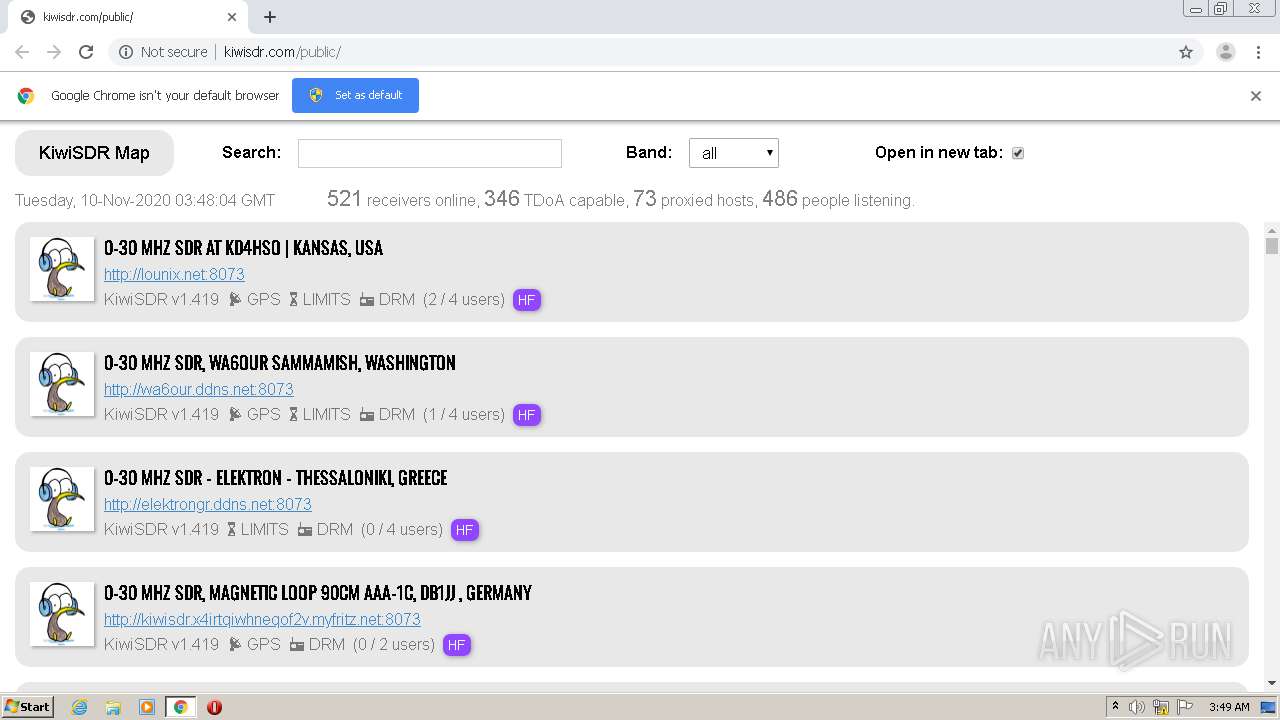
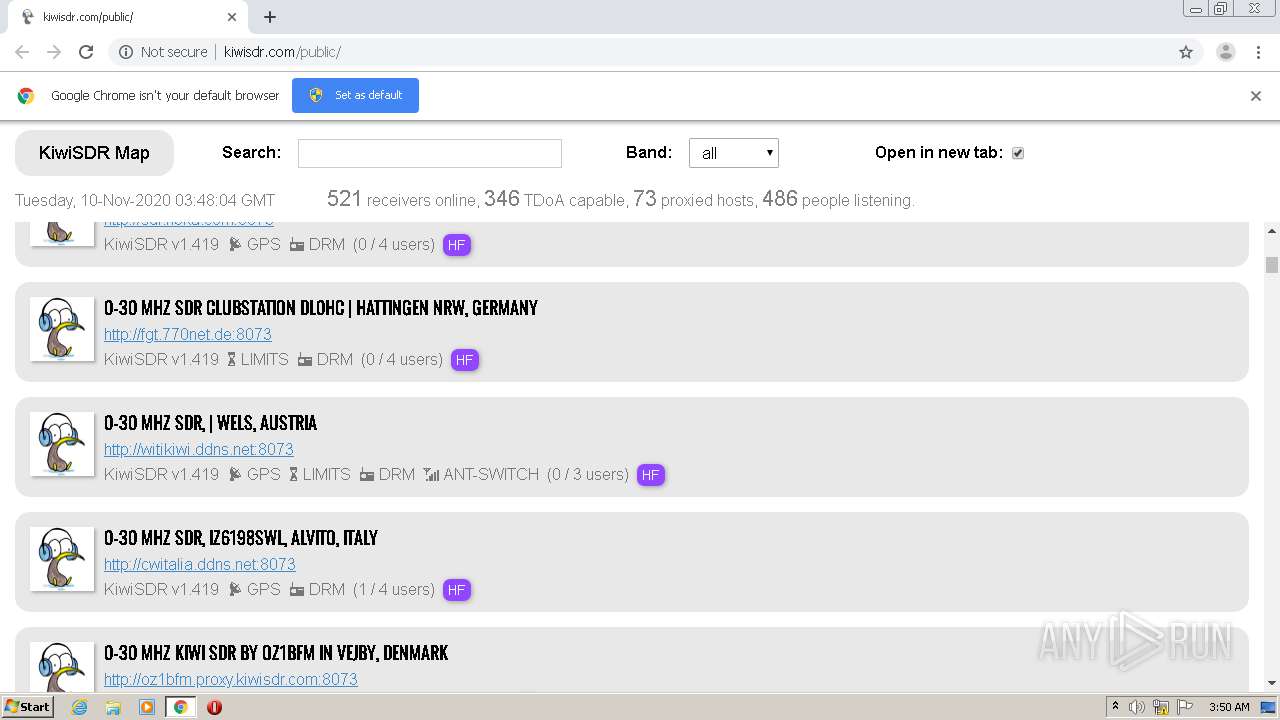
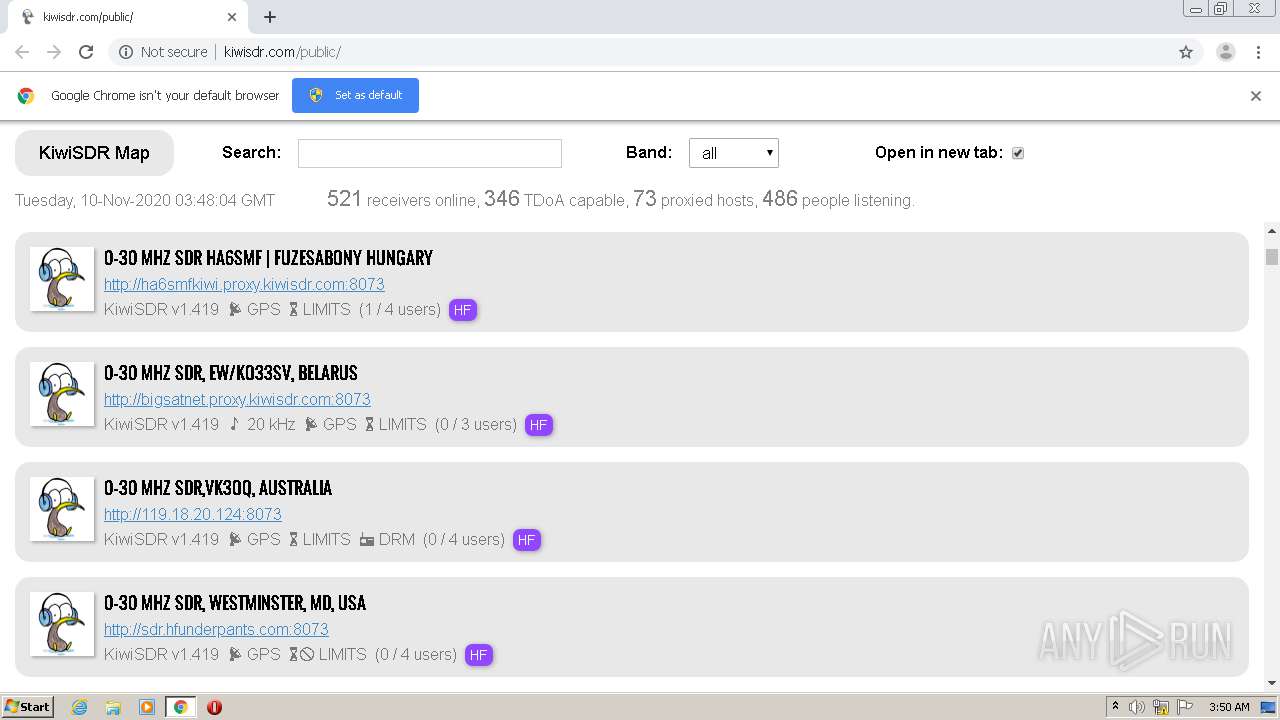
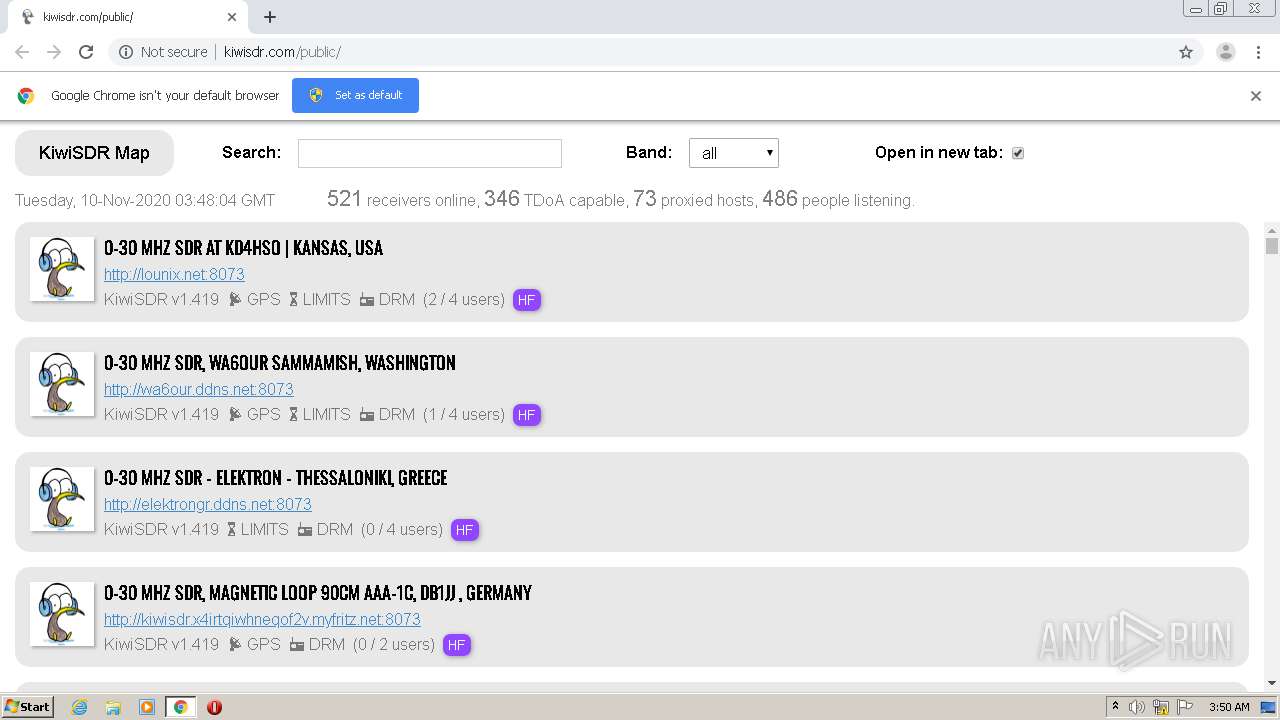
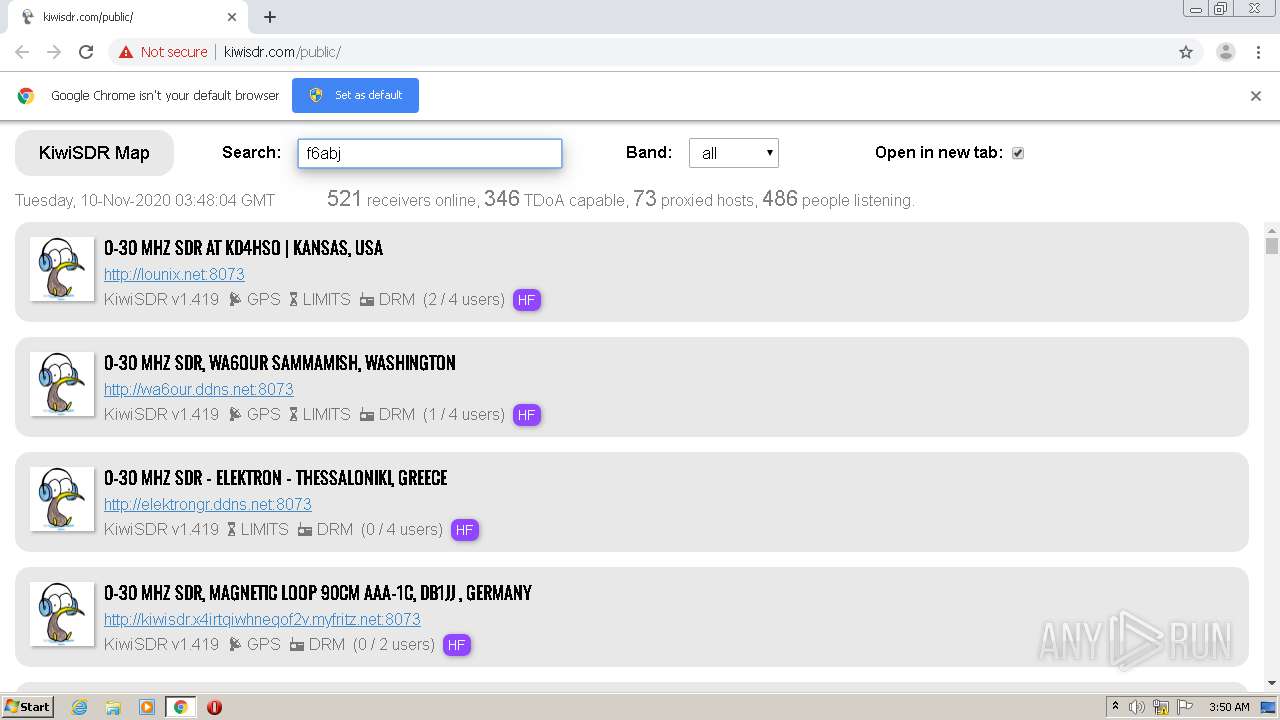
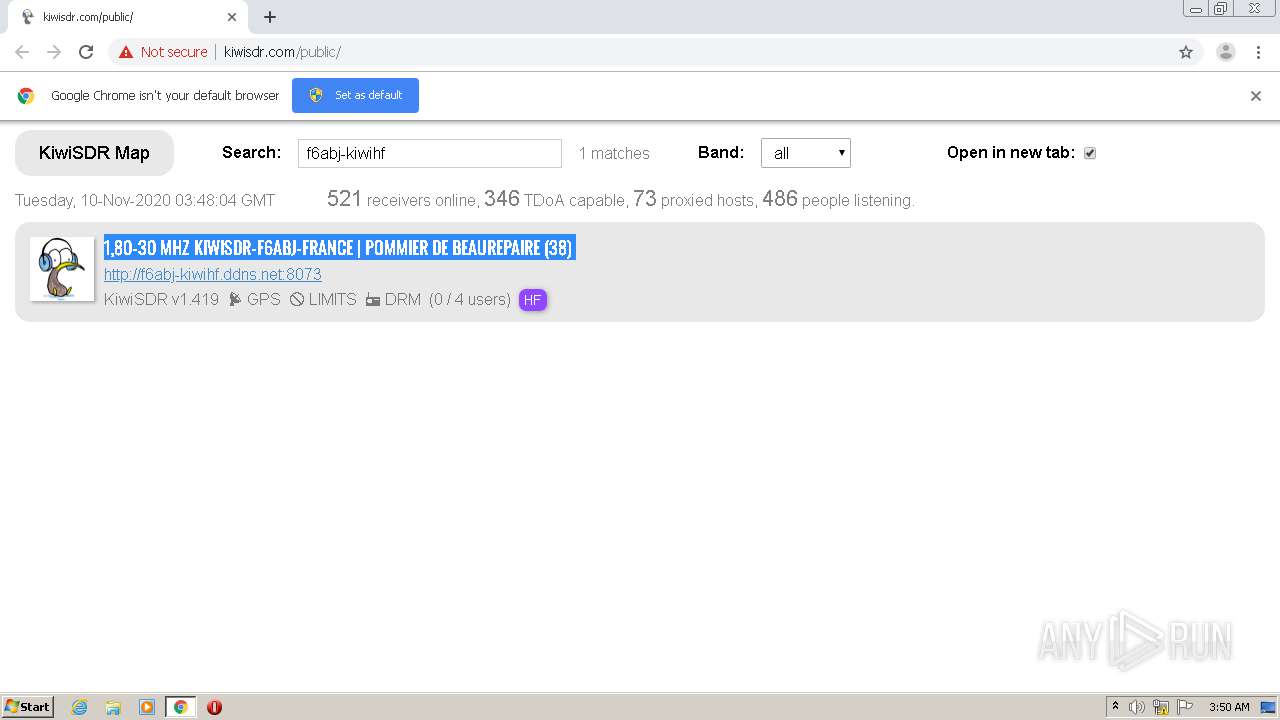
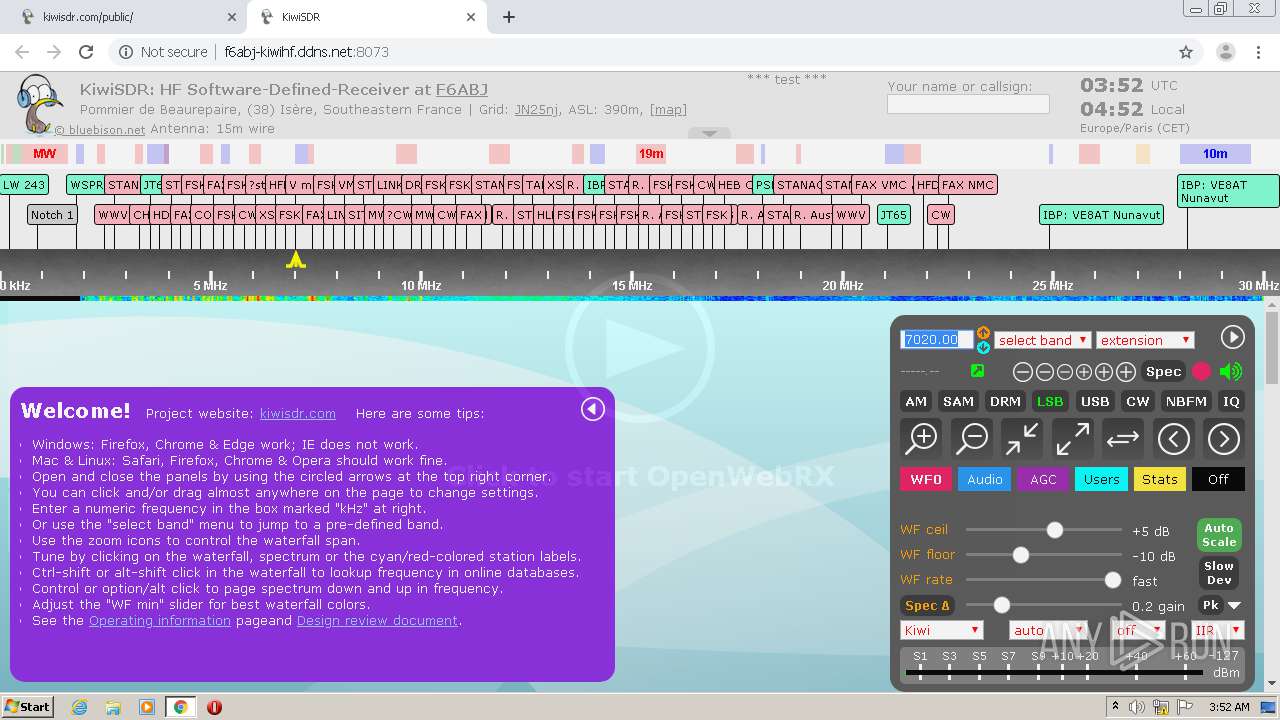
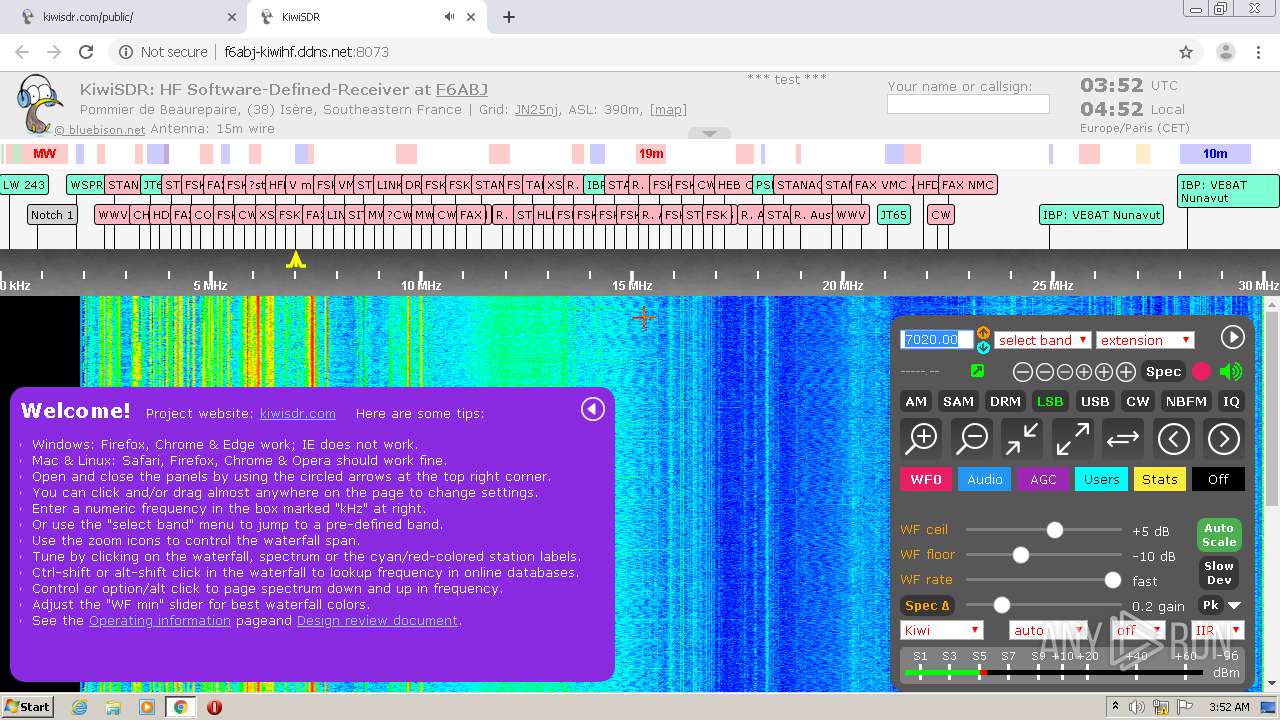
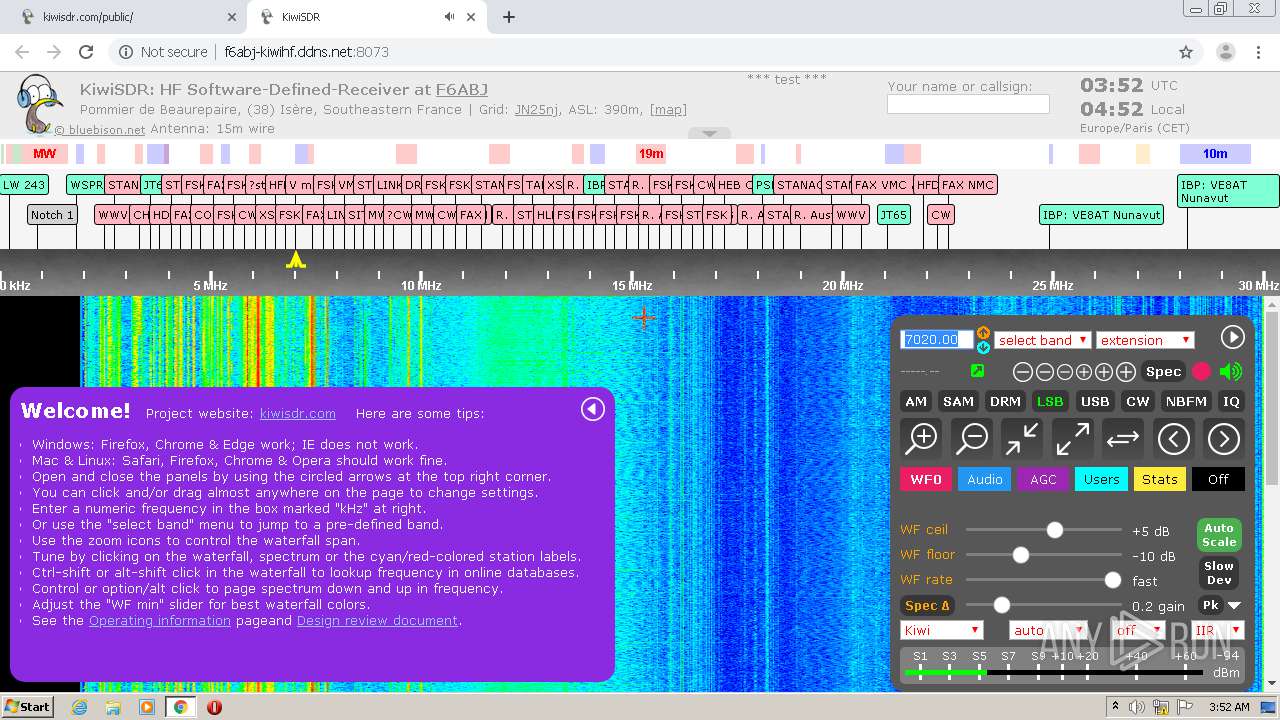
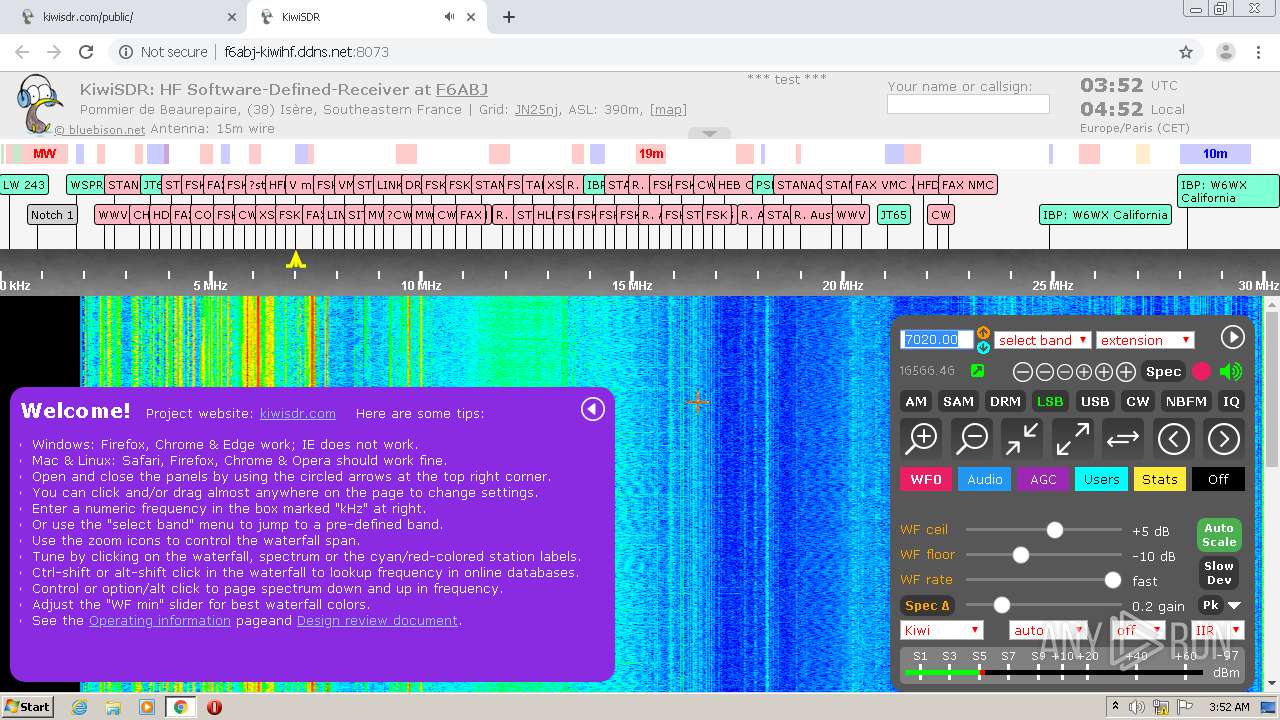
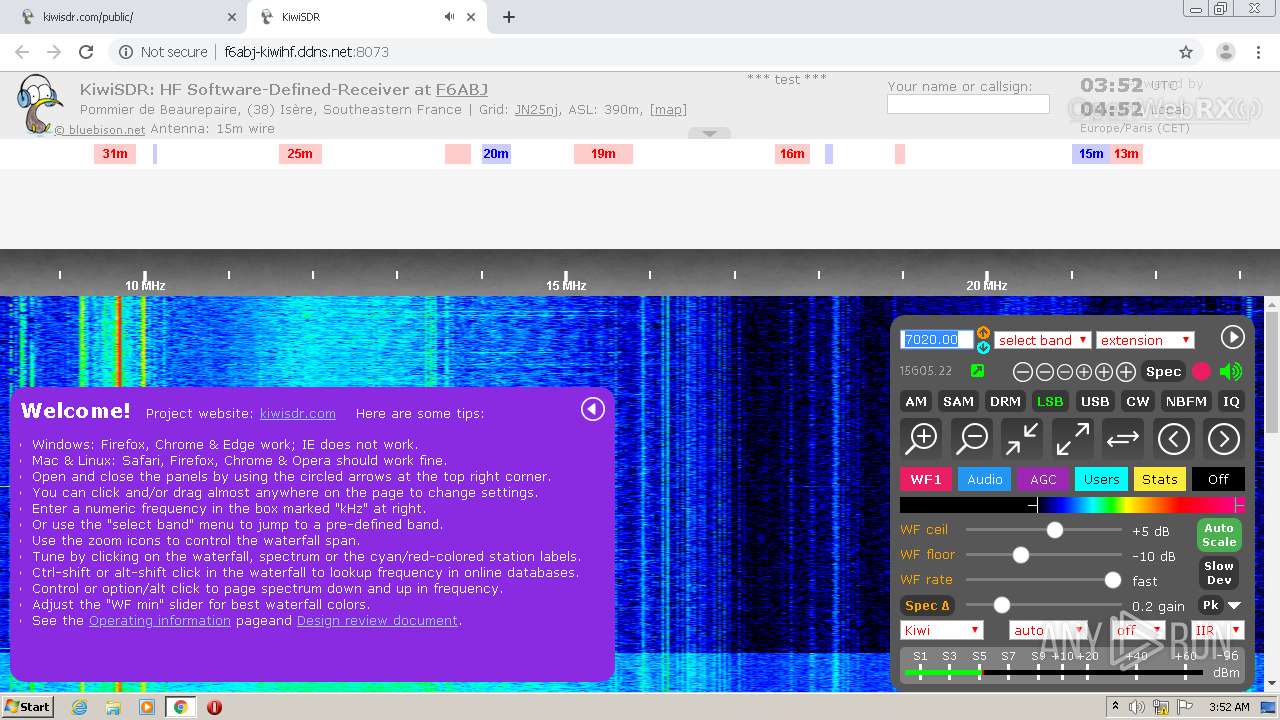
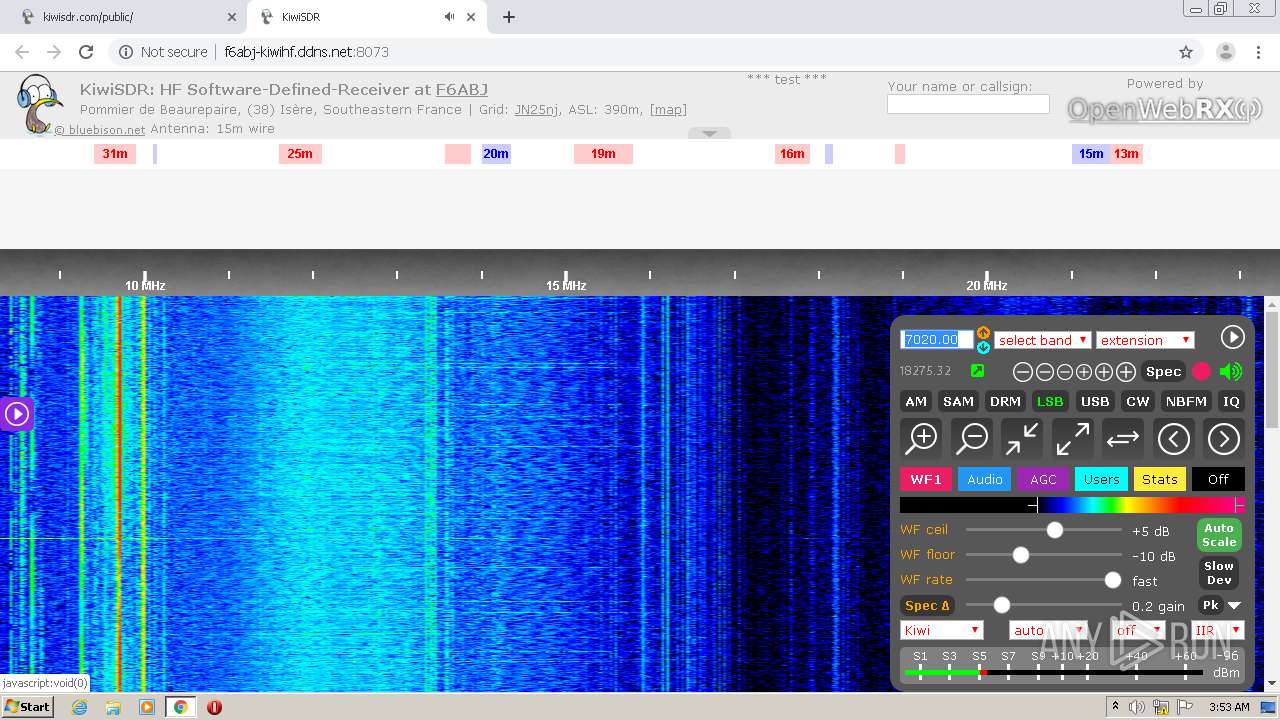
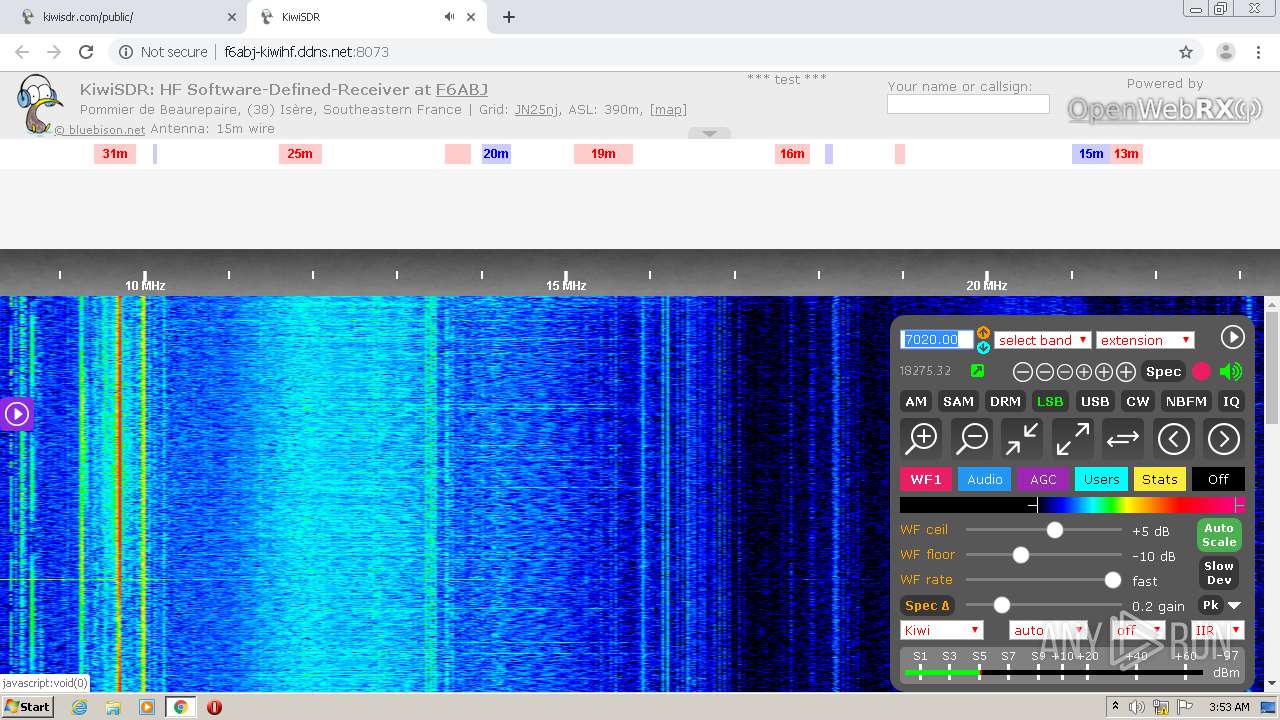
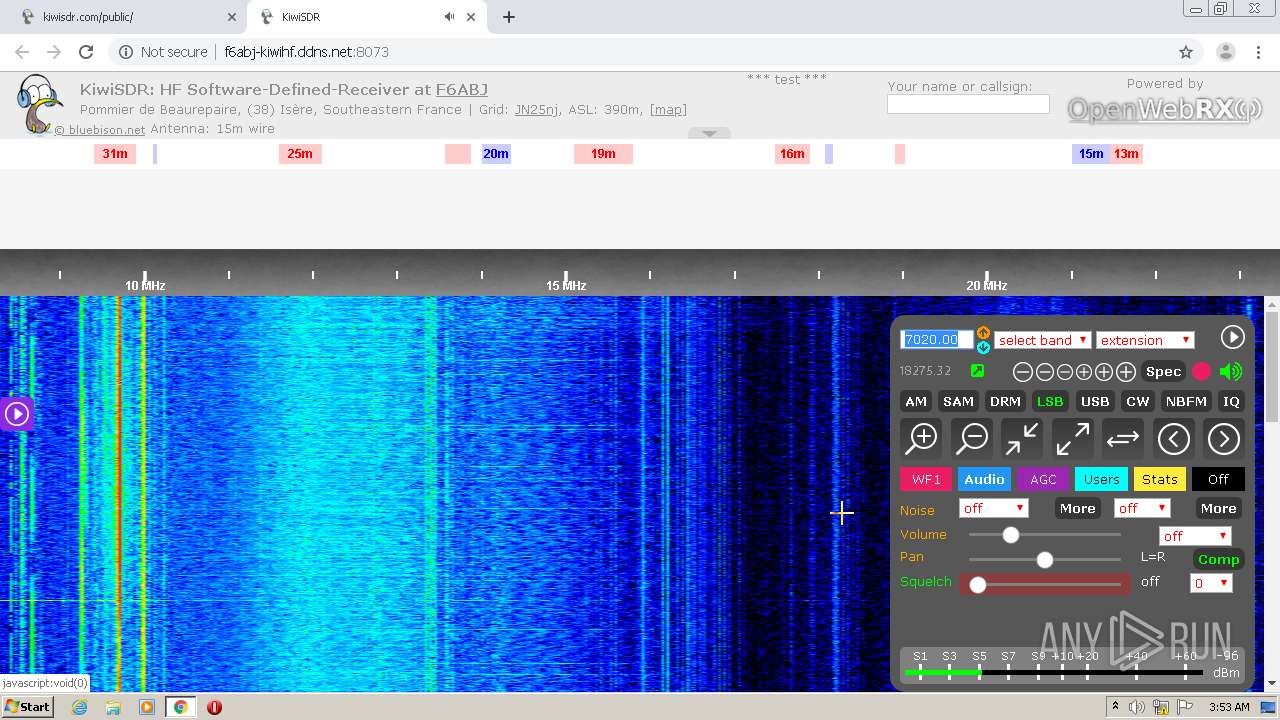
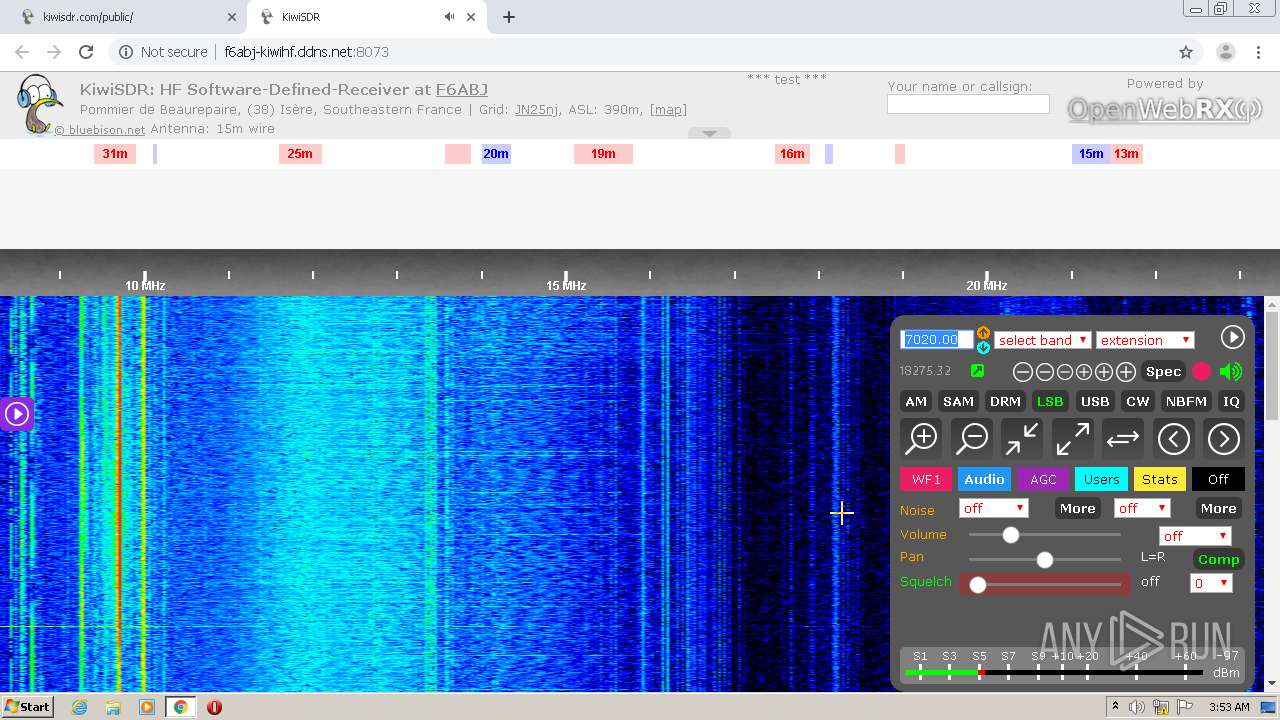
| URL: | http://kiwisdr.com/public/ |
| Full analysis: | https://app.any.run/tasks/1c88dc25-f18b-47d4-8ba7-e8a05b67224e |
| Verdict: | Malicious activity |
| Analysis date: | November 10, 2020, 03:49:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | ECB70C1C56FACD454533A6D811A598E5 |
| SHA1: | FB537FC9DAB25E05F25E5E6FF09F4C9E99A3AC8C |
| SHA256: | E54FD801AAADA70DC503435F25D9FA6C5D568D5C2E67062FF4B5BD32AA5BE972 |
| SSDEEP: | 3:N1KVM/c6HJq:CmU6HJq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2216)
INFO
Reads the hosts file
- chrome.exe (PID: 2216)
- chrome.exe (PID: 184)
Application launched itself
- chrome.exe (PID: 2216)
Reads settings of System Certificates
- chrome.exe (PID: 184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,9650200637404655822,2817768874746894805,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=205174208899254644 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,9650200637404655822,2817768874746894805,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9036239832772131383 --mojo-platform-channel-handle=3808 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,9650200637404655822,2817768874746894805,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5327407845381674886 --mojo-platform-channel-handle=3828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,9650200637404655822,2817768874746894805,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14346709777926223722 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2508 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,9650200637404655822,2817768874746894805,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1849944354143112463 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,9650200637404655822,2817768874746894805,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9677151768606275969 --mojo-platform-channel-handle=3960 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,9650200637404655822,2817768874746894805,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14251703383616631891 --mojo-platform-channel-handle=4112 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,9650200637404655822,2817768874746894805,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9740031912395794677 --mojo-platform-channel-handle=2096 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,9650200637404655822,2817768874746894805,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9618584994338734359 --mojo-platform-channel-handle=3748 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
837
Read events
768
Write events
65
Delete events
4
Modification events
| (PID) Process: | (2216) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2216) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2216) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2216) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2216) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2216-13249453779759500 |
Value: 259 | |||
| (PID) Process: | (2216) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2216) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2216) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2216) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
36
Text files
224
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FAA0DD4-8A8.pma | — | |
MD5:— | SHA256:— | |||
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d42eca59-4e21-40a4-9e95-6af7146bffb0.tmp | — | |
MD5:— | SHA256:— | |||
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF18920a.TMP | text | |
MD5:— | SHA256:— | |||
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF18941d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
36
DNS requests
265
Threats
81
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
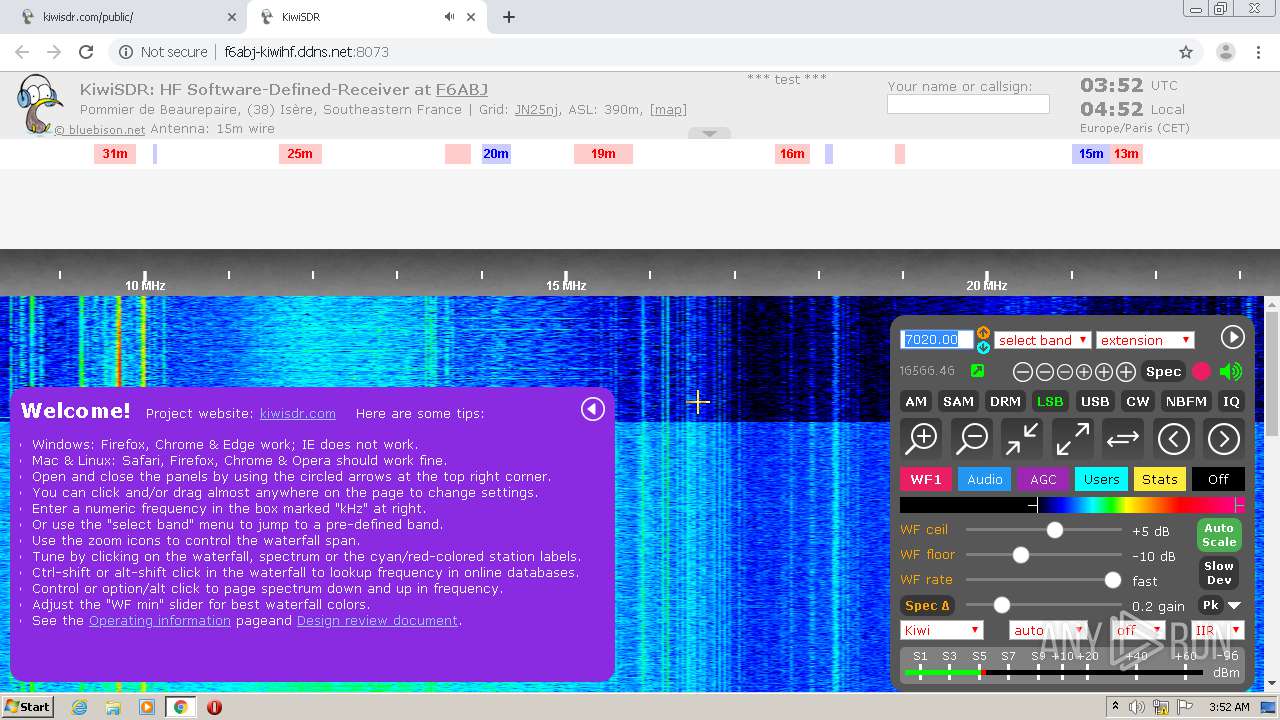
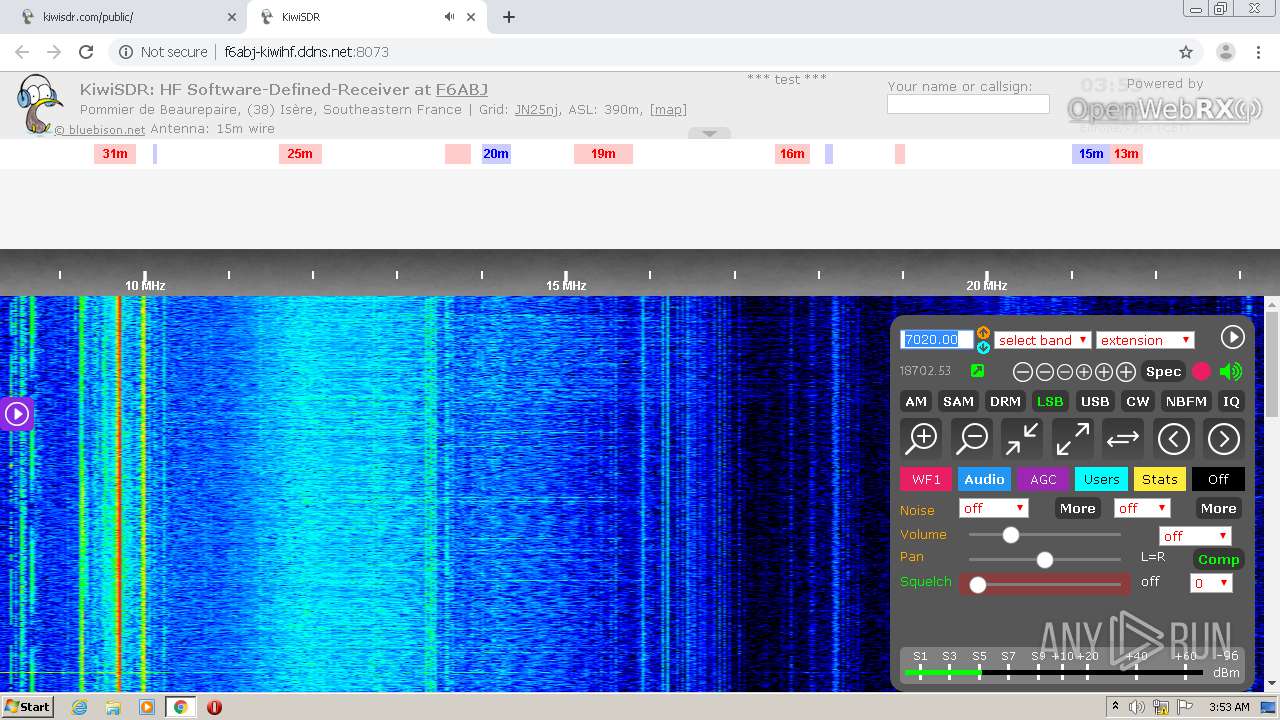
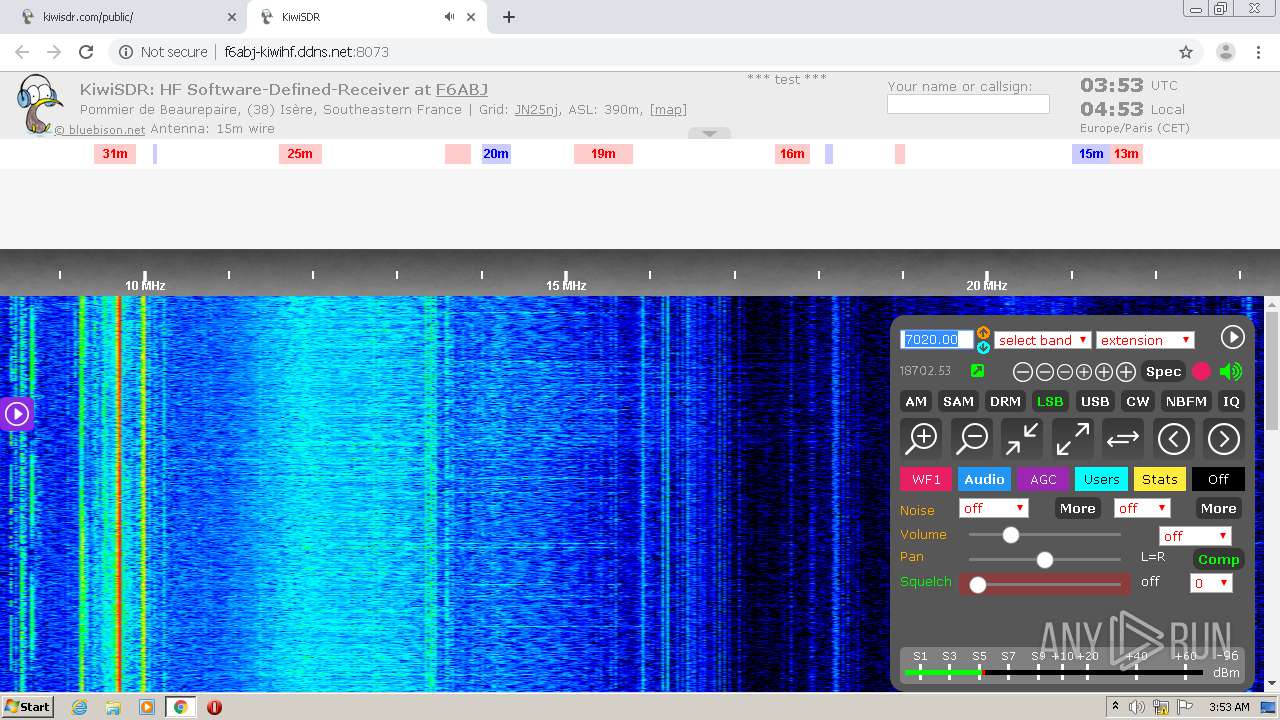
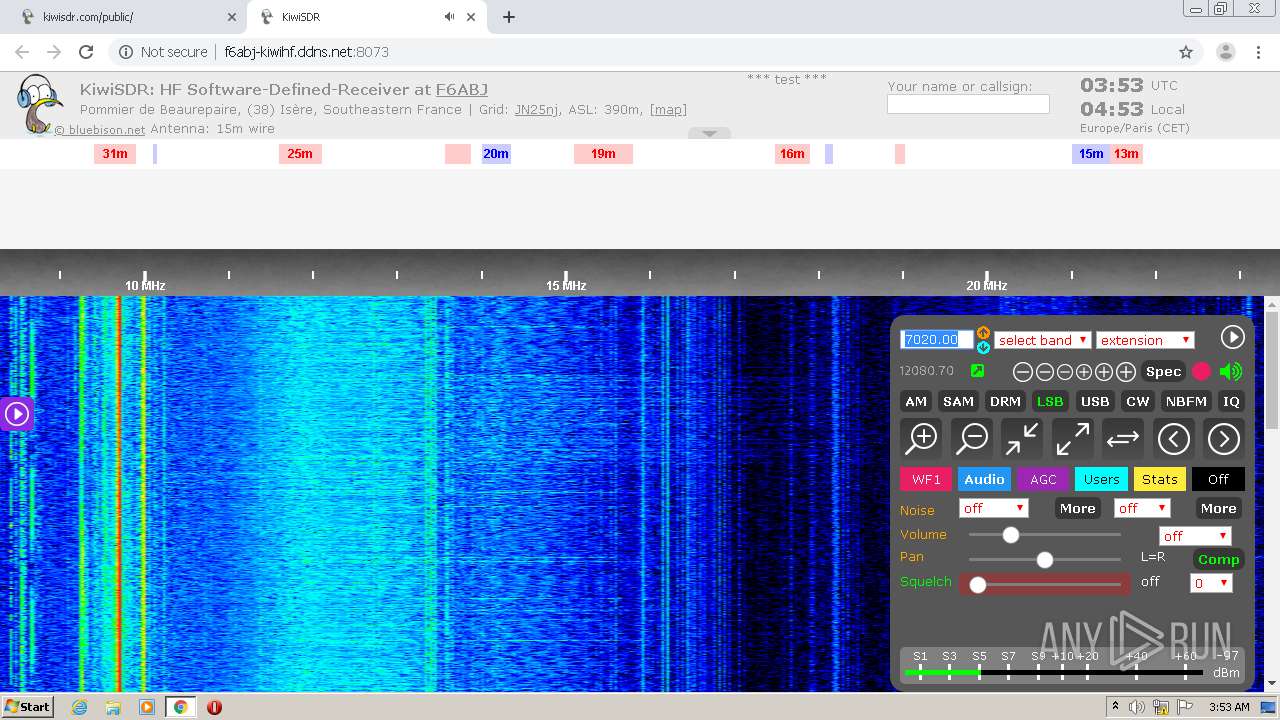
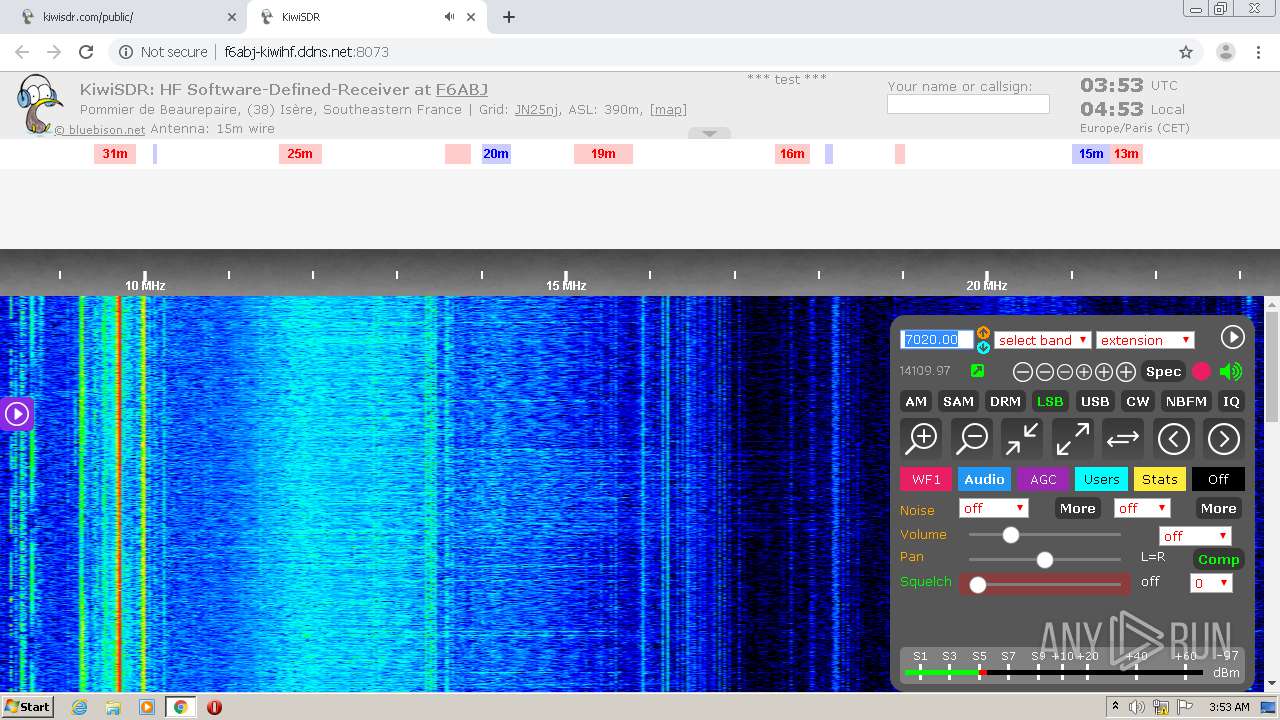
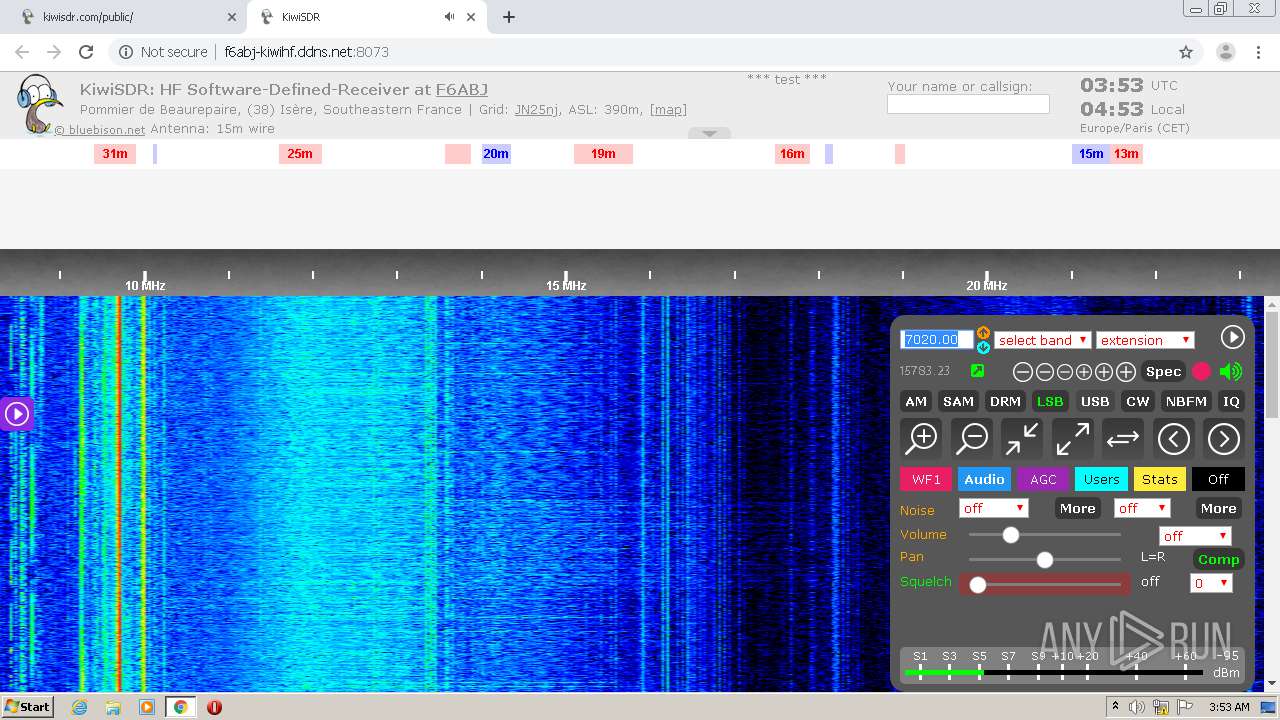
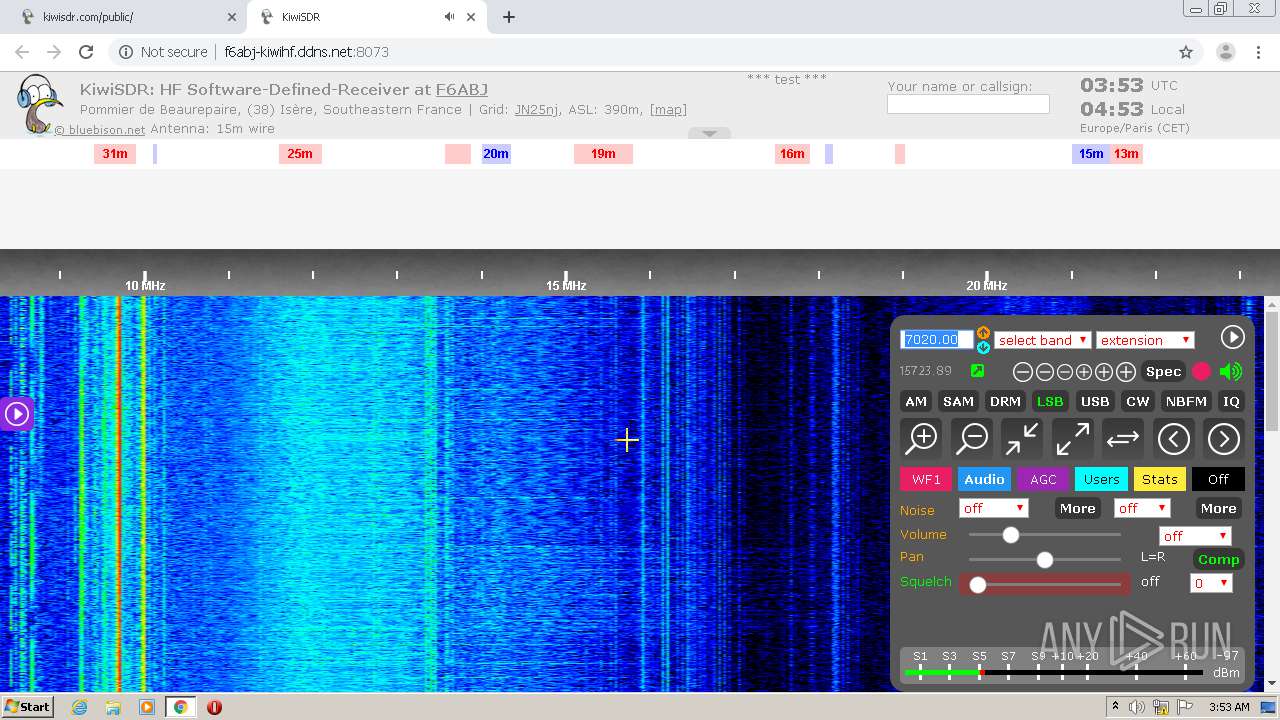
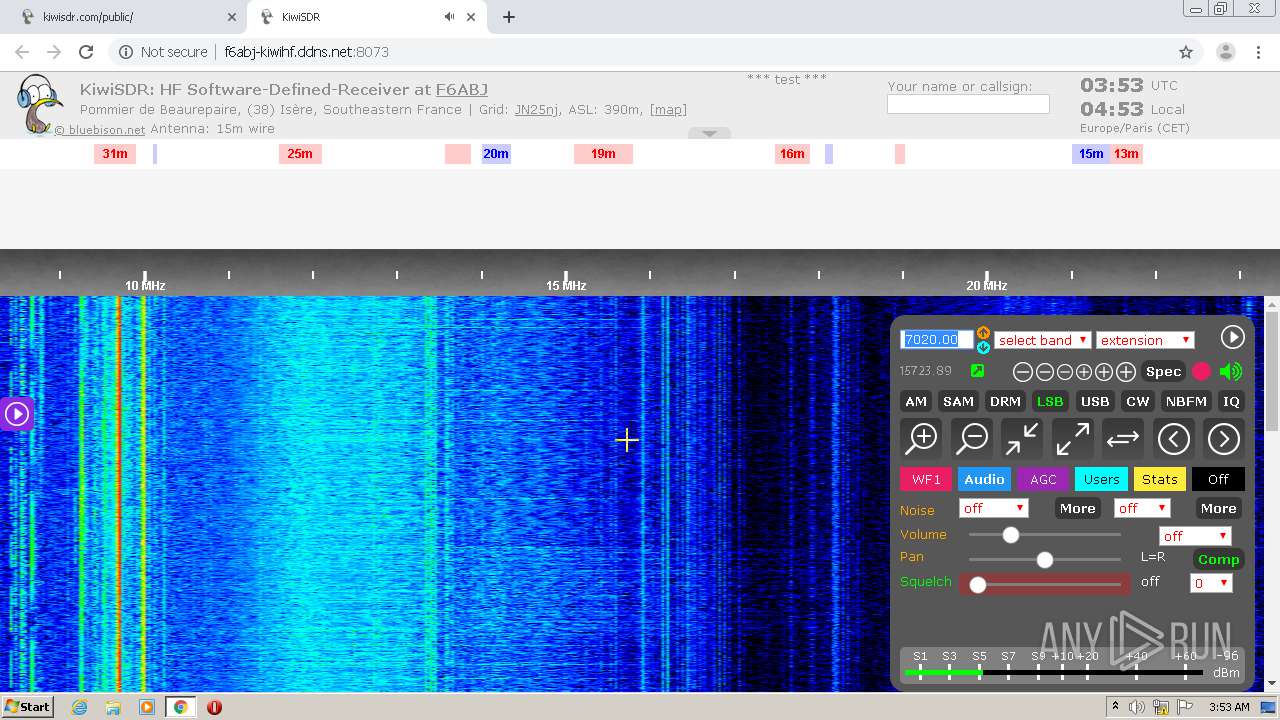
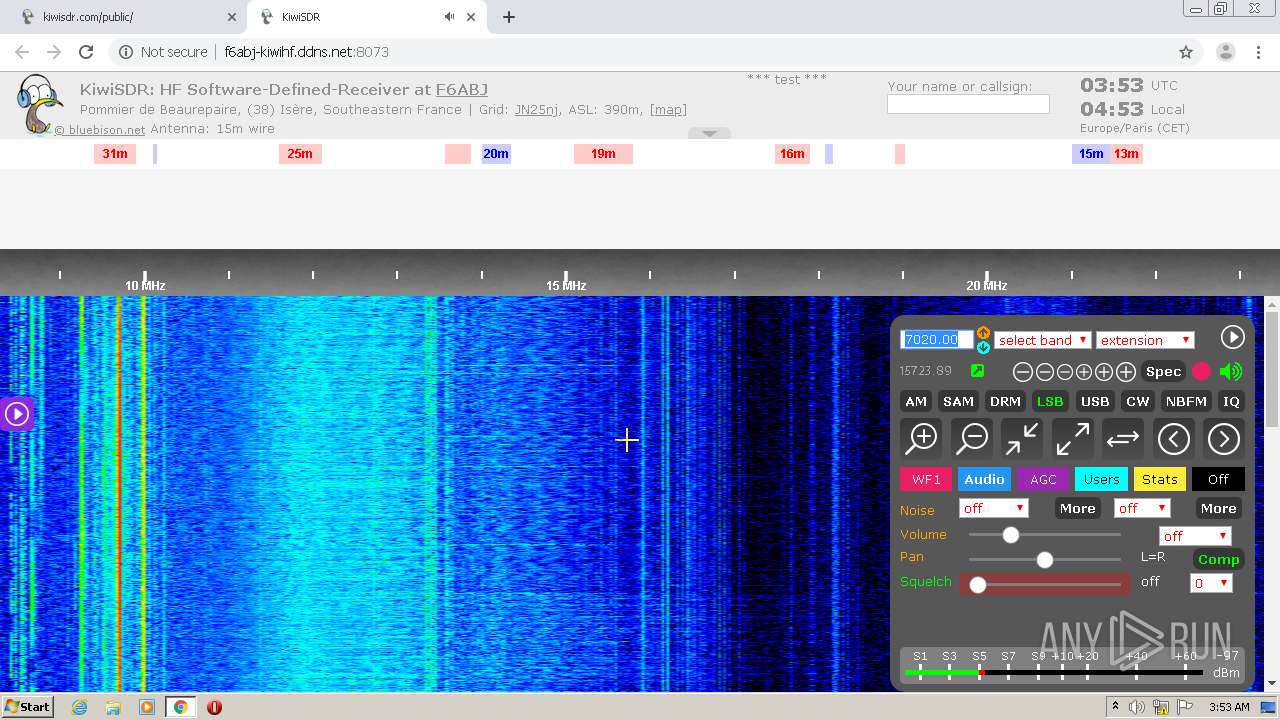
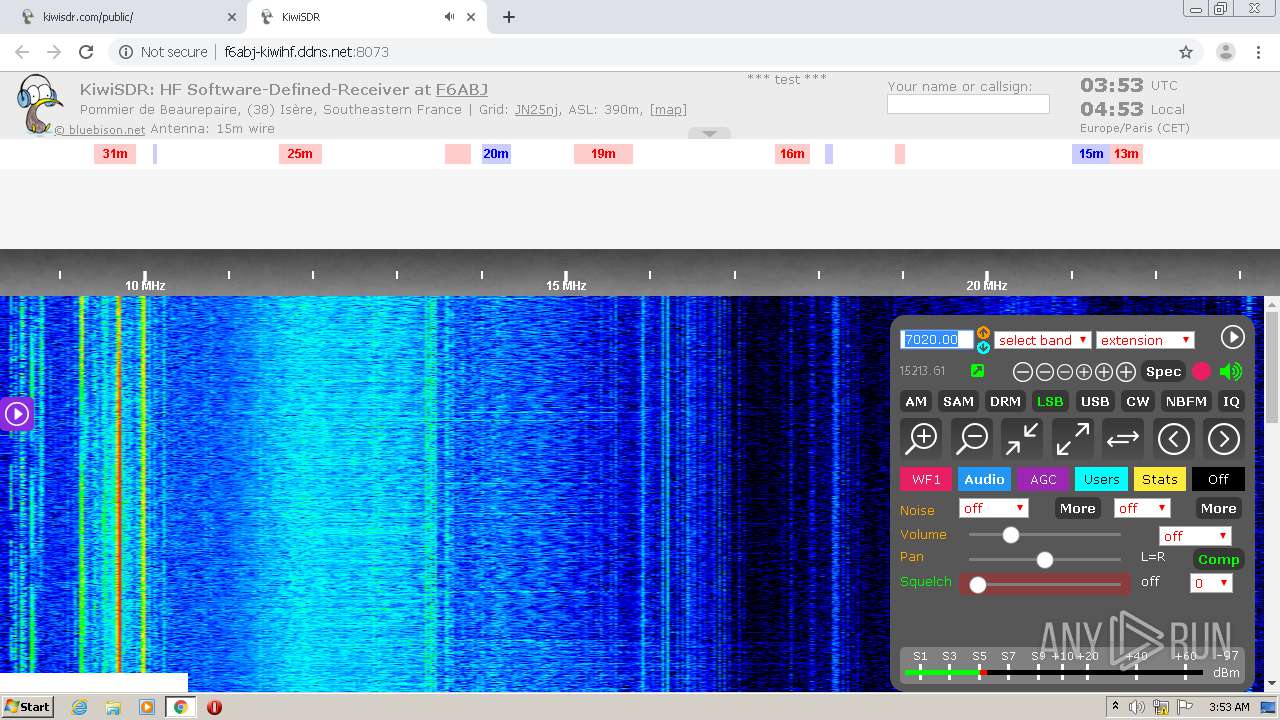
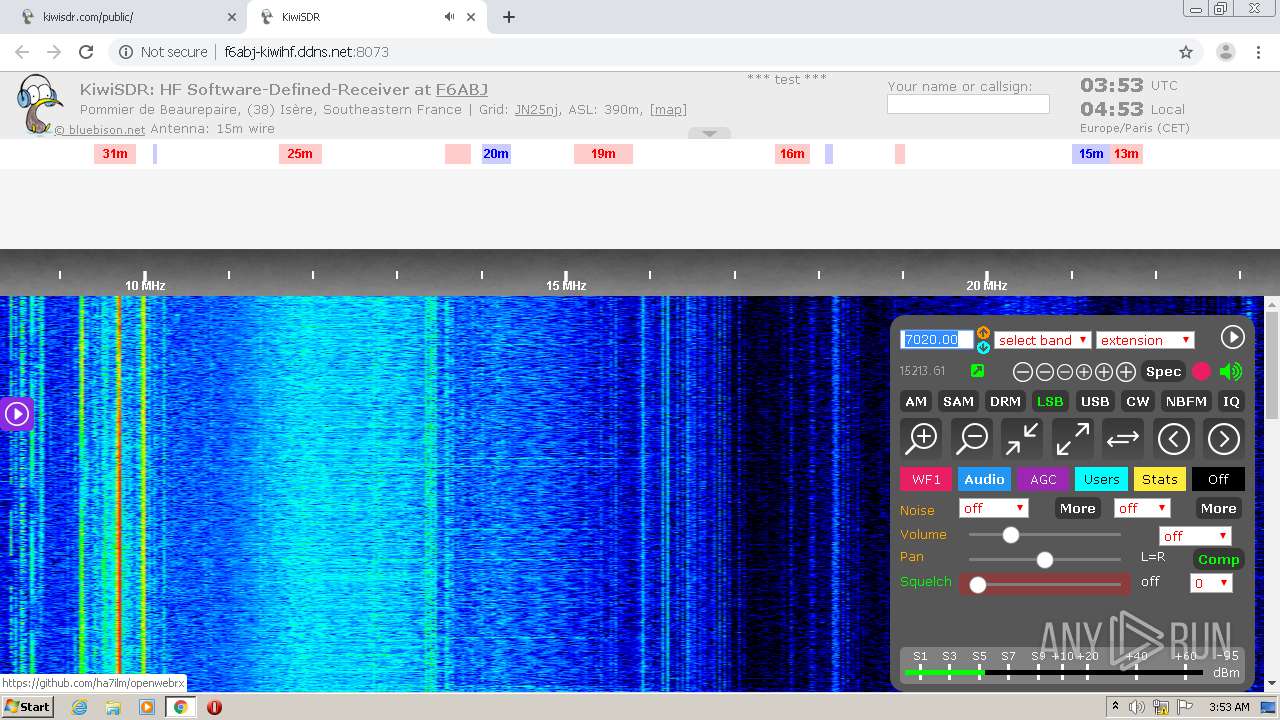
184 | chrome.exe | GET | — | 50.116.2.70:80 | http://kiwisdr.com/favicon.ico | US | — | — | unknown |
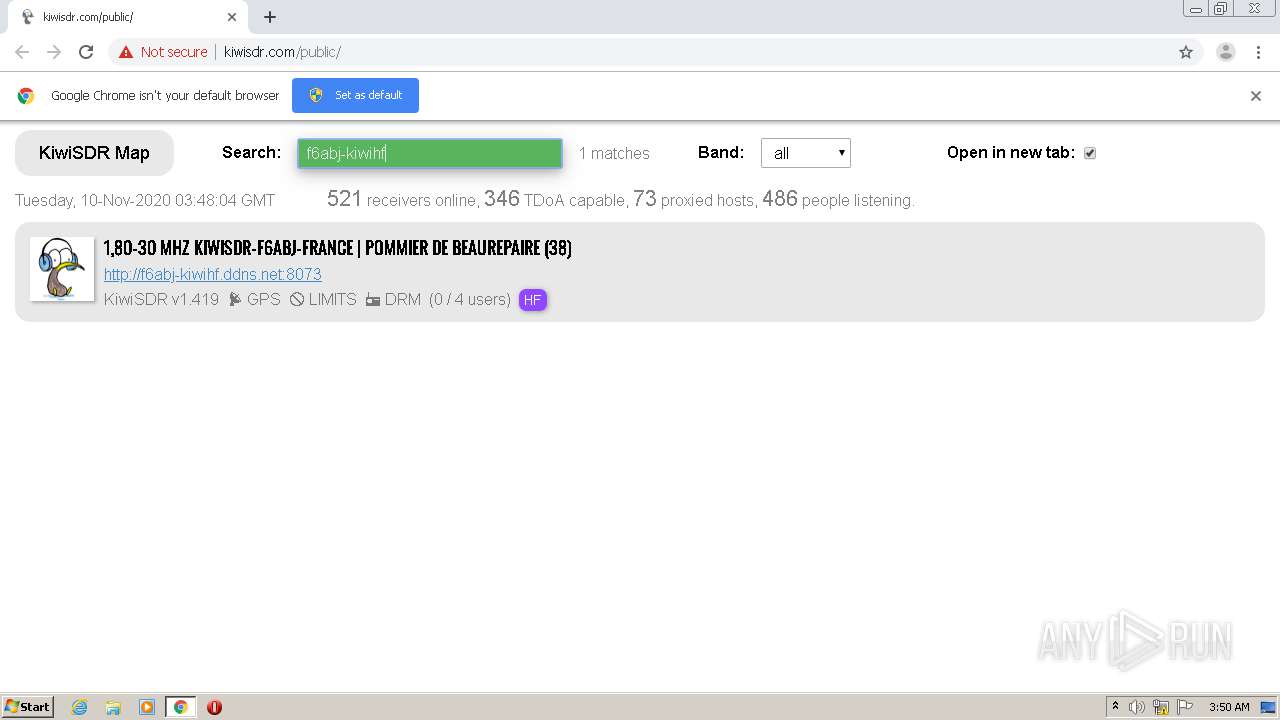
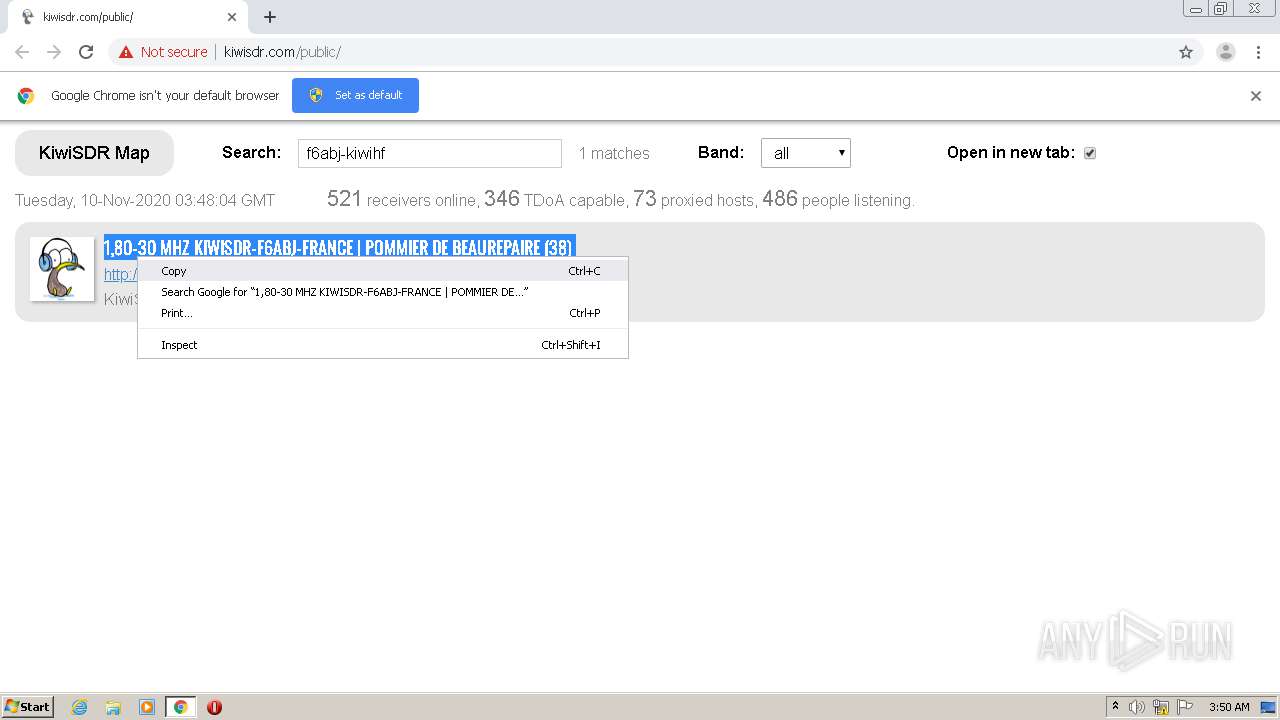
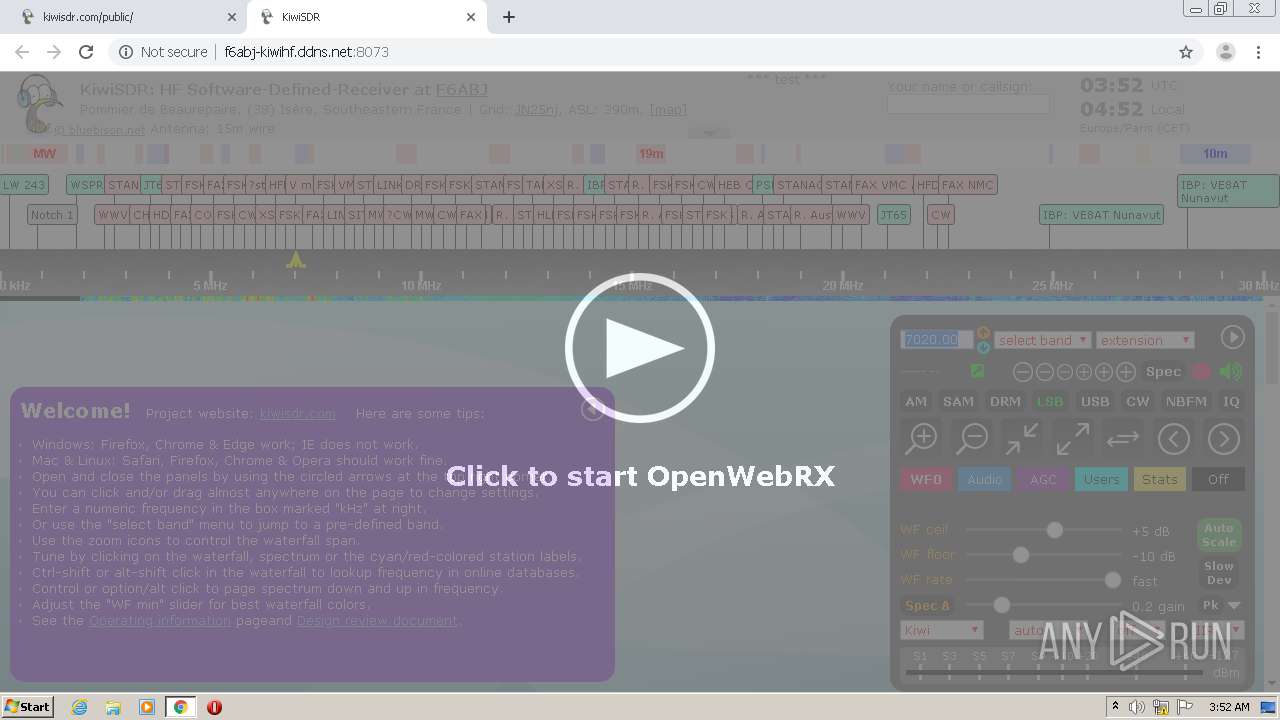
184 | chrome.exe | GET | — | 46.22.85.206:8073 | http://f6abj-kiwihf.ddns.net:8073/ | FR | — | — | malicious |
184 | chrome.exe | GET | — | 46.22.85.206:8073 | http://f6abj-kiwihf.ddns.net:8073/config/config.js | FR | — | — | malicious |
184 | chrome.exe | GET | — | 46.22.85.206:8073 | http://f6abj-kiwihf.ddns.net:8073/kiwisdr.min.css | FR | — | — | malicious |
184 | chrome.exe | GET | — | 46.22.85.206:8073 | http://f6abj-kiwihf.ddns.net:8073/kiwi.config/photo.upload | FR | — | — | malicious |
184 | chrome.exe | GET | — | 46.22.85.206:8073 | http://f6abj-kiwihf.ddns.net:8073/kiwisdr.min.js | FR | — | — | malicious |
184 | chrome.exe | GET | — | 46.22.85.206:8073 | http://f6abj-kiwihf.ddns.net:8073/gfx/kiwi-with-headphones.51x67.png | FR | — | — | malicious |
184 | chrome.exe | GET | — | 46.22.85.206:8073 | http://f6abj-kiwihf.ddns.net:8073/gfx/openwebrx-bottom-arrow-hide.png | FR | — | — | malicious |
184 | chrome.exe | GET | — | 46.22.85.206:8073 | http://f6abj-kiwihf.ddns.net:8073/gfx/openwebrx-bottom-arrow-show.png | FR | — | — | malicious |
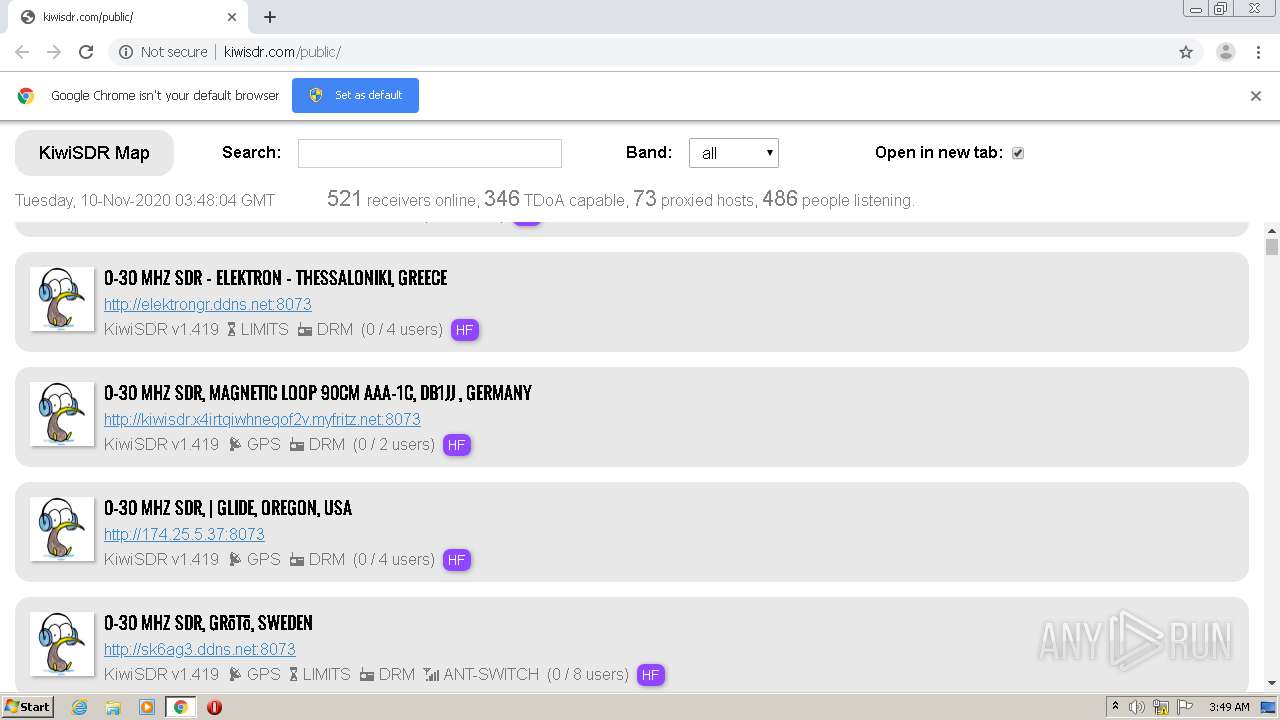
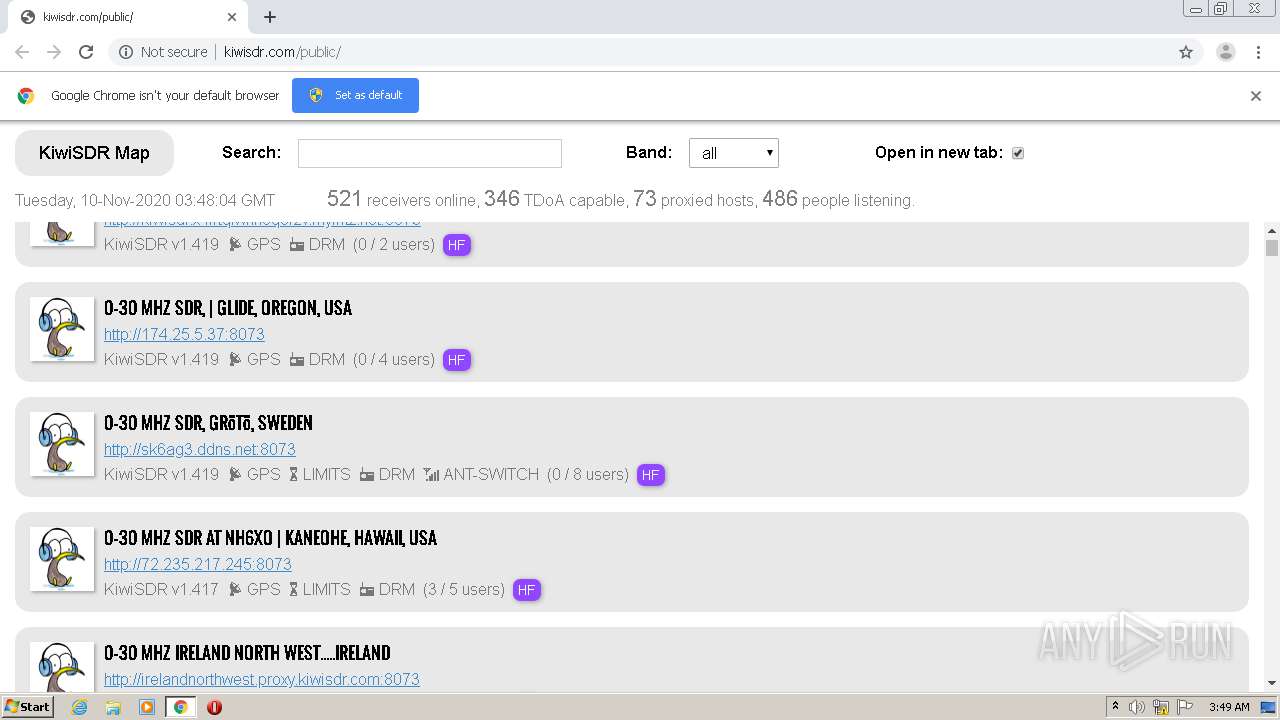
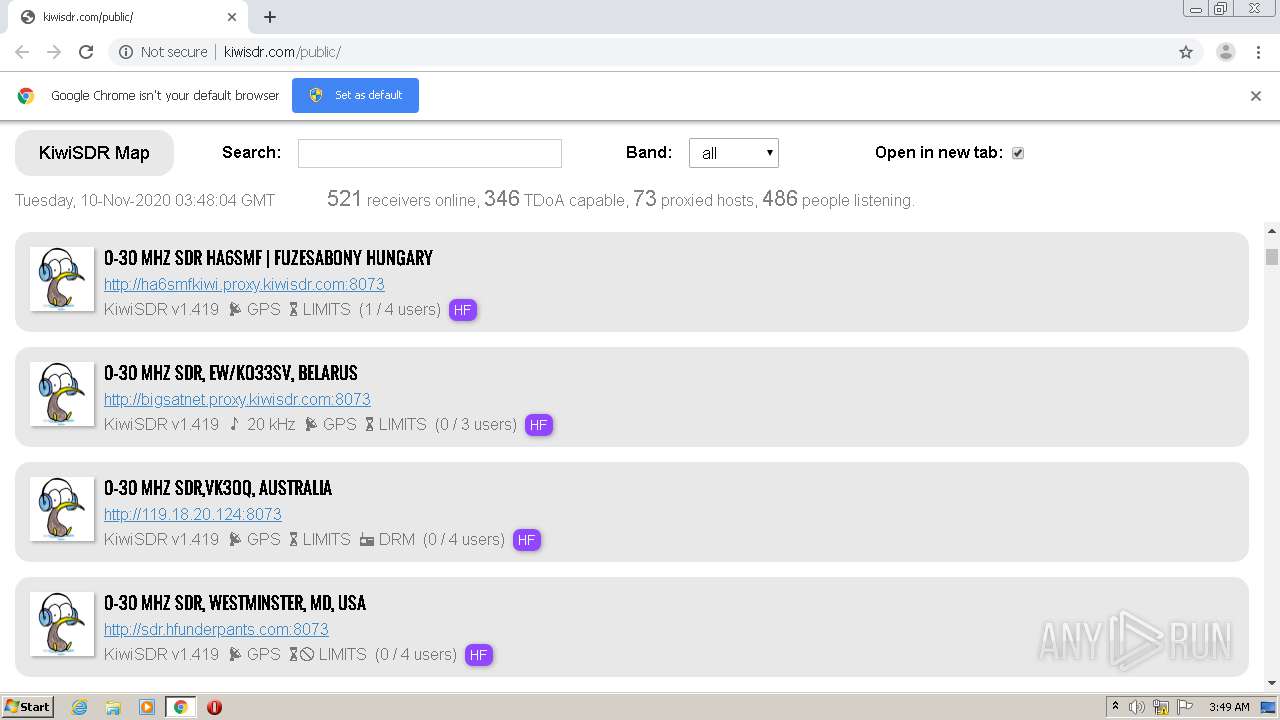
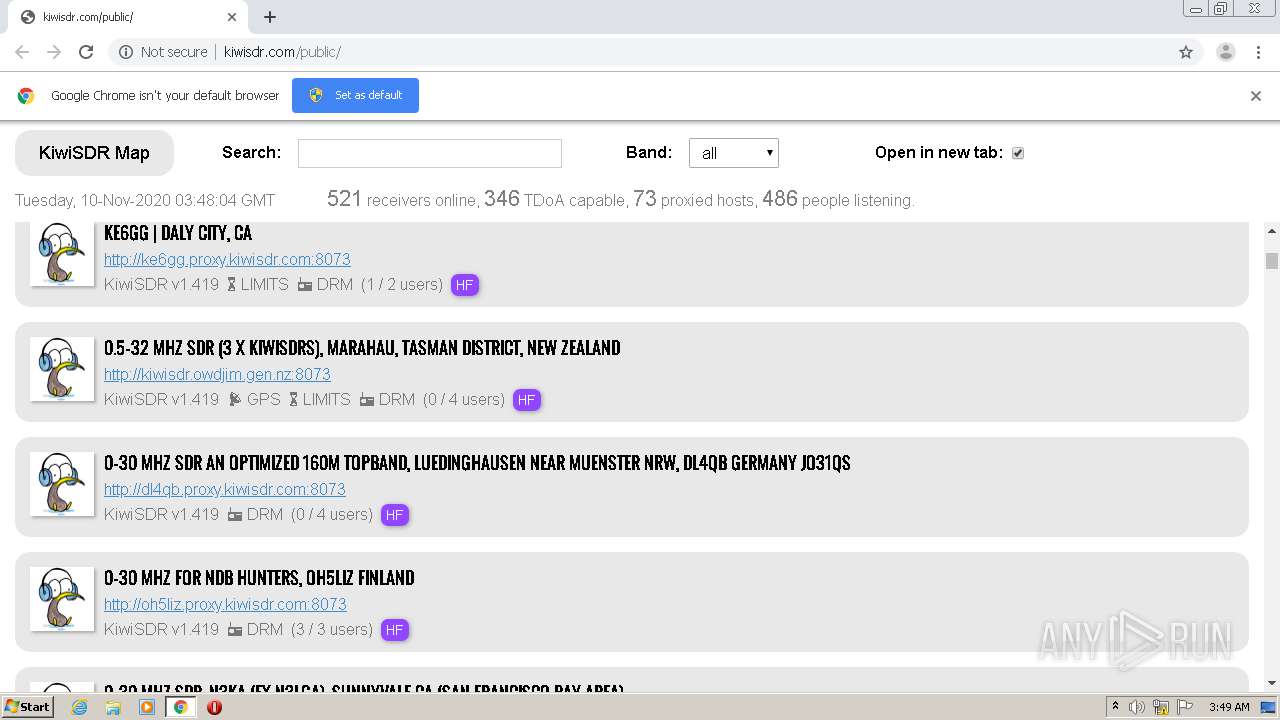
184 | chrome.exe | GET | 200 | 50.116.2.70:80 | http://kiwisdr.com/public/ | US | htm | 79.1 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
184 | chrome.exe | 216.58.198.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 216.58.204.100:443 | www.google.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 142.250.74.238:443 | — | Google Inc. | US | whitelisted |
184 | chrome.exe | 216.58.213.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 216.58.213.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 216.58.214.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.67.70.233:443 | get.geojs.io | — | US | suspicious |
— | — | 46.22.85.206:8073 | f6abj-kiwihf.ddns.net | sas alsatis | FR | malicious |
184 | chrome.exe | 172.67.69.226:443 | ipapi.co | — | US | malicious |
184 | chrome.exe | 216.58.209.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
kiwisdr.com |
| unknown |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
alfaromeo170.myqnapcloud.com |
| unknown |
bigsatnet.proxy.kiwisdr.com |
| unknown |
birdsnest.zapto.org |
| suspicious |
9k2ra-2.proxy.kiwisdr.com |
| unknown |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.zapto .org |
1044 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1044 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.hopto .org |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .world TLD |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
1044 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1044 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1044 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1044 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1044 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |