| File name: | OOSU10.exe |
| Full analysis: | https://app.any.run/tasks/c01c7823-84d4-4da4-95c6-396fc3f5d112 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 22:44:33 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 437A32B530187A8684C2DD0A6F54CDBE |
| SHA1: | B4E70E5F59416BCCADFBA4913CFD801617D1EFA5 |
| SHA256: | E4FDC26DC9A65094777A7C1B168D9FDE4D2DC75F67422913E87A5E46FD9DF533 |
| SSDEEP: | 49152:QuE6xfEyI1avNJjJwJNJ31bQyEydIoaXMsb8ka9exAmNNXbl3xf4jF6ZjiVDSdNO:QfkXMsb8kacBY4ZjiodNMNTEoekp84Ei |
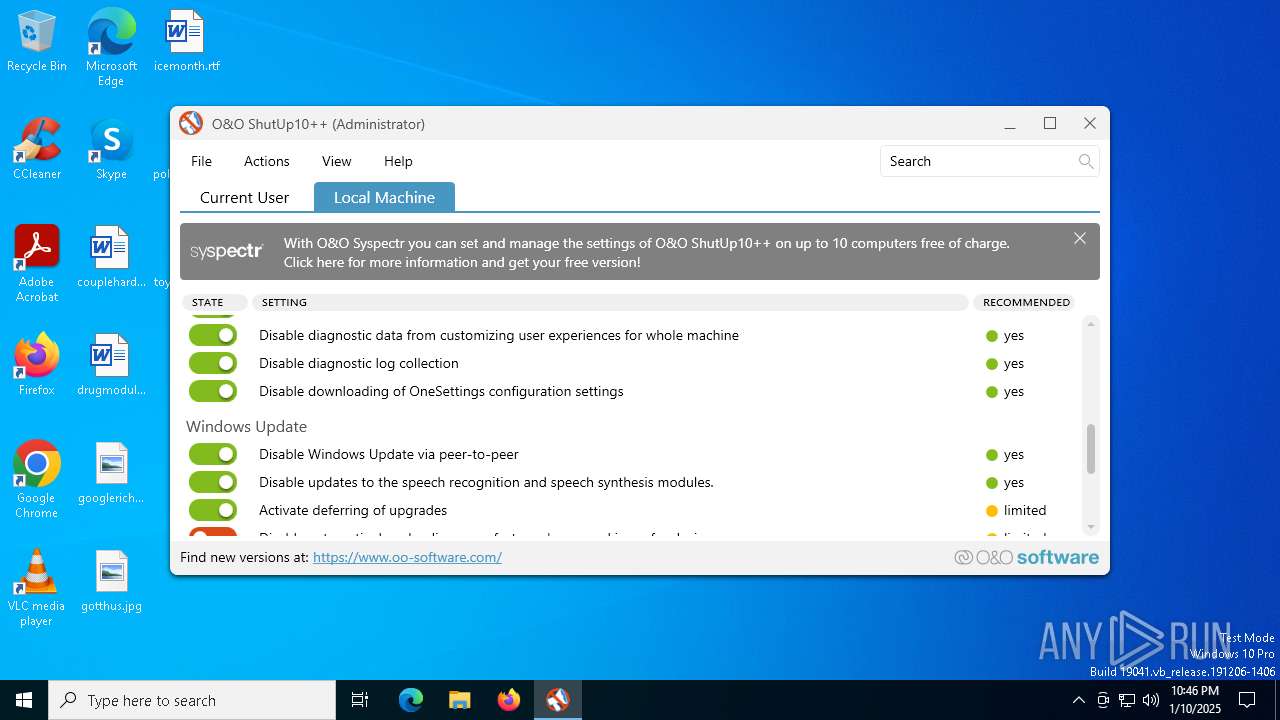
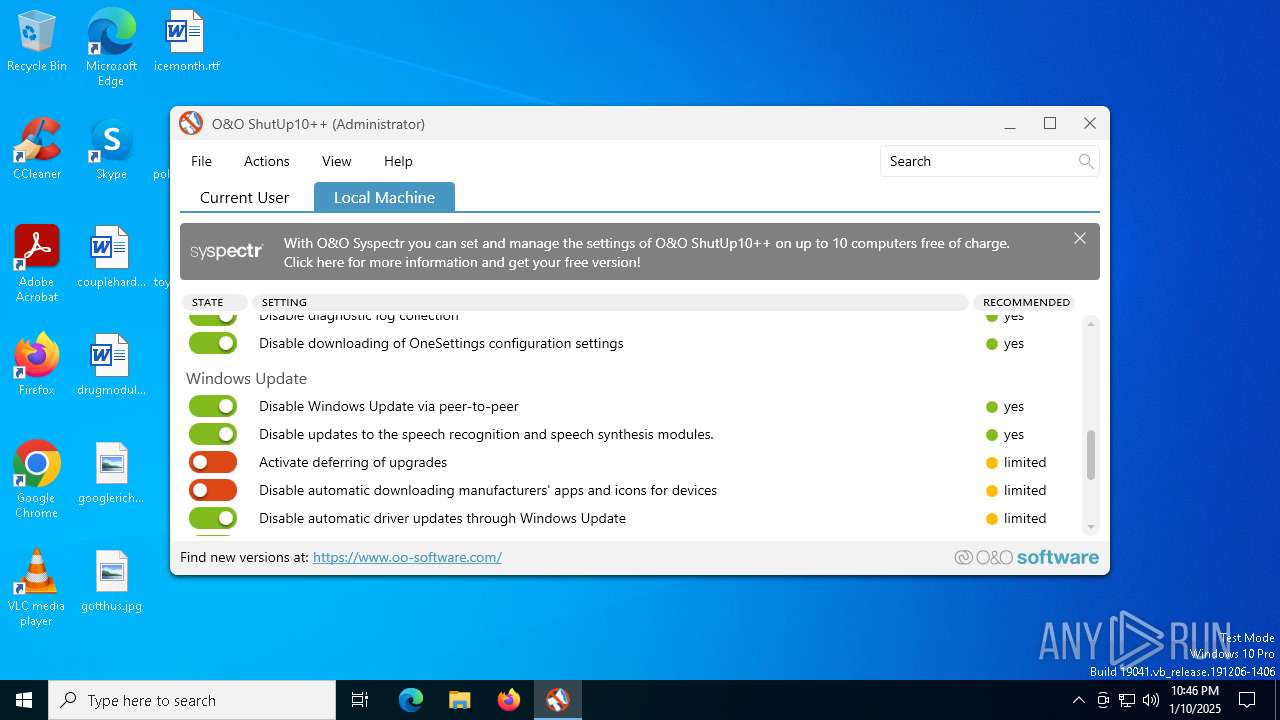
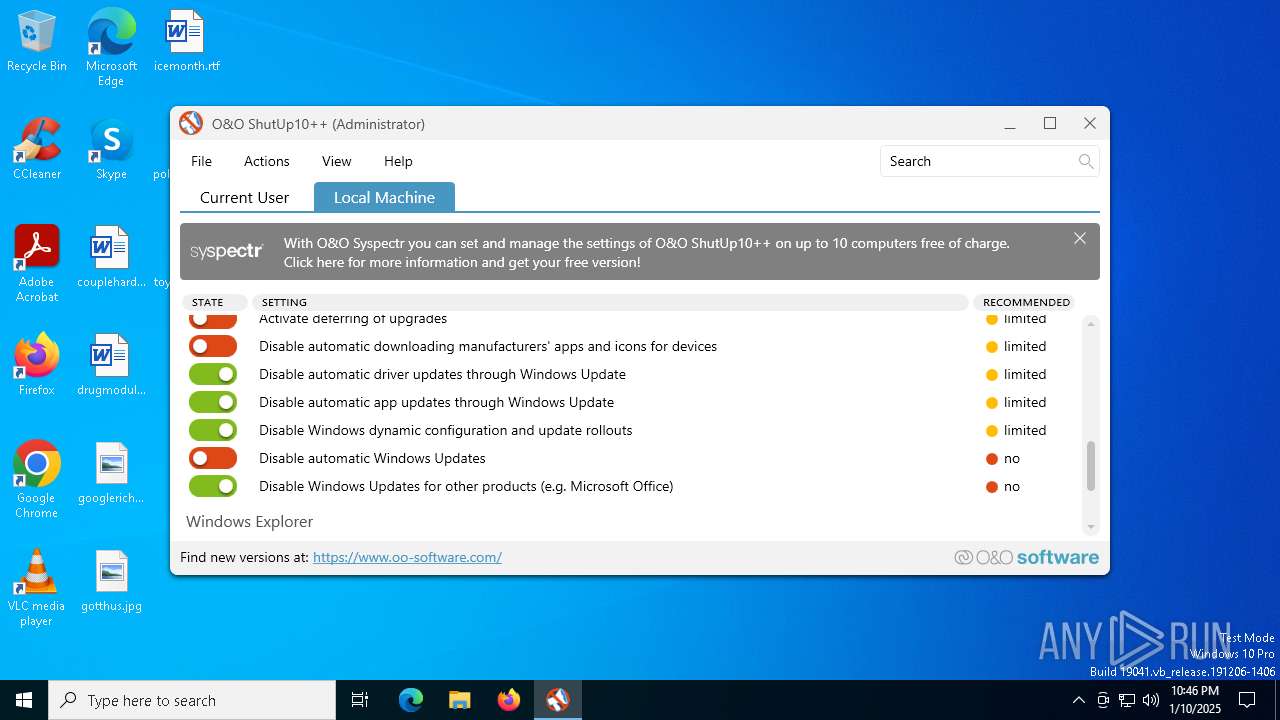
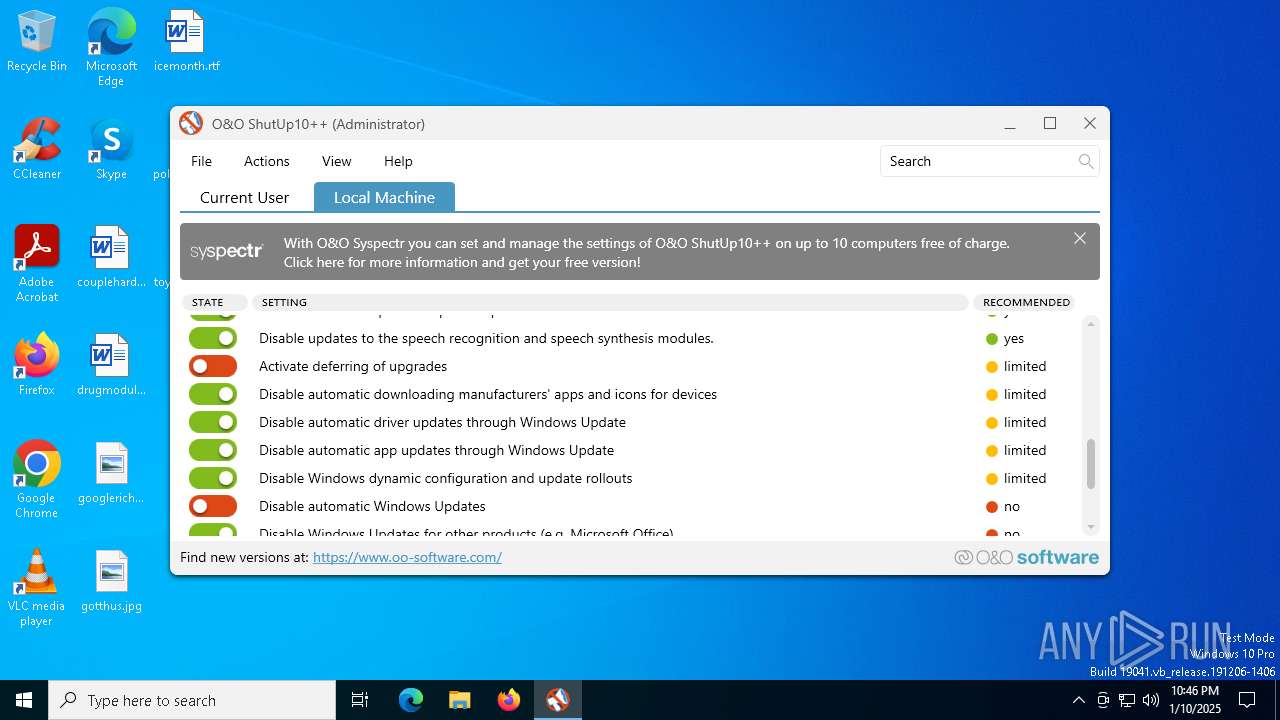
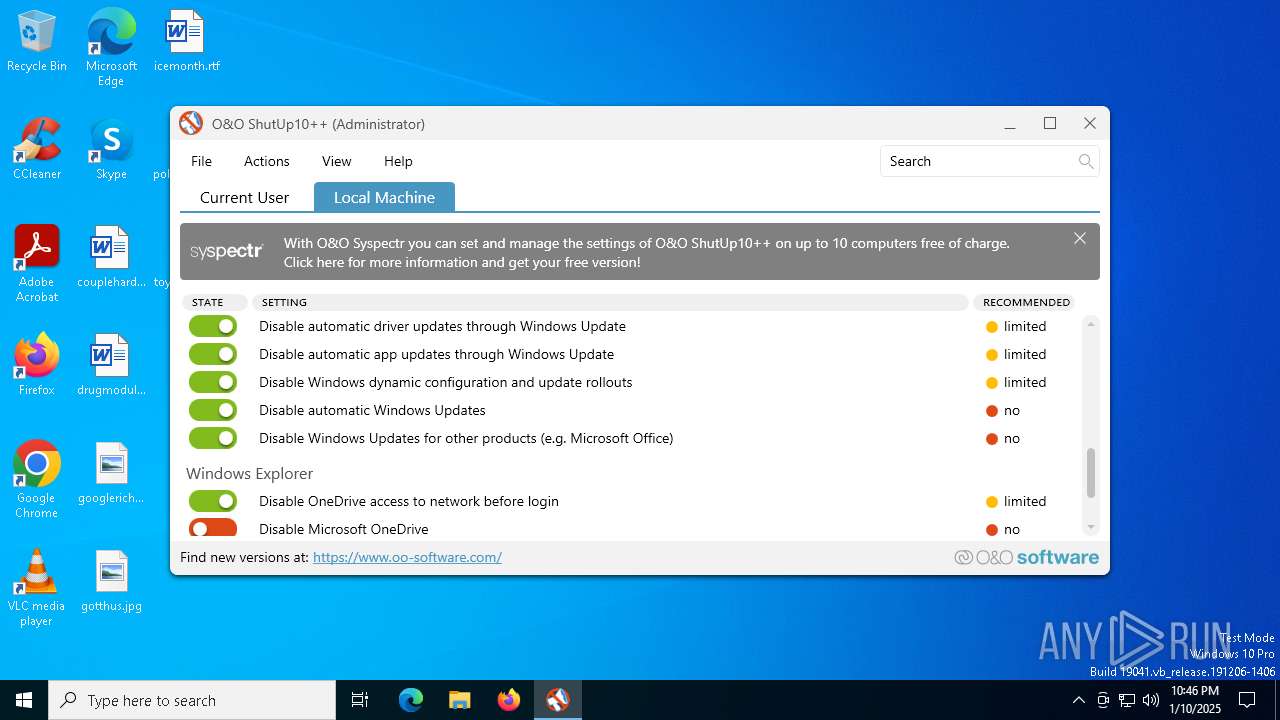
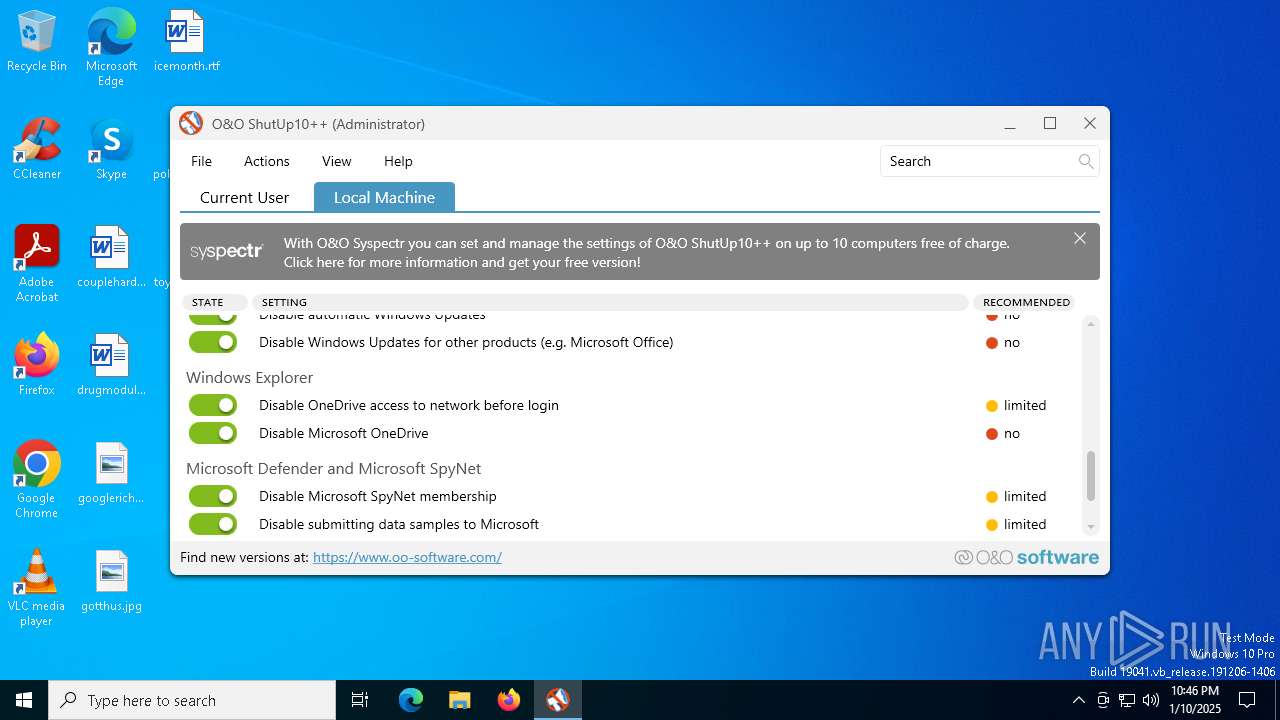
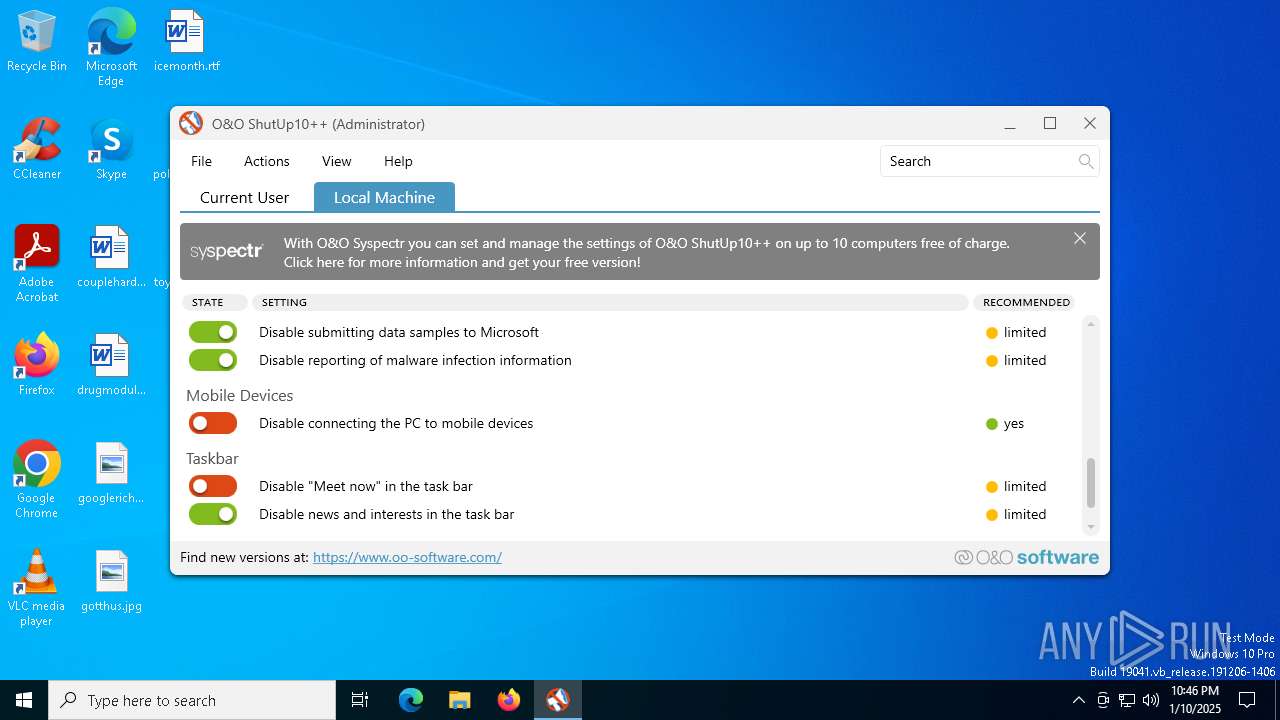
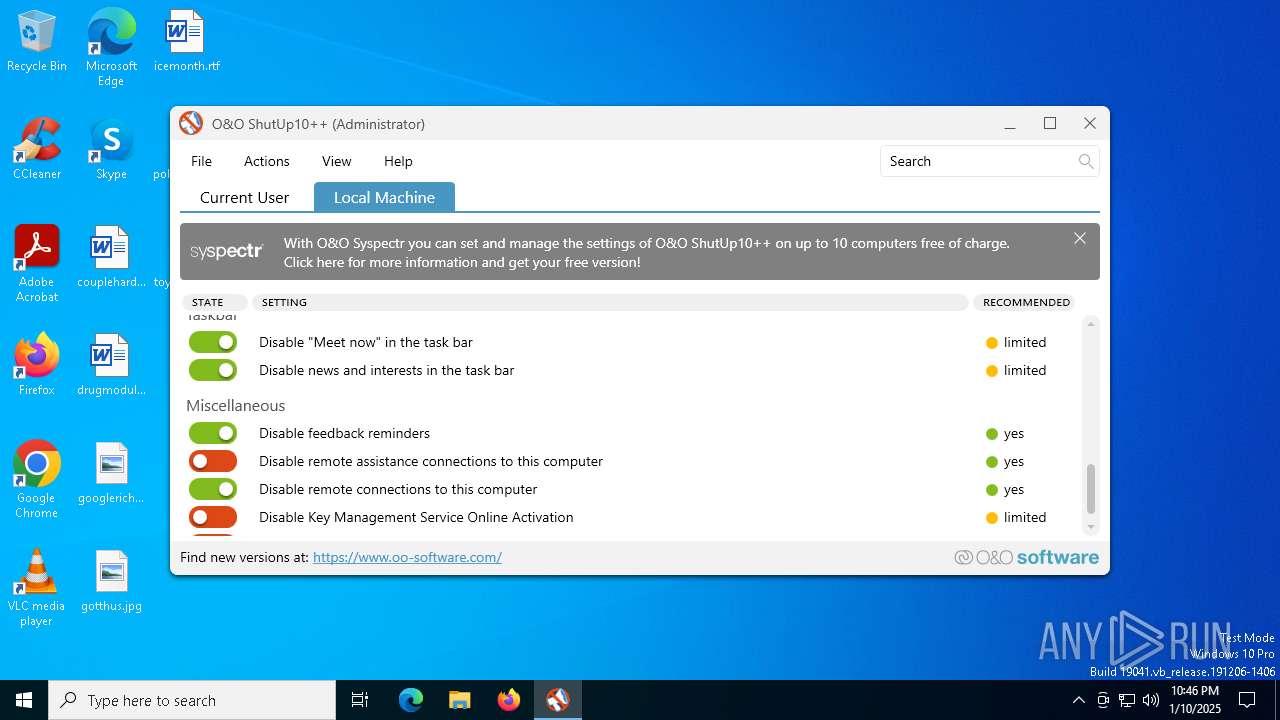
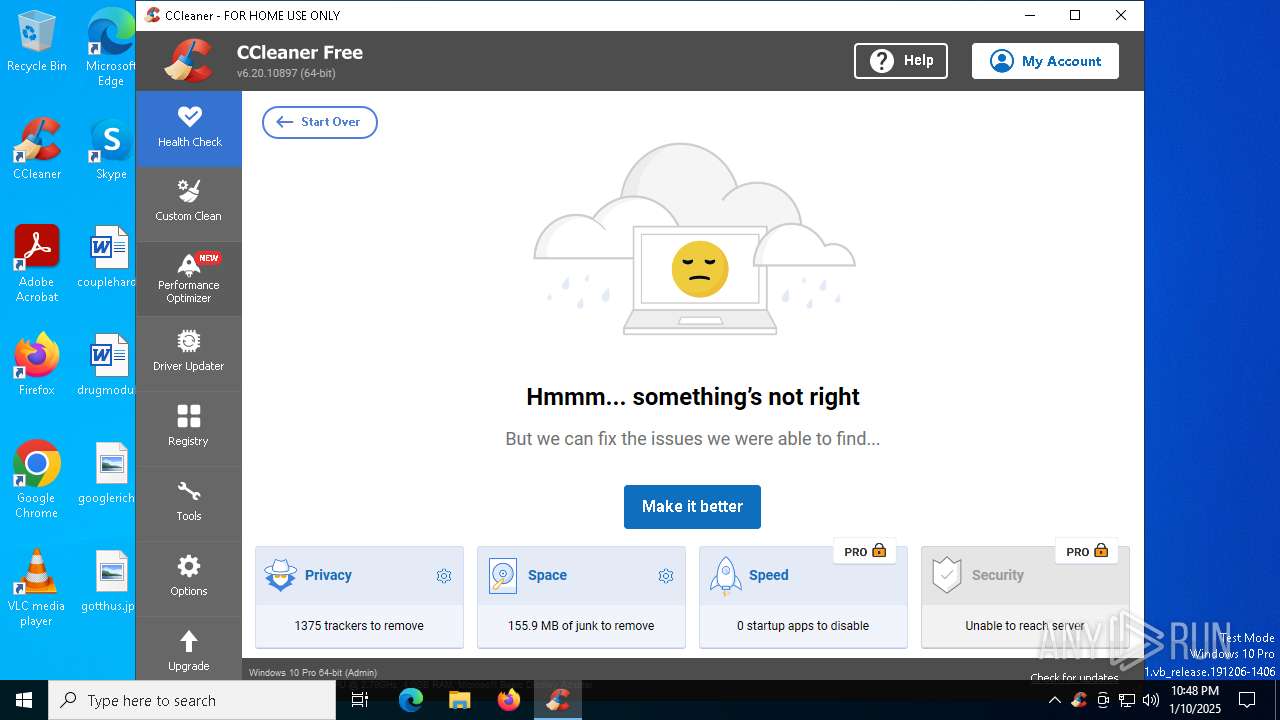
MALICIOUS
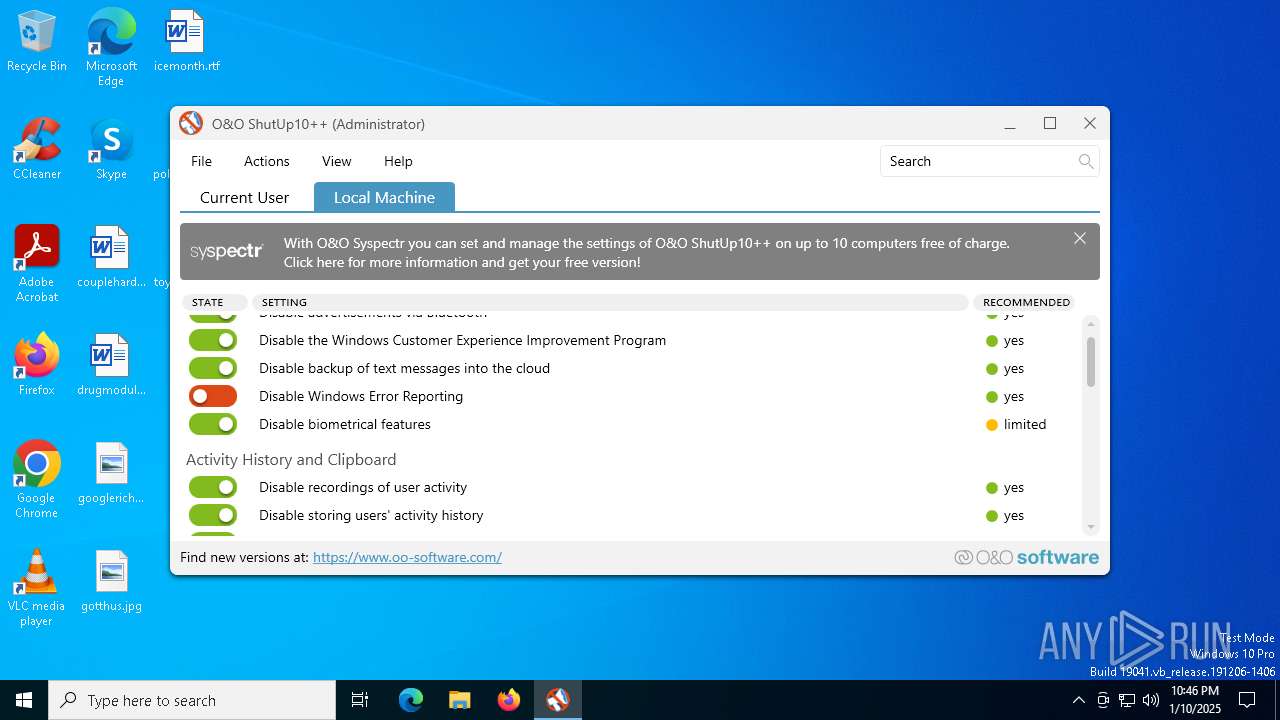
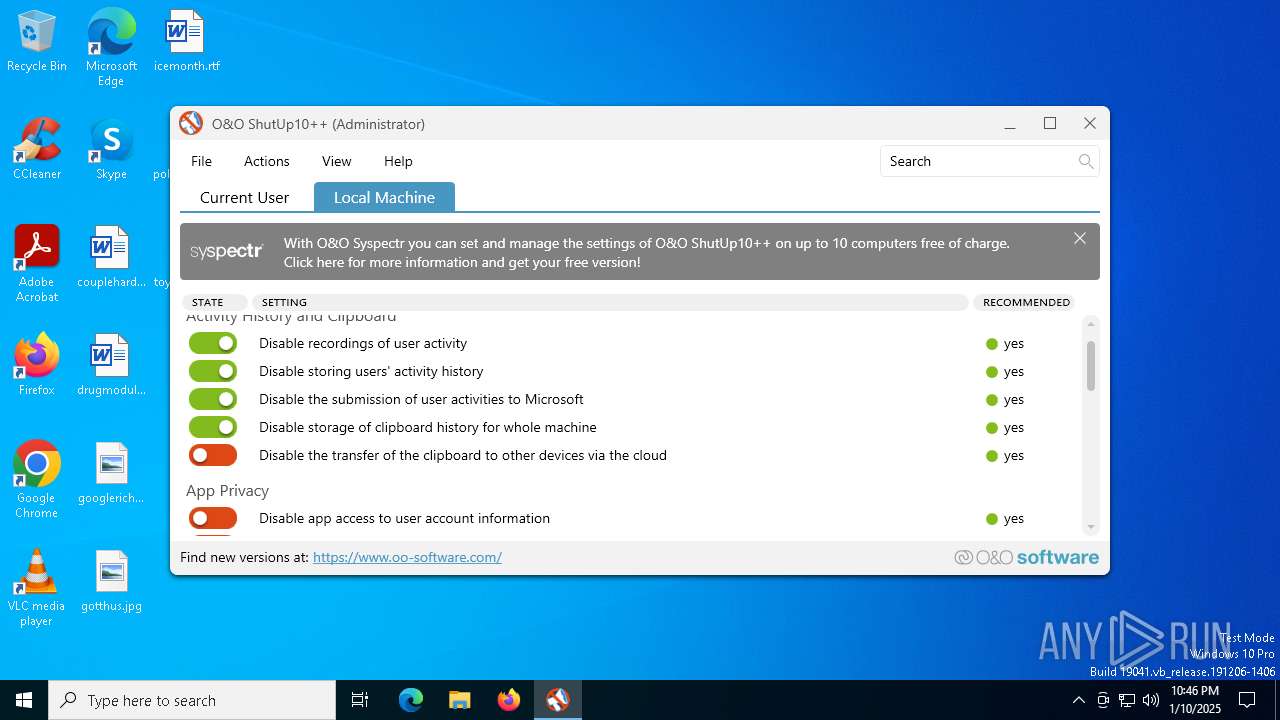
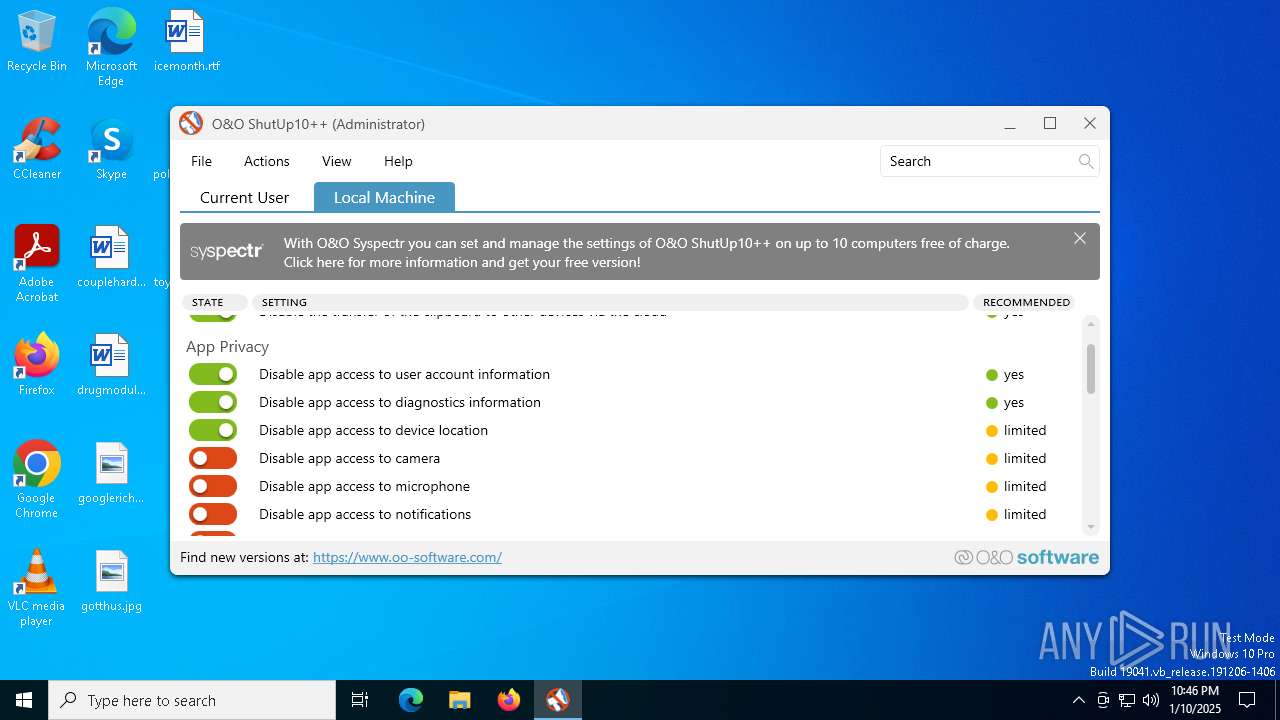
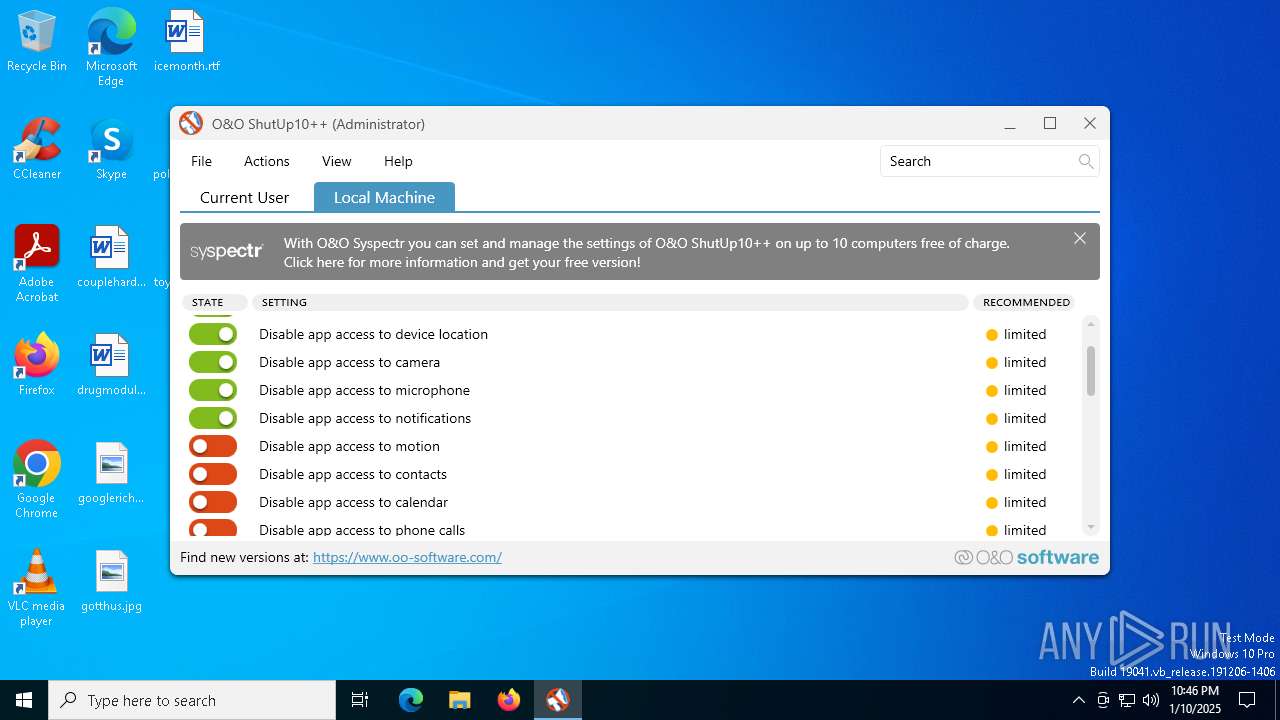
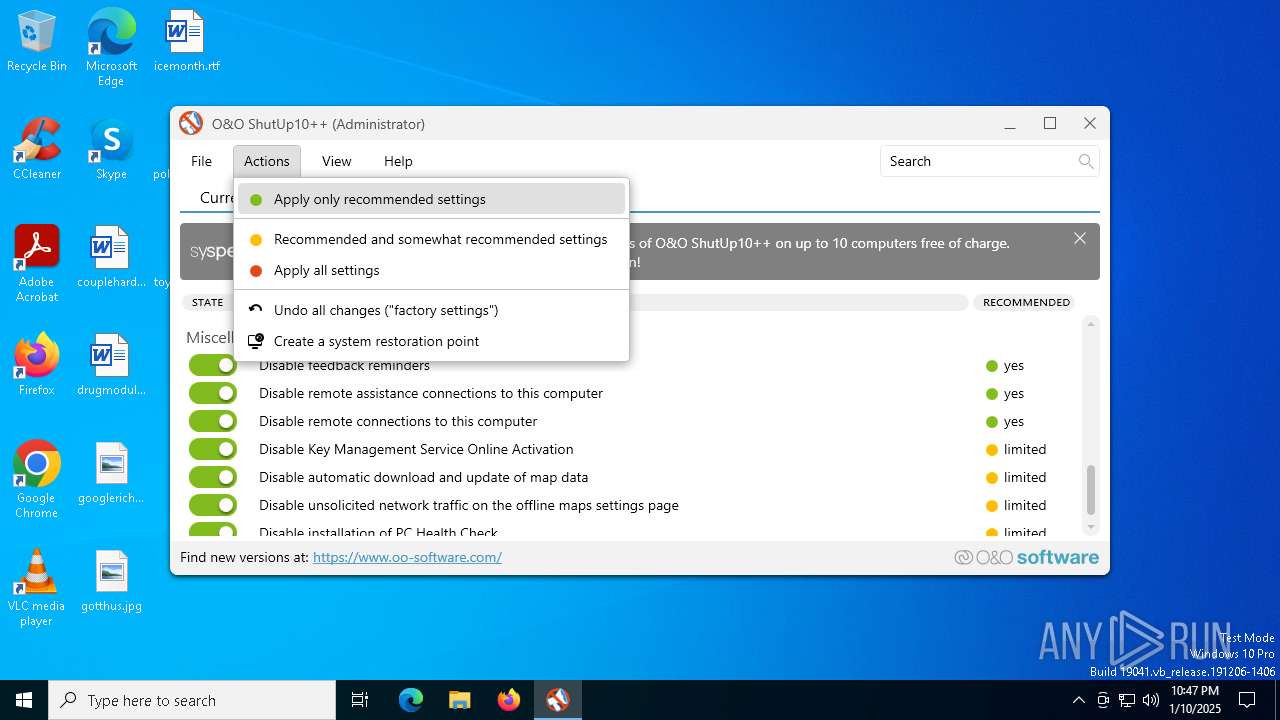
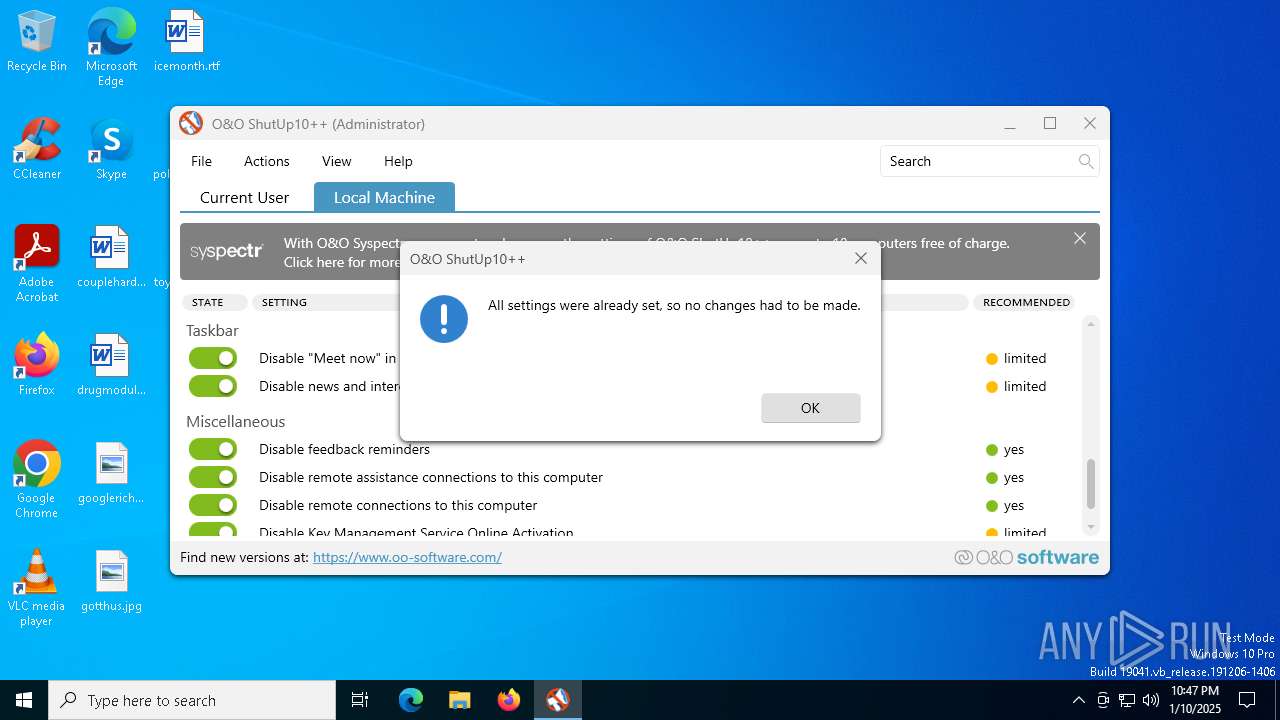
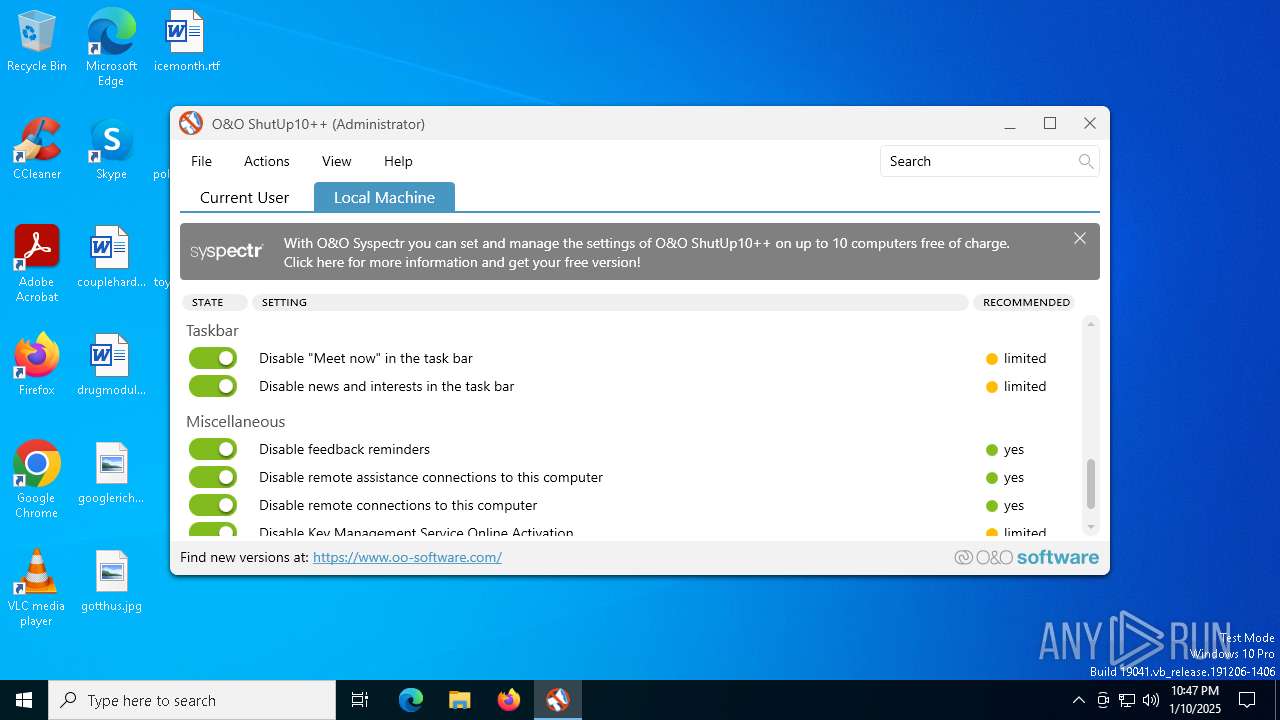
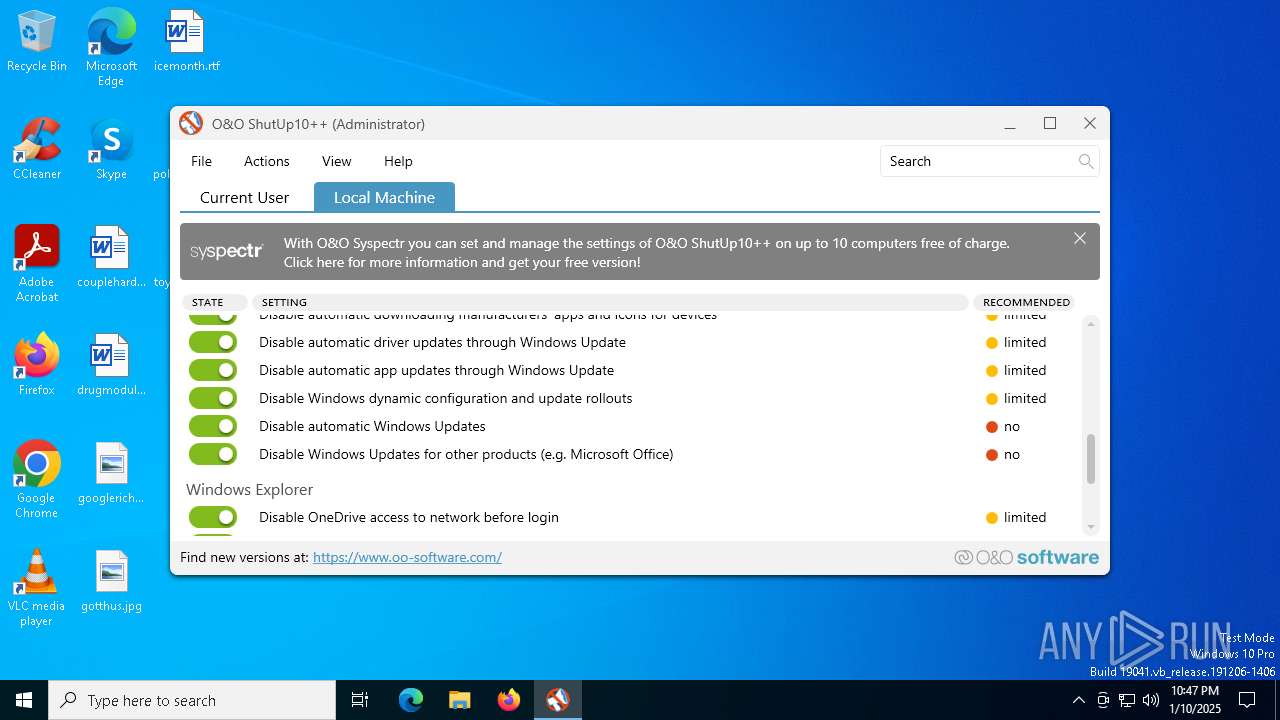
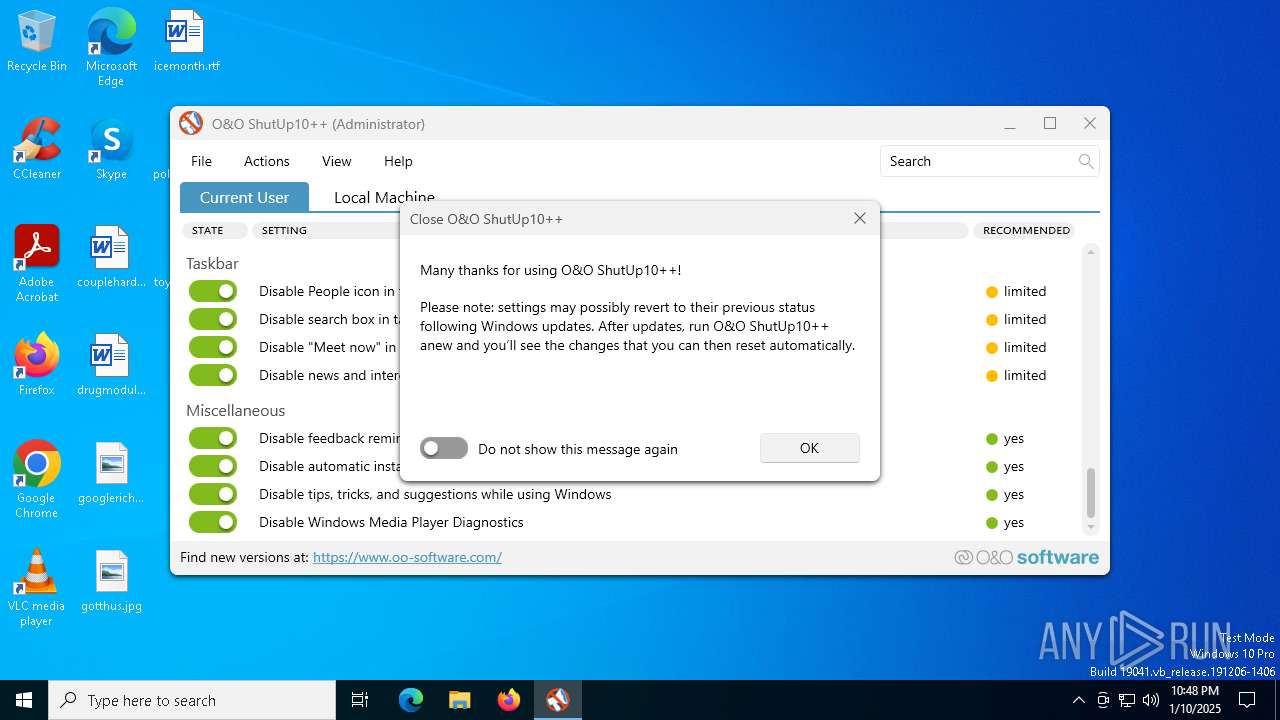
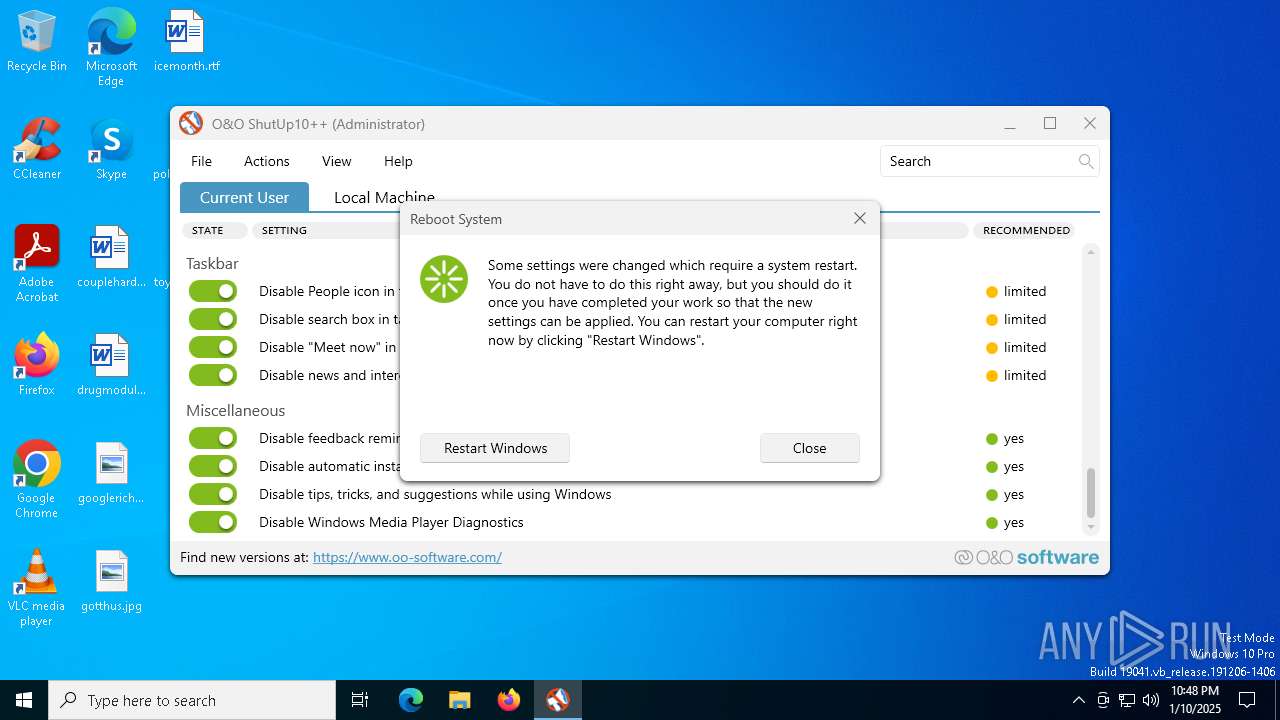
Changes the Windows auto-update feature
- OOSU10.exe (PID: 5092)
Creates or modifies Windows services
- OOSU10.exe (PID: 5092)
Changes the autorun value in the registry
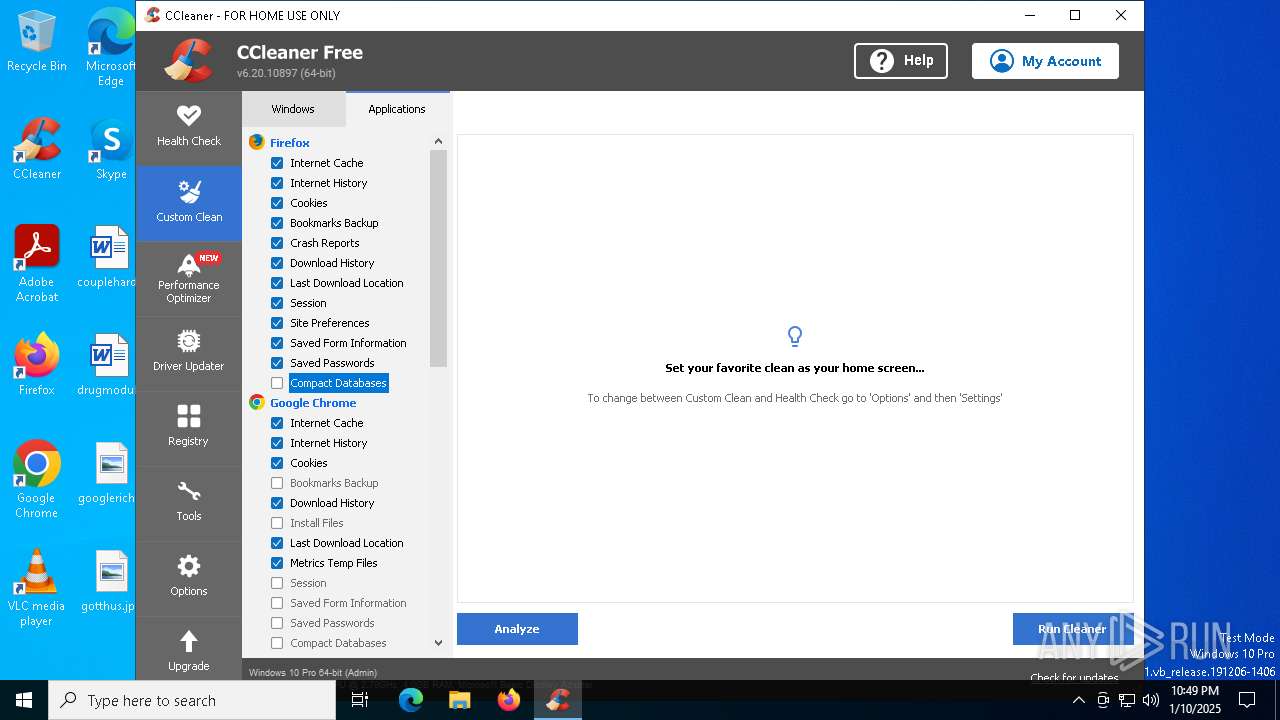
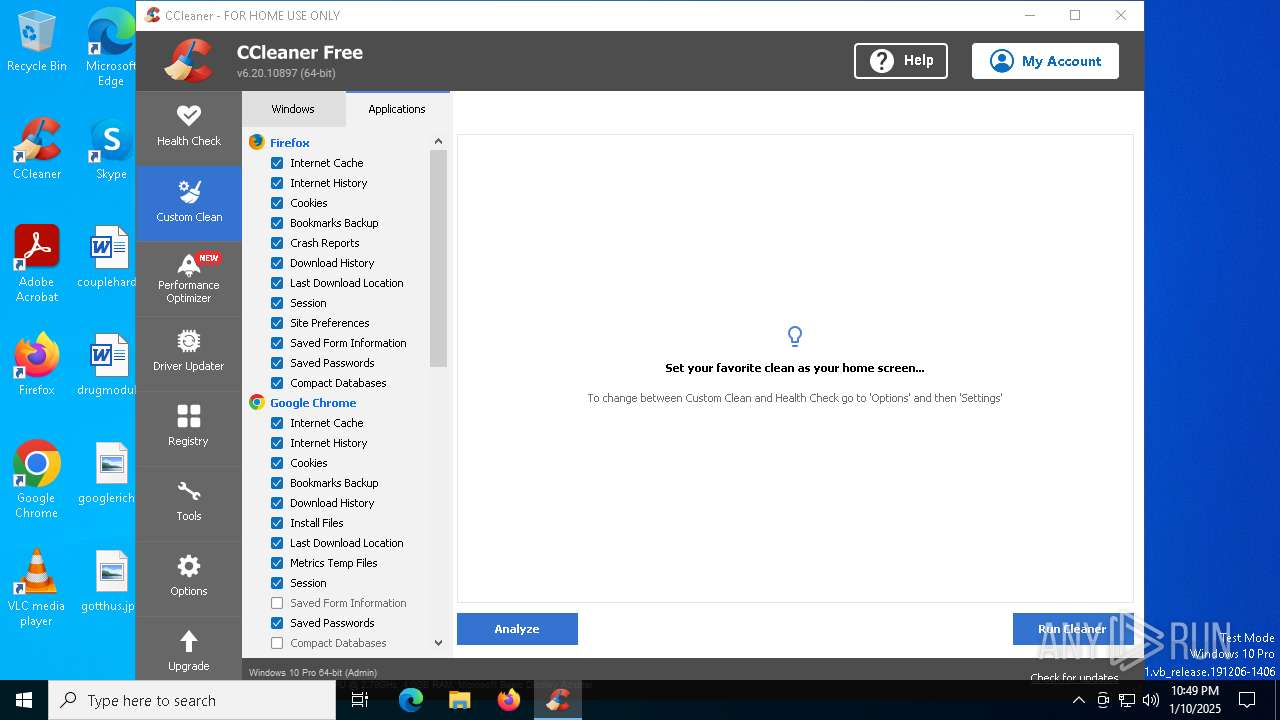
- CCleaner64.exe (PID: 5592)
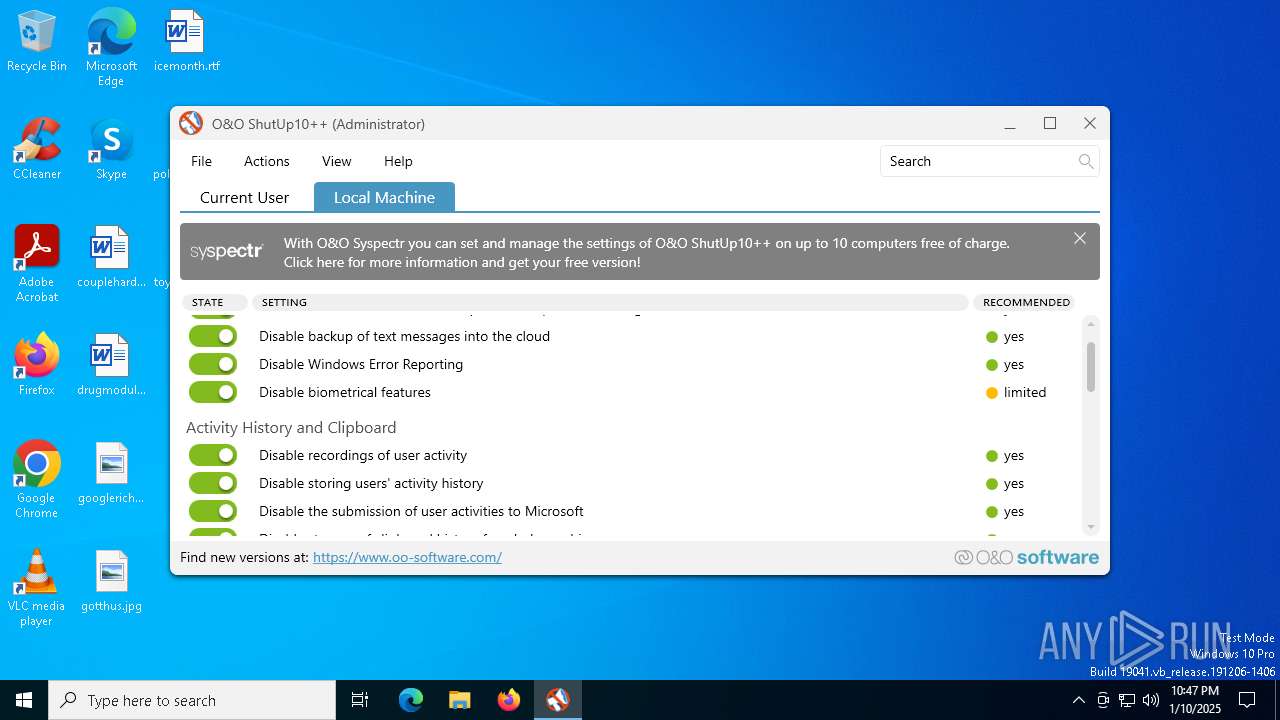
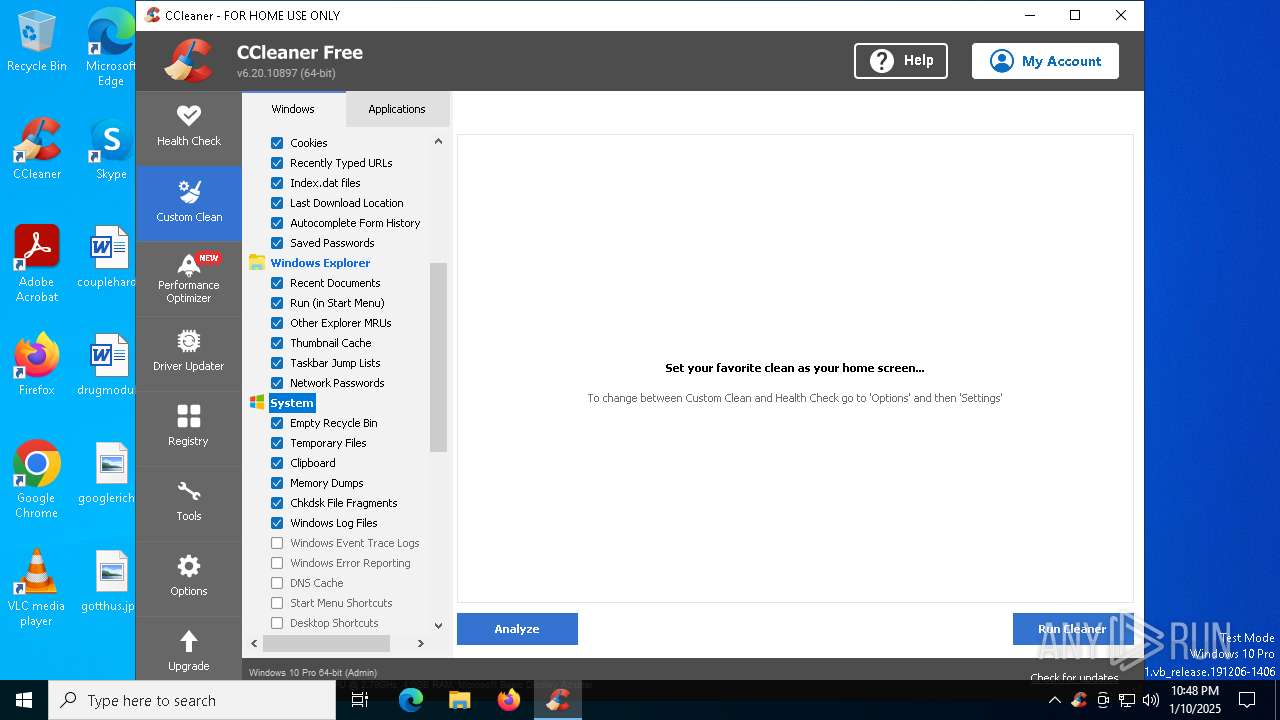
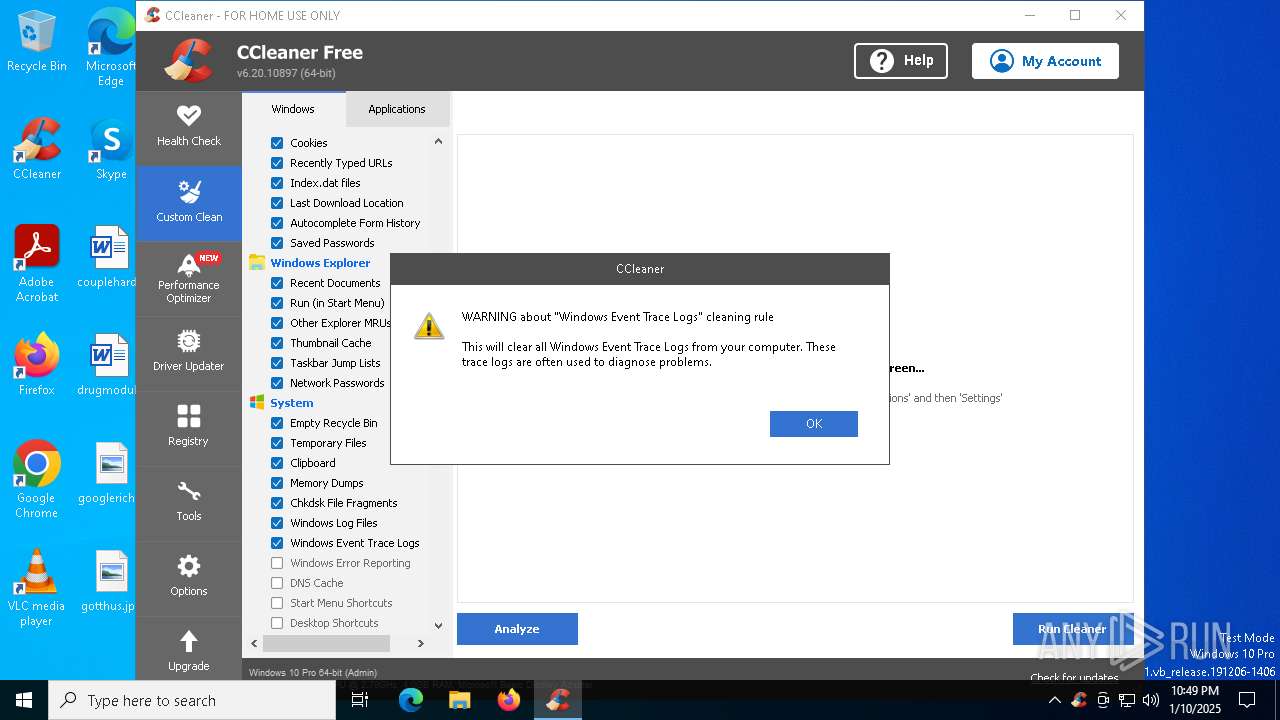
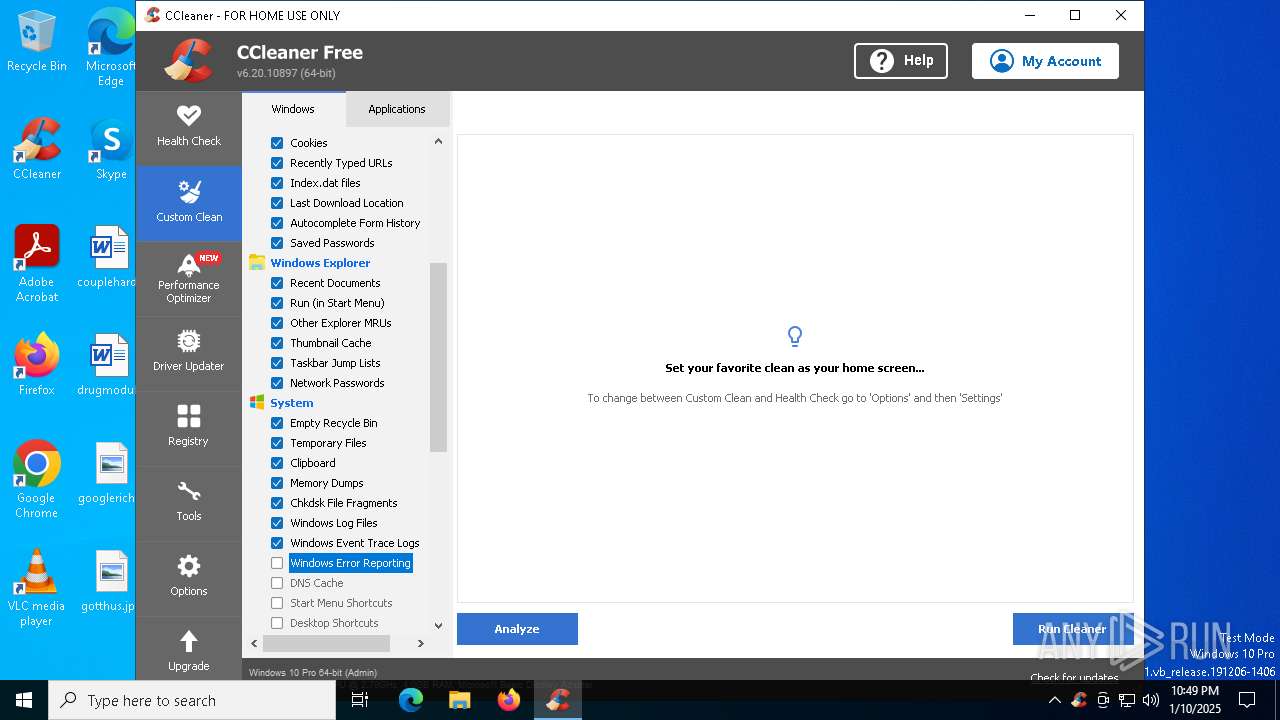
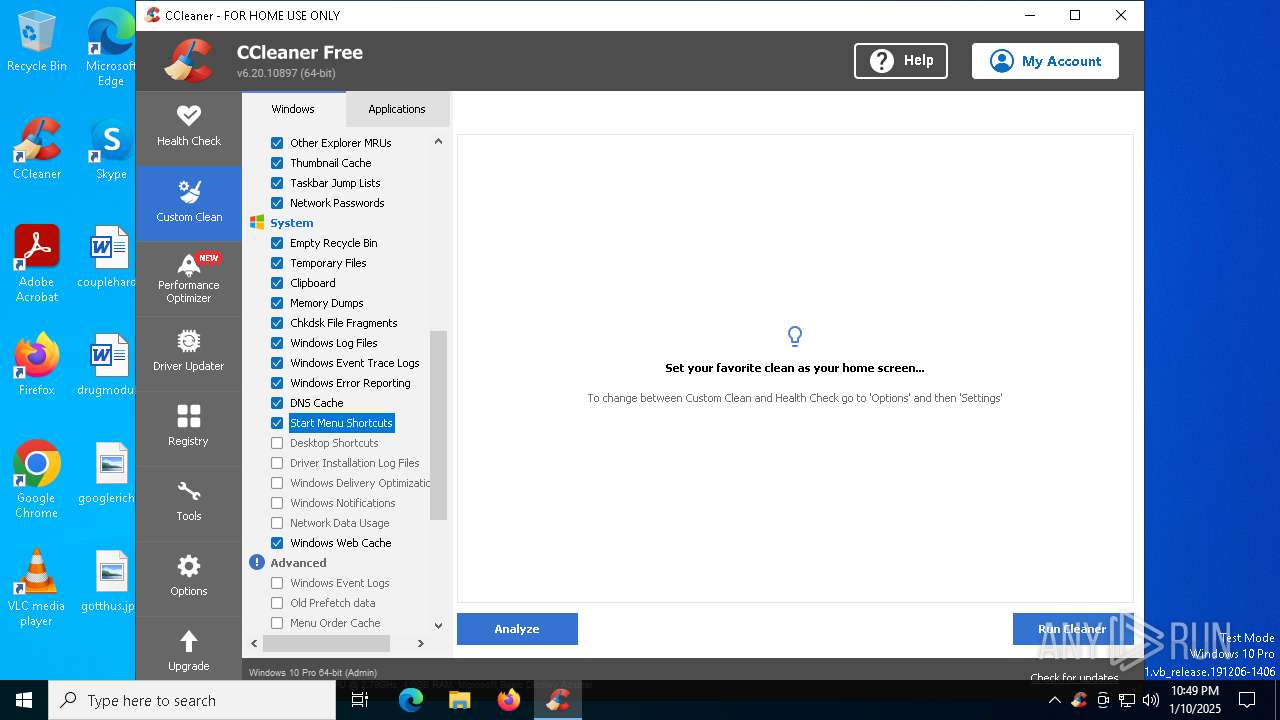
Changes Windows Error Reporting flag
- OOSU10.exe (PID: 5092)
SUSPICIOUS
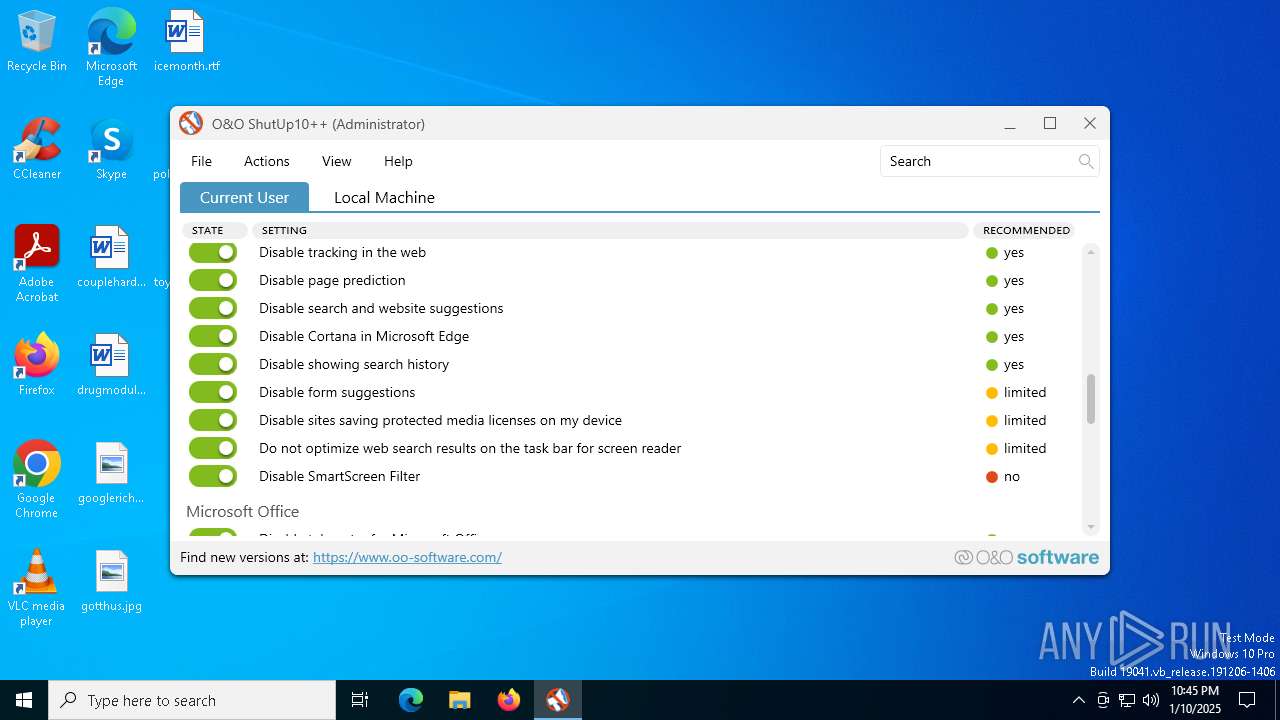
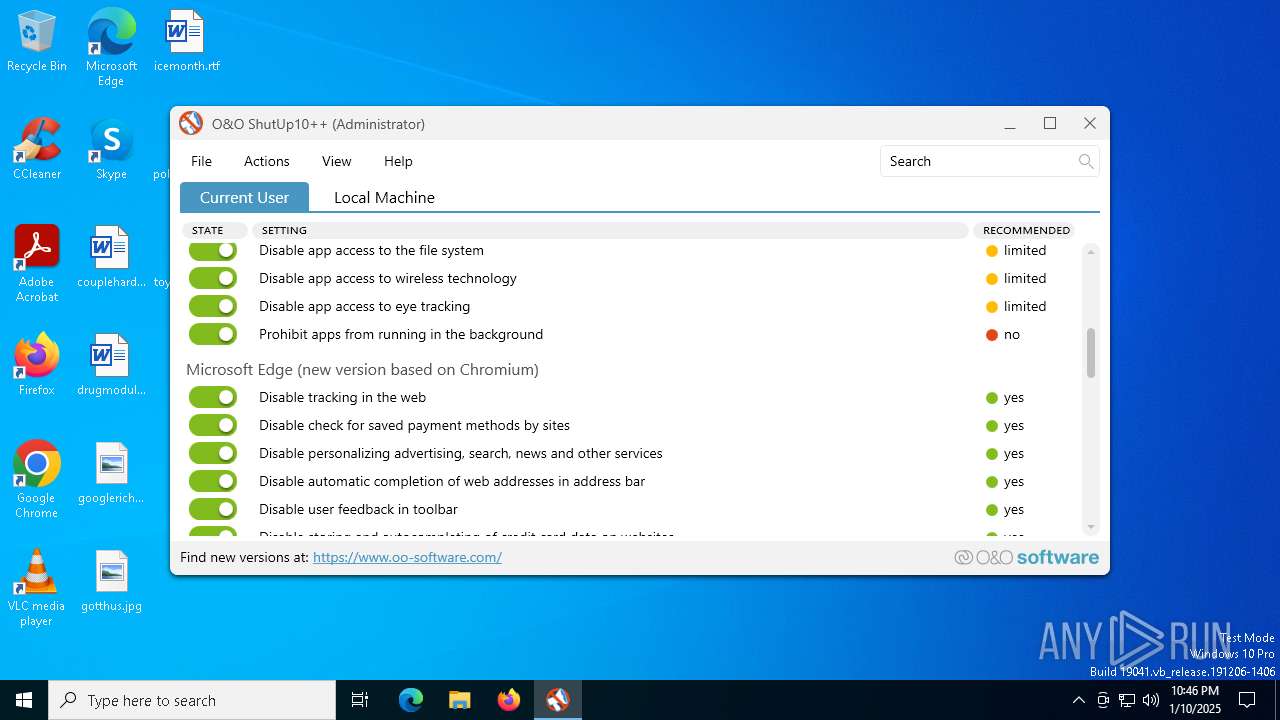
Reads security settings of Internet Explorer
- OOSU10.exe (PID: 5092)
- CCleaner64.exe (PID: 7156)
- CCleaner64.exe (PID: 236)
- CCleaner64.exe (PID: 5592)
Searches for installed software
- dllhost.exe (PID: 6788)
- CCleaner64.exe (PID: 5592)
- CCleaner64.exe (PID: 236)
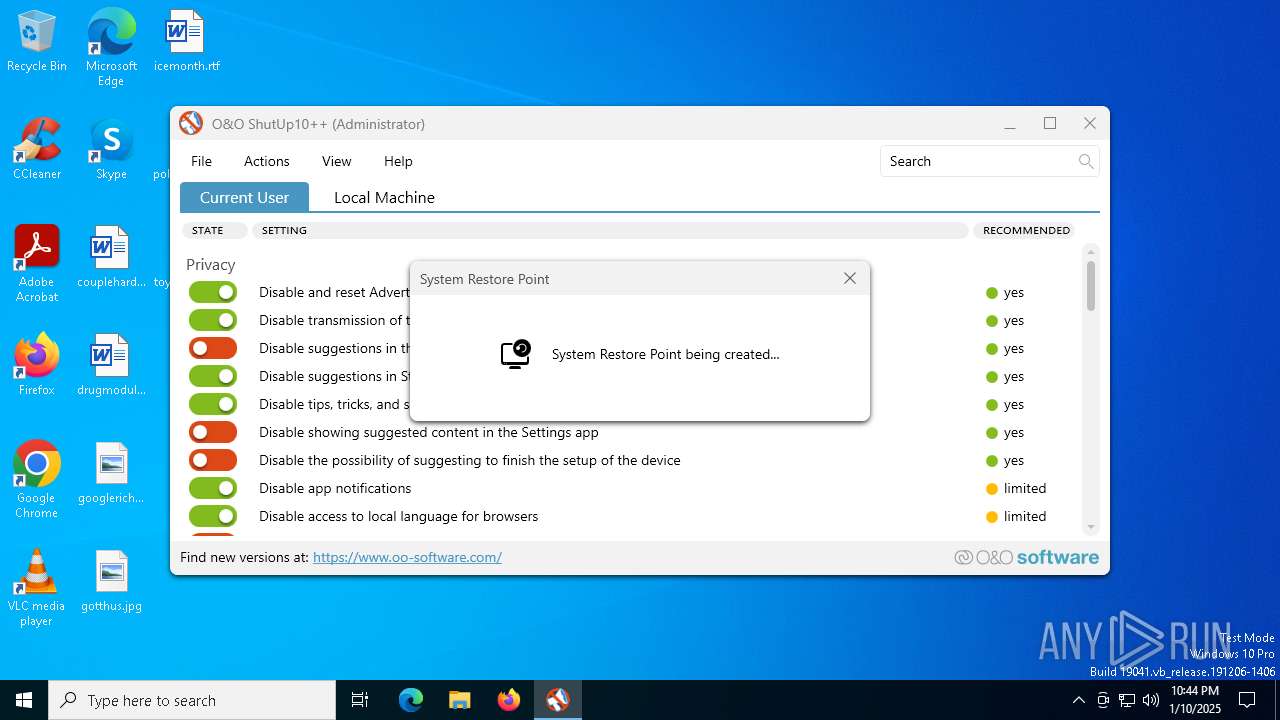
Executes as Windows Service
- VSSVC.exe (PID: 6832)
Process drops legitimate windows executable
- OOSU10.exe (PID: 5092)
Executable content was dropped or overwritten
- OOSU10.exe (PID: 5092)
- CCleaner64.exe (PID: 236)
- CCleaner64.exe (PID: 5592)
Reads the date of Windows installation
- CCleaner64.exe (PID: 7156)
Application launched itself
- CCleaner64.exe (PID: 7156)
- CCleaner64.exe (PID: 236)
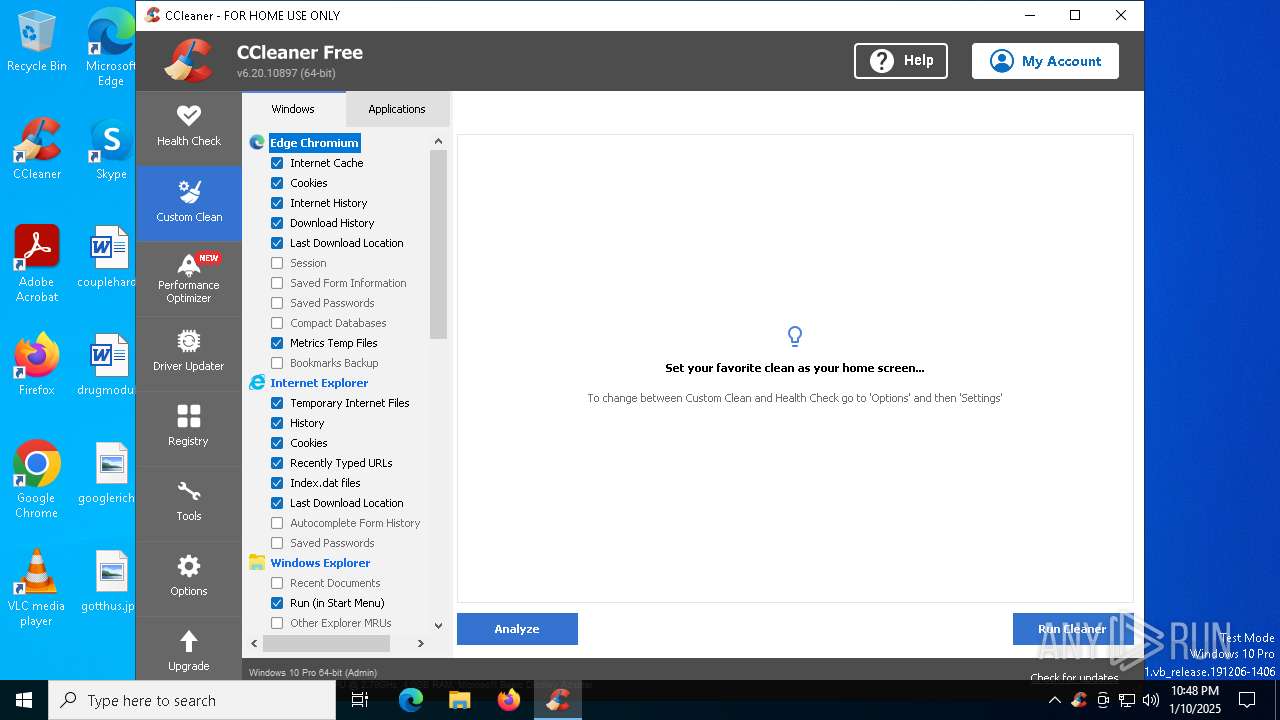
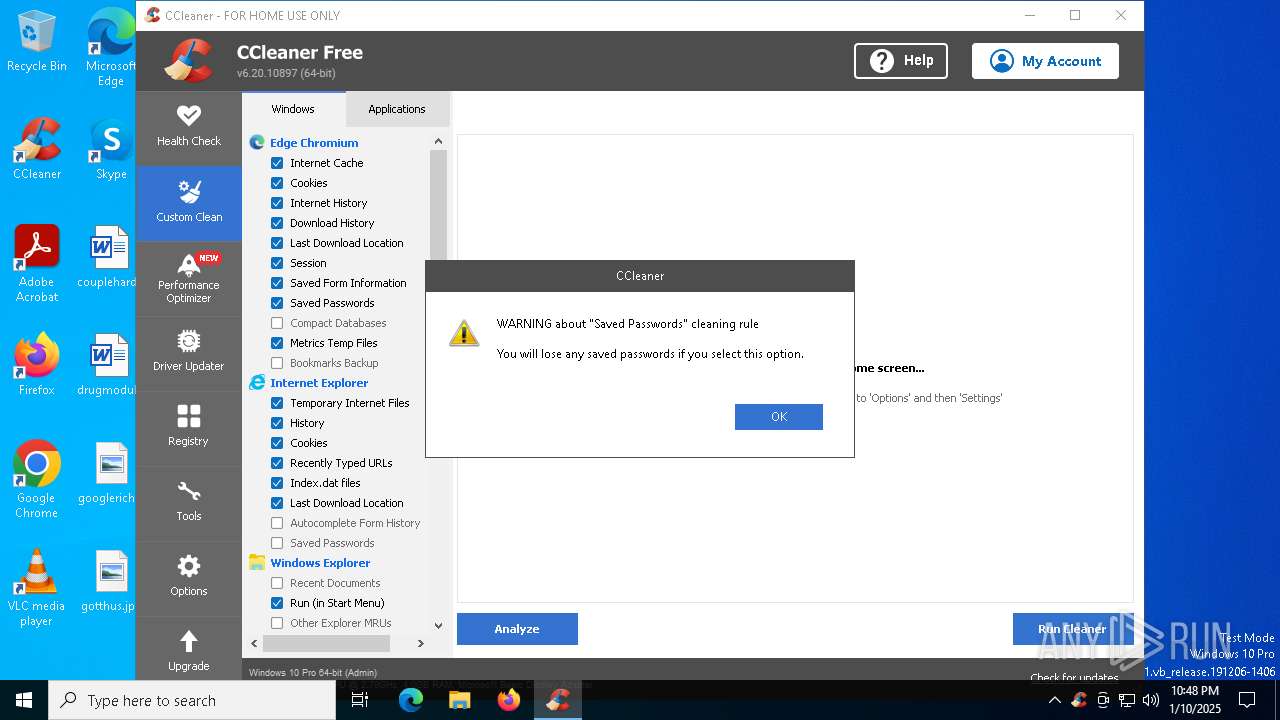
Reads Internet Explorer settings
- CCleaner64.exe (PID: 236)
Checks Windows Trust Settings
- CCleaner64.exe (PID: 236)
- CCleaner64.exe (PID: 5592)
Checks for external IP
- CCleaner64.exe (PID: 236)
The process verifies whether the antivirus software is installed
- CCleaner64.exe (PID: 236)
Starts application from unusual location
- CCleaner64.exe (PID: 236)
Starts a Microsoft application from unusual location
- reg1.exe (PID: 5592)
INFO
Reads the computer name
- OOSU10.exe (PID: 5092)
- CCleaner64.exe (PID: 236)
- CCleaner64.exe (PID: 7156)
- CCleaner64.exe (PID: 5592)
Checks supported languages
- OOSU10.exe (PID: 5092)
- CCleaner64.exe (PID: 7156)
- CCleaner64.exe (PID: 5592)
- CCleaner64.exe (PID: 236)
- reg1.exe (PID: 5592)
Manual execution by a user
- CCleaner64.exe (PID: 7156)
Reads the machine GUID from the registry
- OOSU10.exe (PID: 5092)
- CCleaner64.exe (PID: 236)
- CCleaner64.exe (PID: 5592)
Reads product name
- CCleaner64.exe (PID: 236)
Process checks computer location settings
- CCleaner64.exe (PID: 7156)
- CCleaner64.exe (PID: 236)
Reads Environment values
- CCleaner64.exe (PID: 236)
- CCleaner64.exe (PID: 5592)
- CCleaner64.exe (PID: 7156)
Reads CPU info
- CCleaner64.exe (PID: 236)
Sends debugging messages
- CCleaner64.exe (PID: 236)
- CCleaner64.exe (PID: 5592)
Creates files in the program directory
- CCleaner64.exe (PID: 236)
- CCleaner64.exe (PID: 5592)
Checks proxy server information
- CCleaner64.exe (PID: 236)
Creates files or folders in the user directory
- CCleaner64.exe (PID: 236)
The sample compiled with english language support
- CCleaner64.exe (PID: 236)
- CCleaner64.exe (PID: 5592)
- OOSU10.exe (PID: 5092)
Reads the software policy settings
- CCleaner64.exe (PID: 236)
- CCleaner64.exe (PID: 5592)
Drops encrypted VBS script (Microsoft Script Encoder)
- CCleaner64.exe (PID: 236)
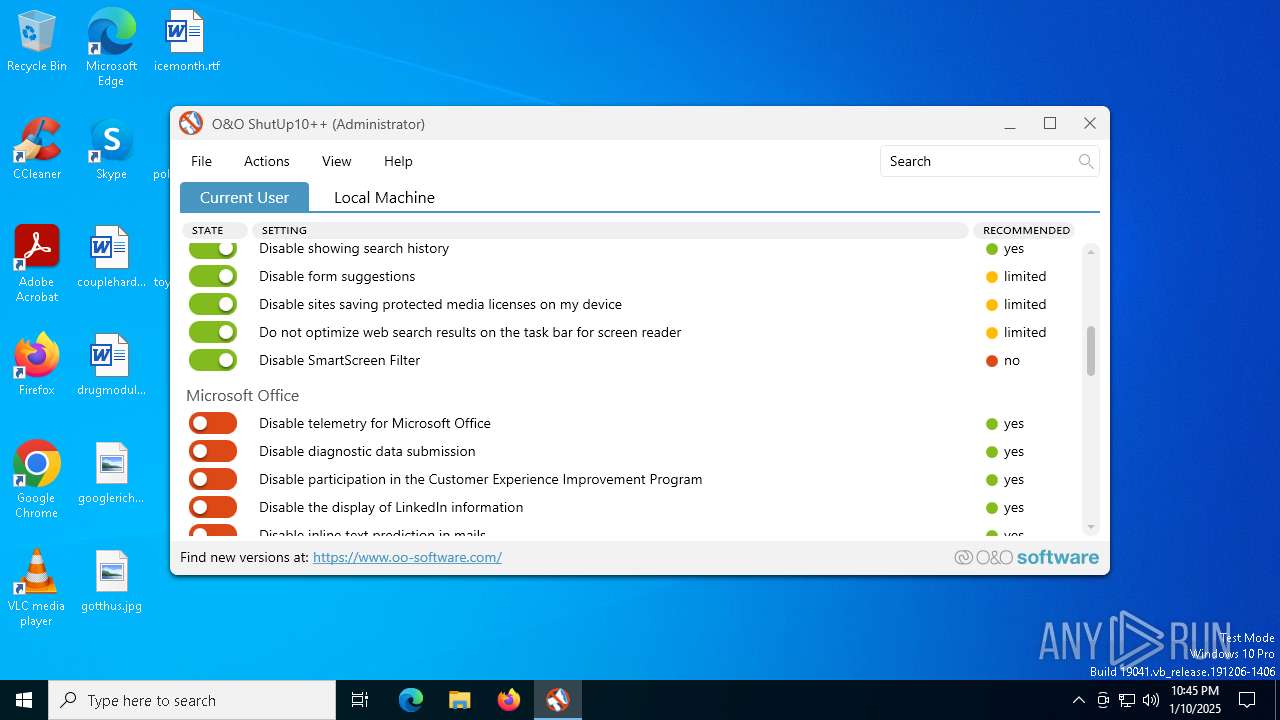
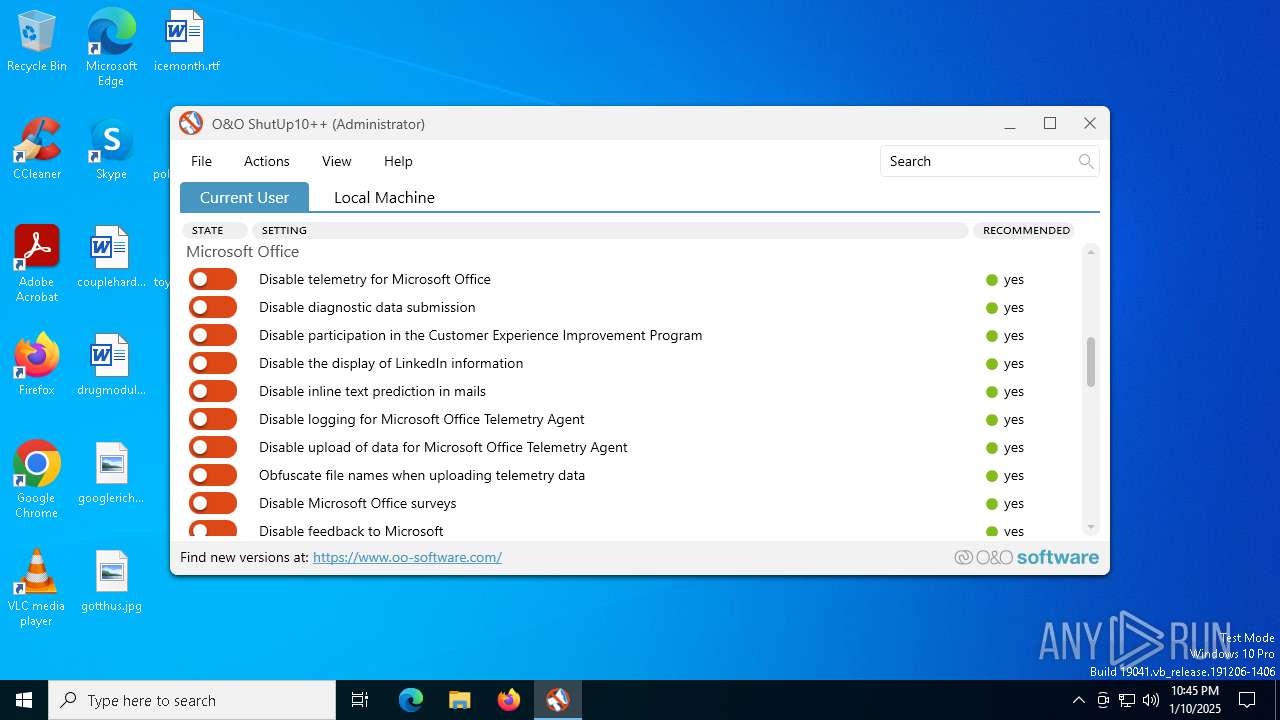
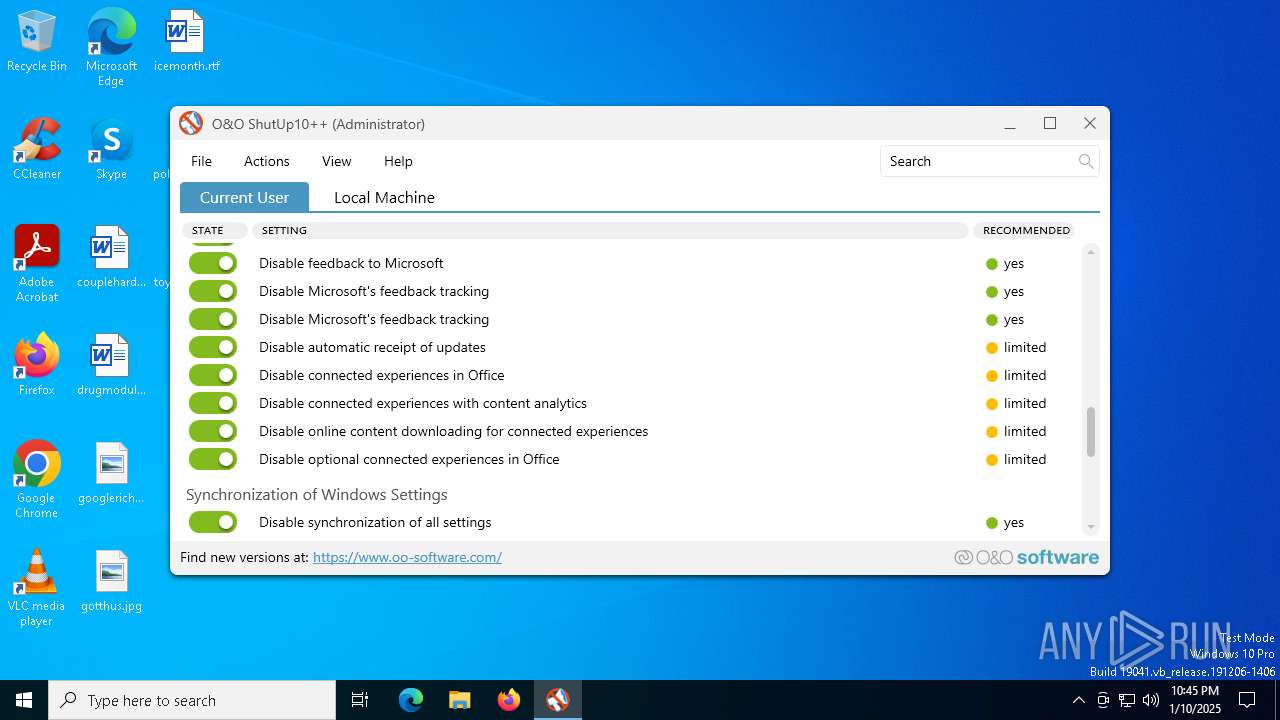
Reads Microsoft Office registry keys
- OOSU10.exe (PID: 5092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2102:07:07 00:16:42+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 2066944 |
| InitializedDataSize: | 37376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1fa88e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.9.1442.423 |
| ProductVersionNumber: | 1.9.1442.423 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
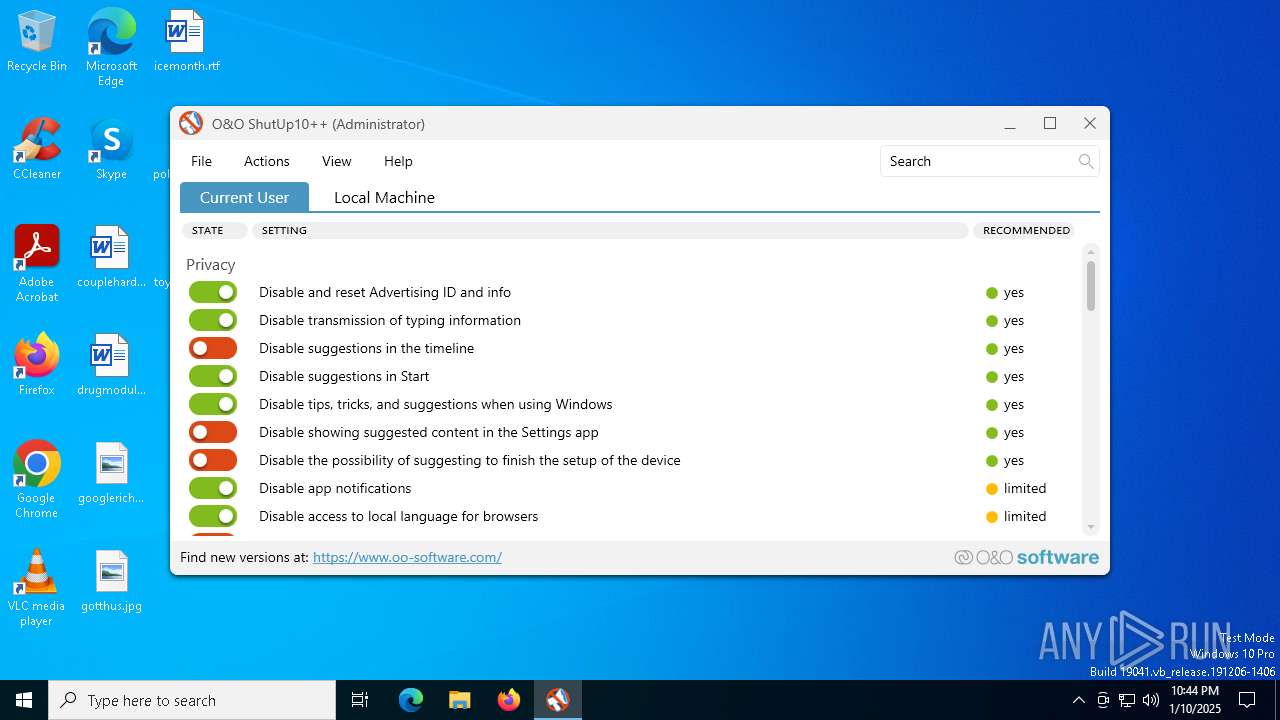
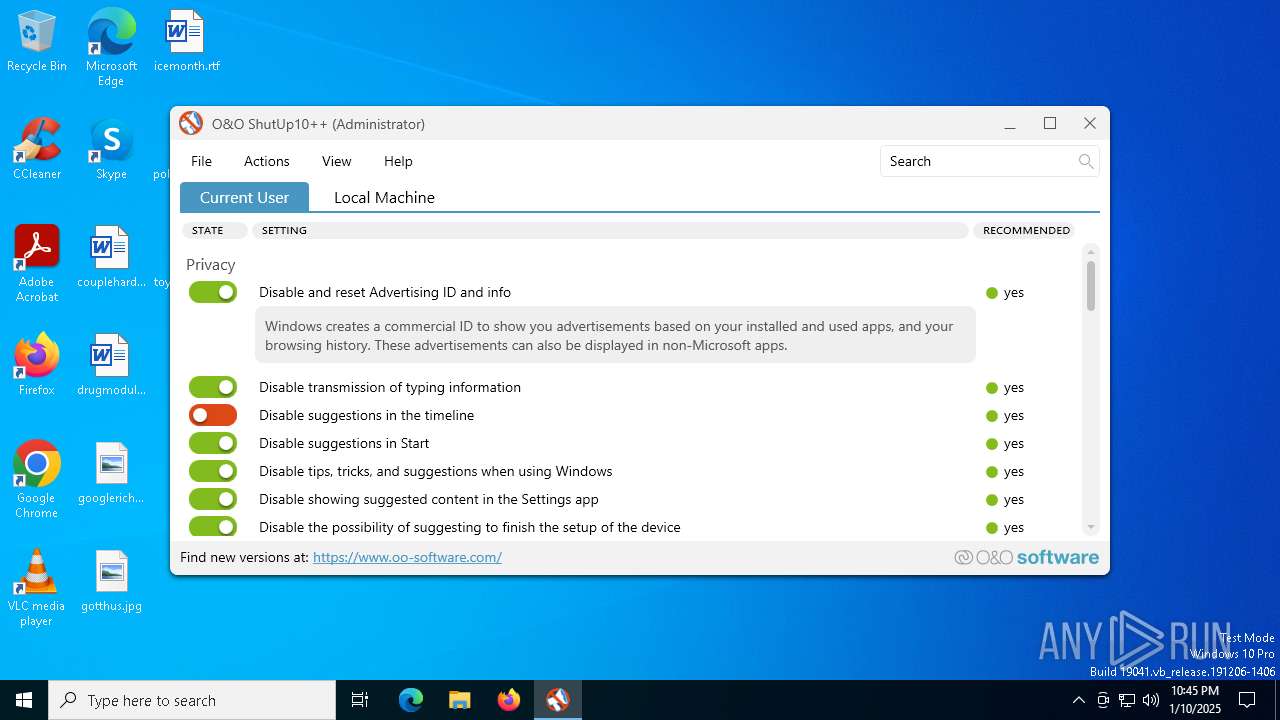
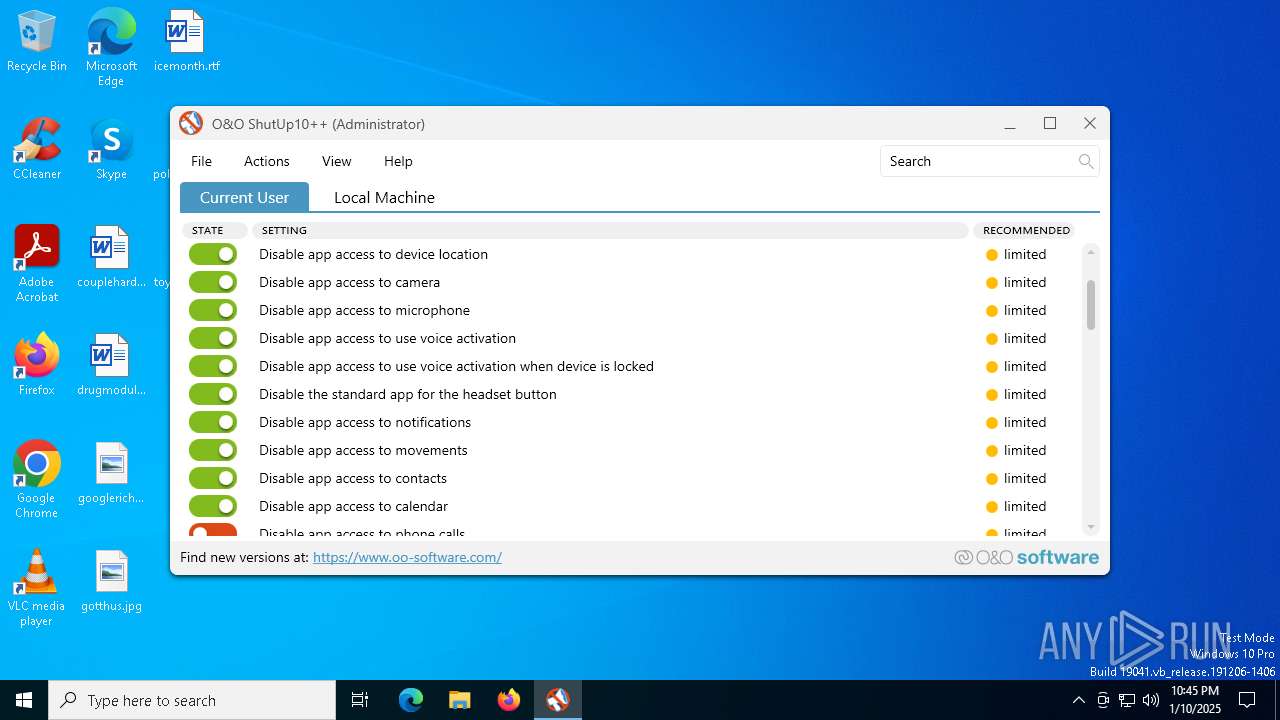
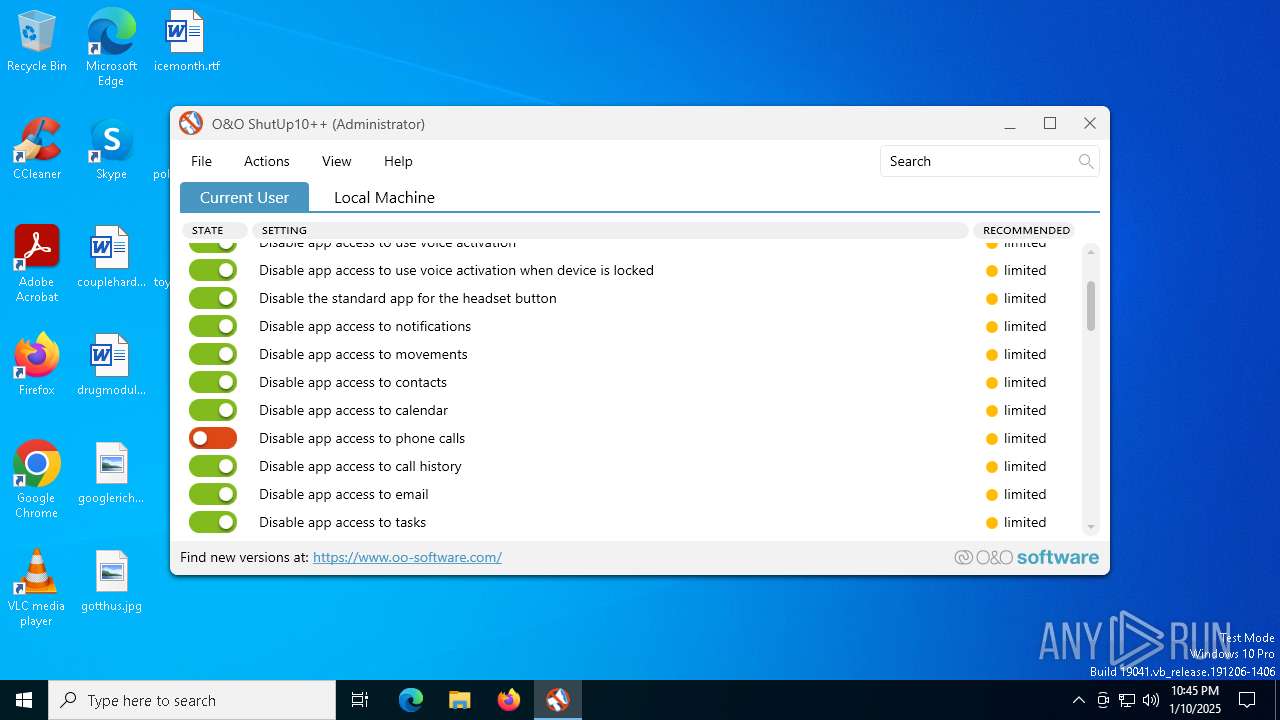
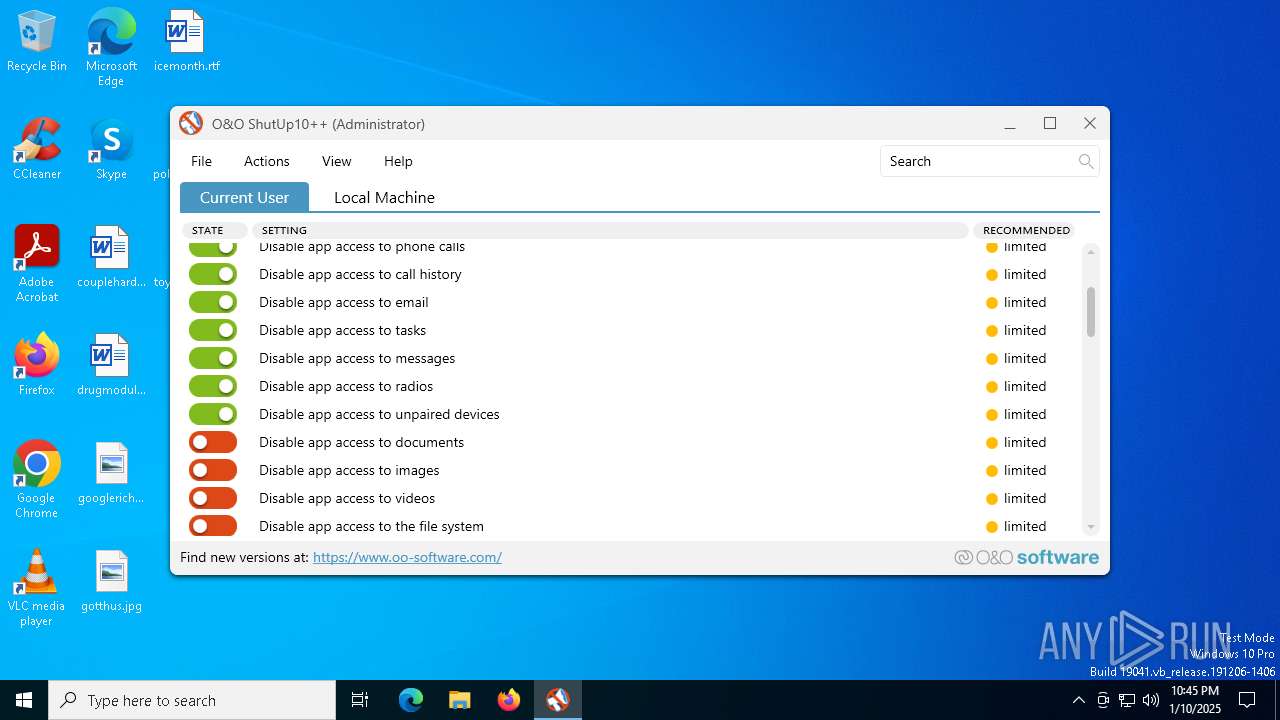
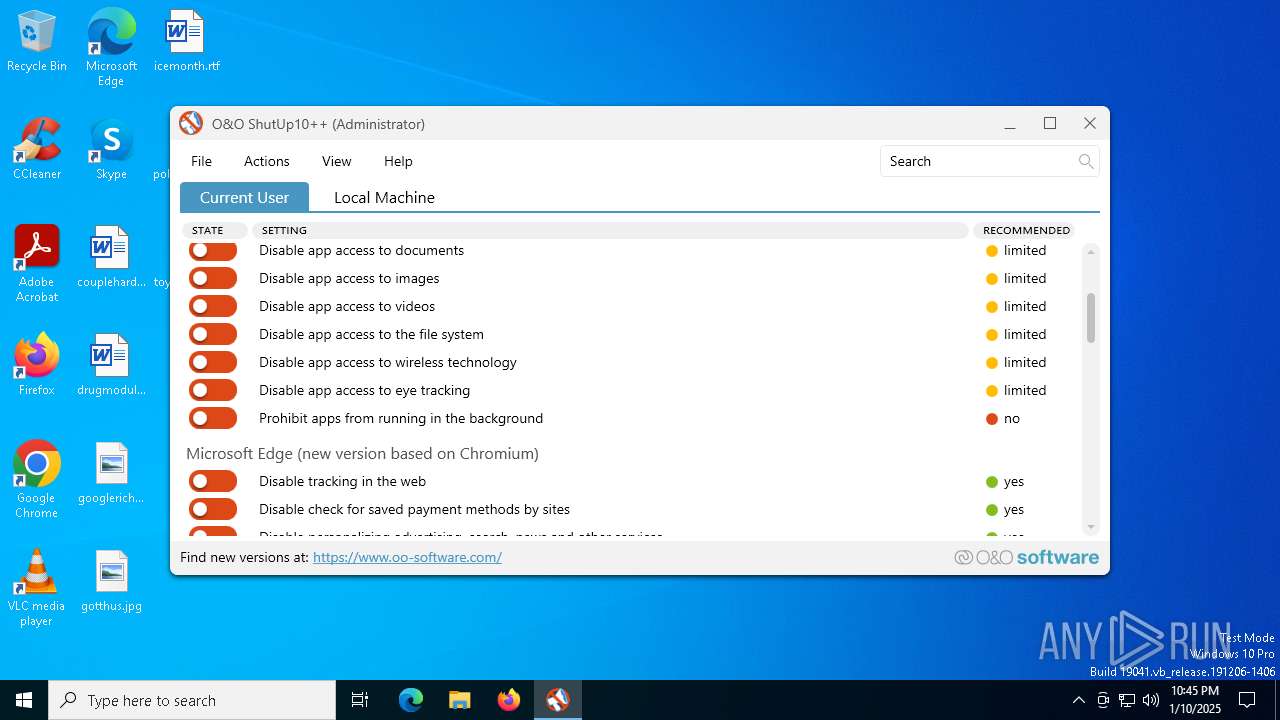
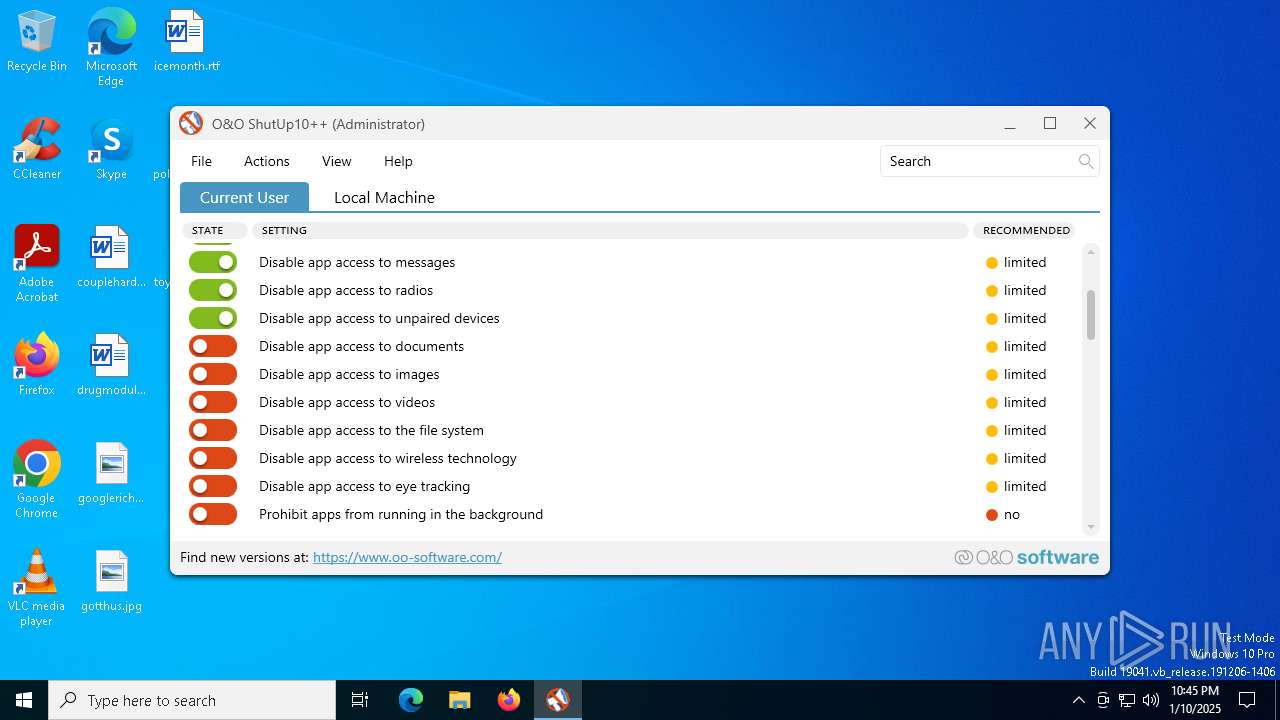
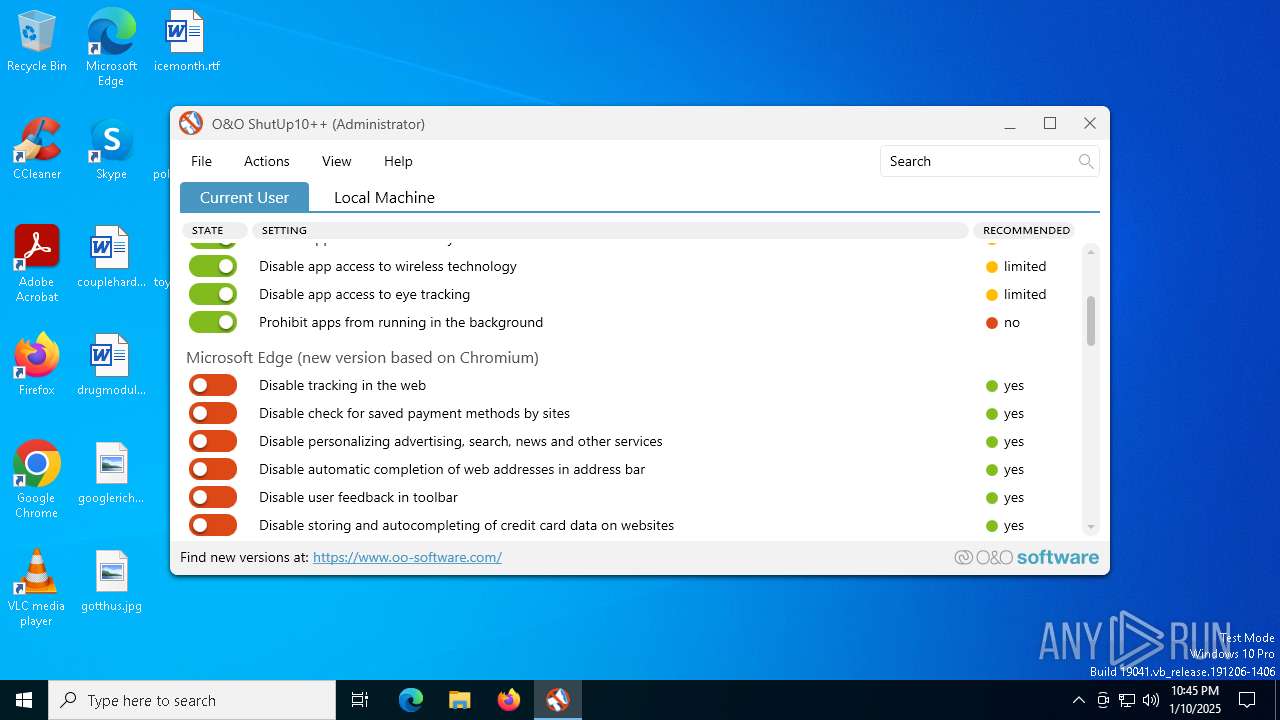
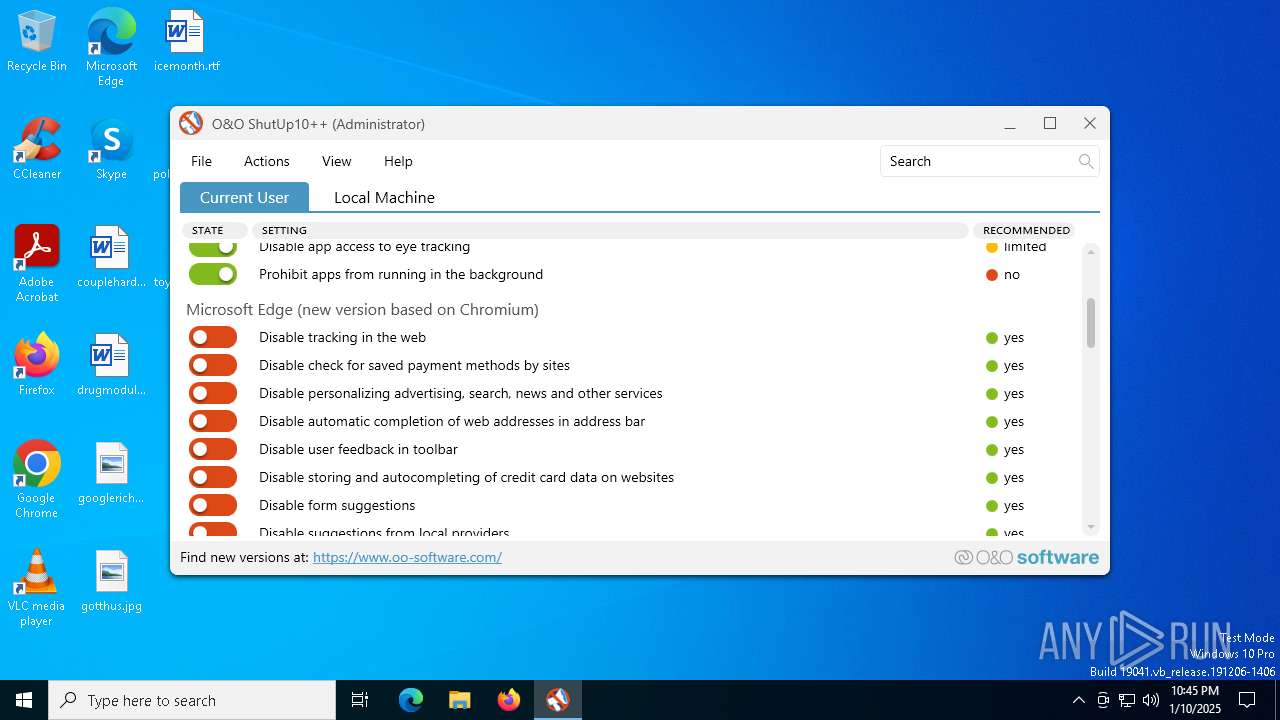
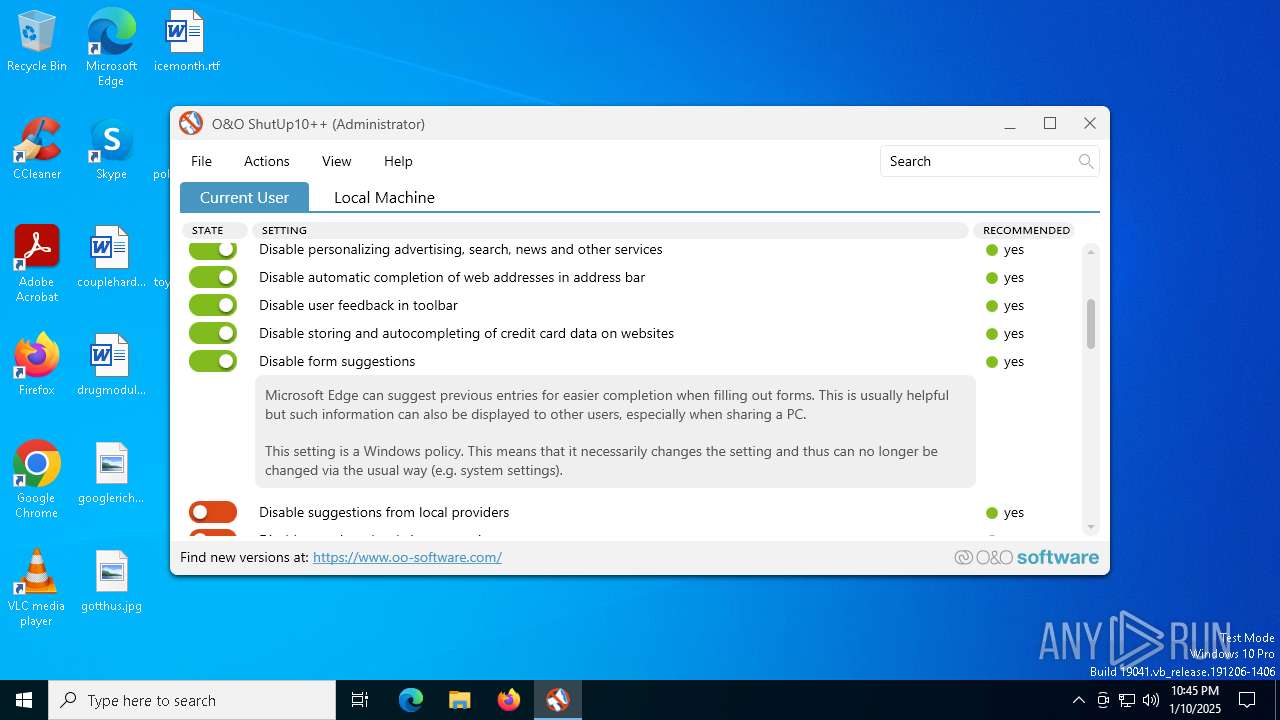
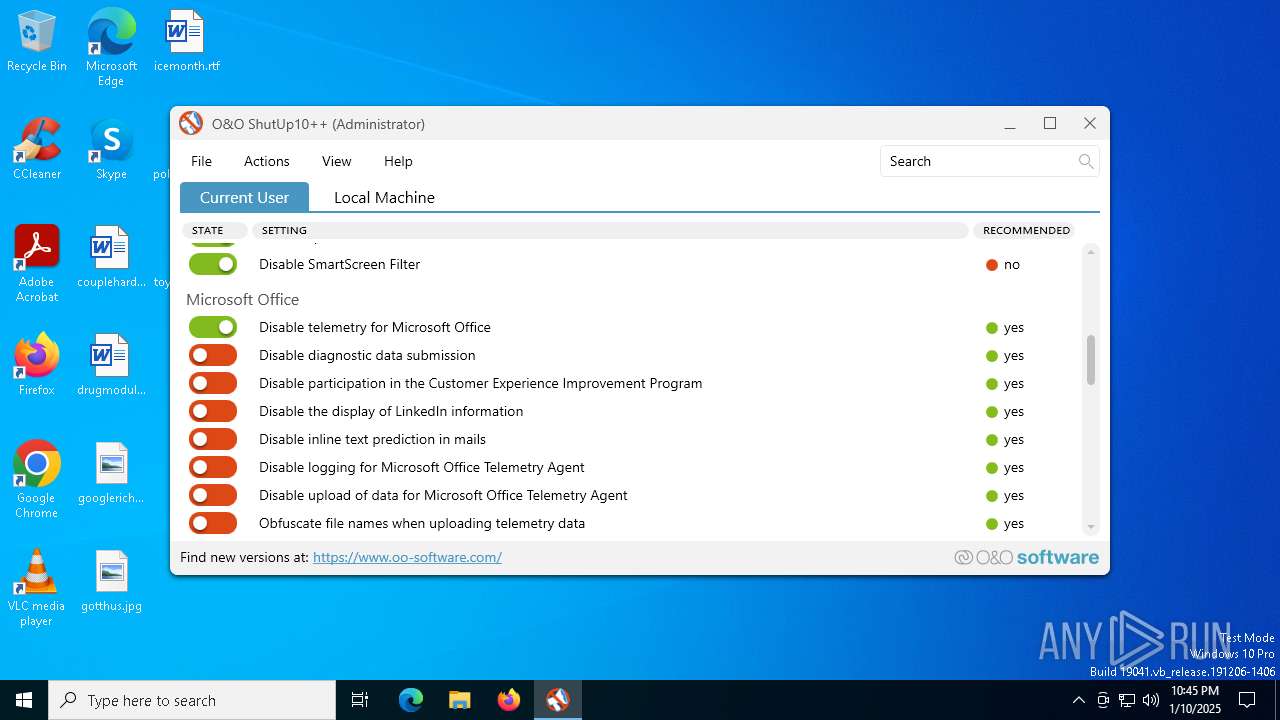
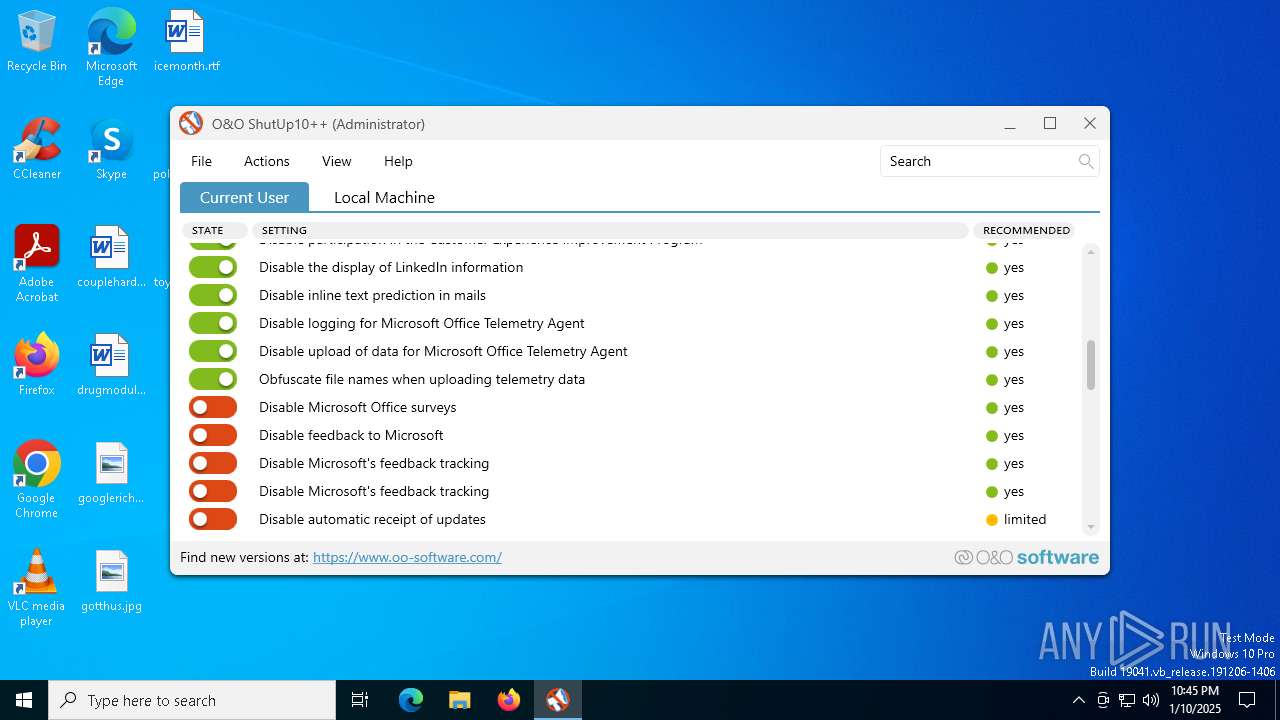
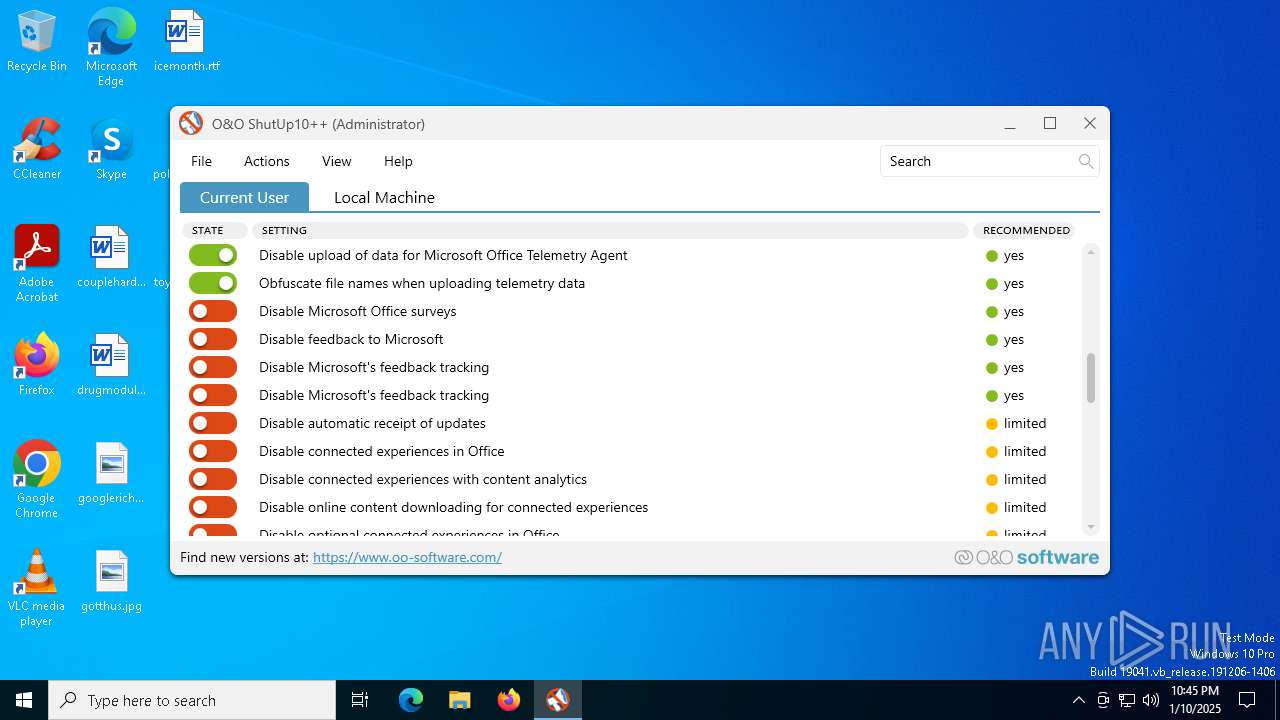
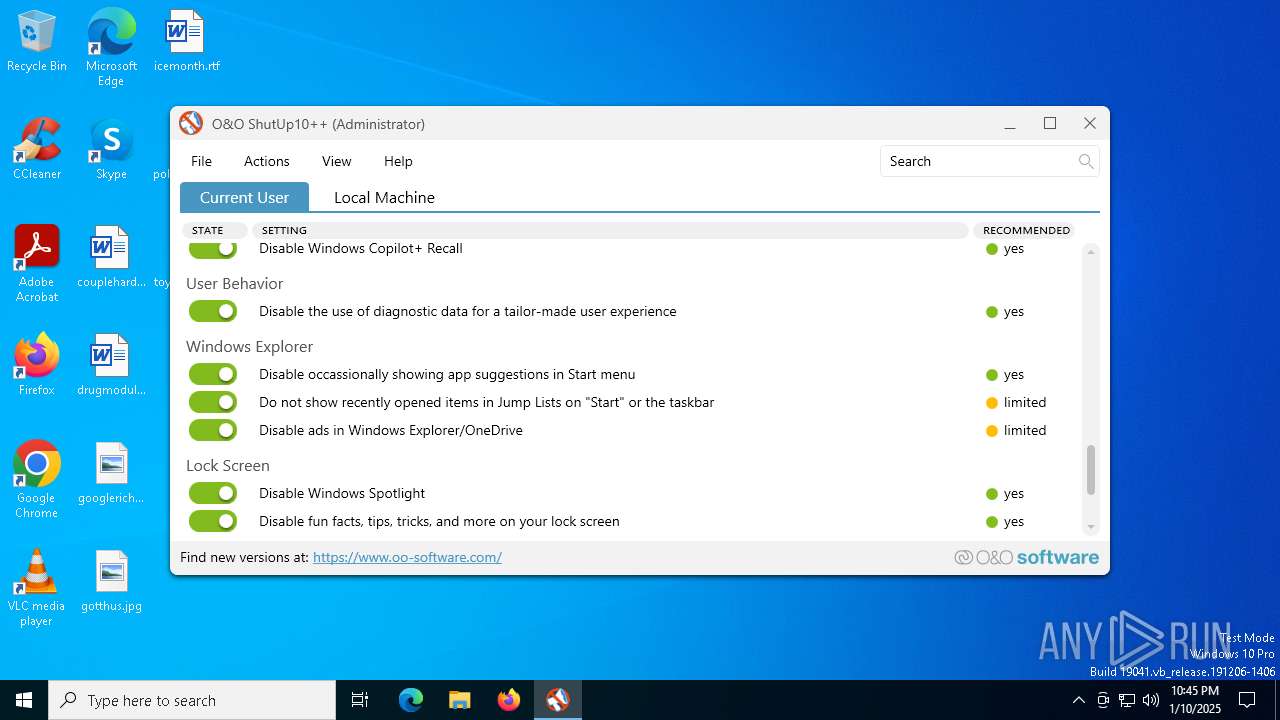
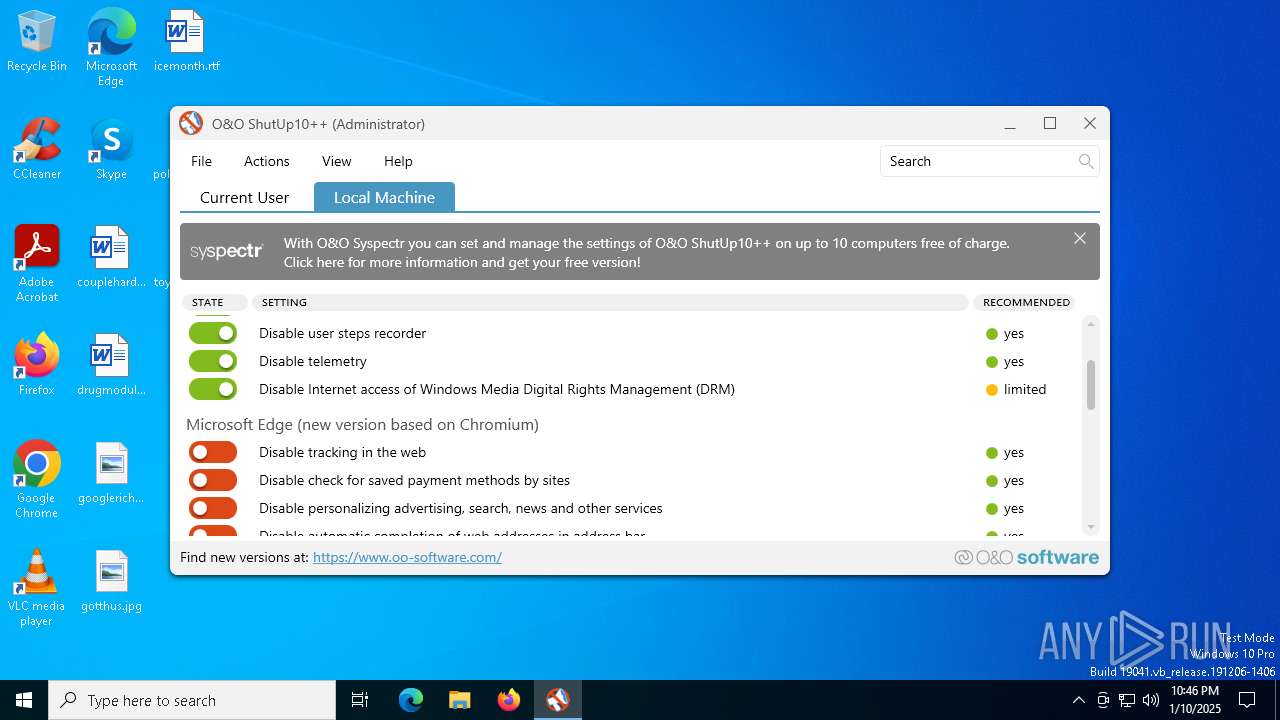
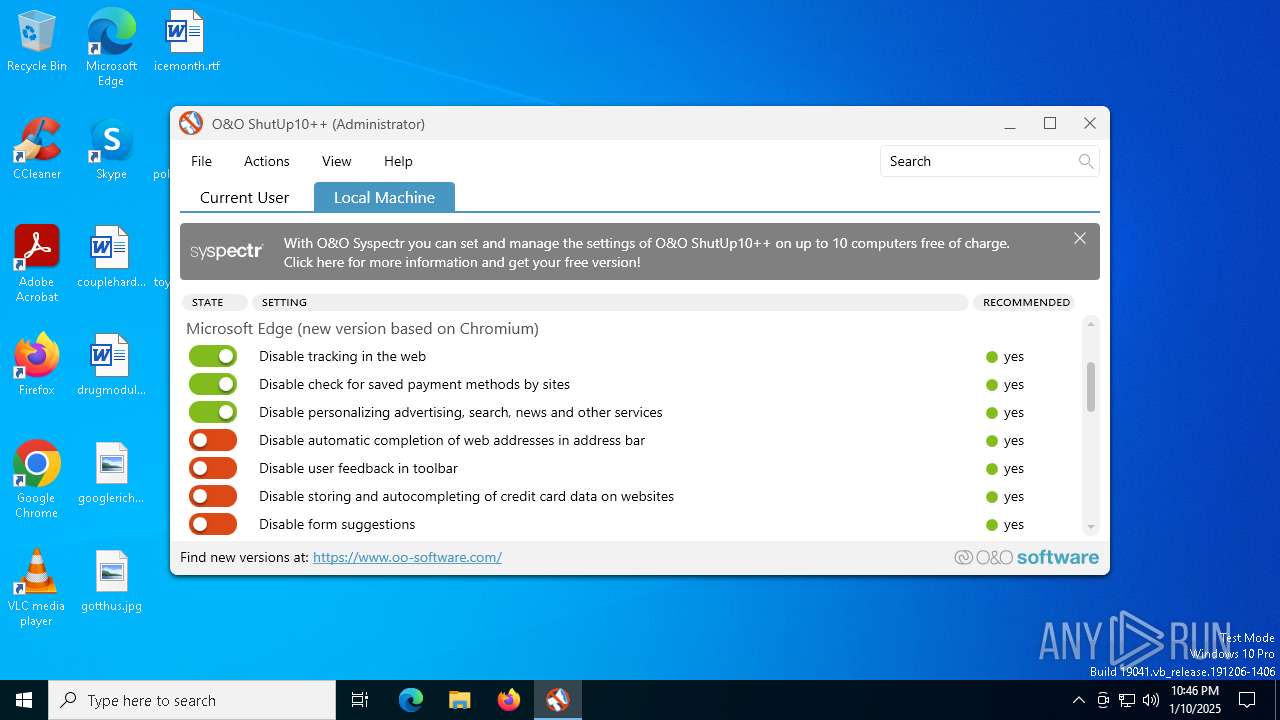
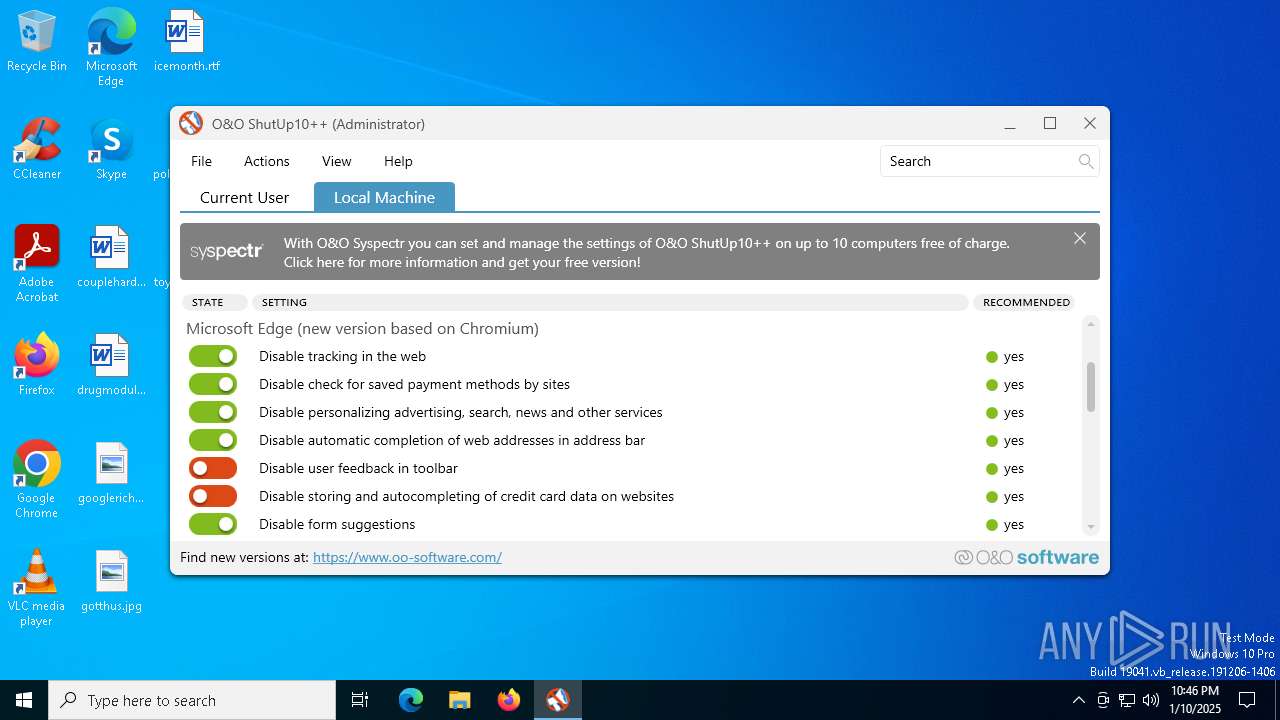
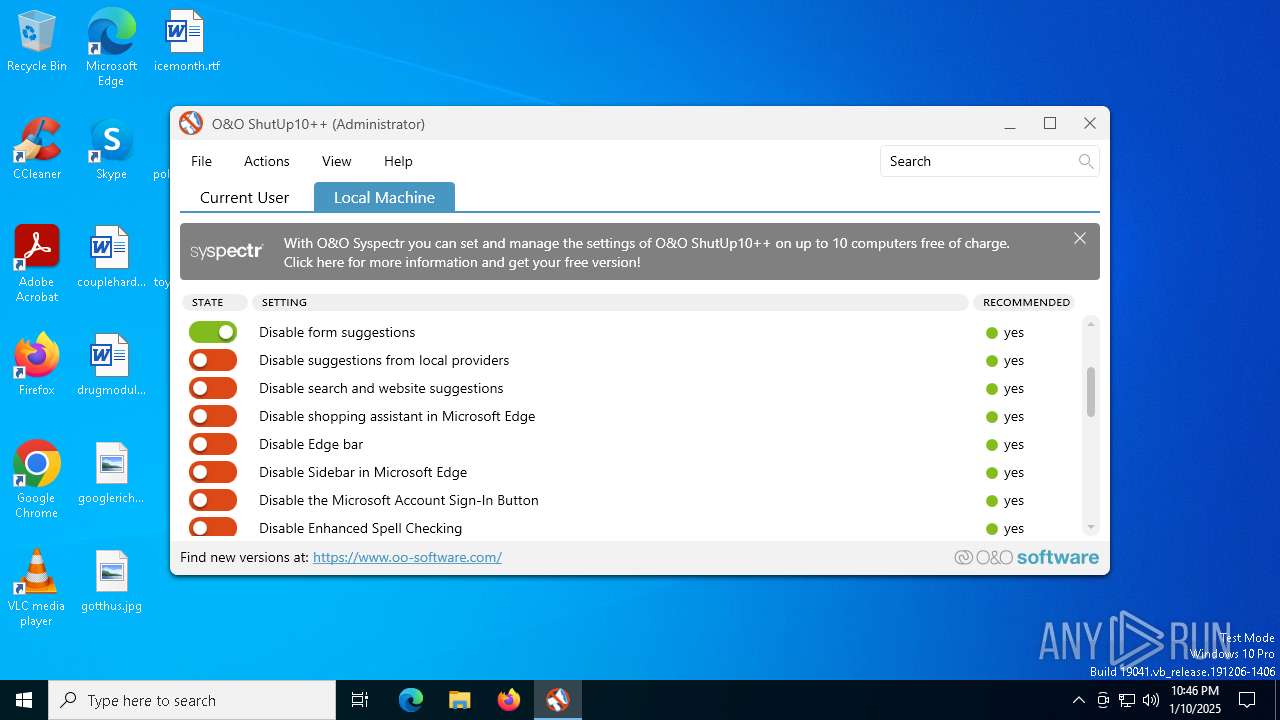
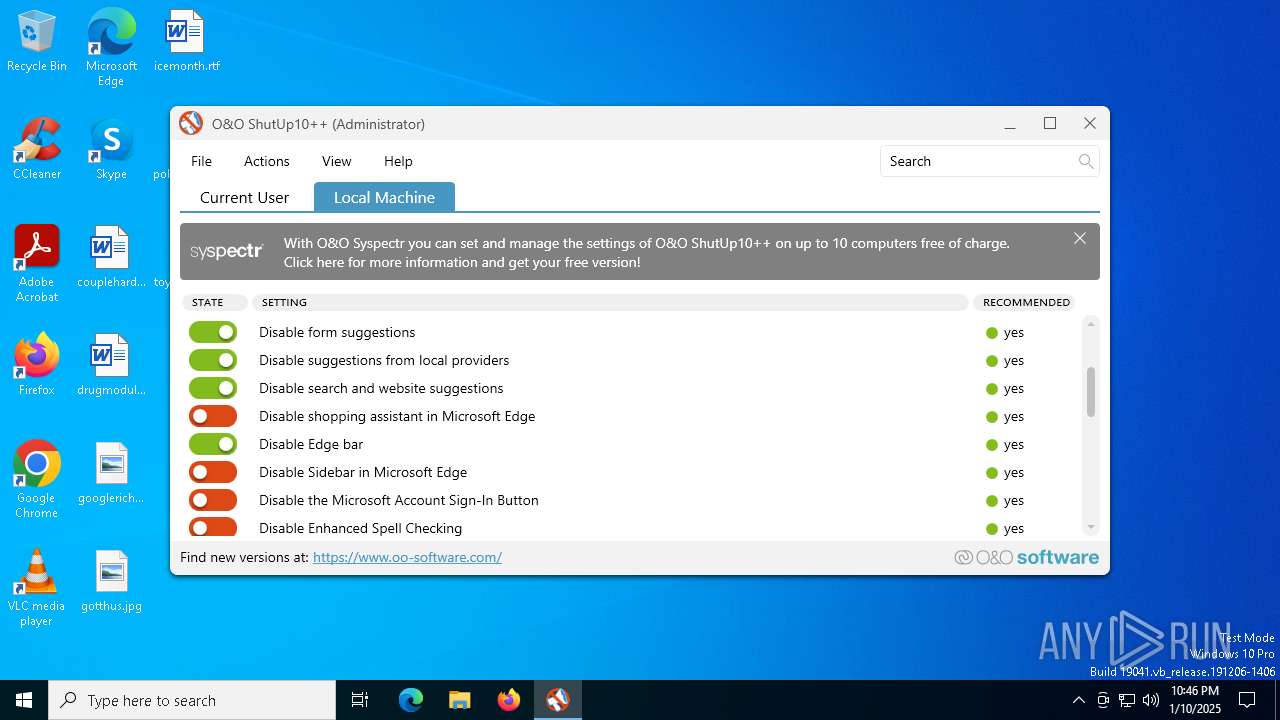
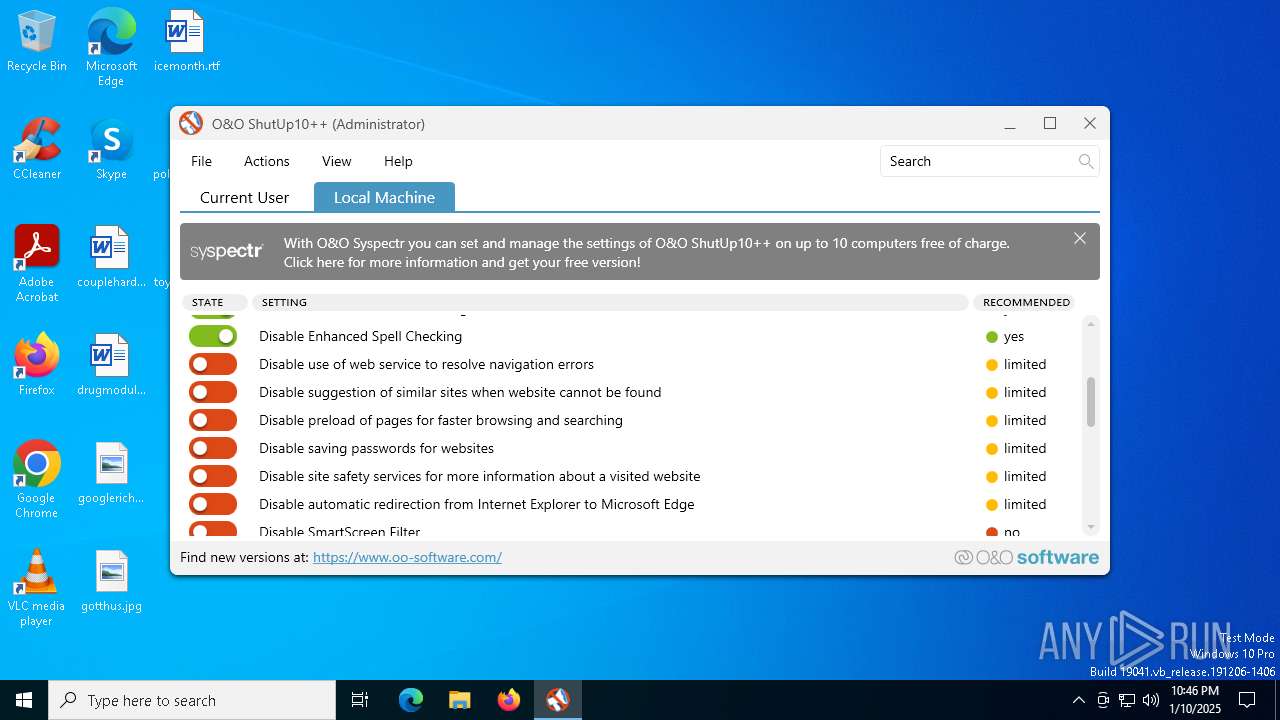
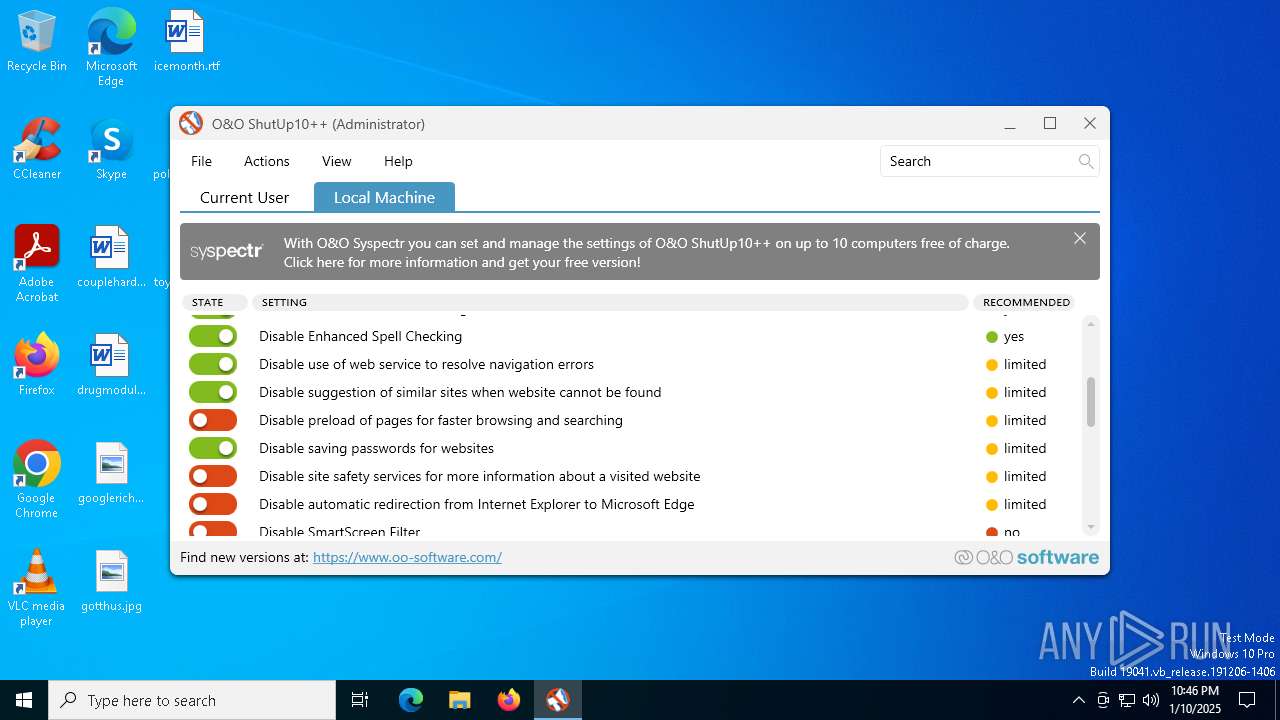
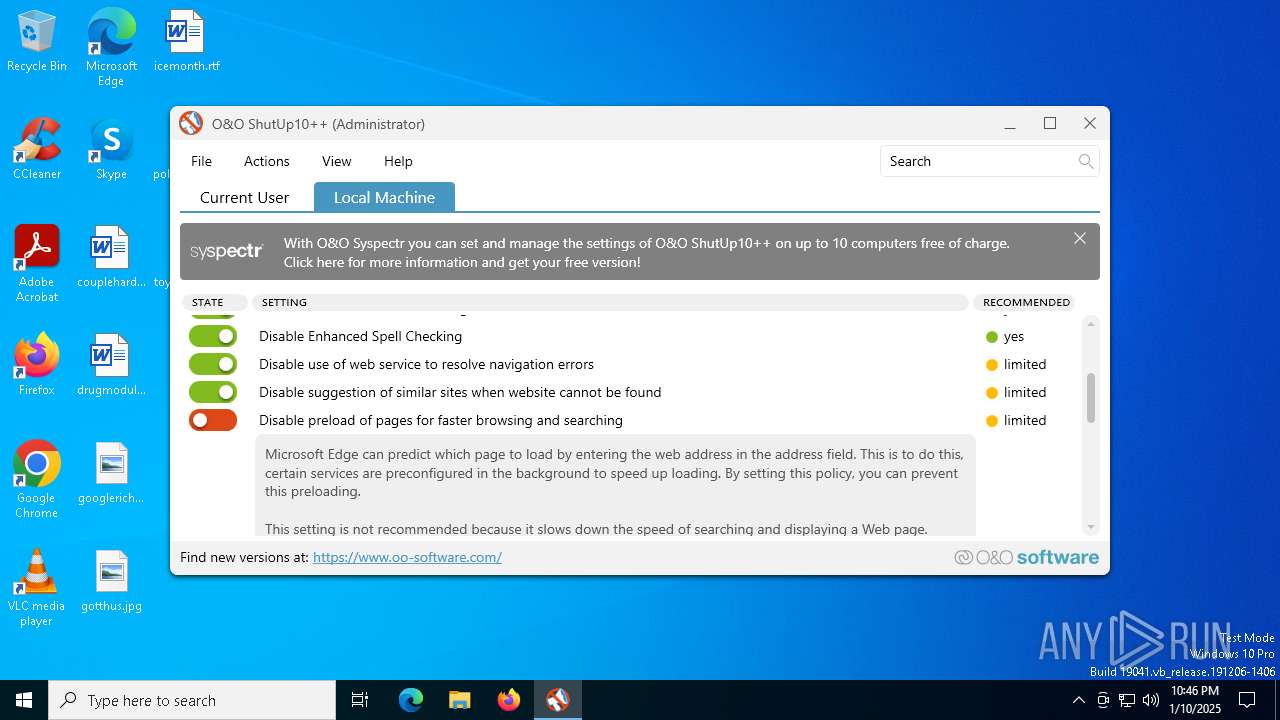
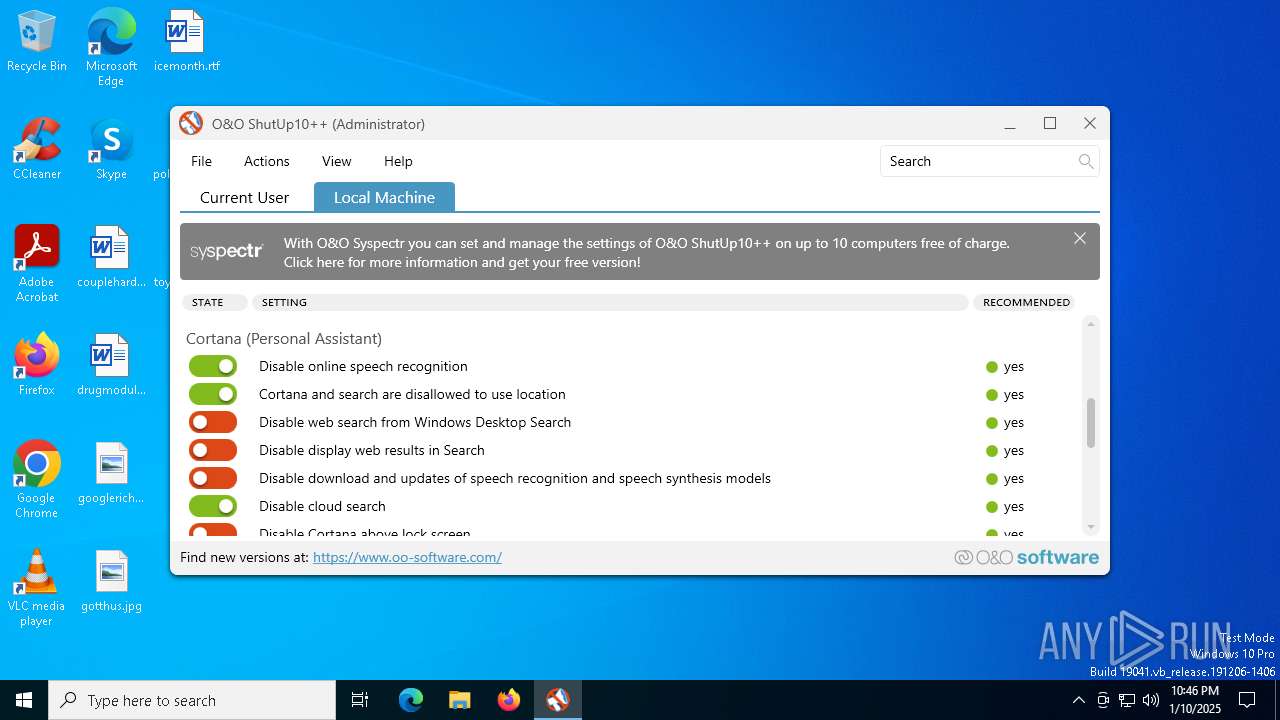
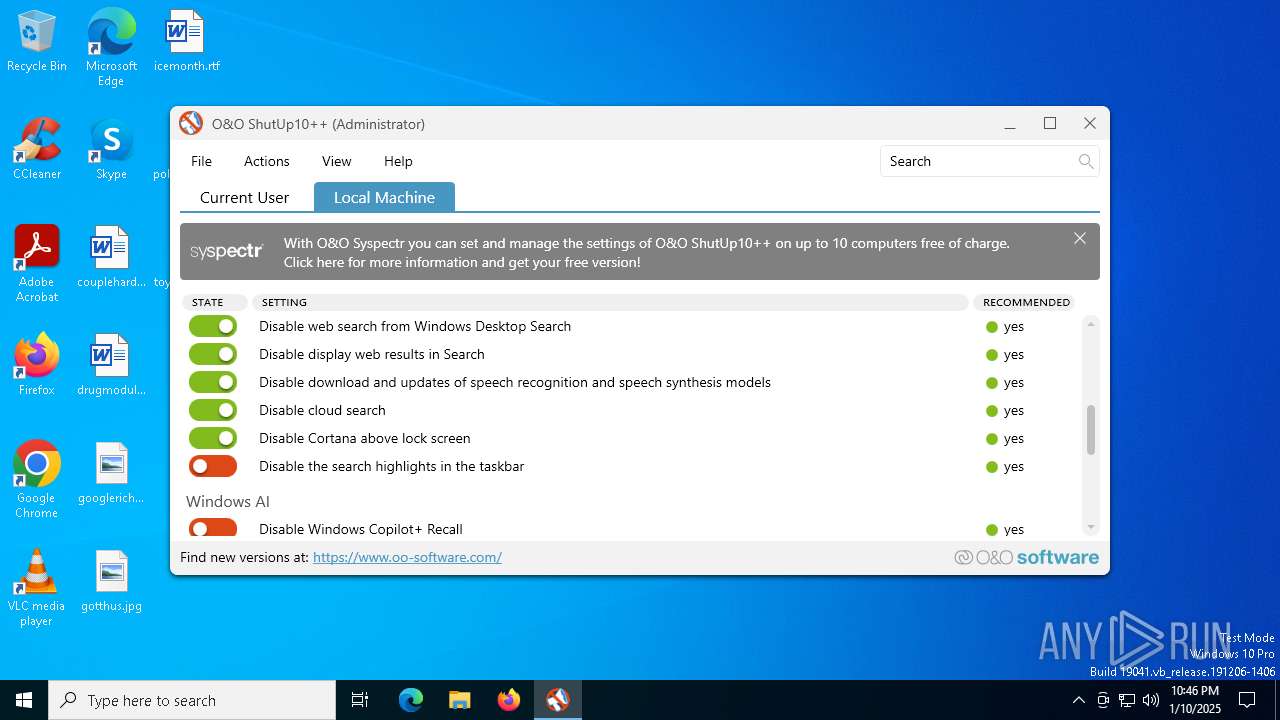
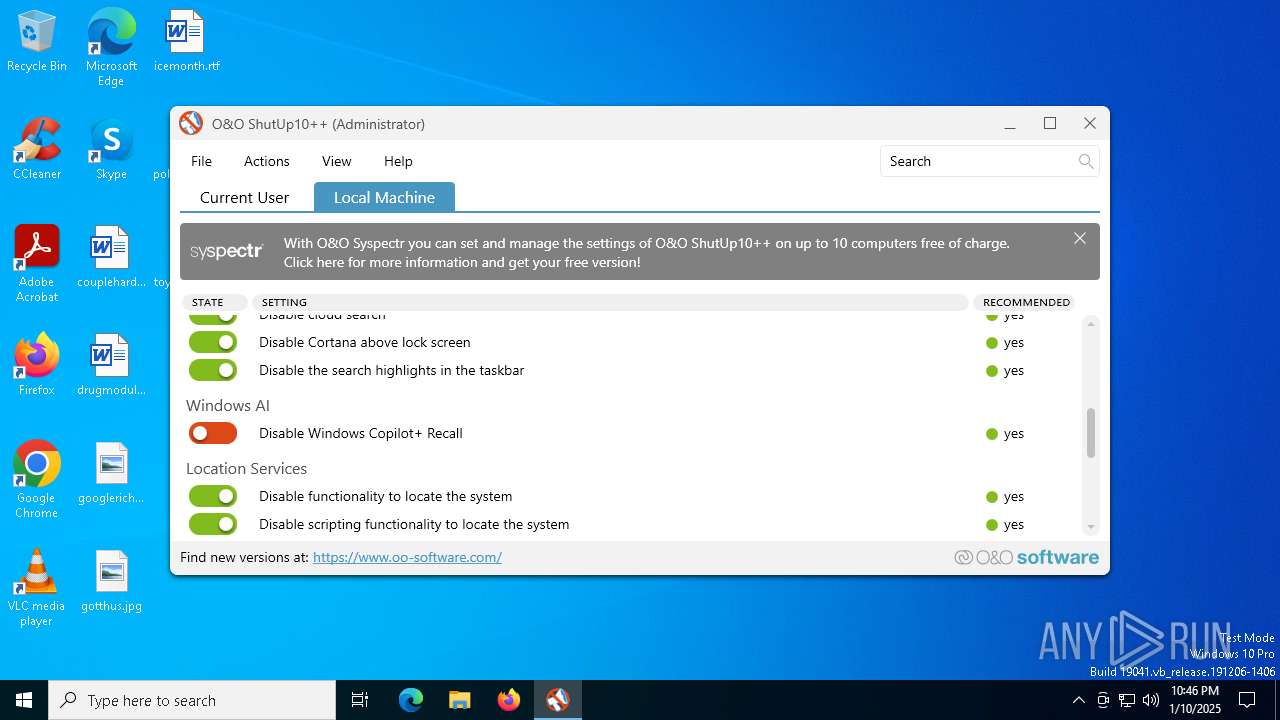
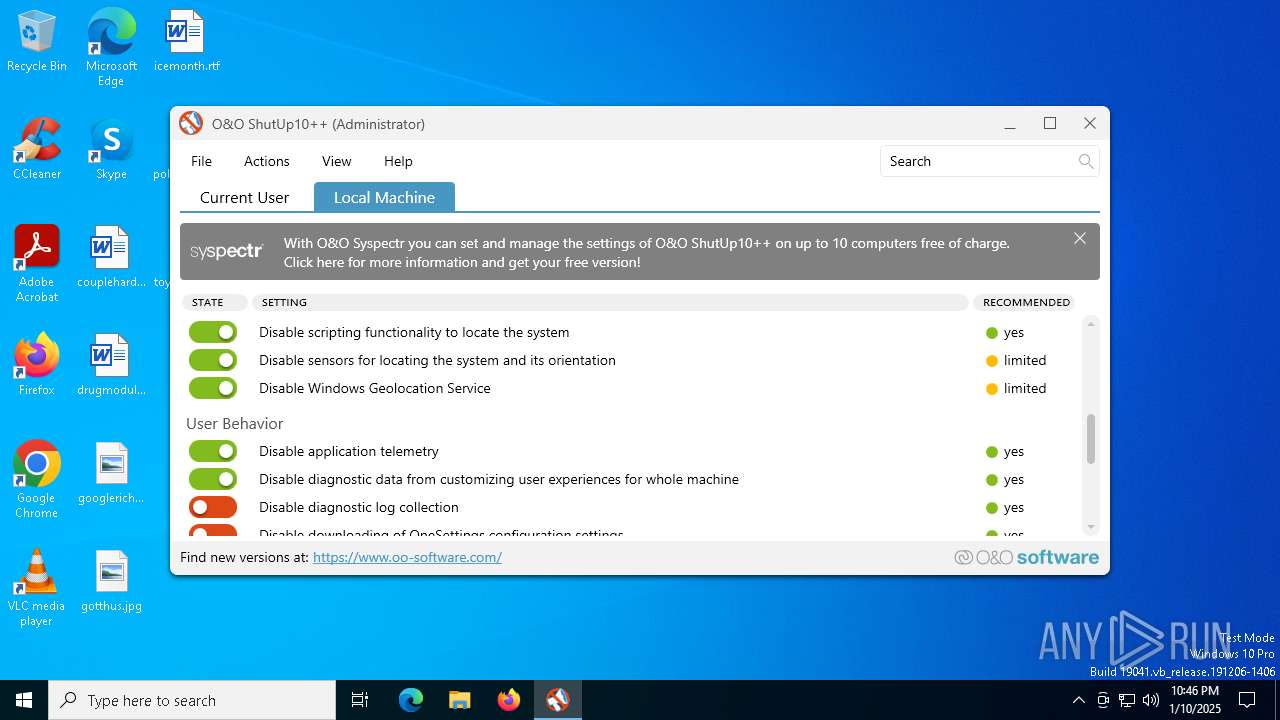
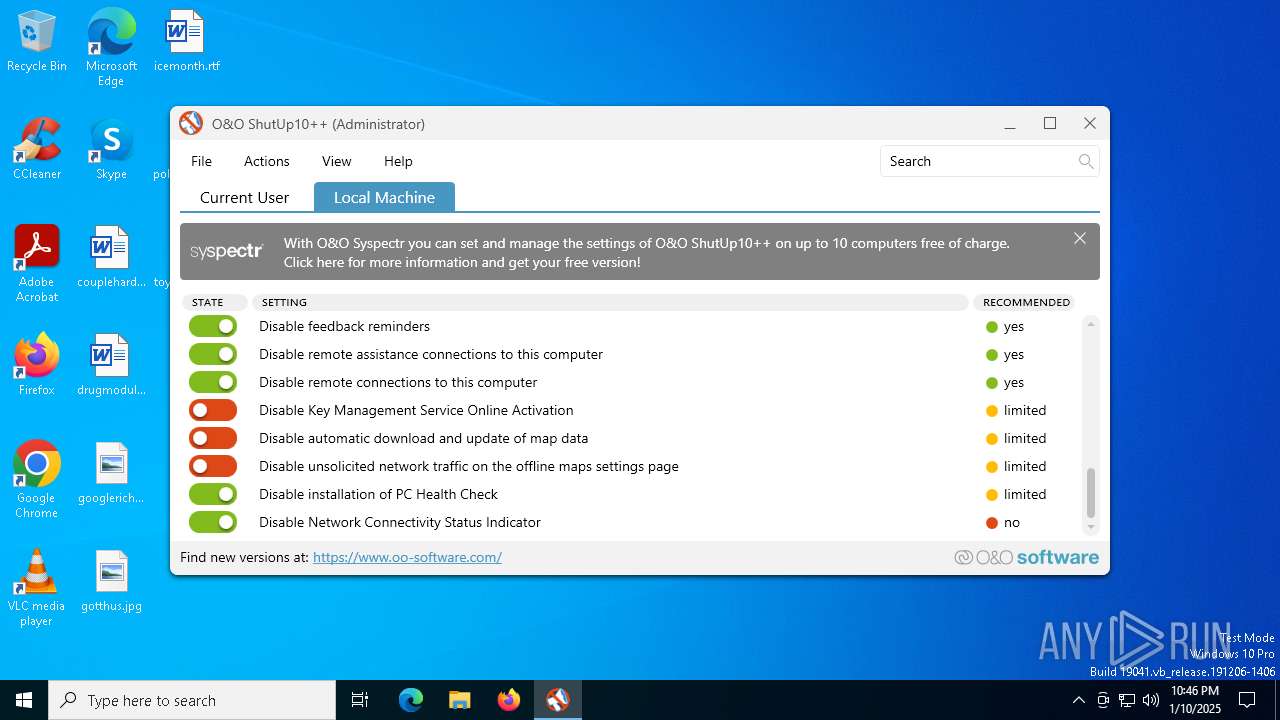
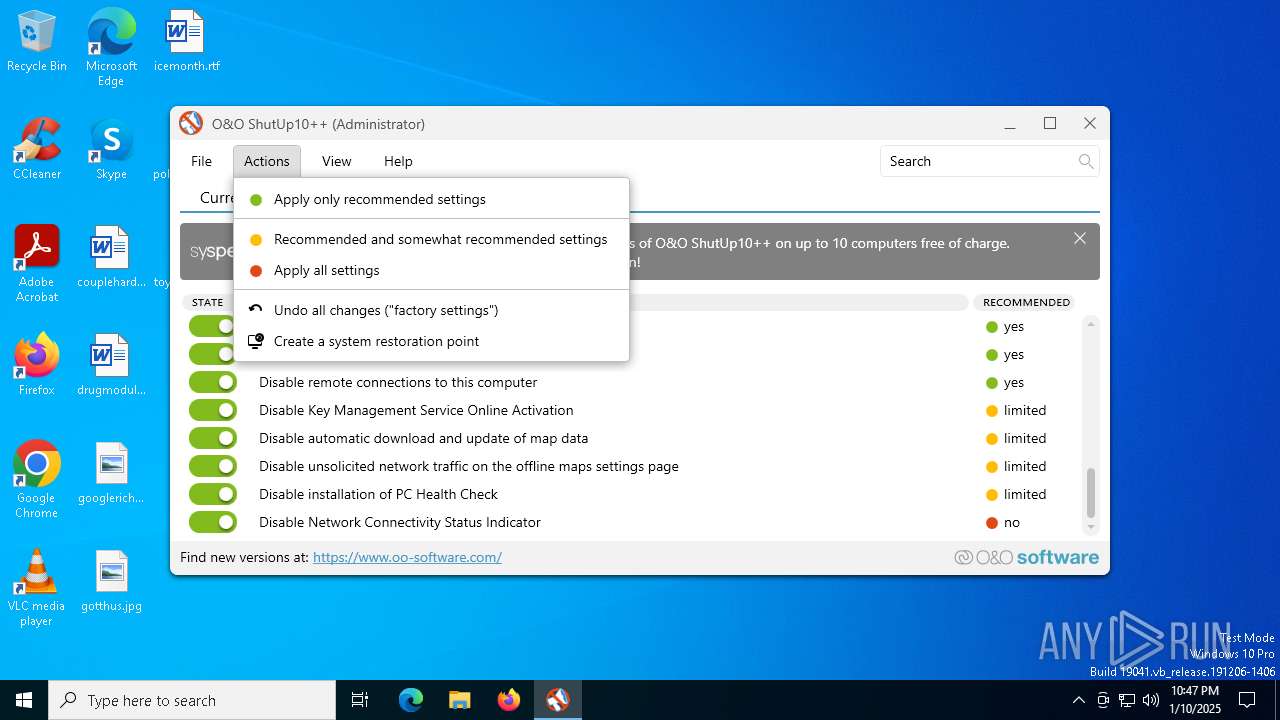
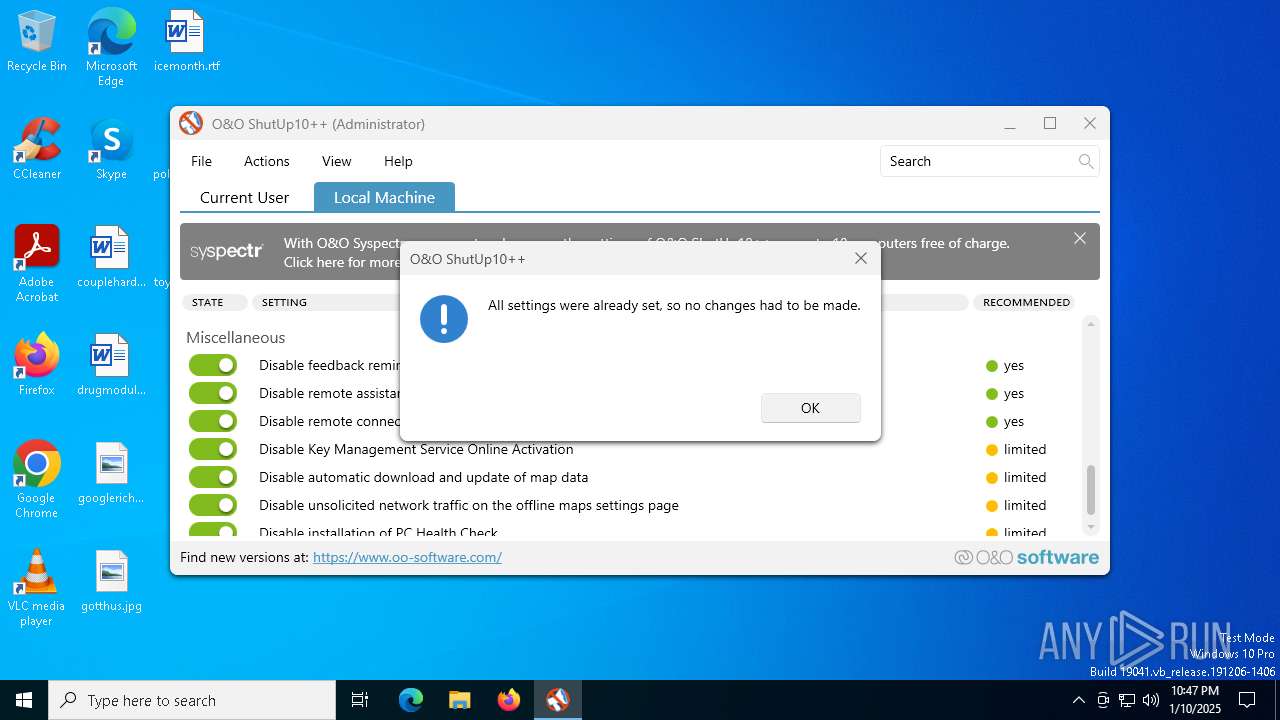
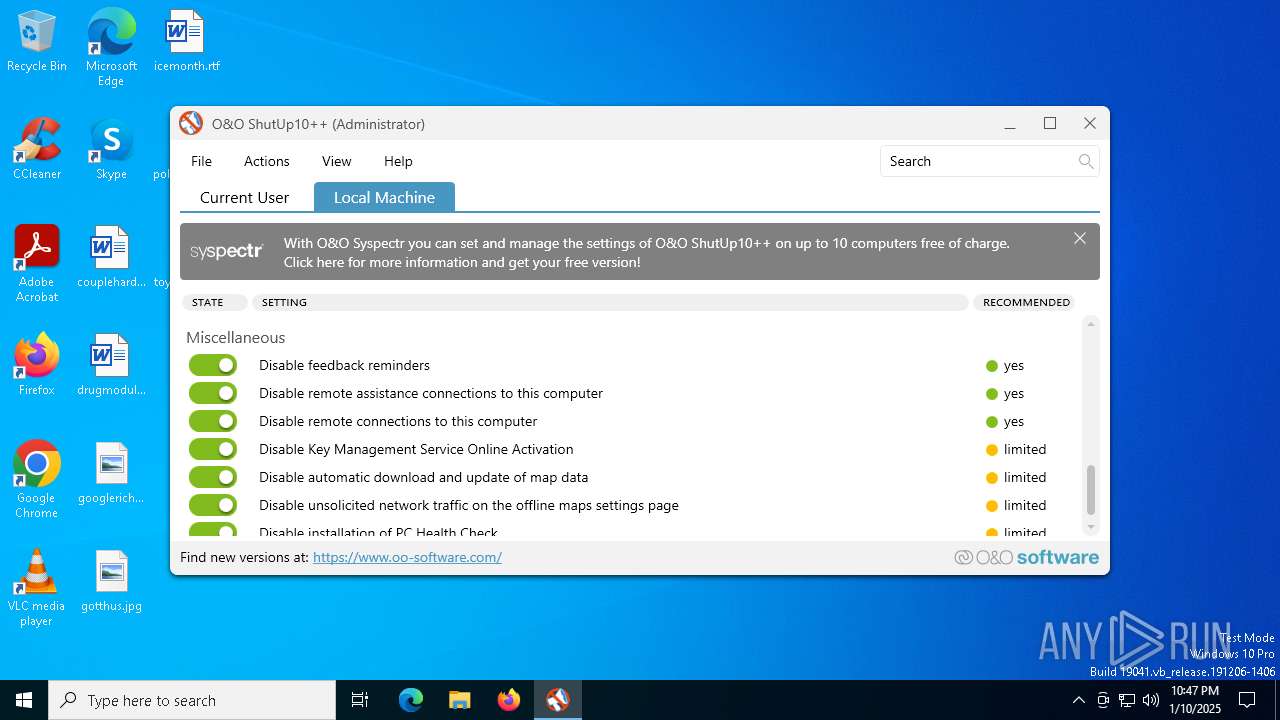
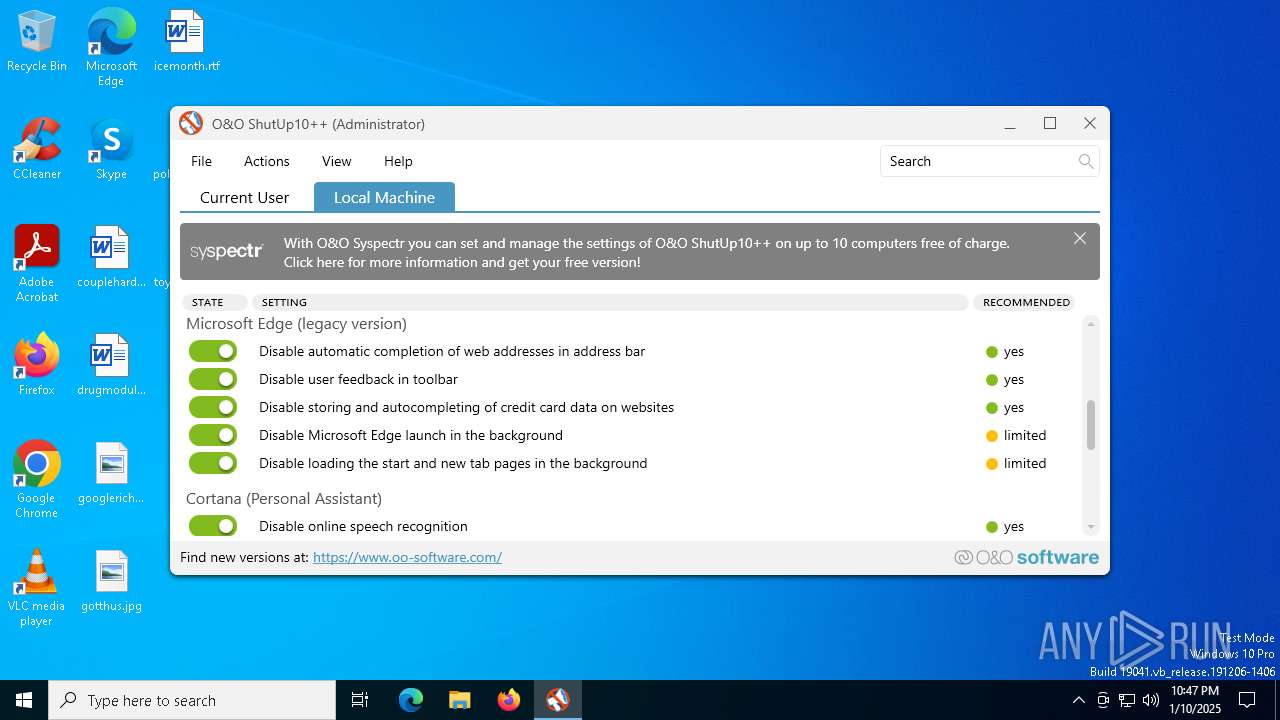
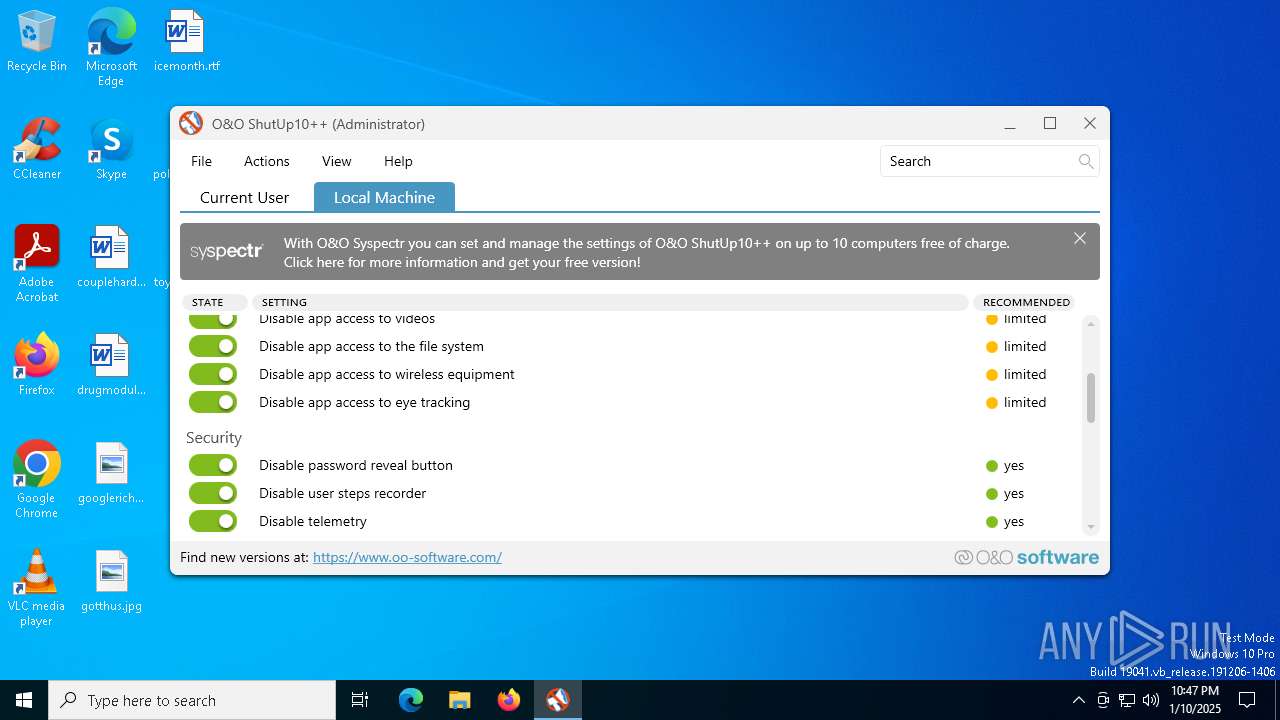
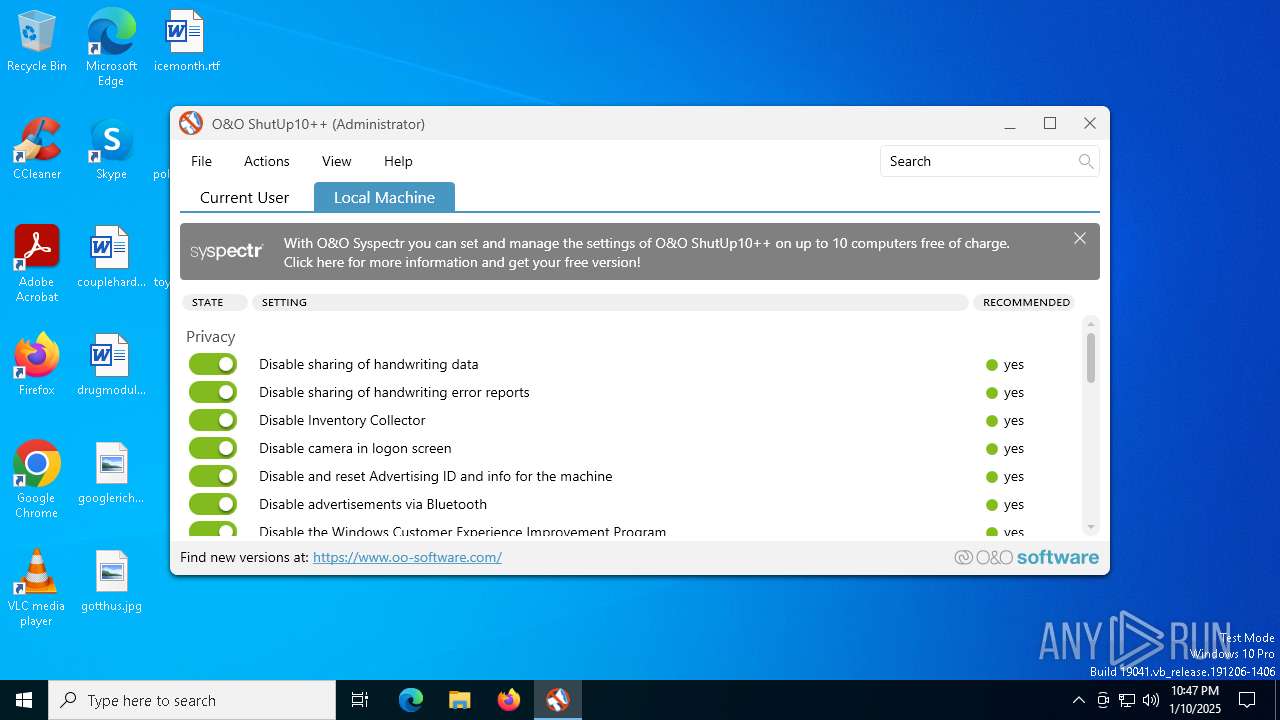
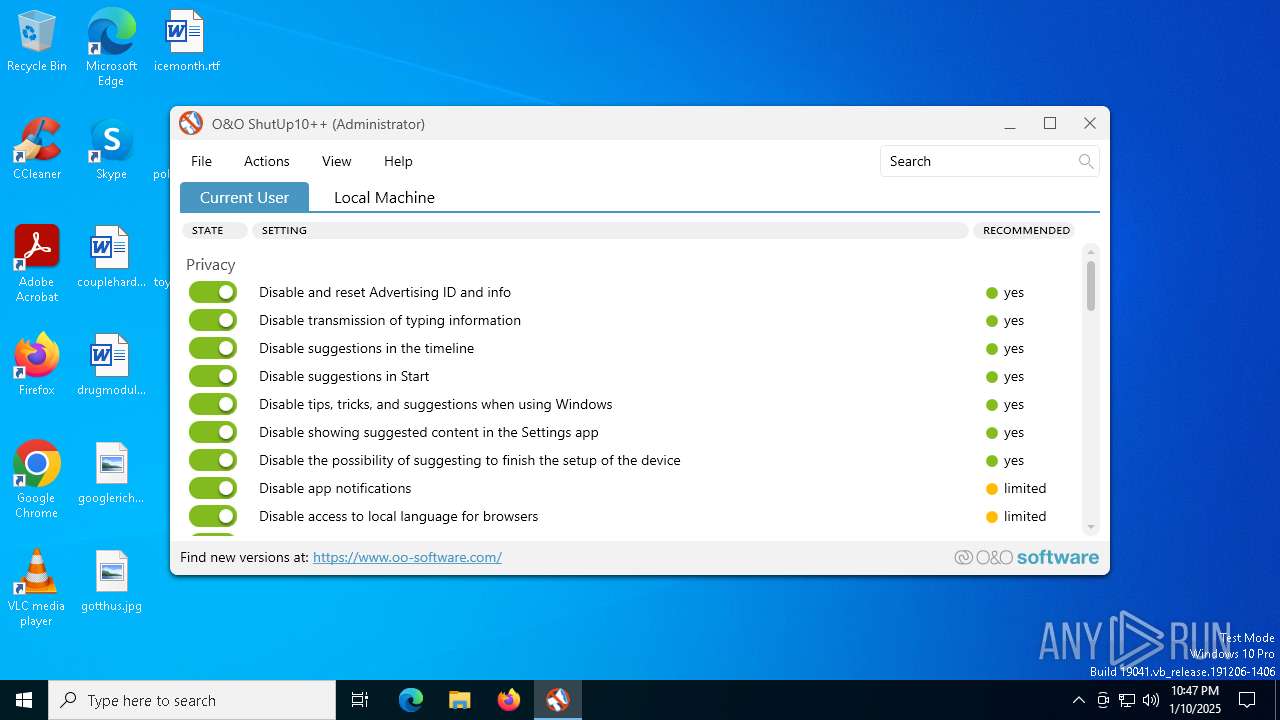
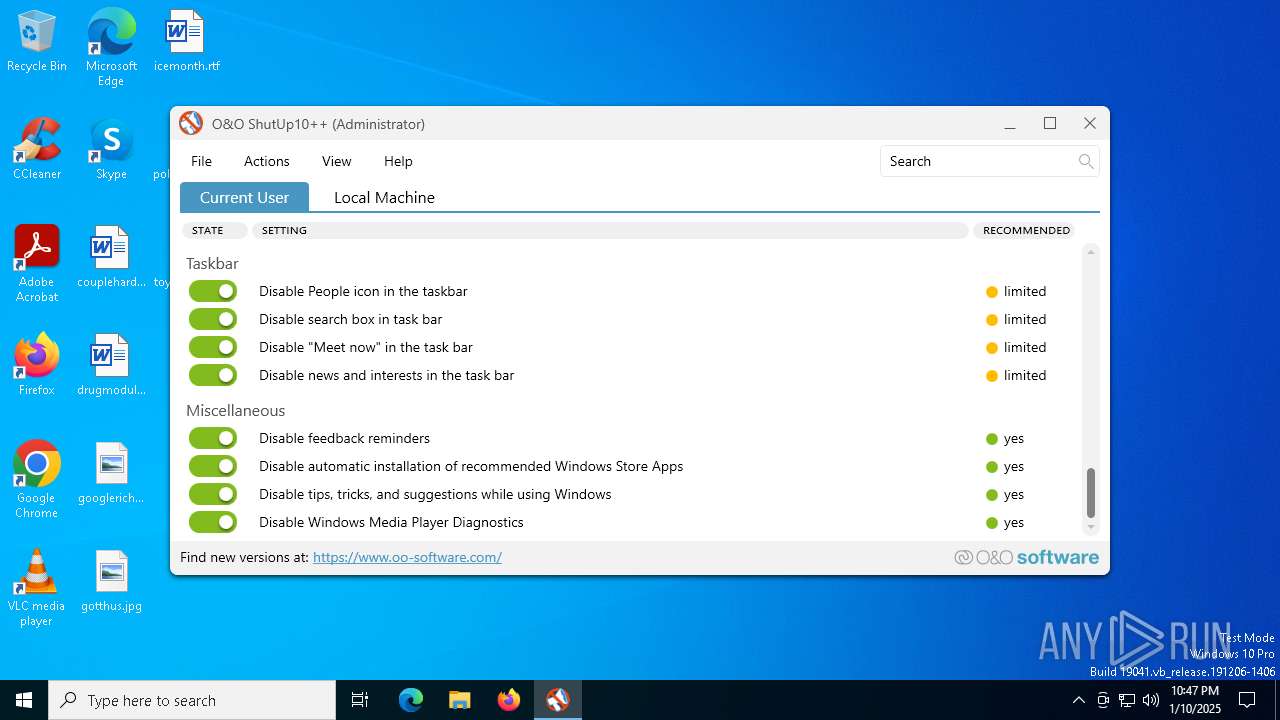
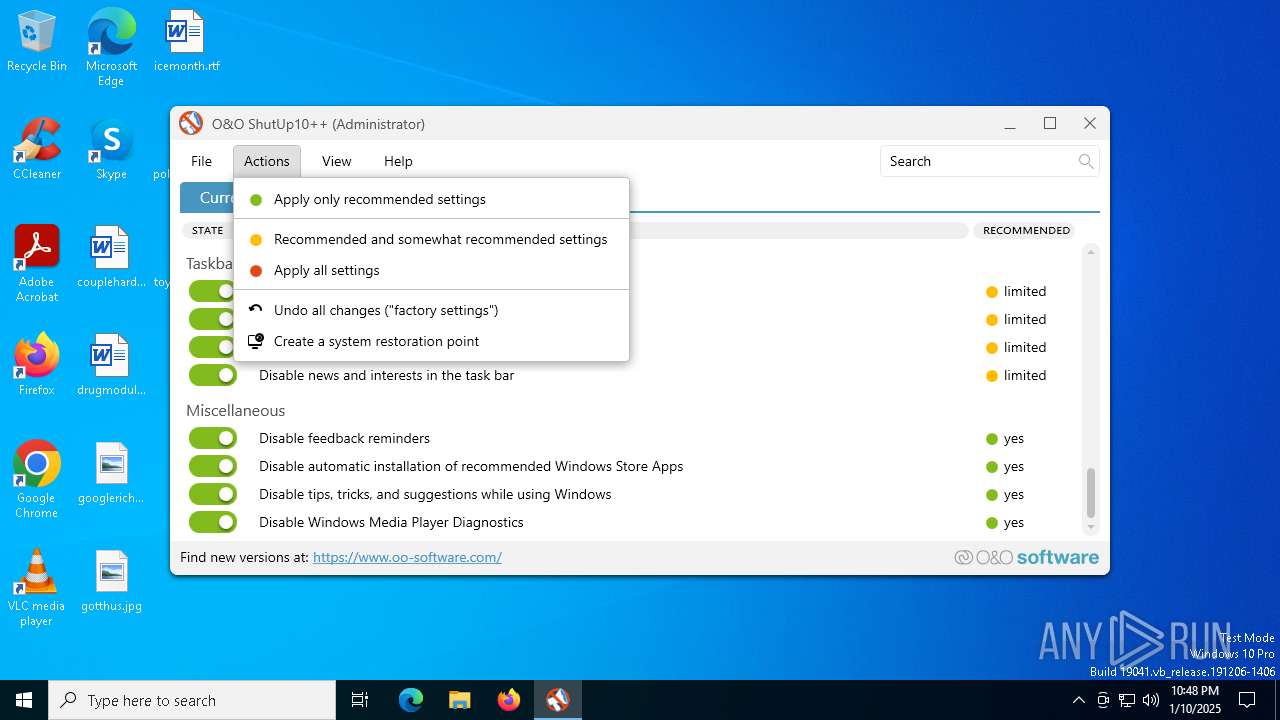
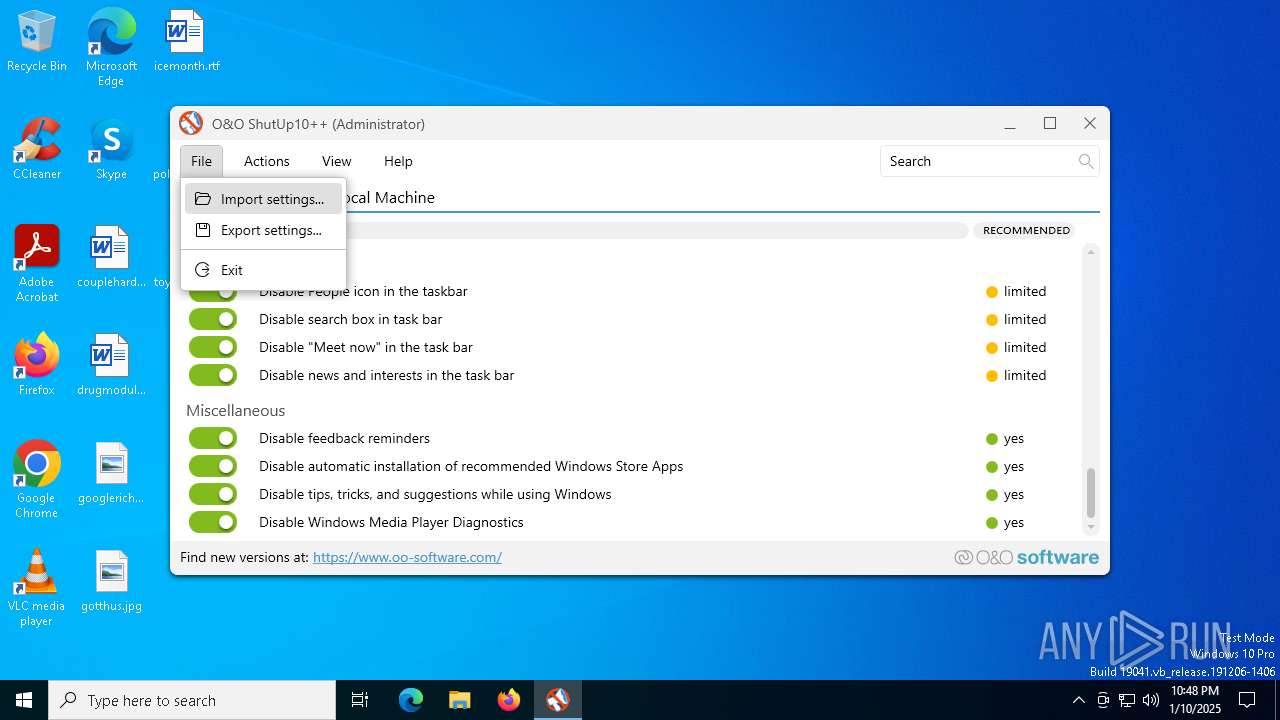
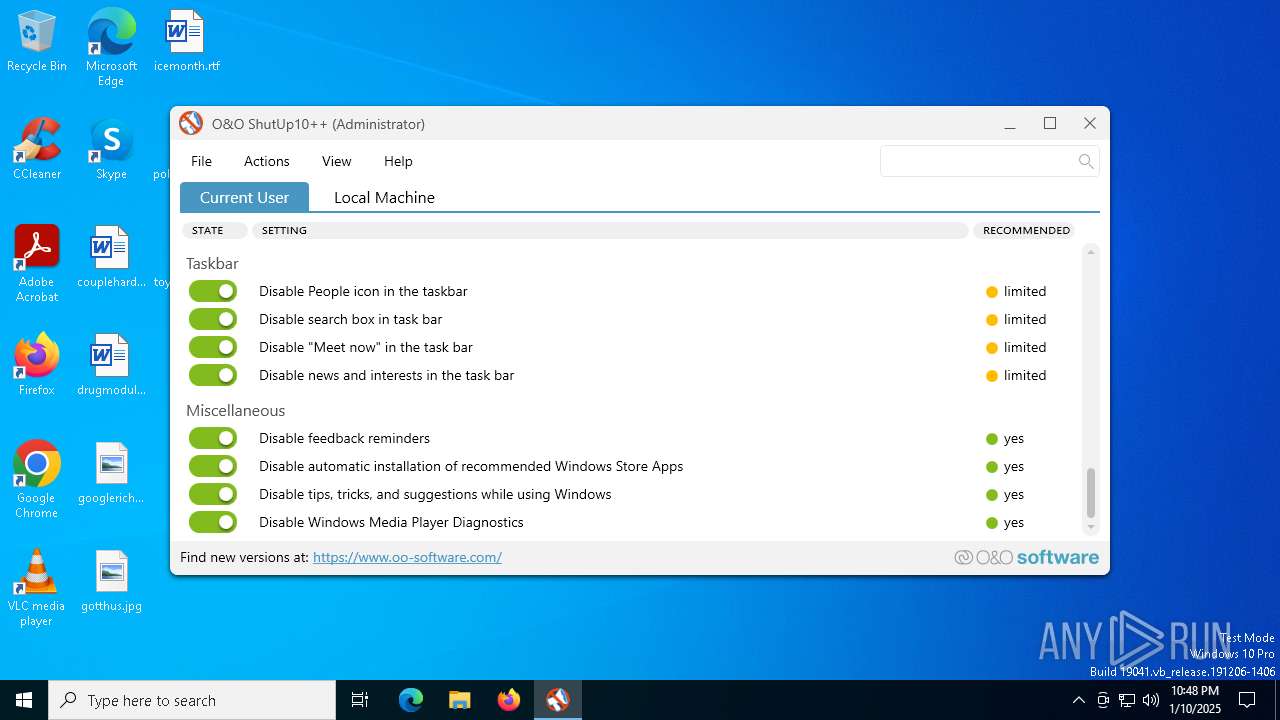
| Comments: | O&O ShutUp10++ - Free antispy tool for Windows 10 and 11 |
| CompanyName: | O&O Software GmbH |
| FileDescription: | O&O ShutUp10++ - Free antispy tool for Windows 10 and 11 |
| FileVersion: | 1.9.1442.423 |
| InternalName: | OOSU10.exe |
| LegalCopyright: | © 2015-2024 O&O Software GmbH, Berlin. |
| LegalTrademarks: | - |
| OriginalFileName: | OOSU10.exe |
| ProductName: | O&O ShutUp10++ |
| ProductVersion: | 1.9.1442.423 |
| AssemblyVersion: | 1.9.1442.423 |
Total processes
143
Monitored processes
9
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
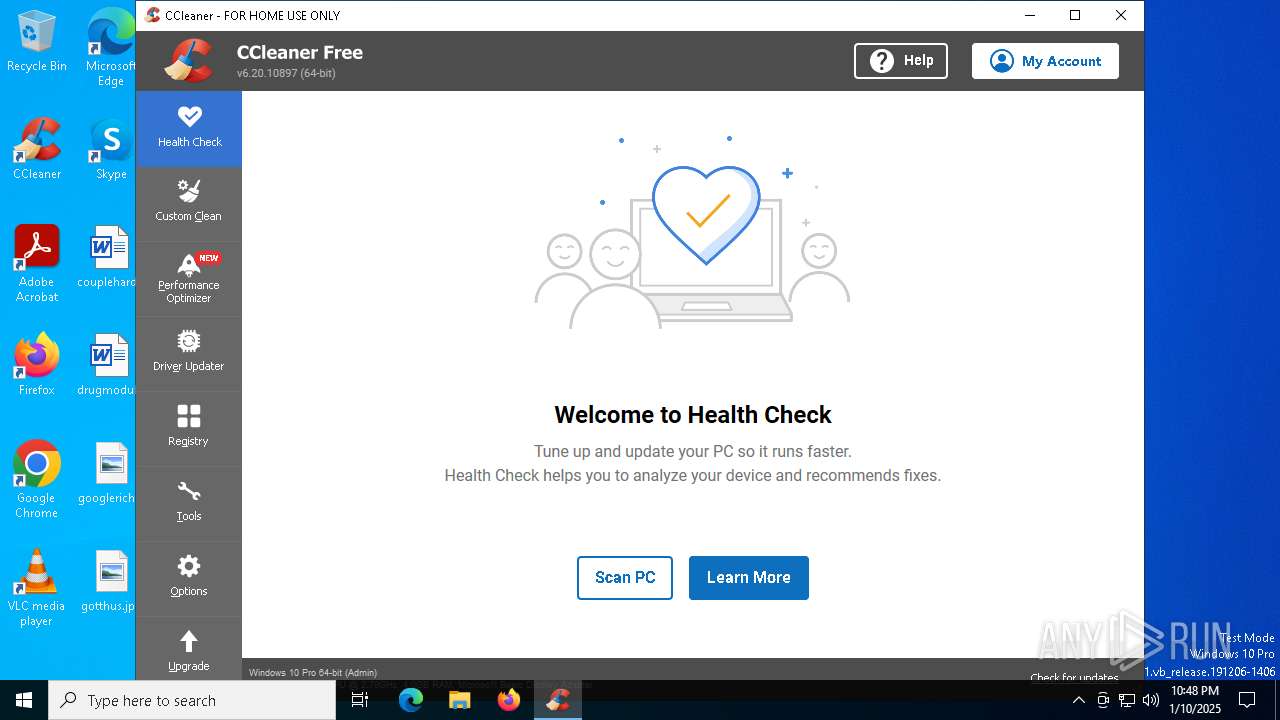
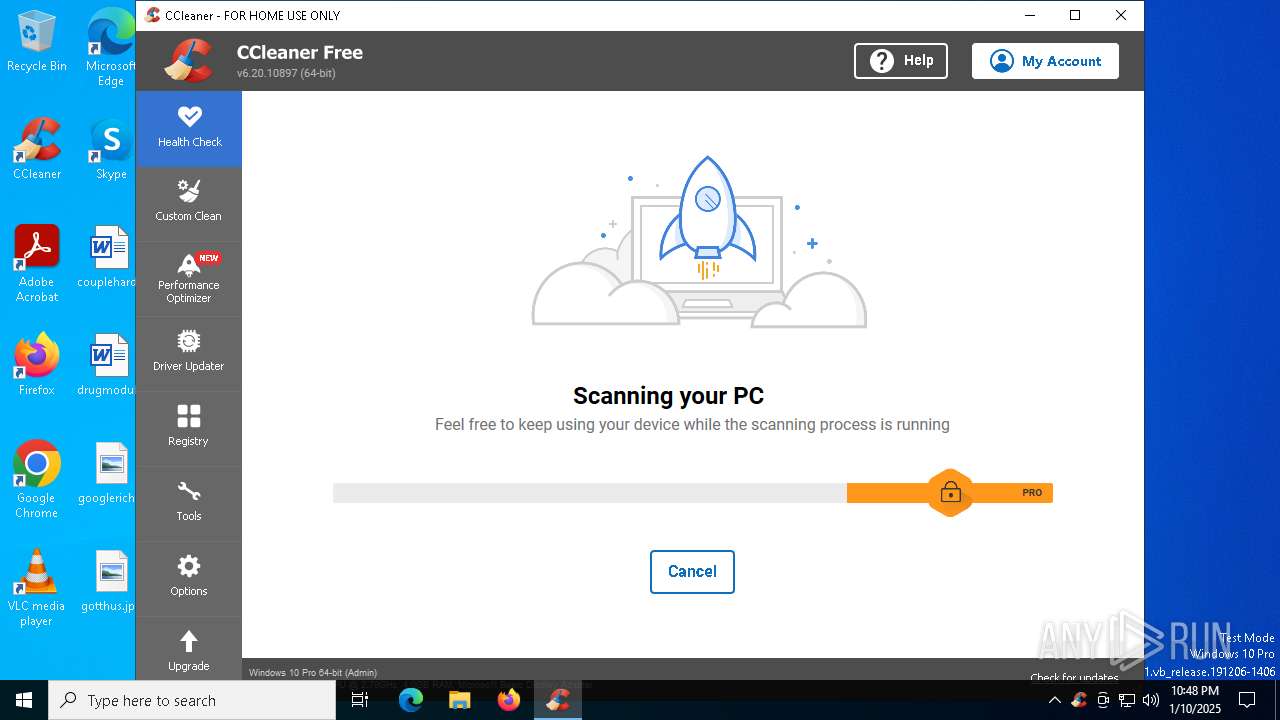
| 236 | "C:\Program Files\CCleaner\CCleaner64.exe" /uac | C:\Program Files\CCleaner\CCleaner64.exe | CCleaner64.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Version: 6.20.0.10897 Modules
| |||||||||||||||
| 3988 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4876 | "C:\Users\admin\Downloads\OOSU10.exe" | C:\Users\admin\Downloads\OOSU10.exe | — | explorer.exe | |||||||||||
User: admin Company: O&O Software GmbH Integrity Level: MEDIUM Description: O&O ShutUp10++ - Free antispy tool for Windows 10 and 11 Exit code: 3221226540 Version: 1.9.1442.423 Modules
| |||||||||||||||
| 5092 | "C:\Users\admin\Downloads\OOSU10.exe" | C:\Users\admin\Downloads\OOSU10.exe | explorer.exe | ||||||||||||
User: admin Company: O&O Software GmbH Integrity Level: HIGH Description: O&O ShutUp10++ - Free antispy tool for Windows 10 and 11 Exit code: 0 Version: 1.9.1442.423 Modules
| |||||||||||||||
| 5592 | "C:\Users\admin\AppData\Local\Temp\reg1.exe" delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore" /v "SystemRestorePointCreationFrequency" /f /reg:64 | C:\Users\admin\AppData\Local\Temp\reg1.exe | — | OOSU10.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
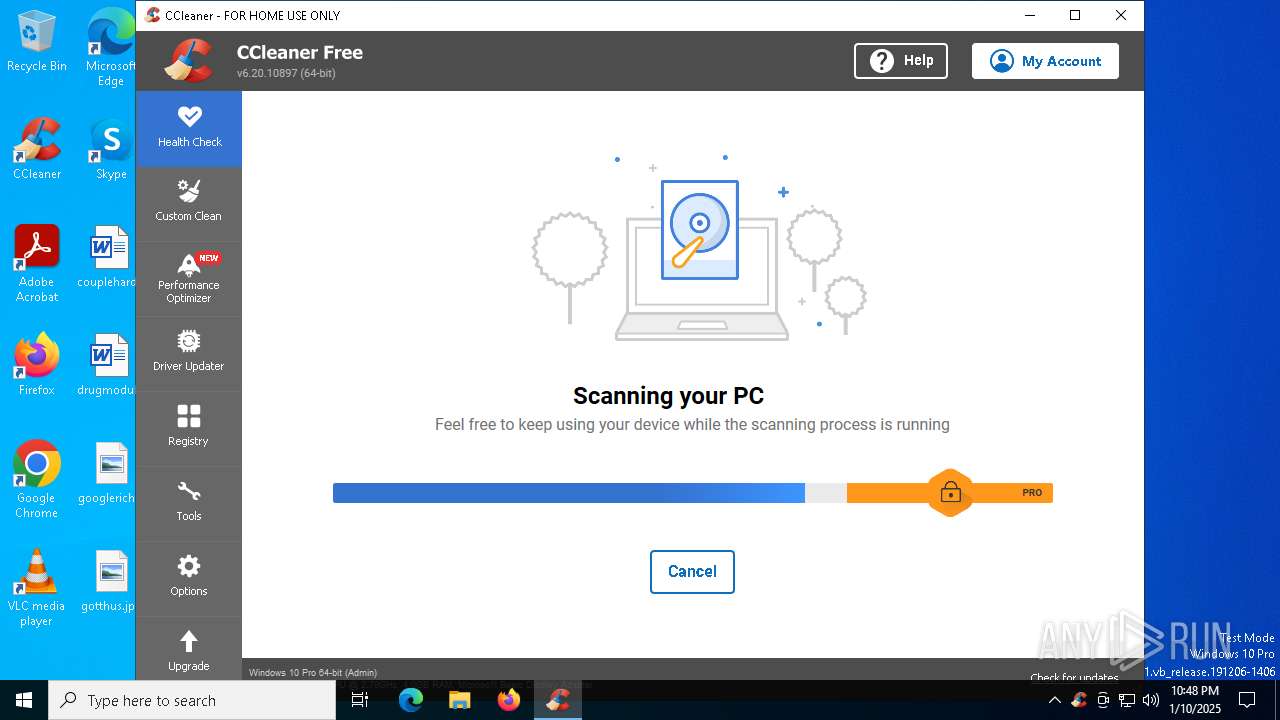
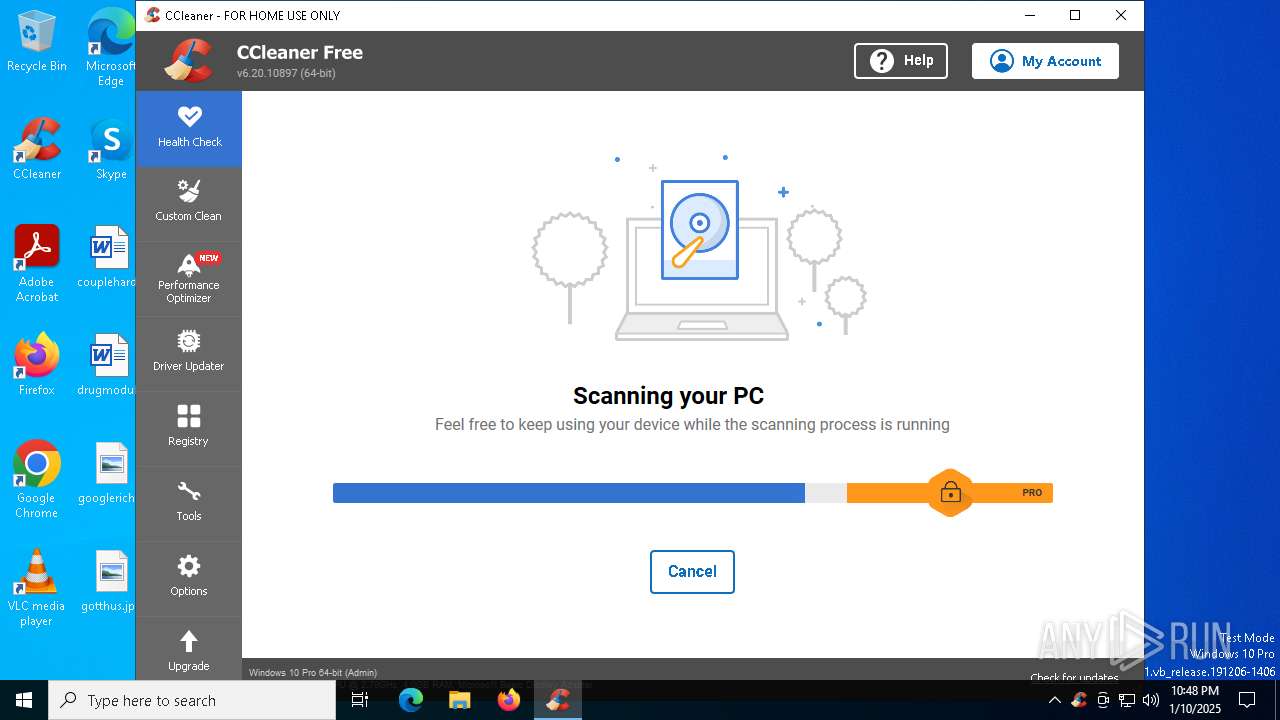
| 5592 | "C:\Program Files\CCleaner\CCleaner64.exe" /monitor | C:\Program Files\CCleaner\CCleaner64.exe | CCleaner64.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Version: 6.20.0.10897 Modules
| |||||||||||||||
| 6788 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6832 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
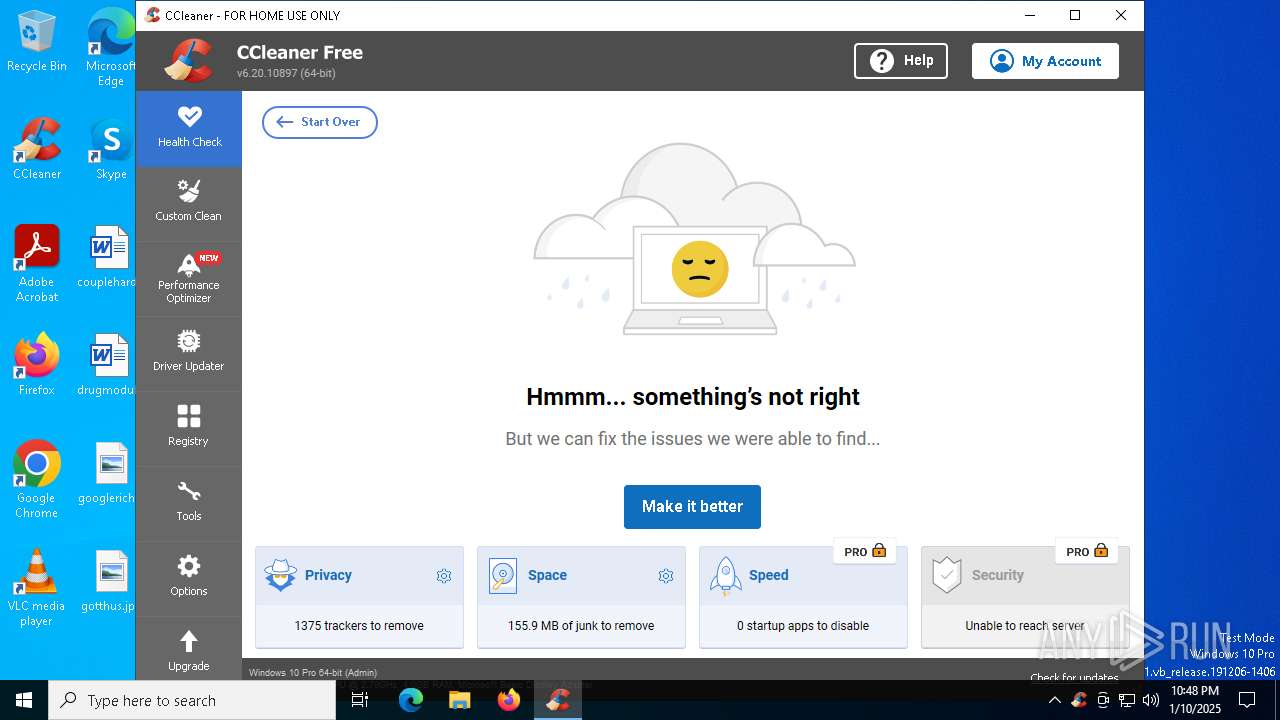
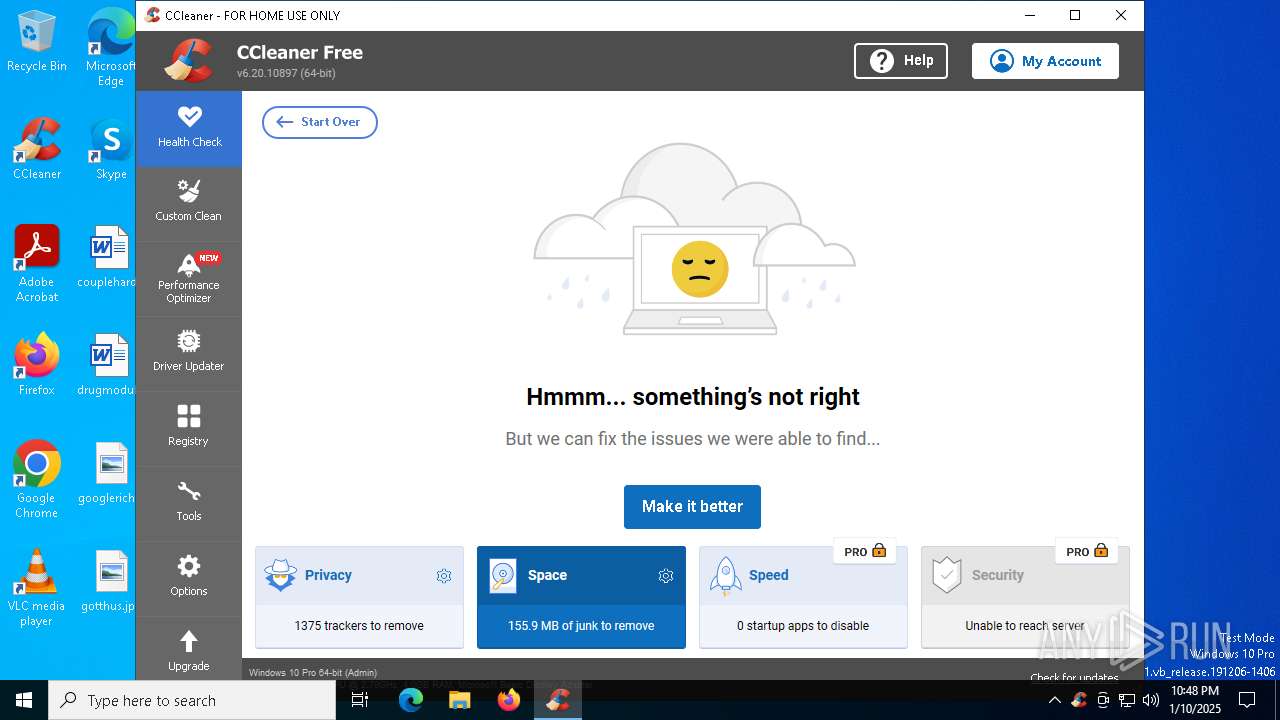
| 7156 | "C:\Program Files\CCleaner\CCleaner64.exe" | C:\Program Files\CCleaner\CCleaner64.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 6.20.0.10897 Modules
| |||||||||||||||
Total events
26 630
Read events
26 070
Write events
482
Delete events
78
Modification events
| (PID) Process: | (5092) OOSU10.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore |
| Operation: | delete value | Name: | SystemRestorePointCreationFrequency |
Value: | |||
| (PID) Process: | (6788) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000006E0C3840B163DB01841A0000A01A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6788) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000BF3A9040B163DB01841A0000A01A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6788) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000045039540B163DB01841A0000A01A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6788) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6788) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000CA732641B163DB01841A0000A01A0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6832) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E5B63441B163DB01B01A0000341B0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6832) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E5B63441B163DB01B01A0000CC1A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6832) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E5B63441B163DB01B01A00002C1B0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6832) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E5B63441B163DB01B01A0000D01A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
6
Suspicious files
29
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6788 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5092 | OOSU10.exe | C:\Users\admin\Downloads\OOSU10.cfg | xml | |
MD5:89EF7C4AD57313D2A8D77952BD68294C | SHA256:6FC5BE004704AFB018FC83A8934F6C8EE54C4F39F35CFD9A5FE0E21453975F7E | |||
| 5092 | OOSU10.exe | C:\Users\admin\AppData\Local\Temp\reg1.exe | executable | |
MD5:227F63E1D9008B36BDBCC4B397780BE4 | SHA256:C0E25B1F9B22DE445298C1E96DDFCEAD265CA030FA6626F61A4A4786CC4A3B7D | |||
| 6788 | dllhost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{2a93c9a2-445b-4650-9dc5-866cf8f51241}_OnDiskSnapshotProp | binary | |
MD5:6E3E3BAA17A9D04CA0EC007836E22A59 | SHA256:6A64D0FBC77933EEC6966A512EBF0CD5D48E5530110BE02036006E0024BE42A8 | |||
| 236 | CCleaner64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4BM0R4WAEQQQXTVZTC9D.temp | binary | |
MD5:6010AB2DDB35A08C82E6AE14857F1779 | SHA256:25BFA3B2A715D72CF859E7E311AE6B79BD1197E1F124EC1D243D4E022C68538D | |||
| 6788 | dllhost.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:6E3E3BAA17A9D04CA0EC007836E22A59 | SHA256:6A64D0FBC77933EEC6966A512EBF0CD5D48E5530110BE02036006E0024BE42A8 | |||
| 236 | CCleaner64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:E935BC5762068CAF3E24A2683B1B8A88 | SHA256:A8ACCFCFEB51BD73DF23B91F4D89FF1A9EB7438EF5B12E8AFDA1A6FF1769E89D | |||
| 236 | CCleaner64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\AFF4C9FF97737D462CF50EC898BC7191_BC43DAD391BCDC812EDD5190FB536EA5 | binary | |
MD5:C58E975B12ECB5B54036A685B55C49B7 | SHA256:407F0C00A53CEAABDF3347B3FB241FC12F584D5AD24BFC9EDE87A7A1C200FCB5 | |||
| 236 | CCleaner64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E573CDF4C6D731D56A665145182FD759_AFB3BE9383420FBAFF24AD413EEA555E | binary | |
MD5:8A9FEFF1785C6992736E608E2926F188 | SHA256:2F6E4177C1AD44F3241A084F75A429FE1FEBB5054146F67501A0215A8631272F | |||
| 236 | CCleaner64.exe | — | ||
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
54
DNS requests
36
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6160 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4640 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
236 | CCleaner64.exe | GET | 200 | 2.19.198.59:80 | http://ncc.avast.com/ncc.txt | unknown | — | — | whitelisted |
4640 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
236 | CCleaner64.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
236 | CCleaner64.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2220 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.163:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
236 | CCleaner64.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
Process | Message |
|---|---|
CCleaner64.exe | [2025-01-10 22:48:20.314] [error ] [settings ] [ 236: 4528] [000000: 0] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner64.exe | [2025-01-10 22:48:20.314] [error ] [ini_access ] [ 236: 4528] [000000: 0] Incorrect ini_accessor configuration! Fixing relative input path to avoid recursion. Input was: Setup
|
CCleaner64.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner64.exe | OnLanguage - en
|
CCleaner64.exe | [2025-01-10 22:48:20.782] [error ] [settings ] [ 236: 5680] [D2EC45: 356] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner64.exe | [2025-01-10 22:48:20.798] [error ] [Burger ] [ 236: 5680] [904E07: 253] [23.2.1118.0] [BurgerReporter.cpp] [253] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner64.exe | [2025-01-10 22:48:20.798] [error ] [Burger ] [ 236: 5680] [904E07: 253] [23.2.1118.0] [BurgerReporter.cpp] [253] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner64.exe | file:///tis/optimizer.tis(1288) : warning :'async' does not contain any 'await'
|
CCleaner64.exe | file:///tis/optimizer.tis(1131) : warning :'await' should be used only inside 'async' or 'event'
|
CCleaner64.exe | startCheckingLicense()
|