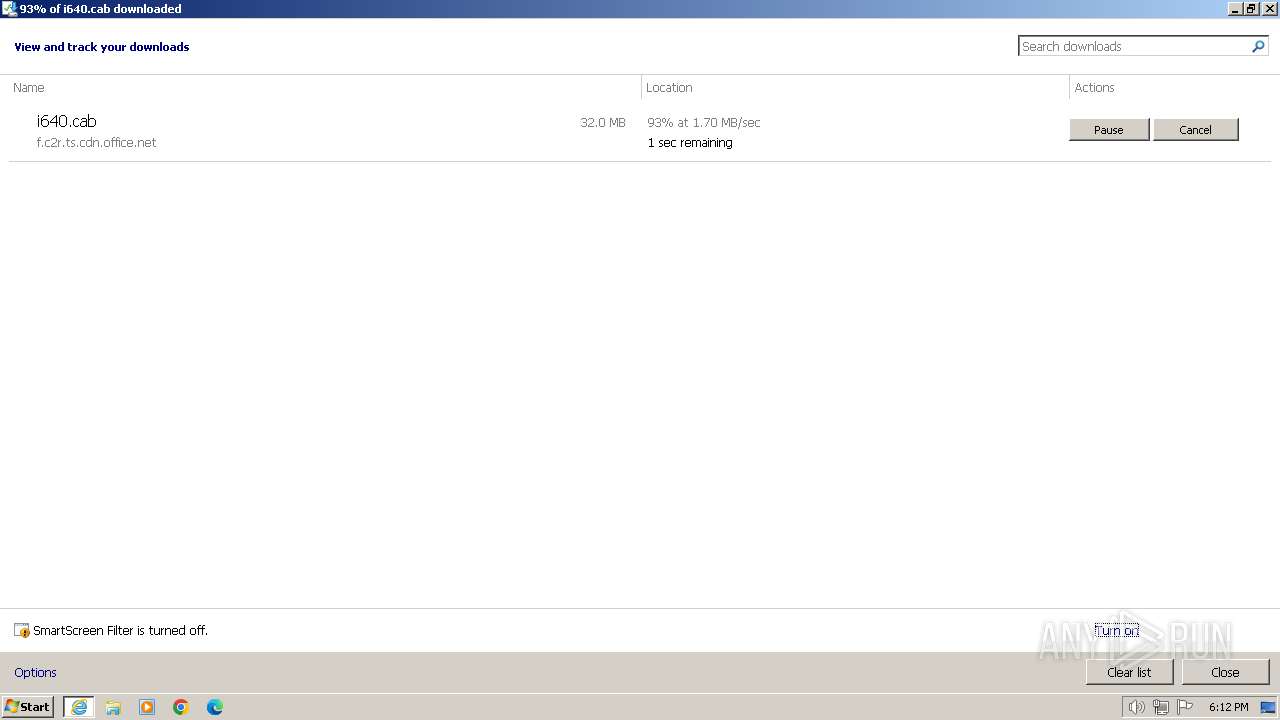
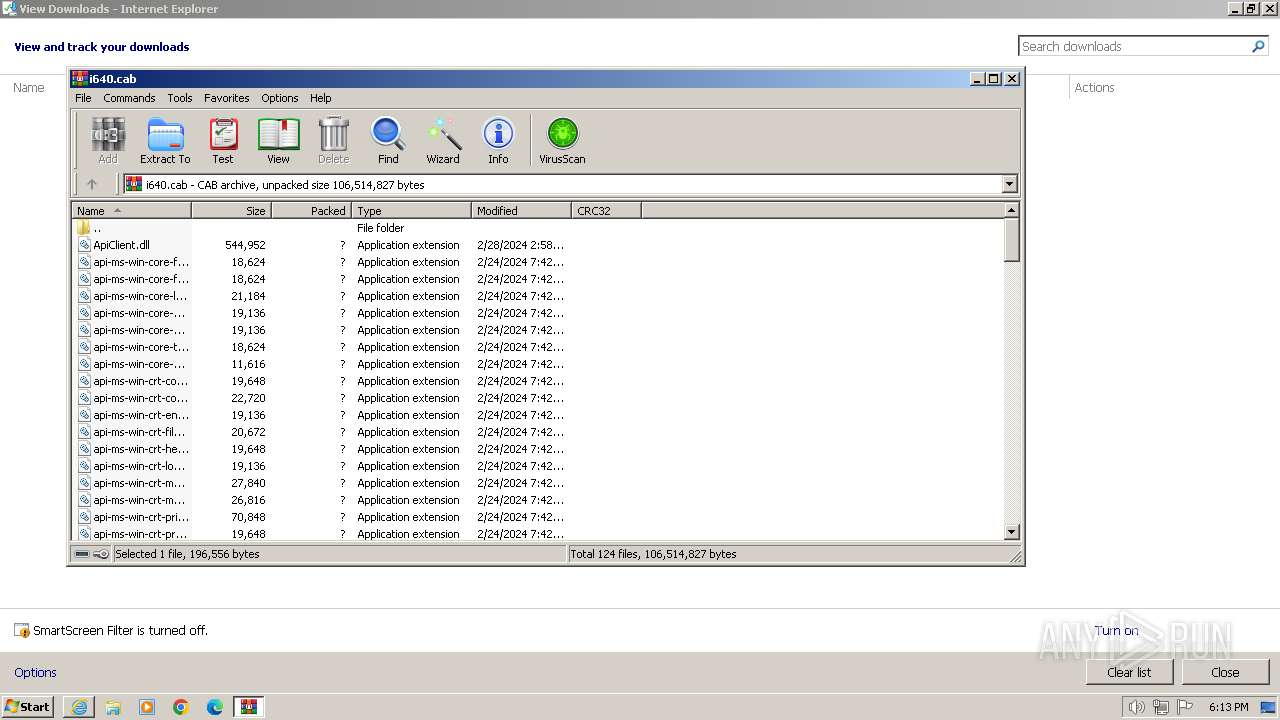
| URL: | http://f.c2r.ts.cdn.office.net/pr/64256afe-f5d9-4f86-8936-8840a6a4f5be/Office/Data/16.0.17425.20008/i640.cab |
| Full analysis: | https://app.any.run/tasks/29503abf-c391-4d6e-8e7b-c9848b9783e2 |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2024, 18:11:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DCBE32F92432F83BBB071355316531F1 |
| SHA1: | 218CEF130A430A1A69422CE5D836CE57A8AFB3AB |
| SHA256: | E5DD0F007752CAF1AD5126FFE7DB82F5631774FB5CCCE0FAA41C0A9B75979E5F |
| SSDEEP: | 3:N1KYLYwyQpuIWBcsSdEddRuiSAxyROLhNoV6Miun:CYLY5CpW9uEfojROLhNogun |
MALICIOUS
No malicious indicators.SUSPICIOUS
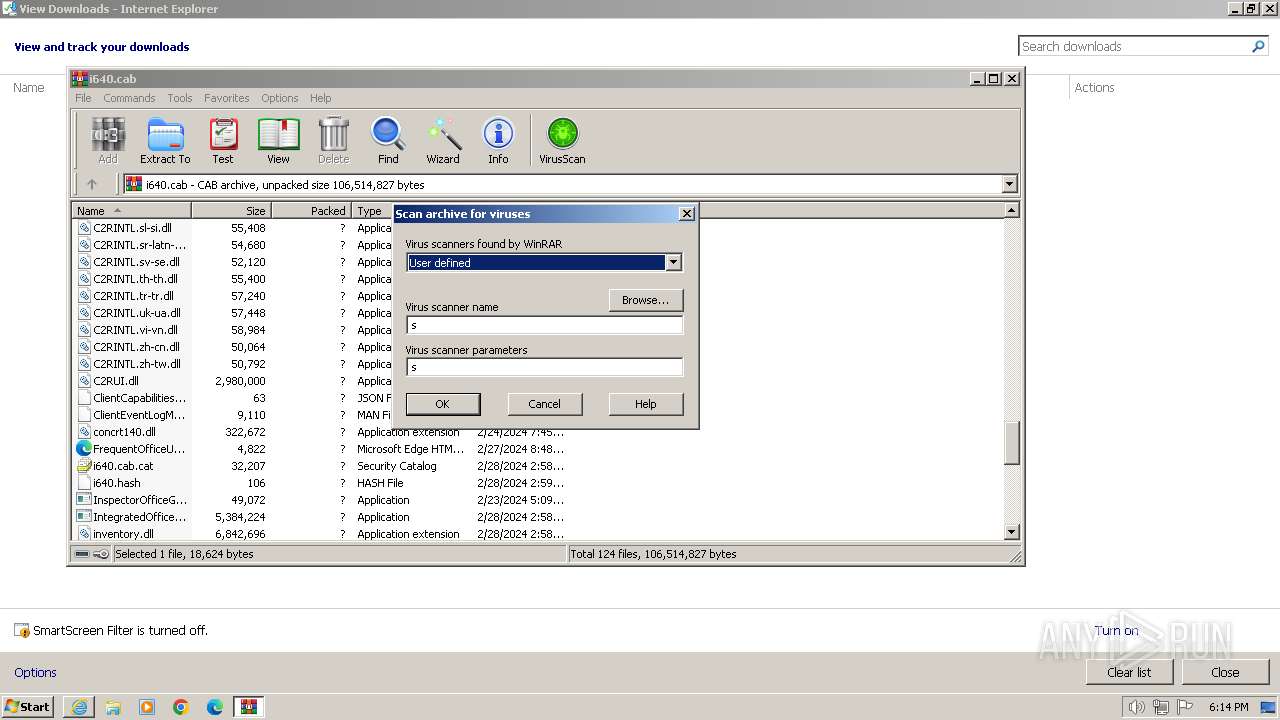
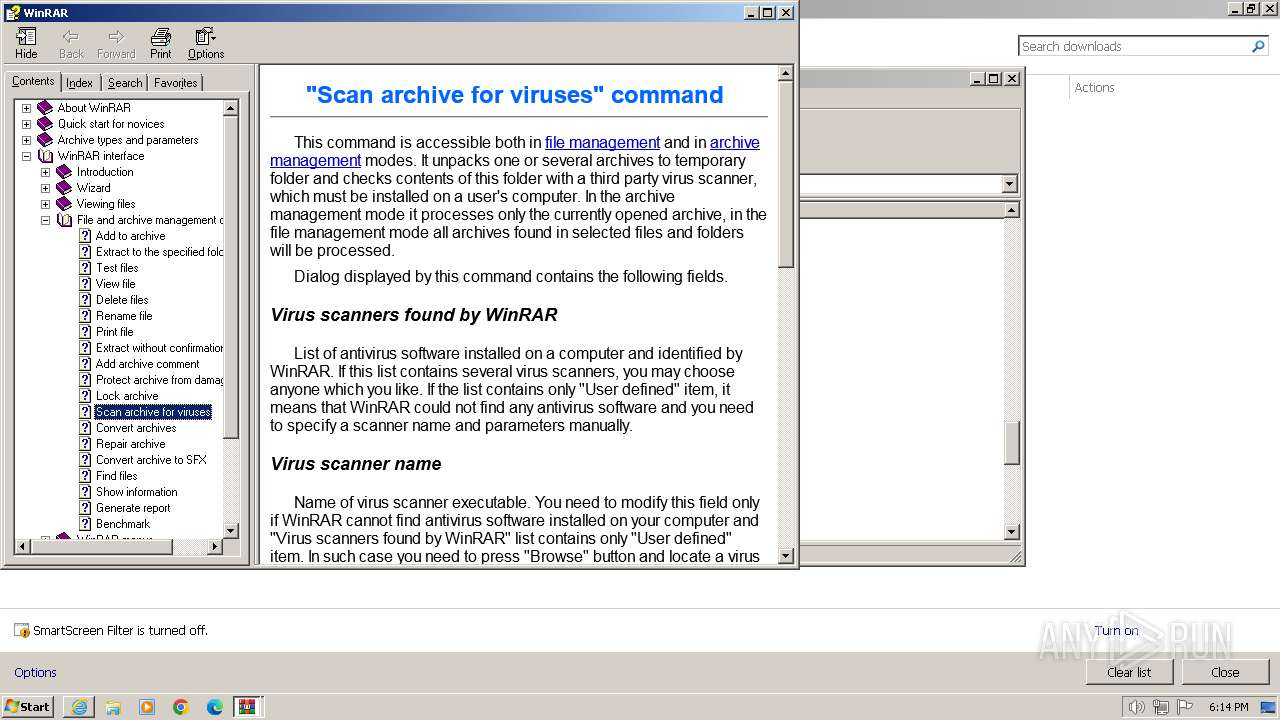
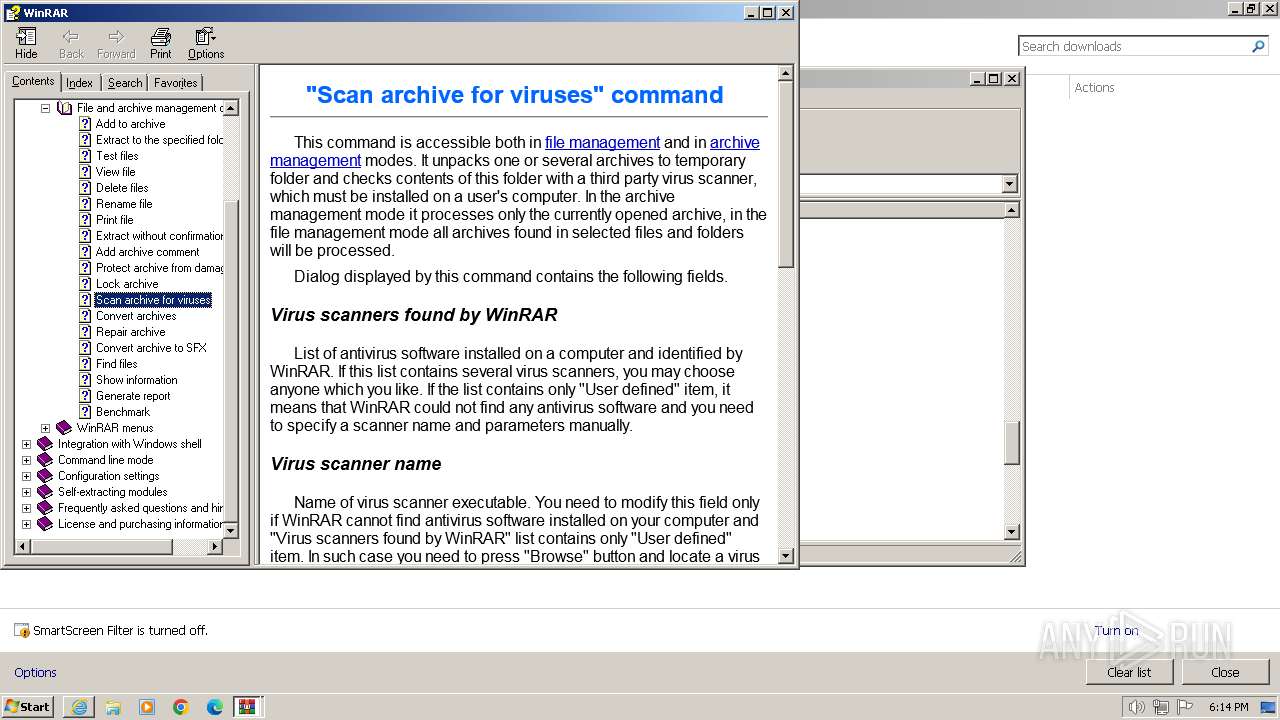
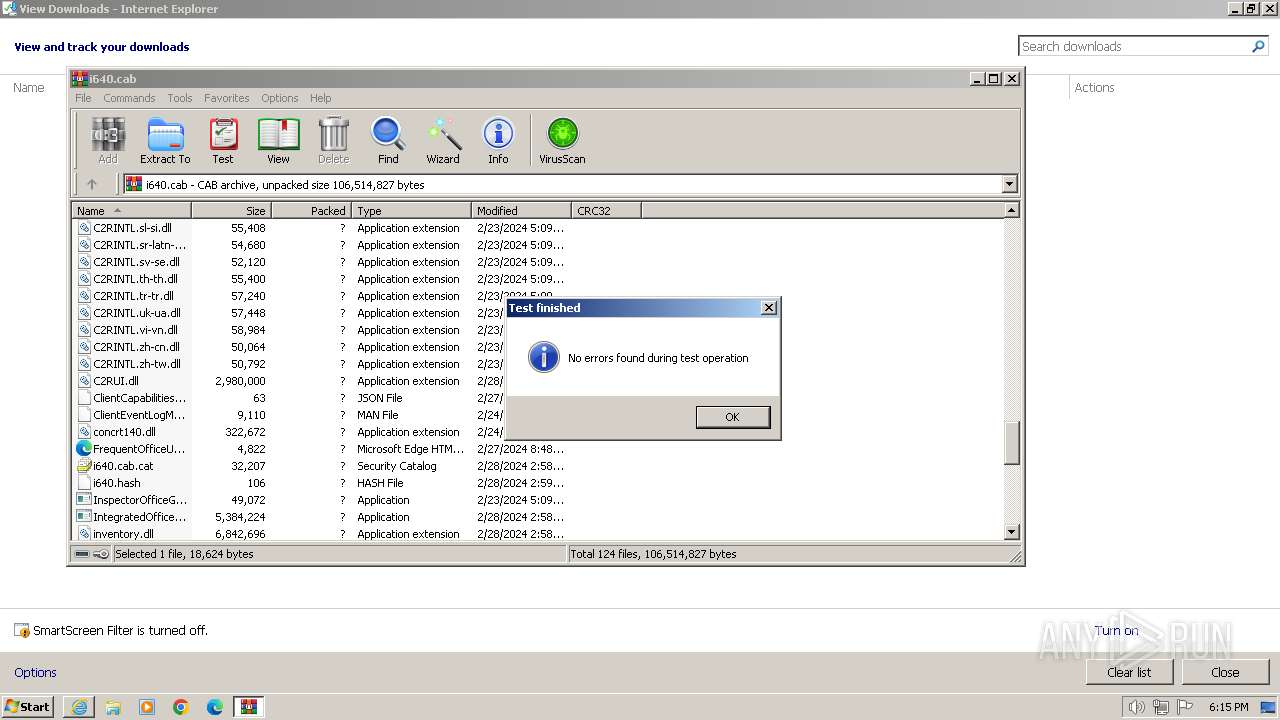
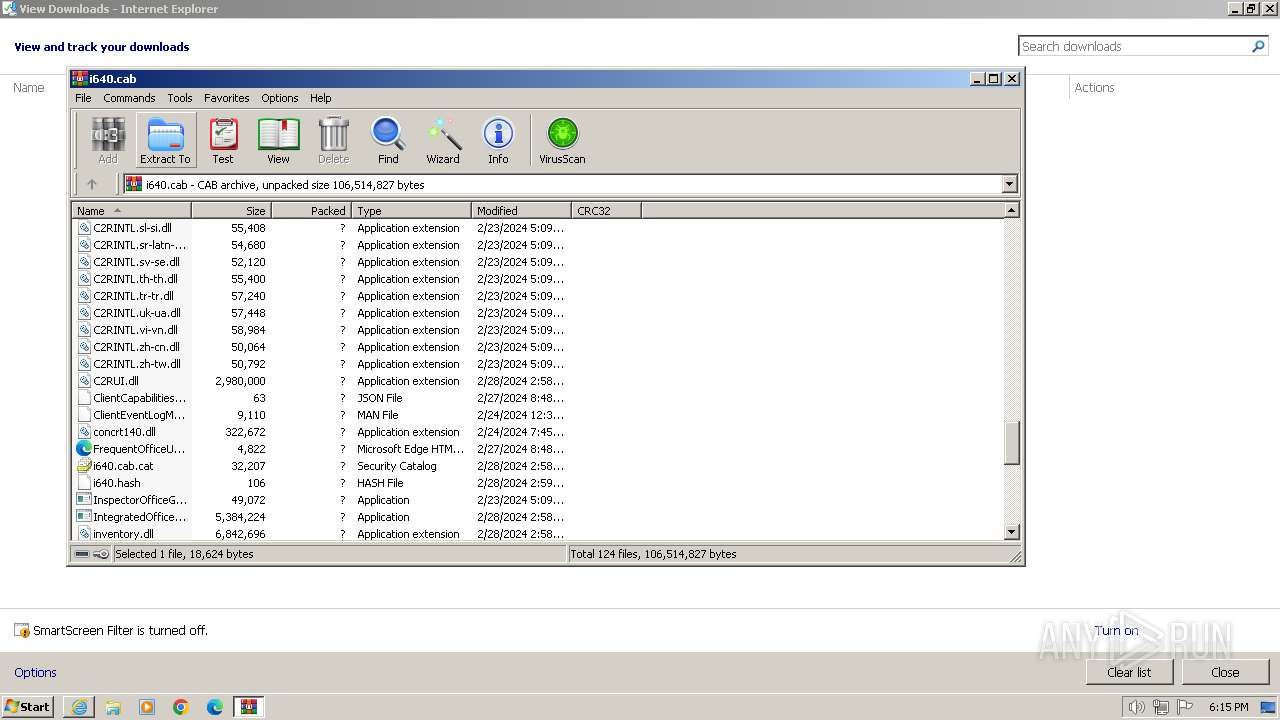
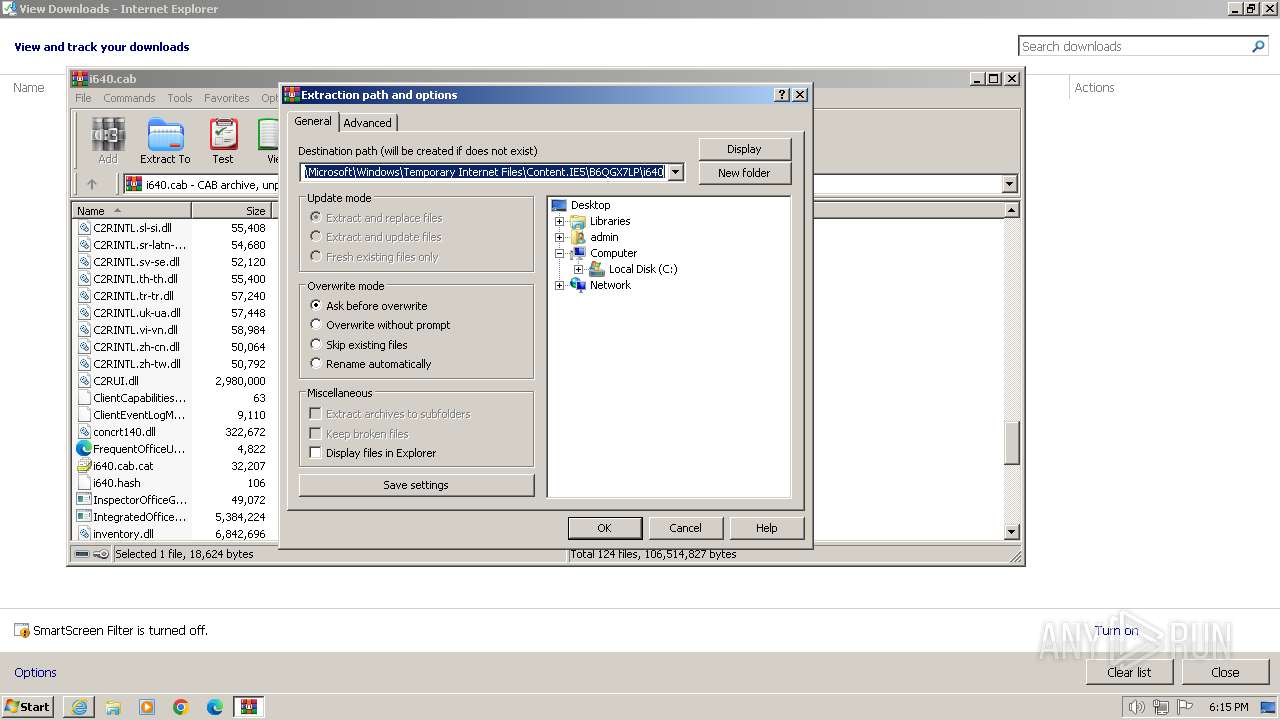
Process drops legitimate windows executable
- WinRAR.exe (PID: 116)
Reads Microsoft Outlook installation path
- WinRAR.exe (PID: 116)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 116)
Reads Internet Explorer settings
- WinRAR.exe (PID: 116)
Creates file in the systems drive root
- WinRAR.exe (PID: 116)
INFO
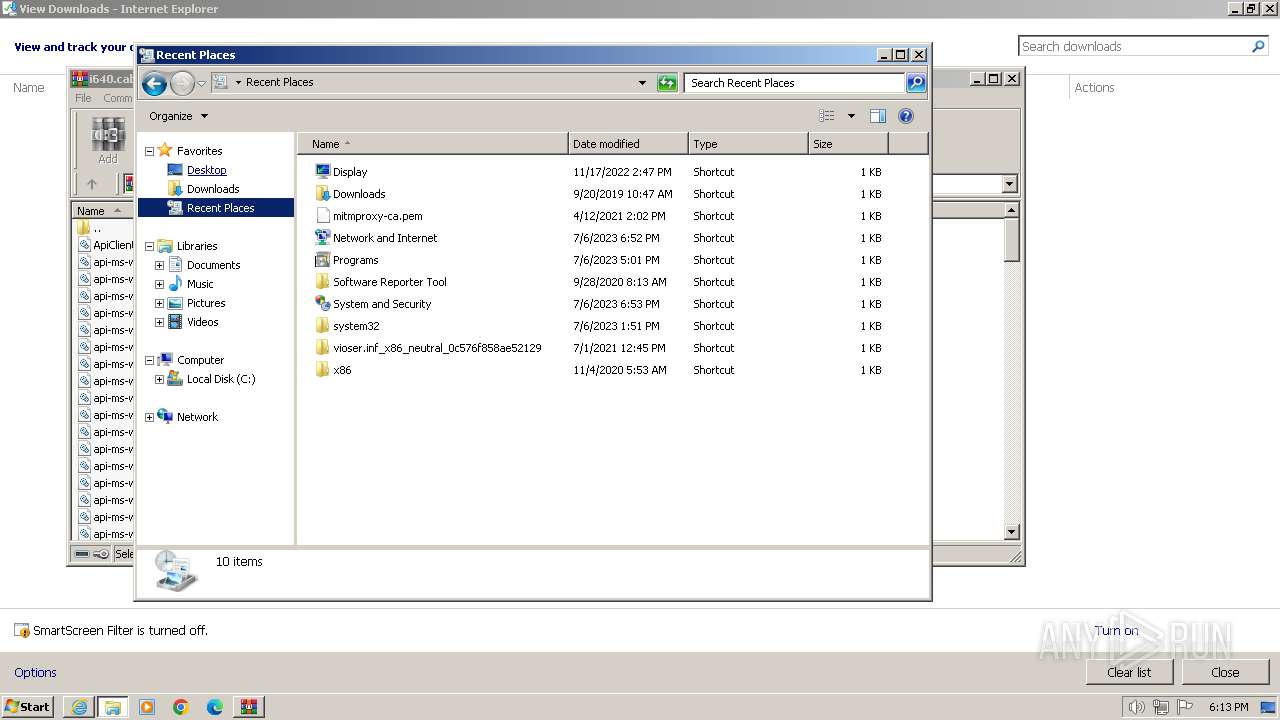
Modifies the phishing filter of IE
- iexplore.exe (PID: 3672)
Checks proxy server information
- WinRAR.exe (PID: 116)
Application launched itself
- iexplore.exe (PID: 3672)
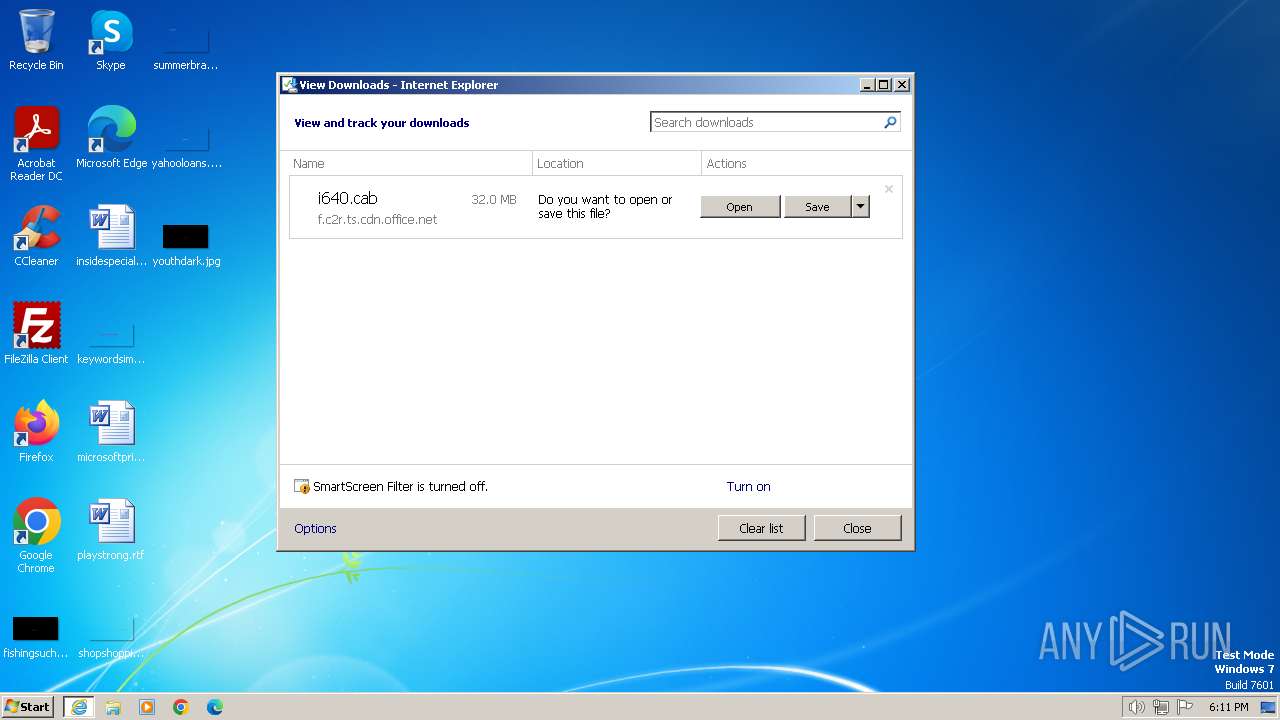
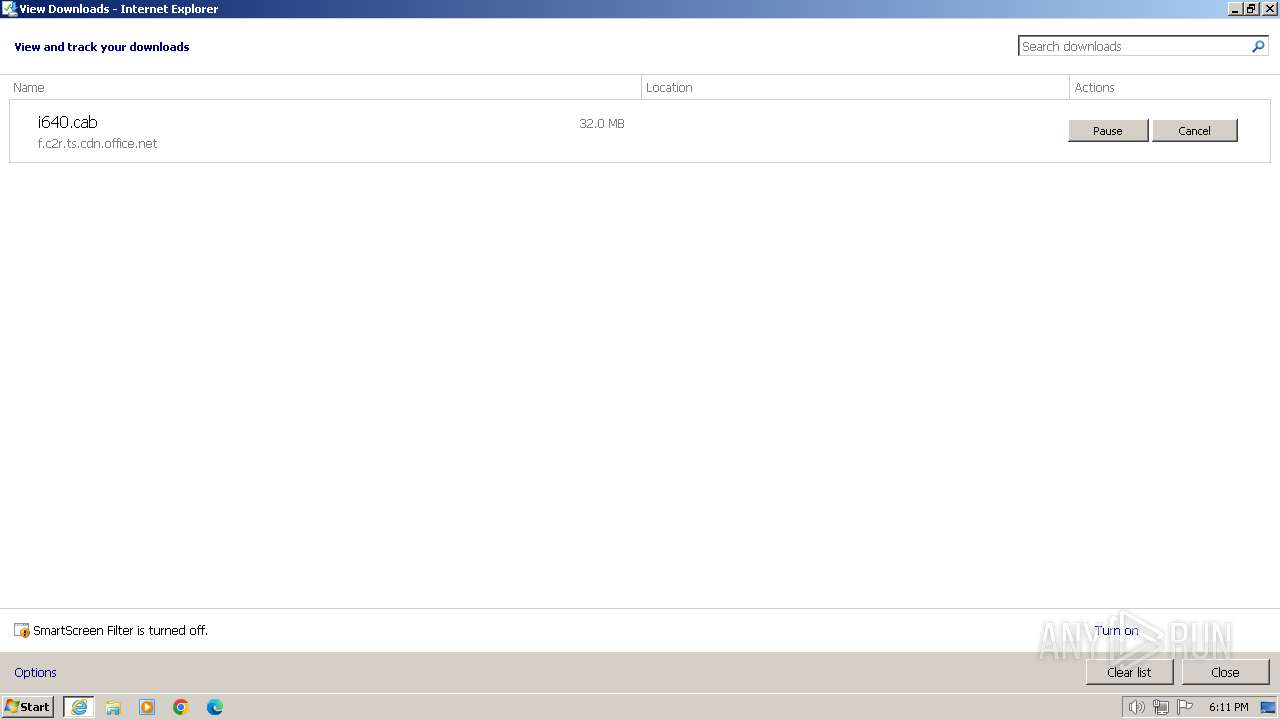
The process uses the downloaded file
- iexplore.exe (PID: 3672)
- WinRAR.exe (PID: 116)
Manual execution by a user
- explorer.exe (PID: 956)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 116)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
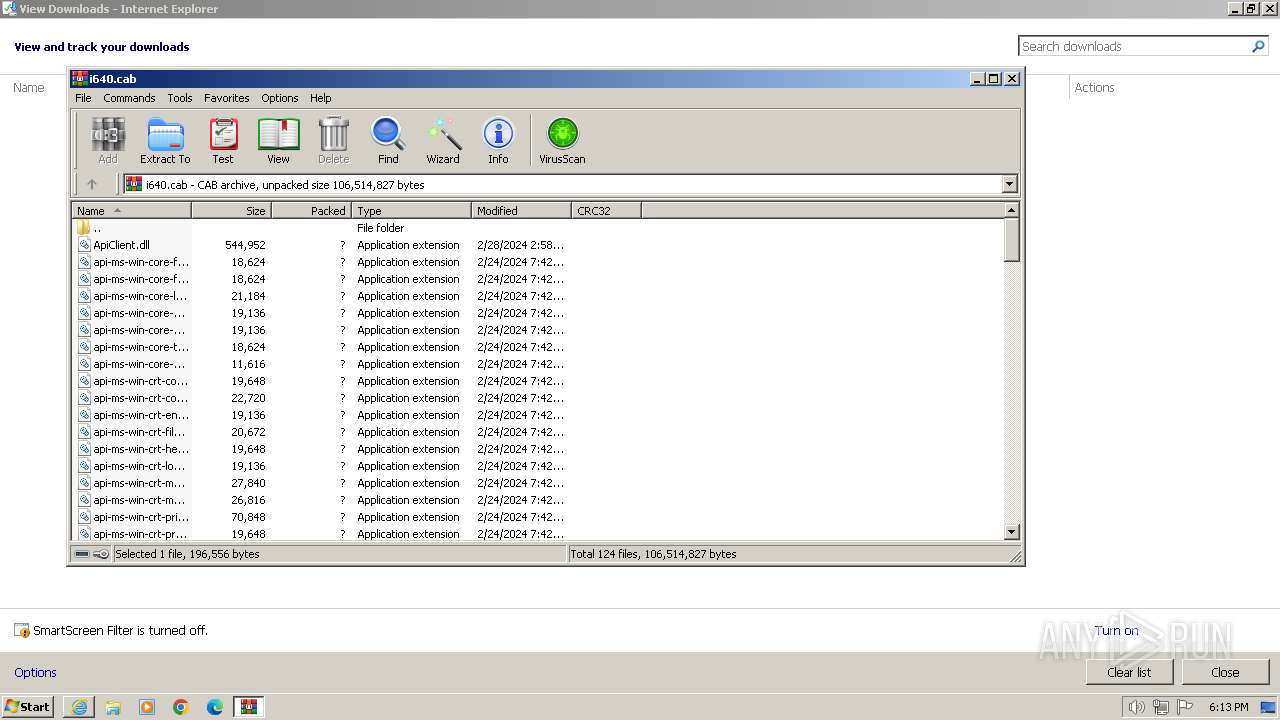
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
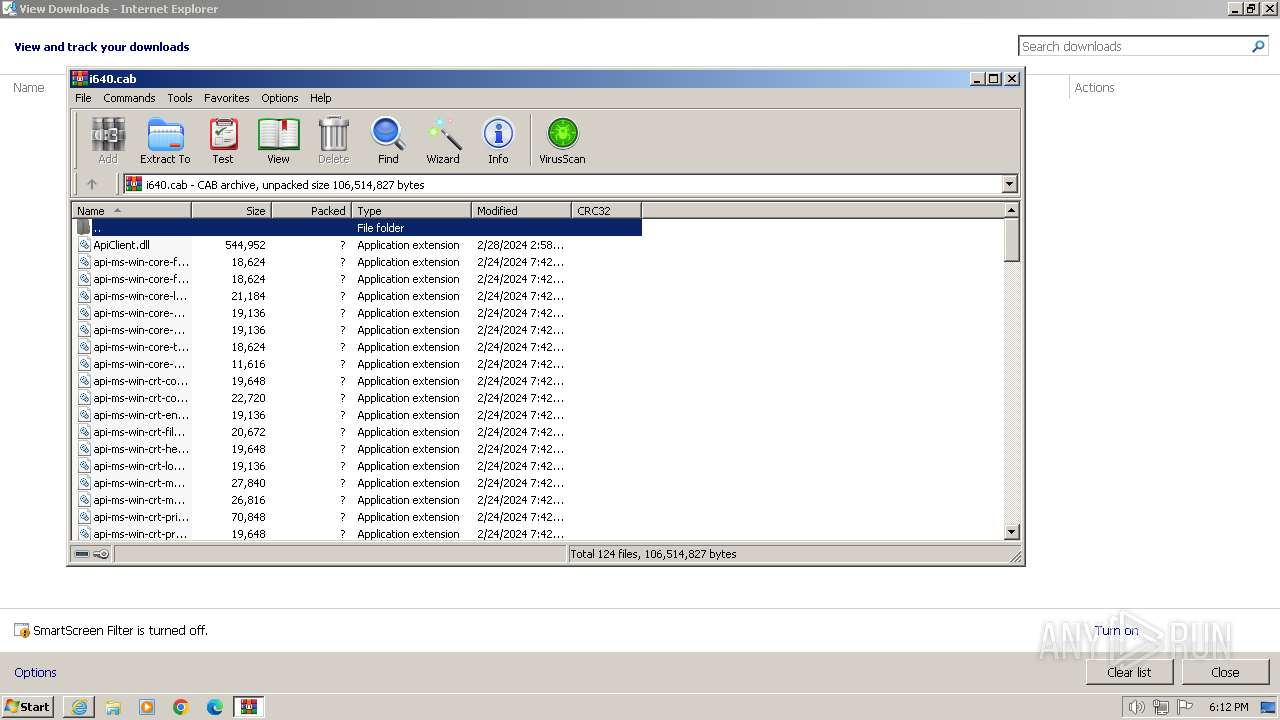
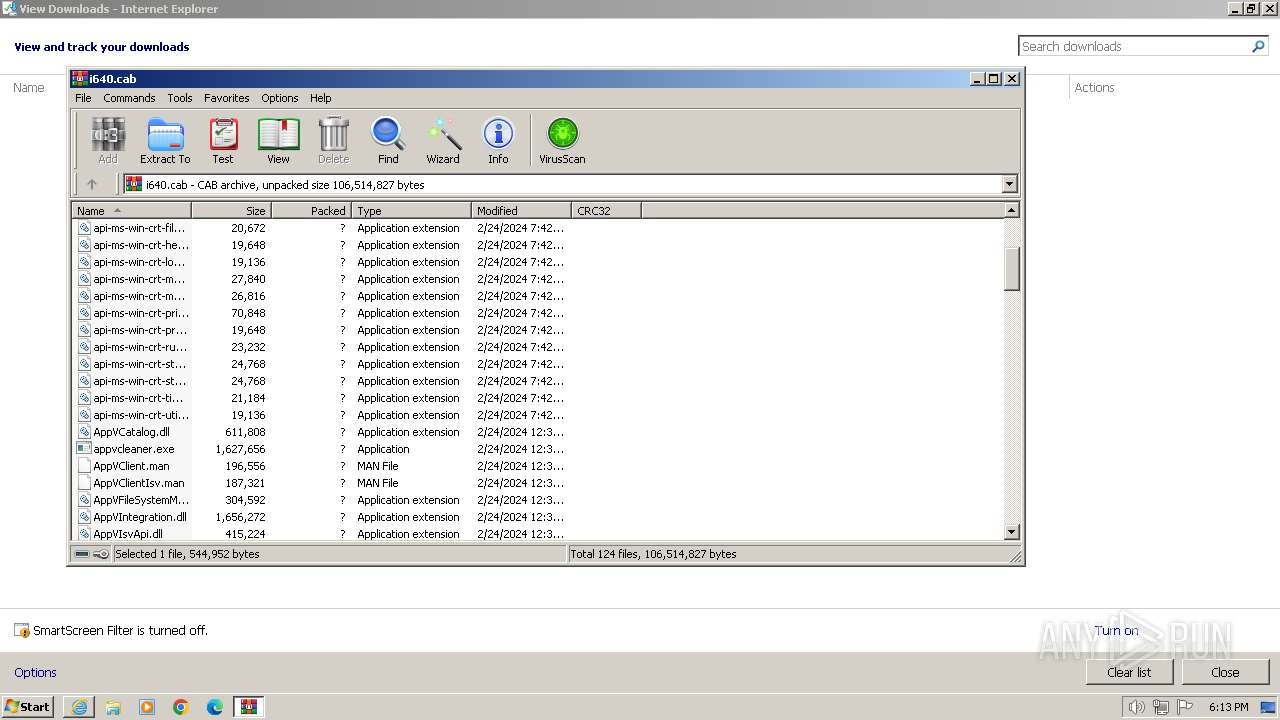
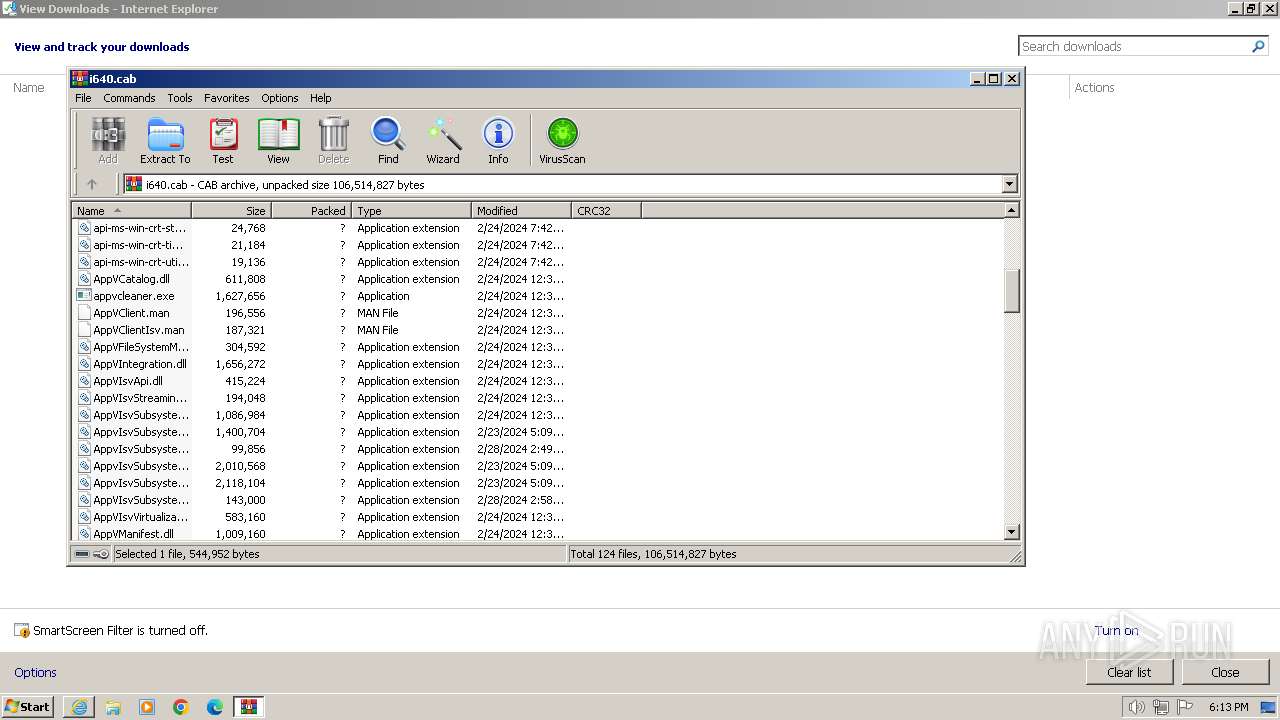
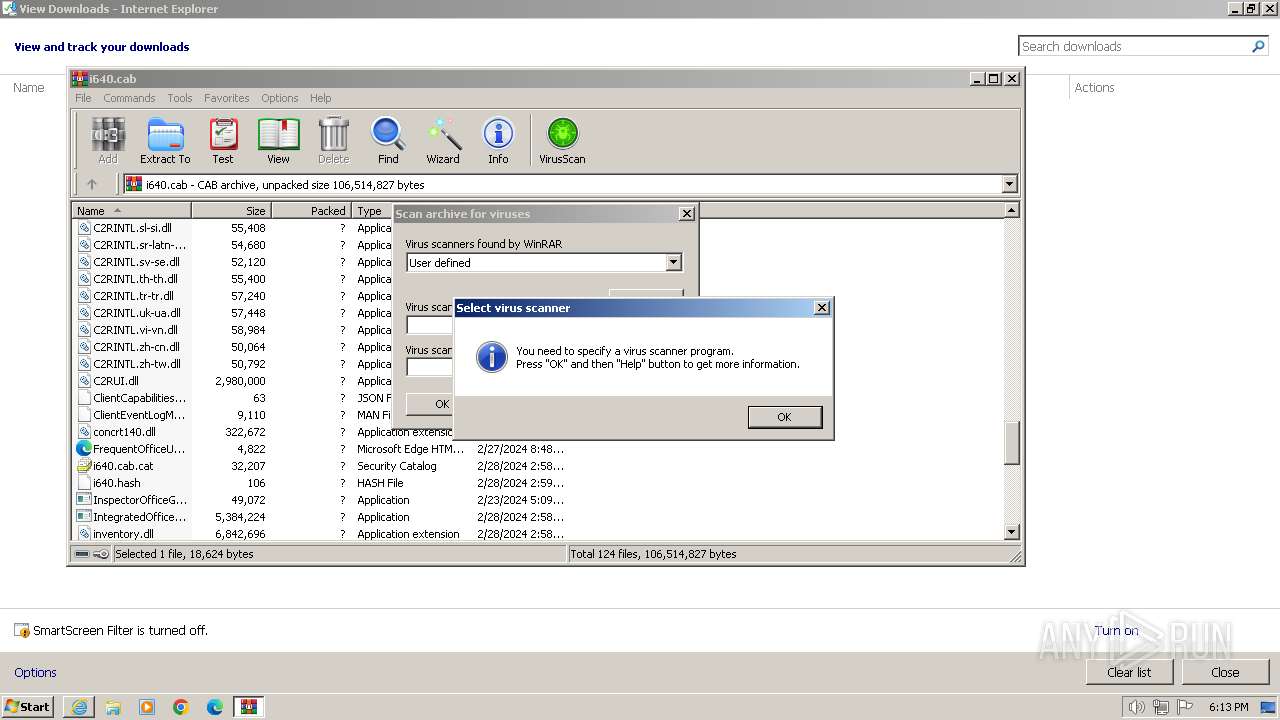
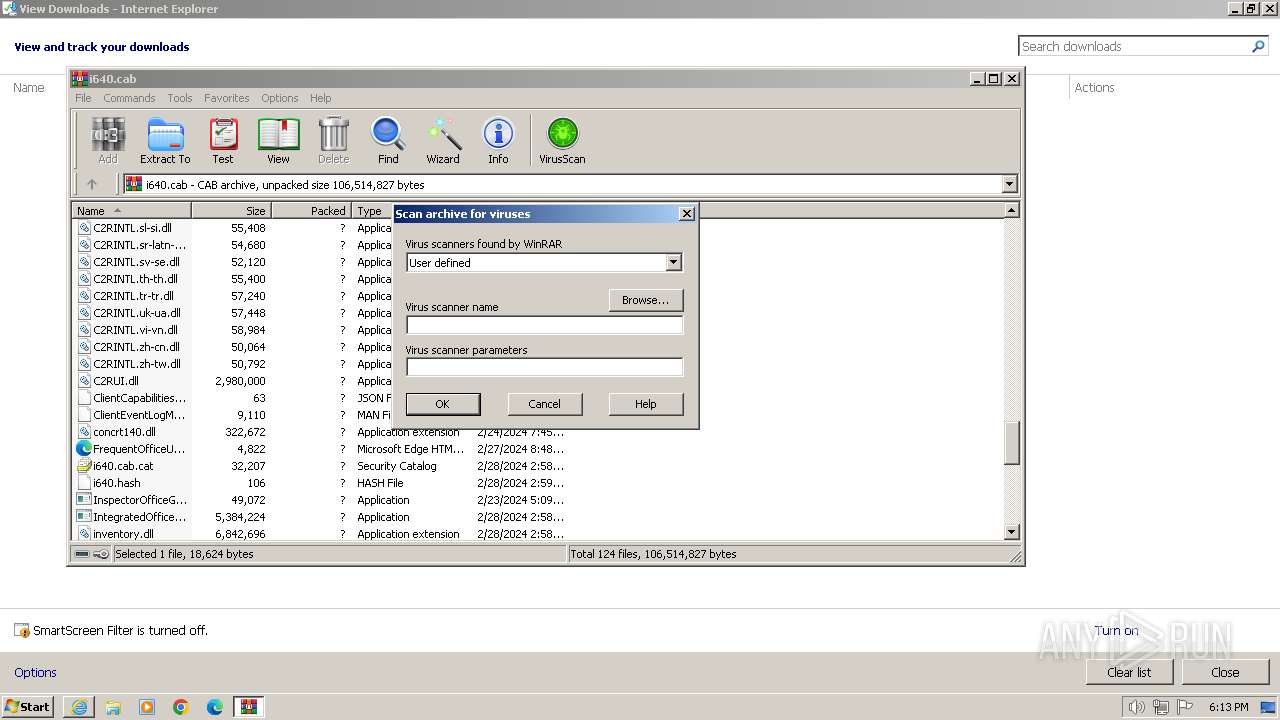
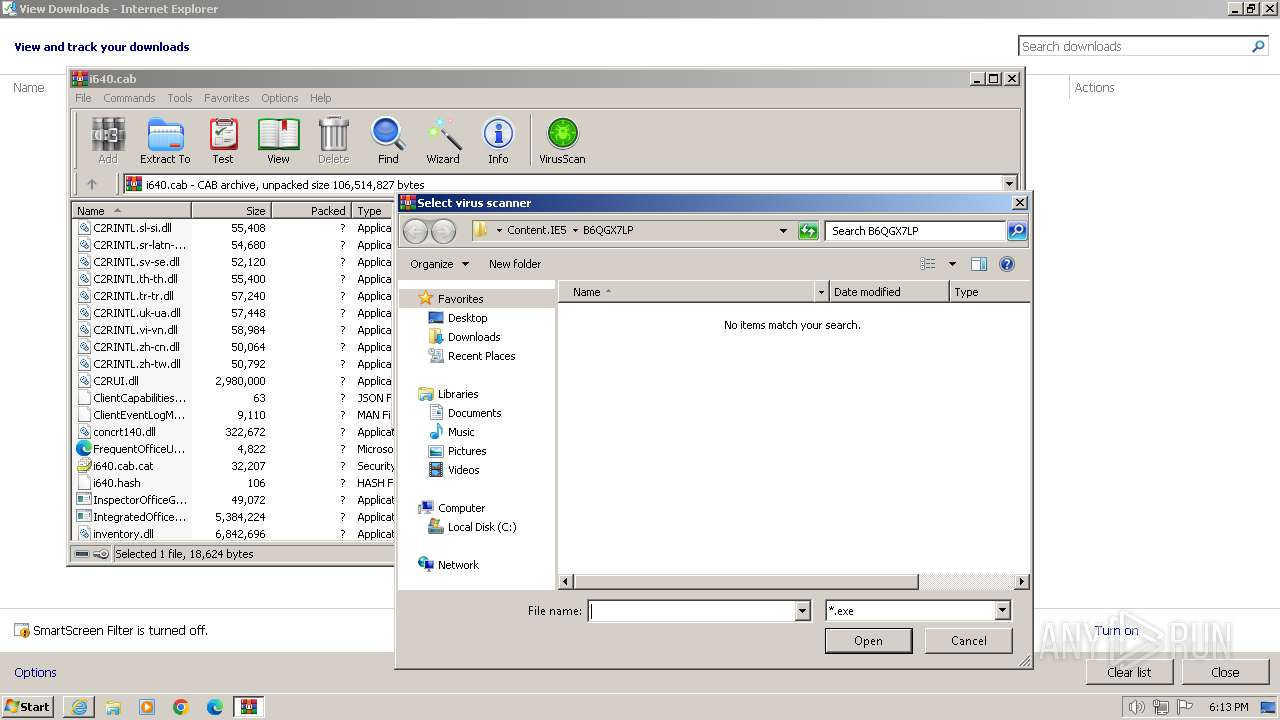
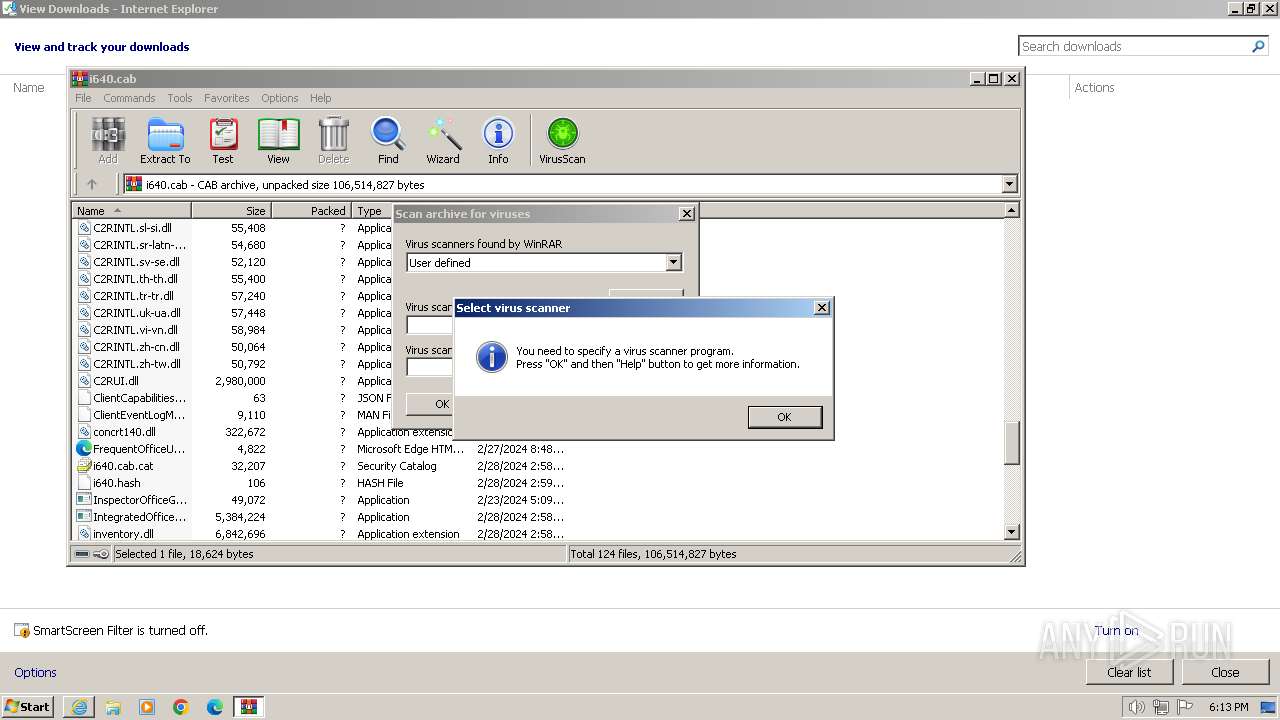
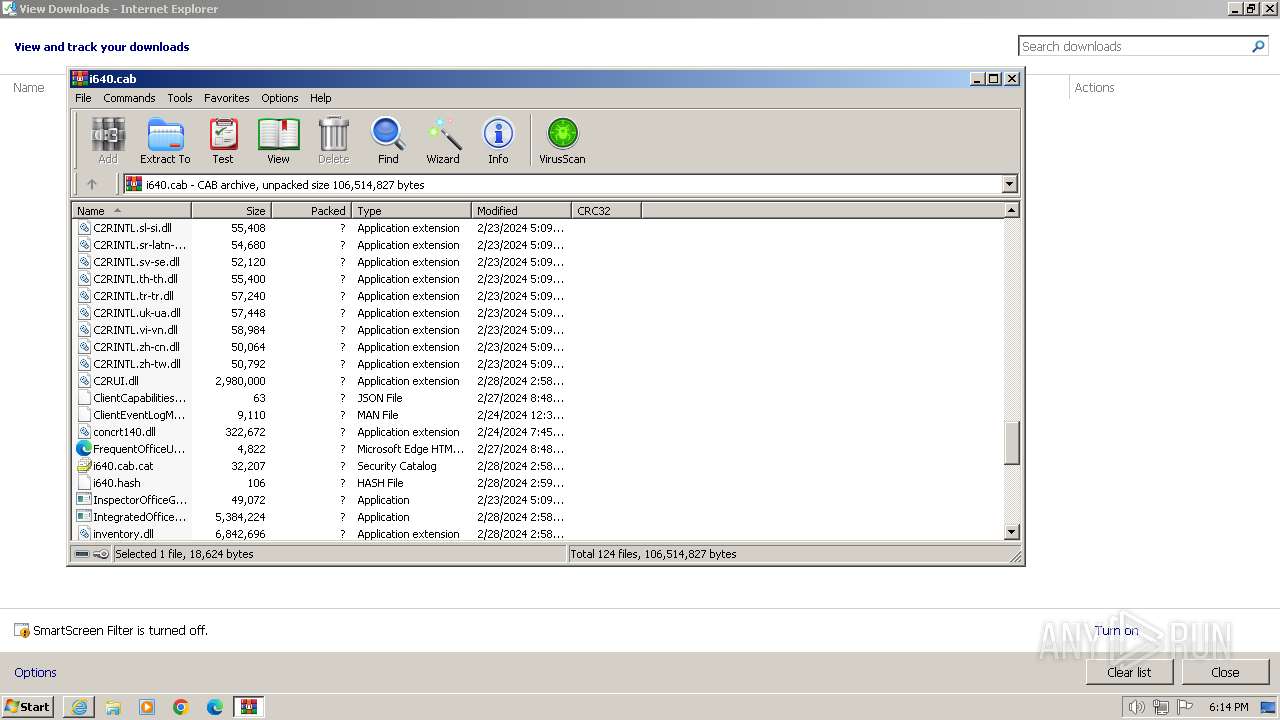
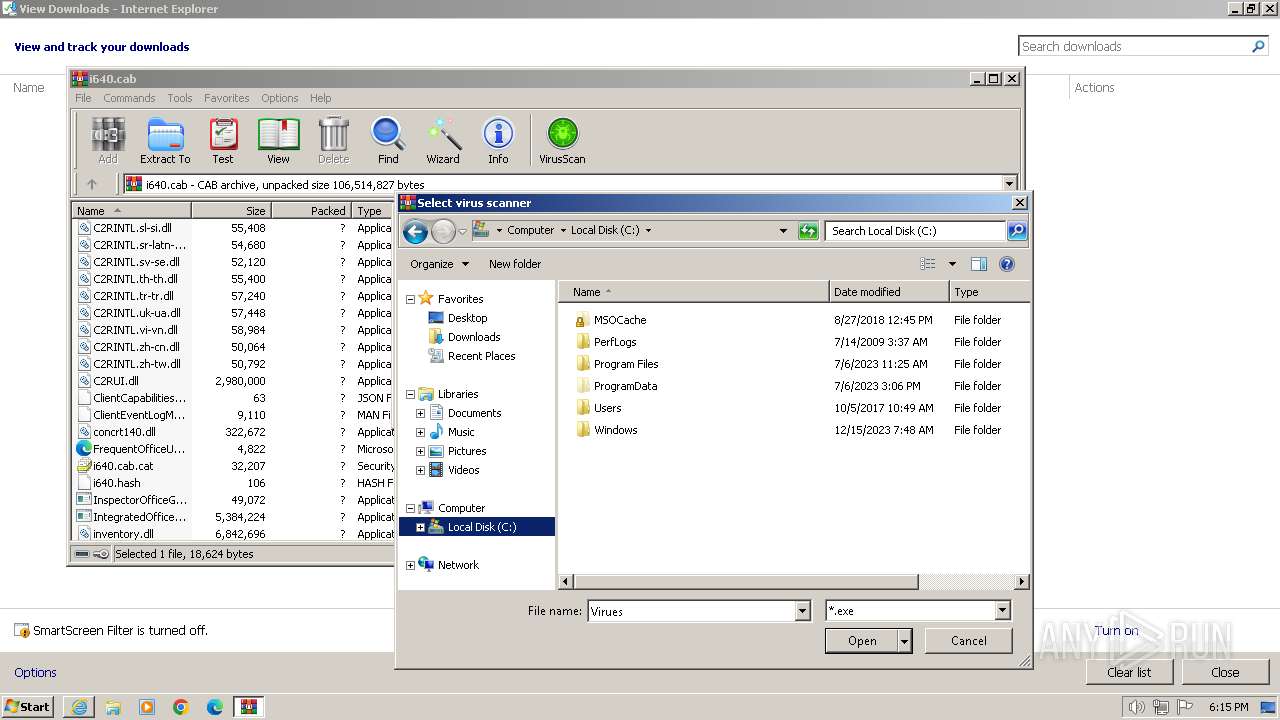
| 116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\i640.cab" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
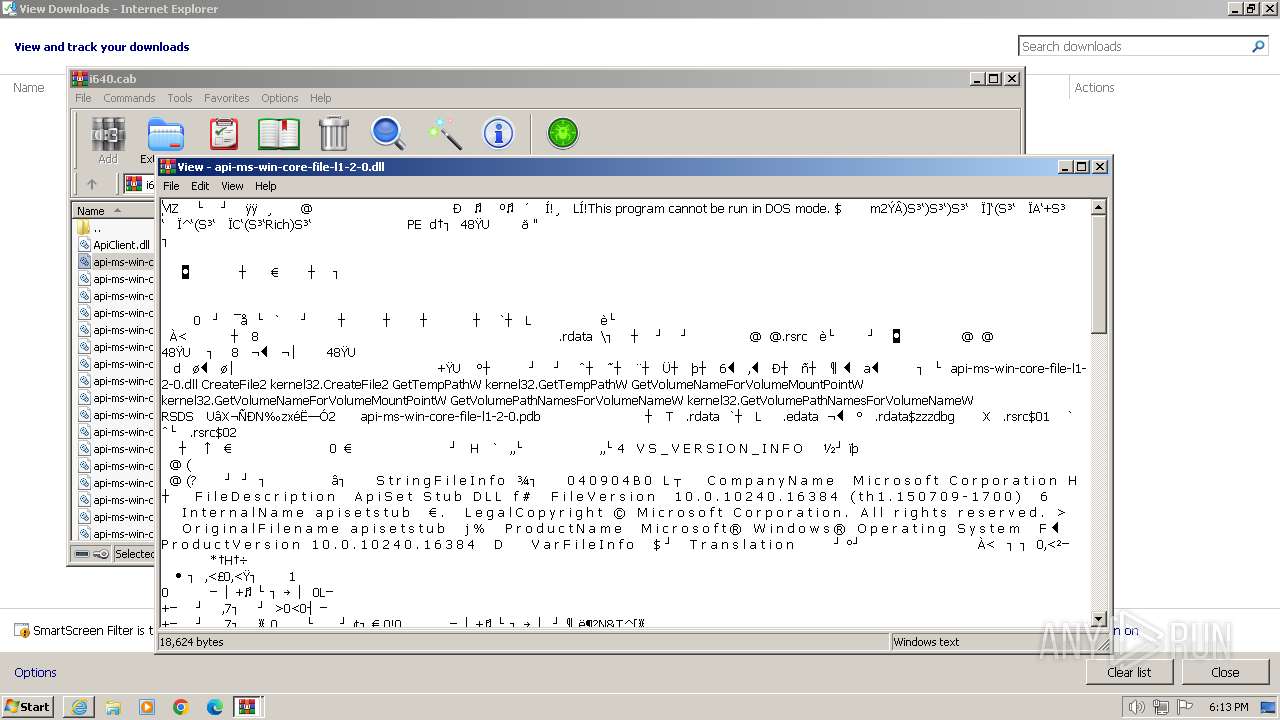
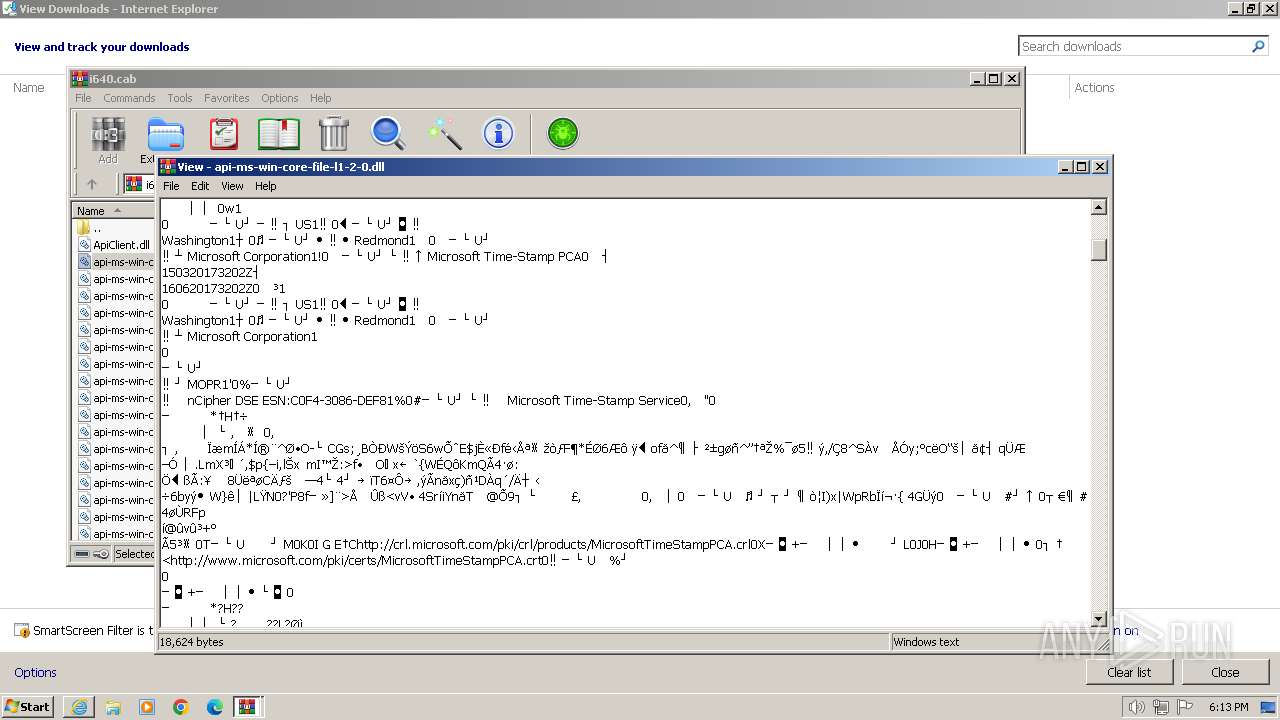
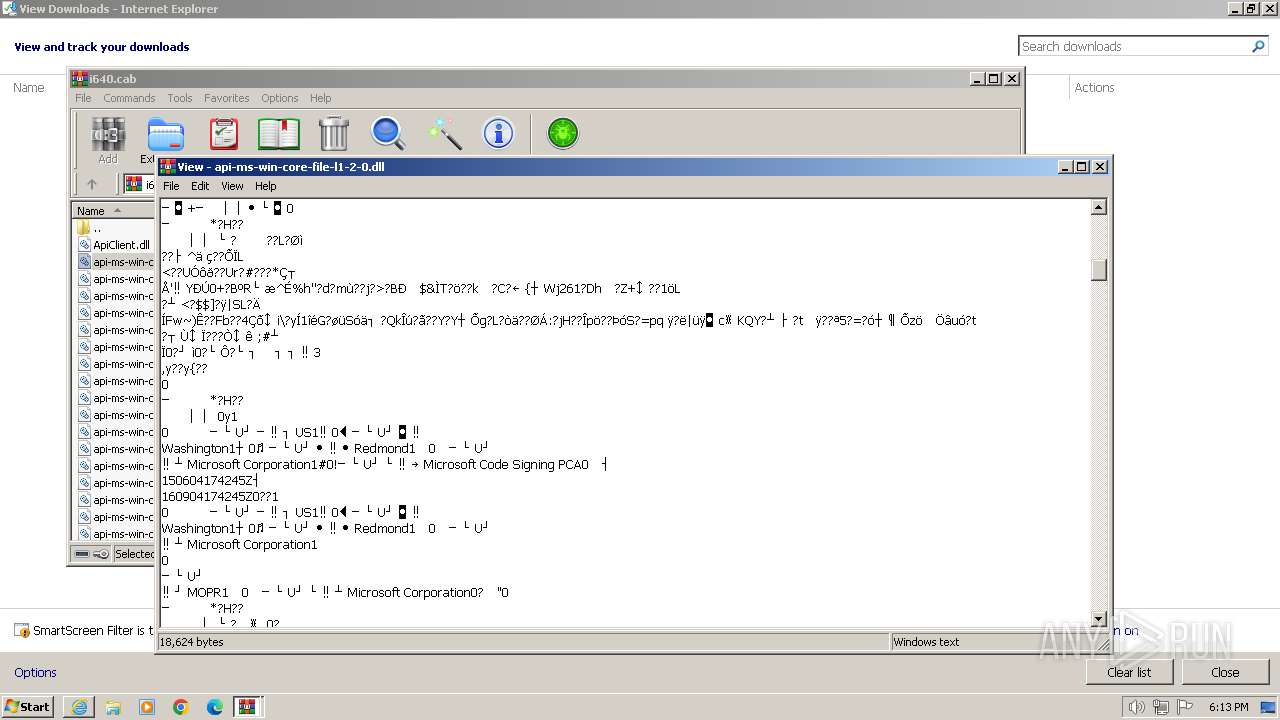
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 956 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3672 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://f.c2r.ts.cdn.office.net/pr/64256afe-f5d9-4f86-8936-8840a6a4f5be/Office/Data/16.0.17425.20008/i640.cab" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3692 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3672 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
25 283
Read events
24 996
Write events
249
Delete events
38
Modification events
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31094129 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31094129 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
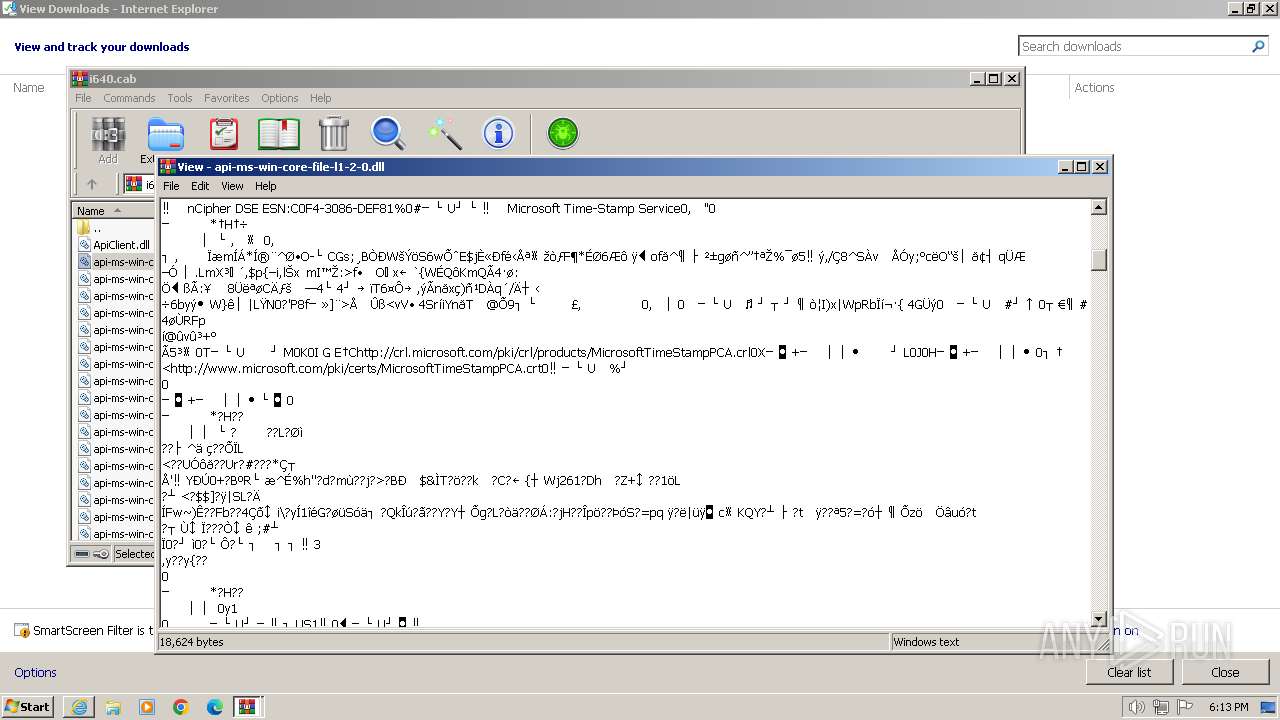
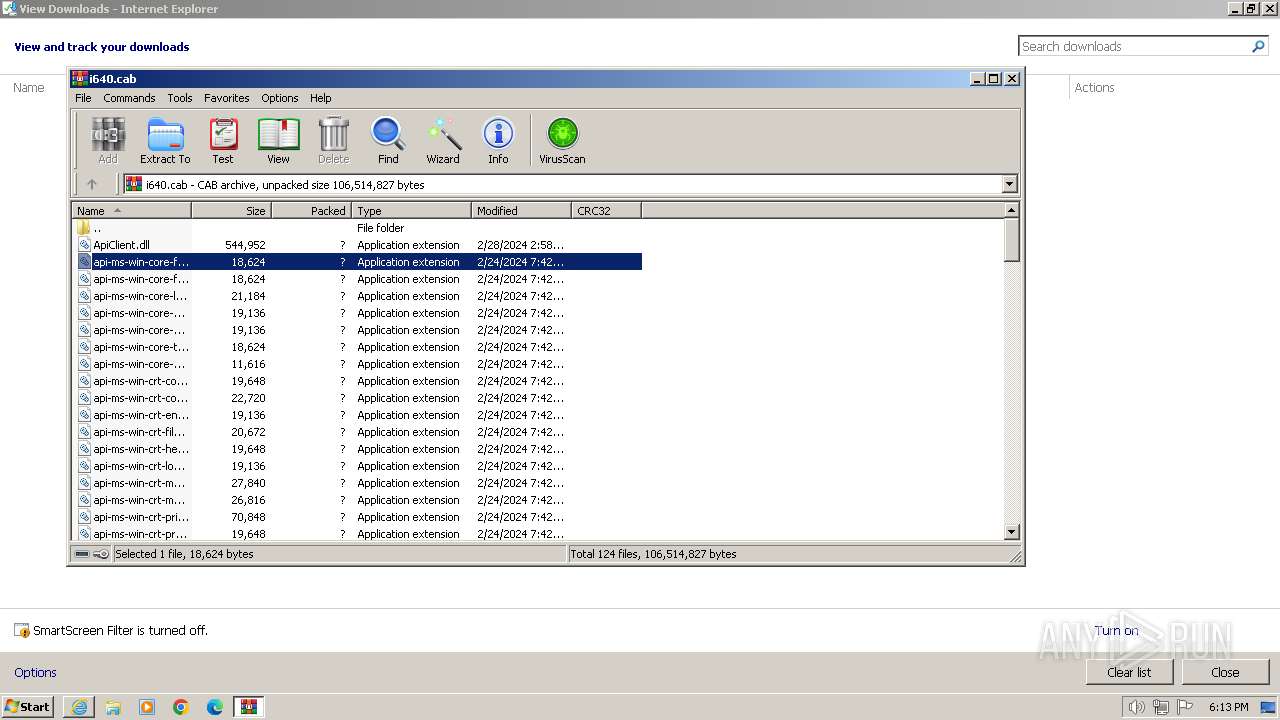
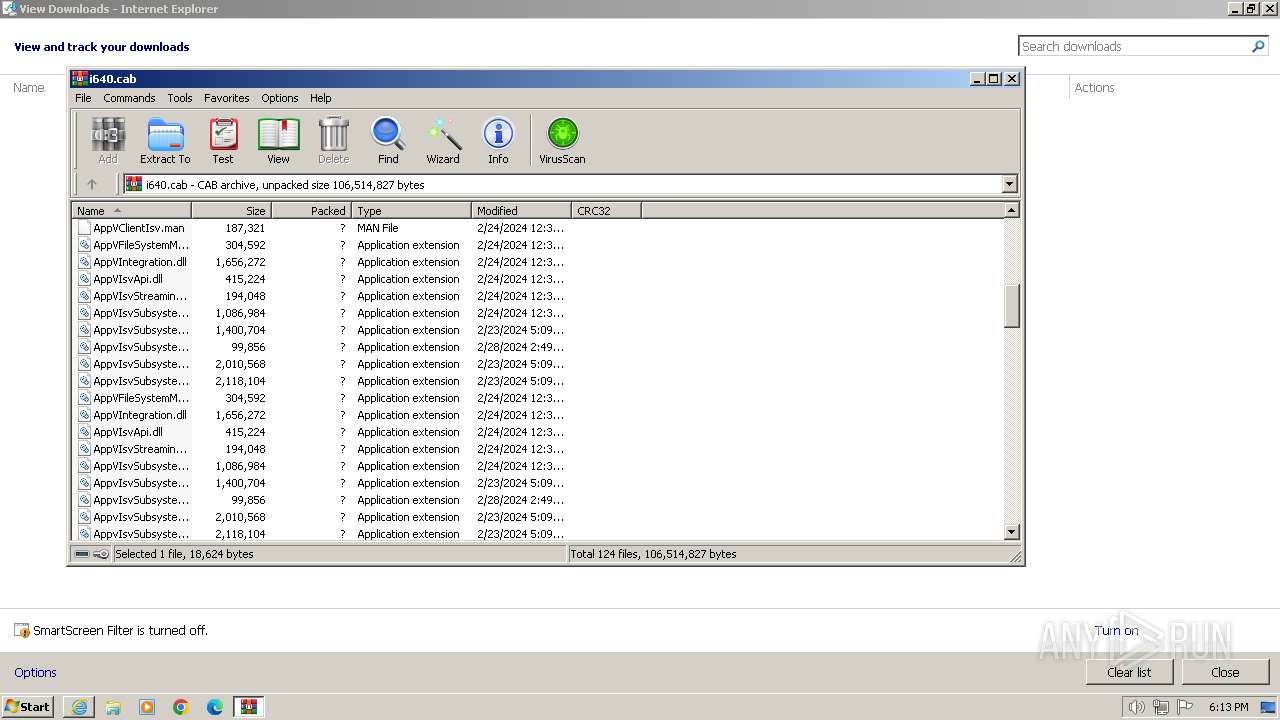
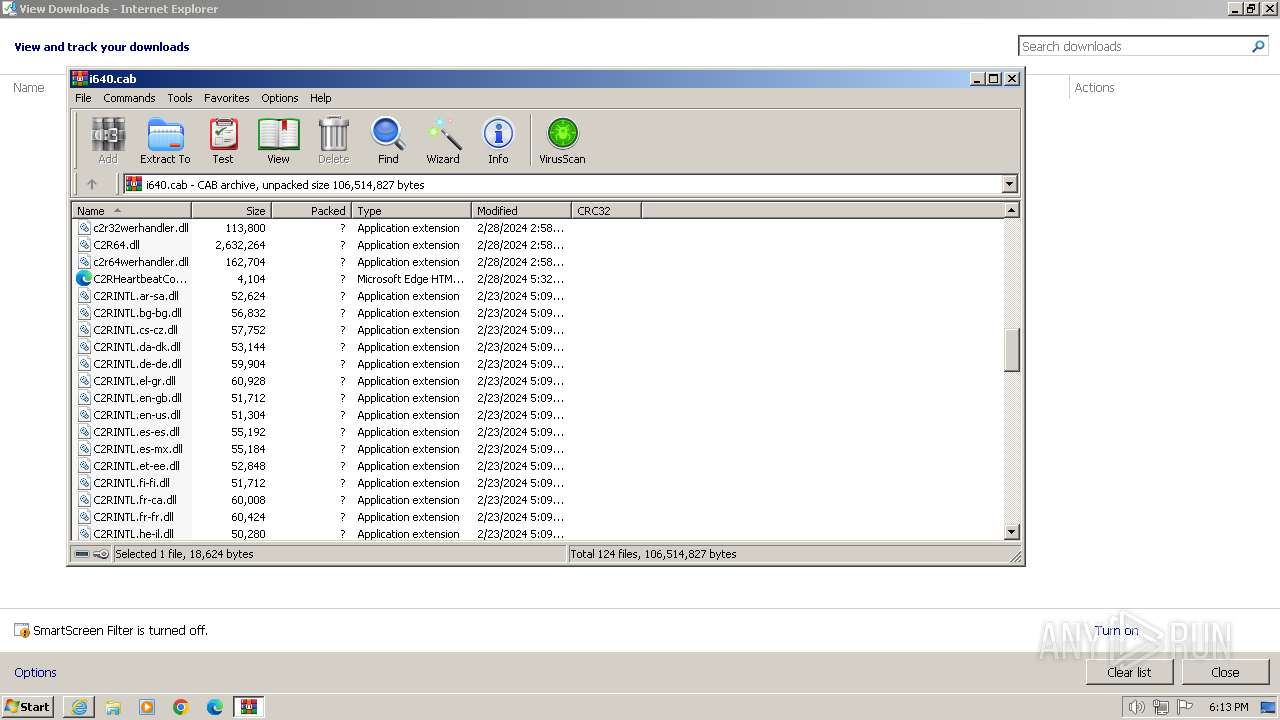
Executable files
225
Suspicious files
18
Text files
34
Unknown types
4
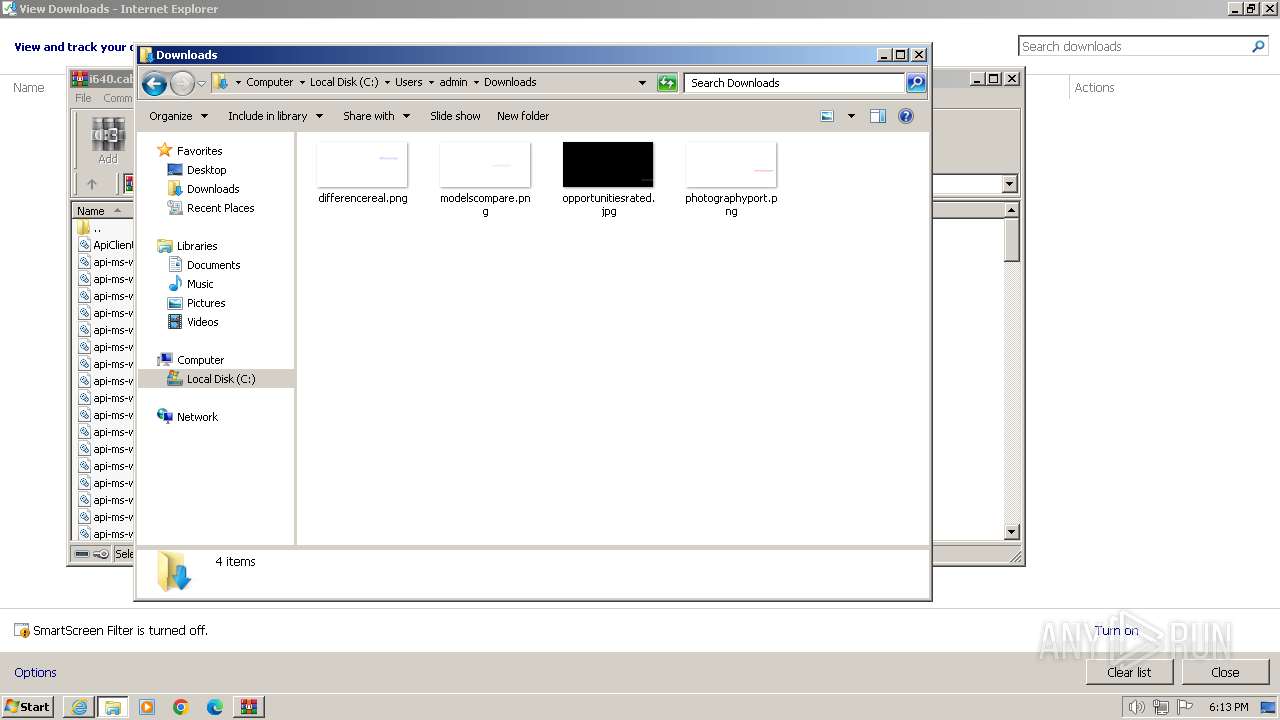
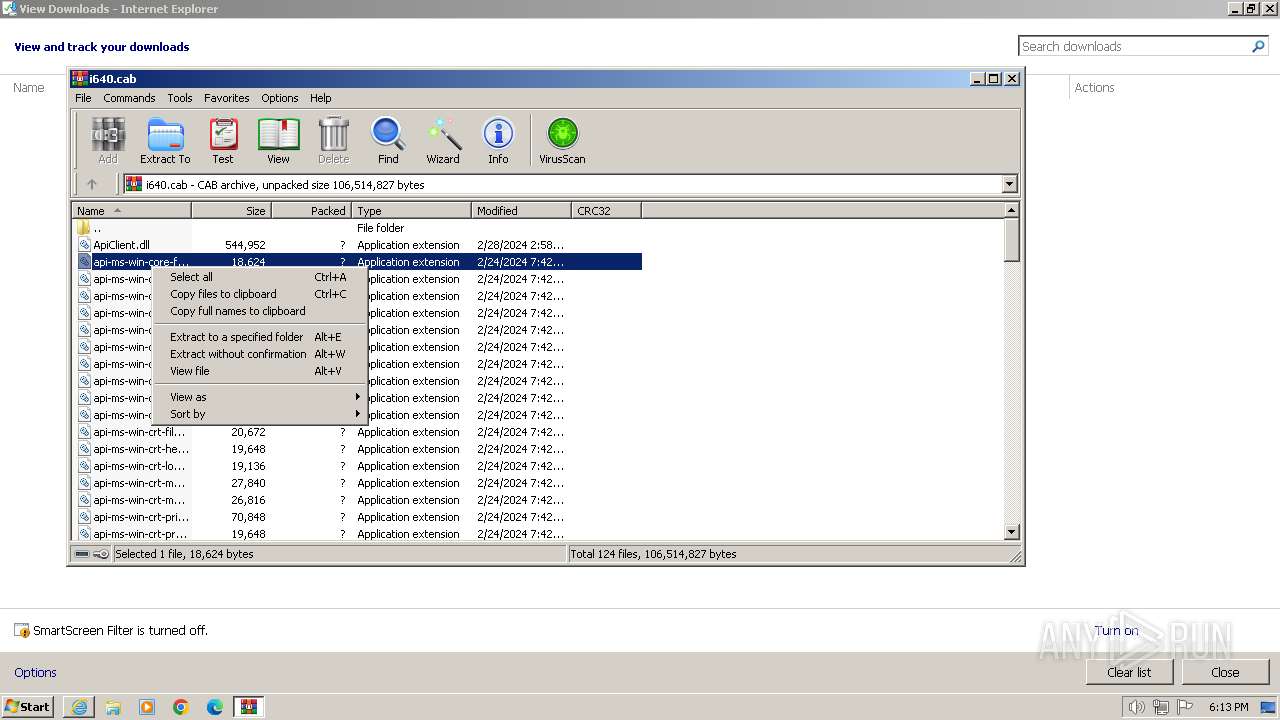
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8BD9D0556C2B74C4.TMP | binary | |
MD5:A507705D9BBC188C22C11FAAB9C0F6F8 | SHA256:CE560CDBE5D08A419C2354105F045E5FE56602B68CD6413C0AE2B6FB3A96FE0B | |||
| 3692 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\i640[1].cab | compressed | |
MD5:D299186A7A7AFCDC3E530947B94F95AC | SHA256:9E23BB89EC4103D073ED731CE75C2B0025BCCCD59AA5659564CE9C9936338A21 | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verAB4E.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{1CBD39F9-E165-11EE-AE0A-12A9866C77DE}.dat | binary | |
MD5:9D3DA14EE2BB13EA39A0465DBB6D450C | SHA256:398F1D37E23FC3393BCB2977C124D51964BB8CBBD033F2D3B06E7D1A44629B61 | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:933B881E04584122E8CD768DEF29FE6A | SHA256:6C1579AABB1CF90EC423F624A4D858BF2C22387CA34527EBD5BE8611D52F50EF | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_C0427F5F77D9B3A439FC620EDAAB6177 | binary | |
MD5:2F66AE4DDF4D862B5B8F18E07EE9509E | SHA256:301D02C79A0814521AB733FB9A4F71265BBDC8237945185B586C509A9ADB8259 | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_C0427F5F77D9B3A439FC620EDAAB6177 | der | |
MD5:CD0A27E1832569358A1912A19D4493D5 | SHA256:023B08365071586AB1328EF7771D915801C78F2EE90609128FF477DE0942758E | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:34928880ABF943839A265FD35B588655 | SHA256:3C6DC265557131E65AADE33CE29F44D93A83353C6FE900326DE46879811E31B6 | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\i640.cab | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
32
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3692 | iexplore.exe | GET | — | 23.50.131.218:80 | http://f.c2r.ts.cdn.office.net/pr/64256afe-f5d9-4f86-8936-8840a6a4f5be/Office/Data/16.0.17425.20008/i640.cab | unknown | — | — | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
3672 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | unknown | binary | 471 b | unknown |
3692 | iexplore.exe | GET | 200 | 23.50.131.218:80 | http://f.c2r.ts.cdn.office.net/pr/64256afe-f5d9-4f86-8936-8840a6a4f5be/Office/Data/16.0.17425.20008/i640.cab | unknown | compressed | 32.0 Mb | unknown |
3672 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
3672 | iexplore.exe | GET | 304 | 23.48.23.67:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?18014fff35250a83 | unknown | — | — | unknown |
3672 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
3672 | iexplore.exe | GET | 304 | 23.48.23.7:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?70b4a85d87201c80 | unknown | — | — | unknown |
1080 | svchost.exe | GET | 200 | 23.48.23.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e90c163b6659448e | unknown | compressed | 67.5 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3692 | iexplore.exe | 23.50.131.218:80 | f.c2r.ts.cdn.office.net | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3692 | iexplore.exe | 23.50.131.200:80 | f.c2r.ts.cdn.office.net | Akamai International B.V. | DE | unknown |
3672 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
3672 | iexplore.exe | 23.48.23.8:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3672 | iexplore.exe | 23.48.23.67:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3672 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
f.c2r.ts.cdn.office.net |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
dns.msftncsi.com |
| shared |