| File name: | x2_2021.exe |
| Full analysis: | https://app.any.run/tasks/dd4c357a-f722-4fed-8c8b-22c9804418b0 |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2021, 00:03:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1A5E0F59BF10C56542B2C6668E7154F4 |
| SHA1: | 7F5E7D7B2DAF142C5FB2A96412CF831A6203E972 |
| SHA256: | E5A49283D9CDA689F31B9EDC08568C6AF29CD7ED416AFCBBCB1E42FAA0BC9A55 |
| SSDEEP: | 98304:JSf2+lB5b9R4FSamiBh38fB73+bVq7qplj4mj7hpqa:JStlvsgiBh38p73+bVaylj4mj9P |
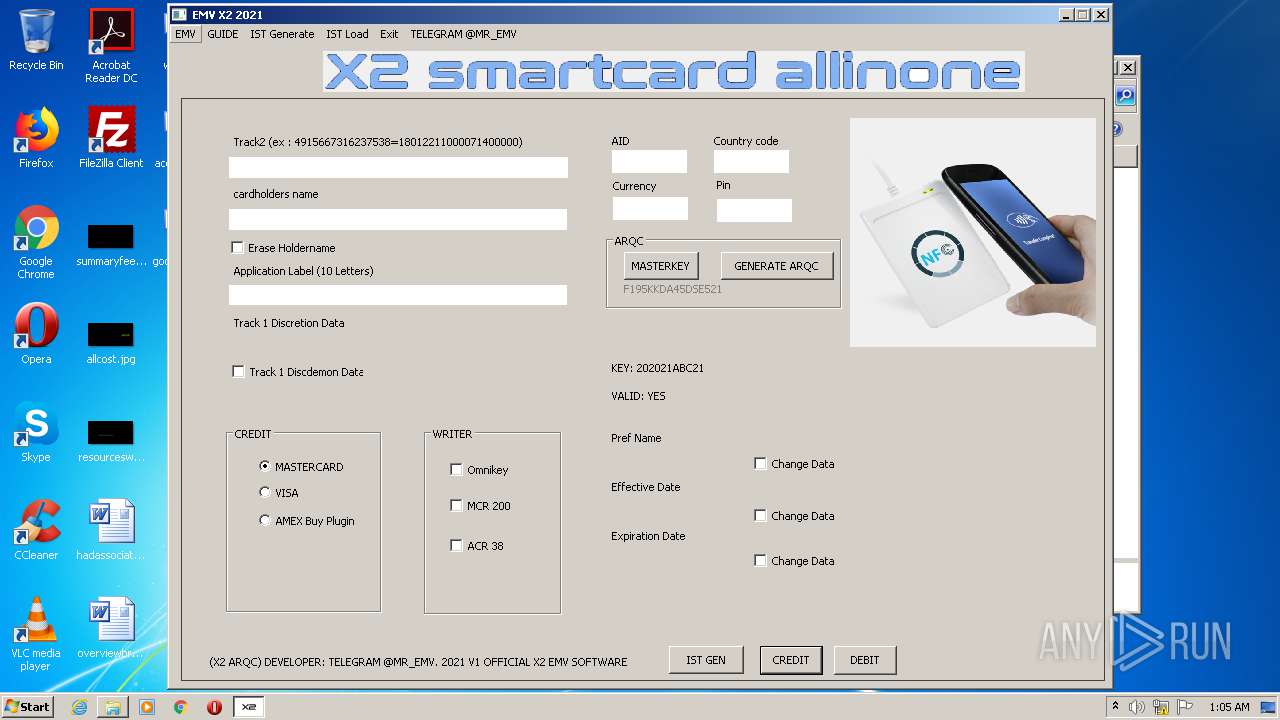
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3180)
- auth removed x2.exe (PID: 1964)
Writes to a start menu file
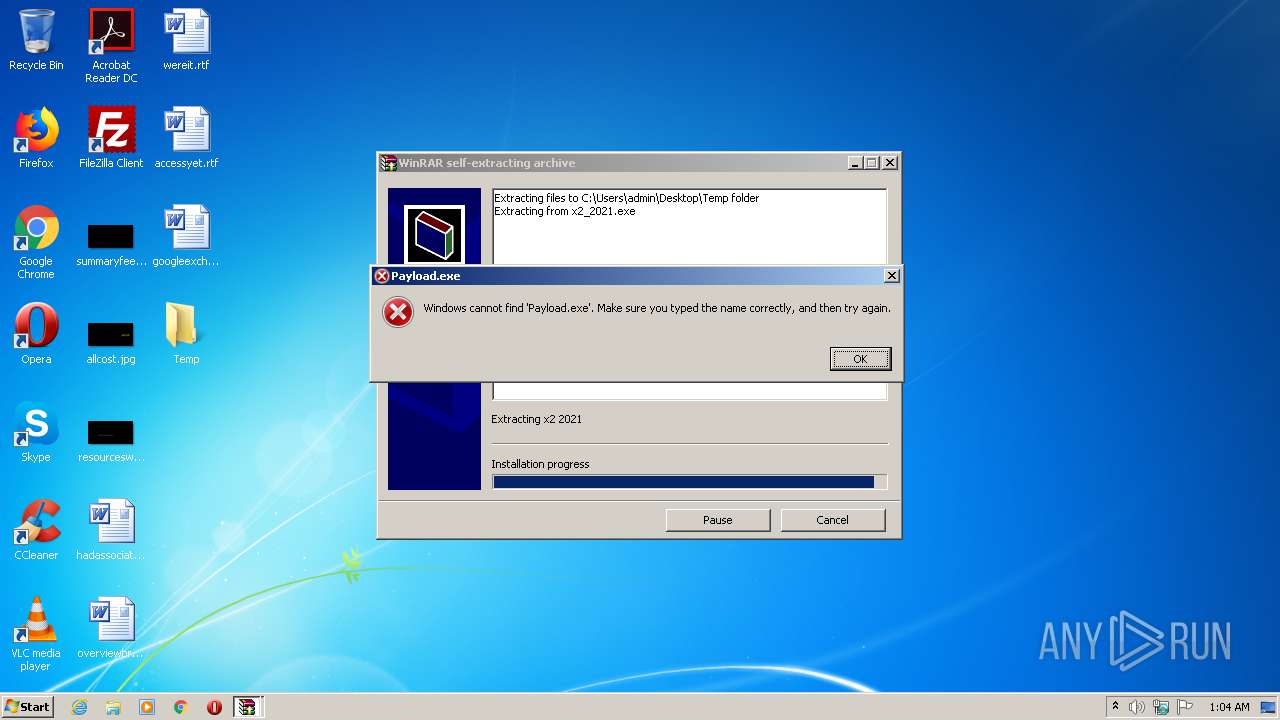
- Payload.exe (PID: 2456)
Application was dropped or rewritten from another process
- Payload.exe (PID: 2456)
- auth removed x2.exe (PID: 1964)
Drops executable file immediately after starts
- Payload.exe (PID: 2456)
SUSPICIOUS
Executable content was dropped or overwritten
- x2_2021.exe (PID: 1692)
- Payload.exe (PID: 2456)
Reads internet explorer settings
- x2_2021.exe (PID: 1692)
Drops a file with a compile date too recent
- x2_2021.exe (PID: 1692)
- Payload.exe (PID: 2456)
Creates files in the user directory
- Payload.exe (PID: 2456)
Drops a file that was compiled in debug mode
- x2_2021.exe (PID: 1692)
INFO
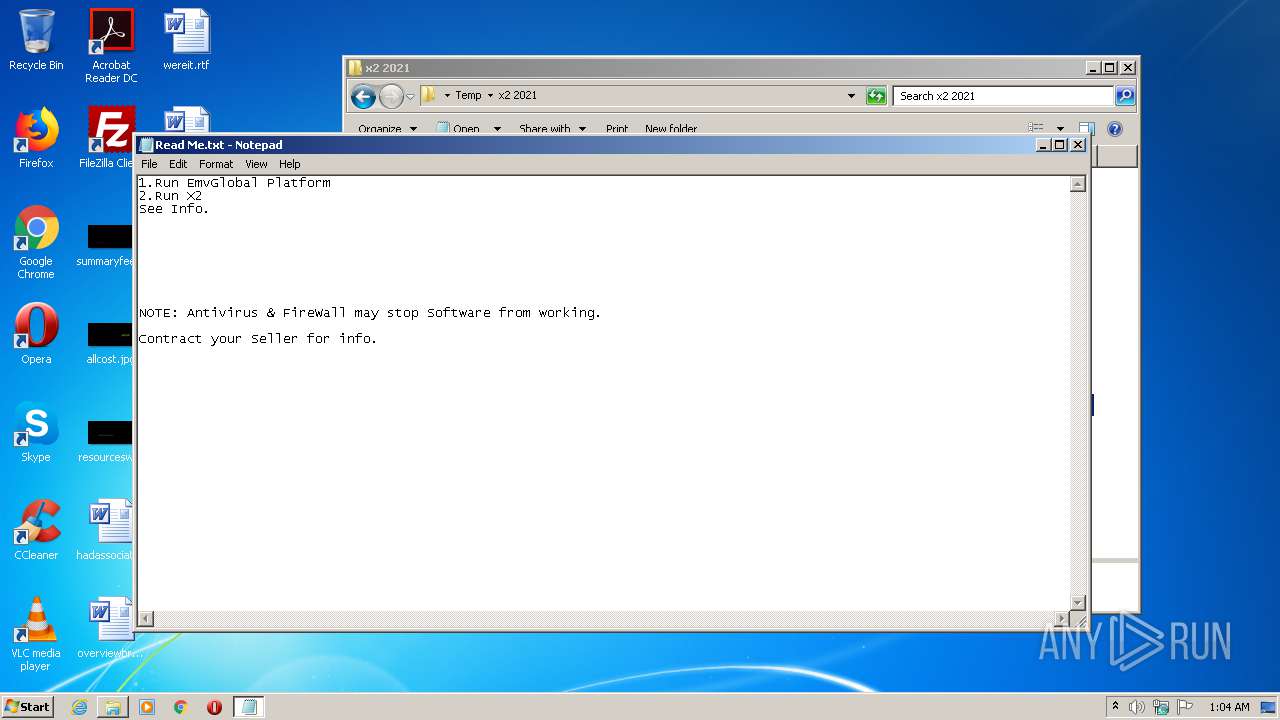
Manual execution by user
- NOTEPAD.EXE (PID: 3324)
- Payload.exe (PID: 2456)
- auth removed x2.exe (PID: 1964)
Dropped object may contain Bitcoin addresses
- x2_2021.exe (PID: 1692)
- Payload.exe (PID: 2456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1cab5 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 196096 |
| CodeSize: | 188416 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2016:08:14 21:15:49+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFE8 | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71025 |
.rdata | 0x0002F000 | 0x000099D0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15287 |
.data | 0x00039000 | 0x0001F8B8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29547 |
.gfids | 0x00059000 | 0x000000F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12367 |
.rsrc | 0x0005A000 | 0x00004680 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.63811 |
.reloc | 0x0005F000 | 0x00001F8C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
12 | 3.12889 | 358 | UNKNOWN | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
43
Monitored processes
5
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
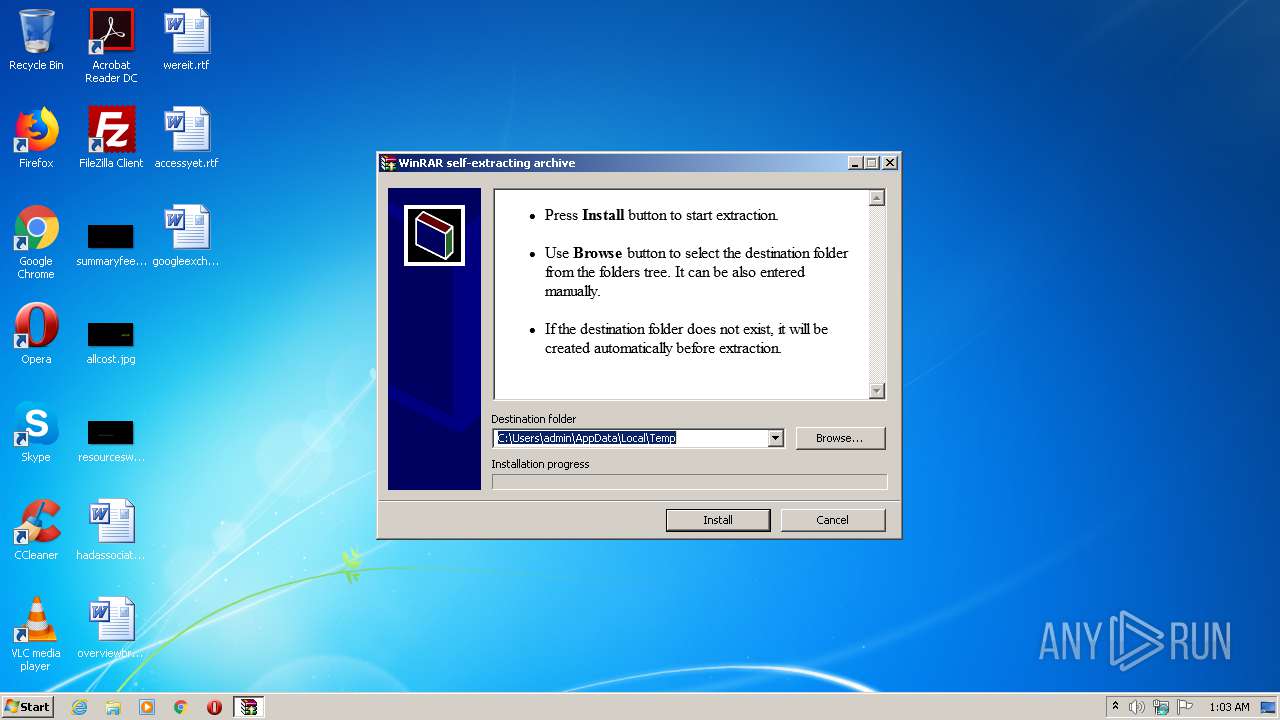
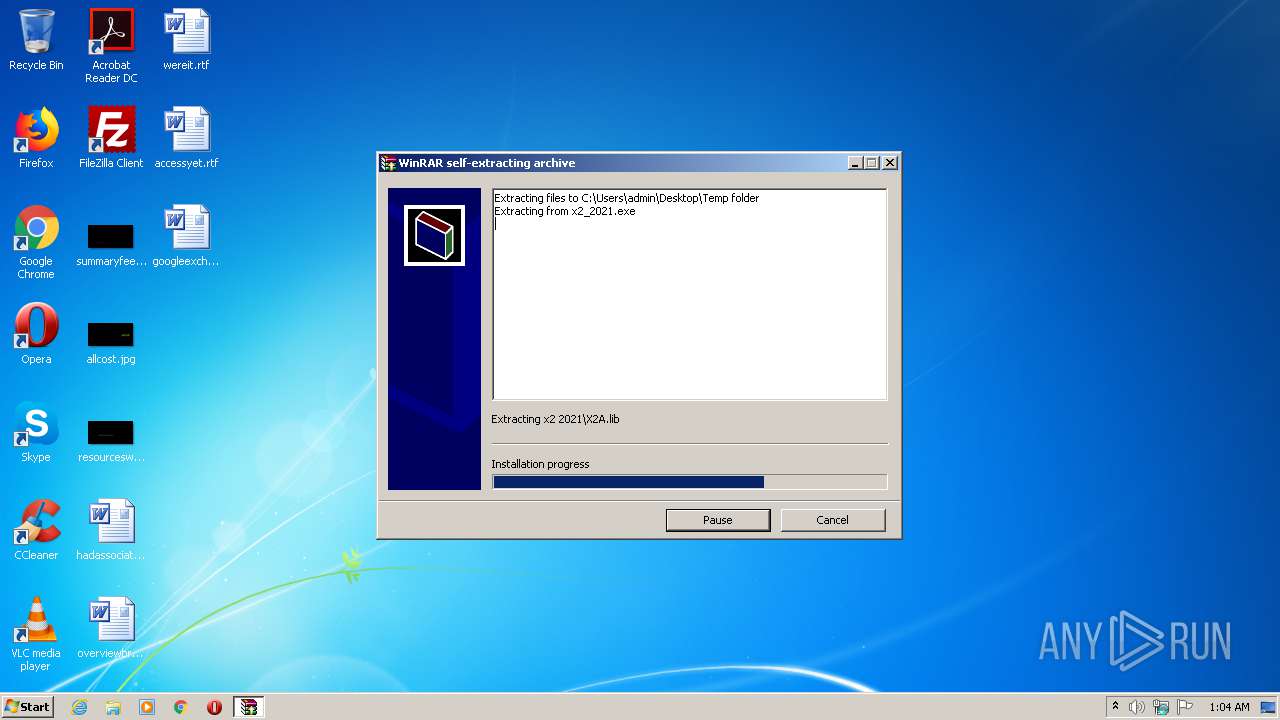
| 1692 | "C:\Users\admin\AppData\Local\Temp\x2_2021.exe" | C:\Users\admin\AppData\Local\Temp\x2_2021.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
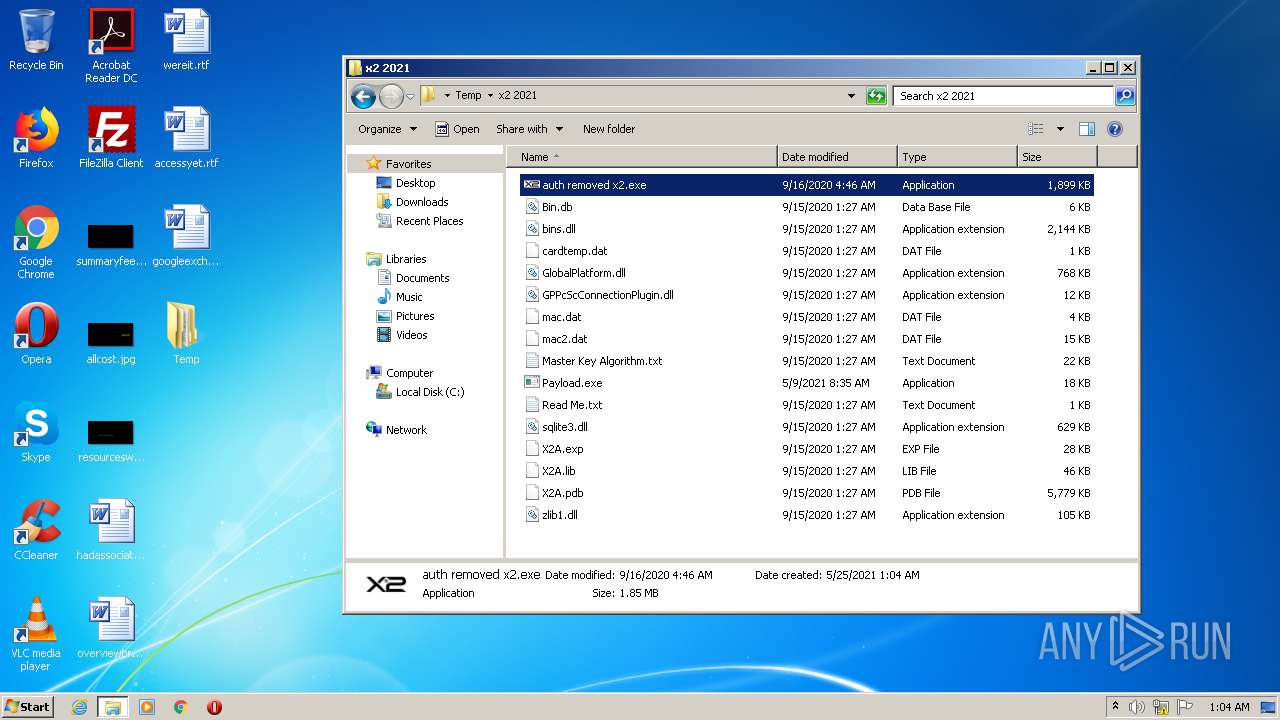
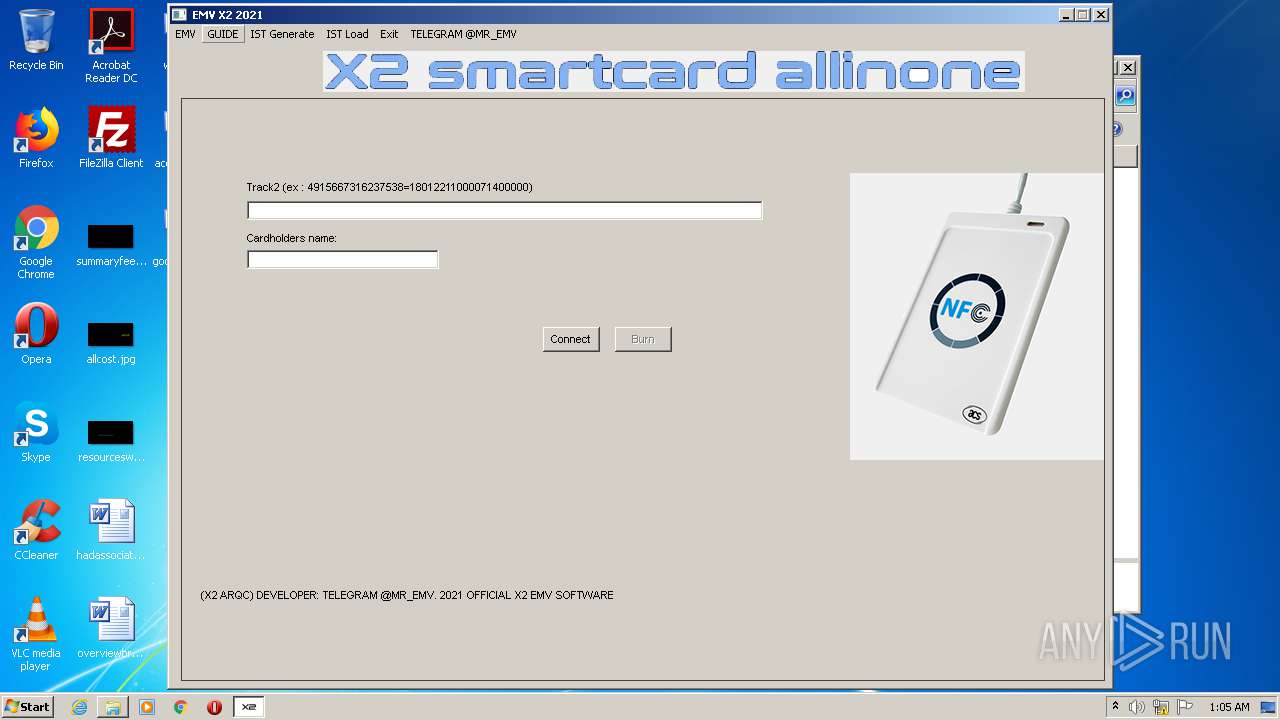
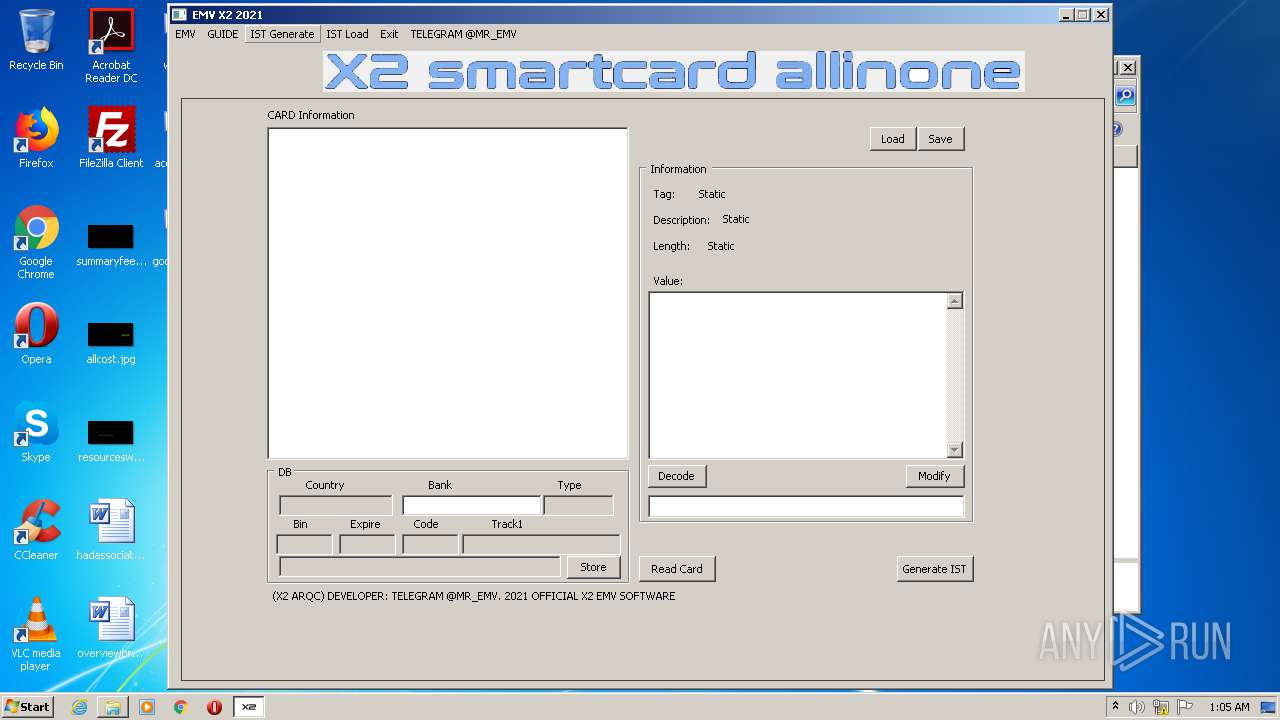
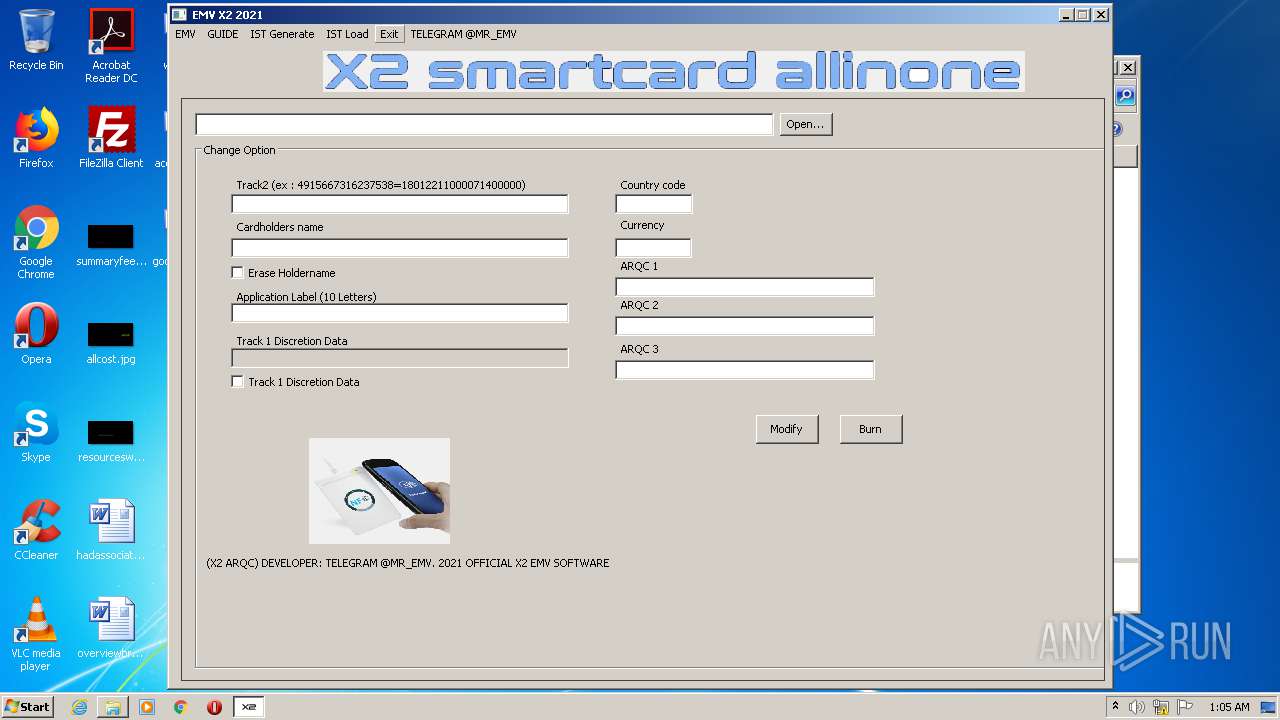
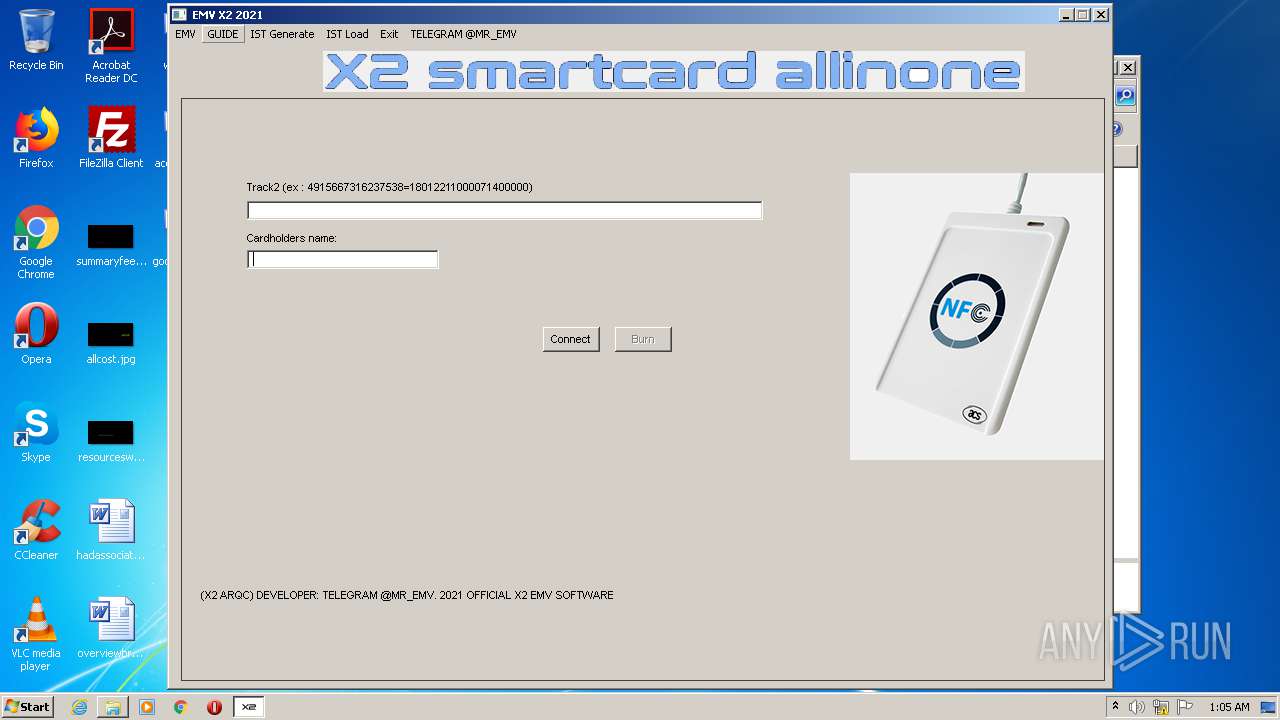
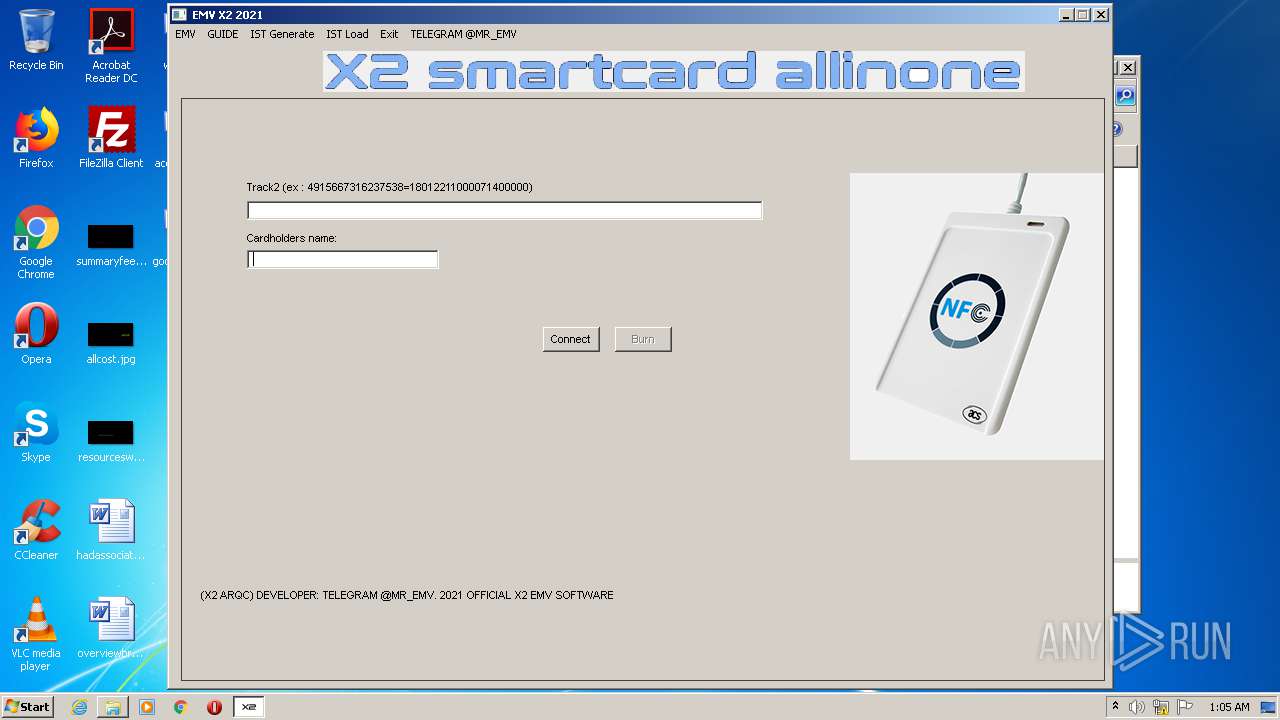
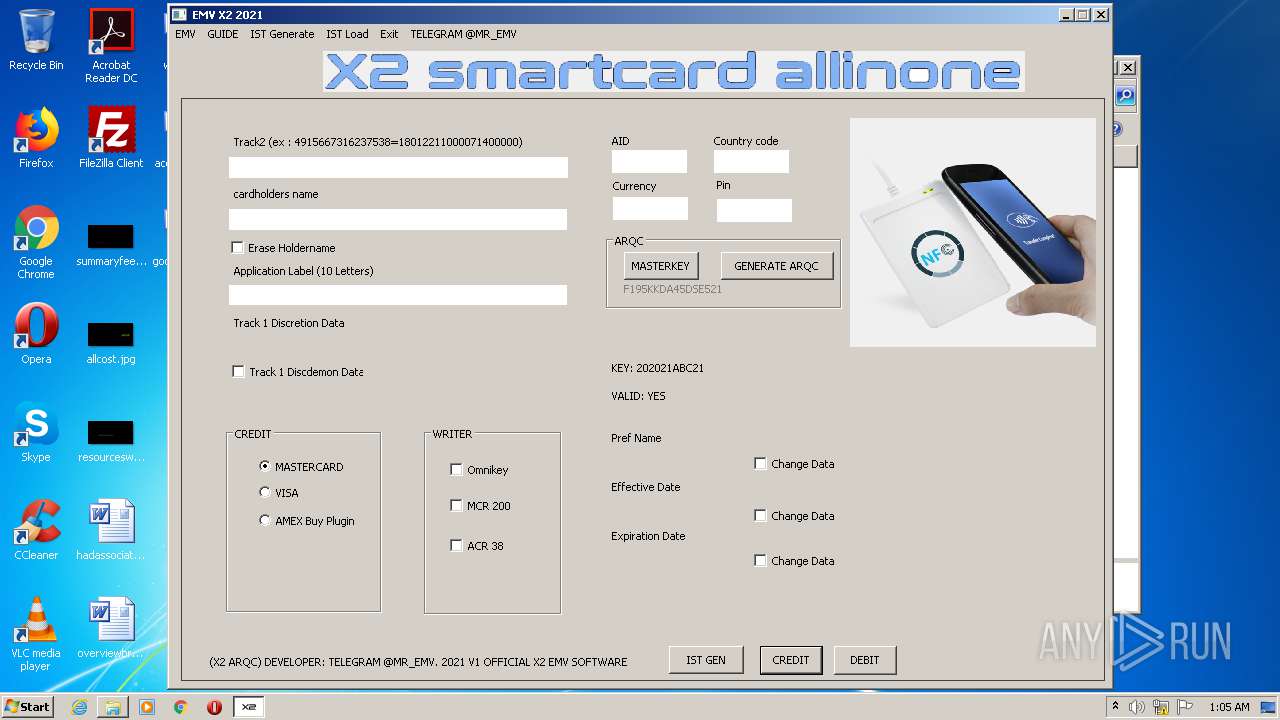
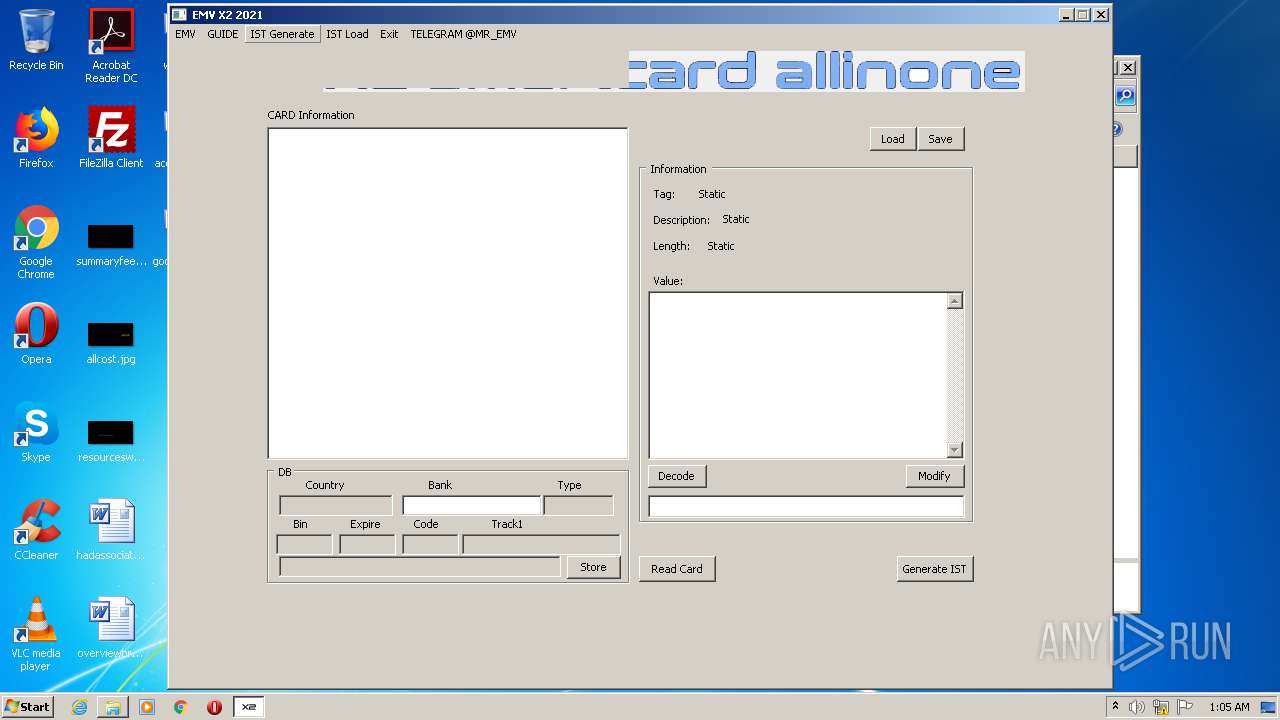
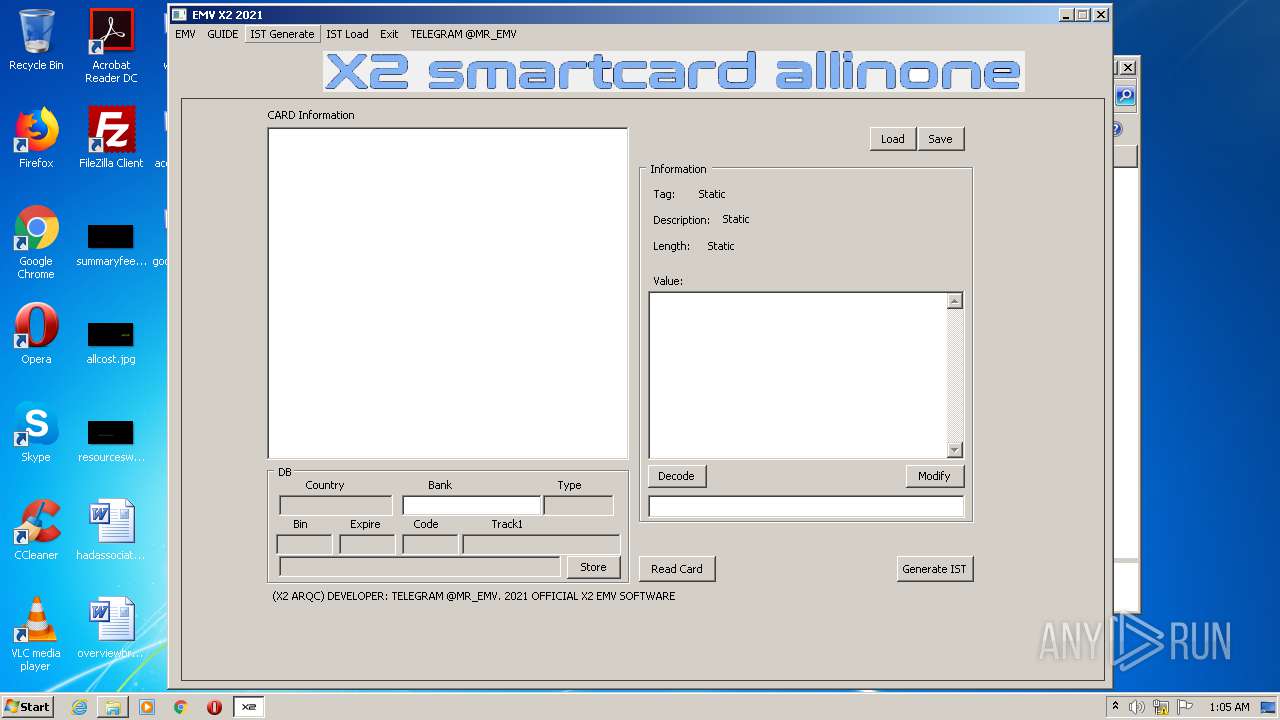
| 1964 | "C:\Users\admin\Desktop\Temp\x2 2021\auth removed x2.exe" | C:\Users\admin\Desktop\Temp\x2 2021\auth removed x2.exe | — | explorer.exe | |||||||||||
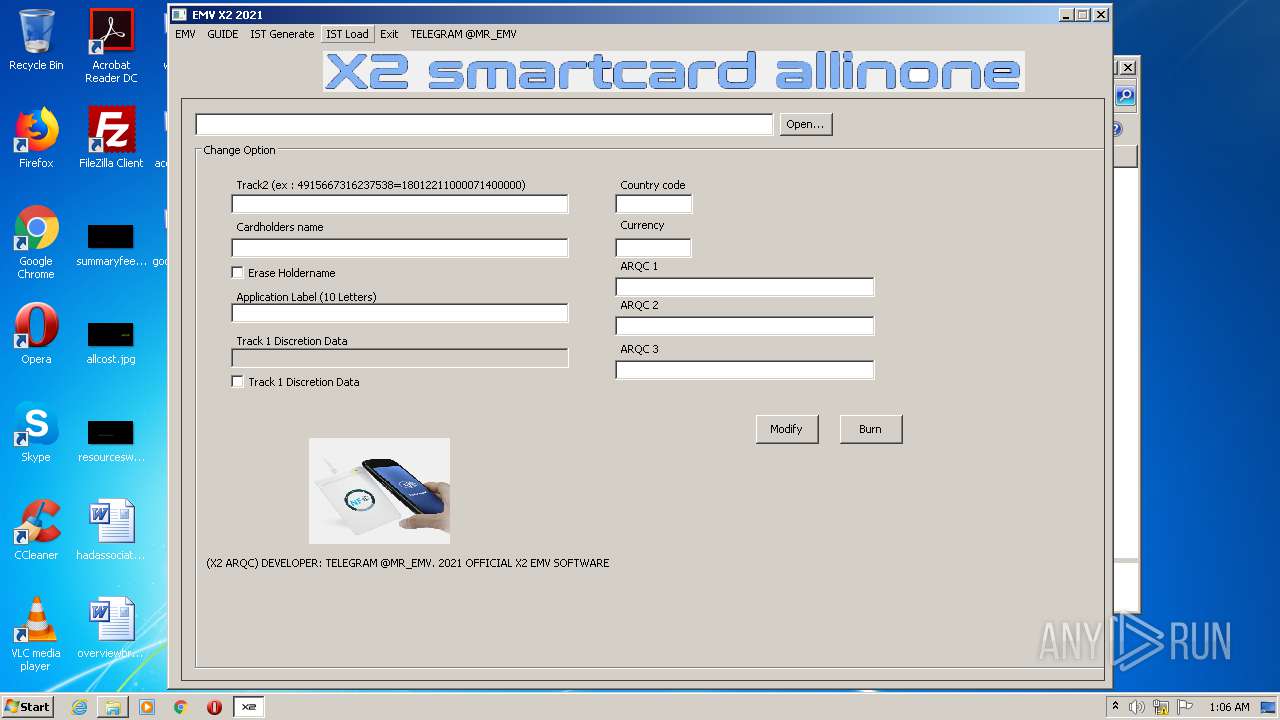
User: admin Company: <X2 ARQC> Integrity Level: MEDIUM Description: <X2> Exit code: 0 Version: 2.1.0.1 Modules
| |||||||||||||||
| 2456 | "C:\Users\admin\Desktop\Temp\x2 2021\Payload.exe" | C:\Users\admin\Desktop\Temp\x2 2021\Payload.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3180 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
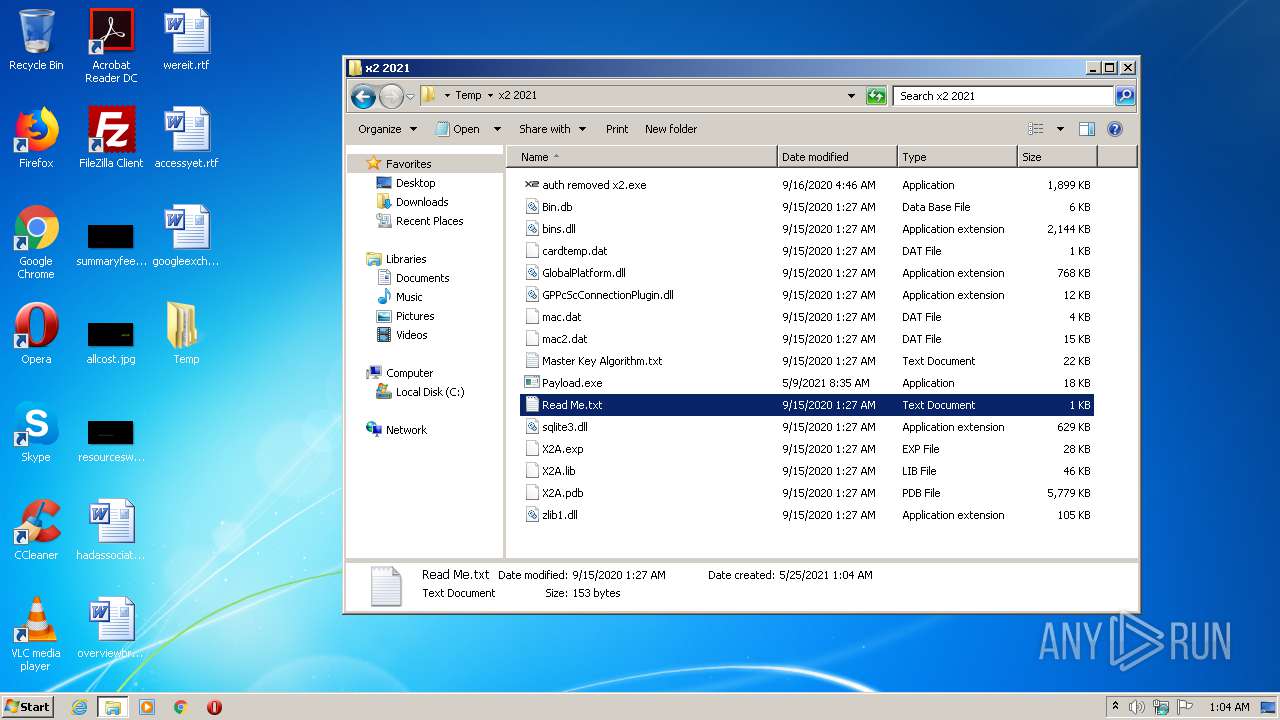
| 3324 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Temp\x2 2021\Read Me.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
495
Read events
486
Write events
9
Delete events
0
Modification events
| (PID) Process: | (1692) x2_2021.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1692) x2_2021.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1692) x2_2021.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1692) x2_2021.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1692) x2_2021.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3180) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3180) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
8
Suspicious files
3
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
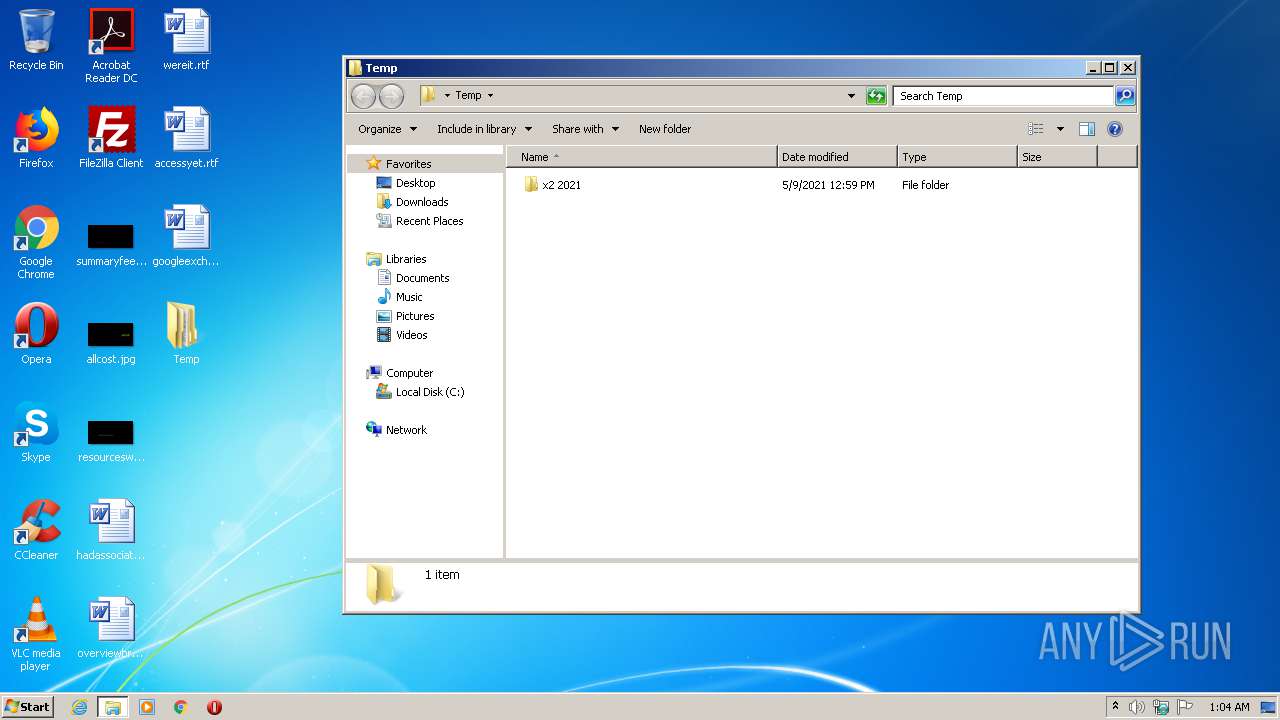
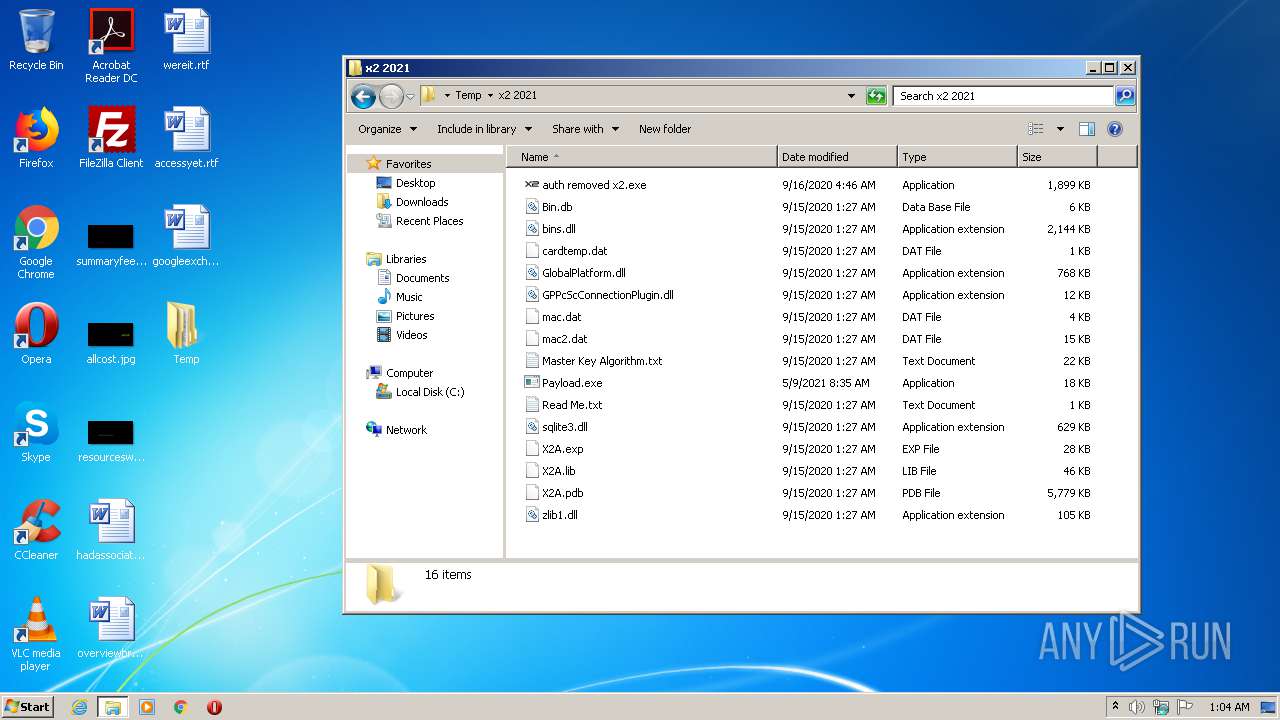
| 1692 | x2_2021.exe | C:\Users\admin\Desktop\Temp\x2 2021\X2A.pdb | — | |
MD5:— | SHA256:— | |||
| 1692 | x2_2021.exe | C:\Users\admin\Desktop\Temp\x2 2021\GlobalPlatform.dll | executable | |
MD5:4696B9FAE32C96D487DAA887D830261B | SHA256:D516E641E63F4195C374ECEDBEE074C345AF178D703FA0761C990141E056B992 | |||
| 1692 | x2_2021.exe | C:\Users\admin\Desktop\Temp\x2 2021\Master Key Algorithm.txt | text | |
MD5:66086C260D724564A1963E475446FACF | SHA256:6527D367E344F2412EFB123FAC90A5E19801667C51414EF08C85AED79BEE1EC1 | |||
| 1692 | x2_2021.exe | C:\Users\admin\Desktop\Temp\x2 2021\mac.dat | compressed | |
MD5:3709E18B229E3DB113BF5C7863C59DB4 | SHA256:9DC70002E82C78EE34C813597925C6CF8AA8D68B7E9CE5BCC70EA9BCAB9DBF4A | |||
| 1692 | x2_2021.exe | C:\Users\admin\Desktop\Temp\x2 2021\zlib1.dll | executable | |
MD5:B8A9E91134E7C89440A0F95470D5E47B | SHA256:42967A768F341D9CE5174EB38A4D63754C3C41739E7D88F4E39CD7354C1FAC71 | |||
| 1692 | x2_2021.exe | C:\Users\admin\Desktop\Temp\x2 2021\X2A.lib | obj | |
MD5:C96884A9FD7E6305A5F4972222AAFD1A | SHA256:1600B8928CEA94572789182E8A97F5BBF545DC1281B698F4DDCDA8A98516070B | |||
| 1692 | x2_2021.exe | C:\Users\admin\Desktop\Temp\x2 2021\GPPcScConnectionPlugin.dll | executable | |
MD5:D65463FC8A37261B6BF5AFBC4139BDD5 | SHA256:789734BBAB7B606E27FAB43F4706250399108DBA98E4428D1B95589DB0A42EA2 | |||
| 1692 | x2_2021.exe | C:\Users\admin\Desktop\Temp\x2 2021\mac2.dat | compressed | |
MD5:CBF974E9DB892E5105C2AD1D4013B1DD | SHA256:E82114E55C2EAEC534ED78F59258AAE46DA1E343476BDC4EA236CA5FA1E4047A | |||
| 1692 | x2_2021.exe | C:\Users\admin\Desktop\Temp\x2 2021\X2A.exp | exp | |
MD5:9658F4486DF81E316B74ED4FD729AA44 | SHA256:13A2DEEDC0FC750D4221332747DAD7ACB00EA0F02AD4C0361473FB3D82043BDE | |||
| 1692 | x2_2021.exe | C:\Users\admin\Desktop\Temp\x2 2021\Payload.exe | executable | |
MD5:7C32401AF9DB64CDDE2717C6EA6A22D7 | SHA256:1430E83A0B78CECD8D7A510D4559BB710CFB56ED303D8EA99B87C20B59F7FCE5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report