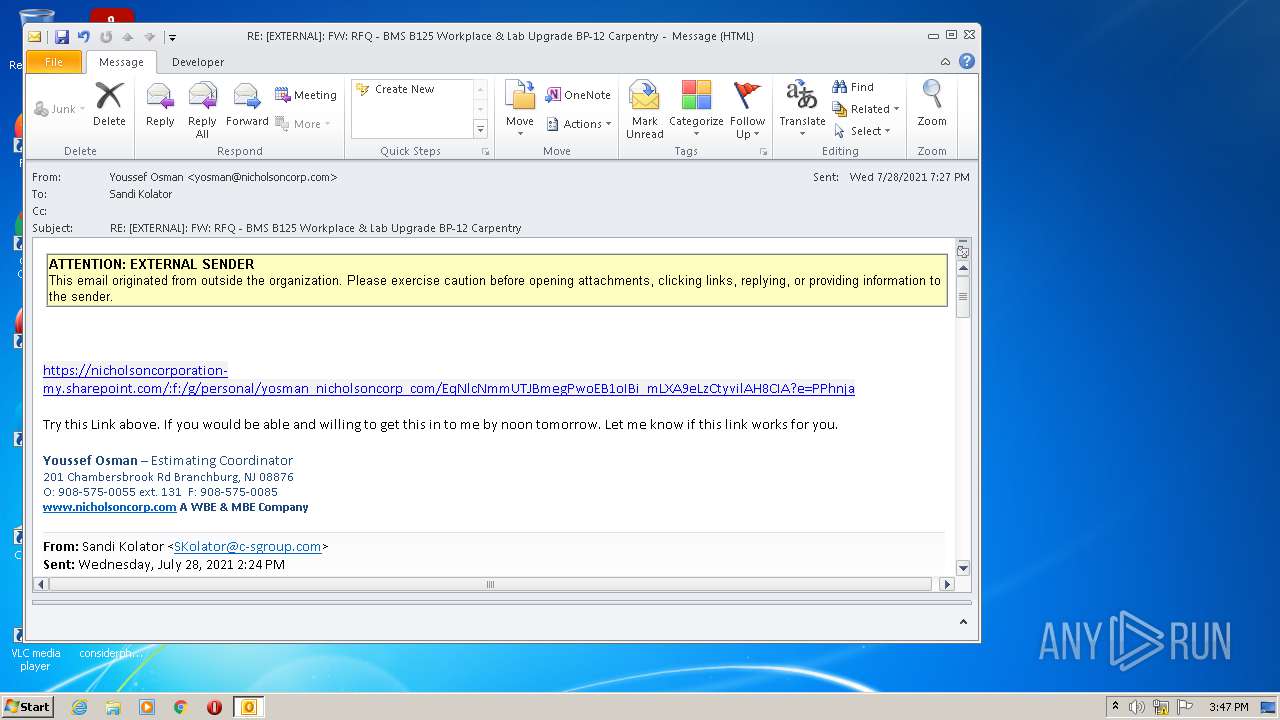
| File name: | noname (3).eml |
| Full analysis: | https://app.any.run/tasks/07205f17-6ff5-410c-b449-6d9baa5a7ce8 |
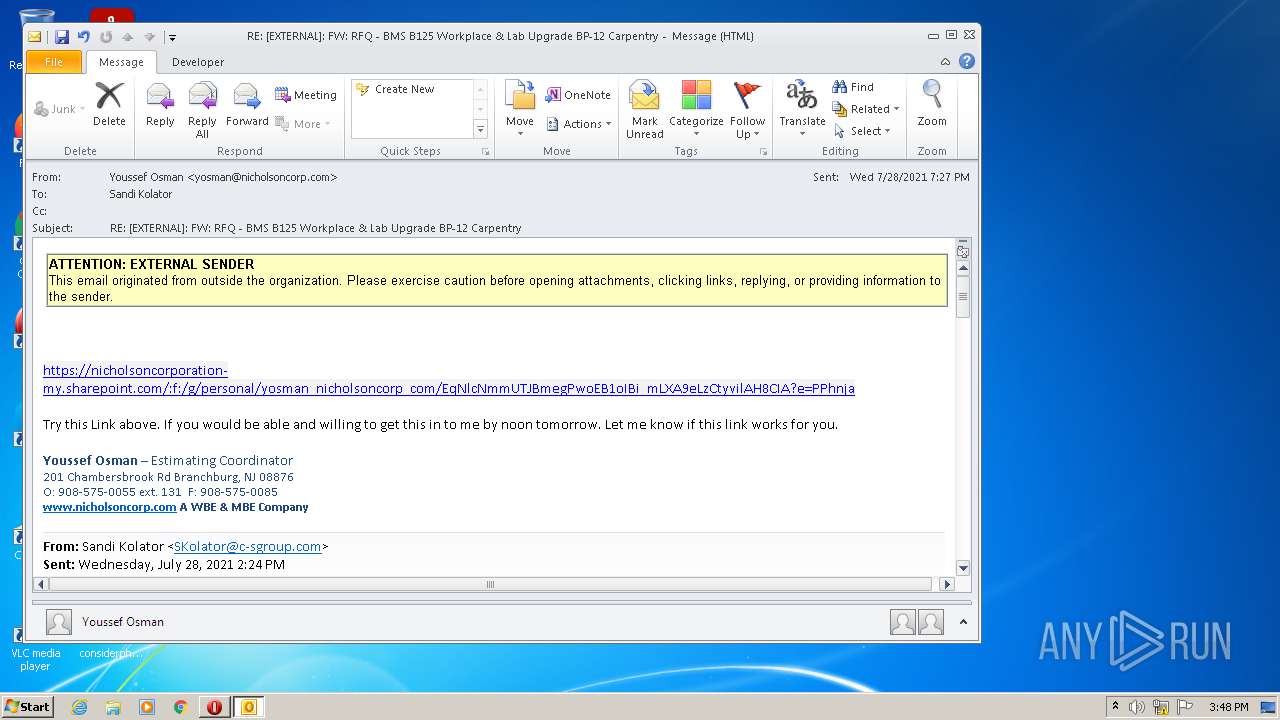
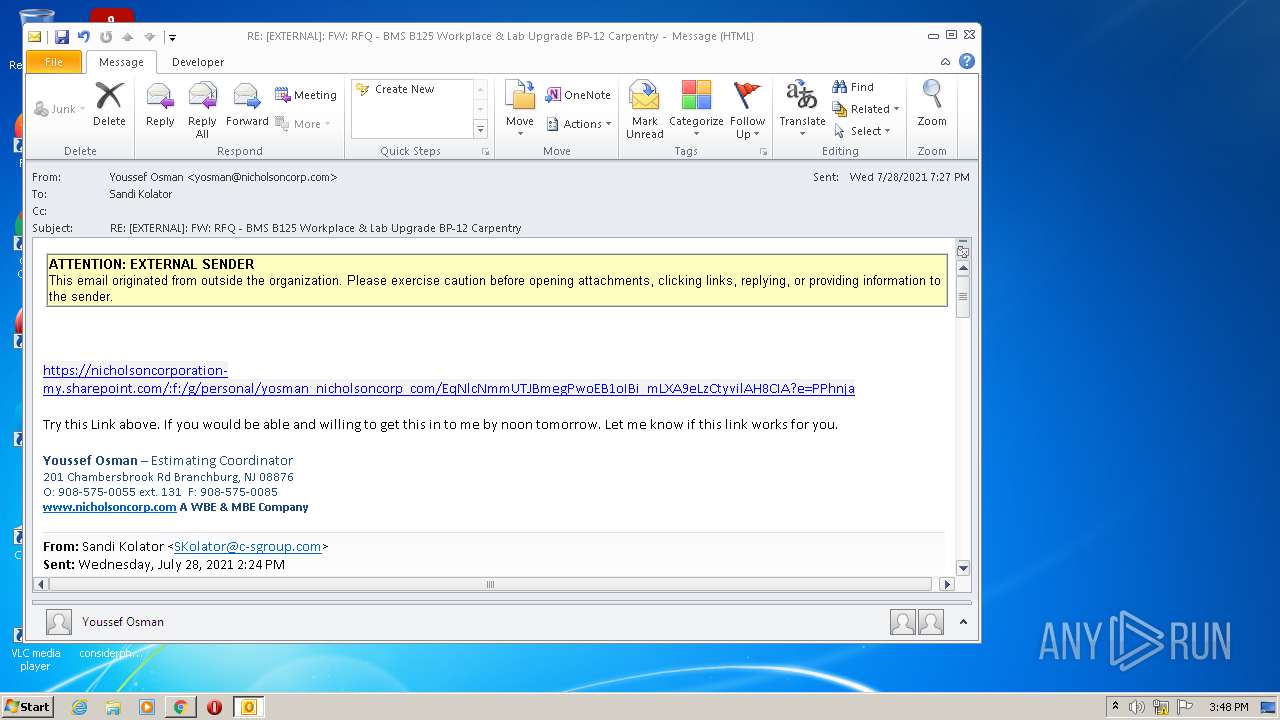
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2021, 14:47:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 162201B0C04A63D4FB47D807BA301B94 |
| SHA1: | 0B58DCD6CDFAA2F009AC54BDCAA982A4A4E6E670 |
| SHA256: | E5EAD8DC2A90EBE693F9EDA2BAEE45A88405A2B86CF7623C0D6C269D15A927DC |
| SSDEEP: | 1536:Tfwf7u5FjkDi+Yv3gE1X0531tQSZ/MnPmsU1AO9nsE2F:Dwf7u5pOjYffi3wSZ/MnuB1tGE2F |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 1880)
SUSPICIOUS
Checks supported languages
- OUTLOOK.EXE (PID: 1876)
Reads the computer name
- OUTLOOK.EXE (PID: 1876)
Searches for installed software
- OUTLOOK.EXE (PID: 1876)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1876)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3044)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1876)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1328)
Executable content was dropped or overwritten
- chrome.exe (PID: 1880)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 1880)
INFO
Checks supported languages
- iexplore.exe (PID: 188)
- iexplore.exe (PID: 3044)
- chrome.exe (PID: 1328)
- chrome.exe (PID: 660)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 896)
- chrome.exe (PID: 2460)
- chrome.exe (PID: 1860)
- chrome.exe (PID: 1584)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 2264)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 2704)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 2000)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 3376)
- chrome.exe (PID: 2548)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 1676)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 1108)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 1956)
- chrome.exe (PID: 4060)
- chrome.exe (PID: 3964)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3344)
- chrome.exe (PID: 2876)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 1880)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 532)
- chrome.exe (PID: 3716)
Reads the computer name
- iexplore.exe (PID: 188)
- iexplore.exe (PID: 3044)
- chrome.exe (PID: 1328)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 2460)
- chrome.exe (PID: 2704)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 3376)
- chrome.exe (PID: 2548)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 1584)
Checks Windows Trust Settings
- iexplore.exe (PID: 188)
- iexplore.exe (PID: 3044)
Reads internet explorer settings
- iexplore.exe (PID: 3044)
Reads settings of System Certificates
- iexplore.exe (PID: 188)
- iexplore.exe (PID: 3044)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 3940)
Changes internet zones settings
- iexplore.exe (PID: 188)
Manual execution by user
- chrome.exe (PID: 1328)
- chrome.exe (PID: 3940)
Application launched itself
- iexplore.exe (PID: 188)
- chrome.exe (PID: 1328)
- chrome.exe (PID: 3940)
Reads the date of Windows installation
- iexplore.exe (PID: 188)
- chrome.exe (PID: 2548)
- chrome.exe (PID: 3756)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1876)
Reads the hosts file
- chrome.exe (PID: 3132)
- chrome.exe (PID: 1328)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 3940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
84
Monitored processes
45
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
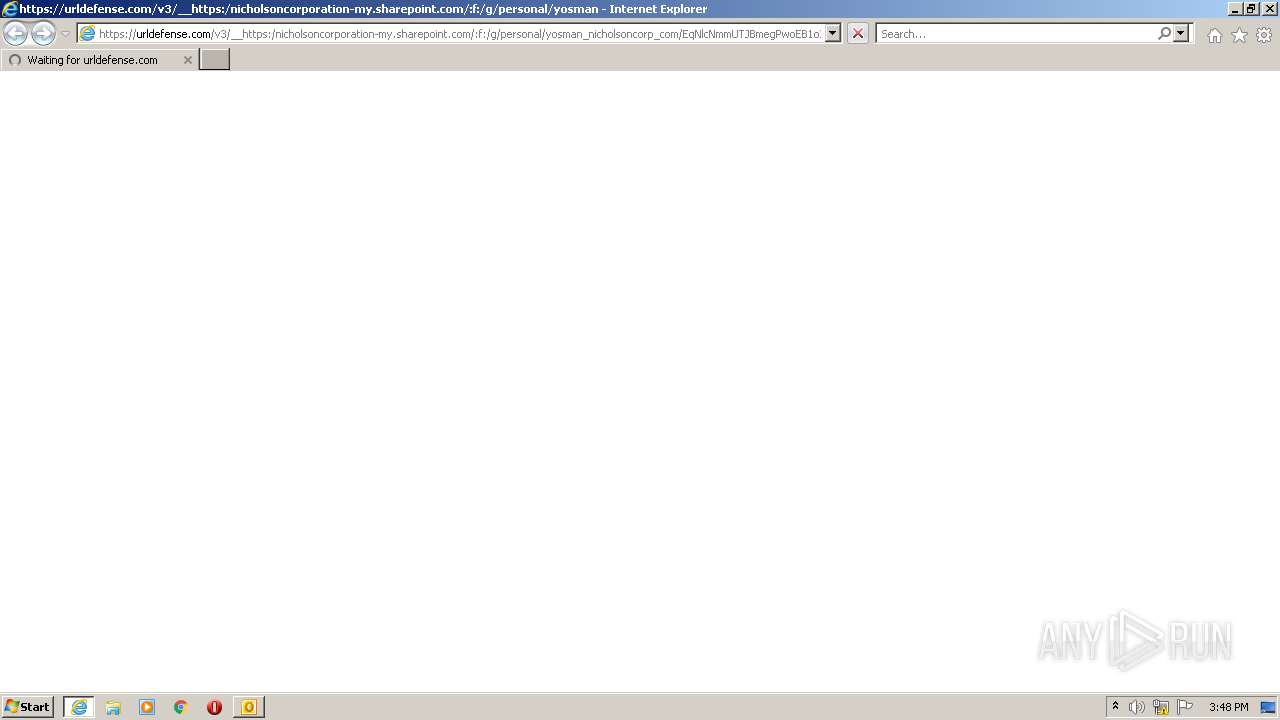
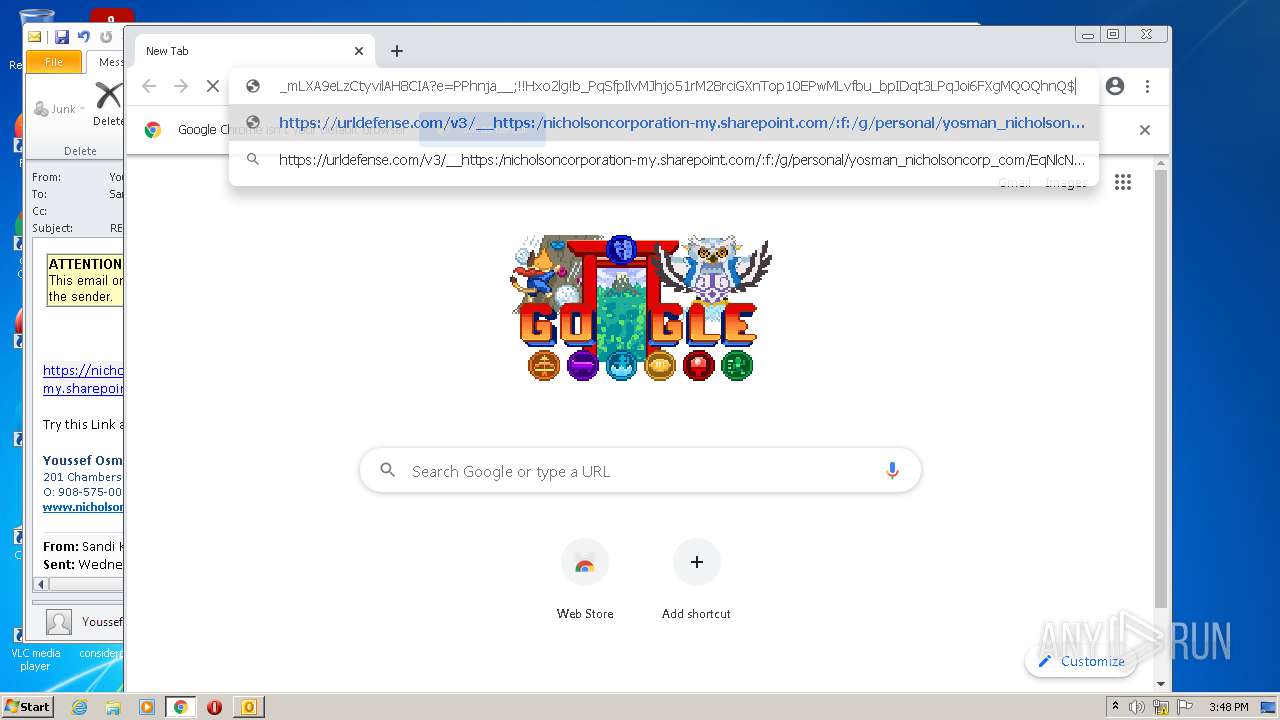
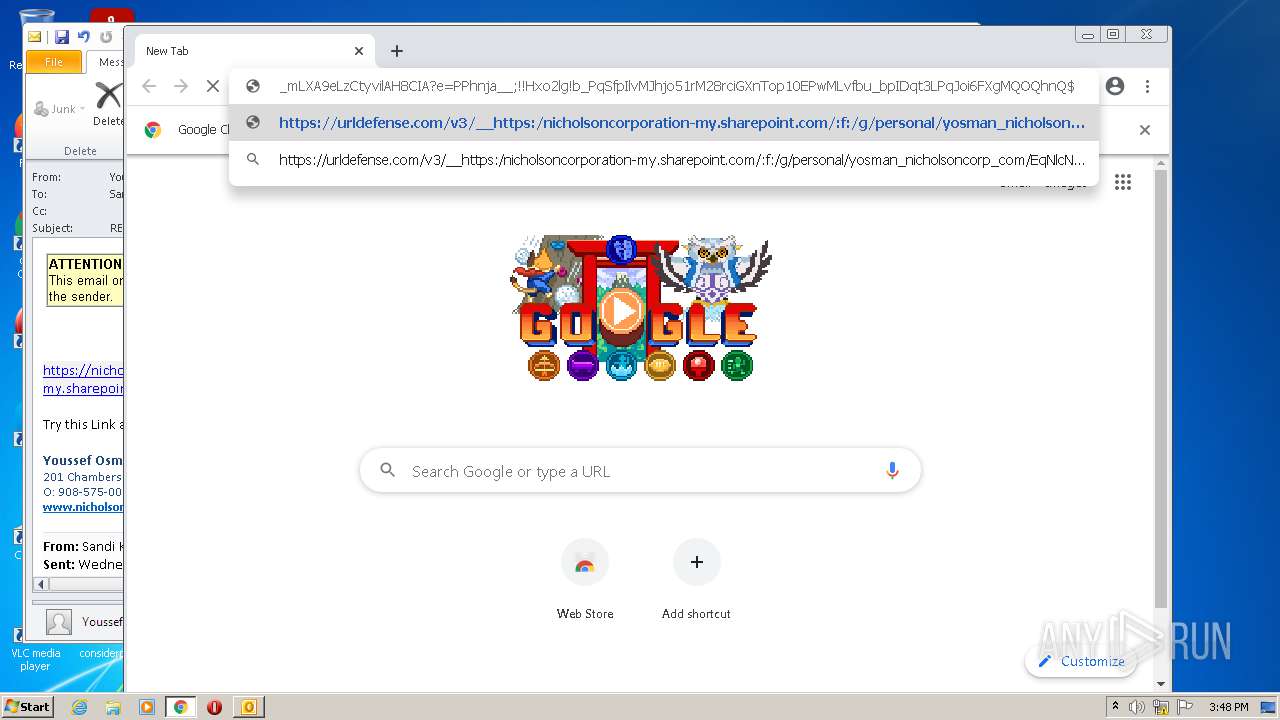
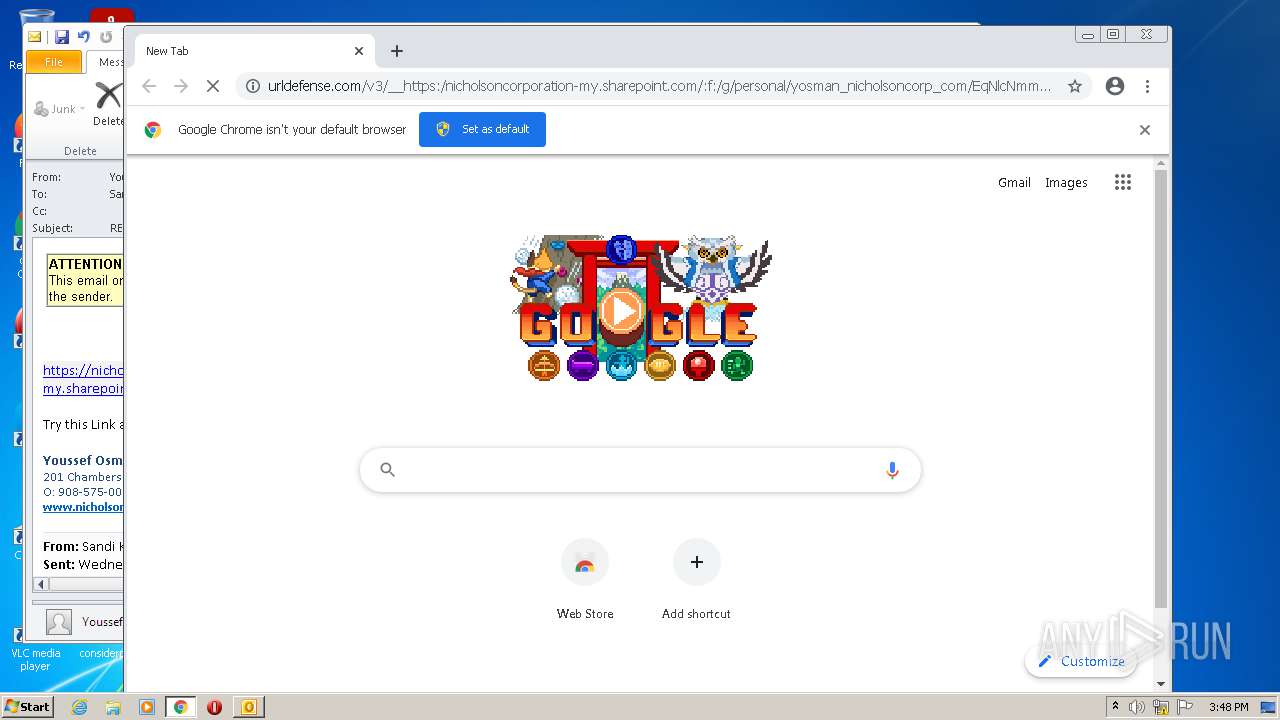
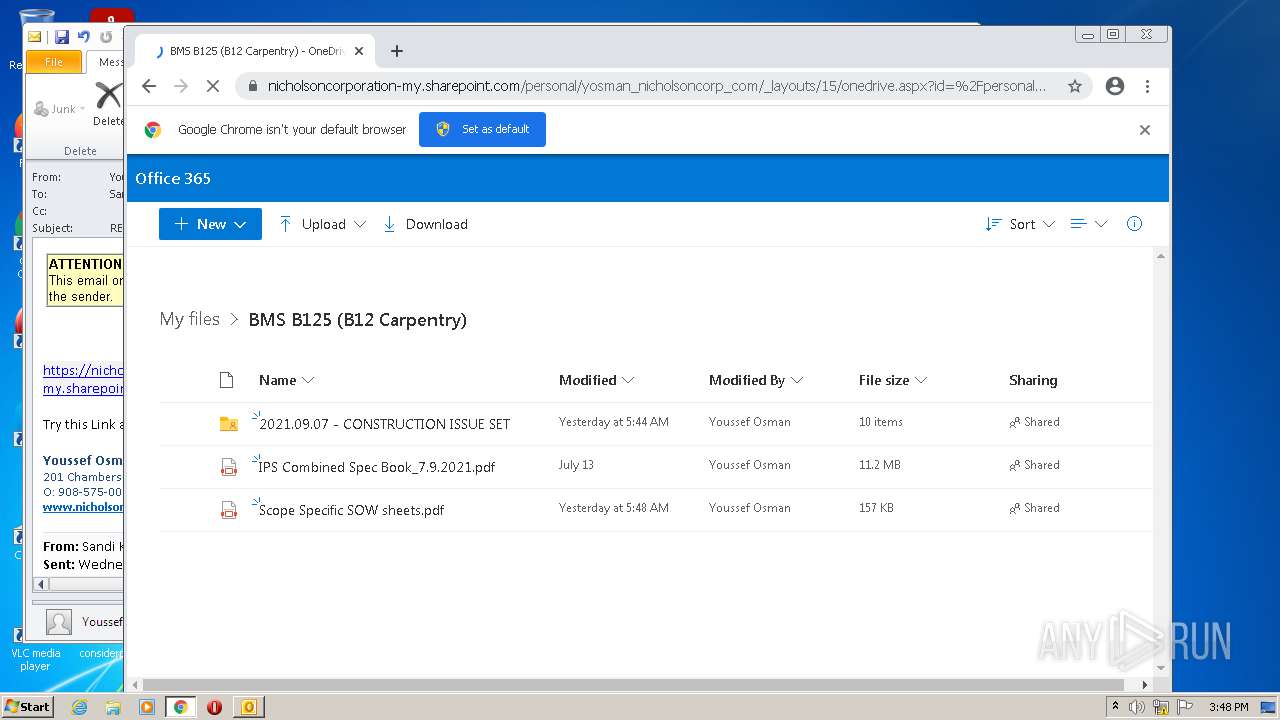
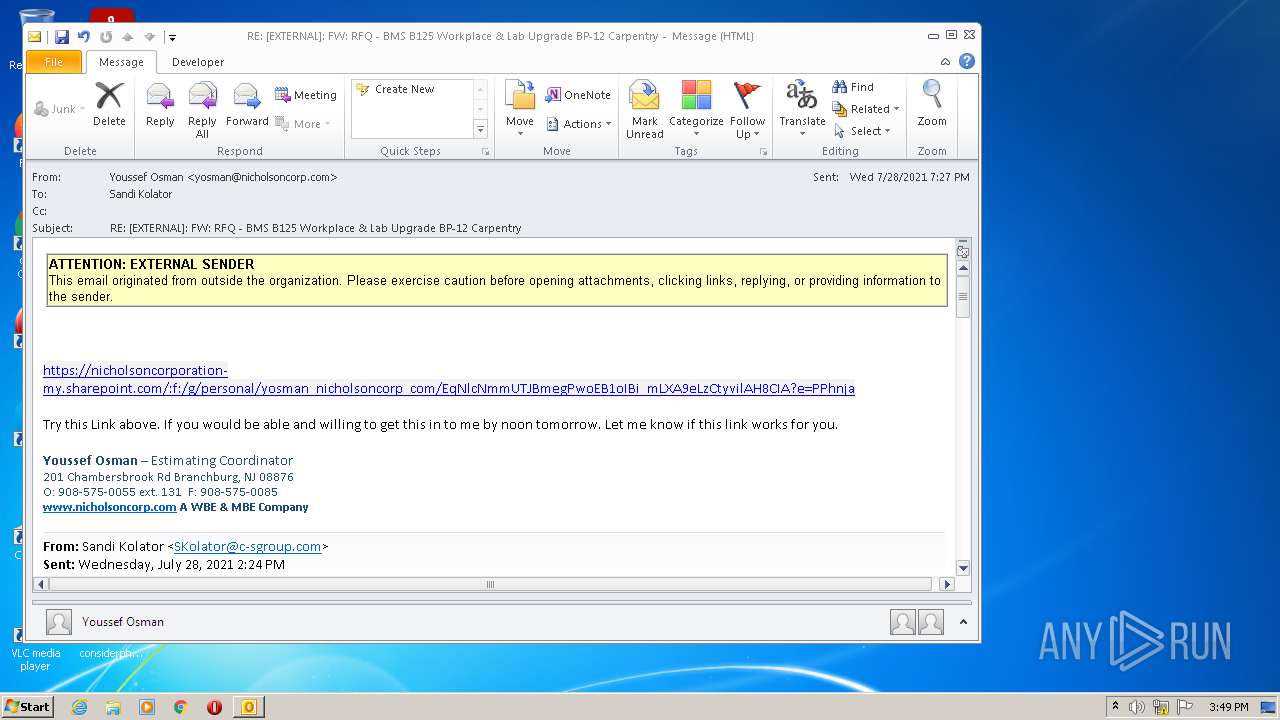
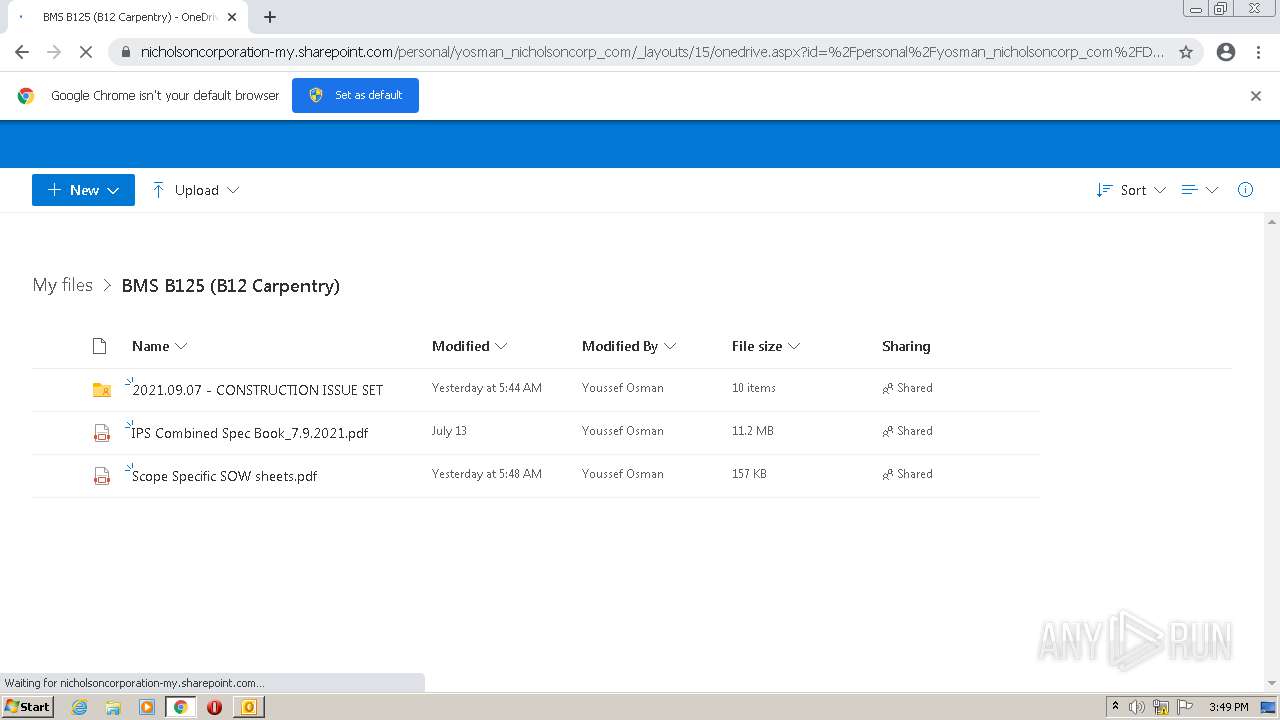
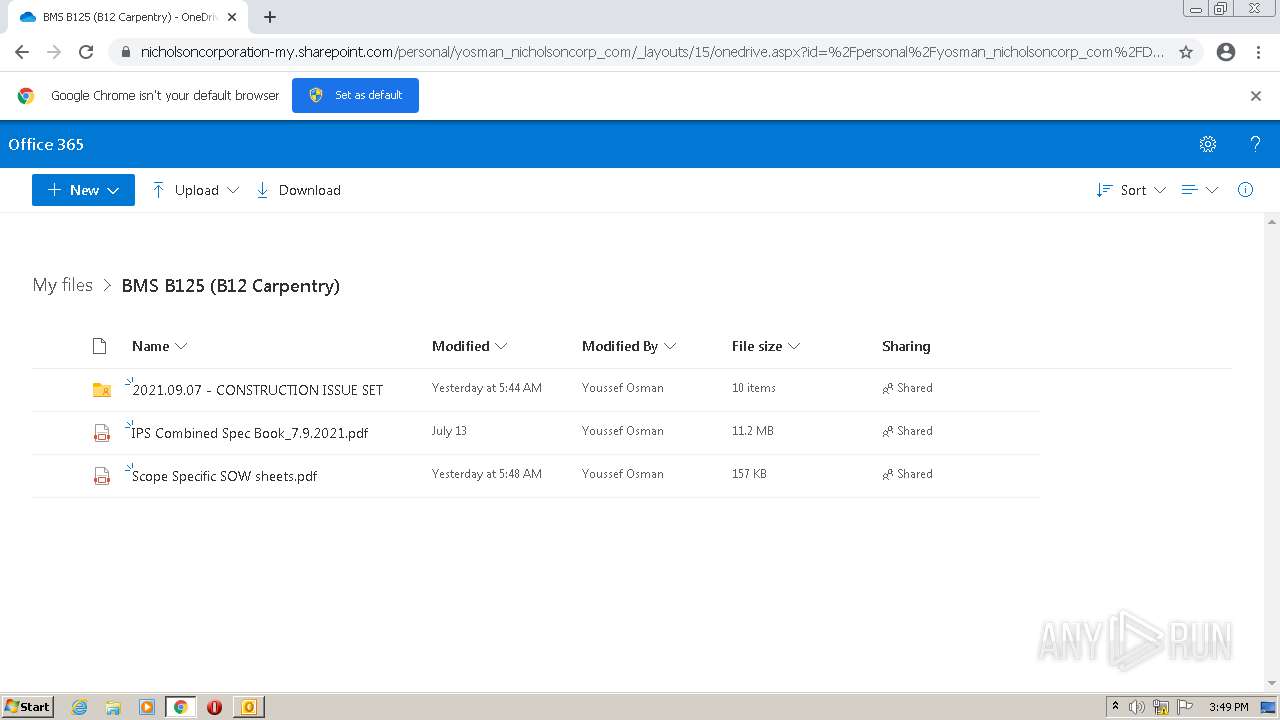
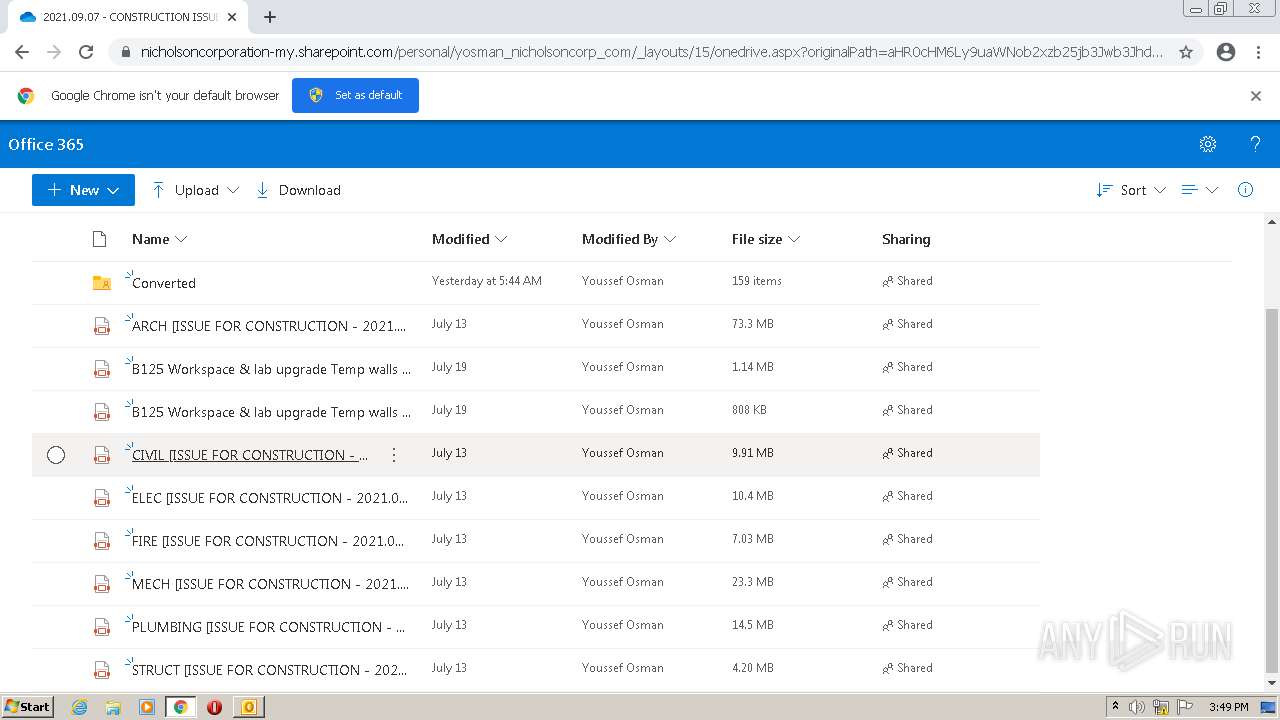
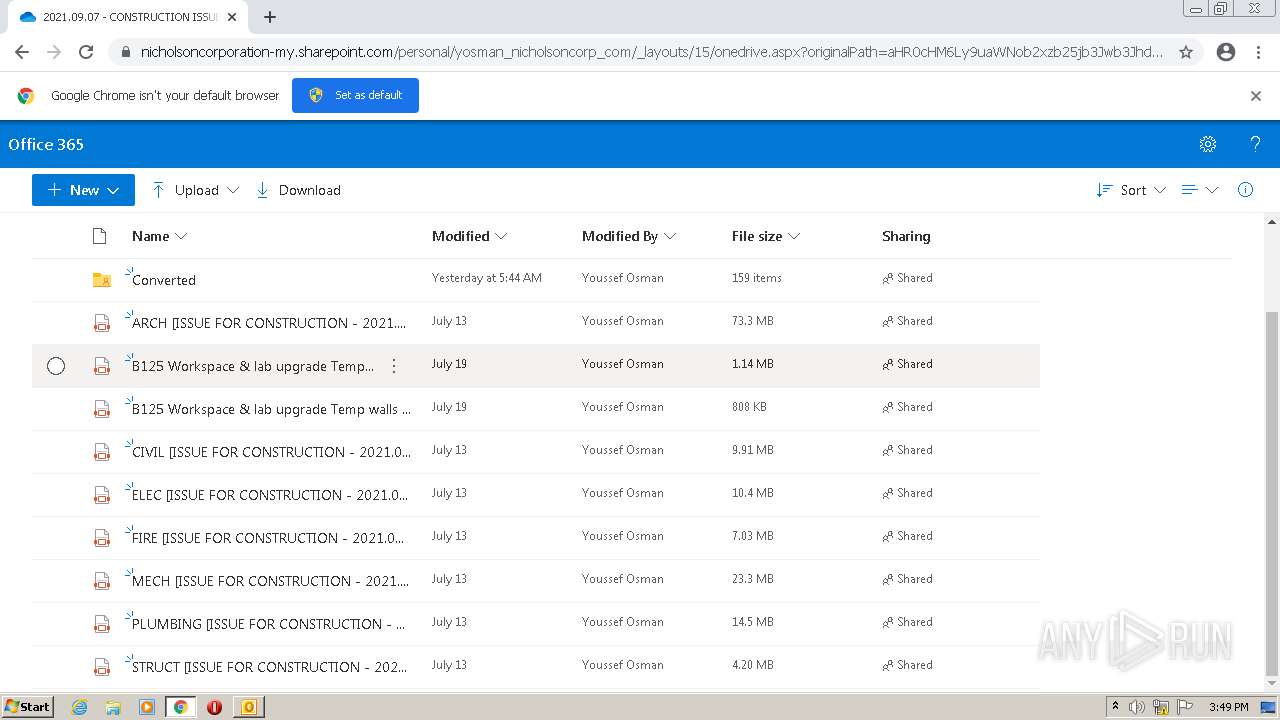
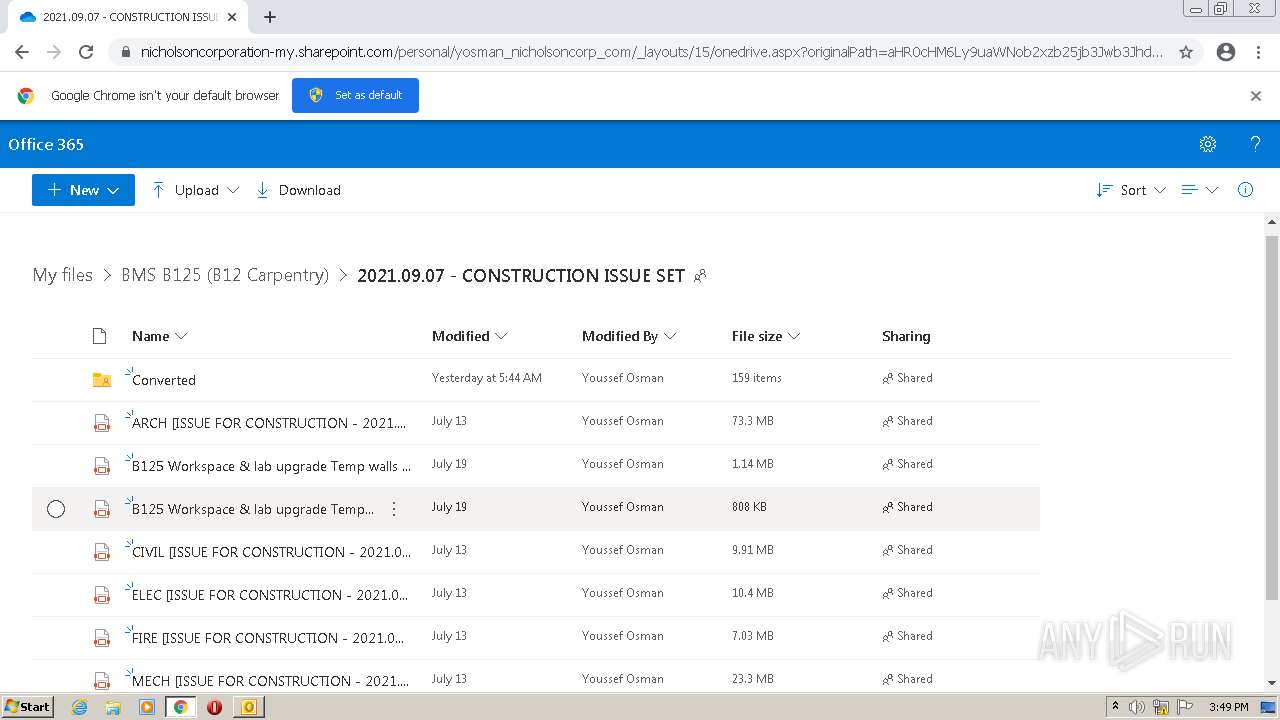
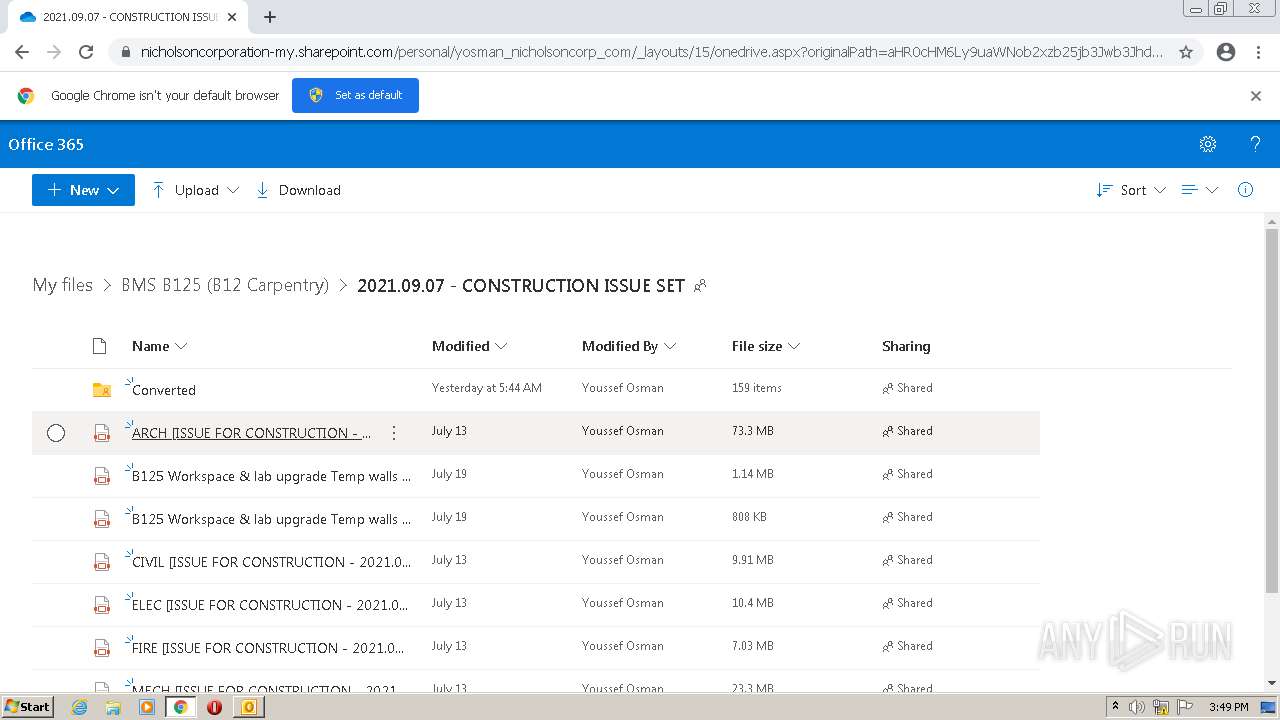
| 188 | "C:\Program Files\Internet Explorer\iexplore.exe" https://urldefense.com/v3/__https:/nicholsoncorporation-my.sharepoint.com/:f:/g/personal/yosman_nicholsoncorp_com/EqNlcNmmUTJBmegPwoEB1oIBi_mLXA9eLzCtyvilAH8CIA?e=PPhnja__;!!Hxo2lg!b_PqSfpIlvMJhjo51rM28rciGXnTop10EPwMLvfbu_bpIDqt3LPqJoi6FXgMQOQhnQ$ | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,14345498743663525396,1420903435215108860,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=952 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x61e1d988,0x61e1d998,0x61e1d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,6015014089394288221,8362682440571930424,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,14345498743663525396,1420903435215108860,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1064,6015014089394288221,8362682440571930424,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1080 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x61eed988,0x61eed998,0x61eed9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,6015014089394288221,8362682440571930424,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1876 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\noname (3).eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
42 026
Read events
41 153
Write events
844
Delete events
29
Modification events
| (PID) Process: | (1876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1876) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
1
Suspicious files
202
Text files
386
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR3315.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1876 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 1876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4E4DA970.dat | image | |
MD5:— | SHA256:— | |||
| 1876 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1876 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\77643AB1.dat | image | |
MD5:— | SHA256:— | |||
| 3044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\72BA427A91F50409B9EAC87F2B59B951_14541052F51AB35E7EEB1FA45936A529 | binary | |
MD5:— | SHA256:— | |||
| 3044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\69C6F6EC64E114822DF688DC12CDD86C | der | |
MD5:— | SHA256:— | |||
| 3044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
134
DNS requests
61
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1876 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
— | — | HEAD | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | — | — | whitelisted |
— | — | HEAD | 200 | 74.125.8.74:80 | http://r5---sn-5hneknee.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=1M&mip=45.92.228.8&mm=28&mn=sn-5hneknee&ms=nvh&mt=1627569253&mv=u&mvi=5&pl=24&shardbypass=yes&smhost=r5---sn-5hnekn76.gvt1.com | US | — | — | whitelisted |
188 | iexplore.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | — | — | whitelisted |
— | — | GET | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 558 b | whitelisted |
3044 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 727 b | whitelisted |
3044 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEQCggUQ1i8HsVWj6t3pjeTok | US | der | 472 b | whitelisted |
— | — | GET | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | html | 558 b | whitelisted |
— | — | GET | 206 | 74.125.8.74:80 | http://r5---sn-5hneknee.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=1M&mip=45.92.228.8&mm=28&mn=sn-5hneknee&ms=nvh&mt=1627569991&mv=u&mvi=5&pl=24&shardbypass=yes&smhost=r5---sn-5hnekn76.gvt1.com | US | binary | 9.52 Kb | whitelisted |
— | — | GET | 206 | 74.125.8.74:80 | http://r5---sn-5hneknee.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=1M&mip=45.92.228.8&mm=28&mn=sn-5hneknee&ms=nvh&mt=1627569253&mv=u&mvi=5&pl=24&shardbypass=yes&smhost=r5---sn-5hnekn76.gvt1.com | US | binary | 5.67 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1876 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3044 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
3044 | iexplore.exe | 2.16.186.33:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
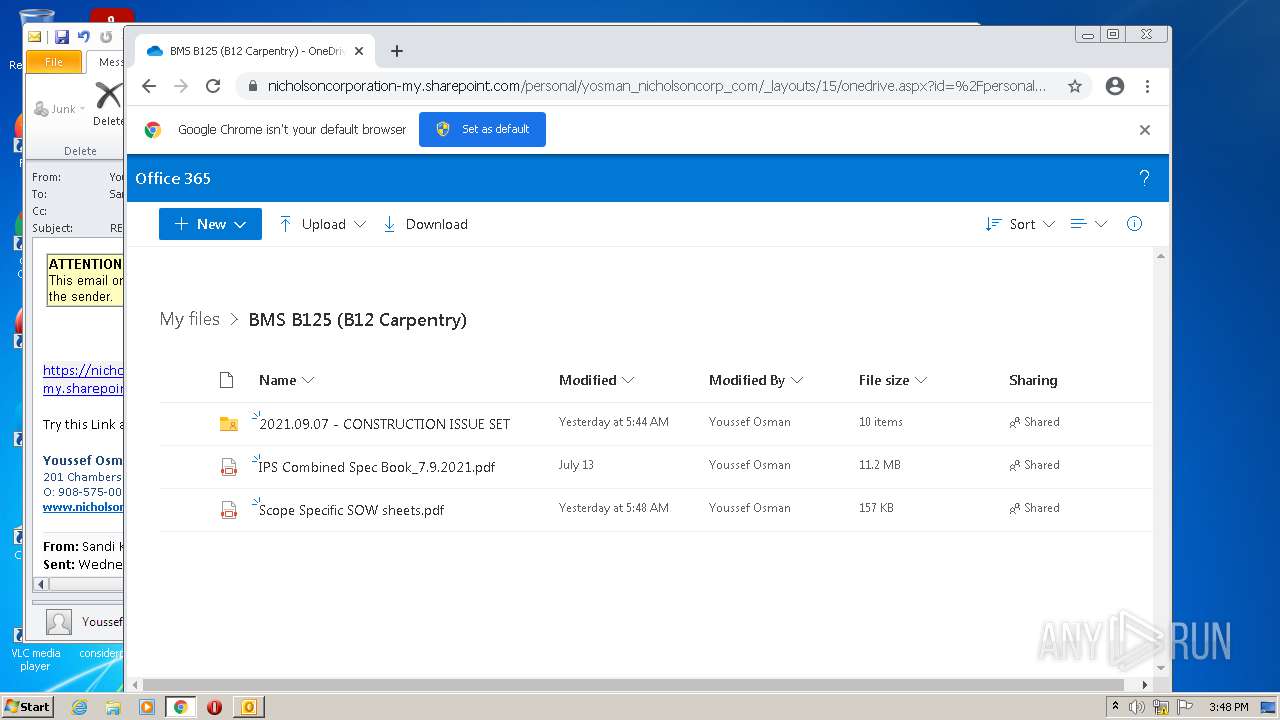
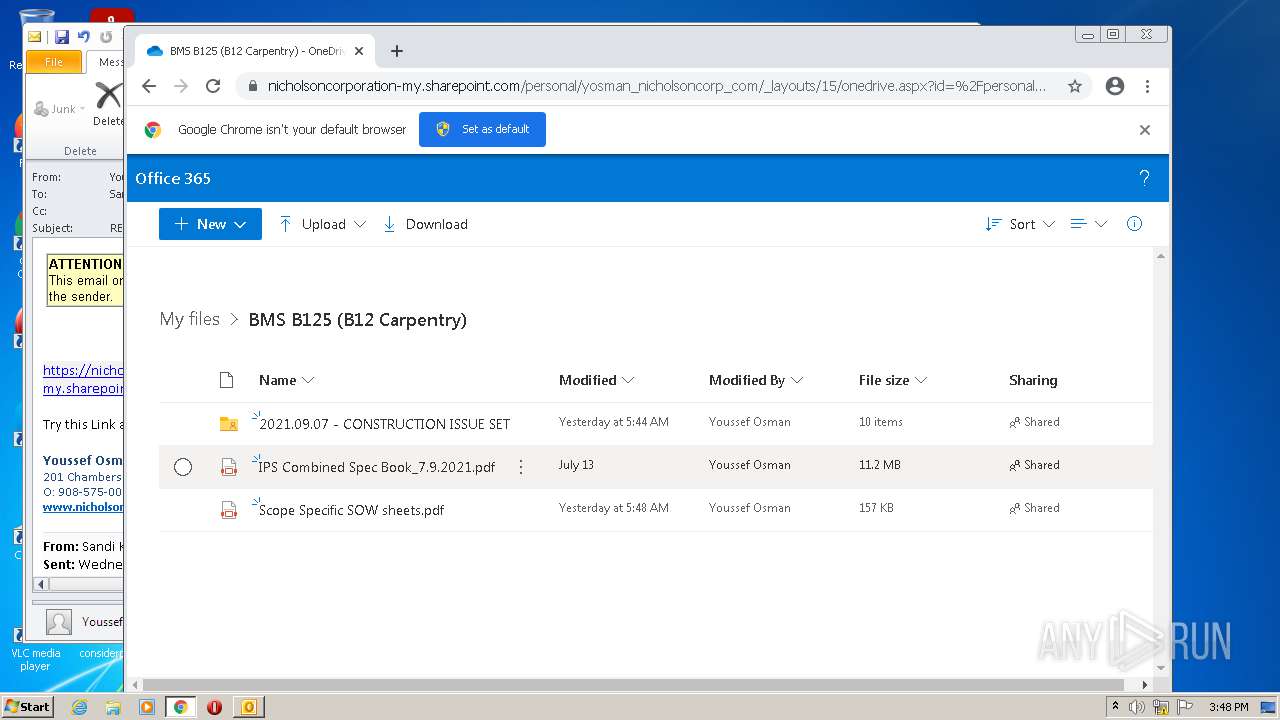
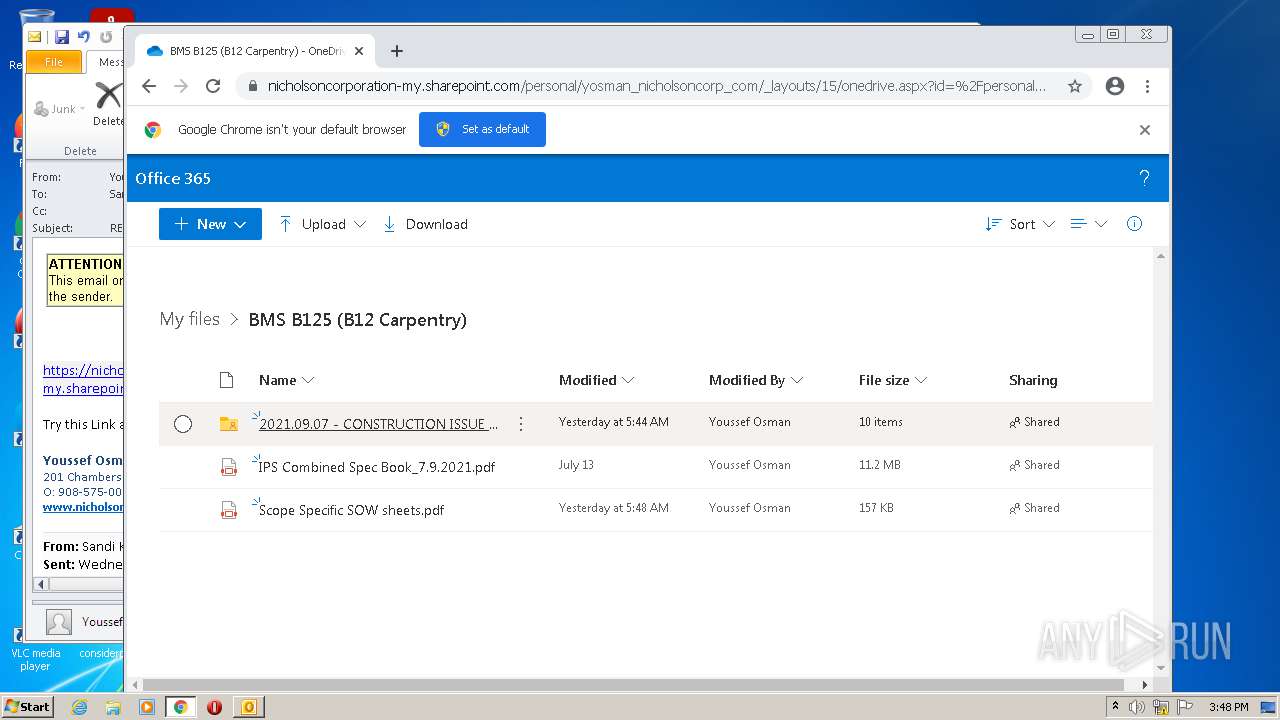
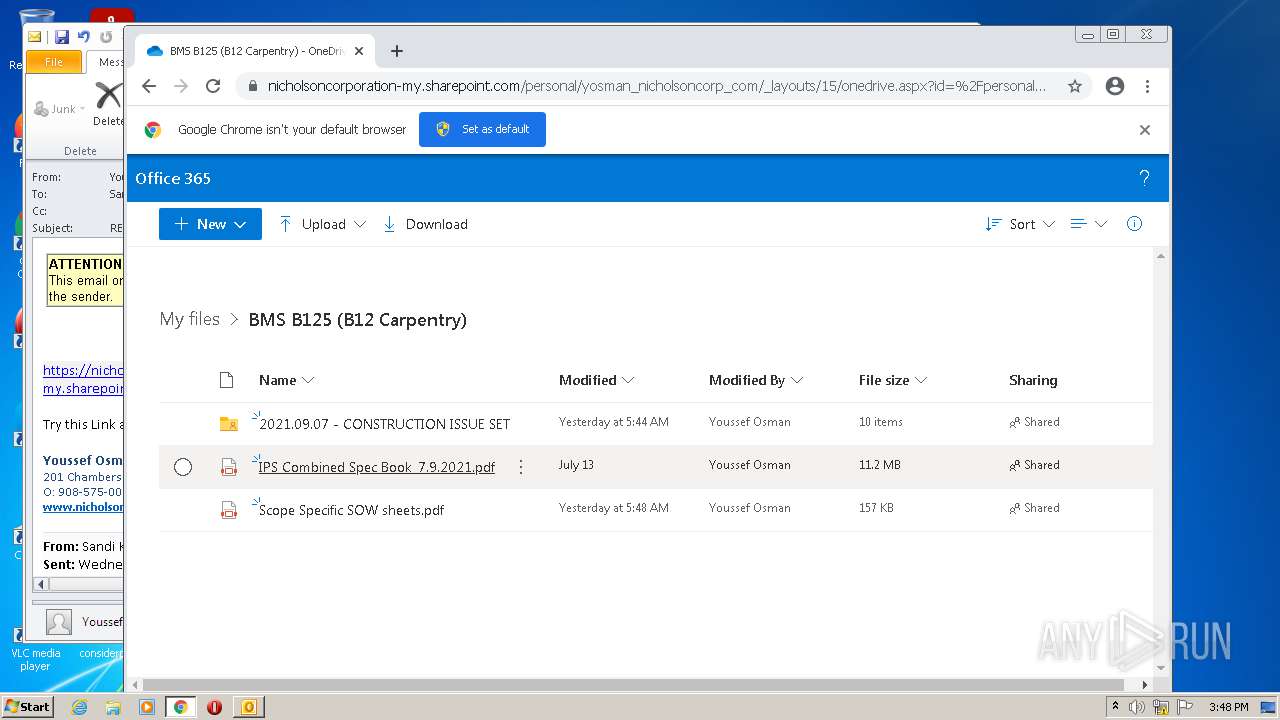
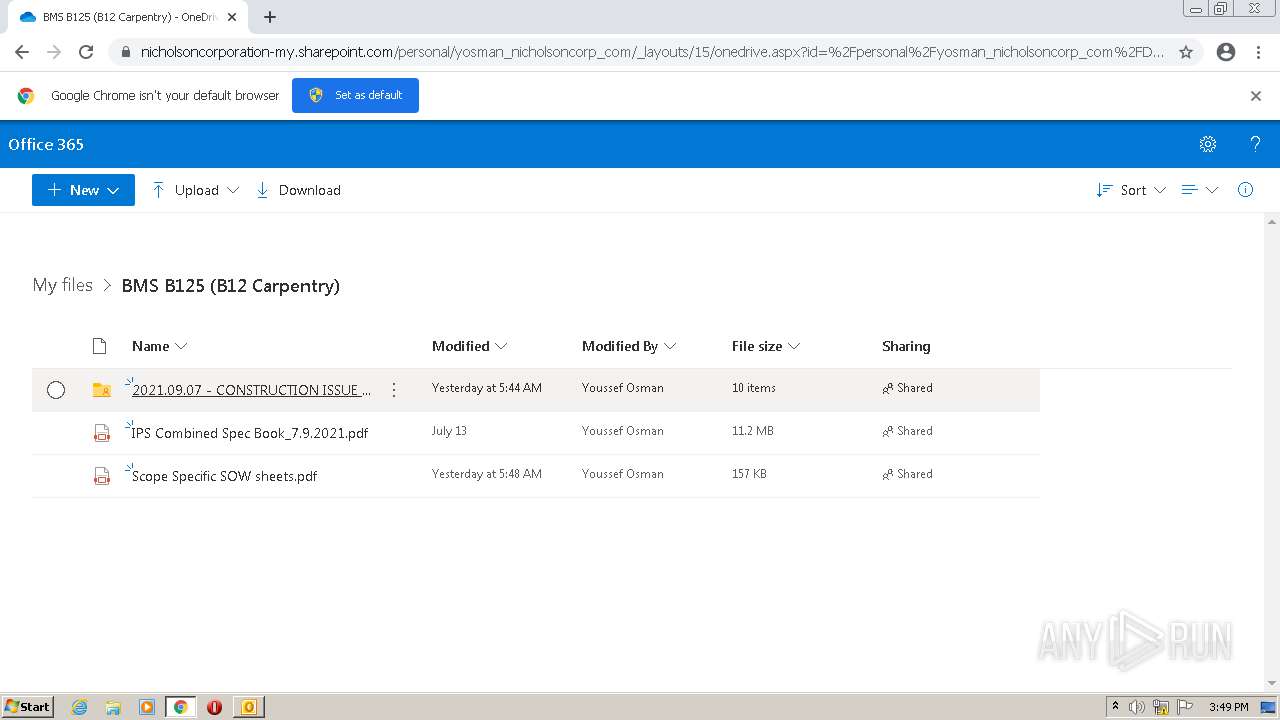
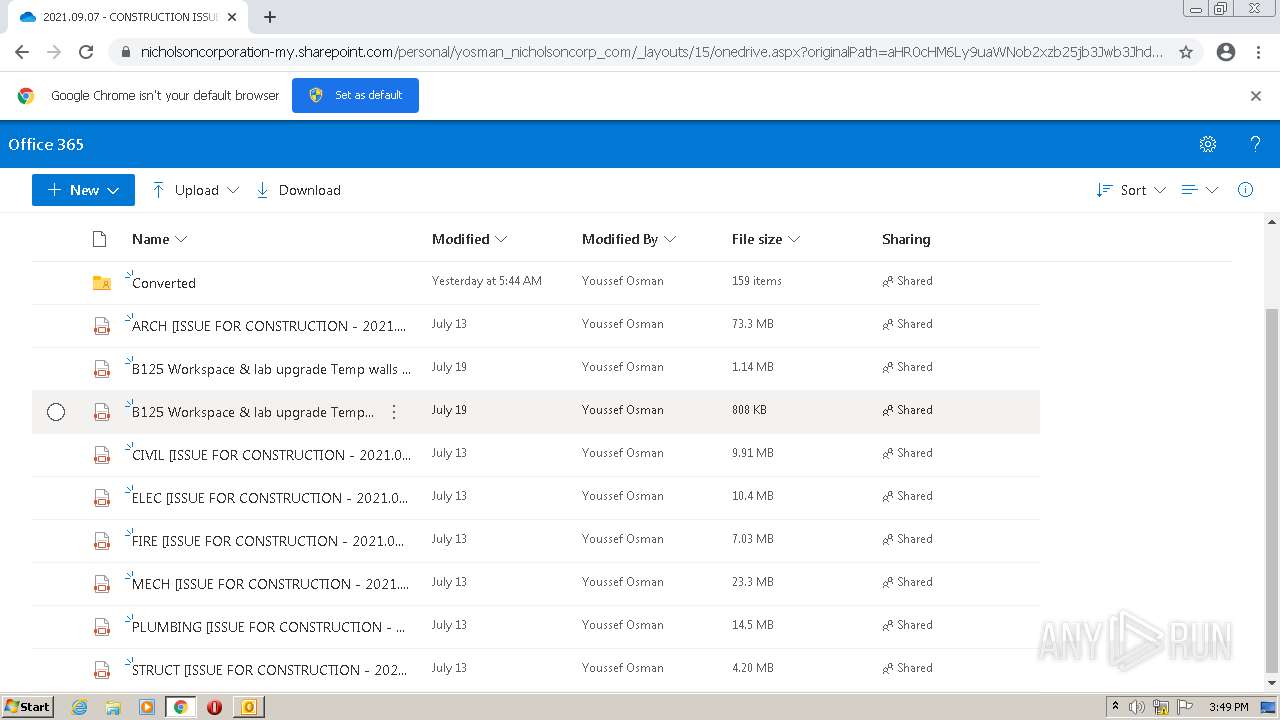
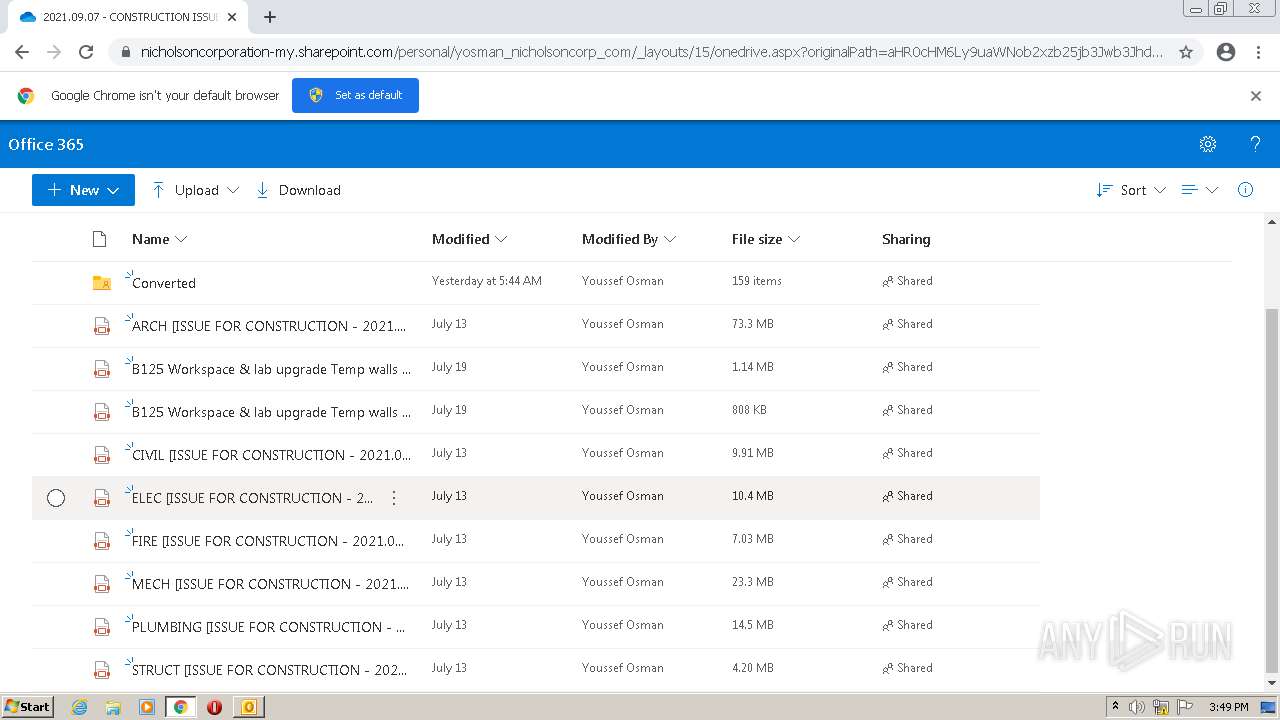
3044 | iexplore.exe | 13.107.136.9:443 | nicholsoncorporation-my.sharepoint.com | Microsoft Corporation | US | whitelisted |
188 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
188 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3044 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3132 | chrome.exe | 142.250.185.100:443 | www.google.com | Google Inc. | US | whitelisted |
3132 | chrome.exe | 142.250.74.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3132 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
urldefense.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
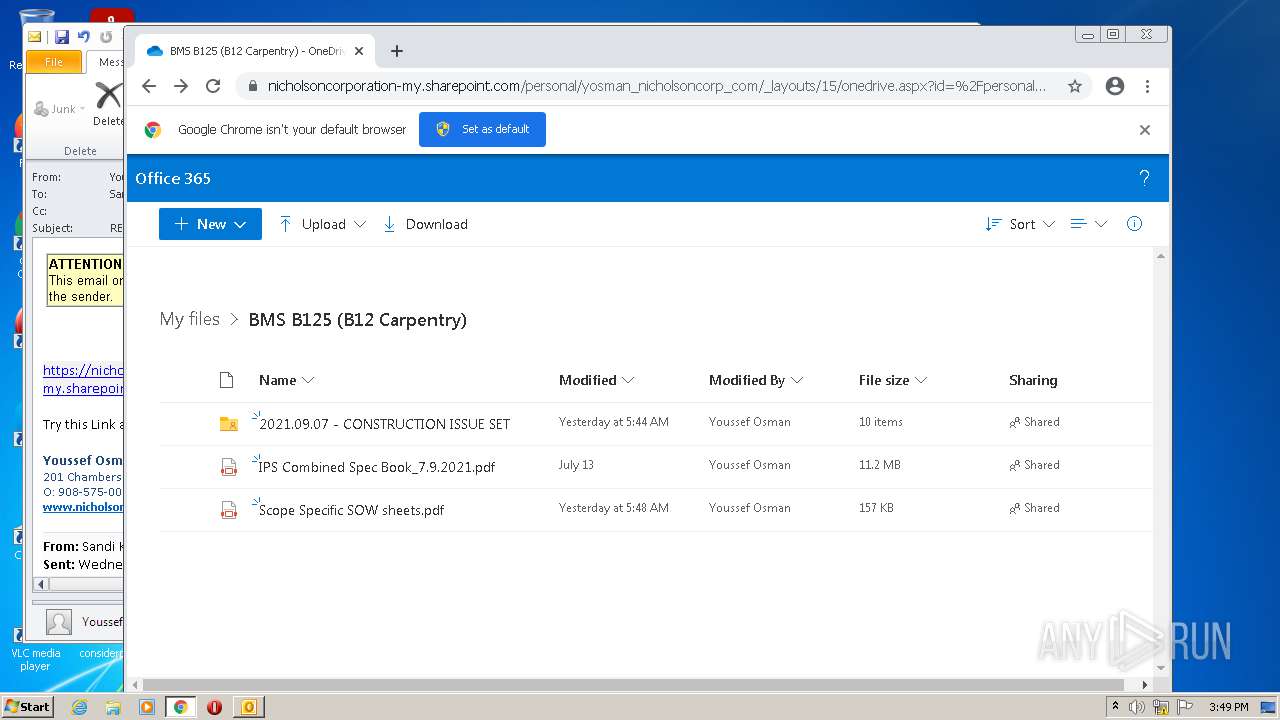
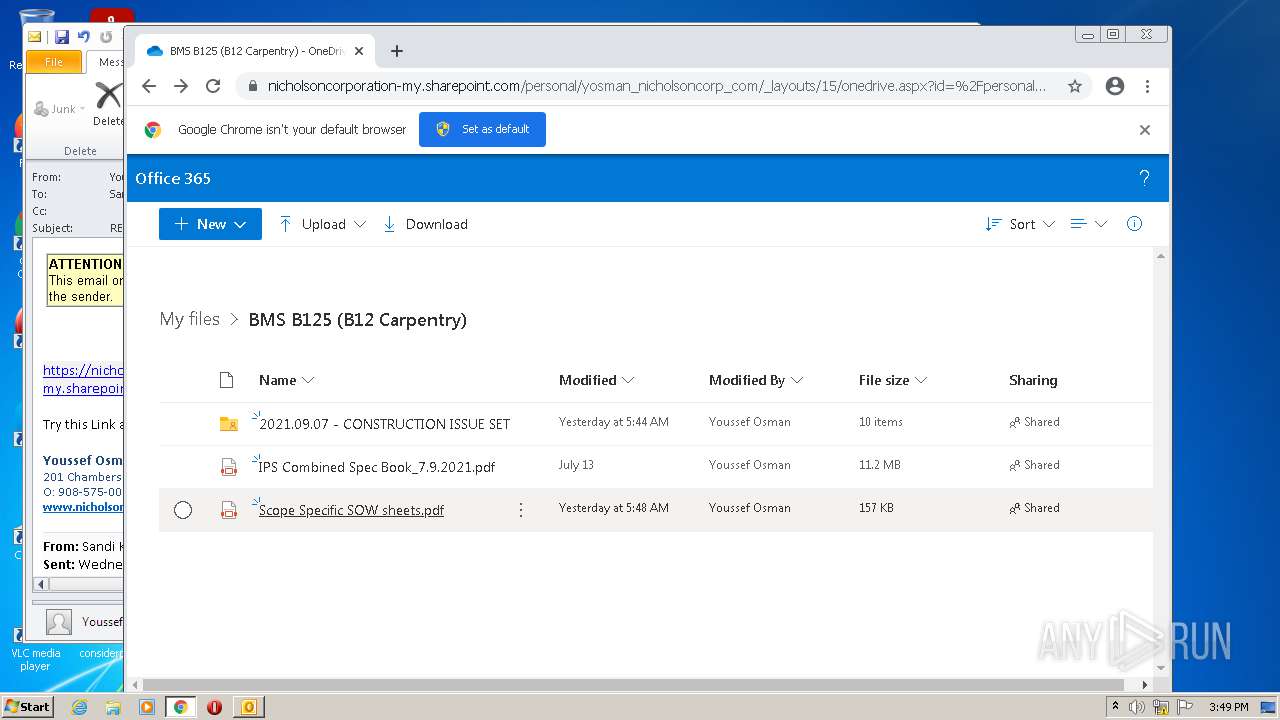
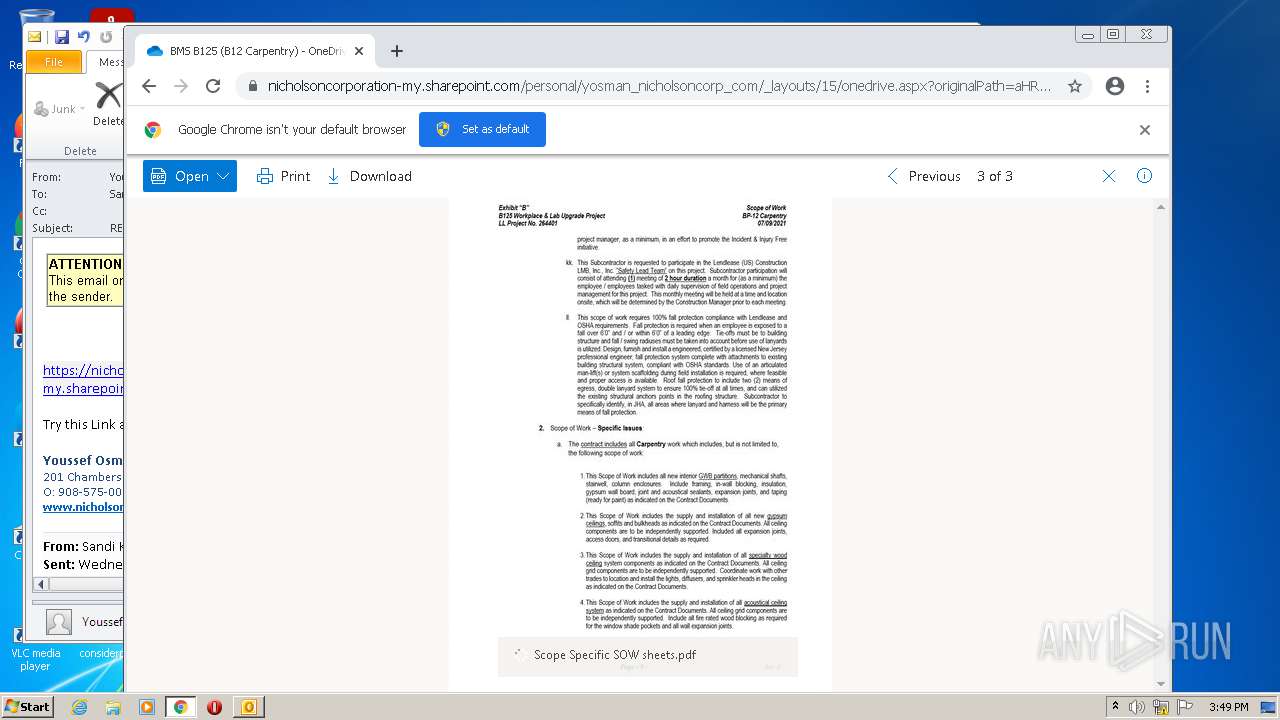
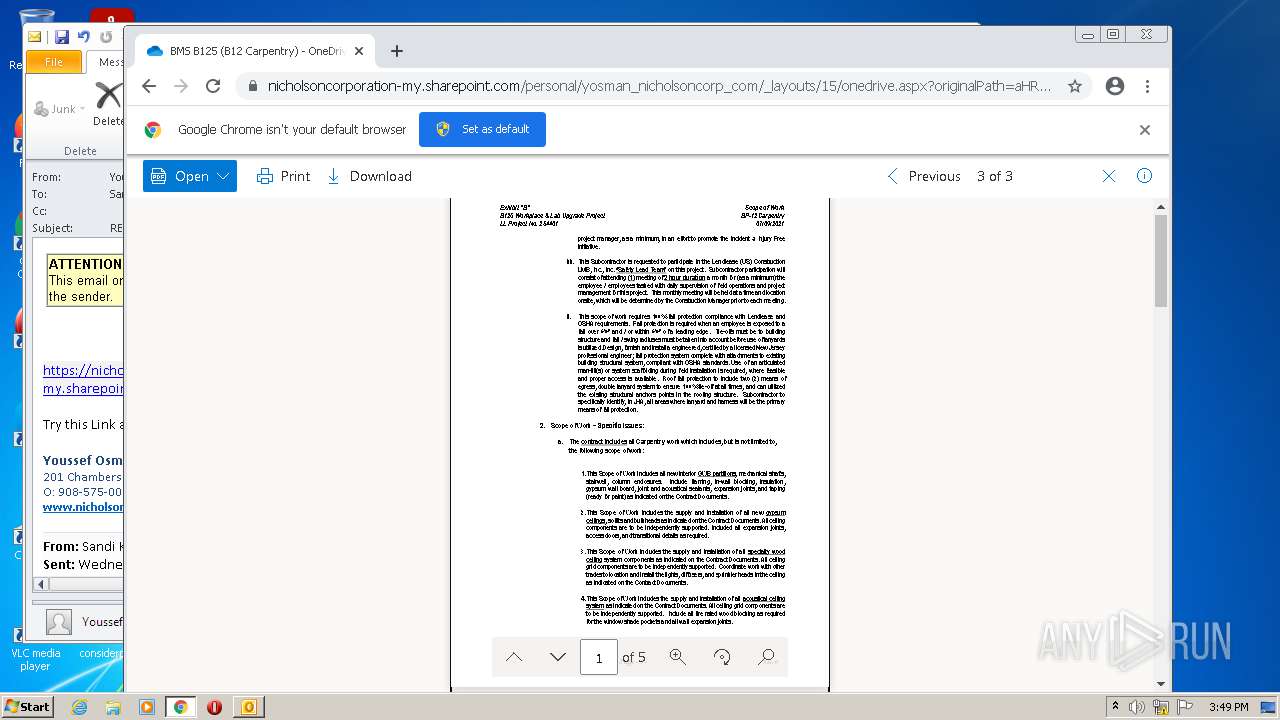
nicholsoncorporation-my.sharepoint.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |