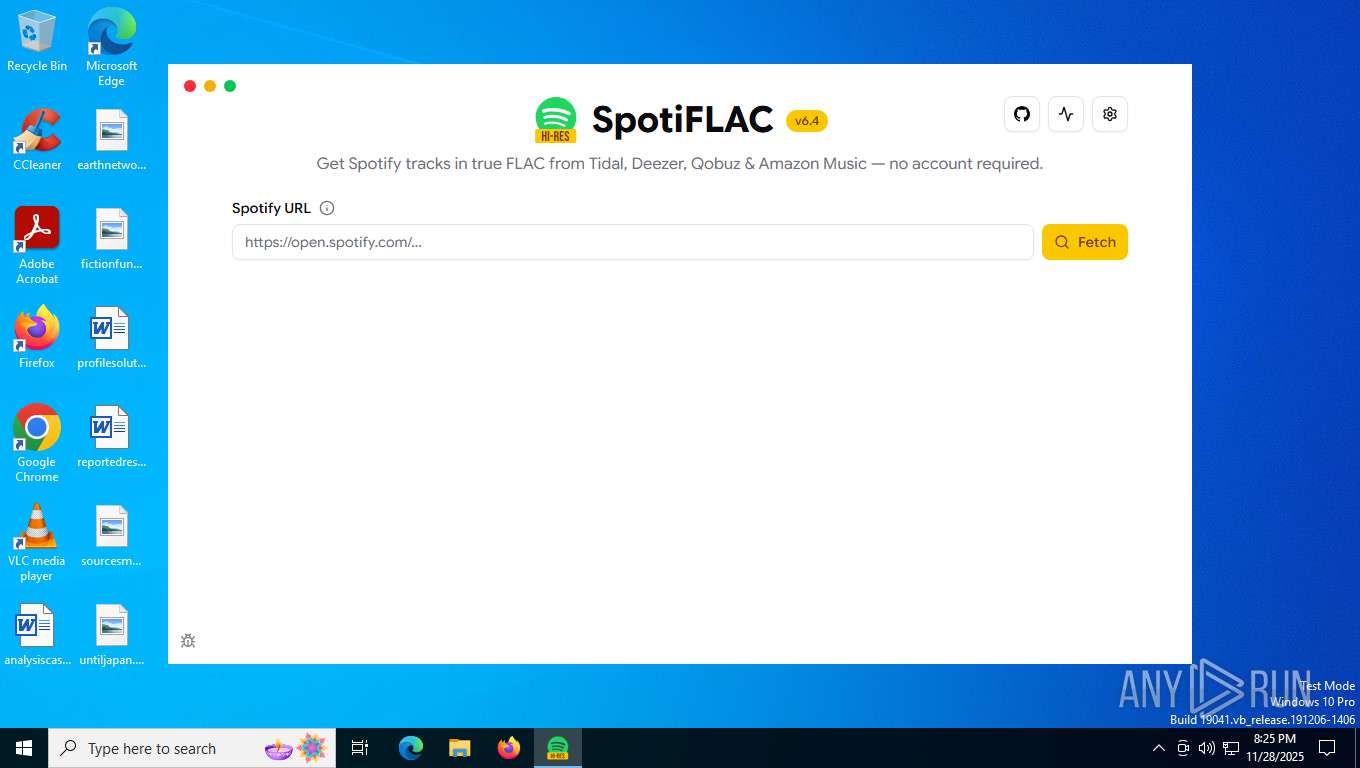
| File name: | SpotiFLAC.exe |
| Full analysis: | https://app.any.run/tasks/753fc5df-e414-4039-91d5-c9950e6da7a6 |
| Verdict: | Malicious activity |
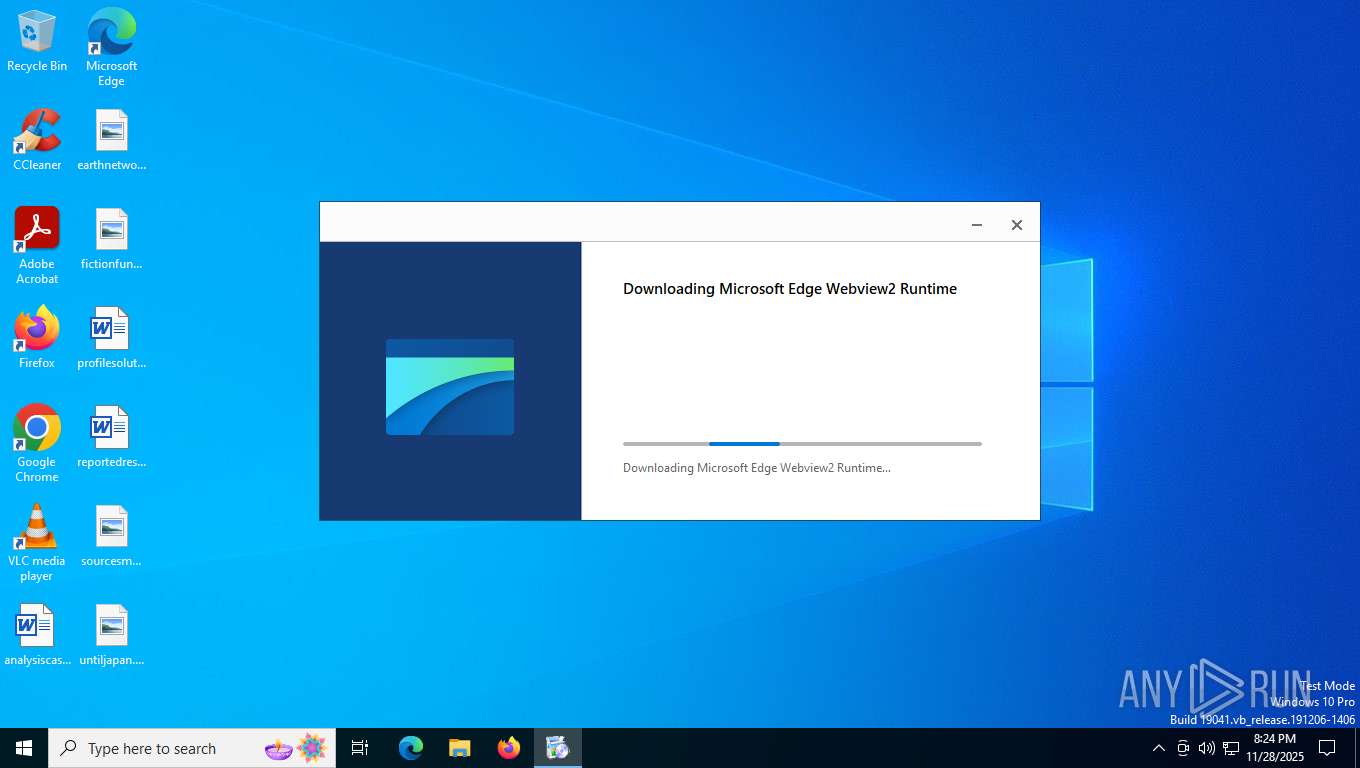
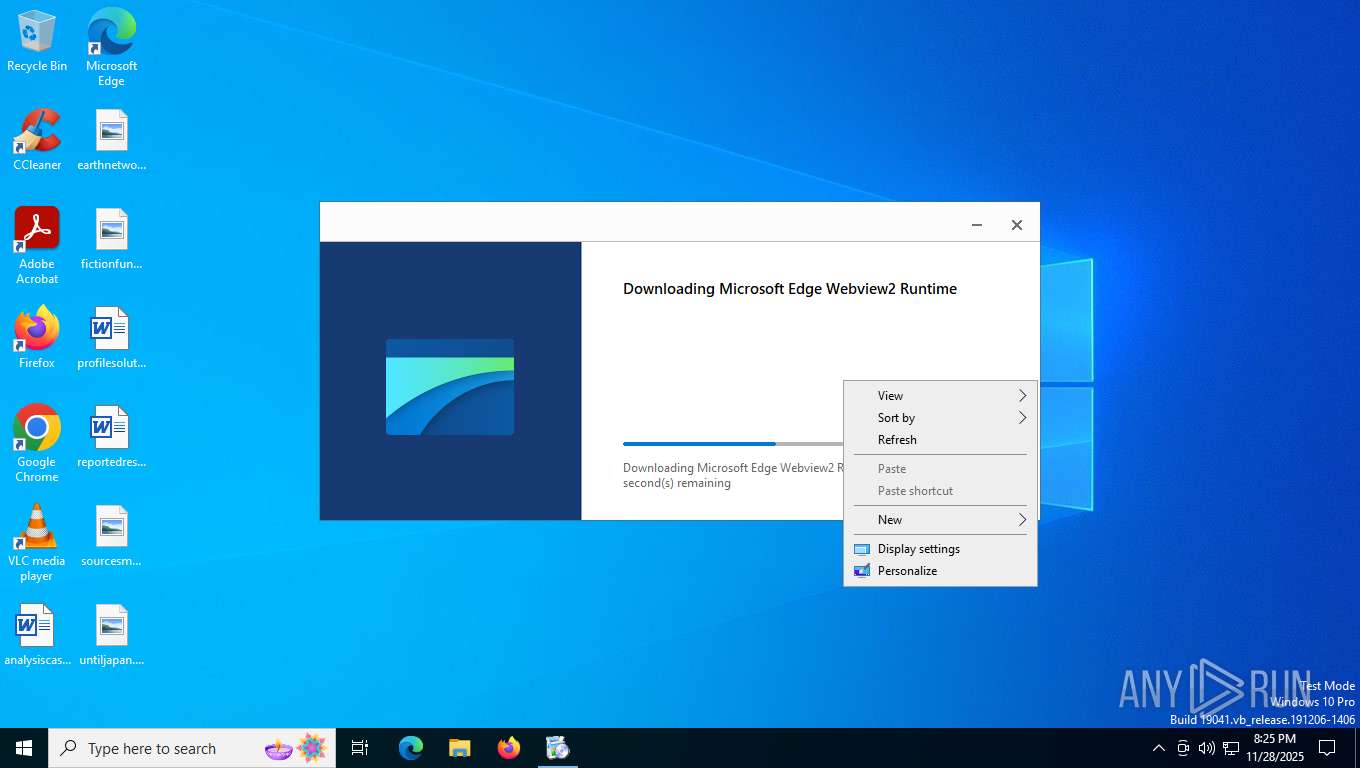
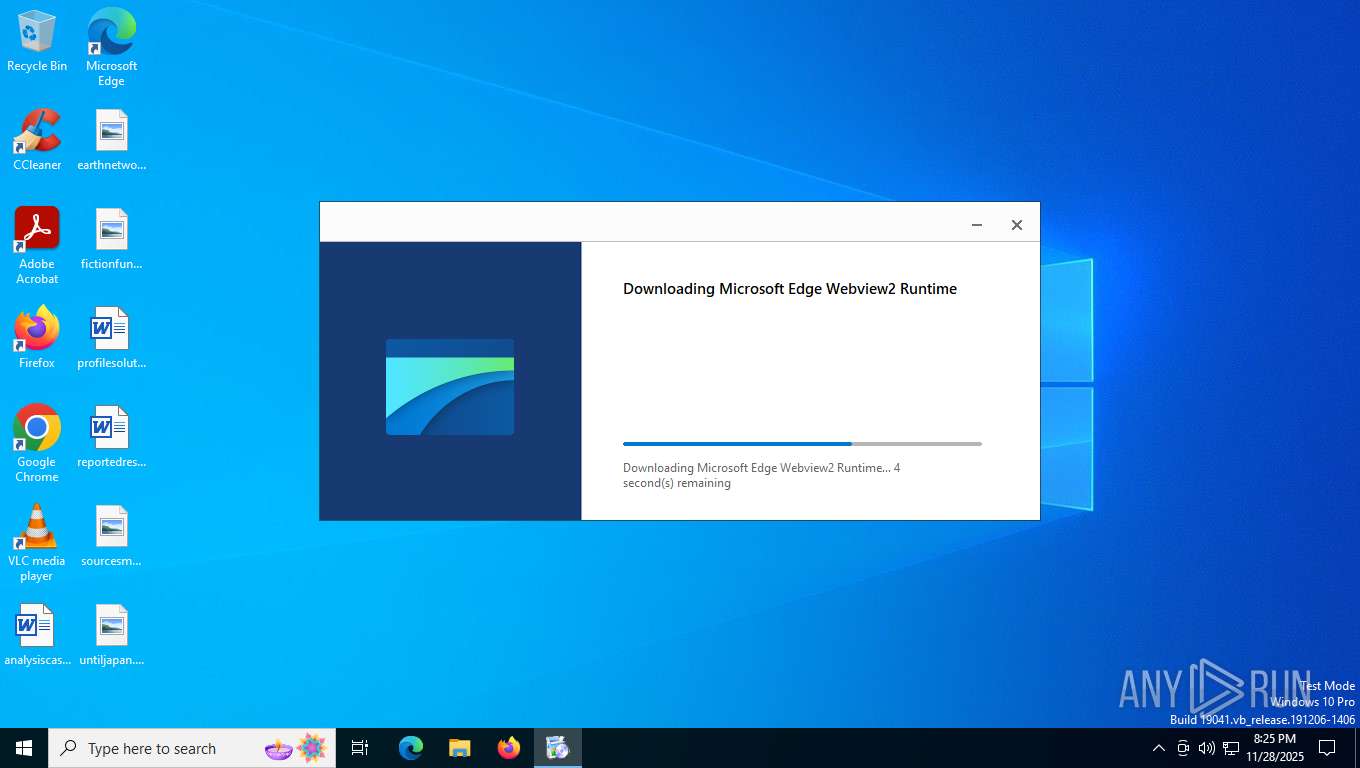
| Analysis date: | November 28, 2025, 20:24:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 3 sections |
| MD5: | 1F0767F573C269101F46CE2C316F6311 |
| SHA1: | 0DD56DB65A6C76C45405C1801E861642CE7204BF |
| SHA256: | E4EAD91B9EBD3D9CCF8031C63786020DB8DDC974392BA1177902A68296EB18CA |
| SSDEEP: | 98304:t997BYRMuUG0YnVJL93gz5go48lYrGHEz2Tvxk+FfCMl9l9aLeQPLx7kDAg7hwOJ:SGtvI3+ |
MALICIOUS
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 2692)
The DLL Hijacking
- msedgewebview2.exe (PID: 3320)
SUSPICIOUS
Executable content was dropped or overwritten
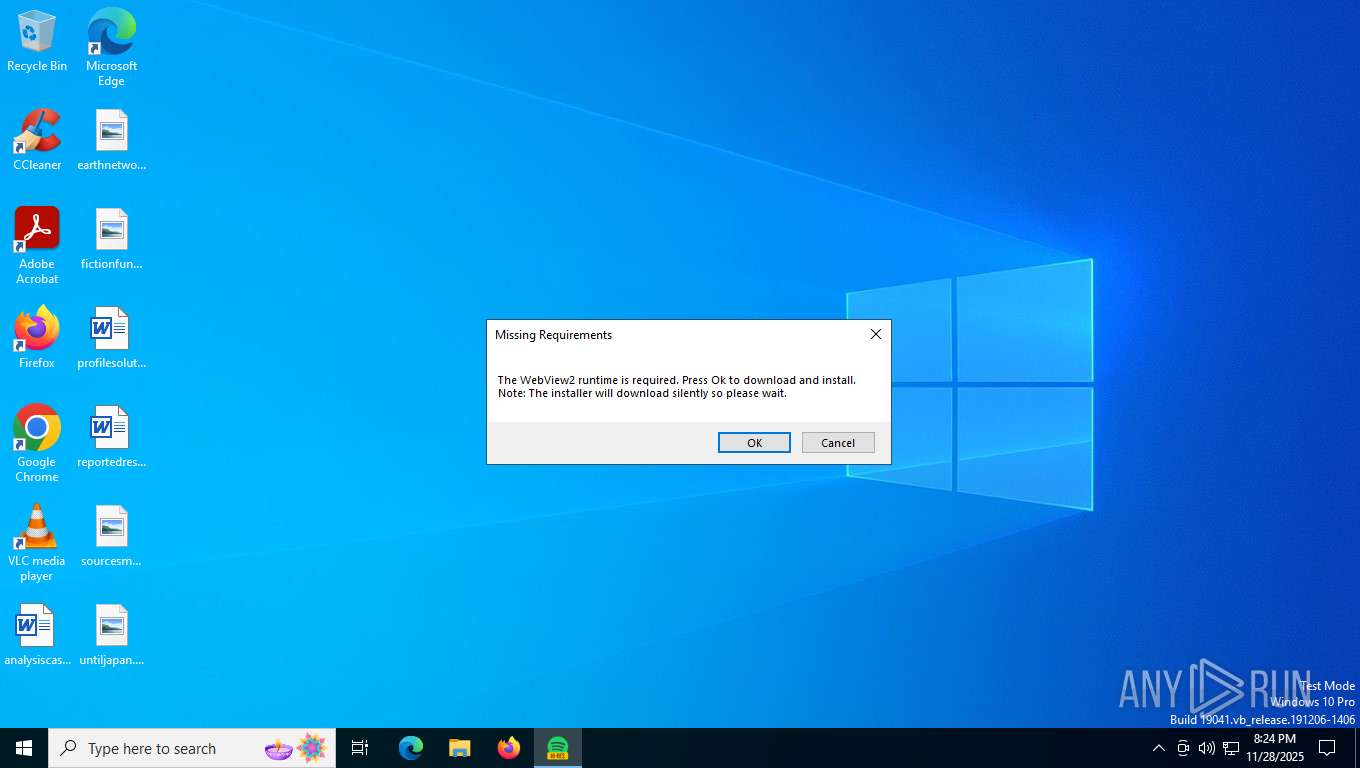
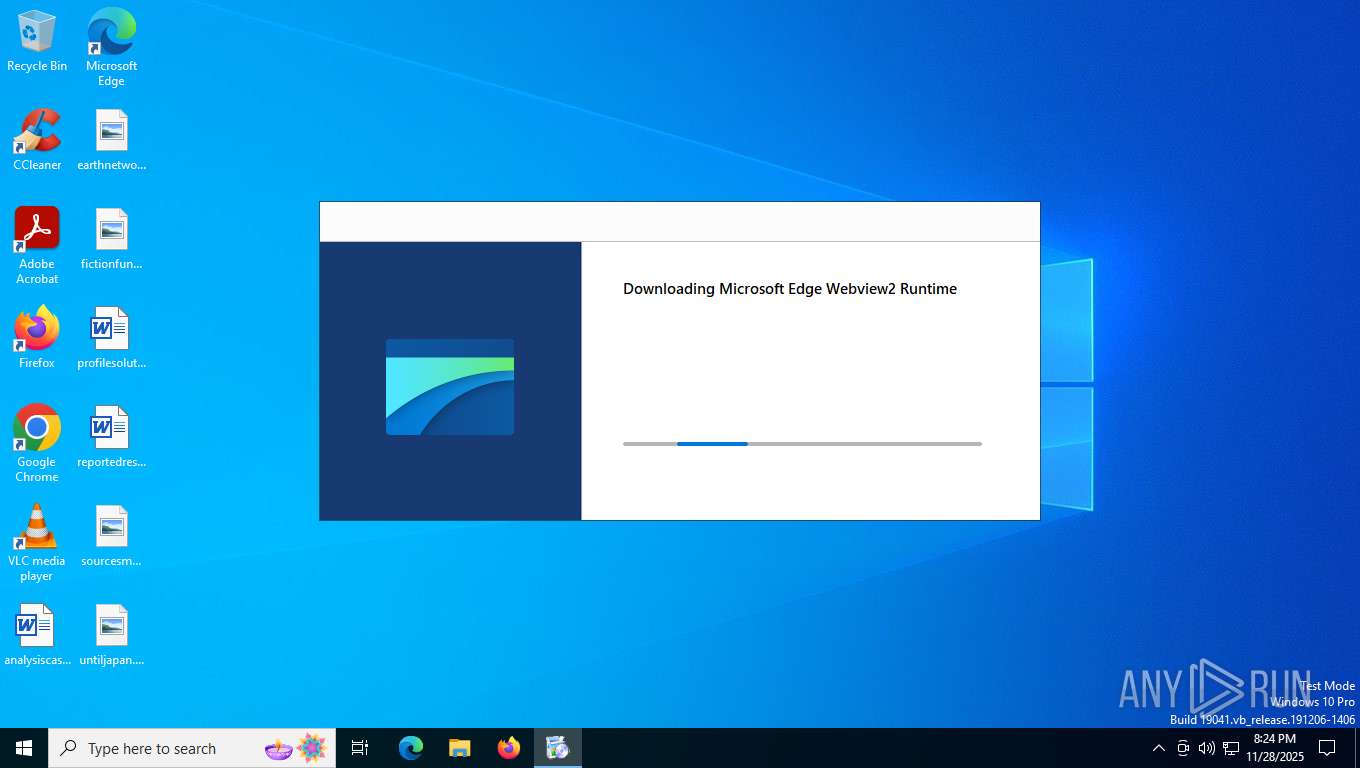
- SpotiFLAC.exe (PID: 4164)
- MicrosoftEdgeWebview2Setup.exe (PID: 6548)
- MicrosoftEdgeUpdate.exe (PID: 2692)
- MicrosoftEdge_X64_142.0.3595.94.exe (PID: 4140)
- setup.exe (PID: 6492)
Process drops legitimate windows executable
- MicrosoftEdgeWebview2Setup.exe (PID: 6548)
- MicrosoftEdgeUpdate.exe (PID: 2692)
- MicrosoftEdge_X64_142.0.3595.94.exe (PID: 4140)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 2692)
- MicrosoftEdgeWebview2Setup.exe (PID: 6548)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 2692)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdate.exe (PID: 6636)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5612)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2176)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6384)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 2692)
- MicrosoftEdgeUpdate.exe (PID: 6712)
- msedgewebview2.exe (PID: 3028)
There is functionality for taking screenshot (YARA)
- SpotiFLAC.exe (PID: 4164)
Searches for installed software
- setup.exe (PID: 6492)
Application launched itself
- MicrosoftEdgeUpdate.exe (PID: 6712)
- setup.exe (PID: 6492)
- msedgewebview2.exe (PID: 3028)
INFO
Reads the computer name
- SpotiFLAC.exe (PID: 4164)
- MicrosoftEdgeUpdate.exe (PID: 2692)
- MicrosoftEdgeUpdate.exe (PID: 6636)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5612)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6384)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2176)
- MicrosoftEdgeUpdate.exe (PID: 4324)
- MicrosoftEdgeUpdate.exe (PID: 2308)
- MicrosoftEdgeUpdate.exe (PID: 6712)
- MicrosoftEdge_X64_142.0.3595.94.exe (PID: 4140)
- setup.exe (PID: 6492)
- MicrosoftEdgeUpdate.exe (PID: 2256)
- msedgewebview2.exe (PID: 3028)
- msedgewebview2.exe (PID: 3320)
- msedgewebview2.exe (PID: 1804)
Reads Environment values
- SpotiFLAC.exe (PID: 4164)
- MicrosoftEdgeUpdate.exe (PID: 4324)
- MicrosoftEdgeUpdate.exe (PID: 2256)
- msedgewebview2.exe (PID: 3028)
Create files in a temporary directory
- SpotiFLAC.exe (PID: 4164)
- MicrosoftEdgeWebview2Setup.exe (PID: 6548)
- msedgewebview2.exe (PID: 3028)
The sample compiled with english language support
- MicrosoftEdgeWebview2Setup.exe (PID: 6548)
- SpotiFLAC.exe (PID: 4164)
- MicrosoftEdgeUpdate.exe (PID: 2692)
- MicrosoftEdge_X64_142.0.3595.94.exe (PID: 4140)
- setup.exe (PID: 6492)
Reads the machine GUID from the registry
- SpotiFLAC.exe (PID: 4164)
- MicrosoftEdgeUpdate.exe (PID: 6712)
- msedgewebview2.exe (PID: 3028)
Checks supported languages
- SpotiFLAC.exe (PID: 4164)
- MicrosoftEdgeWebview2Setup.exe (PID: 6548)
- MicrosoftEdgeUpdate.exe (PID: 2692)
- MicrosoftEdgeUpdate.exe (PID: 6636)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5612)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6384)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2176)
- MicrosoftEdgeUpdate.exe (PID: 4324)
- MicrosoftEdgeUpdate.exe (PID: 2308)
- MicrosoftEdgeUpdate.exe (PID: 6712)
- setup.exe (PID: 6492)
- MicrosoftEdge_X64_142.0.3595.94.exe (PID: 4140)
- setup.exe (PID: 5660)
- MicrosoftEdgeUpdate.exe (PID: 2256)
- msedgewebview2.exe (PID: 3028)
- msedgewebview2.exe (PID: 4048)
- msedgewebview2.exe (PID: 3320)
- msedgewebview2.exe (PID: 1804)
- msedgewebview2.exe (PID: 6244)
- msedgewebview2.exe (PID: 3204)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 2692)
- MicrosoftEdgeUpdate.exe (PID: 6712)
- MicrosoftEdge_X64_142.0.3595.94.exe (PID: 4140)
- setup.exe (PID: 5660)
- setup.exe (PID: 6492)
- msedgewebview2.exe (PID: 3028)
- msedgewebview2.exe (PID: 4048)
- msedgewebview2.exe (PID: 1804)
Launching a file from a Registry key
- MicrosoftEdgeUpdate.exe (PID: 2692)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 2692)
- setup.exe (PID: 6492)
- msedgewebview2.exe (PID: 3028)
- msedgewebview2.exe (PID: 3204)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 4324)
- MicrosoftEdgeUpdate.exe (PID: 6712)
- MicrosoftEdgeUpdate.exe (PID: 2256)
- msedgewebview2.exe (PID: 3028)
UPX packer has been detected
- SpotiFLAC.exe (PID: 4164)
Detects GO elliptic curve encryption (YARA)
- SpotiFLAC.exe (PID: 4164)
Application based on Golang
- SpotiFLAC.exe (PID: 4164)
Creates a software uninstall entry
- setup.exe (PID: 6492)
Reads CPU info
- msedgewebview2.exe (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (87.1) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.4) |
| .exe | | | DOS Executable Generic (6.4) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 3403776 |
| InitializedDataSize: | 40960 |
| UninitializedDataSize: | 8712192 |
| EntryPoint: | 0xb8db00 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.4.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Built using Wails (https://wails.io) |
| CompanyName: | SpotiFLAC |
| FileDescription: | SpotiFLAC |
| LegalCopyright: | Copyright......... |
| ProductName: | SpotiFLAC |
| ProductVersion: | 6.4 |
Total processes
171
Monitored processes
23
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 940 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\142.0.3595.94\msedgewebview2.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Roaming\SpotiFLAC.exe\EBWebView" --webview-exe-name=SpotiFLAC.exe --webview-exe-version=6.4 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --force-high-res-timeticks=disabled --startup-read-main-dll --metrics-shmem-handle=2188,i,2926639164437542251,13331579954601706275,524288 --field-trial-handle=1912,i,5188261680952606124,1721952684639490544,262144 --enable-features=ForceSWDCompWhenDCompFallbackRequired,LocalNetworkAccessForFencedFrameNavigationsWarningOnly,LocalNetworkAccessForNavigationsWarningOnly,LocalNetworkAccessForSubframeNavigationsWarningOnly,LocalNetworkAccessForWorkersWarningOnly,msAggressiveCacheTrimming,msCustomDataPartition,msWebView2NoTabForScreenShare,msWindowsTaskManager --disable-features=BackForwardCache,BackgroundTabLoadingFromPerformanceManager,CloseOmniboxPopupOnInactiveAreaClick,CollectAVProductsInfo,CollectCodeIntegrityInfo,DeferSpeculativeRFHCreation,EnableHangWatcher,FilterAdsOnAbusiveSites,GetWifiProtocol,LoginDetection,MediaFoundationCameraUsageMonitoring,PreconnectToSearch,PreloadingEagerHeuristics,SafetyHub,SegmentationPlatform,ServiceWorkerAutoPreload,SpareRendererForSitePerProcess,Ukm,WebPayments,msAITrackerClassification,msAbydosForWindowlessWV2,msAffirmVirtualCard,msAllowChromeWebstore,msAllowMSAPrtSSOForNonMSAProfile,msApplicationGuard,msAskBeforeClosingMultipleTabs,msAutoToggleAADPrtSSOForNonAADProfile,msAutofillEdgeServiceRequest,msAutofillEnableEdgeSuggestions,msAutomaticTabFreeze,msBrowserSettingsSupported,msCoarseGeolocationService,msDataProtection,msDesktopMode,msDesktopRewards,msDisableVariationsSeedFetchThrottling,msEEProactiveHistory,msETFOffstoreExtensionFileDataCollection,msETFPasswordTheftDNRActionSignals,msEdgeAdPlatformUI,msEdgeAddWebCapturetoCollections,msEdgeAutofillShowDeployedPassword,msEdgeCaptureSelectionInPDF,msEdgeCloudConfigService,msEdgeCloudConfigServiceV2,msEdgeCohorts,msEdgeCollectionsPrismExperiment1,msEdgeCollectionsPrismOverallMigration,msEdgeComposeNext,msEdgeEnableNurturingFramework,msEdgeEnclavePrefsBasic,msEdgeEnclavePrefsNotification,msEdgeFaviconService,msEdgeHJTelemetry,msEdgeHubAppSkype,msEdgeImageEditorUI,msEdgeLinkDoctor,msEdgeMouseGestureDefaultEnabled,msEdgeMouseGestureSupported,msEdgeNewDeviceFre,msEdgeOnRampFRE,msEdgeOnRampImport,msEdgePDFCMHighlightUX,msEdgePasswordIris,msEdgePasswordIrisSaveBubble,msEdgePasswordStrengthCheck,msEdgePinpointFramework,msEdgeProngPersonalization,msEdgeReadingView,msEdgeRose,msEdgeScreenshotUI,msEdgeSendTabToSelf,msEdgeSettingsImport,msEdgeSettingsImportV2,msEdgeShoppingPersistentStorage,msEdgeShoppingUI,msEdgeSmartFind,msEdgeSuperDragDefaultEnabled,msEdgeSuperDragDropSupported,msEdgeTranslate,msEdgeUpdatesMoreMenuPill,msEdgeWebCapture,msEdgeWebCaptureUniformExperience,msEdgeWebContentFilteringFeedback,msEdgeWorkSearchBanner,msEnableCustomJobMemoryLimitsOnXbox,msEnableMIPForPDF,msEnablePdfUpsell,msEnableThirdPartyScanning,msEnableWebSignInCta,msEnableWebToBrowserSignIn,msEndpointDlp,msEntityExtraction,msExtensionTelemetryFramework,msExternalTaskManager,msFileSystemAccessDirectoryIterationBlocklistCheck,msForceBrowserSignIn,msForeignSessionsPage,msGeolocationAccessService,msGeolocationOSLocationPermissionFallback,msGeolocationSQMService,msGeolocationService,msGrowthInfraLaunchSourceLogging,msGuidedSwitchAllowed,msHubPinPersist,msImplicitSignin,msIrm,msIrmv2,msKlarnaVirtualCard,msLlmConsumerDlpPurview,msLoadStatistics,msLogIsEdgePinnedToTaskbarOnLaunch,msMIPCrossTenantPdfViewSupport,msMdatpWebSiteDlp,msNotificationPermissionForPWA,msNumberOfSitesToPin,msNurturingGlobalSitePinningOnCloseModal,msNurturingSitePinningCITopSites,msNurturingSitePinningWithWindowsConsent,msOnHoverSearchInSidebar,msOpenOfficeDocumentsInWebViewer,msPageInteractionRestrictionRevoke,msPasswordBreachDetection,msPdfAnnotationsVisibility,msPdfDataRecovery,msPdfDigitalSignatureRead,msPdfFreeText,msPdfFreeTextForCJK,msPdfHighlightMode,msPdfInking,msPdfKeyphraseSupport,msPdfOOUI,msPdfPopupMarkerRenderer,msPdfShare,msPdfSharedLibrary,msPdfTextNote,msPdfTextNoteMoreMenu,msPdfThumbnailCache,msPdfUnderside,msPdfViewRestore,msPersonalizationUMA,msPriceComparison,msPromptDefaultHandlerForPDF,msReactiveSearch,msReadAloud,msReadAloudPdf,msRedirectToShoreline,msRevokeExtensions,msSaasDlp,msShoppingTrigger,msShorelineSearch,msShorelineSearchFindOnPageWebUI,msShowOfflineGameEntrance,msShowReadAloudIconInAddressBar,msShowUXForAADPrtSSOForNonAADProfile,msSitePinningWithoutUi,msSmartScreenProtection,msSuspendMessageForNewSessionWhenHavingPendingNavigation,msSyncEdgeCollections,msTabResourceStats,msTokenizationAutofillInlineEnabled,msTouchMode,msTriggeringSignalGenerator,msUserUnderstanding,msVideoSuperResolutionUI,msWalletBuyNow,msWalletCheckout,msWalletDiagnosticDataLogger,msWalletHubEntry,msWalletHubIntlP3,msWalletPartialCard,msWalletPasswordCategorization,msWalletPasswordCategorizationPlatformExpansion,msWalletTokenizationCardMetadata,msWalletTokenizedAutofill,msWebAssist,msWebAssistHistorySearchService,msWebOOUI,msWindowsUserActivities,msZipPayVirtualCard --variations-seed-version --trace-process-track-uuid=3190708989122997041 --mojo-platform-channel-handle=2184 /prefetch:3 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\142.0.3595.94\msedgewebview2.exe | msedgewebview2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 142.0.3595.94 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.209.9\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.209.9\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.209.9 Modules
| |||||||||||||||
| 2256 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB1cGRhdGVyPSJPbWFoYSIgdXBkYXRlcnZlcnNpb249IjEuMy4yMDkuOSIgc2hlbGxfdmVyc2lvbj0iMS4zLjIwOS45IiBpc21hY2hpbmU9IjAiIHNlc3Npb25pZD0ie0ExNzg2NzE1LTgyRDEtNDE5OS04QkY1LTFEODFDQ0ExRjYyRH0iIHVzZXJpZD0ie0I0MzE4ODA5LURFMDktNDhCNC05QkNFLTc1QTE1RkVEOEQ5RX0iIGluc3RhbGxzb3VyY2U9InRhZ2dlZG1pIiByZXF1ZXN0aWQ9Ins4NUVDM0NENC01NzJBLTQ0OEUtQjRDOS1DNzk5RUIzNkFDMDJ9IiBkZWR1cD0iY3IiIGRvbWFpbmpvaW5lZD0iMCI-PGh3IGxvZ2ljYWxfY3B1cz0iNiIgcGh5c21lbW9yeT0iNiIgZGlza190eXBlPSIyIiBzc2U9IjEiIHNzZTI9IjEiIHNzZTM9IjEiIHNzc2UzPSIxIiBzc2U0MT0iMSIgc3NlNDI9IjEiIGF2eD0iMSIvPjxvcyBwbGF0Zm9ybT0id2luIiB2ZXJzaW9uPSIxMC4wLjE5MDQ1LjQwNDYiIHNwPSIiIGFyY2g9Ing2NCIgcHJvZHVjdF90eXBlPSI0OCIgaXNfd2lwPSIwIiBpc19pbl9sb2NrZG93bl9tb2RlPSIwIi8-PG9lbSBwcm9kdWN0X21hbnVmYWN0dXJlcj0iREVMTCIgcHJvZHVjdF9uYW1lPSJERUxMIi8-PGV4cCBldGFnPSImcXVvdDtOZTAxeGZ4RnZVV3lkcFpzSjNmU2JVenh4L2lBYTc3eEdaekZWdW02TlBzPSZxdW90OyIvPjxhcHAgYXBwaWQ9IntGMzAxNzIyNi1GRTJBLTQyOTUtOEJERi0wMEMzQTlBN0U0QzV9IiB2ZXJzaW9uPSIiIG5leHR2ZXJzaW9uPSIxNDIuMC4zNTk1Ljk0IiBsYW5nPSJlbiIgYnJhbmQ9IiIgY2xpZW50PSIiIGV4cGVyaW1lbnRzPSJjb25zZW50PWZhbHNlIiBpbnN0YWxsYWdlPSItMSIgaW5zdGFsbGRhdGU9Ii0xIj48dXBkYXRlY2hlY2svPjxldmVudCBldmVudHR5cGU9IjkiIGV2ZW50cmVzdWx0PSIxIiBlcnJvcmNvZGU9IjAiIGV4dHJhY29kZTE9IjAiIHN5c3RlbV91cHRpbWVfdGlja3M9IjE0NTcyMzM3MDIwIiBkb25lX2JlZm9yZV9vb2JlX2NvbXBsZXRlPSIwIi8-PGV2ZW50IGV2ZW50dHlwZT0iNSIgZXZlbnRyZXN1bHQ9IjEiIGVycm9yY29kZT0iMCIgZXh0cmFjb2RlMT0iMCIgc3lzdGVtX3VwdGltZV90aWNrcz0iMTQ1NzIzMzcwMjAiIGRvbmVfYmVmb3JlX29vYmVfY29tcGxldGU9IjAiLz48ZXZlbnQgZXZlbnR0eXBlPSIxIiBldmVudHJlc3VsdD0iMSIgZXJyb3Jjb2RlPSIwIiBleHRyYWNvZGUxPSIwIiBzeXN0ZW1fdXB0aW1lX3RpY2tzPSIxNDY4Njg2NzA2NSIgc291cmNlX3VybF9pbmRleD0iMCIgZG9uZV9iZWZvcmVfb29iZV9jb21wbGV0ZT0iMCIgZG93bmxvYWRlcj0iYml0cyIgdXJsPSJodHRwOi8vbXNlZGdlLmYudGx1LmRsLmRlbGl2ZXJ5Lm1wLm1pY3Jvc29mdC5jb20vZmlsZXN0cmVhbWluZ3NlcnZpY2UvZmlsZXMvMDAzOTIyYTktNjg0Ni00OGUxLWI4NjQtMjAwZWUzMWZkYTc5P1AxPTE3NjQ5NjYyOTgmYW1wO1AyPTQwNCZhbXA7UDM9MiZhbXA7UDQ9TXZ0NUVQNUdlJTJicjdYTjZjekhkZVhJMlVOQUxObzVHSXBTJTJiSmExSTZJWEZxUjA4RHJxb3JmUTRkaDBNJTJiZUtHZThkdEM1b1BSTU91elU2eFV3Wmx0eHclM2QlM2QiIHNlcnZlcl9pcF9oaW50PSIiIGNkbl9jaWQ9Ii0xIiBjZG5fY2NjPSIiIGNkbl9tc2VkZ2VfcmVmPSIiIGNkbl9henVyZV9yZWZfb3JpZ2luX3NoaWVsZD0iIiBjZG5fY2FjaGU9IiIgY2RuX3AzcD0iIiBkb3dubG9hZGVkPSIxODU5Njc3MTIiIHRvdGFsPSIxODU5Njc3MTIiIGRvd25sb2FkX3RpbWVfbXM9Ijg2ODciLz48ZXZlbnQgZXZlbnR0eXBlPSIxIiBldmVudHJlc3VsdD0iMSIgZXJyb3Jjb2RlPSIwIiBleHRyYWNvZGUxPSIwIiBzeXN0ZW1fdXB0aW1lX3RpY2tzPSIxNDY4NzAyMzMzMSIgc291cmNlX3VybF9pbmRleD0iMCIgZG9uZV9iZWZvcmVfb29iZV9jb21wbGV0ZT0iMCIvPjxldmVudCBldmVudHR5cGU9IjYiIGV2ZW50cmVzdWx0PSIxIiBlcnJvcmNvZGU9IjAiIGV4dHJhY29kZTE9IjAiIHN5c3RlbV91cHRpbWVfdGlja3M9IjE0NzA1NjE2ODUzIiBkb25lX2JlZm9yZV9vb2JlX2NvbXBsZXRlPSIwIi8-PGV2ZW50IGV2ZW50dHlwZT0iMiIgZXZlbnRyZXN1bHQ9IjEiIGVycm9yY29kZT0iMCIgZXh0cmFjb2RlMT0iMTk2NzU3IiBzeXN0ZW1fdXB0aW1lX3RpY2tzPSIxNTAyNTc1NDc1MCIgc291cmNlX3VybF9pbmRleD0iMCIgZG9uZV9iZWZvcmVfb29iZV9jb21wbGV0ZT0iMCIgdXBkYXRlX2NoZWNrX3RpbWVfbXM9IjE0MCIgZG93bmxvYWRfdGltZV9tcz0iMTE0NTMiIGRvd25sb2FkZWQ9IjE4NTk2NzcxMiIgdG90YWw9IjE4NTk2NzcxMiIgcGFja2FnZV9jYWNoZV9yZXN1bHQ9IjAiIGluc3RhbGxfdGltZV9tcz0iMzIwMTQiLz48L2FwcD48L3JlcXVlc3Q- | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.209.9 Modules
| |||||||||||||||
| 2308 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /handoff "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=false" /installsource taggedmi /sessionid "{A1786715-82D1-4199-8BF5-1D81CCA1F62D}" | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.209.9 Modules
| |||||||||||||||
| 2692 | C:\Users\admin\AppData\Local\Temp\EU3482.tmp\MicrosoftEdgeUpdate.exe /installsource taggedmi /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Users\admin\AppData\Local\Temp\EU3482.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeWebview2Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.209.9 Modules
| |||||||||||||||
| 3028 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\142.0.3595.94\msedgewebview2.exe" --embedded-browser-webview=1 --webview-exe-name=SpotiFLAC.exe --webview-exe-version=6.4 --user-data-dir="C:\Users\admin\AppData\Roaming\SpotiFLAC.exe\EBWebView" --noerrdialogs --embedded-browser-webview-dpi-awareness=2 --disable-features=msSmartScreenProtection --mojo-named-platform-channel-pipe=4164.1384.11028824266065395100 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\142.0.3595.94\msedgewebview2.exe | SpotiFLAC.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 142.0.3595.94 Modules
| |||||||||||||||
| 3204 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\142.0.3595.94\msedgewebview2.exe" --type=renderer --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Roaming\SpotiFLAC.exe\EBWebView" --webview-exe-name=SpotiFLAC.exe --webview-exe-version=6.4 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --dma-cps-flags=0 --force-high-res-timeticks=disabled --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --js-flags="--expose-gc --ms-user-locale=" --ram-no-pressure-read-main-dll --metrics-shmem-handle=3552,i,14865800451100606518,4048074583993966703,2097152 --field-trial-handle=1912,i,5188261680952606124,1721952684639490544,262144 --enable-features=ForceSWDCompWhenDCompFallbackRequired,LocalNetworkAccessForFencedFrameNavigationsWarningOnly,LocalNetworkAccessForNavigationsWarningOnly,LocalNetworkAccessForSubframeNavigationsWarningOnly,LocalNetworkAccessForWorkersWarningOnly,msAggressiveCacheTrimming,msCustomDataPartition,msWebView2NoTabForScreenShare,msWindowsTaskManager --disable-features=BackForwardCache,BackgroundTabLoadingFromPerformanceManager,CloseOmniboxPopupOnInactiveAreaClick,CollectAVProductsInfo,CollectCodeIntegrityInfo,DeferSpeculativeRFHCreation,EnableHangWatcher,FilterAdsOnAbusiveSites,GetWifiProtocol,LoginDetection,MediaFoundationCameraUsageMonitoring,PreconnectToSearch,PreloadingEagerHeuristics,SafetyHub,SegmentationPlatform,ServiceWorkerAutoPreload,SpareRendererForSitePerProcess,Ukm,WebPayments,msAITrackerClassification,msAbydosForWindowlessWV2,msAffirmVirtualCard,msAllowChromeWebstore,msAllowMSAPrtSSOForNonMSAProfile,msApplicationGuard,msAskBeforeClosingMultipleTabs,msAutoToggleAADPrtSSOForNonAADProfile,msAutofillEdgeServiceRequest,msAutofillEnableEdgeSuggestions,msAutomaticTabFreeze,msBrowserSettingsSupported,msCoarseGeolocationService,msDataProtection,msDesktopMode,msDesktopRewards,msDisableVariationsSeedFetchThrottling,msEEProactiveHistory,msETFOffstoreExtensionFileDataCollection,msETFPasswordTheftDNRActionSignals,msEdgeAdPlatformUI,msEdgeAddWebCapturetoCollections,msEdgeAutofillShowDeployedPassword,msEdgeCaptureSelectionInPDF,msEdgeCloudConfigService,msEdgeCloudConfigServiceV2,msEdgeCohorts,msEdgeCollectionsPrismExperiment1,msEdgeCollectionsPrismOverallMigration,msEdgeComposeNext,msEdgeEnableNurturingFramework,msEdgeEnclavePrefsBasic,msEdgeEnclavePrefsNotification,msEdgeFaviconService,msEdgeHJTelemetry,msEdgeHubAppSkype,msEdgeImageEditorUI,msEdgeLinkDoctor,msEdgeMouseGestureDefaultEnabled,msEdgeMouseGestureSupported,msEdgeNewDeviceFre,msEdgeOnRampFRE,msEdgeOnRampImport,msEdgePDFCMHighlightUX,msEdgePasswordIris,msEdgePasswordIrisSaveBubble,msEdgePasswordStrengthCheck,msEdgePinpointFramework,msEdgeProngPersonalization,msEdgeReadingView,msEdgeRose,msEdgeScreenshotUI,msEdgeSendTabToSelf,msEdgeSettingsImport,msEdgeSettingsImportV2,msEdgeShoppingPersistentStorage,msEdgeShoppingUI,msEdgeSmartFind,msEdgeSuperDragDefaultEnabled,msEdgeSuperDragDropSupported,msEdgeTranslate,msEdgeUpdatesMoreMenuPill,msEdgeWebCapture,msEdgeWebCaptureUniformExperience,msEdgeWebContentFilteringFeedback,msEdgeWorkSearchBanner,msEnableCustomJobMemoryLimitsOnXbox,msEnableMIPForPDF,msEnablePdfUpsell,msEnableThirdPartyScanning,msEnableWebSignInCta,msEnableWebToBrowserSignIn,msEndpointDlp,msEntityExtraction,msExtensionTelemetryFramework,msExternalTaskManager,msFileSystemAccessDirectoryIterationBlocklistCheck,msForceBrowserSignIn,msForeignSessionsPage,msGeolocationAccessService,msGeolocationOSLocationPermissionFallback,msGeolocationSQMService,msGeolocationService,msGrowthInfraLaunchSourceLogging,msGuidedSwitchAllowed,msHubPinPersist,msImplicitSignin,msIrm,msIrmv2,msKlarnaVirtualCard,msLlmConsumerDlpPurview,msLoadStatistics,msLogIsEdgePinnedToTaskbarOnLaunch,msMIPCrossTenantPdfViewSupport,msMdatpWebSiteDlp,msNotificationPermissionForPWA,msNumberOfSitesToPin,msNurturingGlobalSitePinningOnCloseModal,msNurturingSitePinningCITopSites,msNurturingSitePinningWithWindowsConsent,msOnHoverSearchInSidebar,msOpenOfficeDocumentsInWebViewer,msPageInteractionRestrictionRevoke,msPasswordBreachDetection,msPdfAnnotationsVisibility,msPdfDataRecovery,msPdfDigitalSignatureRead,msPdfFreeText,msPdfFreeTextForCJK,msPdfHighlightMode,msPdfInking,msPdfKeyphraseSupport,msPdfOOUI,msPdfPopupMarkerRenderer,msPdfShare,msPdfSharedLibrary,msPdfTextNote,msPdfTextNoteMoreMenu,msPdfThumbnailCache,msPdfUnderside,msPdfViewRestore,msPersonalizationUMA,msPriceComparison,msPromptDefaultHandlerForPDF,msReactiveSearch,msReadAloud,msReadAloudPdf,msRedirectToShoreline,msRevokeExtensions,msSaasDlp,msShoppingTrigger,msShorelineSearch,msShorelineSearchFindOnPageWebUI,msShowOfflineGameEntrance,msShowReadAloudIconInAddressBar,msShowUXForAADPrtSSOForNonAADProfile,msSitePinningWithoutUi,msSmartScreenProtection,msSuspendMessageForNewSessionWhenHavingPendingNavigation,msSyncEdgeCollections,msTabResourceStats,msTokenizationAutofillInlineEnabled,msTouchMode,msTriggeringSignalGenerator,msUserUnderstanding,msVideoSuperResolutionUI,msWalletBuyNow,msWalletCheckout,msWalletDiagnosticDataLogger,msWalletHubEntry,msWalletHubIntlP3,msWalletPartialCard,msWalletPasswordCategorization,msWalletPasswordCategorizationPlatformExpansion,msWalletTokenizationCardMetadata,msWalletTokenizedAutofill,msWebAssist,msWebAssistHistorySearchService,msWebOOUI,msWindowsUserActivities,msZipPayVirtualCard --variations-seed-version --trace-process-track-uuid=3190708990997080739 --mojo-platform-channel-handle=3584 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\142.0.3595.94\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Version: 142.0.3595.94 Modules
| |||||||||||||||
| 3320 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\142.0.3595.94\msedgewebview2.exe" --type=gpu-process --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Roaming\SpotiFLAC.exe\EBWebView" --webview-exe-name=SpotiFLAC.exe --webview-exe-version=6.4 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --no-pre-read-main-dll --force-high-res-timeticks=disabled --gpu-preferences=SAAAAAAAAADgAAAEAAAAAAAAAAAAAGAAAQAAAAAAAAAAAAAAAAAAAAIAAAAAAAAAAAAAAAAAAAAQAAAAAAAAABAAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --startup-read-main-dll --metrics-shmem-handle=1752,i,10078971185185506047,3749491437685298532,262144 --field-trial-handle=1912,i,5188261680952606124,1721952684639490544,262144 --enable-features=ForceSWDCompWhenDCompFallbackRequired,LocalNetworkAccessForFencedFrameNavigationsWarningOnly,LocalNetworkAccessForNavigationsWarningOnly,LocalNetworkAccessForSubframeNavigationsWarningOnly,LocalNetworkAccessForWorkersWarningOnly,msAggressiveCacheTrimming,msCustomDataPartition,msWebView2NoTabForScreenShare,msWindowsTaskManager --disable-features=BackForwardCache,BackgroundTabLoadingFromPerformanceManager,CloseOmniboxPopupOnInactiveAreaClick,CollectAVProductsInfo,CollectCodeIntegrityInfo,DeferSpeculativeRFHCreation,EnableHangWatcher,FilterAdsOnAbusiveSites,GetWifiProtocol,LoginDetection,MediaFoundationCameraUsageMonitoring,PreconnectToSearch,PreloadingEagerHeuristics,SafetyHub,SegmentationPlatform,ServiceWorkerAutoPreload,SpareRendererForSitePerProcess,Ukm,WebPayments,msAITrackerClassification,msAbydosForWindowlessWV2,msAffirmVirtualCard,msAllowChromeWebstore,msAllowMSAPrtSSOForNonMSAProfile,msApplicationGuard,msAskBeforeClosingMultipleTabs,msAutoToggleAADPrtSSOForNonAADProfile,msAutofillEdgeServiceRequest,msAutofillEnableEdgeSuggestions,msAutomaticTabFreeze,msBrowserSettingsSupported,msCoarseGeolocationService,msDataProtection,msDesktopMode,msDesktopRewards,msDisableVariationsSeedFetchThrottling,msEEProactiveHistory,msETFOffstoreExtensionFileDataCollection,msETFPasswordTheftDNRActionSignals,msEdgeAdPlatformUI,msEdgeAddWebCapturetoCollections,msEdgeAutofillShowDeployedPassword,msEdgeCaptureSelectionInPDF,msEdgeCloudConfigService,msEdgeCloudConfigServiceV2,msEdgeCohorts,msEdgeCollectionsPrismExperiment1,msEdgeCollectionsPrismOverallMigration,msEdgeComposeNext,msEdgeEnableNurturingFramework,msEdgeEnclavePrefsBasic,msEdgeEnclavePrefsNotification,msEdgeFaviconService,msEdgeHJTelemetry,msEdgeHubAppSkype,msEdgeImageEditorUI,msEdgeLinkDoctor,msEdgeMouseGestureDefaultEnabled,msEdgeMouseGestureSupported,msEdgeNewDeviceFre,msEdgeOnRampFRE,msEdgeOnRampImport,msEdgePDFCMHighlightUX,msEdgePasswordIris,msEdgePasswordIrisSaveBubble,msEdgePasswordStrengthCheck,msEdgePinpointFramework,msEdgeProngPersonalization,msEdgeReadingView,msEdgeRose,msEdgeScreenshotUI,msEdgeSendTabToSelf,msEdgeSettingsImport,msEdgeSettingsImportV2,msEdgeShoppingPersistentStorage,msEdgeShoppingUI,msEdgeSmartFind,msEdgeSuperDragDefaultEnabled,msEdgeSuperDragDropSupported,msEdgeTranslate,msEdgeUpdatesMoreMenuPill,msEdgeWebCapture,msEdgeWebCaptureUniformExperience,msEdgeWebContentFilteringFeedback,msEdgeWorkSearchBanner,msEnableCustomJobMemoryLimitsOnXbox,msEnableMIPForPDF,msEnablePdfUpsell,msEnableThirdPartyScanning,msEnableWebSignInCta,msEnableWebToBrowserSignIn,msEndpointDlp,msEntityExtraction,msExtensionTelemetryFramework,msExternalTaskManager,msFileSystemAccessDirectoryIterationBlocklistCheck,msForceBrowserSignIn,msForeignSessionsPage,msGeolocationAccessService,msGeolocationOSLocationPermissionFallback,msGeolocationSQMService,msGeolocationService,msGrowthInfraLaunchSourceLogging,msGuidedSwitchAllowed,msHubPinPersist,msImplicitSignin,msIrm,msIrmv2,msKlarnaVirtualCard,msLlmConsumerDlpPurview,msLoadStatistics,msLogIsEdgePinnedToTaskbarOnLaunch,msMIPCrossTenantPdfViewSupport,msMdatpWebSiteDlp,msNotificationPermissionForPWA,msNumberOfSitesToPin,msNurturingGlobalSitePinningOnCloseModal,msNurturingSitePinningCITopSites,msNurturingSitePinningWithWindowsConsent,msOnHoverSearchInSidebar,msOpenOfficeDocumentsInWebViewer,msPageInteractionRestrictionRevoke,msPasswordBreachDetection,msPdfAnnotationsVisibility,msPdfDataRecovery,msPdfDigitalSignatureRead,msPdfFreeText,msPdfFreeTextForCJK,msPdfHighlightMode,msPdfInking,msPdfKeyphraseSupport,msPdfOOUI,msPdfPopupMarkerRenderer,msPdfShare,msPdfSharedLibrary,msPdfTextNote,msPdfTextNoteMoreMenu,msPdfThumbnailCache,msPdfUnderside,msPdfViewRestore,msPersonalizationUMA,msPriceComparison,msPromptDefaultHandlerForPDF,msReactiveSearch,msReadAloud,msReadAloudPdf,msRedirectToShoreline,msRevokeExtensions,msSaasDlp,msShoppingTrigger,msShorelineSearch,msShorelineSearchFindOnPageWebUI,msShowOfflineGameEntrance,msShowReadAloudIconInAddressBar,msShowUXForAADPrtSSOForNonAADProfile,msSitePinningWithoutUi,msSmartScreenProtection,msSuspendMessageForNewSessionWhenHavingPendingNavigation,msSyncEdgeCollections,msTabResourceStats,msTokenizationAutofillInlineEnabled,msTouchMode,msTriggeringSignalGenerator,msUserUnderstanding,msVideoSuperResolutionUI,msWalletBuyNow,msWalletCheckout,msWalletDiagnosticDataLogger,msWalletHubEntry,msWalletHubIntlP3,msWalletPartialCard,msWalletPasswordCategorization,msWalletPasswordCategorizationPlatformExpansion,msWalletTokenizationCardMetadata,msWalletTokenizedAutofill,msWebAssist,msWebAssistHistorySearchService,msWebOOUI,msWindowsUserActivities,msZipPayVirtualCard --variations-seed-version --trace-process-track-uuid=3190708988185955192 --mojo-platform-channel-handle=1908 /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\142.0.3595.94\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Version: 142.0.3595.94 Modules
| |||||||||||||||
| 4048 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\142.0.3595.94\msedgewebview2.exe --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Roaming\SpotiFLAC.exe\EBWebView /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Roaming\SpotiFLAC.exe\EBWebView\Crashpad --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=142.0.7444.176 --annotation=exe=C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\142.0.3595.94\msedgewebview2.exe --annotation=plat=Win64 "--annotation=prod=Edge WebView2" --annotation=ver=142.0.3595.94 --initial-client-data=0x1a0,0x1a4,0x1a8,0x44,0x1b0,0x7fff77ebdb58,0x7fff77ebdb64,0x7fff77ebdb70 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\142.0.3595.94\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 142.0.3595.94 Modules
| |||||||||||||||
Total events
14 906
Read events
13 392
Write events
1 447
Delete events
67
Modification events
| (PID) Process: | (2692) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate |
| Operation: | delete value | Name: | eulaaccepted |
Value: | |||
| (PID) Process: | (6636) MicrosoftEdgeUpdate.exe | Key: | HKEY_CLASSES_ROOT\WOW6432Node\CLSID\{81093D63-7825-417B-BFC8-ADC63FA4E53D}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6636) MicrosoftEdgeUpdate.exe | Key: | HKEY_CLASSES_ROOT\WOW6432Node\CLSID\{5EA43877-C6D8-4885-B77A-C0BB27E94372}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6636) MicrosoftEdgeUpdate.exe | Key: | HKEY_CLASSES_ROOT\WOW6432Node\CLSID\{C653F8DD-ADDC-4230-9528-E4EBC22166DF}\InprocHandler32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6636) MicrosoftEdgeUpdate.exe | Key: | HKEY_CLASSES_ROOT\WOW6432Node\CLSID\{2B49DB21-41C5-44C0-8358-CA4C76205AE1}\InProcServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6384) MicrosoftEdgeUpdateComRegisterShell64.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{C653F8DD-ADDC-4230-9528-E4EBC22166DF} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6384) MicrosoftEdgeUpdateComRegisterShell64.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{C653F8DD-ADDC-4230-9528-E4EBC22166DF}\InprocHandler32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6384) MicrosoftEdgeUpdateComRegisterShell64.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{2B49DB21-41C5-44C0-8358-CA4C76205AE1}\InProcServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (6636) MicrosoftEdgeUpdate.exe | Key: | HKEY_CLASSES_ROOT\WOW6432Node\CLSID\{81093D63-7825-417B-BFC8-ADC63FA4E53D}\InprocServer32 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6636) MicrosoftEdgeUpdate.exe | Key: | HKEY_CLASSES_ROOT\WOW6432Node\CLSID\{81093D63-7825-417B-BFC8-ADC63FA4E53D} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
213
Suspicious files
88
Text files
28
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6548 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EU3482.tmp\MicrosoftEdgeUpdateBroker.exe | executable | |
MD5:51028ACF1DBADCD215385965794F52BD | SHA256:4EE54B8B3BF71FE302BFF5BD908459CCACA44F79C16CCA79F0FE845624C806CE | |||
| 6548 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EU3482.tmp\MicrosoftEdgeUpdate.exe | executable | |
MD5:80306EB362C63D6A63F443A3B2B84EDF | SHA256:B0585142D771FD68F0F939B925E4D32B491CD097350131F8F5C006EB8B2B0397 | |||
| 6548 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EU3482.tmp\MicrosoftEdgeUpdateOnDemand.exe | executable | |
MD5:5FE168ED4E95D490C050411EA04CD06F | SHA256:D0CB5C16470768BD2AE58D9402E8A76A248F4A8467113CBDC3284485D32561AE | |||
| 6548 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EU3482.tmp\MicrosoftEdgeComRegisterShellARM64.exe | executable | |
MD5:CBCA9B8FDCC0BCCE46F7EFCAD2B6EDBA | SHA256:DBACCFA5A06797A8B3E79A9FD19C843929BDE0B7BECF9DE5EB9C15530E7BA8C5 | |||
| 4164 | SpotiFLAC.exe | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | executable | |
MD5:A04BB992DA078E60D91B8182B30CB6BC | SHA256:895980D55492E464FDDD307362E09FA8B36E3322C7414E93A90EEE6AA25F86B4 | |||
| 6548 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EU3482.tmp\CopilotUpdate.exe | executable | |
MD5:87ECDE862DF8E36C8161FFBE44710EB2 | SHA256:763B4D26DC3E5A71A588DB35C1C767E895F80EFE44259820D7617837D24CDC32 | |||
| 6548 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EU3482.tmp\psmachine_64.dll | executable | |
MD5:35270DAEC45836DE4BA868FD0076A0A9 | SHA256:B024E4727C9BA84505CB52CF4AC54F131C1DFECDF44B9E4CE045132826D27DFE | |||
| 6548 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EU3482.tmp\msedgeupdate.dll | executable | |
MD5:515E4B08BDBDA42B874DC631D564A264 | SHA256:0FAC97BED931585843754582E784BE1A7635A2DFC15B020714DF03966D738511 | |||
| 6548 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EU3482.tmp\MicrosoftEdgeUpdateComRegisterShell64.exe | executable | |
MD5:165C4AF6BABB29E4E40DBF927B2F8334 | SHA256:5E75A942899E3577EB7635BD567F2481F968BFC8977A6A3A49CEE87296D4DC6A | |||
| 6548 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EU3482.tmp\psmachine_arm64.dll | executable | |
MD5:772AAB8A267718A53478428893133A92 | SHA256:8694839DCB266D44CC4DD08E555A207D4AEB90E659D4C802EF27CC2D00AE97D1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
36
DNS requests
28
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2348 | svchost.exe | GET | 200 | 23.216.77.13:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5456 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/003922a9-6846-48e1-b864-200ee31fda79?P1=1764966298&P2=404&P3=2&P4=Mvt5EP5Ge%2br7XN6czHdeXI2UNALNo5GIpS%2bJa1I6IXFqR08DrqorfQ4dh0M%2beKGe8dtC5oPRMOuzU6xUwZltxw%3d%3d | US | — | — | whitelisted |
6640 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6524 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | US | binary | 408 b | whitelisted |
6524 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | US | binary | 419 b | whitelisted |
6524 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | US | binary | 813 b | whitelisted |
6524 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
6524 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | NL | binary | 824 b | whitelisted |
6524 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | US | binary | 813 b | whitelisted |
6524 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | US | binary | 402 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
2348 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5912 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5596 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4164 | SpotiFLAC.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
4164 | SpotiFLAC.exe | 2.16.168.116:443 | msedge.sf.dl.delivery.mp.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
4092 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4324 | MicrosoftEdgeUpdate.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6640 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
msedge.sf.dl.delivery.mp.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
msedge.api.cdp.microsoft.com |
| whitelisted |
msedge.f.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5456 | svchost.exe | Misc activity | ET INFO Packed Executable Download |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming directory exists )
|
SpotiFLAC.exe | Warning: AddWebResourceRequestedFilter without SourceKind parameter is deprecated! It does not behave as expected for iframes.Please use AddWebResourceRequestedFilterWithRequestSourceKinds instead. For more information, please see https://go.microsoft.com/fwlink/?linkid=2286319 |