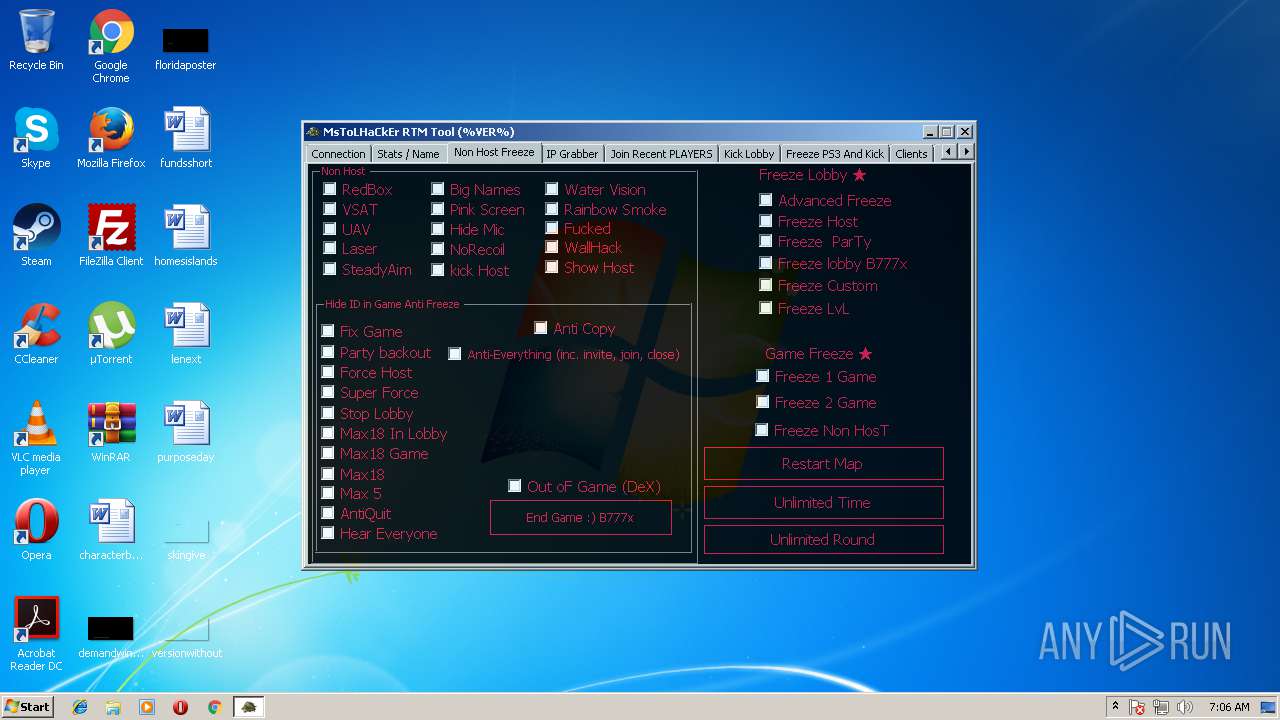
| File name: | RTM TooL By MsToL683H Cracked By DR3MJY.exe |
| Full analysis: | https://app.any.run/tasks/d76c4e31-18f3-4da3-9d03-f939c8b382c9 |
| Verdict: | No threats detected |
| Analysis date: | July 22, 2018, 06:05:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D5ADEBA06CCC4CAF5AD24BB9B7F9A595 |
| SHA1: | 70EC18EF50F000FA740A7E31CA4610427E324F7E |
| SHA256: | E4D4370EB67B78F95575EFB4CC3E20C57A0E7D15D0C44D01D5BAFE3F0824D127 |
| SSDEEP: | 49152:Rqd1wu077X2/6TmEqc2mHiljdQzbAuZ0jhrbxQfOfacw52:Rq0u0fmWTqcYjSZSNxQcZ |
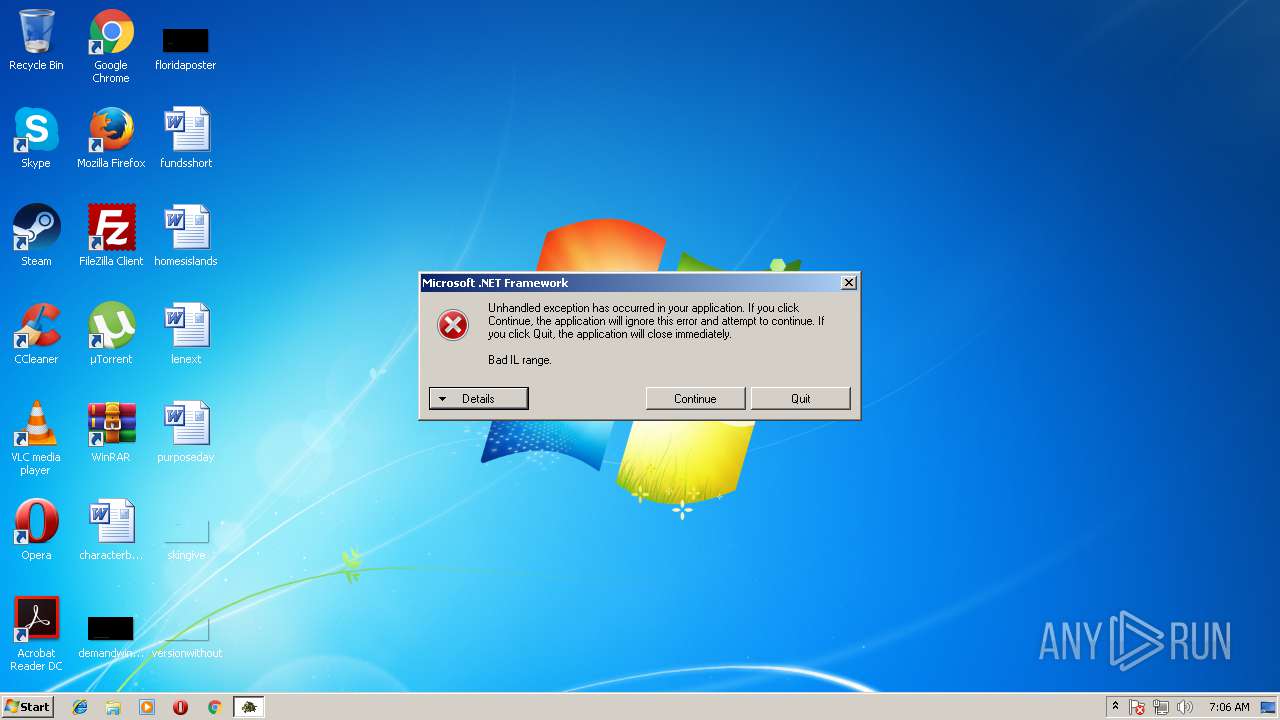
MALICIOUS
Loads dropped or rewritten executable
- RTM TooL By MsToL683H Cracked By DR3MJY.exe (PID: 3524)
Application was dropped or rewritten from another process
- RTM TooL By MsToL683H Cracked By DR3MJY.exe (PID: 3524)
SUSPICIOUS
Executable content was dropped or overwritten
- RTM TooL By MsToL683H Cracked By DR3MJY.exe (PID: 3268)
- RTM TooL By MsToL683H Cracked By DR3MJY.exe (PID: 3524)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 6 (85.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (4.6) |
| .scr | | | Windows screen saver (4.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.1) |
| .exe | | | Win32 Executable (generic) (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 29696 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x80e4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000722C | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51167 |
DATA | 0x00009000 | 0x00000218 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.1517 |
BSS | 0x0000A000 | 0x0000A899 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00015000 | 0x00000864 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.17386 |
.tls | 0x00016000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00017000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x00018000 | 0x000005CC | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.44309 |
.rsrc | 0x00019000 | 0x00001400 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.06319 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.5335 | 4264 | UNKNOWN | Russian - Russia | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 6.90278 | 172 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 1.7815 | 20 | UNKNOWN | Russian - Russia | RT_GROUP_ICON |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
32
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3268 | "C:\Users\admin\AppData\Local\Temp\RTM TooL By MsToL683H Cracked By DR3MJY.exe" | C:\Users\admin\AppData\Local\Temp\RTM TooL By MsToL683H Cracked By DR3MJY.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
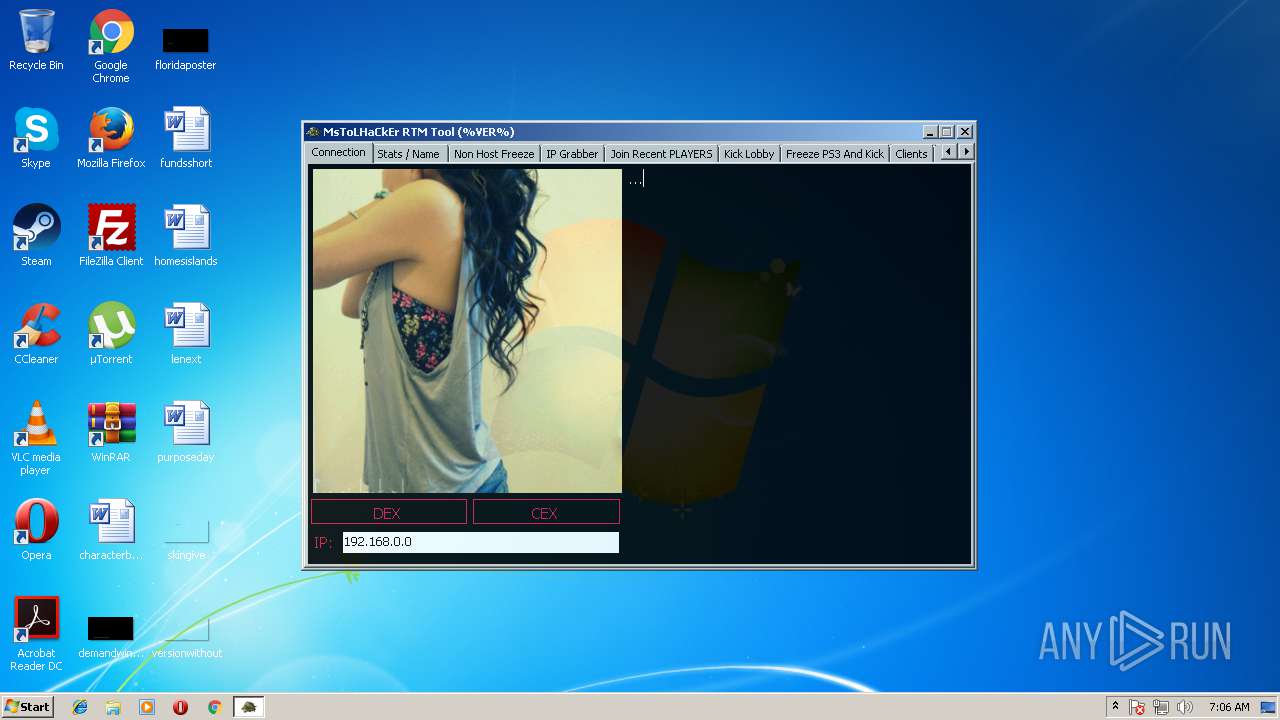
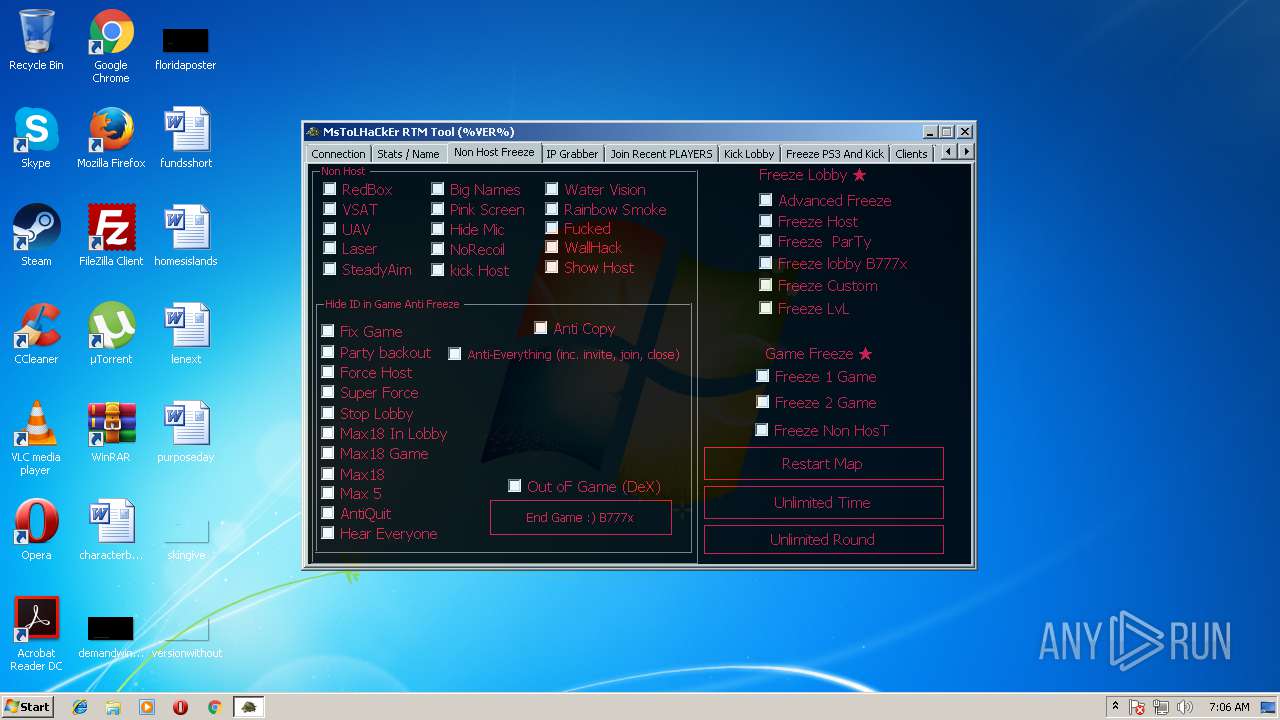
| 3524 | "C:\Users\admin\AppData\Local\Temp\3582-490\RTM TooL By MsToL683H Cracked By DR3MJY.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\RTM TooL By MsToL683H Cracked By DR3MJY.exe | RTM TooL By MsToL683H Cracked By DR3MJY.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
338
Read events
334
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3268) RTM TooL By MsToL683H Cracked By DR3MJY.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3268) RTM TooL By MsToL683H Cracked By DR3MJY.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
5
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3268 | RTM TooL By MsToL683H Cracked By DR3MJY.exe | C:\Users\admin\AppData\Roaming\uTorrent\updates\3.5.1_44332\utorrentie.exe | — | |
MD5:— | SHA256:— | |||
| 3268 | RTM TooL By MsToL683H Cracked By DR3MJY.exe | C:\Users\admin\AppData\Roaming\uTorrent\updates\3.5.3_44494.exe萏 | — | |
MD5:— | SHA256:— | |||
| 3268 | RTM TooL By MsToL683H Cracked By DR3MJY.exe | C:\Users\admin\Downloads\FileZilla_3.34.0_win32-setup.exe캋帢諺ꥰ薓ೄ | — | |
MD5:— | SHA256:— | |||
| 3268 | RTM TooL By MsToL683H Cracked By DR3MJY.exe | C:\Users\admin\AppData\Local\Temp\3582-490\RTM TooL By MsToL683H Cracked By DR3MJY.exe | executable | |
MD5:14E1CB0AA6884F96FA8312660D0654E0 | SHA256:C1D059A7AB8DFC4C656BCC49594F9EB7B1937D24790C7101257A0AC25E52B2F8 | |||
| 3268 | RTM TooL By MsToL683H Cracked By DR3MJY.exe | C:\Users\admin\AppData\Local\Temp\tmp5023.tmp | binary | |
MD5:61C877C88919AD93F9DCC4792ADA2C20 | SHA256:9E1D48F9C0DF9801F71EA44423967FC73158934EBD76BC5080CD2043F3F53EAF | |||
| 3268 | RTM TooL By MsToL683H Cracked By DR3MJY.exe | C:\Users\admin\AppData\Roaming\uTorrent\updates\3.5.1_44332.exe | executable | |
MD5:FD13EEF2F4A7B7EFC83BCAED9F0E3AEE | SHA256:CA112A3297DD17F9370F54170E9BFE39F1DCDAC48AA5D992B59B8A0D4A25E626 | |||
| 3268 | RTM TooL By MsToL683H Cracked By DR3MJY.exe | C:\Users\admin\AppData\Roaming\uTorrent\uTorrent.exe | executable | |
MD5:FD13EEF2F4A7B7EFC83BCAED9F0E3AEE | SHA256:CA112A3297DD17F9370F54170E9BFE39F1DCDAC48AA5D992B59B8A0D4A25E626 | |||
| 3524 | RTM TooL By MsToL683H Cracked By DR3MJY.exe | C:\Users\admin\AppData\Local\MsToLHaCkEr_RTM_Tool\CCAPI.dll | executable | |
MD5:C2FE9E1C387CF29AAC781482C28ECF86 | SHA256:770F65563BC6E2D6B5F3B86EDD655B4F591216CD2F0746A947538546293D86AA | |||
| 3524 | RTM TooL By MsToL683H Cracked By DR3MJY.exe | C:\Users\admin\AppData\Local\MsToLHaCkEr_RTM_Tool\TMAPI.dll | executable | |
MD5:CB3E54453E86E1FB83C6148424511595 | SHA256:7B6B2DA221CDE97B781CADCA6F327D2A9342096C7790651000984FD40B6184C3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report