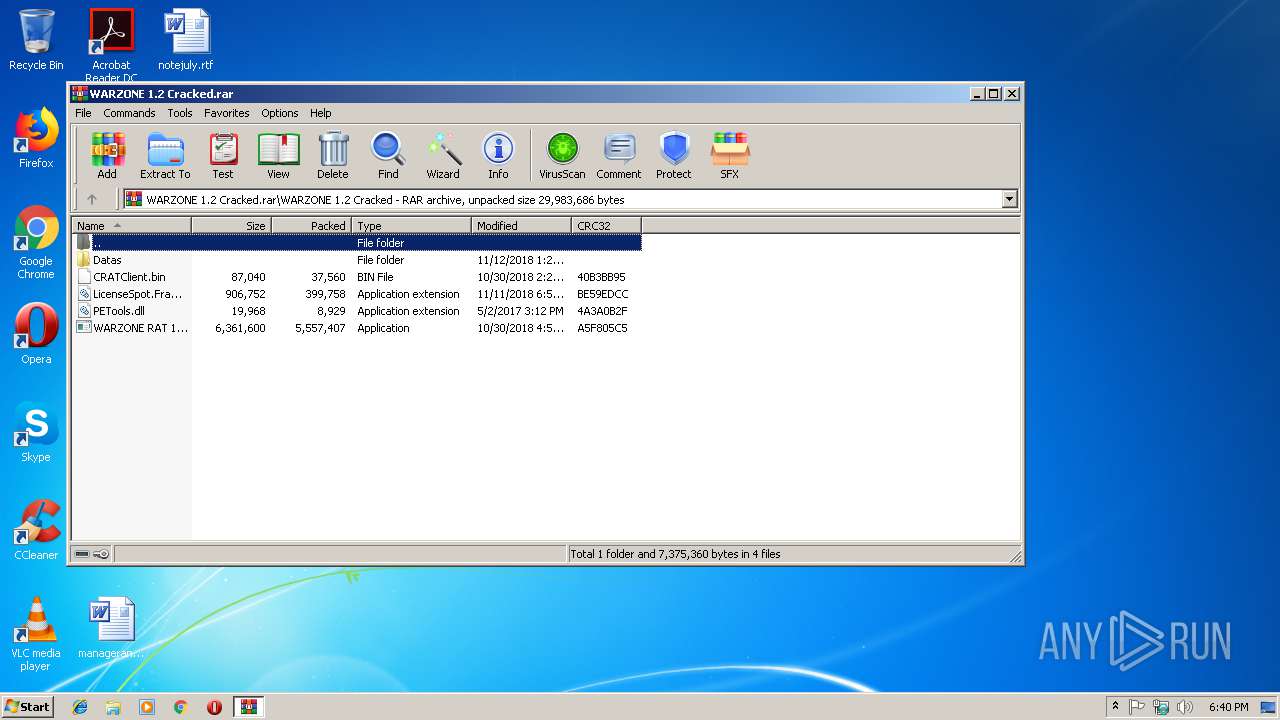
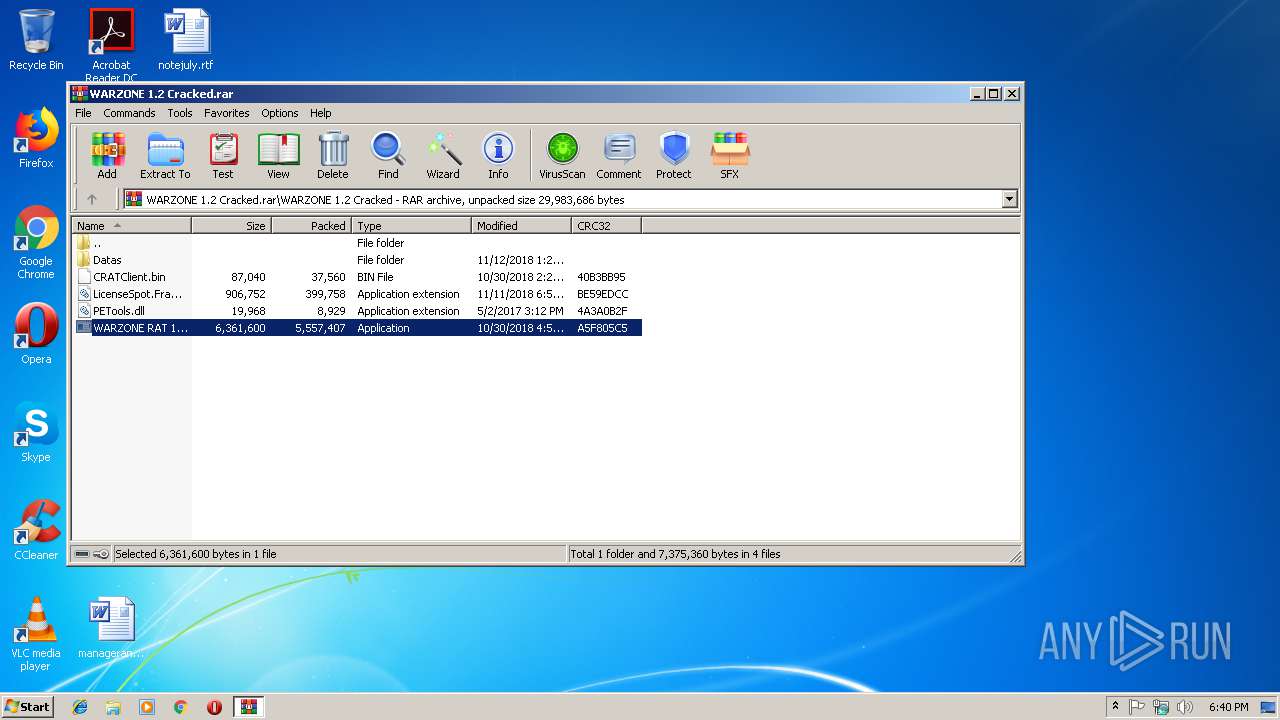
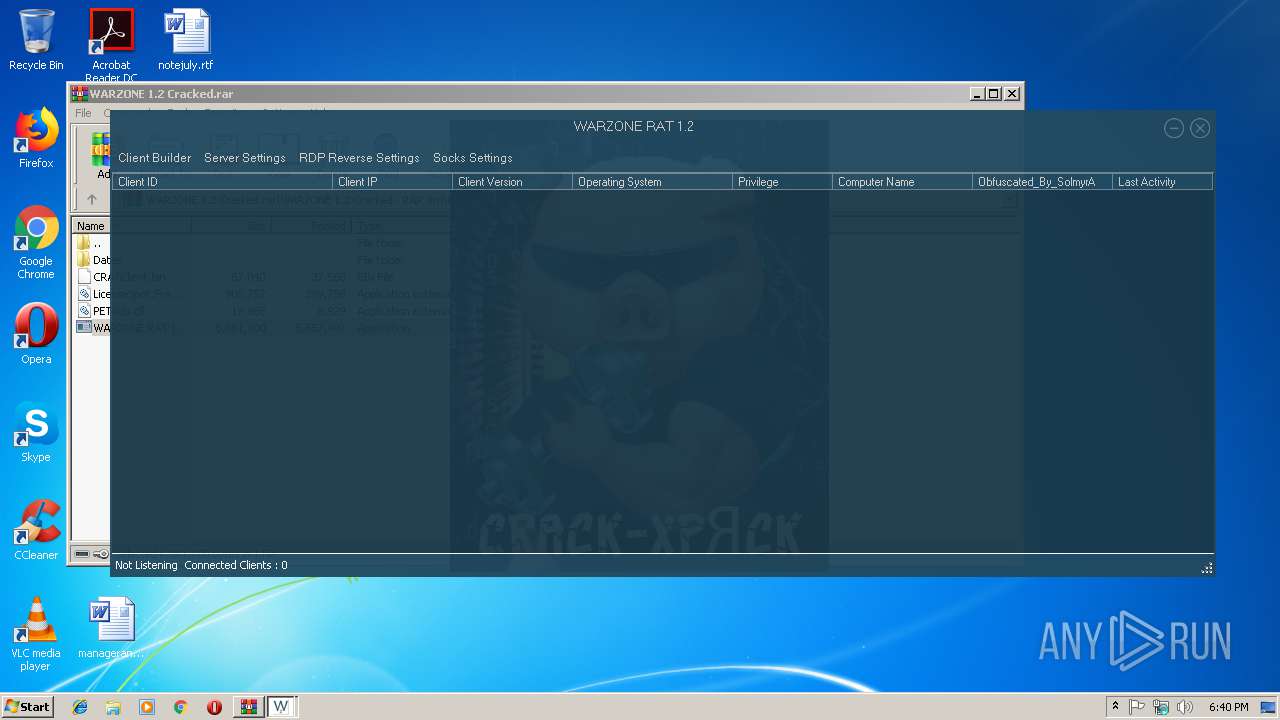
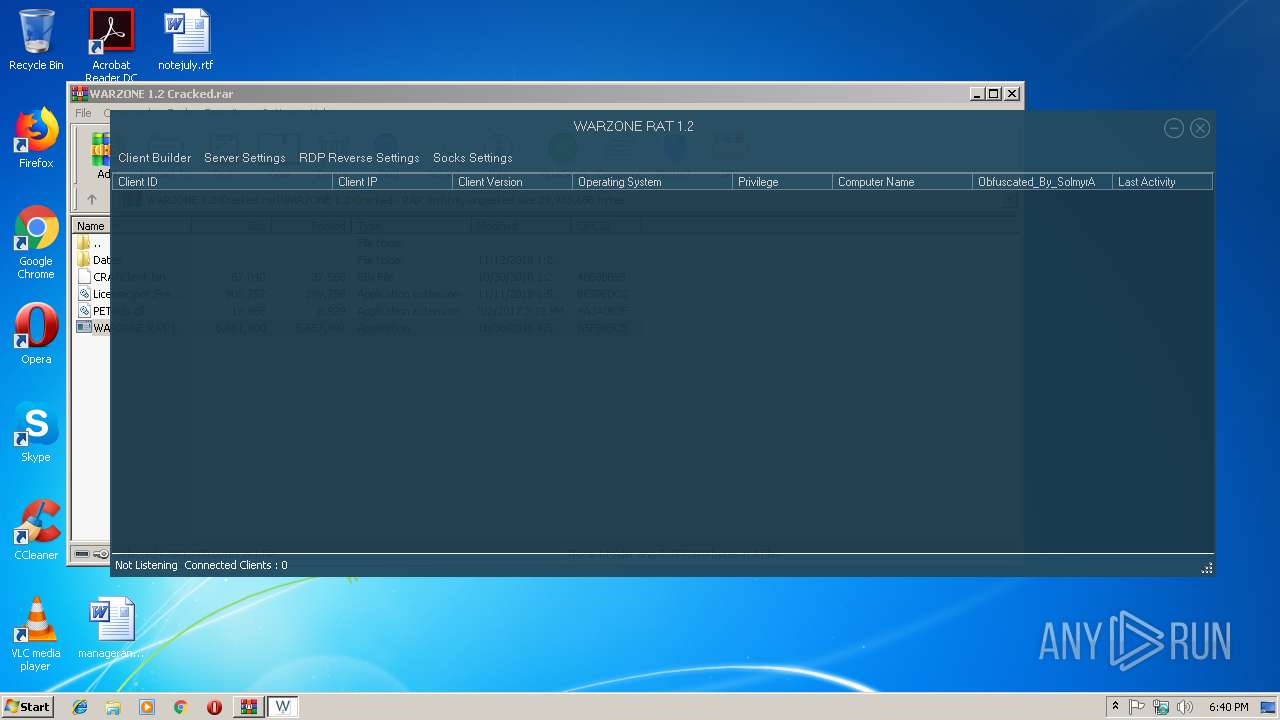
| File name: | WARZONE 1.2 Cracked.rar |
| Full analysis: | https://app.any.run/tasks/2437dd83-f372-41ae-b3d2-5591097f1a28 |
| Verdict: | Suspicious activity |
| Analysis date: | December 31, 2018, 18:39:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5559636807D43160879C2175528D1A99 |
| SHA1: | 718927092235C0246A43AE646259AE5C637C31AE |
| SHA256: | E57F7FE970FE9E4234C6A77388BA5B6FE303747FECC9D73CC63104D5C1BE5589 |
| SSDEEP: | 196608:6l1ylsDUJiSztSy8j+9c3YJc4EA/aaMv9qmWcefazTZh489aTmD2FrUwoX9E0EA:W1yltxtf8aZc4EAiP9GcefazTXx4Tvrm |
MALICIOUS
Application was dropped or rewritten from another process
- WARZONE RAT 1.2.exe (PID: 2352)
Loads dropped or rewritten executable
- WARZONE RAT 1.2.exe (PID: 2352)
SUSPICIOUS
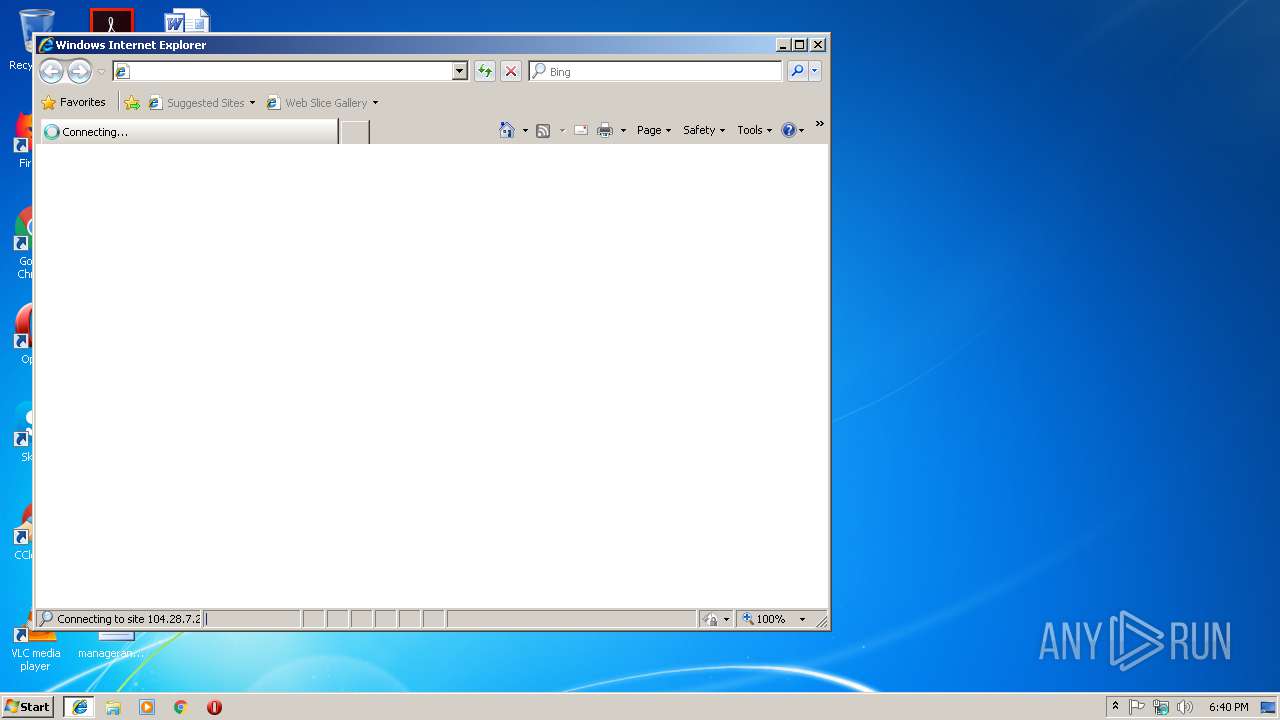
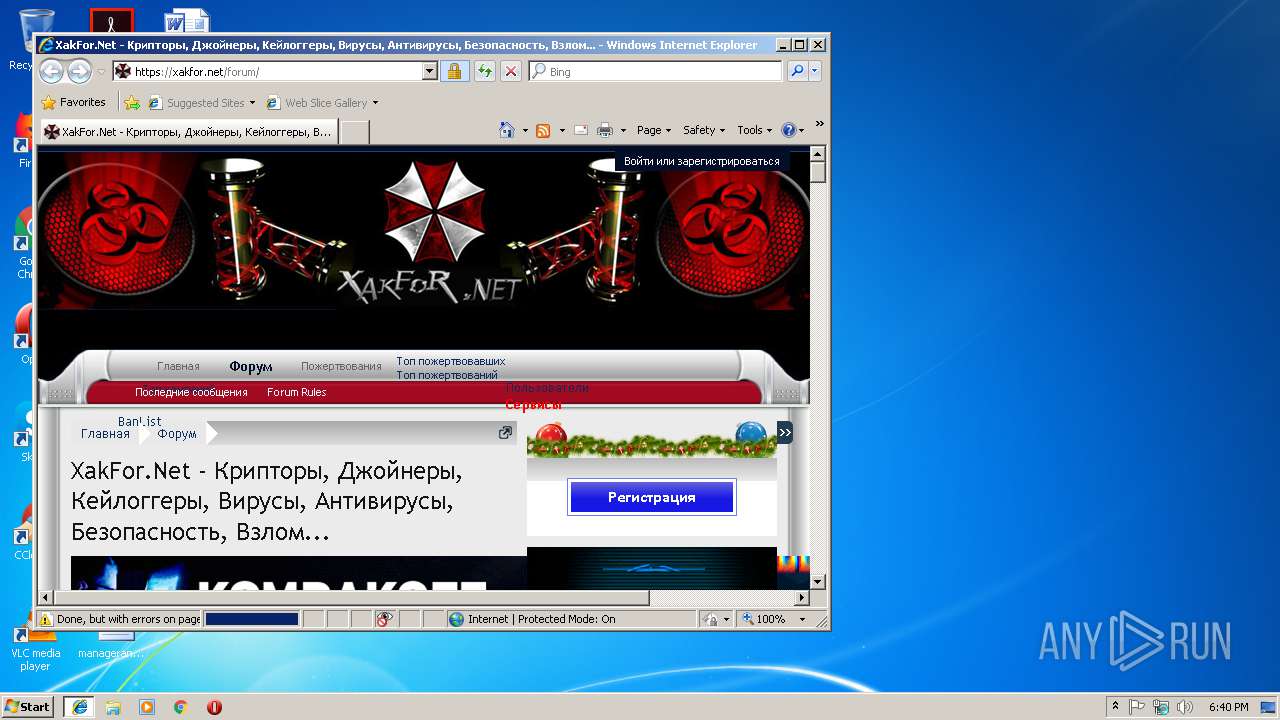
Starts Internet Explorer
- WARZONE RAT 1.2.exe (PID: 2352)
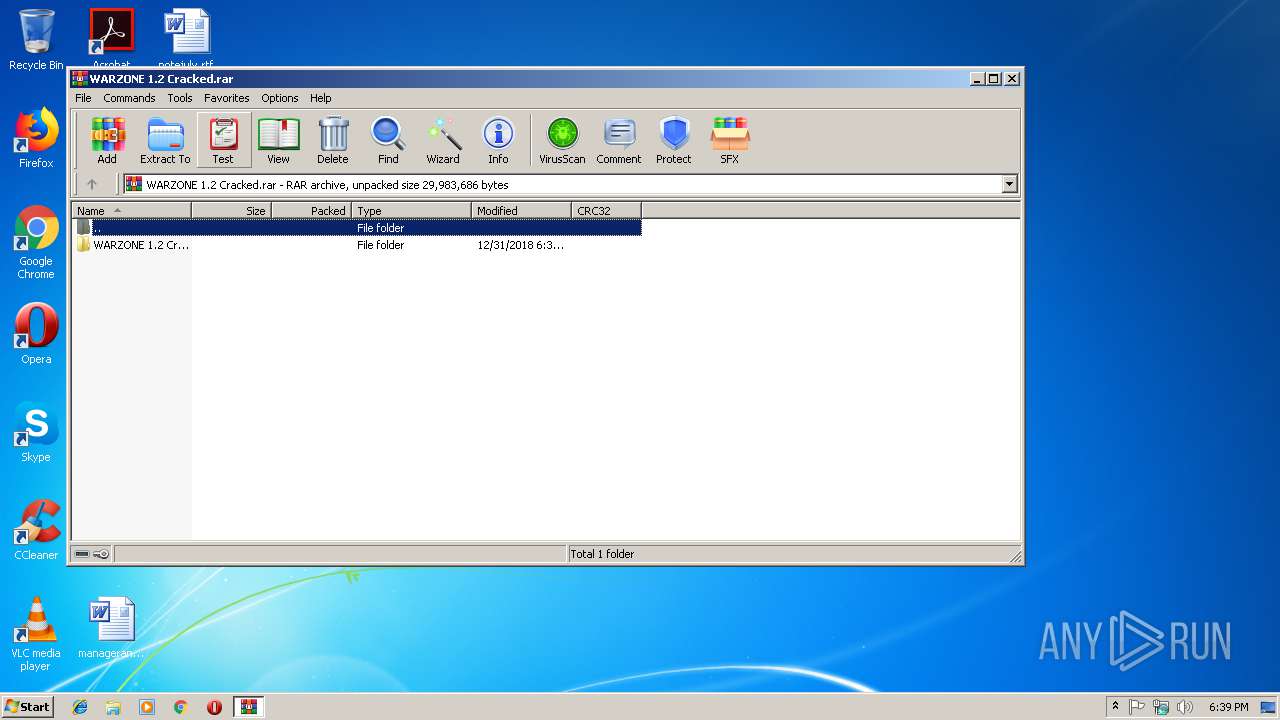
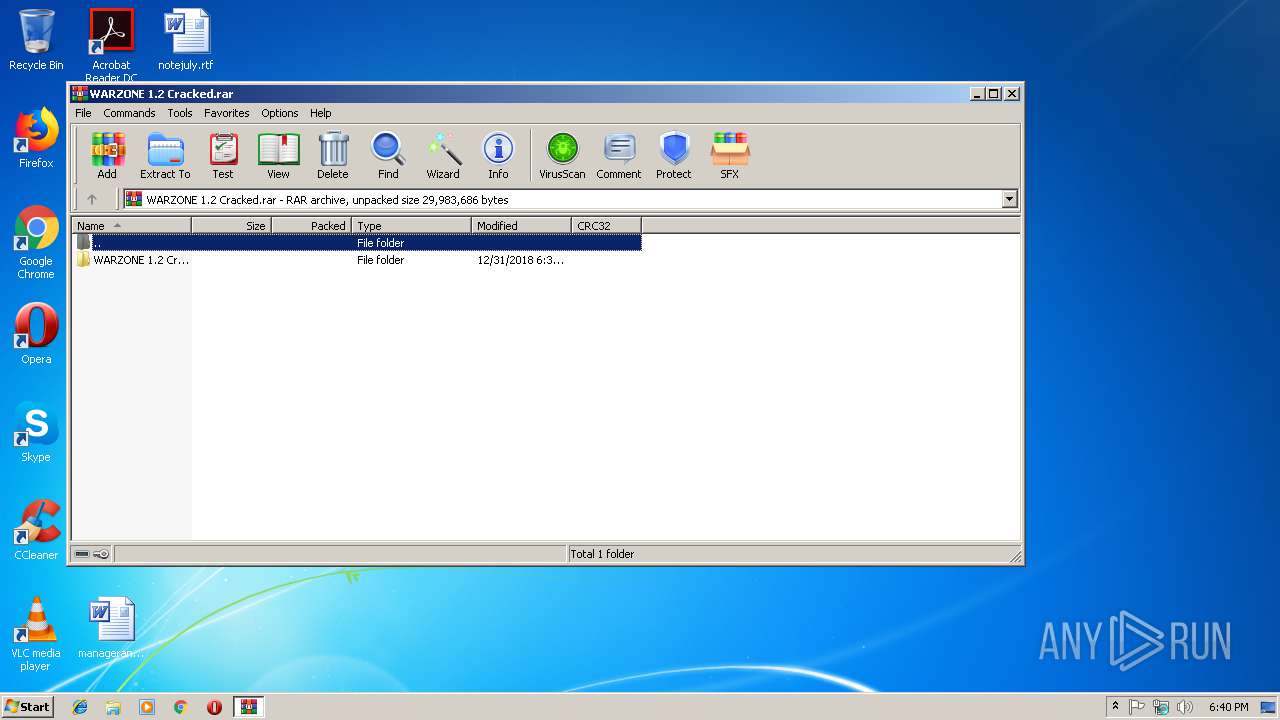
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3808)
INFO
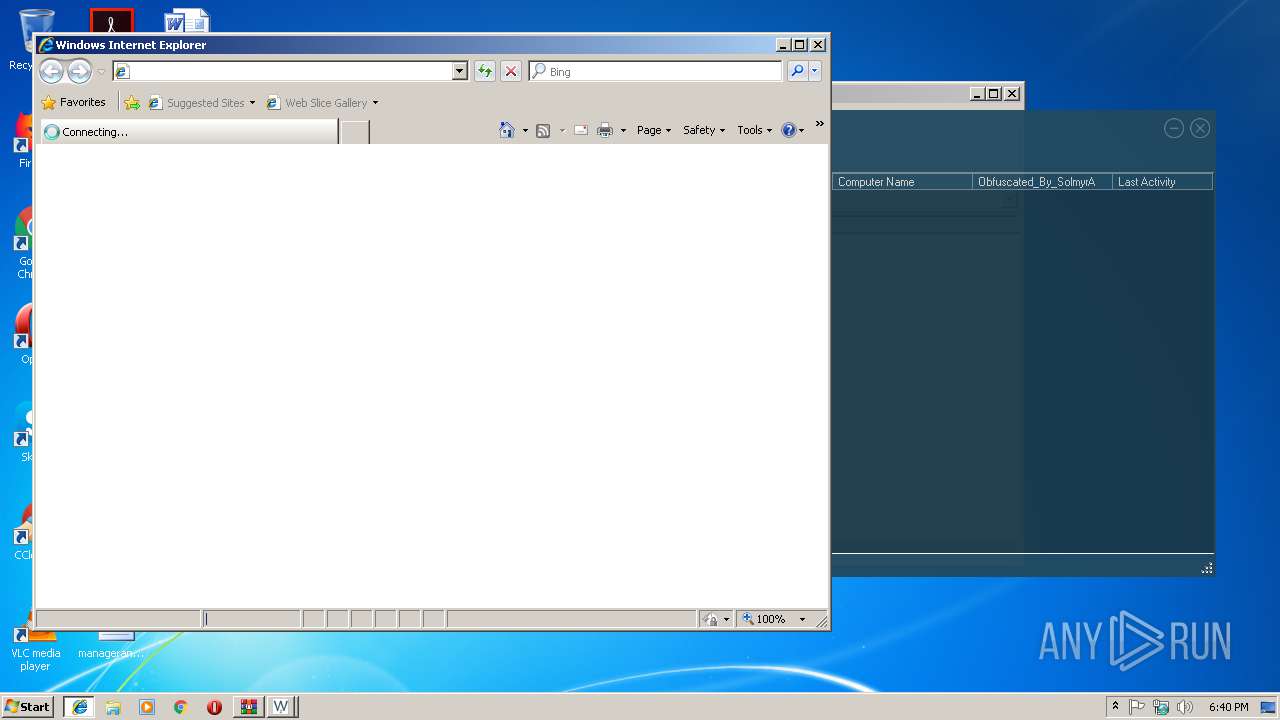
Application launched itself
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 2204)
Reads Internet Cache Settings
- iexplore.exe (PID: 3484)
- iexplore.exe (PID: 2256)
- iexplore.exe (PID: 2204)
Reads internet explorer settings
- iexplore.exe (PID: 3484)
- iexplore.exe (PID: 2256)
Creates files in the user directory
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 3484)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1440)
- iexplore.exe (PID: 2256)
Changes internet zones settings
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 2204)
Reads settings of System Certificates
- iexplore.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1440 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | WARZONE RAT 1.2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2256 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2204 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
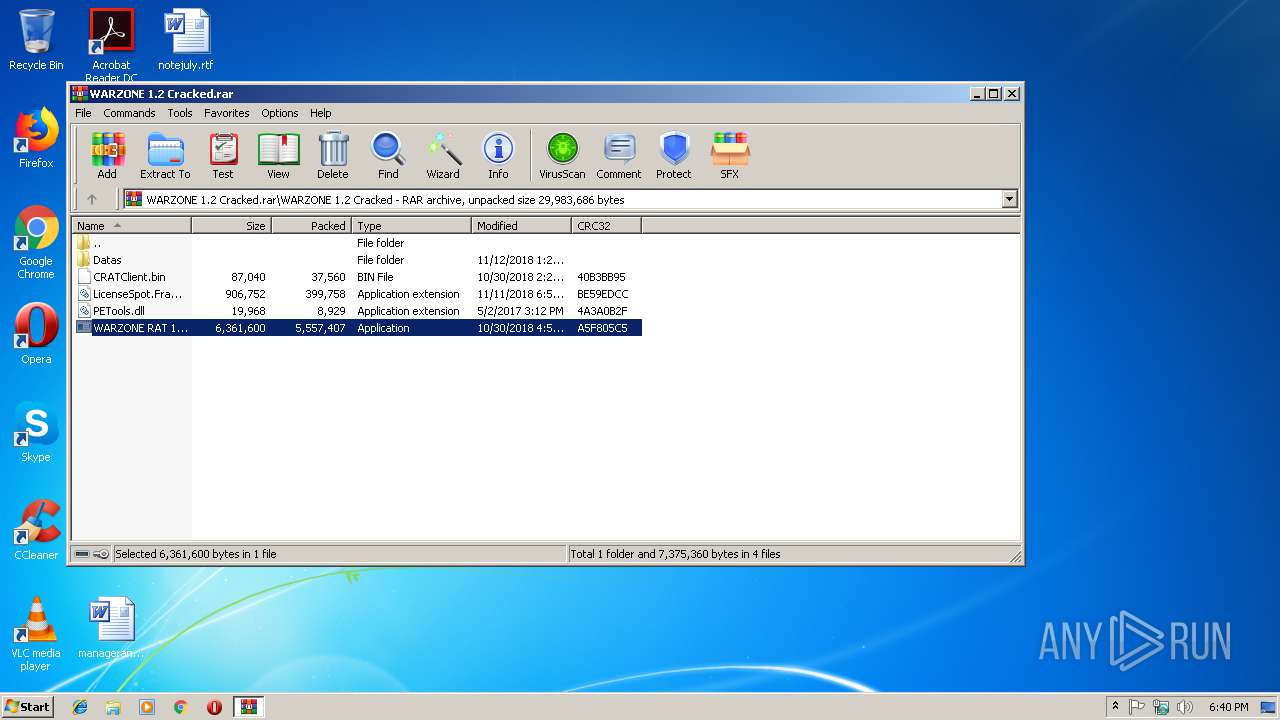
| 2352 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3808.10719\WARZONE 1.2 Cracked\WARZONE RAT 1.2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3808.10719\WARZONE 1.2 Cracked\WARZONE RAT 1.2.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: CRAT Server Exit code: 0 Version: 1.2.0.0 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | WARZONE RAT 1.2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3484 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2972 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
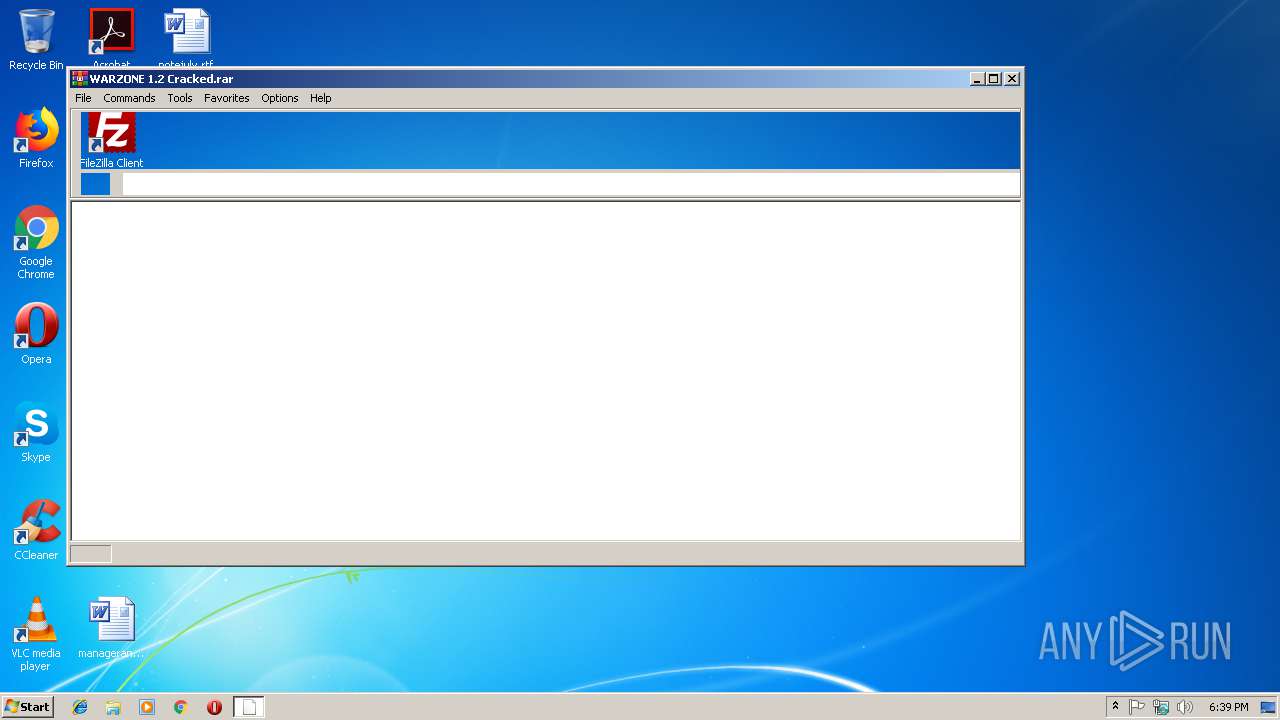
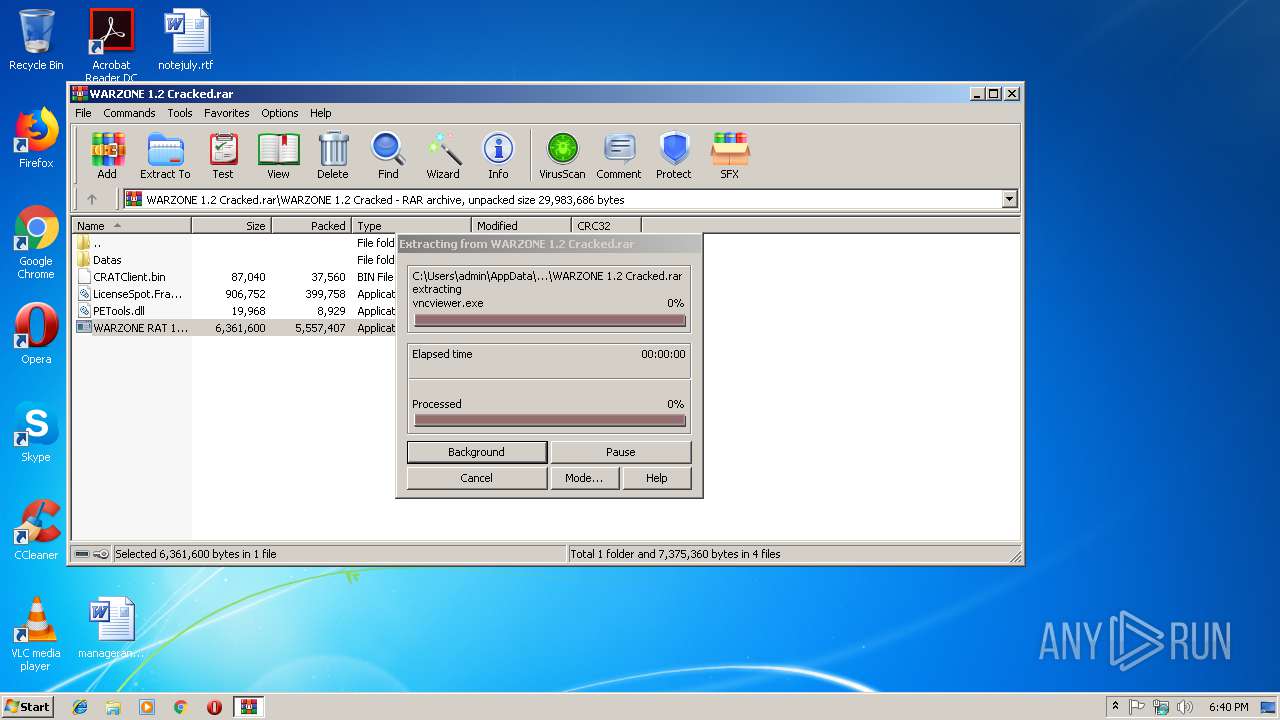
| 3808 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\WARZONE 1.2 Cracked.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 286
Read events
1 151
Write events
131
Delete events
4
Modification events
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\WARZONE 1.2 Cracked.rar | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3808) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
13
Suspicious files
3
Text files
100
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3808 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3808.10719\WARZONE 1.2 Cracked\WARZONE RAT 1.2.exe | executable | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD2552254C913AC95.TMP | — | |
MD5:— | SHA256:— | |||
| 3808 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3808.10719\WARZONE 1.2 Cracked\CRATClient.bin | executable | |
MD5:F9ABB84C2DB2734C3BC77394305CA6A9 | SHA256:C222354A9A87F141CAD4C427431F638A062BB9518F35E4EA4729215761C8A3C4 | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF92B52F297267AEDF.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | image | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF62F30DECFF695D82.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{8560FBD6-0D2B-11E9-BAD8-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
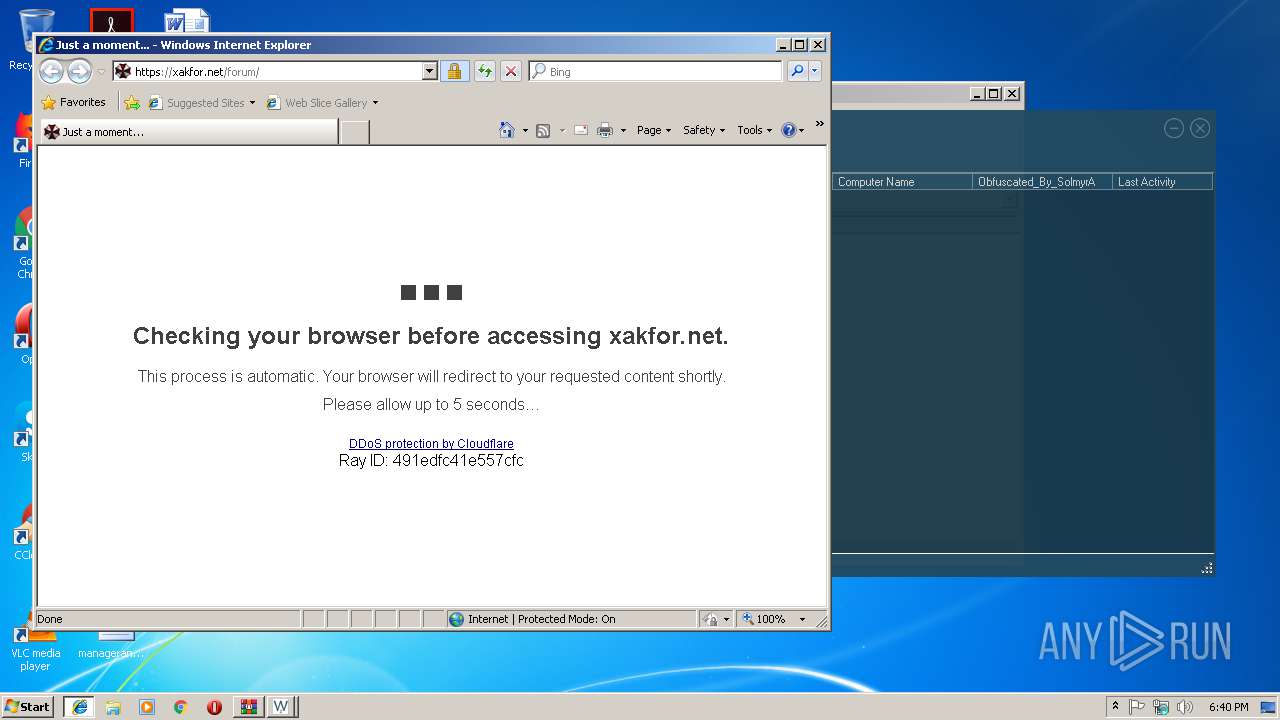
| 2972 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@xakfor[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
30
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2972 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2204 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2972 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3484 | iexplore.exe | 104.28.7.23:443 | xakfor.net | Cloudflare Inc | US | shared |
2204 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2256 | iexplore.exe | 104.28.7.23:443 | xakfor.net | Cloudflare Inc | US | shared |
2972 | iexplore.exe | 104.28.7.23:443 | xakfor.net | Cloudflare Inc | US | shared |
2256 | iexplore.exe | 172.217.16.200:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2256 | iexplore.exe | 81.176.238.211:443 | a.radikal.ru | JSC RTComm.RU | RU | unknown |
2256 | iexplore.exe | 151.101.120.193:443 | i.imgur.com | Fastly | US | malicious |
2256 | iexplore.exe | 81.176.238.212:443 | b.radikal.ru | JSC RTComm.RU | RU | unknown |
2256 | iexplore.exe | 81.176.238.131:443 | s019.radikal.ru | JSC RTComm.RU | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
xakfor.net |
| malicious |
www.googletagmanager.com |
| whitelisted |
i.imgur.com |
| malicious |
a.radikal.ru |
| unknown |
b.radikal.ru |
| unknown |
cse.google.com |
| whitelisted |
s019.radikal.ru |
| suspicious |
www.google.com |
| malicious |
www.free-kassa.ru |
| unknown |