| File name: | Fortect.exe |
| Full analysis: | https://app.any.run/tasks/662a945e-57d3-456b-a3ce-1a395efd3f06 |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2023, 08:00:36 |
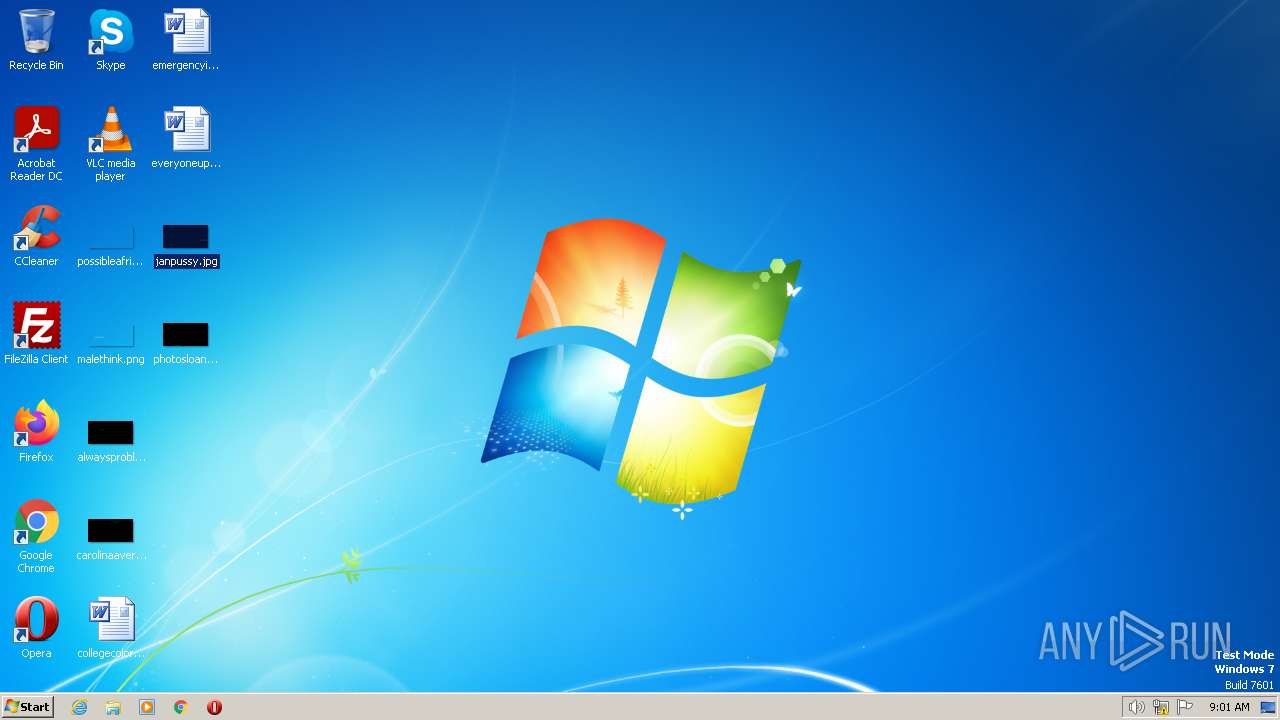
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 01712DE1E76332696B79C25EE32C9704 |
| SHA1: | EACCBC242D11208D882E5E17B1E3C02ADB78AF33 |
| SHA256: | E531F1E904C4A4093A7CC9A960704E428D4BD1F6DD000AA06EC5AABDFC5F4CB7 |
| SSDEEP: | 12288:iYhqRe1sCFnuulCRaIqZPPY1tXHFVX8JPMTz1:iYhqw1skn7lCsvQ11ldJl |
MALICIOUS
Loads dropped or rewritten executable
- Fortect.exe (PID: 4068)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Fortect.exe (PID: 4068)
Reads the Internet Settings
- WMIC.exe (PID: 1144)
- WMIC.exe (PID: 2680)
- WMIC.exe (PID: 3616)
- Fortect.exe (PID: 4068)
Executable content was dropped or overwritten
- Fortect.exe (PID: 4068)
The process creates files with name similar to system file names
- Fortect.exe (PID: 4068)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 2604)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 3044)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 3972)
INFO
Create files in a temporary directory
- Fortect.exe (PID: 4068)
Reads the computer name
- Fortect.exe (PID: 4068)
Checks supported languages
- Fortect.exe (PID: 4068)
The process checks LSA protection
- Fortect.exe (PID: 4068)
- WMIC.exe (PID: 2680)
- WMIC.exe (PID: 3616)
- WMIC.exe (PID: 1144)
- dllhost.exe (PID: 1760)
Reads the machine GUID from the registry
- Fortect.exe (PID: 4068)
Reads Environment values
- Fortect.exe (PID: 4068)
Checks proxy server information
- Fortect.exe (PID: 4068)
Manual execution by a user
- opera.exe (PID: 2660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 5.0.0.7 |
|---|---|
| ProductName: | Fortect |
| OriginalFileName: | Fortect.exe |
| LegalTrademarks: | © Fortect |
| LegalCopyright: | © Fortect |
| InternalName: | Fortect.exe |
| FileVersion: | 5.0.0.7 |
| FileDescription: | Fortect Setup |
| CompanyName: | Fortect |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 5.0.0.7 |
| FileVersionNumber: | 5.0.0.7 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x3640 |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 141824 |
| CodeSize: | 26624 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2021:09:25 21:56:47+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Sep-2021 21:56:47 |
| Detected languages: |
|
| CompanyName: | Fortect |
| FileDescription: | Fortect Setup |
| FileVersion: | 5.0.0.7 |
| InternalName: | Fortect.exe |
| LegalCopyright: | © Fortect |
| LegalTrademarks: | © Fortect |
| OriginalFilename: | Fortect.exe |
| ProductName: | Fortect |
| ProductVersion: | 5.0.0.7 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Sep-2021 21:56:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006676 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41746 |
.rdata | 0x00008000 | 0x0000139A | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14107 |
.data | 0x0000A000 | 0x00020378 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.11058 |
.ndata | 0x0002B000 | 0x0004A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00075000 | 0x0004C138 | 0x0004C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.45788 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30544 | 1128 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.94055 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 2.10094 | 38056 | UNKNOWN | English - United States | RT_ICON |
4 | 2.38655 | 16936 | UNKNOWN | English - United States | RT_ICON |
5 | 7.9328 | 12262 | UNKNOWN | English - United States | RT_ICON |
6 | 2.60741 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.01018 | 4264 | UNKNOWN | English - United States | RT_ICON |
8 | 3.33264 | 2440 | UNKNOWN | English - United States | RT_ICON |
9 | 3.4201 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 3.07075 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
52
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1144 | C:\Windows\System32\wbem\wmic.exe path Win32_ComputerSystemProduct get UUID | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1760 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2604 | C:\Windows\system32\cmd.exe /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe" path Win32_BIOS get SerialNumber | C:\Windows\System32\cmd.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2680 | C:\Windows\System32\wbem\wmic.exe path Win32_BIOS get SerialNumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3044 | C:\Windows\system32\cmd.exe /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe" path Win32_DiskDrive get SerialNumber | C:\Windows\System32\cmd.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3616 | C:\Windows\System32\wbem\wmic.exe path Win32_DiskDrive get SerialNumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3928 | "C:\Users\admin\AppData\Local\Temp\Fortect.exe" | C:\Users\admin\AppData\Local\Temp\Fortect.exe | — | explorer.exe | |||||||||||
User: admin Company: Fortect Integrity Level: MEDIUM Description: Fortect Setup Exit code: 3221226540 Version: 5.0.0.7 Modules
| |||||||||||||||
| 3972 | C:\Windows\system32\cmd.exe /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe" path Win32_ComputerSystemProduct get UUID | C:\Windows\System32\cmd.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4068 | "C:\Users\admin\AppData\Local\Temp\Fortect.exe" | C:\Users\admin\AppData\Local\Temp\Fortect.exe | explorer.exe | ||||||||||||
User: admin Company: Fortect Integrity Level: HIGH Description: Fortect Setup Exit code: 0 Version: 5.0.0.7 Modules
| |||||||||||||||
Total events
1 988
Read events
1 917
Write events
71
Delete events
0
Modification events
| (PID) Process: | (4068) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4068) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4068) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4068) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4068) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4068) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4068) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4068) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2660) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (2660) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
5
Suspicious files
20
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4068 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\nsnC95F.tmp\ExecDos.dll | executable | |
MD5:F920B104C2FE5CA6FEDD2B5825544EE6 | SHA256:4CBC00B2BA0CE3052427A541D72501D45CBD93442A9A85EA249C2894DF529000 | |||
| 4068 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\nsnC95F.tmp\Crypto.dll | executable | |
MD5:5F8DDDD0537CF9D33230C5F690C0ECA0 | SHA256:09140B70AA226CCD3C4EB0EA5DB056E4774004A96B4A32EEB1E51ECD799FDAEA | |||
| 2660 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr27D9.tmp | xml | |
MD5:20BDFDEC9DDE109574E79E1977E28920 | SHA256:84FE7FDA1BA1DF067995D0517ABC13603205D6A7885E5D536555593D8F3279B6 | |||
| 2660 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr278A.tmp | text | |
MD5:3090295D1A039FC4393E1183D686D608 | SHA256:88A7AE135C4DC2C230F96A2BF294B764921BBCE3C4086921A43F498077EEA61E | |||
| 2660 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UCAS5I8SY2MJXKNX0EDJ.temp | binary | |
MD5:FDBCDB294DED05EA01DCAA246B98C2C5 | SHA256:EAEC5A291DBC8E8760BAB0C1BB27CB801F671166CE85310FD173F54111357C4B | |||
| 4068 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\nsnC95F.tmp\INetC.dll | executable | |
MD5:9F3C809A6F525A8EF0C981C84113560E | SHA256:4D7A2D9151E02B971F38D10FFE8937F34227AD5A2CE11E7879DF094482DECA72 | |||
| 4068 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\nsnC95F.tmp\LogEx.dll | executable | |
MD5:065130BD4BC3B4D769FFB0050A5464D0 | SHA256:568871B5048CF3E9A9C200C6527938FC616139353E084C43D283F96BA16B4EBB | |||
| 2660 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:3090295D1A039FC4393E1183D686D608 | SHA256:88A7AE135C4DC2C230F96A2BF294B764921BBCE3C4086921A43F498077EEA61E | |||
| 2660 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:FDBCDB294DED05EA01DCAA246B98C2C5 | SHA256:EAEC5A291DBC8E8760BAB0C1BB27CB801F671166CE85310FD173F54111357C4B | |||
| 2660 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms~RF112da4.TMP | binary | |
MD5:DBC8C3C79F0DFF4745A5E25E13611AEF | SHA256:70C54F2C53CF246603B8DE4755D95C5AA51BF4B232340BEA5879724A1F84F675 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
16
DNS requests
3
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3380 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2660 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
4068 | Fortect.exe | 104.26.2.16:443 | app.fortect.com | CLOUDFLARENET | US | unknown |
2660 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
4068 | Fortect.exe | 104.26.3.16:443 | app.fortect.com | CLOUDFLARENET | US | unknown |
4068 | Fortect.exe | 172.67.75.40:443 | app.fortect.com | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
app.fortect.com |
| malicious |
certs.opera.com |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2660 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2660 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2660 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2660 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2660 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |