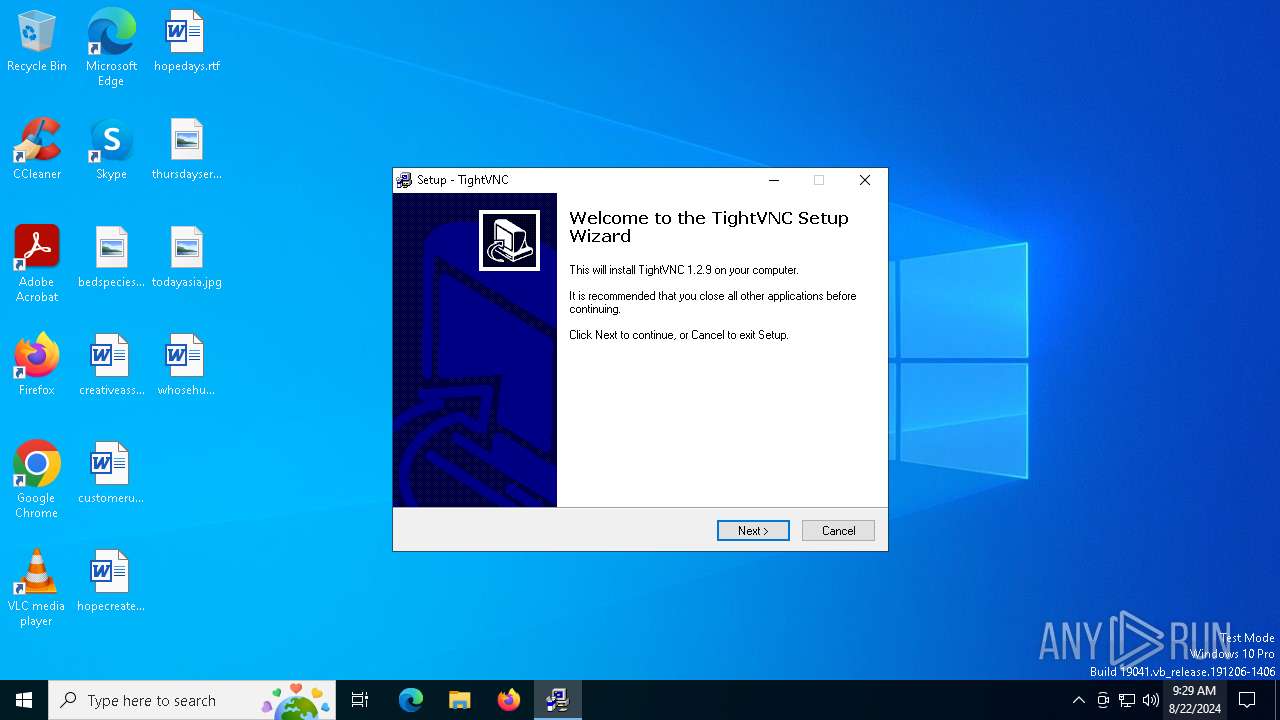
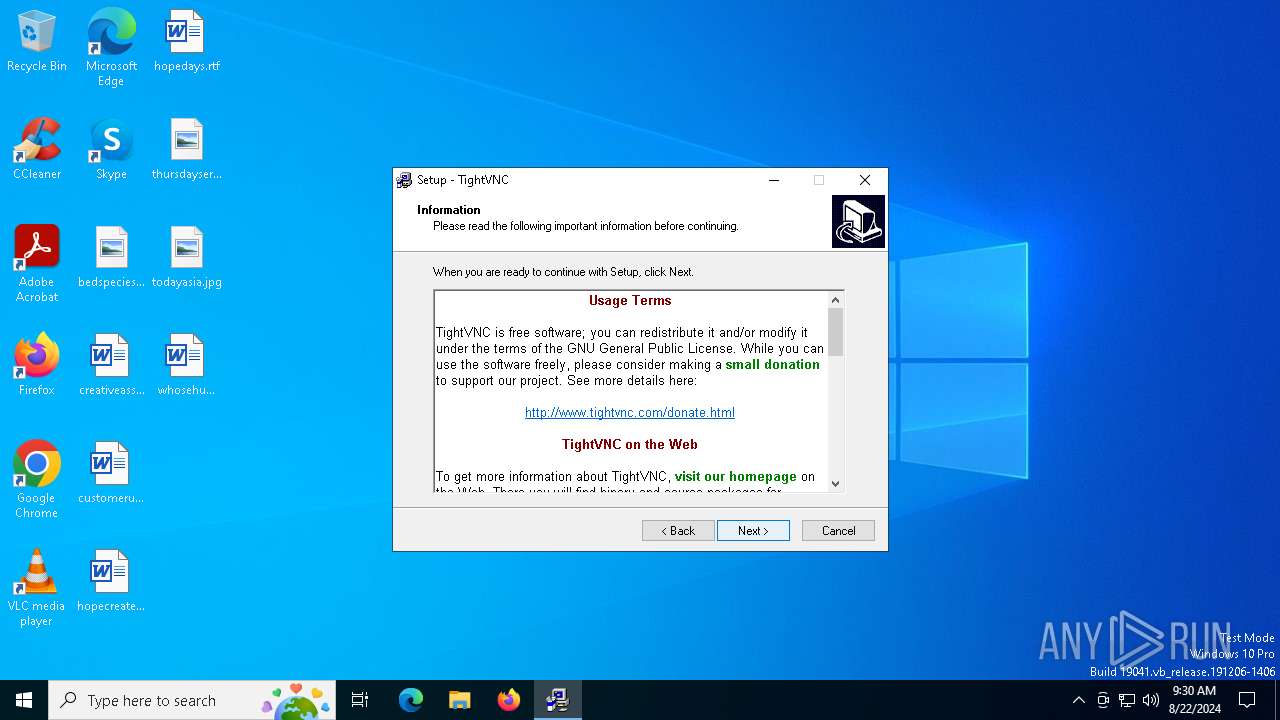
| File name: | tightvnc-1.2.9-setup.exe |
| Full analysis: | https://app.any.run/tasks/c4cc5d33-e88d-462e-bed7-c209938ab157 |
| Verdict: | Malicious activity |
| Analysis date: | August 22, 2024, 09:29:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InnoSetup self-extracting archive |
| MD5: | A9C3FCE096310986C815AC79A600DDAB |
| SHA1: | 6A2705F060745C593E6873BC136D33139882C7D8 |
| SHA256: | E4EBFC8E0866DC83174B25ED6000BF8FBC87CCEF90570CDBEC70D279A4807EB1 |
| SSDEEP: | 49152:IZ8ebL6yloS2tqsyy55gMVQSw4DZVY6j7xxYtFP+5+6qBOiGpH/vH1H7PwJux8Mq:I6HPS9453V/DZVY0KtF25+6qqF3H1jRu |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops the executable file immediately after the start
- tightvnc-1.2.9-setup.exe (PID: 6856)
- INSDCD0.tmp (PID: 6896)
Creates a software uninstall entry
- INSDCD0.tmp (PID: 6896)
Reads the Windows owner or organization settings
- INSDCD0.tmp (PID: 6896)
Executable content was dropped or overwritten
- tightvnc-1.2.9-setup.exe (PID: 6856)
- INSDCD0.tmp (PID: 6896)
Starts application with an unusual extension
- tightvnc-1.2.9-setup.exe (PID: 6856)
Process drops legitimate windows executable
- INSDCD0.tmp (PID: 6896)
INFO
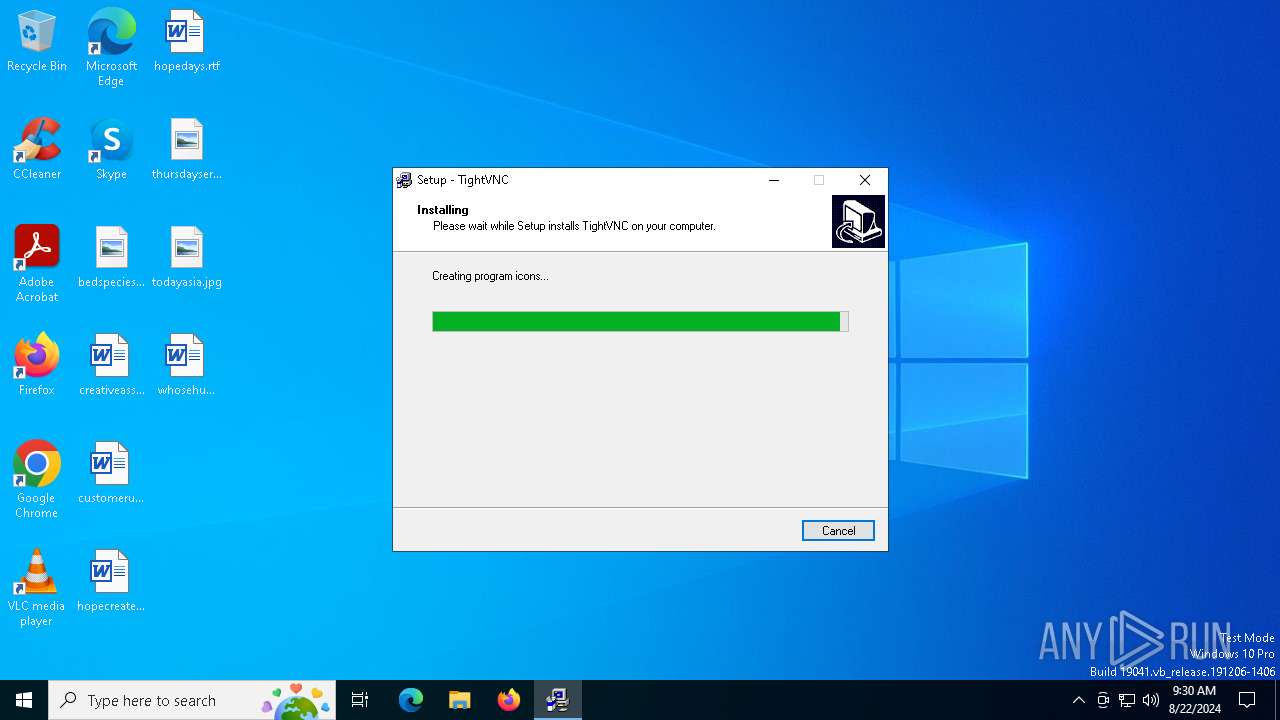
Creates files in the program directory
- INSDCD0.tmp (PID: 6896)
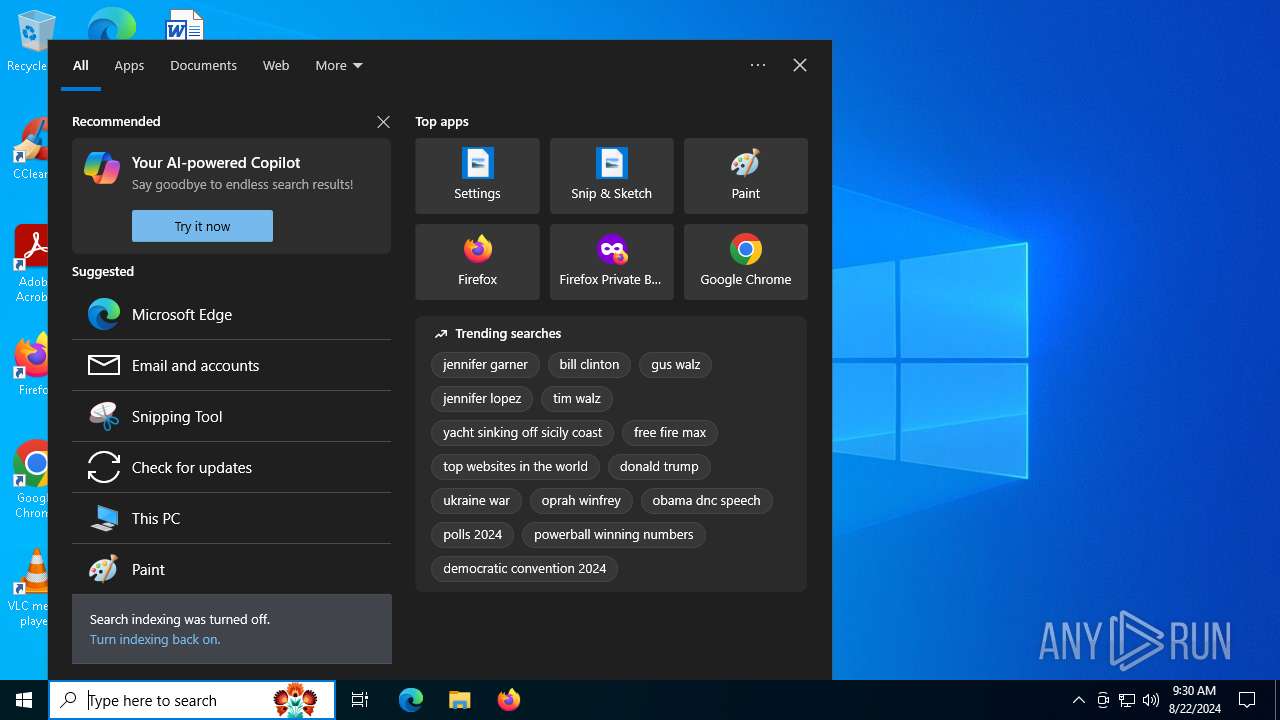
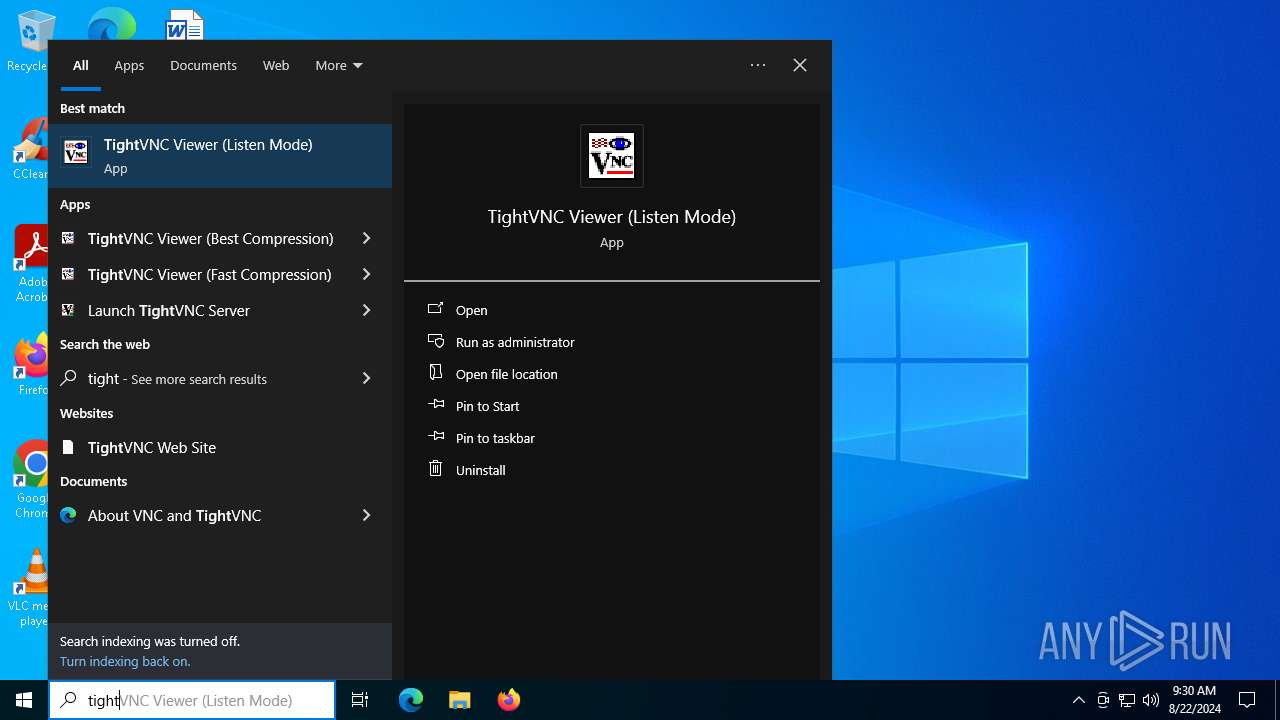
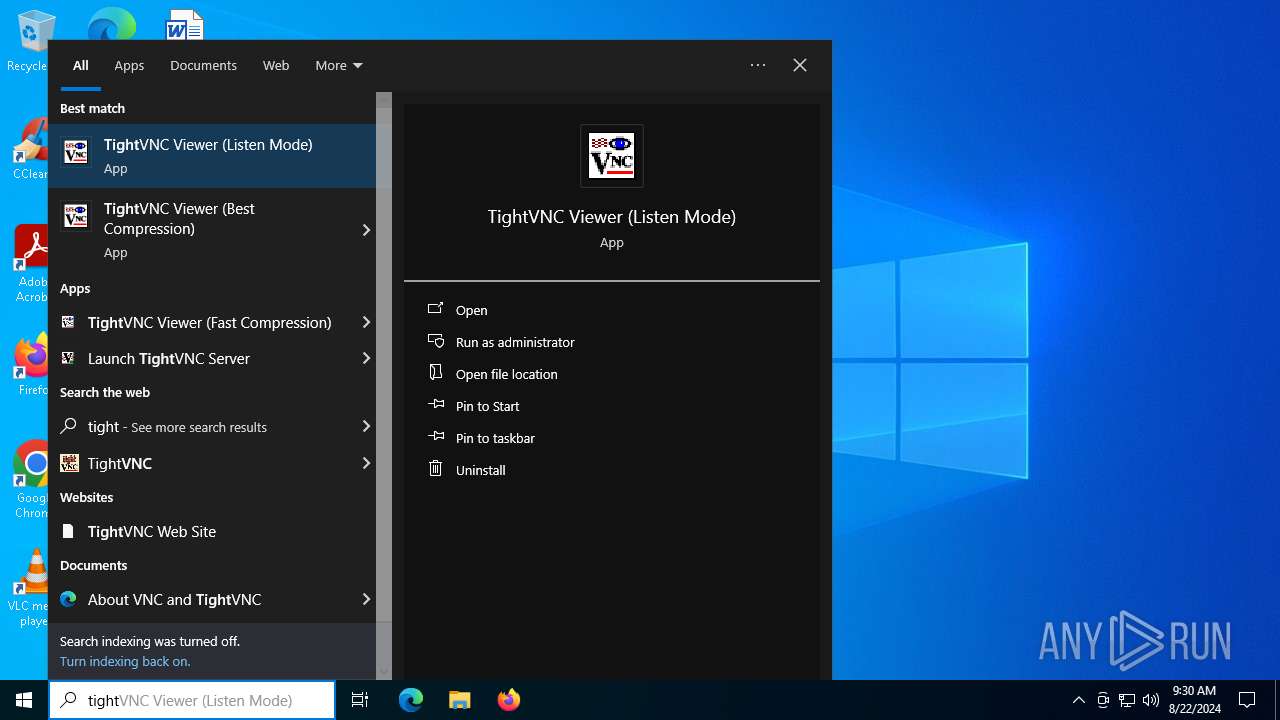
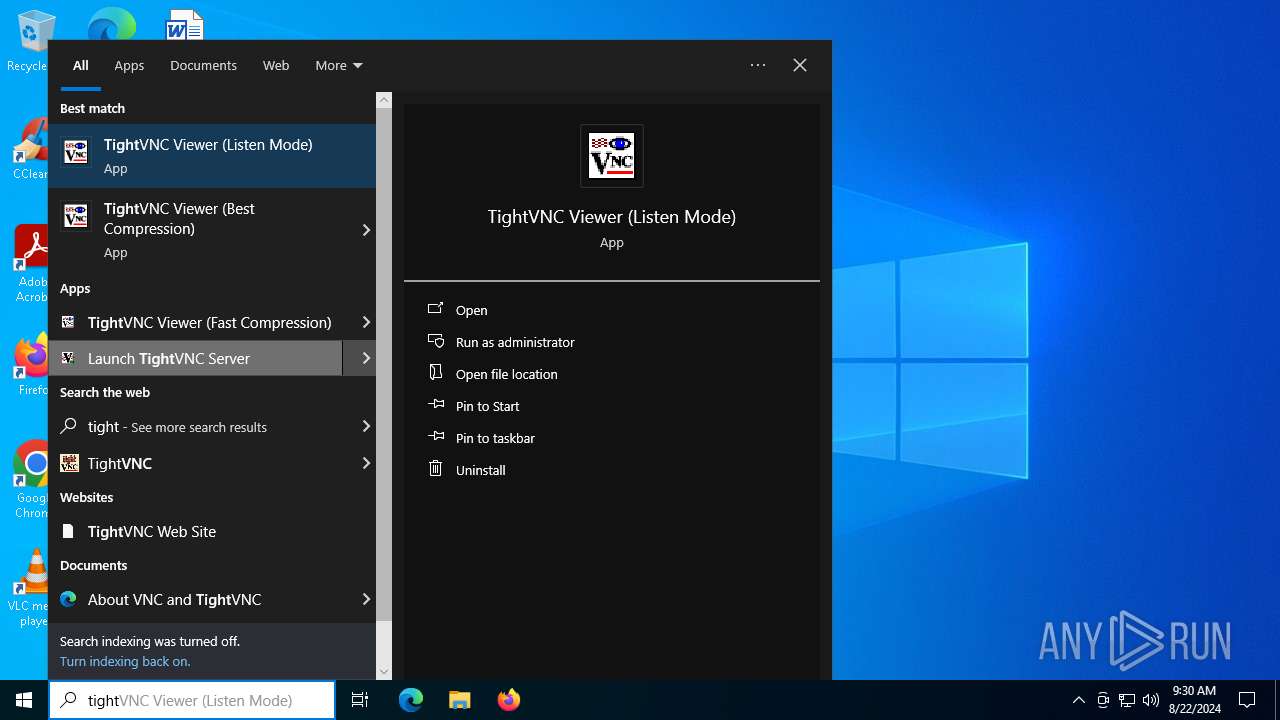
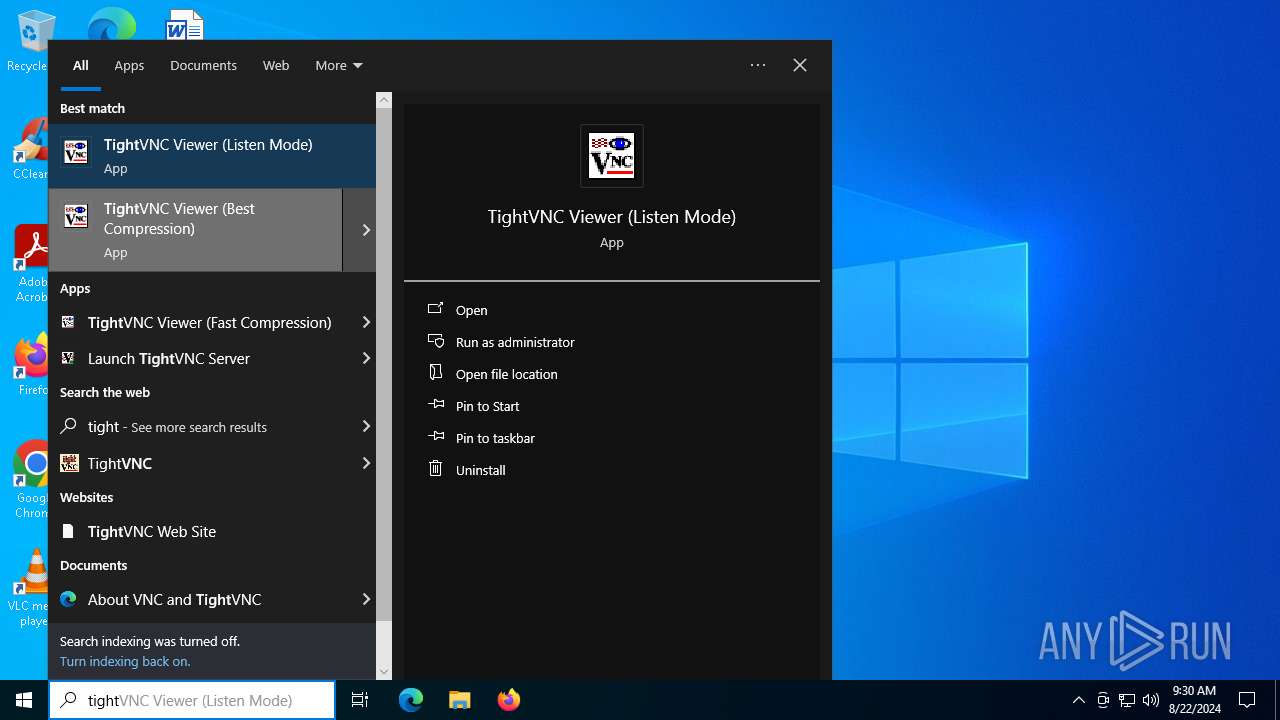
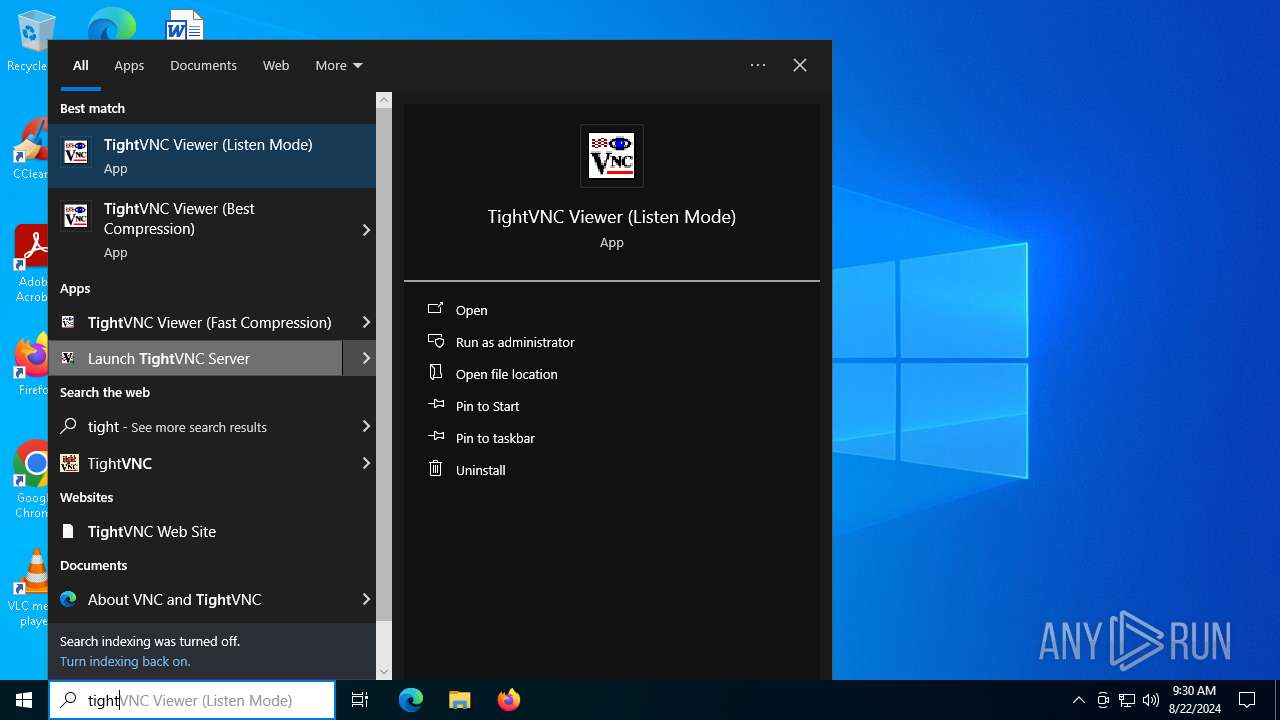
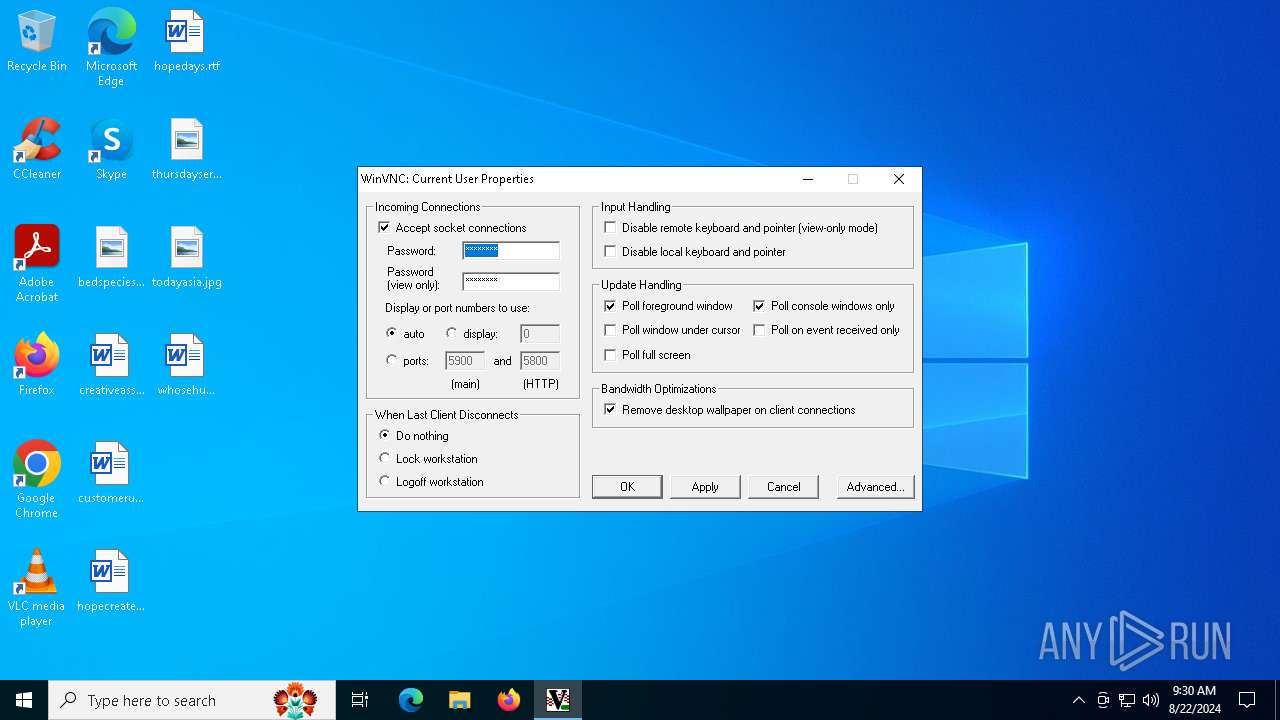
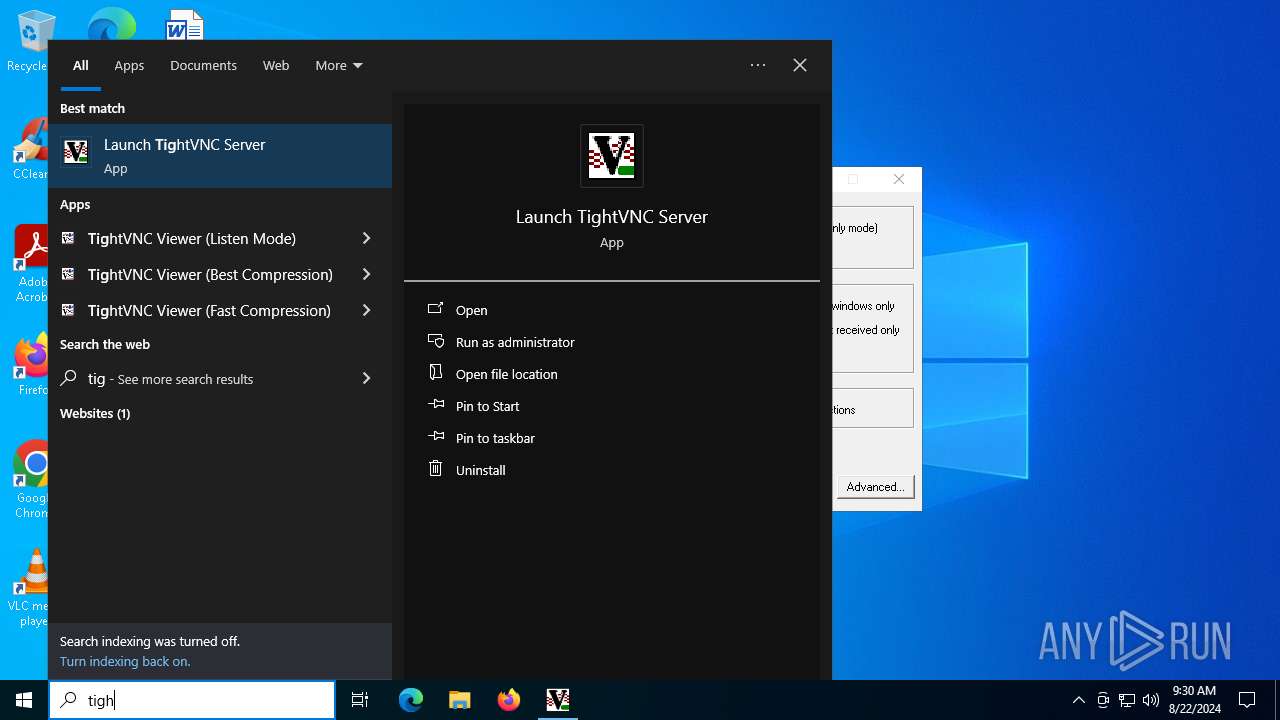
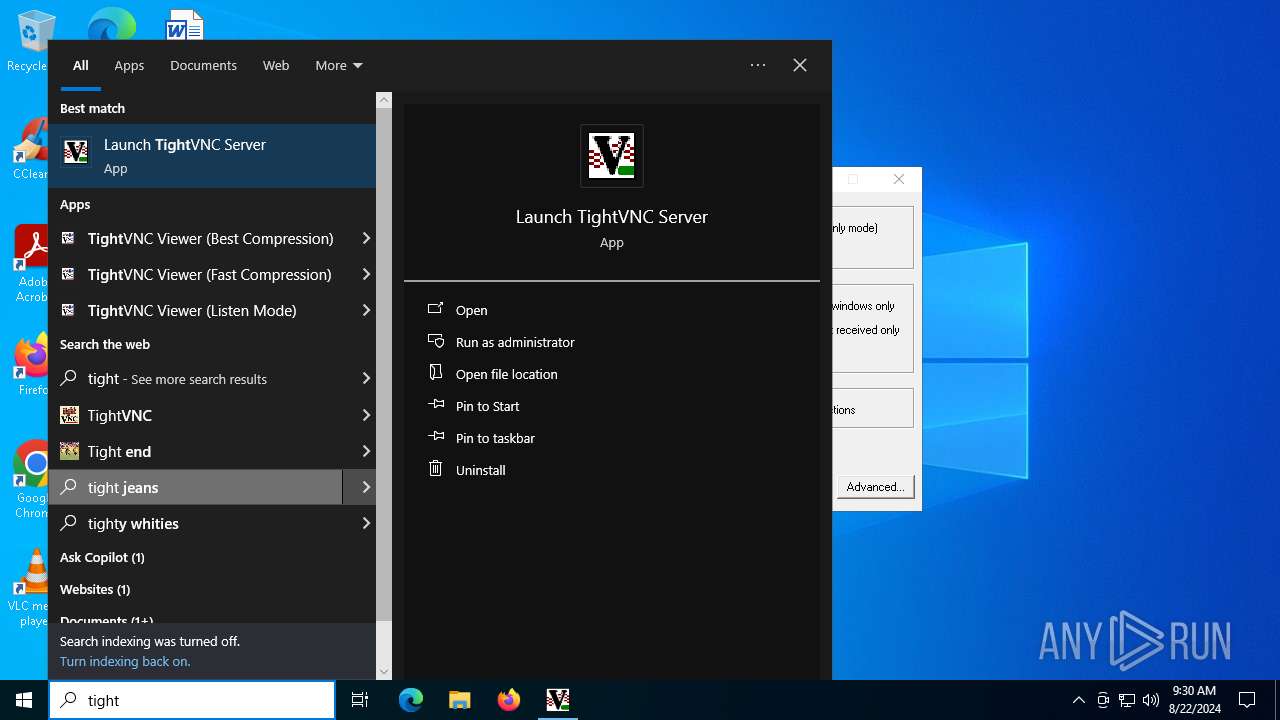
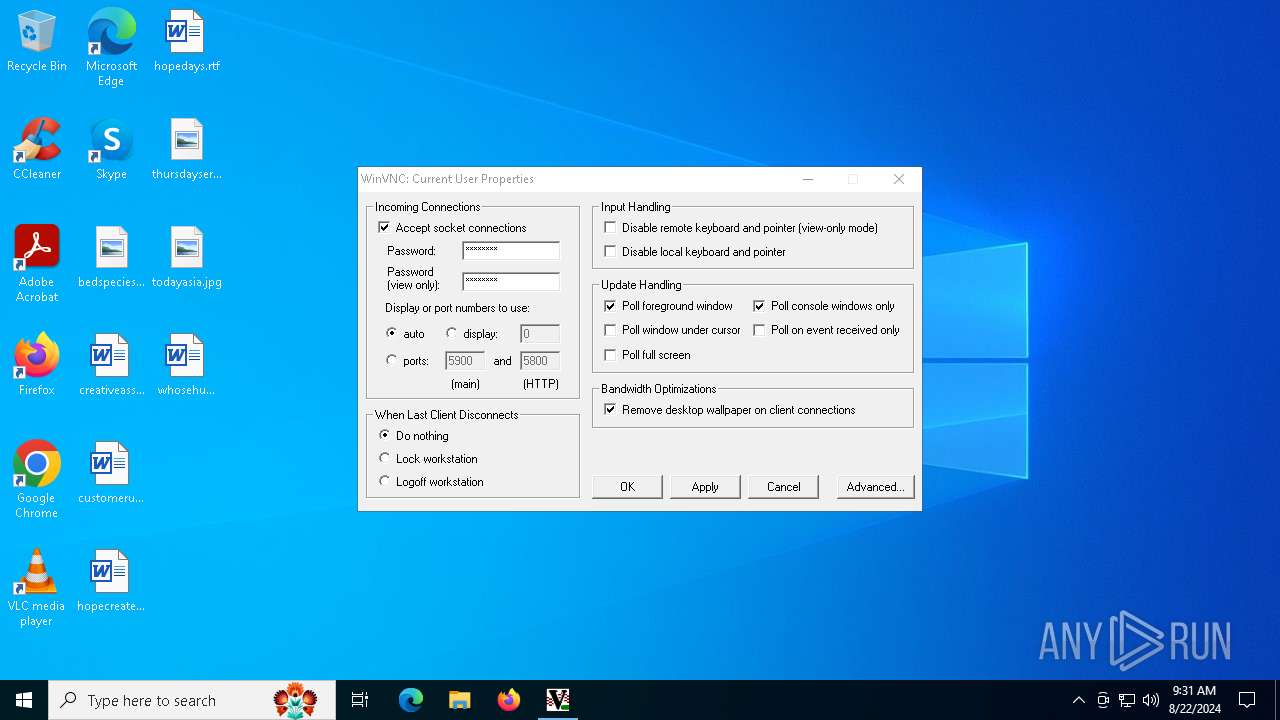
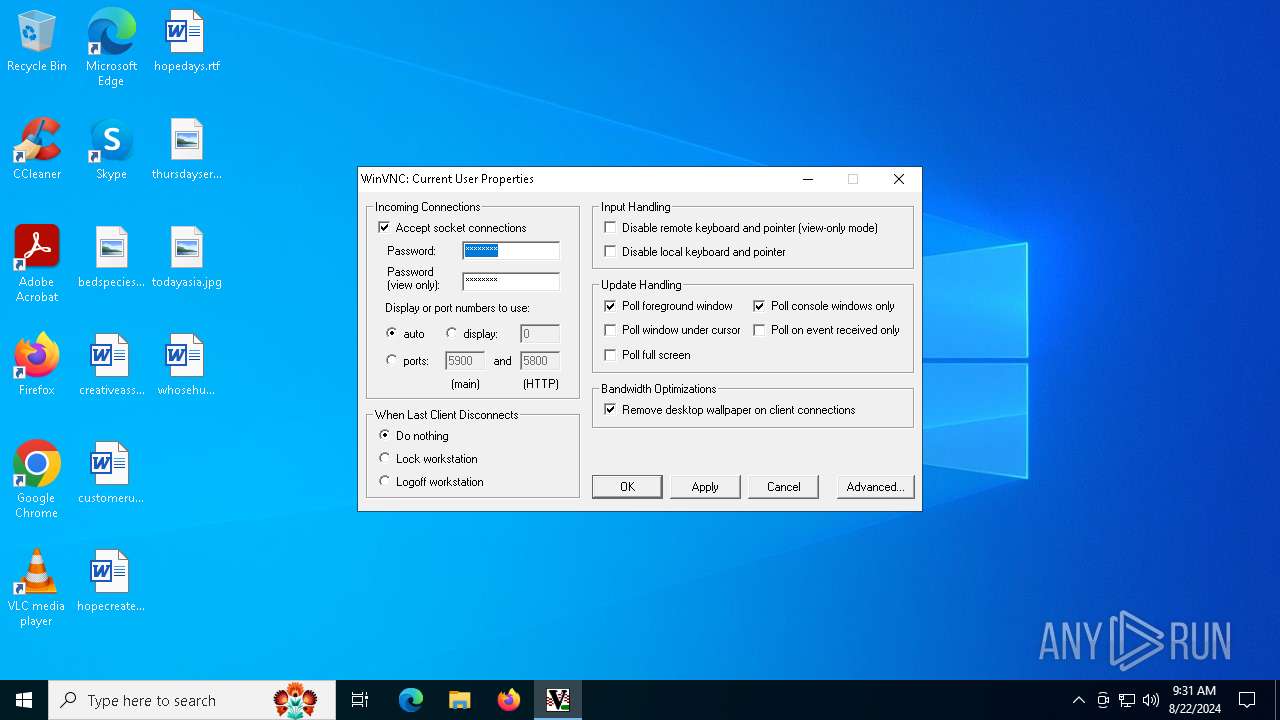
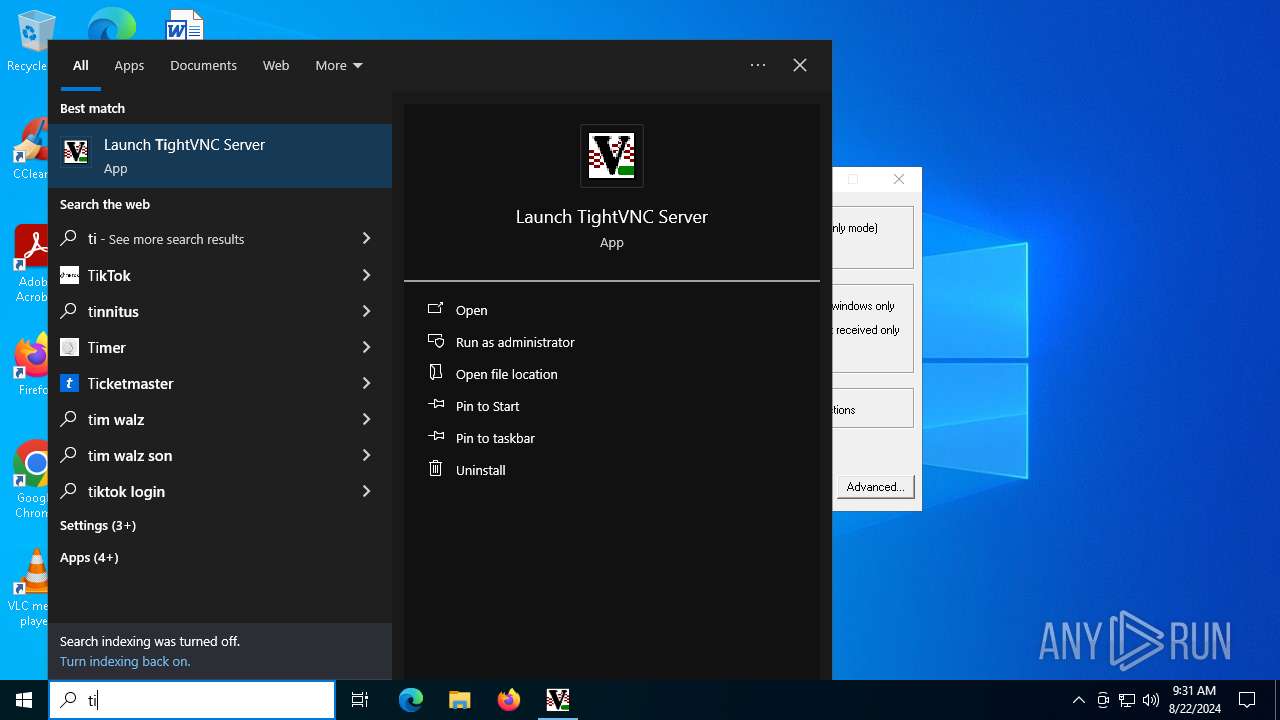
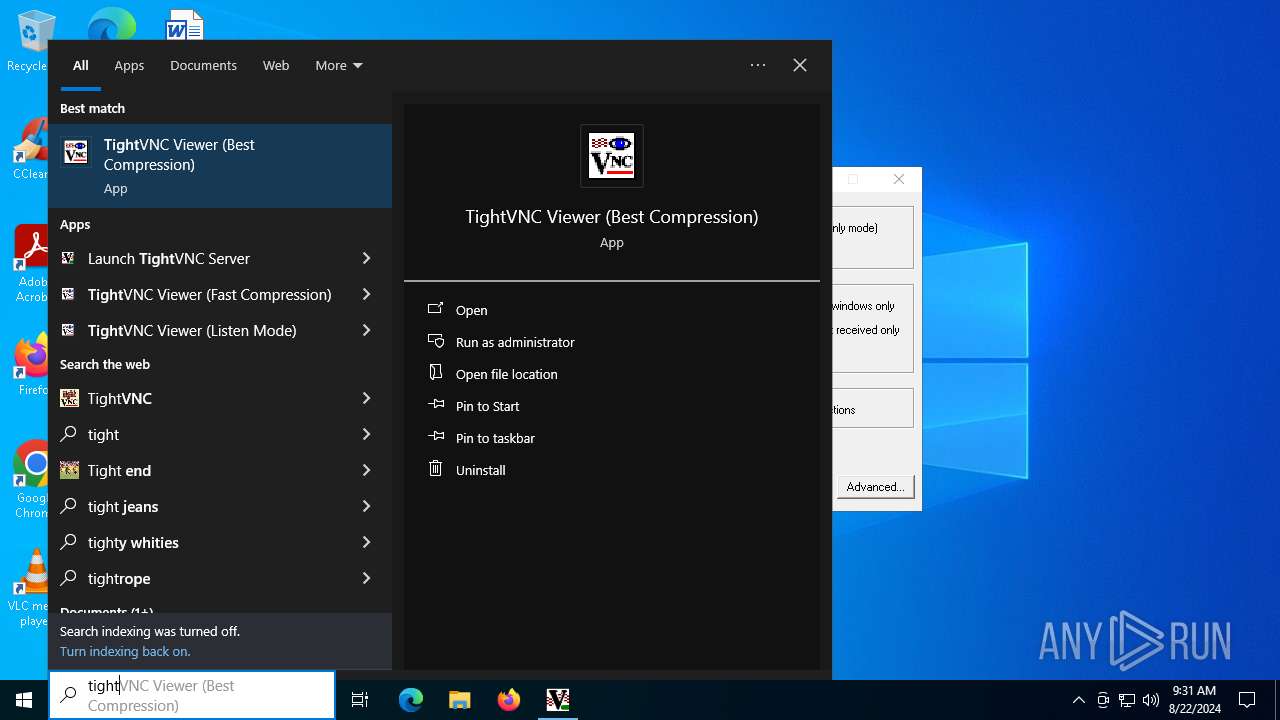
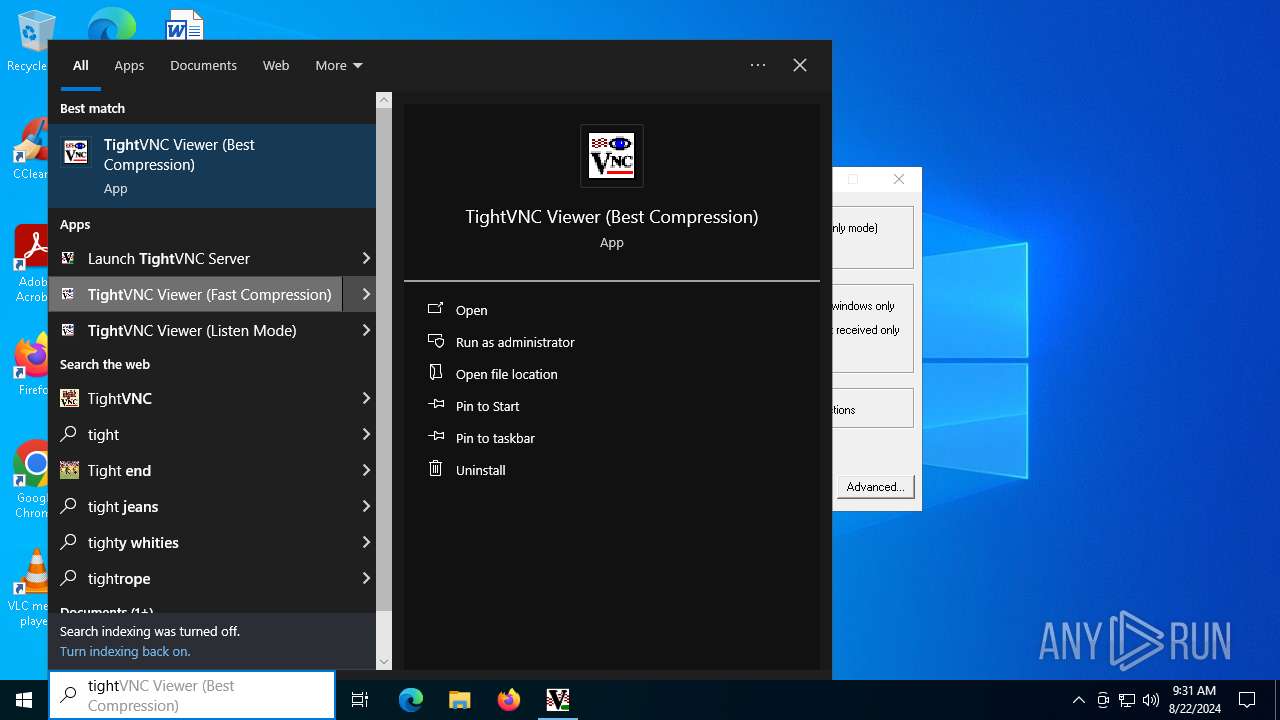
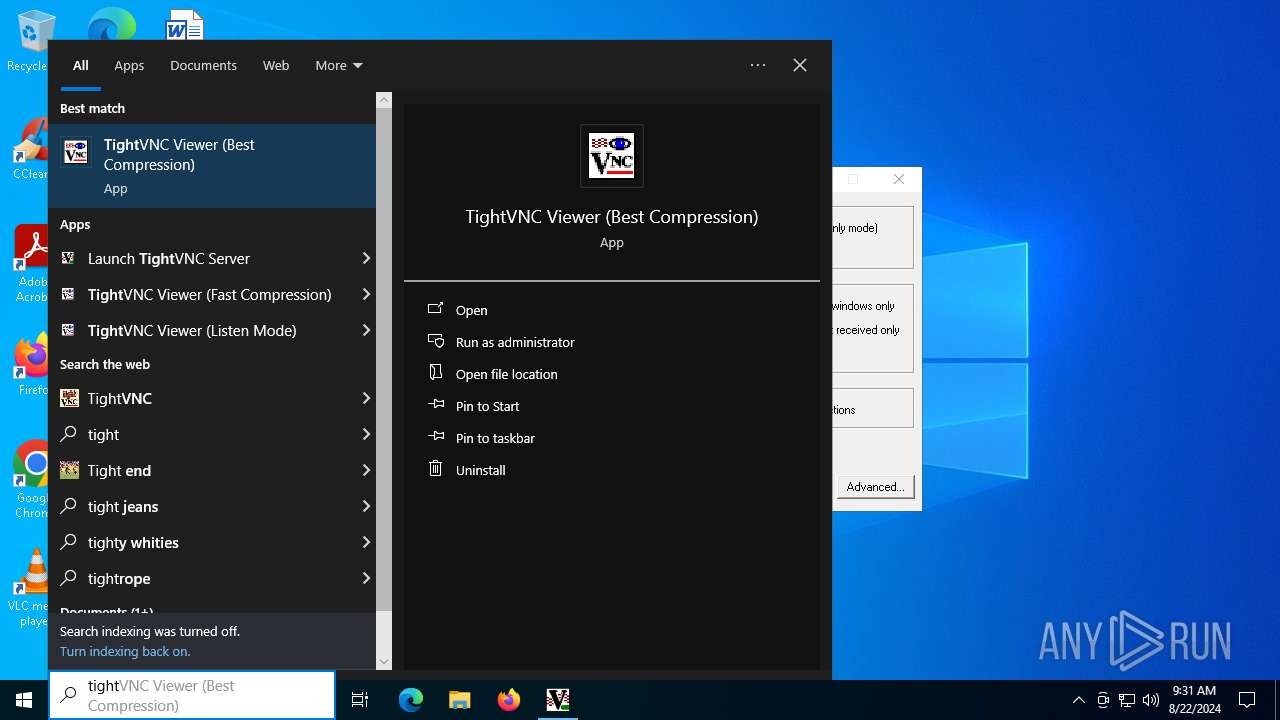
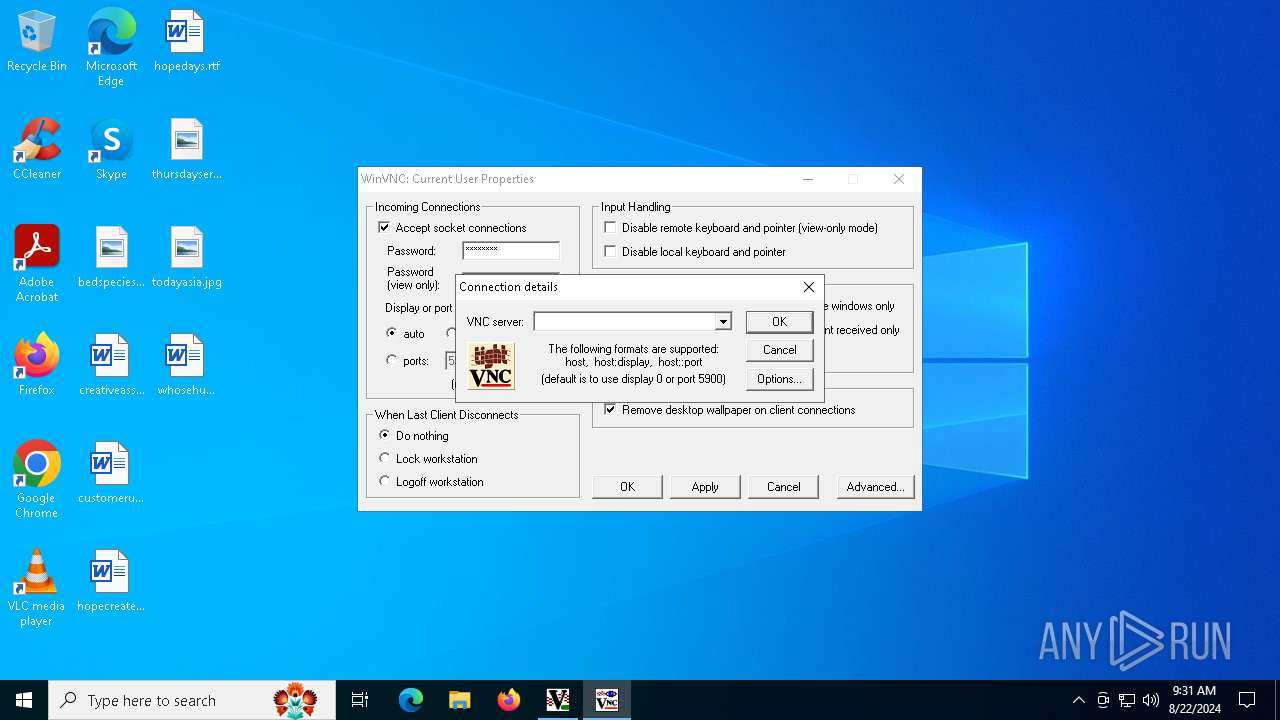
Manual execution by a user
- WinVNC.exe (PID: 5712)
- vncviewer.exe (PID: 1104)
Reads the computer name
- WinVNC.exe (PID: 5712)
- vncviewer.exe (PID: 1104)
- INSDCD0.tmp (PID: 6896)
Checks supported languages
- WinVNC.exe (PID: 5712)
- vncviewer.exe (PID: 1104)
- tightvnc-1.2.9-setup.exe (PID: 6856)
- INSDCD0.tmp (PID: 6896)
Create files in a temporary directory
- tightvnc-1.2.9-setup.exe (PID: 6856)
- INSDCD0.tmp (PID: 6896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (82.8) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.7) |
| .exe | | | Win32 Executable (generic) (3.4) |
| .exe | | | Generic Win/DOS Executable (1.5) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 47104 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xbf98 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
201
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1104 | "C:\Program Files (x86)\TightVNC\vncviewer.exe" -compresslevel 9 -quality 0 | C:\Program Files (x86)\TightVNC\vncviewer.exe | — | explorer.exe | |||||||||||
User: admin Company: Constantin Kaplinsky Integrity Level: MEDIUM Description: vncviewer Version: 1, 2, 9, 0 Modules
| |||||||||||||||
| 5712 | "C:\Program Files (x86)\TightVNC\WinVNC.exe" | C:\Program Files (x86)\TightVNC\WinVNC.exe | — | explorer.exe | |||||||||||
User: admin Company: Constantin Kaplinsky Integrity Level: MEDIUM Description: TightVNC Win32 Server Version: 1, 2, 9, 0 Modules
| |||||||||||||||
| 6768 | "C:\Users\admin\AppData\Local\Temp\tightvnc-1.2.9-setup.exe" | C:\Users\admin\AppData\Local\Temp\tightvnc-1.2.9-setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6856 | "C:\Users\admin\AppData\Local\Temp\tightvnc-1.2.9-setup.exe" | C:\Users\admin\AppData\Local\Temp\tightvnc-1.2.9-setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6896 | C:\Users\admin\AppData\Local\Temp\INSDCD0.tmp /SL3 $7026A C:\Users\admin\AppData\Local\Temp\tightvnc-1.2.9-setup.exe 956215 959629 61952 | C:\Users\admin\AppData\Local\Temp\INSDCD0.tmp | tightvnc-1.2.9-setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 282
Read events
2 263
Write events
19
Delete events
0
Modification events
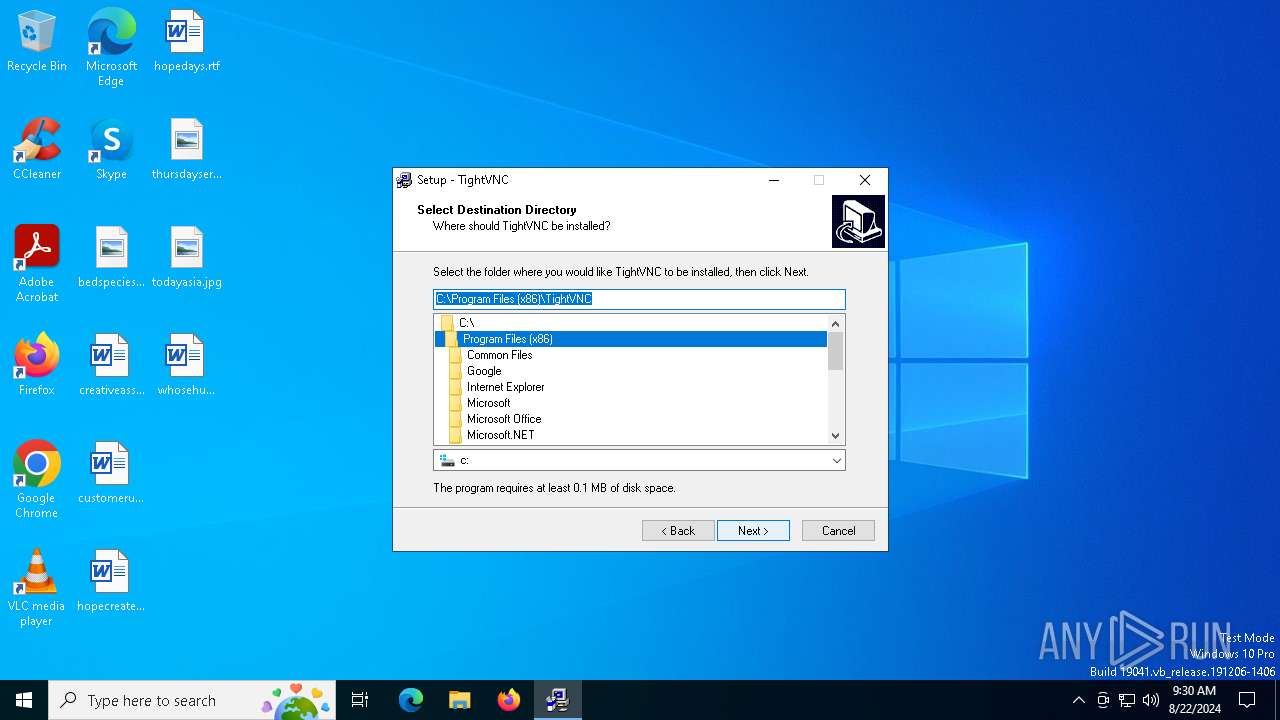
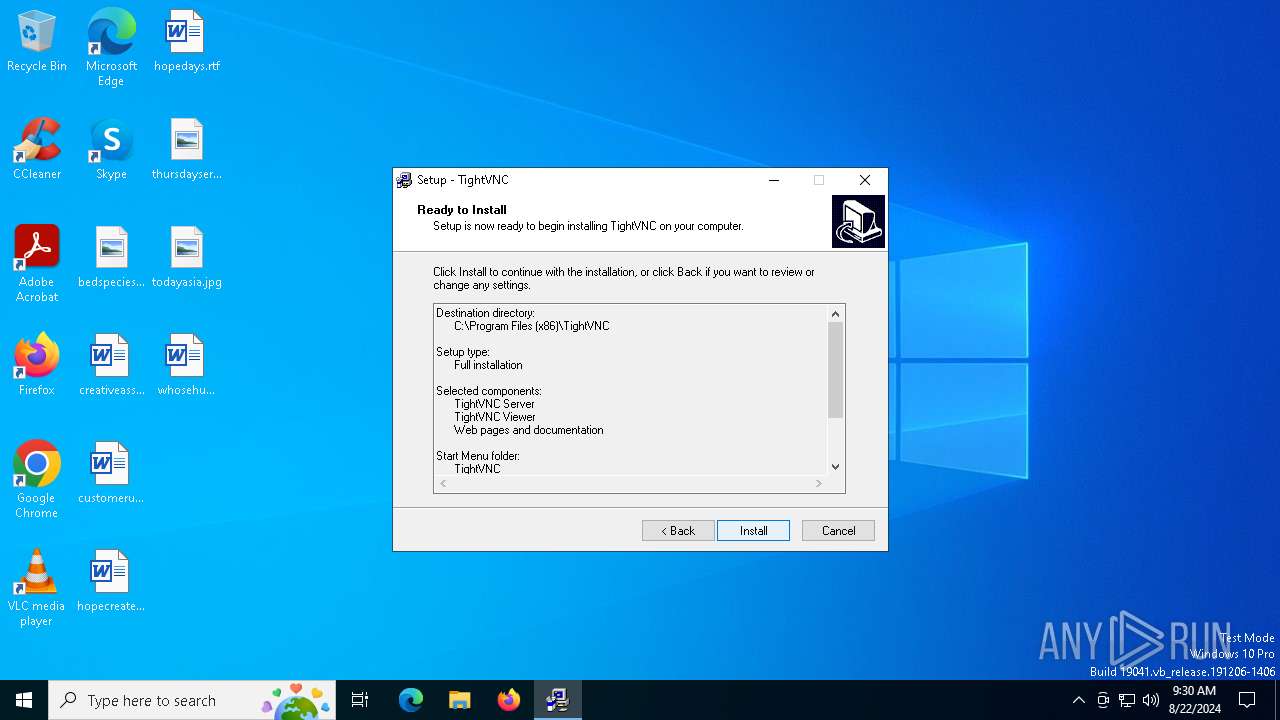
| (PID) Process: | (6896) INSDCD0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\TightVNC_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 3.0.7 | |||
| (PID) Process: | (6896) INSDCD0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\TightVNC_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\TightVNC | |||
| (PID) Process: | (6896) INSDCD0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\TightVNC_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: TightVNC | |||
| (PID) Process: | (6896) INSDCD0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\TightVNC_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
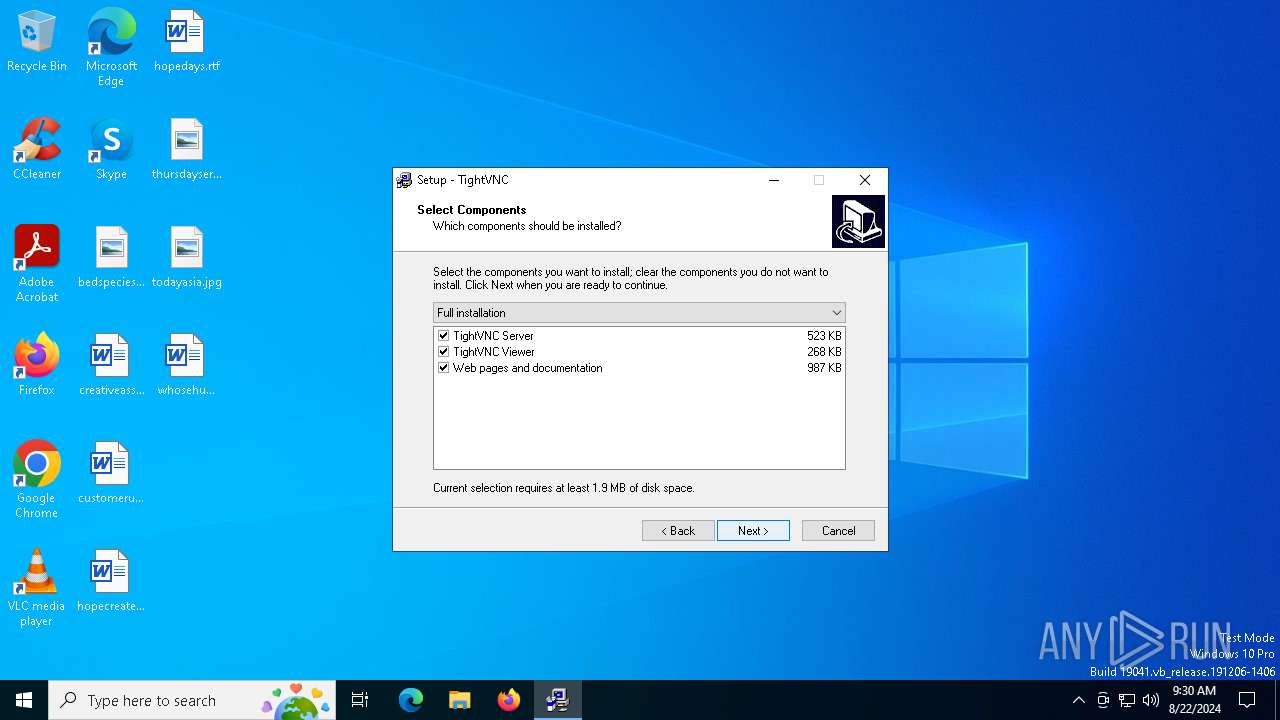
| (PID) Process: | (6896) INSDCD0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\TightVNC_is1 |
| Operation: | write | Name: | Inno Setup: Setup Type |
Value: full | |||
| (PID) Process: | (6896) INSDCD0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\TightVNC_is1 |
| Operation: | write | Name: | Inno Setup: Selected Components |
Value: server,viewer,webdoc | |||
| (PID) Process: | (6896) INSDCD0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\TightVNC_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Components |
Value: | |||
| (PID) Process: | (6896) INSDCD0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\TightVNC_is1 |
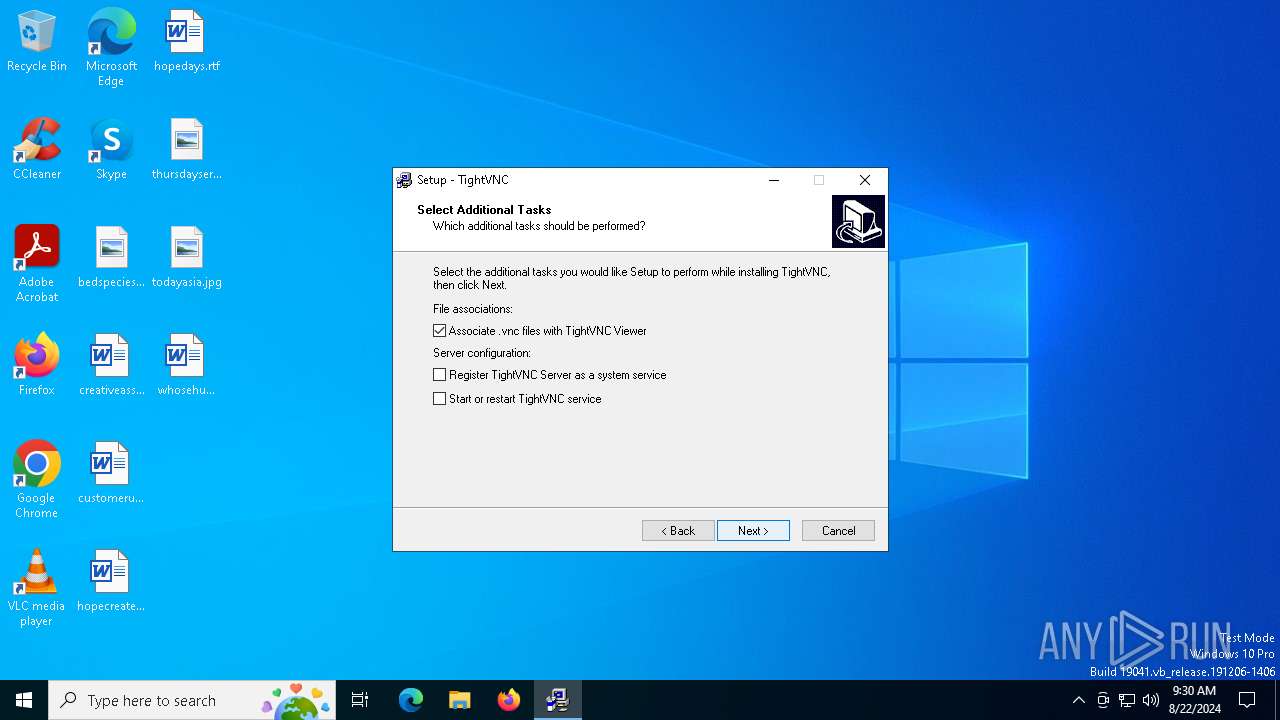
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: associate | |||
| (PID) Process: | (6896) INSDCD0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\TightVNC_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: installservice,startservice | |||
| (PID) Process: | (6896) INSDCD0.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\TightVNC_is1 |
| Operation: | write | Name: | DisplayName |
Value: TightVNC 1.2.9 | |||
Executable files
10
Suspicious files
17
Text files
135
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6896 | INSDCD0.tmp | C:\Users\admin\AppData\Local\Temp\is-E4HM0.tmp\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 6856 | tightvnc-1.2.9-setup.exe | C:\Users\admin\AppData\Local\Temp\INSDCD0.tmp | executable | |
MD5:EC2A3559EF793D976D3F72252ADE0B68 | SHA256:995CA25E8AC883429E67E2985887C2DC122E4D3CCA48D6AB5B545E6A896AE2E1 | |||
| 6896 | INSDCD0.tmp | C:\Program Files (x86)\TightVNC\VNCHooks.dll | executable | |
MD5:12320B551BF9555C02CC114ACEABDE96 | SHA256:DCC8C5F0657BC4C5955E9C6CF18BE4A1255F7F8B19B8042584C33230B76E1518 | |||
| 6896 | INSDCD0.tmp | C:\Program Files (x86)\TightVNC\vncviewer.exe | executable | |
MD5:D7FF34495B0ECF078FBFB5194E11C61B | SHA256:A2E57A71B679CCCAAD92030A6F06B9F3A6F1F5E89737B7EC48E916AF9B601D6F | |||
| 6896 | INSDCD0.tmp | C:\Program Files (x86)\TightVNC\is-D4E94.tmp | executable | |
MD5:D7FF34495B0ECF078FBFB5194E11C61B | SHA256:A2E57A71B679CCCAAD92030A6F06B9F3A6F1F5E89737B7EC48E916AF9B601D6F | |||
| 6896 | INSDCD0.tmp | C:\Program Files (x86)\TightVNC\is-MJTGG.tmp | text | |
MD5:939AB5B5A1847BE03027F2EEB2C0B5D0 | SHA256:1D0E10CBEA3659525235F6066490FB6BD1D772E7DEDE90E214A865986372F066 | |||
| 6896 | INSDCD0.tmp | C:\Program Files (x86)\TightVNC\is-UAKA0.tmp | executable | |
MD5:4430CC72B3A69E91F42043950461FBD1 | SHA256:50C32B8B80073C71DDDB3997B147E9903E60AC6EE5C25DF237BFCE83CBBDA646 | |||
| 6896 | INSDCD0.tmp | C:\Program Files (x86)\TightVNC\is-6KL65.tmp | executable | |
MD5:F58F2F89A111B08A26EAD3A8FD56B65C | SHA256:3431B0A61DFB90F53E465D774B310FC63892FA323CE381C06ACCCEC0D2E19041 | |||
| 6896 | INSDCD0.tmp | C:\Program Files (x86)\TightVNC\is-L14C9.tmp | executable | |
MD5:12320B551BF9555C02CC114ACEABDE96 | SHA256:DCC8C5F0657BC4C5955E9C6CF18BE4A1255F7F8B19B8042584C33230B76E1518 | |||
| 6896 | INSDCD0.tmp | C:\Program Files (x86)\TightVNC\LICENCE.txt | text | |
MD5:3CBEFE3885D918C8D00A6F8D7FF1013C | SHA256:6C4BEACE9AD98F6530A2E9B491E928E010B5996E2ACDB439E8DCE6CB3F25204B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
92
DNS requests
68
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6668 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2628 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6844 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
6720 | svchost.exe | GET | 206 | 23.48.23.65:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b5b66fb2-bcb3-4c8f-913d-3090036ab0d5?P1=1724918557&P2=404&P3=2&P4=Gqi%2flvMQXF%2bIu5P5ayQbHJi6ML%2f7Y4xkfAJMHBgBq8zQX47f1cpb58MBvLgSa4Vy5CuN5sZPwvj4E3%2bGJphgiA%3d%3d | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6720 | svchost.exe | GET | 206 | 23.48.23.65:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b5b66fb2-bcb3-4c8f-913d-3090036ab0d5?P1=1724918557&P2=404&P3=2&P4=Gqi%2flvMQXF%2bIu5P5ayQbHJi6ML%2f7Y4xkfAJMHBgBq8zQX47f1cpb58MBvLgSa4Vy5CuN5sZPwvj4E3%2bGJphgiA%3d%3d | unknown | — | — | whitelisted |
6720 | svchost.exe | HEAD | 200 | 23.48.23.65:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b5b66fb2-bcb3-4c8f-913d-3090036ab0d5?P1=1724918557&P2=404&P3=2&P4=Gqi%2flvMQXF%2bIu5P5ayQbHJi6ML%2f7Y4xkfAJMHBgBq8zQX47f1cpb58MBvLgSa4Vy5CuN5sZPwvj4E3%2bGJphgiA%3d%3d | unknown | — | — | whitelisted |
6720 | svchost.exe | GET | 206 | 23.48.23.65:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b5b66fb2-bcb3-4c8f-913d-3090036ab0d5?P1=1724918557&P2=404&P3=2&P4=Gqi%2flvMQXF%2bIu5P5ayQbHJi6ML%2f7Y4xkfAJMHBgBq8zQX47f1cpb58MBvLgSa4Vy5CuN5sZPwvj4E3%2bGJphgiA%3d%3d | unknown | — | — | whitelisted |
6720 | svchost.exe | GET | 206 | 23.48.23.65:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b5b66fb2-bcb3-4c8f-913d-3090036ab0d5?P1=1724918557&P2=404&P3=2&P4=Gqi%2flvMQXF%2bIu5P5ayQbHJi6ML%2f7Y4xkfAJMHBgBq8zQX47f1cpb58MBvLgSa4Vy5CuN5sZPwvj4E3%2bGJphgiA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1356 | RUXIMICS.exe | 51.11.168.232:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
2120 | MoUsoCoreWorker.exe | 51.11.168.232:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
1292 | svchost.exe | 51.11.168.232:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
1292 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2628 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2628 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6668 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |