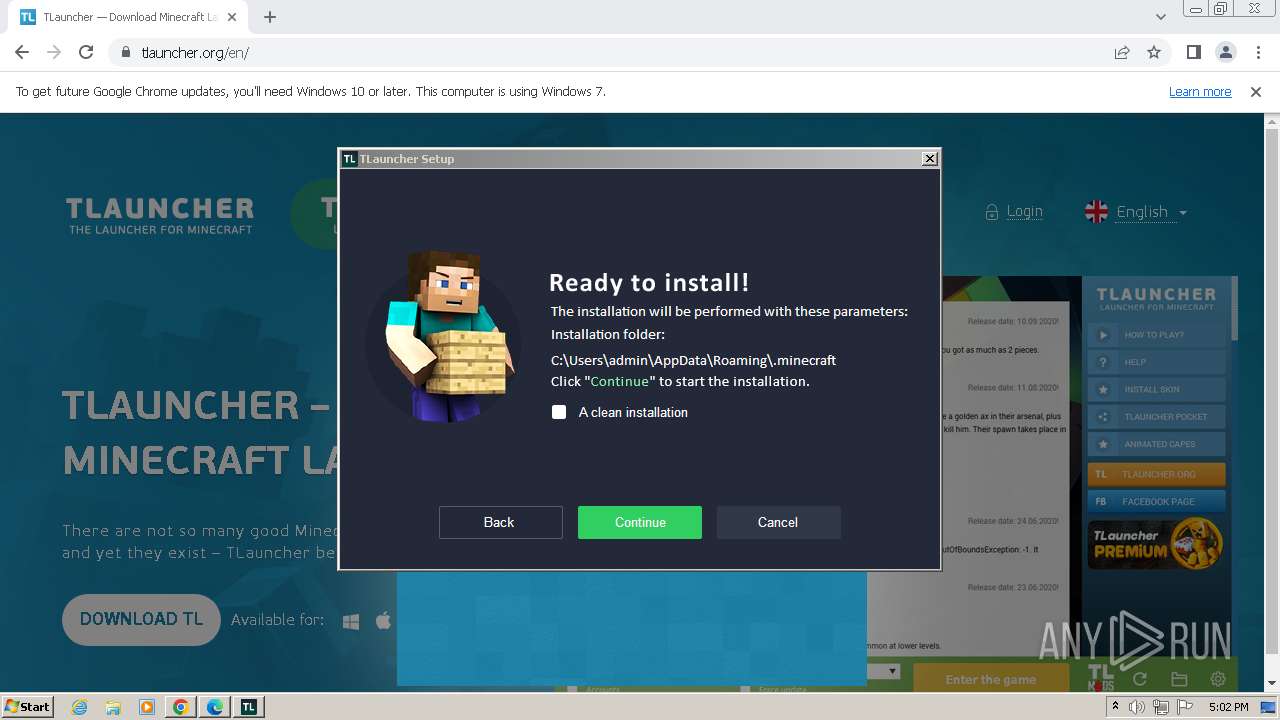
Create files in a temporary directory
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3772)
- irsetup.exe (PID: 3068)
- BrowserInstaller.exe (PID: 3872)
- irsetup.exe (PID: 3640)
- javaw.exe (PID: 280)
- opera-installer-bro.exe (PID: 4036)
- MBSetup.exe (PID: 1240)
- javaw.exe (PID: 3384)
- cpu-z_2.08-en.exe (PID: 2564)
- cpu-z_2.08-en.exe (PID: 3520)
Checks supported languages
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3772)
- irsetup.exe (PID: 3068)
- BrowserInstaller.exe (PID: 3872)
- irsetup.exe (PID: 3640)
- opera-installer-bro.exe (PID: 4036)
- javaw.exe (PID: 280)
- TLauncher.exe (PID: 2080)
- chcp.com (PID: 2752)
- chcp.com (PID: 1580)
- javaw.exe (PID: 3384)
- MBSetup.exe (PID: 1240)
- chcp.com (PID: 2292)
- chcp.com (PID: 1740)
- chcp.com (PID: 2292)
- chcp.com (PID: 4004)
- chcp.com (PID: 3292)
- cpu-z_2.08-en.exe (PID: 2564)
- cpu-z_2.08-en.tmp (PID: 820)
- cpu-z_2.08-en.exe (PID: 3520)
- cpuz.exe (PID: 2052)
- cpu-z_2.08-en.tmp (PID: 1620)
Drops the executable file immediately after the start
- chrome.exe (PID: 3628)
- msedge.exe (PID: 3388)
- msedge.exe (PID: 3076)
Reads the computer name
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3772)
- irsetup.exe (PID: 3068)
- irsetup.exe (PID: 3640)
- BrowserInstaller.exe (PID: 3872)
- javaw.exe (PID: 280)
- MBSetup.exe (PID: 1240)
- javaw.exe (PID: 3384)
- cpu-z_2.08-en.tmp (PID: 820)
- cpu-z_2.08-en.tmp (PID: 1620)
- cpuz.exe (PID: 2052)
Reads the machine GUID from the registry
- irsetup.exe (PID: 3068)
- irsetup.exe (PID: 3640)
- javaw.exe (PID: 280)
- MBSetup.exe (PID: 1240)
- javaw.exe (PID: 3384)
- cpuz.exe (PID: 2052)
Checks proxy server information
- irsetup.exe (PID: 3068)
- irsetup.exe (PID: 3640)
- cpuz.exe (PID: 2052)
Creates files or folders in the user directory
- irsetup.exe (PID: 3640)
- irsetup.exe (PID: 3068)
- javaw.exe (PID: 280)
- javaw.exe (PID: 3384)
- dxdiag.exe (PID: 2724)
- cpuz.exe (PID: 2052)
Creates files in the program directory
- irsetup.exe (PID: 3068)
- javaw.exe (PID: 280)
- javaw.exe (PID: 3384)
- MBSetup.exe (PID: 1240)
- cpu-z_2.08-en.tmp (PID: 1620)
Reads security settings of Internet Explorer
- dxdiag.exe (PID: 2724)
Application was dropped or rewritten from another process
- cpu-z_2.08-en.tmp (PID: 820)
- cpu-z_2.08-en.tmp (PID: 1620)
Reads Environment values
- cpuz.exe (PID: 2052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
177
Monitored processes
107
Malicious processes
18
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | TLauncher.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 296 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1488 --field-trial-handle=1344,i,8139809351815095457,8359201415912445340,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3728 --field-trial-handle=1344,i,8139809351815095457,8359201415912445340,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 444 | wmic os get osarchitecture | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 444 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2308 --field-trial-handle=1344,i,8139809351815095457,8359201415912445340,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 460 | "C:\Users\admin\Downloads\MBSetup.exe" | C:\Users\admin\Downloads\MBSetup.exe | — | msedge.exe | |||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: Malwarebytes Setup Exit code: 3221226540 Version: 4.6.0.352 Modules
| |||||||||||||||
| 568 | "C:\Windows\system32\NOTEPAD.EXE" C:\Program Files\CPUID\CPU-Z\cpuz_readme.txt | C:\Windows\System32\notepad.exe | — | cpu-z_2.08-en.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 668 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=3936 --field-trial-handle=1344,i,8139809351815095457,8359201415912445340,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 820 | "C:\Users\admin\AppData\Local\Temp\is-OL0DD.tmp\cpu-z_2.08-en.tmp" /SL5="$60302,1938476,58368,C:\Users\admin\Downloads\cpu-z_2.08-en.exe" | C:\Users\admin\AppData\Local\Temp\is-OL0DD.tmp\cpu-z_2.08-en.tmp | — | cpu-z_2.08-en.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=42 --mojo-platform-channel-handle=5284 --field-trial-handle=1344,i,8139809351815095457,8359201415912445340,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
52 690
Read events
52 271
Write events
395
Delete events
24
Modification events
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3628) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
480
Suspicious files
3 526
Text files
1 255
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1ece1b.TMP | — | |
MD5:— | SHA256:— | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1ed2ce.TMP | — | |
MD5:— | SHA256:— | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1ece1b.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 3628 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
301
DNS requests
317
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
280 | javaw.exe | GET | 302 | 78.46.66.120:80 | http://res.tlauncher.org/b/libraries/org/tlauncher/picture-bundle/3.72/picture-bundle-3.72.jar | unknown | — | — | unknown |
280 | javaw.exe | GET | 302 | 78.46.66.120:80 | http://res.tlauncher.org/b/client/jre/windows/jre-8u111-windows-i586.tar.gz | unknown | — | — | unknown |
3384 | javaw.exe | HEAD | 200 | 104.20.235.70:80 | http://page.tlauncher.org/ | unknown | — | — | unknown |
3640 | irsetup.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | unknown | binary | 471 b | unknown |
3388 | msedge.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/certs/Microsoft%20Identity%20Verification%20Root%20Certificate%20Authority%202020.crt | unknown | binary | 1.45 Kb | unknown |
3640 | irsetup.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEH1NQqkrQx1%2BZFPnwZqNWHc%3D | unknown | binary | 1.41 Kb | unknown |
3640 | irsetup.exe | GET | 200 | 8.253.207.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c9e4eda37d63bb09 | unknown | compressed | 4.66 Kb | unknown |
3384 | javaw.exe | GET | 200 | 104.26.5.134:80 | http://img.fastrepo.org/update/downloads/configs/client/video/tl-discord-en.png | unknown | image | 49.2 Kb | unknown |
3384 | javaw.exe | GET | 200 | 104.20.234.70:80 | http://repo.tlauncher.org/update/downloads/configs/inner_servers-1.1.json | unknown | binary | 5.35 Kb | unknown |
3388 | msedge.exe | GET | 200 | 23.53.40.49:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ea1d58e835d84cda | unknown | compressed | 61.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3628 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3352 | chrome.exe | 142.250.186.45:443 | accounts.google.com | GOOGLE | US | unknown |
3352 | chrome.exe | 104.20.235.70:443 | tlauncher.org | CLOUDFLARENET | — | unknown |
3352 | chrome.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
3352 | chrome.exe | 172.217.18.100:443 | www.google.com | GOOGLE | US | whitelisted |
3352 | chrome.exe | 104.16.169.131:443 | hcaptcha.com | CLOUDFLARENET | — | unknown |
3352 | chrome.exe | 104.16.57.101:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | unknown |
3352 | chrome.exe | 104.16.87.20:443 | cdn.jsdelivr.net | CLOUDFLARENET | — | shared |
3352 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | GOOGLE | US | whitelisted |
3352 | chrome.exe | 87.250.251.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tlauncher.org |
| unknown |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
hcaptcha.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
www.gstatic.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
280 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
280 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
3076 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
3076 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |