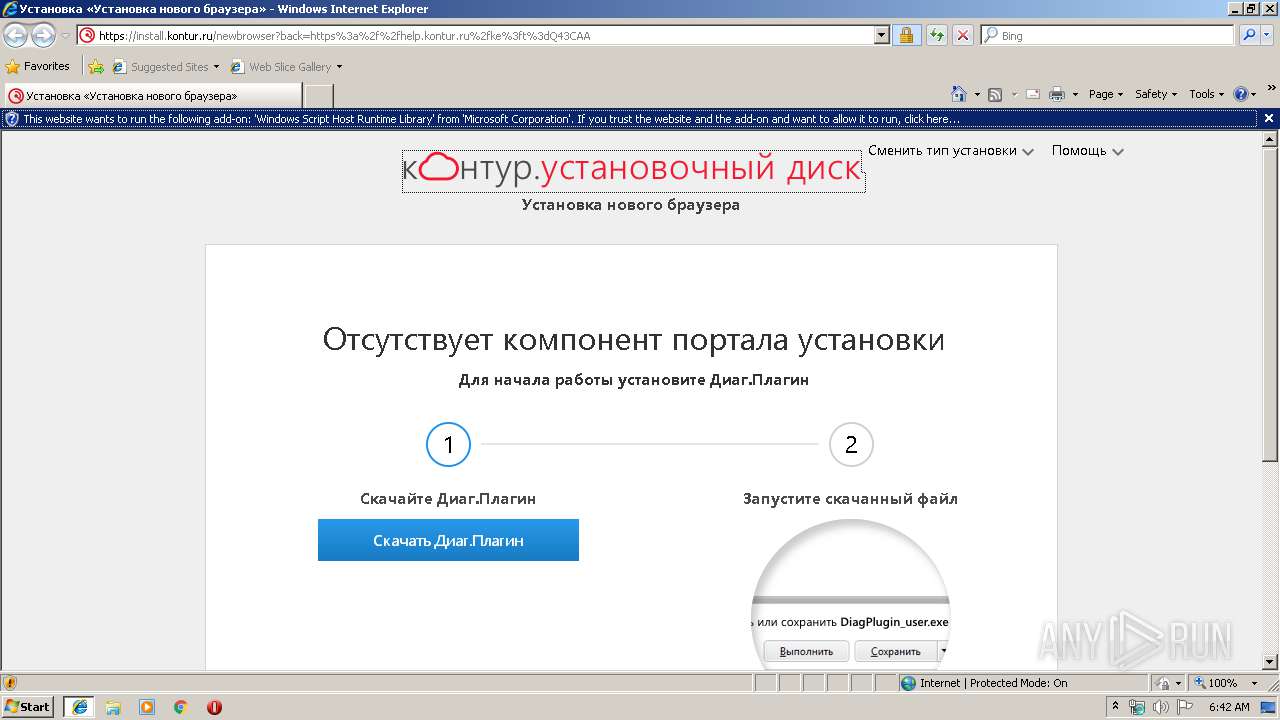
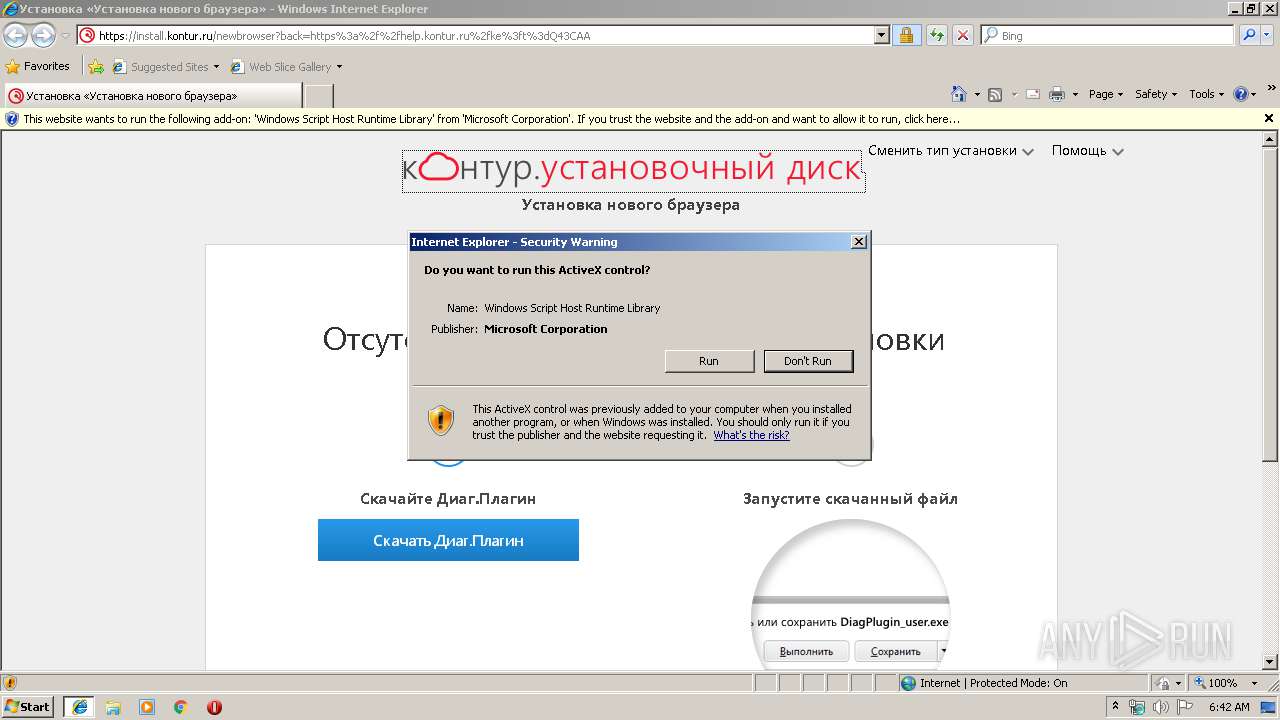
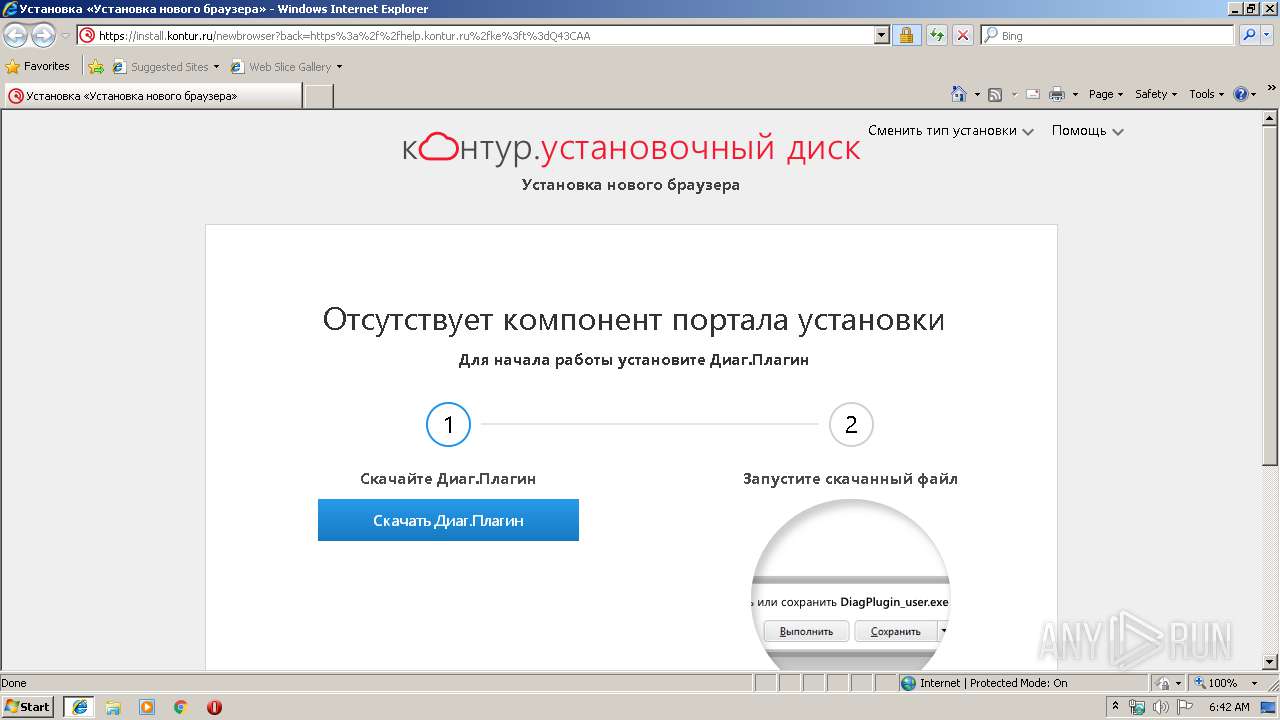
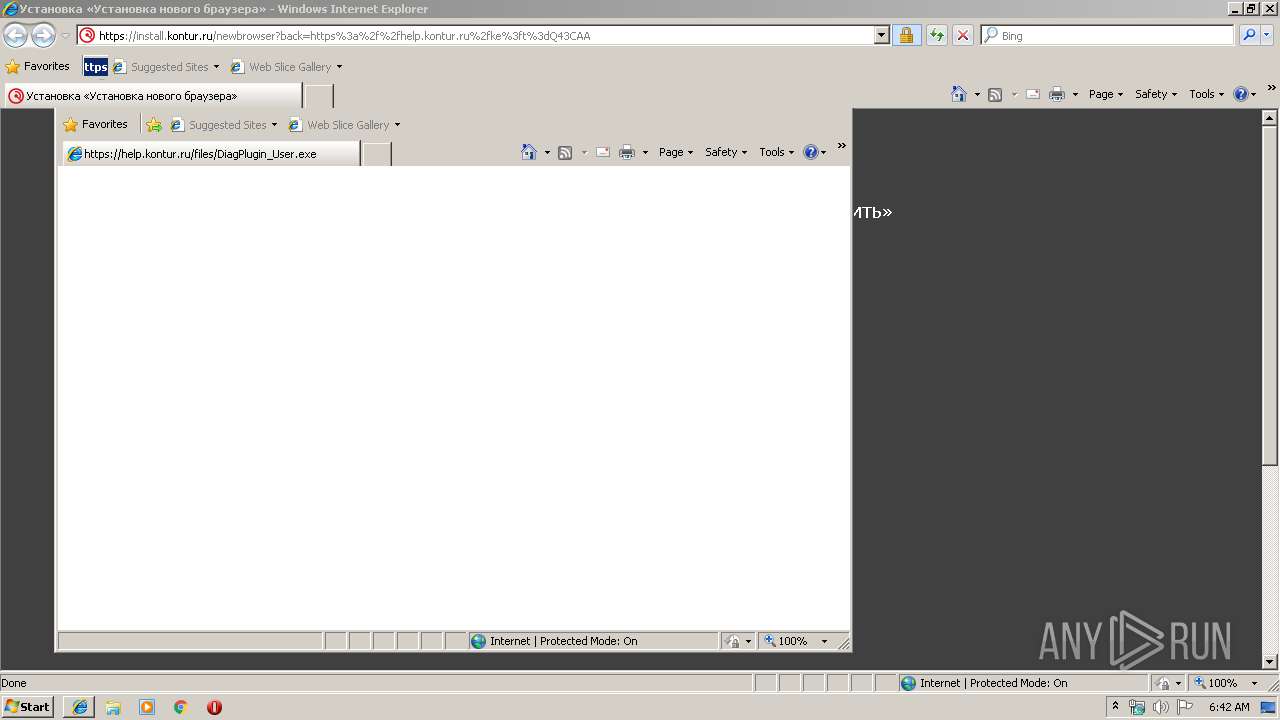
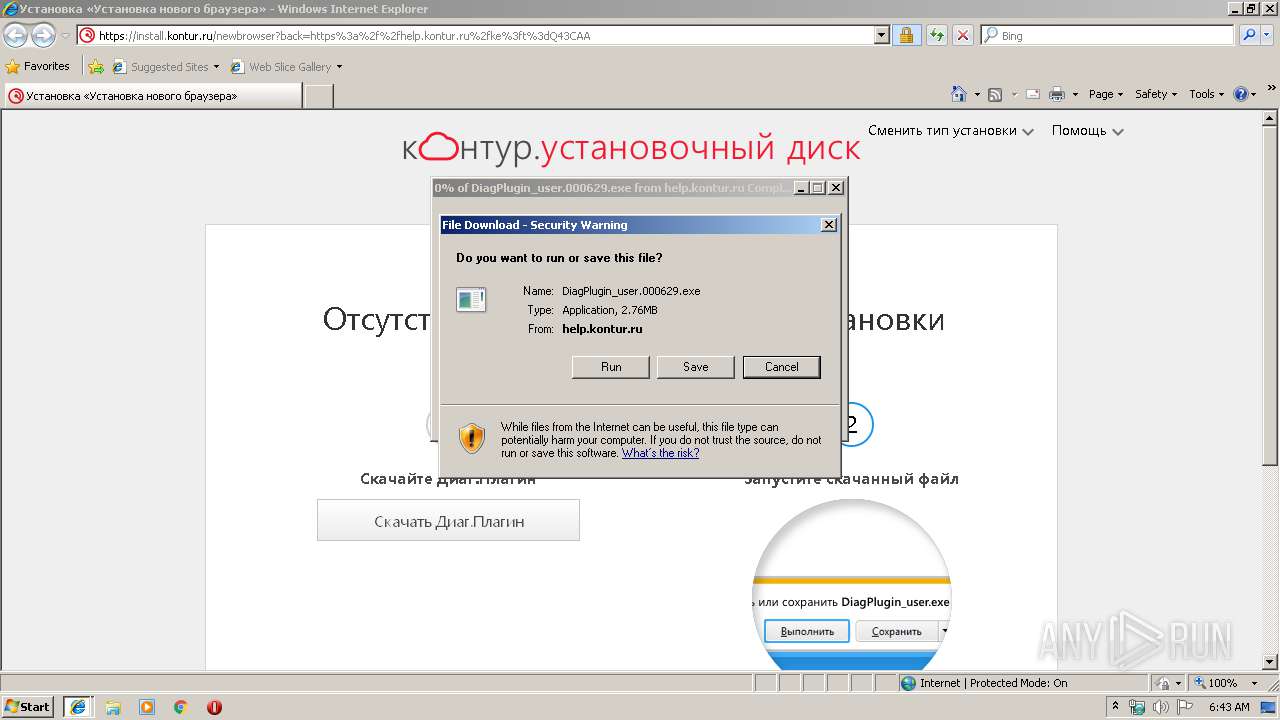
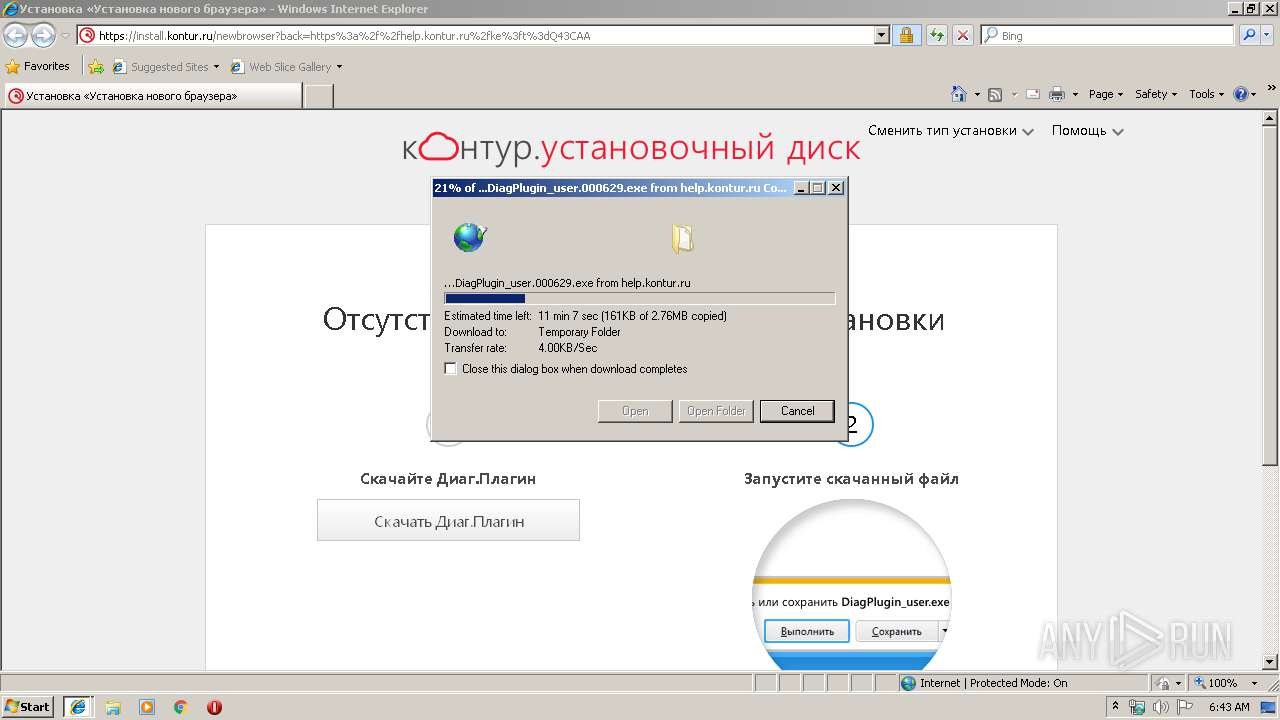
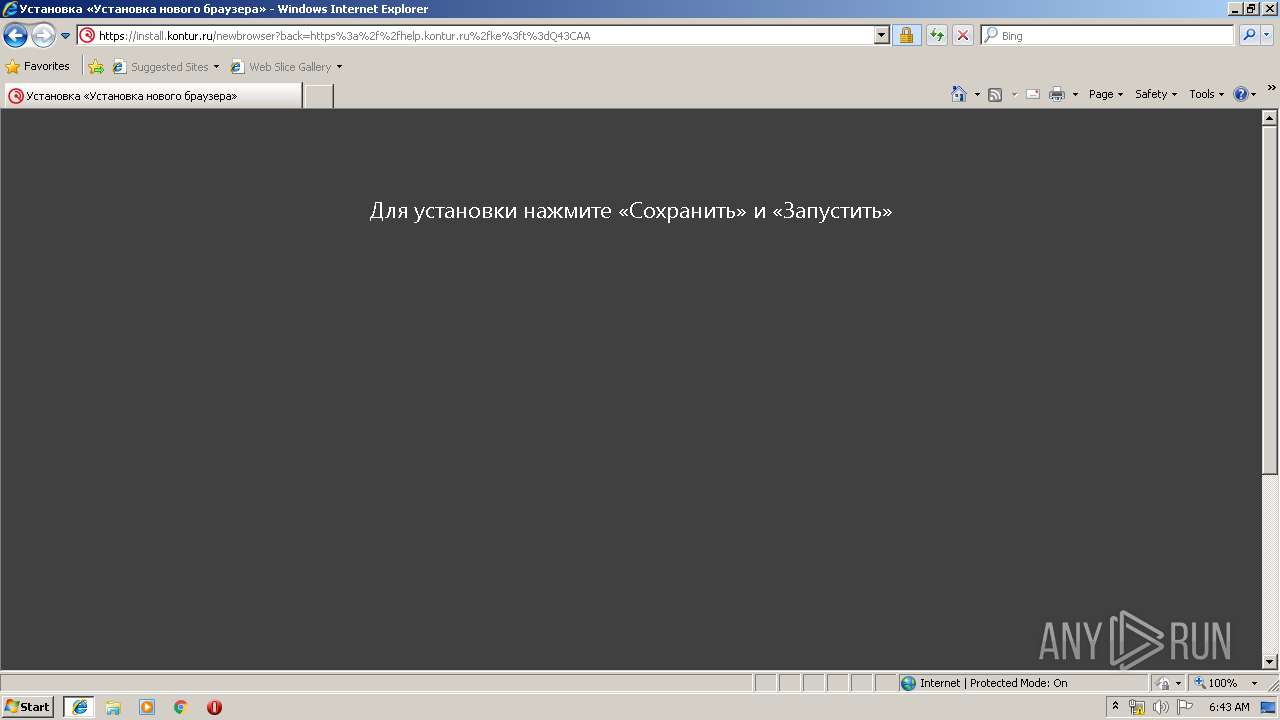
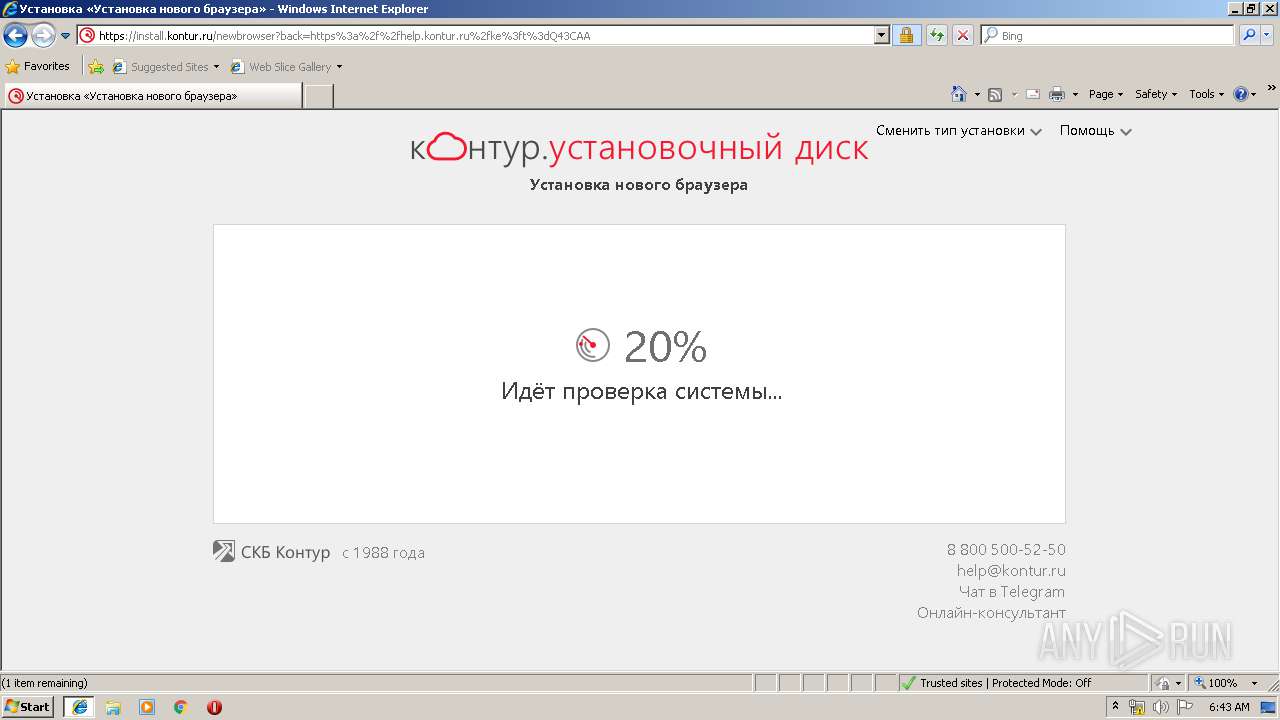
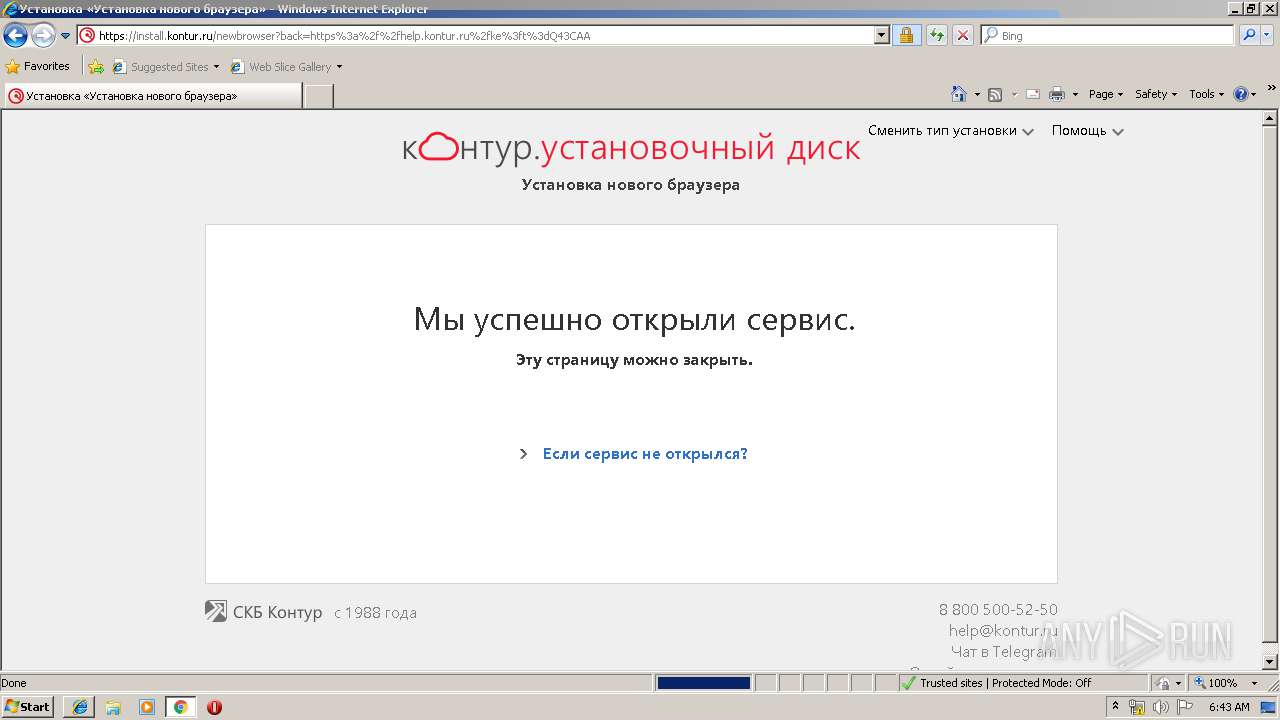
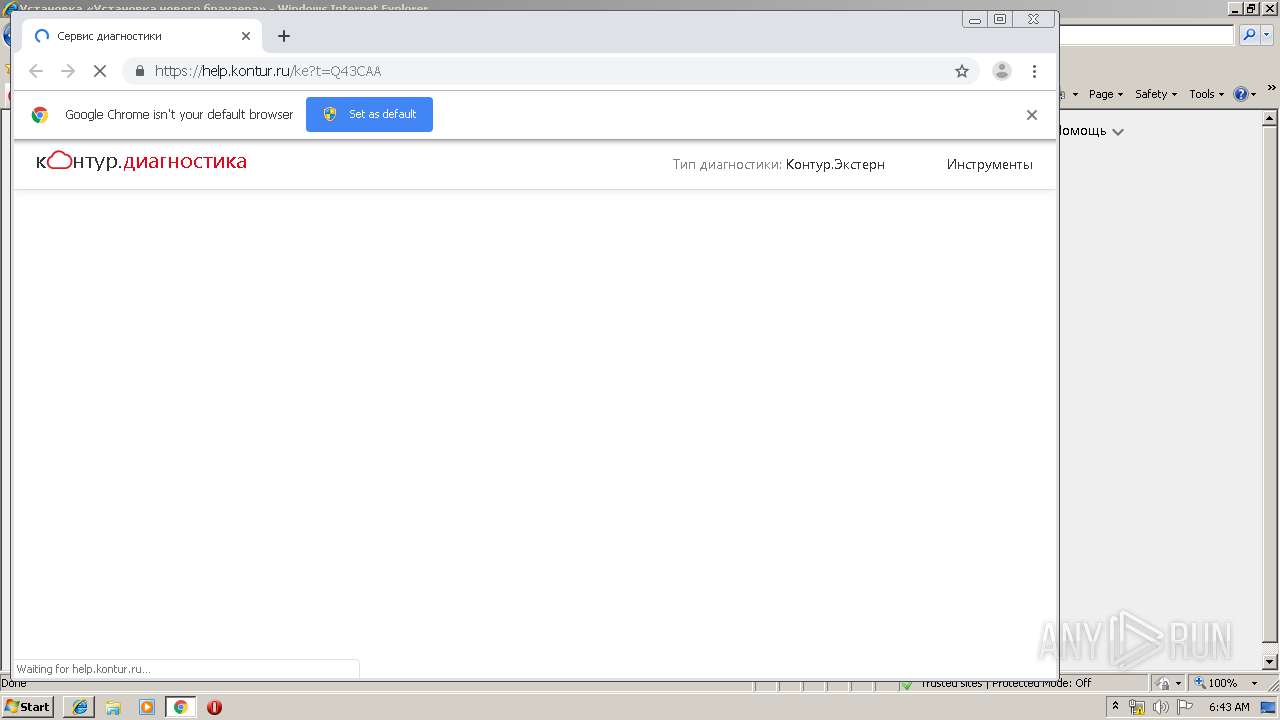
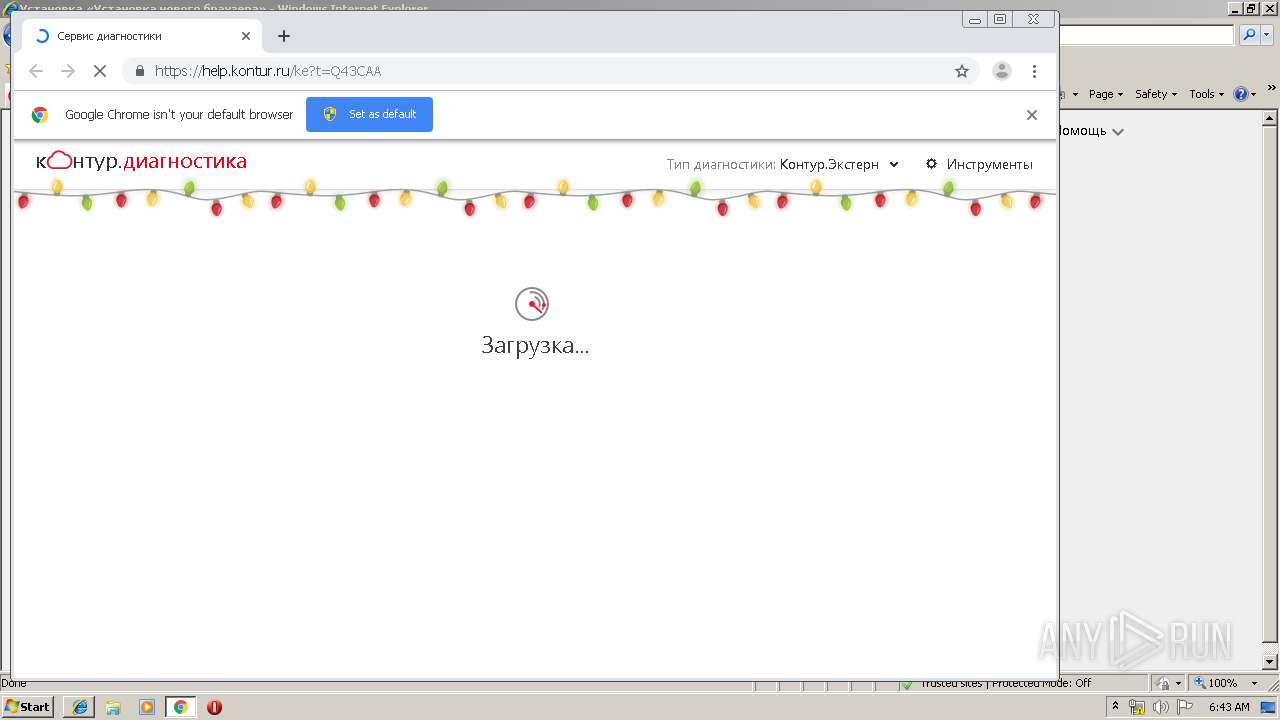
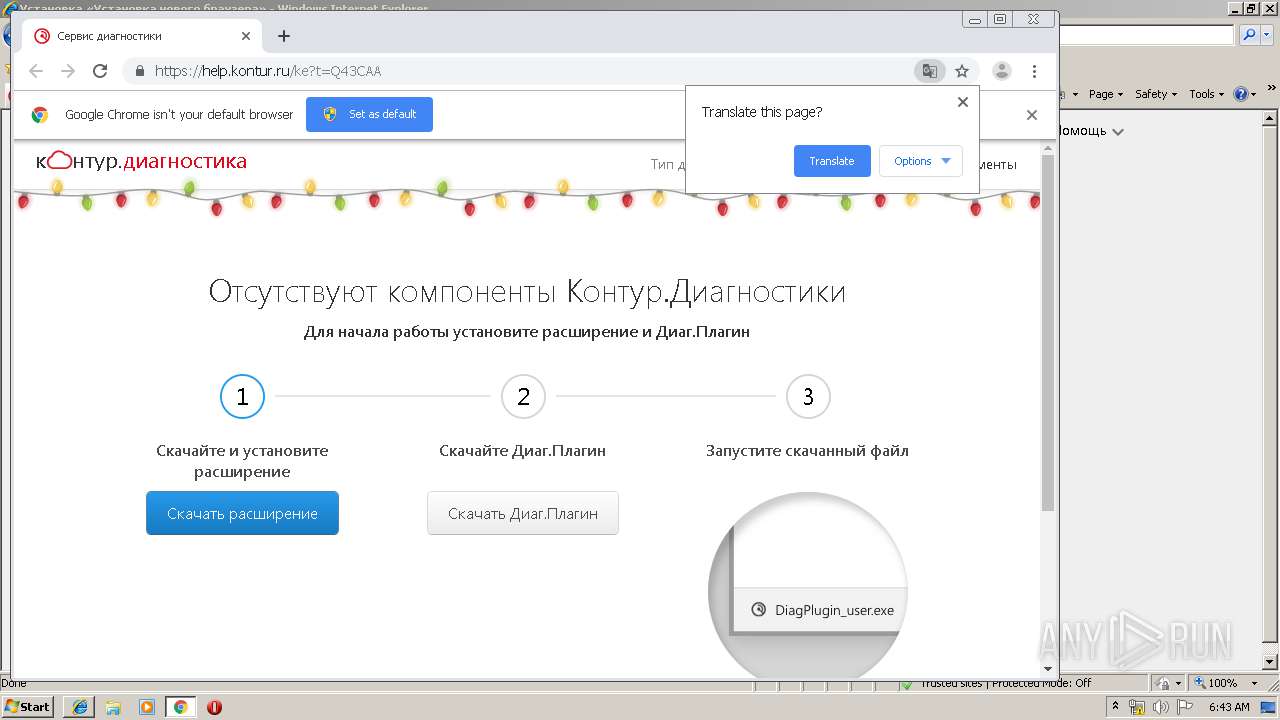
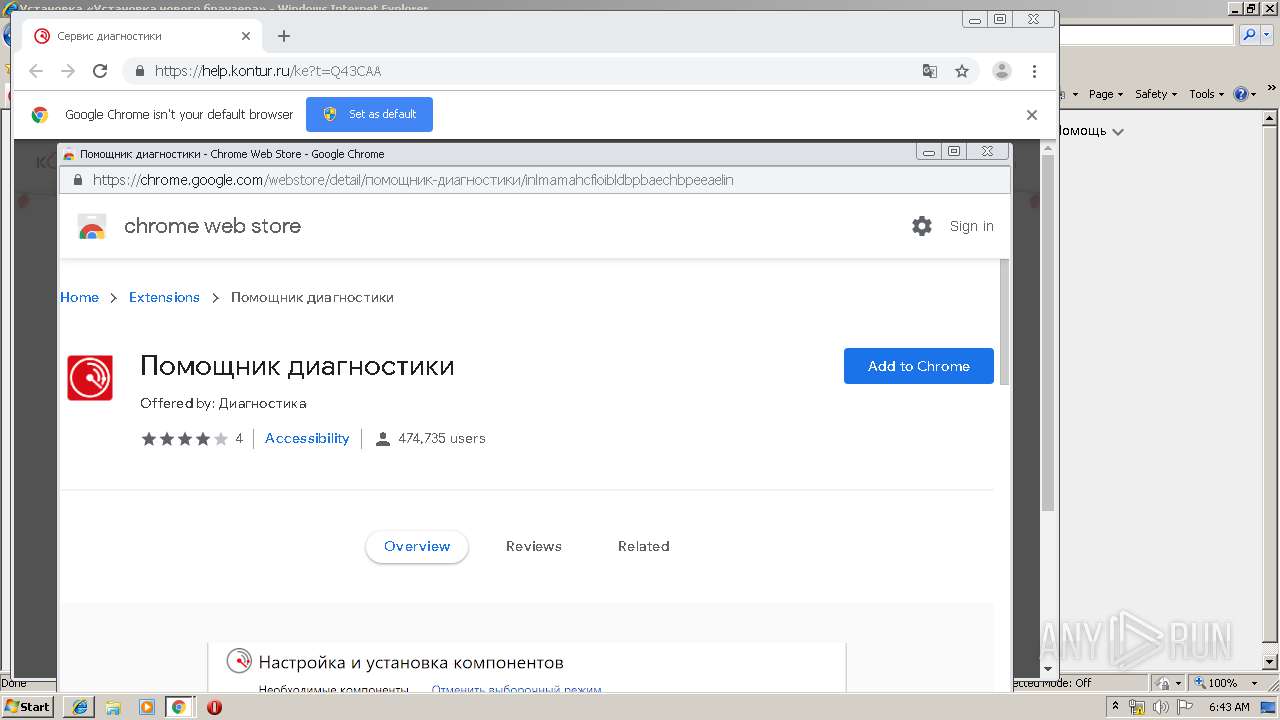
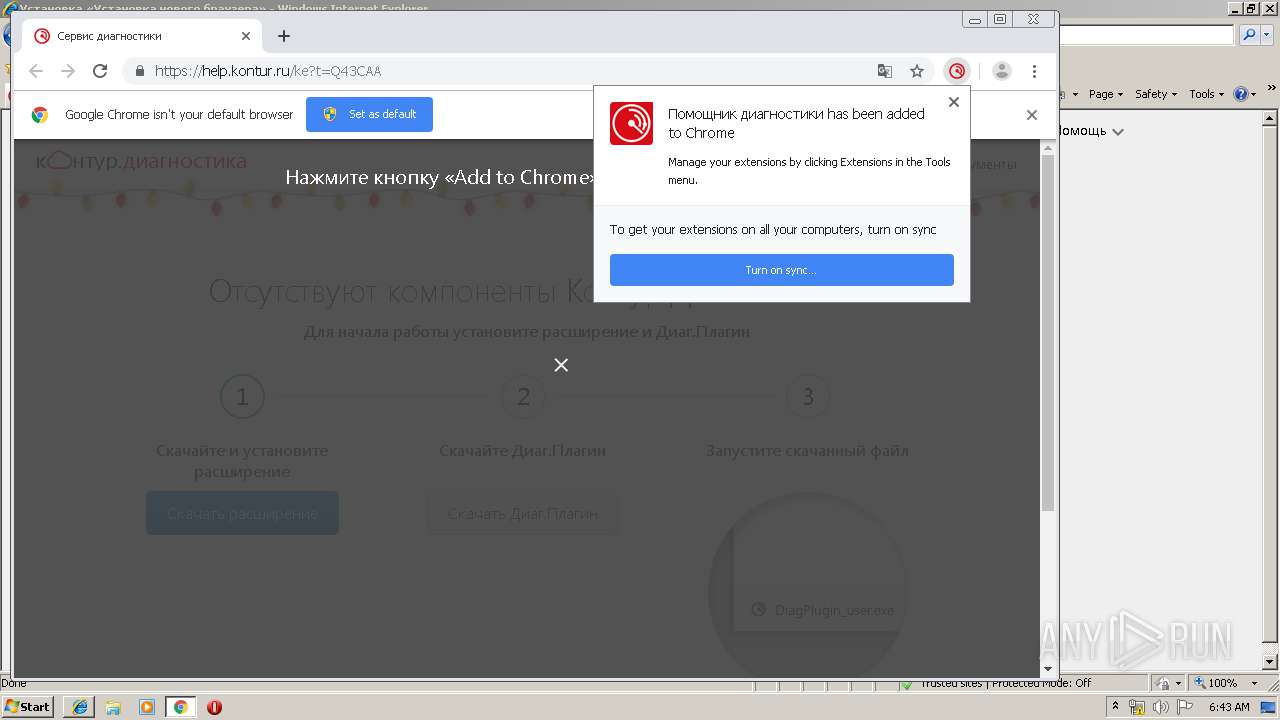
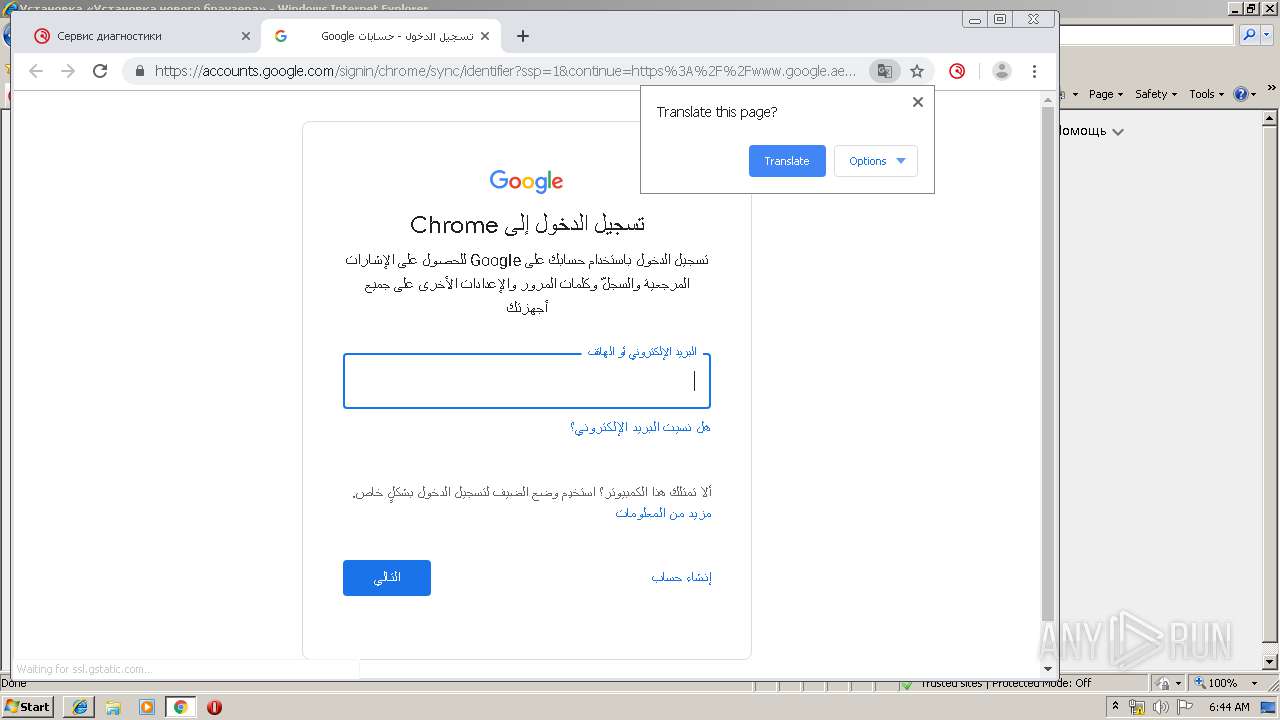
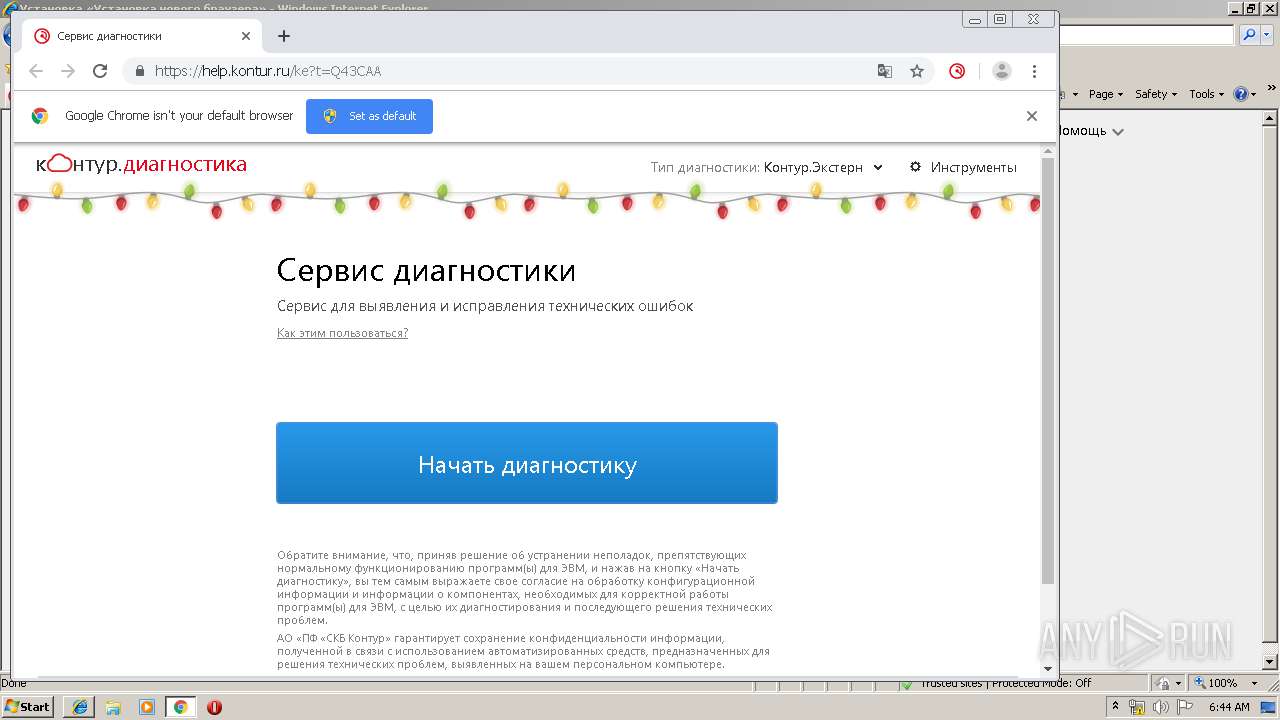
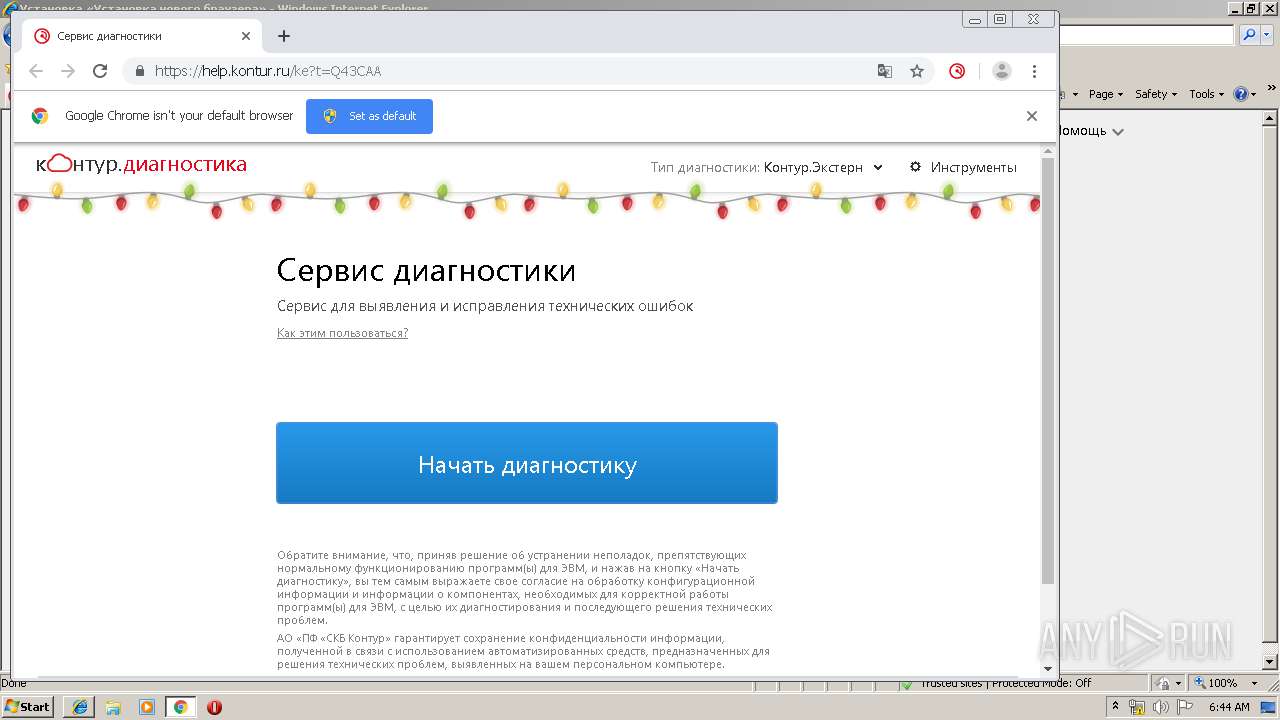
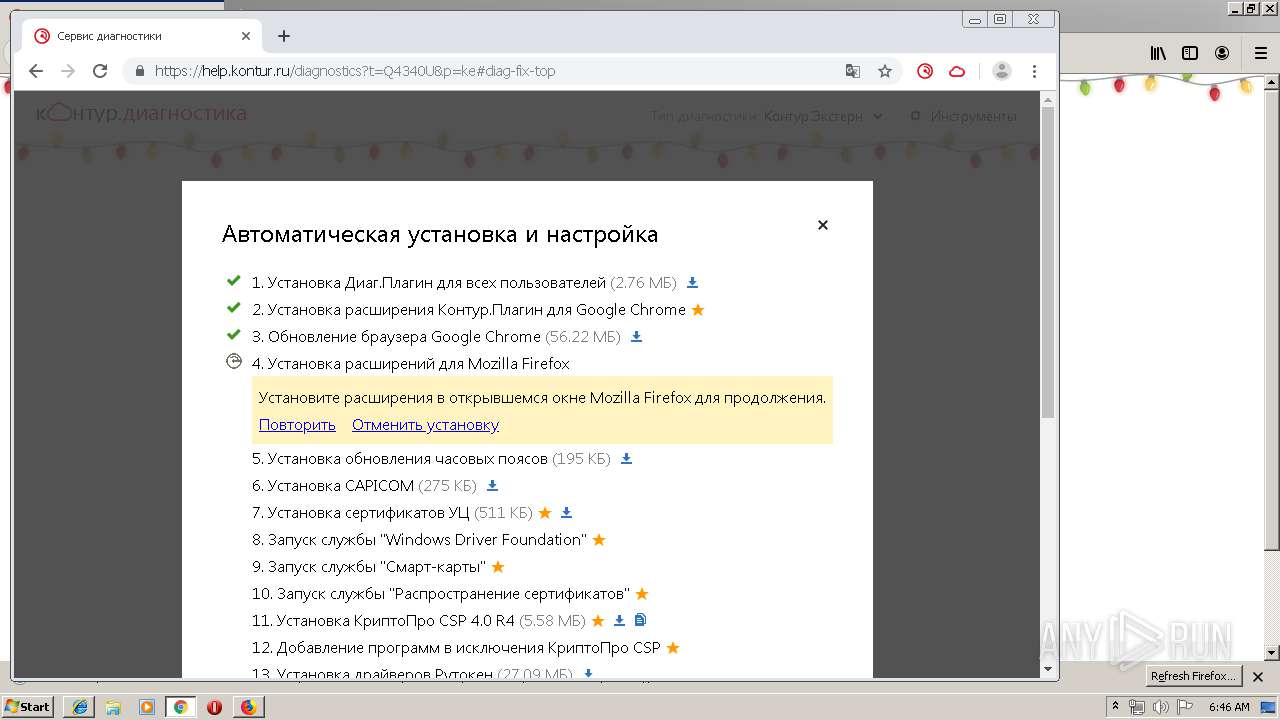
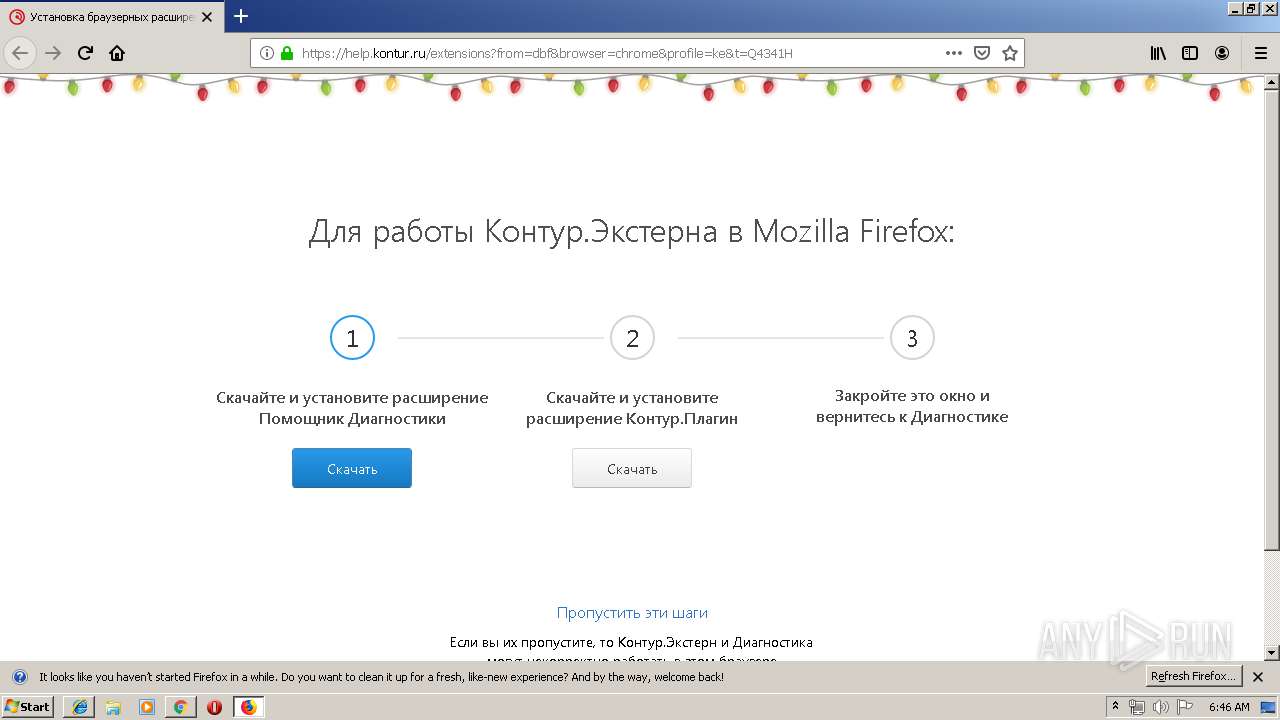
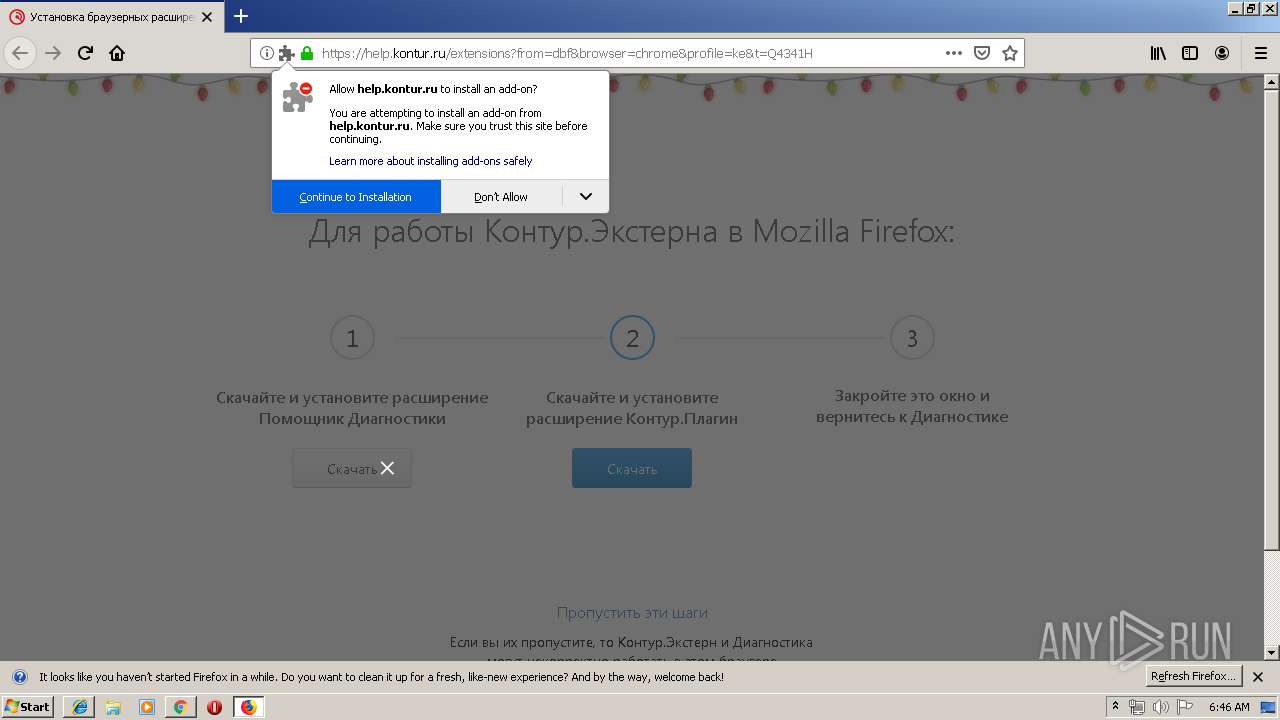
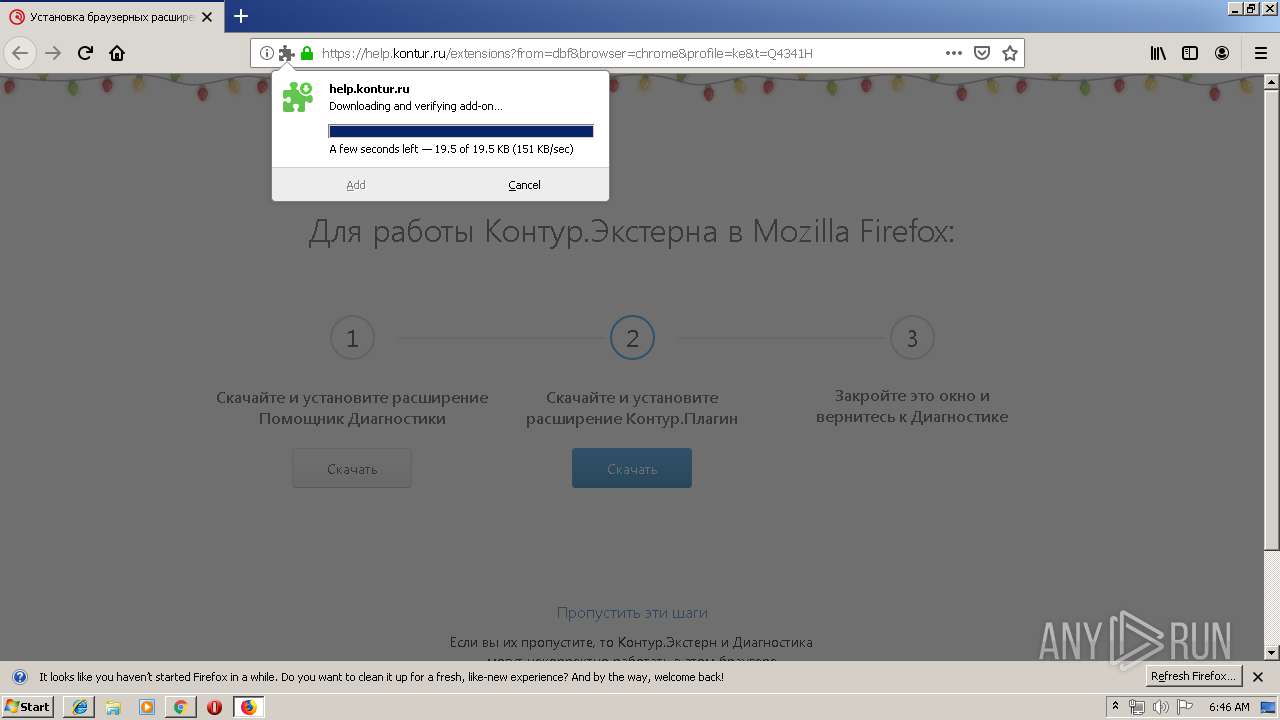
| URL: | https://help.kontur.ru |
| Full analysis: | https://app.any.run/tasks/bee2d598-3d34-4d5b-b510-f9d512769a99 |
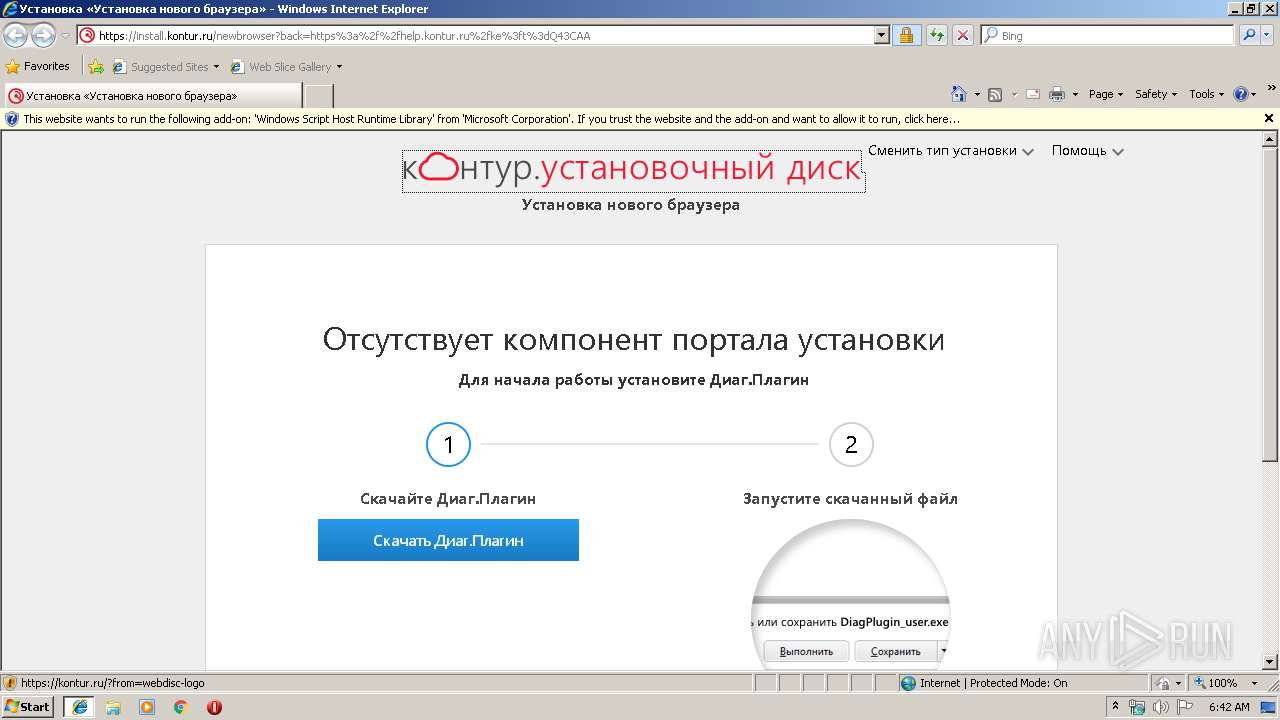
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2020, 06:41:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6BC7BA7505DA0C125CBFF96A2A4B30D5 |
| SHA1: | FCB96E5174B04B7207C04F1CC0FCEAC1C30D212B |
| SHA256: | E4B48F1328212A8EAD5D21BA74D74DFD40A04B740D23C735D84C46D335DA3AF3 |
| SSDEEP: | 3:N88vlMsn:28NRn |
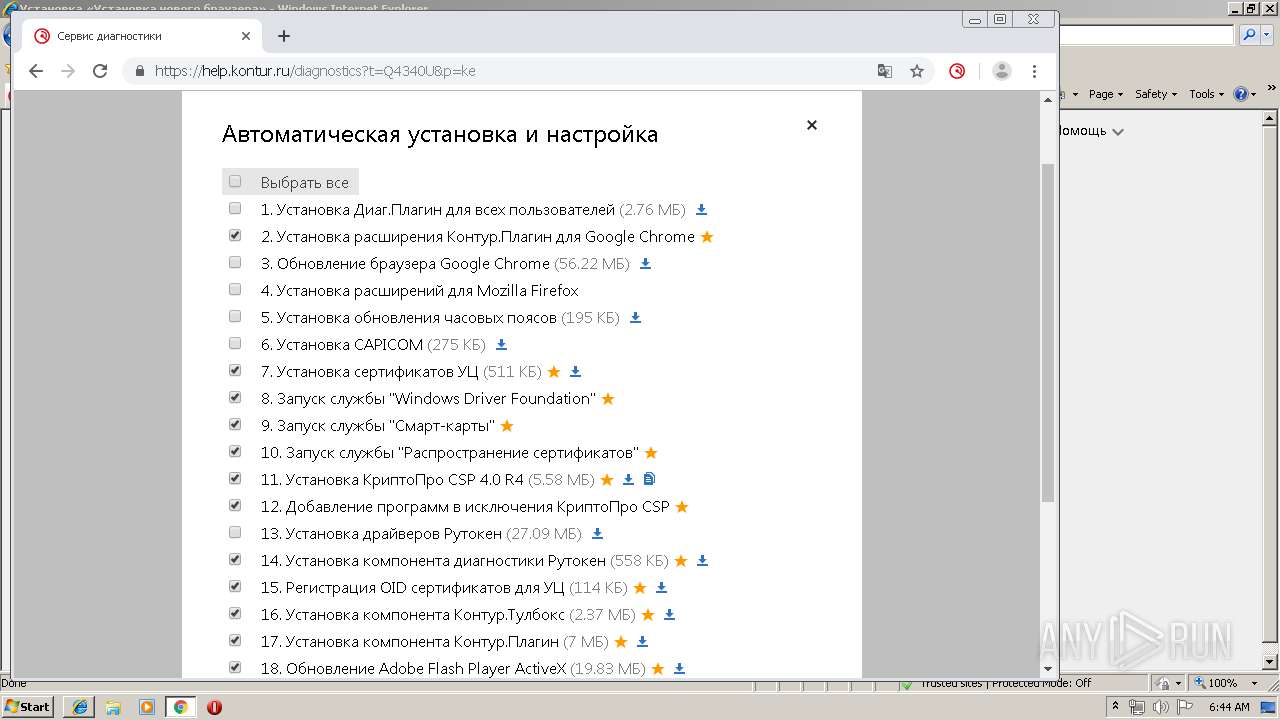
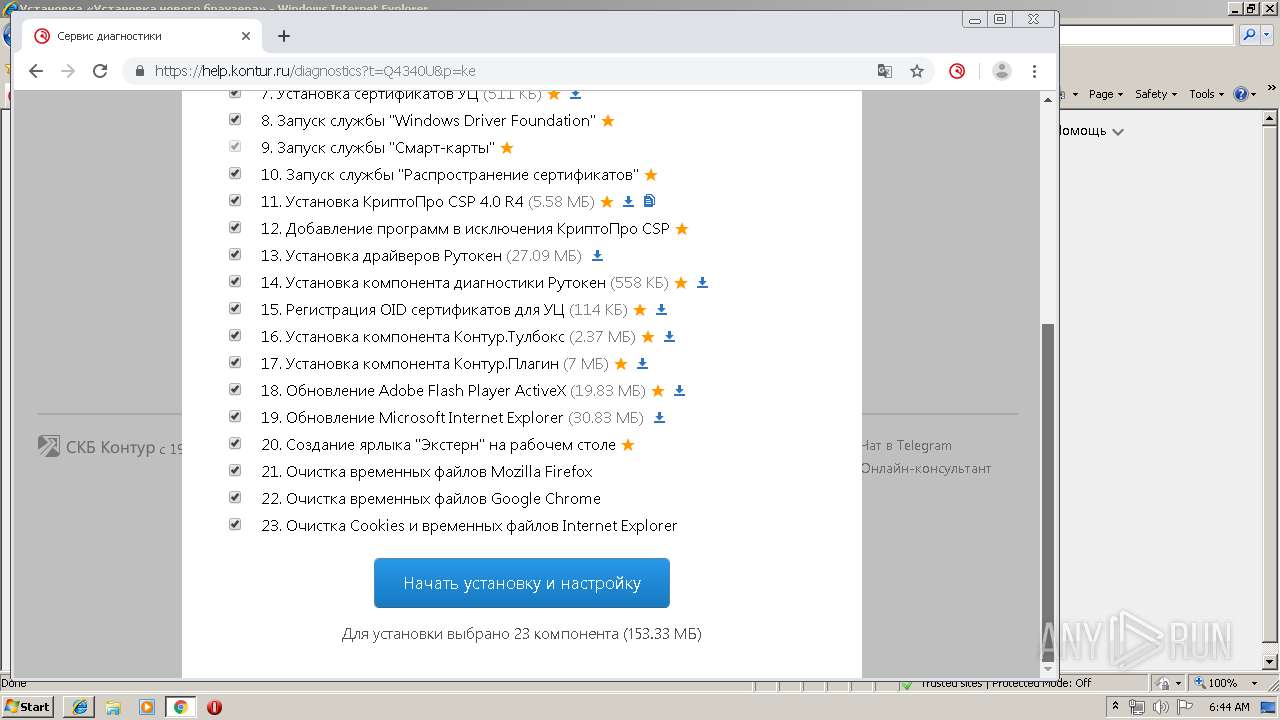
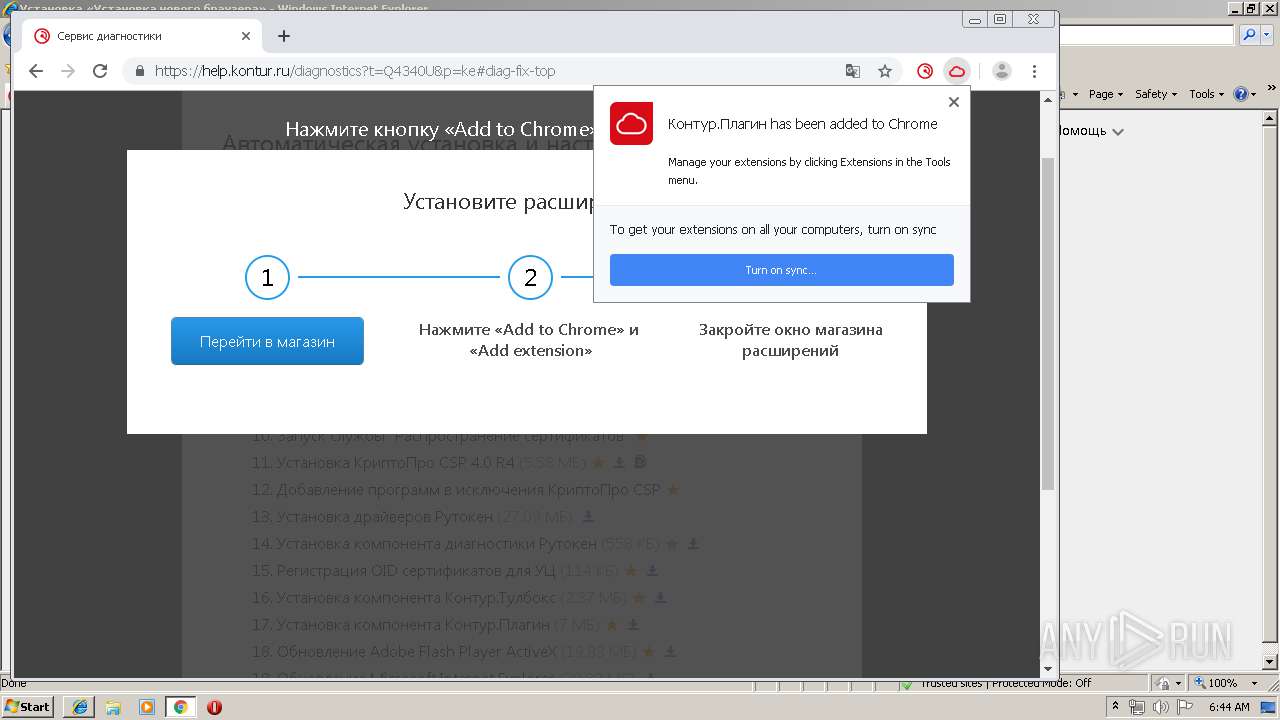
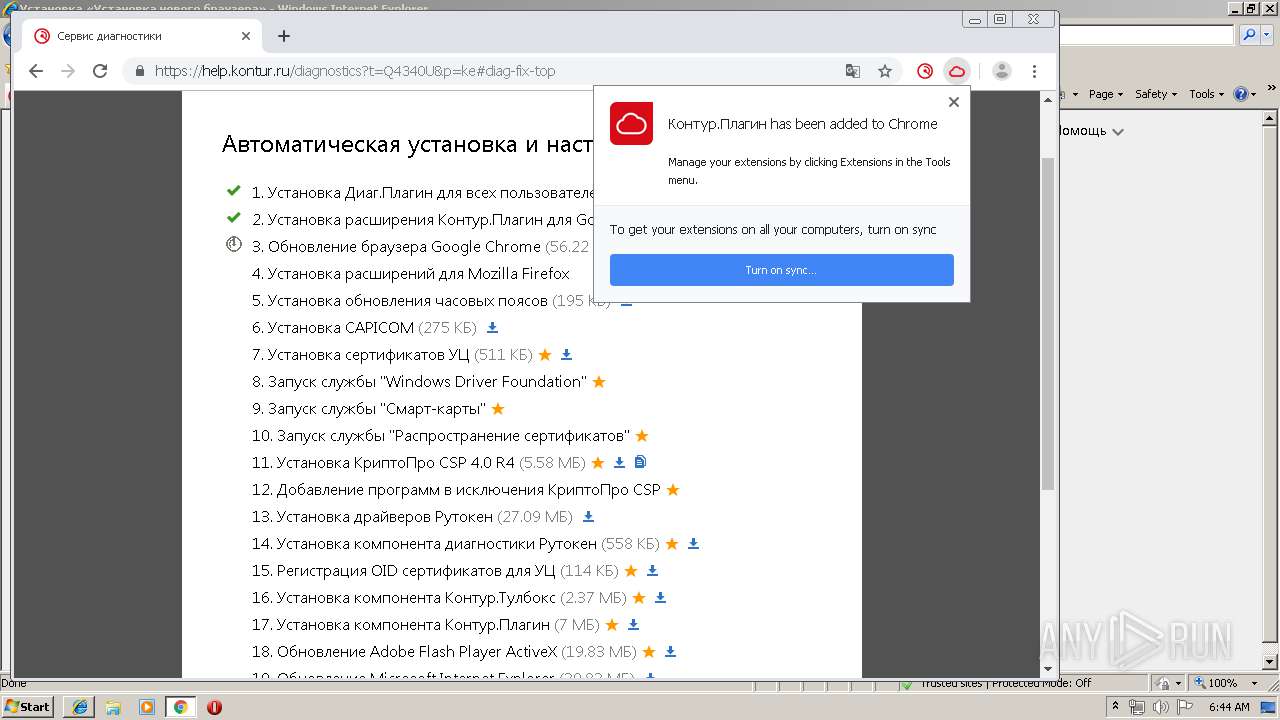
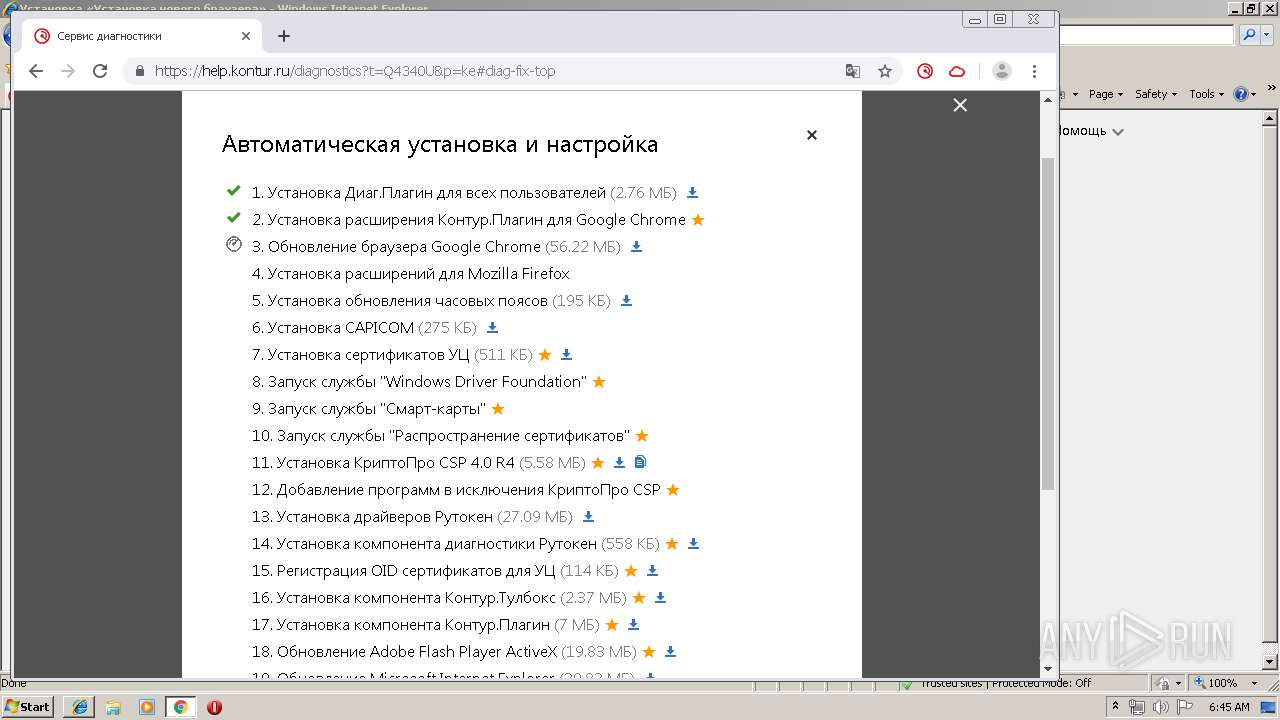
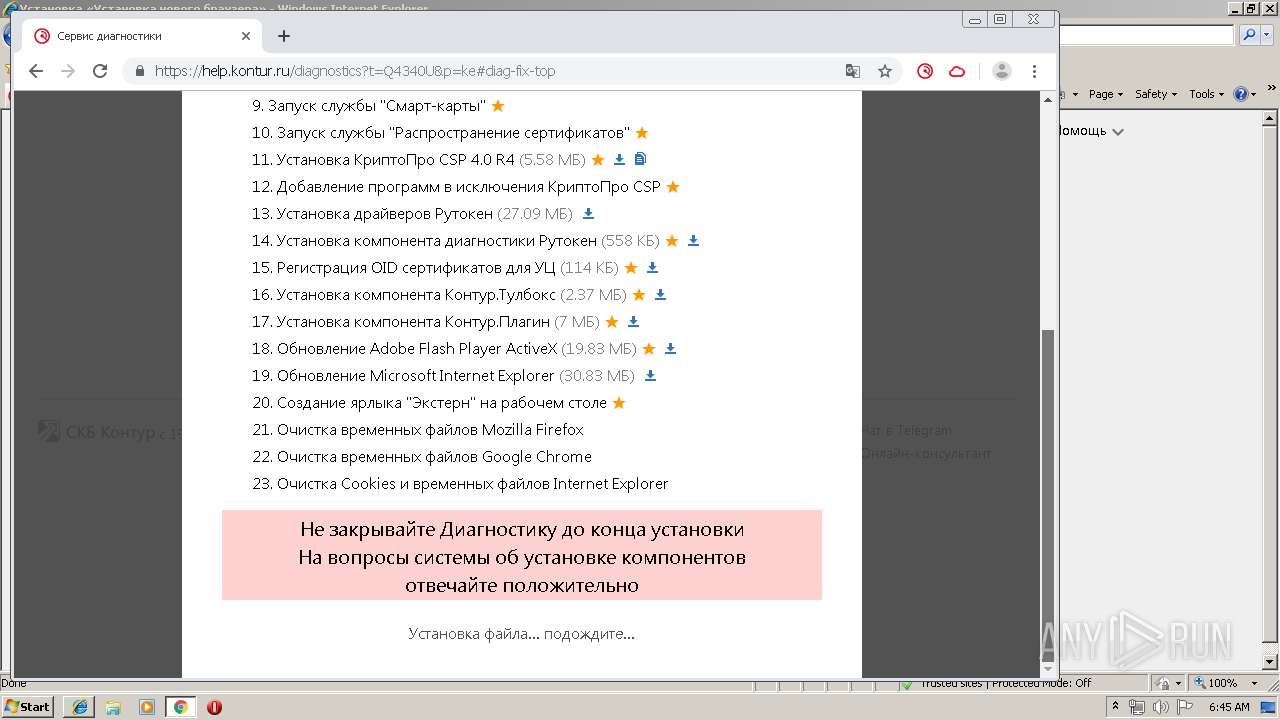
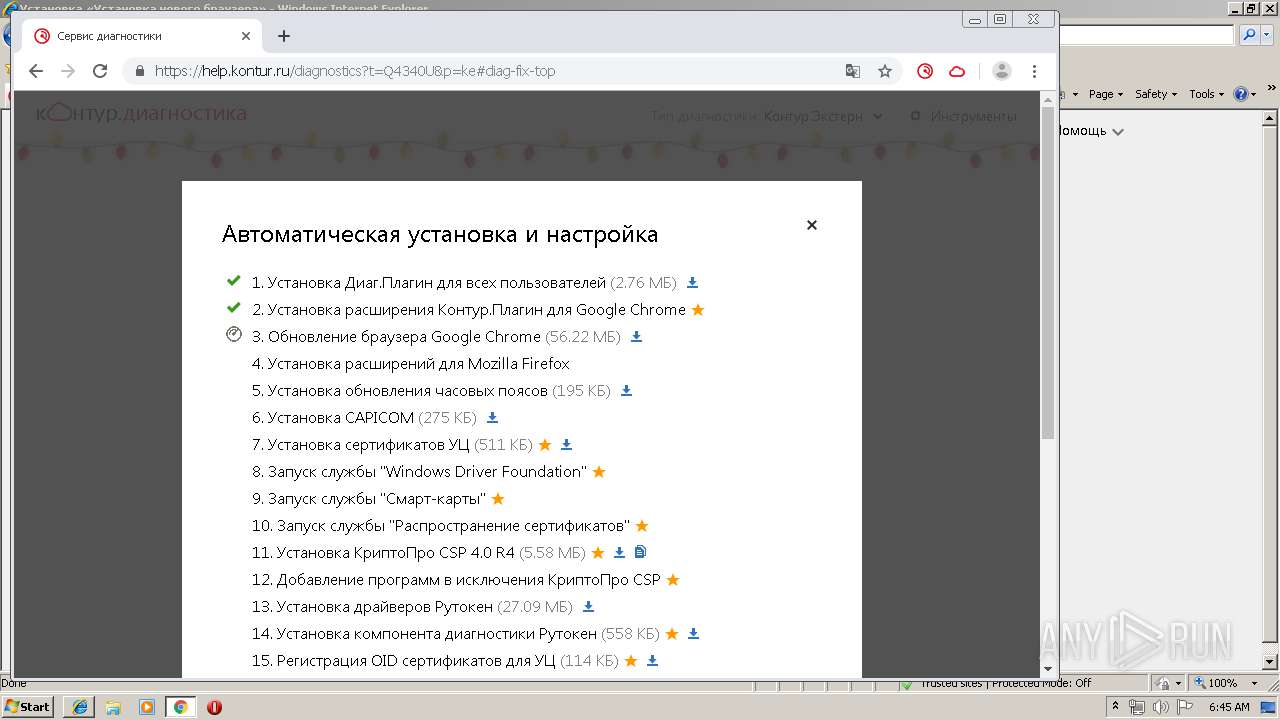
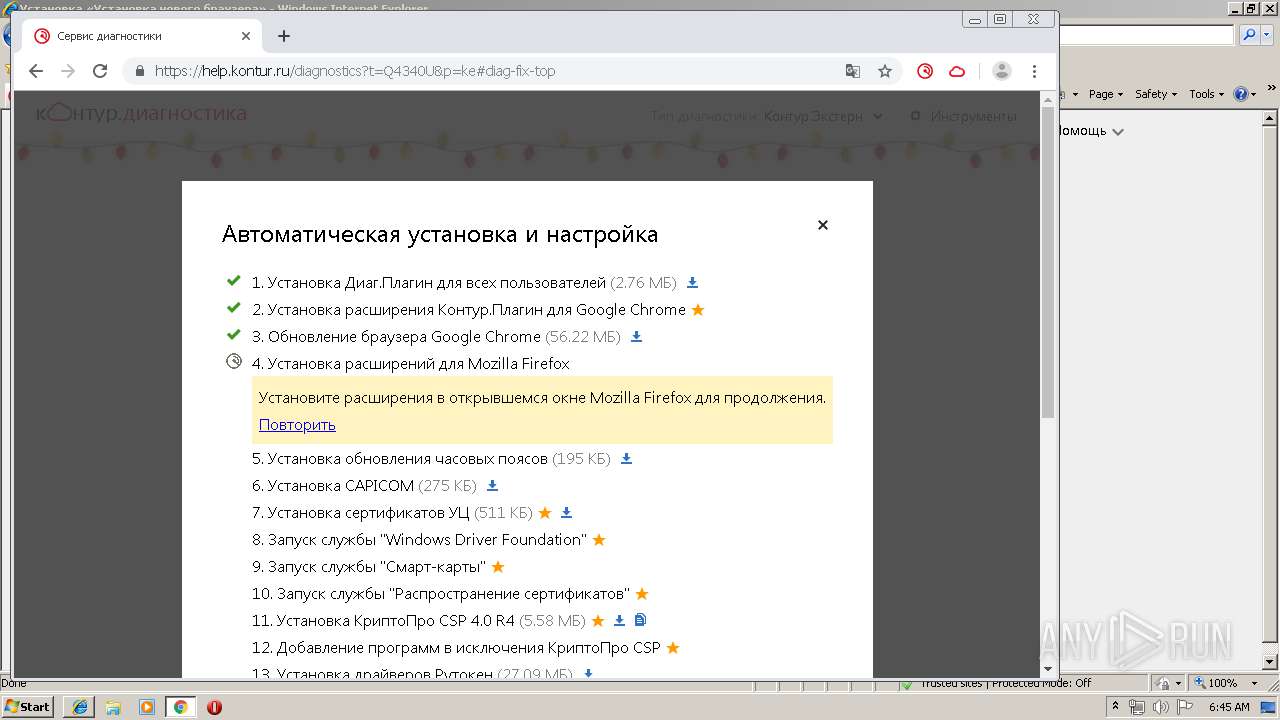
MALICIOUS
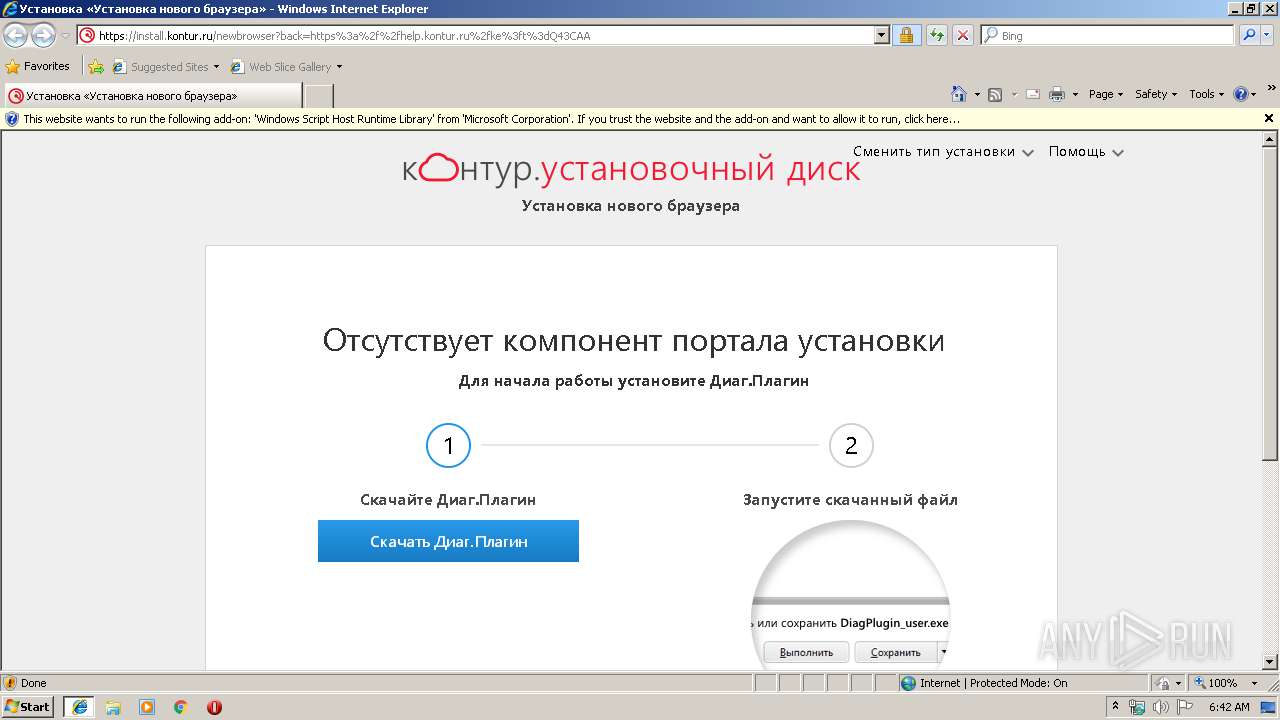
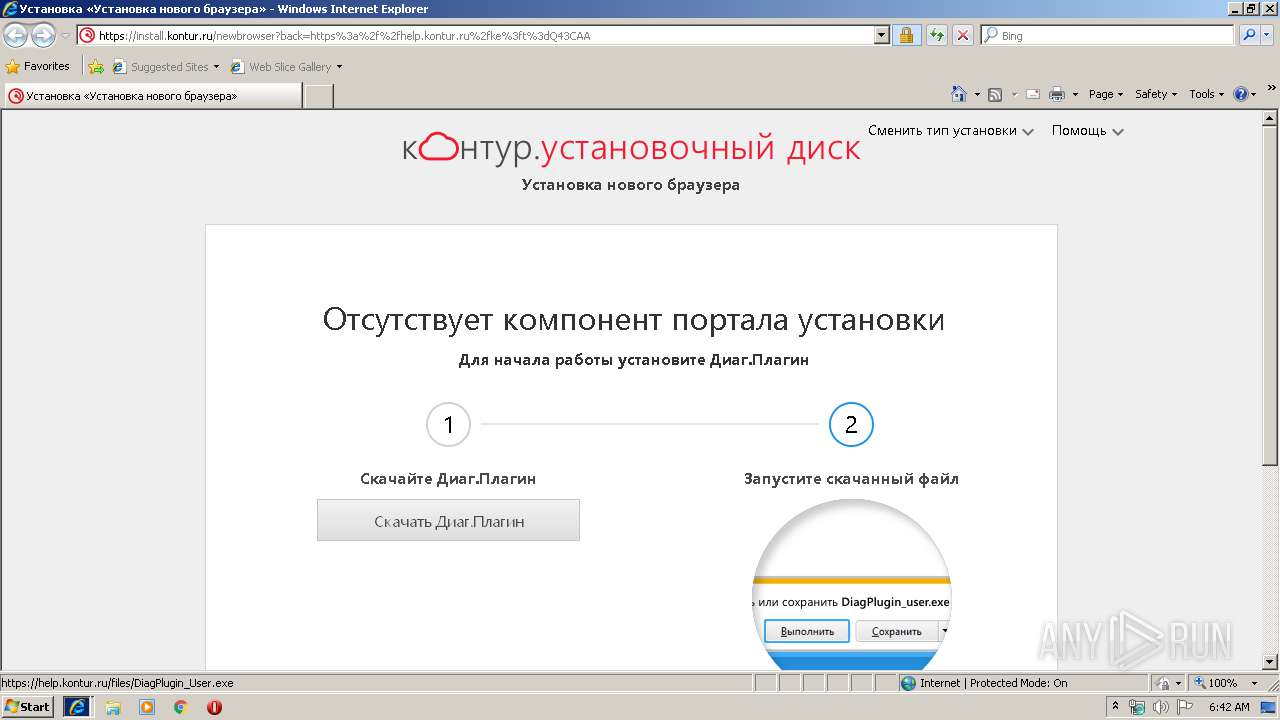
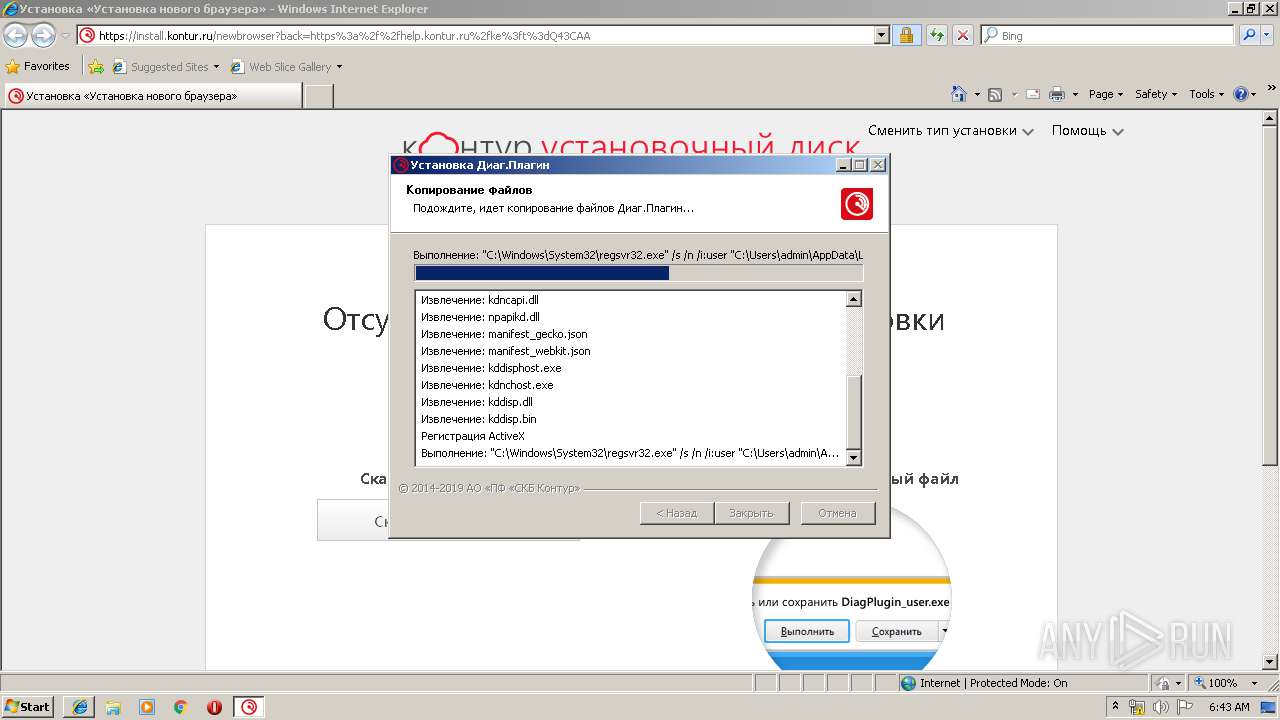
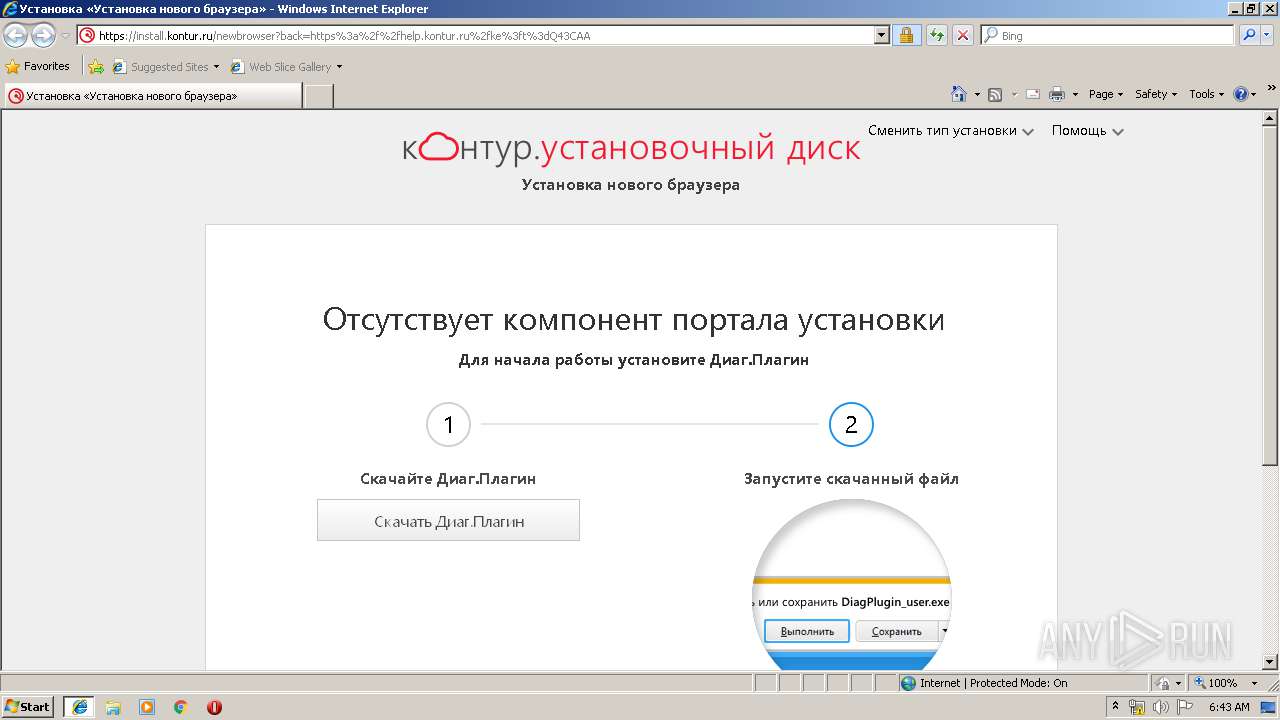
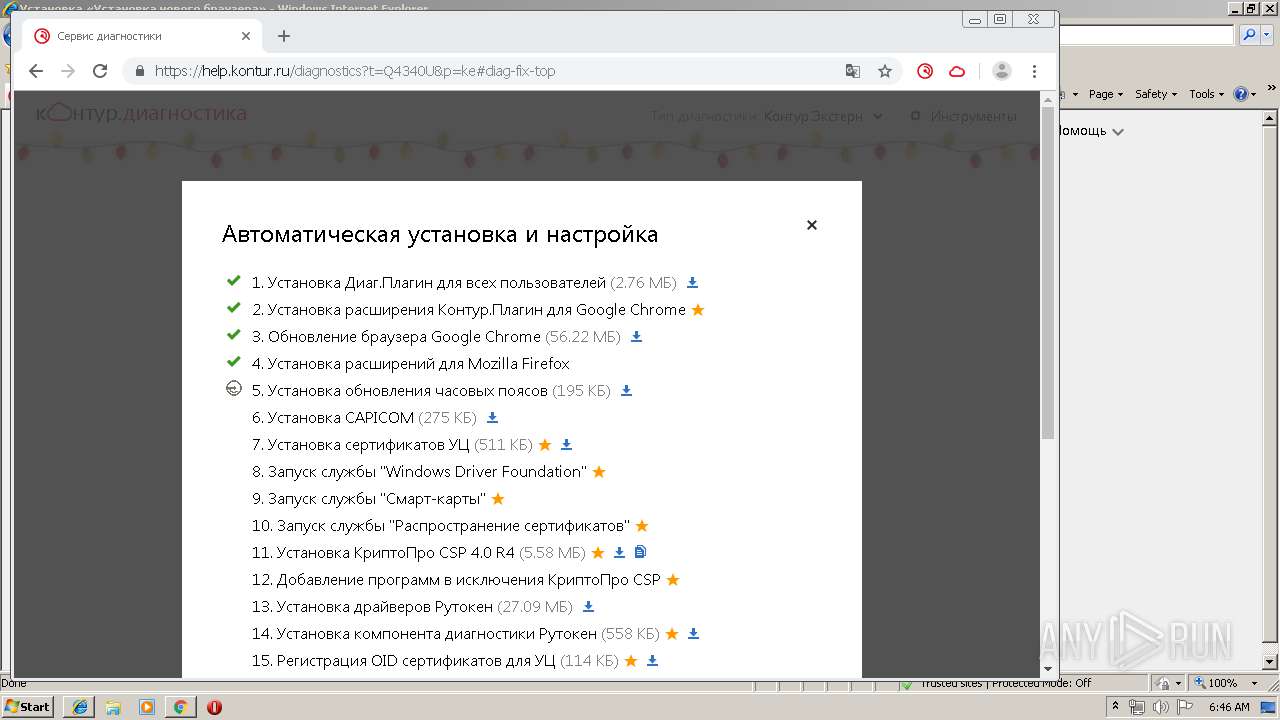
Registers / Runs the DLL via REGSVR32.EXE
- DiagPlugin_user.000629[1].exe (PID: 1636)
- DiagPlugin_admin.exe (PID: 2276)
Loads dropped or rewritten executable
- DiagPlugin_user.000629[1].exe (PID: 1636)
- regsvr32.exe (PID: 2476)
- iexplore.exe (PID: 2260)
- iexplore.exe (PID: 2084)
- kdnchost.exe (PID: 516)
- kdnchost.exe (PID: 1296)
- kdnchost.exe (PID: 2980)
- CertFix_Host.exe (PID: 3432)
- CertFix_Host.exe (PID: 2456)
- kddisphost.exe (PID: 3736)
- DiagPlugin_admin.exe (PID: 2276)
- regsvr32.exe (PID: 3688)
- regsvr32.exe (PID: 3916)
- GoogleUpdate.exe (PID: 3972)
- GoogleUpdate.exe (PID: 1472)
- GoogleUpdate.exe (PID: 3056)
- GoogleUpdate.exe (PID: 3912)
- GoogleUpdate.exe (PID: 1912)
- GoogleUpdate.exe (PID: 4024)
- GoogleUpdate.exe (PID: 3468)
- kdnchost.exe (PID: 4120)
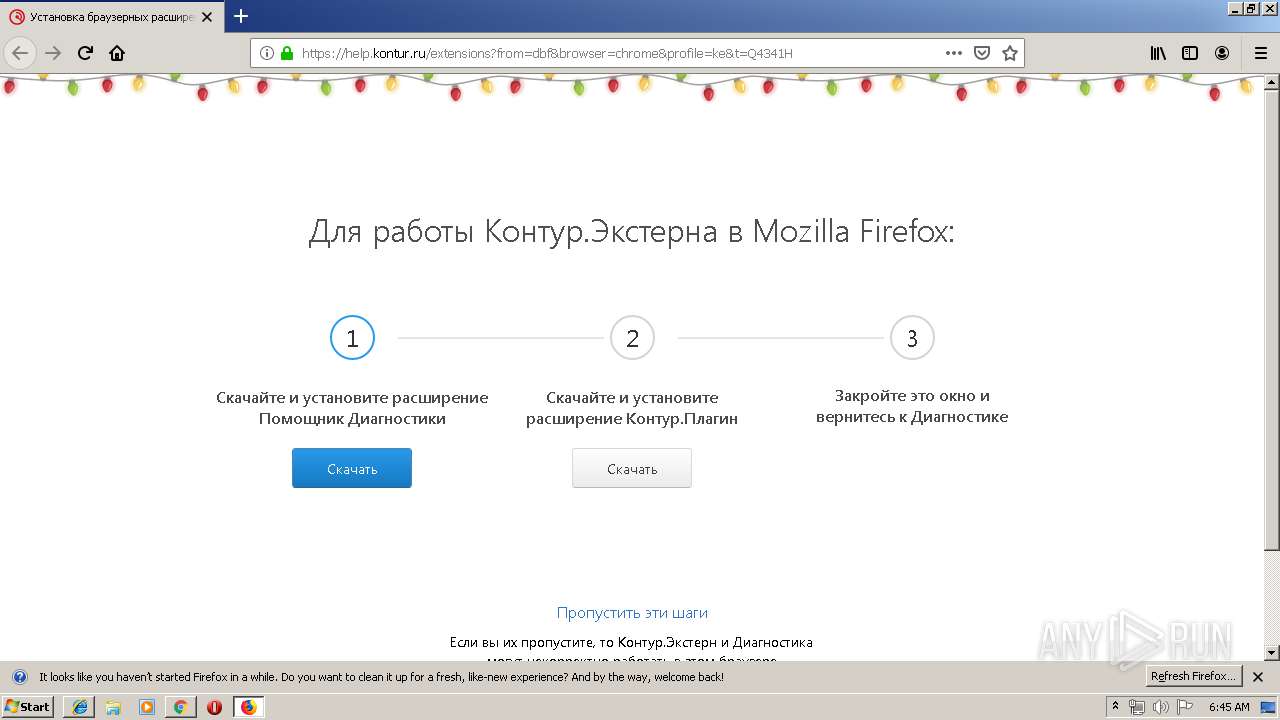
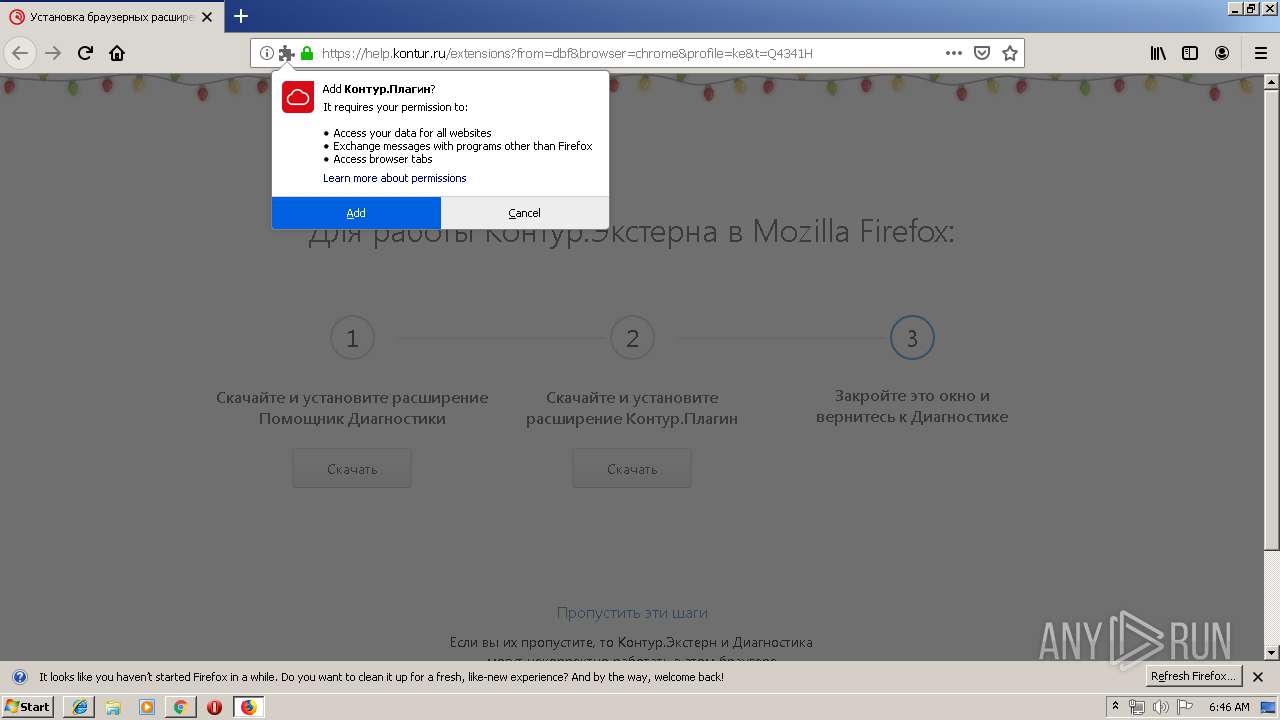
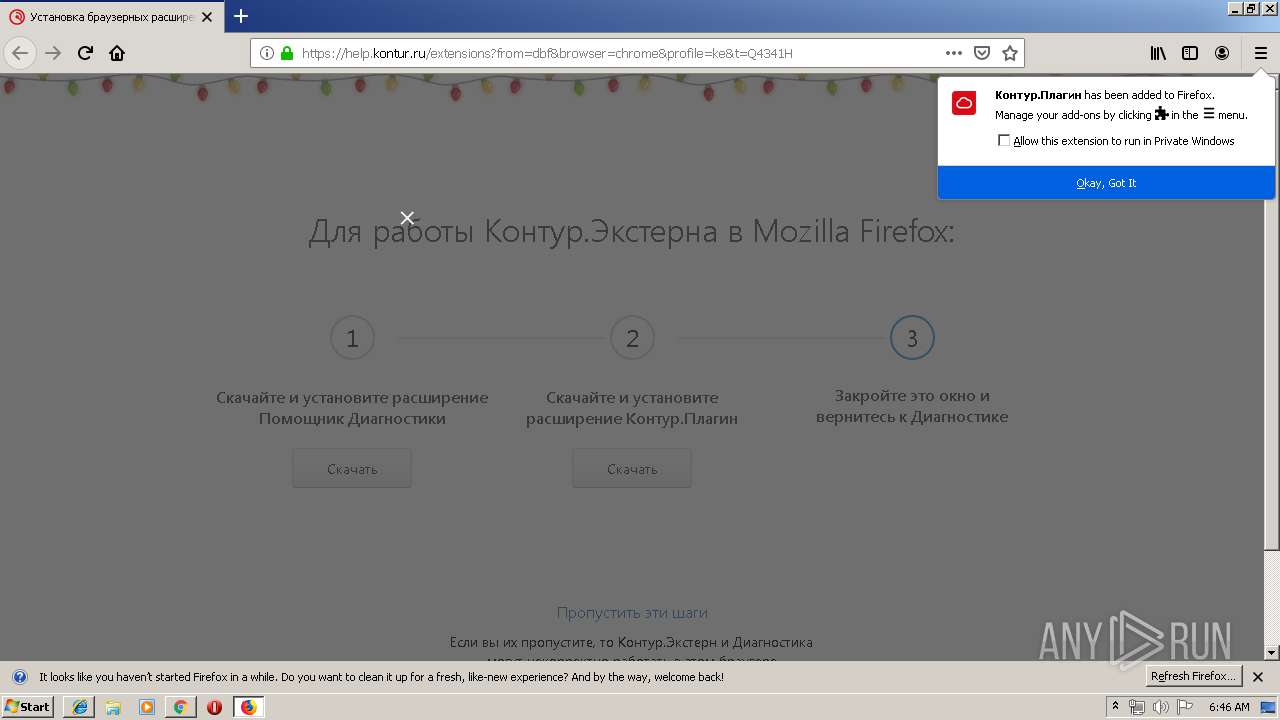
- firefox.exe (PID: 2120)
- updatetimezones_enu.exe (PID: 5012)
- capicom.exe (PID: 4376)
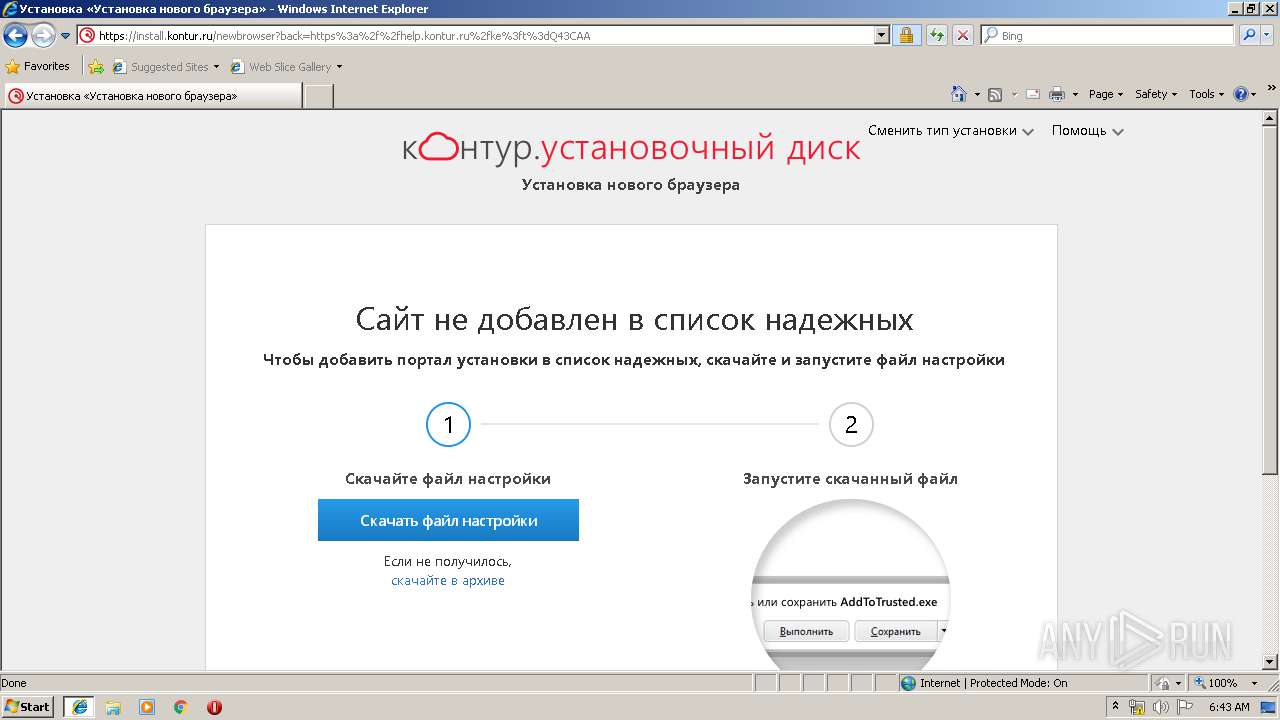
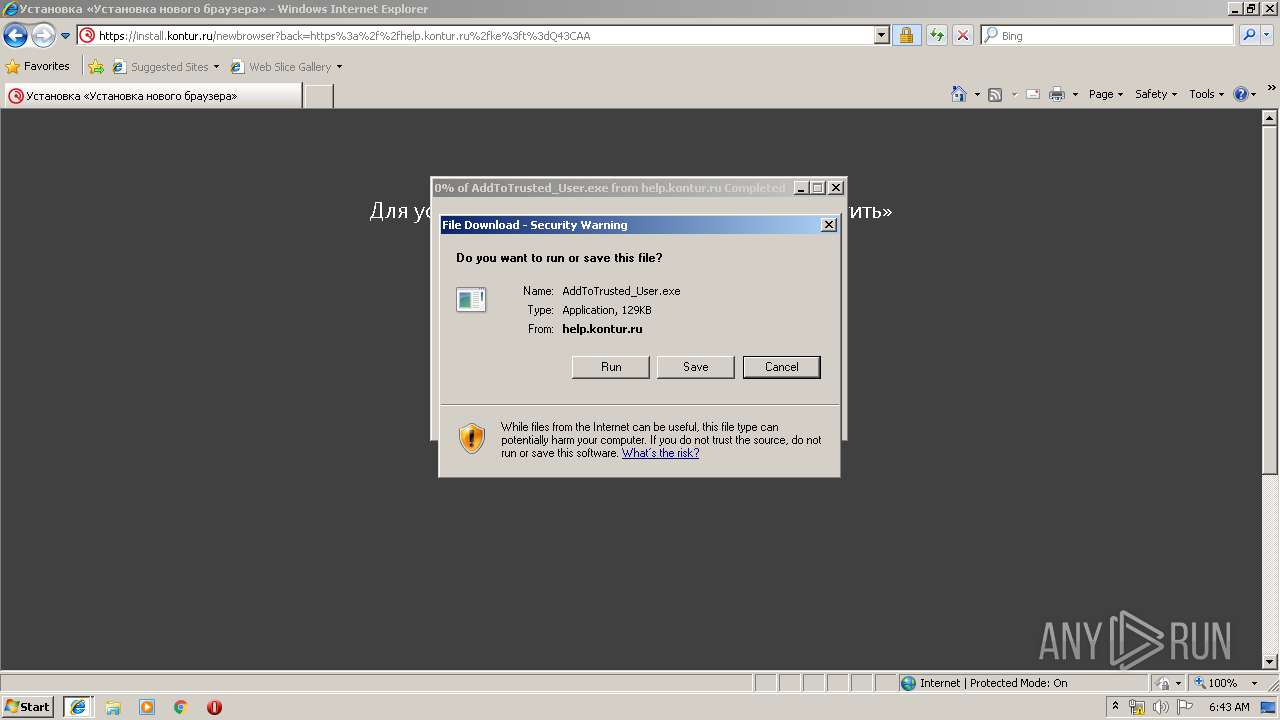
Application was dropped or rewritten from another process
- DiagPlugin_user.000629[1].exe (PID: 1636)
- AddToTrusted_User.exe (PID: 3860)
- addtotrusted_user.exe (PID: 2176)
- addtotrusted_user.exe (PID: 776)
- AddToTrusted_User.exe (PID: 4060)
- addtotrusted_user.exe (PID: 3632)
- addtotrusted_user.exe (PID: 3076)
- AddToTrusted_User[1].exe (PID: 2612)
- kdnchost.exe (PID: 516)
- kdnchost.exe (PID: 1296)
- kdnchost.exe (PID: 2980)
- CertFix_Host.exe (PID: 3432)
- CertFix_Host.exe (PID: 2456)
- kddisphost.exe (PID: 3736)
- DiagPlugin_admin.exe (PID: 2276)
- GoogleUpdate.exe (PID: 1472)
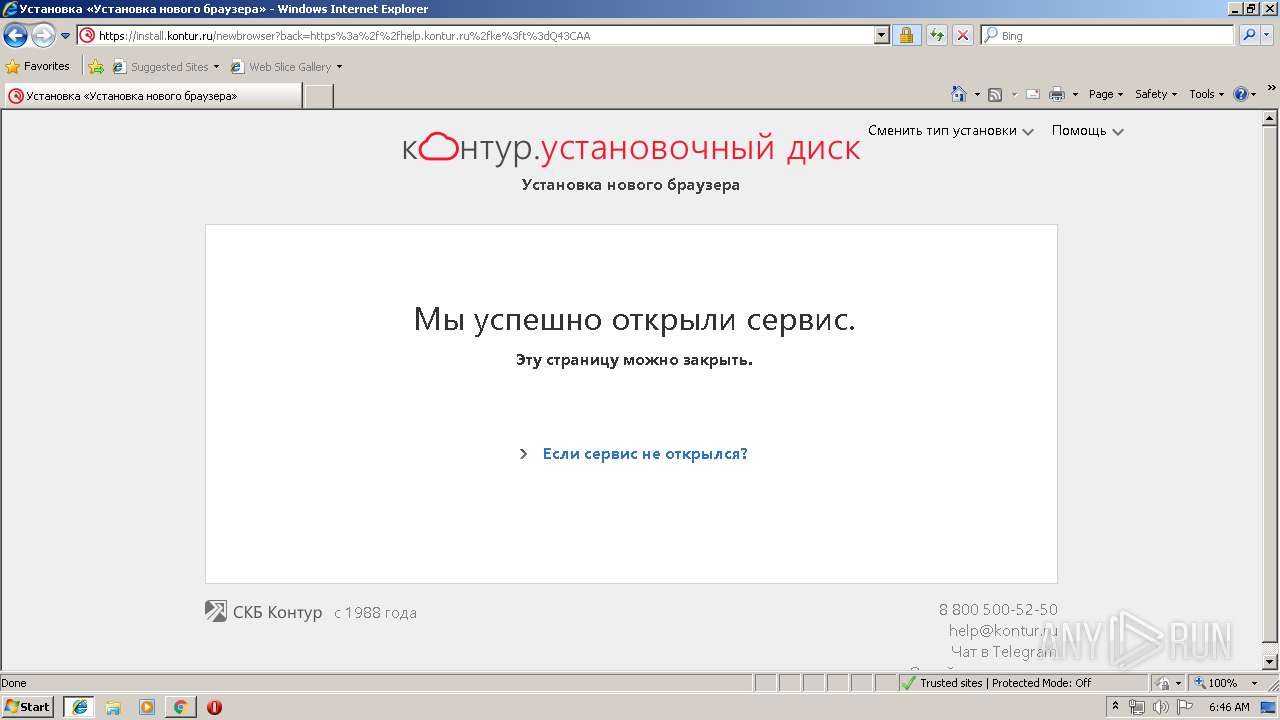
- setup.exe (PID: 2332)
- setup.exe (PID: 2288)
- updatetimezones_enu.exe (PID: 5012)
- nsA468.tmp (PID: 4360)
- tzutil.exe (PID: 4604)
- nsA553.tmp (PID: 5088)
- tzutil.exe (PID: 5632)
- capicom.exe (PID: 4376)
- kdnchost.exe (PID: 4120)
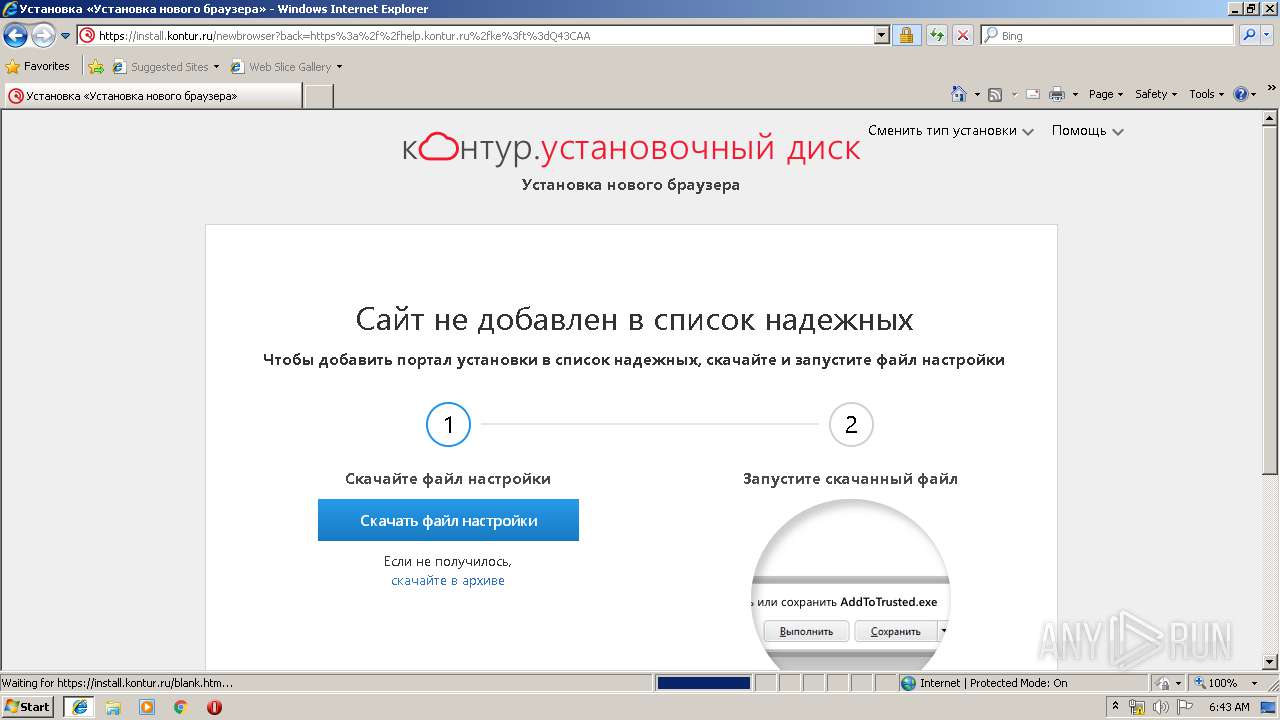
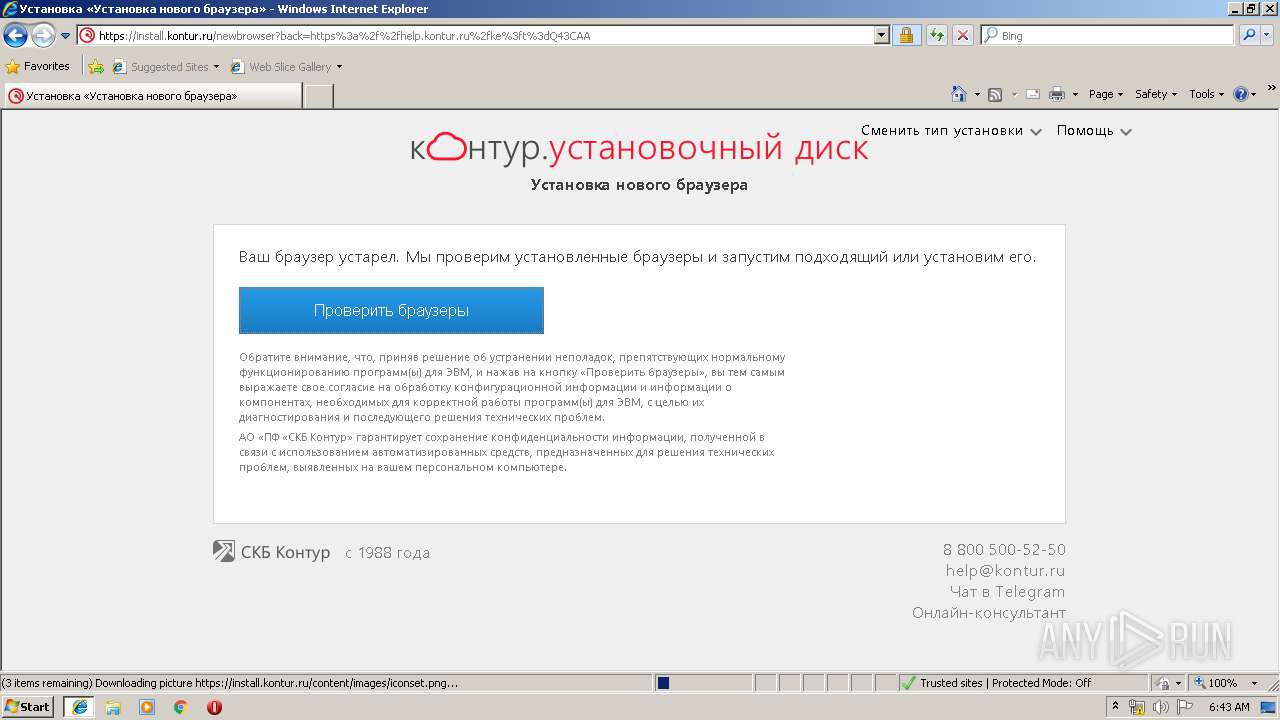
Changes internet zones settings
- AddToTrusted_User[1].exe (PID: 2612)
- DiagPlugin_user.000629[1].exe (PID: 1636)
- DiagPlugin_admin.exe (PID: 2276)
Changes settings of System certificates
- kdnchost.exe (PID: 516)
- kdnchost.exe (PID: 1296)
- kdnchost.exe (PID: 2980)
- CertFix_Host.exe (PID: 2456)
- kddisphost.exe (PID: 3736)
Loads the Task Scheduler COM API
- kdnchost.exe (PID: 2980)
- GoogleUpdate.exe (PID: 1472)
Changes the autorun value in the registry
- setup.exe (PID: 2332)
SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3248)
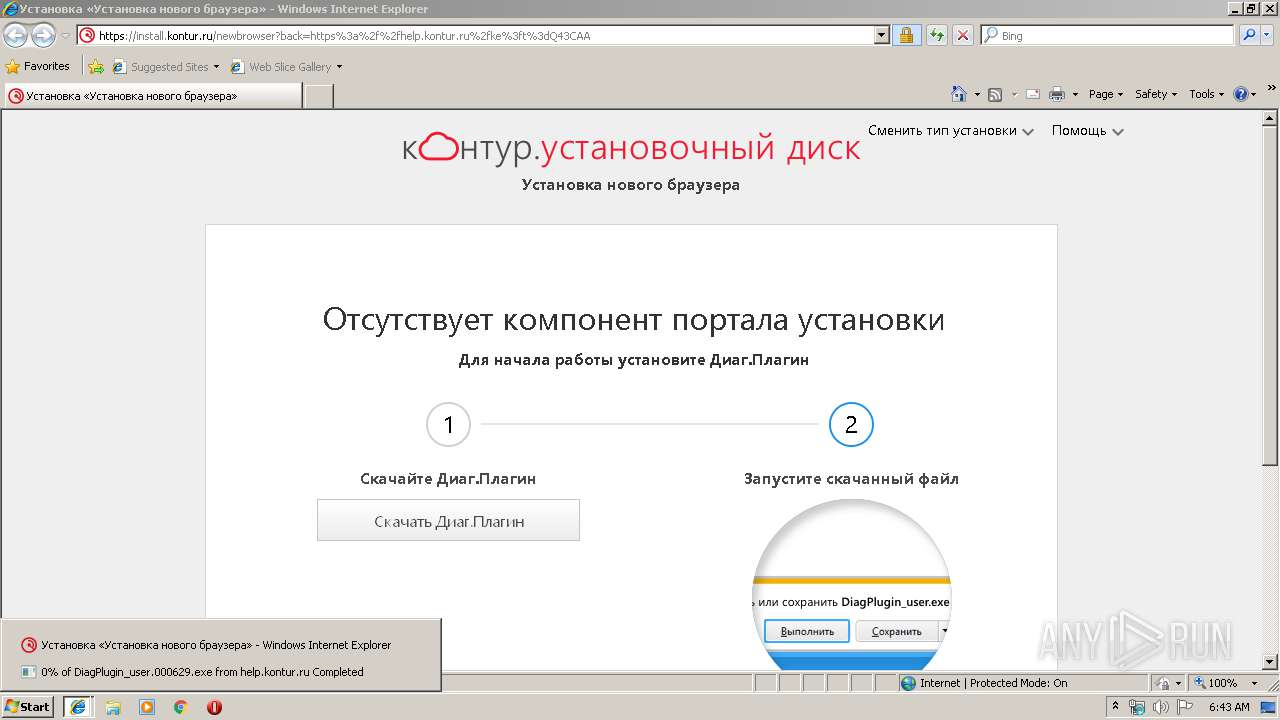
Executable content was dropped or overwritten
- iexplore.exe (PID: 2528)
- iexplore.exe (PID: 1212)
- DiagPlugin_user.000629[1].exe (PID: 1636)
- iexplore.exe (PID: 2260)
- kdnchost.exe (PID: 2980)
- DiagPlugin_admin.exe (PID: 2276)
- GoogleUpdate.exe (PID: 1472)
- chromestandalonesetuplatest.exe (PID: 3780)
- chrome_installer.exe (PID: 2728)
- setup.exe (PID: 2332)
- updatetimezones_enu.exe (PID: 5012)
Creates COM task schedule object
- regsvr32.exe (PID: 2476)
- regsvr32.exe (PID: 3916)
- GoogleUpdate.exe (PID: 3056)
- GoogleUpdate.exe (PID: 1472)
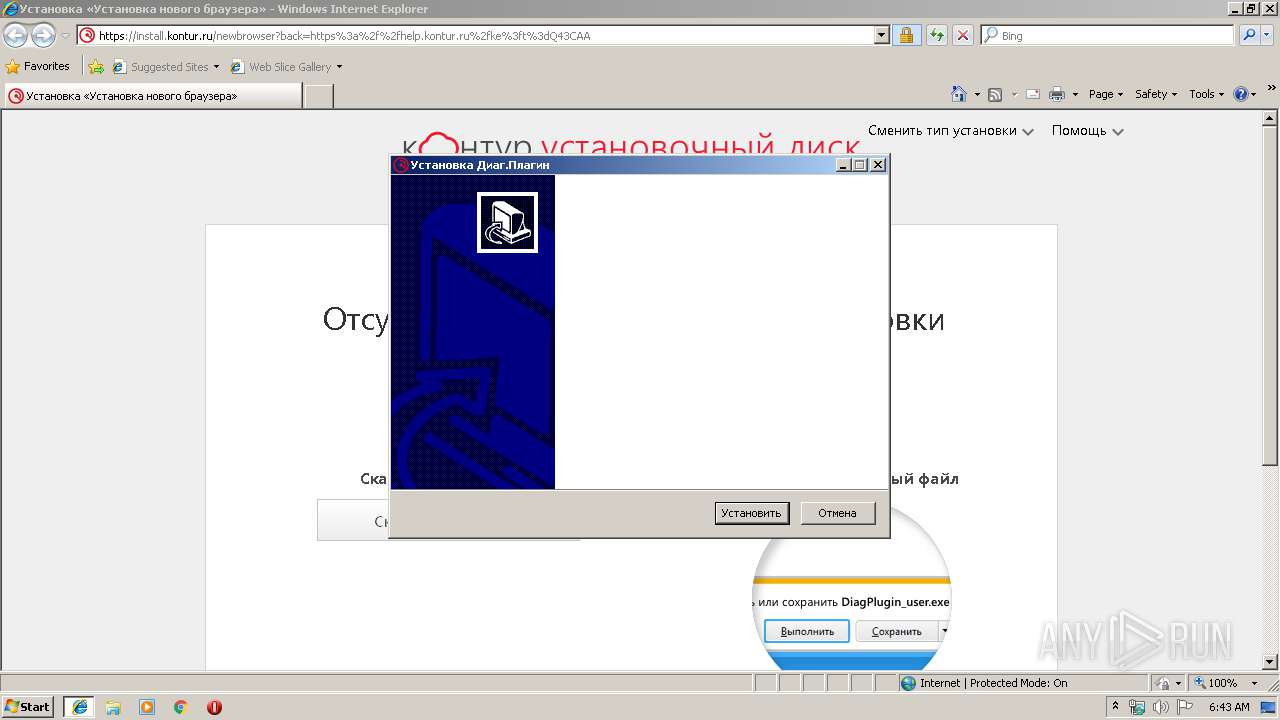
Creates a software uninstall entry
- DiagPlugin_user.000629[1].exe (PID: 1636)
- DiagPlugin_admin.exe (PID: 2276)
- setup.exe (PID: 2332)
Reads Environment values
- iexplore.exe (PID: 2260)
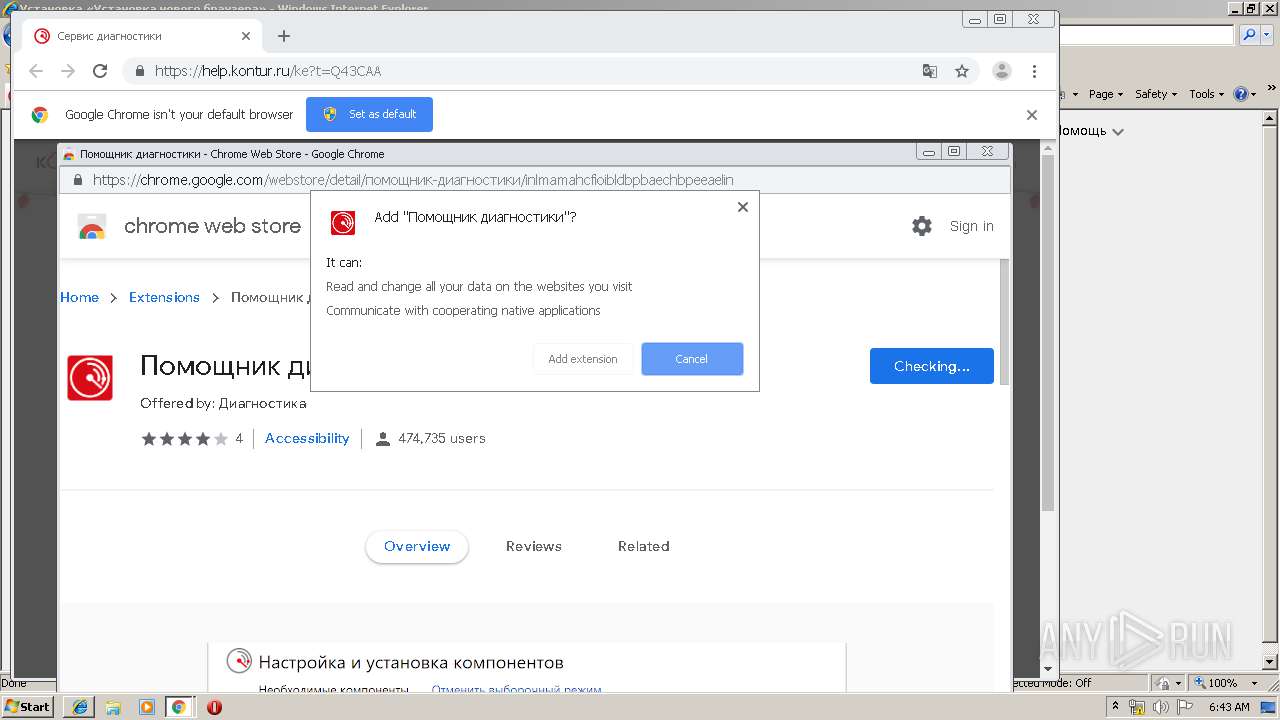
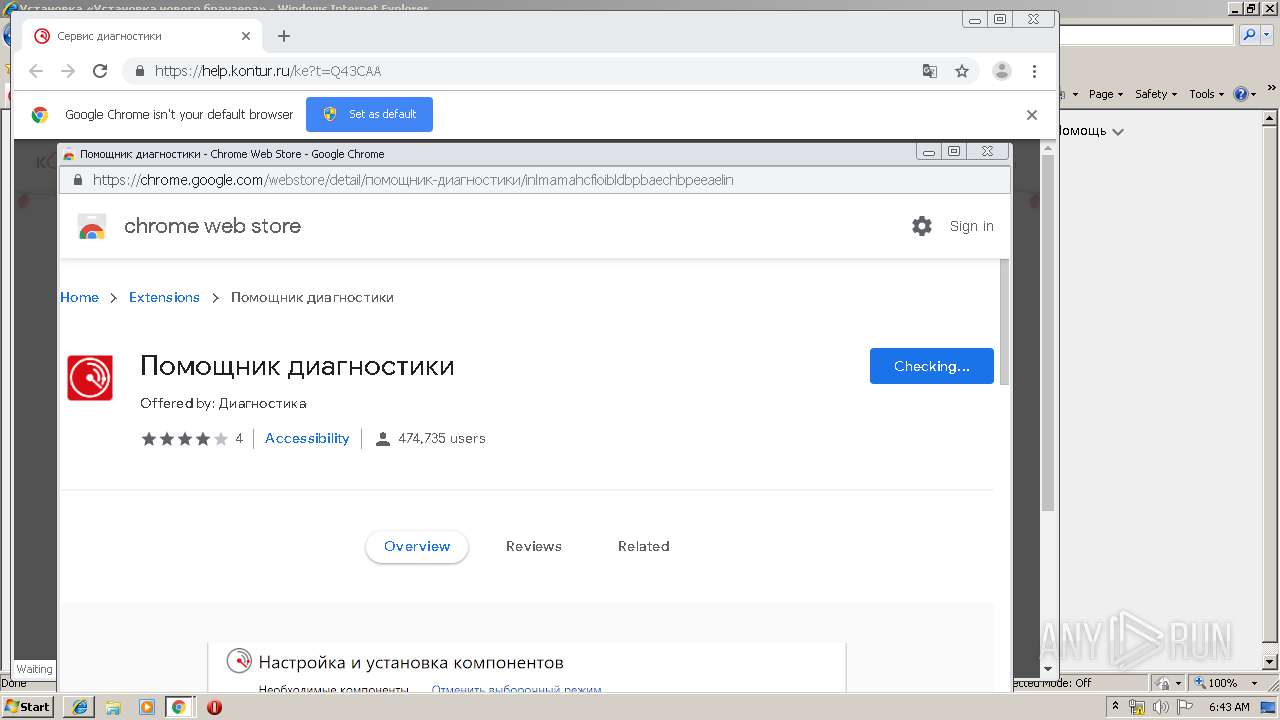
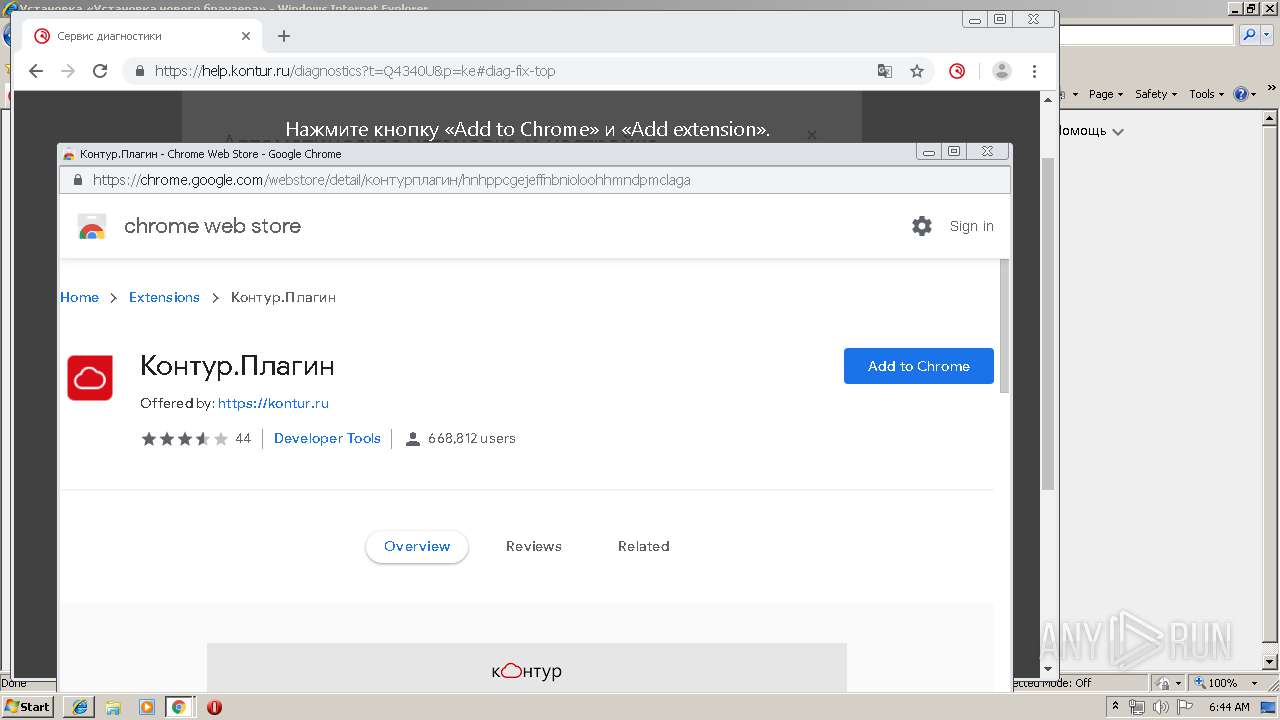
Modifies files in Chrome extension folder
- chrome.exe (PID: 2164)
Starts CMD.EXE for commands execution
- chrome.exe (PID: 2164)
Adds / modifies Windows certificates
- kdnchost.exe (PID: 516)
- kdnchost.exe (PID: 1296)
- kdnchost.exe (PID: 2980)
- CertFix_Host.exe (PID: 2456)
- kddisphost.exe (PID: 3736)
Searches for installed software
- kdnchost.exe (PID: 2980)
Creates files in the program directory
- DiagPlugin_admin.exe (PID: 2276)
- chromestandalonesetuplatest.exe (PID: 3780)
- GoogleUpdate.exe (PID: 1472)
- GoogleUpdate.exe (PID: 1912)
- firefox.exe (PID: 2120)
- setup.exe (PID: 2332)
Disables SEHOP
- GoogleUpdate.exe (PID: 1472)
Executed as Windows Service
- GoogleUpdate.exe (PID: 1912)
Application launched itself
- GoogleUpdate.exe (PID: 1912)
Modifies the open verb of a shell class
- setup.exe (PID: 2332)
Starts application with an unusual extension
- updatetimezones_enu.exe (PID: 5012)
Creates files in the Windows directory
- updatetimezones_enu.exe (PID: 5012)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2528)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3248)
- iexplore.exe (PID: 2260)
- iexplore.exe (PID: 1212)
- iexplore.exe (PID: 2084)
- chrome.exe (PID: 2164)
- firefox.exe (PID: 2120)
Changes internet zones settings
- iexplore.exe (PID: 2528)
Reads Internet Cache Settings
- iexplore.exe (PID: 2260)
- iexplore.exe (PID: 1212)
- iexplore.exe (PID: 2528)
- chrome.exe (PID: 2164)
Reads internet explorer settings
- iexplore.exe (PID: 2260)
- iexplore.exe (PID: 1212)
- iexplore.exe (PID: 2084)
Reads settings of System Certificates
- iexplore.exe (PID: 2528)
- CertFix_Host.exe (PID: 2456)
Application launched itself
- iexplore.exe (PID: 2528)
- chrome.exe (PID: 2164)
- firefox.exe (PID: 2768)
- firefox.exe (PID: 2120)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2084)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2084)
Reads the hosts file
- chrome.exe (PID: 3252)
- chrome.exe (PID: 2164)
Changes settings of System certificates
- iexplore.exe (PID: 2084)
Reads CPU info
- firefox.exe (PID: 2120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
155
Monitored processes
98
Malicious processes
23
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,7668939742481750161,3477074223474055574,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3386398651784609945 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 516 | C:\Users\admin\AppData\Local\SkbKontur\DiagPlugin\3.0.23.207\kdnchost.exe chrome-extension://inlmamahcfioibldbpbaechbpeeaelin/ --parent-window=0 | C:\Users\admin\AppData\Local\SkbKontur\DiagPlugin\3.0.23.207\kdnchost.exe | — | cmd.exe | |||||||||||
User: admin Company: АО "ПФ "СКБ Контур" Integrity Level: MEDIUM Description: Диаг.Плагин - хост-приложение Native Client Exit code: 0 Version: 1.207.28.129 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,7668939742481750161,3477074223474055574,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9546468496791742871 --mojo-platform-channel-handle=3924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 776 | "C:\Users\admin\AppData\Local\Temp\Low\HelpKontur\k5dif5zv\addtotrusted_user.exe" | C:\Users\admin\AppData\Local\Temp\Low\HelpKontur\k5dif5zv\addtotrusted_user.exe | — | iexplore.exe | |||||||||||
User: admin Company: АО "ПФ "СКБ Контур" Integrity Level: LOW Description: Настройка зоны "Надежные сайты" Exit code: 5 Version: 2.0.19.4 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,7668939742481750161,3477074223474055574,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7230983133753327142 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2120.3.1230354310\443638161" -childID 1 -isForBrowser -prefsHandle 1320 -prefMapHandle 776 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2120 "\\.\pipe\gecko-crash-server-pipe.2120" 1608 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,7668939742481750161,3477074223474055574,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17480220722606449199 --mojo-platform-channel-handle=1924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1188 | C:\Windows\system32\cmd.exe /d /c "C:\Users\admin\AppData\Local\SkbKontur\DiagPlugin\3.0.23.207\kdnchost.exe" chrome-extension://inlmamahcfioibldbpbaechbpeeaelin/ --parent-window=0 < \\.\pipe\chrome.nativeMessaging.in.347c72eb4f93e122 > \\.\pipe\chrome.nativeMessaging.out.347c72eb4f93e122 | C:\Windows\system32\cmd.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2528 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,7668939742481750161,3477074223474055574,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15331452819541675999 --mojo-platform-channel-handle=3856 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
8 705
Read events
4 988
Write events
3 491
Delete events
226
Modification events
| (PID) Process: | (2528) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2528) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2528) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2528) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2528) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2528) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2528) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {FC8E6705-3698-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2528) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2528) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2528) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E407010002000E0006002A000A00C100 | |||
Executable files
220
Suspicious files
172
Text files
604
Unknown types
190
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2528 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2528 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DJZQXK78\newbrowser[1].txt | — | |
MD5:— | SHA256:— | |||
| 2260 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@kontur[1].txt | text | |
MD5:— | SHA256:— | |||
| 2260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2260 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DJZQXK78\newbrowser[1].htm | html | |
MD5:— | SHA256:— | |||
| 2260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\Q4TYNFAZ\csspack[1].css | text | |
MD5:— | SHA256:— | |||
| 2260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PU7TA3PL\logo-extern[1].gif | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
166
DNS requests
139
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2260 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp2.globalsign.com/rootr3/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDkgbagepQkweqv7zzfEP | US | der | 1.48 Kb | whitelisted |
2260 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://ocsp.thawte.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQJ1TBLBrQ9OnPHXPVaWb87MxkNlgQUwu79F9f%2Btw%2FGciJ7fvbA4gIz7D4CEH6T6%2Ft8xk5Z6kuad9QG%2FDs%3D | NL | der | 1.30 Kb | whitelisted |
2260 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://ts-ocsp.ws.symantec.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRi82PVYYKWGJWdgVNyePy5kYTdqQQUX5r1blzMzHSa1N197z%2Fb7EyALt0CEA7P9DjI%2Fr81bgTYapgbGlA%3D | NL | der | 1.43 Kb | whitelisted |
2260 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp2.globalsign.com/gsextendcodesignsha2g3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQ3DAV9N6WelMGCzSTdNIqjdmfHiAQU3CxYLCpvNS2feZWoSF3EbT5Tv7kCDEDpfxhRWoewamhEKQ%3D%3D | US | der | 1.55 Kb | whitelisted |
3252 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2456 | CertFix_Host.exe | GET | 200 | 93.184.220.29:80 | http://crl.verisign.com/pca3.crl | US | der | 1.08 Kb | whitelisted |
3252 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
1080 | svchost.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | der | 813 b | whitelisted |
2120 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://status.rapidssl.com/ | US | der | 471 b | shared |
3252 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1212 | iexplore.exe | 46.17.203.72:443 | s.kontur.ru | CJSC Production Company SKB Kontur | RU | unknown |
1212 | iexplore.exe | 172.217.21.200:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1212 | iexplore.exe | 172.217.18.104:443 | ssl.google-analytics.com | Google Inc. | US | suspicious |
2528 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2260 | iexplore.exe | 46.17.203.51:443 | help.kontur.ru | CJSC Production Company SKB Kontur | RU | suspicious |
2260 | iexplore.exe | 46.17.203.45:443 | api.kontur.ru | CJSC Production Company SKB Kontur | RU | unknown |
2260 | iexplore.exe | 172.217.18.104:443 | ssl.google-analytics.com | Google Inc. | US | suspicious |
1212 | iexplore.exe | 172.217.18.162:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
1212 | iexplore.exe | 217.69.133.145:443 | top-fwz1.mail.ru | Limited liability company Mail.Ru | RU | suspicious |
1212 | iexplore.exe | 77.88.21.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
help.kontur.ru |
| suspicious |
www.bing.com |
| whitelisted |
install.kontur.ru |
| suspicious |
api.kontur.ru |
| unknown |
ssl.google-analytics.com |
| whitelisted |
metrika.kontur.ru |
| unknown |
kontur.ru |
| whitelisted |
s.kontur.ru |
| unknown |
www.googletagmanager.com |
| whitelisted |
kontur.site |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
24 ETPRO signatures available at the full report
Process | Message |
|---|---|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_PROCESS_ATTACH
|
CertFix_Host.exe | DLL_PROCESS_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|
CertFix_Host.exe | DLL_THREAD_ATTACH
|