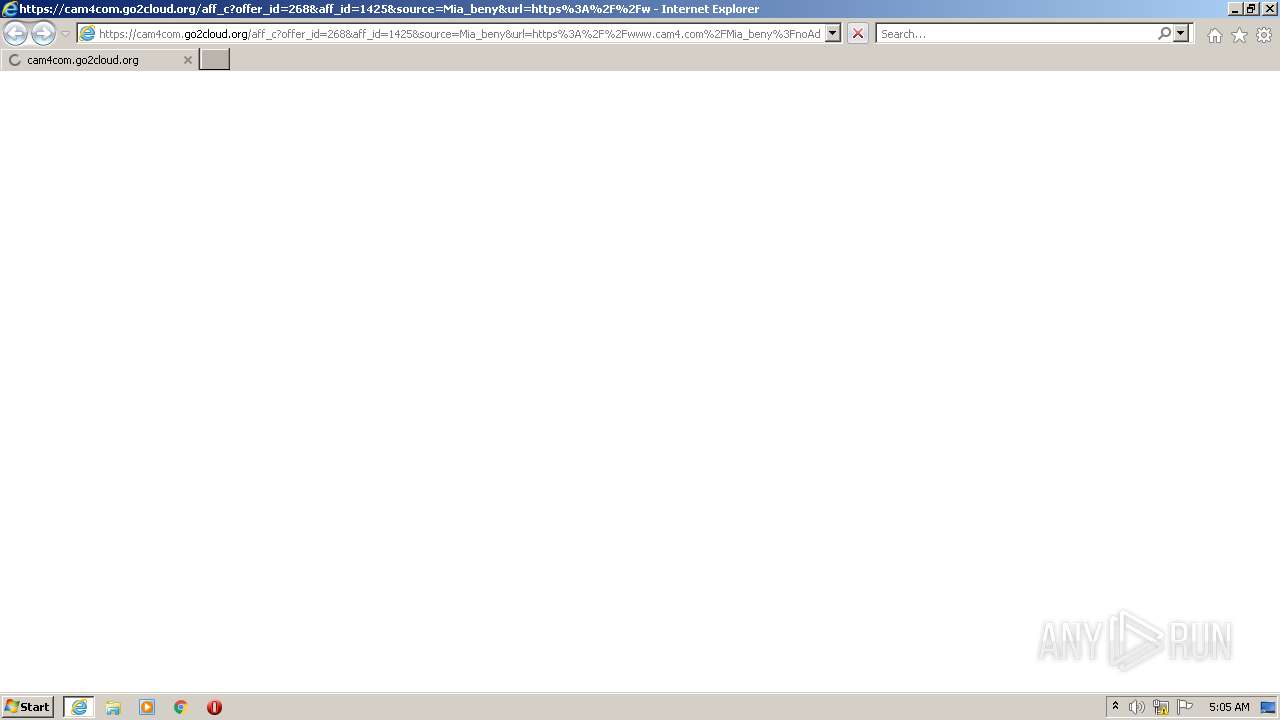
| URL: | https://cam4com.go2cloud.org/aff_c?offer_id=268&aff_id=1425&source=Mia_beny&url=https%3A%2F%2Fwww.cam4.com%2FMia_beny%3FnoAds%3Dtrue%26act%3DhasOffers_%7Btransaction_id%7D_668_670&aff_sub=NTV_FULL_US |
| Full analysis: | https://app.any.run/tasks/1acac908-b155-4049-bc45-fb035ac9658f |
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2022, 05:05:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 016562A43C86BC35BE2513A26FDC6A5E |
| SHA1: | 4915922242601DB52A8DF57CCDC15CFA6E160718 |
| SHA256: | E549B943493557E9D952C04ED52C79BF4441966A8FCDDBD82B907E893739551E |
| SSDEEP: | 6:22gTcfMpeQXKR3zX0KGj6LKkFsGhmpGylSsADGmxI:2m0pPoz0hcKfGqTIsAFC |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3432)
INFO
Checks supported languages
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3432)
Reads settings of System Certificates
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3432)
Reads internet explorer settings
- iexplore.exe (PID: 3432)
Checks Windows Trust Settings
- iexplore.exe (PID: 3432)
- iexplore.exe (PID: 3148)
Reads the computer name
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3432)
Changes internet zones settings
- iexplore.exe (PID: 3148)
Application launched itself
- iexplore.exe (PID: 3148)
Creates files in the user directory
- iexplore.exe (PID: 3432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3148 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://cam4com.go2cloud.org/aff_c?offer_id=268&aff_id=1425&source=Mia_beny&url=https%3A%2F%2Fwww.cam4.com%2FMia_beny%3FnoAds%3Dtrue%26act%3DhasOffers_%7Btransaction_id%7D_668_670&aff_sub=NTV_FULL_US" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3432 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3148 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
15 616
Read events
15 443
Write events
173
Delete events
0
Modification events
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30936507 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30936507 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
29
Text files
75
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:D1424E7A86CFDD062024D3F319708E7D | SHA256:B7D1AB800C639EC1928D369C47B5B40A19BD4FEAE5158CD1C81CE084208FFF34 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:FFF10C76365C5BF6672BCDE9386D8BED | SHA256:B0A2ED00AE8876ED593DCCE3F57F48422FFFA7EAB639E3416C2994A438355DF9 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:E1EAE72E3715286294FAE5B772B54D91 | SHA256:CDF348AD50D67BDDAA3E15E75B24A792DBCF8A8C72519F12C357A96FAF381C03 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:91B26A33F99C14EC65DBCC5910778A41 | SHA256:31B0E2B5A7EDA8B87FCBCAE5071B57C165D768C023407549F2234B82C4A96CF6 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:777768EC26884C3B6E99EFA7589D1427 | SHA256:F97DB049CAEC500B04C47B78E9D6184B27AAC410846FCD36879B4BD87BED4D65 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\FC5A820A001B41D68902E051F36A5282_9132D4808C47FC0C686C64A9BAB02E2C | der | |
MD5:212069F064AE0149940101F2F6B84C06 | SHA256:F3C2EC758D9DDEC26E8F8FD5EBA5E6157021387B6C4BD75DE003BC459EE8449C | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:74B45AEAF96A7353E9E2BB6FD81F4B18 | SHA256:6FD468C5706DA22E4E6062E4CB39951838DC3767CA4BD8B3E16AD2CF24266A33 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\MV1QWARZ.txt | text | |
MD5:FAA0F47A87AE4D6638778C003324621C | SHA256:D117640088225366638003FFF303DCCDB51A4B2ACC8A627257C3A98E38239BDF | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | binary | |
MD5:47E26B91731B6F2BE1F368CC192720F5 | SHA256:640FBE57B45F416ABAB9F3DED2F2C347C7C9E76AA65E601A1E6329A6DC866703 | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | der | |
MD5:B70BCF4BDAEFA239E037C0790D6B4A19 | SHA256:B510E637BA520CC249E461134BEF7EE3E1063B4994C625DB258658E07132F62F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
103
DNS requests
41
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | iexplore.exe | GET | 200 | 23.55.161.162:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?aca855439deafb4e | US | compressed | 4.70 Kb | whitelisted |
3148 | iexplore.exe | GET | 200 | 23.55.161.162:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d85cd64283bf8617 | US | compressed | 4.70 Kb | whitelisted |
3432 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | US | der | 1.41 Kb | whitelisted |
3432 | iexplore.exe | GET | 200 | 18.66.92.207:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3432 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsgccr3dvtlsca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQoKOHJRQbCE%2B3DXqwFiztBxLYdhwQUDZjAc3%2Brvb3ZR0tJrQpKDKw%2Bx3wCDBoDNOXSC%2BXm%2FViWOA%3D%3D | US | der | 1.39 Kb | whitelisted |
3148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
3432 | iexplore.exe | GET | 200 | 108.156.253.168:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEARSIGnUY9UQN2wKlzoedu8%3D | US | der | 471 b | whitelisted |
3432 | iexplore.exe | GET | 200 | 18.66.242.45:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3432 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3432 | iexplore.exe | GET | 200 | 18.66.242.155:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3432 | iexplore.exe | 142.250.186.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3432 | iexplore.exe | 18.202.12.61:443 | cam4com.go2cloud.org | — | US | shared |
3148 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3148 | iexplore.exe | 23.55.161.162:80 | ctldl.windowsupdate.com | Akamai International B.V. | US | unknown |
3148 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3432 | iexplore.exe | 52.210.2.133:443 | cam4com.go2cloud.org | Amazon.com, Inc. | IE | shared |
3432 | iexplore.exe | 18.66.92.207:80 | o.ss2.us | Massachusetts Institute of Technology | US | unknown |
3432 | iexplore.exe | 18.66.242.45:80 | ocsp.rootg2.amazontrust.com | Massachusetts Institute of Technology | US | whitelisted |
3432 | iexplore.exe | 108.156.253.168:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
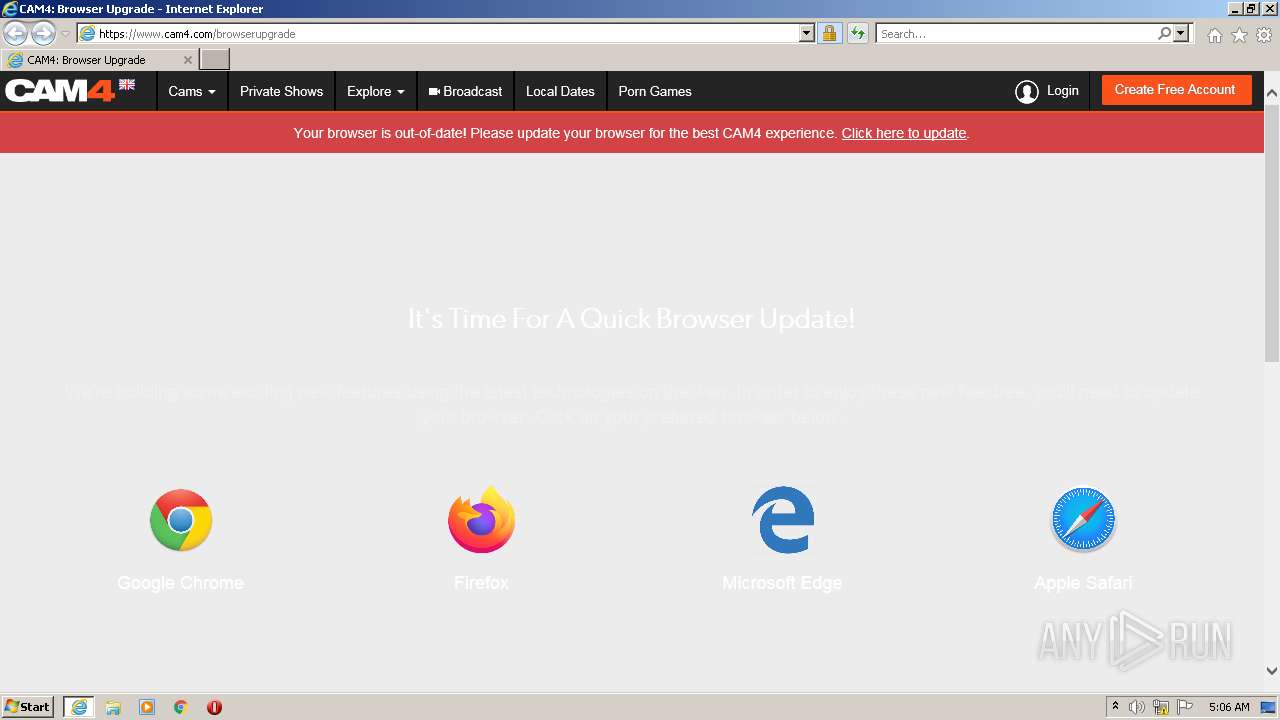
3432 | iexplore.exe | 217.22.17.249:443 | www.cam4.com | Mojohost B.v. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cam4com.go2cloud.org |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3432 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |