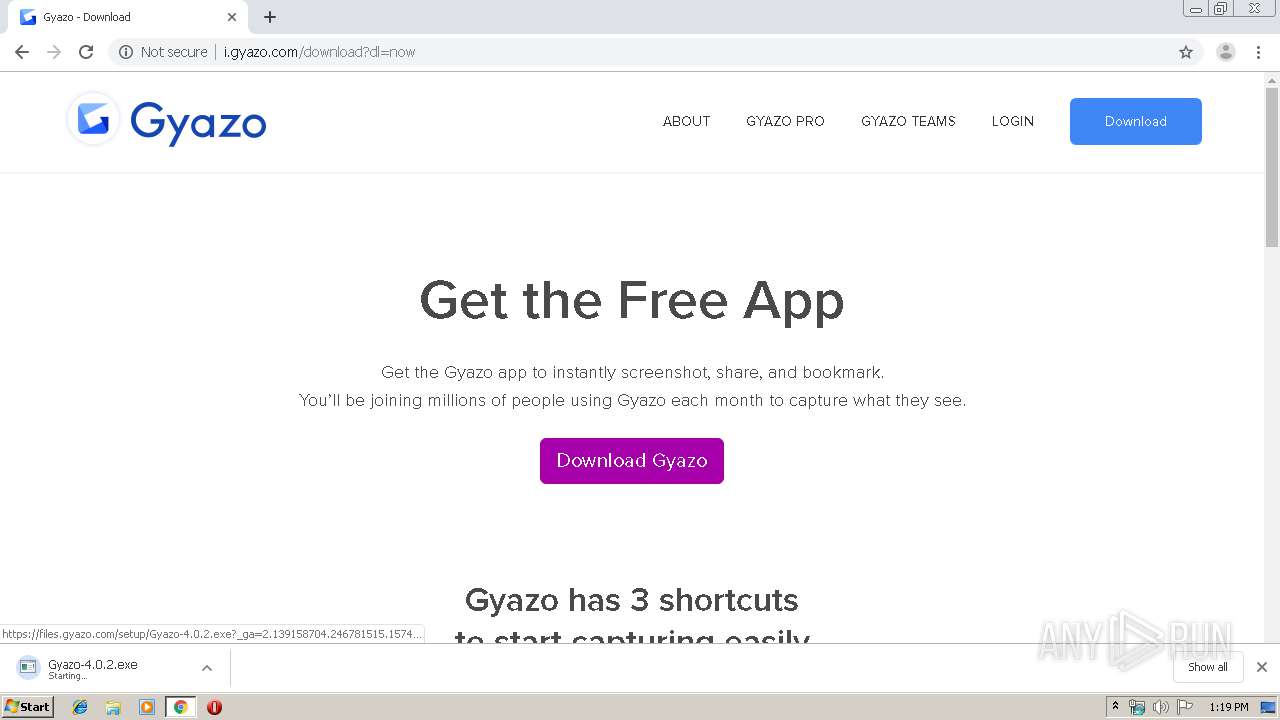
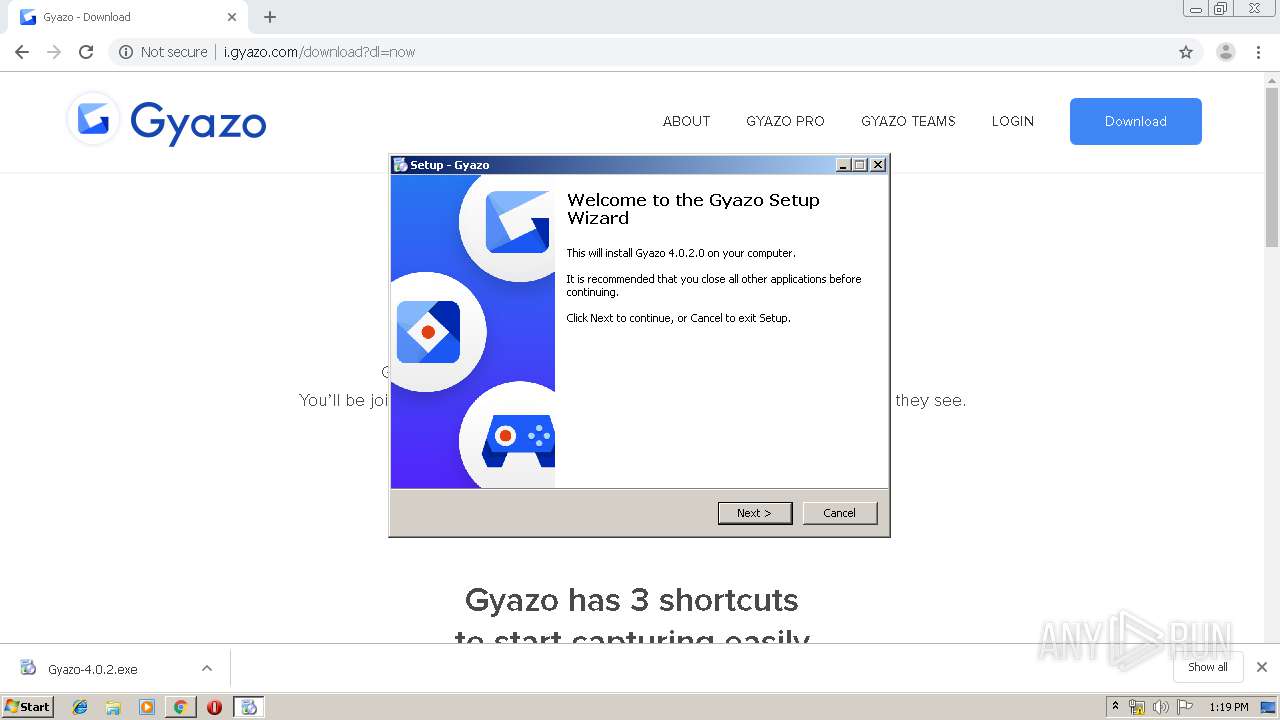
| URL: | http://i.gyazo.com |
| Full analysis: | https://app.any.run/tasks/c1a2962f-d6a1-41c8-99cb-94c63a0a65f7 |
| Verdict: | Malicious activity |
| Analysis date: | November 28, 2019, 13:18:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CB8CE46EB60BB27181C467E6F5FFDD21 |
| SHA1: | AE501ED73BBA6759C69863A401A927BF81ECEEFB |
| SHA256: | E5C2893AAC038D38BDBED81DF97FF37491279C2FA18F8B28717E0136A6C1CA3F |
| SSDEEP: | 3:N1KXdGT:CtK |
MALICIOUS
Changes the autorun value in the registry
- Gyazo-4.0.2.tmp (PID: 3508)
- GyStation.exe (PID: 2156)
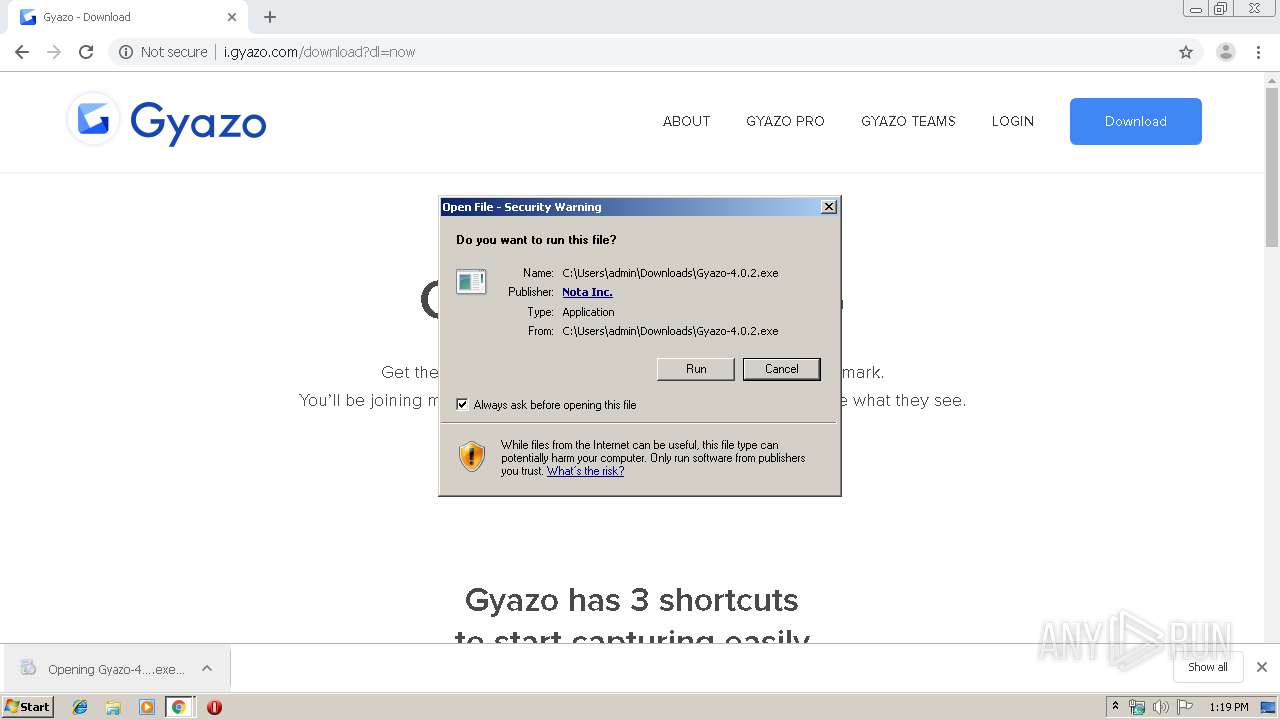
Application was dropped or rewritten from another process
- Gyazo-4.0.2.exe (PID: 3276)
- Gyazo-4.0.2.exe (PID: 3908)
- GyStation.exe (PID: 2156)
- GyStation.exe (PID: 912)
- GyStation.exe (PID: 3476)
Uses Task Scheduler to autorun other applications
- Gyazo-4.0.2.tmp (PID: 3508)
Loads dropped or rewritten executable
- GyStation.exe (PID: 912)
- GyStation.exe (PID: 3476)
- GyStation.exe (PID: 2156)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2384)
- schtasks.exe (PID: 1724)
Uses Task Scheduler to run other applications
- Gyazo-4.0.2.tmp (PID: 3508)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2620)
Executable content was dropped or overwritten
- chrome.exe (PID: 1708)
- Gyazo-4.0.2.exe (PID: 3276)
- chrome.exe (PID: 2620)
- Gyazo-4.0.2.exe (PID: 3908)
- Gyazo-4.0.2.tmp (PID: 3508)
Reads the Windows organization settings
- Gyazo-4.0.2.tmp (PID: 3508)
Reads Windows owner or organization settings
- Gyazo-4.0.2.tmp (PID: 3508)
Creates files in the user directory
- Gyazo-4.0.2.tmp (PID: 3508)
Reads Environment values
- GyStation.exe (PID: 3476)
- GyStation.exe (PID: 912)
- GyStation.exe (PID: 2156)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2620)
Reads the hosts file
- chrome.exe (PID: 2620)
- chrome.exe (PID: 1708)
Application launched itself
- chrome.exe (PID: 2620)
Application was dropped or rewritten from another process
- Gyazo-4.0.2.tmp (PID: 1892)
- Gyazo-4.0.2.tmp (PID: 3508)
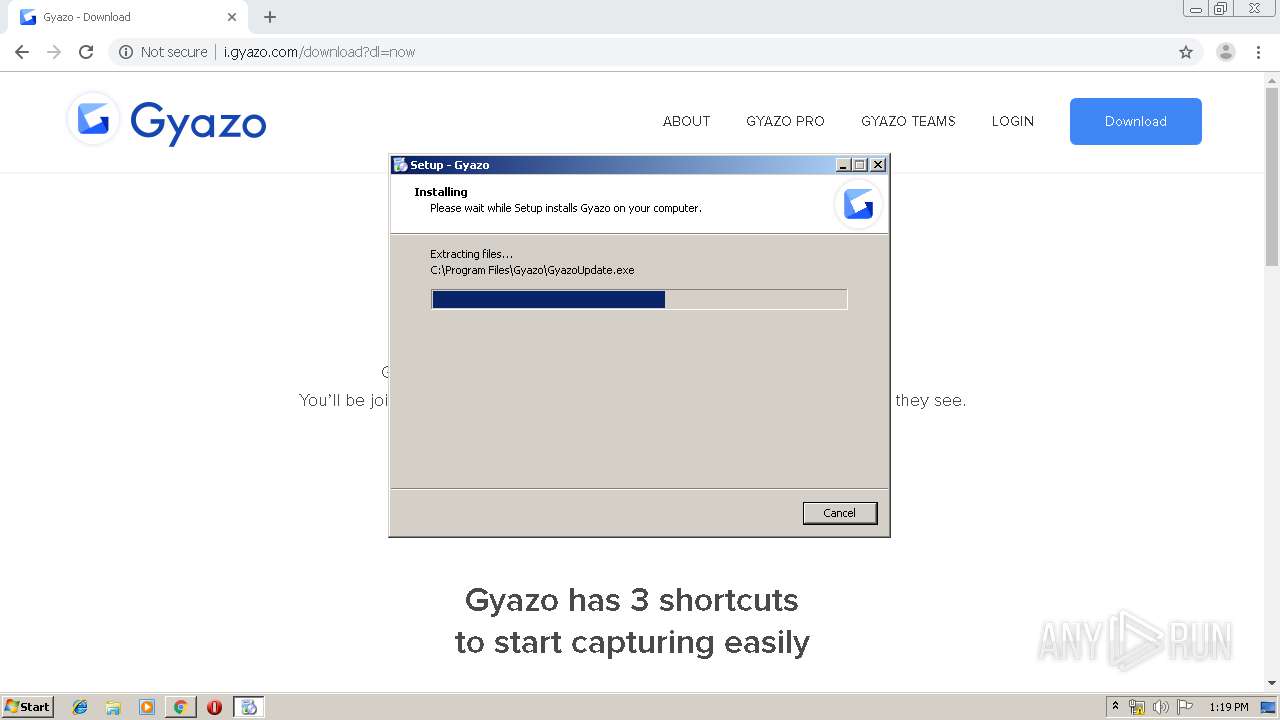
Creates files in the program directory
- Gyazo-4.0.2.tmp (PID: 3508)
Creates a software uninstall entry
- Gyazo-4.0.2.tmp (PID: 3508)
Dropped object may contain Bitcoin addresses
- Gyazo-4.0.2.tmp (PID: 3508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
37
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14260971027505471666,17652931593623239358,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16399206637018512459 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14260971027505471666,17652931593623239358,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5874807499219953594 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14260971027505471666,17652931593623239358,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1919524249007391715 --mojo-platform-channel-handle=3696 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Gyazo\GyStation.exe" /balloon "Welcome to Gyazo!@Left click the icon then drag to capture, right click for settings." | C:\Program Files\Gyazo\GyStation.exe | — | Gyazo-4.0.2.tmp | |||||||||||
User: admin Company: Nota Inc. Integrity Level: MEDIUM Description: GyStation Exit code: 0 Version: 4.0.2.0 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14260971027505471666,17652931593623239358,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12841319619546645312 --mojo-platform-channel-handle=3824 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14260971027505471666,17652931593623239358,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12857064569078103771 --mojo-platform-channel-handle=3764 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,14260971027505471666,17652931593623239358,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8676459735612573715 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14260971027505471666,17652931593623239358,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12600160151976811355 --mojo-platform-channel-handle=1520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,14260971027505471666,17652931593623239358,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7271051787058160245 --mojo-platform-channel-handle=4444 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1724 | "C:\Windows\System32\schtasks.exe" /Create /TN GyazoUpdateTaskMachine /TR "\"C:\Program Files\Gyazo\GyazoUpdate.exe"\" /SC ONLOGON /F /RL HIGHEST /DELAY 0020:00 | C:\Windows\System32\schtasks.exe | — | Gyazo-4.0.2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 691
Read events
1 528
Write events
152
Delete events
11
Modification events
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2620-13219420699116750 |
Value: 259 | |||
Executable files
49
Suspicious files
89
Text files
218
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a8ae.TMP | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\af97c630-3327-4b33-9058-05ea0d448801.tmp | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
72
DNS requests
56
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1708 | chrome.exe | GET | 301 | 104.244.42.69:80 | http://t.co/i/adsct?p_id=Twitter&p_user_id=0&txn_id=nyxbd&events=%5B%5B%22pageview%22%2Cnull%5D%5D&tw_sale_amount=0&tw_order_quantity=0&tw_iframe_status=0 | US | — | — | shared |
1708 | chrome.exe | GET | 200 | 104.19.143.111:80 | http://i.gyazo.com/dist/sprite-c62088bb49.svg | US | image | 30.9 Kb | whitelisted |
1708 | chrome.exe | GET | 200 | 172.217.16.130:80 | http://www.googletagservices.com/tag/js/gpt.js | US | text | 15.3 Kb | whitelisted |
1708 | chrome.exe | GET | 200 | 151.101.12.157:80 | http://static.ads-twitter.com/uwt.js | US | text | 1.91 Kb | whitelisted |
1708 | chrome.exe | GET | 200 | 104.19.143.111:80 | http://i.gyazo.com/ | US | html | 5.88 Kb | whitelisted |
1708 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://www.google-analytics.com/r/collect?v=1&_v=j79&a=150403057&t=pageview&_s=1&dl=http%3A%2F%2Fi.gyazo.com%2F&ul=en-us&de=UTF-8&dt=Gyazo%20%C2%B7%20Capture%20and%20share%20on-screen%20moments%20instantly&sd=24-bit&sr=1280x720&vp=1264x572&je=0&_u=YGDACEABB~&jid=320335666&gjid=287515157&cid=2128372283.1574947103&tid=UA-2827501-10&_gid=246781515.1574947103&_r=1&cd1=Guest&cd2=NotSignedUp&cd5=none&z=628456328 | US | html | 416 b | whitelisted |
1708 | chrome.exe | GET | 200 | 130.211.5.208:80 | http://cdn.mxpnl.com/libs/mixpanel-2-latest.min.js | US | text | 23.3 Kb | whitelisted |
1708 | chrome.exe | GET | 200 | 216.58.207.34:80 | http://www.googleadservices.com/pagead/conversion_async.js | US | text | 9.39 Kb | whitelisted |
1708 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://www.google-analytics.com/r/collect?v=1&_v=j79&a=150403057&t=pageview&_s=1&dl=http%3A%2F%2Fi.gyazo.com%2F&ul=en-us&de=UTF-8&dt=Gyazo%20%C2%B7%20Capture%20and%20share%20on-screen%20moments%20instantly&sd=24-bit&sr=1280x720&vp=1264x572&je=0&_u=YGDACEABB~&jid=1302023583&gjid=371781525&cid=2128372283.1574947103&tid=UA-2827501-30&_gid=246781515.1574947103&_r=1&z=1766300156 | US | html | 418 b | whitelisted |
1708 | chrome.exe | GET | 304 | 151.101.12.157:80 | http://static.ads-twitter.com/uwt.js | US | compressed | 1.91 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1708 | chrome.exe | 104.19.143.111:80 | i.gyazo.com | Cloudflare Inc | US | shared |
1708 | chrome.exe | 104.19.142.111:443 | i.gyazo.com | Cloudflare Inc | US | shared |
1708 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.217.16.200:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.217.16.130:80 | www.googletagservices.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.217.18.98:443 | adservice.google.es | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.217.21.226:443 | adservice.google.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 216.58.210.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 130.211.5.208:80 | cdn.mxpnl.com | Google Inc. | US | whitelisted |
1708 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
i.gyazo.com |
| whitelisted |
accounts.google.com |
| shared |
assets.gyazo.com |
| suspicious |
www.googletagservices.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
adservice.google.es |
| whitelisted |
adservice.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |