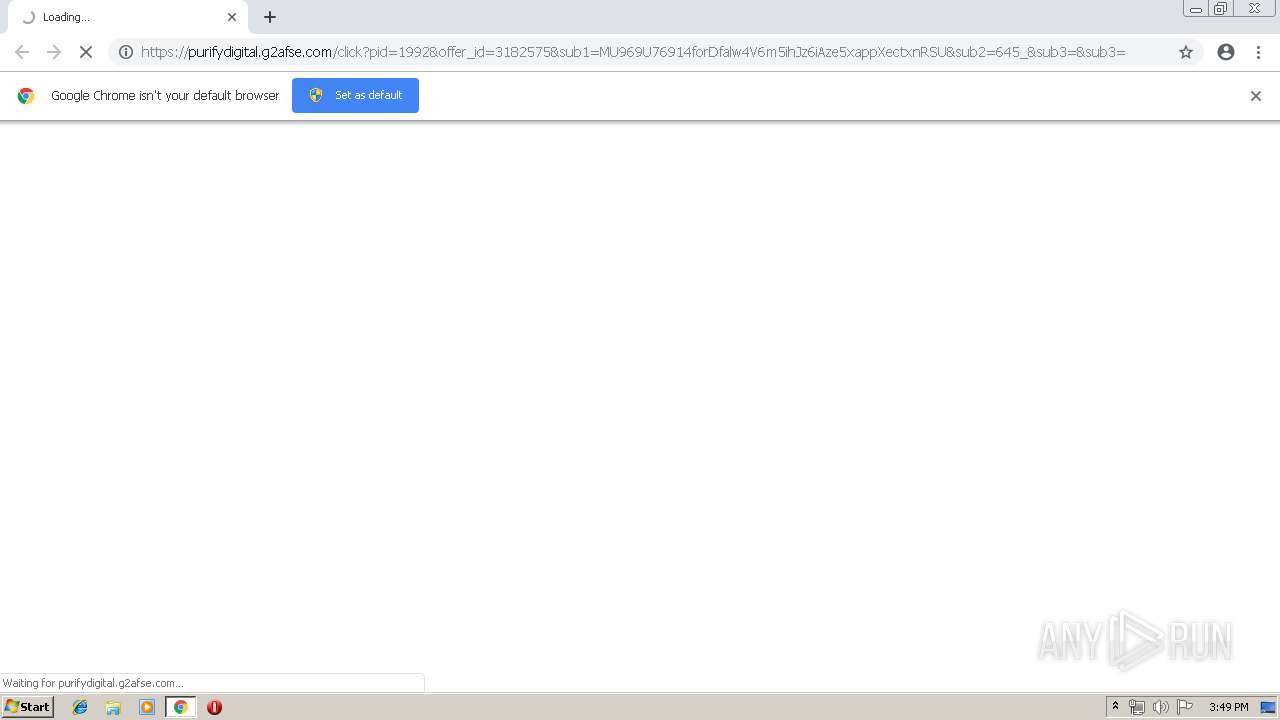
| URL: | https://purifydigital.g2afse.com/click?pid=1992&offer_id=3182575&sub1=MU969U76914forDfalw4V6m5ihJz6iAze5xappXectxnRSU&sub2=645_&sub3=&sub3= |
| Full analysis: | https://app.any.run/tasks/e7427708-6e99-47eb-9439-9d29f1891fc6 |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2019, 14:49:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 29FF59D28DEA541F1CEFA56448F3EE86 |
| SHA1: | E68E0BE9B275DA665F8DD5C4101B43758DE950E2 |
| SHA256: | E5C9E40F8607DAB284949DA080C602FE64AC2075C76C47002F2A875405B60D06 |
| SSDEEP: | 3:N8UcDcMnq53GJMk/FzPdX2WQ0HQn0V5G7dEKQ3XzudzTHfn:2UyRe2JM6PdXxHQ0XG7GKQ30/n |
MALICIOUS
No malicious indicators.SUSPICIOUS
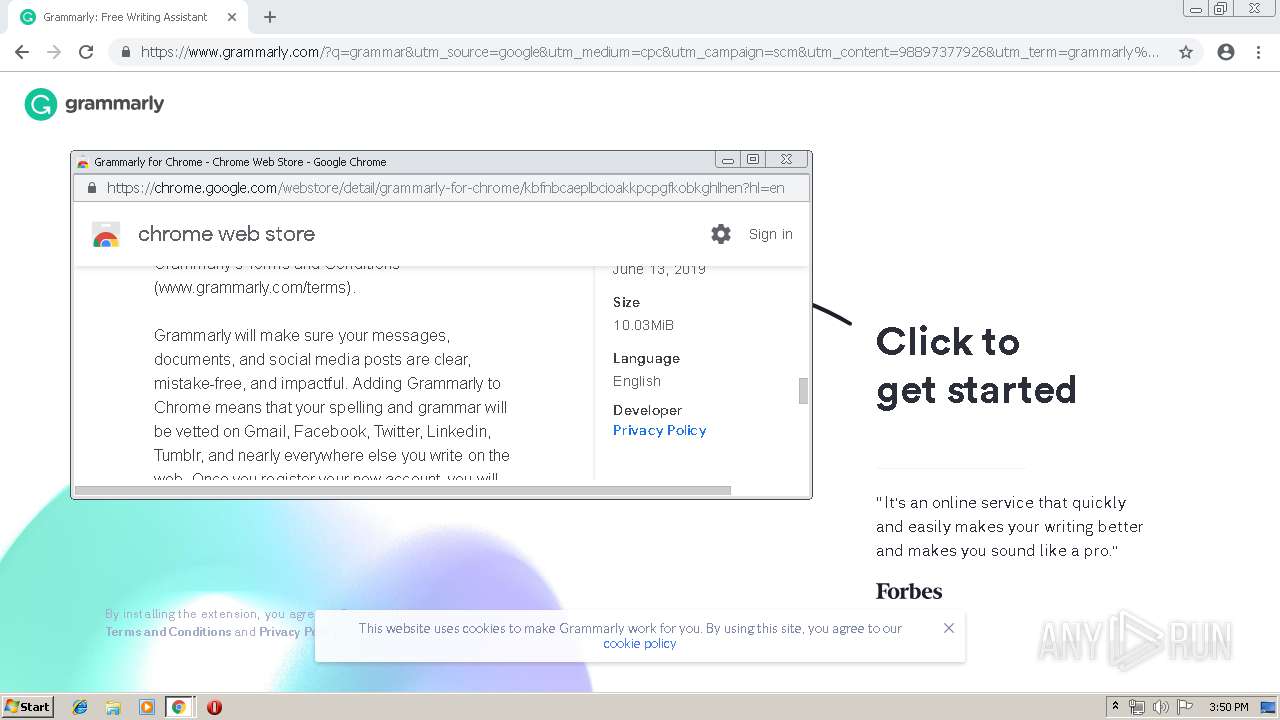
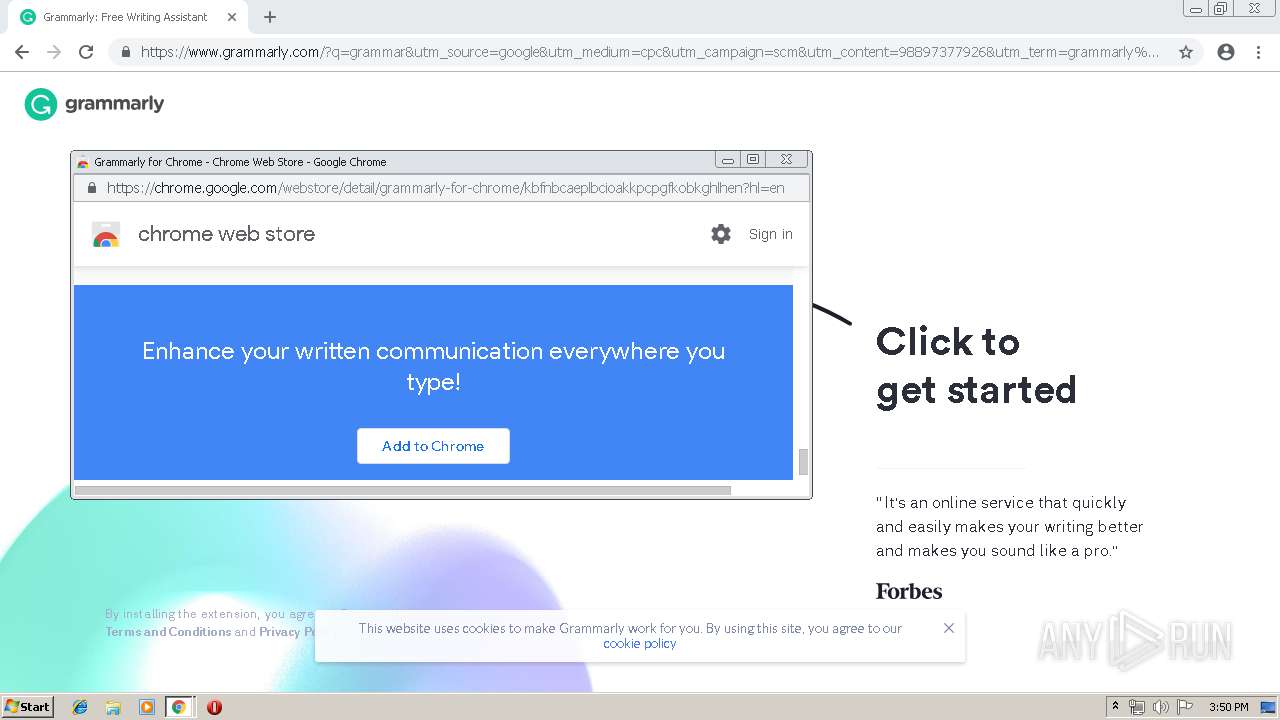
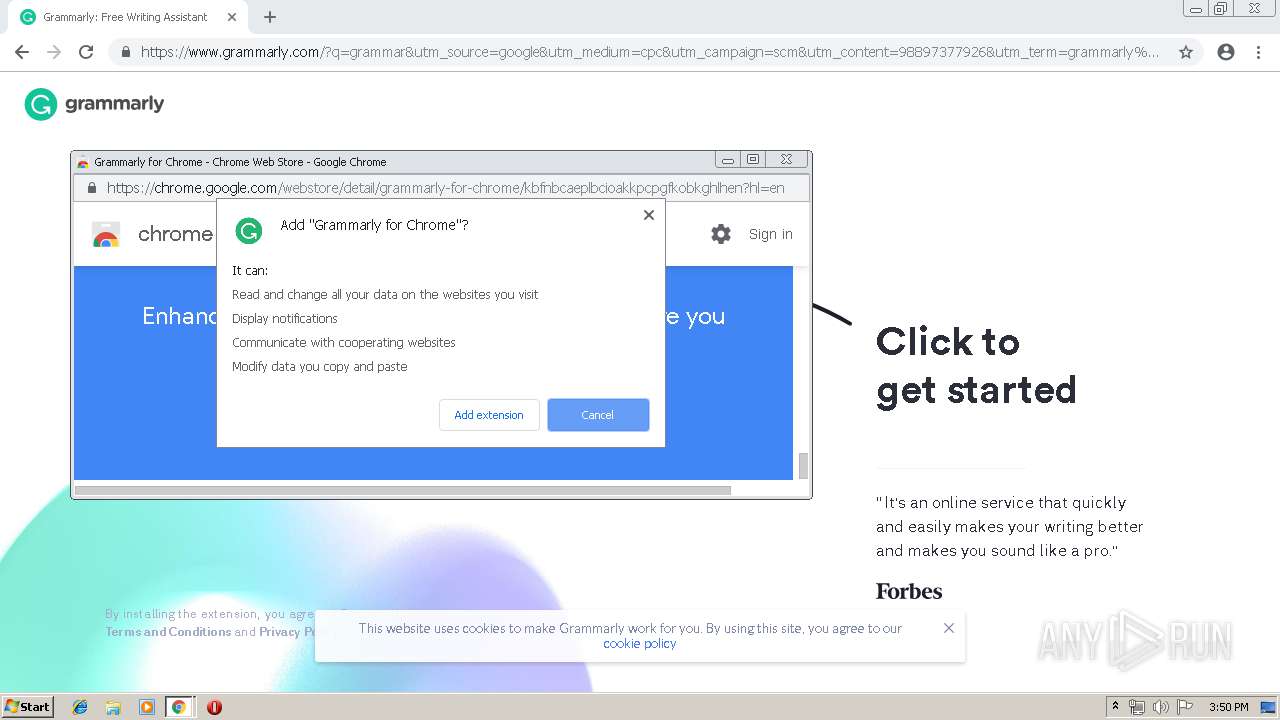
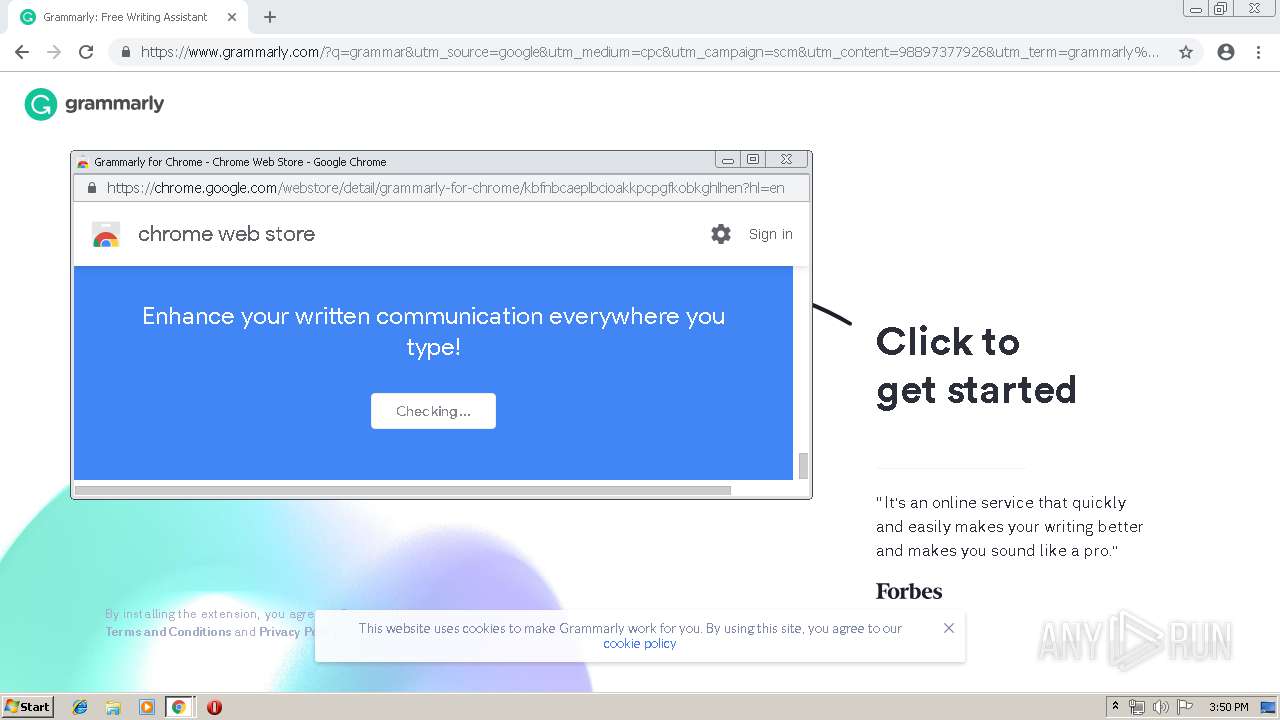
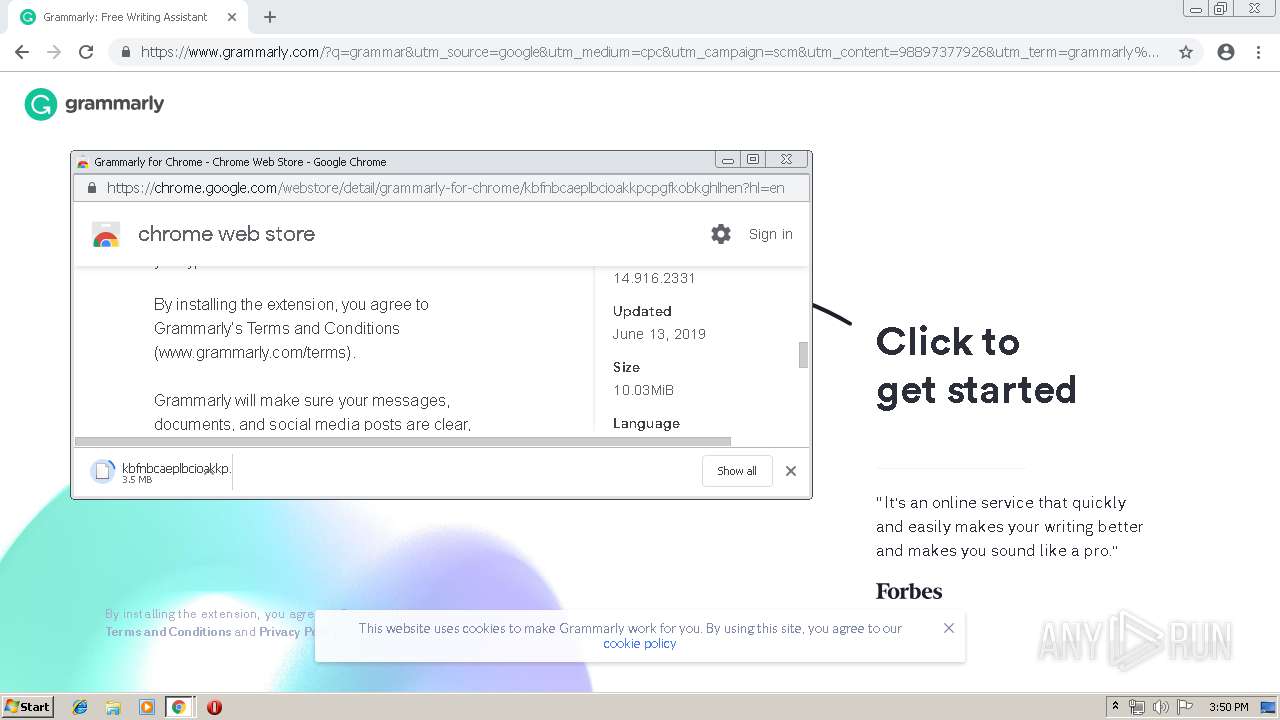
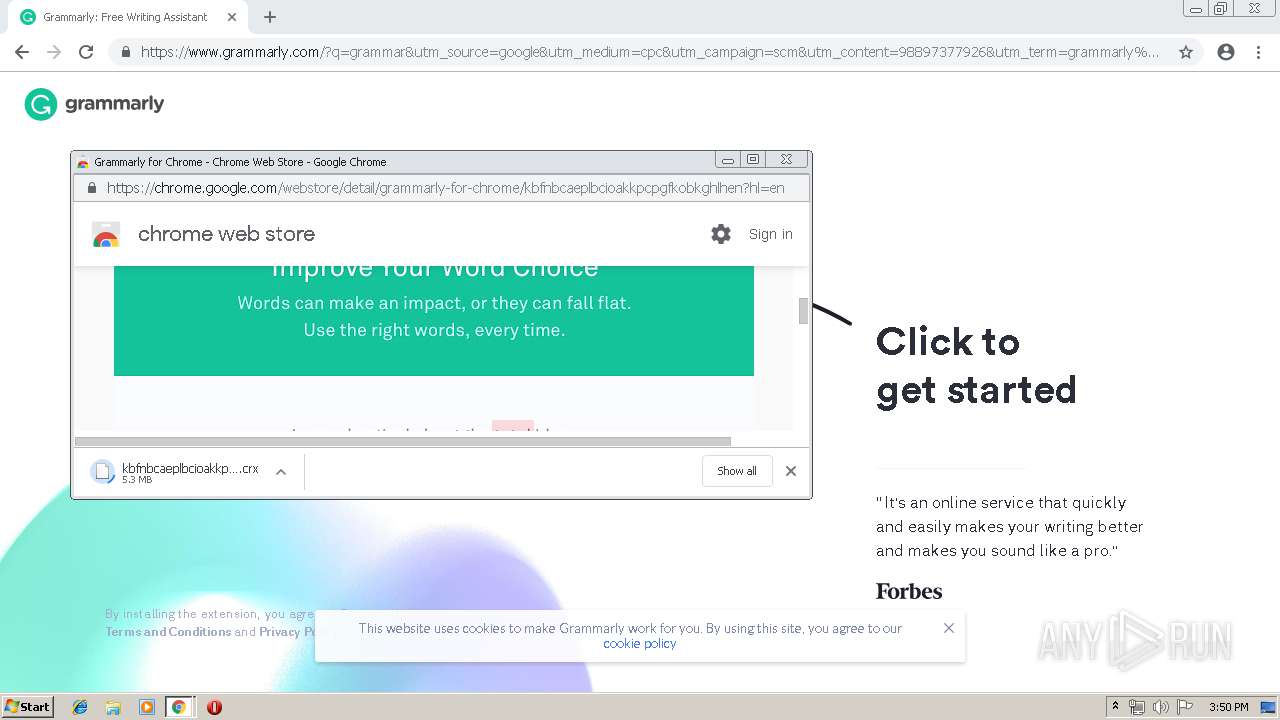
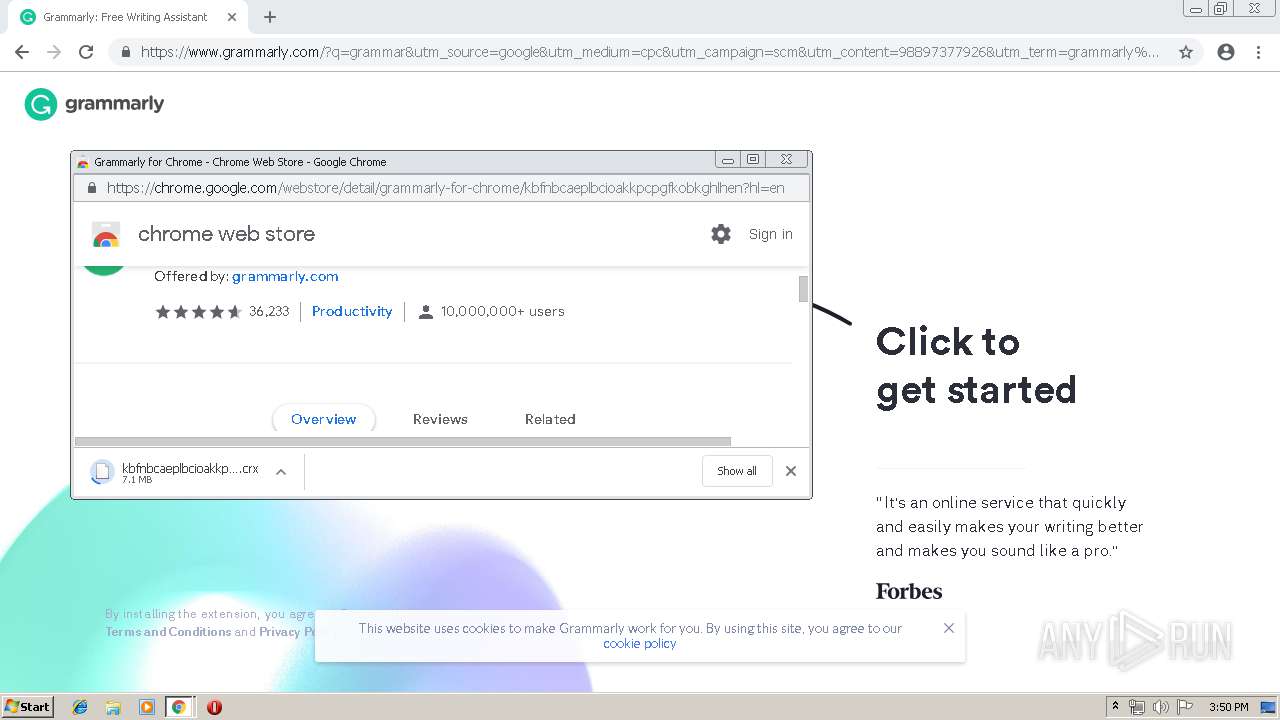
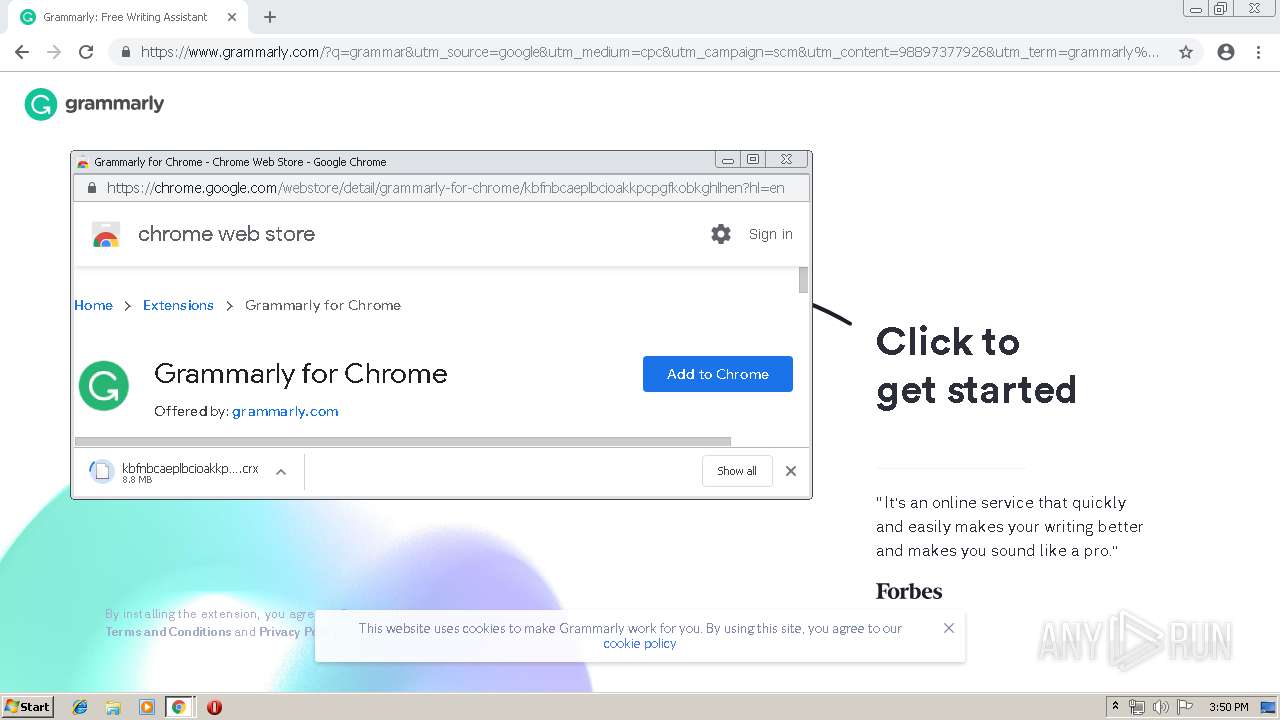
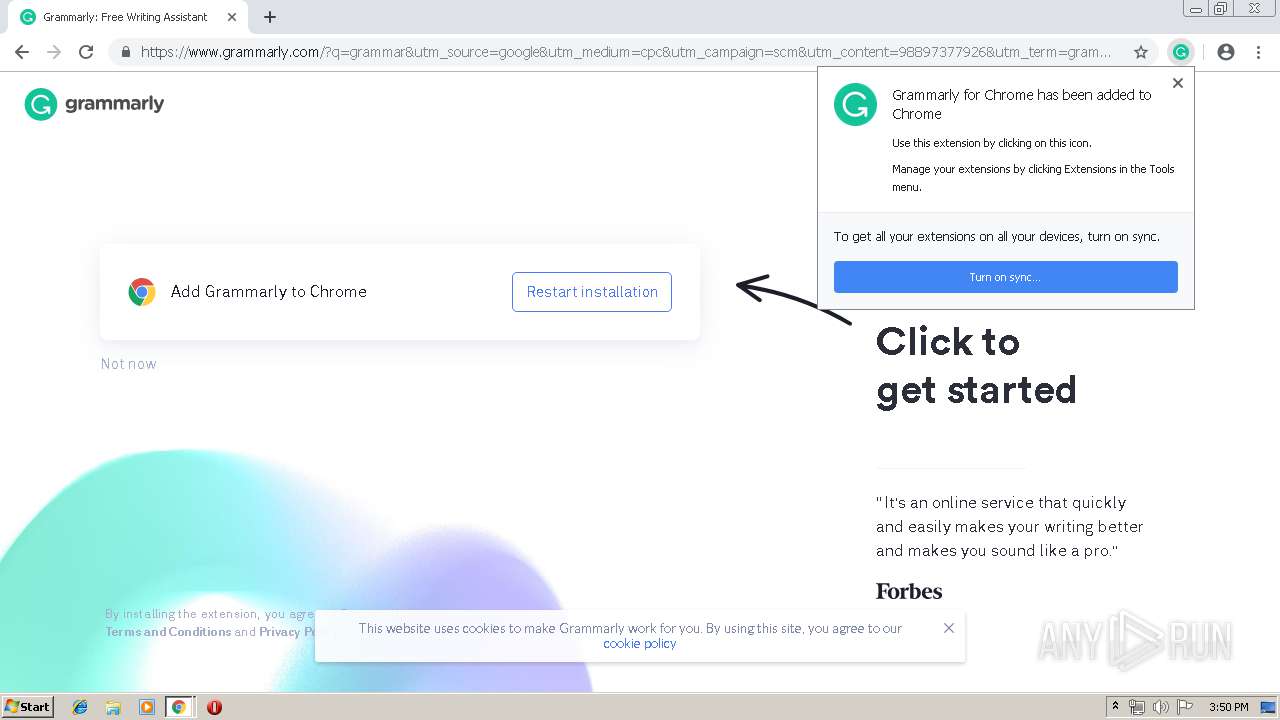
Modifies files in Chrome extension folder
- chrome.exe (PID: 2500)
INFO
Application launched itself
- chrome.exe (PID: 2500)
Changes settings of System certificates
- chrome.exe (PID: 2500)
Reads Internet Cache Settings
- chrome.exe (PID: 2500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
54
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10924365669941542681 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10924365669941542681 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16551619987280803520 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16551619987280803520 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1504316623394693240 --mojo-platform-channel-handle=6948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=295809310998017700 --mojo-platform-channel-handle=4604 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10911016118249821896 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10911016118249821896 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5656 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=18364663704058552508 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18364663704058552508 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4720 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7774534890721559871 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7774534890721559871 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2480 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13805259978544961274 --mojo-platform-channel-handle=3996 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14414533065490920015 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14414533065490920015 --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
755
Read events
608
Write events
141
Delete events
6
Modification events
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1128) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2500-13205170165470000 |
Value: 259 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
Executable files
0
Suspicious files
279
Text files
280
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF134019.TMP | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a72f2993-cb3e-40a4-8bd1-f023a3159c4c.tmp | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
88
TCP/UDP connections
203
DNS requests
138
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
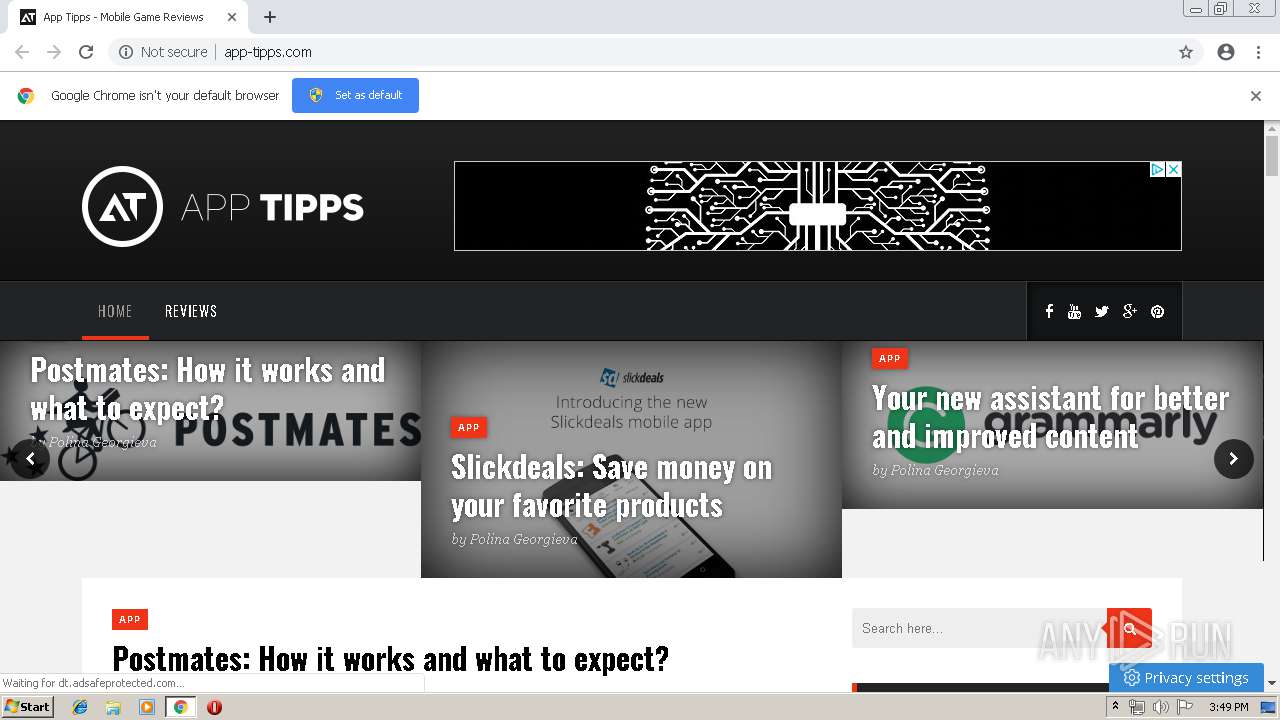
2500 | chrome.exe | GET | 200 | 172.64.131.34:80 | http://app-tipps.com/wp-content/themes/kappa-child/style.css?ver=5.0.3 | US | text | 924 b | suspicious |
2500 | chrome.exe | GET | 200 | 172.64.131.34:80 | http://app-tipps.com/wp-content/plugins/newsletter-subscription-form/options/css/form-style.css?ver=5.0.3 | US | text | 313 b | suspicious |
2500 | chrome.exe | GET | 200 | 172.64.131.34:80 | http://app-tipps.com/wp-content/themes/kappa/assets/css/jetpack.css?ver=5.0.3 | US | text | 1.00 Kb | suspicious |
2500 | chrome.exe | GET | 200 | 172.64.131.34:80 | http://app-tipps.com/wp-content/themes/kappa/assets/css/responsive.css?ver=5.0.3 | US | text | 785 b | suspicious |
2500 | chrome.exe | GET | 200 | 172.64.131.34:80 | http://app-tipps.com/wp-content/uploads/2016/10/logo-app_tips_v1.png | US | image | 21.6 Kb | suspicious |
2500 | chrome.exe | GET | 200 | 172.64.131.34:80 | http://app-tipps.com/wp-content/themes/kappa/assets/css/slicknav.css?ver=5.0.3 | US | text | 698 b | suspicious |
2500 | chrome.exe | GET | 200 | 172.64.131.34:80 | http://app-tipps.com/wp-content/themes/kappa-child/custom.js?ver=1 | US | text | 1.23 Kb | suspicious |
2500 | chrome.exe | GET | 200 | 172.64.131.34:80 | http://app-tipps.com/wp-content/themes/kappa/style.css | US | text | 4.67 Kb | suspicious |
2500 | chrome.exe | GET | 200 | 172.217.21.194:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 33.2 Kb | whitelisted |
2500 | chrome.exe | GET | 200 | 172.64.131.34:80 | http://app-tipps.com/wp-content/themes/kappa/assets/css/owl.carousel.css?ver=5.0.3 | US | text | 554 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2500 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2500 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2500 | chrome.exe | 172.64.131.34:80 | app-tipps.com | Cloudflare Inc | US | shared |
2500 | chrome.exe | 172.217.21.194:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2500 | chrome.exe | 216.58.205.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2500 | chrome.exe | 172.217.23.163:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2500 | chrome.exe | 212.32.252.82:443 | purifydigital.g2afse.com | LeaseWeb Netherlands B.V. | NL | suspicious |
2500 | chrome.exe | 104.16.134.22:443 | live.demand.supply | Cloudflare Inc | US | shared |
2500 | chrome.exe | 216.58.210.2:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2500 | chrome.exe | 216.58.207.66:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
purifydigital.g2afse.com |
| suspicious |
accounts.google.com |
| shared |
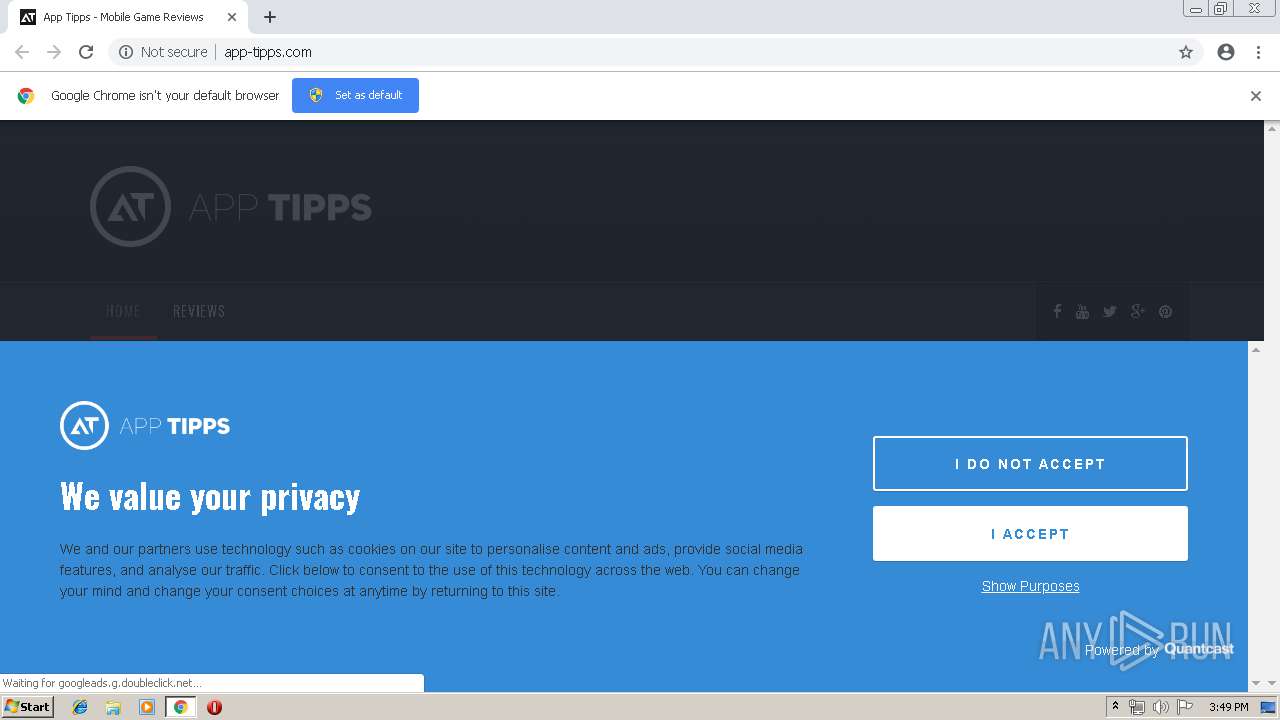
app-tipps.com |
| suspicious |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
live.demand.supply |
| unknown |
fonts.gstatic.com |
| whitelisted |
s.w.org |
| whitelisted |