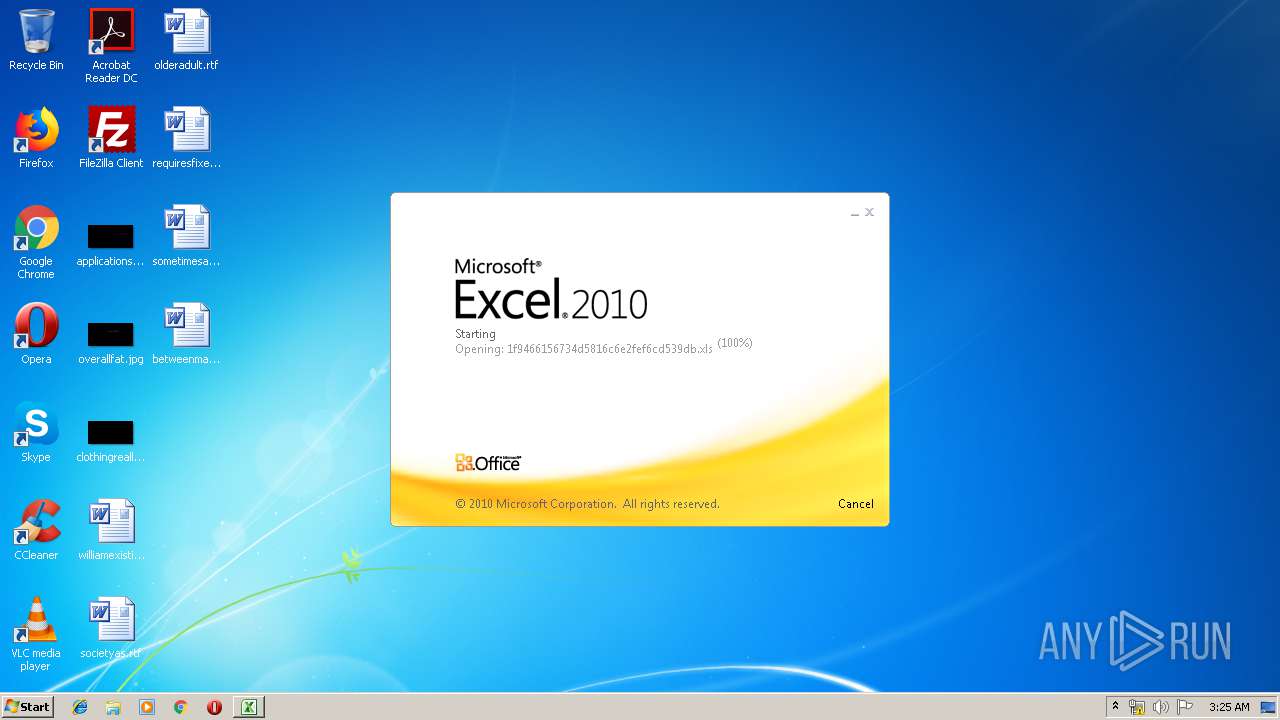
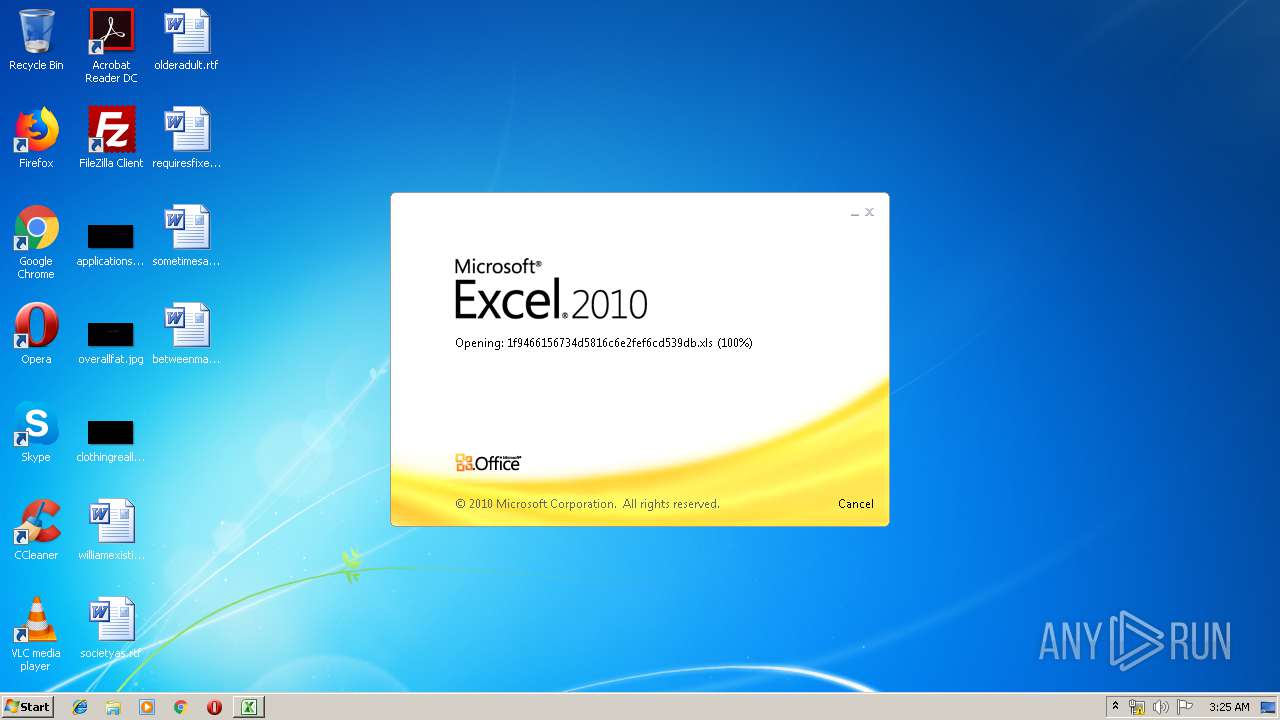
| File name: | 1f9466156734d5816c6e2fef6cd539db.xls |
| Full analysis: | https://app.any.run/tasks/94b4ebff-1aaf-4acb-864b-28b26b269c9b |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | June 17, 2019, 02:24:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.3, Code page: 1252, Last Saved By: Administrator, Name of Creating Application: Microsoft Excel, Create Time/Date: Sun May 5 19:23:48 2019, Last Saved Time/Date: Sun May 5 19:24:08 2019, Security: 0 |
| MD5: | 1F9466156734D5816C6E2FEF6CD539DB |
| SHA1: | F0CE85E82D02EE09B43E06DFFE8A1F801C545087 |
| SHA256: | E5620DA7870A8CDC2F3D8C58BBCC7989DB19E61FDF54C8B85A5D95BF6D285883 |
| SSDEEP: | 3072:K7k3hbdlylKsgqopeJBWhZFGkE+cL2NdAUwuapti1xkZB+oHZ3omMSBDICPICJ:+k3hbdlylKsgqopeJBWhZFVE+W2NdASE |
MALICIOUS
Requests a remote executable file from MS Office
- EXCEL.EXE (PID: 3292)
SUSPICIOUS
No suspicious indicators.INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3292)
Creates files in the user directory
- EXCEL.EXE (PID: 3292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 31 |
|---|---|
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
| Author: | - |
| LastModifiedBy: | Administrator |
| Software: | Microsoft Excel |
| CreateDate: | 2019:05:05 18:23:48 |
| ModifyDate: | 2019:05:05 18:24:08 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | Sheet1 |
| HeadingPairs: |
|
Total processes
32
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3292 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
551
Read events
522
Write events
22
Delete events
7
Modification events
| (PID) Process: | (3292) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | -z! |
Value: 2D7A2100DC0C0000010000000000000000000000 | |||
| (PID) Process: | (3292) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3292) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3292) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: DC0C00005A46ACE5B324D50100000000 | |||
| (PID) Process: | (3292) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | -z! |
Value: 2D7A2100DC0C0000010000000000000000000000 | |||
| (PID) Process: | (3292) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3292) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3292) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3292) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3292) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\1201ED |
| Operation: | write | Name: | 1201ED |
Value: 04000000DC0C00004600000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00310066003900340036003600310035003600370033003400640035003800310036006300360065003200660065006600360063006400350033003900640062002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000F06EAAE7B324D501ED011200ED01120000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3292 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRFA0D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3292 | EXCEL.EXE | GET | 404 | 27.121.66.127:80 | http://operationharvest.co.nz/wp-admin/lp.exe | AU | html | 332 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3292 | EXCEL.EXE | 27.121.66.127:80 | operationharvest.co.nz | NetRegistry Pty Ltd. | AU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
operationharvest.co.nz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3292 | EXCEL.EXE | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
3292 | EXCEL.EXE | A Network Trojan was detected | AV TROJAN Possible infected Wordpress - Payload download attempt |
3292 | EXCEL.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |