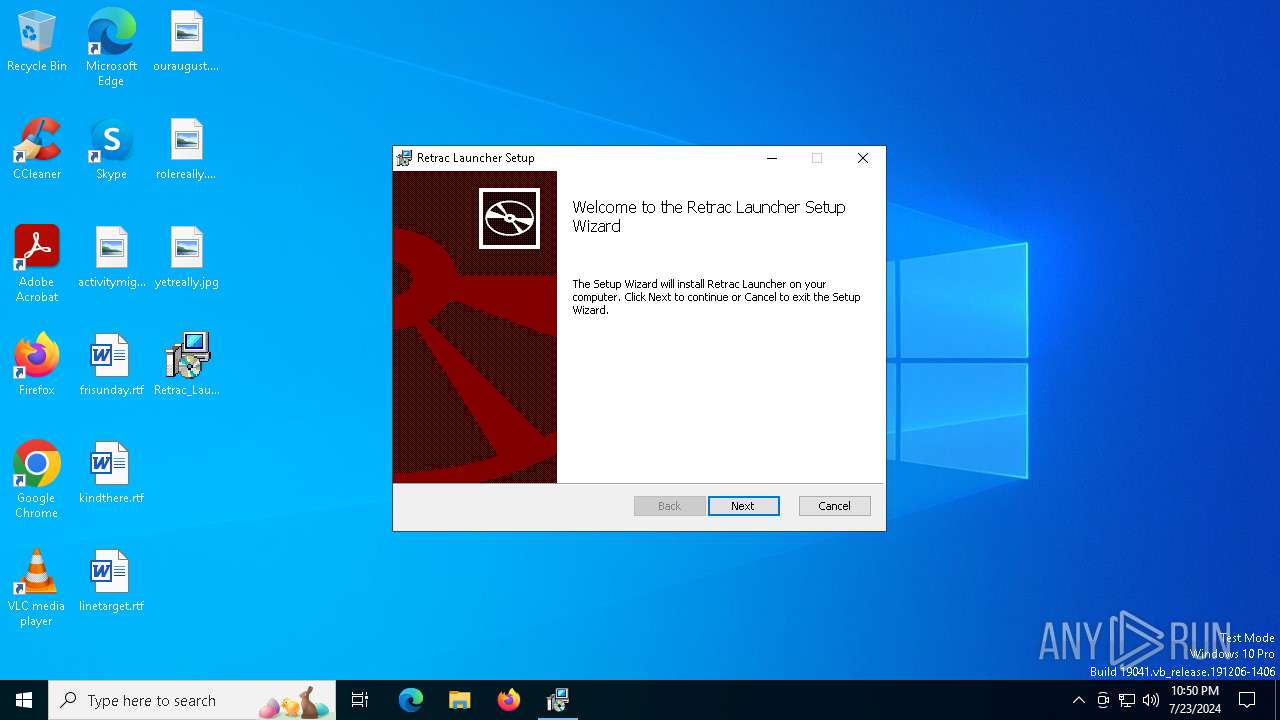
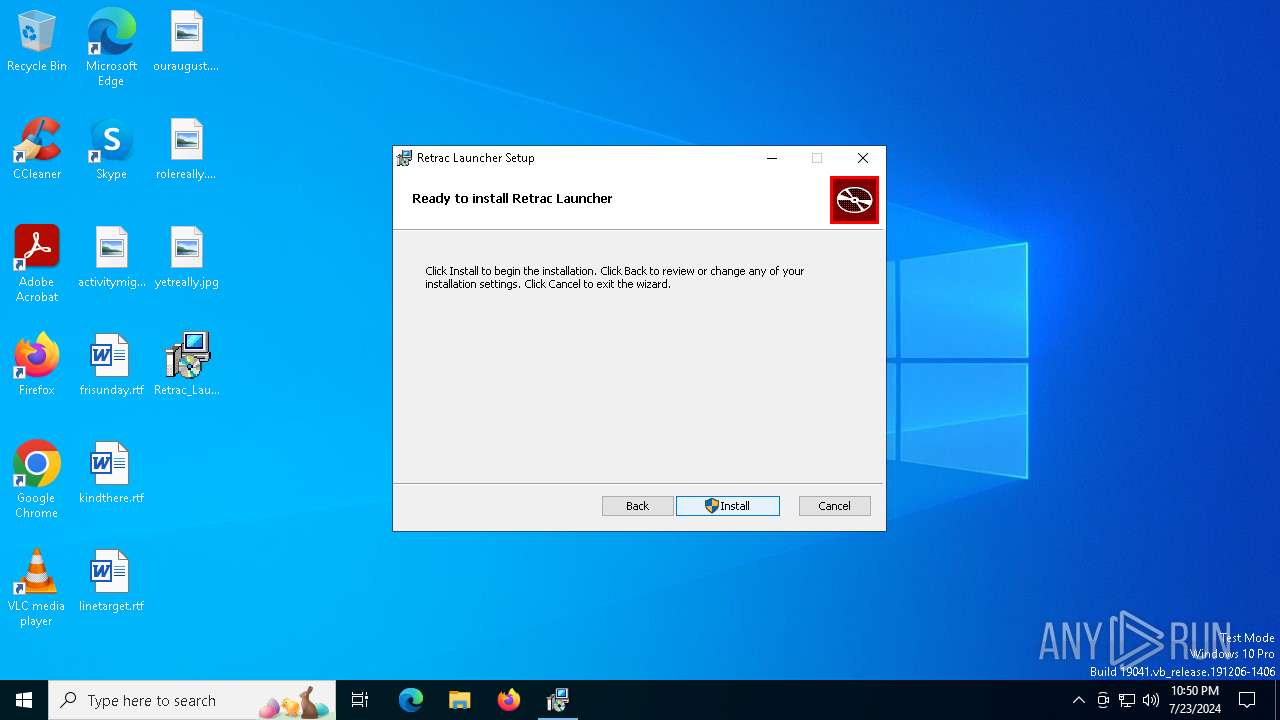
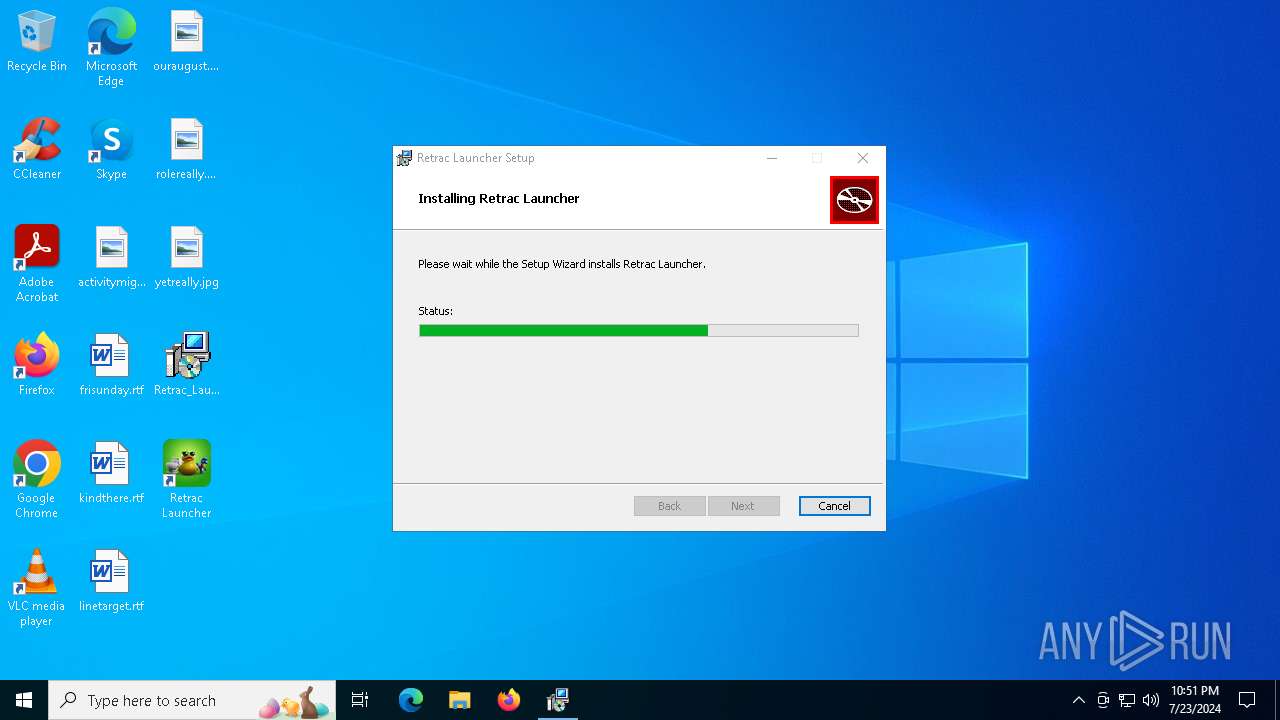
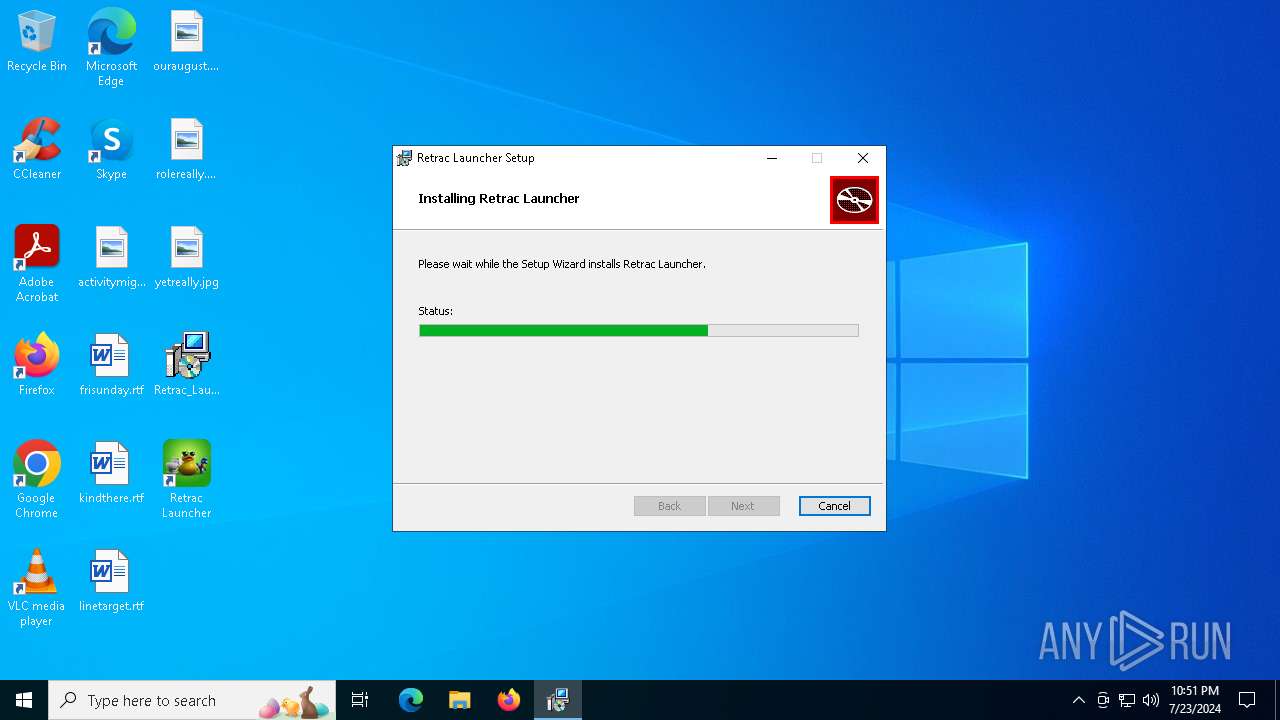
| File name: | Retrac_Launcher_1.0.9_x64_en-US.msi |
| Full analysis: | https://app.any.run/tasks/db0a8ab8-281a-4244-a393-d28fd3dc5d6c |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | July 23, 2024, 22:50:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Retrac Launcher, Author: retrac, Keywords: Installer, Comments: This installer database contains the logic and data required to install Retrac Launcher., Template: x64;0, Revision Number: {40B8E828-9C76-48B1-A498-F10EA833B7D1}, Create Time/Date: Sat Jul 13 22:10:24 2024, Last Saved Time/Date: Sat Jul 13 22:10:24 2024, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | 79A3EF34FB61355DF68B7931C56F08F5 |
| SHA1: | F945151E501116AA5D2FBE3698CD55FF9B766691 |
| SHA256: | E54675FDCD9D66F78F122B7DD4B61F2ACD77951DCDD32914AF8ACE2FF71FD18C |
| SSDEEP: | 98304:rOQkEhQW6Lq6aYfYO75qRmL5w55IP4IDU2rn/W3JWALJgBVJolNBDYLUA5ts7pF4:PQOfn3FP81 |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 3140)
- msiexec.exe (PID: 372)
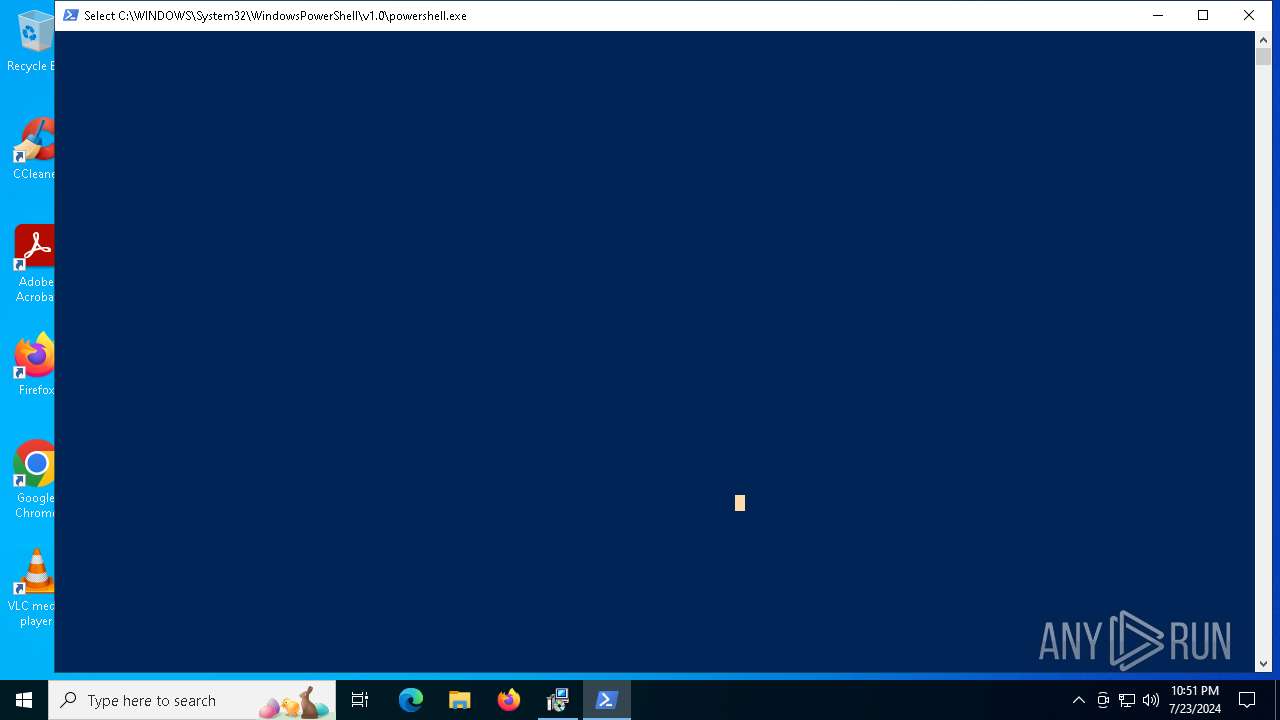
Run PowerShell with an invisible window
- powershell.exe (PID: 2120)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6524)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 372)
Powershell scripting: start process
- msiexec.exe (PID: 372)
Request a resource from the Internet using PowerShell's cmdlet
- msiexec.exe (PID: 372)
Downloads file from URI
- powershell.exe (PID: 2120)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 372)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 372)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 2120)
INFO
Executable content was dropped or overwritten
- msiexec.exe (PID: 3140)
- msiexec.exe (PID: 372)
Checks supported languages
- msiexec.exe (PID: 372)
- msiexec.exe (PID: 4448)
Reads the computer name
- msiexec.exe (PID: 372)
- msiexec.exe (PID: 4448)
Creates a software uninstall entry
- msiexec.exe (PID: 372)
Checks proxy server information
- powershell.exe (PID: 2120)
- slui.exe (PID: 6620)
Disables trace logs
- powershell.exe (PID: 2120)
Reads the software policy settings
- slui.exe (PID: 6620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Retrac Launcher |
| Author: | retrac |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Retrac Launcher. |
| Template: | x64;0 |
| RevisionNumber: | {40B8E828-9C76-48B1-A498-F10EA833B7D1} |
| CreateDate: | 2024:07:13 22:10:24 |
| ModifyDate: | 2024:07:13 22:10:24 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
135
Monitored processes
9
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 944 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | powershell.exe -NoProfile -windowstyle hidden try { [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12 } catch {}; Invoke-WebRequest -Uri "https://go.microsoft.com/fwlink/p/?LinkId=2124703" -OutFile "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" ; Start-Process -FilePath "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" -ArgumentList ('/silent', '/install') -Wait | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3140 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\Retrac_Launcher_1.0.9_x64_en-US.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4448 | C:\Windows\syswow64\MsiExec.exe -Embedding BE526BE3EDC3A92EC76CA29170474882 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4468 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6524 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6620 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 136
Read events
14 842
Write events
284
Delete events
10
Modification events
| (PID) Process: | (372) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000003C9D2EC352DDDA017401000080050000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000003C9D2EC352DDDA017401000080050000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000005F6A84C352DDDA017401000080050000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000005F6A84C352DDDA017401000080050000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000753789C352DDDA017401000080050000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000E25390C352DDDA017401000080050000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (372) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000008FF009C452DDDA017401000080050000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (372) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000003FB80EC452DDDA0174010000C41B0000E8030000010000000000000000000000EA7E104CF9772B49BF7ECC50C651BE6F00000000000000000000000000000000 | |||
| (PID) Process: | (6524) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000F6631FC452DDDA017C19000050080000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
2
Suspicious files
12
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 372 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 372 | msiexec.exe | C:\Windows\Installer\ea350.msi | — | |
MD5:— | SHA256:— | |||
| 372 | msiexec.exe | C:\Windows\Installer\ea352.msi | — | |
MD5:— | SHA256:— | |||
| 372 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{4c107eea-77f9-492b-bf7e-cc50c651be6f}_OnDiskSnapshotProp | binary | |
MD5:59D5AF3113A2D94BE9863857AA19DE6B | SHA256:C535B238808E082D0CC4F222E7AE500CB9DF380B073D3BD86C0CD9E259C0FCA0 | |||
| 372 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:44472E6BF33F40CE324A745E71FE1EE6 | SHA256:595B1ECAEC3D21C63370576A03F32E2F4A994BA9A4A5B7DE771337611E043FBF | |||
| 372 | msiexec.exe | C:\Windows\Installer\MSIAA16.tmp | binary | |
MD5:E3F91E6BC1D2F2F21BB6FA5DE918E548 | SHA256:7398690A60300610A7D2C6DC423448CB4338A3ABE4A70A0CF504D7CAAD8080E4 | |||
| 372 | msiexec.exe | C:\Windows\Installer\{7DD522F6-E5CD-4B2E-9A9D-A445D8FF8695}\ProductIcon | image | |
MD5:B57F2765879042B033B21C525C289D80 | SHA256:B9F884956C9D614CCE40B8E362F814C279AC9C93BBFBA75601587BCD6B7CD117 | |||
| 372 | msiexec.exe | C:\Users\Public\Desktop\Retrac Launcher.lnk | lnk | |
MD5:49C9B1B08330F8F82AD48C1DE75944DA | SHA256:20FF15CE5155AE3B0E4267E024F4C60D4E414679B56731C91A58252DA6BCB290 | |||
| 2120 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_43bqfvhe.qmb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 372 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Retrac Launcher\Retrac Launcher.lnk~RFeabeb.TMP | lnk | |
MD5:64557393C75C181546661B8792BDC590 | SHA256:6A0EA67FD40F5DA0F1AEBEDE3A165F4954B4DD417AB60CFFA6EC88CD8C17E5F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 301 | 184.30.21.171:443 | https://go.microsoft.com/fwlink/p/?LinkId=2124703 | US | — | — | unknown |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | unknown |
— | — | POST | 200 | 20.189.173.1:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | US | binary | 9 b | unknown |
— | — | POST | 401 | 4.209.32.67:443 | https://licensing.mp.microsoft.com/v7.0/licenses/content | US | binary | 340 b | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3164 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6012 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2628 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4204 | svchost.exe | 4.209.32.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5720 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |