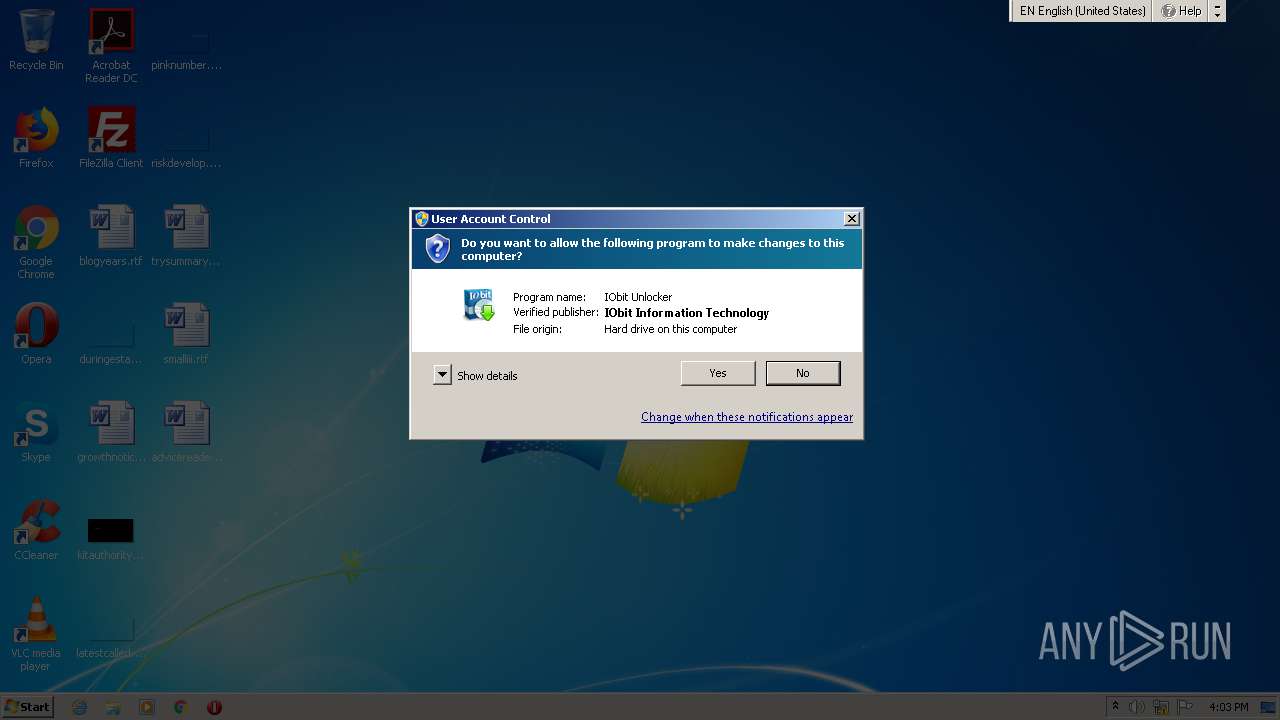
| File name: | unlocker-setup.exe |
| Full analysis: | https://app.any.run/tasks/b96423f5-a32a-4e71-9389-1709325af1f0 |
| Verdict: | Malicious activity |
| Analysis date: | October 17, 2020, 15:03:36 |
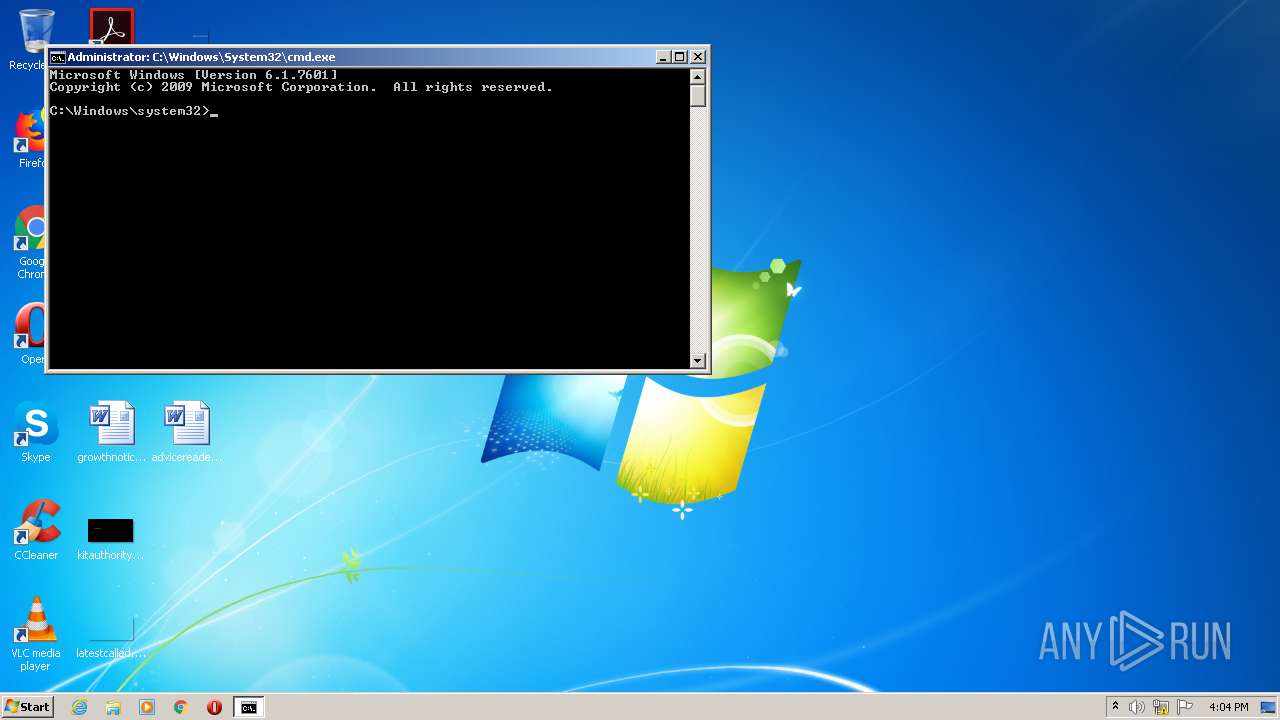
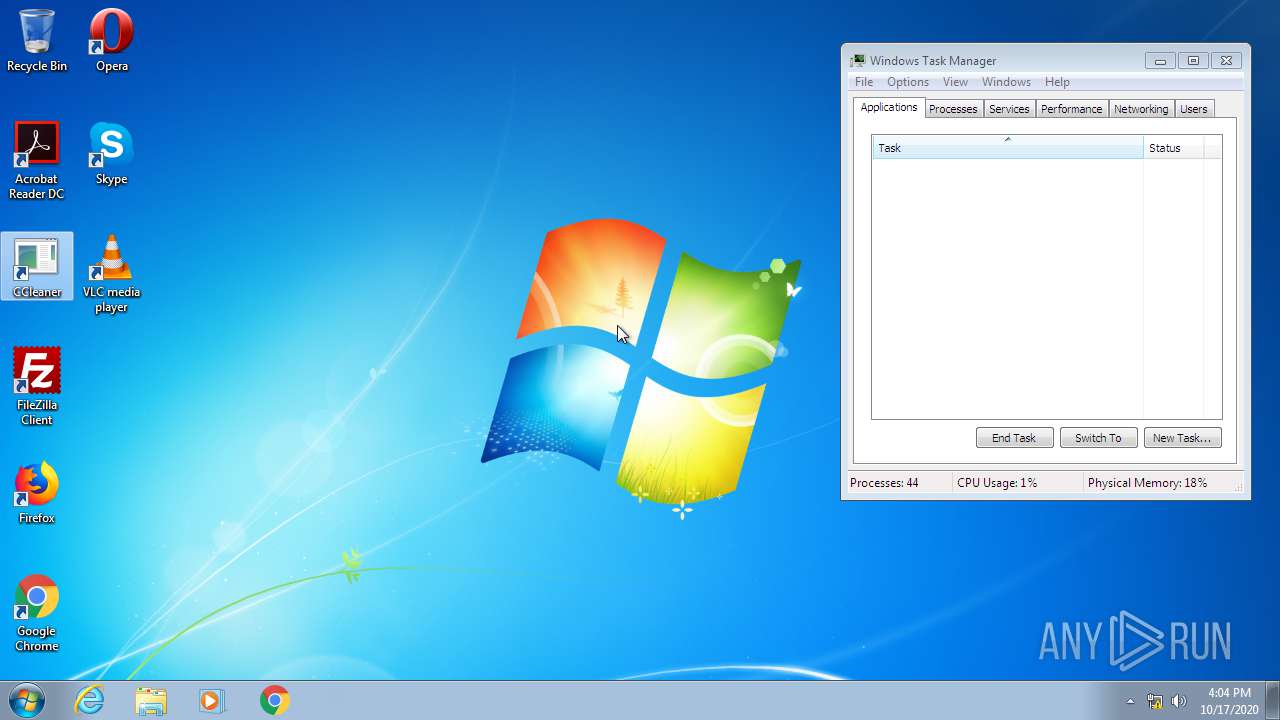
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 81ED97F9FAD6703413F25E652A4AF9DF |
| SHA1: | 30B788EC245AA48546AD0716B841A00ADBA0AD75 |
| SHA256: | E5C1B479630E958E8F8E07AC42D43DCDB8D5AC639B20EBB1515FC9345F1DA801 |
| SSDEEP: | 49152:nx6Qw1/hIghVYpUpZhHXVY9cUJGQB26BmcEgbnBsj+dZ4JS6Qa:spfhVdp/Adm9Qsj0ZC |
MALICIOUS
Loads the Task Scheduler COM API
- rundll32.exe (PID: 2416)
Changes internet zones settings
- ie4uinit.exe (PID: 3288)
SUSPICIOUS
Executable content was dropped or overwritten
- unlocker-setup.exe (PID: 2516)
Executed as Windows Service
- taskhost.exe (PID: 2660)
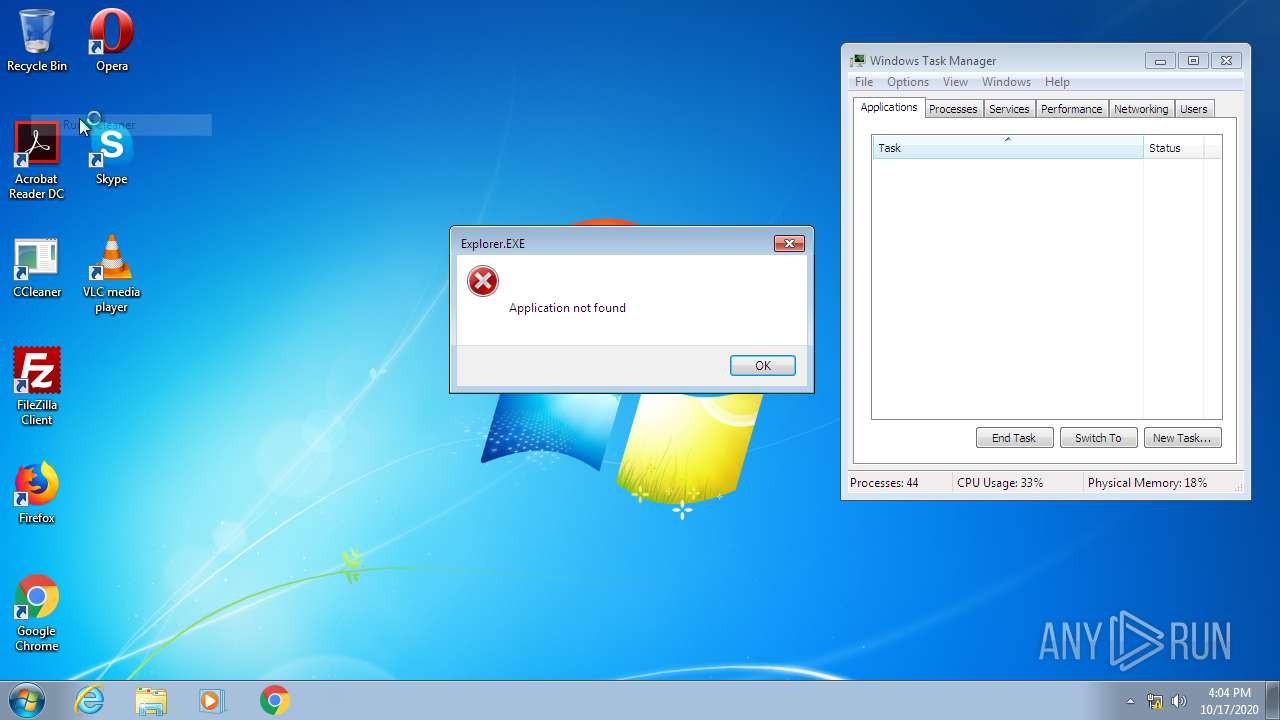
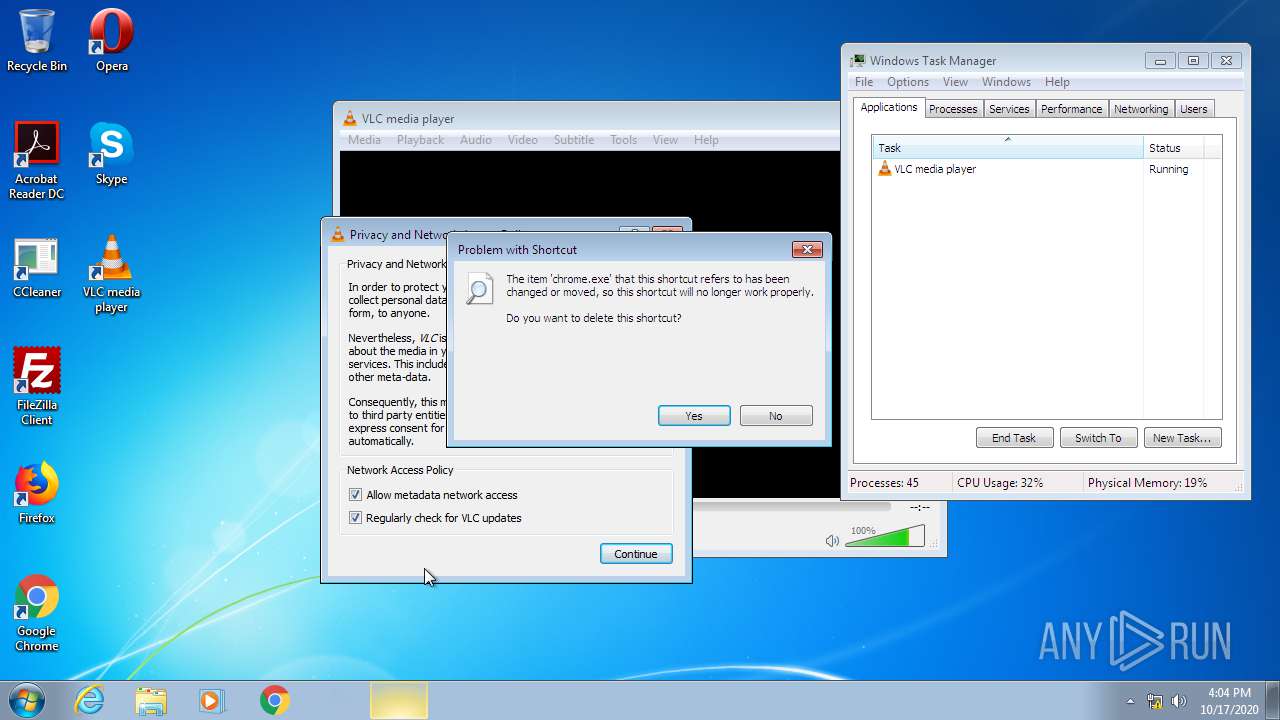
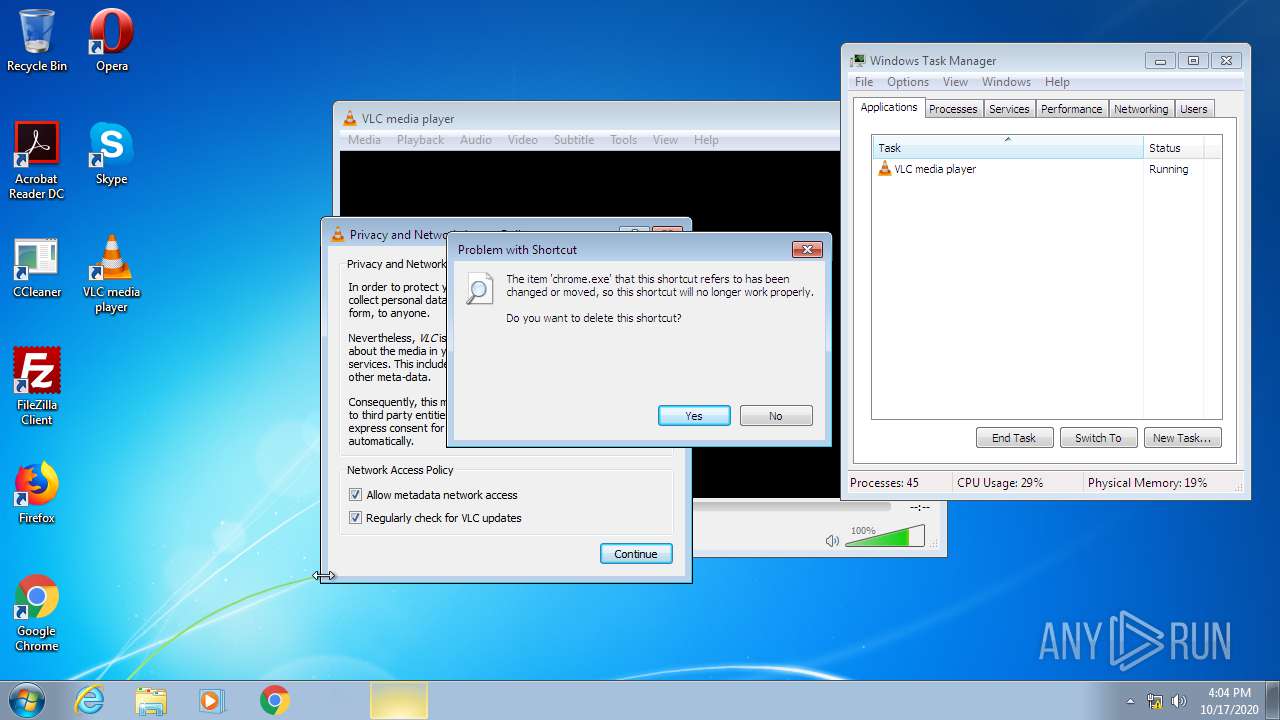
Application launched itself
- ie4uinit.exe (PID: 3288)
- chrmstp.exe (PID: 3896)
- rundll32.exe (PID: 2416)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 2416)
- ie4uinit.exe (PID: 3288)
Creates files in the program directory
- ie4uinit.exe (PID: 3288)
- chrmstp.exe (PID: 3896)
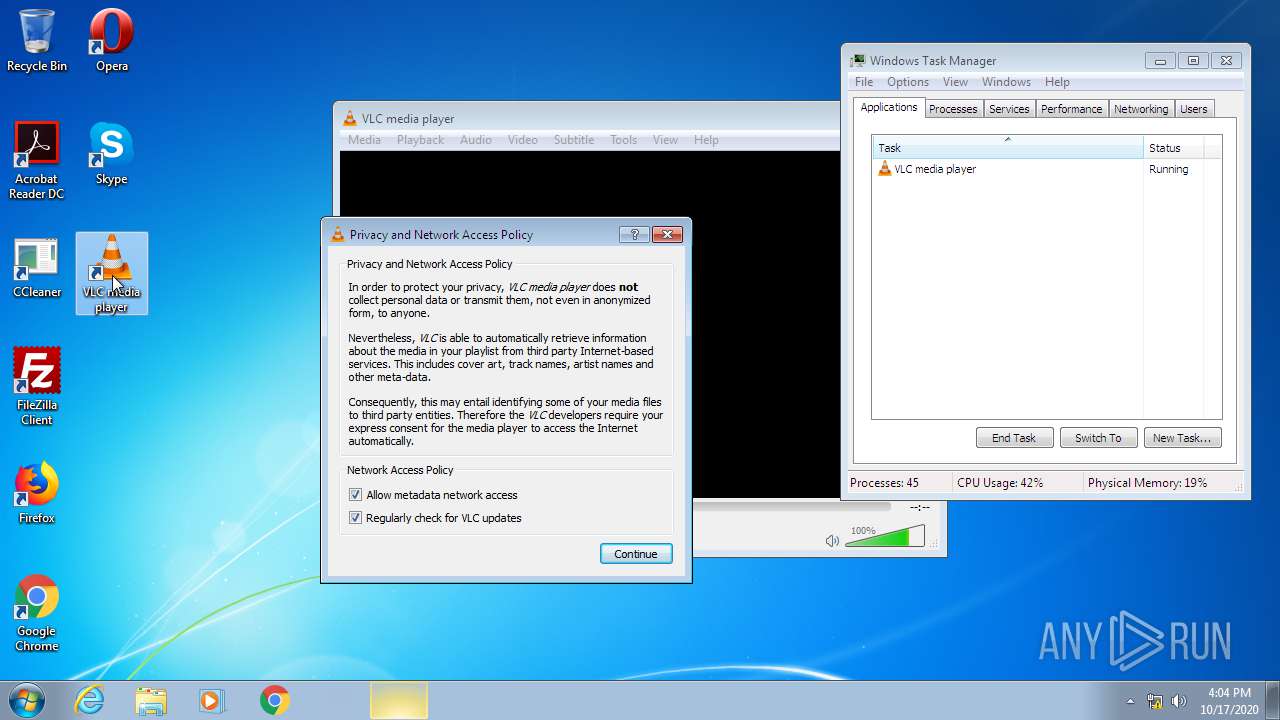
- vlc.exe (PID: 2496)
Reads Internet Cache Settings
- ie4uinit.exe (PID: 3288)
- taskhost.exe (PID: 2660)
Writes to a desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 3288)
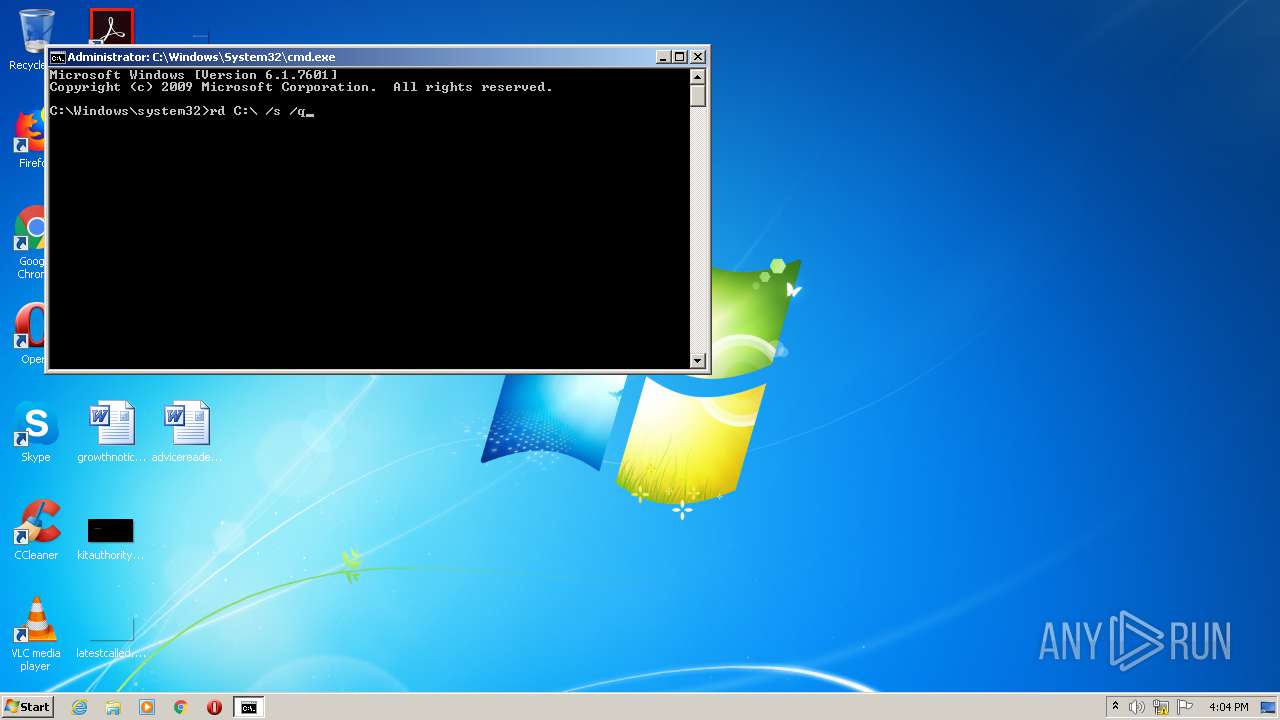
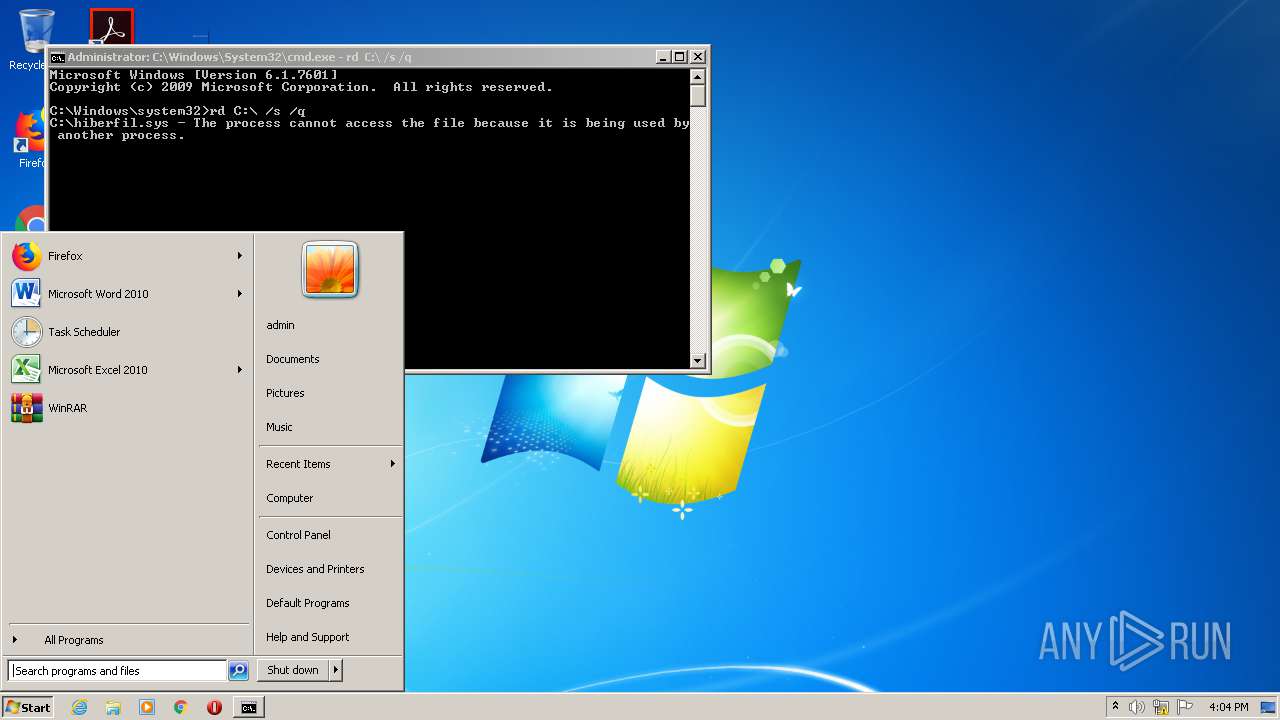
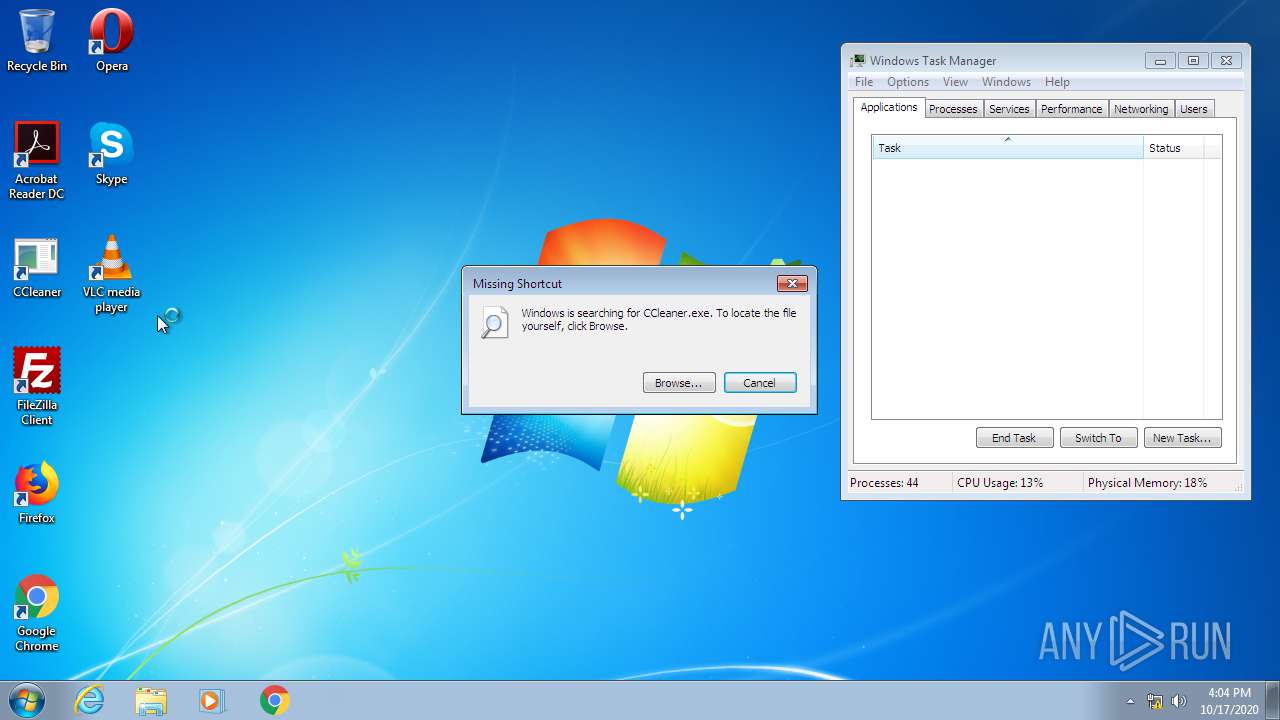
Removes files from Windows directory
- cmd.exe (PID: 3584)
INFO
Application was dropped or rewritten from another process
- unlocker-setup.tmp (PID: 1724)
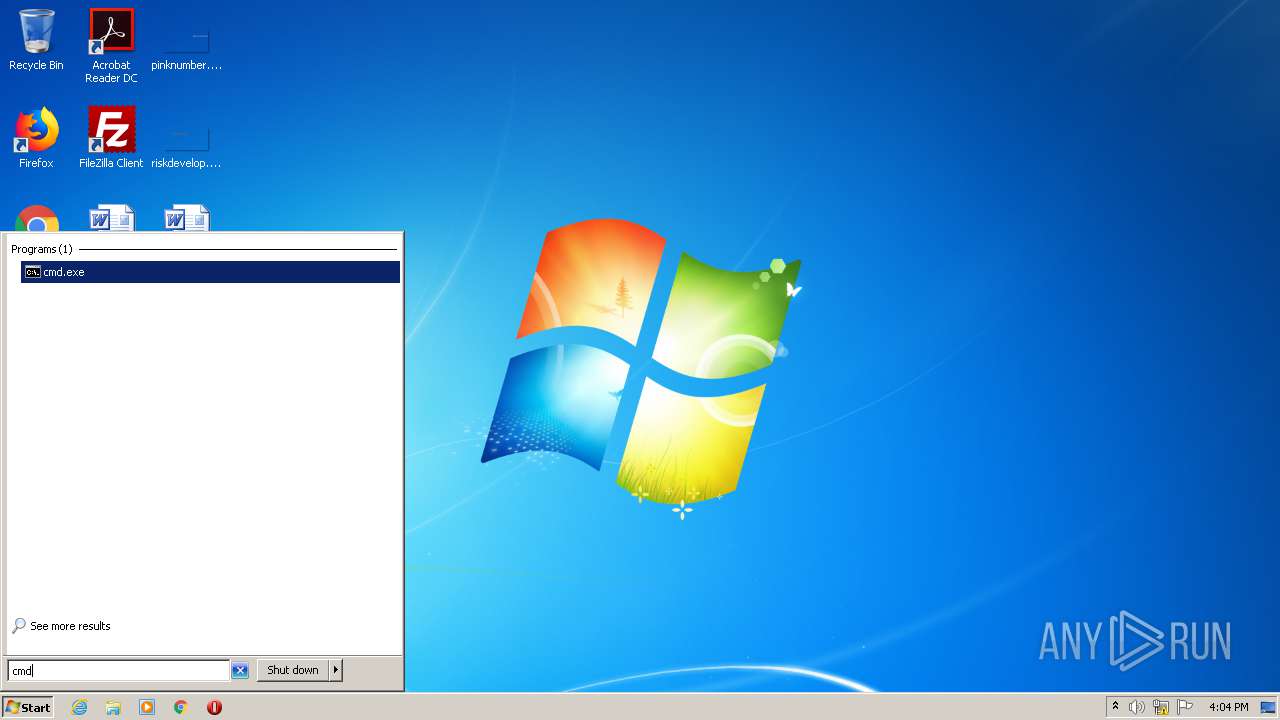
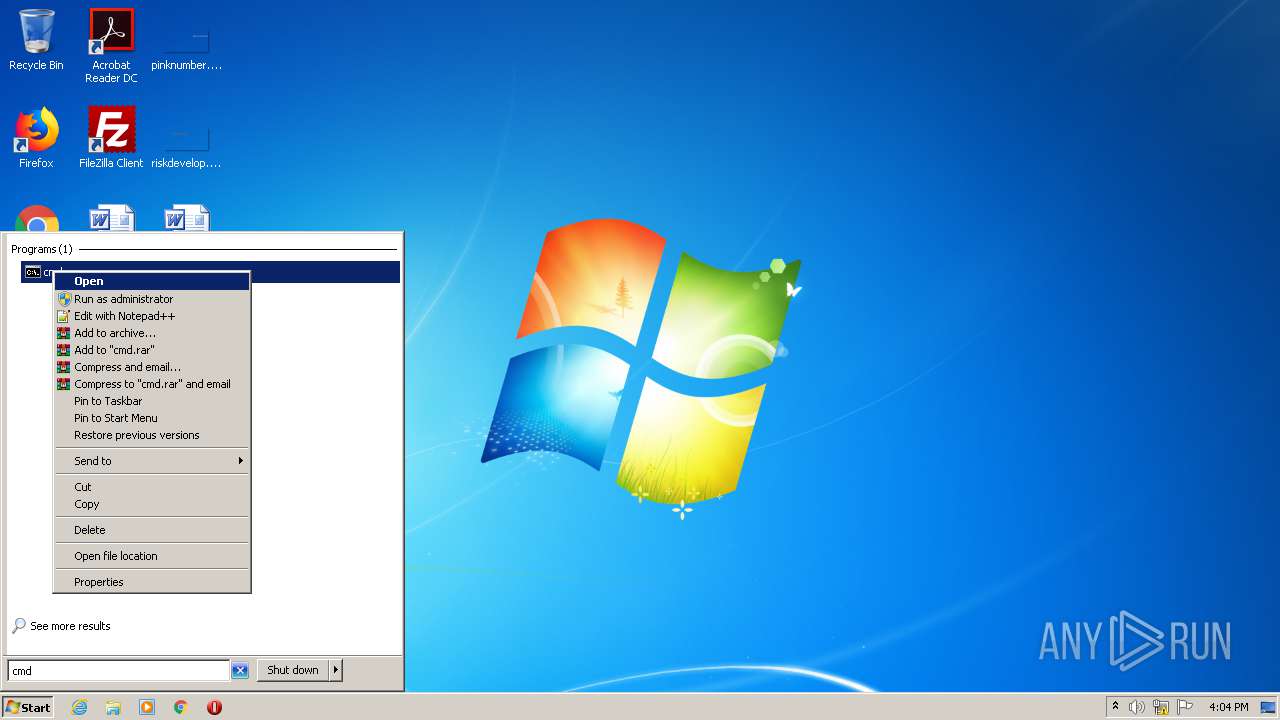
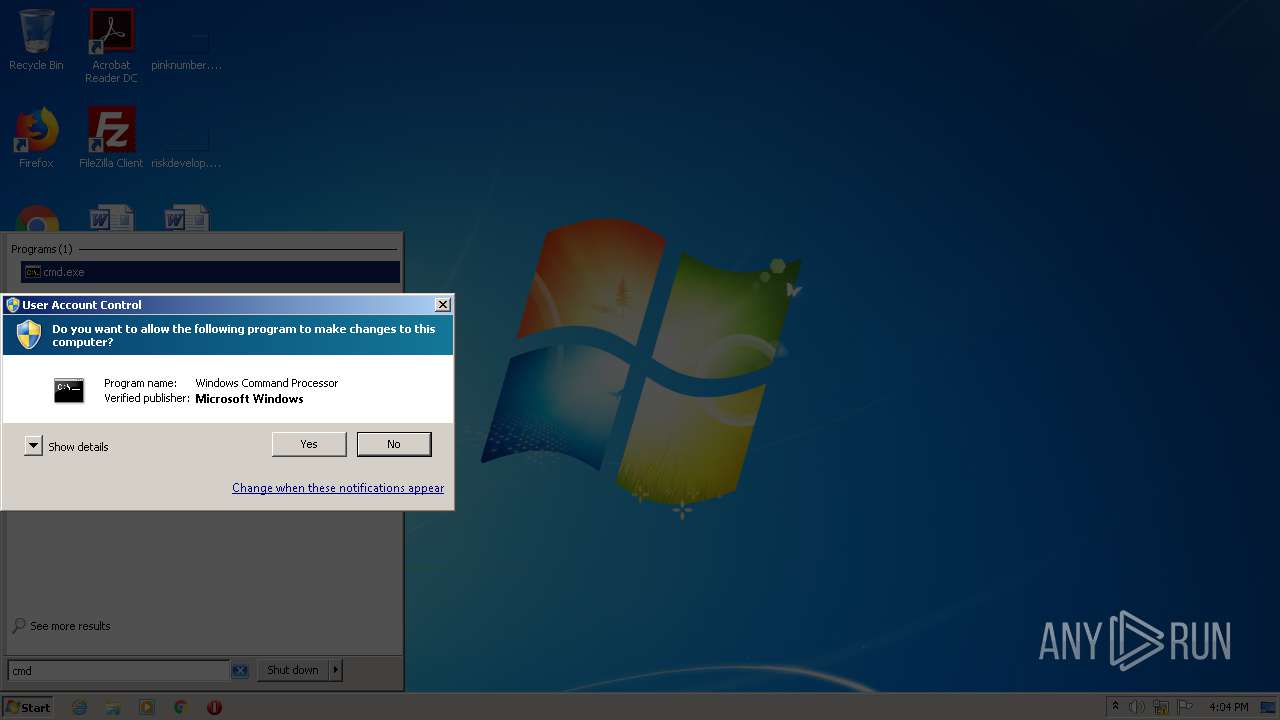
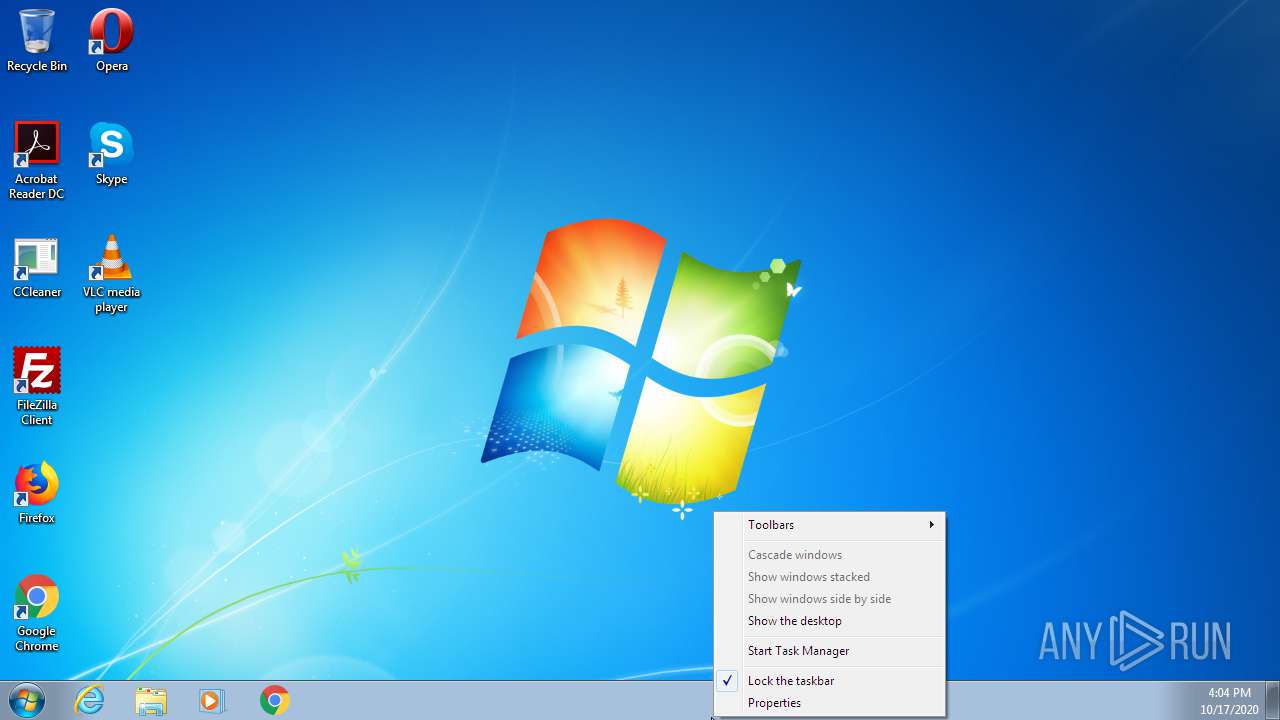
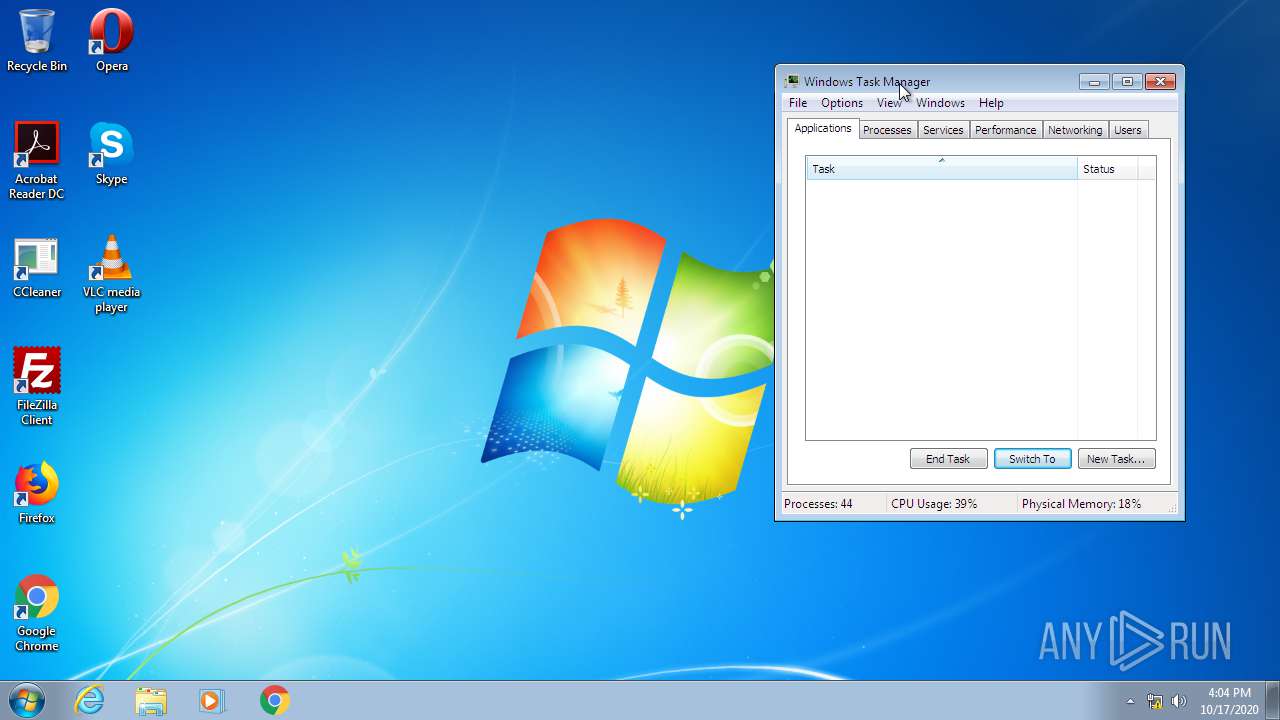
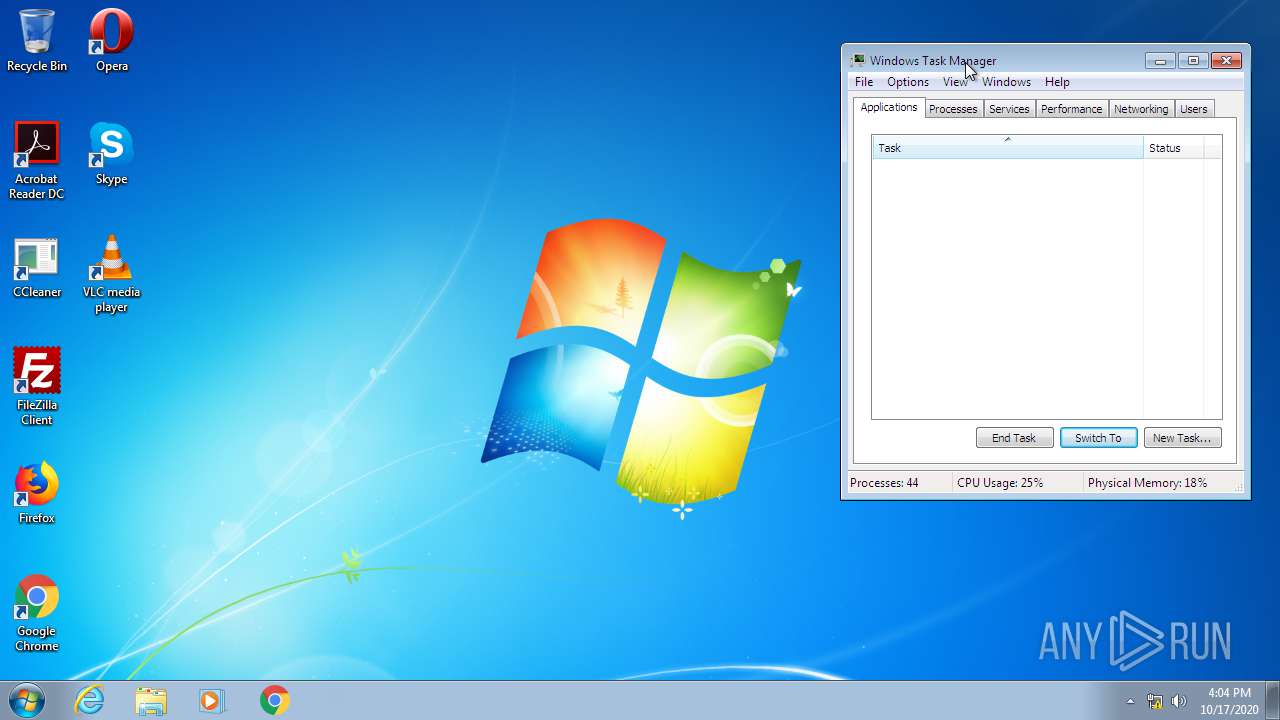
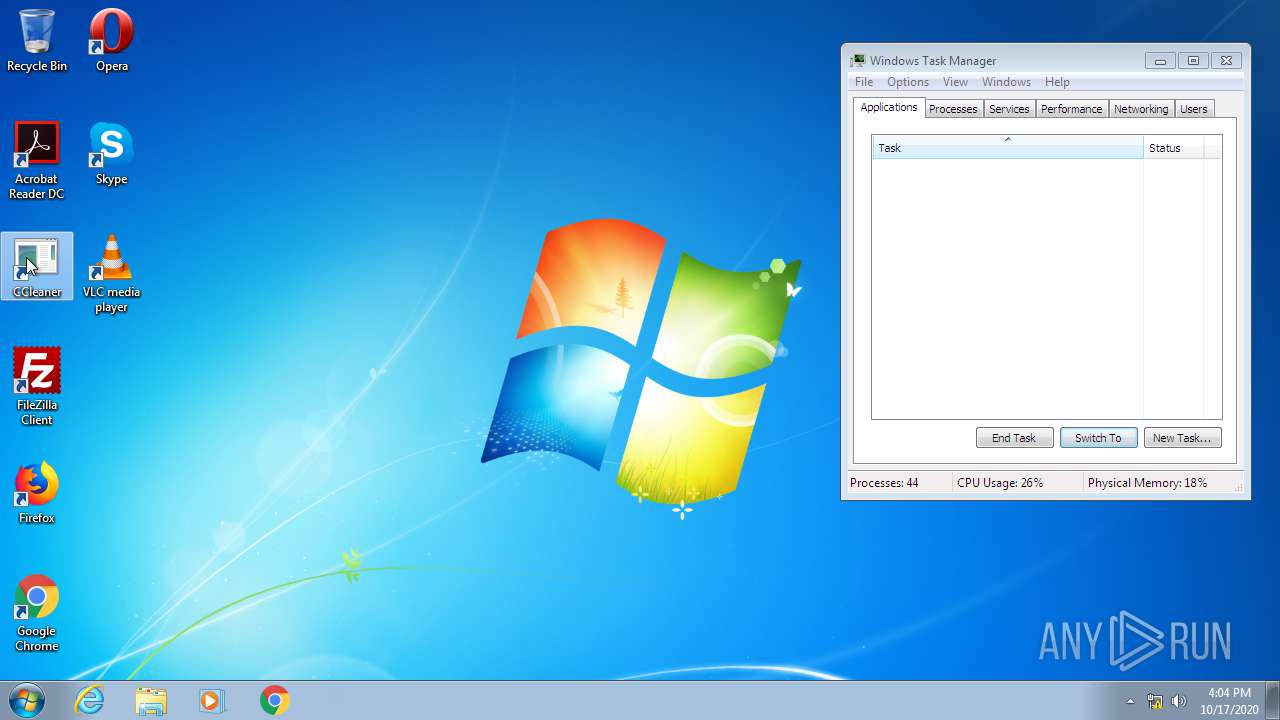
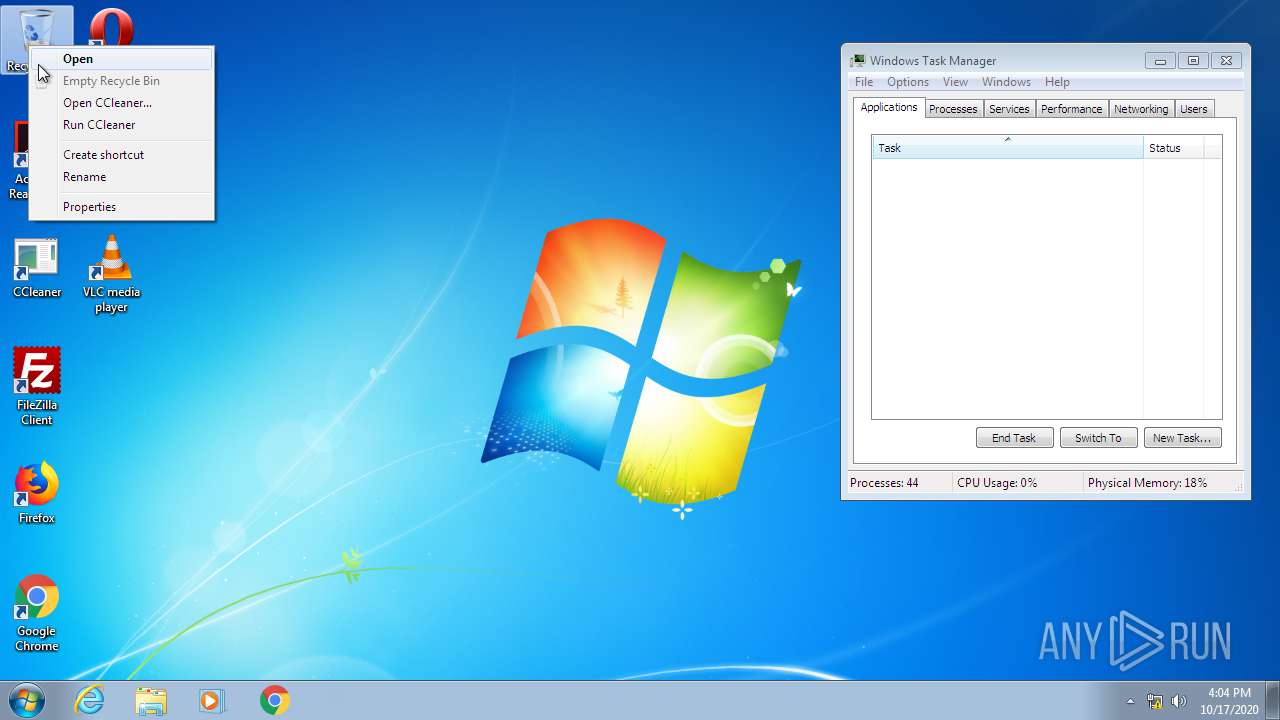
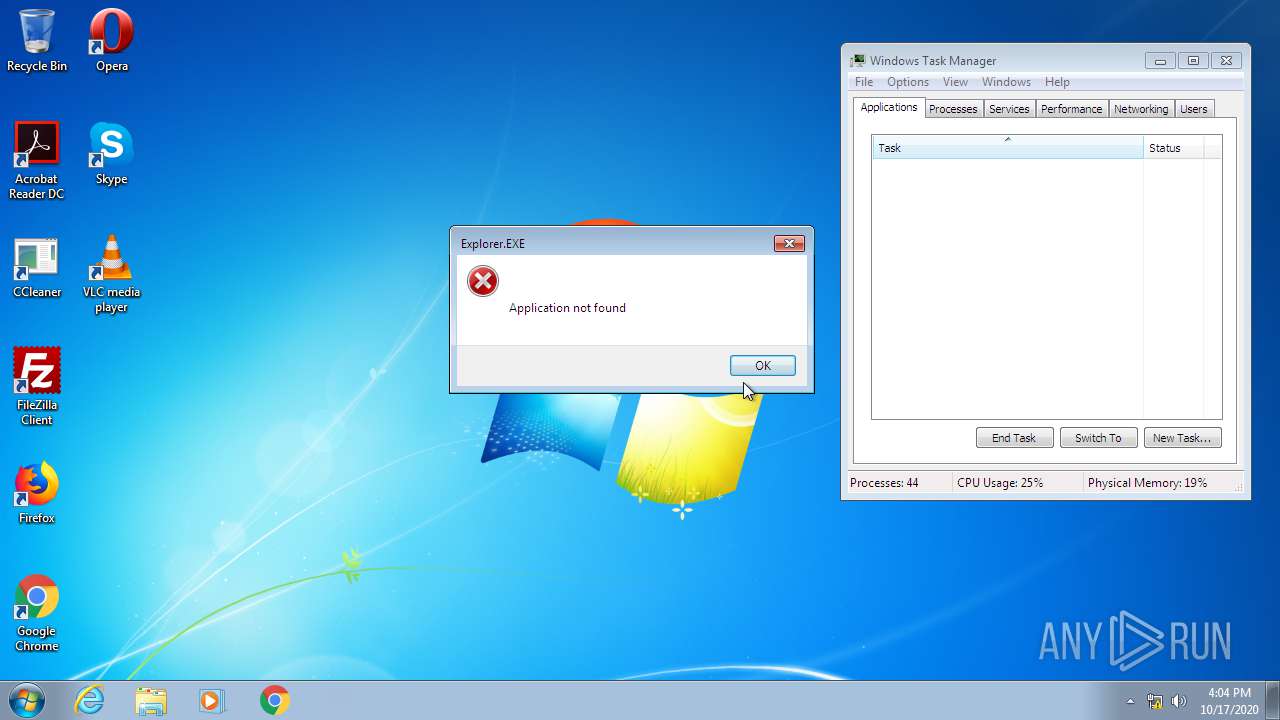
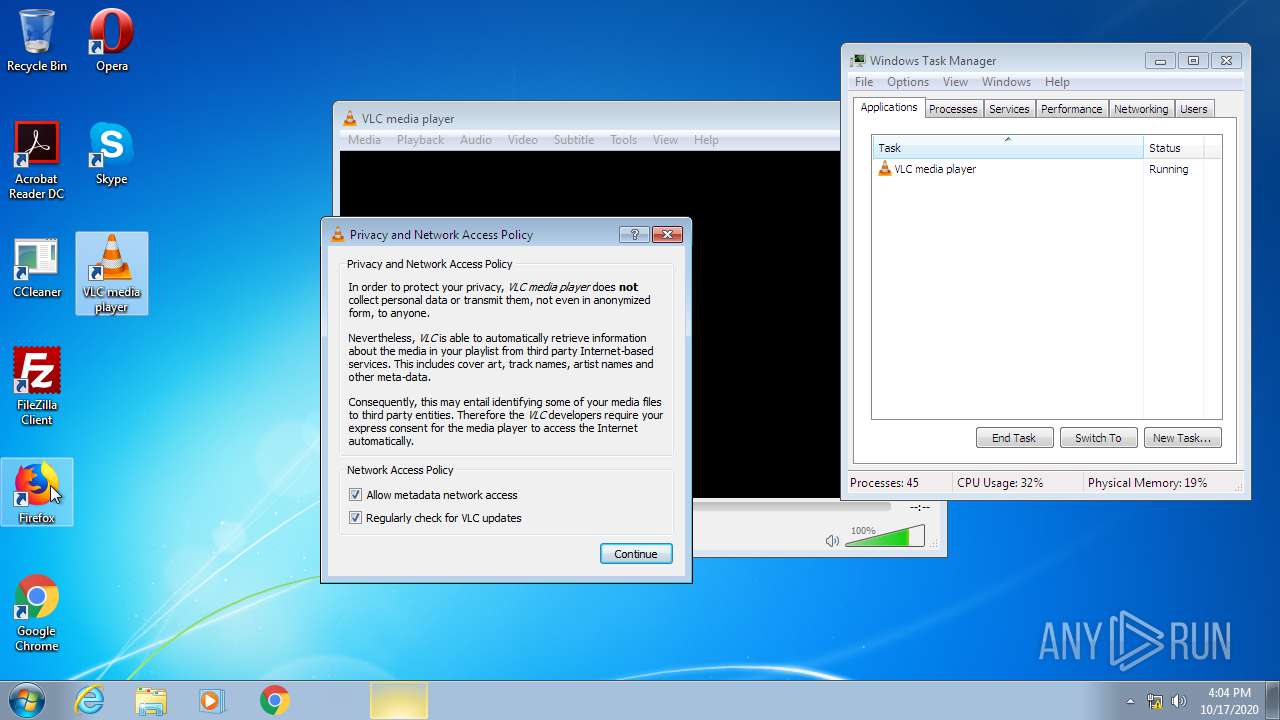
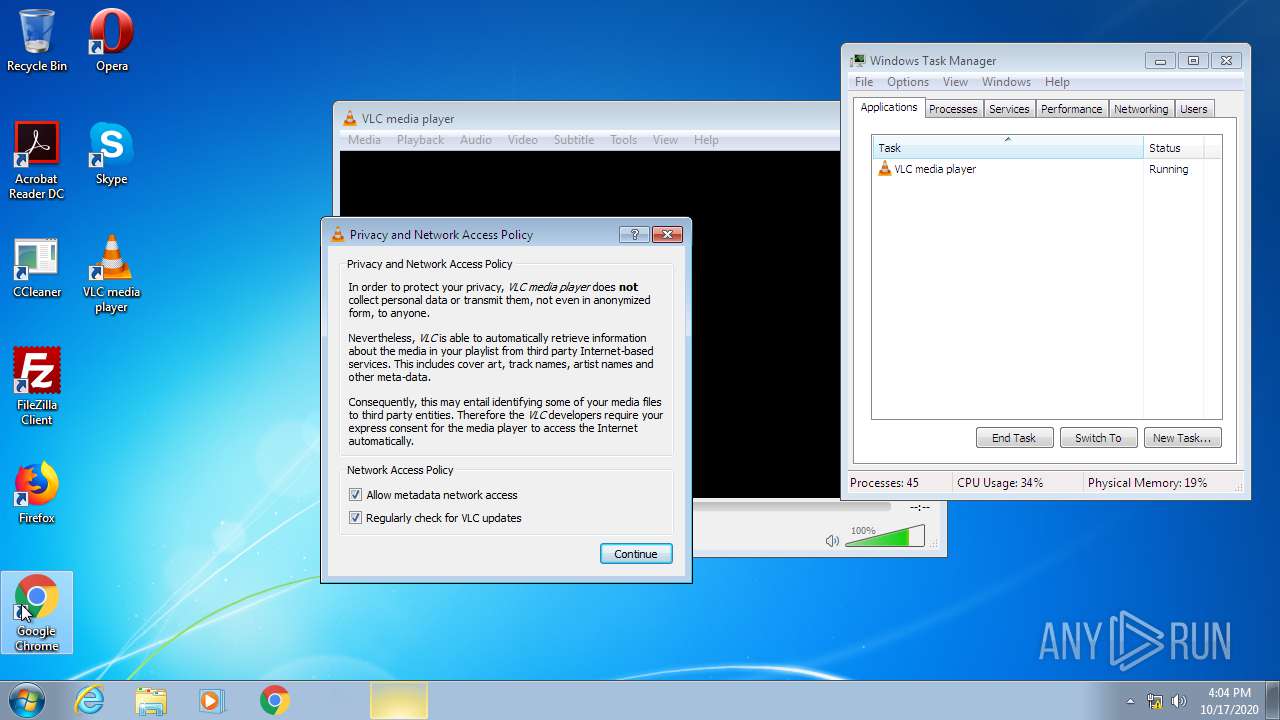
Manual execution by user
- ie4uinit.exe (PID: 3288)
- cmd.exe (PID: 3584)
- ie4uinit.exe (PID: 3368)
- chrmstp.exe (PID: 3896)
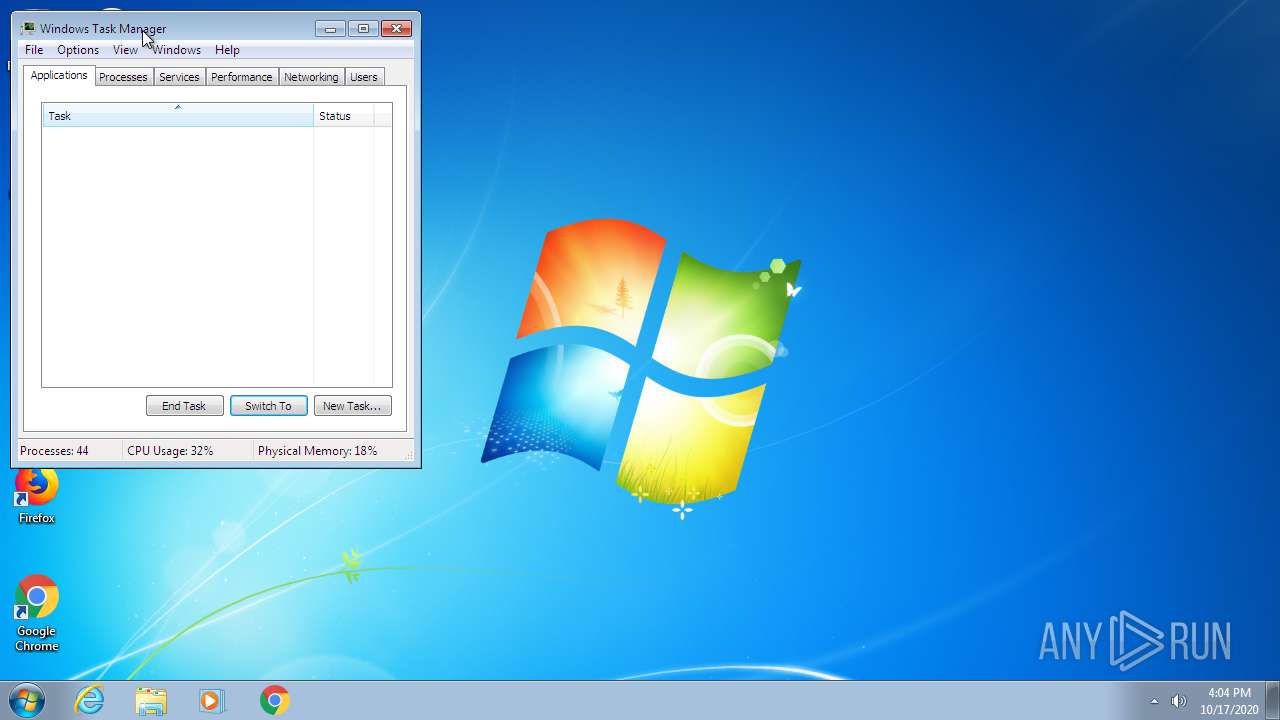
- taskmgr.exe (PID: 1084)
- vlc.exe (PID: 2496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:07:16 15:24:20+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65024 |
| InitializedDataSize: | 73728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.2.1 |
| ProductVersionNumber: | 1.1.2.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | IObit |
| FileDescription: | IObit Unlocker |
| FileVersion: | 1.1.2.1 |
| LegalCopyright: | Copyright © 2005-2018 |
| ProductName: | IObit Unlocker |
| ProductVersion: | 1.1.2.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jul-2015 13:24:20 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | IObit |
| FileDescription: | IObit Unlocker |
| FileVersion: | 1.1.2.1 |
| LegalCopyright: | Copyright © 2005-2018 |
| ProductName: | IObit Unlocker |
| ProductVersion: | 1.1.2.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 16-Jul-2015 13:24:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F134 | 0x0000F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39165 |
.itext | 0x00011000 | 0x00000B44 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.74124 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.24753 |
.bss | 0x00013000 | 0x000056B8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000DD0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97188 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0001000C | 0x00010200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.32948 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.62094 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.61321 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.08823 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.32232 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 6.35527 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 6.11081 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
71
Monitored processes
15
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | C:\Windows\System32\rundll32 advpack.dll,LaunchINFSectionEx C:\Windows\system32\ieuinit.inf,Install,,36 | C:\Windows\System32\rundll32.exe | — | ie4uinit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1084 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | "C:\Users\admin\AppData\Local\Temp\is-I39SL.tmp\unlocker-setup.tmp" /SL5="$A0164,1967081,139776,C:\Users\admin\AppData\Local\Temp\unlocker-setup.exe" | C:\Users\admin\AppData\Local\Temp\is-I39SL.tmp\unlocker-setup.tmp | — | unlocker-setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 2 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1792 | C:\Windows\system32\RunDll32.exe C:\Windows\system32\migration\WininetPlugin.dll,MigrateCacheForUser /m /0 | C:\Windows\system32\RunDll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\75.0.3770.100\Installer\chrmstp.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Windows\TEMP\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0xd0,0xd8,0xdc,0xcc,0xe0,0xc42238,0xc42248,0xc42254 | C:\Program Files\Google\Chrome\Application\75.0.3770.100\Installer\chrmstp.exe | — | chrmstp.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2416 | C:\Windows\System32\rundll32 C:\Windows\system32\migration\WininetPlugin.dll,MigrateCacheForUser /m | C:\Windows\System32\rundll32.exe | — | ie4uinit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | C:\Windows\system32\RunDll32.exe C:\Windows\system32\migration\WininetPlugin.dll,MigrateCacheForUser /m /0 | C:\Windows\system32\RunDll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
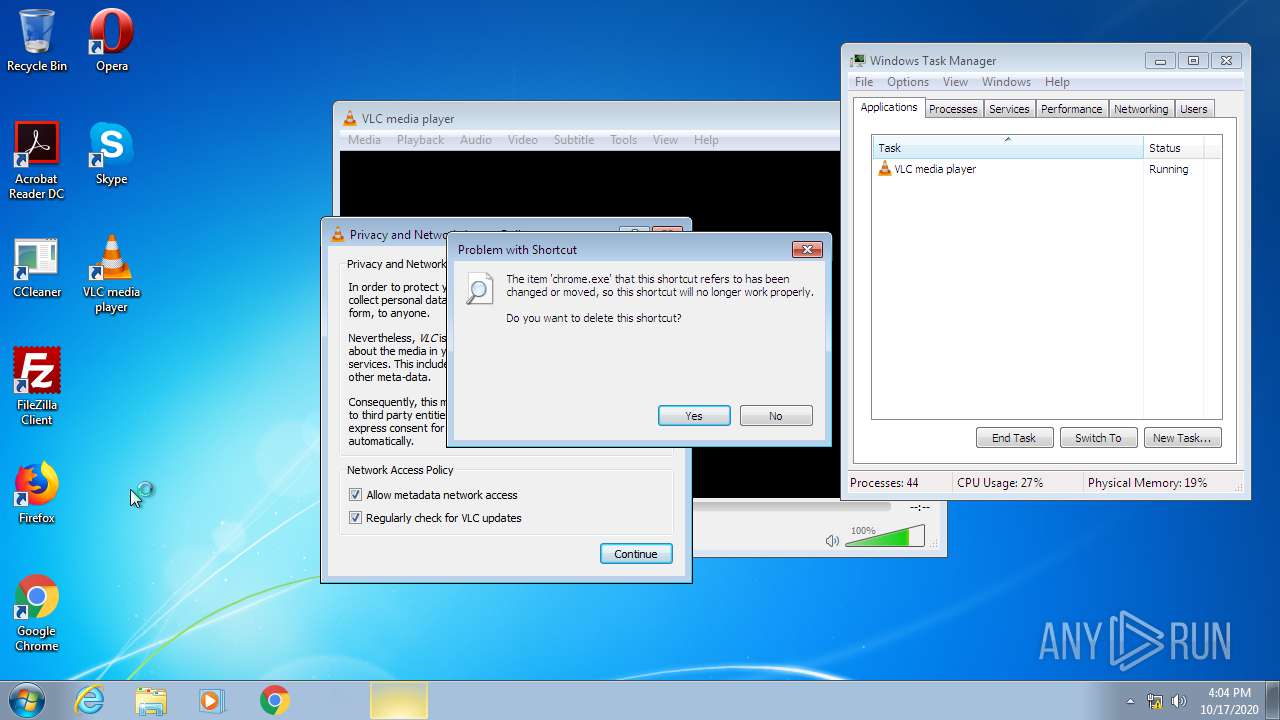
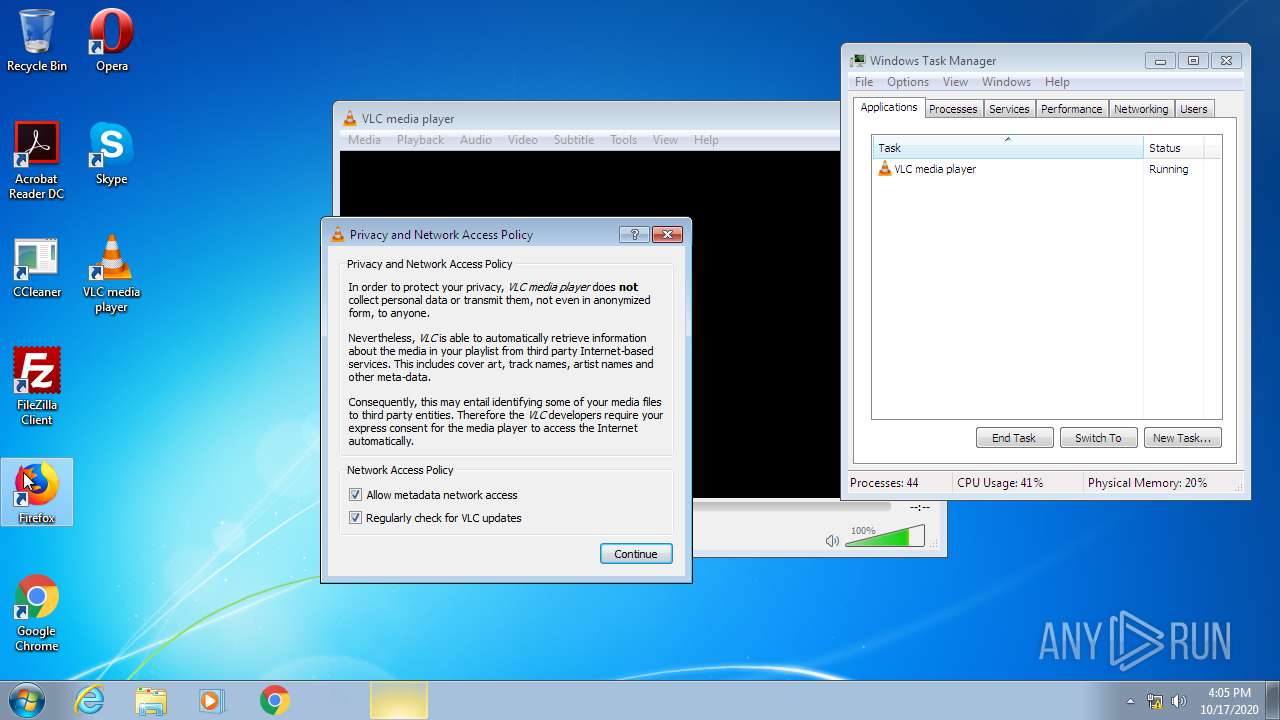
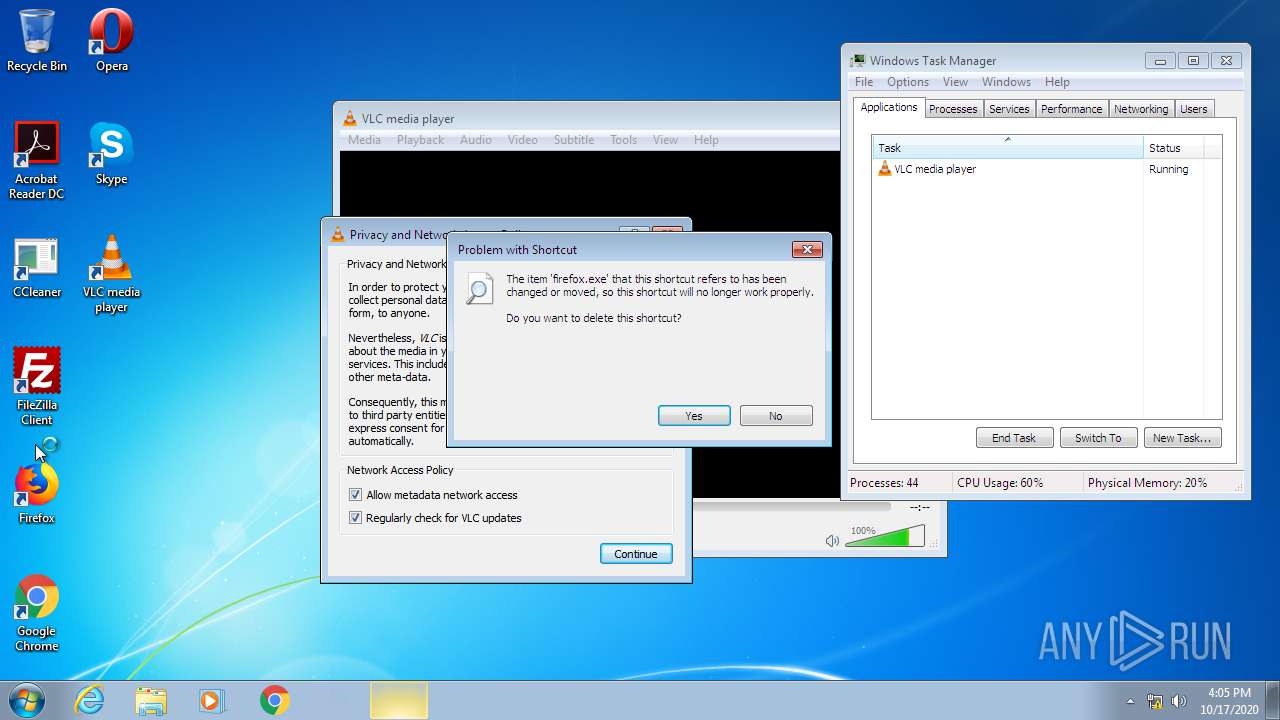
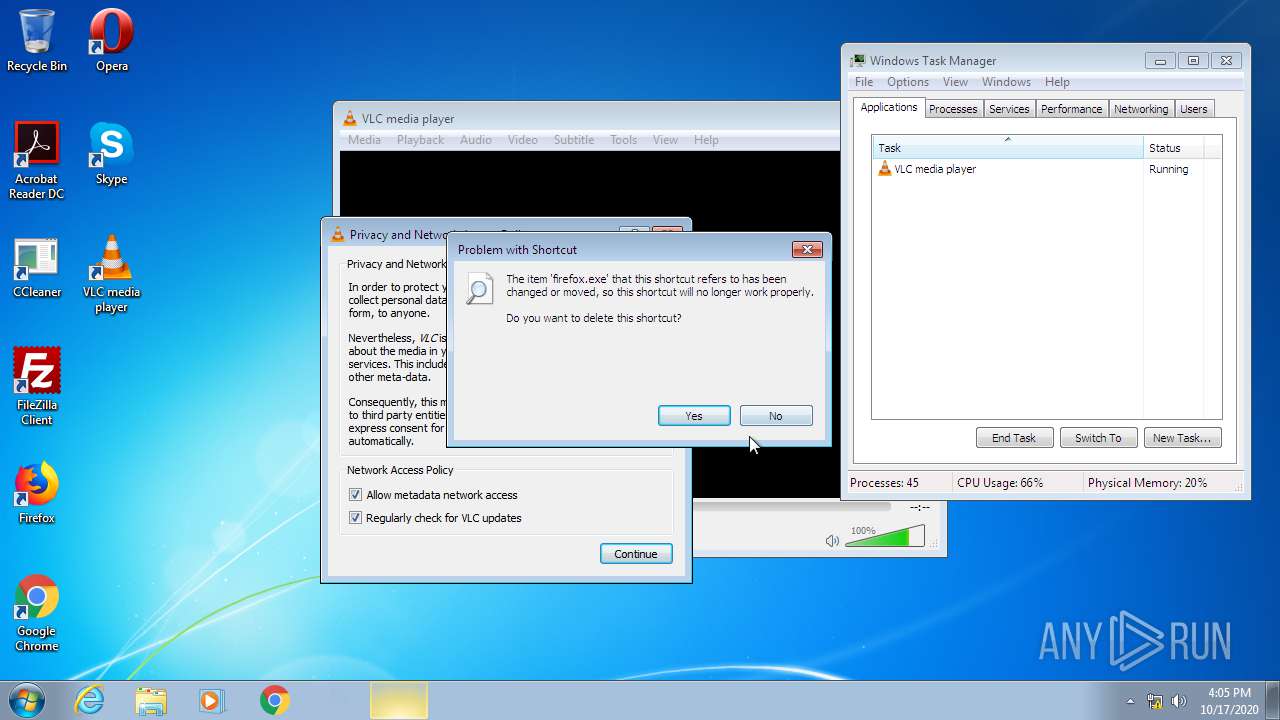
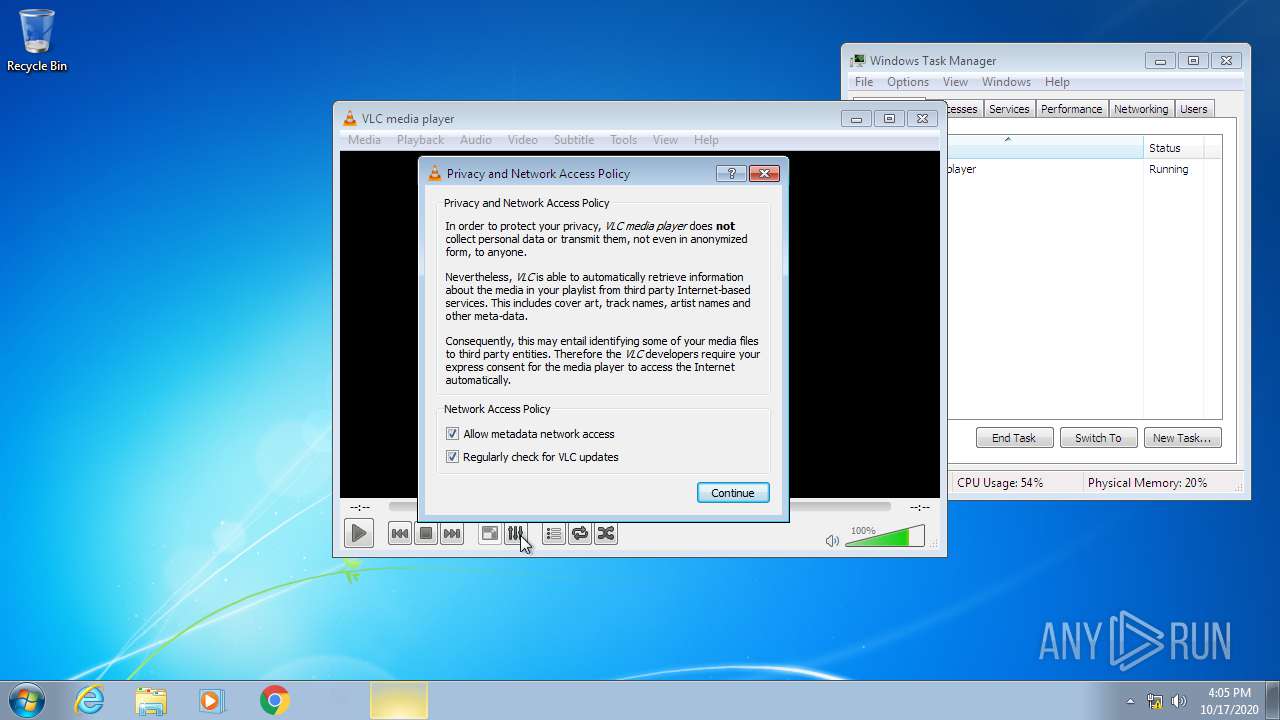
| 2496 | "C:\Program Files\VideoLAN\VLC\vlc.exe" | C:\Program Files\VideoLAN\VLC\vlc.exe | — | Explorer.EXE | |||||||||||
User: admin Company: VideoLAN Integrity Level: HIGH Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\AppData\Local\Temp\unlocker-setup.exe" | C:\Users\admin\AppData\Local\Temp\unlocker-setup.exe | explorer.exe | ||||||||||||
User: admin Company: IObit Integrity Level: MEDIUM Description: IObit Unlocker Exit code: 2 Version: 1.1.2.1 Modules
| |||||||||||||||
| 2660 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 014
Read events
704
Write events
306
Delete events
4
Modification events
| (PID) Process: | (3288) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Suggested Sites |
| Operation: | write | Name: | LogFileFolder |
Value: C:\Users\Administrator\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low | |||
| (PID) Process: | (3288) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\CLSID\{871C5380-42A0-1069-A2EA-08002B30309D}\ShellFolder |
| Operation: | write | Name: | Attributes |
Value: 0 | |||
| (PID) Process: | (3288) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Active Setup\Installed Components\>{26923b43-4d38-484f-9b9e-de460746276c} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3288) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\BrowserEmulation |
| Operation: | write | Name: | CVListTTL |
Value: 0 | |||
| (PID) Process: | (3288) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\3 |
| Operation: | write | Name: | IEPropFontName |
Value: Times New Roman | |||
| (PID) Process: | (3288) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\3 |
| Operation: | write | Name: | IEFixedFontName |
Value: Courier New | |||
| (PID) Process: | (3288) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\4 |
| Operation: | write | Name: | IEPropFontName |
Value: Times New Roman | |||
| (PID) Process: | (3288) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\4 |
| Operation: | write | Name: | IEFixedFontName |
Value: Courier New | |||
| (PID) Process: | (3288) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\5 |
| Operation: | write | Name: | IEPropFontName |
Value: Times New Roman | |||
| (PID) Process: | (3288) ie4uinit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\International\Scripts\5 |
| Operation: | write | Name: | IEFixedFontName |
Value: Courier New | |||
Executable files
1
Suspicious files
7
Text files
62
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3288 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Temp\RGIC539.tmp | — | |
MD5:— | SHA256:— | |||
| 3288 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Temp\RGIC569.tmp | — | |
MD5:— | SHA256:— | |||
| 3288 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Temp\RGIC694.tmp | — | |
MD5:— | SHA256:— | |||
| 3288 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Temp\RGIC6C4.tmp | — | |
MD5:— | SHA256:— | |||
| 3288 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Temp\RGIC79F.tmp | — | |
MD5:— | SHA256:— | |||
| 2660 | taskhost.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\WebCache\V01tmp.log | — | |
MD5:— | SHA256:— | |||
| 2660 | taskhost.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\WebCache\V01.log | — | |
MD5:— | SHA256:— | |||
| 2660 | taskhost.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | — | |
MD5:— | SHA256:— | |||
| 2480 | RunDll32.exe | C:\Users\Administrator\AppData\Local\Microsoft\Feeds Cache\1D82PHEW\fwlink[1] | — | |
MD5:— | SHA256:— | |||
| 2480 | RunDll32.exe | C:\Users\Administrator\AppData\Local\Microsoft\Feeds Cache\KZ4WKBBC\fwlink[1] | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report