| File name: | acff4bc8180417126563b61755dd464c.exe |
| Full analysis: | https://app.any.run/tasks/f3a5599b-95bd-4f61-aa25-3453bf7e7fd5 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 16:50:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | ACFF4BC8180417126563B61755DD464C |
| SHA1: | E246A80F90D88D5DF99E4E75BB44825FDC22A531 |
| SHA256: | E5E6DF5B10DE610AD7BA25D4BA98A3AF2788D45C143D8FA3ADB6F0843C0B1AAB |
| SSDEEP: | 12288:XwyY2yr62rm/sOAsCqyZObu+r5oZTKlVVVVVj:XXyr6LlAsCqyZObQk |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Reads security settings of Internet Explorer
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Checks Windows Trust Settings
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Reads settings of System Certificates
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Connects to unusual port
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
INFO
Checks supported languages
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Checks proxy server information
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Reads the computer name
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Reads the machine GUID from the registry
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Creates files or folders in the user directory
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Create files in a temporary directory
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Reads Environment values
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Reads product name
- acff4bc8180417126563b61755dd464c.exe (PID: 796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Clipper DOS Executable (19.1) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
| .vxd | | | VXD Driver (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:06 04:06:44+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 209408 |
| InitializedDataSize: | 40488448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3704 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 37.0.0.0 |
| ProductVersionNumber: | 46.0.0.0 |
| FileFlagsMask: | 0x145a |
| FileFlags: | (none) |
| FileOS: | Unknown (0x20723) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Unknown (0452) |
| CharacterSet: | Unknown (30F3) |
| FileDescription: | Mabling |
| LegalCopyright: | Copyright (C) 2022, Crazy |
| OriginalFileName: | Munpler |
| ProductsVersion: | 19.3.71.61 |
| ProductionVersion: | 16.78.79.2 |
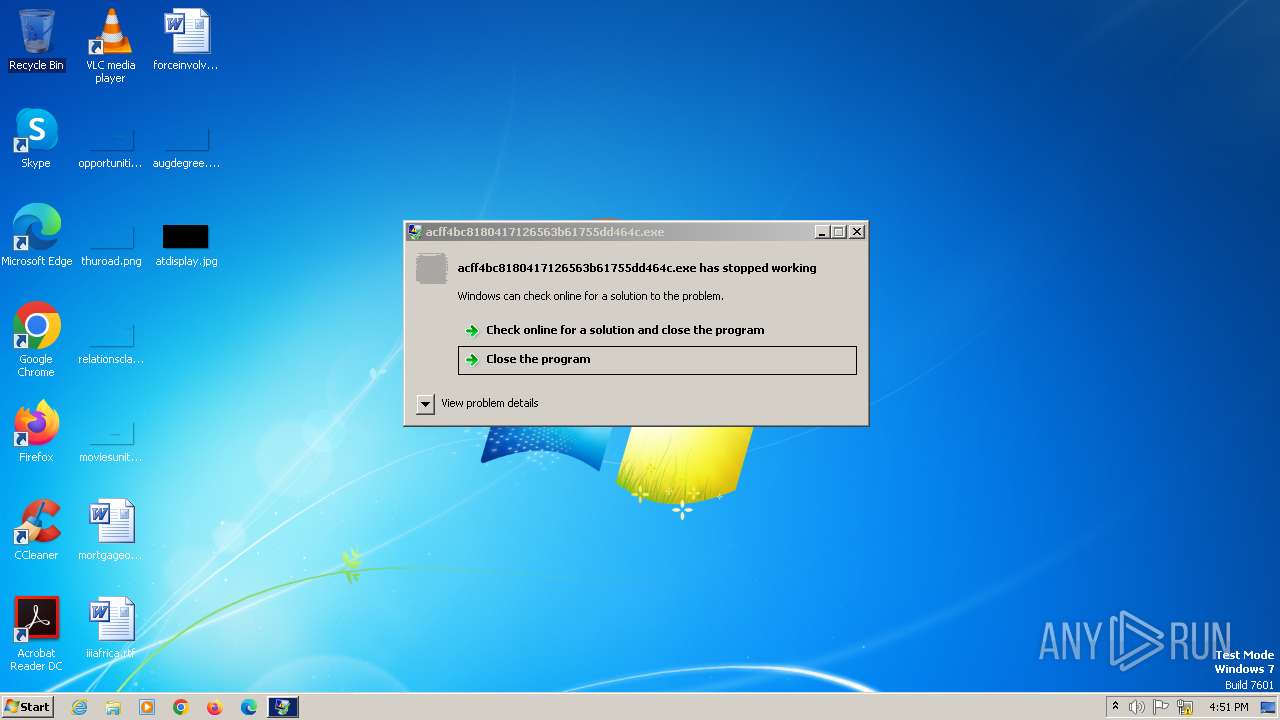
Total processes
36
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 796 | "C:\Users\admin\AppData\Local\Temp\acff4bc8180417126563b61755dd464c.exe" | C:\Users\admin\AppData\Local\Temp\acff4bc8180417126563b61755dd464c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
947
Read events
930
Write events
17
Delete events
0
Modification events
| (PID) Process: | (796) acff4bc8180417126563b61755dd464c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (796) acff4bc8180417126563b61755dd464c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (796) acff4bc8180417126563b61755dd464c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (796) acff4bc8180417126563b61755dd464c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000C1000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (796) acff4bc8180417126563b61755dd464c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (796) acff4bc8180417126563b61755dd464c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (796) acff4bc8180417126563b61755dd464c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (796) acff4bc8180417126563b61755dd464c.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (796) acff4bc8180417126563b61755dd464c.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\15A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
4
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 796 | acff4bc8180417126563b61755dd464c.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\RP79GQKC.txt | text | |
MD5:FE69F8C5750D9F36D6D54FE710D83ED3 | SHA256:627C3C9FF5D4E53B2CB0D74A6A52A47DD9CC3CF536C1FEEB6E1C1878BA52D194 | |||
| 796 | acff4bc8180417126563b61755dd464c.exe | C:\Users\admin\AppData\Local\Temp\Cab28FE.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 796 | acff4bc8180417126563b61755dd464c.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:348DD53AD3F2102D1CA204B7C266A29D | SHA256:A6092B2A03A53C9C7CA2C511643915D44065533299953F76D426982BEE824998 | |||
| 796 | acff4bc8180417126563b61755dd464c.exe | C:\Users\admin\AppData\Local\Temp\Tar28FF.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 796 | acff4bc8180417126563b61755dd464c.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
11
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
796 | acff4bc8180417126563b61755dd464c.exe | GET | 200 | 184.24.77.173:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2f0eea2783f97309 | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
796 | acff4bc8180417126563b61755dd464c.exe | 149.154.167.99:443 | t.me | Telegram Messenger Inc | GB | unknown |
796 | acff4bc8180417126563b61755dd464c.exe | 116.202.184.4:9000 | — | Hetzner Online GmbH | DE | unknown |
796 | acff4bc8180417126563b61755dd464c.exe | 184.24.77.173:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t.me |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
796 | acff4bc8180417126563b61755dd464c.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
1 ETPRO signatures available at the full report