| URL: | global.ketchcdn.com/web/v3/consent/ngrok/update |
| Full analysis: | https://app.any.run/tasks/922543cd-4ff3-48a1-8ba3-7c39516e627e |
| Verdict: | Malicious activity |
| Analysis date: | April 27, 2024, 13:41:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 38390C68A062691C8EED891BCD1F69EB |
| SHA1: | 8B273D5E13C1E6DB351E62A809B71939E9F73B42 |
| SHA256: | E5DA327C2F5C58EE760745F504E7570616B2BD5AE1AEFAF86F0BD2A09133B29B |
| SSDEEP: | 3:6r7oKIJALxeQCKACAn:64KiE4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
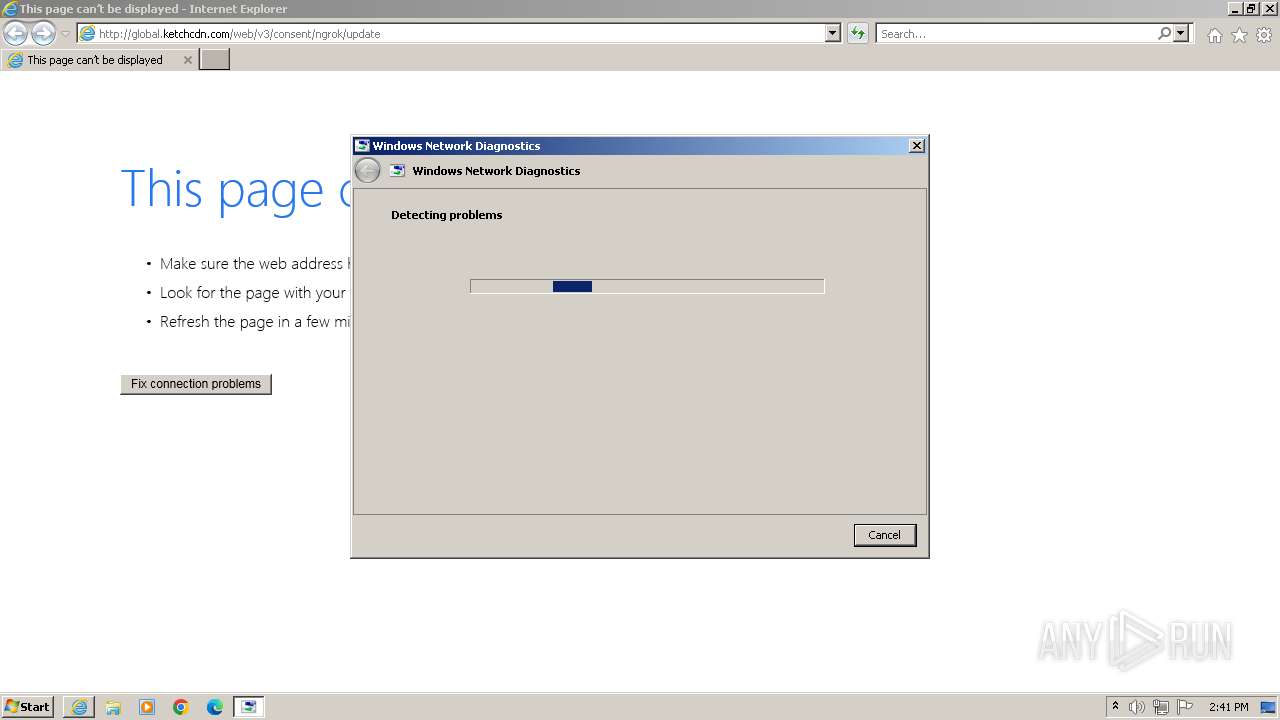
Reads the Internet Settings
- sdiagnhost.exe (PID: 1488)
INFO
Application launched itself
- iexplore.exe (PID: 3984)
Reads the software policy settings
- msdt.exe (PID: 1580)
Reads security settings of Internet Explorer
- msdt.exe (PID: 1580)
- sdiagnhost.exe (PID: 1488)
Create files in a temporary directory
- msdt.exe (PID: 1580)
Checks supported languages
- wmpnscfg.exe (PID: 1592)
Manual execution by a user
- wmpnscfg.exe (PID: 1592)
Drops the executable file immediately after the start
- msdt.exe (PID: 1580)
Reads the computer name
- wmpnscfg.exe (PID: 1592)
Creates files or folders in the user directory
- msdt.exe (PID: 1580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1580 | -modal 65856 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDF5073.tmp -ep NetworkDiagnosticsWeb | C:\Windows\System32\msdt.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 4294967295 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3984 | "C:\Program Files\Internet Explorer\iexplore.exe" "global.ketchcdn.com/web/v3/consent/ngrok/update" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4044 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3984 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
18 213
Read events
17 853
Write events
191
Delete events
169
Modification events
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31103144 | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31103144 | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
11
Text files
22
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:FA40F8FEC3A01DD561A75A08584B78BC | SHA256:33753775832F7F503861D9CF91F795E3E9246A7A8774E74D597E84F20B800632 | |||
| 3984 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3984 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\NDF5073.tmp | binary | |
MD5:479CE992C3905462BC8FD0E076B5418B | SHA256:EE4BC1E6066C8DC296235E055E6F76E7693F717A4F7BB03E3484DA6CE994342C | |||
| 1580 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_214bdc17-70df-42c8-a2b4-f87205624f1a\result\ResultReport.xml | — | |
MD5:— | SHA256:— | |||
| 1580 | msdt.exe | C:\Users\admin\AppData\Local\Diagnostics\460911090\2024042713.000\DebugReport.xml | — | |
MD5:— | SHA256:— | |||
| 3984 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:A7C0915D6FED4419FBAFA515916A1709 | SHA256:4BAD789D309F123BCBF2F0B3A89A5ED163D64E34B57FB8027970AE0106F87288 | |||
| 3984 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:23C901D115CECD2AD39B7483F420BCF6 | SHA256:02E13B2DFBA01C8B0425C955945FFE6749D5BF606CB86A9380E9E3E53A332BB8 | |||
| 1580 | msdt.exe | C:\Users\admin\AppData\Local\Diagnostics\460911090\2024042713.000\NetworkDiagnostics.0.debugreport.xml | — | |
MD5:— | SHA256:— | |||
| 3984 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1580 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_214bdc17-70df-42c8-a2b4-f87205624f1a\UtilitySetConstants.ps1 | text | |
MD5:0C75AE5E75C3E181D13768909C8240BA | SHA256:DE5C231C645D3AE1E13694284997721509F5DE64EE5C96C966CDFDA9E294DB3F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
33
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3984 | iexplore.exe | GET | 304 | 23.53.40.42:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c21588876f974d24 | unknown | — | — | unknown |
3984 | iexplore.exe | GET | 304 | 23.53.40.42:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8644b833ad892dd7 | unknown | — | — | unknown |
3984 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
1088 | svchost.exe | GET | 304 | 23.53.40.42:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b7b91cedcdb05bd4 | unknown | — | — | unknown |
3984 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
4044 | iexplore.exe | GET | 301 | 151.101.1.91:80 | http://global.ketchcdn.com/web/v3/consent/ngrok/update | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4044 | iexplore.exe | 151.101.1.91:80 | global.ketchcdn.com | FASTLY | US | unknown |
4044 | iexplore.exe | 151.101.1.91:443 | global.ketchcdn.com | FASTLY | US | unknown |
3984 | iexplore.exe | 92.122.215.95:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3984 | iexplore.exe | 23.53.40.42:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3984 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
840 | svchost.exe | 151.101.1.91:80 | global.ketchcdn.com | FASTLY | US | unknown |
3984 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
global.ketchcdn.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |