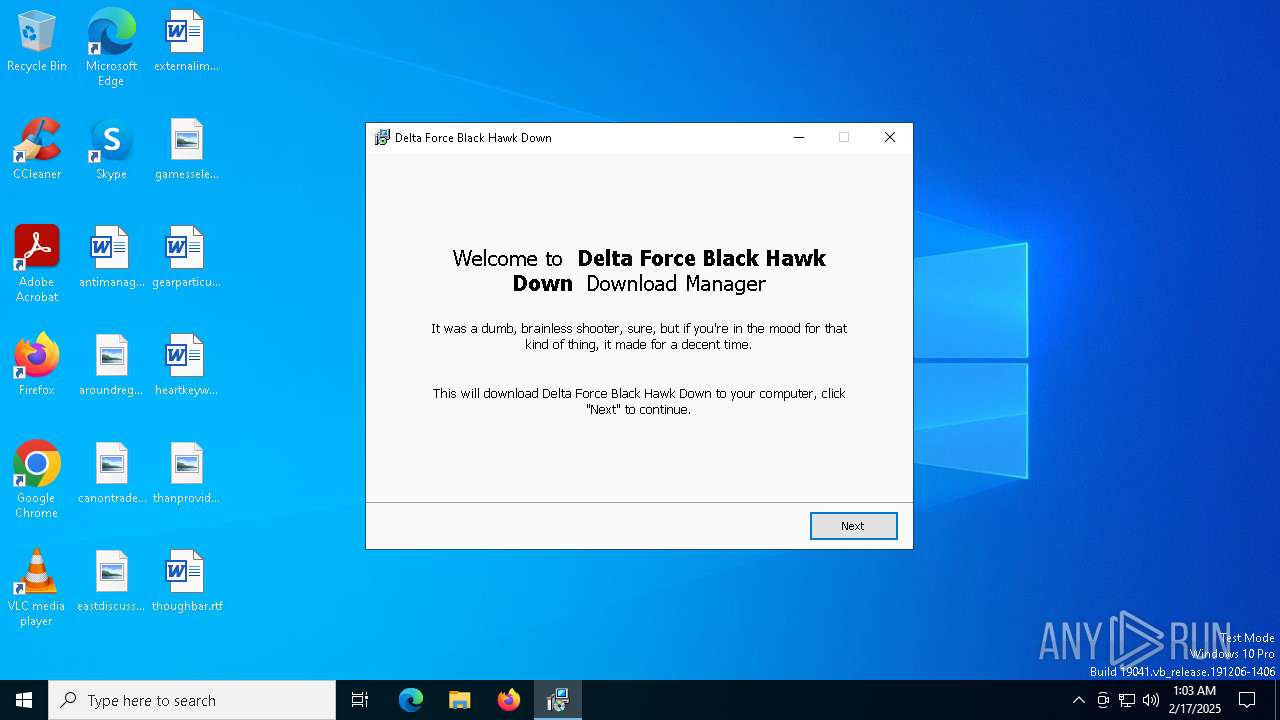
| File name: | Delta Force Black Hawk Down_Gaw-JW1.exe |
| Full analysis: | https://app.any.run/tasks/370e0d2d-39d2-4c16-8aa0-c7296e8c744a |
| Verdict: | Malicious activity |
| Analysis date: | February 17, 2025, 01:03:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 10 sections |
| MD5: | AF45BC08A07F1BA16ABE59F29072EBCC |
| SHA1: | 66EDEA40BA7B38A45BD856E6889BBA12384C458F |
| SHA256: | E555C06879ED4EDA6277E1FA8A4985590E70D8FA81421103048803E386DAAF28 |
| SSDEEP: | 98304:o+QqZ8fuG1aI4ixlYM0Z38bs9l5hCgrduoLbq1mfdtEu8bFXM4cw/3qiYiXBgkbY:lxsRkun5v9iN57CC/ra0U0T |
MALICIOUS
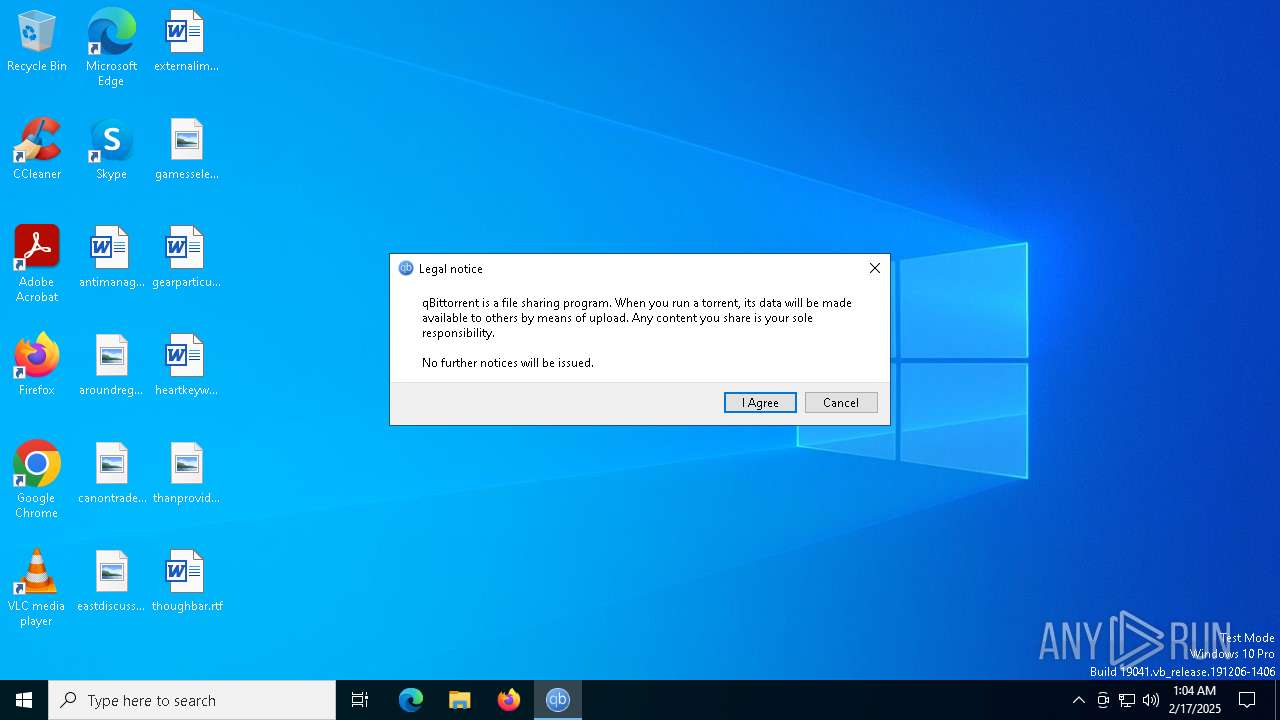
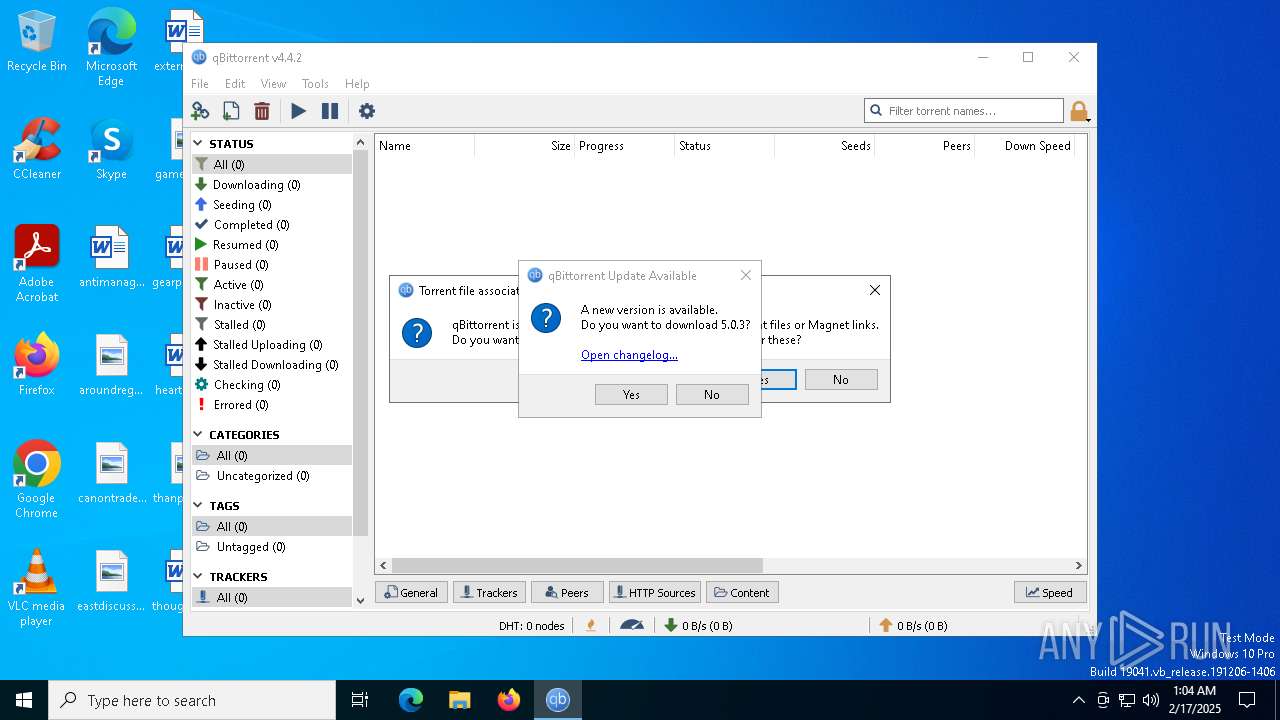
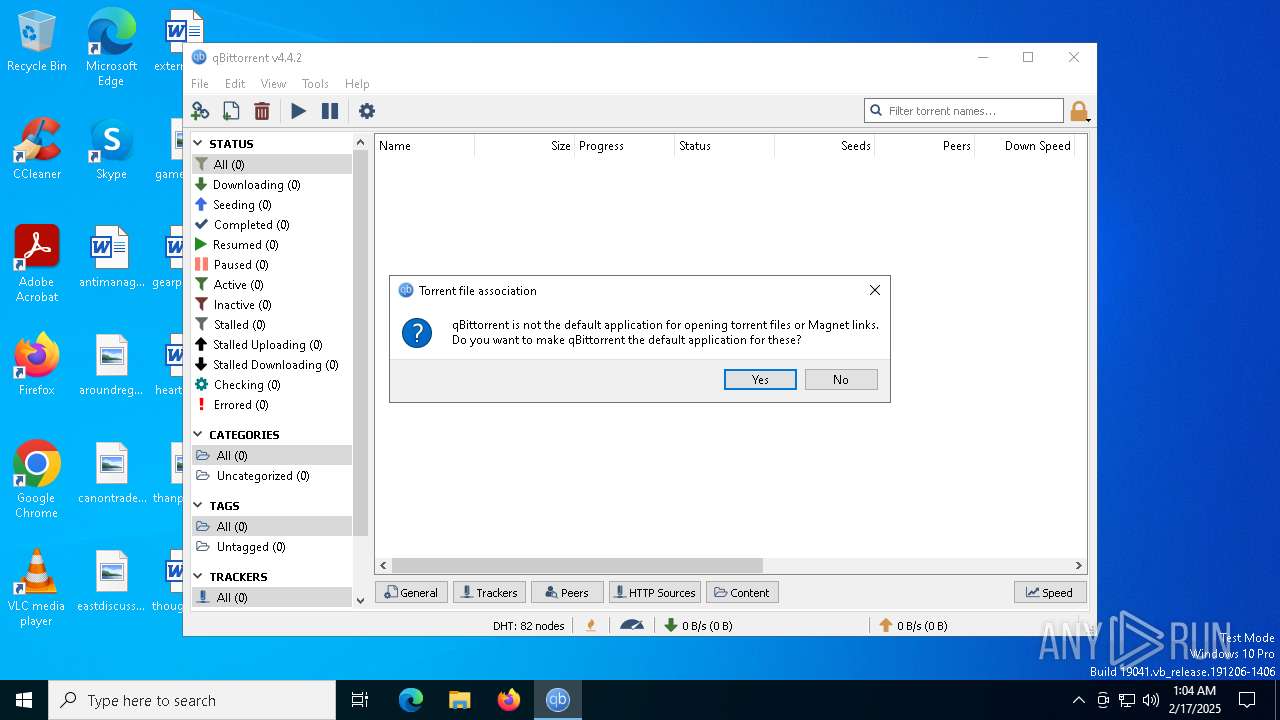
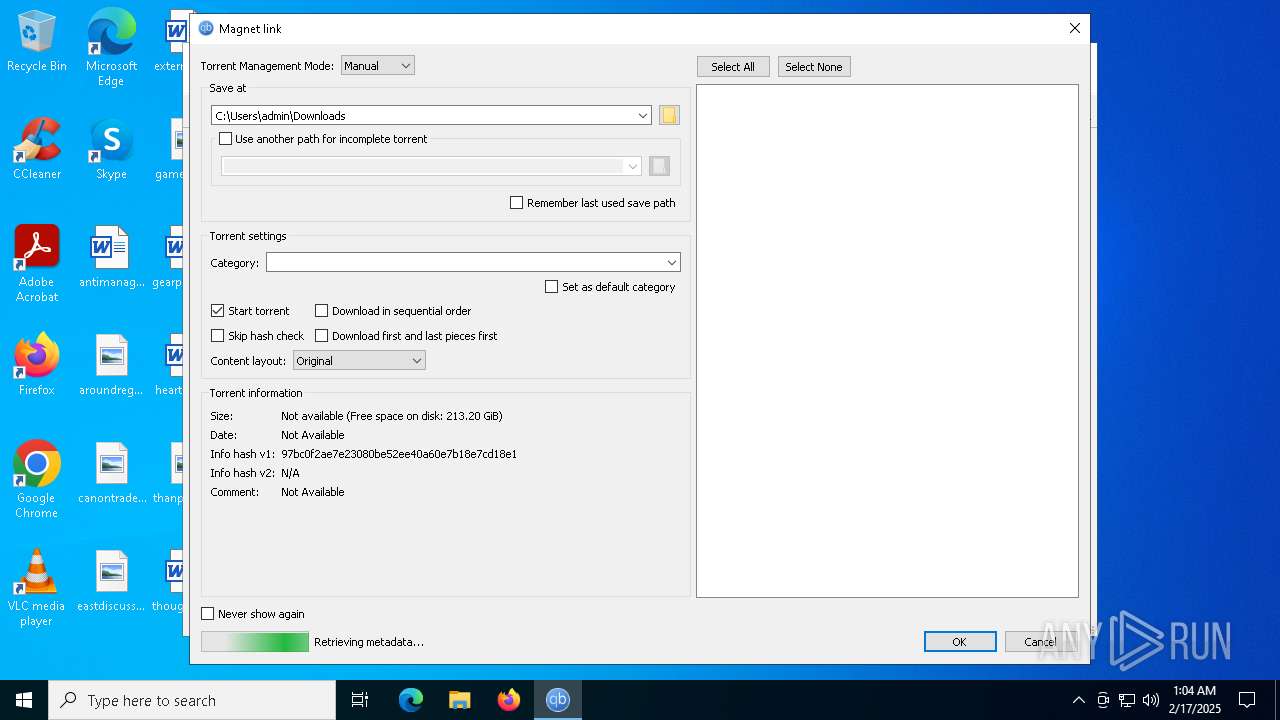
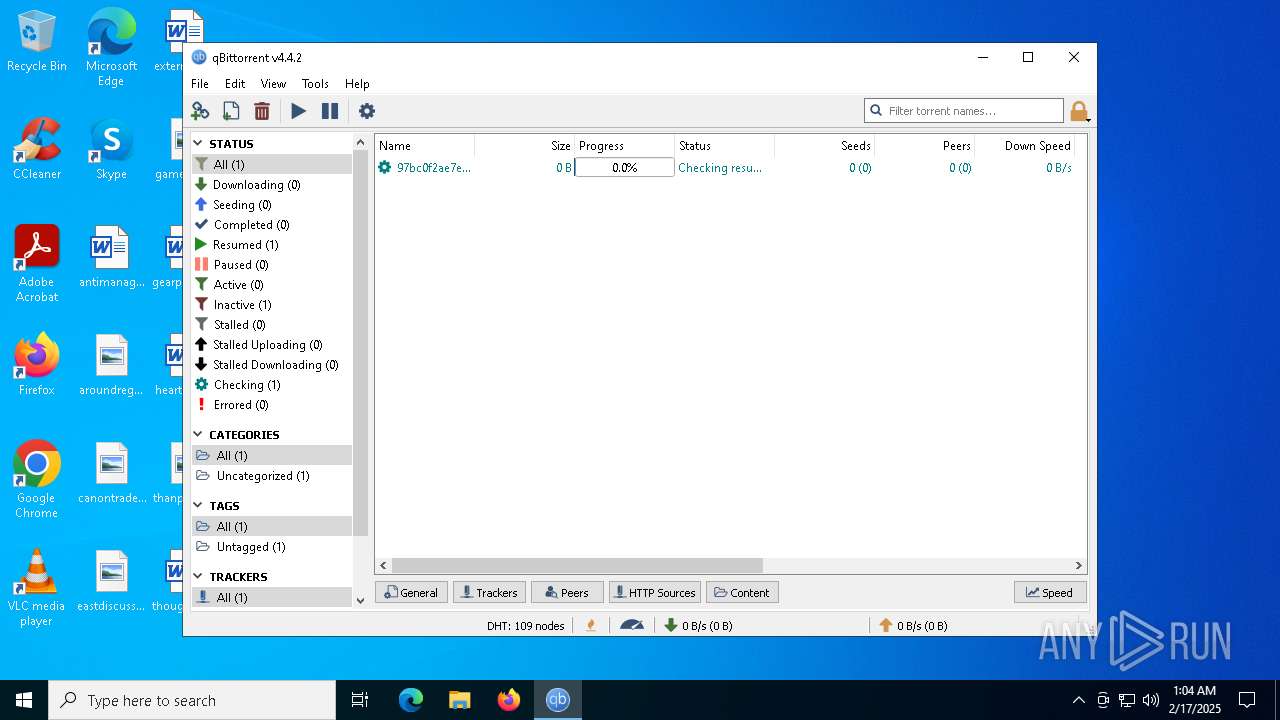
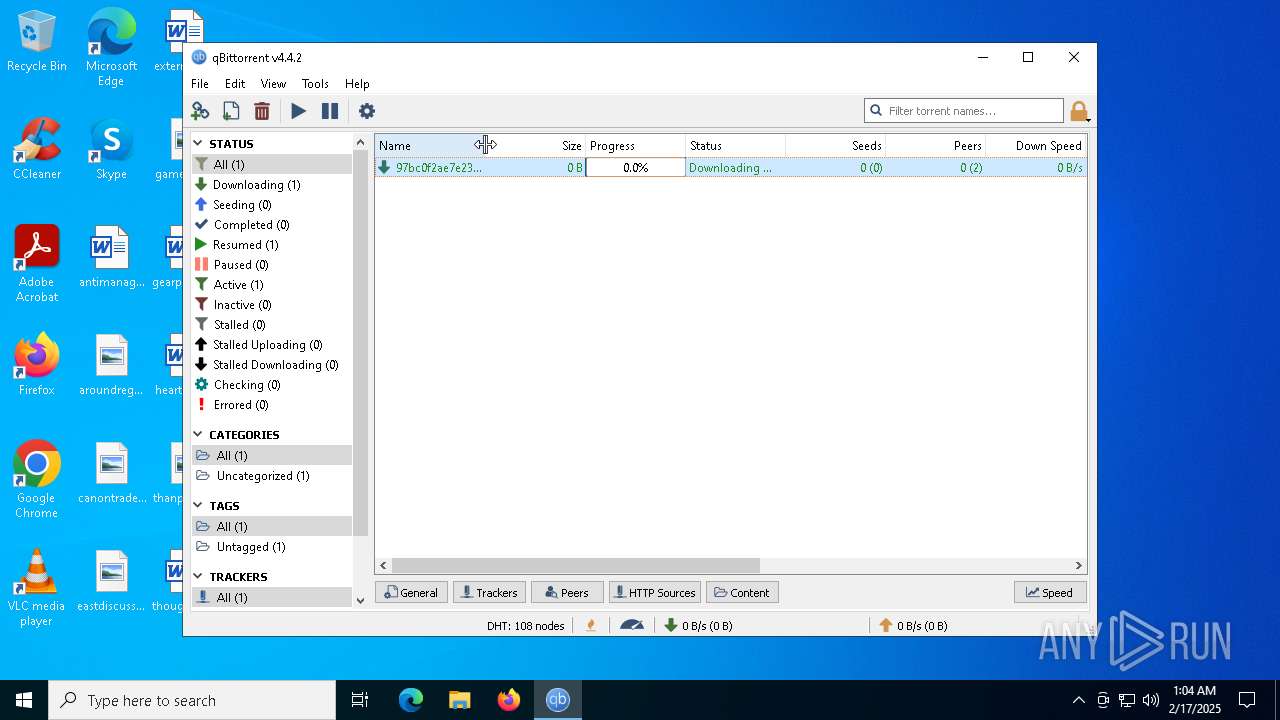
BITTORRENT has been detected (SURICATA)
- qbittorrent.exe (PID: 3524)
SUSPICIOUS
Reads security settings of Internet Explorer
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6348)
Executable content was dropped or overwritten
- Delta Force Black Hawk Down_Gaw-JW1.exe (PID: 6328)
- Delta Force Black Hawk Down_Gaw-JW1.exe (PID: 6548)
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
Reads the Windows owner or organization settings
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
There is functionality for taking screenshot (YARA)
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
Connects to unusual port
- qbittorrent.exe (PID: 3524)
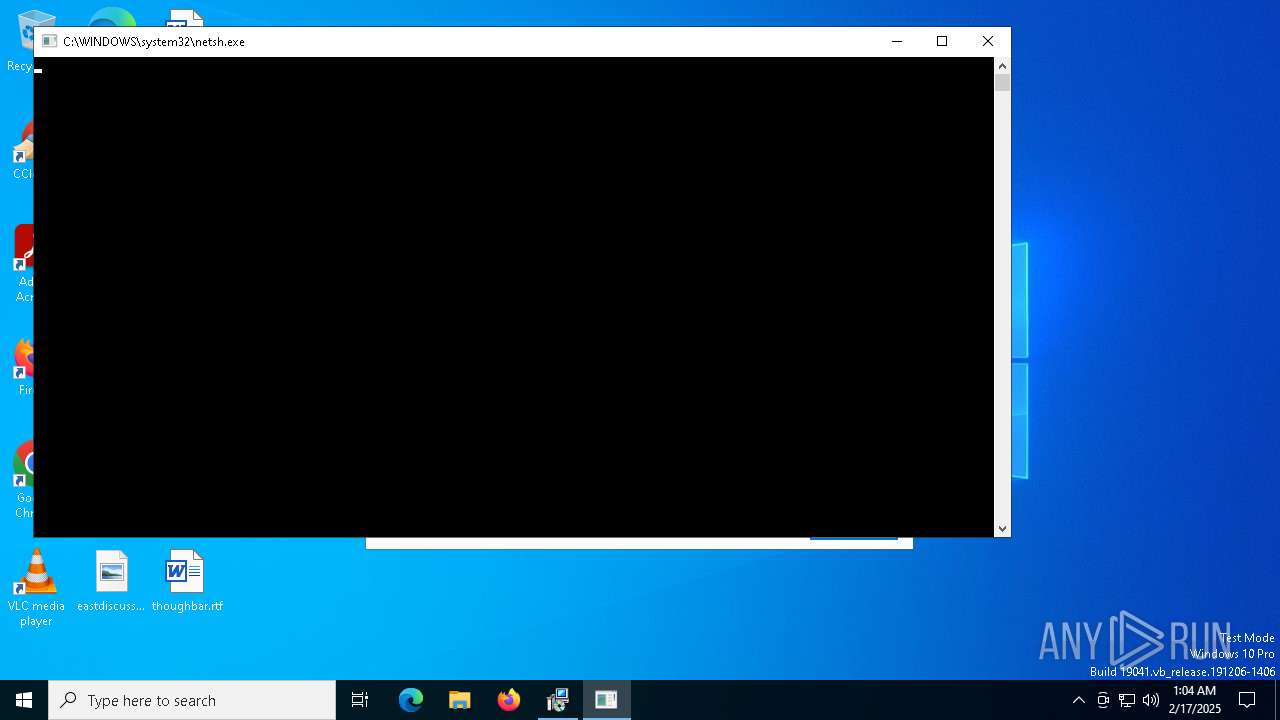
Uses NETSH.EXE to add a firewall rule or allowed programs
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
INFO
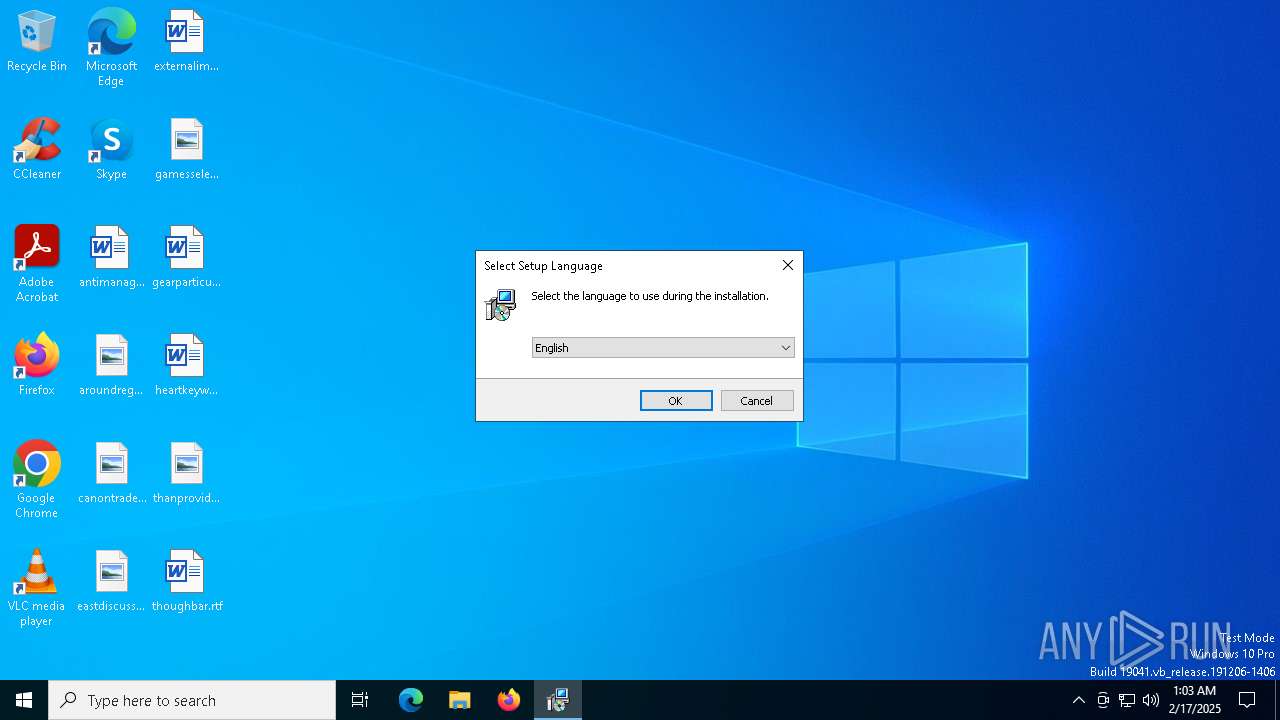
Checks supported languages
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6348)
- Delta Force Black Hawk Down_Gaw-JW1.exe (PID: 6328)
- Delta Force Black Hawk Down_Gaw-JW1.exe (PID: 6548)
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
- qbittorrent.exe (PID: 3524)
Reads the computer name
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6348)
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
- qbittorrent.exe (PID: 3524)
Create files in a temporary directory
- Delta Force Black Hawk Down_Gaw-JW1.exe (PID: 6328)
- Delta Force Black Hawk Down_Gaw-JW1.exe (PID: 6548)
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
Process checks computer location settings
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6348)
The sample compiled with english language support
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
Reads the software policy settings
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
Compiled with Borland Delphi (YARA)
- Delta Force Black Hawk Down_Gaw-JW1.exe (PID: 6328)
- Delta Force Black Hawk Down_Gaw-JW1.exe (PID: 6548)
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6348)
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
Detects InnoSetup installer (YARA)
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6348)
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
- Delta Force Black Hawk Down_Gaw-JW1.exe (PID: 6548)
- Delta Force Black Hawk Down_Gaw-JW1.exe (PID: 6328)
Creates files or folders in the user directory
- qbittorrent.exe (PID: 3524)
Qt framework related mutex has been found
- qbittorrent.exe (PID: 3524)
Reads the machine GUID from the registry
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
- qbittorrent.exe (PID: 3524)
Checks proxy server information
- Delta Force Black Hawk Down_Gaw-JW1.tmp (PID: 6576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:15 09:48:30+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.310.12.0 |
| ProductVersionNumber: | 5.310.12.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Axium Audit, OOO Download Manager |
| FileVersion: | 5.310.12 |
| LegalCopyright: | © Axium Audit |
| OriginalFileName: | |
| ProductName: | Axium Audit, OOO |
| ProductVersion: | 5.310.12 |
Total processes
134
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
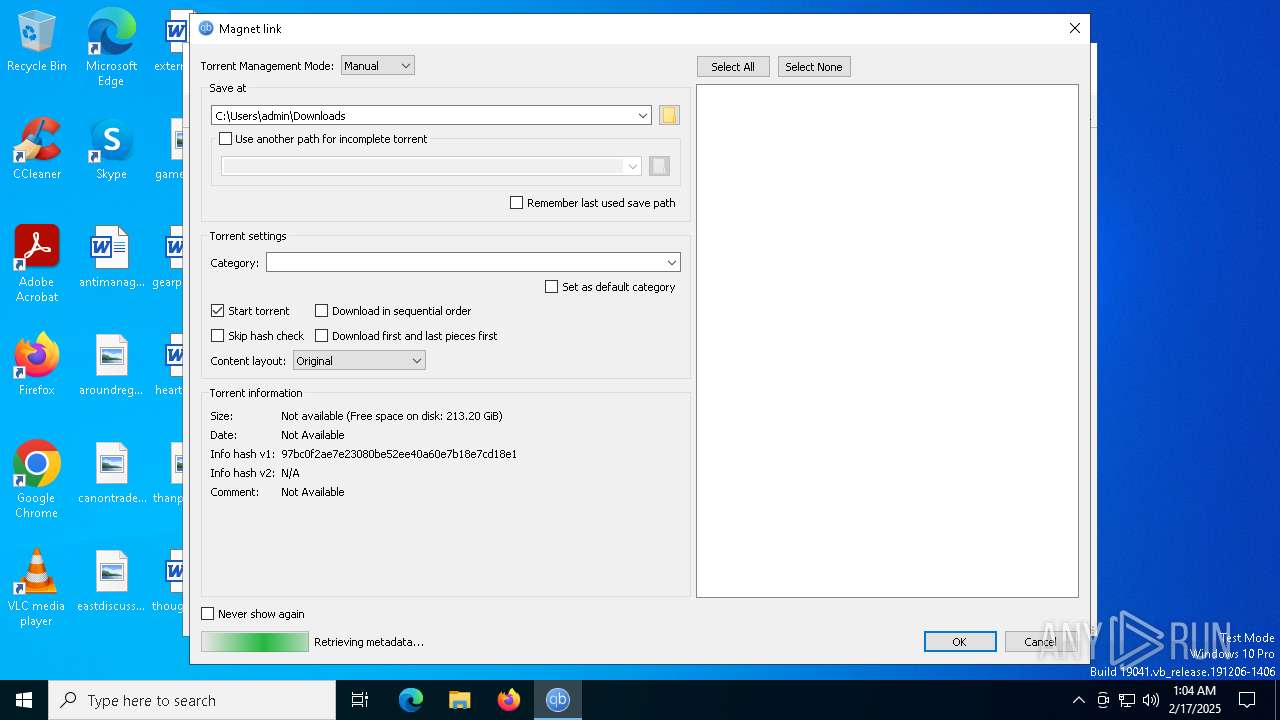
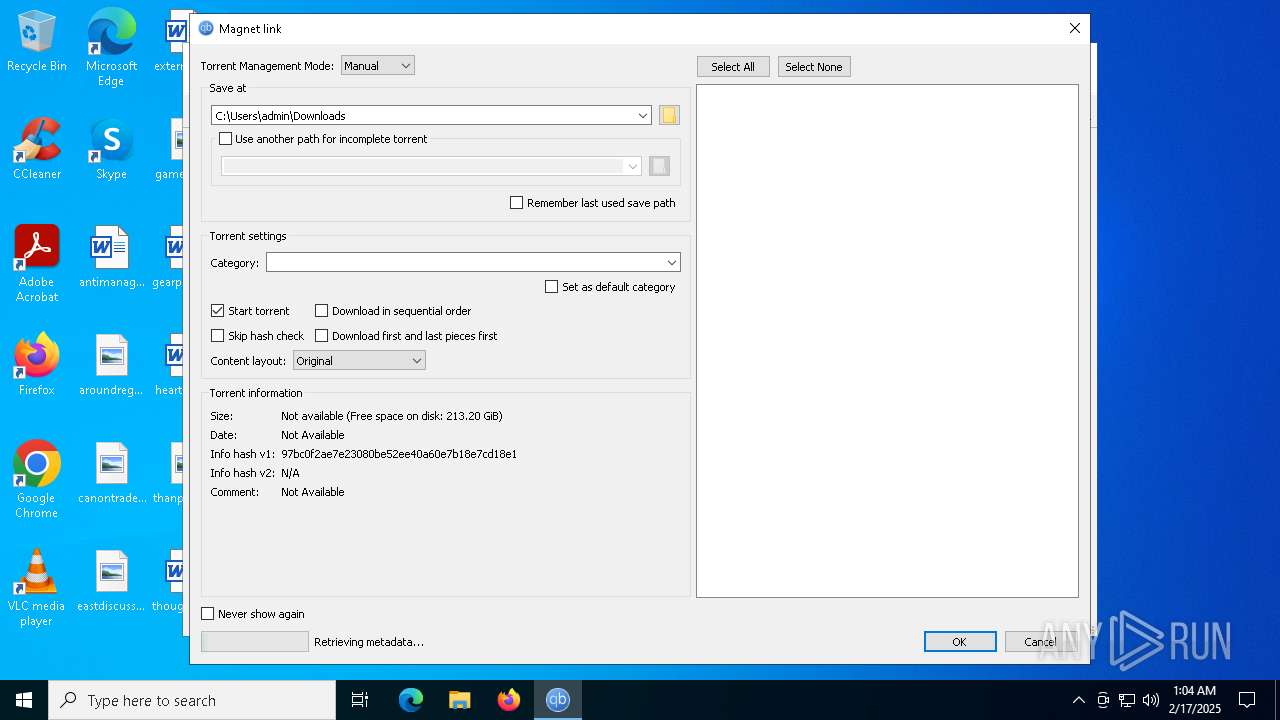
| 3524 | "C:\Users\admin\AppData\Local\Temp\is-FKRK8.tmp\qbittorrent.exe" magnet:?xt=urn:btih:97BC0F2AE7E23080BE52EE40A60E7B18E7CD18E1 | C:\Users\admin\AppData\Local\Temp\is-FKRK8.tmp\qbittorrent.exe | Delta Force Black Hawk Down_Gaw-JW1.tmp | ||||||||||||
User: admin Company: The qBittorrent Project Integrity Level: HIGH Description: qBittorrent - A Bittorrent Client Version: v4.4.2 Modules
| |||||||||||||||
| 5300 | "netsh" firewall add allowedprogramC:\Users\admin\AppData\Local\Temp\is-FKRK8.tmp\qbittorrent.exe "qBittorrent" ENABLE | C:\Windows\SysWOW64\netsh.exe | — | Delta Force Black Hawk Down_Gaw-JW1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6328 | "C:\Users\admin\AppData\Local\Temp\Delta Force Black Hawk Down_Gaw-JW1.exe" | C:\Users\admin\AppData\Local\Temp\Delta Force Black Hawk Down_Gaw-JW1.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Axium Audit, OOO Download Manager Exit code: 0 Version: 5.310.12 Modules
| |||||||||||||||
| 6348 | "C:\Users\admin\AppData\Local\Temp\is-J6ONJ.tmp\Delta Force Black Hawk Down_Gaw-JW1.tmp" /SL5="$80284,13566766,780800,C:\Users\admin\AppData\Local\Temp\Delta Force Black Hawk Down_Gaw-JW1.exe" | C:\Users\admin\AppData\Local\Temp\is-J6ONJ.tmp\Delta Force Black Hawk Down_Gaw-JW1.tmp | — | Delta Force Black Hawk Down_Gaw-JW1.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 6548 | "C:\Users\admin\AppData\Local\Temp\Delta Force Black Hawk Down_Gaw-JW1.exe" /SPAWNWND=$50242 /NOTIFYWND=$80284 | C:\Users\admin\AppData\Local\Temp\Delta Force Black Hawk Down_Gaw-JW1.exe | Delta Force Black Hawk Down_Gaw-JW1.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Axium Audit, OOO Download Manager Exit code: 0 Version: 5.310.12 Modules
| |||||||||||||||
| 6576 | "C:\Users\admin\AppData\Local\Temp\is-M8SIC.tmp\Delta Force Black Hawk Down_Gaw-JW1.tmp" /SL5="$602C2,13566766,780800,C:\Users\admin\AppData\Local\Temp\Delta Force Black Hawk Down_Gaw-JW1.exe" /SPAWNWND=$50242 /NOTIFYWND=$80284 | C:\Users\admin\AppData\Local\Temp\is-M8SIC.tmp\Delta Force Black Hawk Down_Gaw-JW1.tmp | Delta Force Black Hawk Down_Gaw-JW1.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
4 808
Read events
4 806
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3524) qbittorrent.exe | Key: | HKEY_CLASSES_ROOT\magnet |
| Operation: | write | Name: | Content Type |
Value: application/x-magnet | |||
| (PID) Process: | (3524) qbittorrent.exe | Key: | HKEY_CLASSES_ROOT\magnet |
| Operation: | write | Name: | URL Protocol |
Value: | |||
Executable files
8
Suspicious files
8
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3524 | qbittorrent.exe | C:\Users\admin\AppData\Local\qBittorrent\GeoDB\dbip-country-lite.mmdb.LIGPei | — | |
MD5:— | SHA256:— | |||
| 3524 | qbittorrent.exe | C:\Users\admin\AppData\Local\qBittorrent\GeoDB\dbip-country-lite.mmdb | — | |
MD5:— | SHA256:— | |||
| 6548 | Delta Force Black Hawk Down_Gaw-JW1.exe | C:\Users\admin\AppData\Local\Temp\is-M8SIC.tmp\Delta Force Black Hawk Down_Gaw-JW1.tmp | executable | |
MD5:49312C19FA9B298CA2AE71E14F07CCF3 | SHA256:74C20B61D428450E2C0B3974381684190D8BBD2AEF3D573C86A3A954598319A5 | |||
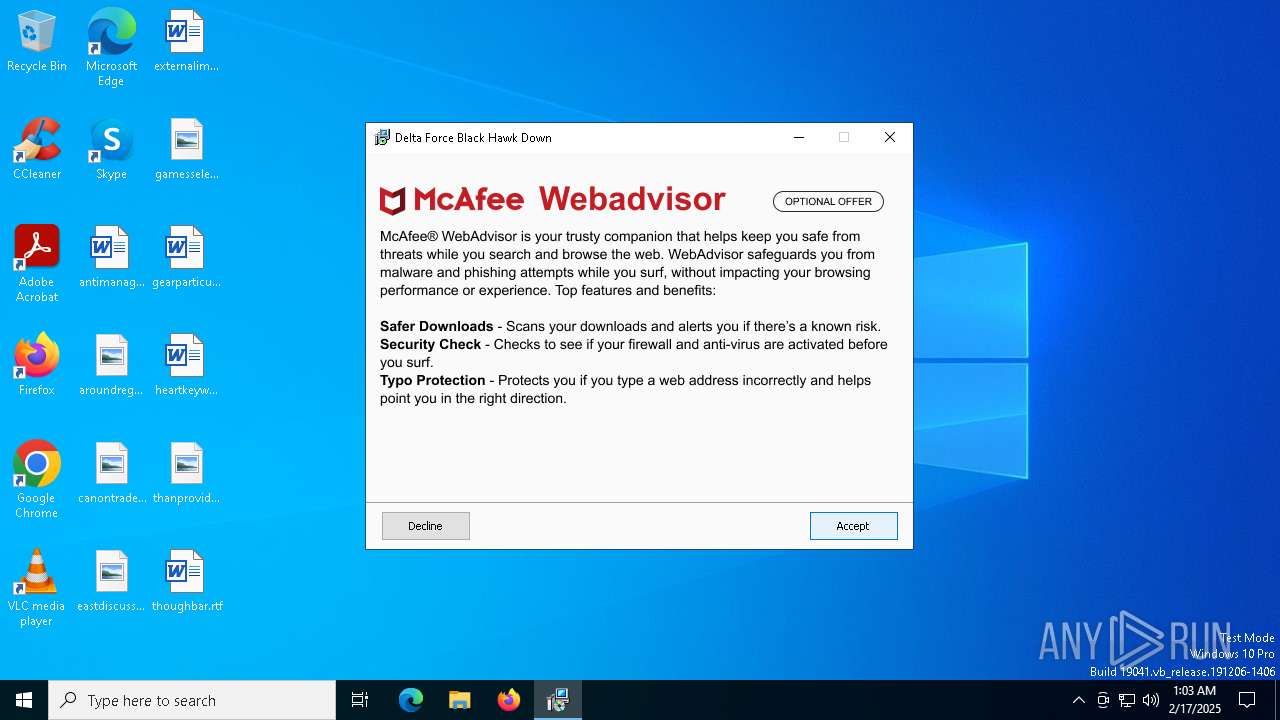
| 6576 | Delta Force Black Hawk Down_Gaw-JW1.tmp | C:\Users\admin\AppData\Local\Temp\is-FKRK8.tmp\AVG_AV.png | image | |
MD5:AEE8E80B35DCB3CF2A5733BA99231560 | SHA256:35BBD8F390865173D65BA2F38320A04755541A0783E9F825FDB9862F80D97AA9 | |||
| 6576 | Delta Force Black Hawk Down_Gaw-JW1.tmp | C:\Users\admin\AppData\Local\Temp\is-FKRK8.tmp\WeatherZero.png | image | |
MD5:9AC6287111CB2B272561781786C46CDD | SHA256:AB99CDB7D798CB7B7D8517584D546AA4ED54ECA1B808DE6D076710C8A400C8C4 | |||
| 6576 | Delta Force Black Hawk Down_Gaw-JW1.tmp | C:\Users\admin\AppData\Local\Temp\is-FKRK8.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 6576 | Delta Force Black Hawk Down_Gaw-JW1.tmp | C:\Users\admin\AppData\Local\Temp\is-FKRK8.tmp\is-4S019.tmp | image | |
MD5:AEE8E80B35DCB3CF2A5733BA99231560 | SHA256:35BBD8F390865173D65BA2F38320A04755541A0783E9F825FDB9862F80D97AA9 | |||
| 6576 | Delta Force Black Hawk Down_Gaw-JW1.tmp | C:\Users\admin\AppData\Local\Temp\is-FKRK8.tmp\is-0RTCU.tmp | image | |
MD5:DB6C259CD7B58F2F7A3CCA0C38834D0E | SHA256:494169CDD9C79EB4668378F770BFA55D4B140F23A682FF424441427DFAB0CED2 | |||
| 6576 | Delta Force Black Hawk Down_Gaw-JW1.tmp | C:\Users\admin\AppData\Local\Temp\is-FKRK8.tmp\finish.png | image | |
MD5:1BDB17B59DD0FC8360B30C5CE46762A0 | SHA256:49911E40F4E80C8342524034A6A96907703EF9EF4ABDB6175AD6F93824DF6CBE | |||
| 6576 | Delta Force Black Hawk Down_Gaw-JW1.tmp | C:\Users\admin\AppData\Local\Temp\is-FKRK8.tmp\qbittorrent.exe | executable | |
MD5:22A34900ADA67EAD7E634EB693BD3095 | SHA256:3CEC1E40E8116A35AAC6DF3DA0356864E5D14BC7687C502C7936EE9B7C1B9C58 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
213
DNS requests
27
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
936 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6168 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
936 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
188 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.16.110.121:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
d3ben4sjdmrs9v.cloudfront.net |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | INFO [ANY.RUN] P2P BitTorrent Protocol |
3524 | qbittorrent.exe | Misc activity | INFO [ANY.RUN] P2P BitTorrent Protocol |
Process | Message |
|---|---|
qbittorrent.exe | QObject::startTimer: Timers cannot have negative intervals
|