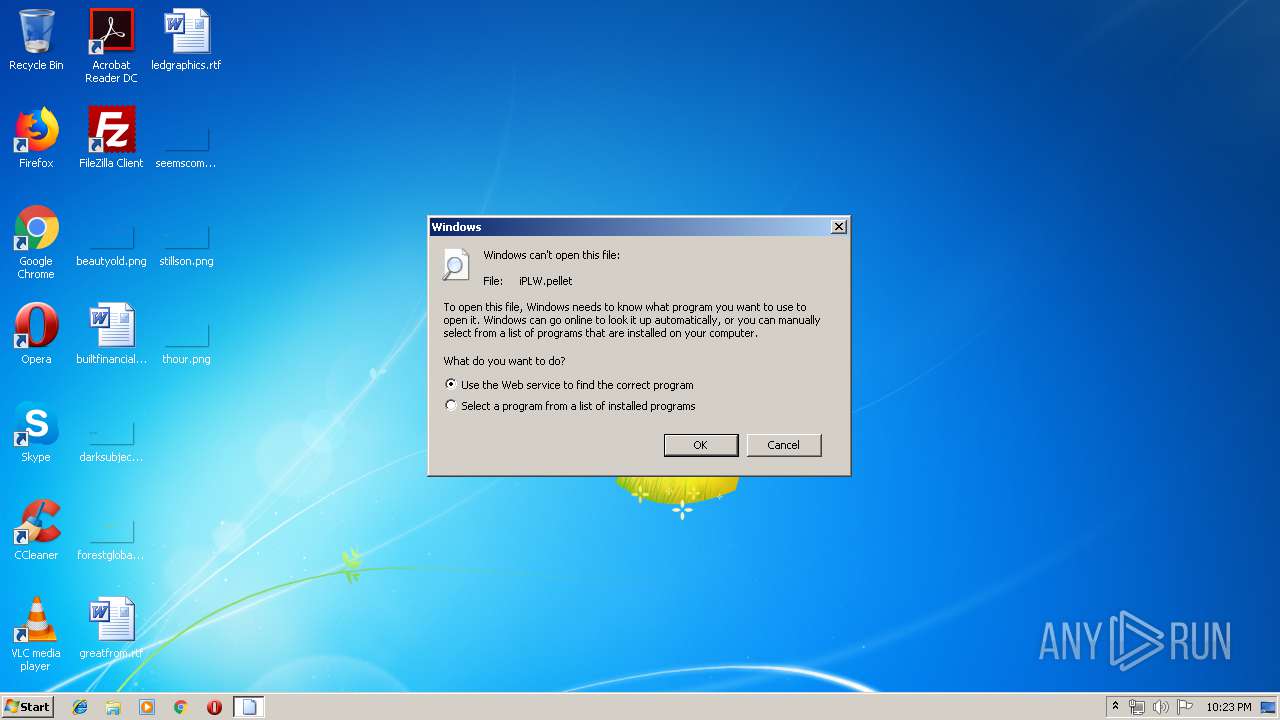
| File name: | iPLW.pellet |
| Full analysis: | https://app.any.run/tasks/aff0f687-eeaa-4a32-a54f-4ea86ebdeed3 |
| Verdict: | No threats detected |
| Analysis date: | June 20, 2019, 21:23:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (console) Intel 80386, for MS Windows |
| MD5: | 696023F6D2D5F712E5EDC8903BB52A56 |
| SHA1: | FF104561E4C99477BE8EFD565170191224AC4DDD |
| SHA256: | E51641D116627618A145ED6BA17AE2AD14BD1BEA2E652AE7109B8C1001FEC60A |
| SSDEEP: | 12288:JQmSDZBFbAIVLuMyxKcuaJ5y07McJsVmhAT2EMP+yupHJnbn:JQ4xKcTo07EVYs2xEppbn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | DOS Executable Generic (100) |
|---|
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 03-Apr-2013 21:48:56 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x00E8 |
| Pages in file: | 0x0000 |
| Relocations: | 0x5B00 |
| Size of header: | 0x4552 |
| Min extra paragraphs: | 0x8955 |
| Max extra paragraphs: | 0x81E5 |
| Initial SS value: | 0x37C3 |
| Initial SP value: | 0x0015 |
| Checksum: | 0xFF00 |
| Initial IP value: | 0x89D3 |
| Initial CS value: | 0x57C3 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x680A |
| OEM information: | 0x0005 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Apr-2013 21:48:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000759E6 | 0x00075A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67757 |
.rdata | 0x00077000 | 0x000262E5 | 0x00026400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.94662 |
.data | 0x0009E000 | 0x00016EE8 | 0x00011800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.19369 |
.reloc | 0x000B5000 | 0x00009AA2 | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.83104 |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
WININET.dll |
WS2_32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
Init | 1 | 0x000015DC |
_ReflectiveLoader@0 | 2 | 0x0000213E |
buffer_from_file | 3 | 0x0005B621 |
buffer_to_file | 4 | 0x0005B6F3 |
channel_close | 5 | 0x000622A0 |
channel_create | 6 | 0x00062453 |
channel_create_datagram | 7 | 0x0006250B |
channel_create_pool | 8 | 0x00062551 |
channel_create_stream | 9 | 0x000624C5 |
channel_default_io_handler | 10 | 0x000623DB |
Total processes
31
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2796 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\iPLW.pellet | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report