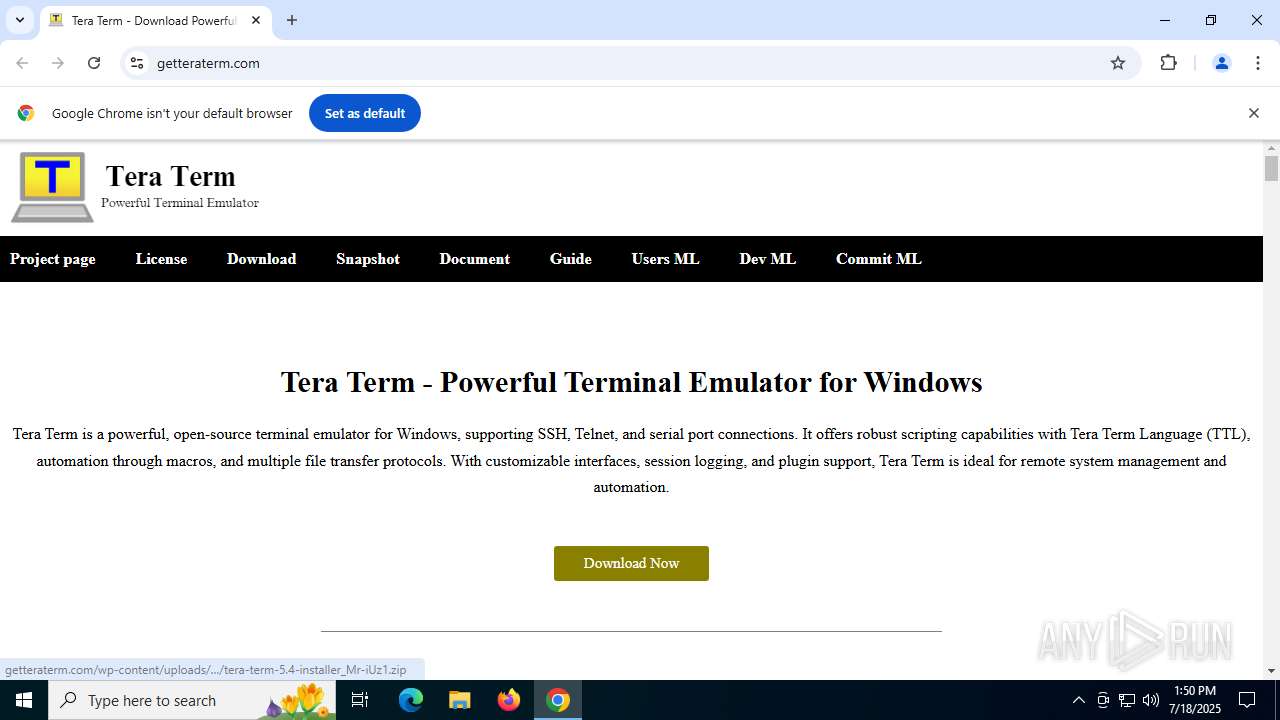
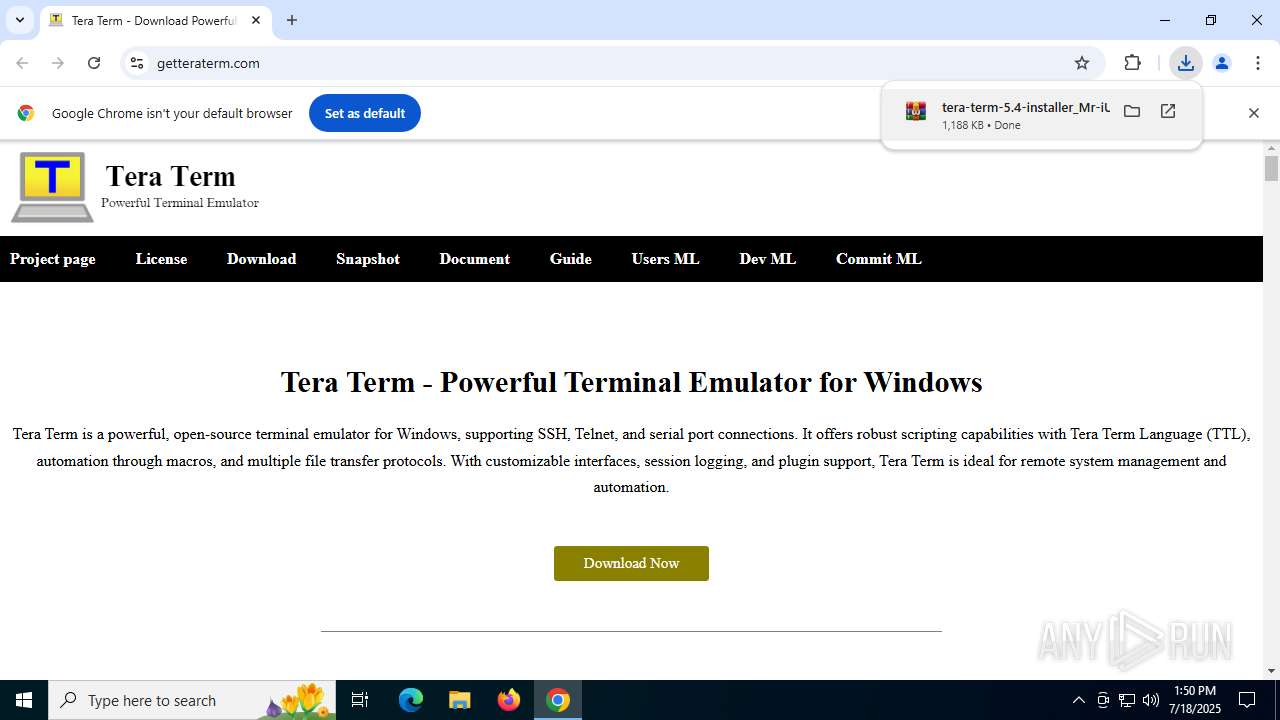
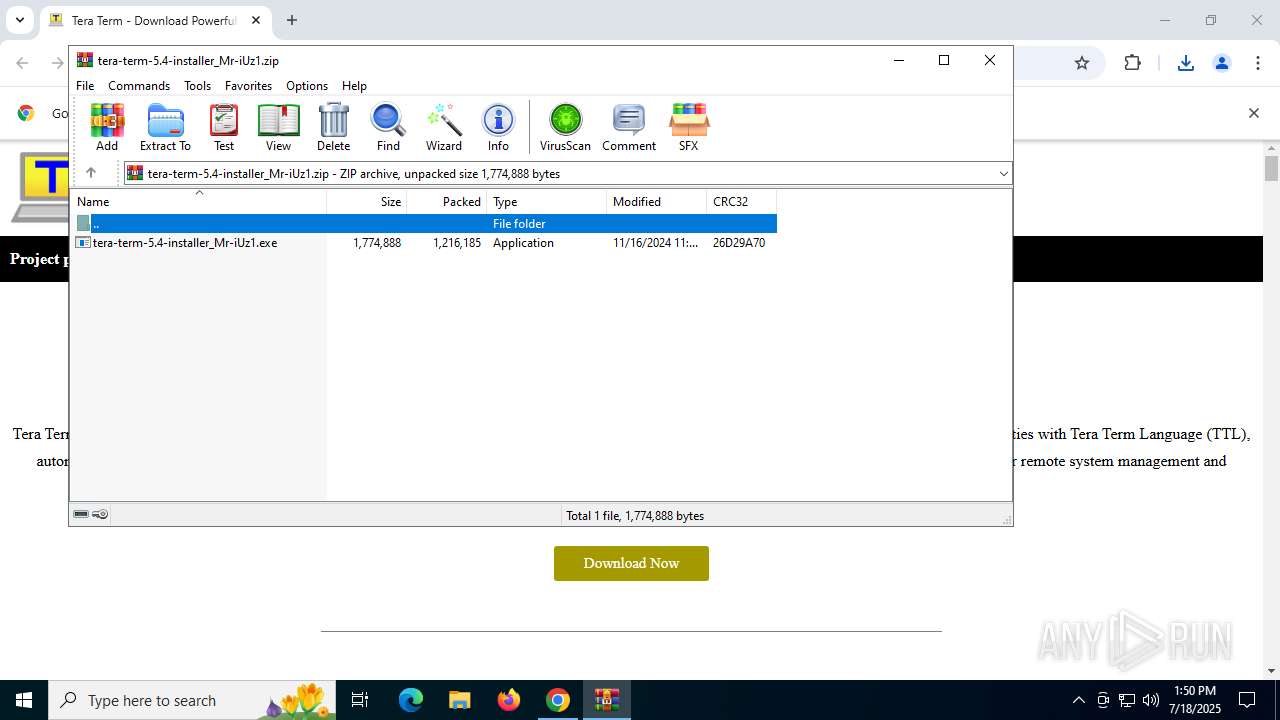
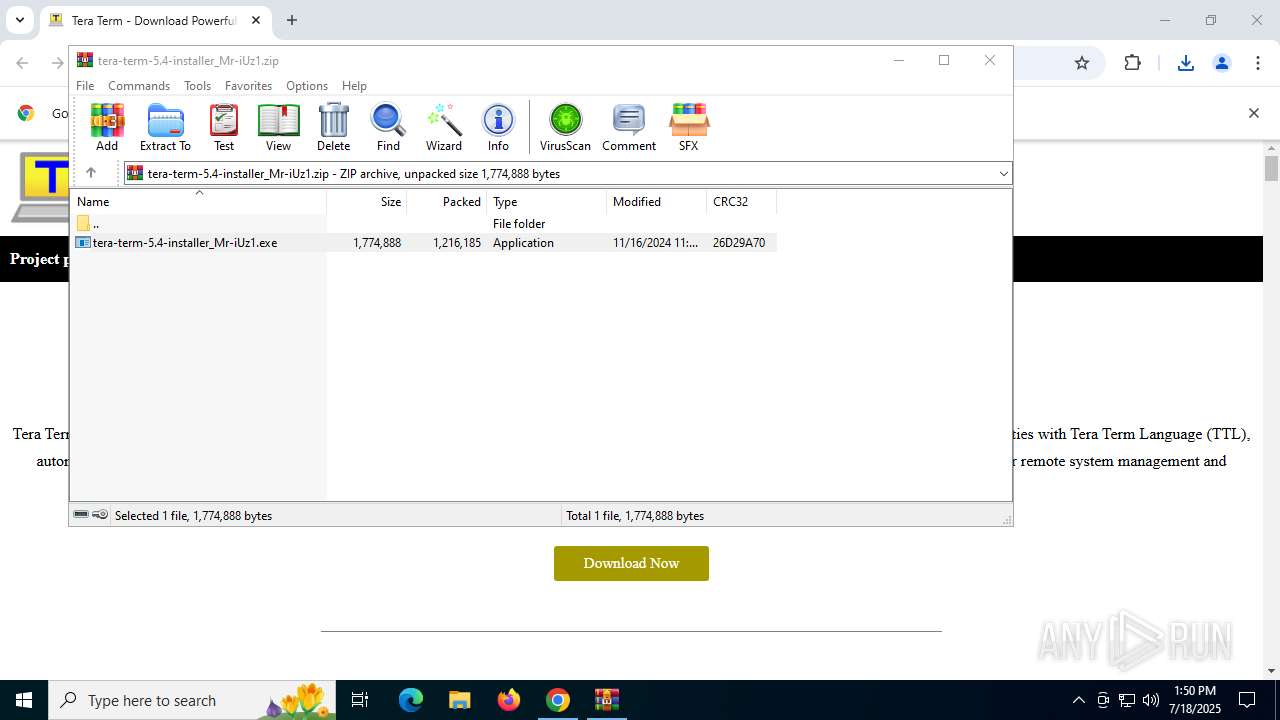
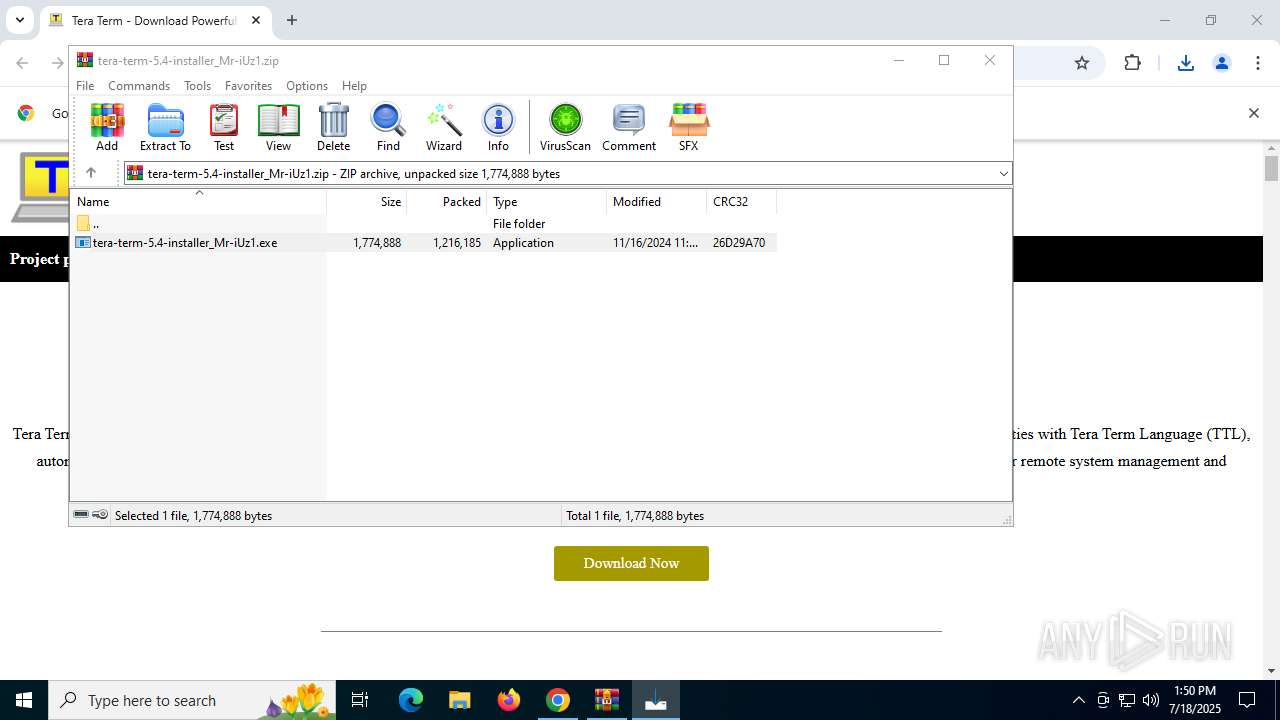
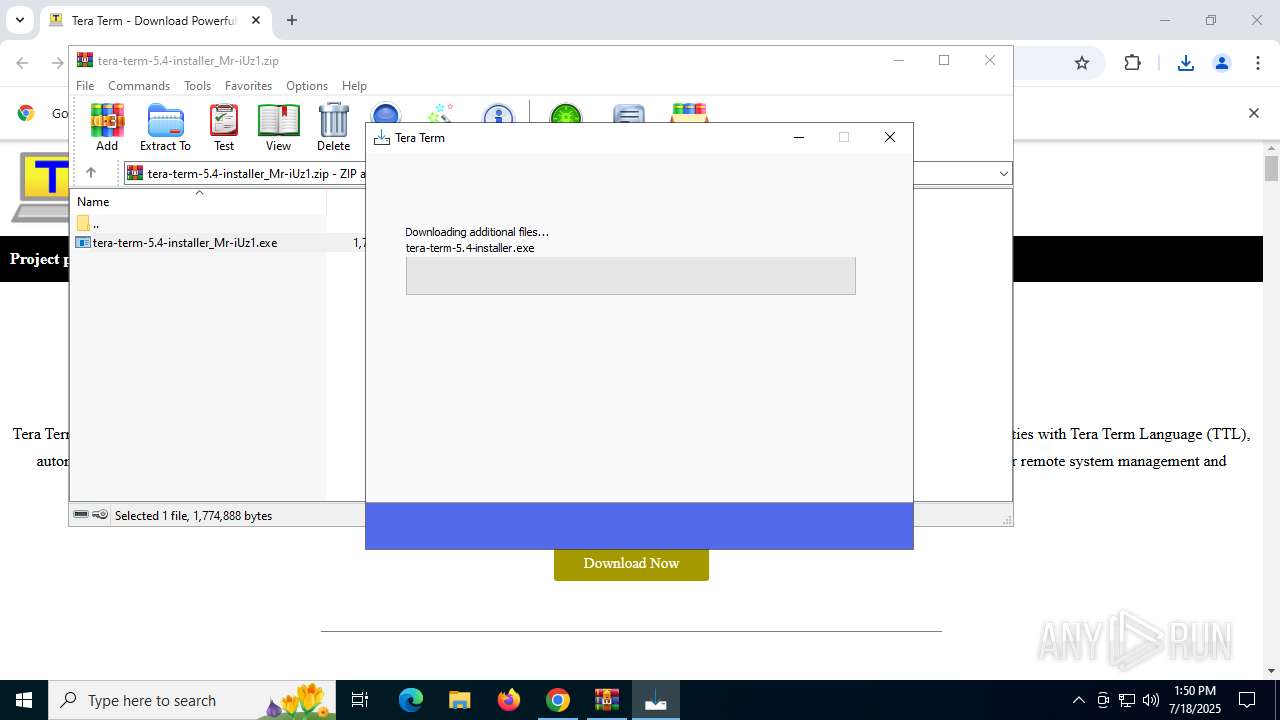
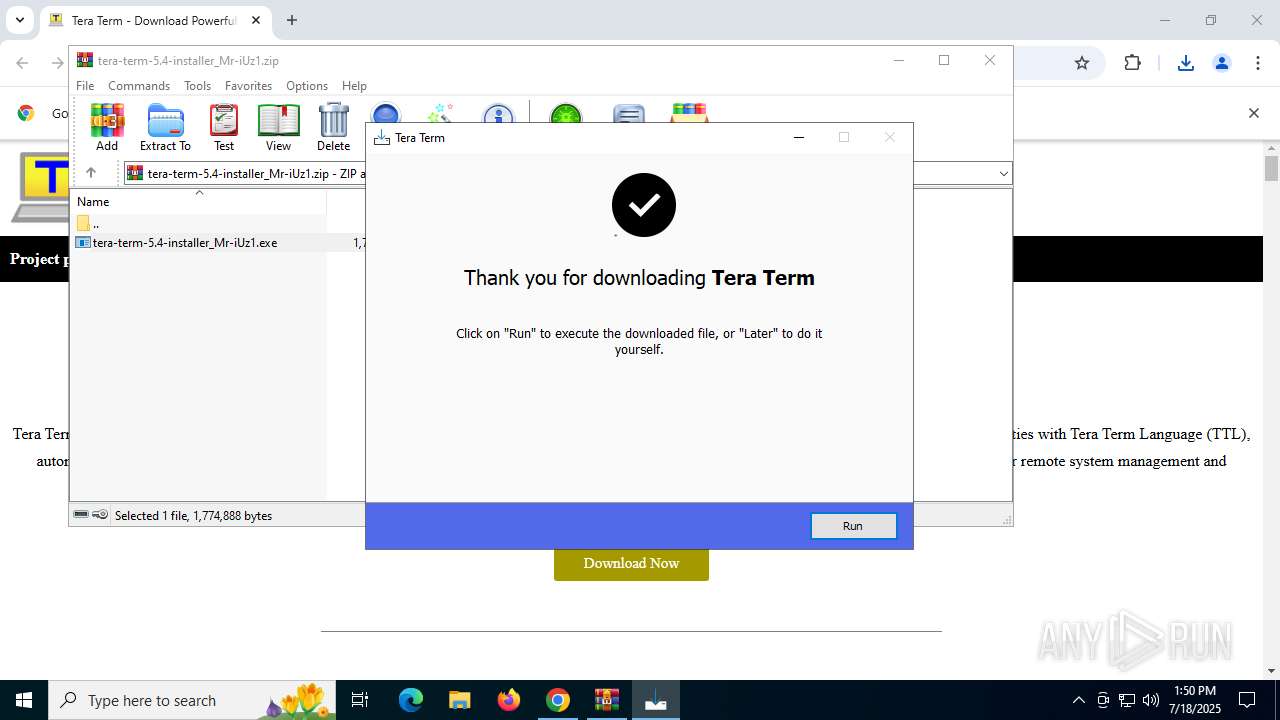
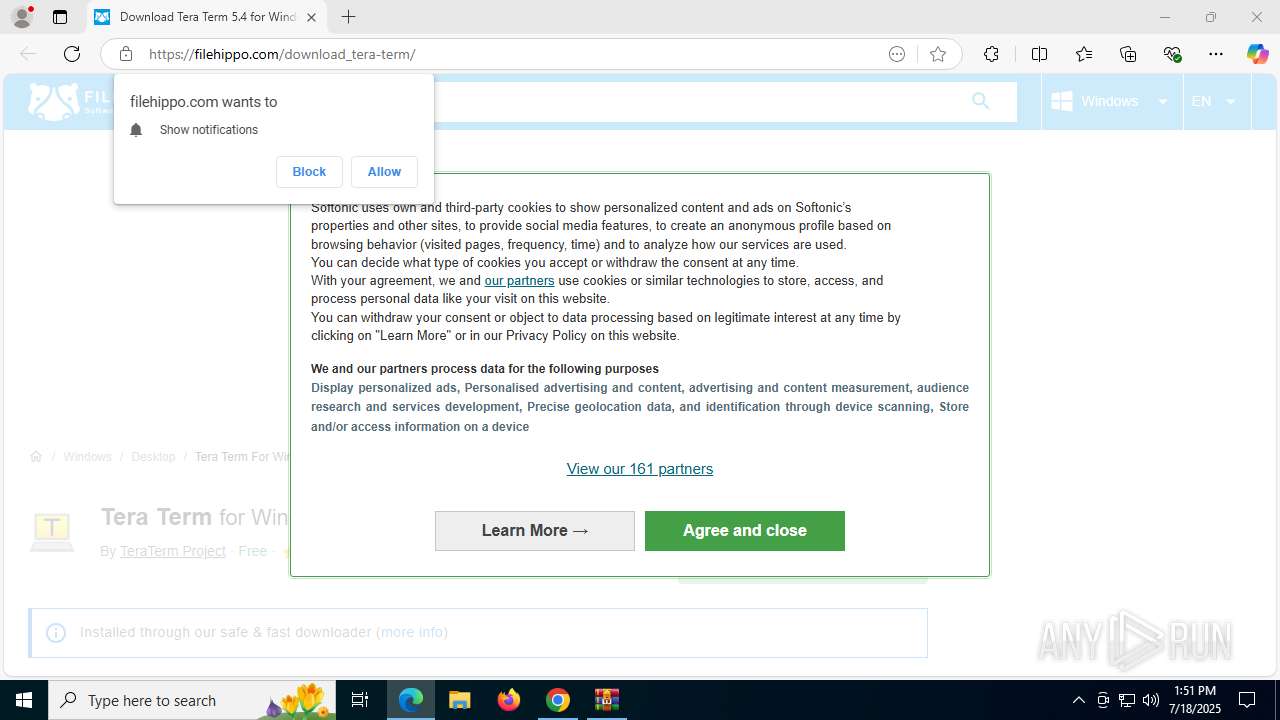
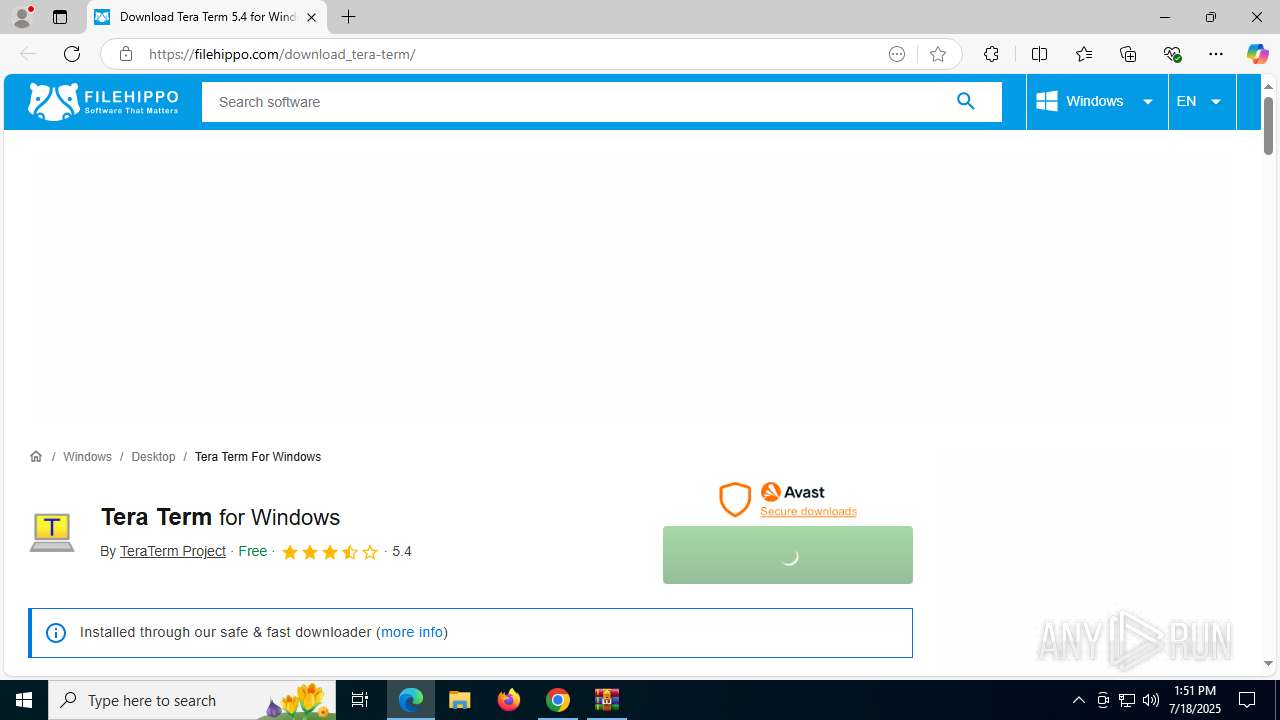
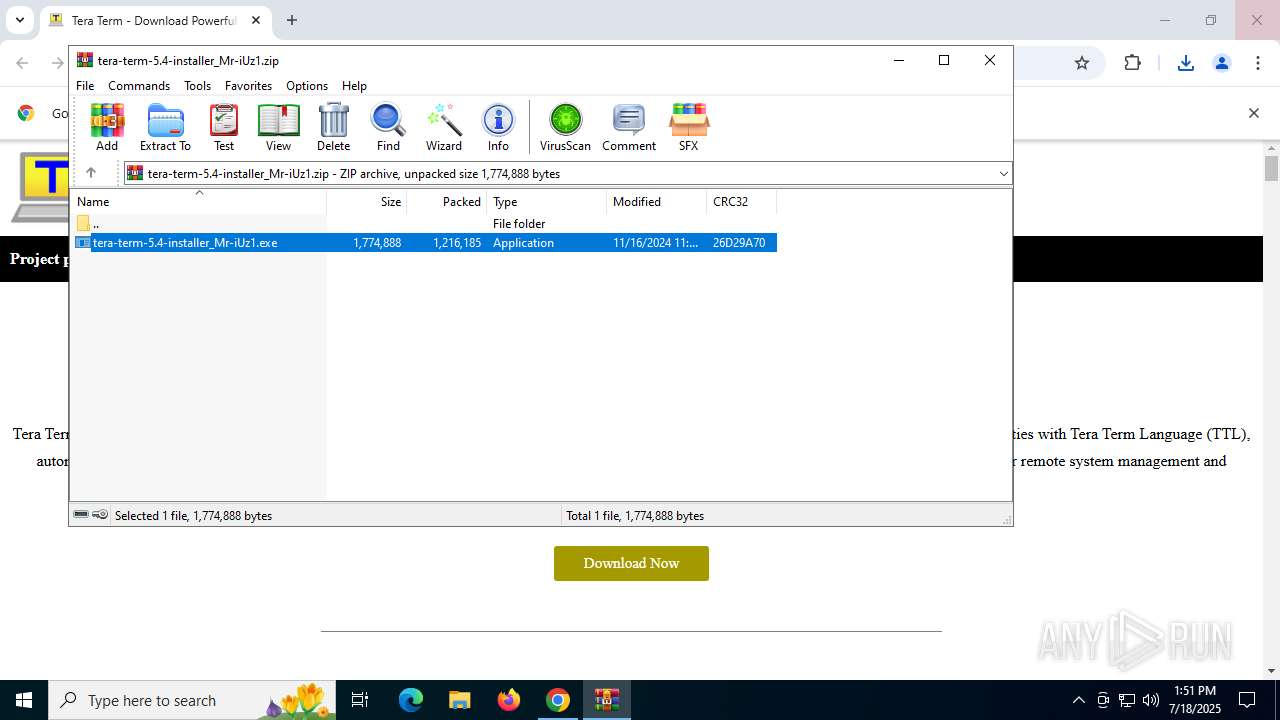
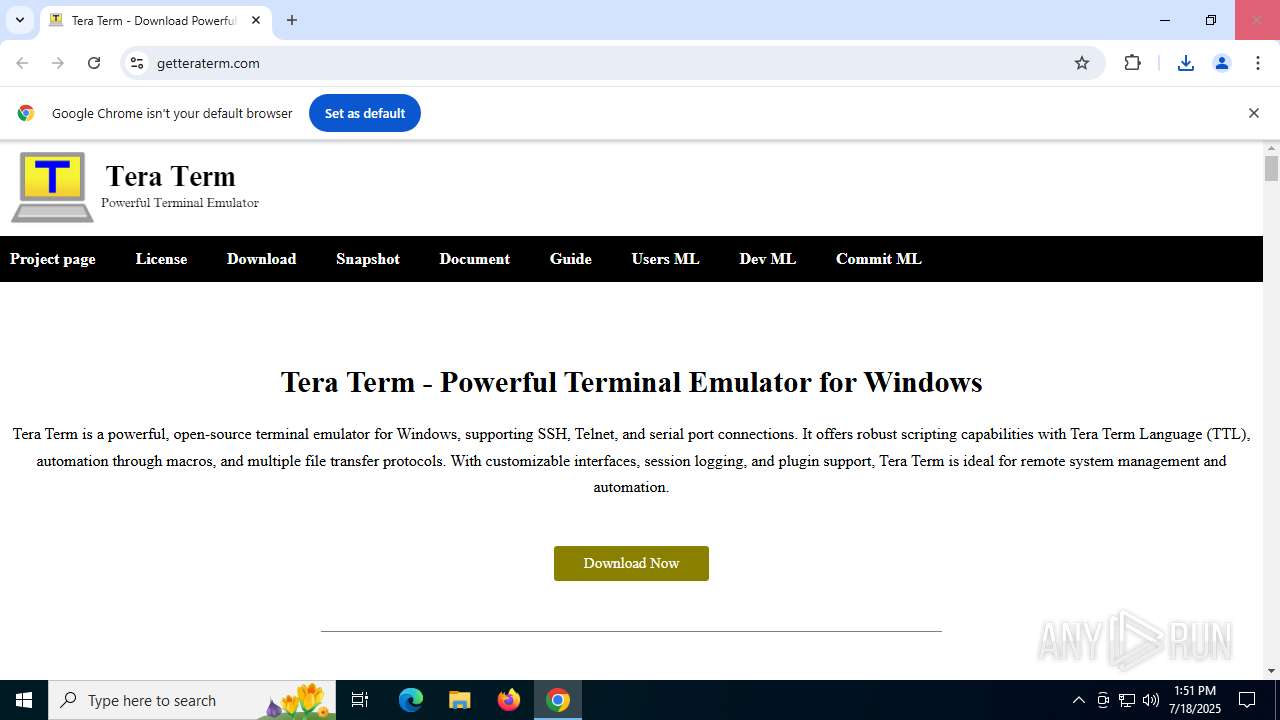
| URL: | getteraterm.com |
| Full analysis: | https://app.any.run/tasks/319c95de-492a-4fbf-9eba-64cccdadd621 |
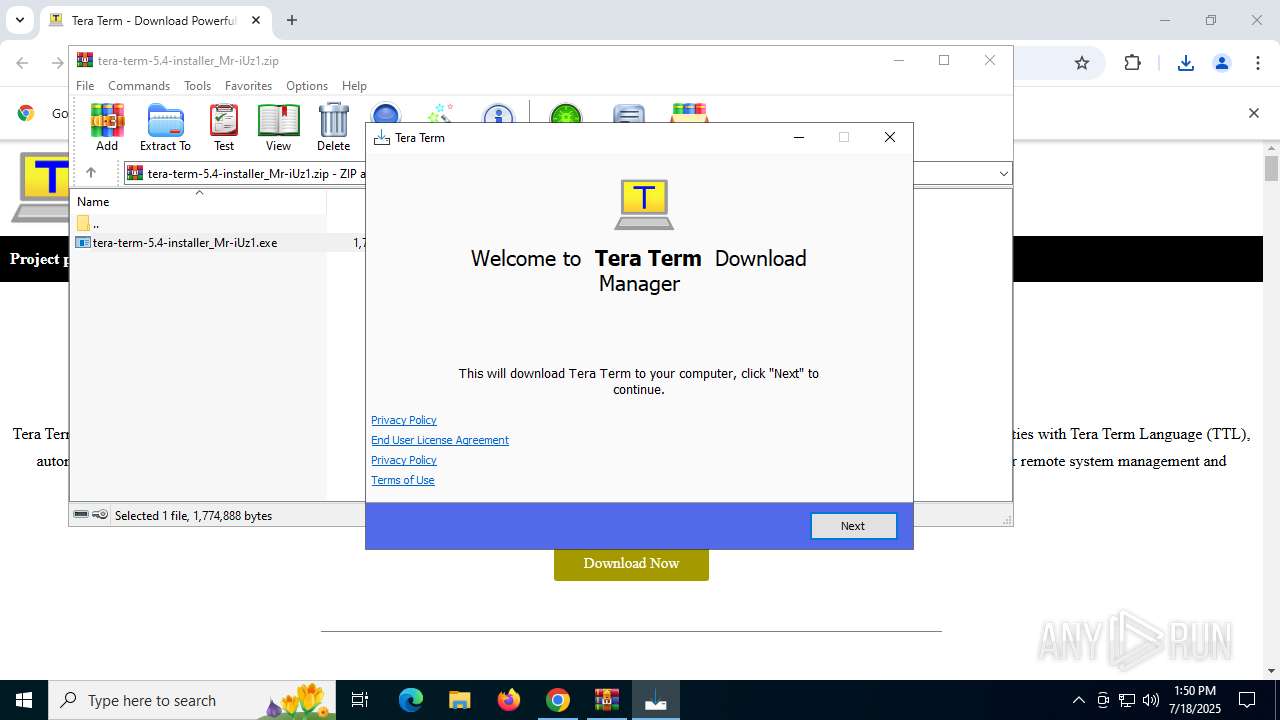
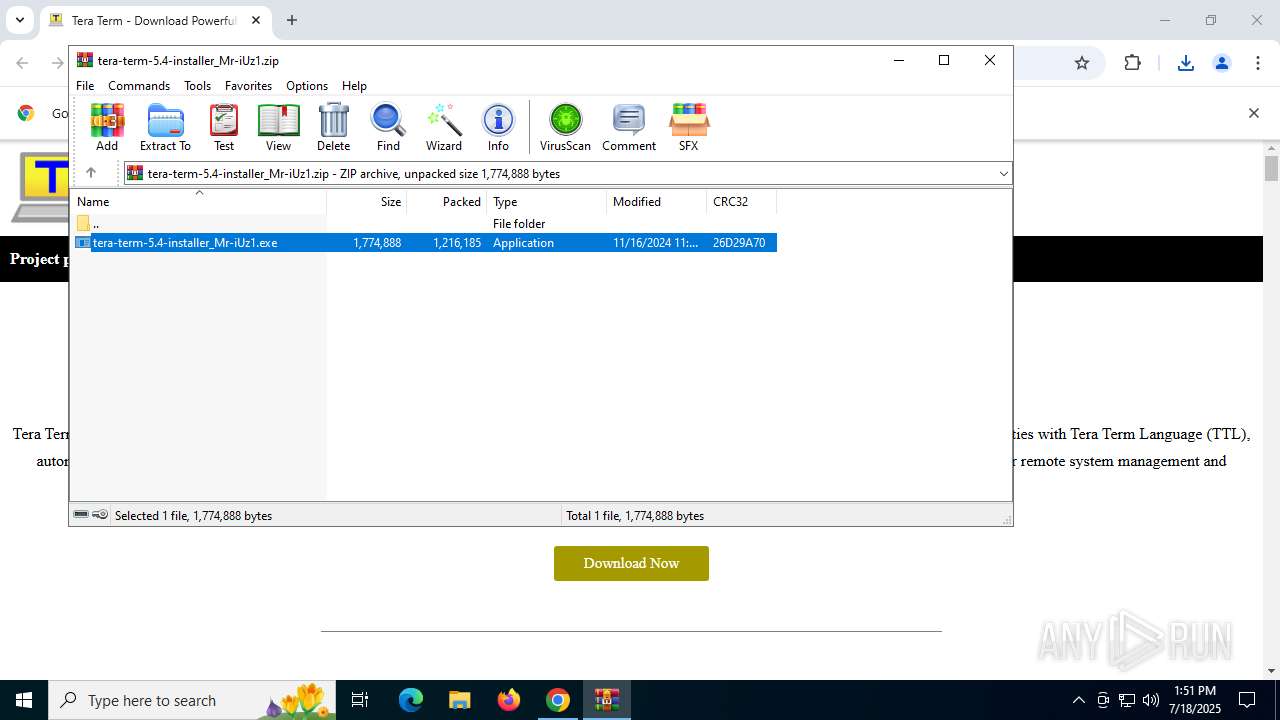
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2025, 13:50:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7E4A7E6E787B631DFBFA4EF831BD101E |
| SHA1: | 5D0B28AAA1DA901D7C83BE7004DCDC789DC51572 |
| SHA256: | E5D8A02E56227015D8432CB8D9199456F41149F25AFEA27827B1F1EA1932BEE8 |
| SSDEEP: | 3:cIGT:NGT |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7964)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- saBSI.exe (PID: 1880)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 7340)
- saBSI.exe (PID: 7580)
- installer.exe (PID: 1380)
- uihost.exe (PID: 6776)
Executable content was dropped or overwritten
- tera-term-5.4-installer_Mr-iUz1.exe (PID: 7404)
- tera-term-5.4-installer_Mr-iUz1.exe (PID: 5564)
- saBSI.exe (PID: 1880)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- saBSI.exe (PID: 7580)
- installer.exe (PID: 5468)
- installer.exe (PID: 1380)
Reads the Windows owner or organization settings
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
Adds/modifies Windows certificates
- saBSI.exe (PID: 1880)
- servicehost.exe (PID: 8828)
The process verifies whether the antivirus software is installed
- saBSI.exe (PID: 7580)
- installer.exe (PID: 5468)
- installer.exe (PID: 1380)
- servicehost.exe (PID: 8828)
- uihost.exe (PID: 6776)
- cmd.exe (PID: 9440)
- cmd.exe (PID: 6764)
- updater.exe (PID: 8292)
Executes application which crashes
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
The process creates files with name similar to system file names
- installer.exe (PID: 1380)
Creates/Modifies COM task schedule object
- installer.exe (PID: 1380)
Creates a software uninstall entry
- installer.exe (PID: 1380)
- servicehost.exe (PID: 8828)
Process drops legitimate windows executable
- installer.exe (PID: 1380)
Executes as Windows Service
- servicehost.exe (PID: 8828)
Reads Mozilla Firefox installation path
- uihost.exe (PID: 6776)
- servicehost.exe (PID: 8828)
Searches for installed software
- updater.exe (PID: 8292)
Starts CMD.EXE for commands execution
- updater.exe (PID: 8292)
INFO
Application launched itself
- chrome.exe (PID: 6796)
- msedge.exe (PID: 7636)
- msedge.exe (PID: 7616)
- msedge.exe (PID: 3396)
- msedge.exe (PID: 9636)
- msedge.exe (PID: 3392)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7964)
- chrome.exe (PID: 7576)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6796)
Reads the computer name
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 7340)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- saBSI.exe (PID: 1880)
- saBSI.exe (PID: 7580)
- installer.exe (PID: 1380)
- identity_helper.exe (PID: 8584)
- servicehost.exe (PID: 8828)
- uihost.exe (PID: 6776)
- identity_helper.exe (PID: 10200)
- updater.exe (PID: 8292)
- identity_helper.exe (PID: 5188)
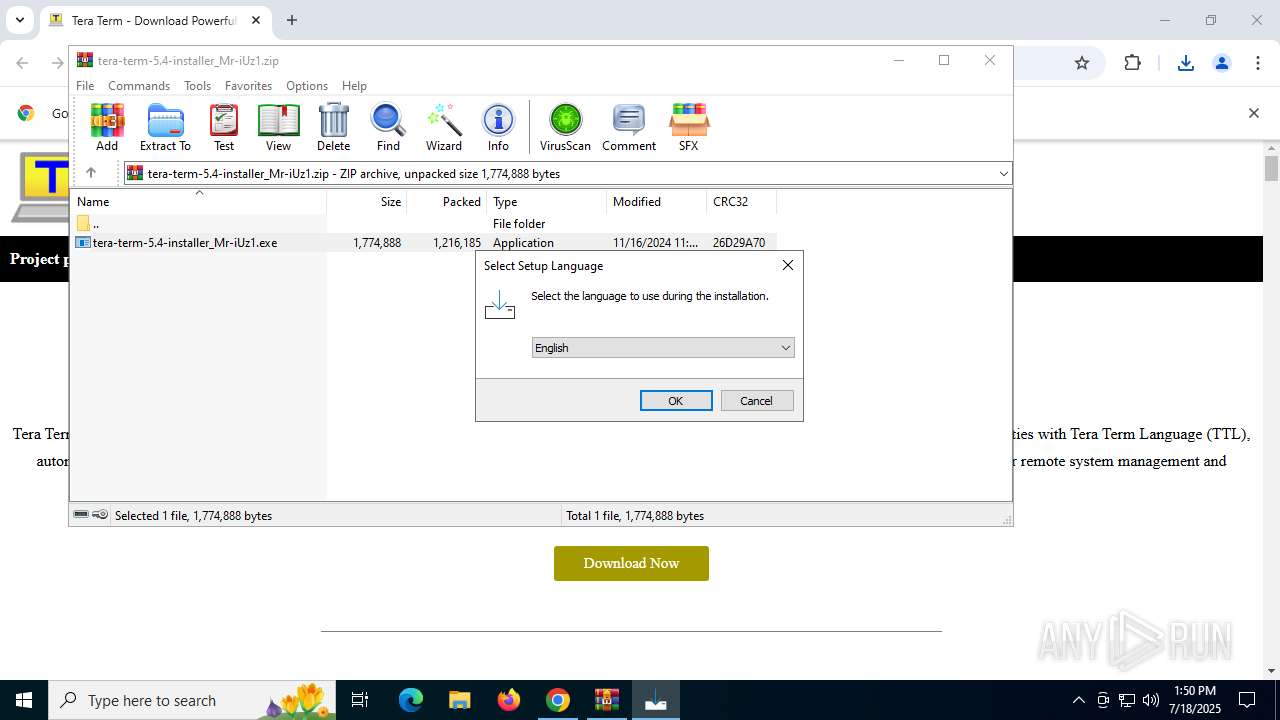
Checks supported languages
- tera-term-5.4-installer_Mr-iUz1.exe (PID: 7404)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 7340)
- tera-term-5.4-installer_Mr-iUz1.exe (PID: 5564)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- saBSI.exe (PID: 1880)
- installer.exe (PID: 1380)
- installer.exe (PID: 5468)
- identity_helper.exe (PID: 8584)
- servicehost.exe (PID: 8828)
- uihost.exe (PID: 6776)
- saBSI.exe (PID: 7580)
- identity_helper.exe (PID: 10200)
- updater.exe (PID: 8292)
- identity_helper.exe (PID: 5188)
Create files in a temporary directory
- tera-term-5.4-installer_Mr-iUz1.exe (PID: 7404)
- tera-term-5.4-installer_Mr-iUz1.exe (PID: 5564)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- saBSI.exe (PID: 7580)
- installer.exe (PID: 1380)
Process checks computer location settings
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 7340)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- servicehost.exe (PID: 8828)
Reads the software policy settings
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- saBSI.exe (PID: 1880)
- saBSI.exe (PID: 7580)
- installer.exe (PID: 1380)
- WerFault.exe (PID: 5184)
- WerFault.exe (PID: 8384)
- servicehost.exe (PID: 8828)
- updater.exe (PID: 8292)
- uihost.exe (PID: 6776)
Reads the machine GUID from the registry
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- saBSI.exe (PID: 1880)
- saBSI.exe (PID: 7580)
- installer.exe (PID: 1380)
- servicehost.exe (PID: 8828)
- uihost.exe (PID: 6776)
- updater.exe (PID: 8292)
Detects InnoSetup installer (YARA)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 7340)
- tera-term-5.4-installer_Mr-iUz1.exe (PID: 7404)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- tera-term-5.4-installer_Mr-iUz1.exe (PID: 5564)
Checks proxy server information
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- saBSI.exe (PID: 1880)
- saBSI.exe (PID: 7580)
- WerFault.exe (PID: 5184)
- WerFault.exe (PID: 8384)
Compiled with Borland Delphi (YARA)
- tera-term-5.4-installer_Mr-iUz1.exe (PID: 7404)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 7340)
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- tera-term-5.4-installer_Mr-iUz1.exe (PID: 5564)
Creates files in the program directory
- saBSI.exe (PID: 1880)
- saBSI.exe (PID: 7580)
- installer.exe (PID: 5468)
- installer.exe (PID: 1380)
- servicehost.exe (PID: 8828)
- uihost.exe (PID: 6776)
The sample compiled with english language support
- tera-term-5.4-installer_Mr-iUz1.tmp (PID: 5372)
- saBSI.exe (PID: 1880)
- installer.exe (PID: 5468)
- installer.exe (PID: 1380)
Manual execution by a user
- msedge.exe (PID: 3396)
Reads Environment values
- identity_helper.exe (PID: 8584)
- identity_helper.exe (PID: 10200)
- identity_helper.exe (PID: 5188)
Creates files or folders in the user directory
- WerFault.exe (PID: 5184)
- WerFault.exe (PID: 8384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
232
Monitored processes
84
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2144,i,15775873752222950209,11479033013441941422,262144 --variations-seed-version --mojo-platform-channel-handle=2408 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x284,0x288,0x28c,0x27c,0x2a0,0x7ffc3f2ff208,0x7ffc3f2ff214,0x7ffc3f2ff220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=2952,i,16429336828154197326,5686848205405323577,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=2936,i,16429336828154197326,5686848205405323577,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
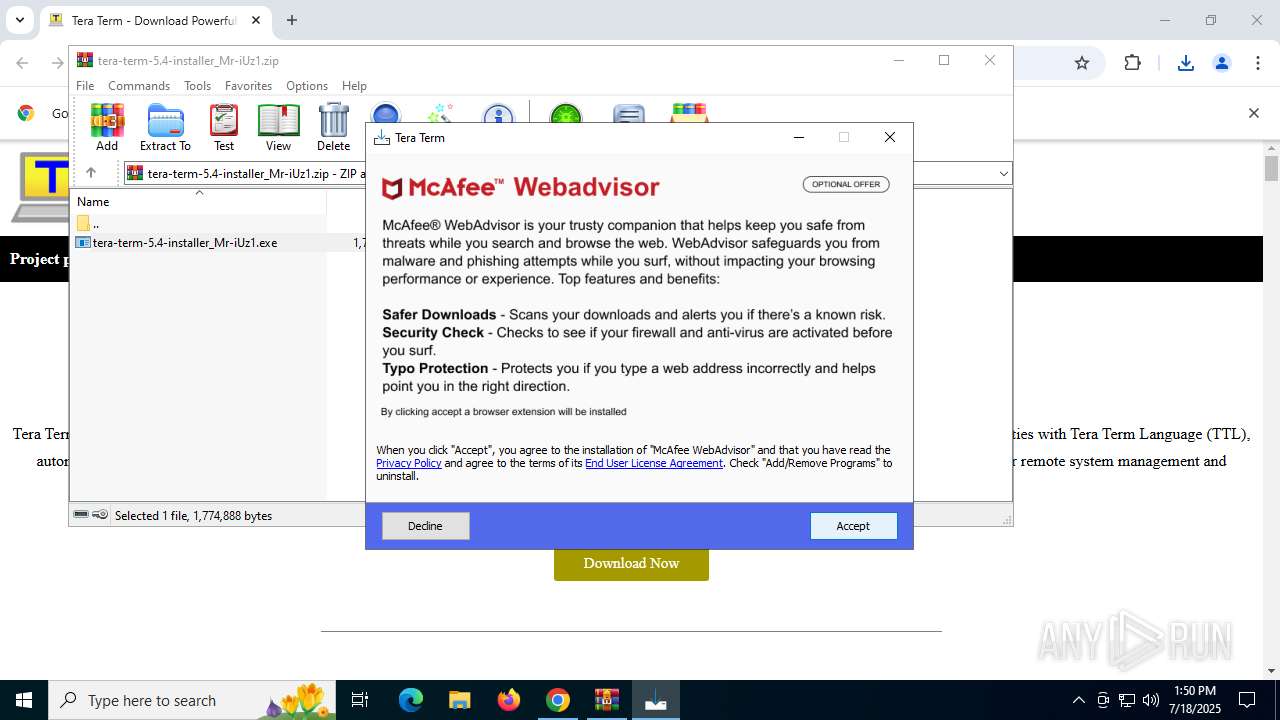
| 1380 | "C:\Program Files\McAfee\Temp706838591\installer.exe" /setOem:Affid=91082 /s /thirdparty /upgrade | C:\Program Files\McAfee\Temp706838591\installer.exe | installer.exe | ||||||||||||
User: admin Company: McAfee, LLC Integrity Level: HIGH Description: McAfee WebAdvisor(installer) Exit code: 0 Version: 4,1,1,1057 Modules
| |||||||||||||||
| 1852 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5660,i,10643983514228774147,2748578781470212101,262144 --variations-seed-version --mojo-platform-channel-handle=5732 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1880 | "C:\Users\admin\AppData\Local\Temp\is-80TL8.tmp\component0_extract\saBSI.exe" /affid 91082 PaidDistribution=true CountryCode=DE InstallID=GnjW0t7MBixrpx3kCPWlefTiFQGKcPMGxX6xDij6F62A8wu14Rov1J13lSYw3hjyMEVfSSCxuudnqpoceky | C:\Users\admin\AppData\Local\Temp\is-80TL8.tmp\component0_extract\saBSI.exe | tera-term-5.4-installer_Mr-iUz1.tmp | ||||||||||||
User: admin Company: McAfee, LLC Integrity Level: HIGH Description: McAfee WebAdvisor(bootstrap installer) Exit code: 0 Version: 4,1,1,865 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2284,i,16429336828154197326,5686848205405323577,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2448 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2388 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2388,i,15775873752222950209,11479033013441941422,262144 --variations-seed-version --mojo-platform-channel-handle=2364 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
49 262
Read events
48 914
Write events
334
Delete events
14
Modification events
| (PID) Process: | (6796) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6796) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6796) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6796) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6796) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6796) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (7964) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7964) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7964) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7964) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\tera-term-5.4-installer_Mr-iUz1.zip | |||
Executable files
26
Suspicious files
680
Text files
878
Unknown types
83
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF18d0b8.TMP | — | |
MD5:— | SHA256:— | |||
| 6796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF18d0b8.TMP | — | |
MD5:— | SHA256:— | |||
| 6796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF18d0d8.TMP | — | |
MD5:— | SHA256:— | |||
| 6796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF18d0d8.TMP | — | |
MD5:— | SHA256:— | |||
| 6796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF18d0d8.TMP | — | |
MD5:— | SHA256:— | |||
| 6796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF18d0d8.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
286
DNS requests
257
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2972 | chrome.exe | GET | 200 | 142.250.186.78:80 | http://clients2.google.com/time/1/current?cup2key=8:wEvO6sceExvaurLJCpyzuYcQ9D4VVQ_JcLUtWpAQzsk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2064 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
620 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:6o2mpS3M59mo7q_1ymQ01B3CmhMjxC2C-0mwlSgOYtk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7508 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5184 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7508 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5184 | WerFault.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5600 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3288 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2972 | chrome.exe | 172.217.16.202:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
2972 | chrome.exe | 142.250.186.78:80 | clients2.google.com | GOOGLE | US | whitelisted |
2972 | chrome.exe | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2972 | chrome.exe | 104.21.80.1:443 | getteraterm.com | CLOUDFLARENET | — | unknown |
2972 | chrome.exe | 142.250.185.162:443 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
getteraterm.com |
| unknown |
accounts.google.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
www.youtube.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2972 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2972 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2972 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2972 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
620 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-80TL8.tmp\component0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-80TL8.tmp\component0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-80TL8.tmp\component0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-80TL8.tmp\component0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-80TL8.tmp\component0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-80TL8.tmp\component0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|