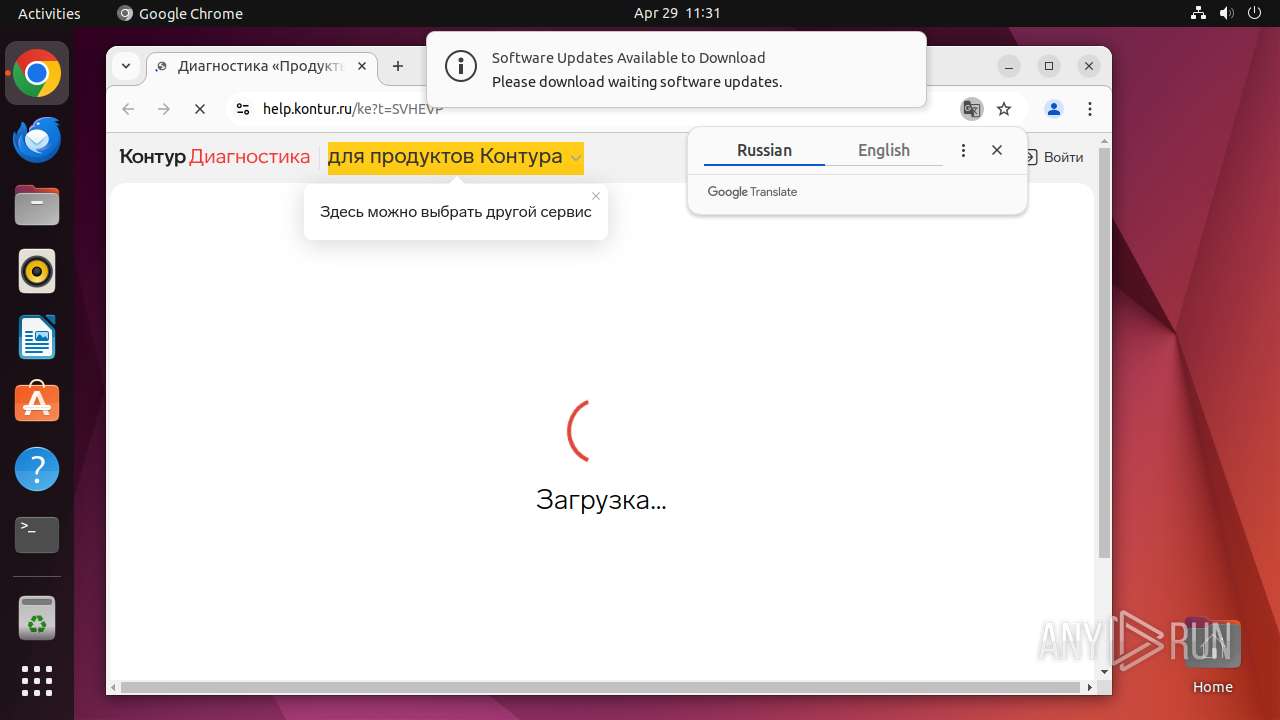
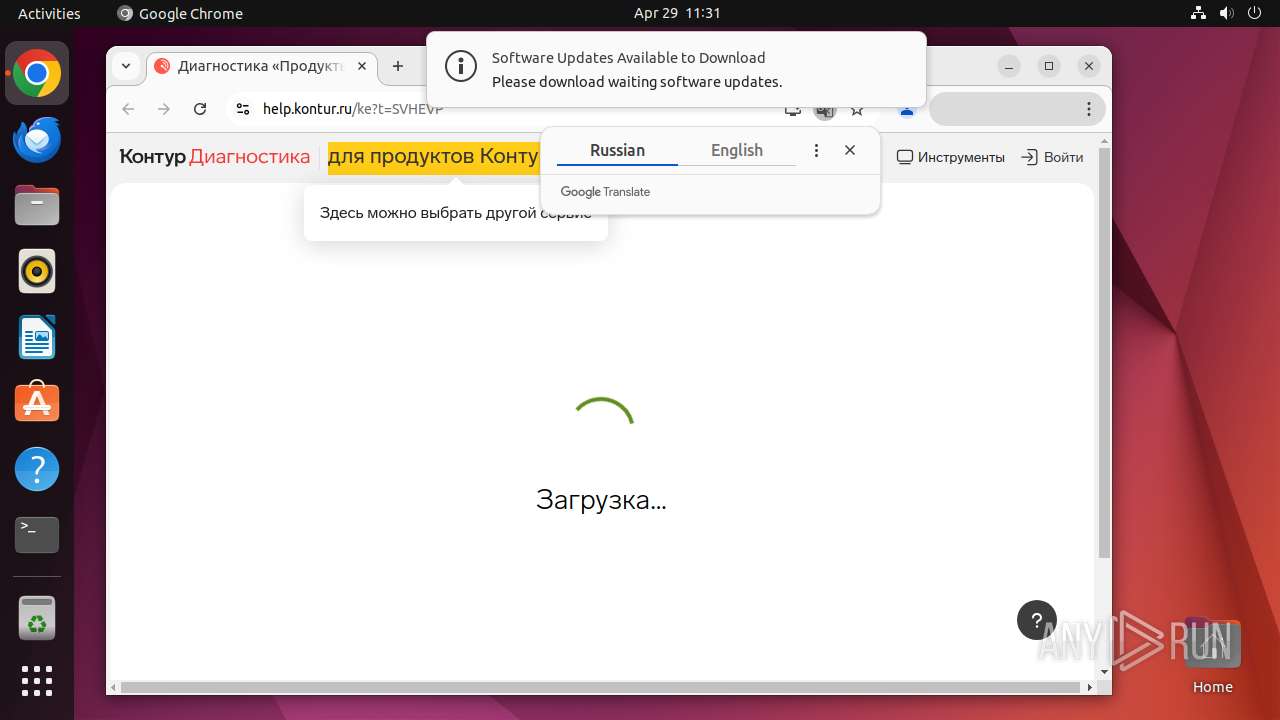
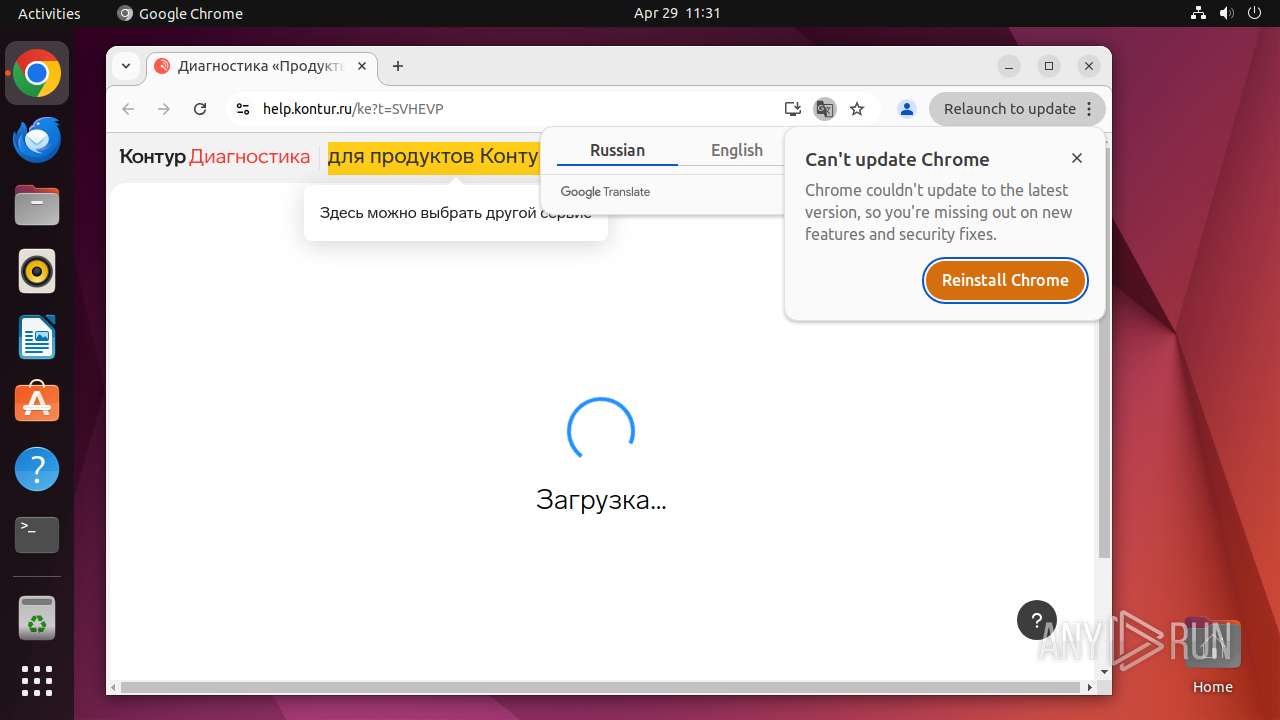
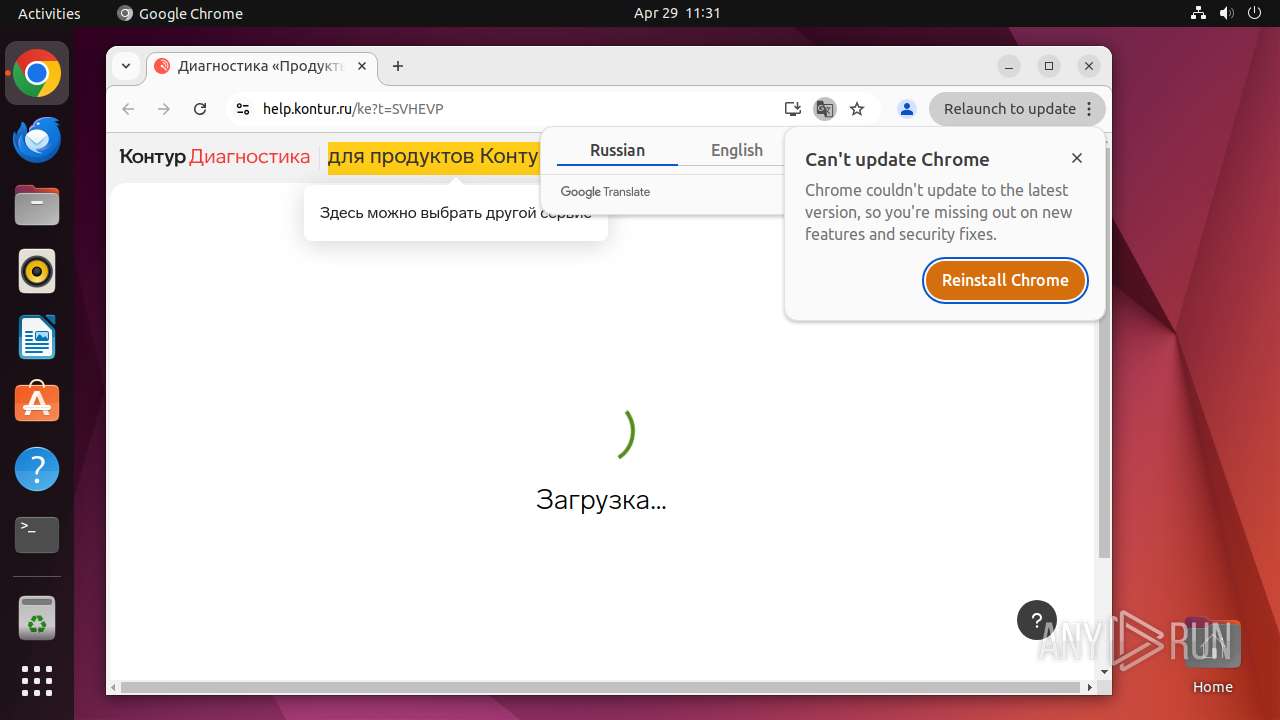
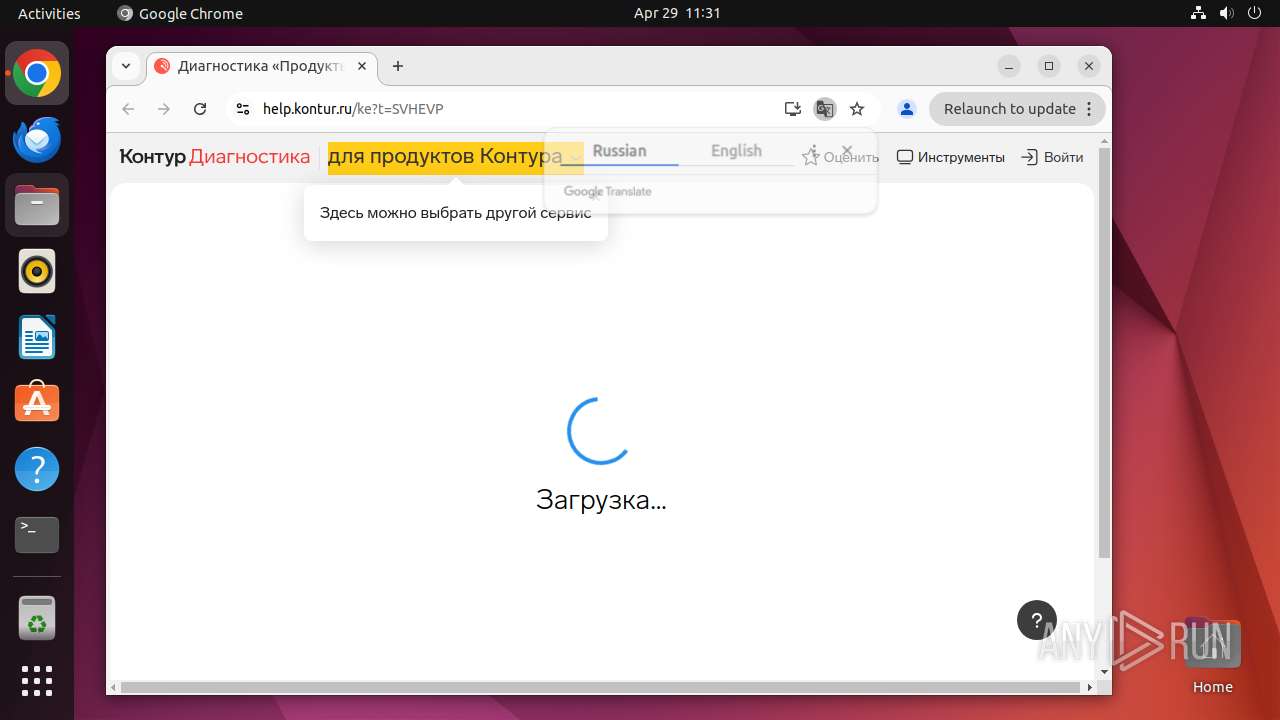
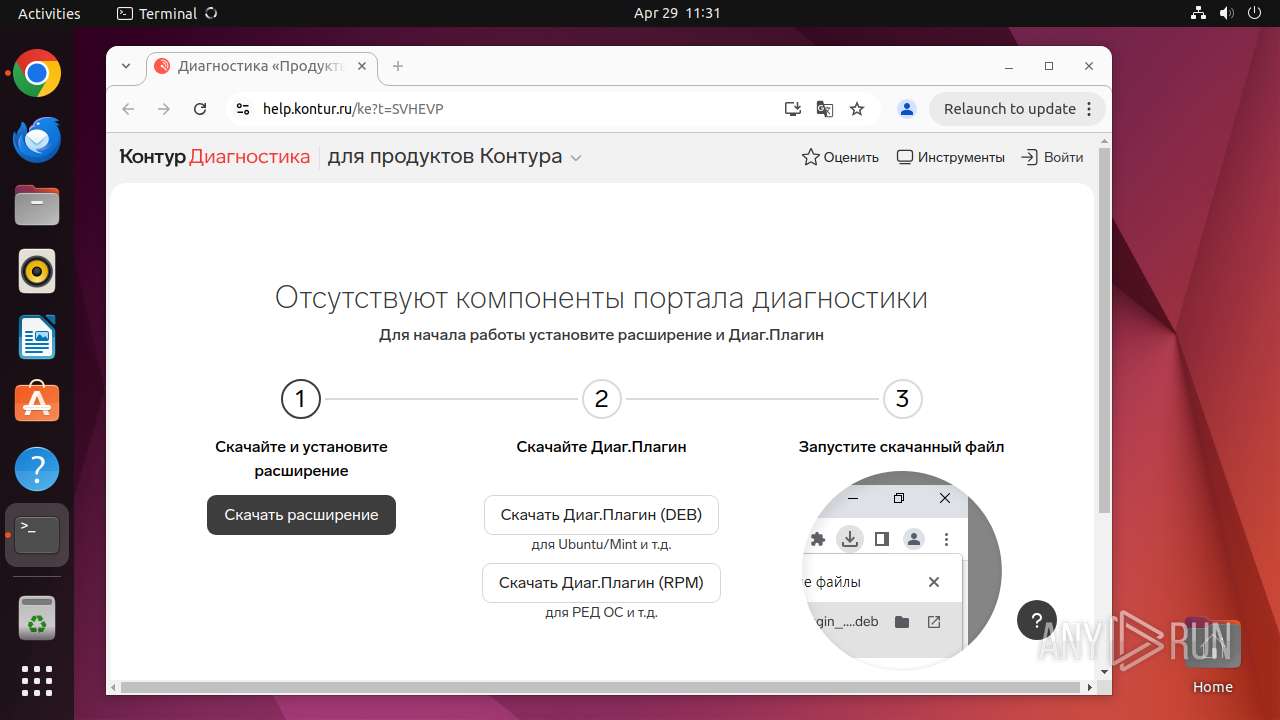
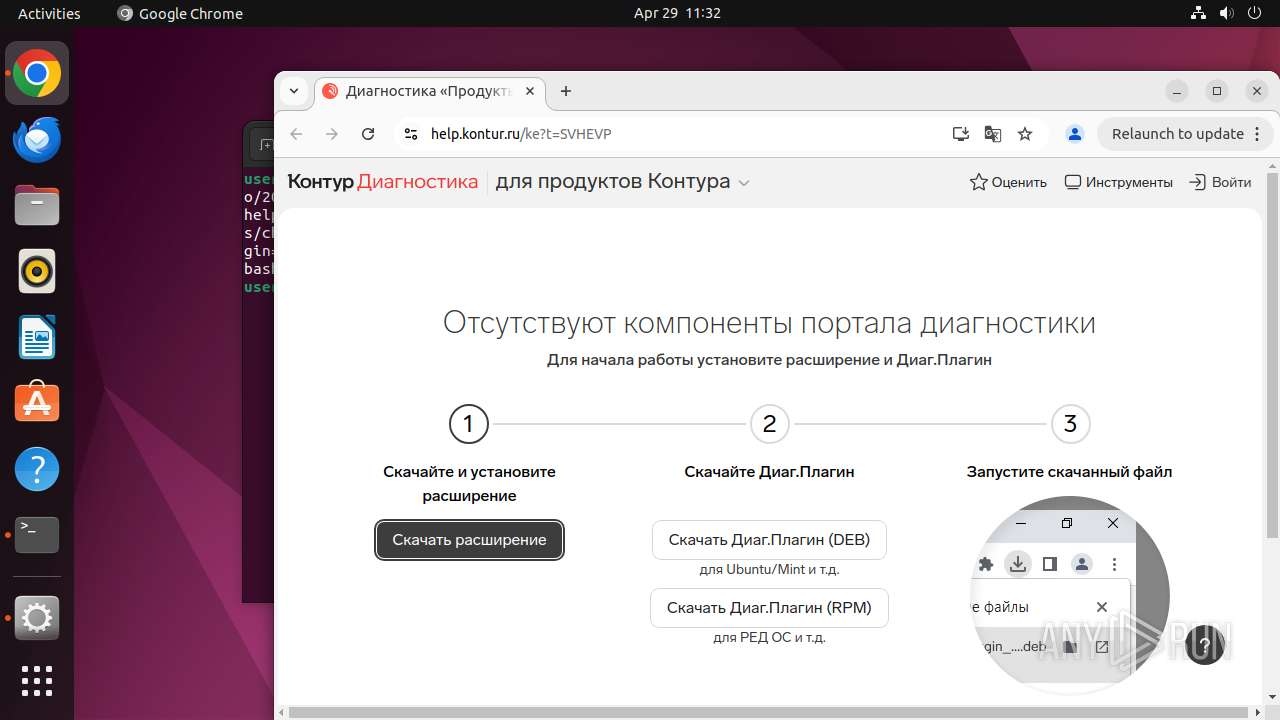
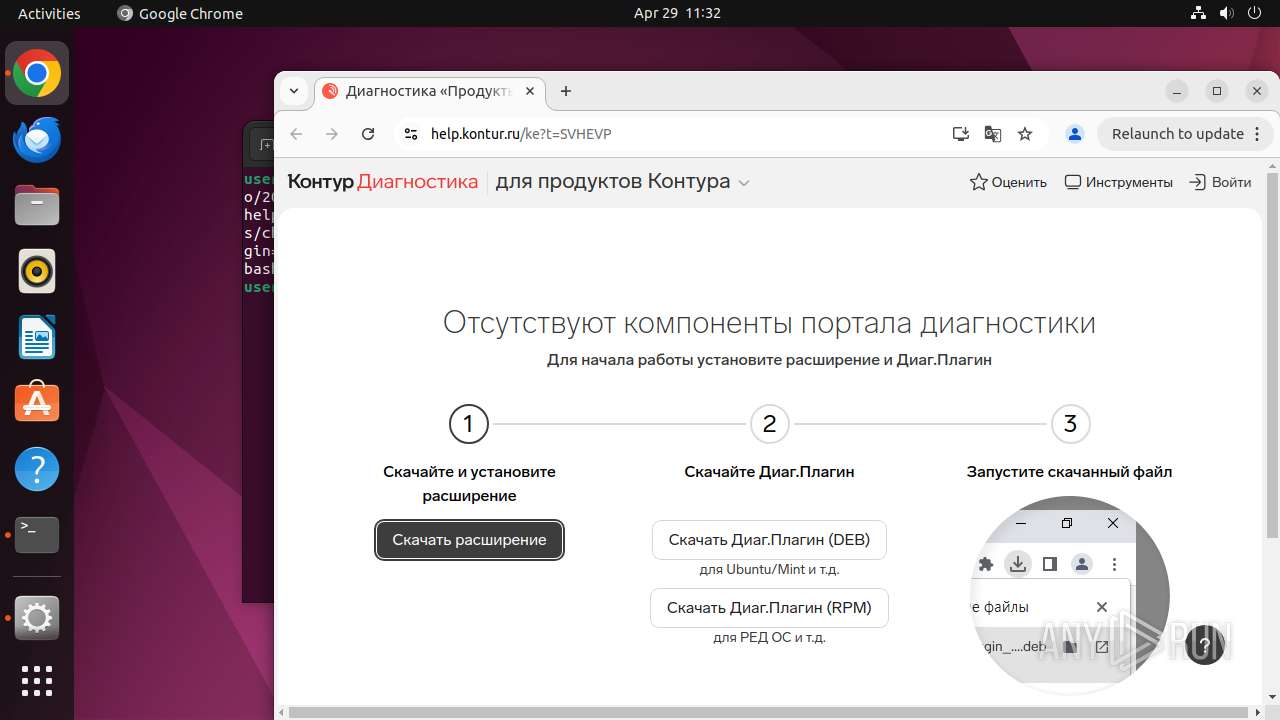
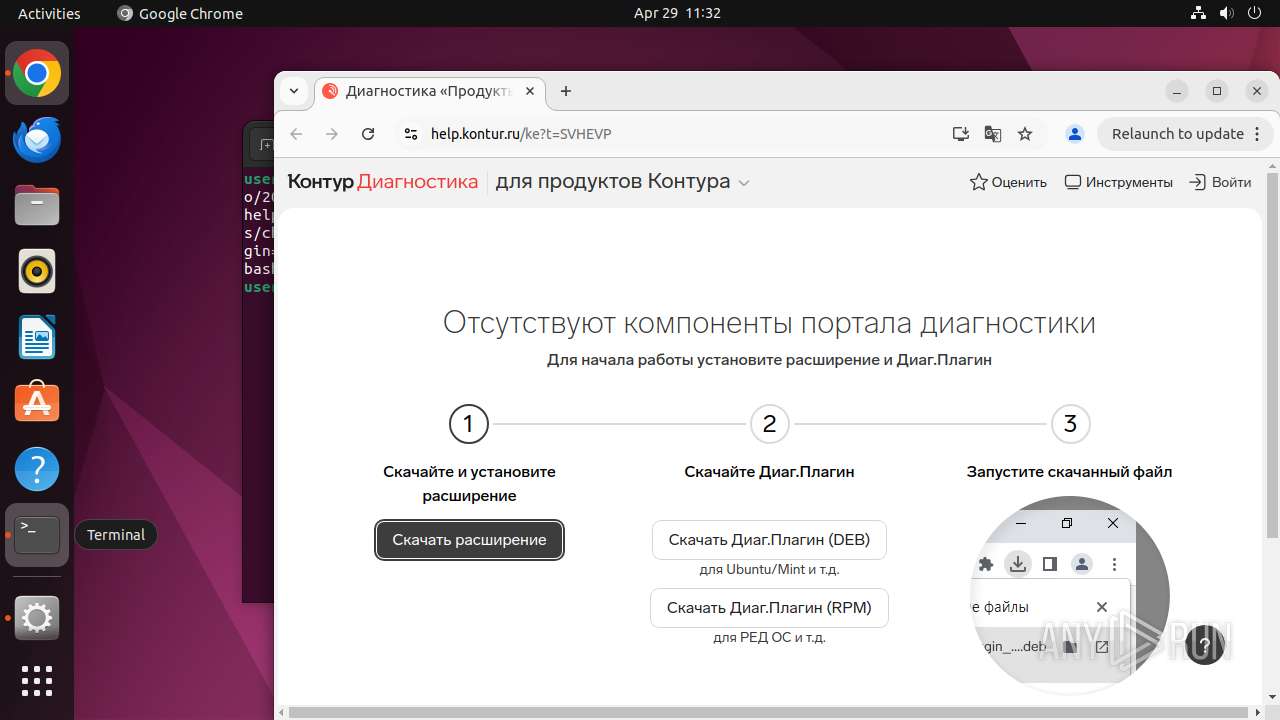
| URL: | https://help.kontur.ru |
| Full analysis: | https://app.any.run/tasks/e86a6760-2cfc-4d78-ba75-b05ecd5f23f5 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 10:30:55 |
| OS: | Ubuntu 22.04.2 |
| Indicators: | |
| MD5: | 6BC7BA7505DA0C125CBFF96A2A4B30D5 |
| SHA1: | FCB96E5174B04B7207C04F1CC0FCEAC1C30D212B |
| SHA256: | E4B48F1328212A8EAD5D21BA74D74DFD40A04B740D23C735D84C46D335DA3AF3 |
| SSDEEP: | 3:N88vlMsn:28NRn |
MALICIOUS
No malicious indicators.SUSPICIOUS
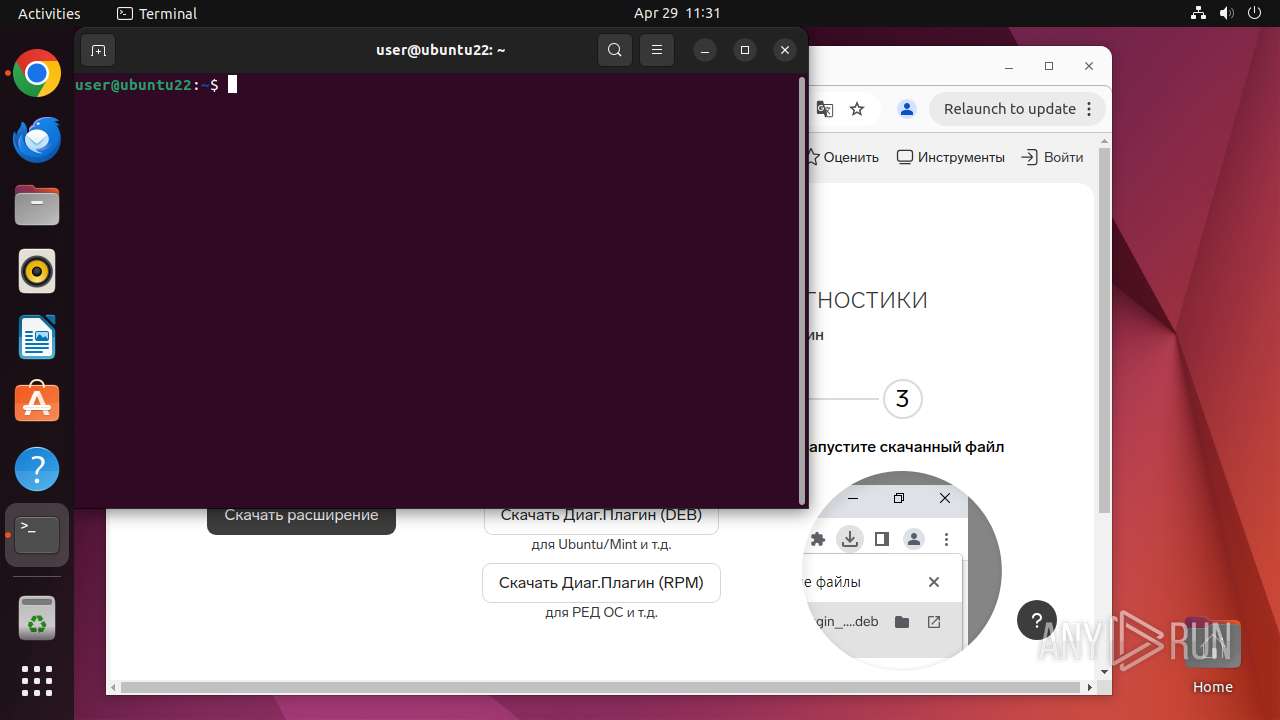
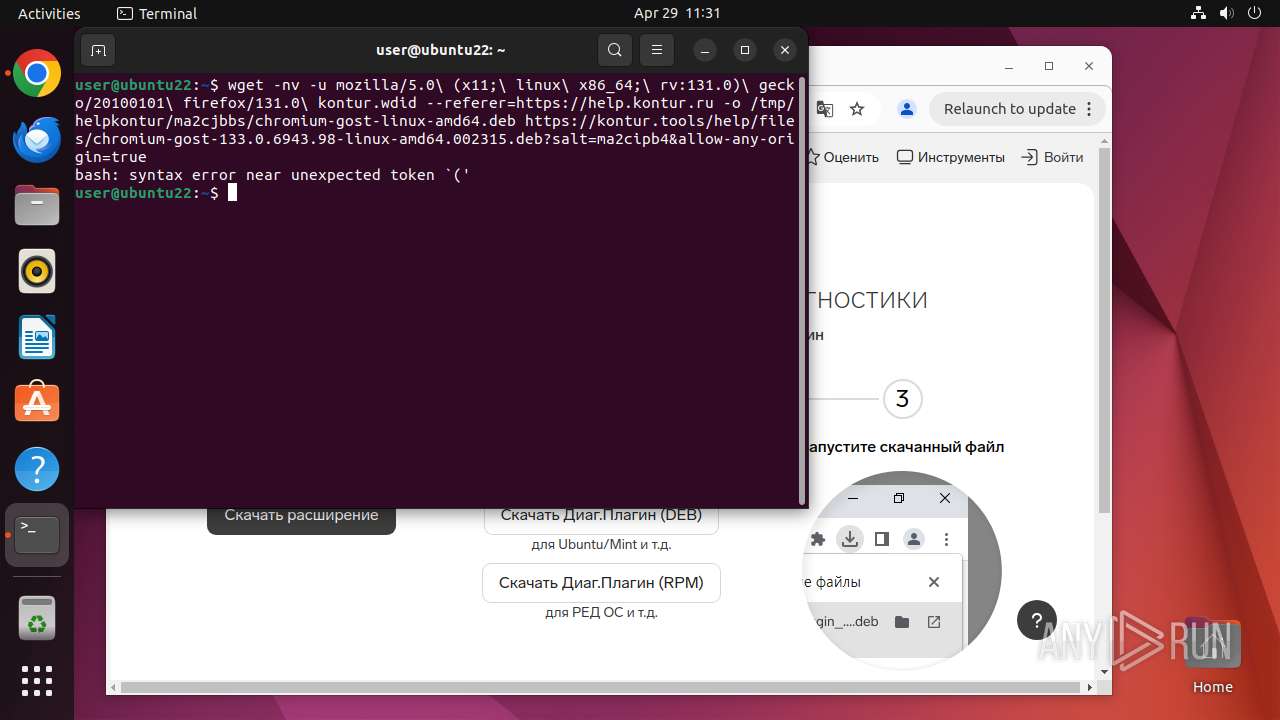
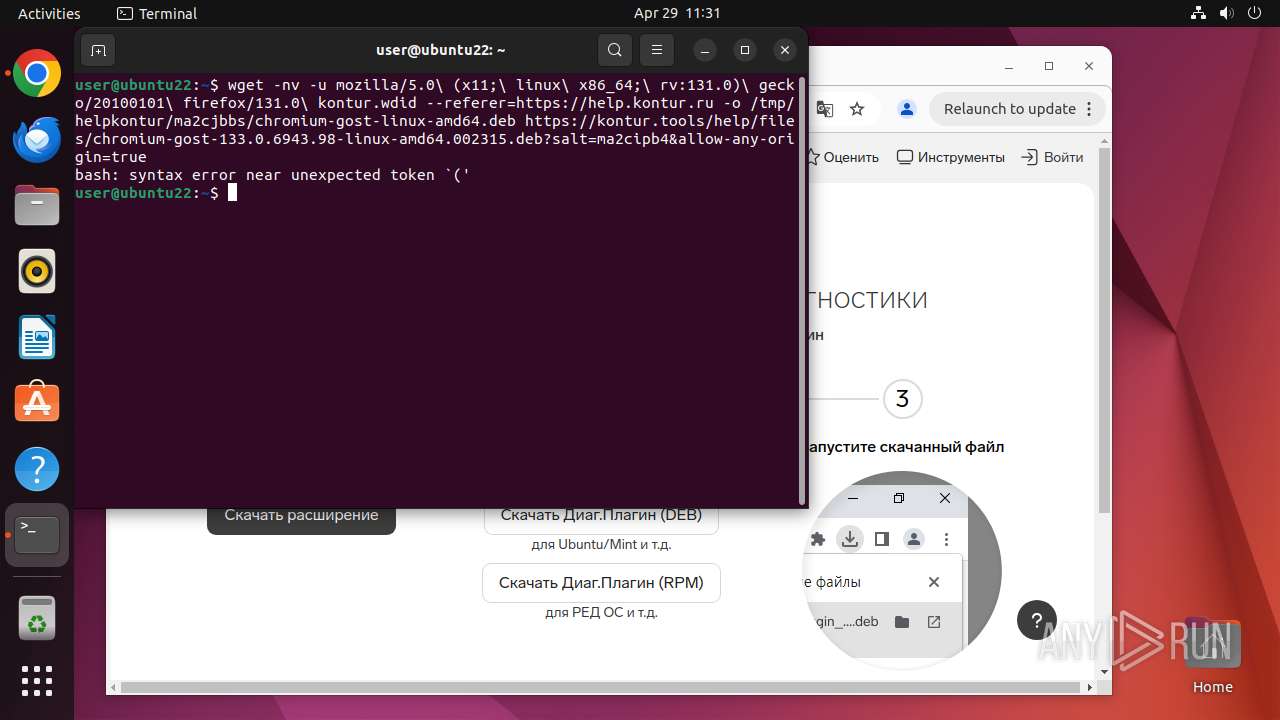
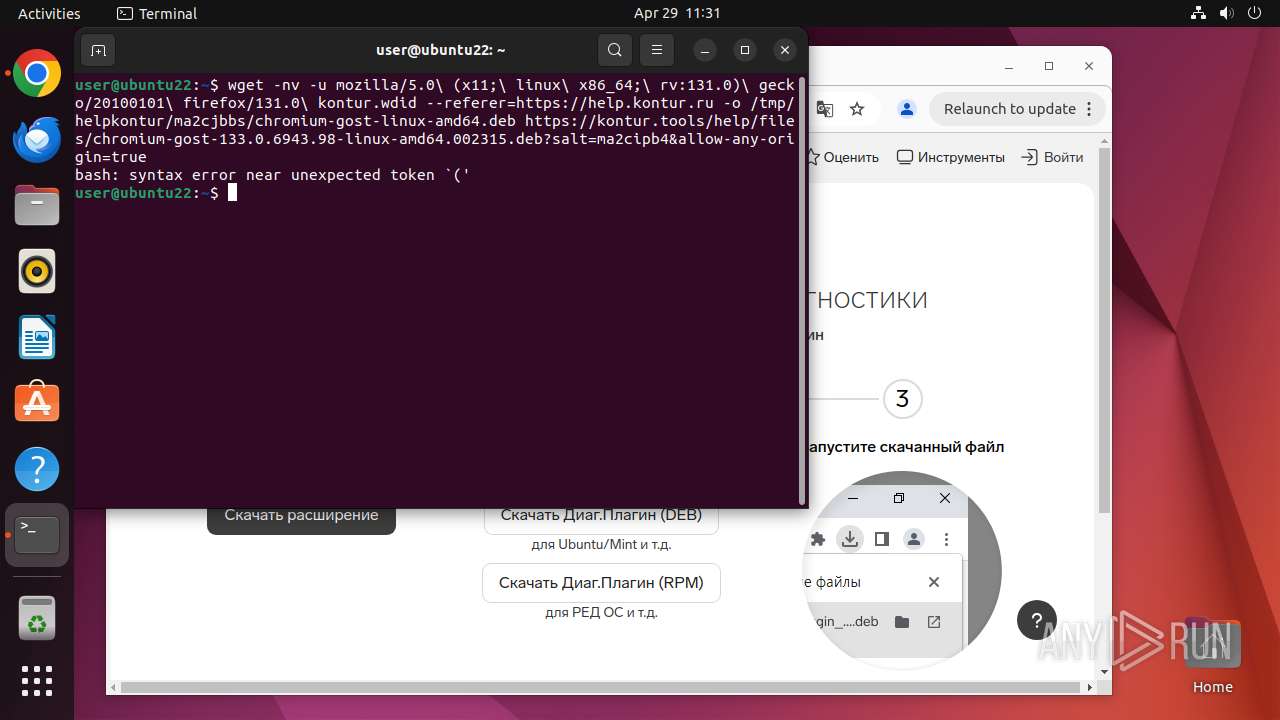
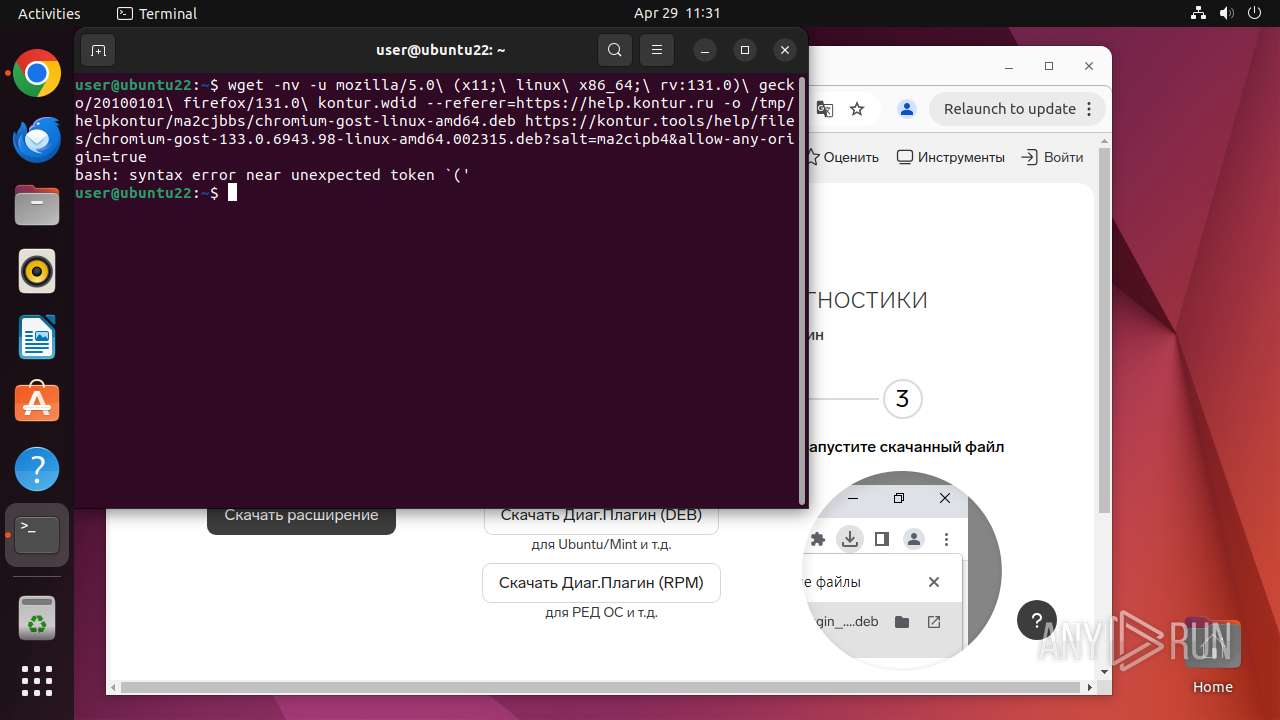
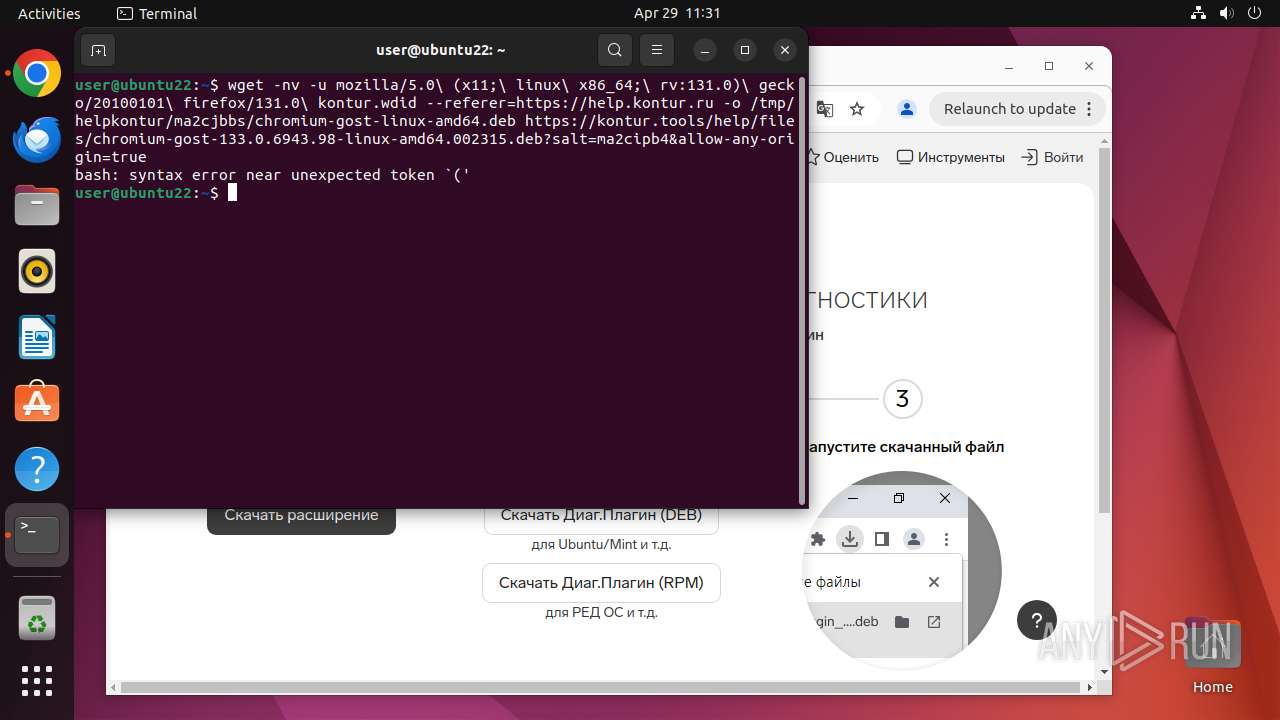
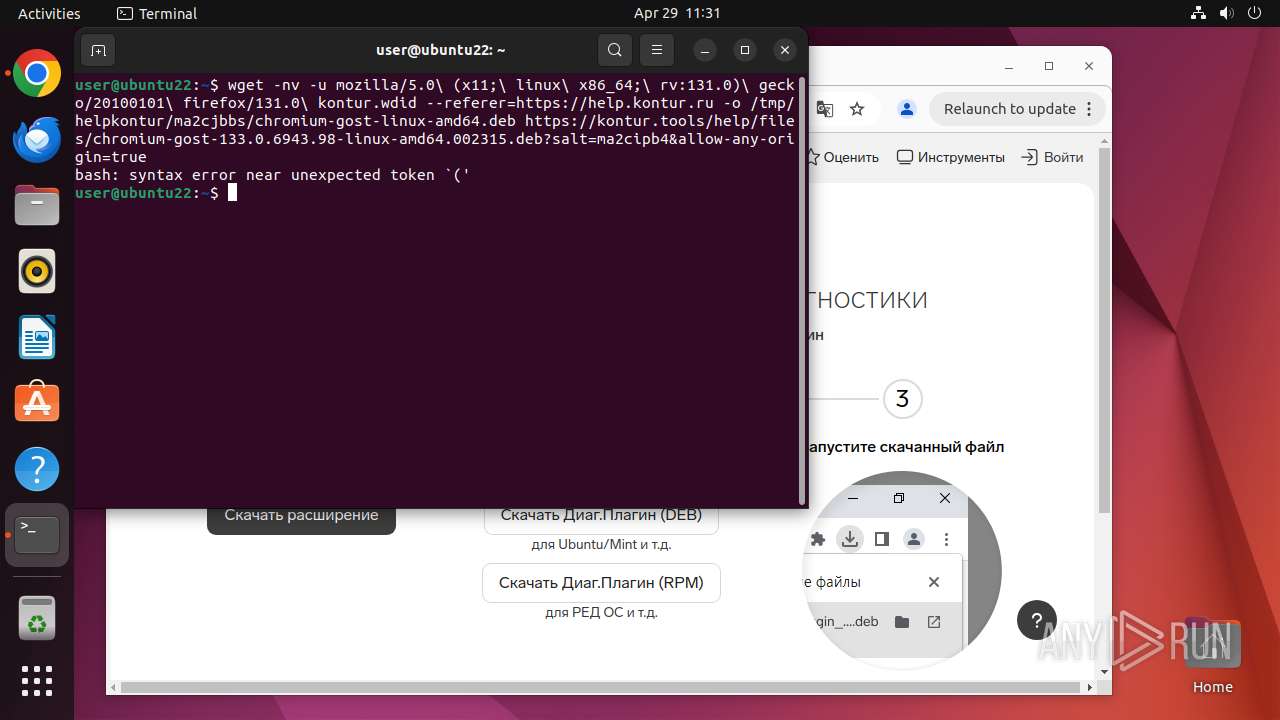
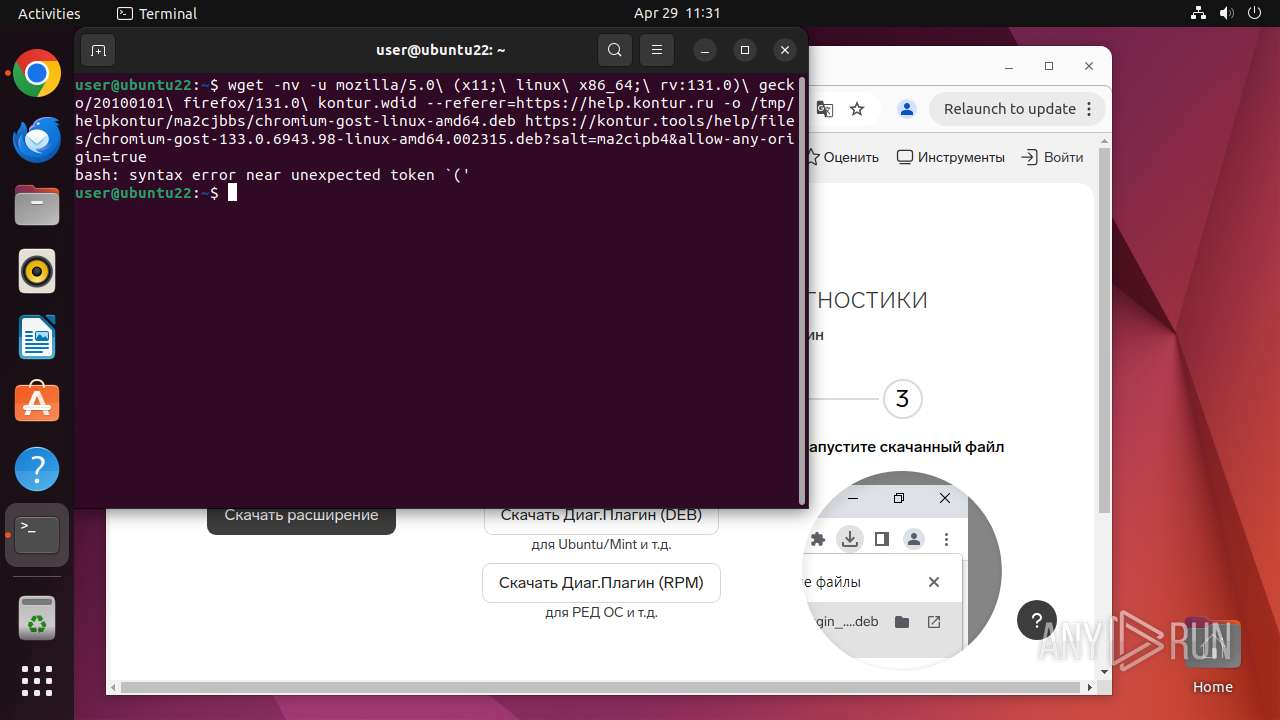
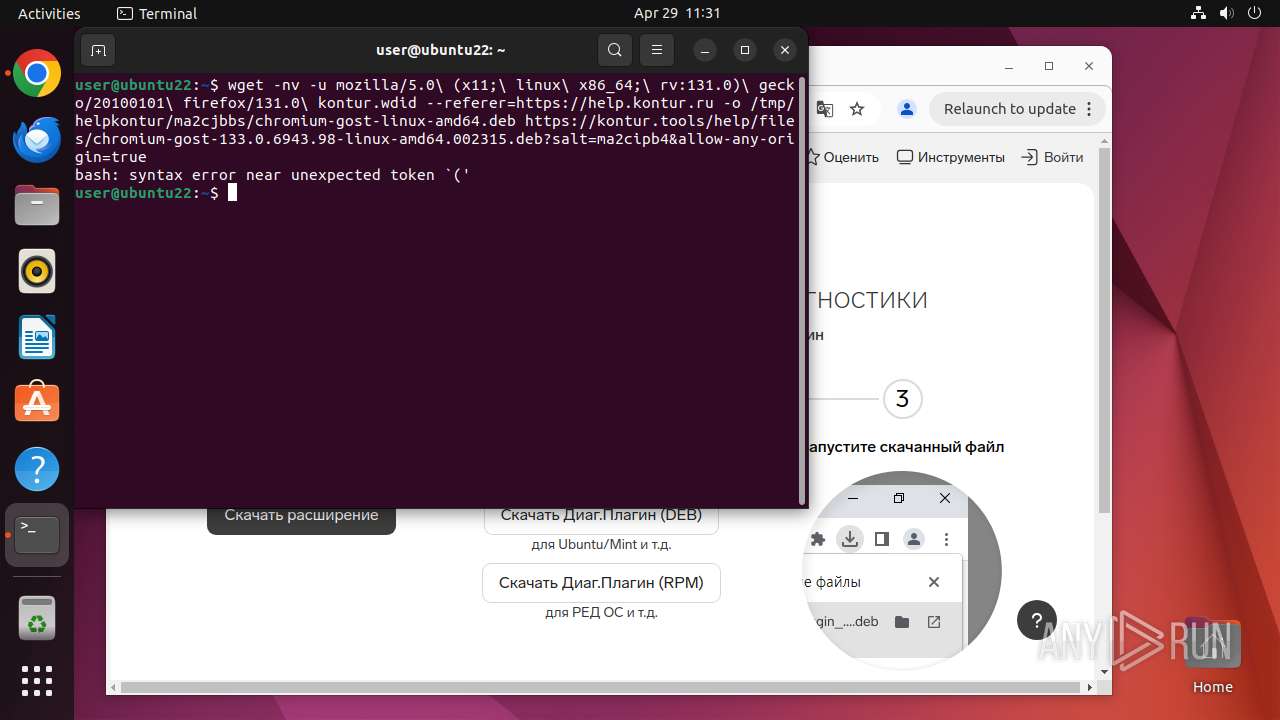
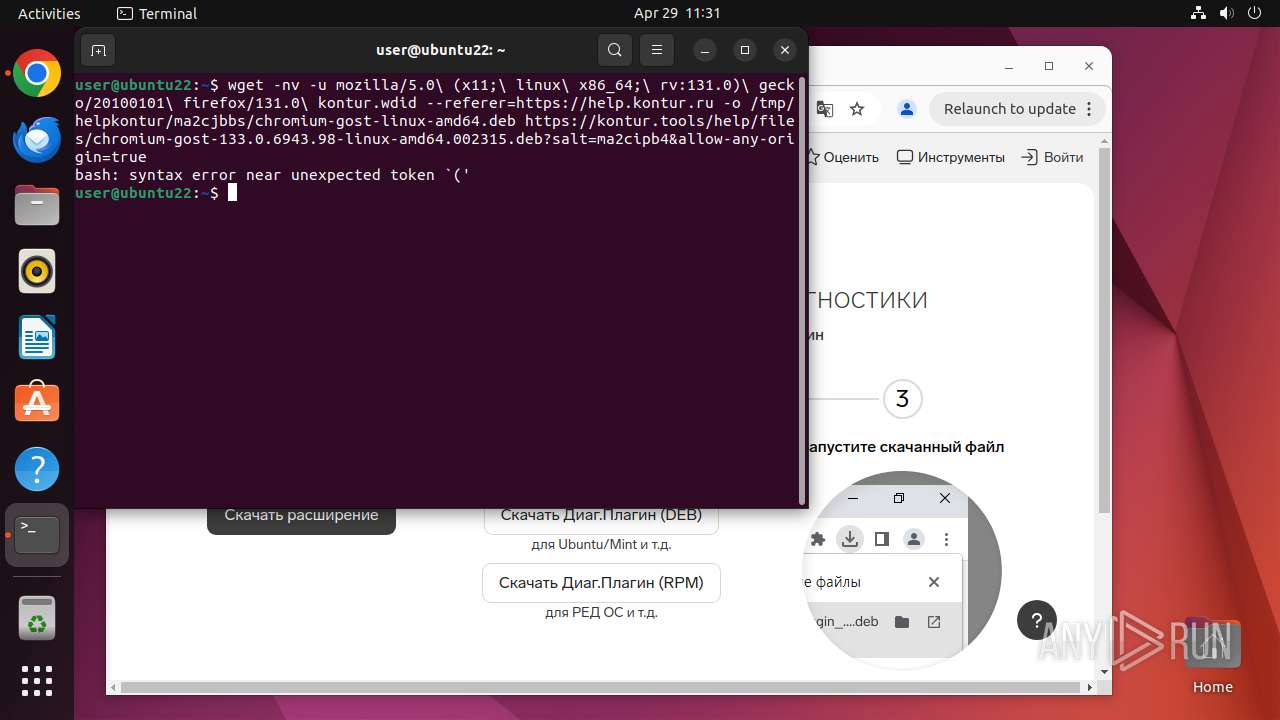
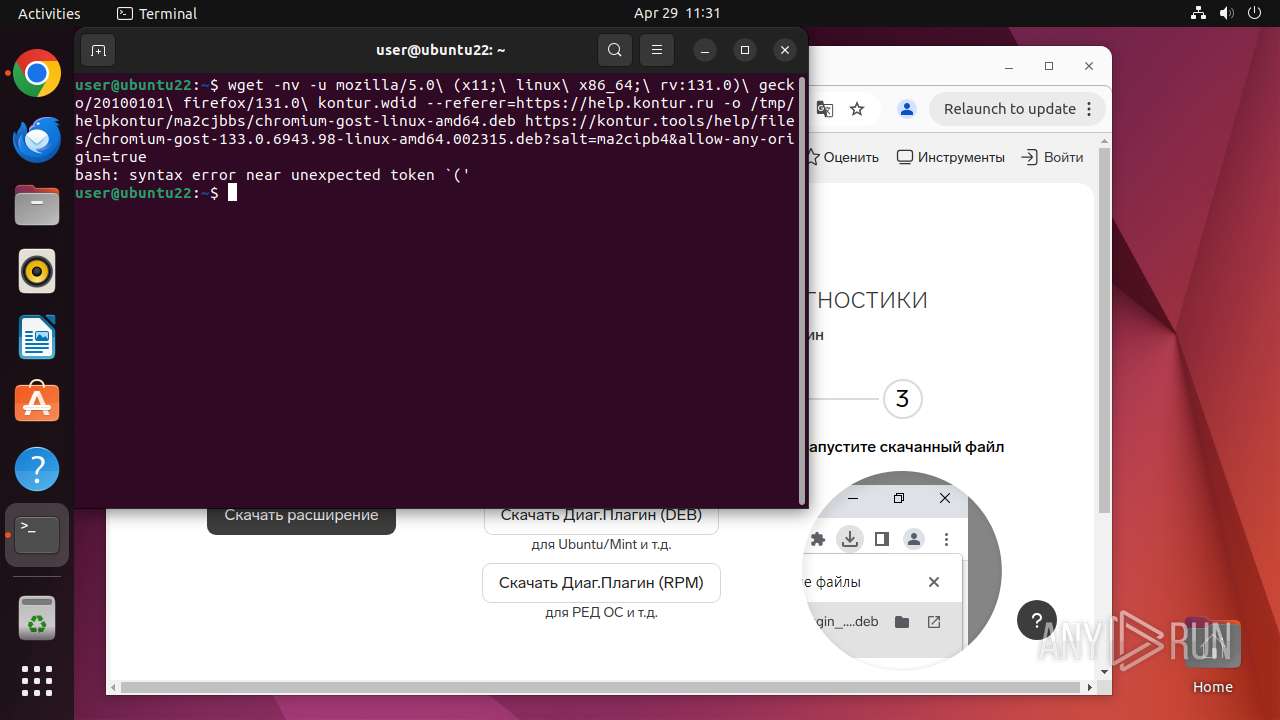
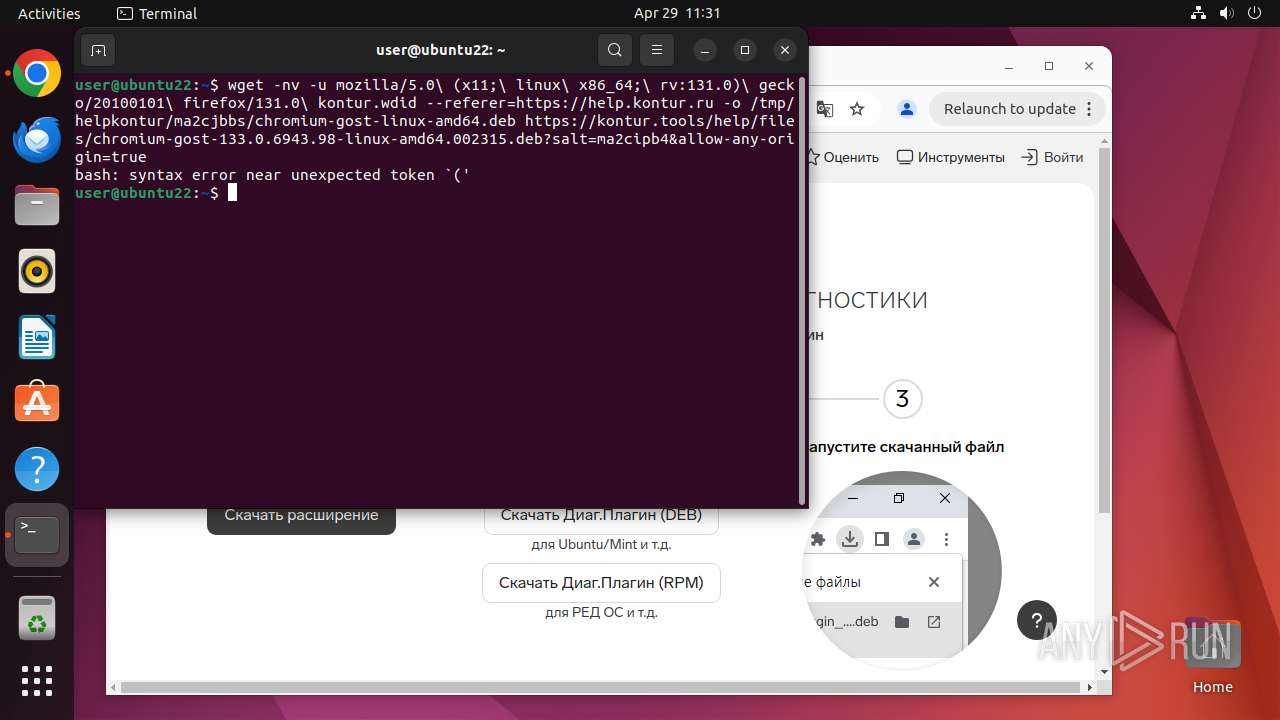
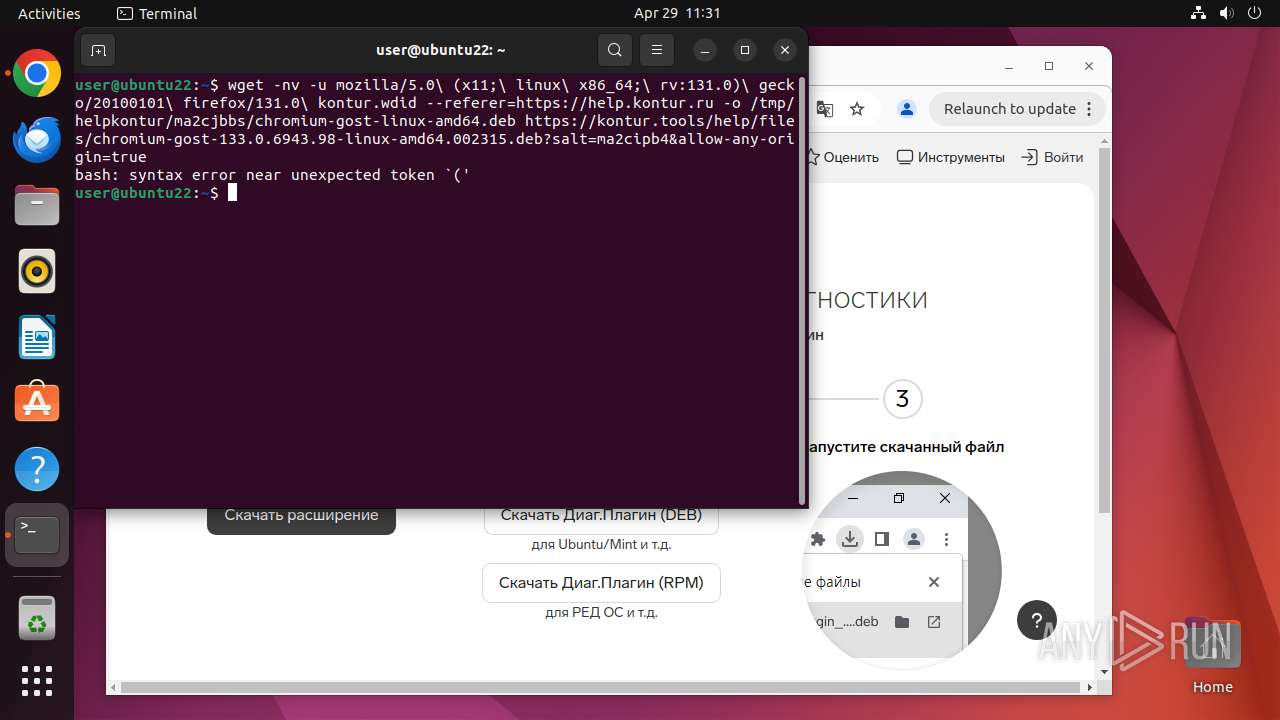
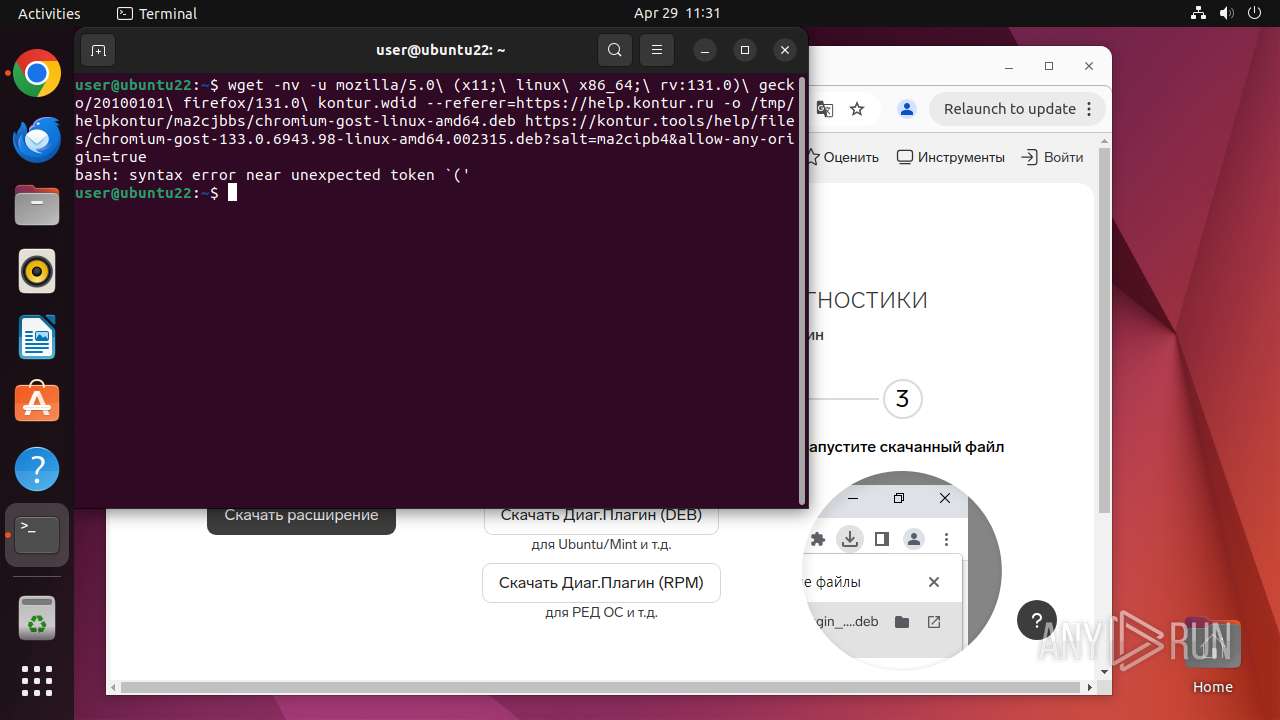
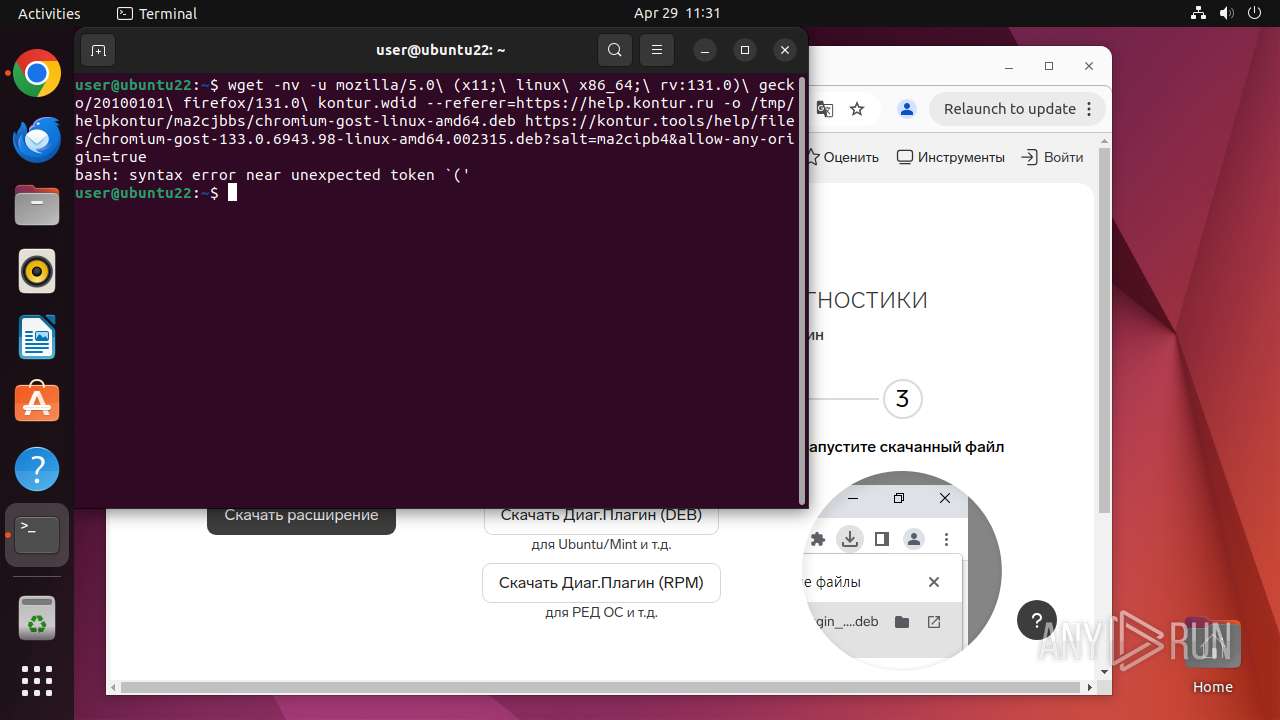
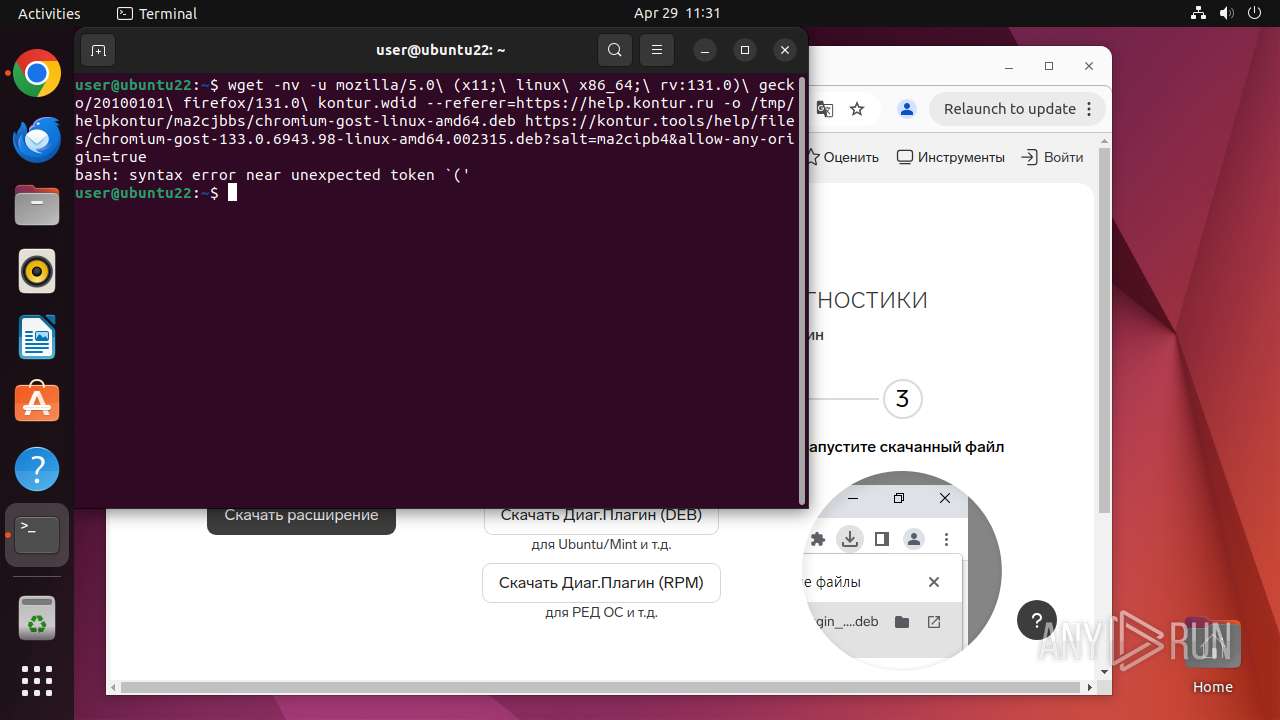
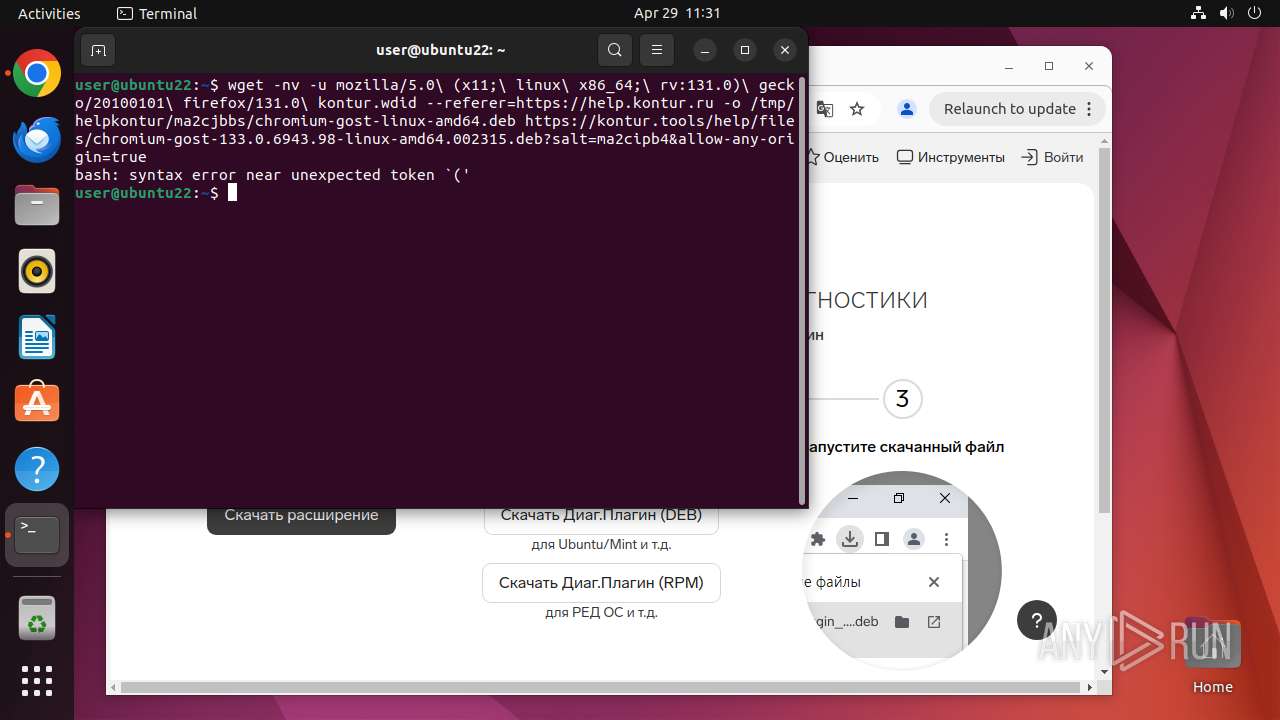
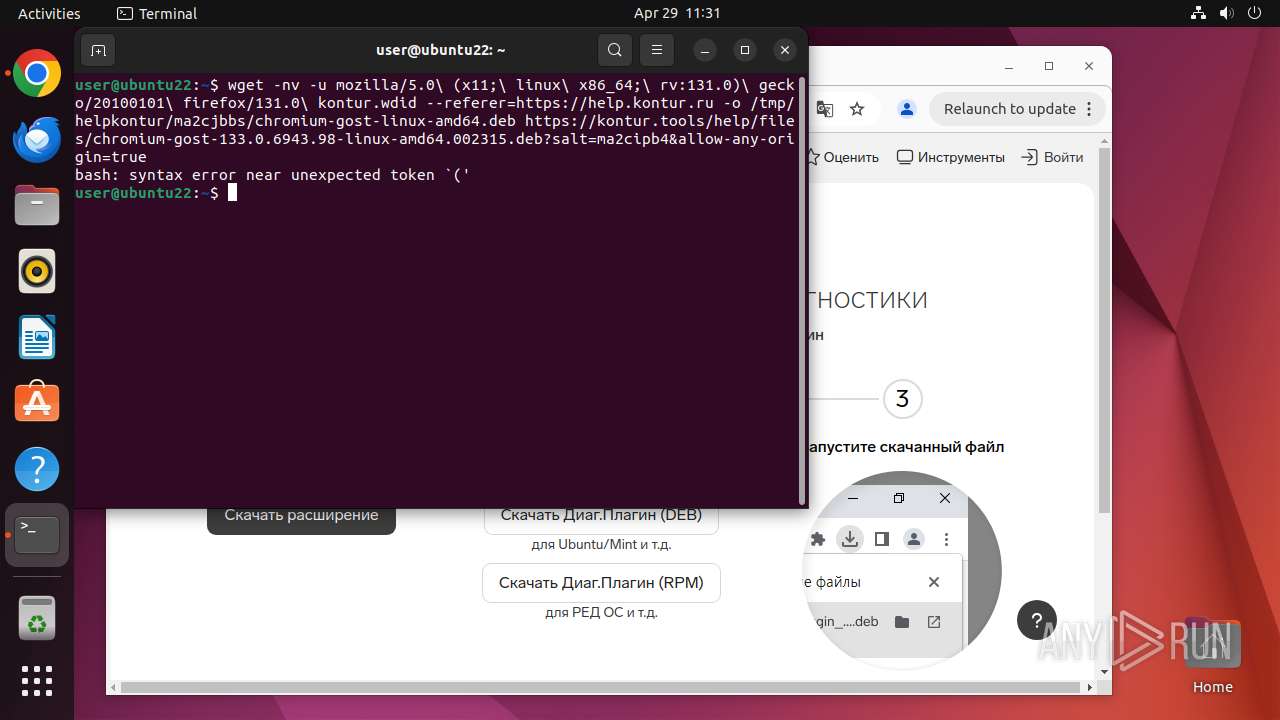
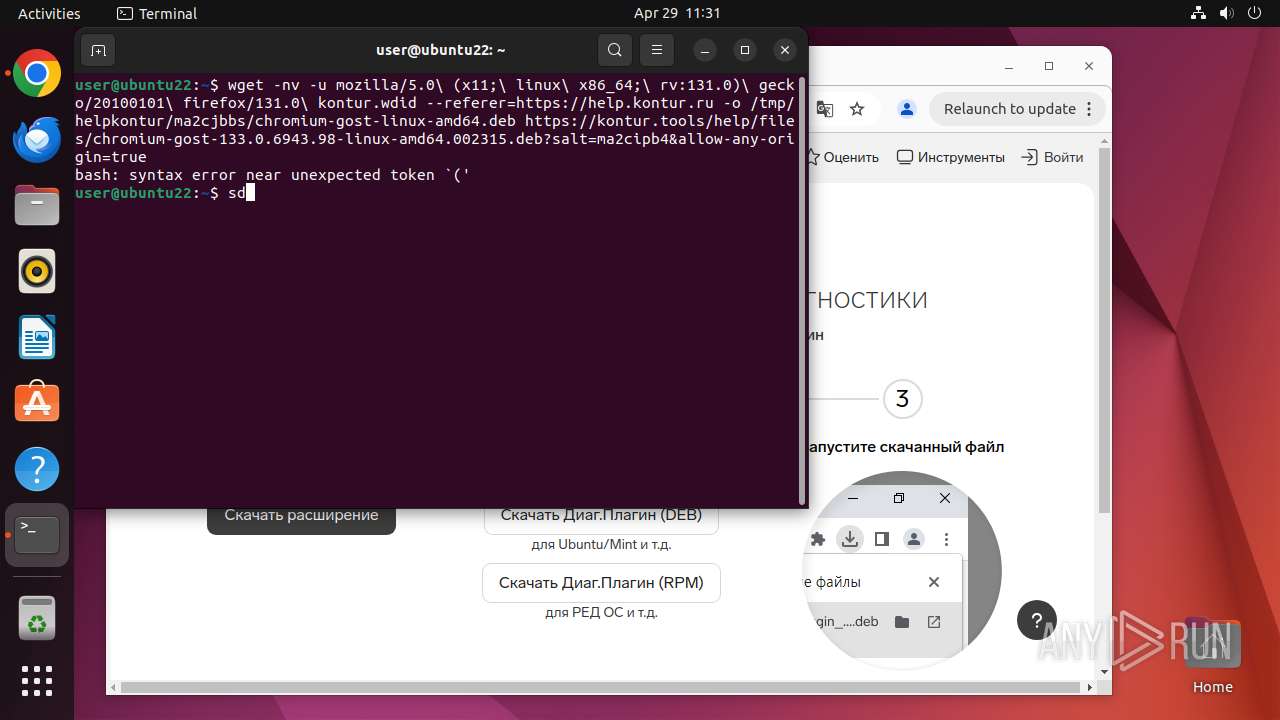
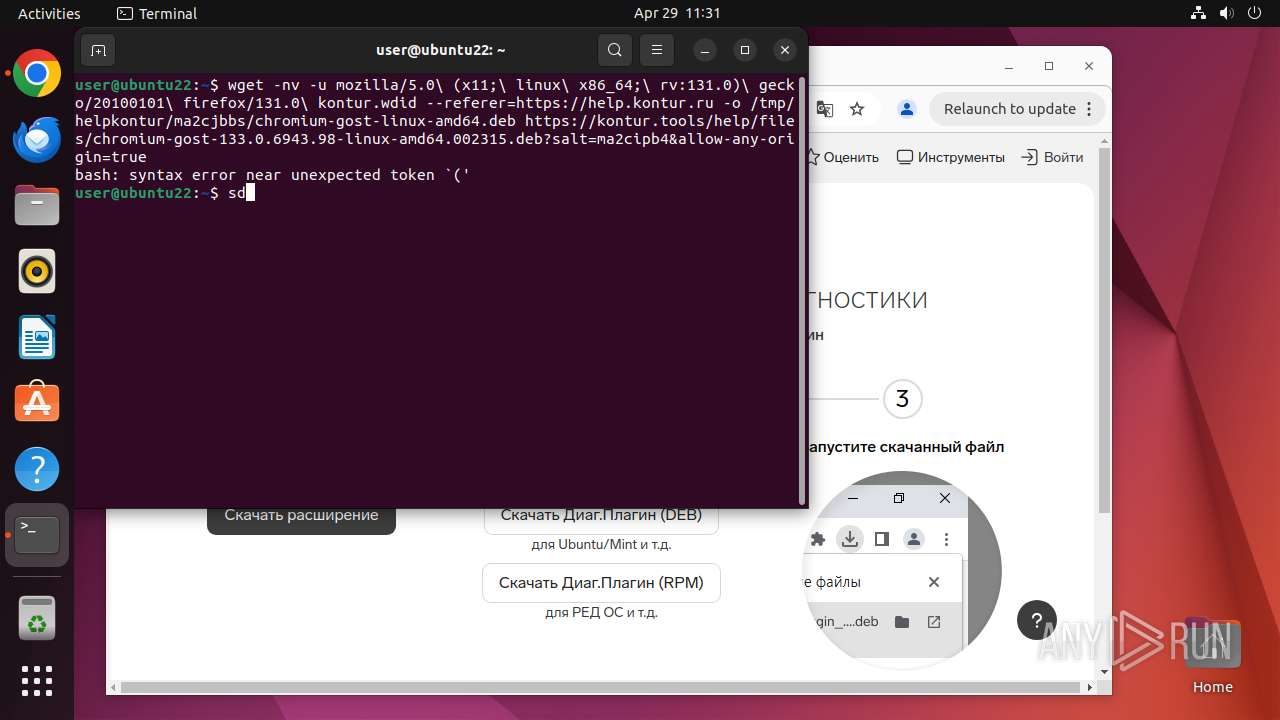
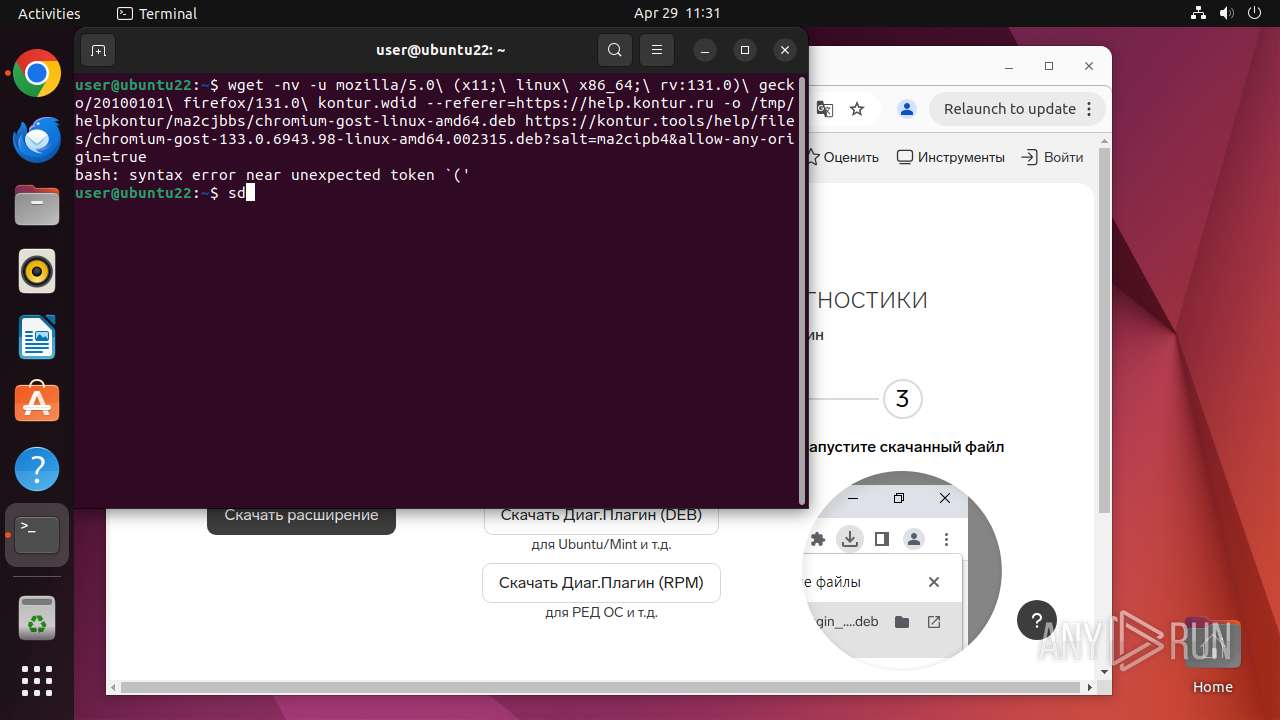
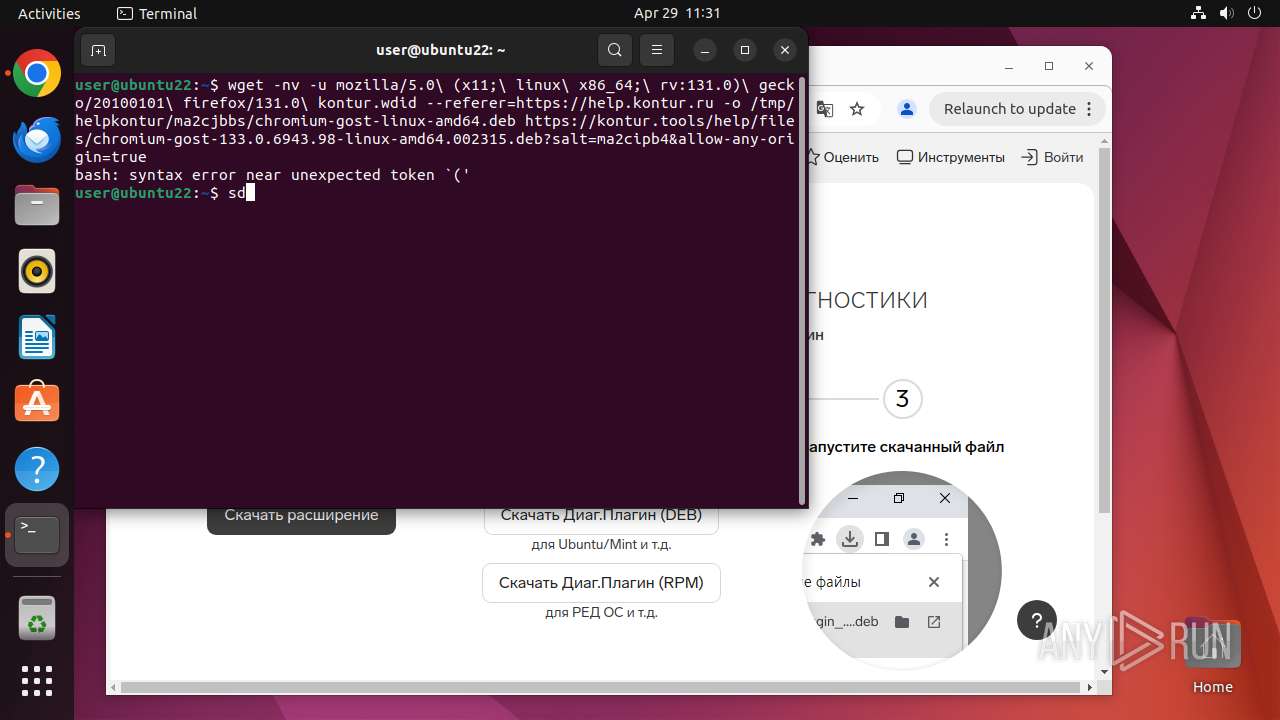
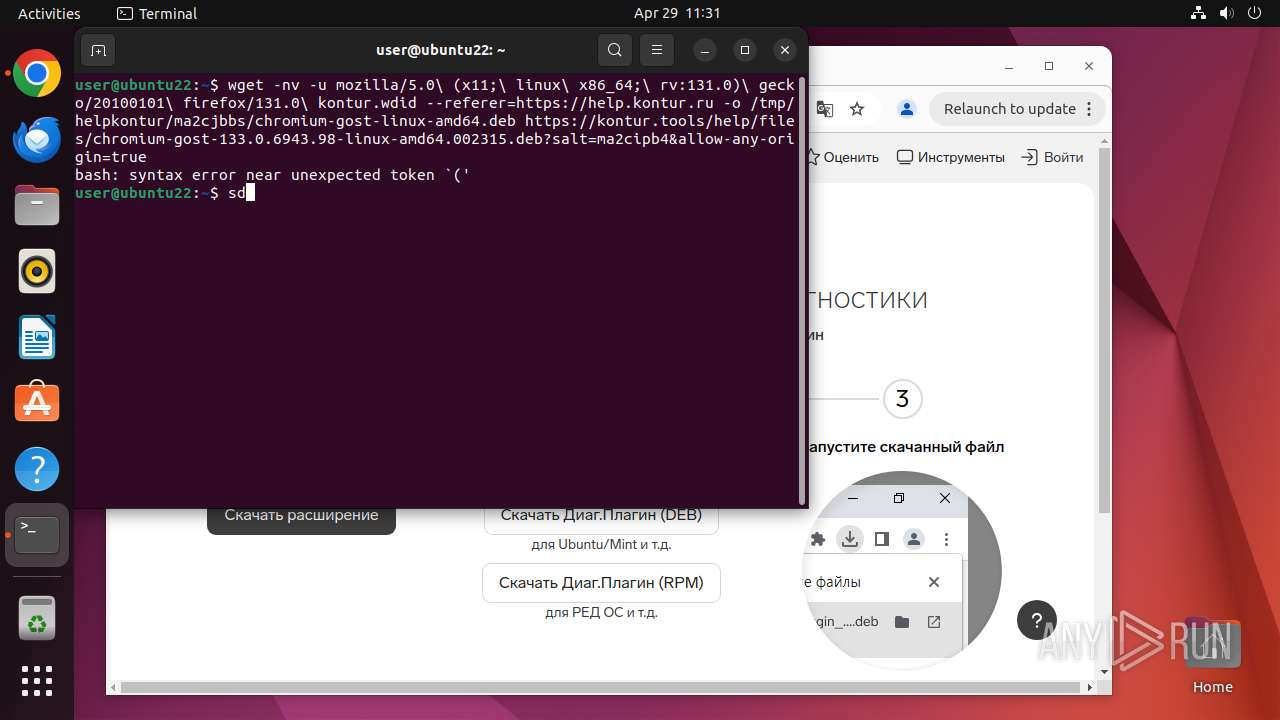
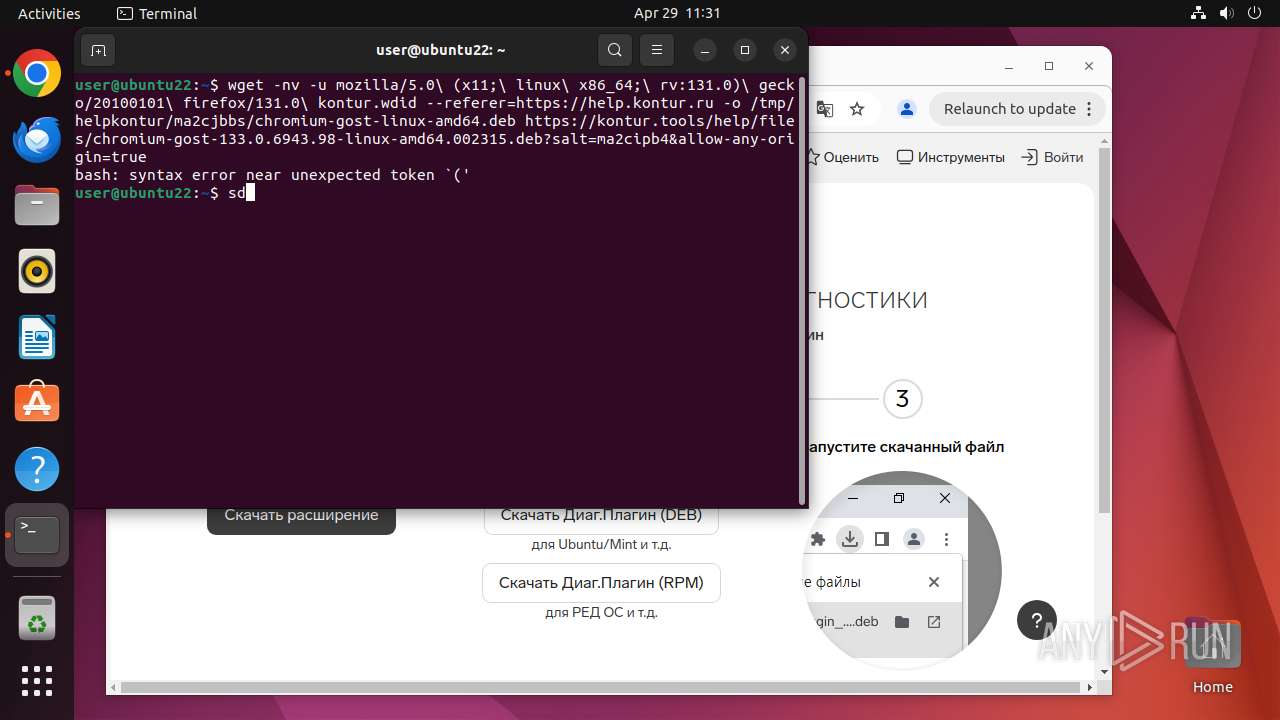
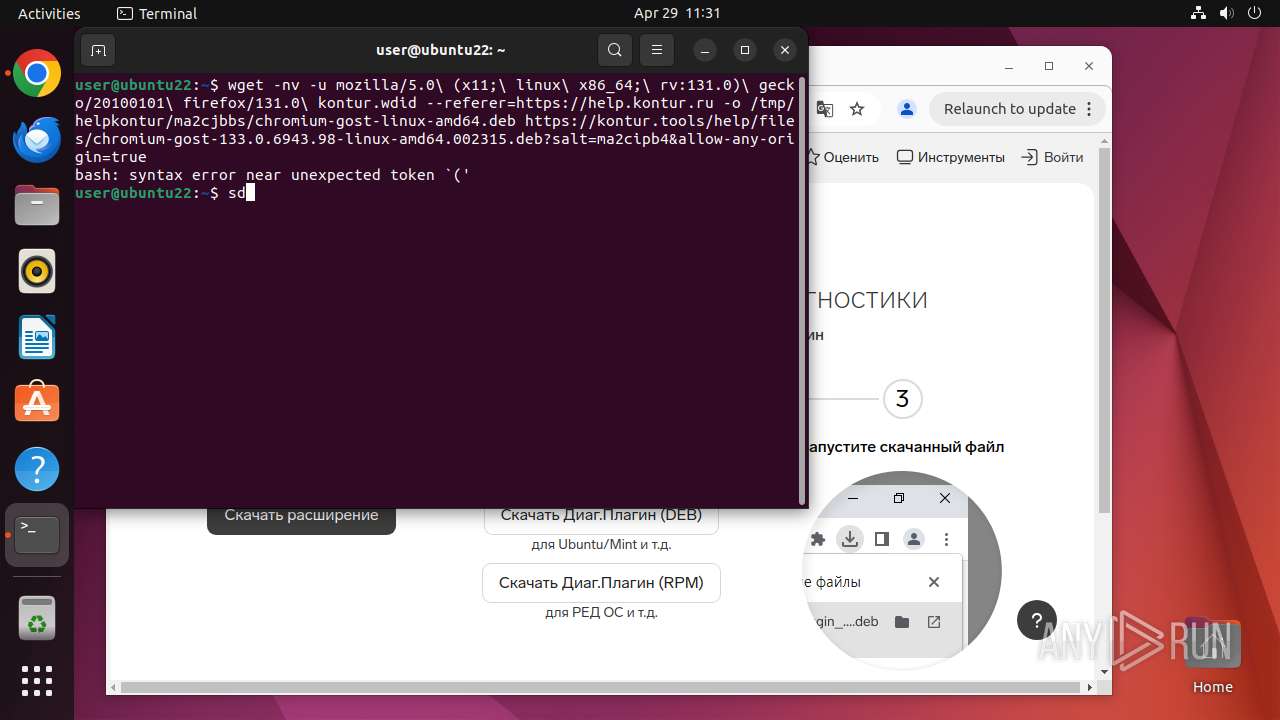
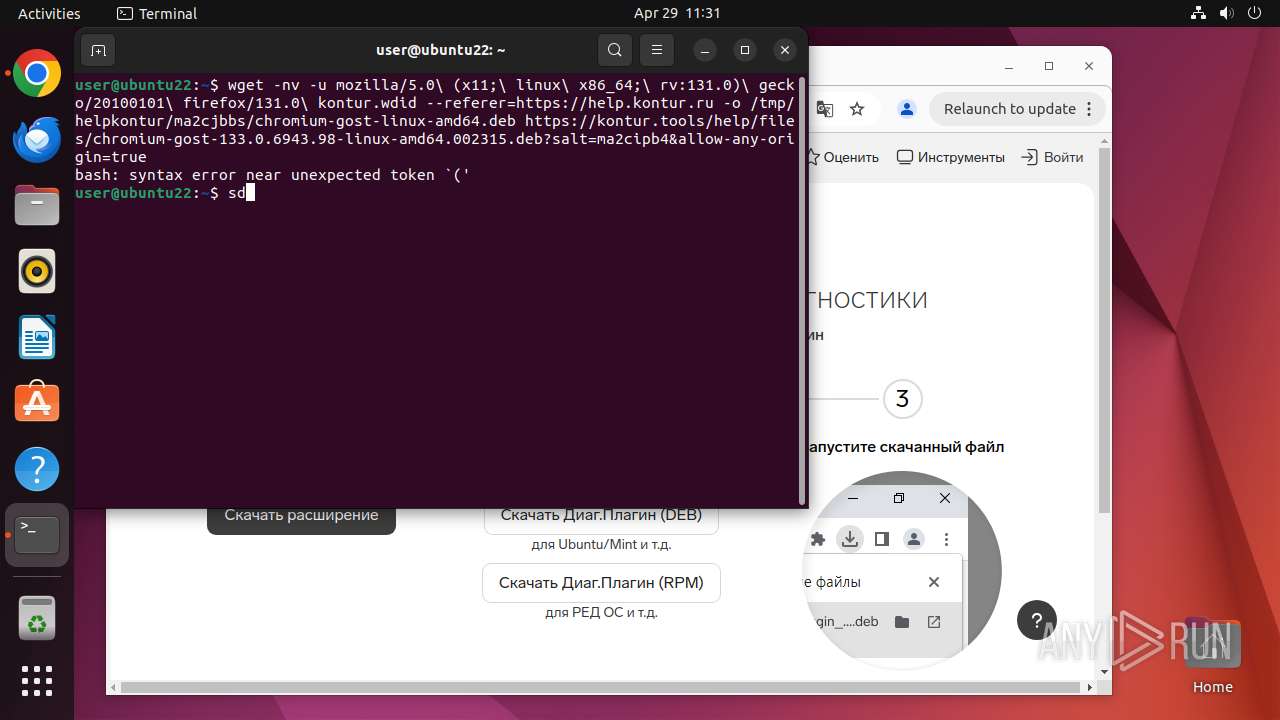
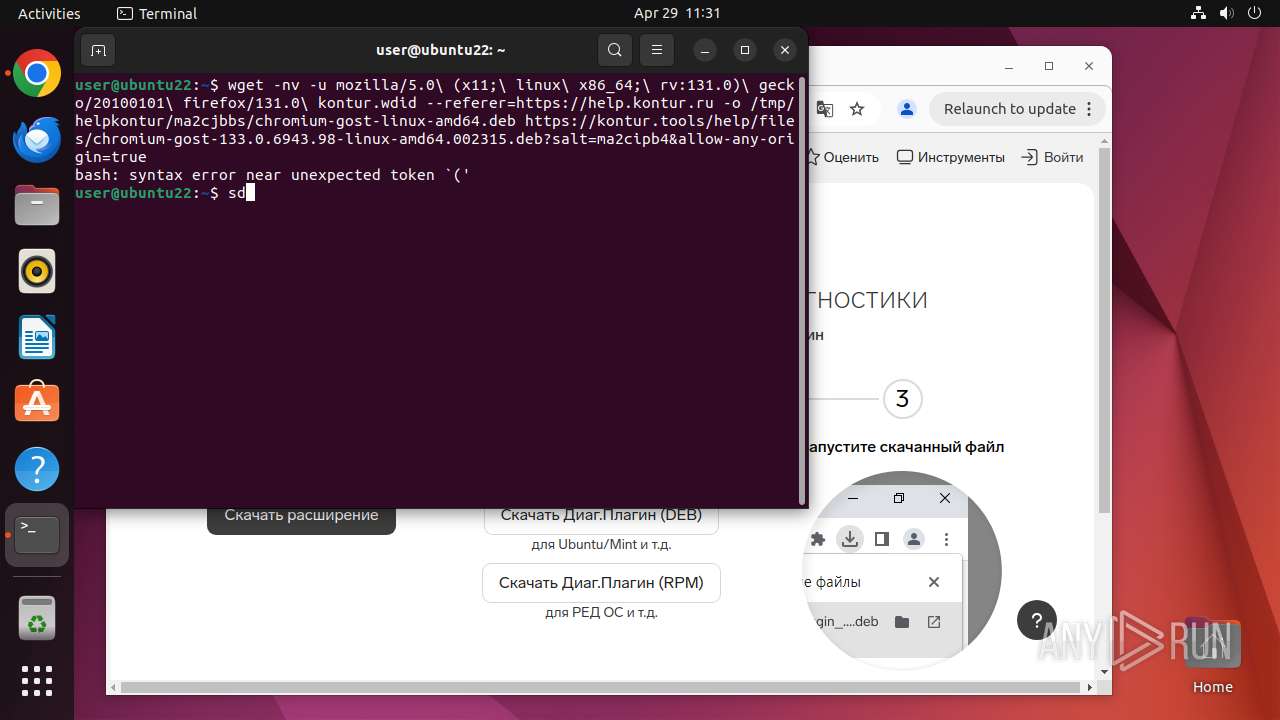
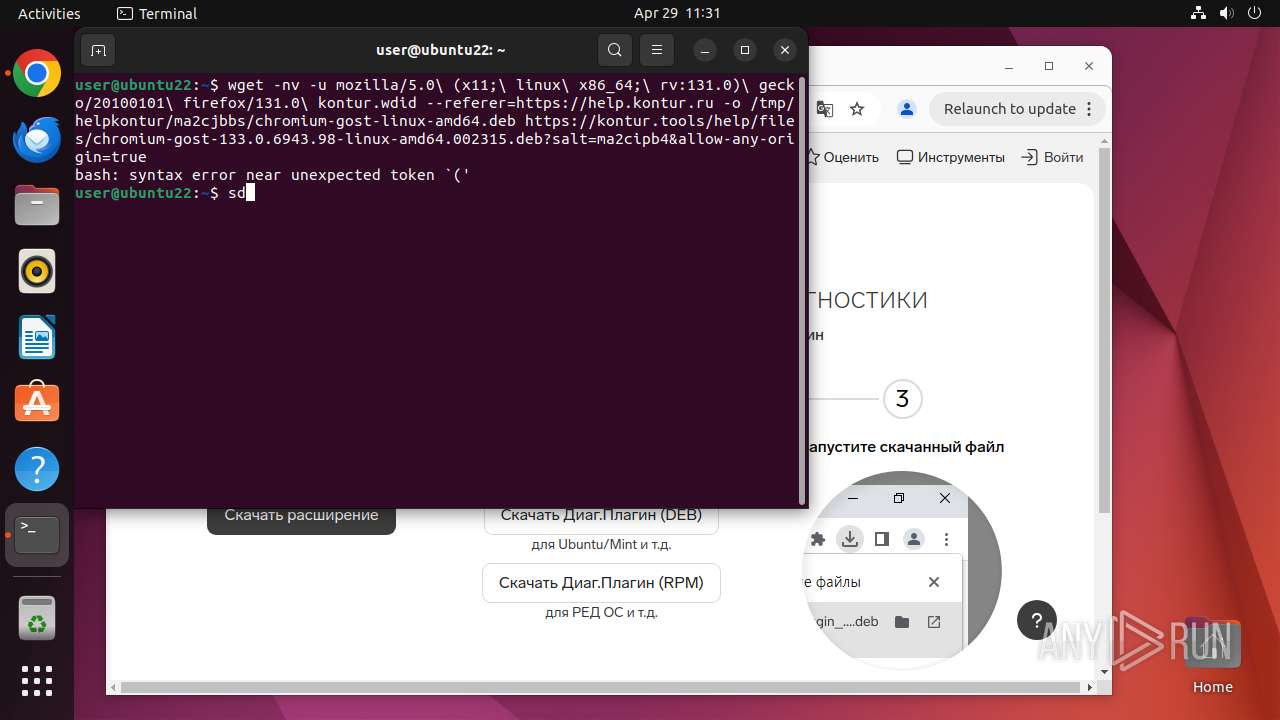
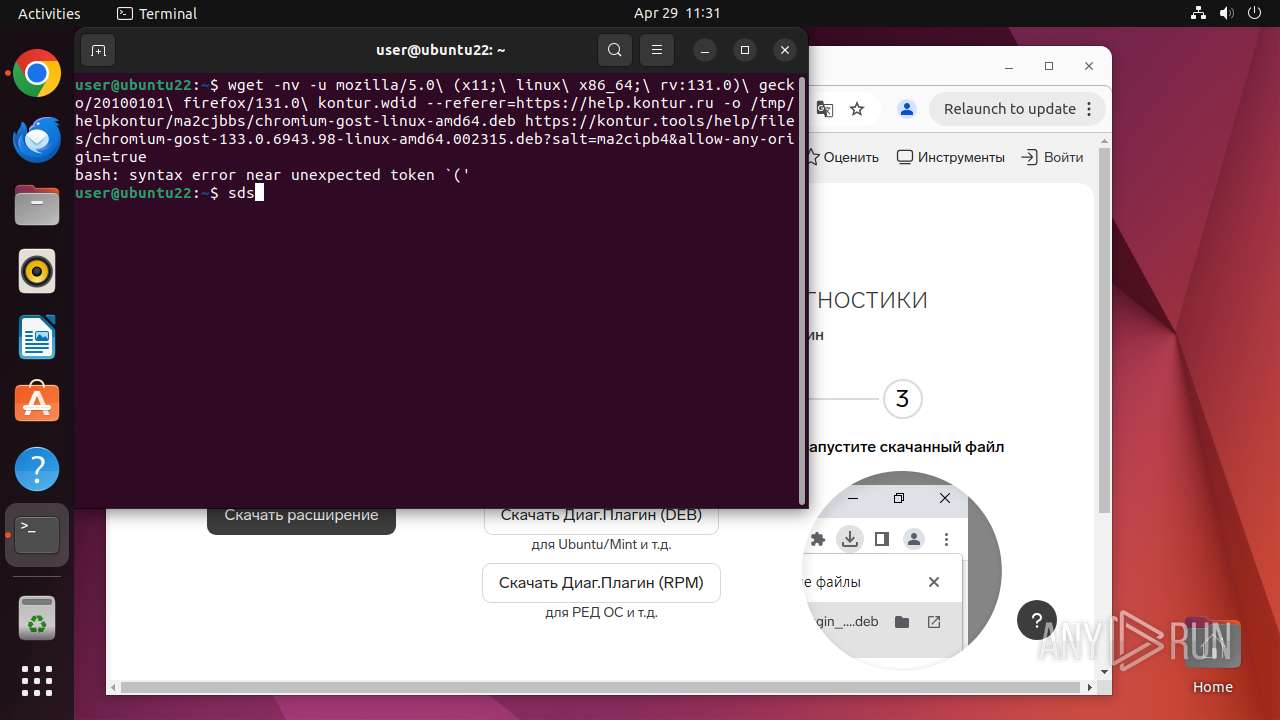
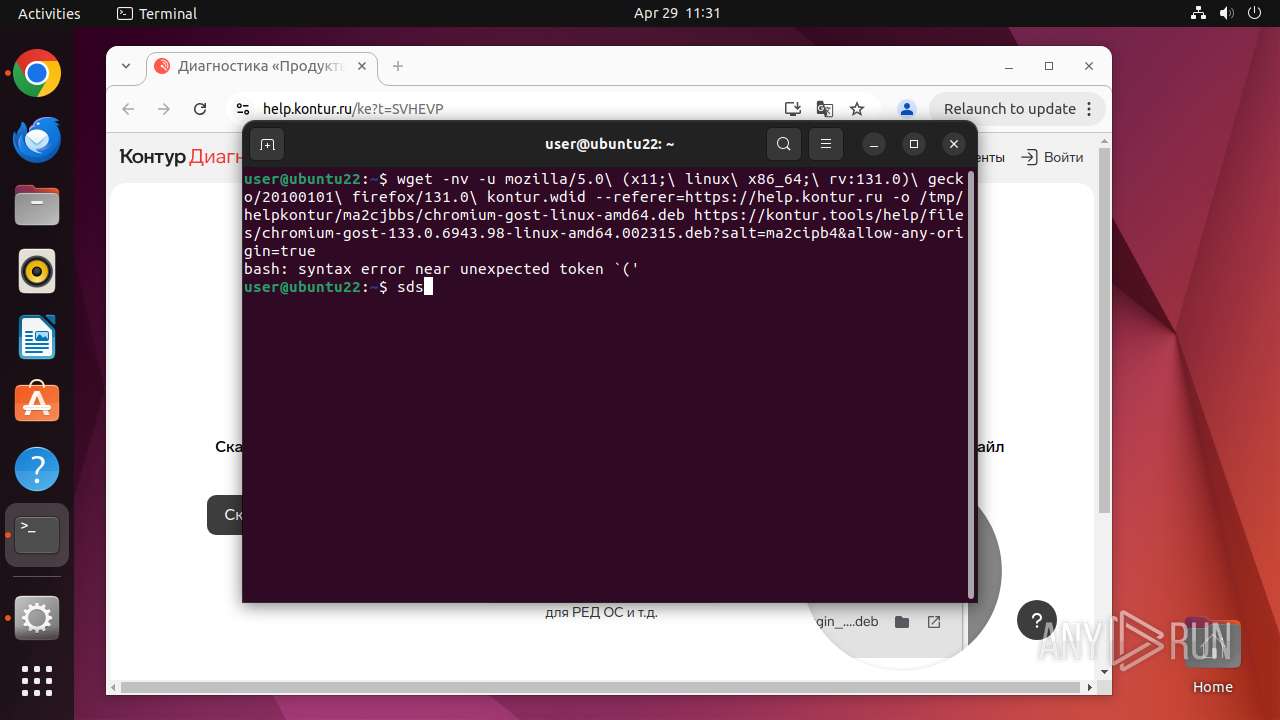
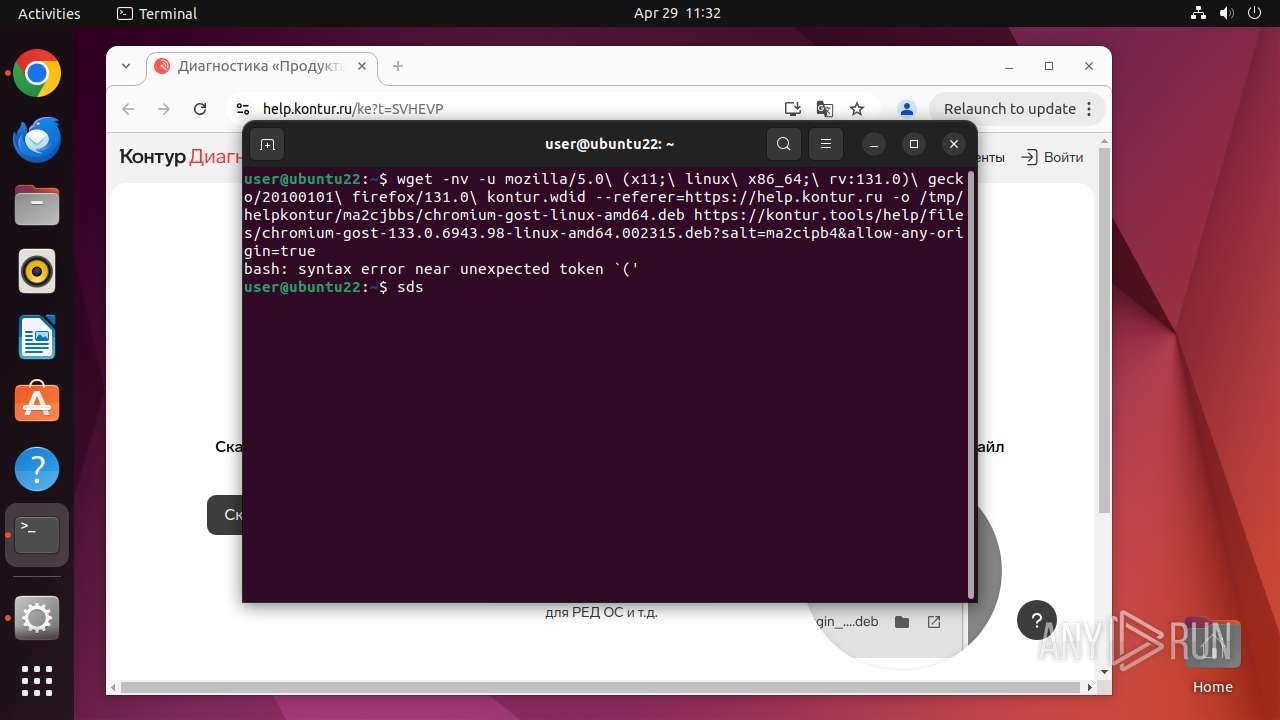
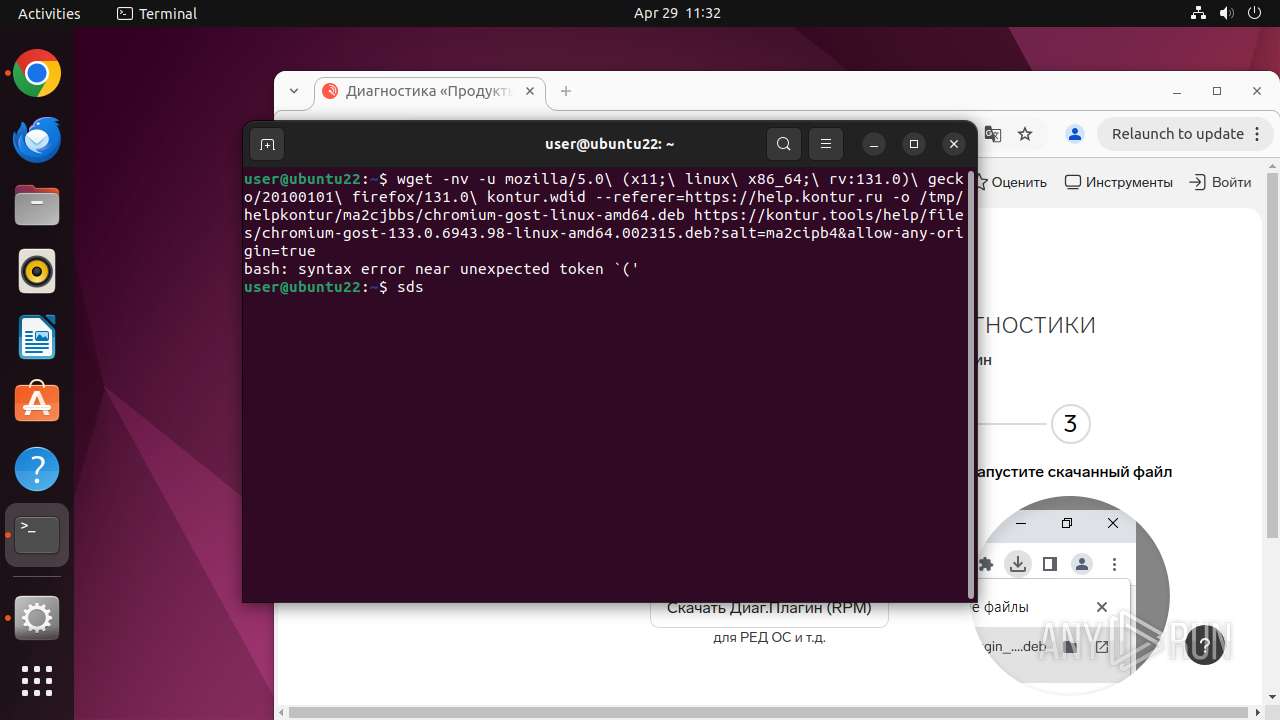
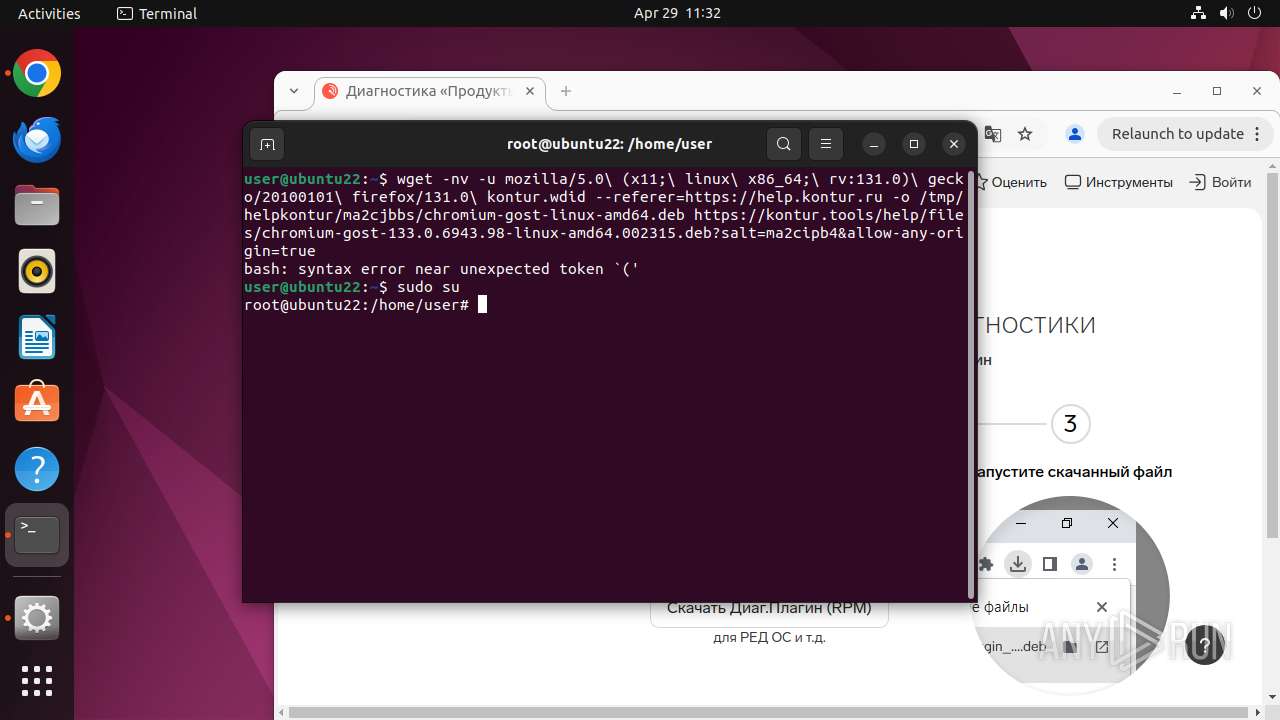
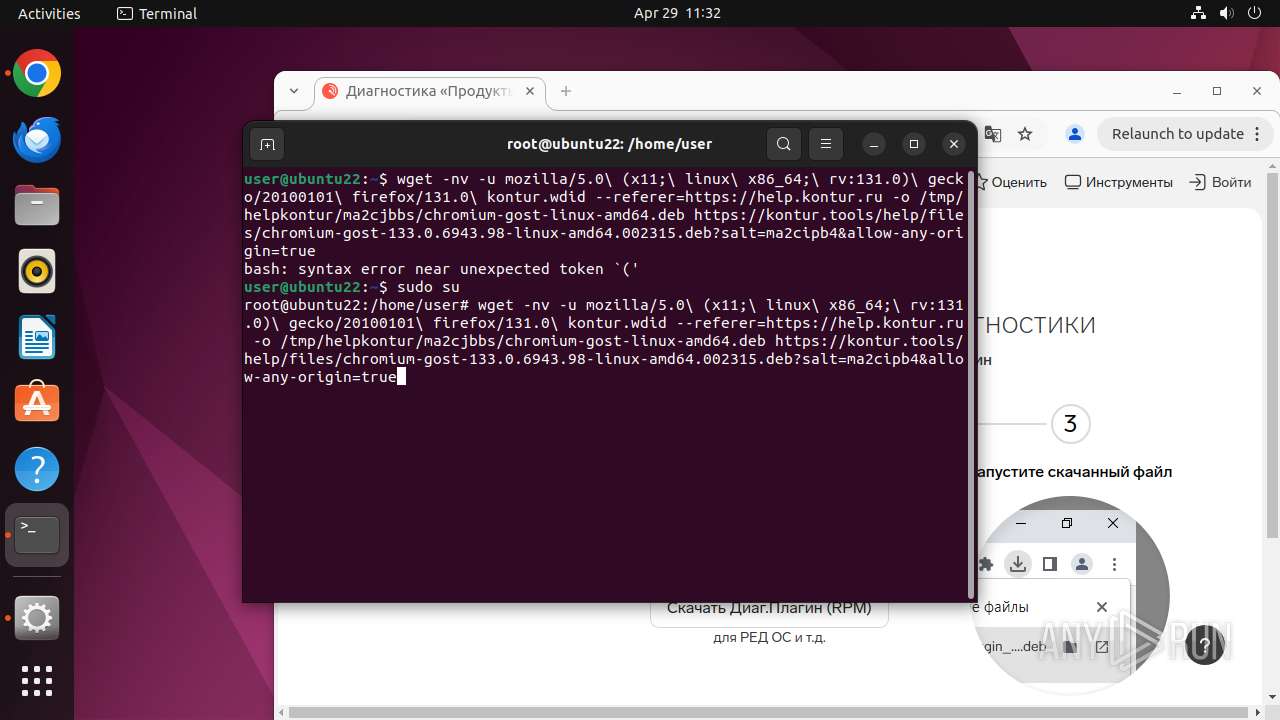
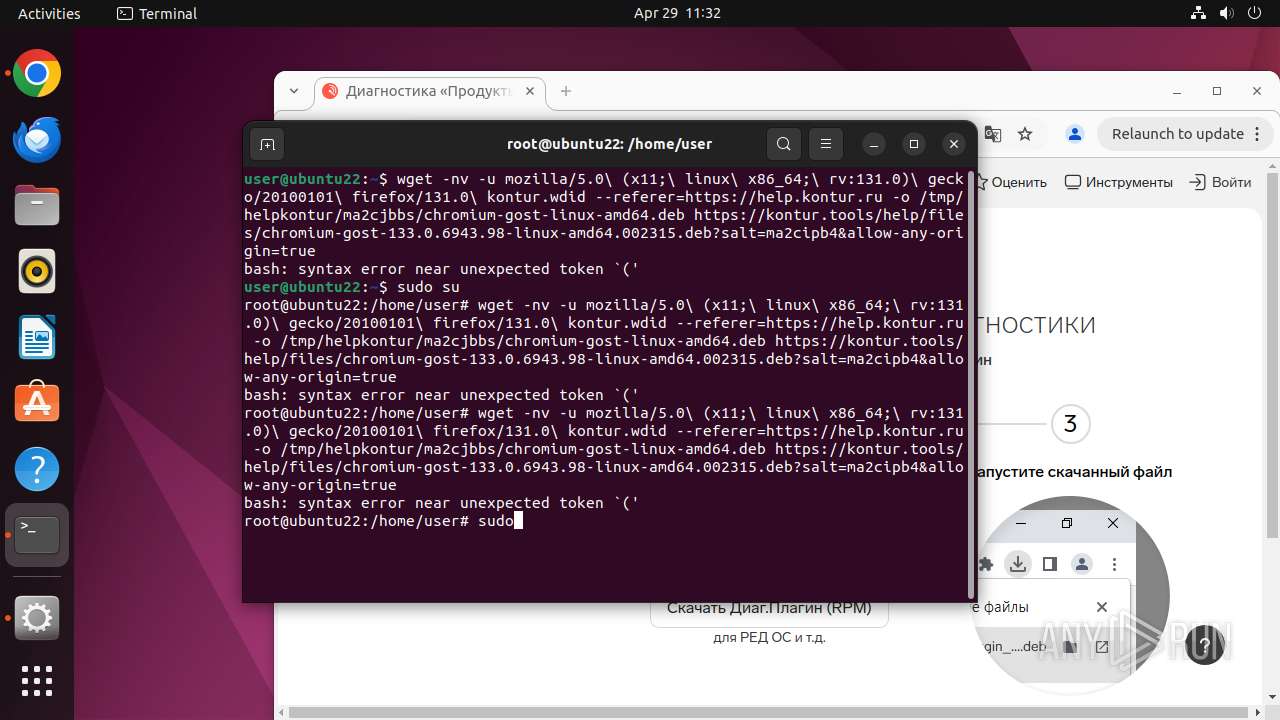
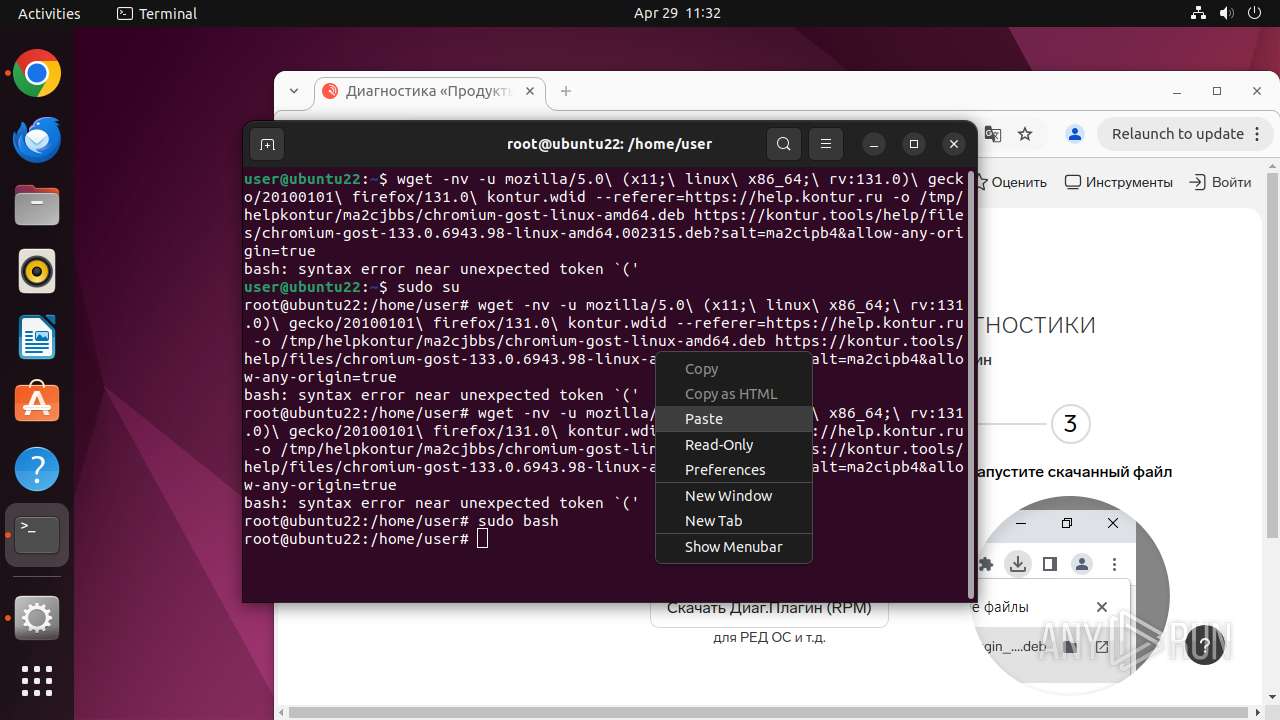
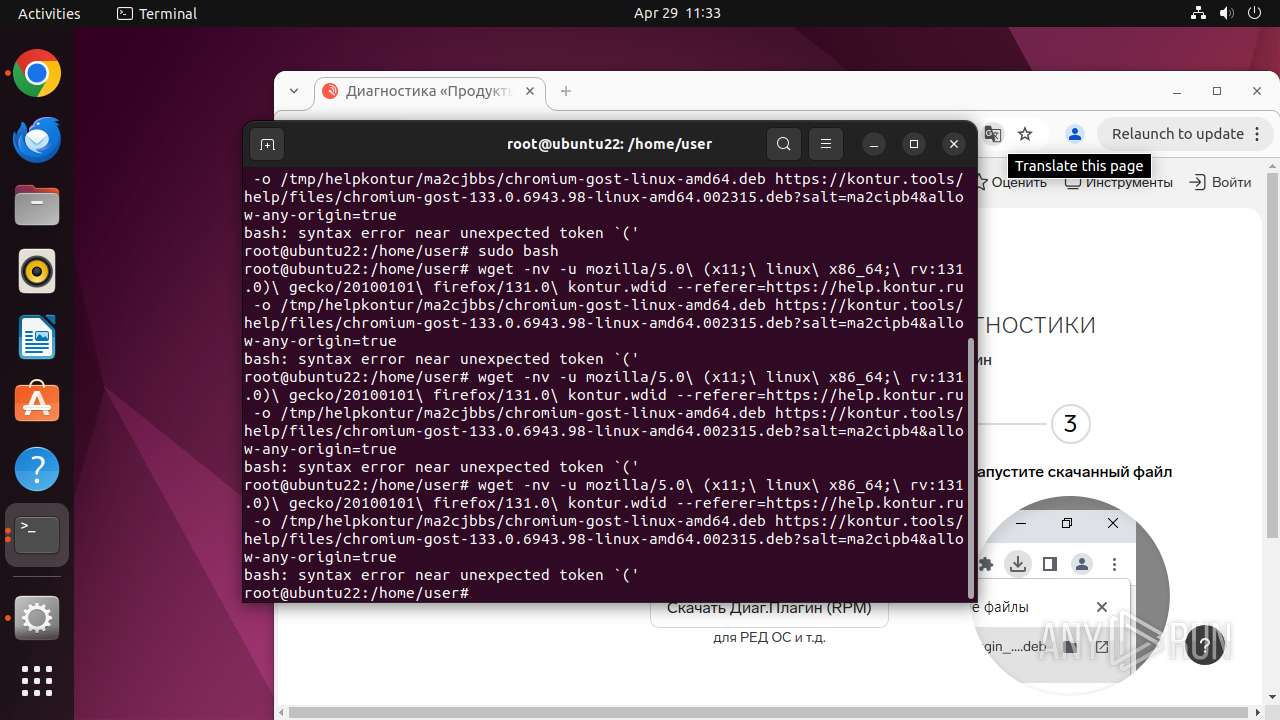
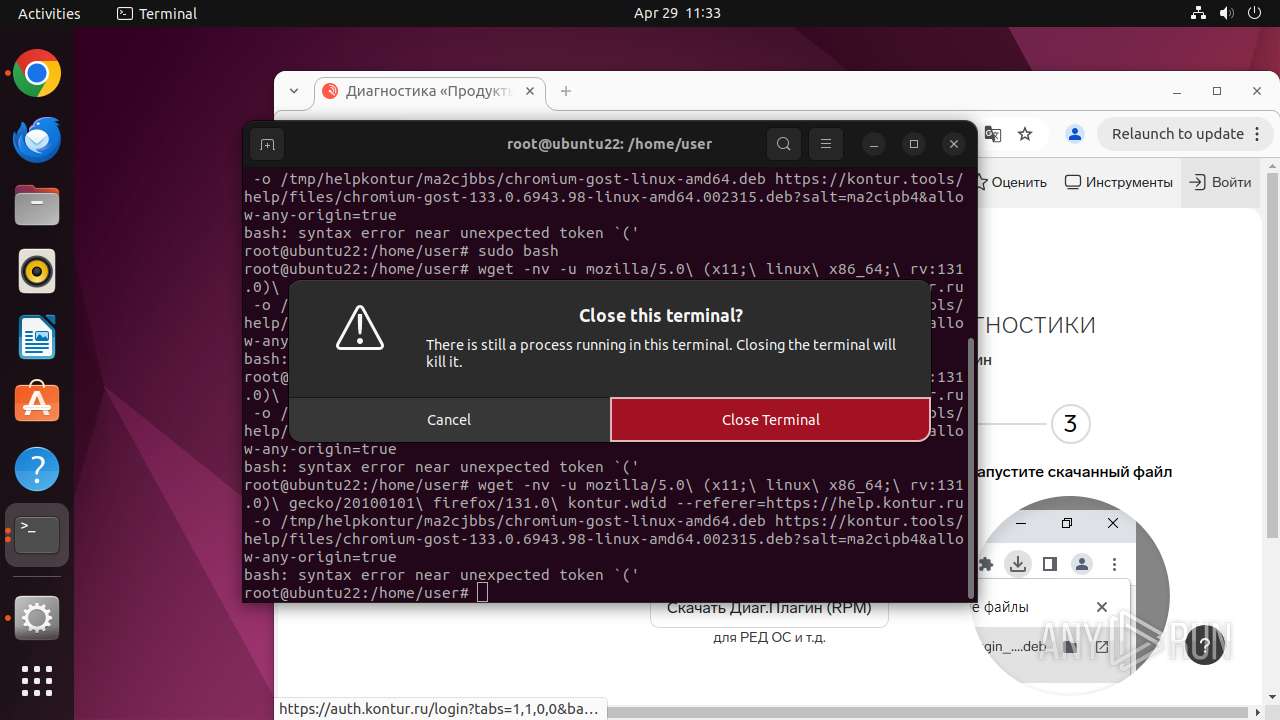
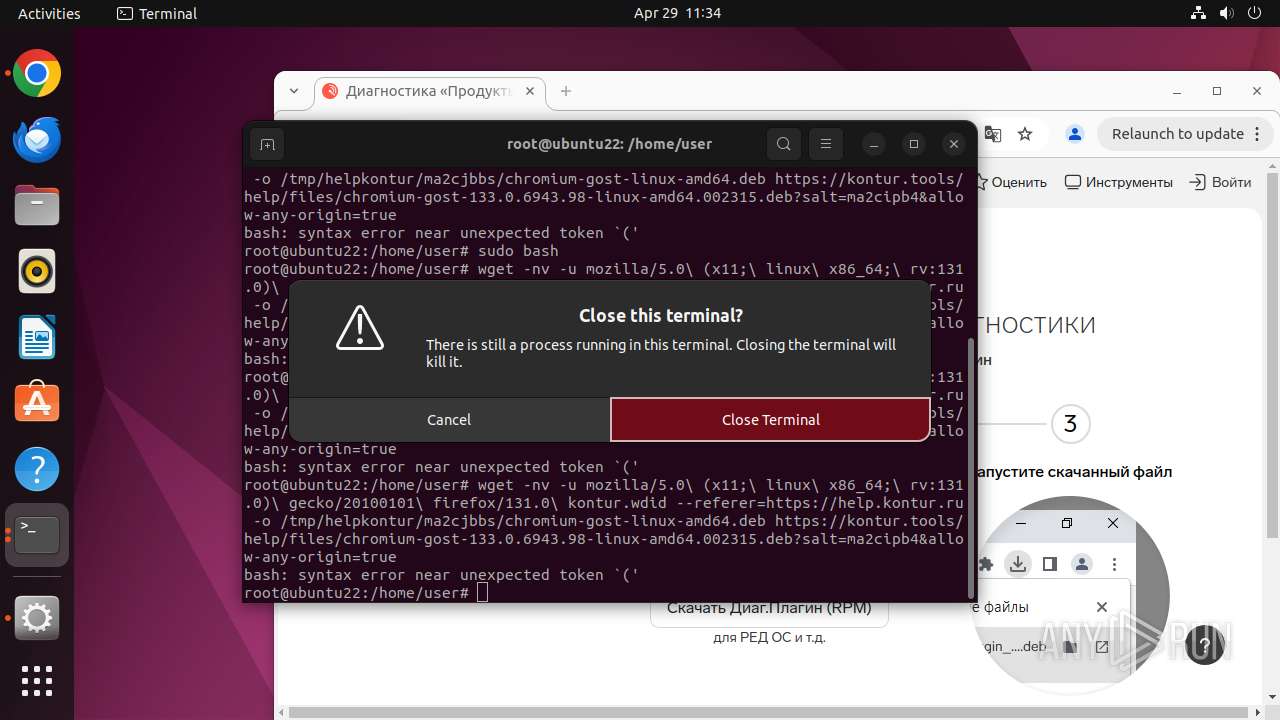
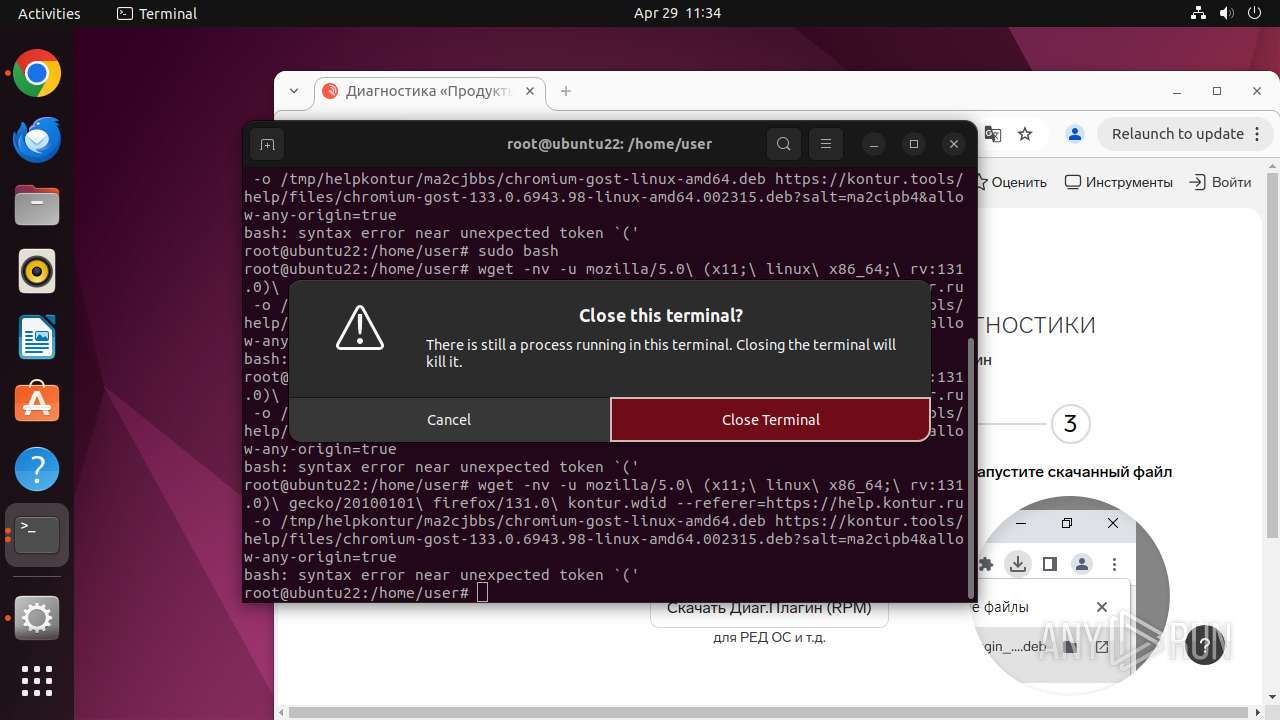
Executes commands using command-line interpreter
- sudo (PID: 39494)
- chrome (PID: 39495)
- gnome-terminal-server (PID: 39772)
INFO
Checks timezone
- python3.10 (PID: 39765)
- chrome (PID: 39495)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
310
Monitored processes
92
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
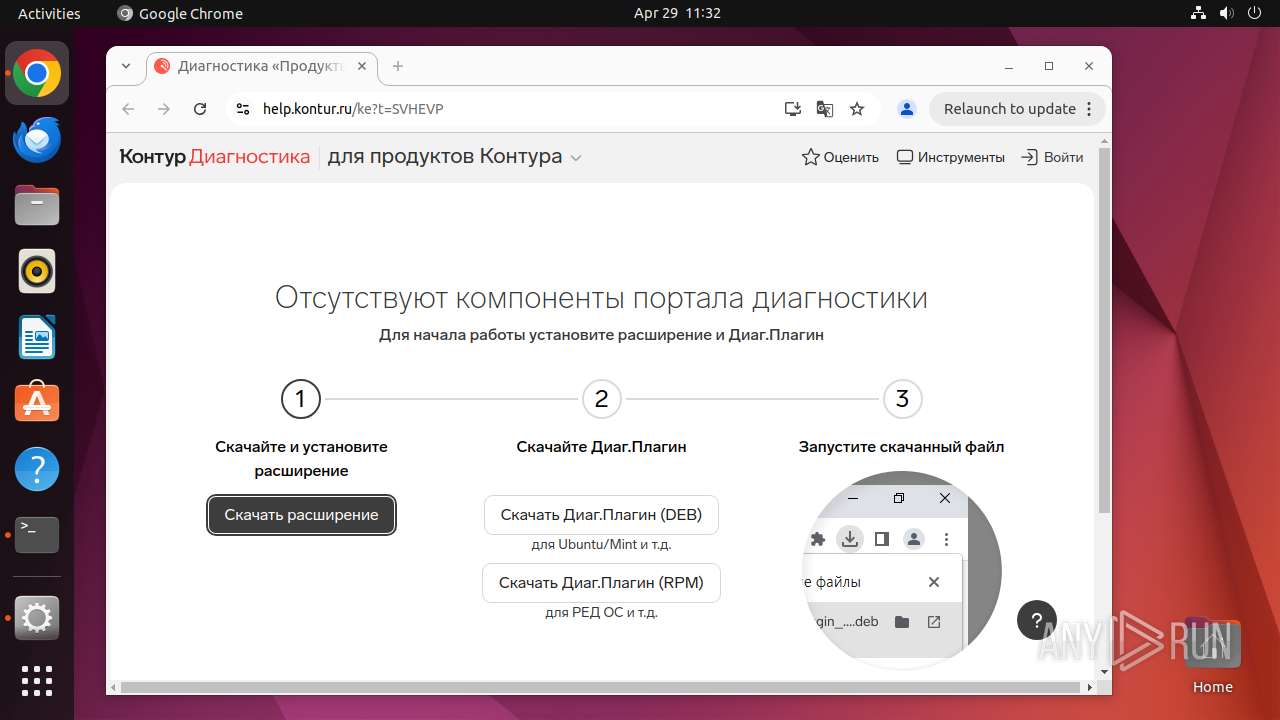
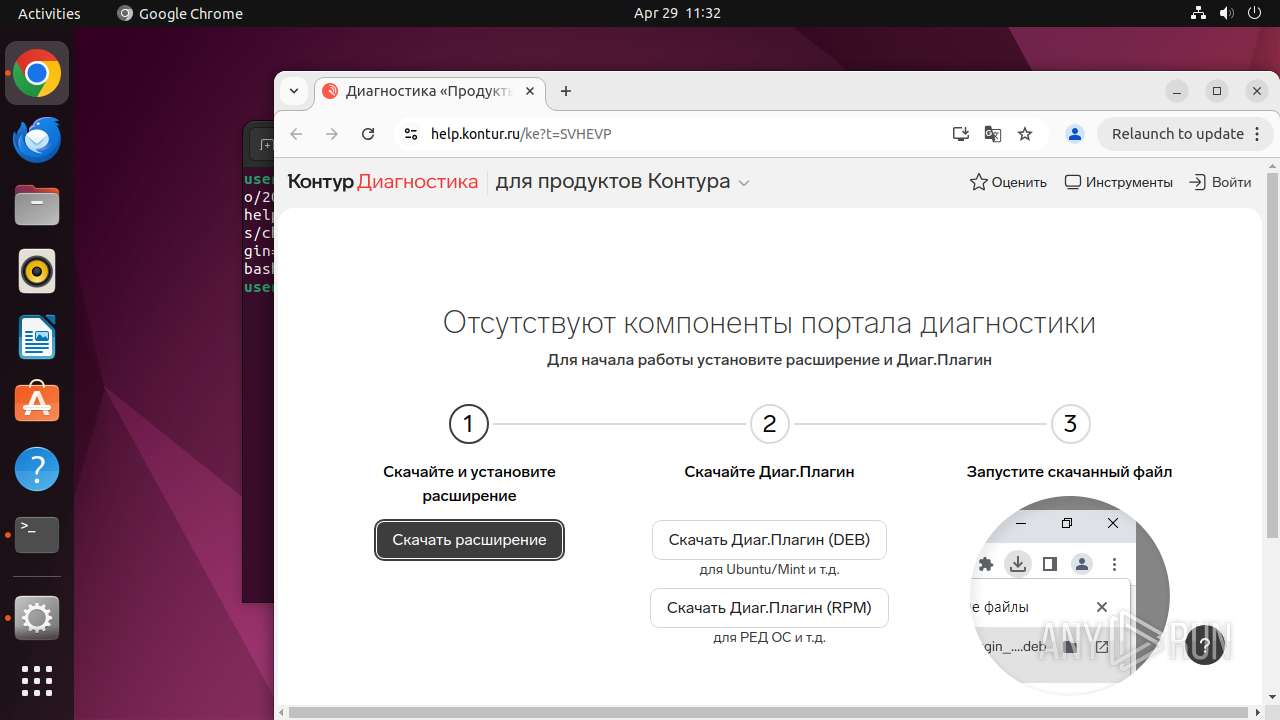
| 39493 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://help\.kontur\.ru " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 39494 | sudo -iu user google-chrome https://help.kontur.ru | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 39495 | /usr/bin/google-chrome https://help.kontur.ru | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 39496 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39497 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39498 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39499 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39500 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 39501 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 39502 | "/opt/google/chrome/chrome https://help\.kontur\." | /opt/google/chrome/chrome | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
194
Text files
5
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 39495 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 39495 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 39495 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 39495 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 39495 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 39495 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 39541 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 39627 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 39495 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
| 39495 | chrome | /home/user/.config/google-chrome/Default/DawnWebGPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
51
DNS requests
53
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aclxnidwwkj5di3vduduj2gqpgpq_4.10.2891.0/oimompecagnajdejgnnjijobebaeigek_4.10.2891.0_linux_b4hin3q5s66ws2322cyyfp35lu.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackabrtjqqtlkfg42dx6l6he4s7q_20250411.743742949.14/obedbbhbpmojnkanicioggnmelmoomoc_20250411.743742949.14_all_ENGB500000_ad6zlqy7zvlwybrc56kgnjb2psiq.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adkaslei6jmqagifn5oqq5omgktq_504/lmelglejhemejginpboagddgdfbepgmp_504_all_ZZ_ackkcxflam4xeajohqyztitlin2q.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/advsmb52xq3kv4d7uo3oa25kja5q_9747/hfnkpimlhhgieaddgfemjhofmfblmnib_9747_all_adgo3gm7255tv6igd7ufn4zh2r5q.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adfsnc2pdt3qaf4hwbwm6urhgf5a_2025.4.23.0/niikhdgajlphfehepabhhblakbdgeefj_2025.04.23.00_all_cumg7qttmli5i4tswkgpwksdxe.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrovrpquemobbwthbstjwffhima_2025.1.17.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2025.01.17.01_all_dd5w5blqtgwb4xkyhfpmehllye.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lnu3li27zsanbe2hcsfjuvm5fq_1.0.7.1744928549/laoigpblnllgcgjnjnllmfolckpjlhki_1.0.7.1744928549_all_ady56p6vtubsna6mhkx6lu2qml3a.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adnwswi5bi3pd3idmkzwee46s2gq_2025.3.26.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.3.26.1143_all_k7ciobm2xv32lbqoijkr6ievde.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.97:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 91.189.91.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 91.189.91.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
1178 | snap-store | 37.19.194.81:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
39543 | chrome | 142.250.186.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
39543 | chrome | 142.250.186.170:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
39543 | chrome | 108.177.119.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
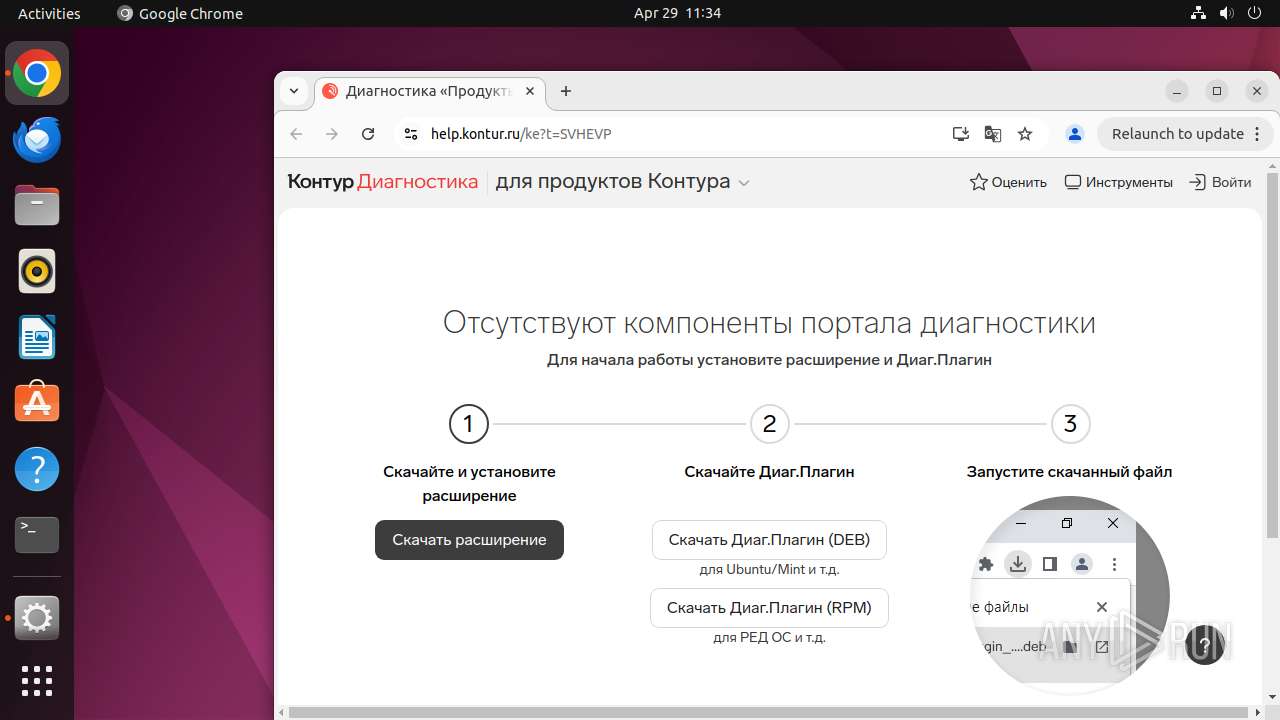
39543 | chrome | 46.17.203.51:443 | help.kontur.ru | JSC SKB Kontur production | RU | whitelisted |
39543 | chrome | 87.250.251.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
help.kontur.ru |
| whitelisted |
accounts.google.com |
| whitelisted |
s.kontur.ru |
| whitelisted |
mc.yandex.ru |
| whitelisted |
api.snapcraft.io |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
39543 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39543 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39543 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39543 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39543 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39543 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39543 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39543 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39543 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39543 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |