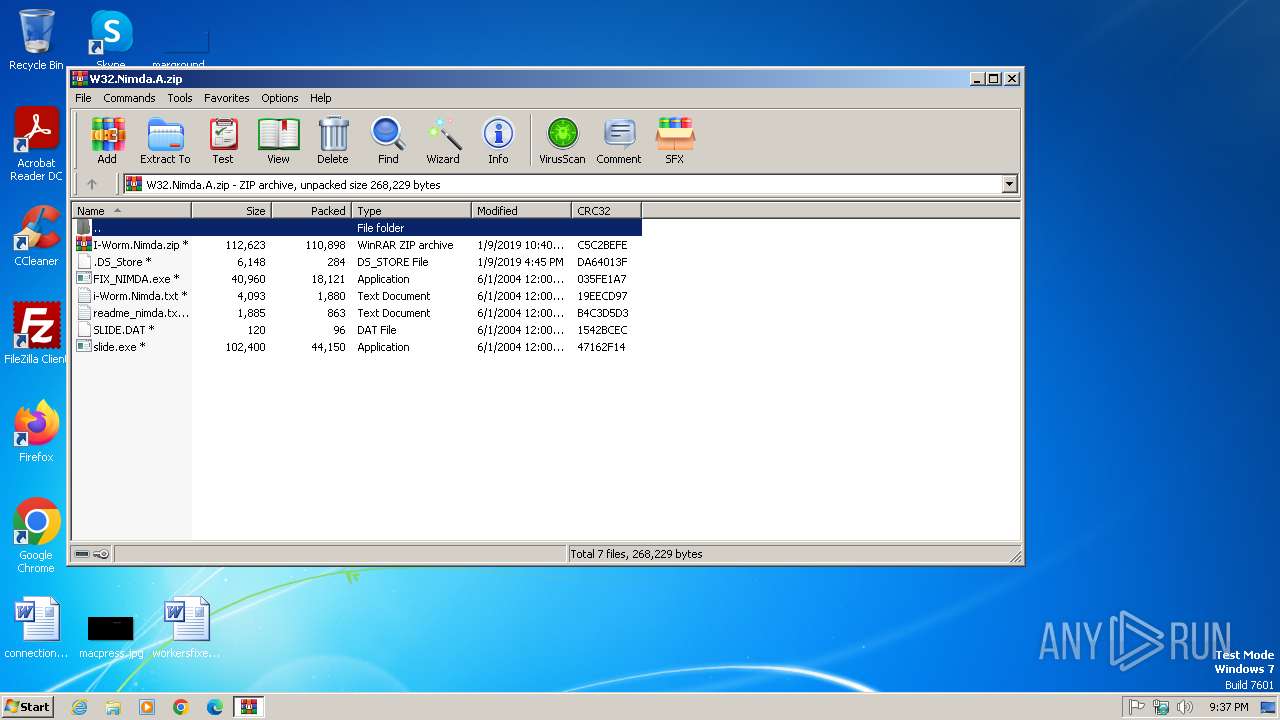
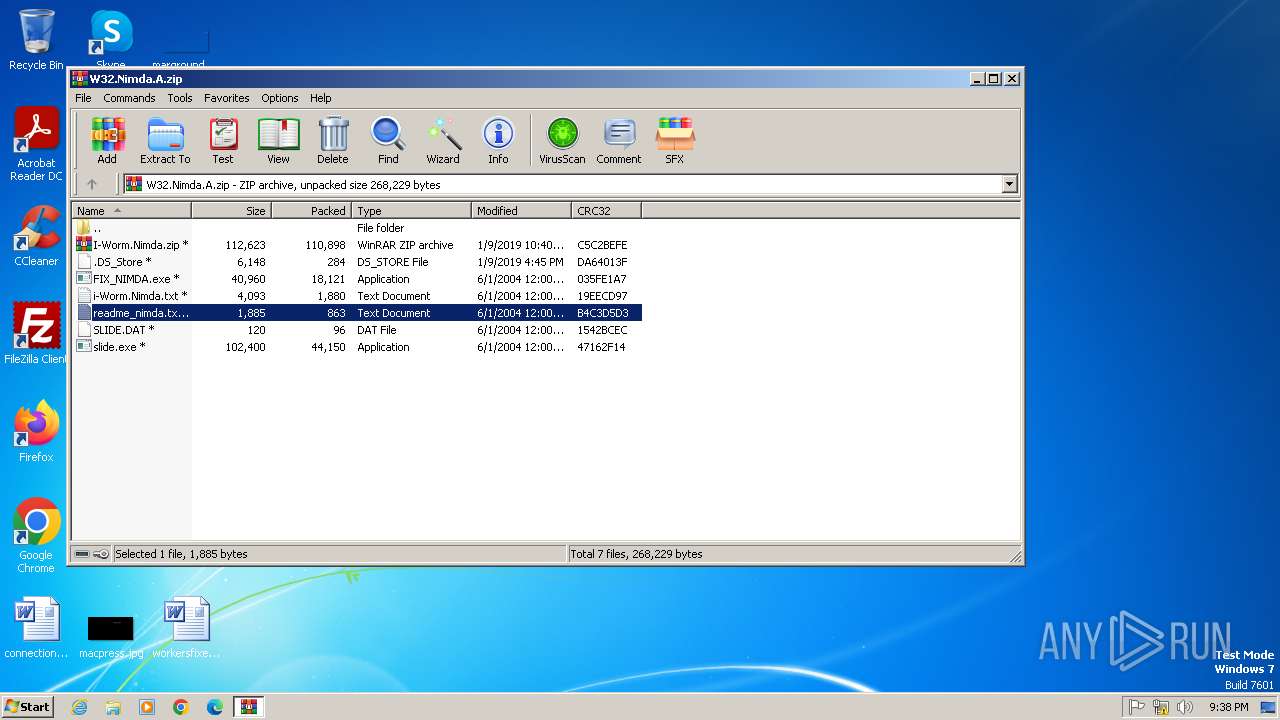
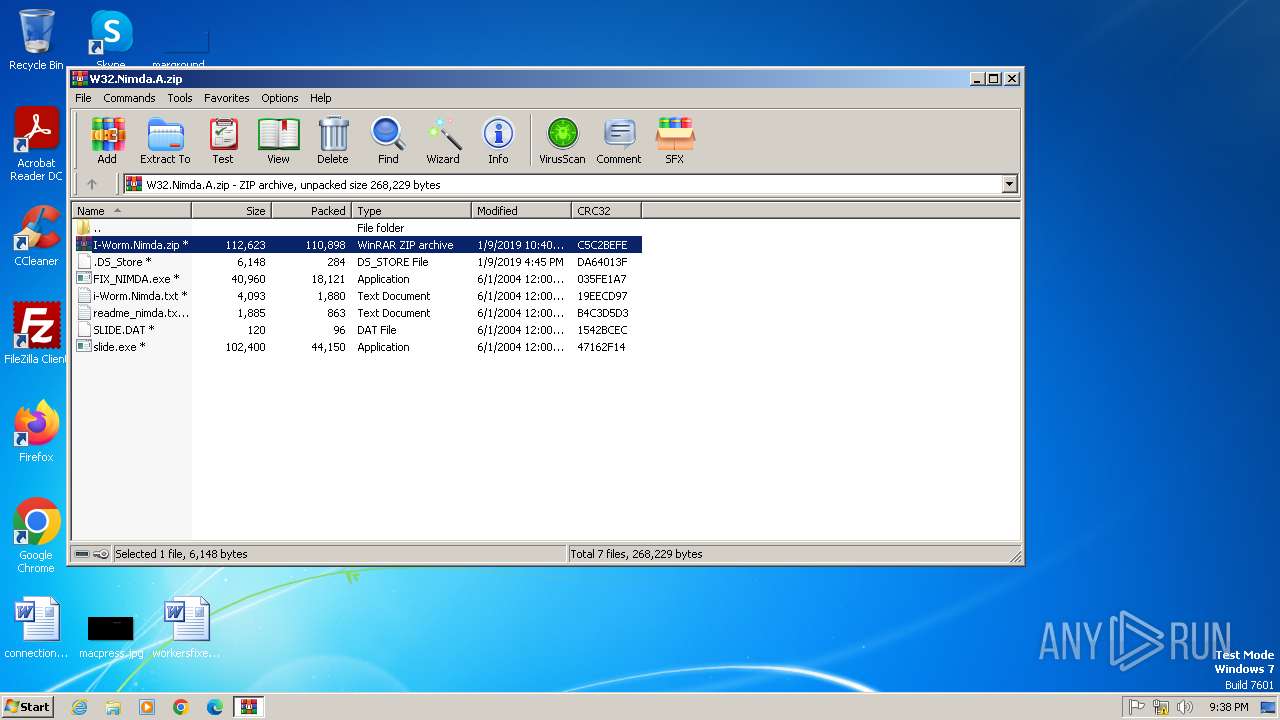
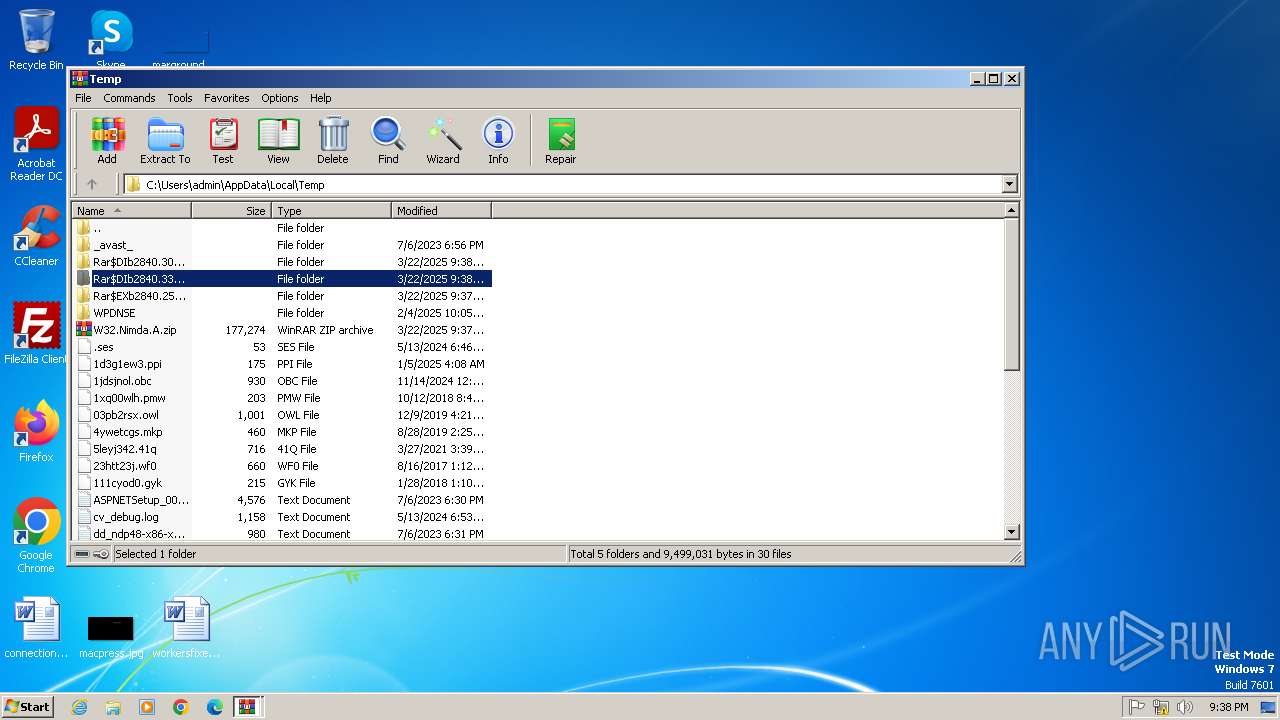
| File name: | W32.Nimda.A.zip |
| Full analysis: | https://app.any.run/tasks/f4f31f49-c90b-47c9-9dc0-c020f8e25788 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2025, 21:37:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | B62632C8E6AAFA05A07CAD52B2E25AA5 |
| SHA1: | 35C626A3513F8866095F891F69C593DE6D87EBD2 |
| SHA256: | E56E79F9DC8752E11B66C3DEA5282E835EF280A46A2B5D98AF19222D11B72767 |
| SSDEEP: | 6144:F5+YTd3QOMgyjGyrQb+MU5opgJcvd7JEZ:F5+YhogyjGK4ZqWgZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
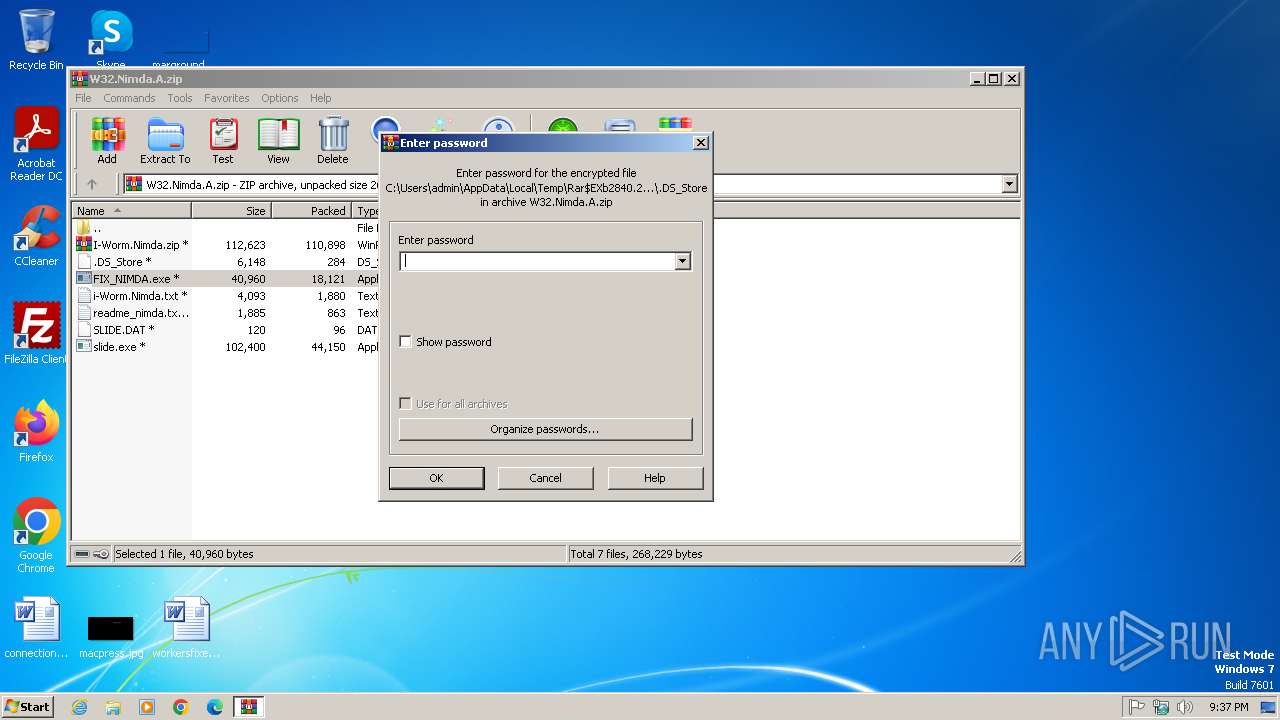
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2840)
- WinRAR.exe (PID: 2612)
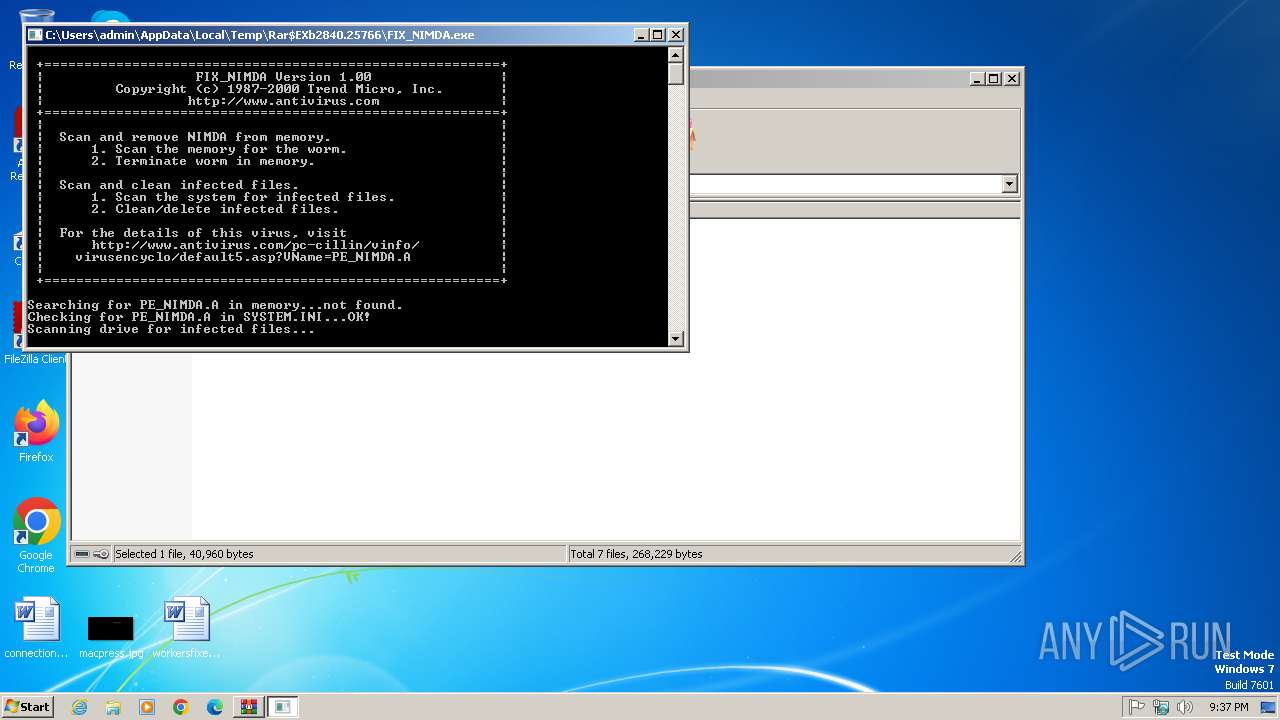
Creates file in the systems drive root
- FIX_NIMDA.exe (PID: 1404)
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 2840)
Application launched itself
- WinRAR.exe (PID: 2840)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2840)
- WinRAR.exe (PID: 2612)
Checks supported languages
- FIX_NIMDA.exe (PID: 1404)
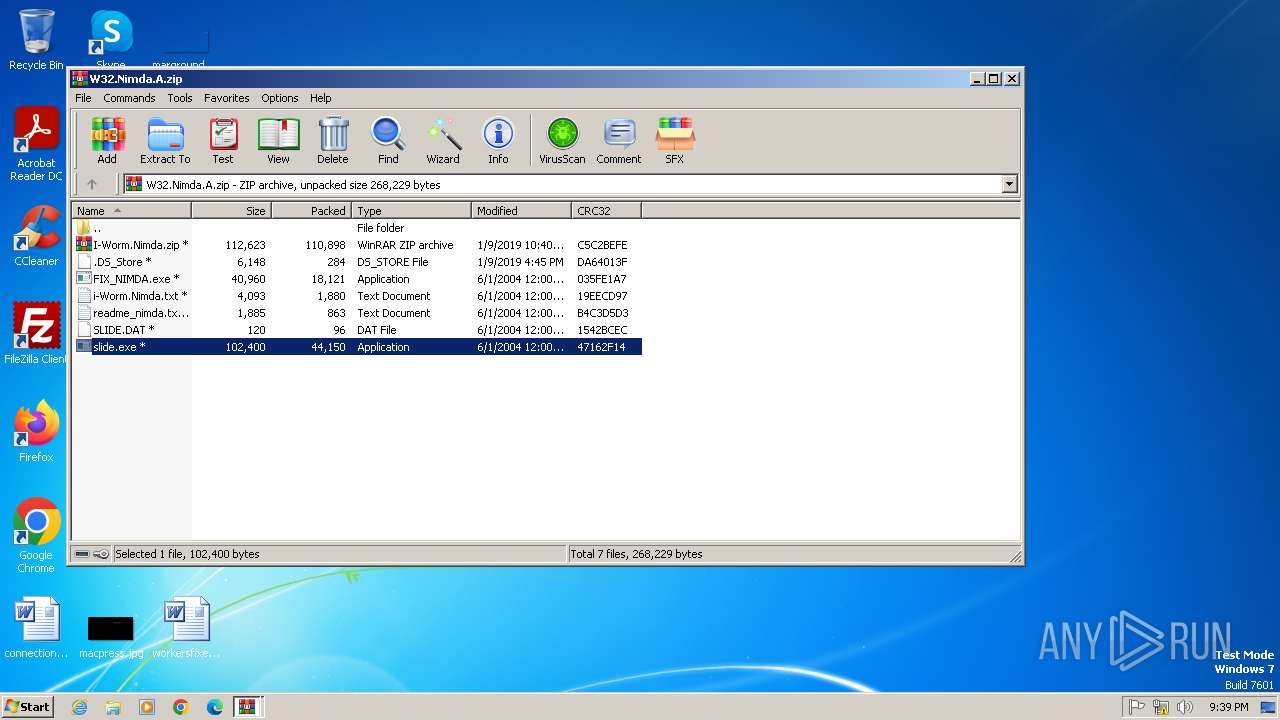
- slide.exe (PID: 2832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:01:09 16:45:30 |
| ZipCRC: | 0xda64013f |
| ZipCompressedSize: | 284 |
| ZipUncompressedSize: | 6148 |
| ZipFileName: | .DS_Store |
Total processes
39
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
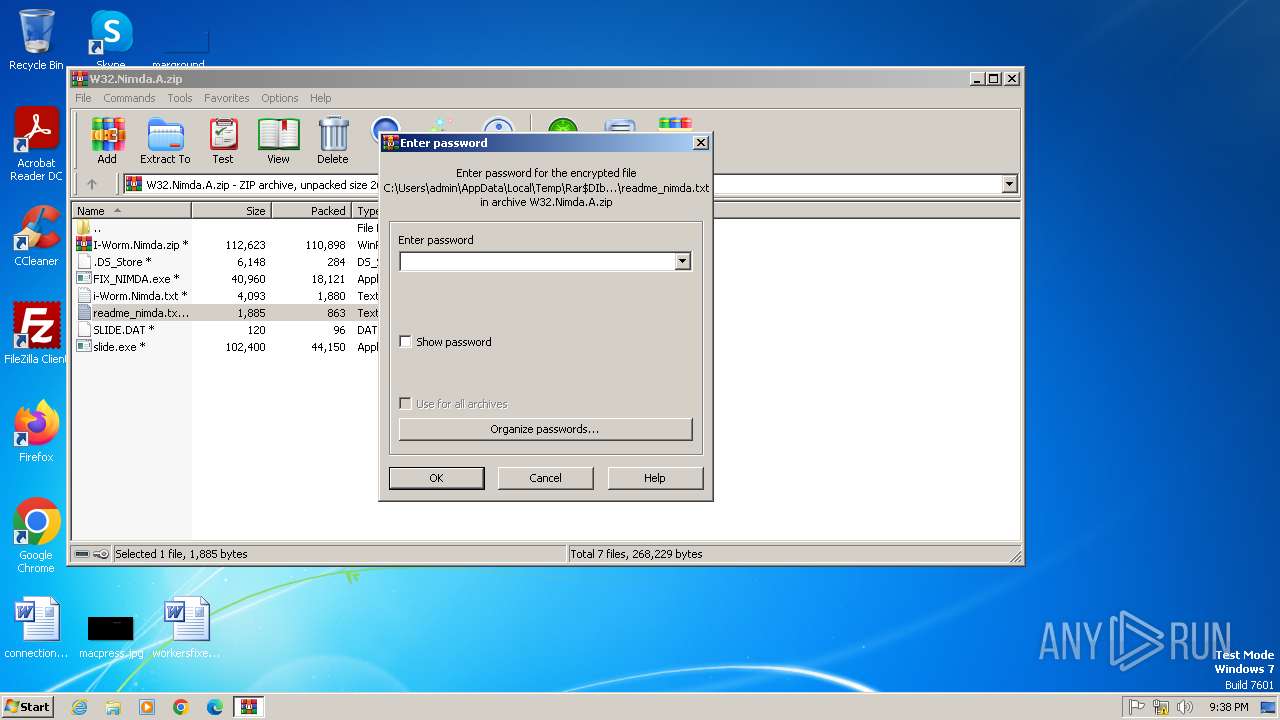
| 628 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIb2840.30555\readme_nimda.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
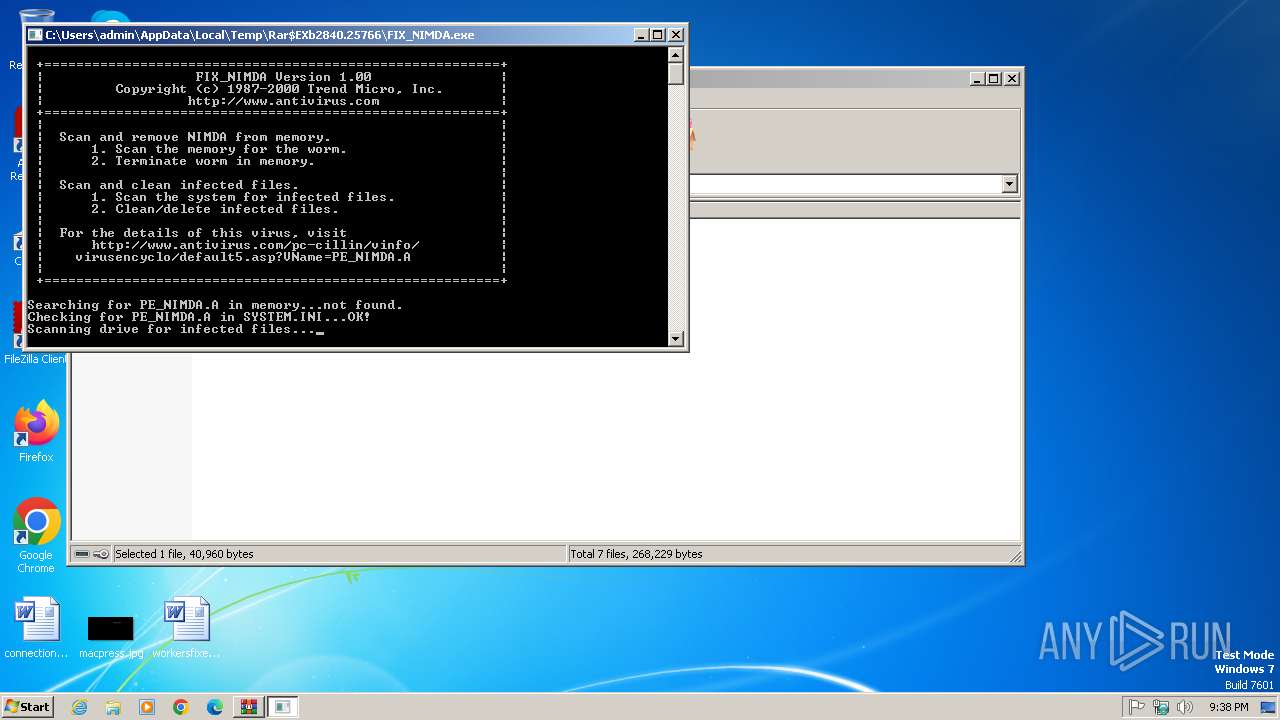
| 1404 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2840.25766\FIX_NIMDA.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2840.25766\FIX_NIMDA.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
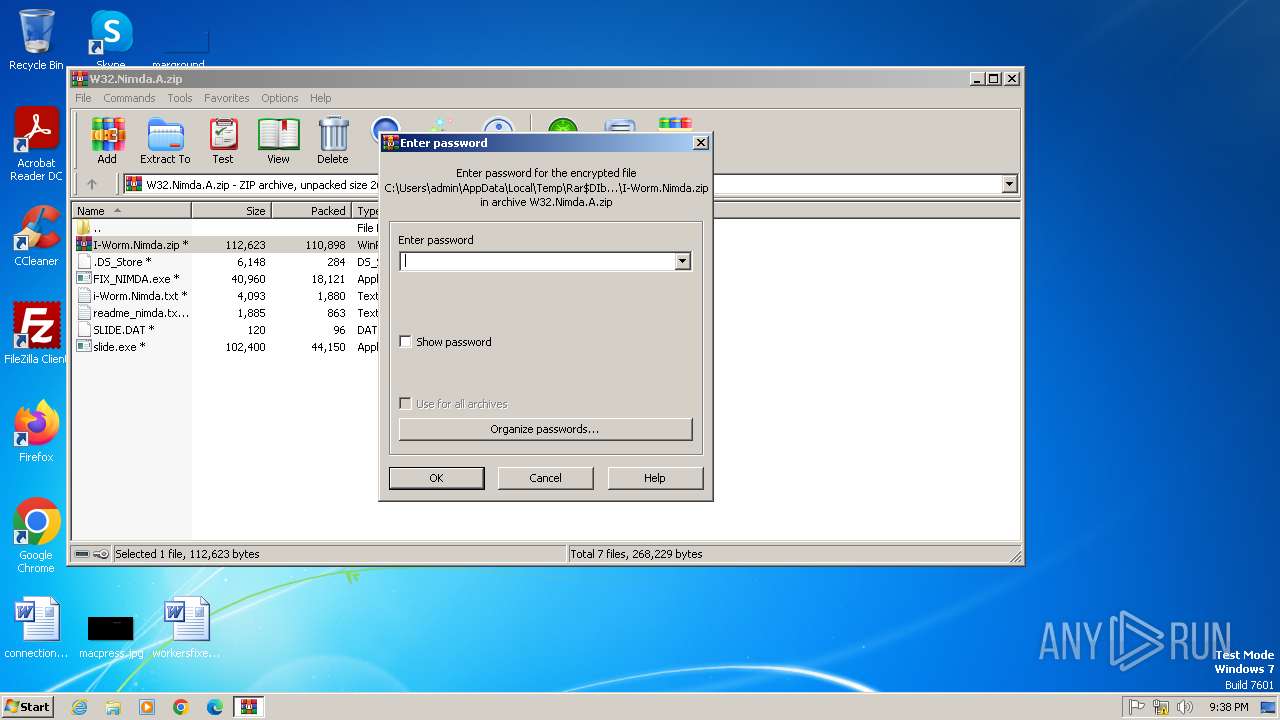
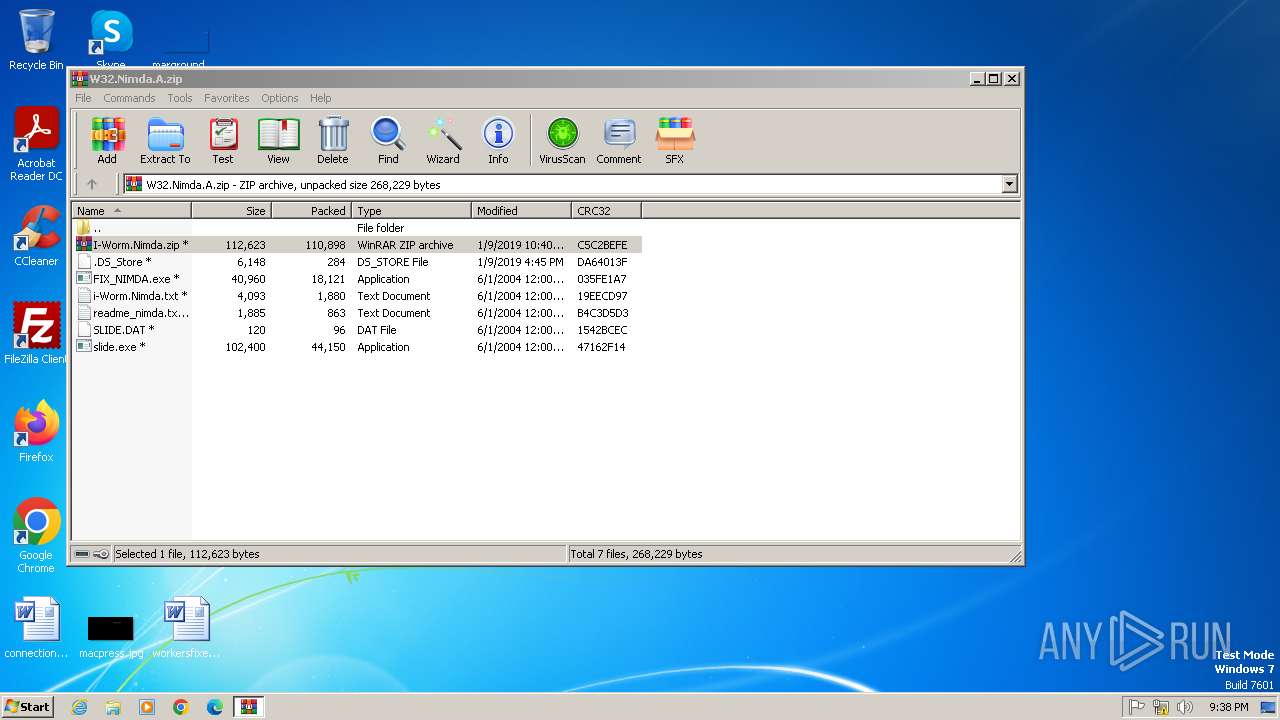
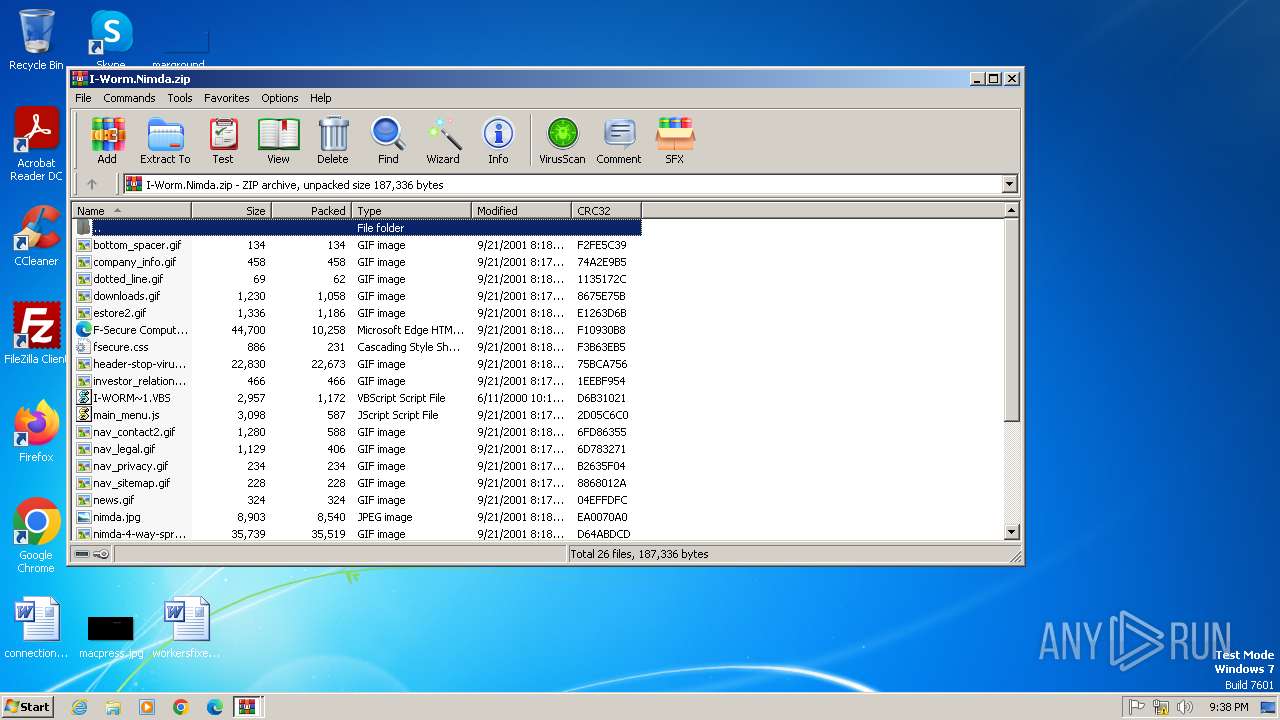
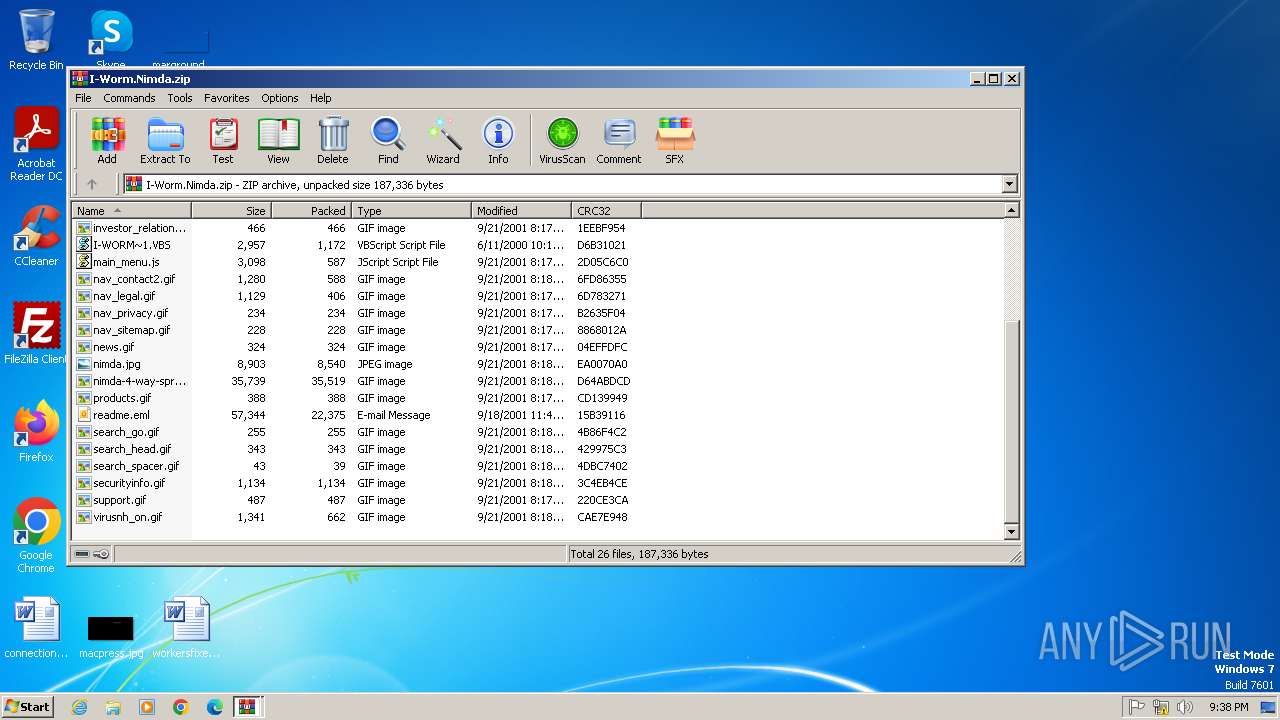
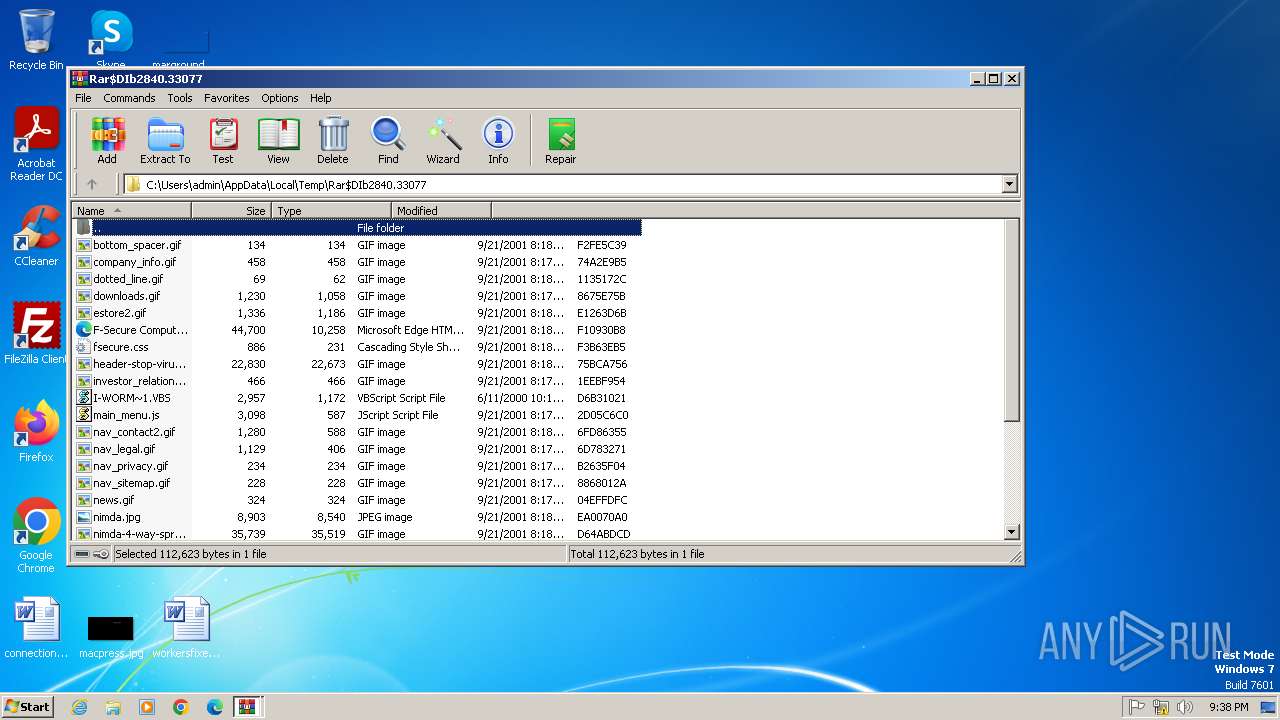
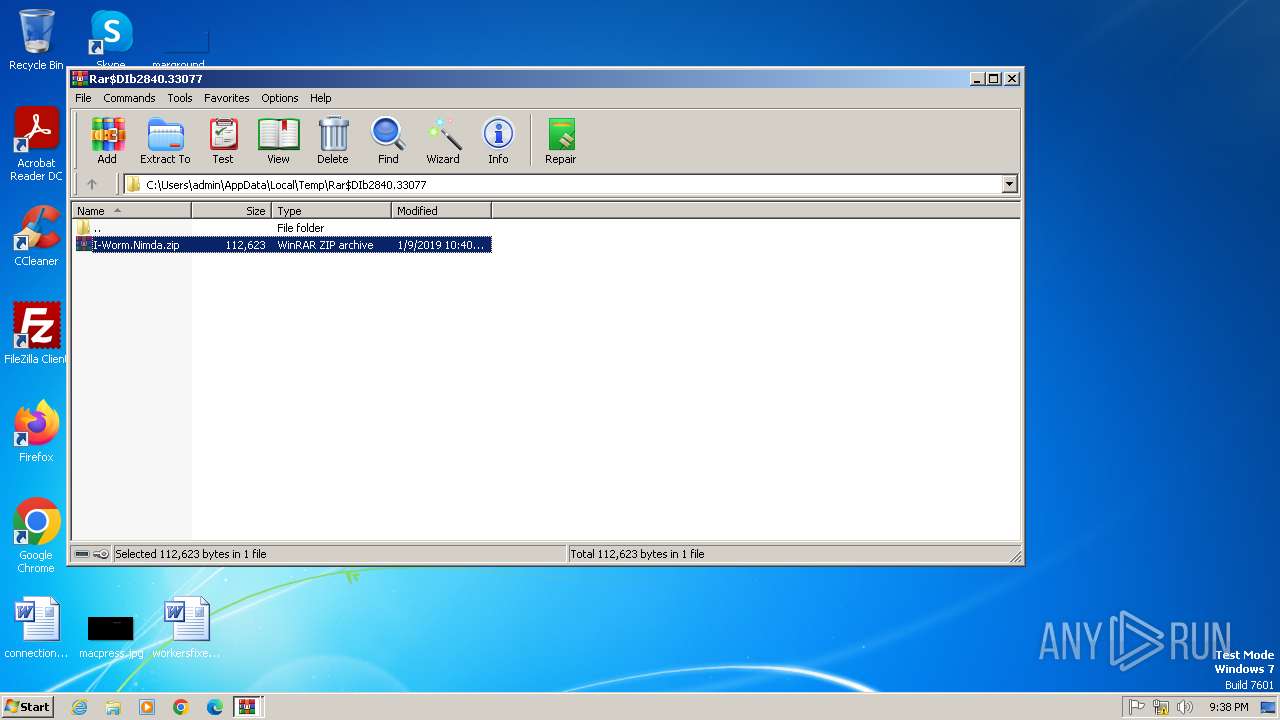
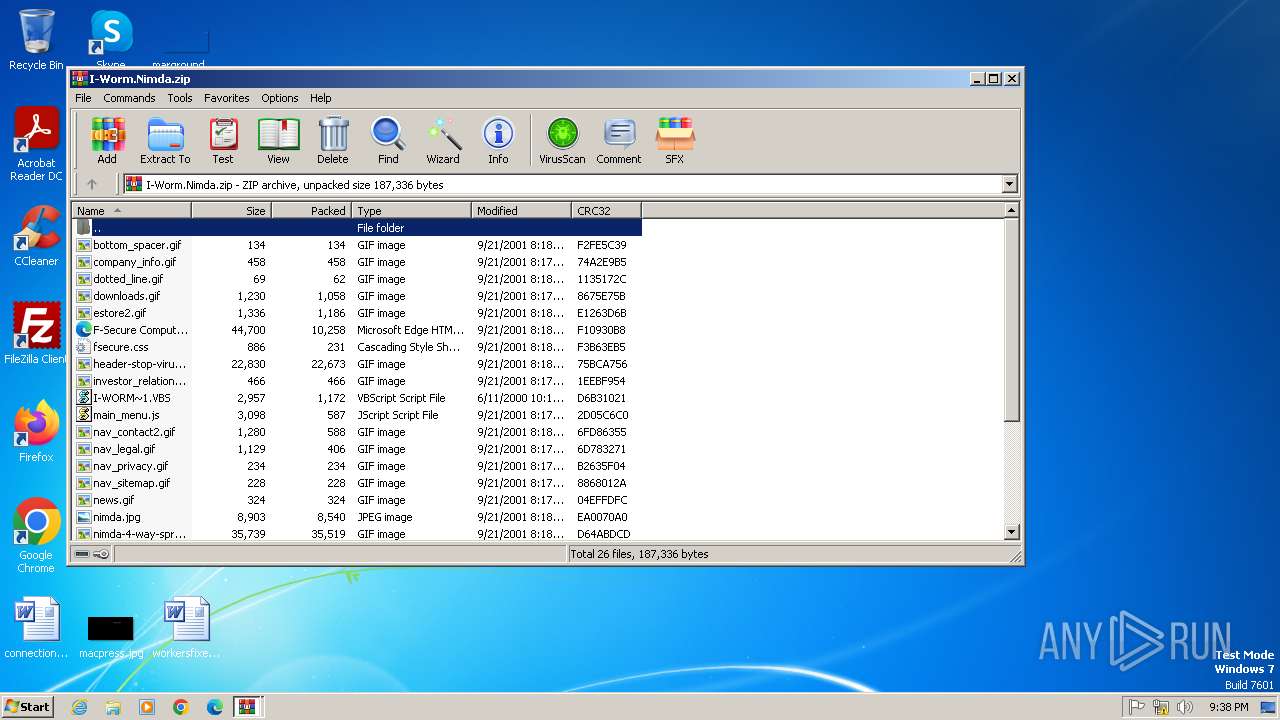
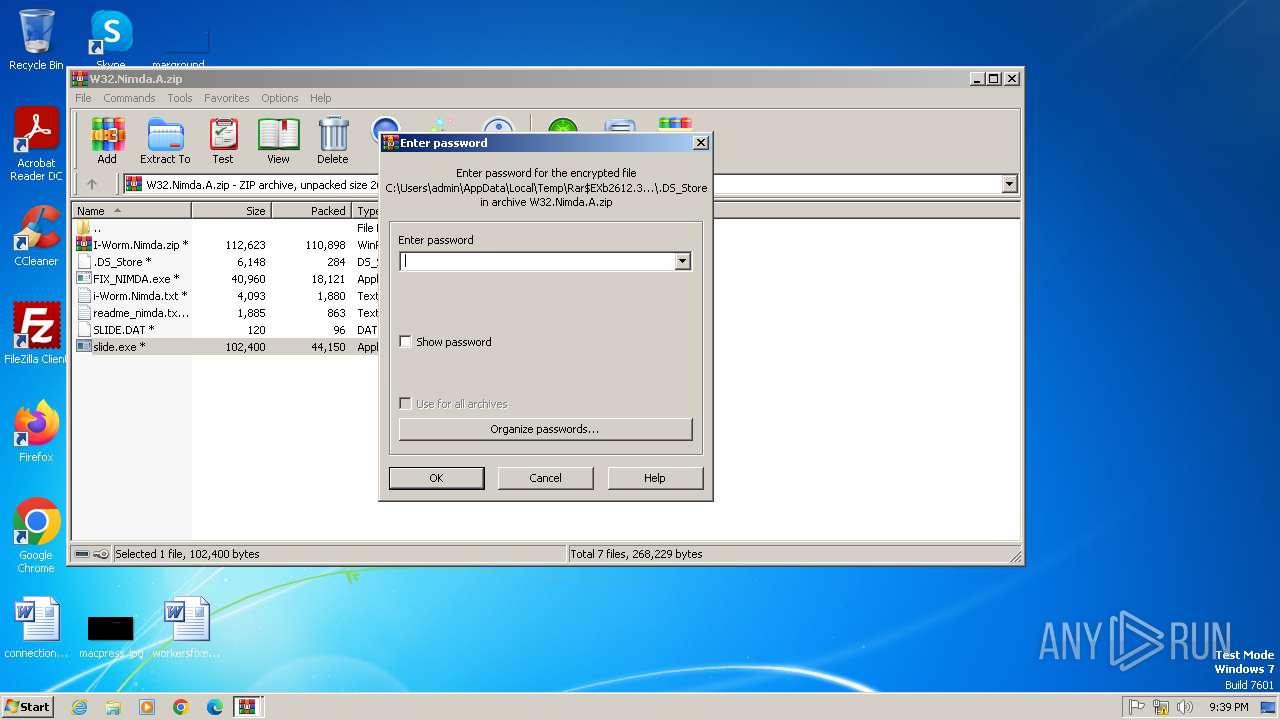
| 2612 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb2840.33077\I-Worm.Nimda.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2832 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2612.35208\slide.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2612.35208\slide.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
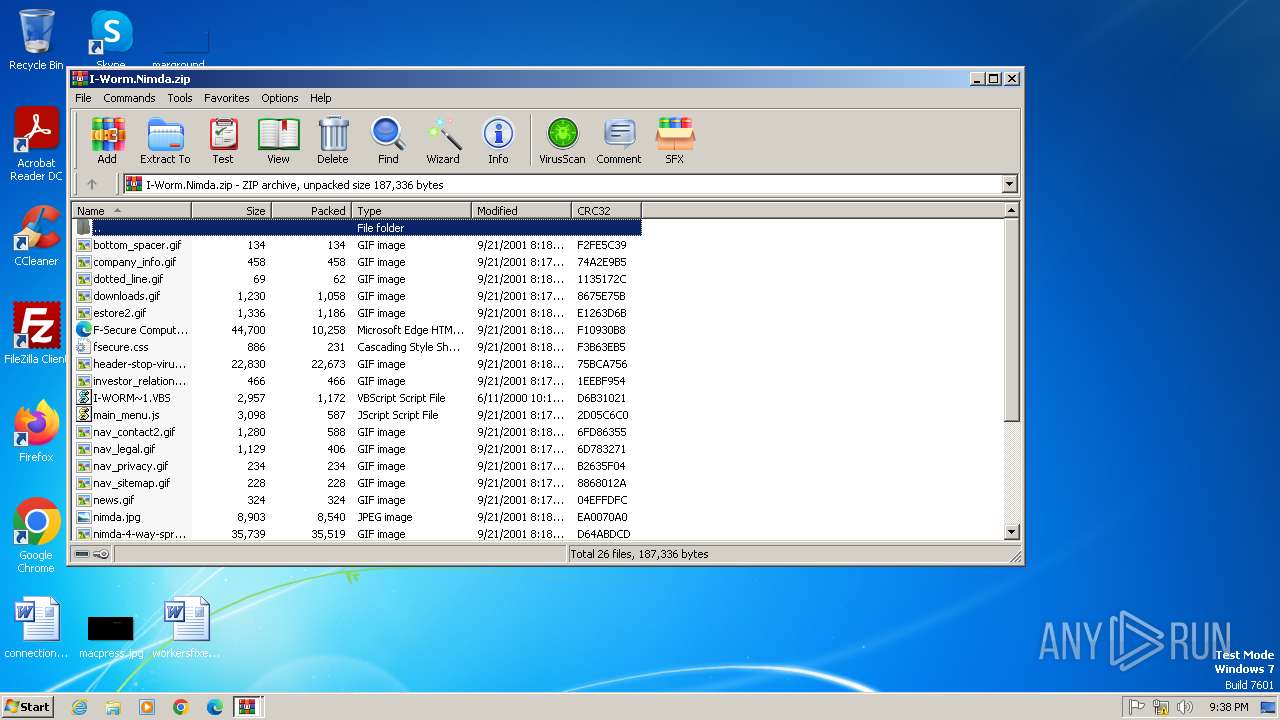
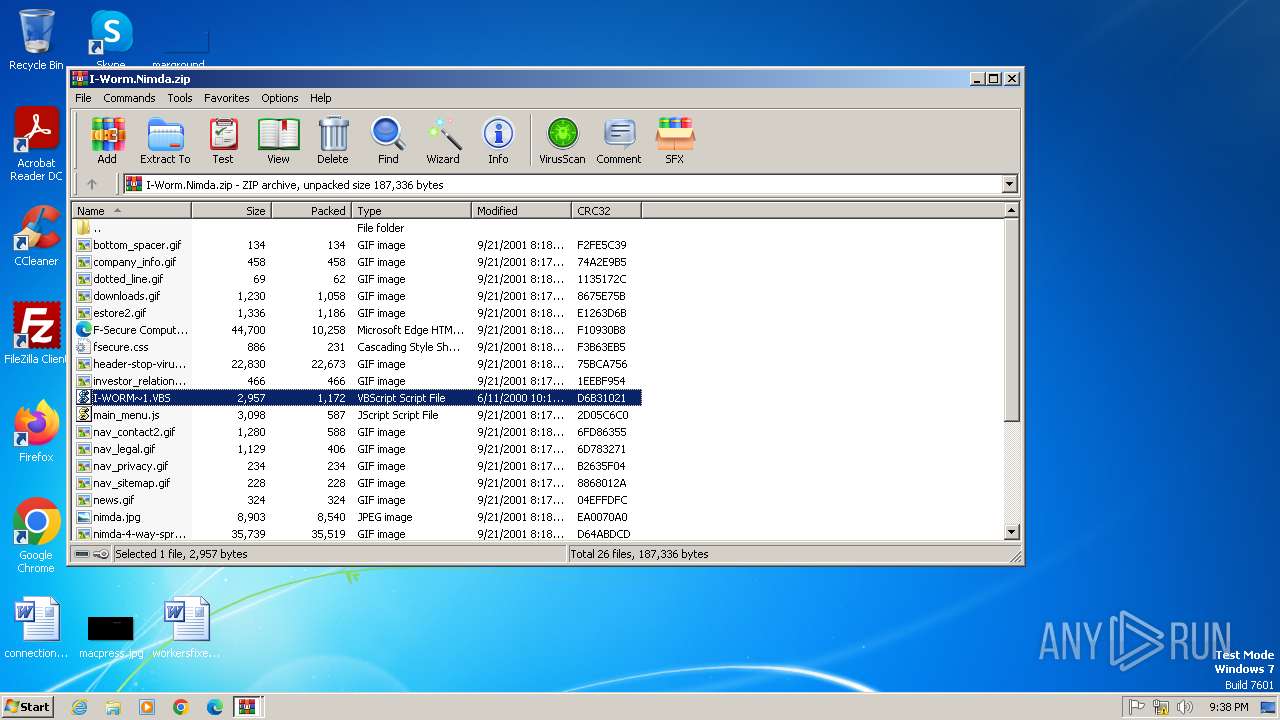
| 2840 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\W32.Nimda.A.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
3 482
Read events
3 408
Write events
74
Delete events
0
Modification events
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\W32.Nimda.A.zip | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
Executable files
4
Suspicious files
7
Text files
5
Unknown types
0
Dropped files
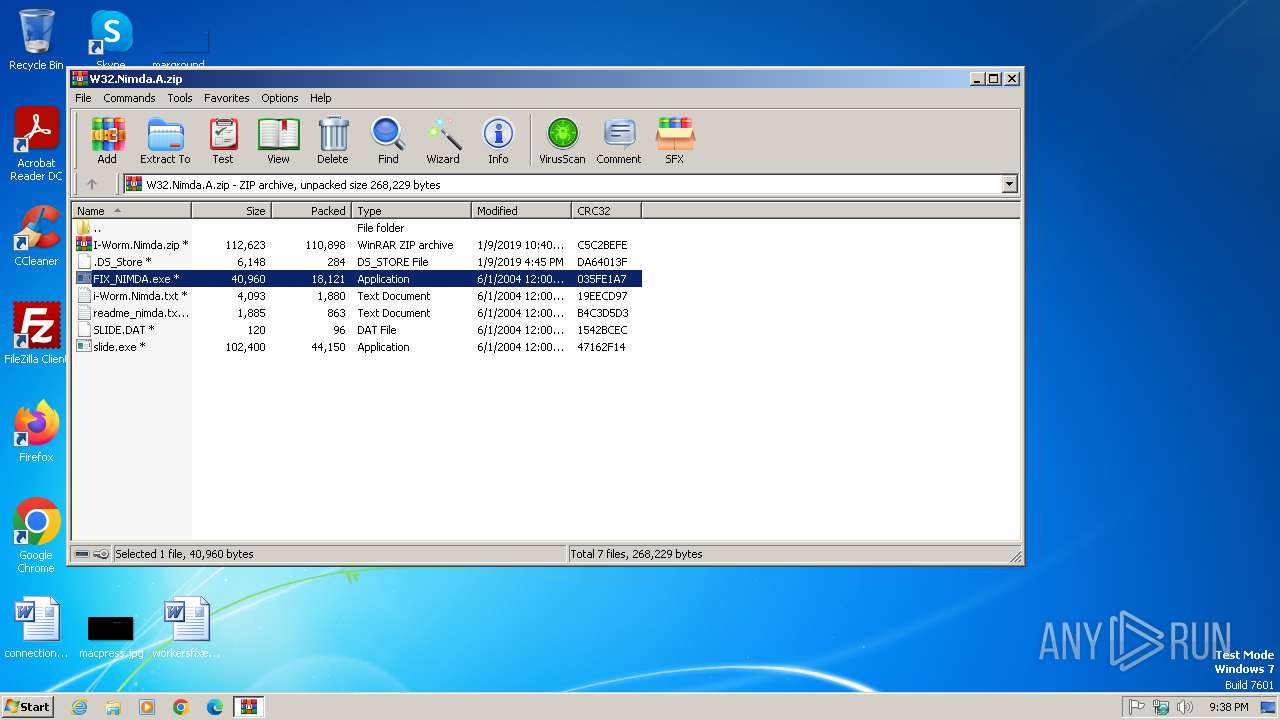
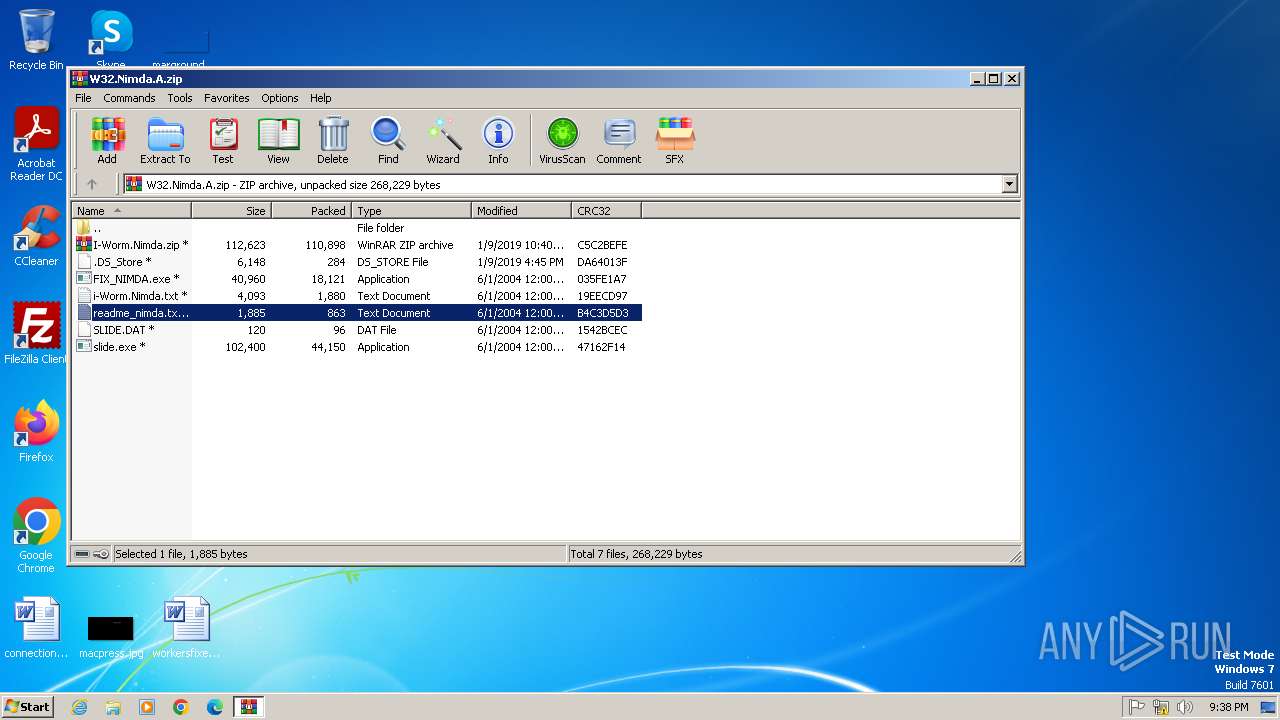
PID | Process | Filename | Type | |
|---|---|---|---|---|
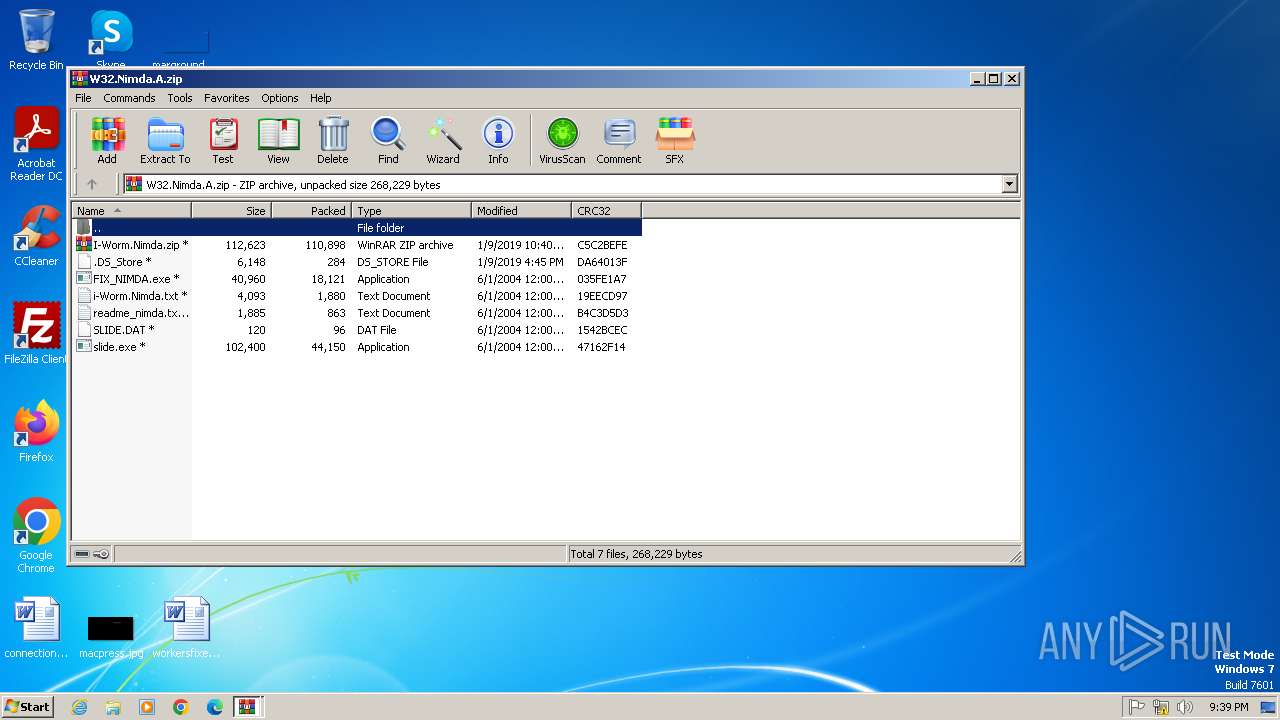
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2840.25766\i-Worm.Nimda.txt | text | |
MD5:A2B2A4DF2FE6A1D85E9032E3E50B365F | SHA256:B1FF29B2C351F1DB2AB0D4E388FAF2DD23E353F515709906C655F87D1C892D30 | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2840.25766\.DS_Store | binary | |
MD5:5885DE8B7051C934F6E083E67FE04E0F | SHA256:D4840E77AE5DDE7D977D0C7C4C8F962DADE3F77B999A21BD19265CFE4883318C | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2840.25766\SLIDE.DAT | binary | |
MD5:087B30CDDE1487F4F90ABD2659EDD19D | SHA256:62F699631A33D6C04B5C8041E55C6287151C1527394D958651BF14F05C4904CF | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2840.25766\I-Worm.Nimda.zip | compressed | |
MD5:844855B2EC58F20718CFF30D874AB43E | SHA256:70E37EA05B1D89E37E04B1C2CE98731E65B6C37CF718DC72A109D862CA36CC2A | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2840.25766\slide.exe | executable | |
MD5:06F46062E7D56457252A9A3E3A73405A | SHA256:8E2BDCAEE8DFEFCFE42740A43A0079EB1BABFC530200BCFB57B1B1A548852AF1 | |||
| 2612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2612.35208\I-Worm.Nimda.zip | compressed | |
MD5:844855B2EC58F20718CFF30D874AB43E | SHA256:70E37EA05B1D89E37E04B1C2CE98731E65B6C37CF718DC72A109D862CA36CC2A | |||
| 2612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2612.35208\SLIDE.DAT | binary | |
MD5:087B30CDDE1487F4F90ABD2659EDD19D | SHA256:62F699631A33D6C04B5C8041E55C6287151C1527394D958651BF14F05C4904CF | |||
| 2612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2612.35208\i-Worm.Nimda.txt | text | |
MD5:A2B2A4DF2FE6A1D85E9032E3E50B365F | SHA256:B1FF29B2C351F1DB2AB0D4E388FAF2DD23E353F515709906C655F87D1C892D30 | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2840.33077\I-Worm.Nimda.zip | compressed | |
MD5:844855B2EC58F20718CFF30D874AB43E | SHA256:70E37EA05B1D89E37E04B1C2CE98731E65B6C37CF718DC72A109D862CA36CC2A | |||
| 2612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2612.35208\FIX_NIMDA.exe | executable | |
MD5:36D433DC87FDBFFABABDE57EF3C3C130 | SHA256:3F5A6D8334F31ACD4D9E2811CA705E0BCF4A1C9F672D2FB4933A00ADF46B2F5A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |