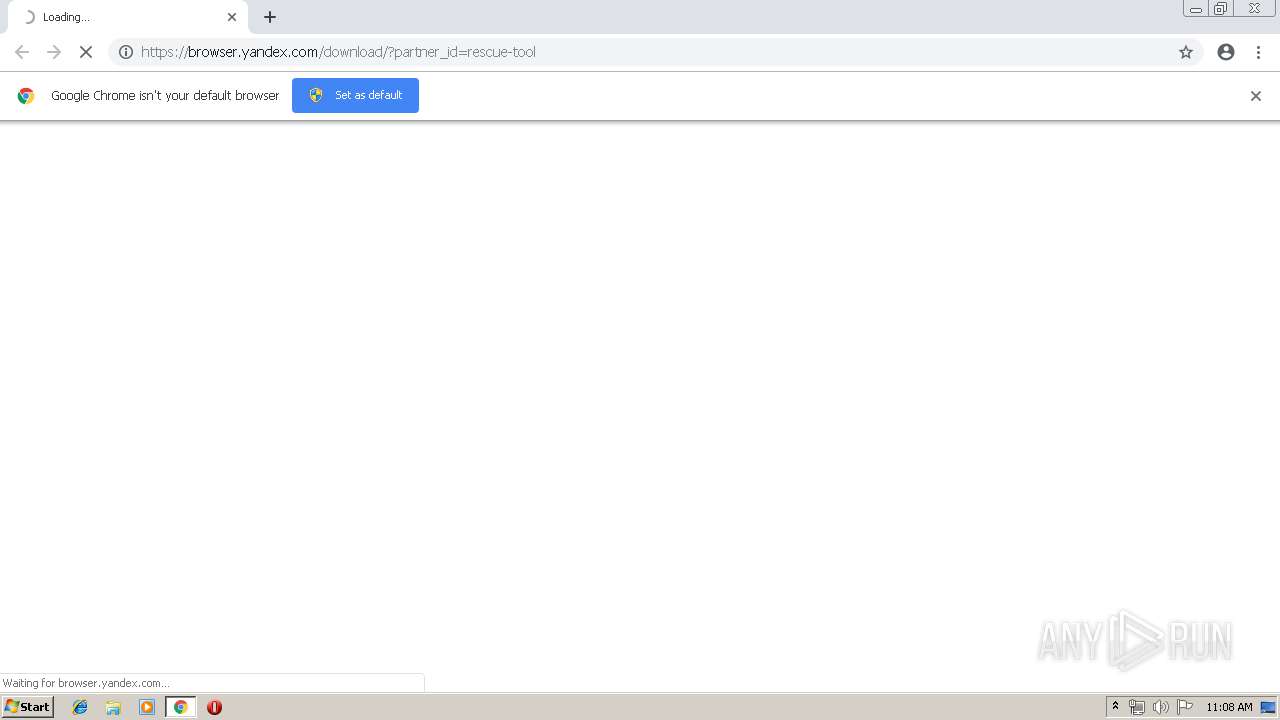
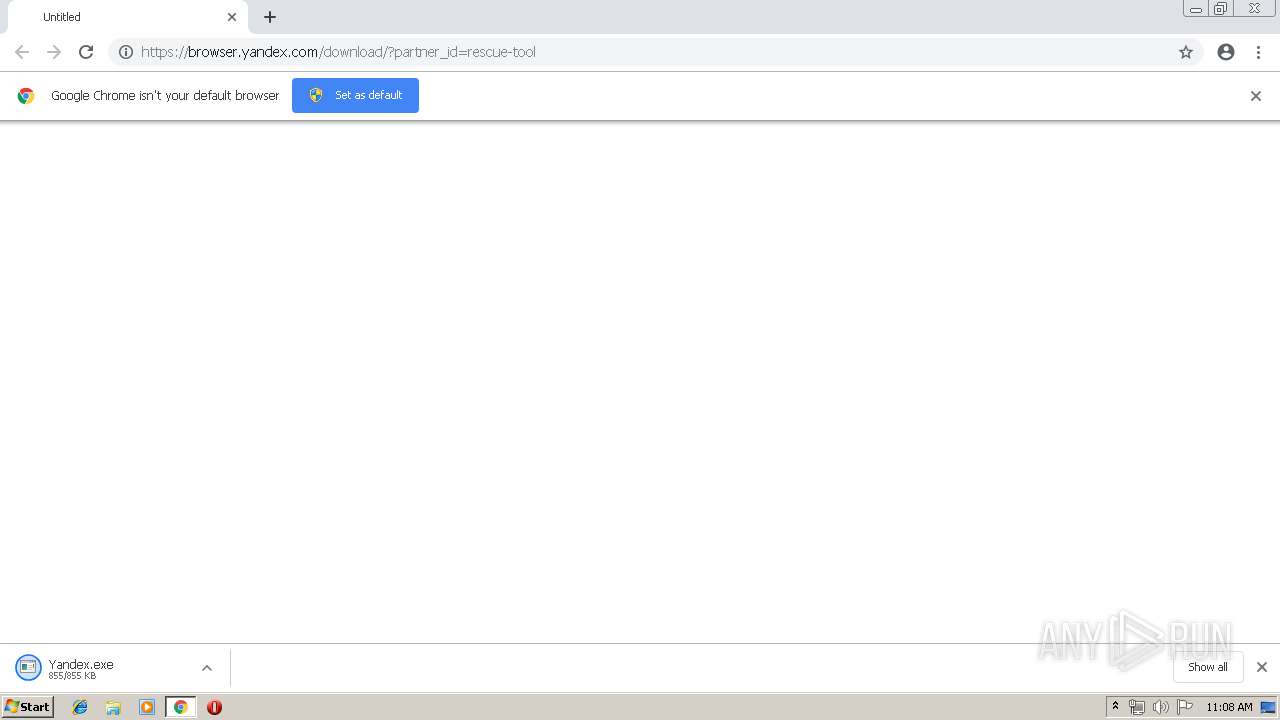
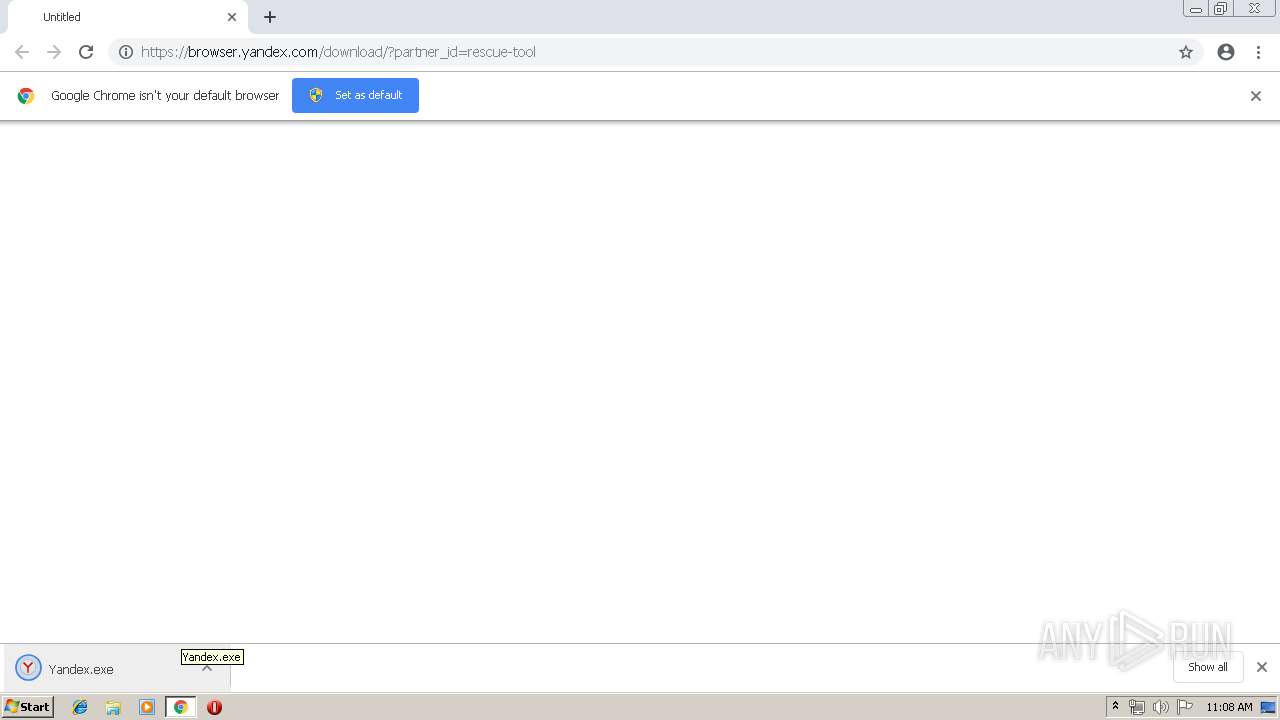
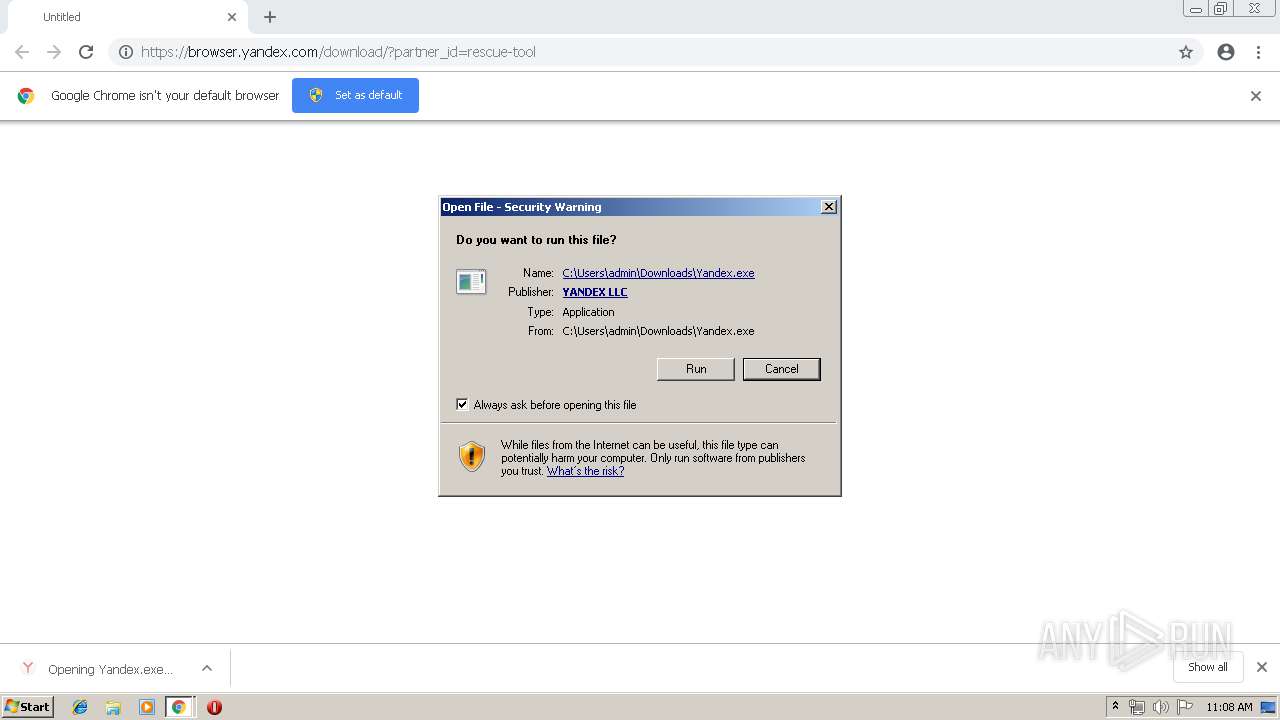
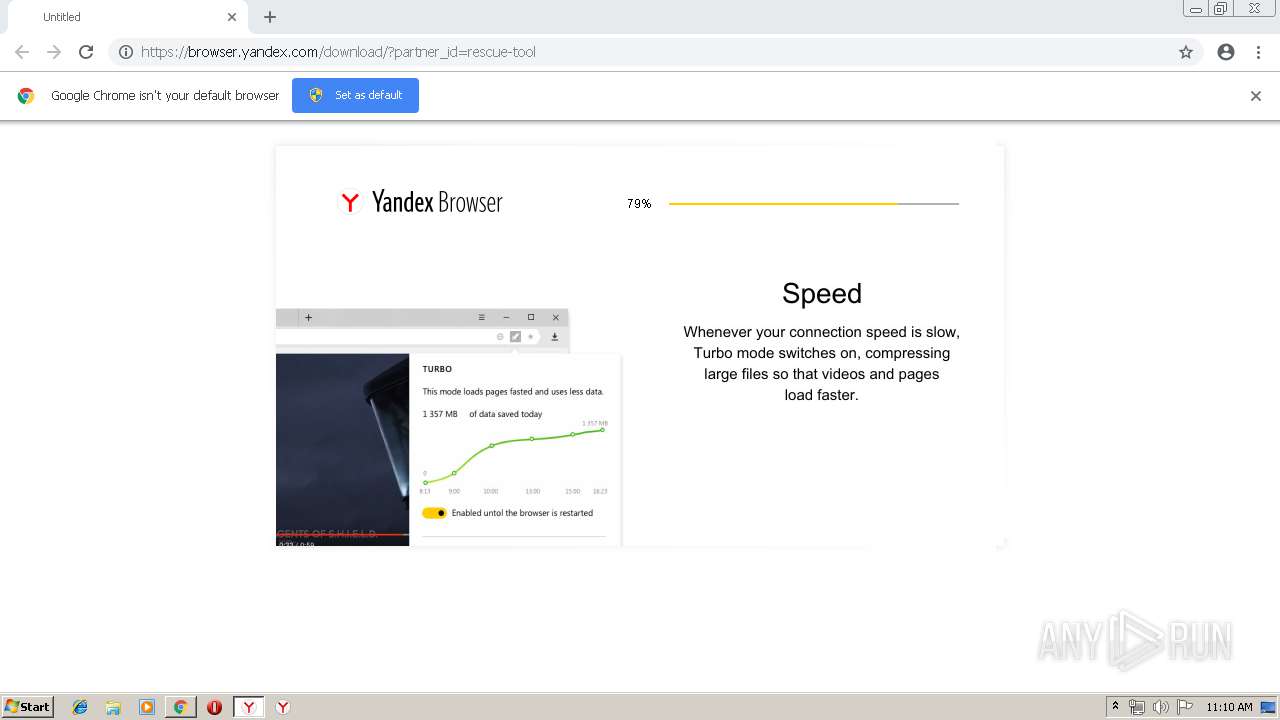
| URL: | https://browser.yandex.com/download/?partner_id=rescue-tool |
| Full analysis: | https://app.any.run/tasks/fd37a22b-65c8-4b5b-b528-3eb4e511707e |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2019, 10:08:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CDB9484D48835EFADE6287796ED1A77B |
| SHA1: | 4C22CFA3B49337C568D8007819FDB2B412A7EDC5 |
| SHA256: | E4CB0DD56B381F103651AA83BDEC5AB4650BF3CC9742C4105FEFC97FDAEB342F |
| SSDEEP: | 3:N8UcoiSKLaYAPZKJn:204ubRS |
MALICIOUS
Application was dropped or rewritten from another process
- Yandex.exe (PID: 3392)
- setup.exe (PID: 920)
- Yandex.exe (PID: 3380)
- setup.exe (PID: 3272)
- setup.exe (PID: 2672)
- Yandex.exe (PID: 2304)
- service_update.exe (PID: 2600)
- service_update.exe (PID: 2080)
- service_update.exe (PID: 1076)
- service_update.exe (PID: 1668)
- service_update.exe (PID: 2756)
- service_update.exe (PID: 2416)
- clidmgr.exe (PID: 3180)
- clidmgr.exe (PID: 3948)
- service_update.exe (PID: 3924)
- clidmgr.exe (PID: 1652)
- browser.exe (PID: 2676)
- browser.exe (PID: 2824)
- browser.exe (PID: 3796)
- clidmgr.exe (PID: 1548)
- service_update.exe (PID: 3216)
- browser.exe (PID: 3036)
- browser.exe (PID: 2612)
- browser.exe (PID: 2380)
- browser.exe (PID: 3948)
- browser.exe (PID: 2208)
- browser.exe (PID: 3400)
- browser.exe (PID: 1836)
- browser.exe (PID: 856)
- browser.exe (PID: 3628)
- browser.exe (PID: 2548)
- browser.exe (PID: 3696)
- browser.exe (PID: 300)
- browser.exe (PID: 3024)
- browser.exe (PID: 1348)
- browser.exe (PID: 2452)
- browser.exe (PID: 2580)
- browser.exe (PID: 3476)
- browser.exe (PID: 3880)
- browser.exe (PID: 3764)
- browser.exe (PID: 3484)
- browser.exe (PID: 2088)
Loads the Task Scheduler DLL interface
- service_update.exe (PID: 3216)
- service_update.exe (PID: 3924)
- browser.exe (PID: 2676)
Loads the Task Scheduler COM API
- service_update.exe (PID: 2080)
- browser.exe (PID: 2676)
Loads dropped or rewritten executable
- chrome.exe (PID: 3448)
- browser.exe (PID: 2676)
- browser.exe (PID: 2824)
- browser.exe (PID: 3036)
- browser.exe (PID: 2580)
- browser.exe (PID: 2612)
- browser.exe (PID: 2380)
- browser.exe (PID: 3948)
- browser.exe (PID: 2208)
- browser.exe (PID: 3764)
- browser.exe (PID: 3400)
- browser.exe (PID: 1836)
- browser.exe (PID: 856)
- browser.exe (PID: 2548)
- browser.exe (PID: 3628)
- browser.exe (PID: 3696)
- browser.exe (PID: 300)
- browser.exe (PID: 3796)
- browser.exe (PID: 3024)
- browser.exe (PID: 2452)
- browser.exe (PID: 1348)
- browser.exe (PID: 3476)
- browser.exe (PID: 3880)
- browser.exe (PID: 3484)
- browser.exe (PID: 2088)
Changes settings of System certificates
- setup.exe (PID: 2672)
Changes the autorun value in the registry
- browser.exe (PID: 2676)
Actions looks like stealing of personal data
- browser.exe (PID: 2676)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2220)
- Yandex.exe (PID: 2304)
- chrome.exe (PID: 2644)
- yb8A80.tmp (PID: 3788)
- setup.exe (PID: 2672)
- service_update.exe (PID: 2600)
- service_update.exe (PID: 1076)
Creates files in the user directory
- Yandex.exe (PID: 3380)
- setup.exe (PID: 2672)
- clidmgr.exe (PID: 3180)
- browser.exe (PID: 2676)
Starts itself from another location
- Yandex.exe (PID: 2304)
Starts application with an unusual extension
- Yandex.exe (PID: 3392)
Adds / modifies Windows certificates
- setup.exe (PID: 2672)
Application launched itself
- setup.exe (PID: 3272)
- Yandex.exe (PID: 3380)
- service_update.exe (PID: 1668)
- service_update.exe (PID: 3216)
- browser.exe (PID: 2676)
Modifies the open verb of a shell class
- setup.exe (PID: 2672)
Creates files in the Windows directory
- service_update.exe (PID: 1668)
- service_update.exe (PID: 3216)
- service_update.exe (PID: 3924)
- service_update.exe (PID: 2416)
Creates files in the program directory
- service_update.exe (PID: 1076)
Creates a software uninstall entry
- setup.exe (PID: 2672)
Removes files from Windows directory
- service_update.exe (PID: 2416)
- service_update.exe (PID: 1668)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2644)
Reads the cookies of Google Chrome
- browser.exe (PID: 3880)
INFO
Application launched itself
- chrome.exe (PID: 2644)
Reads settings of System Certificates
- Yandex.exe (PID: 3380)
- browser.exe (PID: 2676)
Dropped object may contain Bitcoin addresses
- setup.exe (PID: 2672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
100
Monitored processes
60
Malicious processes
17
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --type=renderer --field-trial-handle=916,3489589523307529204,13519851419163298957,131072 --js-flags="--no-enable-liveedit --no-untrusted-code-mitigations --stack-trace-limit=1" --disable-gpu-compositing --service-pipe-token=6773873210558658390 --lang=en-US --user-id=3766AA28-8BD7-42A4-8992-09BC2288084E --brand-id=int --help-url=https://api.browser.yandex.com/redirect/help/ --user-agent-info --translate-security-origin=https://yastatic.net --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-instaserp --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6773873210558658390 --renderer-client-id=15 --mojo-platform-channel-handle=4928 /prefetch:1 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: LOW Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fc80f18,0x6fc80f28,0x6fc80f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 856 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data\Crashpad" --url=https://crash-reports.browser.yandex.net/submit --annotation=install_date=1555236626 --annotation=machine_id=5f735395d68db0638bd0a2a58101e17a --annotation=main_process_pid=3628 --annotation=metrics_client_id=ae9fa067bca740af866f7bda88aa93cb --annotation=plat=Win32 --annotation=prod=Yandex --annotation=session_logout=False --annotation=ver=19.3.2.177 --initial-client-data=0xa4,0xac,0xb0,0xa0,0xb4,0x6d1b2270,0x6d1b2280,0x6d1b228c,0xa8 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 920 | C:\Users\admin\AppData\Local\Temp\YB_3C921.tmp\setup.exe --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data\Crashpad" --url=https://crash-reports.browser.yandex.net/submit --annotation=machine_id=5f735395d68db0638bd0a2a58101e17a --annotation=main_process_pid=2672 --annotation=plat=Win32 --annotation=prod=Yandex --annotation=session_logout=False --annotation=ver=19.3.2.177 --initial-client-data=0xfc,0x104,0x108,0xf8,0x10c,0x1039b00,0x1039b10,0x1039b1c,0x100 | C:\Users\admin\AppData\Local\Temp\YB_3C921.tmp\setup.exe | — | setup.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: HIGH Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 1076 | "C:\Users\admin\AppData\Local\Temp\2600_27818\service_update.exe" --setup --spawned_in_protected_dir | C:\Users\admin\AppData\Local\Temp\2600_27818\service_update.exe | service_update.exe | ||||||||||||
User: admin Company: YANDEX LLC Integrity Level: HIGH Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,13393198885379610823,10023244291737608231,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16937619042709707045 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16937619042709707045 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --broupdater-stat-bits --broupdater-stat-name=dayuse --bits_job_guid={BC3F1333-6E18-4A31-8DB5-979EC9FF25BF} | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | svchost.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 3221225547 Version: 19.3.2.177 Modules
| |||||||||||||||
| 1548 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\clidmgr.exe" --appid=searchband --vendor-xml-path="C:\Users\admin\AppData\Local\Temp\clids_searchband.xml" | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\clidmgr.exe | setup.exe | ||||||||||||
User: admin Company: Yandex Integrity Level: HIGH Description: ClidManagerModule Exit code: 4294967293 Version: 1,0,0,44 Modules
| |||||||||||||||
| 1652 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\clidmgr.exe" --appid=searchband --vendor-xml-path="C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Temp\source2672_7988\Browser-bin\clids_searchband.xml" | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\clidmgr.exe | setup.exe | ||||||||||||
User: admin Company: Yandex Integrity Level: HIGH Description: ClidManagerModule Exit code: 4294967291 Version: 1,0,0,44 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Yandex\YandexBrowser\19.3.2.177\service_update.exe" --run-as-service | C:\Program Files\Yandex\YandexBrowser\19.3.2.177\service_update.exe | services.exe | ||||||||||||
User: SYSTEM Company: YANDEX LLC Integrity Level: SYSTEM Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
Total events
3 740
Read events
3 081
Write events
640
Delete events
19
Modification events
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2644-13199710105489625 |
Value: 259 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
37
Suspicious files
460
Text files
837
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a139b7ef-61b3-45d7-8324-50fbb38c53b3.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
166
DNS requests
85
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3380 | Yandex.exe | GET | 200 | 104.18.20.226:80 | http://crl.globalsign.net/root.crl | US | der | 782 b | whitelisted |
3380 | Yandex.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkfDD%2F78IrsoD5b%2Bp1JR | US | der | 1.49 Kb | whitelisted |
2416 | service_update.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.62 Kb | whitelisted |
2416 | service_update.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEQDkBUeDDgxkUpdvejVJwN1I | US | der | 1.66 Kb | whitelisted |
1668 | service_update.exe | GET | 200 | 104.18.21.226:80 | http://crl.globalsign.com/gs/gstimestampingg2.crl | US | der | 905 b | whitelisted |
3380 | Yandex.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gscodesigng3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTHTu2Y6Nr%2FMkfa3PrlxnwonnIpxQQUs9Pm1XFWfTlYs3jSK7j3oR%2F9S5sCDGUxOJI7m%2BYpSWV%2FXQ%3D%3D | US | der | 1.50 Kb | whitelisted |
3380 | Yandex.exe | GET | 200 | 104.18.21.226:80 | http://crl.globalsign.com/gs/gstimestampingg2.crl | US | der | 905 b | whitelisted |
1668 | service_update.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gscodesigng3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTHTu2Y6Nr%2FMkfa3PrlxnwonnIpxQQUs9Pm1XFWfTlYs3jSK7j3oR%2F9S5sCDGUxOJI7m%2BYpSWV%2FXQ%3D%3D | US | der | 1.50 Kb | whitelisted |
2220 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
2220 | chrome.exe | GET | 200 | 173.194.182.138:80 | http://r5---sn-hpa7znsz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.26.195&mm=28&mn=sn-hpa7znsz&ms=nvh&mt=1555236634&mv=m&pl=25&shardbypass=yes | US | crx | 842 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2220 | chrome.exe | 87.250.250.237:443 | browser.yandex.com | YANDEX LLC | RU | whitelisted |
2220 | chrome.exe | 5.45.205.242:443 | download.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
2220 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 172.217.16.142:443 | clients4.google.com | Google Inc. | US | whitelisted |
2220 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3380 | Yandex.exe | 5.45.205.245:443 | download.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
2220 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3380 | Yandex.exe | 5.45.205.221:443 | cache-default99i.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3380 | Yandex.exe | 87.250.250.82:443 | api.browser.yandex.net | YANDEX LLC | RU | whitelisted |
3380 | Yandex.exe | 37.140.166.229:443 | cache-default05h.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
browser.yandex.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
download.cdn.yandex.net |
| whitelisted |
cache-default04h.cdn.yandex.net |
| whitelisted |
clients4.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
api.browser.yandex.net |
| whitelisted |
api.browser.yandex.ru |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3380 | Yandex.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
Process | Message |
|---|---|
clidmgr.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|
clidmgr.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|
clidmgr.exe | GetSidFromEnumSess(): ProfileImagePath(1) = C:\Users\admin
|
clidmgr.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = S-1-5-21-1302019708-1500728564-335382590-1000
|
clidmgr.exe | GetLoggedCreds_WTSSessionInfo(): szUserName = admin, szDomain = USER-PC, dwSessionId = 1
|
clidmgr.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|
clidmgr.exe | GetSidFromEnumSess(): ProfileImagePath(1) = C:\Users\admin
|
clidmgr.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = S-1-5-21-1302019708-1500728564-335382590-1000
|
clidmgr.exe | GetLoggedCreds_WTSSessionInfo(): szUserName = admin, szDomain = USER-PC, dwSessionId = 1
|
clidmgr.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|