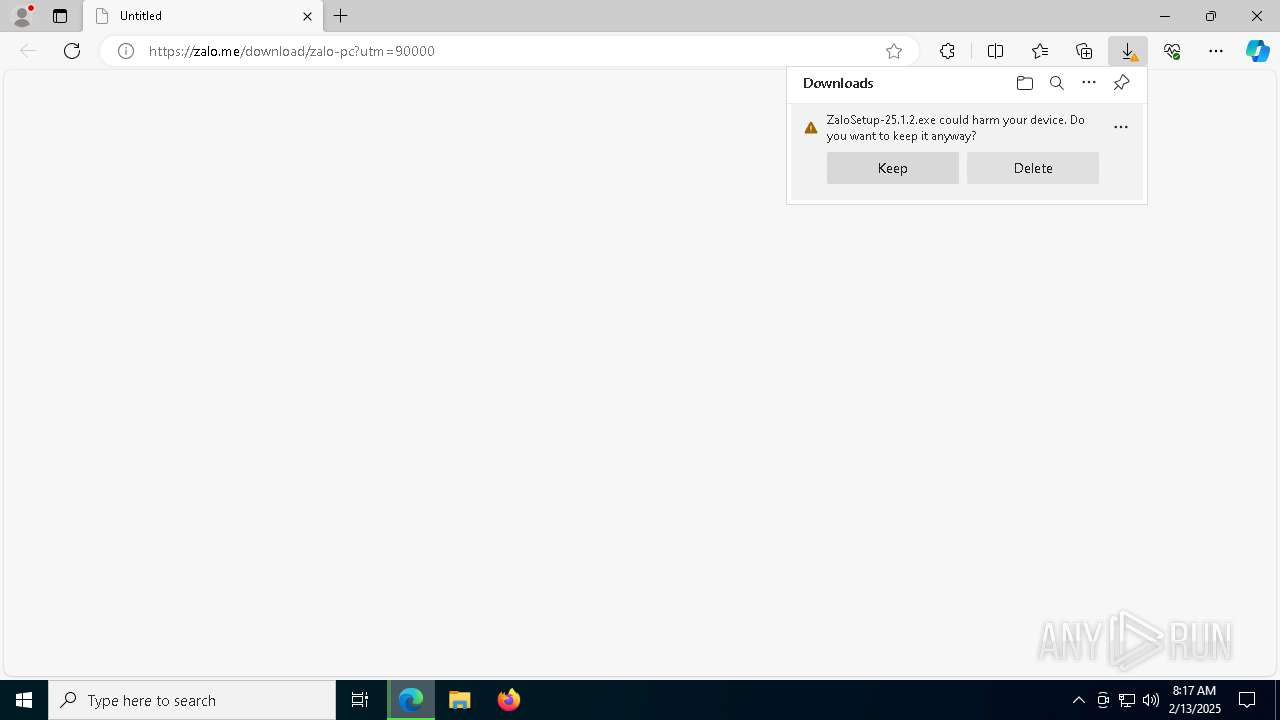
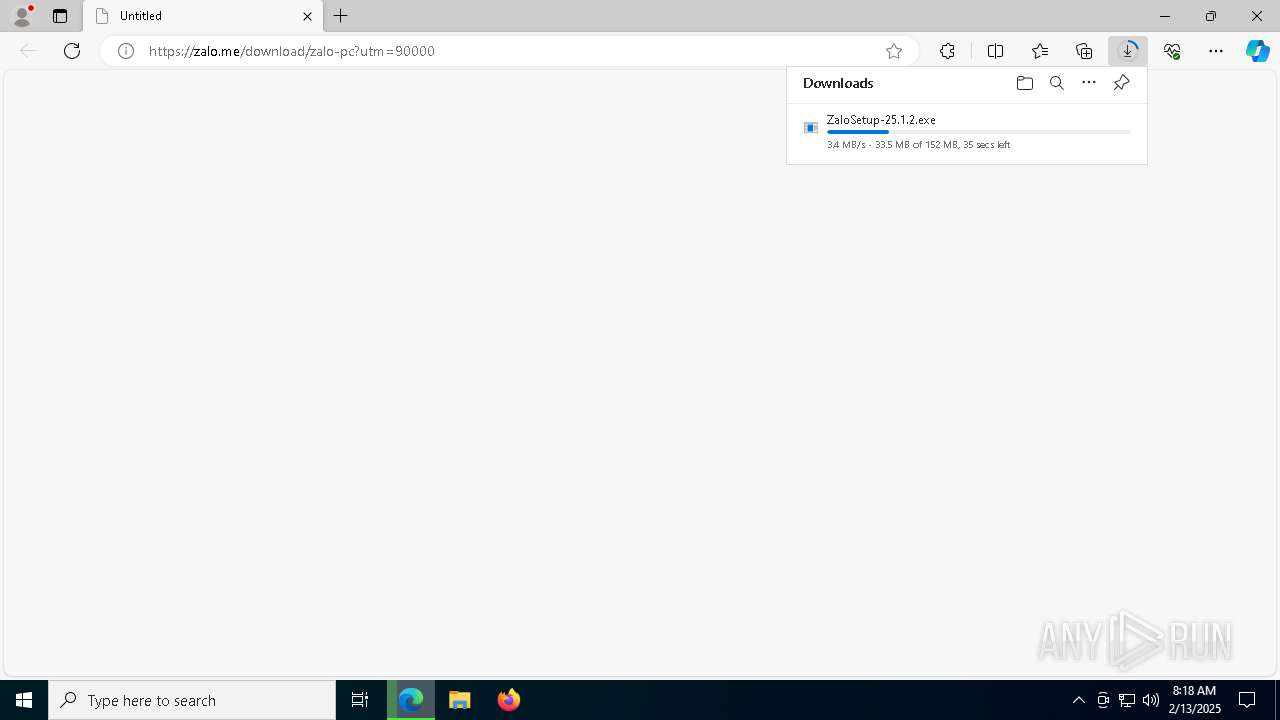
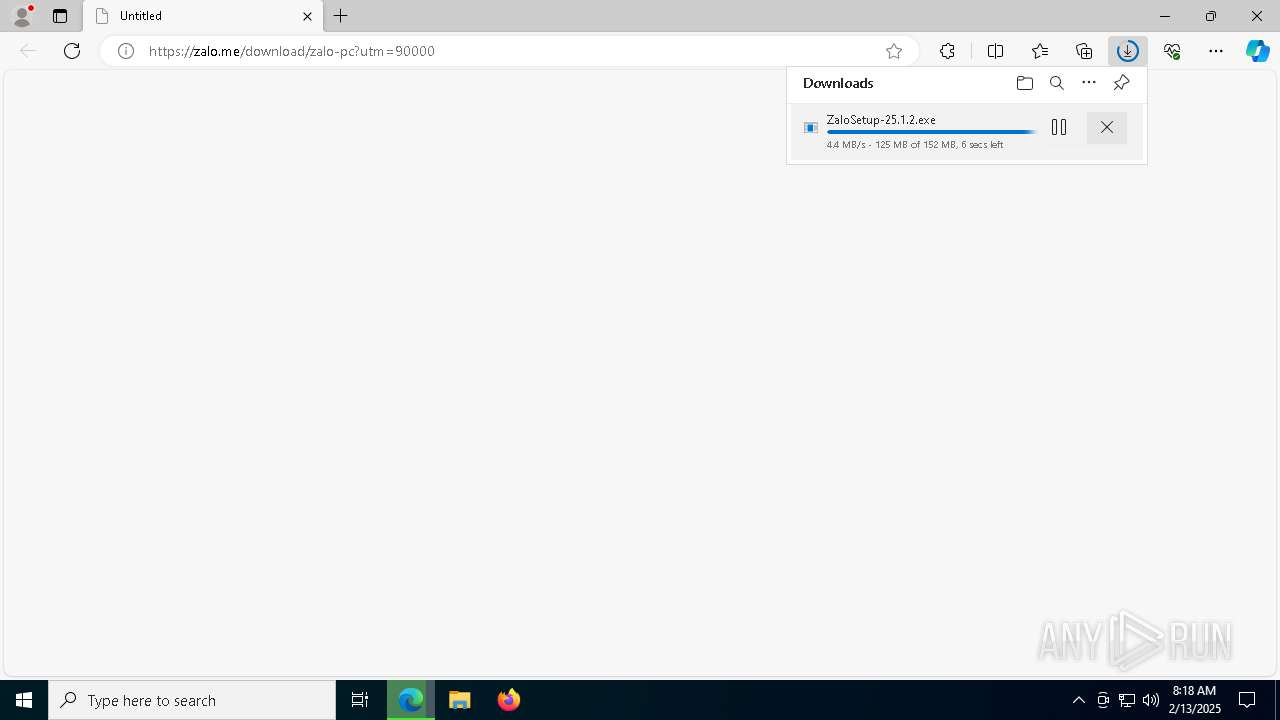
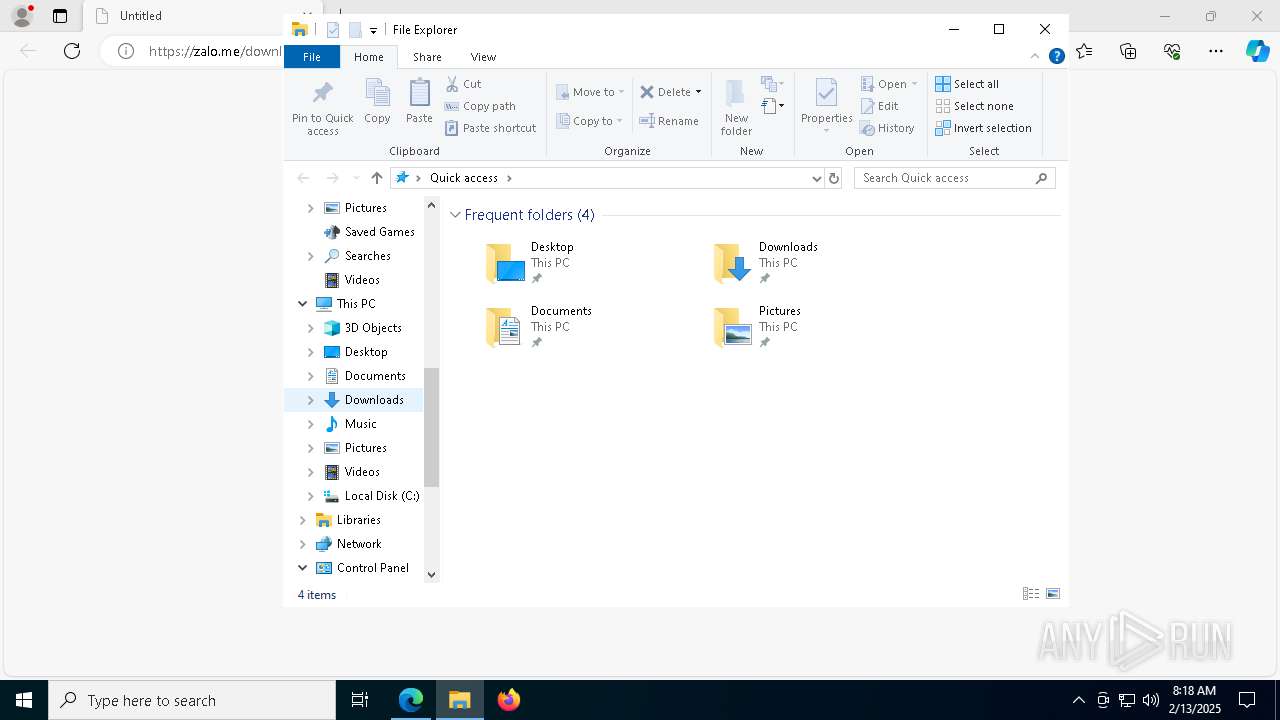
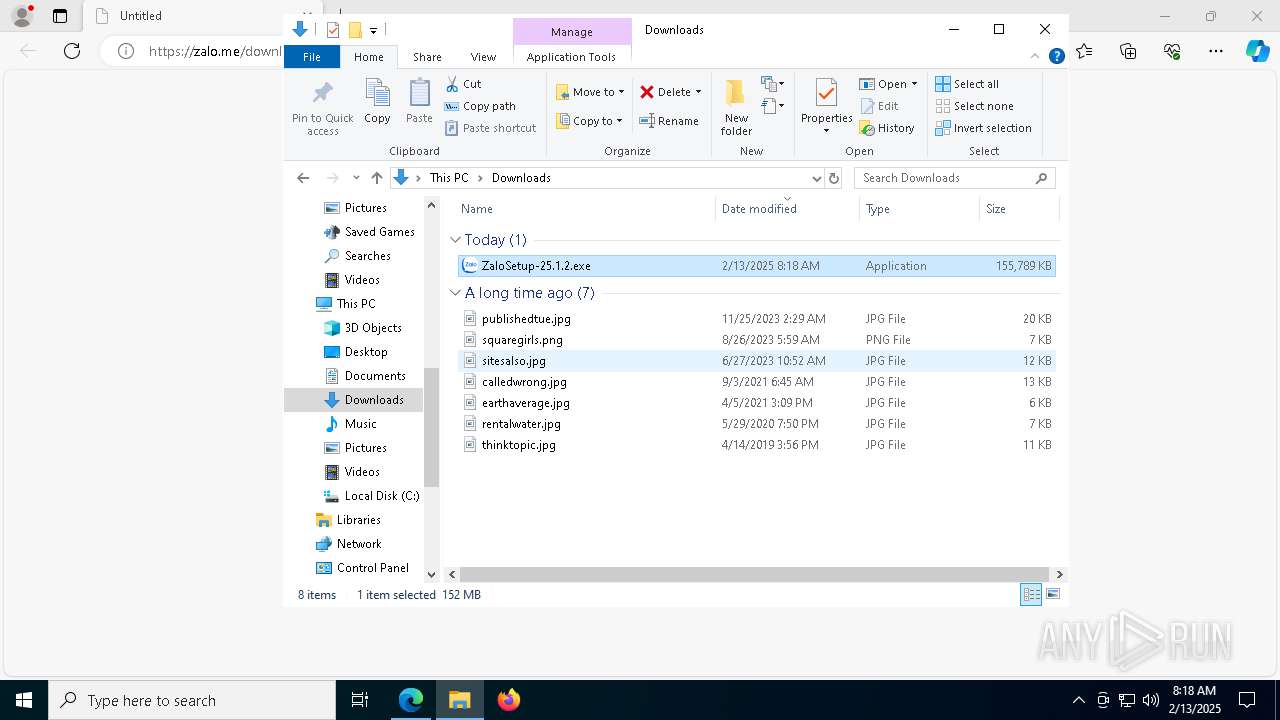
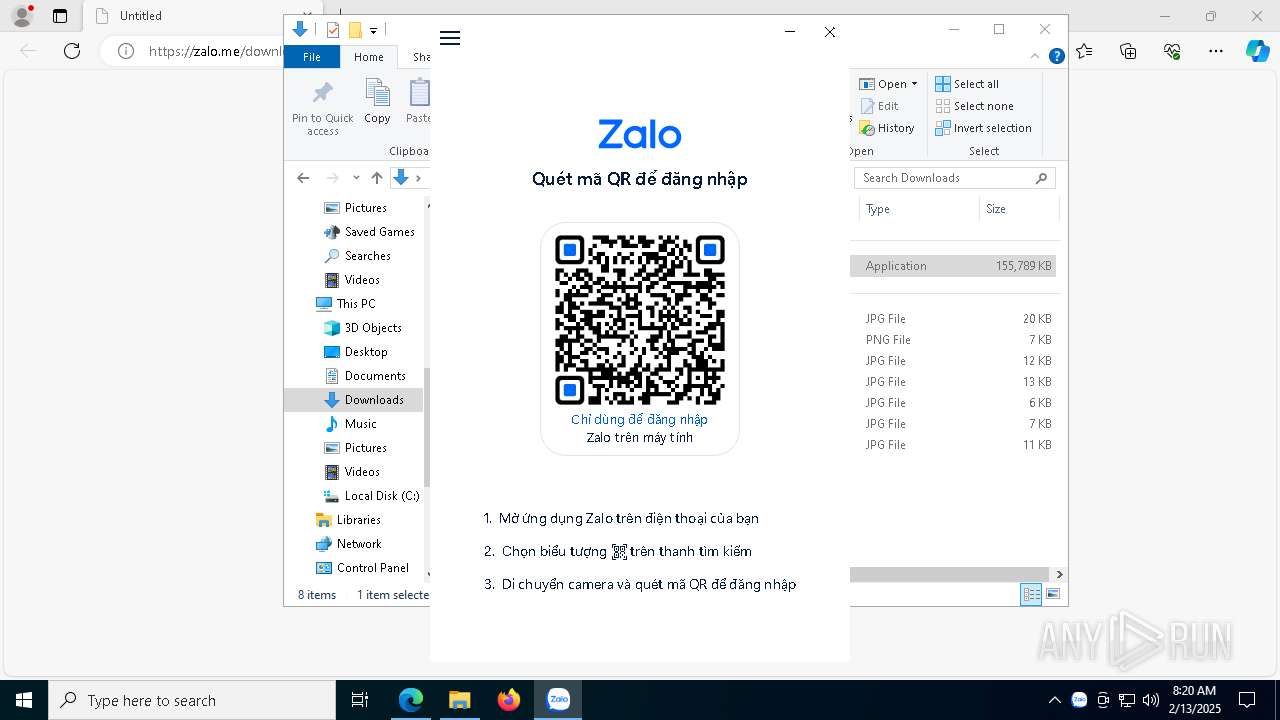
| URL: | https://zalo.me/download/zalo-pc?utm=90000 |
| Full analysis: | https://app.any.run/tasks/095e0632-7300-46a6-93c4-eeaef10dac17 |
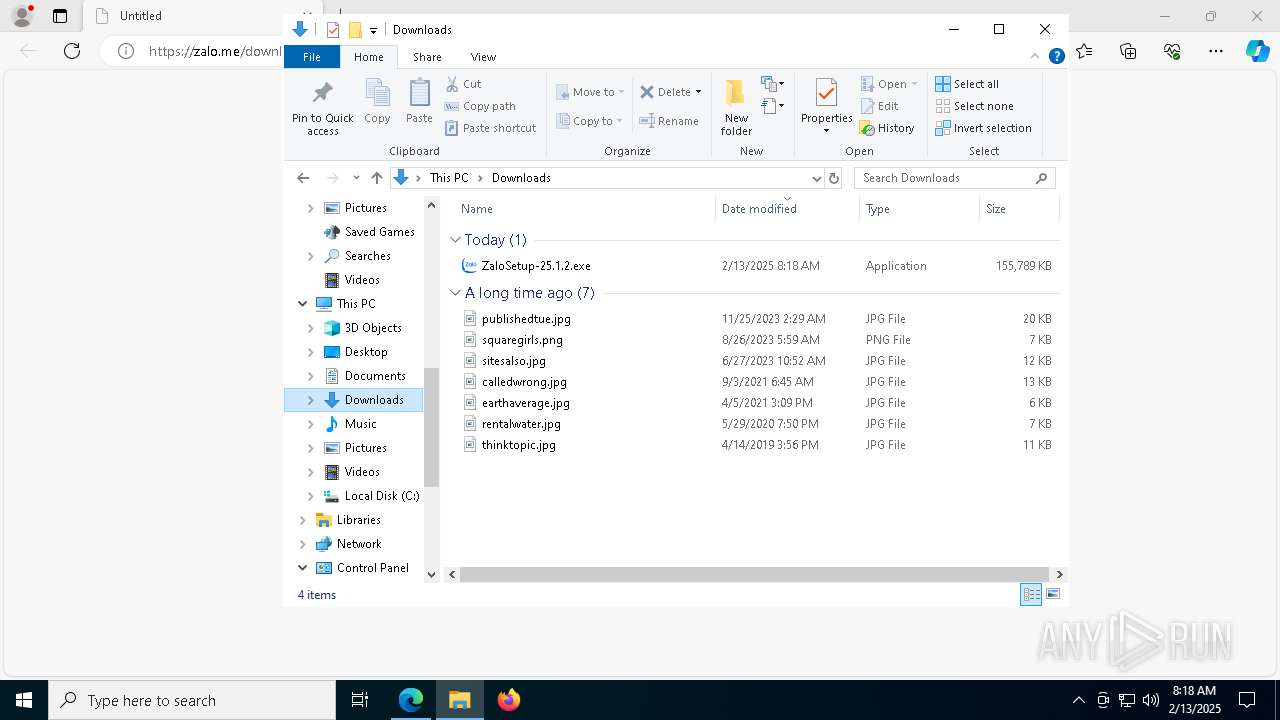
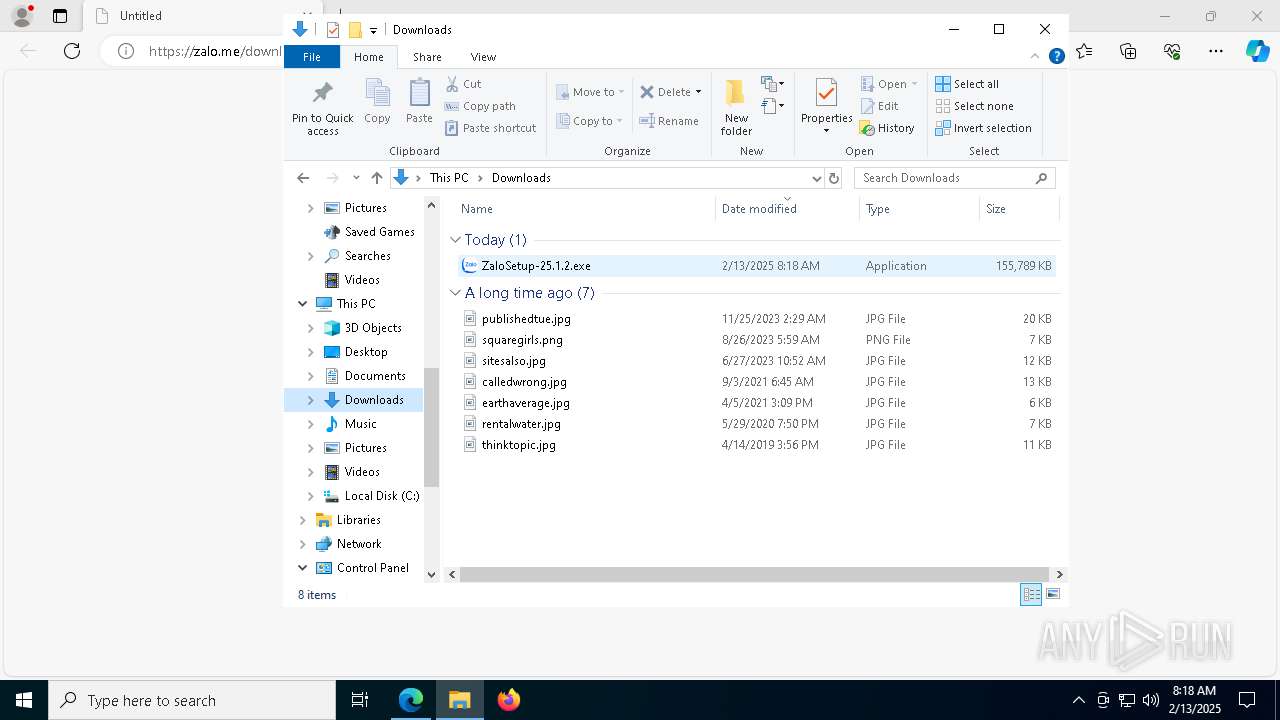
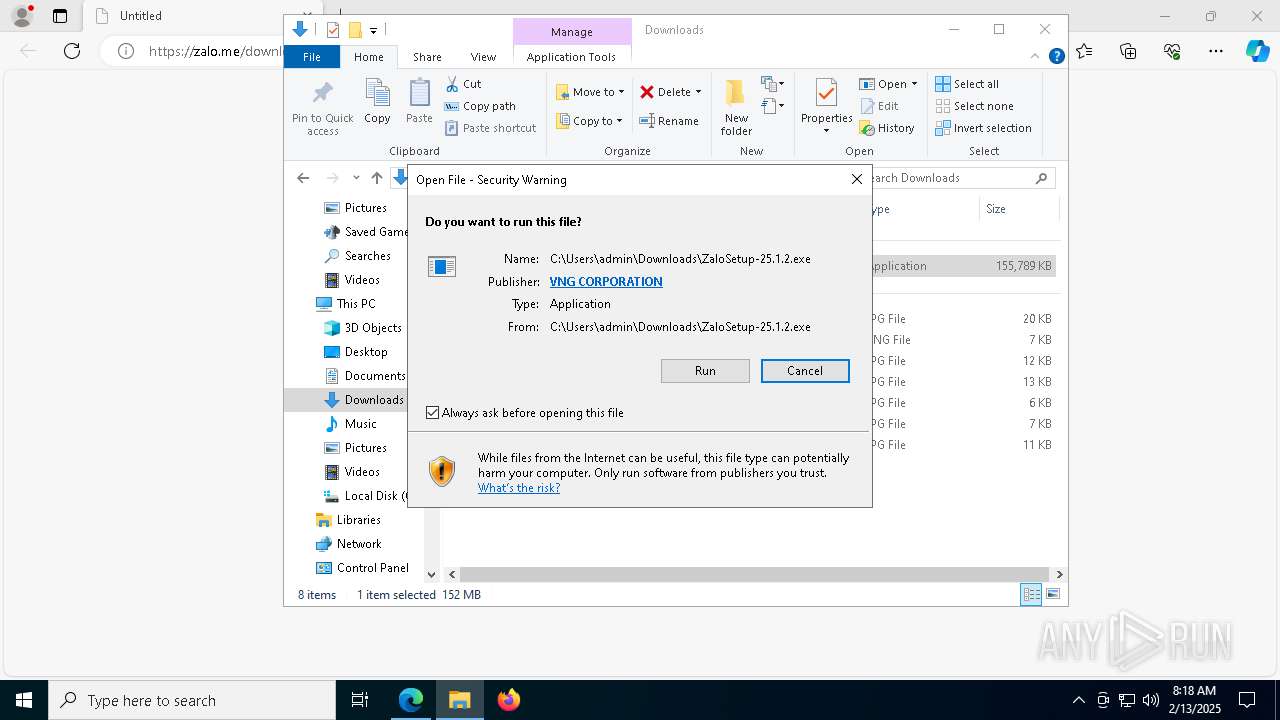
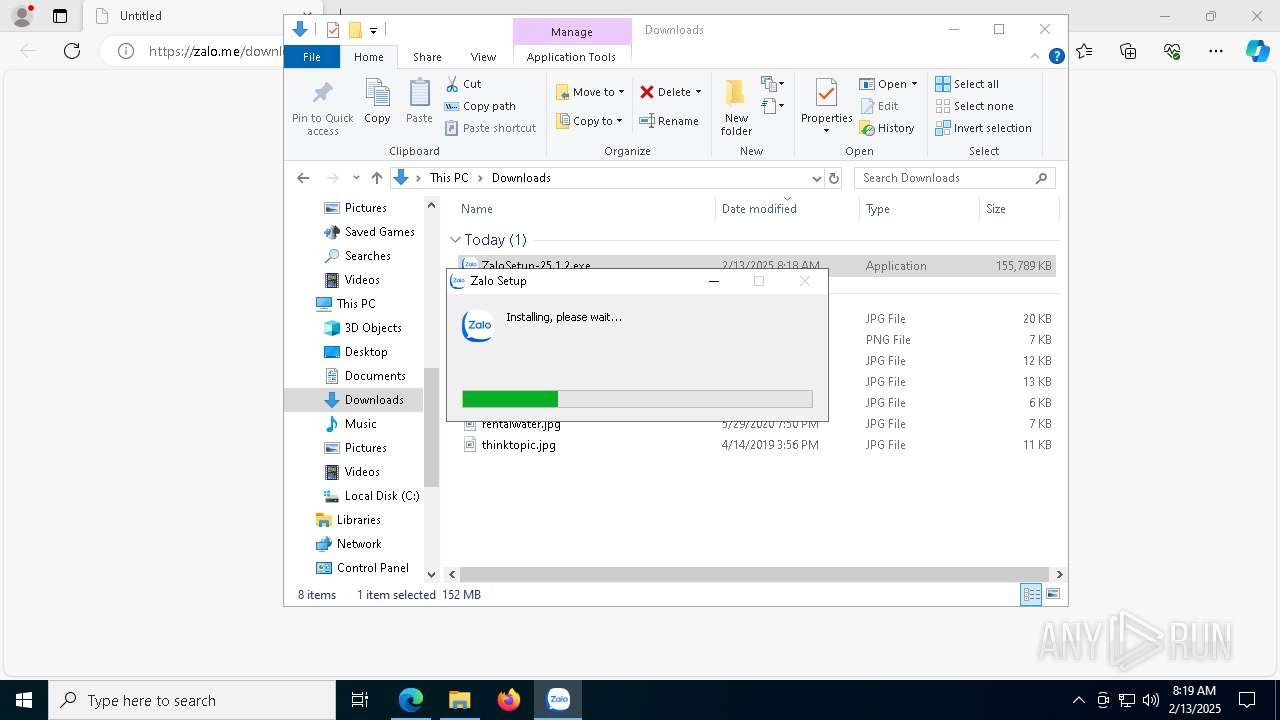
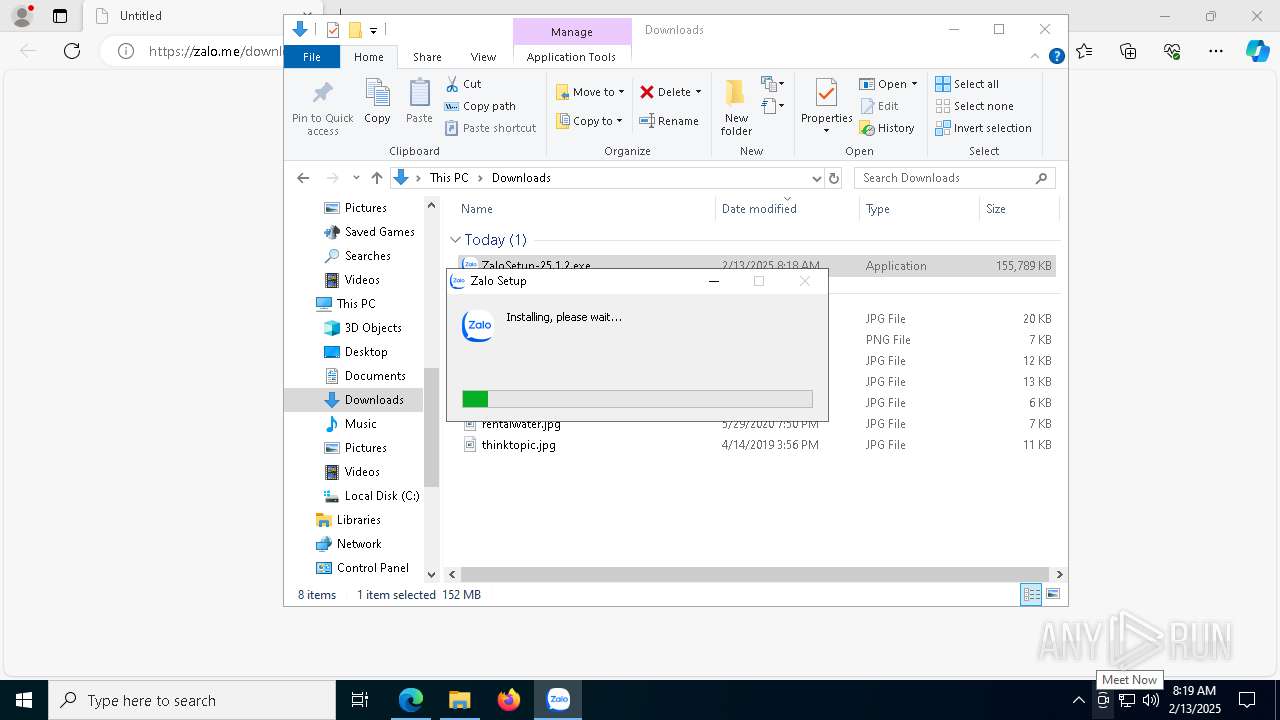
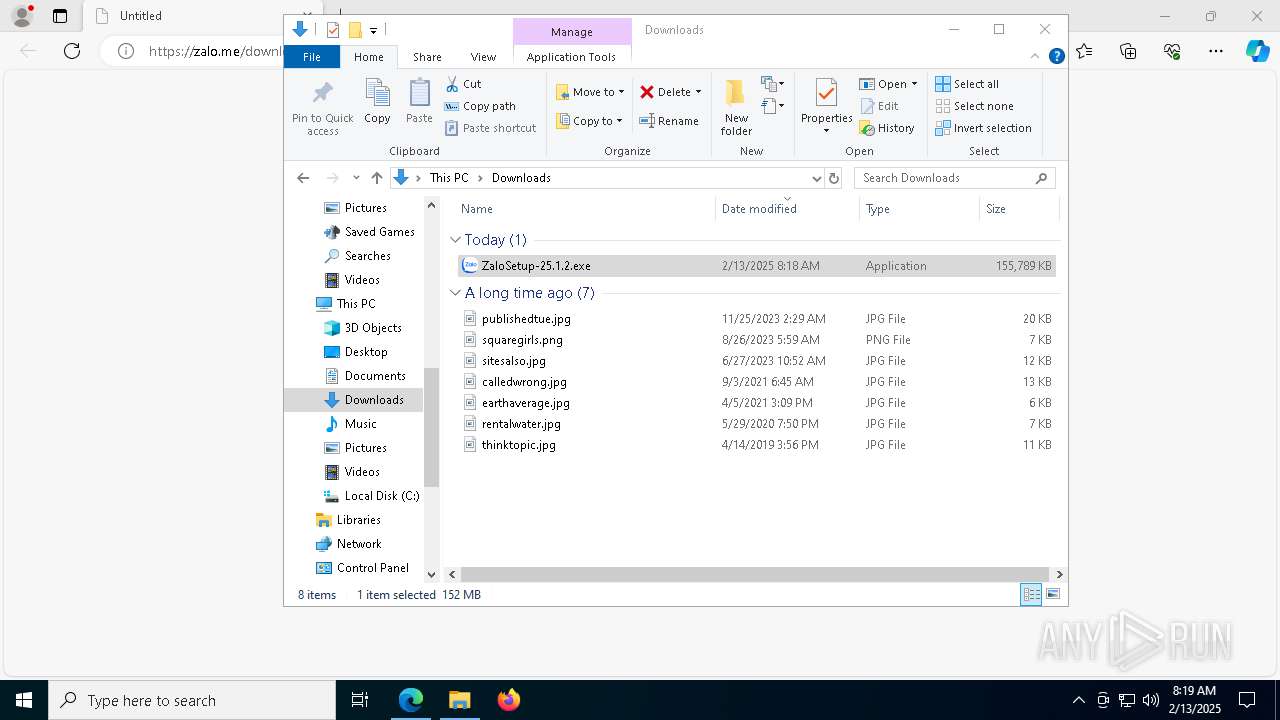
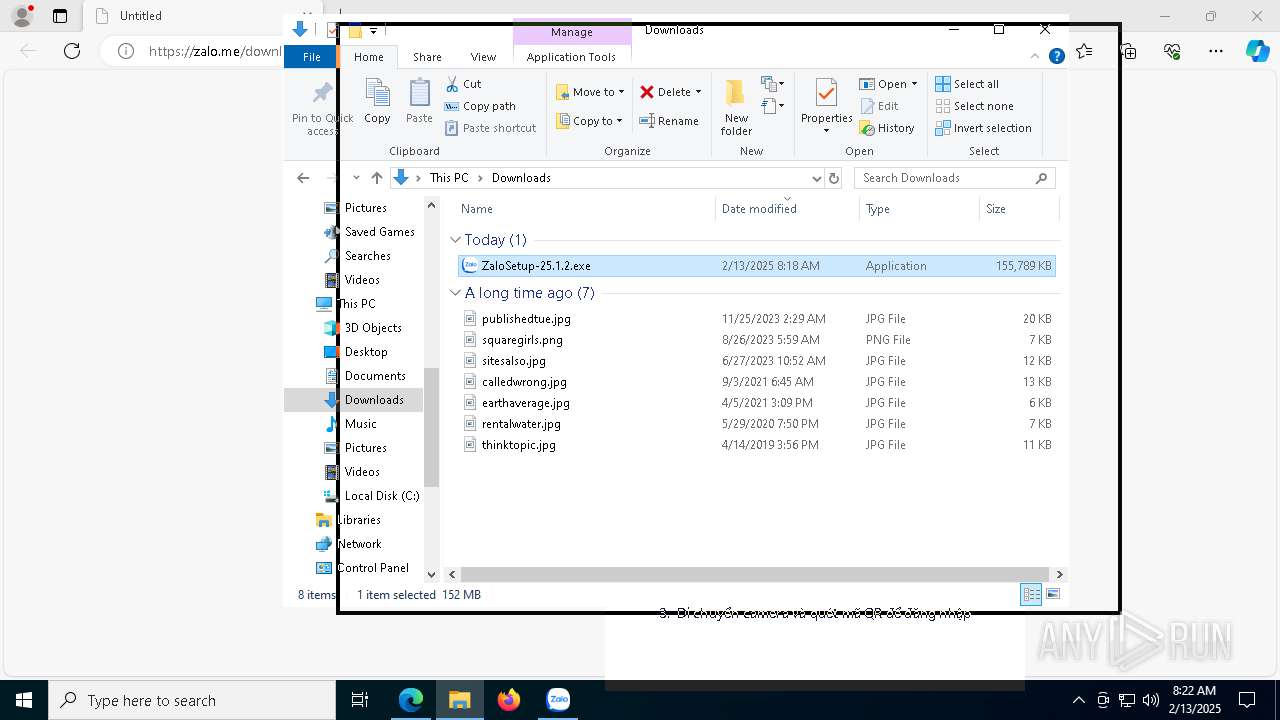
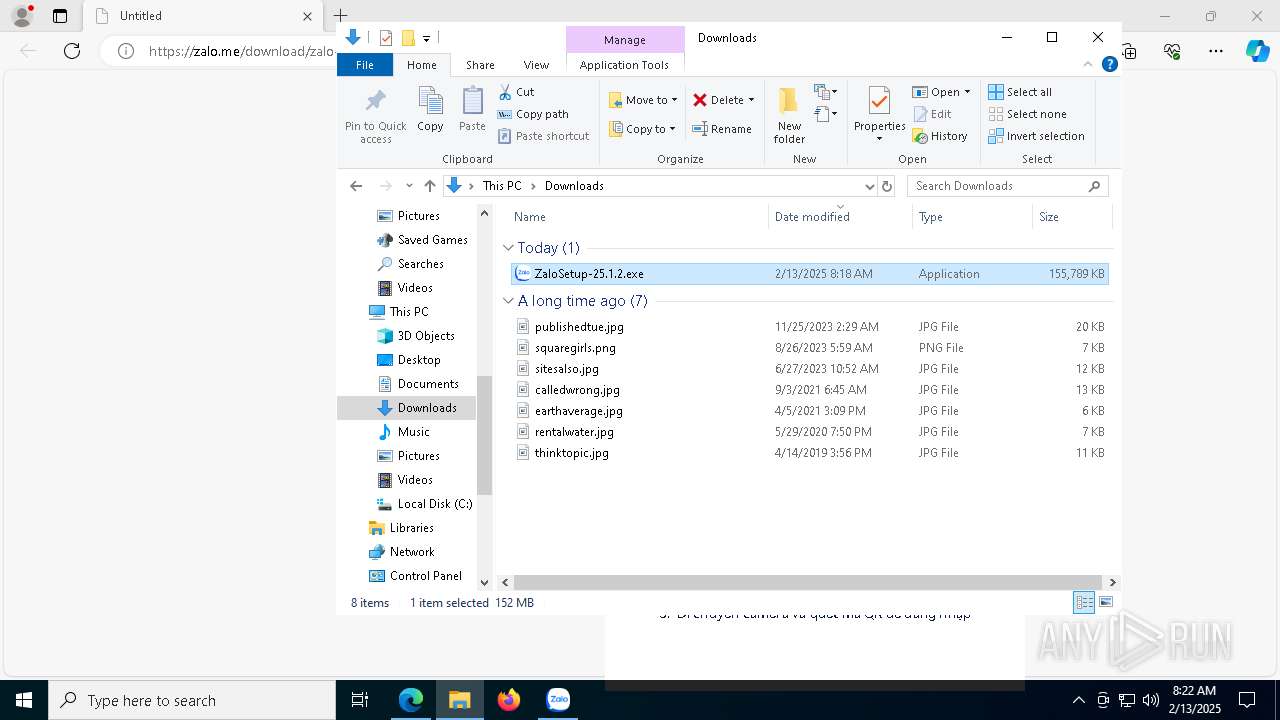
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2025, 08:17:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F89A4C7F8605F0C41404FB5A17DEE377 |
| SHA1: | 0EA92BC6932D3B5070A85994D48F64ECD817F764 |
| SHA256: | E53066D44D7CBD98220001C6A752C5E903349373F5945F41B4E06E79FCE91D1B |
| SSDEEP: | 3:N8tIv2oTUMX:2tI/AMX |
MALICIOUS
Executing a file with an untrusted certificate
- ZaloSetup-25.1.2.exe (PID: 4516)
- Zalo.exe (PID: 7892)
- Zalo.exe (PID: 1876)
- Zalo.exe (PID: 7100)
- Zalo.exe (PID: 4308)
- ZaloCap.exe (PID: 7724)
- Zalo.exe (PID: 3640)
- Zalo.exe (PID: 1220)
- Zalo.exe (PID: 7728)
- Zalo.exe (PID: 1076)
- Zalo.exe (PID: 1140)
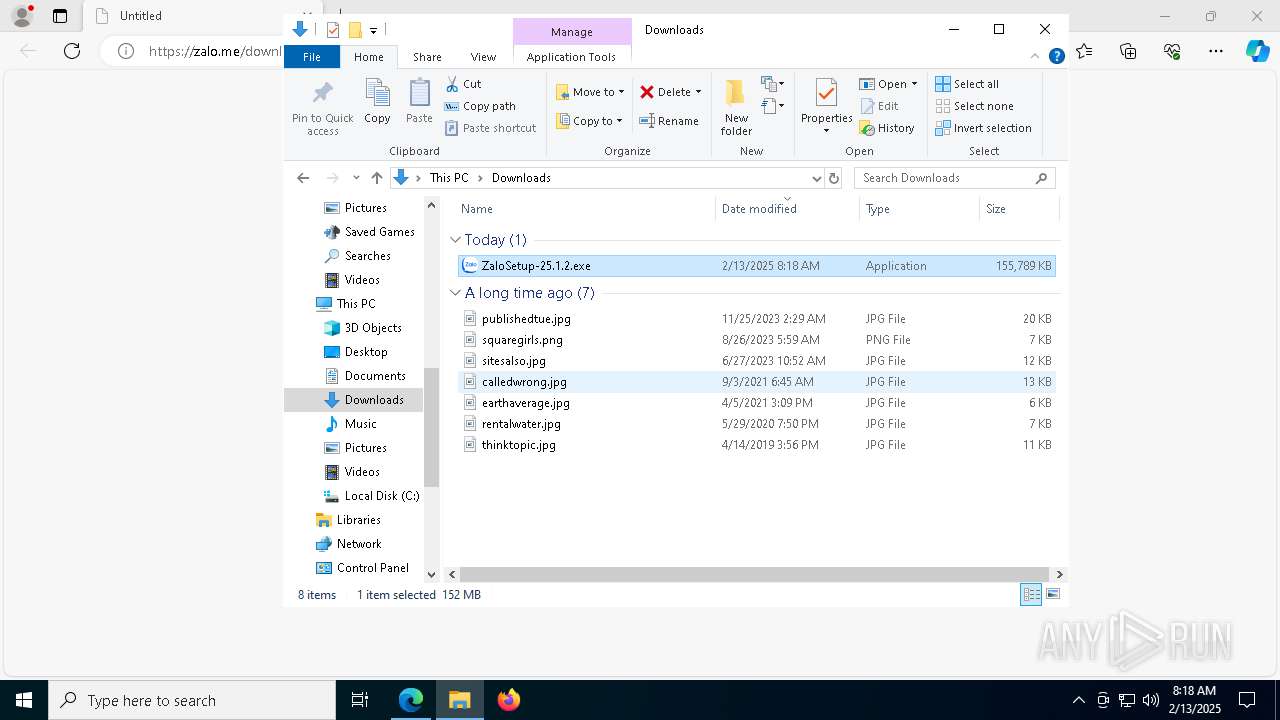
Changes the autorun value in the registry
- reg.exe (PID: 3692)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- ZaloSetup-25.1.2.exe (PID: 4516)
Reads security settings of Internet Explorer
- ZaloSetup-25.1.2.exe (PID: 4516)
Drops 7-zip archiver for unpacking
- ZaloSetup-25.1.2.exe (PID: 4516)
Executable content was dropped or overwritten
- ZaloSetup-25.1.2.exe (PID: 4516)
There is functionality for taking screenshot (YARA)
- ZaloSetup-25.1.2.exe (PID: 4516)
- Zalo.exe (PID: 4308)
Process drops legitimate windows executable
- ZaloSetup-25.1.2.exe (PID: 4516)
The process drops C-runtime libraries
- ZaloSetup-25.1.2.exe (PID: 4516)
Creates a software uninstall entry
- ZaloSetup-25.1.2.exe (PID: 4516)
The process creates files with name similar to system file names
- ZaloSetup-25.1.2.exe (PID: 4516)
Application launched itself
- Zalo.exe (PID: 7100)
Uses REG/REGEDIT.EXE to modify registry
- Zalo.exe (PID: 7100)
Starts CMD.EXE for commands execution
- Zalo.exe (PID: 7728)
- Zalo.exe (PID: 1076)
- Zalo.exe (PID: 1220)
- Zalo.exe (PID: 3640)
Starts application with an unusual extension
- cmd.exe (PID: 7924)
- cmd.exe (PID: 5912)
- cmd.exe (PID: 4864)
- cmd.exe (PID: 5304)
Uses WMIC.EXE to obtain operating system information
- Zalo.exe (PID: 7100)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 7764)
INFO
Application launched itself
- msedge.exe (PID: 6328)
- msedge.exe (PID: 7820)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
- WMIC.exe (PID: 4672)
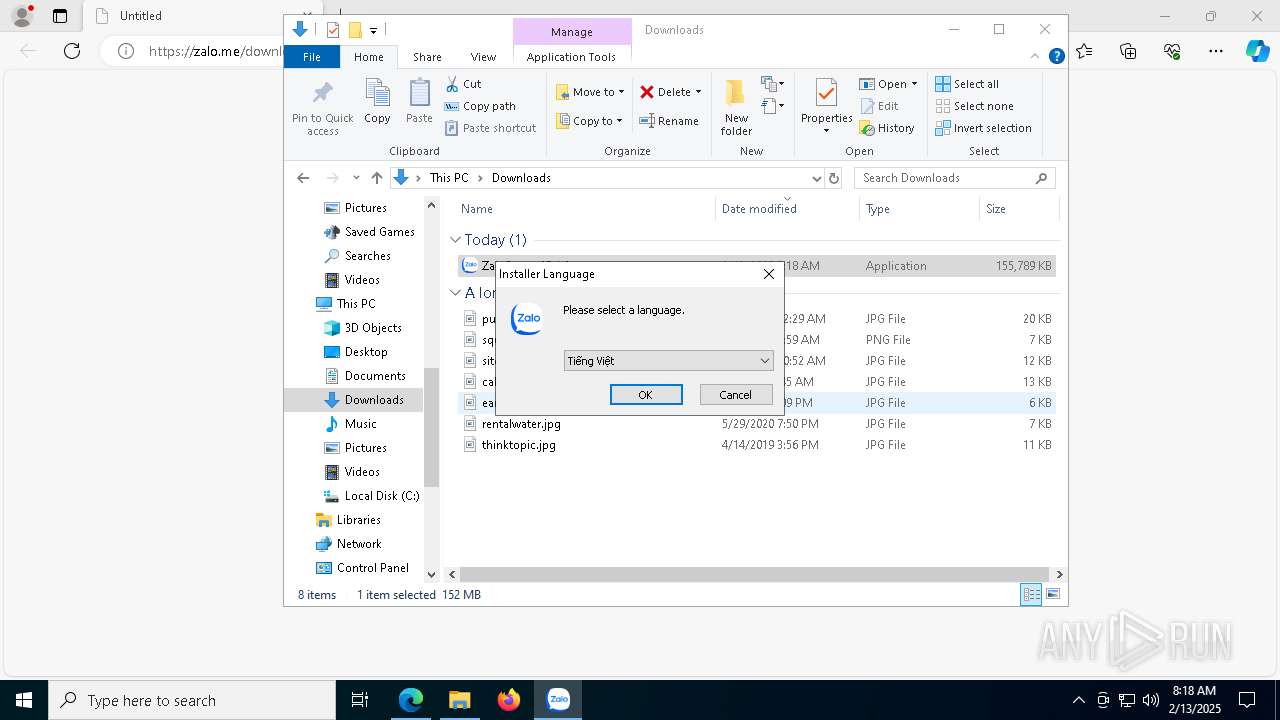
Checks supported languages
- identity_helper.exe (PID: 8016)
- ZaloSetup-25.1.2.exe (PID: 4516)
- Zalo.exe (PID: 7100)
- Zalo.exe (PID: 4308)
- Zalo.exe (PID: 1876)
- Zalo.exe (PID: 7892)
- Zalo.exe (PID: 3640)
- ZaloCap.exe (PID: 7724)
- Zalo.exe (PID: 7728)
- Zalo.exe (PID: 1220)
- Zalo.exe (PID: 1076)
- chcp.com (PID: 4640)
- chcp.com (PID: 7584)
- chcp.com (PID: 768)
- chcp.com (PID: 5456)
- PLUGScheduler.exe (PID: 7764)
- Zalo.exe (PID: 1140)
- identity_helper.exe (PID: 8080)
Creates files or folders in the user directory
- explorer.exe (PID: 4488)
- ZaloSetup-25.1.2.exe (PID: 4516)
- Zalo.exe (PID: 7100)
- Zalo.exe (PID: 1220)
- Zalo.exe (PID: 1076)
- Zalo.exe (PID: 3640)
- Zalo.exe (PID: 1876)
- Zalo.exe (PID: 1140)
Reads Environment values
- identity_helper.exe (PID: 8016)
- identity_helper.exe (PID: 8080)
Reads the computer name
- identity_helper.exe (PID: 8016)
- ZaloSetup-25.1.2.exe (PID: 4516)
- Zalo.exe (PID: 7100)
- Zalo.exe (PID: 1876)
- Zalo.exe (PID: 4308)
- ZaloCap.exe (PID: 7724)
- Zalo.exe (PID: 3640)
- Zalo.exe (PID: 1076)
- PLUGScheduler.exe (PID: 7764)
- Zalo.exe (PID: 1140)
- identity_helper.exe (PID: 8080)
Checks proxy server information
- explorer.exe (PID: 4488)
- ZaloSetup-25.1.2.exe (PID: 4516)
- Zalo.exe (PID: 7100)
Executable content was dropped or overwritten
- msedge.exe (PID: 6328)
The sample compiled with english language support
- ZaloSetup-25.1.2.exe (PID: 4516)
Reads the software policy settings
- explorer.exe (PID: 4488)
- Zalo.exe (PID: 7100)
Create files in a temporary directory
- ZaloSetup-25.1.2.exe (PID: 4516)
- Zalo.exe (PID: 7100)
Reads CPU info
- Zalo.exe (PID: 7100)
- Zalo.exe (PID: 3640)
- Zalo.exe (PID: 1076)
- Zalo.exe (PID: 1220)
- Zalo.exe (PID: 7728)
Process checks computer location settings
- Zalo.exe (PID: 7100)
- Zalo.exe (PID: 3640)
- Zalo.exe (PID: 1076)
- Zalo.exe (PID: 1220)
- Zalo.exe (PID: 7728)
Changes the display of characters in the console
- cmd.exe (PID: 4864)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 5912)
Node.js compiler has been detected
- Zalo.exe (PID: 7100)
- Zalo.exe (PID: 4308)
- Zalo.exe (PID: 1876)
Reads the machine GUID from the registry
- Zalo.exe (PID: 7100)
- Zalo.exe (PID: 1140)
Creates files in the program directory
- PLUGScheduler.exe (PID: 7764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
223
Monitored processes
88
Malicious processes
9
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --mojo-platform-channel-handle=4168 --field-trial-handle=2476,i,16977655482037235221,18120717862284183719,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 308 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5364 --field-trial-handle=2268,i,2244330295466159046,12201927549253561440,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3376 --field-trial-handle=2268,i,2244330295466159046,12201927549253561440,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 648 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | chcp | C:\Windows\SysWOW64\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2644 --field-trial-handle=2268,i,2244330295466159046,12201927549253561440,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1076 | "C:\Users\admin\AppData\Local\Programs\Zalo\Zalo-25.1.2\Zalo.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\ZaloData" --app-user-model-id=com.vng.zalo --app-path="C:\Users\admin\AppData\Local\Programs\Zalo\Zalo-25.1.2\resources\app.asar" --enable-experimental-web-platform-features --no-sandbox --no-zygote --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=3236 --field-trial-handle=1808,i,7565084531684393067,9224958151273354389,131072 --enable-features=JXL --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Programs\Zalo\Zalo-25.1.2\Zalo.exe | — | Zalo.exe | |||||||||||
User: admin Company: VNG Corp. Integrity Level: MEDIUM Description: Zalo Version: 25.1.2 Modules
| |||||||||||||||
| 1140 | "C:\Users\admin\AppData\Local\Programs\Zalo\Zalo-25.1.2\Zalo.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --user-data-dir="C:\Users\admin\AppData\Roaming\ZaloData" --gpu-preferences=UAAAAAAAAADoAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAACQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=2508 --field-trial-handle=1808,i,7565084531684393067,9224958151273354389,131072 --enable-features=JXL --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\Programs\Zalo\Zalo-25.1.2\Zalo.exe | — | Zalo.exe | |||||||||||
User: admin Company: VNG Corp. Integrity Level: MEDIUM Description: Zalo Exit code: 0 Version: 25.1.2 Modules
| |||||||||||||||
| 1220 | "C:\Users\admin\AppData\Local\Programs\Zalo\Zalo-25.1.2\Zalo.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\ZaloData" --app-user-model-id=com.vng.zalo --app-path="C:\Users\admin\AppData\Local\Programs\Zalo\Zalo-25.1.2\resources\app.asar" --no-sandbox --no-zygote --node-integration-in-worker --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3052 --field-trial-handle=1808,i,7565084531684393067,9224958151273354389,131072 --enable-features=JXL --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Programs\Zalo\Zalo-25.1.2\Zalo.exe | — | Zalo.exe | |||||||||||
User: admin Company: VNG Corp. Integrity Level: MEDIUM Description: Zalo Version: 25.1.2 Modules
| |||||||||||||||
| 1864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4220 --field-trial-handle=2476,i,16977655482037235221,18120717862284183719,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
35 854
Read events
35 684
Write events
145
Delete events
25
Modification events
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F0062000000000000000000000001000000F87F0000E091780C | |||
| (PID) Process: | (6328) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6328) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6328) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6328) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6328) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 83643DFA978C2F00 | |||
| (PID) Process: | (6328) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E77AE8FA978C2F00 | |||
| (PID) Process: | (6328) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6328) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (6328) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E1C352FA978C2F00 | |||
Executable files
175
Suspicious files
730
Text files
126
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF137aff.TMP | — | |
MD5:— | SHA256:— | |||
| 6328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF137aff.TMP | — | |
MD5:— | SHA256:— | |||
| 6328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF137b0f.TMP | — | |
MD5:— | SHA256:— | |||
| 6328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF137b0f.TMP | — | |
MD5:— | SHA256:— | |||
| 6328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF137b0f.TMP | — | |
MD5:— | SHA256:— | |||
| 6328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6328 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
98
DNS requests
103
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4444 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4444 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
1804 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
1804 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
4504 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739802949&P2=404&P3=2&P4=M99xKToJwZ5Ul%2fE9Pnzhx%2bMS%2fo1vzj89hzMvB29qnXs5D%2boeowMxAnubF13QltZel%2bDGP4AYXLBq3VXpZYM4EQ%3d%3d | US | — | — | whitelisted |
7636 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
4488 | explorer.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEA%2B4p0C5FY0DUUO8WdnwQCk%3D | US | binary | 312 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5064 | SearchApp.exe | 184.86.251.4:443 | edgeservices.bing.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4444 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4444 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6696 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6328 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6696 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
zalo.me |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
res-download-pc.zadn.vn |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4516 | ZaloSetup-25.1.2.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
4516 | ZaloSetup-25.1.2.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
4516 | ZaloSetup-25.1.2.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
4516 | ZaloSetup-25.1.2.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
4516 | ZaloSetup-25.1.2.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
Process | Message |
|---|---|
ZaloCap.exe | Logger configuration: "CONF: :/texts/log_conf.txt # LOG_LEVEL: ALL # LOG_FILES: C:/Users/admin/AppData/Roaming/ZaloApp/scrshot.log|StdOutput\n\twith pattern: #TIME | #MESSAGE"
|
ZaloCap.exe | Logger configuration after reading settings: "CONF: :/texts/log_conf.txt # LOG_LEVEL: ALL # LOG_FILES: C:/Users/admin/AppData/Roaming/ZaloApp/scrshot.log|StdOutput\n\twith pattern: #TIME | #MESSAGE"
|
ZaloCap.exe | " 2025/02/13 - 08:19:56:735 | App started"
|
ZaloCap.exe | " 2025/02/13 - 08:19:56:799 | class NS_ScrollCaptureApp::TrickLoaderThread::run | Start"
|
ZaloCap.exe | " 2025/02/13 - 08:19:56:799 | class MainWindow::connectEvents | Connecting communication module & app ..."
|
ZaloCap.exe | param = ("C:\\Users\\admin\\AppData\\Local\\Programs\\Zalo\\Zalo-25.1.2\\plugins\\capture\\ZaloCap.exe", "zalo2017", "C:\\Users\\admin\\AppData\\Roaming\\ZaloData\\cal")
|
ZaloCap.exe | " 2025/02/13 - 08:20:02:650 | class NS_ScrollCaptureApp::TrickLoaderThread::run | End"
|