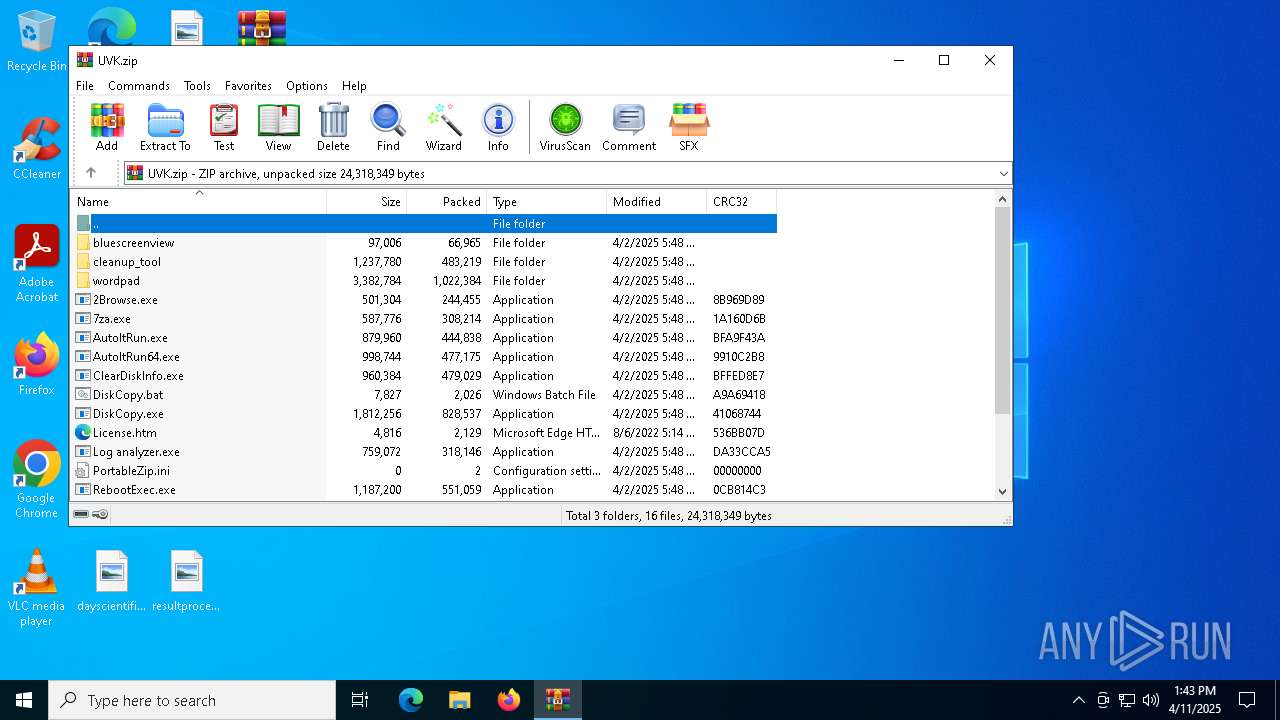
| File name: | UVK.zip |
| Full analysis: | https://app.any.run/tasks/4b74499a-778a-42cf-9eab-60751b867229 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2025, 13:43:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 1A2824A15BE321DC0B5528676569CDA7 |
| SHA1: | 7D6D0A4E575791F40E49980D0B88B881B9235FCB |
| SHA256: | E4AEDAB2BED230A2C67BC5CD9C5128E567289E8417C9659C2C7A4EEE5F672C27 |
| SSDEEP: | 98304:QaGMtowojMI2TN2TvtRsjCdyrc8OpocohCxNX3tlbAHwE+o8NeheezPT4yP5yVZm:9Ic9Ys3L5PiC6zzzEEhBiQJfa |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts a Microsoft application from unusual location
- cleanup.exe (PID: 7676)
- cleanup.exe (PID: 7628)
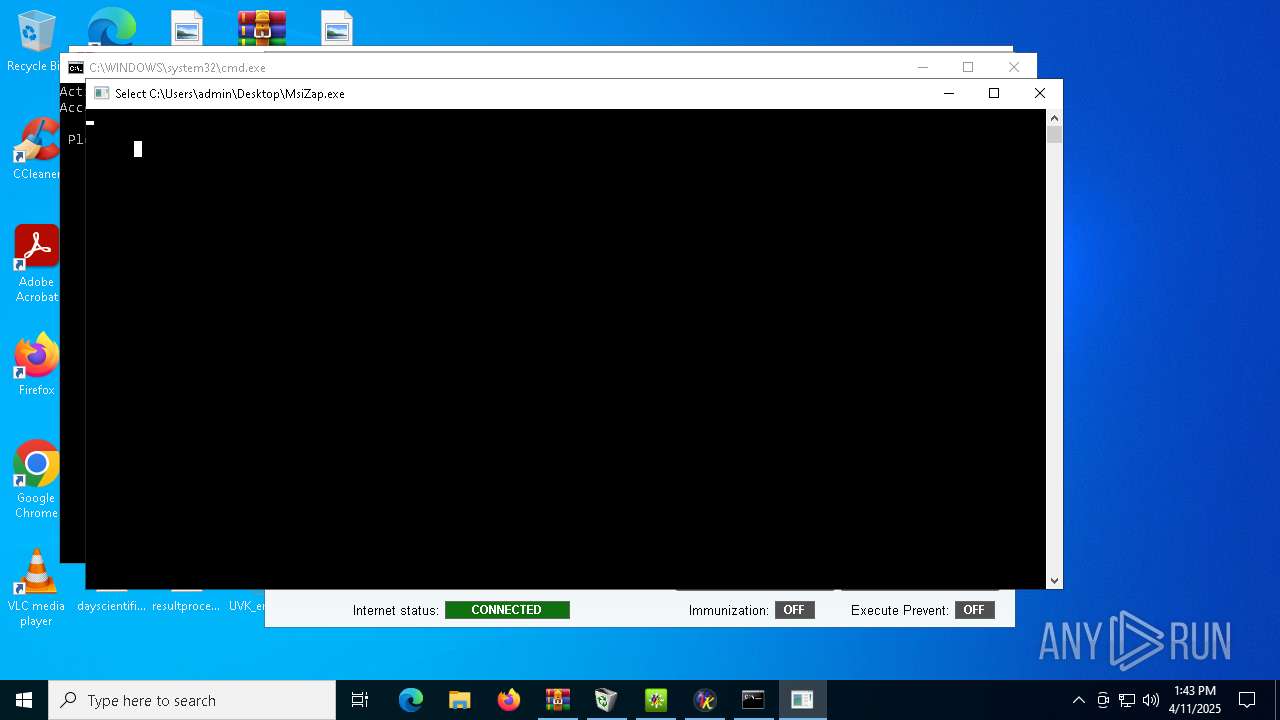
- MsiZap.exe (PID: 6032)
- MsiZap.exe (PID: 2148)
The process checks if it is being run in the virtual environment
- UVK_en64.exe (PID: 7904)
Reads security settings of Internet Explorer
- UVK_en64.exe (PID: 7904)
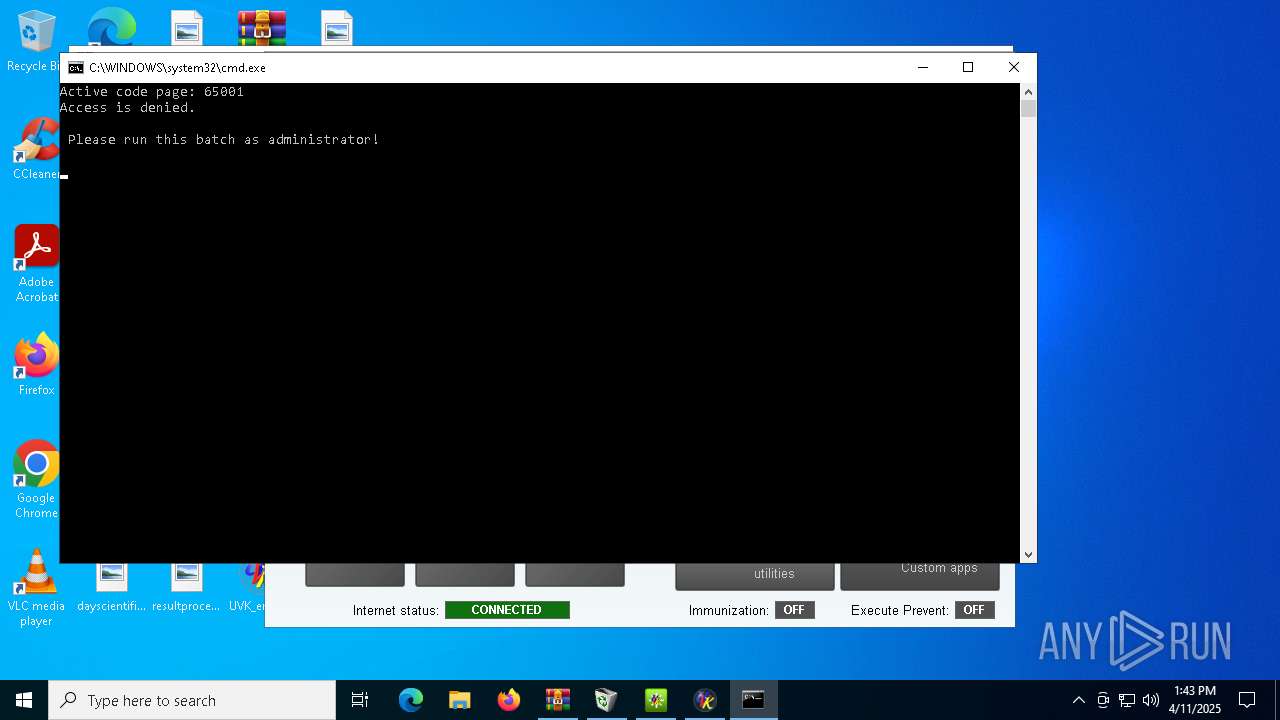
Starts application with an unusual extension
- cmd.exe (PID: 8136)
There is functionality for taking screenshot (YARA)
- RebootExec.exe (PID: 7812)
- UVK_en64.exe (PID: 7904)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7460)
Manual execution by a user
- cleanup.exe (PID: 7676)
- cleanup.exe (PID: 7628)
- UVK_en.exe (PID: 7724)
- UVK_en.exe (PID: 7772)
- RebootExec.exe (PID: 7812)
- UVK_en64.exe (PID: 7852)
- UVK_en64.exe (PID: 7904)
- cmd.exe (PID: 8136)
- MsiZap.exe (PID: 6032)
- MsiZap.exe (PID: 2148)
Checks supported languages
- cleanup.exe (PID: 7676)
- UVK_en.exe (PID: 7772)
- RebootExec.exe (PID: 7812)
- UVK_en64.exe (PID: 7904)
- chcp.com (PID: 8184)
- MsiZap.exe (PID: 2148)
Create files in a temporary directory
- cleanup.exe (PID: 7676)
Reads the computer name
- cleanup.exe (PID: 7676)
- UVK_en.exe (PID: 7772)
- RebootExec.exe (PID: 7812)
- UVK_en64.exe (PID: 7904)
Checks proxy server information
- UVK_en64.exe (PID: 7904)
- slui.exe (PID: 660)
Reads the machine GUID from the registry
- UVK_en64.exe (PID: 7904)
Reads the software policy settings
- UVK_en64.exe (PID: 7904)
- slui.exe (PID: 660)
Changes the display of characters in the console
- cmd.exe (PID: 8136)
Creates files or folders in the user directory
- UVK_en64.exe (PID: 7904)
Creates files in the program directory
- UVK_en64.exe (PID: 7904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (33.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:04:02 17:48:40 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | bluescreenview/ |
Total processes
140
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\Desktop\MsiZap.exe" | C:\Users\admin\Desktop\MsiZap.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® Installer Data Zapper Version: 3.1.4000.2726 Modules
| |||||||||||||||
| 3020 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | MsiZap.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6032 | "C:\Users\admin\Desktop\MsiZap.exe" | C:\Users\admin\Desktop\MsiZap.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® Installer Data Zapper Exit code: 3221226540 Version: 3.1.4000.2726 Modules
| |||||||||||||||
| 7460 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\UVK.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
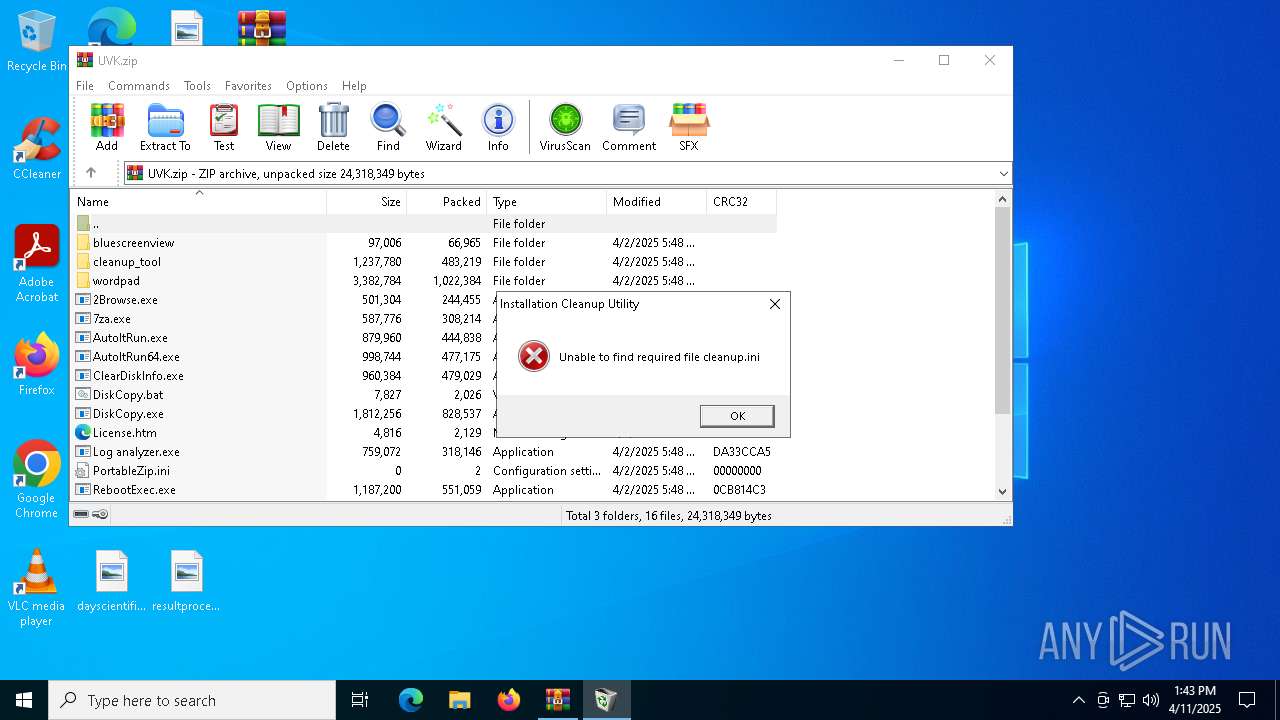
| 7628 | "C:\Users\admin\Desktop\cleanup.exe" | C:\Users\admin\Desktop\cleanup.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Installer Clean Up UI Application Exit code: 3221226540 Version: 2.5.1.0 Modules
| |||||||||||||||
| 7676 | "C:\Users\admin\Desktop\cleanup.exe" | C:\Users\admin\Desktop\cleanup.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Installer Clean Up UI Application Version: 2.5.1.0 Modules
| |||||||||||||||
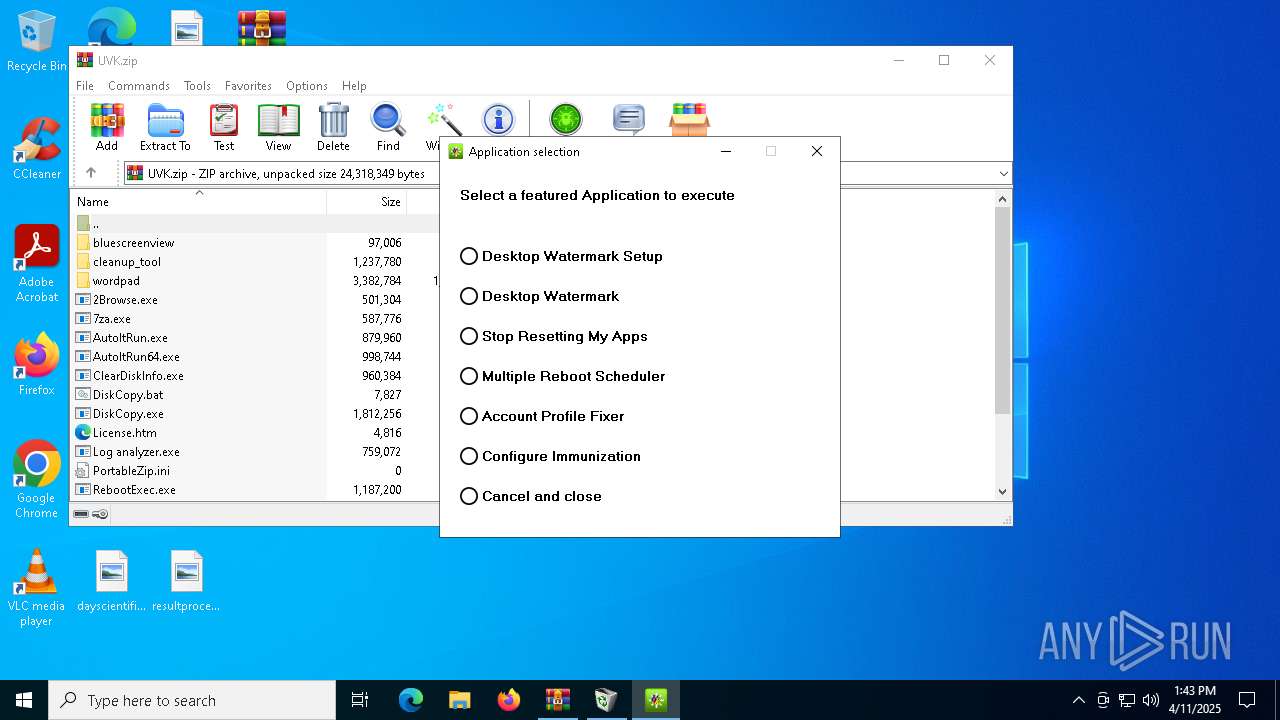
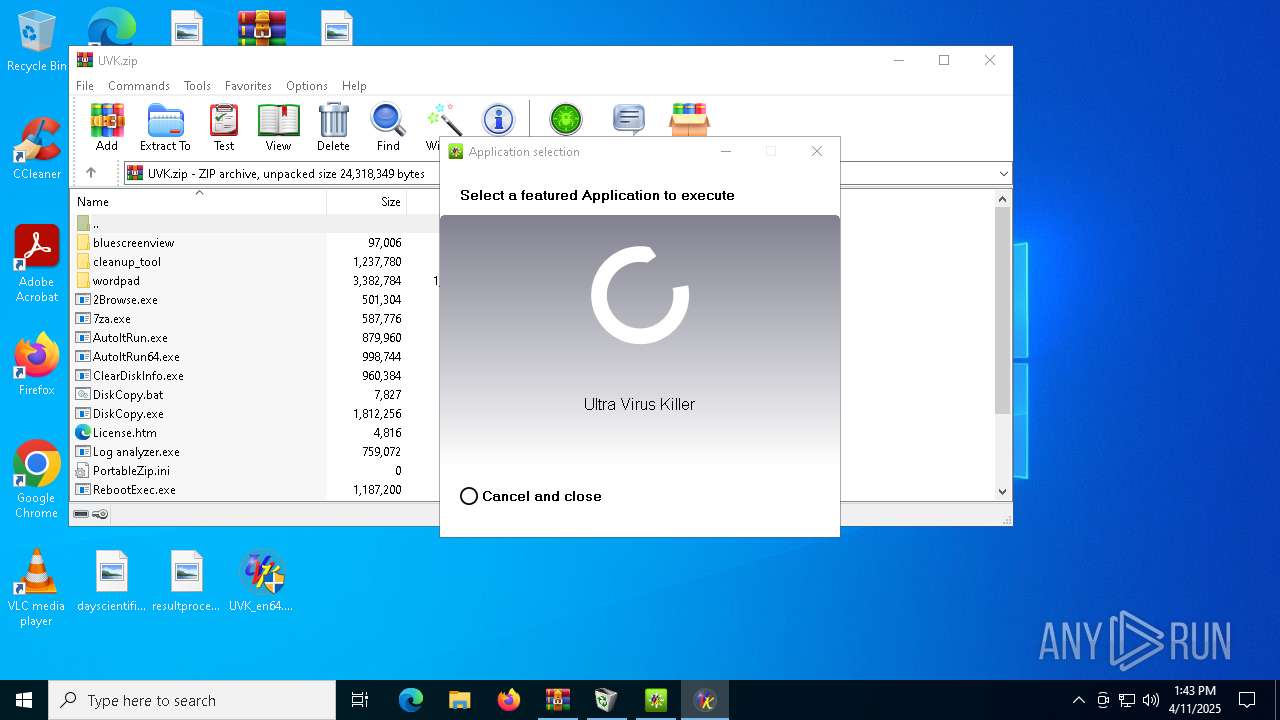
| 7724 | "C:\Users\admin\Desktop\UVK_en.exe" | C:\Users\admin\Desktop\UVK_en.exe | — | explorer.exe | |||||||||||
User: admin Company: Carifred.com Integrity Level: MEDIUM Description: Ultra Virus Killer Exit code: 3221226540 Version: 11.10.17.5 Modules
| |||||||||||||||
| 7772 | "C:\Users\admin\Desktop\UVK_en.exe" | C:\Users\admin\Desktop\UVK_en.exe | explorer.exe | ||||||||||||
User: admin Company: Carifred.com Integrity Level: HIGH Description: Ultra Virus Killer Exit code: 4294967295 Version: 11.10.17.5 Modules
| |||||||||||||||
| 7812 | "C:\Users\admin\Desktop\RebootExec.exe" | C:\Users\admin\Desktop\RebootExec.exe | — | explorer.exe | |||||||||||
User: admin Company: Carifred Integrity Level: MEDIUM Description: UVK reboot command parser Version: 4.7.0.0 Modules
| |||||||||||||||
Total events
9 482
Read events
9 466
Write events
16
Delete events
0
Modification events
| (PID) Process: | (7460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\UVK.zip | |||
| (PID) Process: | (7460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7460) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7904) UVK_en64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Carifred\UVK - Ultra Virus Killer |
| Operation: | write | Name: | FirewallPath |
Value: C:\Users\admin\Desktop\UVK_en64.exe | |||
| (PID) Process: | (7904) UVK_en64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Carifred\UVK - Ultra Virus Killer |
| Operation: | write | Name: | Flag |
Value: 4656 | |||
Executable files
0
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7676 | cleanup.exe | C:\Users\admin\AppData\Local\Temp\cleanup_main.log | text | |
MD5:982253ED6BAD4967D06BA46F40F14984 | SHA256:B16346D4587FCDCACF2250A194A460944B7E1E40CFA63B6CD28B5A7380015961 | |||
| 7904 | UVK_en64.exe | C:\Users\admin\Desktop\Logs\Log_2025-04-11.ini | binary | |
MD5:8DEC338A65360C80B84A52E801C1139A | SHA256:901375FF5C816C38D99CA2B0A46C2C3C1E32472FDCE961D652507B5475BE96FA | |||
| 7904 | UVK_en64.exe | C:\Users\admin\Desktop\urls | html | |
MD5:71D05D03828E8EB6736B08CF8996D684 | SHA256:C40B60D876E0992300C2B225C310BEAE577E167D640C2A0D9EC9E8ECFB53C9D3 | |||
| 7904 | UVK_en64.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\urls[1] | html | |
MD5:71D05D03828E8EB6736B08CF8996D684 | SHA256:C40B60D876E0992300C2B225C310BEAE577E167D640C2A0D9EC9E8ECFB53C9D3 | |||
| 7904 | UVK_en64.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\checkversion[1].htm | text | |
MD5:85FEAEA4F429FC3F530C6B6BA31ADF6D | SHA256:F94078C025C31F8CCC12E7F5E40AD0BE6ABC6A2B3EB6C4126B2D0ED3B5621DCF | |||
| 7676 | cleanup.exe | C:\Users\admin\AppData\Local\Temp\cleanup_actions.log | text | |
MD5:982253ED6BAD4967D06BA46F40F14984 | SHA256:B16346D4587FCDCACF2250A194A460944B7E1E40CFA63B6CD28B5A7380015961 | |||
| 7676 | cleanup.exe | C:\Users\admin\AppData\Local\Temp\cleanup_errors.log | text | |
MD5:982253ED6BAD4967D06BA46F40F14984 | SHA256:B16346D4587FCDCACF2250A194A460944B7E1E40CFA63B6CD28B5A7380015961 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
39
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
5988 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5988 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5988 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
5988 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5988 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 20.3.187.198:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
5988 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 20.12.23.50:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | unknown |
— | — | GET | 304 | 20.12.23.50:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7904 | UVK_en64.exe | 74.208.128.80:443 | www.carifred.com | IONOS SE | US | suspicious |
5988 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5988 | SIHClient.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5988 | SIHClient.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5988 | SIHClient.exe | 20.3.187.198:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.carifred.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |