| File name: | SAB4.0.bat |
| Full analysis: | https://app.any.run/tasks/17e05e0a-eeb6-4fd3-a7da-0224812ba6b6 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | June 21, 2025, 08:59:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 3BD308E6323FAE028E5EAD4AC2DB9B87 |
| SHA1: | A434403503219114E5B3A2607F23713D1C18C0DD |
| SHA256: | E4B92757DD9267E07F228888D1B5D425CEDF99D6837D70B129AF69E615C52156 |
| SSDEEP: | 96:nQI8rib8wDIH5E8+aWkBxtvxaNWHvEqJ0IEXvEgR:nQIqCIHvnWkBvYNWHvxuDXcgR |
MALICIOUS
Disables task manager
- reg.exe (PID: 5456)
- reg.exe (PID: 22028)
- reg.exe (PID: 18916)
- reg.exe (PID: 22436)
- reg.exe (PID: 22444)
- reg.exe (PID: 22456)
- reg.exe (PID: 15708)
- reg.exe (PID: 20676)
- reg.exe (PID: 22352)
- reg.exe (PID: 13876)
- reg.exe (PID: 10552)
- reg.exe (PID: 8548)
- reg.exe (PID: 10784)
- reg.exe (PID: 8792)
- reg.exe (PID: 17116)
- reg.exe (PID: 19928)
- reg.exe (PID: 8324)
- reg.exe (PID: 12612)
- reg.exe (PID: 436)
- reg.exe (PID: 14892)
- reg.exe (PID: 9824)
- reg.exe (PID: 14856)
- reg.exe (PID: 9380)
- reg.exe (PID: 21256)
- reg.exe (PID: 10044)
- reg.exe (PID: 14560)
- reg.exe (PID: 13764)
- reg.exe (PID: 14920)
- reg.exe (PID: 15672)
- reg.exe (PID: 17940)
- reg.exe (PID: 19084)
- reg.exe (PID: 20380)
- reg.exe (PID: 14864)
- reg.exe (PID: 24164)
Disables Windows firewall
- reg.exe (PID: 1896)
- reg.exe (PID: 1932)
- reg.exe (PID: 5416)
- reg.exe (PID: 21092)
- reg.exe (PID: 11524)
- reg.exe (PID: 14472)
- reg.exe (PID: 8084)
- reg.exe (PID: 16064)
- reg.exe (PID: 22444)
- reg.exe (PID: 16768)
- reg.exe (PID: 20092)
- reg.exe (PID: 20956)
- reg.exe (PID: 13096)
- reg.exe (PID: 8272)
- reg.exe (PID: 20016)
- reg.exe (PID: 16988)
- reg.exe (PID: 17928)
- reg.exe (PID: 11528)
- reg.exe (PID: 14592)
- reg.exe (PID: 15828)
- reg.exe (PID: 9164)
- reg.exe (PID: 13468)
- reg.exe (PID: 19400)
- reg.exe (PID: 19008)
- reg.exe (PID: 11068)
- reg.exe (PID: 22576)
- reg.exe (PID: 22732)
- reg.exe (PID: 22780)
- reg.exe (PID: 21316)
- reg.exe (PID: 22568)
- reg.exe (PID: 22724)
- reg.exe (PID: 22744)
- reg.exe (PID: 23116)
- reg.exe (PID: 17956)
- reg.exe (PID: 23492)
- reg.exe (PID: 23484)
- reg.exe (PID: 10212)
- reg.exe (PID: 19648)
- reg.exe (PID: 23180)
- reg.exe (PID: 22568)
- reg.exe (PID: 14068)
- reg.exe (PID: 18560)
- reg.exe (PID: 22724)
- reg.exe (PID: 23808)
- reg.exe (PID: 23824)
- reg.exe (PID: 23736)
- reg.exe (PID: 23976)
- reg.exe (PID: 17944)
- reg.exe (PID: 19028)
- reg.exe (PID: 18864)
- reg.exe (PID: 24156)
- reg.exe (PID: 24148)
- reg.exe (PID: 23932)
- reg.exe (PID: 23968)
- reg.exe (PID: 24172)
- reg.exe (PID: 24180)
Changes firewall settings
- reg.exe (PID: 1896)
- reg.exe (PID: 1932)
- reg.exe (PID: 5416)
- reg.exe (PID: 21092)
- reg.exe (PID: 11524)
- reg.exe (PID: 14472)
- reg.exe (PID: 16064)
- reg.exe (PID: 8084)
- reg.exe (PID: 22444)
- reg.exe (PID: 16768)
- reg.exe (PID: 20092)
- reg.exe (PID: 20956)
- reg.exe (PID: 8272)
- reg.exe (PID: 13096)
- reg.exe (PID: 11528)
- reg.exe (PID: 14592)
- reg.exe (PID: 20016)
- reg.exe (PID: 16988)
- reg.exe (PID: 17928)
- reg.exe (PID: 9164)
- reg.exe (PID: 15828)
- reg.exe (PID: 13468)
- reg.exe (PID: 19400)
- reg.exe (PID: 11068)
- reg.exe (PID: 22724)
- reg.exe (PID: 22732)
- reg.exe (PID: 22576)
- reg.exe (PID: 22780)
- reg.exe (PID: 19008)
- reg.exe (PID: 21316)
- reg.exe (PID: 22568)
- reg.exe (PID: 23116)
- reg.exe (PID: 22744)
- reg.exe (PID: 23492)
- reg.exe (PID: 17956)
- reg.exe (PID: 23484)
- reg.exe (PID: 19648)
- reg.exe (PID: 10212)
- reg.exe (PID: 23180)
- reg.exe (PID: 22568)
- reg.exe (PID: 14068)
- reg.exe (PID: 22724)
- reg.exe (PID: 18560)
- reg.exe (PID: 17944)
- reg.exe (PID: 23808)
- reg.exe (PID: 23824)
- reg.exe (PID: 23736)
- reg.exe (PID: 23976)
- reg.exe (PID: 23932)
- reg.exe (PID: 18864)
- reg.exe (PID: 19028)
- reg.exe (PID: 24156)
- reg.exe (PID: 24180)
- reg.exe (PID: 24148)
- reg.exe (PID: 23968)
- reg.exe (PID: 24172)
Disables Windows Defender
- reg.exe (PID: 1472)
- reg.exe (PID: 12776)
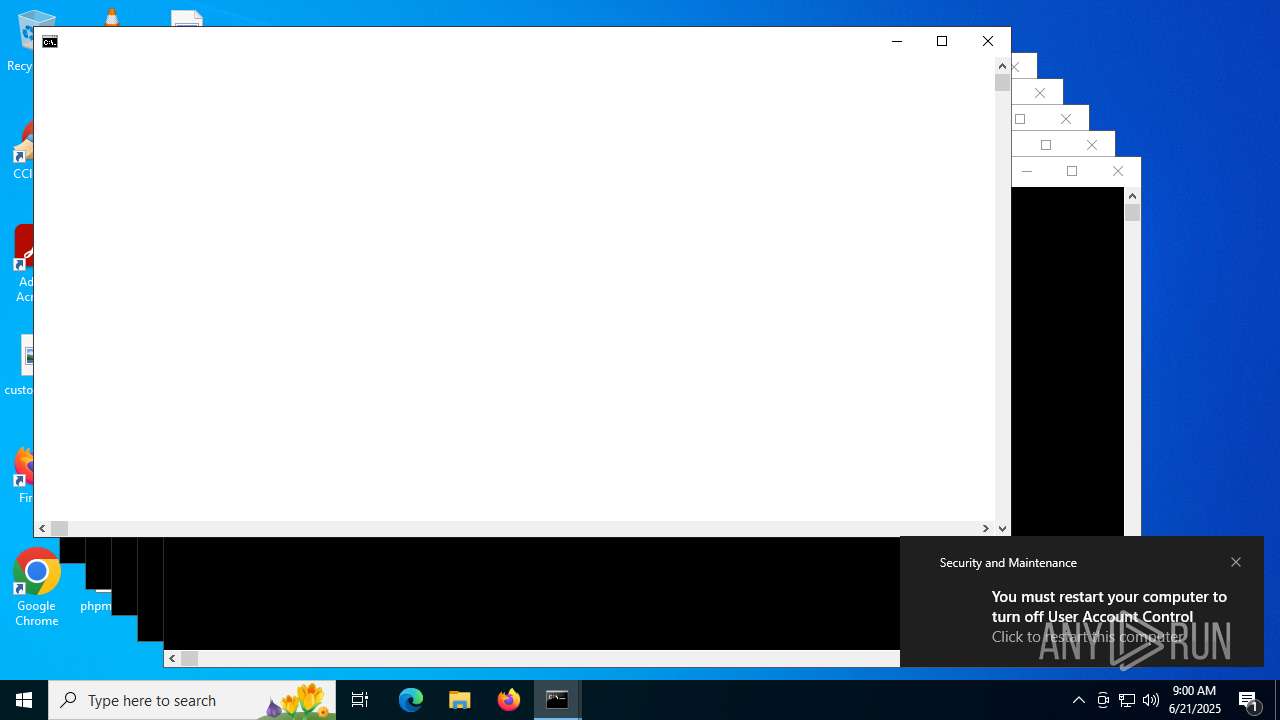
UAC/LUA settings modification
- reg.exe (PID: 7056)
- reg.exe (PID: 23860)
Uses NET.EXE to stop Windows Update service
- cmd.exe (PID: 472)
- net.exe (PID: 1096)
Starts NET.EXE for service management
- cmd.exe (PID: 472)
- net.exe (PID: 1096)
Create files in the Startup directory
- cmd.exe (PID: 472)
Attempting to use instant messaging service
- powershell.exe (PID: 7444)
- powershell.exe (PID: 7960)
- powershell.exe (PID: 8268)
- powershell.exe (PID: 7828)
- powershell.exe (PID: 10252)
- powershell.exe (PID: 11732)
- powershell.exe (PID: 14824)
- powershell.exe (PID: 15284)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 20440)
- powershell.exe (PID: 9864)
- powershell.exe (PID: 9692)
- powershell.exe (PID: 20524)
- powershell.exe (PID: 17628)
- powershell.exe (PID: 21496)
- powershell.exe (PID: 12860)
- powershell.exe (PID: 10308)
Stealers network behavior
- powershell.exe (PID: 7444)
- powershell.exe (PID: 7960)
- powershell.exe (PID: 7828)
- powershell.exe (PID: 8268)
- powershell.exe (PID: 10252)
- powershell.exe (PID: 11732)
- powershell.exe (PID: 14824)
- powershell.exe (PID: 15284)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 9864)
- powershell.exe (PID: 9692)
- powershell.exe (PID: 20440)
- powershell.exe (PID: 17628)
- powershell.exe (PID: 20524)
- powershell.exe (PID: 21496)
- powershell.exe (PID: 12860)
- powershell.exe (PID: 10308)
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 22444)
- reg.exe (PID: 22028)
- reg.exe (PID: 22456)
- reg.exe (PID: 22436)
- reg.exe (PID: 18916)
- reg.exe (PID: 15708)
- reg.exe (PID: 13876)
- reg.exe (PID: 20676)
- reg.exe (PID: 22352)
- reg.exe (PID: 10552)
- reg.exe (PID: 8548)
- reg.exe (PID: 8324)
- reg.exe (PID: 10784)
- reg.exe (PID: 19928)
- reg.exe (PID: 8792)
- reg.exe (PID: 17116)
- reg.exe (PID: 10044)
- reg.exe (PID: 436)
- reg.exe (PID: 14856)
- reg.exe (PID: 14892)
- reg.exe (PID: 9824)
- reg.exe (PID: 21256)
- reg.exe (PID: 12612)
- reg.exe (PID: 14560)
- reg.exe (PID: 13764)
- reg.exe (PID: 9380)
- reg.exe (PID: 14920)
- reg.exe (PID: 15672)
- reg.exe (PID: 17940)
- reg.exe (PID: 19084)
- reg.exe (PID: 20380)
- reg.exe (PID: 14864)
- reg.exe (PID: 24164)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3028)
- cmd.exe (PID: 472)
- cmd.exe (PID: 3924)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 1712)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 6428)
- cmd.exe (PID: 6504)
- cmd.exe (PID: 6232)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 4216)
- cmd.exe (PID: 1564)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 5012)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 3480)
- cmd.exe (PID: 2120)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 3488)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 11672)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 10604)
- cmd.exe (PID: 8468)
- cmd.exe (PID: 9300)
- cmd.exe (PID: 8796)
- cmd.exe (PID: 9540)
- cmd.exe (PID: 9340)
- cmd.exe (PID: 9644)
- cmd.exe (PID: 9148)
- cmd.exe (PID: 10008)
- cmd.exe (PID: 8580)
- cmd.exe (PID: 9384)
- cmd.exe (PID: 9896)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 9316)
- cmd.exe (PID: 10032)
- cmd.exe (PID: 9792)
- cmd.exe (PID: 9720)
- cmd.exe (PID: 10928)
- cmd.exe (PID: 10592)
- cmd.exe (PID: 10864)
- cmd.exe (PID: 10516)
- cmd.exe (PID: 10888)
- cmd.exe (PID: 10940)
- cmd.exe (PID: 11112)
- cmd.exe (PID: 11164)
- cmd.exe (PID: 11020)
- cmd.exe (PID: 10024)
- cmd.exe (PID: 10196)
- cmd.exe (PID: 10856)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 13216)
- cmd.exe (PID: 8772)
- cmd.exe (PID: 11656)
- cmd.exe (PID: 9108)
- cmd.exe (PID: 10496)
- cmd.exe (PID: 11716)
- cmd.exe (PID: 10972)
- cmd.exe (PID: 10836)
- cmd.exe (PID: 11408)
- cmd.exe (PID: 11624)
- cmd.exe (PID: 11932)
- cmd.exe (PID: 13184)
- cmd.exe (PID: 10456)
- cmd.exe (PID: 12816)
- cmd.exe (PID: 11636)
- cmd.exe (PID: 11648)
- cmd.exe (PID: 12912)
- cmd.exe (PID: 12952)
- cmd.exe (PID: 9672)
- cmd.exe (PID: 12672)
- cmd.exe (PID: 13936)
- cmd.exe (PID: 13844)
- cmd.exe (PID: 13852)
- cmd.exe (PID: 2348)
- cmd.exe (PID: 14144)
- cmd.exe (PID: 14652)
- cmd.exe (PID: 14712)
- cmd.exe (PID: 13888)
- cmd.exe (PID: 19056)
- cmd.exe (PID: 15968)
- cmd.exe (PID: 16288)
- cmd.exe (PID: 16296)
- cmd.exe (PID: 15768)
- cmd.exe (PID: 3160)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 14836)
- cmd.exe (PID: 15732)
- cmd.exe (PID: 20424)
- cmd.exe (PID: 15528)
- cmd.exe (PID: 14784)
- cmd.exe (PID: 17920)
- cmd.exe (PID: 18332)
- cmd.exe (PID: 16584)
- cmd.exe (PID: 19204)
- cmd.exe (PID: 19448)
- cmd.exe (PID: 13136)
- cmd.exe (PID: 18892)
- cmd.exe (PID: 19512)
- cmd.exe (PID: 19504)
- cmd.exe (PID: 19672)
- cmd.exe (PID: 15536)
- cmd.exe (PID: 20400)
- cmd.exe (PID: 6036)
- cmd.exe (PID: 9524)
- cmd.exe (PID: 20352)
- cmd.exe (PID: 19924)
- cmd.exe (PID: 19228)
- cmd.exe (PID: 7684)
- cmd.exe (PID: 18868)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 19356)
- cmd.exe (PID: 10168)
- cmd.exe (PID: 8508)
- cmd.exe (PID: 22504)
- cmd.exe (PID: 22316)
- cmd.exe (PID: 11172)
- cmd.exe (PID: 17780)
- cmd.exe (PID: 11800)
- cmd.exe (PID: 2296)
- cmd.exe (PID: 21008)
- cmd.exe (PID: 21228)
- cmd.exe (PID: 21272)
- cmd.exe (PID: 20804)
- cmd.exe (PID: 17608)
- cmd.exe (PID: 21140)
- cmd.exe (PID: 21372)
- cmd.exe (PID: 20940)
- cmd.exe (PID: 21768)
- cmd.exe (PID: 21436)
- cmd.exe (PID: 12084)
- cmd.exe (PID: 17540)
- cmd.exe (PID: 13744)
- cmd.exe (PID: 21244)
- cmd.exe (PID: 12572)
- cmd.exe (PID: 19240)
- cmd.exe (PID: 21804)
- cmd.exe (PID: 16560)
- cmd.exe (PID: 16500)
- cmd.exe (PID: 14600)
- cmd.exe (PID: 11144)
- cmd.exe (PID: 15804)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 9876)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 21980)
- cmd.exe (PID: 21912)
- cmd.exe (PID: 18708)
- cmd.exe (PID: 15044)
- cmd.exe (PID: 13552)
- cmd.exe (PID: 17340)
- cmd.exe (PID: 13072)
- cmd.exe (PID: 20608)
- cmd.exe (PID: 22416)
- cmd.exe (PID: 9196)
- cmd.exe (PID: 14572)
- cmd.exe (PID: 16084)
- cmd.exe (PID: 20848)
- cmd.exe (PID: 13084)
- cmd.exe (PID: 13424)
- cmd.exe (PID: 19236)
- cmd.exe (PID: 14348)
- cmd.exe (PID: 20232)
- cmd.exe (PID: 17296)
- cmd.exe (PID: 18448)
- cmd.exe (PID: 13480)
- cmd.exe (PID: 21996)
- cmd.exe (PID: 12864)
- cmd.exe (PID: 16792)
- cmd.exe (PID: 15216)
- cmd.exe (PID: 10616)
- cmd.exe (PID: 15388)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 11492)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 9096)
- cmd.exe (PID: 10460)
- cmd.exe (PID: 11368)
- cmd.exe (PID: 21860)
- cmd.exe (PID: 424)
- cmd.exe (PID: 15952)
- cmd.exe (PID: 18280)
- cmd.exe (PID: 8228)
- cmd.exe (PID: 9748)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 3028)
- cmd.exe (PID: 472)
- cmd.exe (PID: 3924)
- cmd.exe (PID: 1712)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 4216)
- cmd.exe (PID: 6232)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 6504)
- cmd.exe (PID: 1564)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 5012)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 6428)
- cmd.exe (PID: 2120)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 3488)
- cmd.exe (PID: 3480)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 10604)
- cmd.exe (PID: 8468)
- cmd.exe (PID: 8796)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 9300)
- cmd.exe (PID: 11672)
- cmd.exe (PID: 9148)
- cmd.exe (PID: 9540)
- cmd.exe (PID: 8580)
- cmd.exe (PID: 9340)
- cmd.exe (PID: 9384)
- cmd.exe (PID: 9792)
- cmd.exe (PID: 9720)
- cmd.exe (PID: 10008)
- cmd.exe (PID: 9644)
- cmd.exe (PID: 9896)
- cmd.exe (PID: 10024)
- cmd.exe (PID: 10196)
- cmd.exe (PID: 9316)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 13184)
- cmd.exe (PID: 10592)
- cmd.exe (PID: 10516)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 10032)
- cmd.exe (PID: 10888)
- cmd.exe (PID: 10928)
- cmd.exe (PID: 10864)
- cmd.exe (PID: 10940)
- cmd.exe (PID: 10836)
- cmd.exe (PID: 10856)
- cmd.exe (PID: 8772)
- cmd.exe (PID: 11020)
- cmd.exe (PID: 11112)
- cmd.exe (PID: 10496)
- cmd.exe (PID: 11164)
- cmd.exe (PID: 9108)
- cmd.exe (PID: 11716)
- cmd.exe (PID: 11932)
- cmd.exe (PID: 11656)
- cmd.exe (PID: 10972)
- cmd.exe (PID: 11624)
- cmd.exe (PID: 13216)
- cmd.exe (PID: 11408)
- cmd.exe (PID: 10456)
- cmd.exe (PID: 11648)
- cmd.exe (PID: 11636)
- cmd.exe (PID: 9672)
- cmd.exe (PID: 12816)
- cmd.exe (PID: 12952)
- cmd.exe (PID: 12912)
- cmd.exe (PID: 12672)
- cmd.exe (PID: 13936)
- cmd.exe (PID: 13888)
- cmd.exe (PID: 2348)
- cmd.exe (PID: 13852)
- cmd.exe (PID: 13844)
- cmd.exe (PID: 14144)
- cmd.exe (PID: 14712)
- cmd.exe (PID: 14652)
- cmd.exe (PID: 14836)
- cmd.exe (PID: 15768)
- cmd.exe (PID: 15732)
- cmd.exe (PID: 19056)
- cmd.exe (PID: 16296)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 15528)
- cmd.exe (PID: 15968)
- cmd.exe (PID: 16288)
- cmd.exe (PID: 3160)
- cmd.exe (PID: 14784)
- cmd.exe (PID: 16584)
- cmd.exe (PID: 20424)
- cmd.exe (PID: 17920)
- cmd.exe (PID: 18332)
- cmd.exe (PID: 19204)
- cmd.exe (PID: 18892)
- cmd.exe (PID: 19228)
- cmd.exe (PID: 19512)
- cmd.exe (PID: 19504)
- cmd.exe (PID: 19448)
- cmd.exe (PID: 19672)
- cmd.exe (PID: 13136)
- cmd.exe (PID: 20352)
- cmd.exe (PID: 15536)
- cmd.exe (PID: 19924)
- cmd.exe (PID: 9524)
- cmd.exe (PID: 20400)
- cmd.exe (PID: 6036)
- cmd.exe (PID: 7684)
- cmd.exe (PID: 18868)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 19356)
- cmd.exe (PID: 10168)
- cmd.exe (PID: 8508)
- cmd.exe (PID: 22504)
- cmd.exe (PID: 11172)
- cmd.exe (PID: 17780)
- cmd.exe (PID: 11800)
- cmd.exe (PID: 2296)
- cmd.exe (PID: 21008)
- cmd.exe (PID: 22316)
- cmd.exe (PID: 21228)
- cmd.exe (PID: 21272)
- cmd.exe (PID: 20940)
- cmd.exe (PID: 21140)
- cmd.exe (PID: 21372)
- cmd.exe (PID: 20804)
- cmd.exe (PID: 12084)
- cmd.exe (PID: 21768)
- cmd.exe (PID: 17540)
- cmd.exe (PID: 17608)
- cmd.exe (PID: 21436)
- cmd.exe (PID: 13744)
- cmd.exe (PID: 19240)
- cmd.exe (PID: 11144)
- cmd.exe (PID: 21244)
- cmd.exe (PID: 12572)
- cmd.exe (PID: 21804)
- cmd.exe (PID: 16500)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 13552)
- cmd.exe (PID: 21980)
- cmd.exe (PID: 14600)
- cmd.exe (PID: 15804)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 22416)
- cmd.exe (PID: 13072)
- cmd.exe (PID: 17340)
- cmd.exe (PID: 16084)
- cmd.exe (PID: 20608)
- cmd.exe (PID: 20848)
- cmd.exe (PID: 16560)
- cmd.exe (PID: 18708)
- cmd.exe (PID: 21912)
- cmd.exe (PID: 9196)
- cmd.exe (PID: 14572)
- cmd.exe (PID: 13084)
- cmd.exe (PID: 16792)
- cmd.exe (PID: 13424)
- cmd.exe (PID: 13480)
- cmd.exe (PID: 21996)
- cmd.exe (PID: 9876)
- cmd.exe (PID: 15044)
- cmd.exe (PID: 17296)
- cmd.exe (PID: 18448)
- cmd.exe (PID: 15216)
- cmd.exe (PID: 20232)
- cmd.exe (PID: 12864)
- cmd.exe (PID: 19236)
- cmd.exe (PID: 14348)
- cmd.exe (PID: 10616)
- cmd.exe (PID: 15388)
- cmd.exe (PID: 9096)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 11492)
- cmd.exe (PID: 10460)
- cmd.exe (PID: 15952)
- cmd.exe (PID: 21860)
- cmd.exe (PID: 11368)
- cmd.exe (PID: 18280)
- cmd.exe (PID: 424)
- cmd.exe (PID: 9308)
- cmd.exe (PID: 7724)
- cmd.exe (PID: 9748)
- cmd.exe (PID: 17000)
- cmd.exe (PID: 8228)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 10624)
- cmd.exe (PID: 18360)
- cmd.exe (PID: 9324)
- cmd.exe (PID: 22520)
- cmd.exe (PID: 17488)
- cmd.exe (PID: 22296)
- cmd.exe (PID: 10524)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 13644)
- cmd.exe (PID: 10512)
- cmd.exe (PID: 15948)
Starts process via Powershell
- powershell.exe (PID: 5772)
- powershell.exe (PID: 12168)
- powershell.exe (PID: 5692)
- powershell.exe (PID: 5620)
- powershell.exe (PID: 14160)
- powershell.exe (PID: 13760)
- powershell.exe (PID: 13972)
- powershell.exe (PID: 14468)
- powershell.exe (PID: 14488)
- powershell.exe (PID: 14616)
- powershell.exe (PID: 14804)
- powershell.exe (PID: 14628)
- powershell.exe (PID: 15048)
- powershell.exe (PID: 14896)
- powershell.exe (PID: 15000)
- powershell.exe (PID: 15060)
- powershell.exe (PID: 14884)
- powershell.exe (PID: 15224)
- powershell.exe (PID: 15148)
- powershell.exe (PID: 15156)
- powershell.exe (PID: 15356)
- powershell.exe (PID: 12340)
- powershell.exe (PID: 14392)
- powershell.exe (PID: 14136)
- powershell.exe (PID: 14724)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 15436)
- powershell.exe (PID: 15460)
- powershell.exe (PID: 3704)
- powershell.exe (PID: 15688)
- powershell.exe (PID: 15724)
- powershell.exe (PID: 16044)
- powershell.exe (PID: 15652)
- powershell.exe (PID: 15756)
- powershell.exe (PID: 16464)
- powershell.exe (PID: 16760)
- powershell.exe (PID: 16816)
- powershell.exe (PID: 17476)
- powershell.exe (PID: 17600)
- powershell.exe (PID: 17648)
- powershell.exe (PID: 18452)
- powershell.exe (PID: 18660)
- powershell.exe (PID: 19388)
- powershell.exe (PID: 3752)
- powershell.exe (PID: 19156)
- powershell.exe (PID: 20012)
- powershell.exe (PID: 6960)
- powershell.exe (PID: 7644)
- powershell.exe (PID: 8176)
- powershell.exe (PID: 9596)
- powershell.exe (PID: 7768)
- powershell.exe (PID: 11156)
- powershell.exe (PID: 19780)
- powershell.exe (PID: 20756)
- powershell.exe (PID: 21200)
- powershell.exe (PID: 21392)
- powershell.exe (PID: 22048)
- powershell.exe (PID: 7328)
- powershell.exe (PID: 9812)
- powershell.exe (PID: 14060)
- powershell.exe (PID: 20364)
- powershell.exe (PID: 15056)
- powershell.exe (PID: 10568)
- powershell.exe (PID: 14352)
- powershell.exe (PID: 12352)
- powershell.exe (PID: 7180)
- powershell.exe (PID: 7240)
- powershell.exe (PID: 20028)
- powershell.exe (PID: 7664)
- powershell.exe (PID: 10224)
- powershell.exe (PID: 10292)
- powershell.exe (PID: 15796)
- powershell.exe (PID: 22708)
- powershell.exe (PID: 23004)
Executing commands from a ".bat" file
- powershell.exe (PID: 5772)
- cmd.exe (PID: 472)
- powershell.exe (PID: 12168)
- powershell.exe (PID: 5692)
- powershell.exe (PID: 5620)
- powershell.exe (PID: 14160)
- powershell.exe (PID: 14616)
- powershell.exe (PID: 13972)
- powershell.exe (PID: 14628)
- powershell.exe (PID: 14136)
- powershell.exe (PID: 14884)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 15048)
- powershell.exe (PID: 15148)
- powershell.exe (PID: 15000)
- powershell.exe (PID: 15724)
- powershell.exe (PID: 14724)
- powershell.exe (PID: 15156)
- powershell.exe (PID: 14468)
- powershell.exe (PID: 13760)
- powershell.exe (PID: 14804)
- powershell.exe (PID: 14488)
- powershell.exe (PID: 15224)
- powershell.exe (PID: 15460)
- powershell.exe (PID: 12340)
- powershell.exe (PID: 16044)
- powershell.exe (PID: 15356)
- powershell.exe (PID: 15688)
- powershell.exe (PID: 14392)
- powershell.exe (PID: 15652)
- powershell.exe (PID: 15060)
- powershell.exe (PID: 3704)
- powershell.exe (PID: 16760)
- powershell.exe (PID: 15436)
- powershell.exe (PID: 16816)
- powershell.exe (PID: 15756)
- powershell.exe (PID: 14896)
- powershell.exe (PID: 17648)
- powershell.exe (PID: 16464)
- powershell.exe (PID: 17476)
- powershell.exe (PID: 17600)
- powershell.exe (PID: 18660)
- powershell.exe (PID: 18452)
- powershell.exe (PID: 19388)
- powershell.exe (PID: 19156)
- powershell.exe (PID: 3752)
- powershell.exe (PID: 6960)
- powershell.exe (PID: 7644)
- powershell.exe (PID: 8176)
- powershell.exe (PID: 9596)
- powershell.exe (PID: 20012)
- powershell.exe (PID: 7768)
- powershell.exe (PID: 19780)
- powershell.exe (PID: 20756)
- powershell.exe (PID: 11156)
- powershell.exe (PID: 21392)
- powershell.exe (PID: 9812)
- powershell.exe (PID: 22048)
- powershell.exe (PID: 21200)
- powershell.exe (PID: 7328)
- powershell.exe (PID: 14060)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 472)
- cmd.exe (PID: 3924)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 1712)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 6428)
- cmd.exe (PID: 6504)
- cmd.exe (PID: 4216)
- cmd.exe (PID: 5012)
- cmd.exe (PID: 1564)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 3480)
- cmd.exe (PID: 6232)
- cmd.exe (PID: 2120)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 3488)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 8468)
- cmd.exe (PID: 8796)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 9384)
- cmd.exe (PID: 10024)
- cmd.exe (PID: 13216)
- cmd.exe (PID: 10496)
- cmd.exe (PID: 13184)
- cmd.exe (PID: 11932)
- cmd.exe (PID: 10456)
- cmd.exe (PID: 9672)
- cmd.exe (PID: 12672)
- cmd.exe (PID: 2348)
- cmd.exe (PID: 13888)
- cmd.exe (PID: 14144)
- cmd.exe (PID: 19056)
- cmd.exe (PID: 15768)
- cmd.exe (PID: 3160)
- cmd.exe (PID: 15732)
- cmd.exe (PID: 20424)
- cmd.exe (PID: 14836)
- cmd.exe (PID: 14784)
- cmd.exe (PID: 16584)
- cmd.exe (PID: 18892)
- cmd.exe (PID: 19448)
- cmd.exe (PID: 13136)
- cmd.exe (PID: 19672)
- cmd.exe (PID: 9524)
- cmd.exe (PID: 20352)
- cmd.exe (PID: 17920)
- cmd.exe (PID: 19924)
- cmd.exe (PID: 7684)
- cmd.exe (PID: 18868)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 10168)
- cmd.exe (PID: 8508)
- cmd.exe (PID: 22504)
- cmd.exe (PID: 11172)
- cmd.exe (PID: 2296)
- cmd.exe (PID: 21008)
- cmd.exe (PID: 21228)
- cmd.exe (PID: 21272)
- cmd.exe (PID: 21140)
- cmd.exe (PID: 21372)
- cmd.exe (PID: 20940)
- cmd.exe (PID: 21768)
- cmd.exe (PID: 17540)
- cmd.exe (PID: 12084)
- cmd.exe (PID: 21436)
- cmd.exe (PID: 12572)
- cmd.exe (PID: 21244)
- cmd.exe (PID: 19240)
- cmd.exe (PID: 13744)
- cmd.exe (PID: 11144)
- cmd.exe (PID: 21804)
- cmd.exe (PID: 16500)
- cmd.exe (PID: 14600)
- cmd.exe (PID: 15804)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 21980)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 13552)
- cmd.exe (PID: 21912)
- cmd.exe (PID: 17340)
- cmd.exe (PID: 13072)
- cmd.exe (PID: 16084)
- cmd.exe (PID: 18708)
- cmd.exe (PID: 20848)
- cmd.exe (PID: 22416)
- cmd.exe (PID: 9196)
- cmd.exe (PID: 14572)
- cmd.exe (PID: 20608)
- cmd.exe (PID: 13084)
- cmd.exe (PID: 13424)
- cmd.exe (PID: 16792)
- cmd.exe (PID: 17296)
- cmd.exe (PID: 21996)
- cmd.exe (PID: 18448)
- cmd.exe (PID: 13480)
- cmd.exe (PID: 12864)
- cmd.exe (PID: 15216)
- cmd.exe (PID: 10616)
- cmd.exe (PID: 15388)
- cmd.exe (PID: 9096)
- cmd.exe (PID: 9016)
- cmd.exe (PID: 10460)
- cmd.exe (PID: 21860)
- cmd.exe (PID: 11368)
- cmd.exe (PID: 15952)
- cmd.exe (PID: 424)
- cmd.exe (PID: 18280)
- cmd.exe (PID: 8228)
- cmd.exe (PID: 9748)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5772)
- cmd.exe (PID: 472)
- powershell.exe (PID: 12168)
- powershell.exe (PID: 5692)
- powershell.exe (PID: 5620)
- powershell.exe (PID: 14160)
- powershell.exe (PID: 14616)
- powershell.exe (PID: 13972)
- powershell.exe (PID: 14896)
- powershell.exe (PID: 14628)
- powershell.exe (PID: 14136)
- powershell.exe (PID: 14884)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 15724)
- powershell.exe (PID: 14724)
- powershell.exe (PID: 15048)
- powershell.exe (PID: 15148)
- powershell.exe (PID: 15000)
- powershell.exe (PID: 15156)
- powershell.exe (PID: 14468)
- powershell.exe (PID: 14488)
- powershell.exe (PID: 13760)
- powershell.exe (PID: 14804)
- powershell.exe (PID: 15224)
- powershell.exe (PID: 15460)
- powershell.exe (PID: 12340)
- powershell.exe (PID: 16044)
- powershell.exe (PID: 15356)
- powershell.exe (PID: 15688)
- powershell.exe (PID: 14392)
- powershell.exe (PID: 16760)
- powershell.exe (PID: 15060)
- powershell.exe (PID: 3704)
- powershell.exe (PID: 15652)
- powershell.exe (PID: 15436)
- powershell.exe (PID: 16816)
- powershell.exe (PID: 15756)
- powershell.exe (PID: 17648)
- powershell.exe (PID: 16464)
- powershell.exe (PID: 17476)
- powershell.exe (PID: 17600)
- powershell.exe (PID: 18660)
- powershell.exe (PID: 18452)
- powershell.exe (PID: 19388)
- powershell.exe (PID: 19156)
- powershell.exe (PID: 3752)
- powershell.exe (PID: 6960)
- powershell.exe (PID: 7644)
- powershell.exe (PID: 8176)
- powershell.exe (PID: 9596)
- powershell.exe (PID: 20012)
- powershell.exe (PID: 7768)
- powershell.exe (PID: 19780)
- powershell.exe (PID: 20756)
- powershell.exe (PID: 11156)
- powershell.exe (PID: 21392)
- powershell.exe (PID: 22048)
- powershell.exe (PID: 21200)
- powershell.exe (PID: 9812)
- powershell.exe (PID: 7328)
- powershell.exe (PID: 14060)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 472)
- cmd.exe (PID: 9120)
- cmd.exe (PID: 1712)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 3480)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 8468)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 6428)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 5012)
- cmd.exe (PID: 3924)
- cmd.exe (PID: 4216)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 2120)
- cmd.exe (PID: 3488)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 6232)
- cmd.exe (PID: 6504)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 1564)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 7820)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 472)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 6536)
The process connected to a server suspected of theft
- powershell.exe (PID: 2876)
- powershell.exe (PID: 7856)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 7224)
- powershell.exe (PID: 7960)
- powershell.exe (PID: 8268)
- powershell.exe (PID: 7828)
- powershell.exe (PID: 8328)
- powershell.exe (PID: 8424)
- powershell.exe (PID: 8620)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8992)
- powershell.exe (PID: 10252)
- powershell.exe (PID: 9272)
- powershell.exe (PID: 6320)
- powershell.exe (PID: 10092)
- powershell.exe (PID: 12024)
- powershell.exe (PID: 11732)
- powershell.exe (PID: 12444)
- powershell.exe (PID: 4752)
- powershell.exe (PID: 13548)
- powershell.exe (PID: 14824)
- powershell.exe (PID: 15600)
- powershell.exe (PID: 15284)
- powershell.exe (PID: 13352)
- powershell.exe (PID: 16676)
- powershell.exe (PID: 18828)
- powershell.exe (PID: 17572)
- powershell.exe (PID: 20060)
- powershell.exe (PID: 15364)
- powershell.exe (PID: 9728)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 4012)
- powershell.exe (PID: 9420)
- powershell.exe (PID: 20440)
- powershell.exe (PID: 9692)
- powershell.exe (PID: 9864)
- powershell.exe (PID: 17628)
- powershell.exe (PID: 20524)
- powershell.exe (PID: 9828)
- powershell.exe (PID: 21496)
- powershell.exe (PID: 8616)
- powershell.exe (PID: 11176)
- powershell.exe (PID: 10692)
- powershell.exe (PID: 13380)
- powershell.exe (PID: 12860)
- powershell.exe (PID: 14732)
- powershell.exe (PID: 10308)
- powershell.exe (PID: 15876)
Windows service management via SC.EXE
- sc.exe (PID: 6180)
Starts SC.EXE for service management
- cmd.exe (PID: 472)
Application launched itself
- cmd.exe (PID: 472)
Possible usage of Discord/Telegram API has been detected (YARA)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 3924)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 4708)
INFO
Disables trace logs
- powershell.exe (PID: 2876)
- netsh.exe (PID: 3756)
- powershell.exe (PID: 7856)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7960)
- powershell.exe (PID: 7224)
- powershell.exe (PID: 7828)
- powershell.exe (PID: 8268)
- powershell.exe (PID: 8260)
- powershell.exe (PID: 8328)
- powershell.exe (PID: 8676)
- powershell.exe (PID: 8292)
- powershell.exe (PID: 8620)
- powershell.exe (PID: 8956)
- powershell.exe (PID: 8424)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8536)
- powershell.exe (PID: 8740)
- powershell.exe (PID: 8992)
- powershell.exe (PID: 9272)
- powershell.exe (PID: 10252)
- powershell.exe (PID: 9916)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 6320)
- powershell.exe (PID: 10092)
- powershell.exe (PID: 10788)
- powershell.exe (PID: 12024)
- powershell.exe (PID: 11732)
- powershell.exe (PID: 12444)
- powershell.exe (PID: 12396)
- powershell.exe (PID: 4752)
- powershell.exe (PID: 13548)
- powershell.exe (PID: 13076)
- powershell.exe (PID: 15600)
- powershell.exe (PID: 14824)
- powershell.exe (PID: 13352)
- powershell.exe (PID: 14744)
- powershell.exe (PID: 15928)
- powershell.exe (PID: 15284)
- powershell.exe (PID: 16676)
- powershell.exe (PID: 17216)
- powershell.exe (PID: 17572)
- powershell.exe (PID: 18828)
- powershell.exe (PID: 18968)
- powershell.exe (PID: 18072)
- powershell.exe (PID: 15364)
- powershell.exe (PID: 20060)
- powershell.exe (PID: 9728)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 4012)
- powershell.exe (PID: 9420)
- powershell.exe (PID: 9864)
- powershell.exe (PID: 20440)
- powershell.exe (PID: 9692)
- powershell.exe (PID: 20524)
- powershell.exe (PID: 17628)
- powershell.exe (PID: 8276)
- powershell.exe (PID: 9828)
- powershell.exe (PID: 21496)
- powershell.exe (PID: 8616)
- powershell.exe (PID: 10692)
- powershell.exe (PID: 11176)
- powershell.exe (PID: 13380)
- powershell.exe (PID: 12860)
- powershell.exe (PID: 14732)
- powershell.exe (PID: 15876)
- powershell.exe (PID: 10308)
- powershell.exe (PID: 15232)
- powershell.exe (PID: 8060)
- powershell.exe (PID: 8496)
Checks proxy server information
- powershell.exe (PID: 2876)
- powershell.exe (PID: 7856)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 7224)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7960)
- powershell.exe (PID: 7828)
- powershell.exe (PID: 8268)
- powershell.exe (PID: 8328)
- powershell.exe (PID: 8260)
- powershell.exe (PID: 8292)
- powershell.exe (PID: 8956)
- powershell.exe (PID: 8620)
- powershell.exe (PID: 8676)
- powershell.exe (PID: 8424)
- powershell.exe (PID: 8536)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8740)
- powershell.exe (PID: 10252)
- powershell.exe (PID: 9272)
- powershell.exe (PID: 8992)
- powershell.exe (PID: 9916)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 6320)
- powershell.exe (PID: 10092)
- powershell.exe (PID: 12024)
- powershell.exe (PID: 11732)
- powershell.exe (PID: 12444)
- powershell.exe (PID: 10788)
- powershell.exe (PID: 12396)
- powershell.exe (PID: 4752)
- powershell.exe (PID: 13548)
- powershell.exe (PID: 15600)
- powershell.exe (PID: 13076)
- powershell.exe (PID: 14824)
- powershell.exe (PID: 14744)
- powershell.exe (PID: 13352)
- powershell.exe (PID: 15928)
- powershell.exe (PID: 15284)
- powershell.exe (PID: 16676)
- powershell.exe (PID: 17216)
- powershell.exe (PID: 17572)
- powershell.exe (PID: 18828)
- powershell.exe (PID: 18968)
- powershell.exe (PID: 18072)
- powershell.exe (PID: 20060)
- powershell.exe (PID: 15364)
- powershell.exe (PID: 9728)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 4012)
- slui.exe (PID: 13824)
- powershell.exe (PID: 9420)
- powershell.exe (PID: 9864)
- powershell.exe (PID: 20440)
- powershell.exe (PID: 9692)
- powershell.exe (PID: 20524)
- powershell.exe (PID: 17628)
- powershell.exe (PID: 9828)
- powershell.exe (PID: 8276)
- powershell.exe (PID: 21496)
- powershell.exe (PID: 8616)
- powershell.exe (PID: 10692)
- powershell.exe (PID: 11176)
- powershell.exe (PID: 13380)
- powershell.exe (PID: 12860)
- powershell.exe (PID: 14732)
- powershell.exe (PID: 15876)
- powershell.exe (PID: 15232)
- powershell.exe (PID: 10308)
- powershell.exe (PID: 8060)
- powershell.exe (PID: 8496)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2876)
- powershell.exe (PID: 7856)
- powershell.exe (PID: 7224)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7960)
- powershell.exe (PID: 7828)
- powershell.exe (PID: 8260)
- powershell.exe (PID: 8328)
- powershell.exe (PID: 8268)
- powershell.exe (PID: 8676)
- powershell.exe (PID: 8292)
- powershell.exe (PID: 8424)
- powershell.exe (PID: 8956)
- powershell.exe (PID: 8620)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8536)
- powershell.exe (PID: 8740)
- powershell.exe (PID: 10252)
- powershell.exe (PID: 8992)
- powershell.exe (PID: 9272)
- powershell.exe (PID: 9916)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 6320)
- powershell.exe (PID: 10092)
- powershell.exe (PID: 12024)
- powershell.exe (PID: 10788)
- powershell.exe (PID: 11732)
- powershell.exe (PID: 12444)
- powershell.exe (PID: 12396)
- powershell.exe (PID: 4752)
- powershell.exe (PID: 13548)
- powershell.exe (PID: 13076)
- powershell.exe (PID: 14824)
- powershell.exe (PID: 15600)
- powershell.exe (PID: 15928)
- powershell.exe (PID: 13352)
- powershell.exe (PID: 14744)
- powershell.exe (PID: 15284)
- powershell.exe (PID: 17216)
- powershell.exe (PID: 16676)
- powershell.exe (PID: 17572)
- powershell.exe (PID: 18968)
- powershell.exe (PID: 18072)
- powershell.exe (PID: 18828)
- powershell.exe (PID: 15364)
- powershell.exe (PID: 20060)
- powershell.exe (PID: 9728)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 4012)
- powershell.exe (PID: 9420)
- powershell.exe (PID: 20440)
- powershell.exe (PID: 9692)
- powershell.exe (PID: 9864)
- powershell.exe (PID: 17628)
- powershell.exe (PID: 20524)
- powershell.exe (PID: 8276)
- powershell.exe (PID: 9828)
- powershell.exe (PID: 21496)
- powershell.exe (PID: 8616)
- powershell.exe (PID: 10692)
- powershell.exe (PID: 13380)
- powershell.exe (PID: 11176)
- powershell.exe (PID: 12860)
- powershell.exe (PID: 14732)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 2876)
- powershell.exe (PID: 7856)
- powershell.exe (PID: 7224)
- powershell.exe (PID: 7444)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7960)
- powershell.exe (PID: 7828)
- powershell.exe (PID: 8268)
- powershell.exe (PID: 8260)
- powershell.exe (PID: 8328)
- powershell.exe (PID: 8676)
- powershell.exe (PID: 8424)
- powershell.exe (PID: 8292)
- powershell.exe (PID: 8956)
- powershell.exe (PID: 8620)
- powershell.exe (PID: 8664)
- powershell.exe (PID: 8536)
- powershell.exe (PID: 8740)
- powershell.exe (PID: 9916)
- powershell.exe (PID: 10252)
- powershell.exe (PID: 8992)
- powershell.exe (PID: 6320)
- powershell.exe (PID: 9076)
- powershell.exe (PID: 9272)
- powershell.exe (PID: 12024)
- powershell.exe (PID: 10788)
- powershell.exe (PID: 10092)
- powershell.exe (PID: 11732)
- powershell.exe (PID: 12444)
- powershell.exe (PID: 12396)
- powershell.exe (PID: 13548)
- powershell.exe (PID: 13076)
- powershell.exe (PID: 4752)
- powershell.exe (PID: 15600)
- powershell.exe (PID: 14824)
- powershell.exe (PID: 13352)
- powershell.exe (PID: 15928)
- powershell.exe (PID: 15284)
- powershell.exe (PID: 14744)
- powershell.exe (PID: 16676)
- powershell.exe (PID: 17216)
- powershell.exe (PID: 18968)
- powershell.exe (PID: 17572)
- powershell.exe (PID: 18072)
- powershell.exe (PID: 18828)
- powershell.exe (PID: 15364)
- powershell.exe (PID: 20060)
- powershell.exe (PID: 9728)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 4012)
- powershell.exe (PID: 9420)
- powershell.exe (PID: 20440)
- powershell.exe (PID: 9692)
- powershell.exe (PID: 9864)
- powershell.exe (PID: 20524)
- powershell.exe (PID: 17628)
- powershell.exe (PID: 8276)
- powershell.exe (PID: 9828)
- powershell.exe (PID: 21496)
- powershell.exe (PID: 8616)
- powershell.exe (PID: 10692)
- powershell.exe (PID: 11176)
- powershell.exe (PID: 13380)
- powershell.exe (PID: 12860)
- powershell.exe (PID: 14732)
Reads mouse settings
- reg.exe (PID: 1128)
- reg.exe (PID: 14224)
- reg.exe (PID: 21336)
- reg.exe (PID: 16200)
- reg.exe (PID: 19152)
- reg.exe (PID: 20268)
- reg.exe (PID: 7836)
- reg.exe (PID: 22128)
- reg.exe (PID: 18052)
- reg.exe (PID: 11552)
- reg.exe (PID: 16216)
- reg.exe (PID: 10840)
- reg.exe (PID: 15984)
- reg.exe (PID: 10232)
- reg.exe (PID: 17244)
- reg.exe (PID: 15280)
- reg.exe (PID: 17368)
- reg.exe (PID: 15760)
- reg.exe (PID: 13700)
- reg.exe (PID: 17596)
- reg.exe (PID: 20916)
- reg.exe (PID: 9160)
- reg.exe (PID: 10156)
- reg.exe (PID: 20188)
- reg.exe (PID: 17740)
- reg.exe (PID: 11504)
- reg.exe (PID: 18428)
- reg.exe (PID: 14736)
- reg.exe (PID: 17704)
- reg.exe (PID: 10104)
- reg.exe (PID: 7408)
- reg.exe (PID: 17884)
- reg.exe (PID: 13492)
Reads the computer name
- ShellExperienceHost.exe (PID: 6536)
Checks supported languages
- ShellExperienceHost.exe (PID: 6536)
Launching a file from the Startup directory
- cmd.exe (PID: 472)
Manual execution by a user
- cmd.exe (PID: 7956)
- rundll32.exe (PID: 8380)
- cmd.exe (PID: 8580)
- cmd.exe (PID: 9148)
- cmd.exe (PID: 9300)
- cmd.exe (PID: 9340)
- rundll32.exe (PID: 9436)
- cmd.exe (PID: 9540)
- cmd.exe (PID: 9644)
- cmd.exe (PID: 9720)
- cmd.exe (PID: 9792)
- cmd.exe (PID: 9896)
- rundll32.exe (PID: 10136)
- cmd.exe (PID: 10196)
- cmd.exe (PID: 9316)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 9788)
- cmd.exe (PID: 10032)
- cmd.exe (PID: 10592)
- cmd.exe (PID: 10516)
- cmd.exe (PID: 10604)
- cmd.exe (PID: 10008)
- cmd.exe (PID: 10836)
- cmd.exe (PID: 10928)
- cmd.exe (PID: 10888)
- cmd.exe (PID: 11020)
- cmd.exe (PID: 10940)
- cmd.exe (PID: 11112)
- cmd.exe (PID: 11164)
- cmd.exe (PID: 9108)
- cmd.exe (PID: 10972)
- cmd.exe (PID: 10856)
- cmd.exe (PID: 11408)
- cmd.exe (PID: 8772)
- cmd.exe (PID: 11624)
- cmd.exe (PID: 11636)
- cmd.exe (PID: 10864)
- cmd.exe (PID: 11672)
- cmd.exe (PID: 11716)
- cmd.exe (PID: 11648)
- cmd.exe (PID: 11656)
- cmd.exe (PID: 12816)
- cmd.exe (PID: 12912)
- cmd.exe (PID: 12952)
- cmd.exe (PID: 13852)
- cmd.exe (PID: 13844)
- cmd.exe (PID: 13936)
- cmd.exe (PID: 14652)
- cmd.exe (PID: 14712)
- cmd.exe (PID: 15968)
- cmd.exe (PID: 16296)
- cmd.exe (PID: 16288)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 15528)
- cmd.exe (PID: 18332)
- cmd.exe (PID: 19228)
- cmd.exe (PID: 19204)
- cmd.exe (PID: 19504)
- cmd.exe (PID: 19512)
- cmd.exe (PID: 20400)
- cmd.exe (PID: 15536)
- cmd.exe (PID: 6036)
- cmd.exe (PID: 19356)
- cmd.exe (PID: 17780)
- cmd.exe (PID: 11800)
- cmd.exe (PID: 17608)
- cmd.exe (PID: 20804)
- cmd.exe (PID: 22316)
- cmd.exe (PID: 16560)
- cmd.exe (PID: 15044)
- cmd.exe (PID: 9876)
- cmd.exe (PID: 19236)
- cmd.exe (PID: 20232)
- cmd.exe (PID: 14348)
- cmd.exe (PID: 11492)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 9308)
- cmd.exe (PID: 22520)
- cmd.exe (PID: 17488)
- cmd.exe (PID: 9324)
- cmd.exe (PID: 15948)
- cmd.exe (PID: 10512)
- cmd.exe (PID: 1560)
- cmd.exe (PID: 14544)
- cmd.exe (PID: 12028)
- cmd.exe (PID: 13672)
- cmd.exe (PID: 15028)
- cmd.exe (PID: 9560)
- cmd.exe (PID: 21716)
- cmd.exe (PID: 23768)
Attempting to use instant messaging service
- powershell.exe (PID: 7444)
- powershell.exe (PID: 7960)
- powershell.exe (PID: 7828)
- powershell.exe (PID: 8268)
- powershell.exe (PID: 8260)
- powershell.exe (PID: 10252)
- powershell.exe (PID: 11732)
- powershell.exe (PID: 14824)
- powershell.exe (PID: 13352)
- powershell.exe (PID: 15284)
- powershell.exe (PID: 17572)
- powershell.exe (PID: 18828)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 9420)
- powershell.exe (PID: 9864)
- powershell.exe (PID: 9692)
- powershell.exe (PID: 20440)
- powershell.exe (PID: 17628)
- powershell.exe (PID: 20524)
- powershell.exe (PID: 21496)
- powershell.exe (PID: 12860)
- powershell.exe (PID: 10308)
Reads the software policy settings
- slui.exe (PID: 13824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(3888) cmd.exe
Discord-Webhook-Tokens (1)1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
Discord-Info-Links
1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
Get Webhook Infohttps://discord.com/api/webhooks/1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
(PID) Process(3924) cmd.exe
Discord-Webhook-Tokens (1)1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
Discord-Info-Links
1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
Get Webhook Infohttps://discord.com/api/webhooks/1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
(PID) Process(5600) cmd.exe
Discord-Webhook-Tokens (1)1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
Discord-Info-Links
1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
Get Webhook Infohttps://discord.com/api/webhooks/1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
(PID) Process(4708) cmd.exe
Discord-Webhook-Tokens (1)1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
Discord-Info-Links
1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
Get Webhook Infohttps://discord.com/api/webhooks/1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1
Total processes
1 284
Monitored processes
1 095
Malicious processes
127
Suspicious processes
129
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | REG ADD "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer" /v SmartScreenEnabled /t REG_SZ /d "Off" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 360 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Downloads\copy_1014.bat" | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Downloads\copy_20258.bat" | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System" /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\SAB4.0.bat" | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | net stop wuauserv | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | REG ADD "HKCU\Control Panel\Mouse" /v SwapMouseButtons /t REG_SZ /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
804 599
Read events
804 401
Write events
198
Delete events
0
Modification events
| (PID) Process: | (5772) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (5772) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (1128) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Mouse |
| Operation: | write | Name: | SwapMouseButtons |
Value: 1 | |||
| (PID) Process: | (2612) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoDesktop |
Value: 1 | |||
| (PID) Process: | (5124) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SmartScreenEnabled |
Value: Off | |||
| (PID) Process: | (1896) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SharedAccess\Parameters\FirewallPolicy\DomainProfile |
| Operation: | write | Name: | EnableFirewall |
Value: 0 | |||
| (PID) Process: | (1932) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile |
| Operation: | write | Name: | EnableFirewall |
Value: 0 | |||
| (PID) Process: | (5416) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SharedAccess\Parameters\FirewallPolicy\PublicProfile |
| Operation: | write | Name: | EnableFirewall |
Value: 0 | |||
| (PID) Process: | (1472) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (5628) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Tcpip6\Parameters |
| Operation: | write | Name: | DisabledComponents |
Value: | |||
Executable files
0
Suspicious files
5
Text files
457
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5772 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_azjewv2n.kli.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 472 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\MyAutoStart.bat | text | |
MD5:3BD308E6323FAE028E5EAD4AC2DB9B87 | SHA256:E4B92757DD9267E07F228888D1B5D425CEDF99D6837D70B129AF69E615C52156 | |||
| 472 | cmd.exe | C:\Users\admin\Downloads\VARIETY_WOLFED_effortdate.png | image | |
MD5:27FE925E9CA708F52FB63CFEFFFB9C70 | SHA256:AFE8B170E74DC3AFB74860D0D6633A1B0BCDE4C58F829E794A85A537A498F881 | |||
| 5772 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:5152302EB5DF17894E9382679A7F36D4 | SHA256:1FB7295E12F9F324CA6B63FCE514B2AF5B6A034D45318A507A49409CDE87A6FD | |||
| 2876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xk0eh3ji.v3e.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 472 | cmd.exe | C:\Users\admin\Downloads\copy_23080.bat | text | |
MD5:3BD308E6323FAE028E5EAD4AC2DB9B87 | SHA256:E4B92757DD9267E07F228888D1B5D425CEDF99D6837D70B129AF69E615C52156 | |||
| 472 | cmd.exe | C:\Users\admin\Downloads\VARIETY_WOLFED_memberproposed.png | image | |
MD5:AC5263D4DB25DAB3CD3A621F6E63FF6C | SHA256:4E97B00B5A9A9858C789AEFE5CF917B17CB87EC2CC2B4760B2C12094DB611BFD | |||
| 472 | cmd.exe | C:\Users\admin\Downloads\copy_10422.bat | text | |
MD5:3BD308E6323FAE028E5EAD4AC2DB9B87 | SHA256:E4B92757DD9267E07F228888D1B5D425CEDF99D6837D70B129AF69E615C52156 | |||
| 472 | cmd.exe | C:\Users\admin\Downloads\copy_22643.bat | text | |
MD5:3BD308E6323FAE028E5EAD4AC2DB9B87 | SHA256:E4B92757DD9267E07F228888D1B5D425CEDF99D6837D70B129AF69E615C52156 | |||
| 472 | cmd.exe | C:\Users\admin\Downloads\copy_5794.bat | text | |
MD5:3BD308E6323FAE028E5EAD4AC2DB9B87 | SHA256:E4B92757DD9267E07F228888D1B5D425CEDF99D6837D70B129AF69E615C52156 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
97
TCP/UDP connections
108
DNS requests
23
Threats
241
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.159.128:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 400 | 20.190.159.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.159.131:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 404 | 162.159.137.232:443 | https://discord.com/api/webhooks/1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1 | unknown | binary | 45 b | whitelisted |
— | — | POST | 200 | 20.190.159.4:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 16.7 Kb | whitelisted |
— | — | POST | 404 | 162.159.137.232:443 | https://discord.com/api/webhooks/1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1 | unknown | binary | 45 b | whitelisted |
— | — | POST | 200 | 40.126.31.131:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 404 | 162.159.135.232:443 | https://discord.com/api/webhooks/1385864776902774865/NxFnzjTjNF0AFMRMbF63CBItfiGK1xQaLlpolNP5QAbGKVfs4h48tJsrLB-XoxUgYlA1 | unknown | binary | 45 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.55.104.172:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3100 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2876 | powershell.exe | 162.159.128.233:443 | discord.com | CLOUDFLARENET | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
discord.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
2876 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2876 | powershell.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Discord |
2876 | powershell.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
2200 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7856 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
7856 | powershell.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
7856 | powershell.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Discord |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |