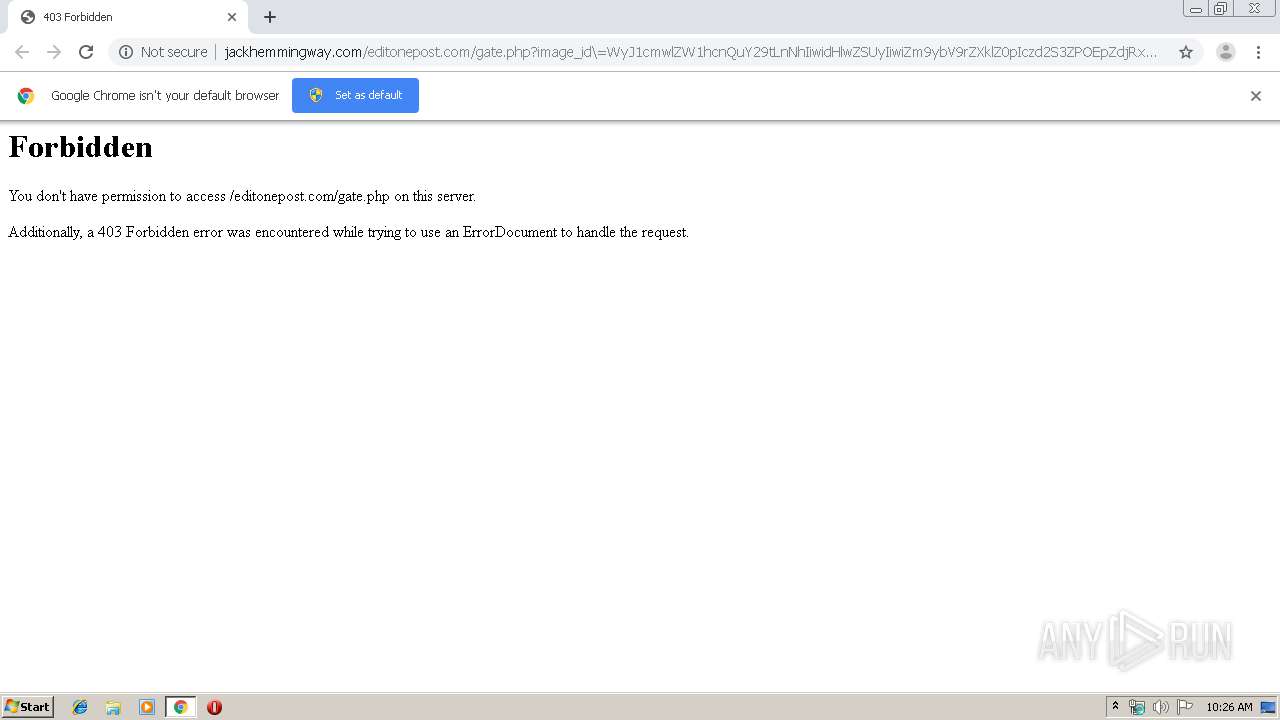
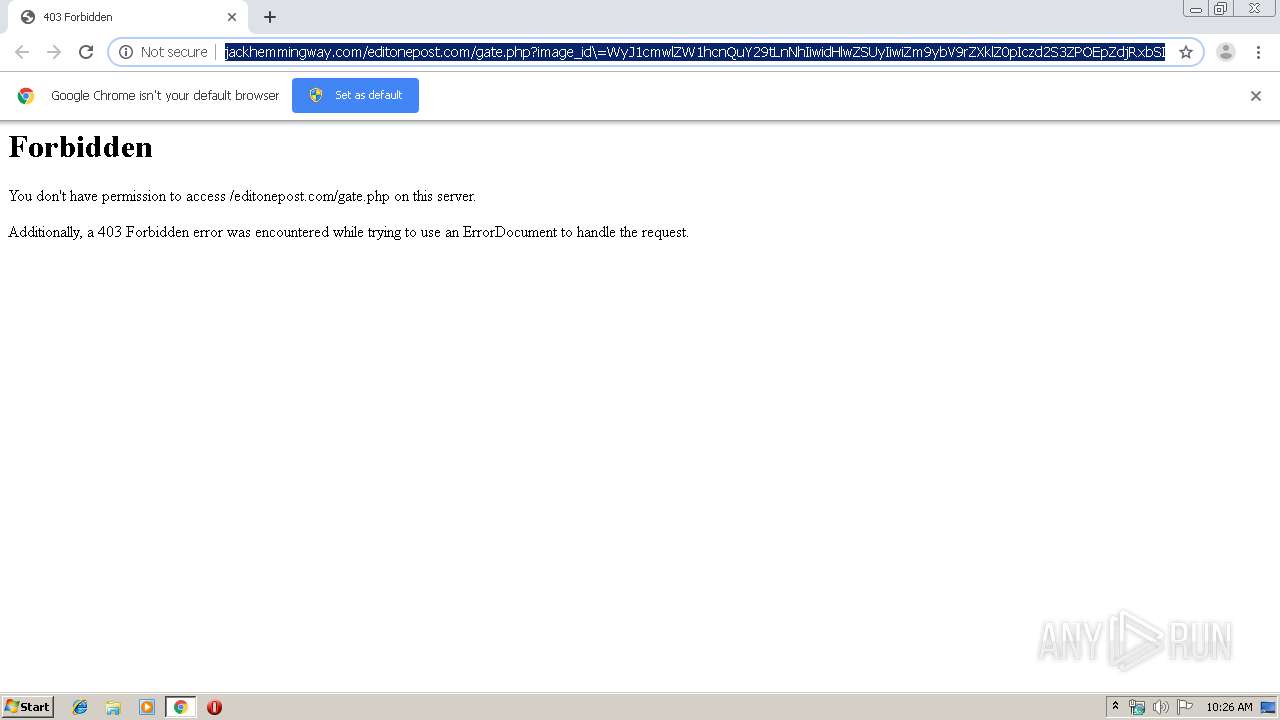
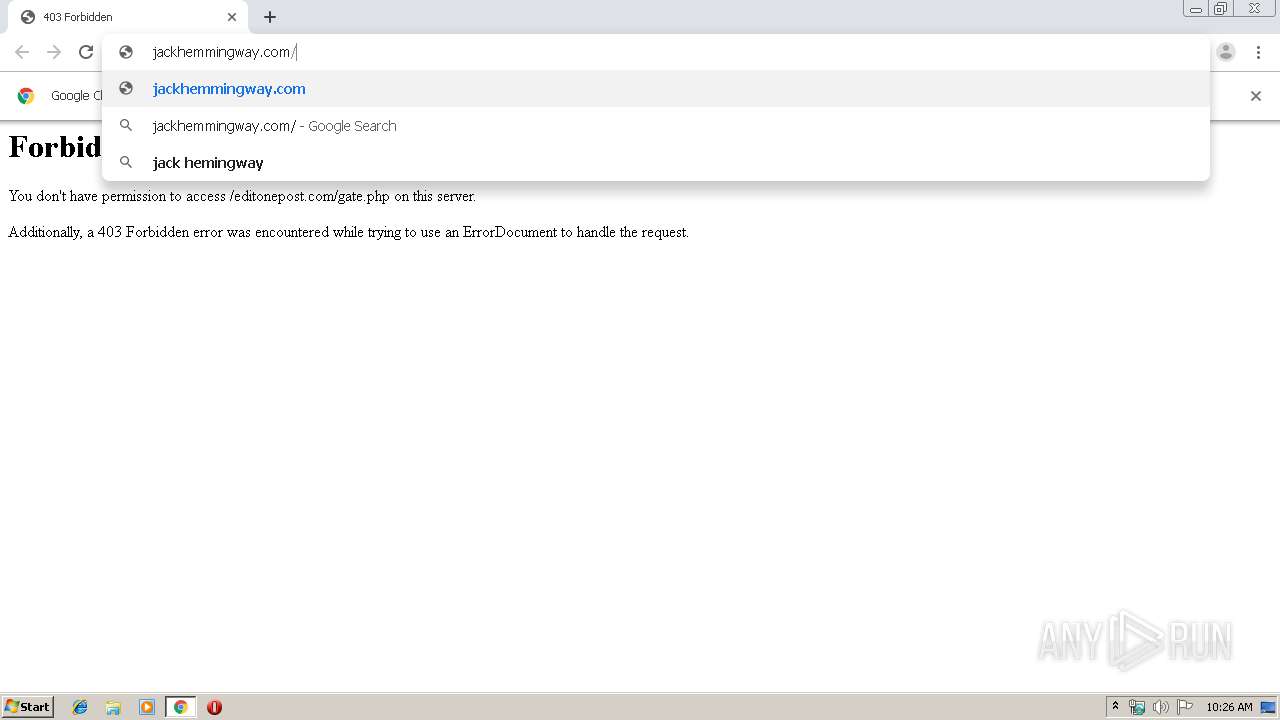
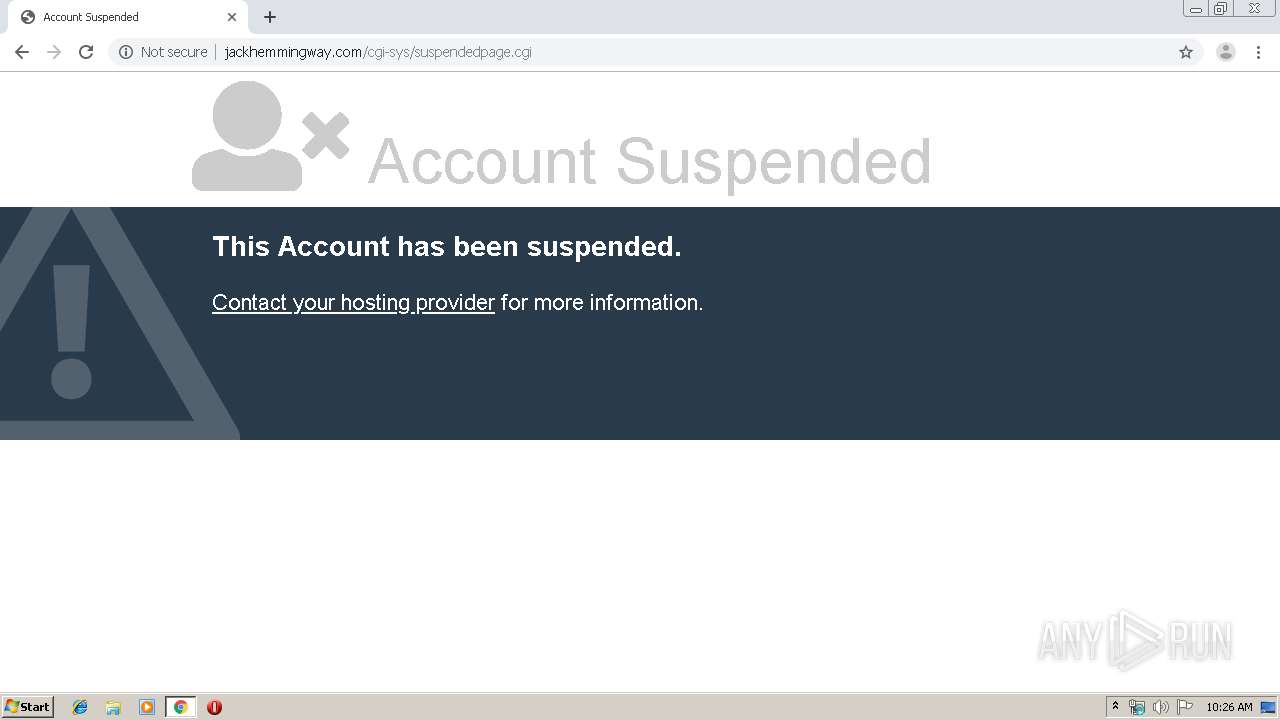
| URL: | http://jackhemmingway.com/editonepost.com/gate.php?image_id\=WyJ1cmwlZW1hcnQuY29tLnNhIiwidHlwZSUyIiwiZm9ybV9rZXklZ0pIczd2S3ZPOEpZdjRxbSIsInByb2R1Y3QlNDQ0IiwiZm9ybV9rZXklZ0pIczd2S3ZPOEpZdjRxbSIsInJhdGluZ3NbM10lMTEiLCJyYXRpbmdzWzNdJTEyIiwicmF0aW5nc1szXSUxMyI |
| Full analysis: | https://app.any.run/tasks/81e52a91-c929-44de-b40f-0442e0073609 |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 09:25:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 47A0986F78A53B583B667179A35779AD |
| SHA1: | E15C86D099053DE5DCC37A2BA782F0CE3537F7FE |
| SHA256: | E5F75A9AC20B810FC286E6002E859CE2123C951C3854913D06B9B918057337E6 |
| SSDEEP: | 6:CUlqRD26ALD4XSy9tTh/1bb3G3ftTh/1bb3drVpWppa/yt9c:B+XAhol/1n3Ctl/1n3Pasyk |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2864)
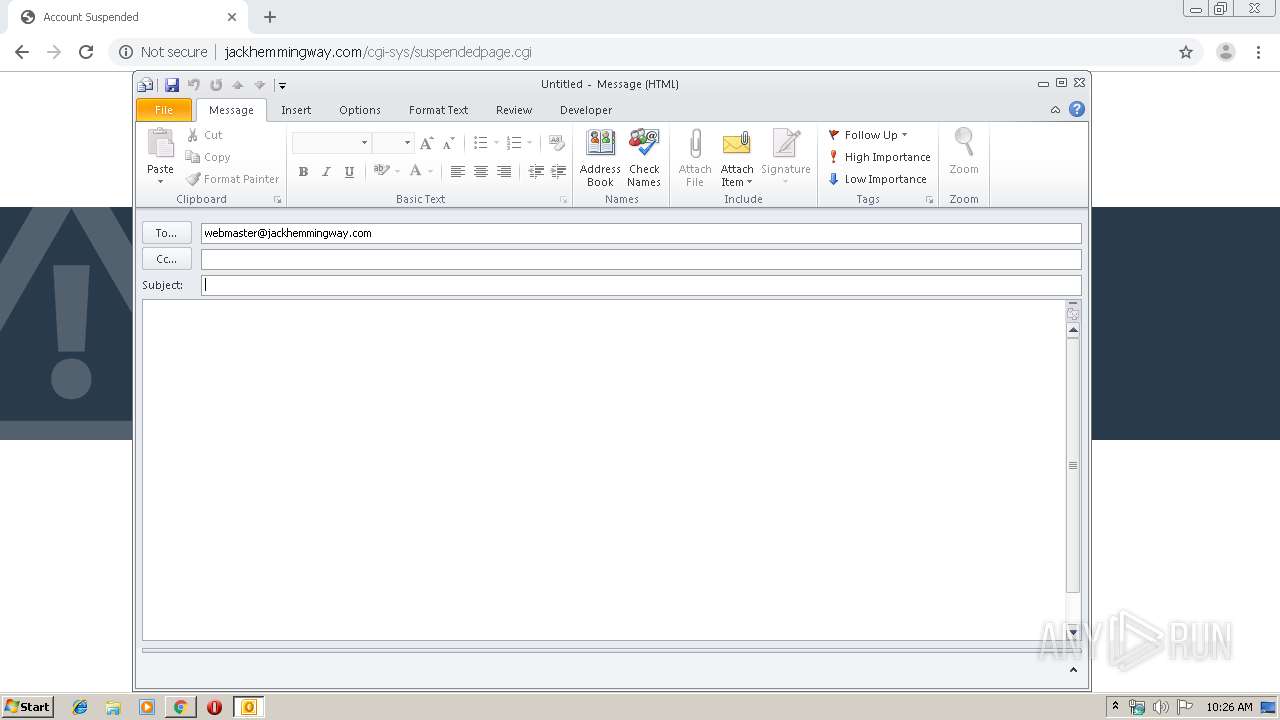
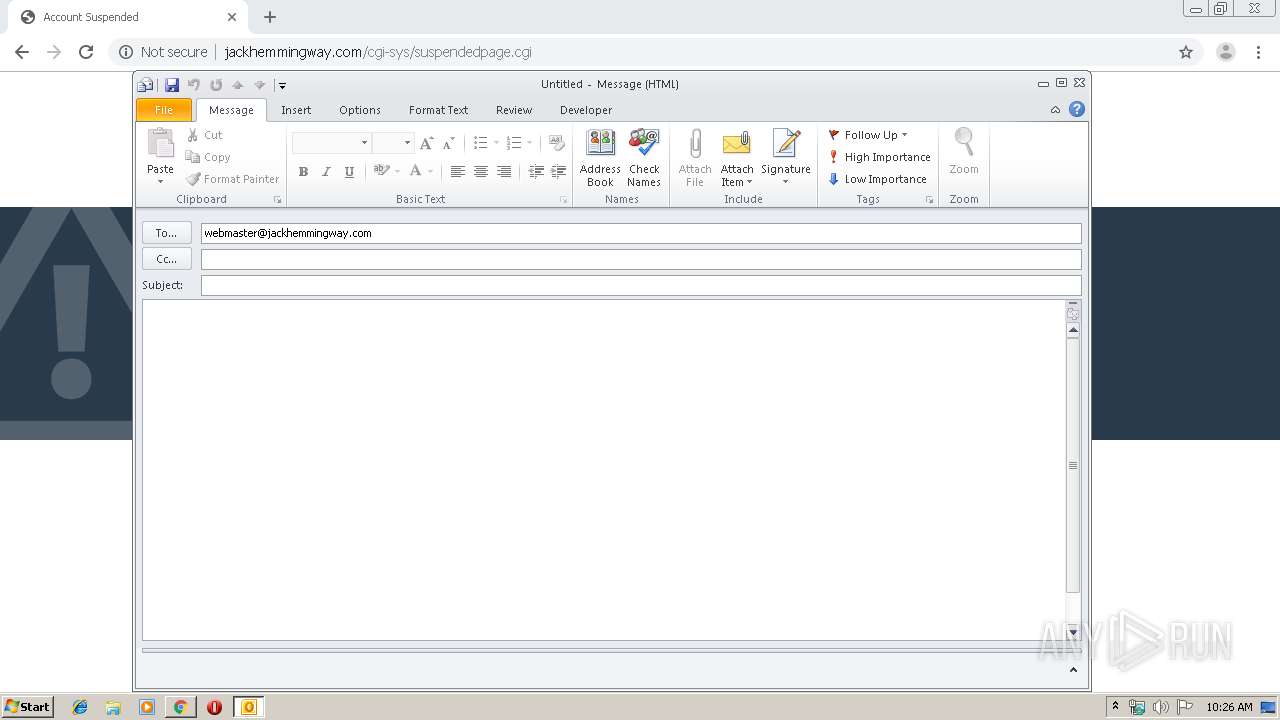
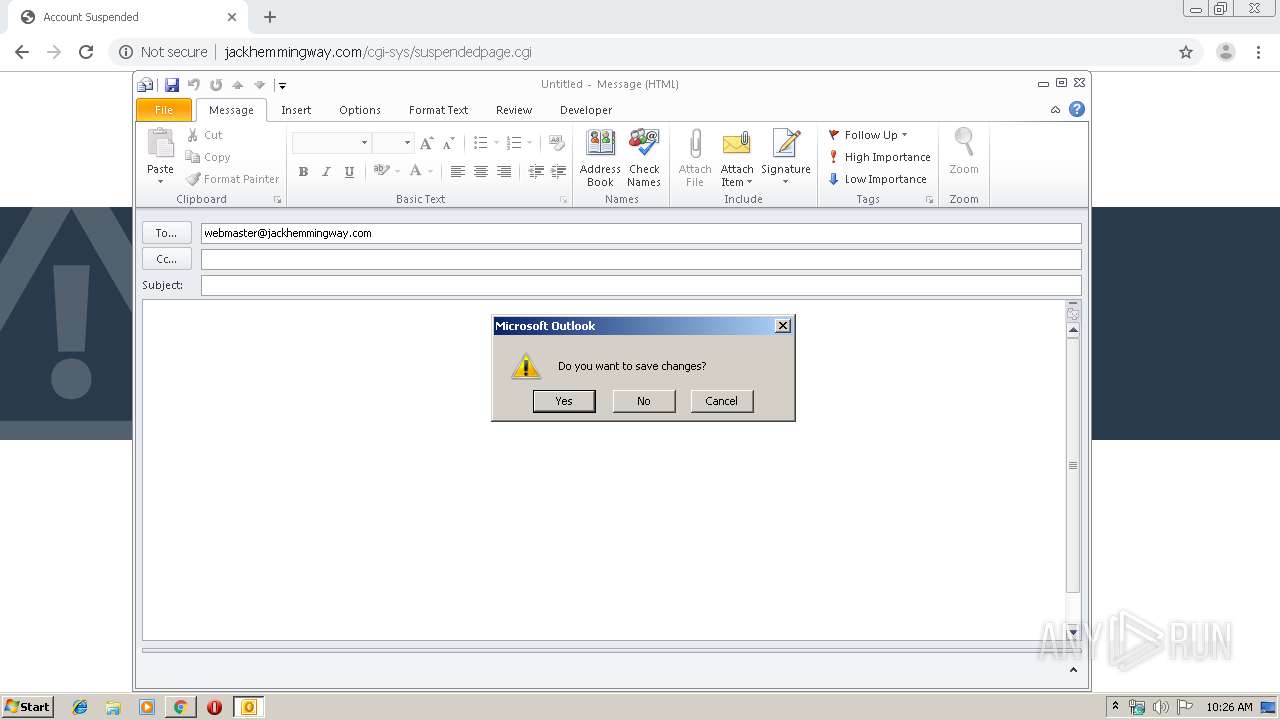
Creates files in the user directory
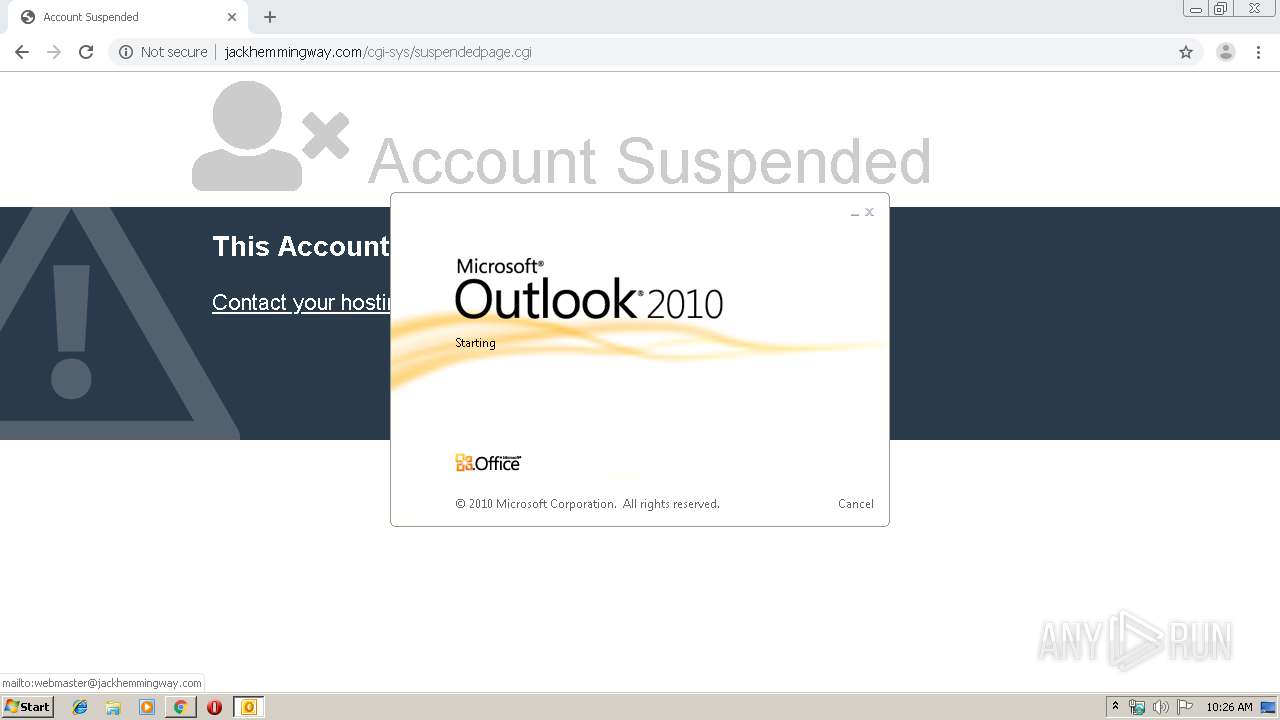
- OUTLOOK.EXE (PID: 3164)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3164)
INFO
Reads the hosts file
- chrome.exe (PID: 2864)
- chrome.exe (PID: 1456)
Application launched itself
- chrome.exe (PID: 2864)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,8591586559856836119,2810093039238291947,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1784443606060418859 --mojo-platform-channel-handle=1528 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,8591586559856836119,2810093039238291947,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16761686896719726882 --mojo-platform-channel-handle=4112 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,8591586559856836119,2810093039238291947,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10722020659601288519 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2964 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,8591586559856836119,2810093039238291947,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5203897353032463441 --mojo-platform-channel-handle=3448 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,8591586559856836119,2810093039238291947,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5013417369760224371 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,8591586559856836119,2810093039238291947,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8824176374964792118 --mojo-platform-channel-handle=3656 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2868 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,8591586559856836119,2810093039238291947,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15331024275174766261 --mojo-platform-channel-handle=3684 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,8591586559856836119,2810093039238291947,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15352340117713324897 --mojo-platform-channel-handle=3652 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://jackhemmingway.com/editonepost.com/gate.php?image_id\=WyJ1cmwlZW1hcnQuY29tLnNhIiwidHlwZSUyIiwiZm9ybV9rZXklZ0pIczd2S3ZPOEpZdjRxbSIsInByb2R1Y3QlNDQ0IiwiZm9ybV9rZXklZ0pIczd2S3ZPOEpZdjRxbSIsInJhdGluZ3NbM10lMTEiLCJyYXRpbmdzWzNdJTEyIiwicmF0aW5nc1szXSUxMyI" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 803
Read events
1 308
Write events
469
Delete events
26
Modification events
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2712) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2864-13213358770553125 |
Value: 259 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2864) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
7
Text files
234
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7b66ca01-1eef-4556-b4ab-5cb5c4f8870b.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF168d41.TMP | text | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF168d41.TMP | text | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF168d41.TMP | text | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF168d7f.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
17
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1456 | chrome.exe | GET | 403 | 107.180.4.169:80 | http://jackhemmingway.com/editonepost.com/gate.php?image_id\=WyJ1cmwlZW1hcnQuY29tLnNhIiwidHlwZSUyIiwiZm9ybV9rZXklZ0pIczd2S3ZPOEpZdjRxbSIsInByb2R1Y3QlNDQ0IiwiZm9ybV9rZXklZ0pIczd2S3ZPOEpZdjRxbSIsInJhdGluZ3NbM10lMTEiLCJyYXRpbmdzWzNdJTEyIiwicmF0aW5nc1szXSUxMyI | US | html | 352 b | malicious |
1456 | chrome.exe | GET | — | 23.111.9.35:80 | http://use.fontawesome.com/releases/v5.0.6/webfonts/fa-solid-900.woff2 | US | — | — | whitelisted |
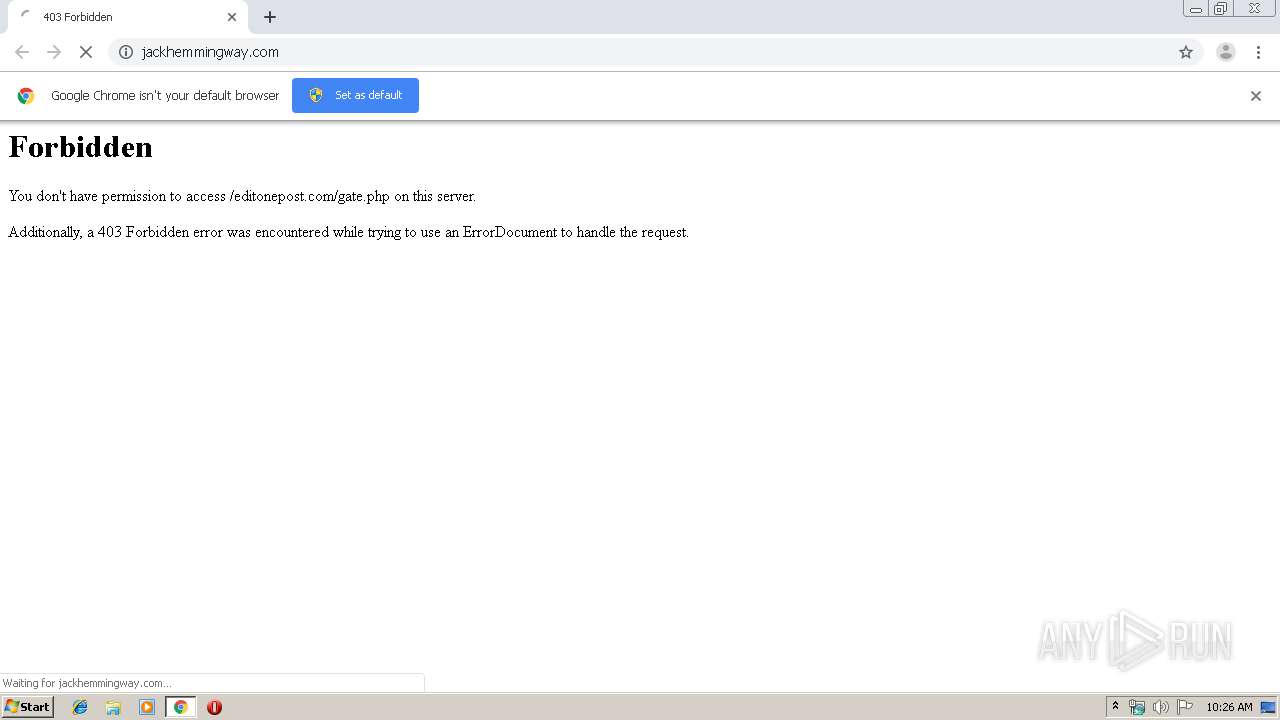
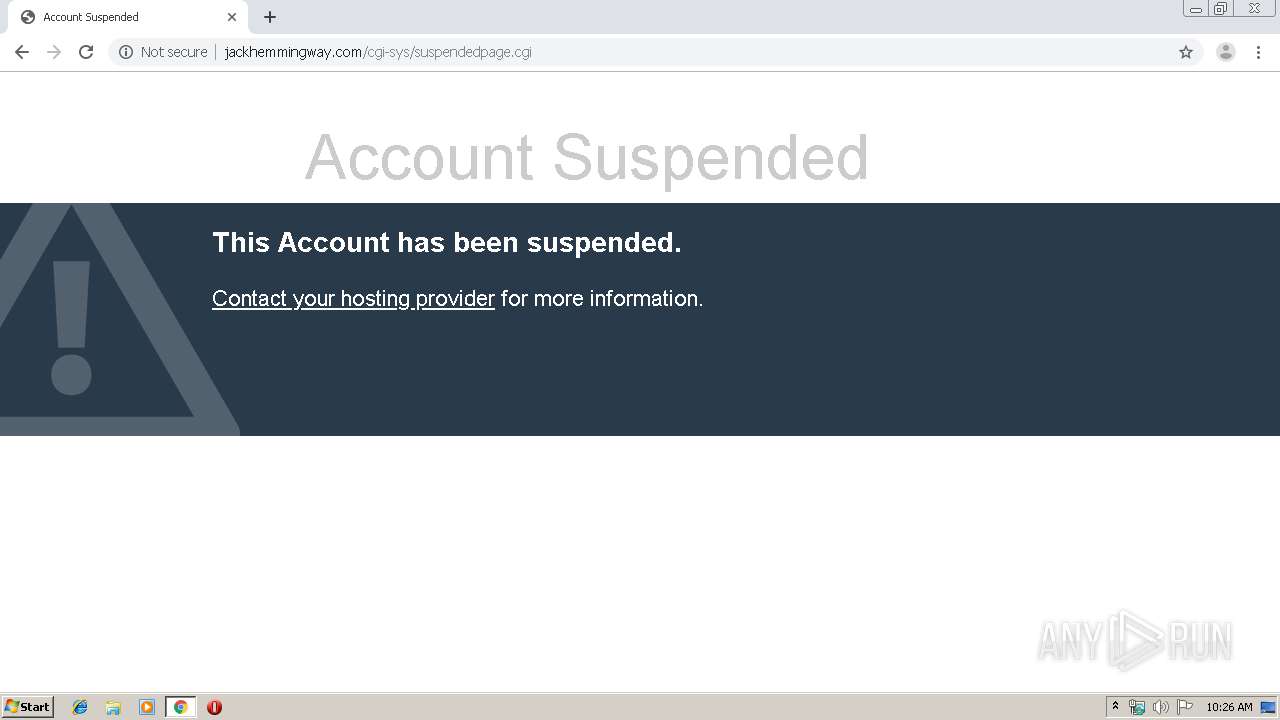
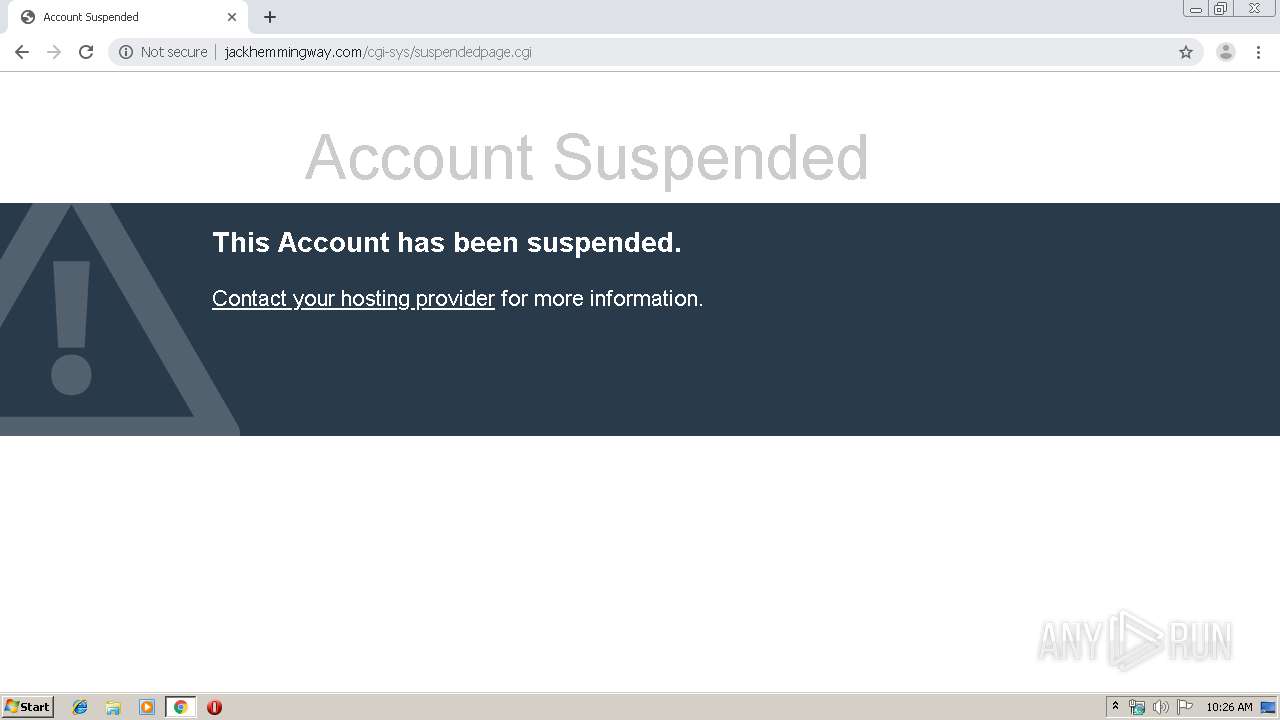
1456 | chrome.exe | GET | 200 | 107.180.4.169:80 | http://jackhemmingway.com/cgi-sys/suspendedpage.cgi | US | html | 4.01 Kb | malicious |
1456 | chrome.exe | GET | 200 | 107.180.4.169:80 | http://jackhemmingway.com/cgi-sys/suspendedpage.cgi | US | html | 4.01 Kb | malicious |
1456 | chrome.exe | GET | 302 | 107.180.4.169:80 | http://jackhemmingway.com/favicon.ico | US | html | 235 b | malicious |
1456 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3164 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1456 | chrome.exe | GET | 200 | 107.180.4.169:80 | http://jackhemmingway.com/cgi-sys/suspendedpage.cgi | US | html | 4.01 Kb | malicious |
1456 | chrome.exe | GET | 200 | 172.217.133.135:80 | http://r2---sn-hpa7znsd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.128.27.133&mm=28&mn=sn-hpa7znsd&ms=nvh&mt=1568885061&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
1456 | chrome.exe | GET | 302 | 107.180.4.169:80 | http://jackhemmingway.com/favicon.ico | US | html | 235 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1456 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1456 | chrome.exe | 107.180.4.169:80 | jackhemmingway.com | GoDaddy.com, LLC | US | malicious |
1456 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1456 | chrome.exe | 216.58.206.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
1456 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
1456 | chrome.exe | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1456 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1456 | chrome.exe | 172.217.22.35:443 | www.google.it | Google Inc. | US | whitelisted |
3164 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1456 | chrome.exe | 172.217.133.135:80 | r2---sn-hpa7znsd.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
jackhemmingway.com |
| malicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-hpa7znsd.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.it |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1456 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Volexity - JS Sniffer Data Theft Beacon Detected |