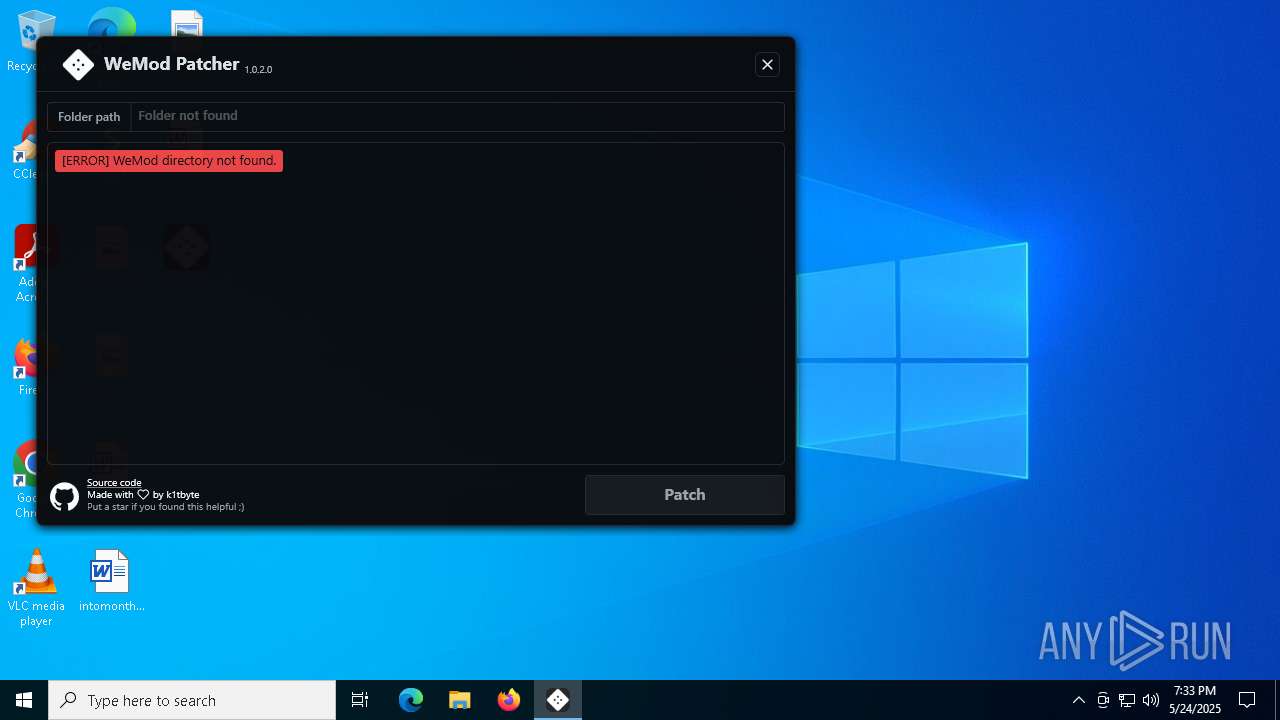
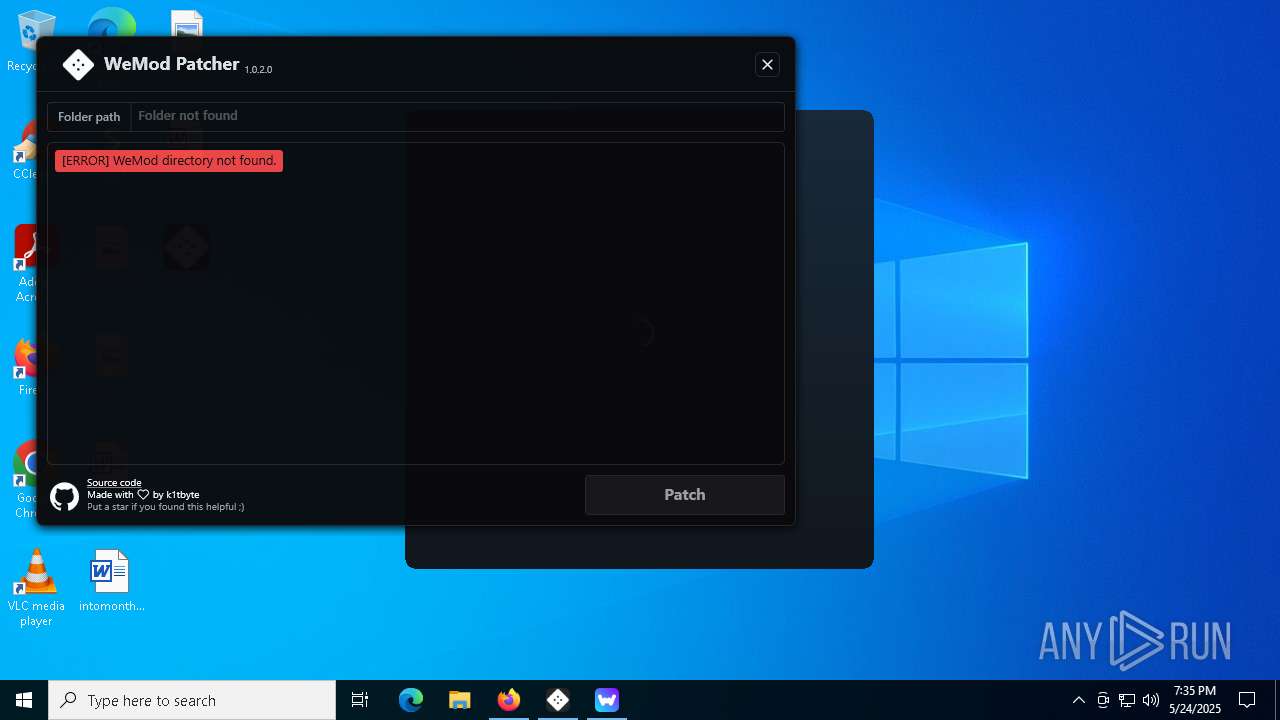
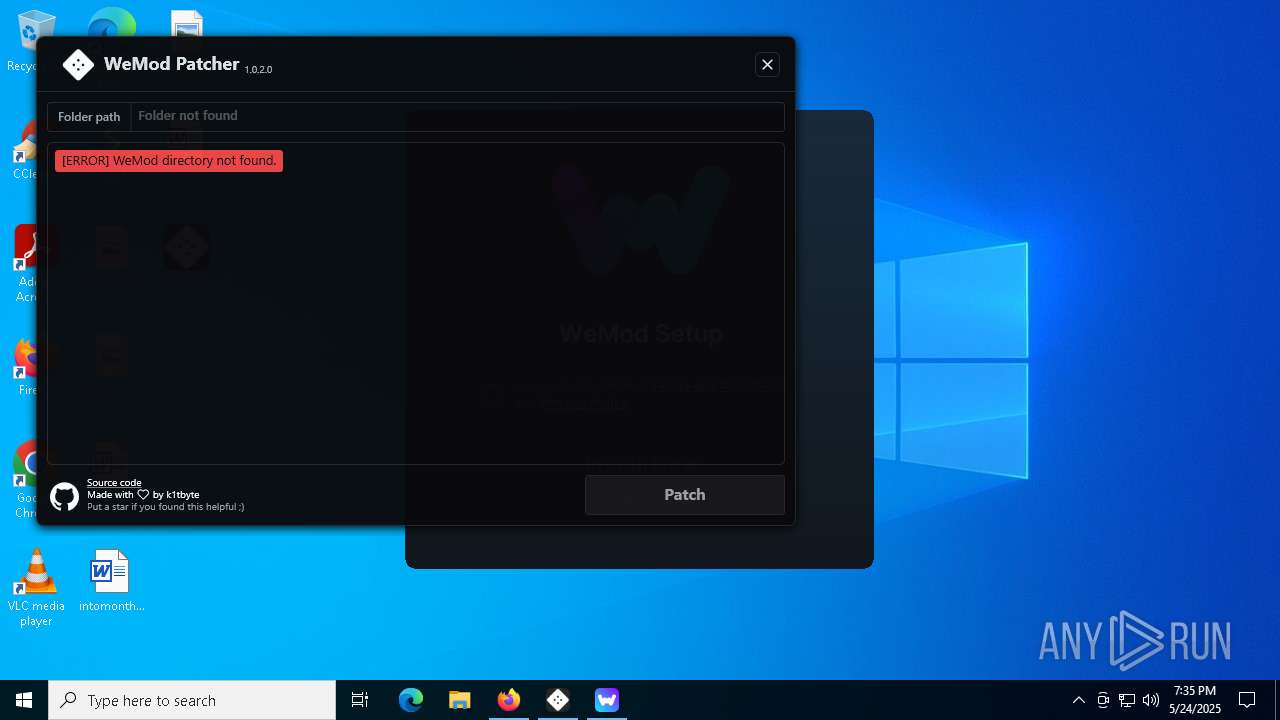
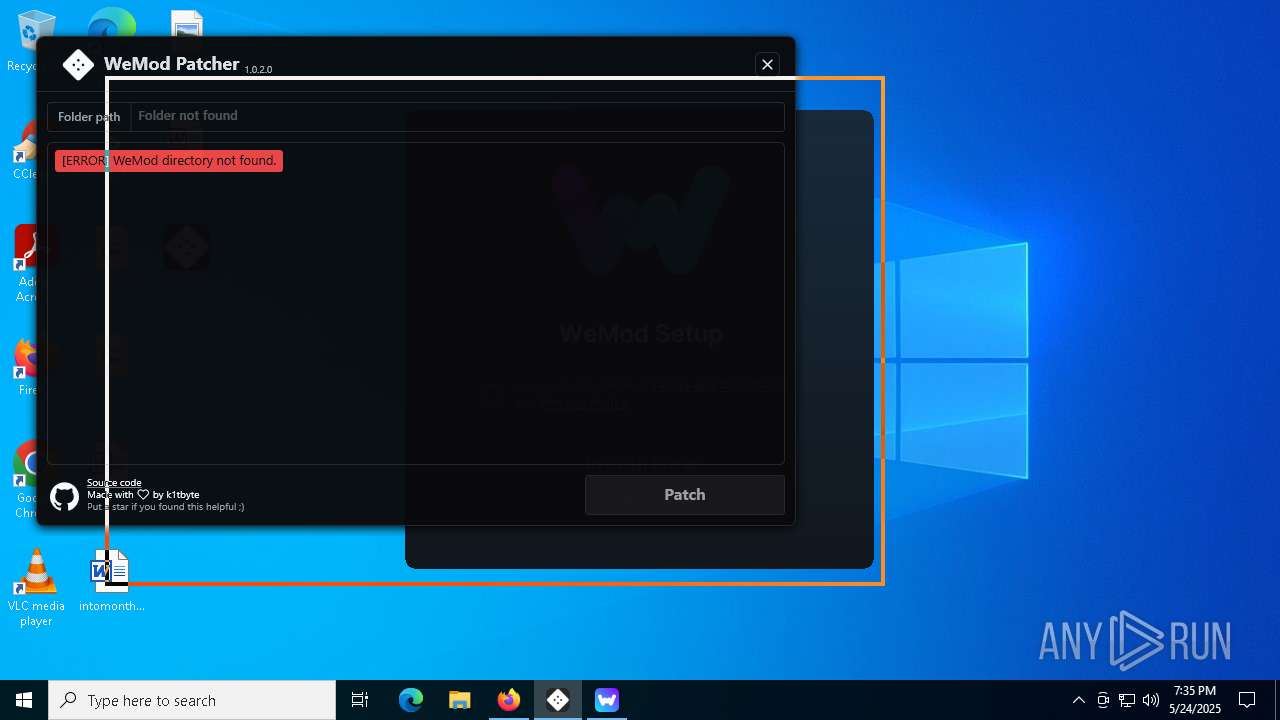
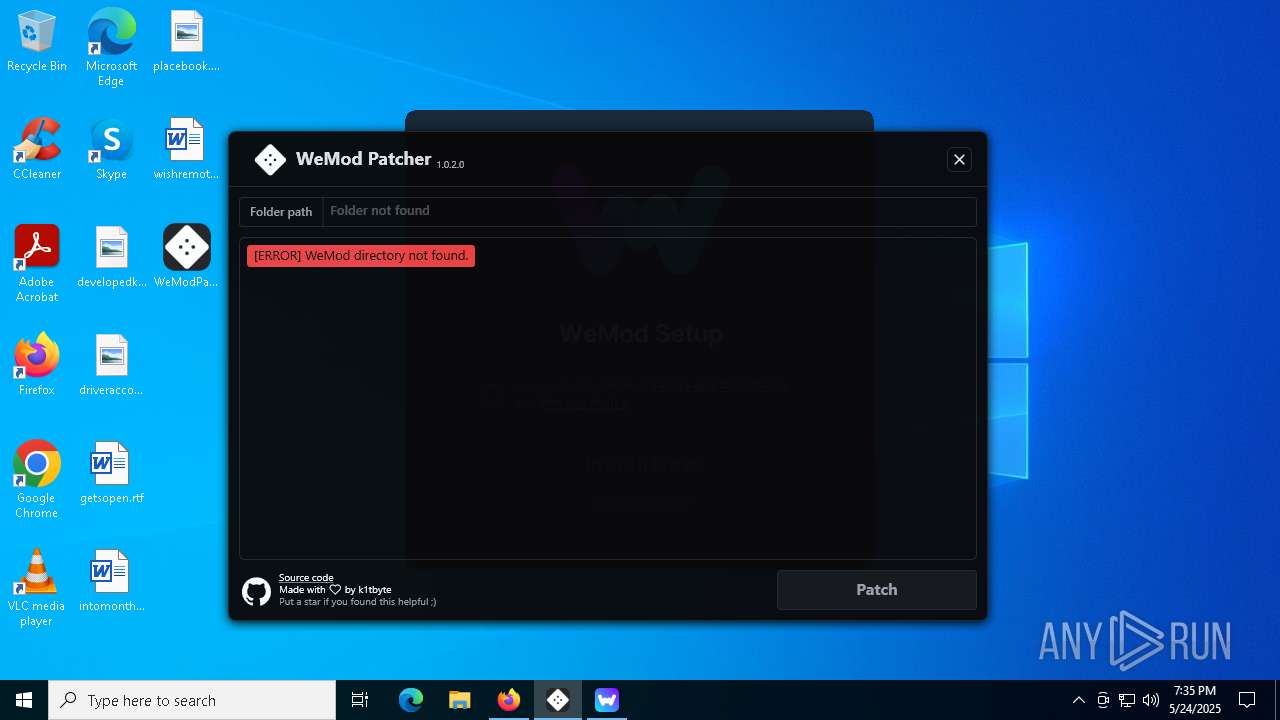
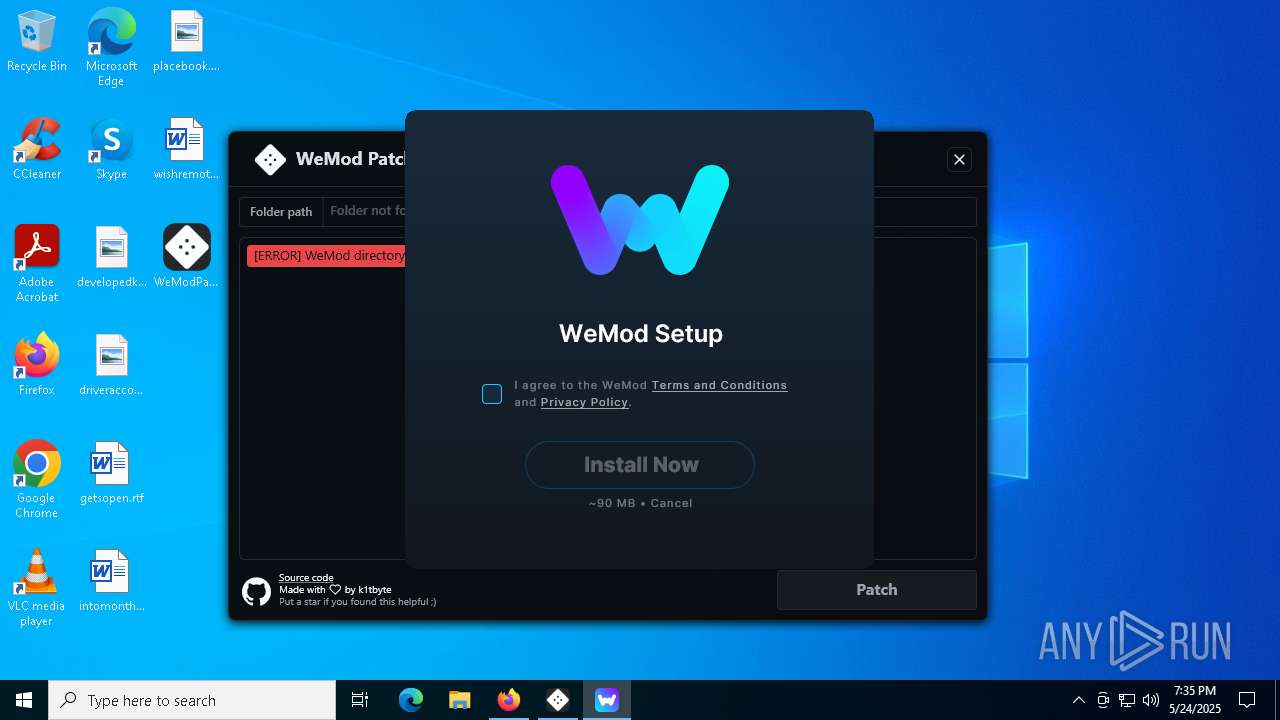
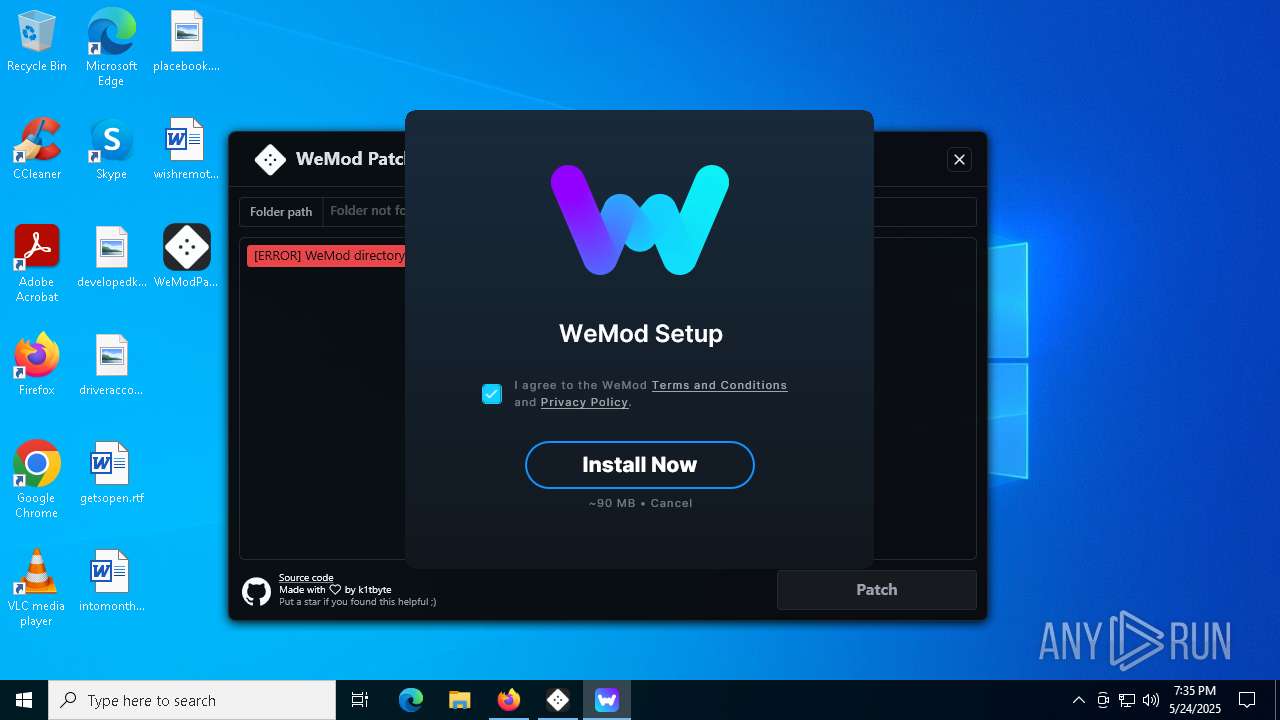
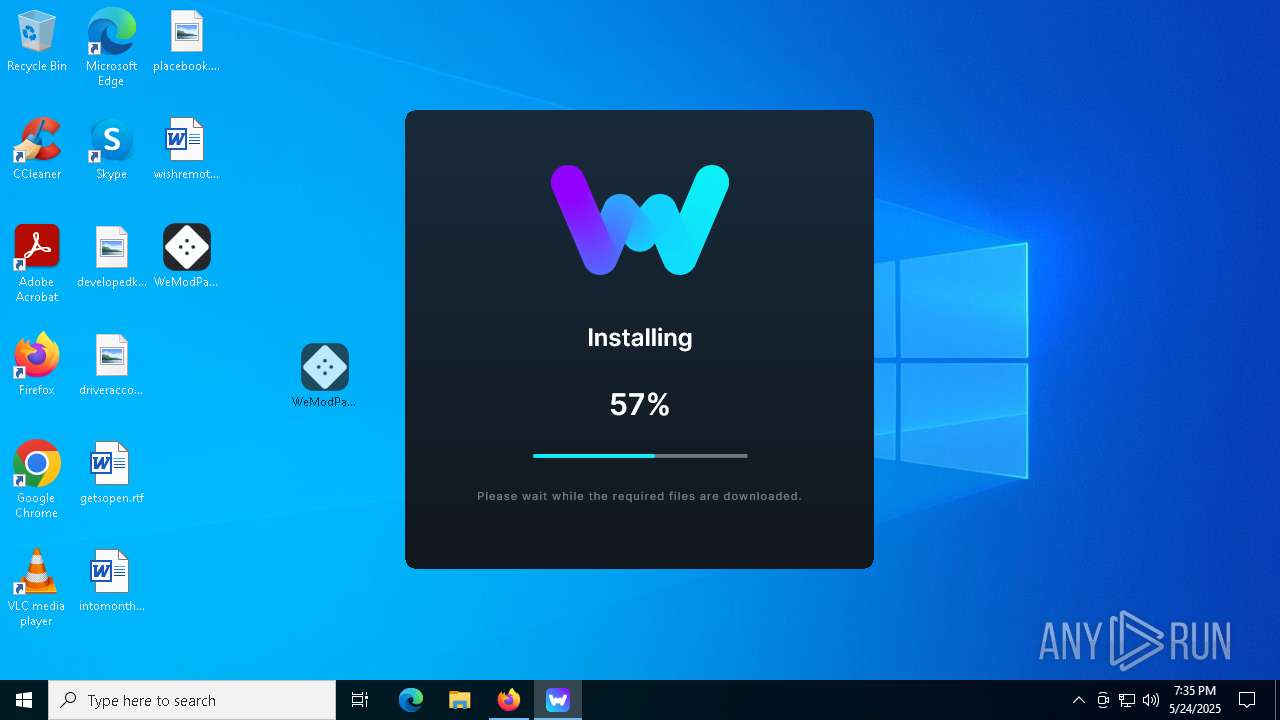
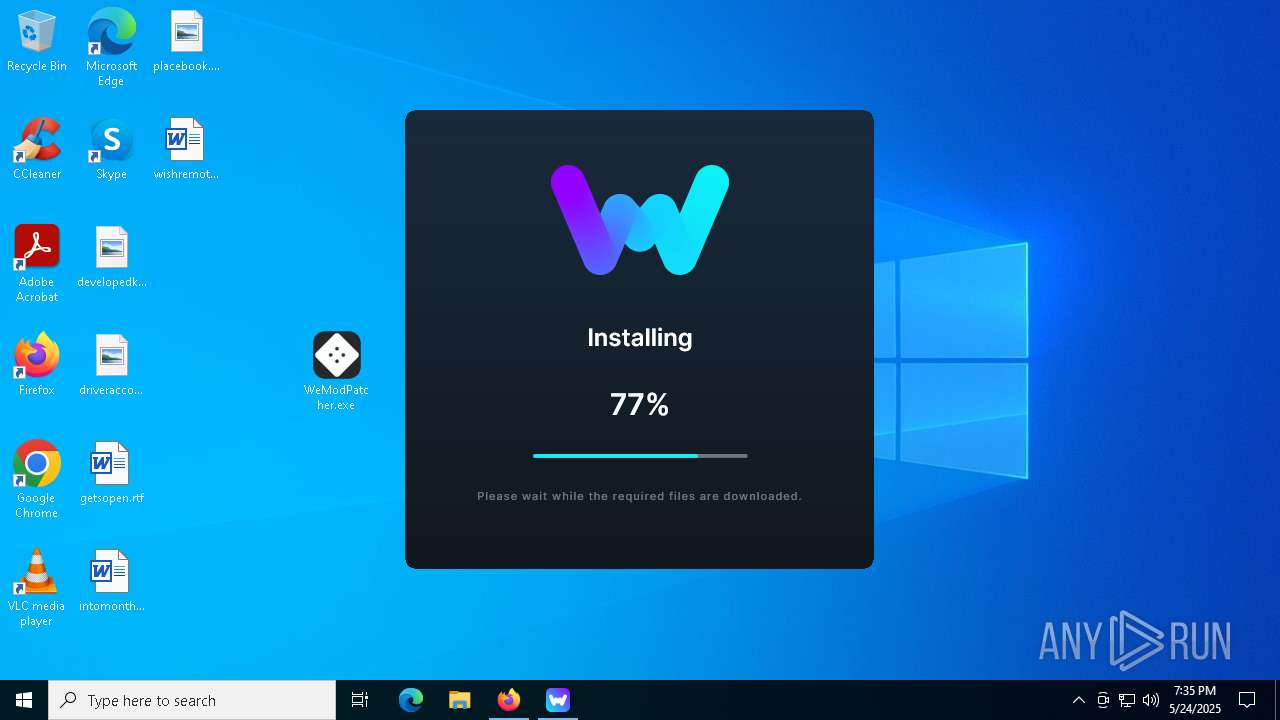
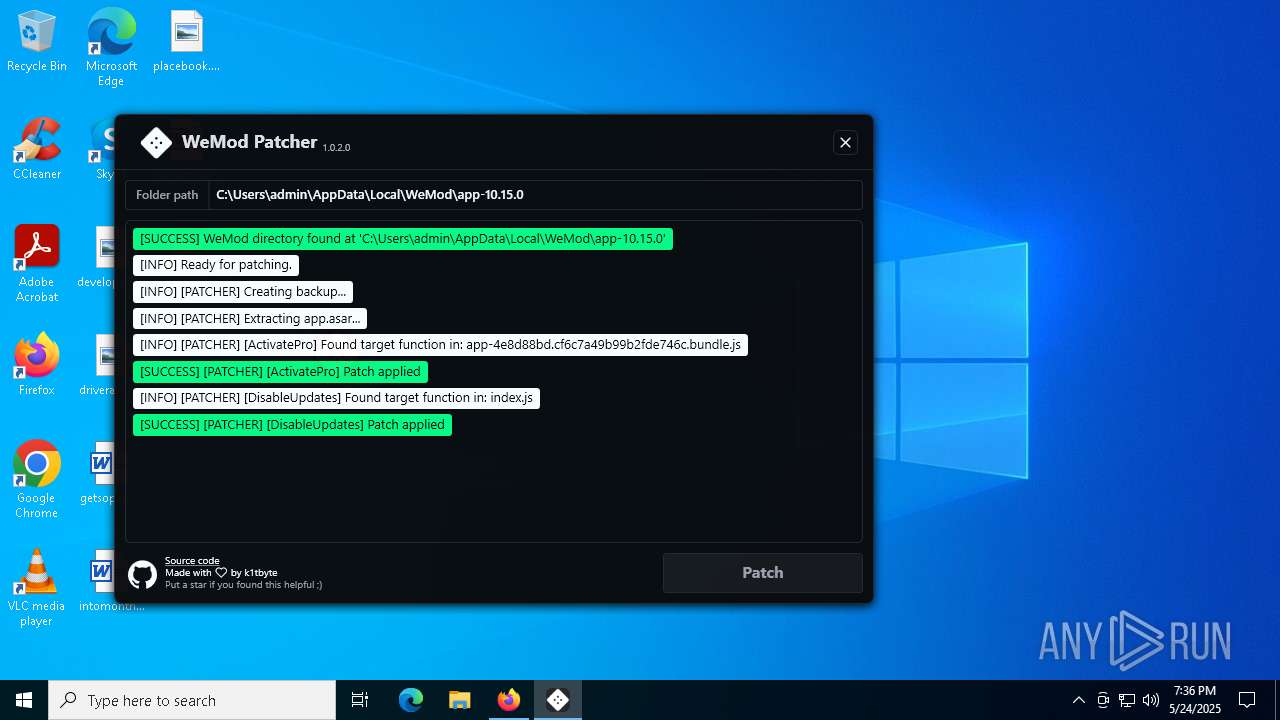
| File name: | WeModPatcher.exe |
| Full analysis: | https://app.any.run/tasks/e0d28839-1e97-492a-be74-289ba58b20ed |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2025, 19:32:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | F4B4FAA2150FEAA3112B646B16AAAE5D |
| SHA1: | 5A83C437E5E1ECBA2587563014220D8FB09AF3EE |
| SHA256: | E4F3BA47A68EA42F79681960862E193822BD4F3598294406930E7D06AA62F1BA |
| SSDEEP: | 6144:/E8kAJ3NgyH5rv0CK/xAcaX5yMM8kwJBAeW4jrpnp8oSNl15kewzNLsOGaeI9bXC:88DtZb0+JBAoFp8oSNl15keSGUBOcX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- WeMod-Setup.exe (PID: 8116)
- Update.exe (PID: 7876)
Reads Microsoft Outlook installation path
- WeMod-Setup.exe (PID: 8116)
Reads Internet Explorer settings
- WeMod-Setup.exe (PID: 8116)
Executable content was dropped or overwritten
- WeMod-Setup-638837121129775991.exe (PID: 4376)
- Update.exe (PID: 7876)
Process drops legitimate windows executable
- Update.exe (PID: 7876)
Reads the date of Windows installation
- Update.exe (PID: 7876)
- WeMod-Setup.exe (PID: 8116)
Creates a software uninstall entry
- Update.exe (PID: 7876)
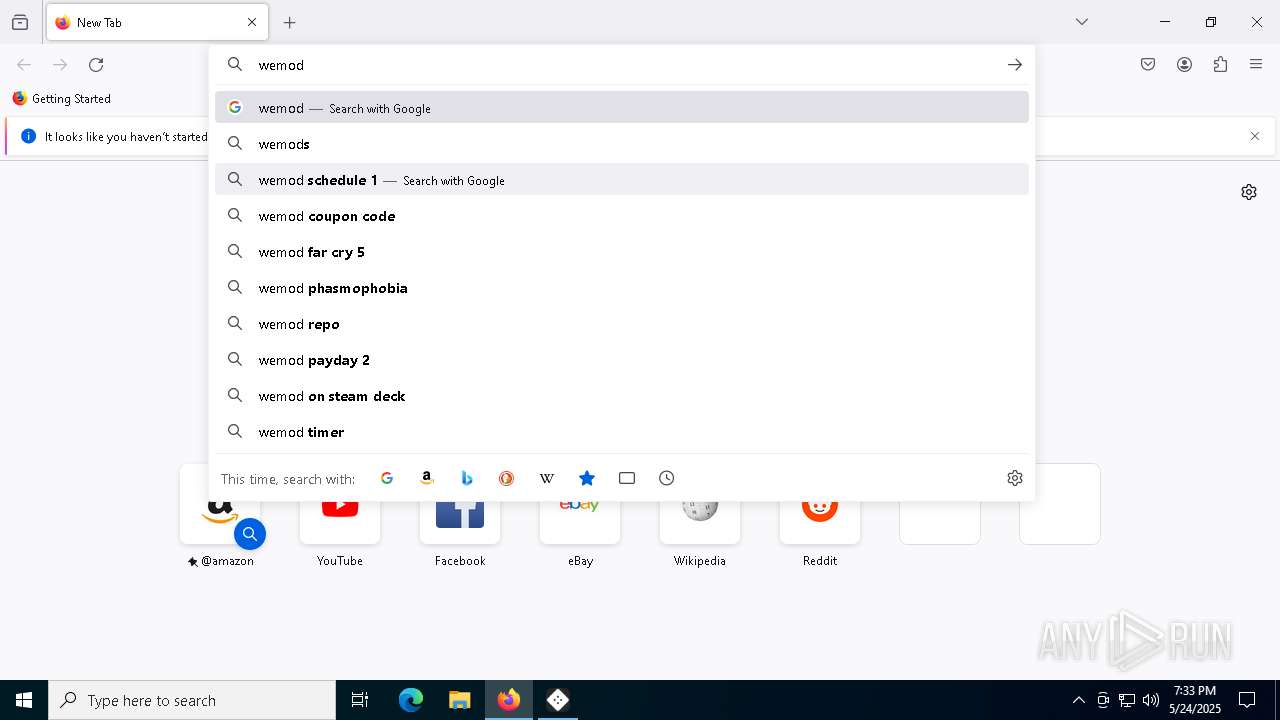
Searches for installed software
- Update.exe (PID: 7876)
Application launched itself
- WeMod.exe (PID: 732)
- WeMod.exe (PID: 4784)
INFO
Checks supported languages
- WeModPatcher.exe (PID: 6964)
- WeMod-Setup.exe (PID: 8116)
- WeMod-Setup-638837121129775991.exe (PID: 4376)
- Update.exe (PID: 7876)
- squirrel.exe (PID: 4944)
- WeMod.exe (PID: 2284)
- Update.exe (PID: 7336)
- Update.exe (PID: 4776)
Disables trace logs
- WeModPatcher.exe (PID: 6964)
- WeMod-Setup.exe (PID: 8116)
- Update.exe (PID: 7876)
Reads the machine GUID from the registry
- WeModPatcher.exe (PID: 6964)
- WeMod-Setup.exe (PID: 8116)
- Update.exe (PID: 7876)
- squirrel.exe (PID: 4944)
- Update.exe (PID: 7336)
- Update.exe (PID: 4776)
Reads the computer name
- WeModPatcher.exe (PID: 6964)
- WeMod-Setup.exe (PID: 8116)
- Update.exe (PID: 7876)
- squirrel.exe (PID: 4944)
- Update.exe (PID: 7336)
- Update.exe (PID: 4776)
Reads the software policy settings
- WeModPatcher.exe (PID: 6964)
- slui.exe (PID: 4008)
- WeMod-Setup.exe (PID: 8116)
- slui.exe (PID: 7336)
- Update.exe (PID: 7876)
Reads Environment values
- WeModPatcher.exe (PID: 6964)
- WeMod-Setup.exe (PID: 8116)
- WeMod.exe (PID: 2284)
- Update.exe (PID: 7876)
Checks proxy server information
- WeModPatcher.exe (PID: 6964)
- WeMod-Setup.exe (PID: 8116)
- slui.exe (PID: 7336)
- Update.exe (PID: 7876)
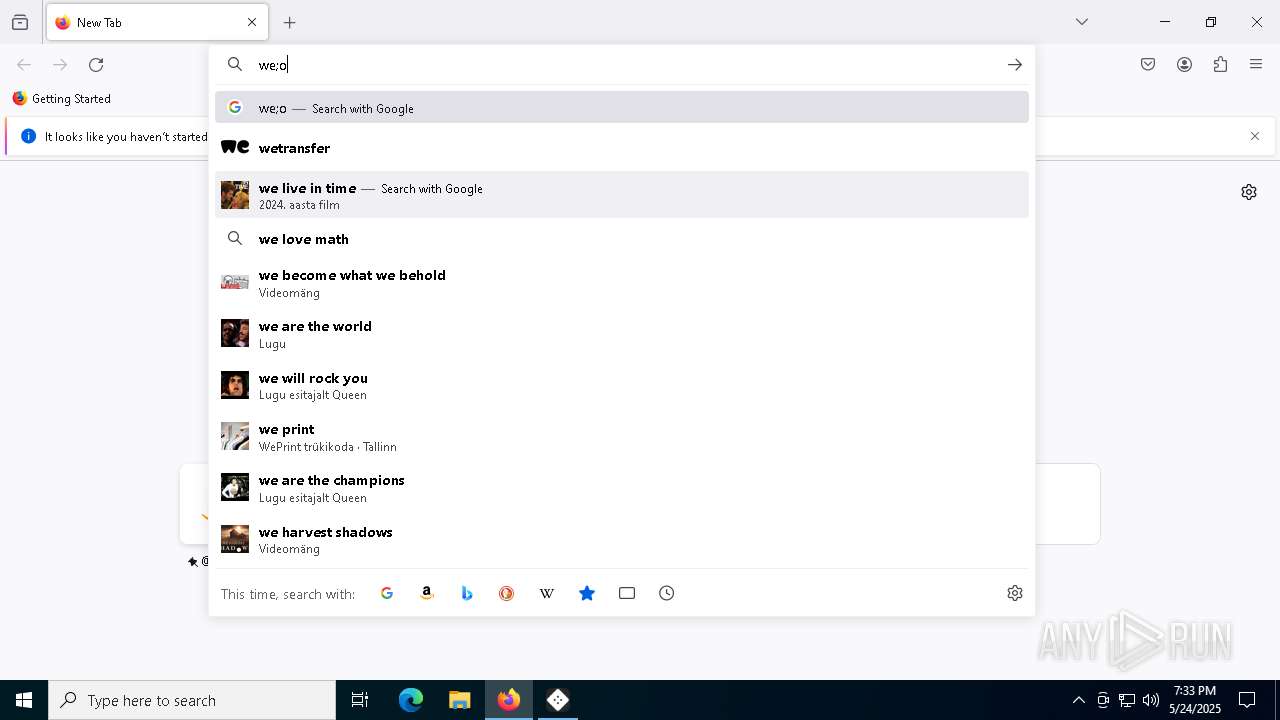
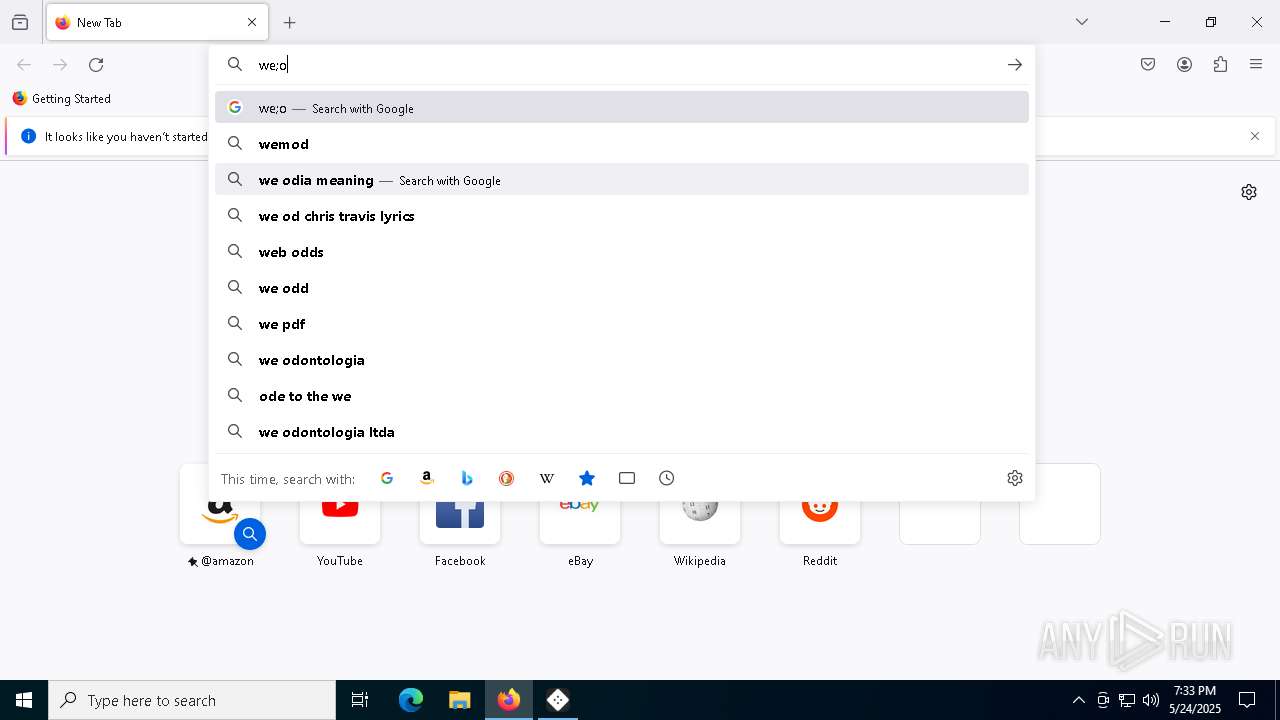
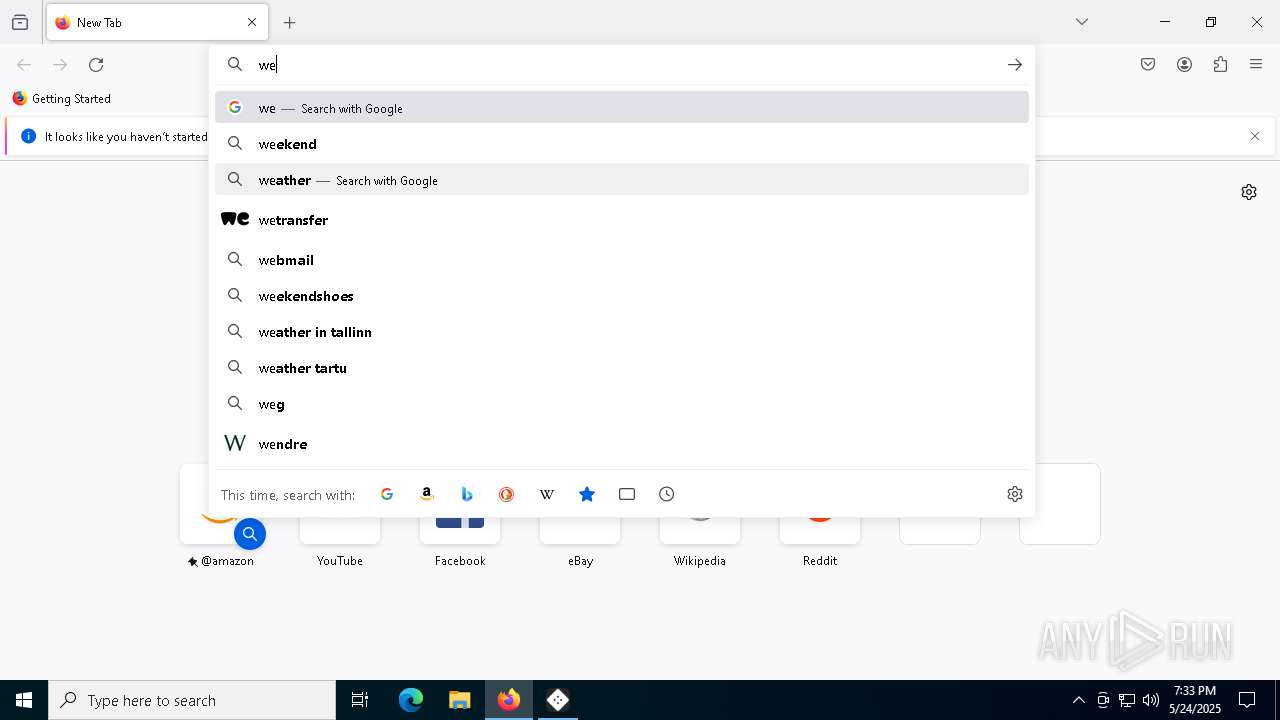
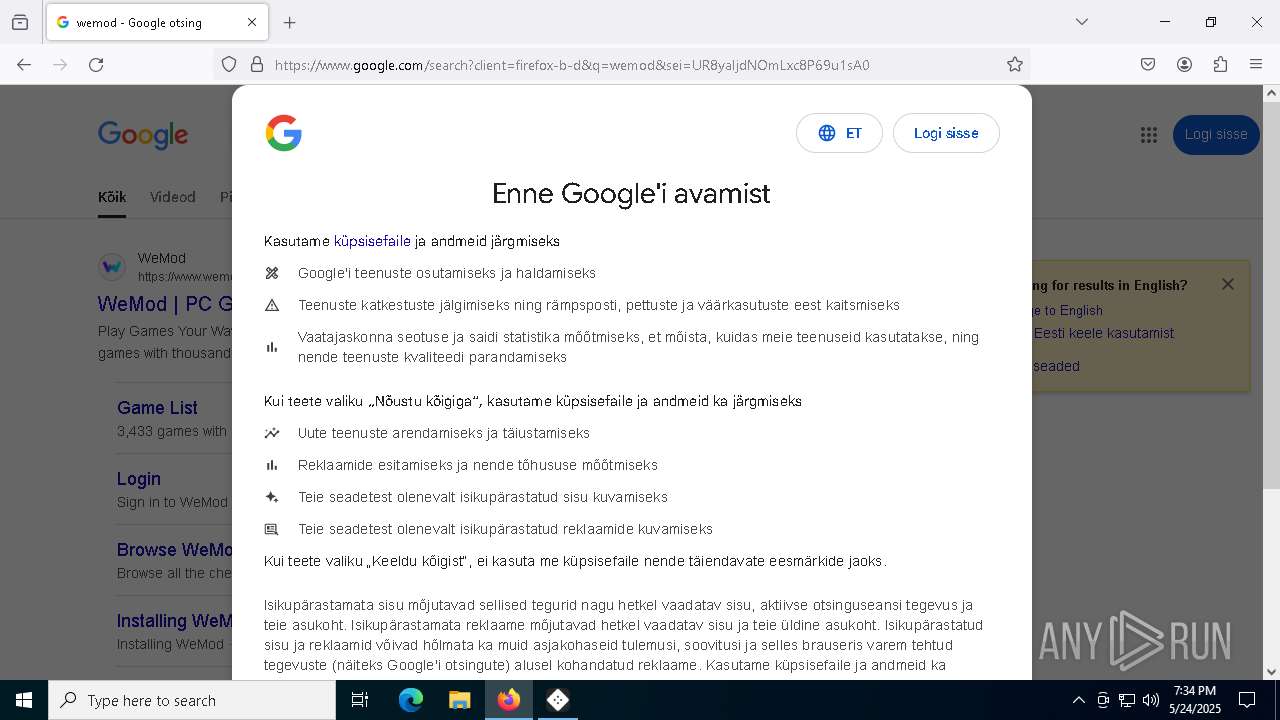
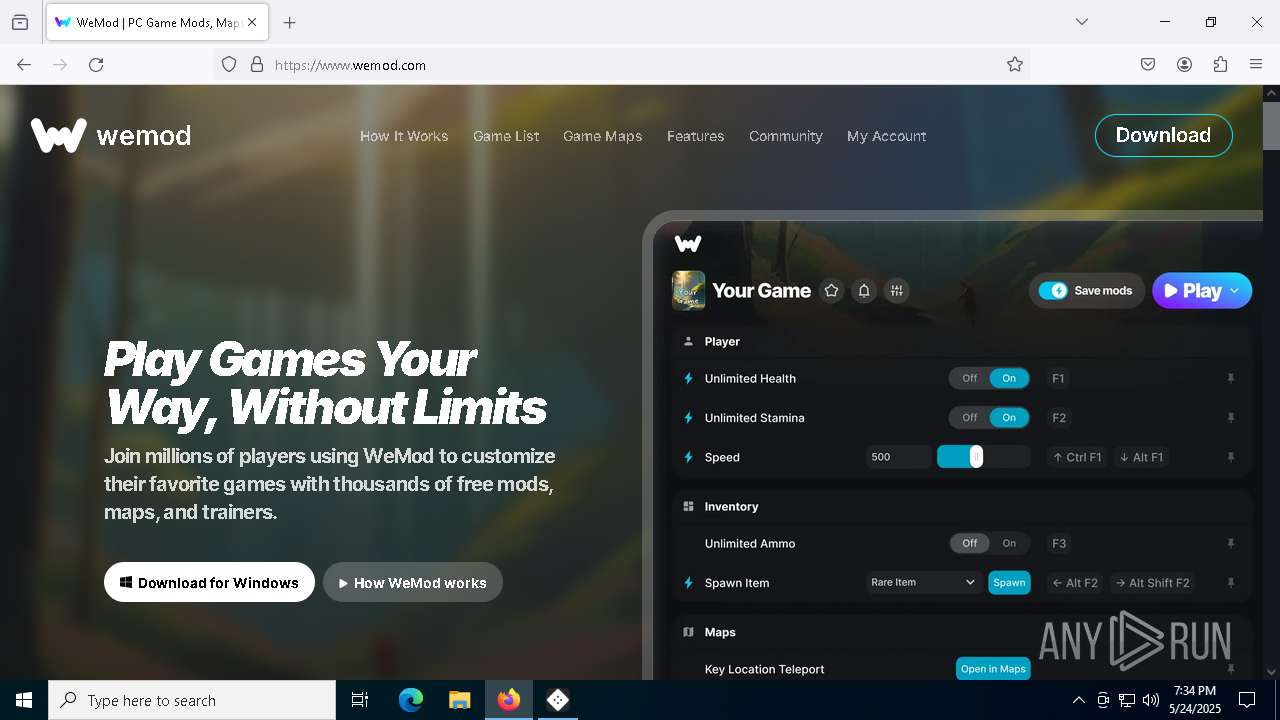
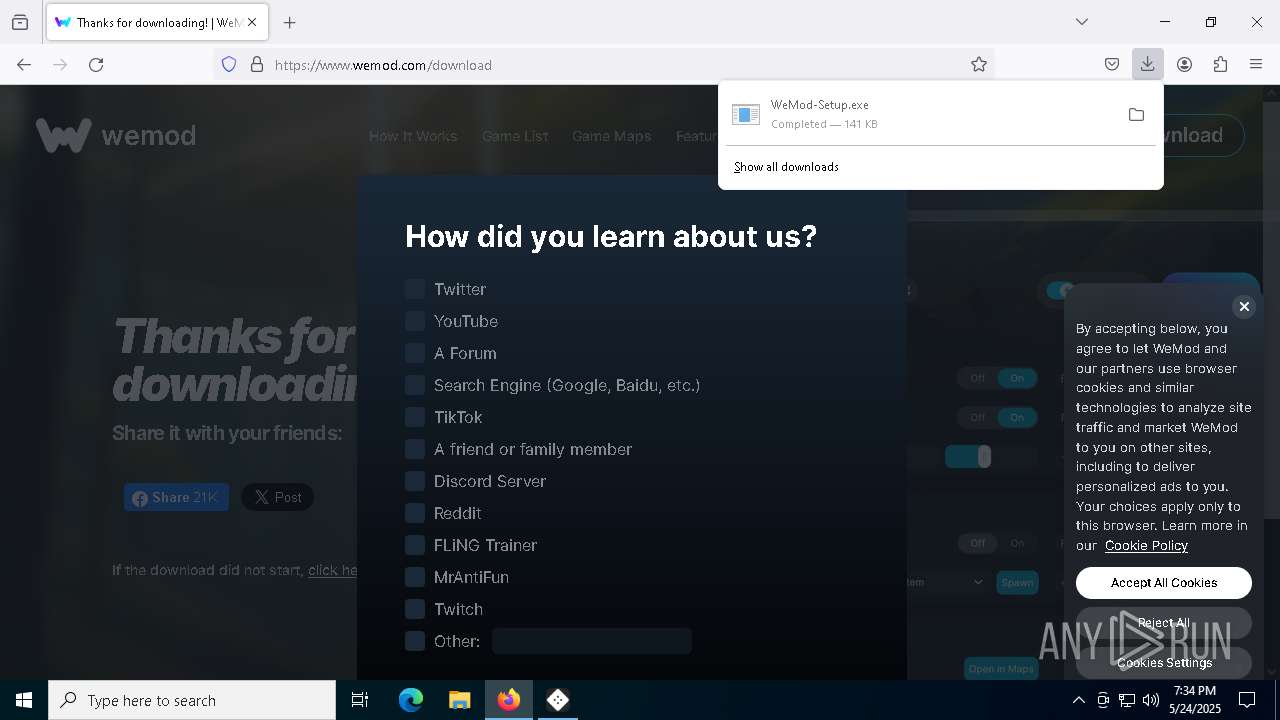
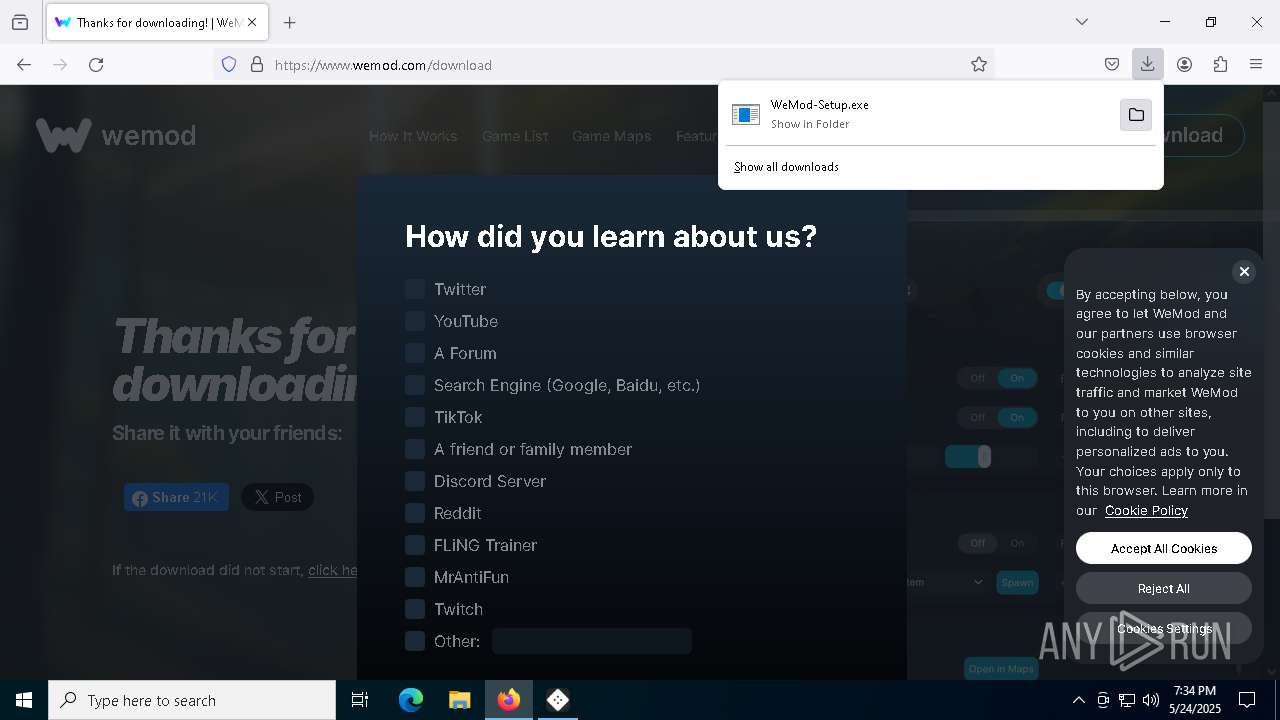
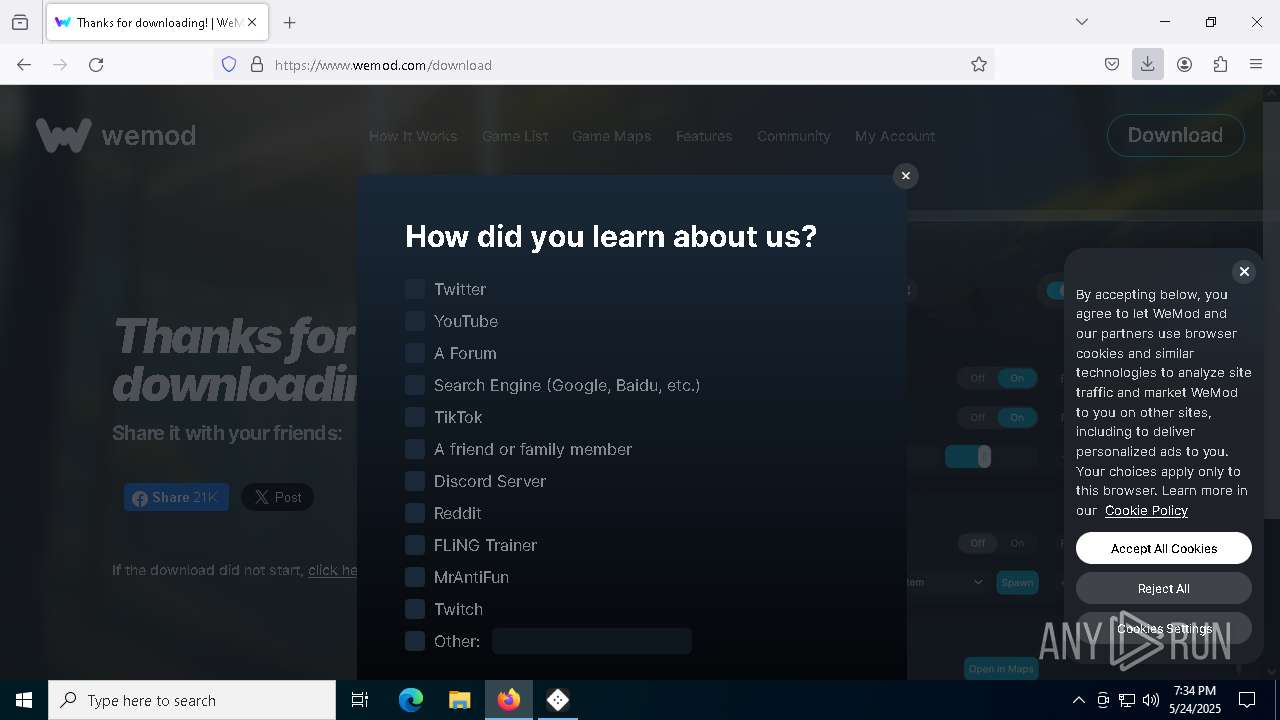
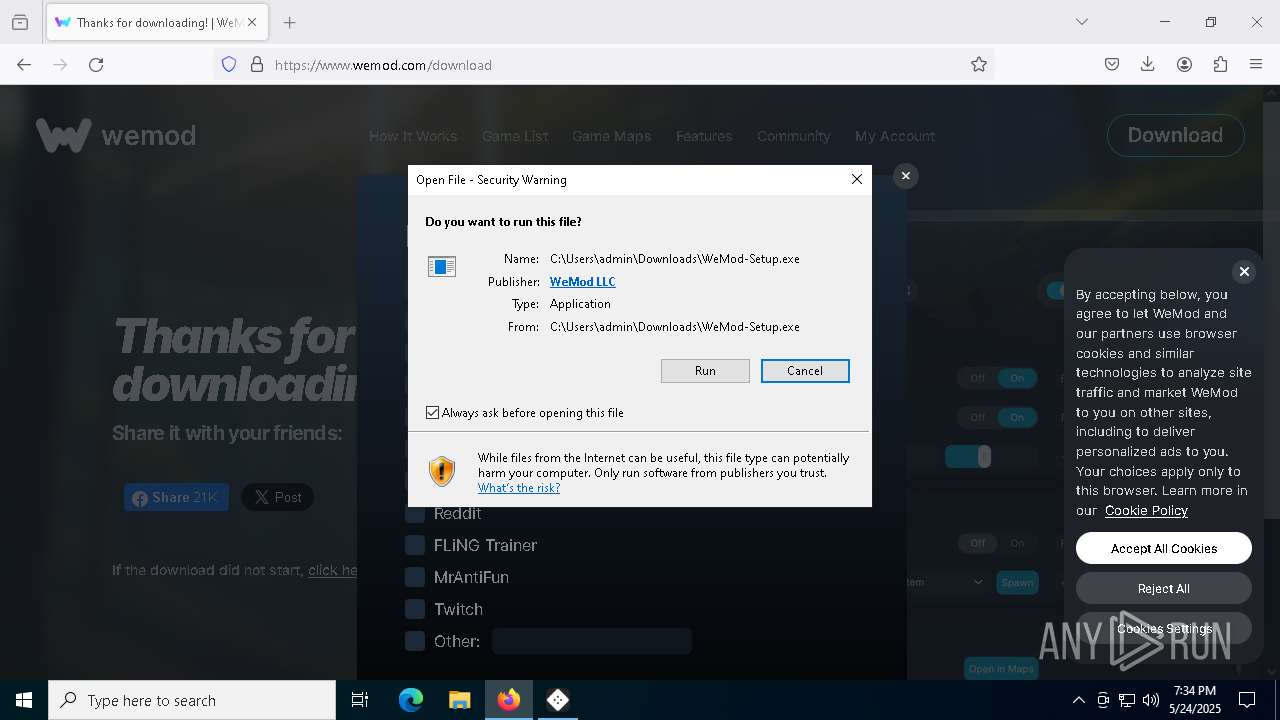
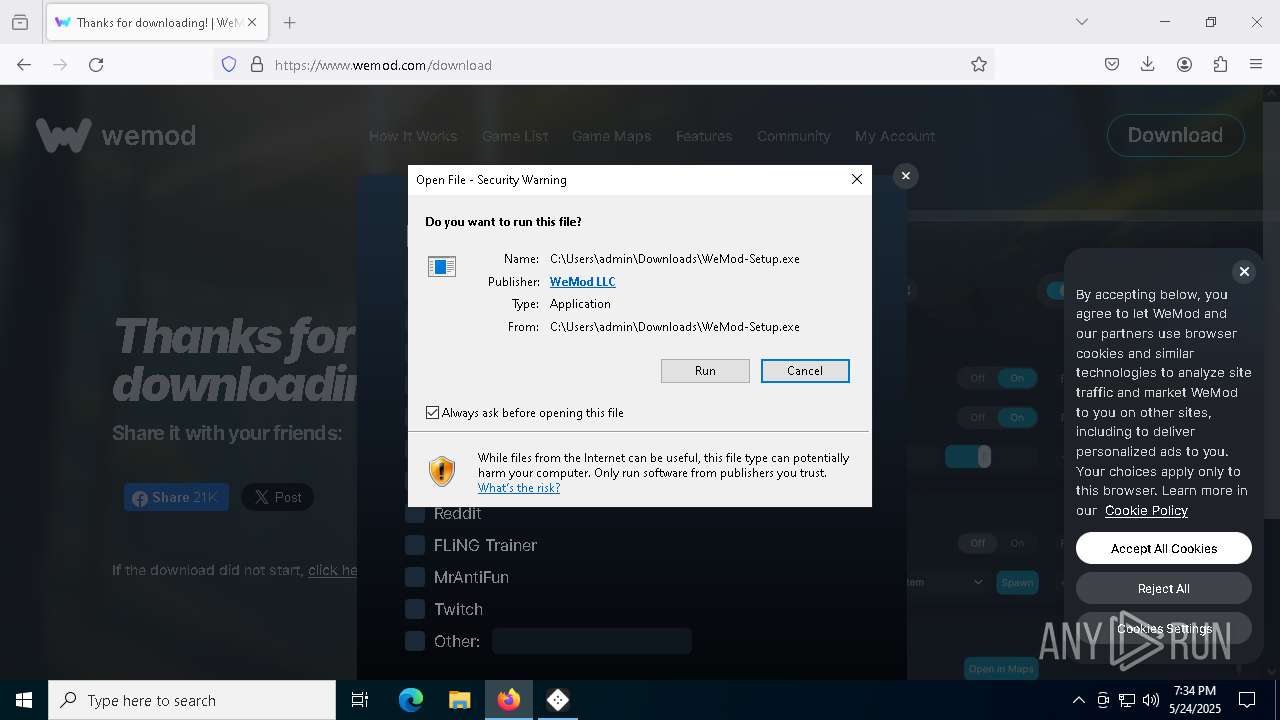
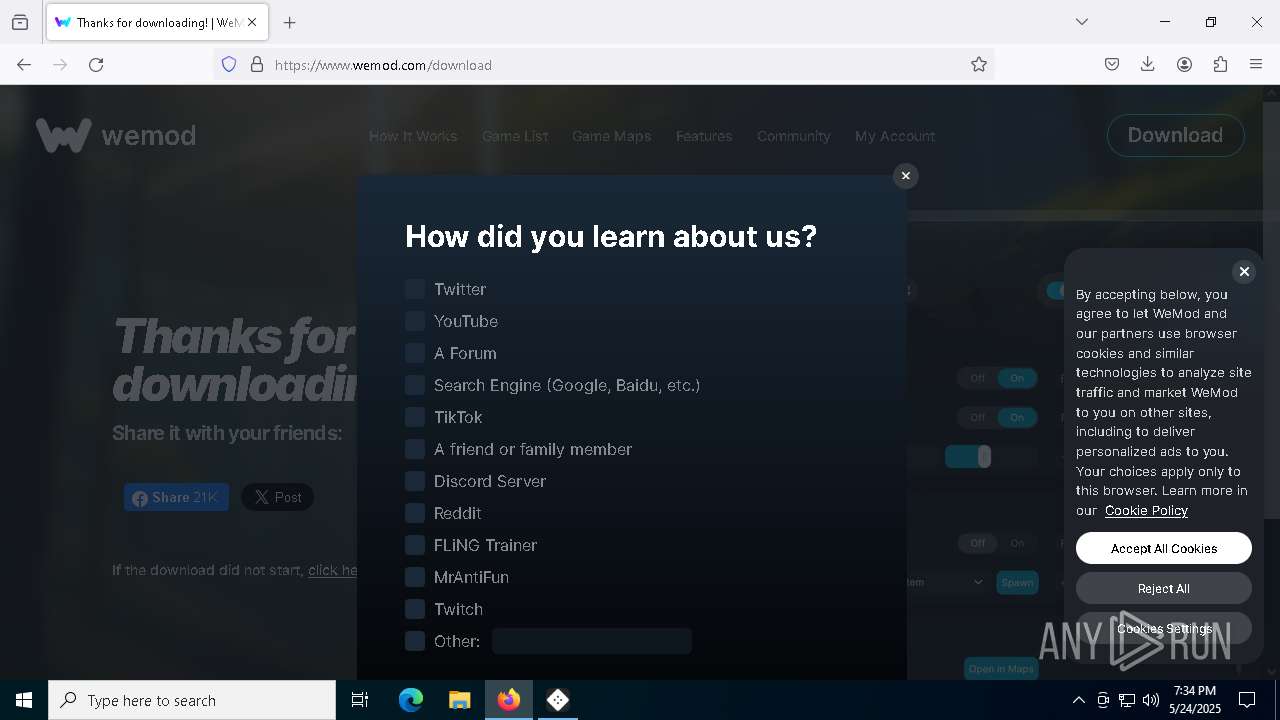
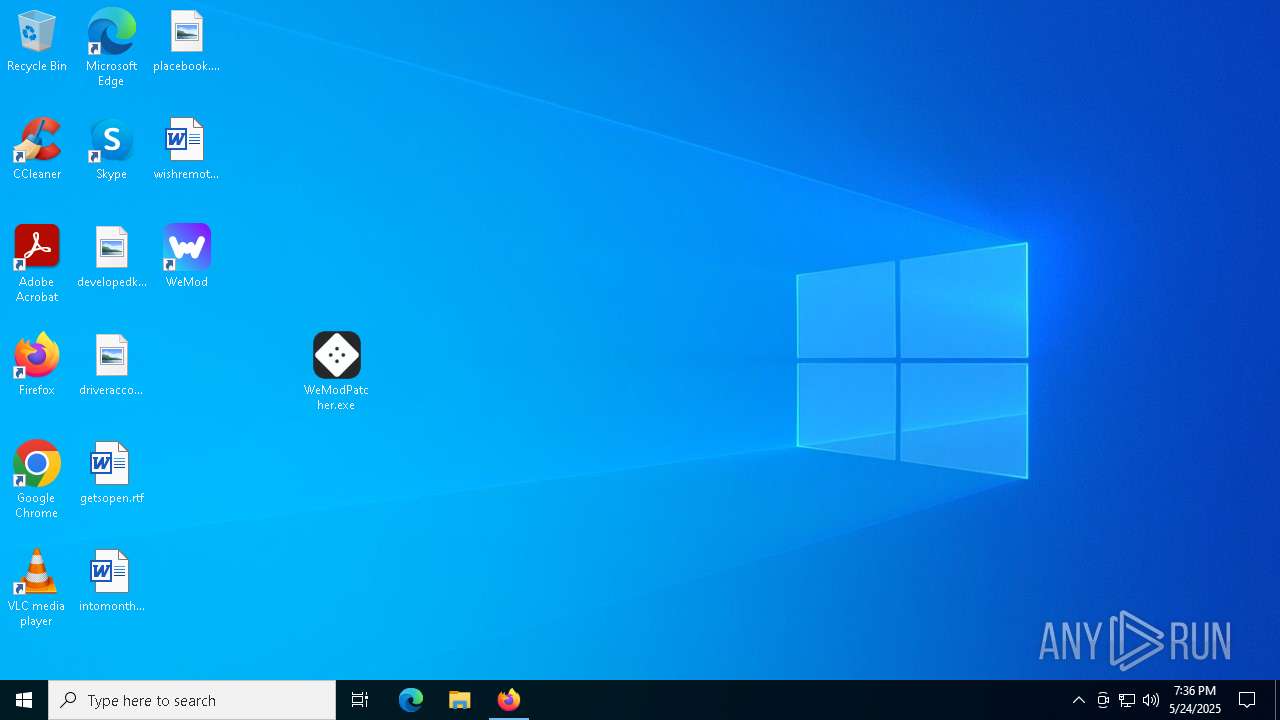
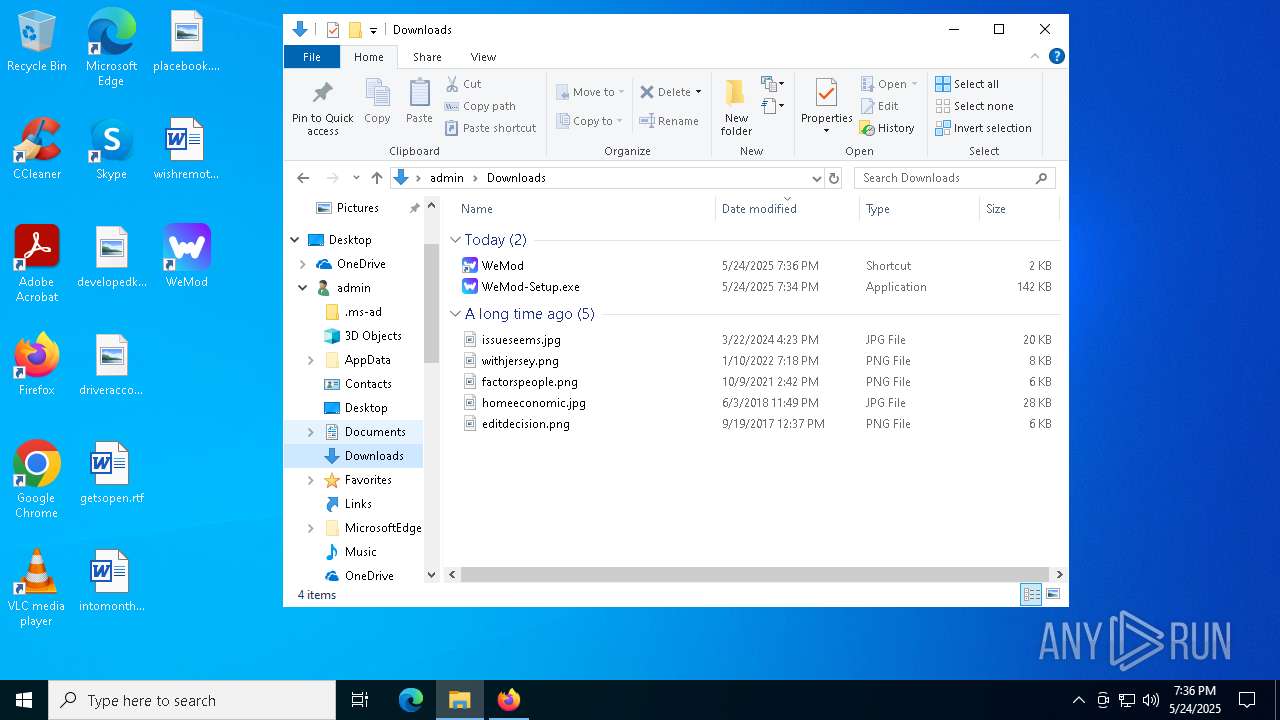
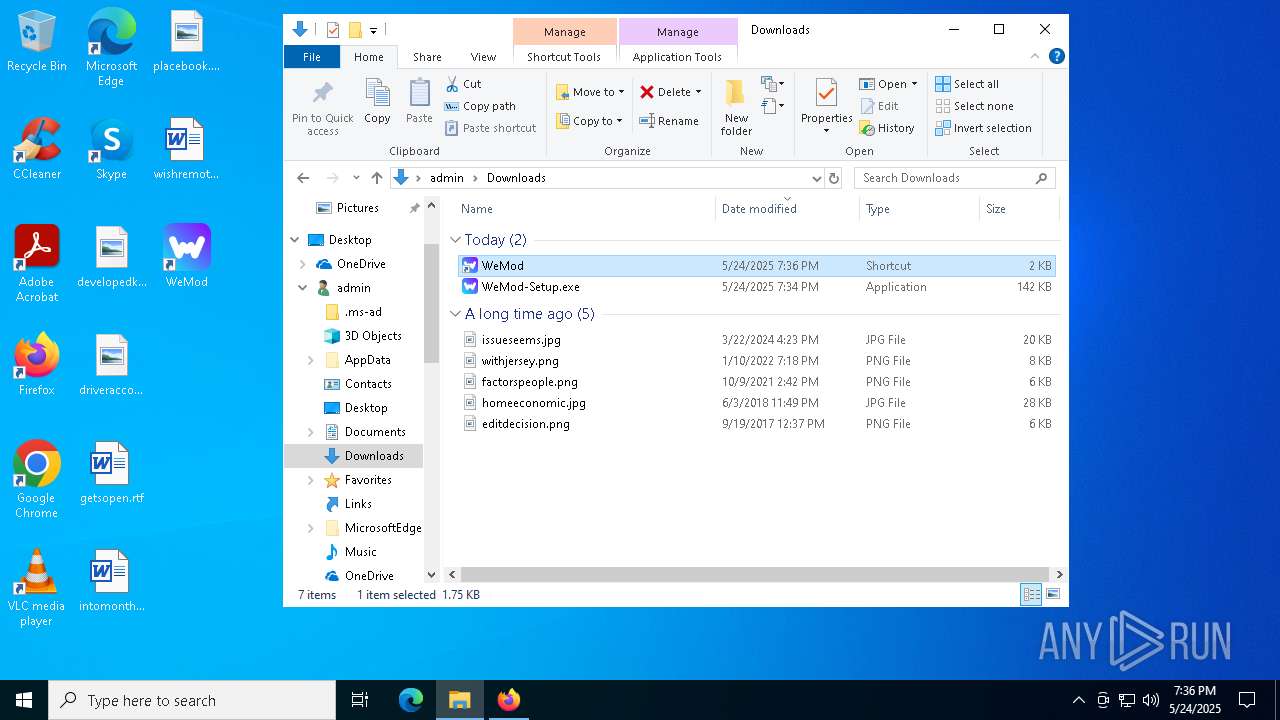
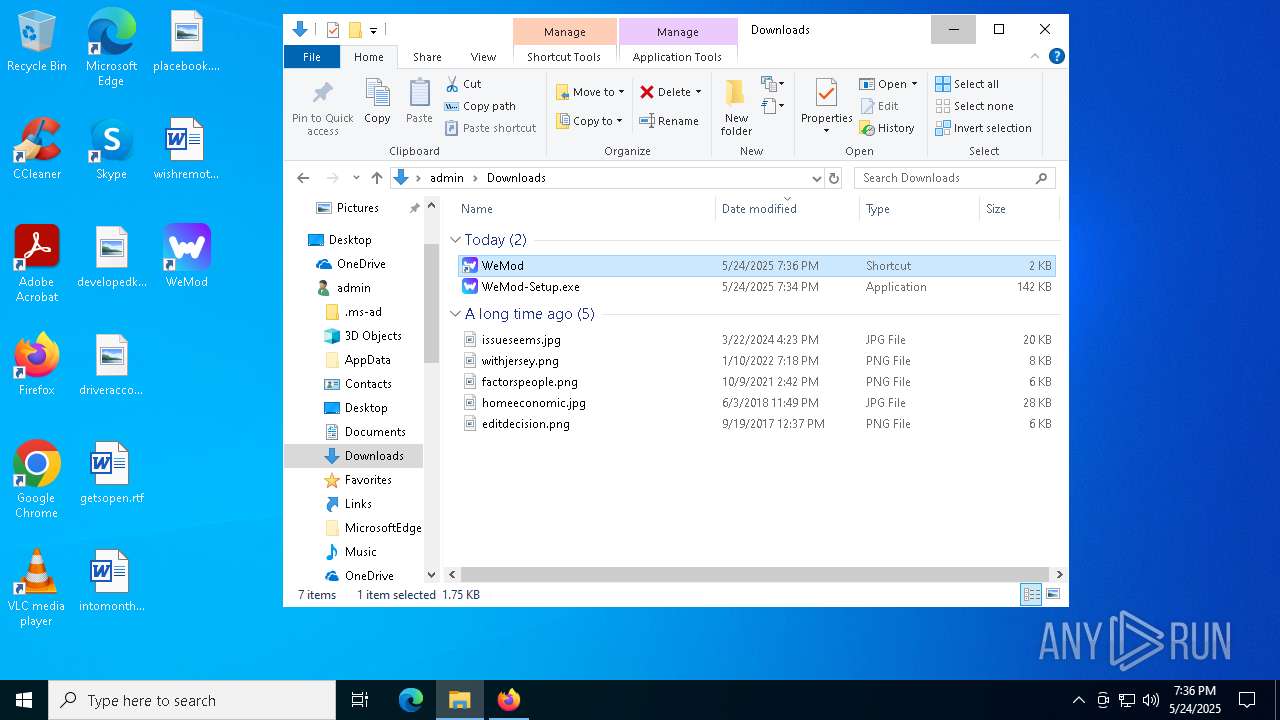
Manual execution by a user
- firefox.exe (PID: 5956)
- WeModPatcher.exe (PID: 2288)
- WeModPatcher.exe (PID: 2896)
Application launched itself
- firefox.exe (PID: 5956)
- firefox.exe (PID: 4652)
Executable content was dropped or overwritten
- firefox.exe (PID: 4652)
Creates files or folders in the user directory
- WeMod-Setup.exe (PID: 8116)
- WeMod-Setup-638837121129775991.exe (PID: 4376)
- Update.exe (PID: 7876)
- squirrel.exe (PID: 4944)
- Update.exe (PID: 7336)
- Update.exe (PID: 4776)
Create files in a temporary directory
- WeMod-Setup.exe (PID: 8116)
- Update.exe (PID: 7876)
The sample compiled with english language support
- Update.exe (PID: 7876)
Process checks computer location settings
- Update.exe (PID: 7876)
- WeMod-Setup.exe (PID: 8116)
Reads product name
- WeMod.exe (PID: 2284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2085:11:10 12:48:33+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 8 |
| CodeSize: | 790528 |
| InitializedDataSize: | 92160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.2.0 |
| ProductVersionNumber: | 1.0.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WeModPatcher |
| FileVersion: | 1.0.2.0 |
| InternalName: | WeModPatcher.exe |
| LegalCopyright: | Copyright © 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | WeModPatcher.exe |
| ProductName: | WeModPatcher |
| ProductVersion: | 1.0.2.0 |
| AssemblyVersion: | 1.0.2.0 |
Total processes
175
Monitored processes
41
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | C:\Users\admin\AppData\Local\WeMod\Update.exe --checkForUpdate https://api.wemod.com/client/channels/stable?osVersion=10.0.19045 | C:\Users\admin\AppData\Local\WeMod\Update.exe | WeMod.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 728 | "C:\Users\admin\AppData\Local\WeMod\app-10.15.0\WeMod.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --force-ui-direction=ltr --user-data-dir="C:\Users\admin\AppData\Roaming\WeMod" --field-trial-handle=2164,i,16961128773736578881,7898539553677396411,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2120 /prefetch:3 | C:\Users\admin\AppData\Local\WeMod\app-10.15.0\WeMod.exe | WeMod.exe | ||||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - The Ultimate Game Companion Exit code: 0 Version: 10.15.0 Modules
| |||||||||||||||
| 732 | "C:\Users\admin\AppData\Local\WeMod\app-10.15.0\WeMod.exe" wemod://?_inst=y2Z00dBgU2YxU6JV | C:\Users\admin\AppData\Local\WeMod\app-10.15.0\WeMod.exe | — | Update.exe | |||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - The Ultimate Game Companion Exit code: 0 Version: 10.15.0 Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\AppData\Local\WeMod\app-10.15.0\WeMod.exe" --squirrel-install 10.15.0 | C:\Users\admin\AppData\Local\WeMod\app-10.15.0\WeMod.exe | — | Update.exe | |||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - The Ultimate Game Companion Exit code: 0 Version: 10.15.0 Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\Desktop\WeModPatcher.exe" eyJQYXRjaFR5cGVzIjpbMSwyXSwiUGF0Y2hNZXRob2QiOjEsIlBhdGgiOiJDOlxcVXNlcnNcXGFkbWluXFxBcHBEYXRhXFxMb2NhbFxcV2VNb2RcXGFwcC0xMC4xNS4wIn0= | C:\Users\admin\Desktop\WeModPatcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WeModPatcher Exit code: 0 Version: 1.0.2.0 Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\Desktop\WeModPatcher.exe" | C:\Users\admin\Desktop\WeModPatcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: WeModPatcher Exit code: 0 Version: 1.0.2.0 Modules
| |||||||||||||||
| 3240 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2152 -parentBuildID 20240213221259 -prefsHandle 2144 -prefMapHandle 2140 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {61505e20-712a-4515-b9d6-bd376ec2686e} 4652 "\\.\pipe\gecko-crash-server-pipe.4652" 26886d82b10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4008 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4208 | "C:\Users\admin\AppData\Local\WeMod\app-10.15.0\WeMod.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\WeMod" --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1824,i,16961128773736578881,7898539553677396411,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=1768 /prefetch:2 | C:\Users\admin\AppData\Local\WeMod\app-10.15.0\WeMod.exe | — | WeMod.exe | |||||||||||
User: admin Company: WeMod Integrity Level: LOW Description: WeMod - The Ultimate Game Companion Exit code: 0 Version: 10.15.0 Modules
| |||||||||||||||
| 4376 | "C:\Users\admin\AppData\Local\Temp\WeMod-Setup-638837121129775991.exe" --silent | C:\Users\admin\AppData\Local\Temp\WeMod-Setup-638837121129775991.exe | WeMod-Setup.exe | ||||||||||||
User: admin Company: WeMod Integrity Level: MEDIUM Description: WeMod - The Ultimate Gaming Companion Exit code: 0 Version: 10.15.0 Modules
| |||||||||||||||
Total events
42 248
Read events
42 064
Write events
143
Delete events
41
Modification events
| (PID) Process: | (6964) WeModPatcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WeModPatcher_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6964) WeModPatcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WeModPatcher_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6964) WeModPatcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WeModPatcher_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6964) WeModPatcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WeModPatcher_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6964) WeModPatcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WeModPatcher_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6964) WeModPatcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WeModPatcher_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6964) WeModPatcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WeModPatcher_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6964) WeModPatcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WeModPatcher_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6964) WeModPatcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WeModPatcher_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6964) WeModPatcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WeModPatcher_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
28
Suspicious files
626
Text files
136
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4652 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4652 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 4652 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\protections.sqlite-journal | binary | |
MD5:218B2B54ABF5629DABE63912C864E054 | SHA256:36215FFD84FCA8F64DF392465F5D3F81DBAAA8208C564D220AC480F00AFC506E | |||
| 4652 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | binary | |
MD5:3B156E12141F8CBCE9D60CDCE2077617 | SHA256:E6287E44B44ABEA20E1B2E3F415D22B9E5E5FBBC155AD9DADBABA63951B2AF6F | |||
| 4652 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | binary | |
MD5:CFBBA9A53BBBE90F445A9F75C4CCD4E5 | SHA256:1AB4A591E909B70F3F45B58D47463C886CABA91AE09ECC967E4515055D37AA25 | |||
| 4652 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 4652 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:7B2C28211031E0C8A6BF7D9723A3F649 | SHA256:FACC00DD6EAB6C6CF13EA4FA11F44C4A17815B34BB27DF6052E782E26D13B921 | |||
| 4652 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 4652 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4652 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
202
DNS requests
235
Threats
55
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.185:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.185:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4652 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4652 | firefox.exe | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
4652 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4652 | firefox.exe | POST | 200 | 184.24.77.77:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.185:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.185:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6964 | WeModPatcher.exe | 140.82.121.5:443 | api.github.com | GITHUB | US | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
api.github.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
728 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
728 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
728 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
728 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
728 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
728 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
728 | WeMod.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |