| File name: | e426b6613ee3bff6f9549ebfbf3e1b20.exe |
| Full analysis: | https://app.any.run/tasks/54fc3358-08a6-4aa9-bc22-689f65c3df1b |
| Verdict: | Malicious activity |
| Threats: | DarkGate is a loader, which possesses extensive functionality, ranging from keylogging to crypto mining. Written in Delphi, this malware is known for the use of AutoIT scripts in its infection process. Thanks to this malicious software’s versatile architecture, it is widely used by established threat actors. |
| Analysis date: | May 18, 2024, 13:06:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | E426B6613EE3BFF6F9549EBFBF3E1B20 |
| SHA1: | 2E58E0571E9489859B9EB18C73ECE2625F3A33C7 |
| SHA256: | E51705A1121ABD62D9BC3CA5D0F40BCCF1E4F3804F35666758162A9A2E57B331 |
| SSDEEP: | 49152:XlnYP0977nrWszwjPneBYrpd6R8O4V9fE1S+zOCs3nq7IgGgz6mmTnLM8fEftUf8:XlYErW8QfeBYrev4Vt+SIOClkgGgz63R |
MALICIOUS
Drops the executable file immediately after the start
- e426b6613ee3bff6f9549ebfbf3e1b20.exe (PID: 1492)
- powershell.exe (PID: 4920)
- armsvc.exe (PID: 2252)
- GoogleUpdate.exe (PID: 7860)
- updater.exe (PID: 1276)
- updater.exe (PID: 2796)
Creates a writable file in the system directory
- armsvc.exe (PID: 2252)
- msdtc.exe (PID: 6772)
Connects to the CnC server
- armsvc.exe (PID: 2252)
Actions looks like stealing of personal data
- armsvc.exe (PID: 2252)
- DiagnosticsHub.StandardCollector.Service.exe (PID: 4004)
- SearchIndexer.exe (PID: 7272)
SUSPICIOUS
Executes as Windows Service
- armsvc.exe (PID: 2252)
- FlashPlayerUpdateService.exe (PID: 4108)
- AppVClient.exe (PID: 5836)
- alg.exe (PID: 5060)
- MicrosoftEdgeUpdate.exe (PID: 2764)
- DiagnosticsHub.StandardCollector.Service.exe (PID: 4004)
- GameInputSvc.exe (PID: 6372)
- FXSSVC.exe (PID: 6256)
- GoogleUpdate.exe (PID: 6624)
- maintenanceservice.exe (PID: 6708)
- msdtc.exe (PID: 6772)
- PerceptionSimulationService.exe (PID: 7056)
- perfhost.exe (PID: 7132)
- PSEXESVC.exe (PID: 4944)
- Locator.exe (PID: 6344)
- SensorDataService.exe (PID: 6480)
- snmptrap.exe (PID: 2288)
- Spectrum.exe (PID: 3808)
- ssh-agent.exe (PID: 6736)
- TieringEngineService.exe (PID: 6628)
- AgentService.exe (PID: 6288)
- wbengine.exe (PID: 4988)
- VSSVC.exe (PID: 920)
- vds.exe (PID: 5392)
- WmiApSrv.exe (PID: 7196)
- MicrosoftEdgeUpdate.exe (PID: 7460)
- GoogleUpdate.exe (PID: 7860)
- updater.exe (PID: 7772)
- updater.exe (PID: 2796)
- updater.exe (PID: 4288)
Executable content was dropped or overwritten
- e426b6613ee3bff6f9549ebfbf3e1b20.exe (PID: 1492)
- armsvc.exe (PID: 2252)
- GoogleUpdate.exe (PID: 7860)
- updater.exe (PID: 1276)
- updater.exe (PID: 2796)
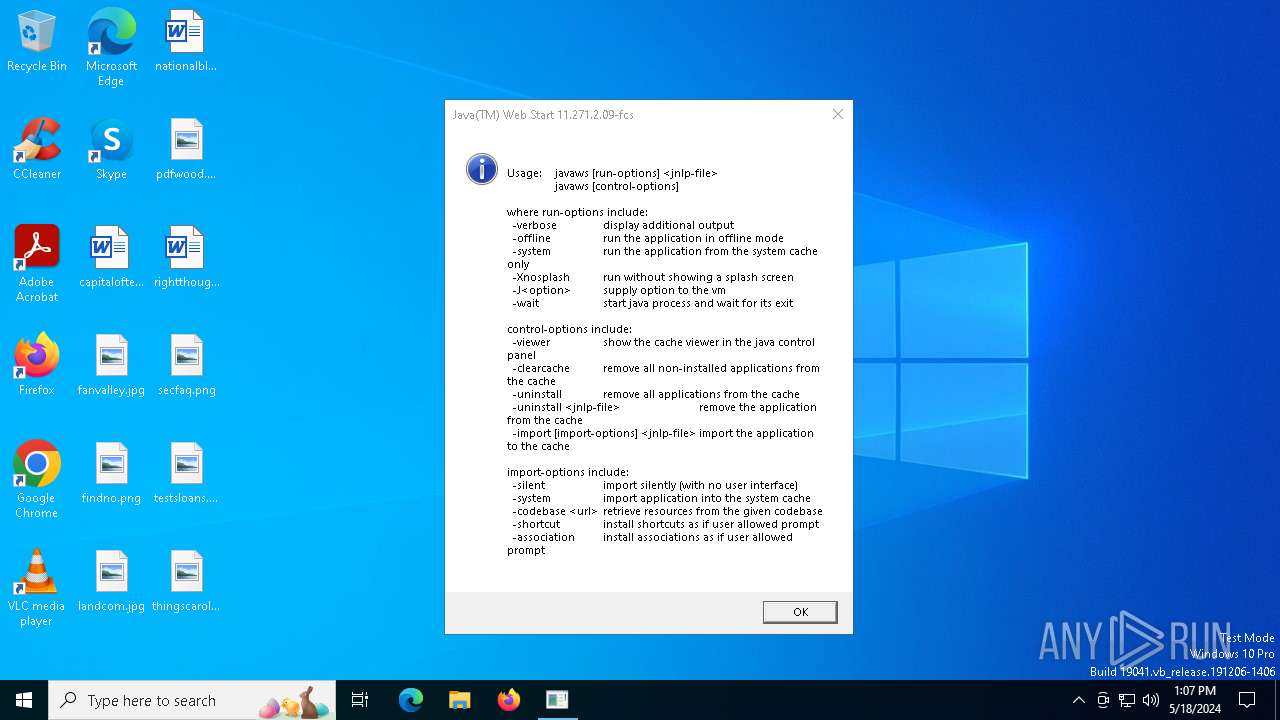
Checks for Java to be installed
- e426b6613ee3bff6f9549ebfbf3e1b20.exe (PID: 1492)
Process drops legitimate windows executable
- e426b6613ee3bff6f9549ebfbf3e1b20.exe (PID: 1492)
- armsvc.exe (PID: 2252)
Application launched itself
- MicrosoftEdgeUpdate.exe (PID: 2764)
- MicrosoftEdgeUpdate.exe (PID: 5548)
- GameInputSvc.exe (PID: 6372)
- GoogleUpdate.exe (PID: 6624)
- GoogleUpdate.exe (PID: 6764)
- MicrosoftEdgeUpdate.exe (PID: 7460)
- updater.exe (PID: 1276)
- GoogleUpdate.exe (PID: 7860)
- updater.exe (PID: 7772)
- updater.exe (PID: 7832)
- updater.exe (PID: 2796)
- updater.exe (PID: 4288)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6216)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6404)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6472)
- MicrosoftEdgeUpdate.exe (PID: 6160)
Contacting a server suspected of hosting an CnC
- armsvc.exe (PID: 2252)
INFO
Checks supported languages
- e426b6613ee3bff6f9549ebfbf3e1b20.exe (PID: 1492)
- armsvc.exe (PID: 2252)
- javaws.exe (PID: 3644)
- FlashPlayerUpdateService.exe (PID: 4108)
- MicrosoftEdgeUpdate.exe (PID: 2764)
- MicrosoftEdgeUpdate.exe (PID: 5548)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6216)
- MicrosoftEdgeUpdate.exe (PID: 6160)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6404)
- elevation_service.exe (PID: 6504)
- MicrosoftEdgeUpdate.exe (PID: 6588)
- GoogleUpdate.exe (PID: 6624)
- maintenanceservice.exe (PID: 6708)
- GoogleUpdate.exe (PID: 6828)
- GoogleUpdate.exe (PID: 6764)
- GoogleCrashHandler.exe (PID: 6868)
- GoogleCrashHandler64.exe (PID: 6904)
- GoogleUpdate.exe (PID: 6928)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6472)
- PSEXESVC.exe (PID: 4944)
- elevation_service.exe (PID: 6664)
- ssh-agent.exe (PID: 6736)
- MicrosoftEdgeUpdate.exe (PID: 7460)
- GoogleUpdate.exe (PID: 7860)
- MicrosoftEdgeUpdate.exe (PID: 7572)
- UpdaterSetup.exe (PID: 7404)
- GoogleUpdate.exe (PID: 7412)
- updater.exe (PID: 7664)
- updater.exe (PID: 1276)
- updater.exe (PID: 7772)
- updater.exe (PID: 7616)
- updater.exe (PID: 824)
- updater.exe (PID: 7832)
- updater.exe (PID: 2796)
- updater.exe (PID: 1788)
- updater.exe (PID: 4288)
- updater.exe (PID: 6380)
Creates files or folders in the user directory
- e426b6613ee3bff6f9549ebfbf3e1b20.exe (PID: 1492)
- GoogleUpdate.exe (PID: 6828)
Reads the computer name
- e426b6613ee3bff6f9549ebfbf3e1b20.exe (PID: 1492)
- armsvc.exe (PID: 2252)
- FlashPlayerUpdateService.exe (PID: 4108)
- MicrosoftEdgeUpdate.exe (PID: 5548)
- MicrosoftEdgeUpdate.exe (PID: 2764)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6216)
- MicrosoftEdgeUpdate.exe (PID: 6160)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6472)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6404)
- elevation_service.exe (PID: 6504)
- MicrosoftEdgeUpdate.exe (PID: 6588)
- elevation_service.exe (PID: 6664)
- GoogleUpdate.exe (PID: 6624)
- maintenanceservice.exe (PID: 6708)
- GoogleUpdate.exe (PID: 6764)
- GoogleUpdate.exe (PID: 6828)
- GoogleCrashHandler.exe (PID: 6868)
- GoogleUpdate.exe (PID: 6928)
- GoogleCrashHandler64.exe (PID: 6904)
- PSEXESVC.exe (PID: 4944)
- ssh-agent.exe (PID: 6736)
- MicrosoftEdgeUpdate.exe (PID: 7460)
- MicrosoftEdgeUpdate.exe (PID: 7572)
- GoogleUpdate.exe (PID: 7860)
- GoogleUpdate.exe (PID: 7412)
- updater.exe (PID: 7616)
- updater.exe (PID: 7832)
- updater.exe (PID: 7772)
- updater.exe (PID: 824)
- updater.exe (PID: 2796)
- updater.exe (PID: 1788)
- updater.exe (PID: 4288)
- updater.exe (PID: 6380)
- updater.exe (PID: 1276)
The executable file from the user directory is run by the Powershell process
- e426b6613ee3bff6f9549ebfbf3e1b20.exe (PID: 1492)
Checks proxy server information
- e426b6613ee3bff6f9549ebfbf3e1b20.exe (PID: 1492)
Creates files in the program directory
- FXSSVC.exe (PID: 6256)
- maintenanceservice.exe (PID: 6708)
- GoogleUpdate.exe (PID: 6624)
- GoogleUpdate.exe (PID: 6828)
- GoogleUpdate.exe (PID: 6764)
- GoogleUpdate.exe (PID: 6928)
- SearchIndexer.exe (PID: 7272)
- GoogleUpdate.exe (PID: 7860)
- UpdaterSetup.exe (PID: 7404)
- GoogleUpdate.exe (PID: 7412)
- updater.exe (PID: 1276)
- updater.exe (PID: 7664)
- updater.exe (PID: 2796)
- updater.exe (PID: 4288)
Reads the software policy settings
- GameInputSvc.exe (PID: 6412)
- GoogleUpdate.exe (PID: 6828)
- MicrosoftEdgeUpdate.exe (PID: 7572)
- MicrosoftEdgeUpdate.exe (PID: 7460)
- GoogleUpdate.exe (PID: 7860)
- GoogleUpdate.exe (PID: 7412)
Executes as Windows Service
- elevation_service.exe (PID: 6504)
- elevation_service.exe (PID: 6664)
- SearchIndexer.exe (PID: 7272)
Checks transactions between databases Windows and Oracle
- msdtc.exe (PID: 6772)
Reads the time zone
- TieringEngineService.exe (PID: 6628)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 7572)
Reads the machine GUID from the registry
- GoogleUpdate.exe (PID: 7860)
- GoogleUpdate.exe (PID: 6828)
- GoogleUpdate.exe (PID: 7412)
- updater.exe (PID: 4288)
Process checks whether UAC notifications are on
- updater.exe (PID: 1276)
- updater.exe (PID: 7772)
- updater.exe (PID: 7832)
- updater.exe (PID: 2796)
- updater.exe (PID: 4288)
Reads security settings of Internet Explorer
- SearchProtocolHost.exe (PID: 5244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2020:06:18 07:30:01+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 260608 |
| InitializedDataSize: | 275968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13bf4 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.261.2.12 |
| ProductVersionNumber: | 8.0.2610.12 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Oracle Corporation |
| FileDescription: | Java(TM) Web Start Launcher |
| FileVersion: | 11.261.2.12 |
| FullVersion: | 11.261.2.12 |
| InternalName: | Java(TM) Web Start Launcher |
| LegalCopyright: | Copyright © 2020 |
| OriginalFileName: | javaws.exe |
| ProductName: | Java(TM) Platform SE 8 U261 |
| ProductVersion: | 8.0.2610.12 |
Total processes
188
Monitored processes
63
Malicious processes
7
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 824 | "C:\Program Files (x86)\Google\GoogleUpdater\126.0.6462.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\126.0.6462.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=126.0.6462.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x304,0x308,0x30c,0x300,0x310,0x80965c,0x809668,0x809674 | C:\Program Files (x86)\Google\GoogleUpdater\126.0.6462.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: GoogleUpdater (x86) Version: 126.0.6462.0 Modules
| |||||||||||||||
| 920 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | "C:\WINDOWS\SystemTemp\Google7404_1064113256\bin\updater.exe" --update --system --enable-logging --vmodule=*/chrome/updater/*=2 /sessionid {9D781948-DA9E-44AE-8167-856F8BC8B514} | C:\Windows\SystemTemp\Google7404_1064113256\bin\updater.exe | UpdaterSetup.exe | ||||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: GoogleUpdater (x86) Exit code: 0 Version: 126.0.6462.0 Modules
| |||||||||||||||
| 1492 | "C:\Users\admin\AppData\Local\Temp\e426b6613ee3bff6f9549ebfbf3e1b20.exe" | C:\Users\admin\AppData\Local\Temp\e426b6613ee3bff6f9549ebfbf3e1b20.exe | powershell.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.261.2.12 Modules
| |||||||||||||||
| 1788 | "C:\Program Files (x86)\Google\GoogleUpdater\126.0.6462.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\126.0.6462.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=126.0.6462.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x2f8,0x2fc,0x300,0x2f4,0x304,0x80965c,0x809668,0x809674 | C:\Program Files (x86)\Google\GoogleUpdater\126.0.6462.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: GoogleUpdater (x86) Version: 126.0.6462.0 Modules
| |||||||||||||||
| 2084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2252 | "C:\Program Files (x86)\Common Files\Adobe\ARM\1.0\armsvc.exe" | C:\Program Files (x86)\Common Files\Adobe\ARM\1.0\armsvc.exe | services.exe | ||||||||||||
User: SYSTEM Company: Adobe Inc. Integrity Level: SYSTEM Description: Acrobat Update Service Version: 1.824.460.1042 Modules
| |||||||||||||||
| 2288 | C:\WINDOWS\System32\snmptrap.exe | C:\Windows\System32\snmptrap.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: SNMP Trap Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2764 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /svc | C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.147.37 Modules
| |||||||||||||||
| 2796 | "C:\Program Files (x86)\Google\GoogleUpdater\126.0.6462.0\updater.exe" --system --windows-service --service=update-internal | C:\Program Files (x86)\Google\GoogleUpdater\126.0.6462.0\updater.exe | services.exe | ||||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: GoogleUpdater (x86) Version: 126.0.6462.0 Modules
| |||||||||||||||
Total events
50 511
Read events
45 239
Write events
5 138
Delete events
134
Modification events
| (PID) Process: | (4920) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4920) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4920) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4920) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2252) armsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Adobe\Adobe ARM\1.0\ARM |
| Operation: | write | Name: | iLastSvcSuccess |
Value: 1128703 | |||
| (PID) Process: | (2764) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Integers |
| Operation: | write | Name: | omaha_version |
Value: 1100B90003000100 | |||
| (PID) Process: | (2764) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Booleans |
| Operation: | write | Name: | is_system_install |
Value: 01000000 | |||
| (PID) Process: | (2764) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Counts |
| Operation: | write | Name: | goopdate_main |
Value: 1500000000000000 | |||
| (PID) Process: | (2764) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Counts |
| Operation: | write | Name: | goopdate_constructor |
Value: 1500000000000000 | |||
| (PID) Process: | (2764) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Integers |
| Operation: | write | Name: | windows_major_version |
Value: 0A00000000000000 | |||
Executable files
152
Suspicious files
17
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4920 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | — | |
MD5:— | SHA256:— | |||
| 4920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tlkmtopt.iij.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4920 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1129eb.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 4920 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_md1tr4am.lqe.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1492 | e426b6613ee3bff6f9549ebfbf3e1b20.exe | C:\Program Files (x86)\Common Files\Adobe\ARM\1.0\armsvc.exe | executable | |
MD5:108449299FEA11099726D5A7A29B21D4 | SHA256:02F7C51F44DA0C8DC48A273D25A7AA1B720F2EF73C30A8D86FE27E59B7469572 | |||
| 1492 | e426b6613ee3bff6f9549ebfbf3e1b20.exe | C:\WINDOWS\system32\DiagSvcs\DiagnosticsHub.StandardCollector.Service.exe | executable | |
MD5:AE53AC95A497FEF7429AF1920AE10323 | SHA256:A3A84164B56628327968BBF1FACDB030BF9E6180ABBC11FB42C29681BA5A4242 | |||
| 1492 | e426b6613ee3bff6f9549ebfbf3e1b20.exe | C:\Users\admin\AppData\Roaming\26b799fa89ba8c8f.bin | binary | |
MD5:55BA0C1D314D0ECE25BE38241E668325 | SHA256:49901ED2C4C0C04A50B586672F65238FC63461446B1A62DCF03DBE05775B1232 | |||
| 4920 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:60F008BEB98784C1ACED21D650B0BE1C | SHA256:08499AFE7892C4548D8E62236BC8AD51B522706DF6C28F955EF25D888167AAA8 | |||
| 1492 | e426b6613ee3bff6f9549ebfbf3e1b20.exe | C:\WINDOWS\System32\alg.exe | executable | |
MD5:F42549A2A7F8D66779D6AD9BE165BE28 | SHA256:0C062BE8BE2F72F3372B06C3723A3D76BE3ECF86CA89BF511F9D538A1E212E7F | |||
| 1492 | e426b6613ee3bff6f9549ebfbf3e1b20.exe | C:\WINDOWS\system32\AppVClient.exe | executable | |
MD5:9BB576E4AC9ECA67FB099340E0E7DFBF | SHA256:3D5D03EB2B0BC41989C82A3591733DAD00BA4C0505714982156F38AADC84993B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
270
TCP/UDP connections
41
DNS requests
22
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5140 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1492 | e426b6613ee3bff6f9549ebfbf3e1b20.exe | POST | 200 | 35.91.124.102:80 | http://pywolwnvd.biz/eecrm | unknown | — | — | unknown |
2252 | armsvc.exe | POST | 200 | 18.141.10.107:80 | http://ssbzmoy.biz/yx | unknown | — | — | unknown |
6888 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/update2/adr2fk6rlvrmglkypfvpaazgpfrq_126.0.6462.0/UpdaterSetup.exe | unknown | — | — | unknown |
2252 | armsvc.exe | POST | 200 | 35.91.124.102:80 | http://pywolwnvd.biz/vxjaltwrwkslbudt | unknown | — | — | unknown |
6888 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/update2/adr2fk6rlvrmglkypfvpaazgpfrq_126.0.6462.0/UpdaterSetup.exe | unknown | — | — | unknown |
6888 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/update2/adr2fk6rlvrmglkypfvpaazgpfrq_126.0.6462.0/UpdaterSetup.exe | unknown | — | — | unknown |
2252 | armsvc.exe | POST | 200 | 54.244.188.177:80 | http://cvgrf.biz/tginmsexdb | unknown | — | — | unknown |
— | — | GET | 204 | 172.217.18.14:443 | https://clients2.google.com/service/check2?crx3=true&appid=%7B430FD4D0-B729-4F61-AA34-91526481799D%7D&appversion=1.3.36.372&applang=&machine=1&version=1.3.36.372&userid=&osversion=10.0&servicepack= | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4364 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2384 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5140 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
5944 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
1492 | e426b6613ee3bff6f9549ebfbf3e1b20.exe | 35.91.124.102:80 | pywolwnvd.biz | AMAZON-02 | US | unknown |
2252 | armsvc.exe | 35.91.124.102:80 | pywolwnvd.biz | AMAZON-02 | US | unknown |
5140 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
pywolwnvd.biz |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
ssbzmoy.biz |
| unknown |
clients2.google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
msedge.api.cdp.microsoft.com |
| whitelisted |
update.googleapis.com |
| unknown |
geo.prod.do.dsp.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2184 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2184 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2252 | armsvc.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value Snkz |
2184 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2252 | armsvc.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value btst |
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
— | — | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value Snkz |
— | — | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value btst |
2184 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2 ETPRO signatures available at the full report