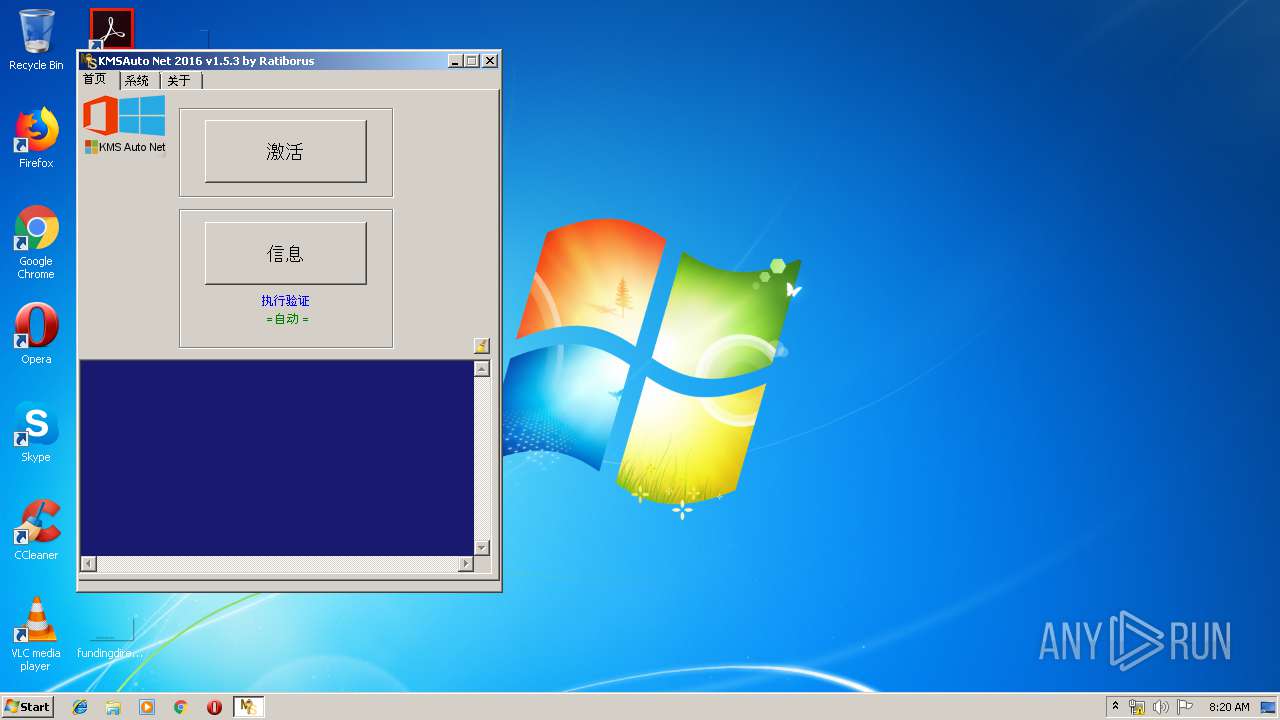
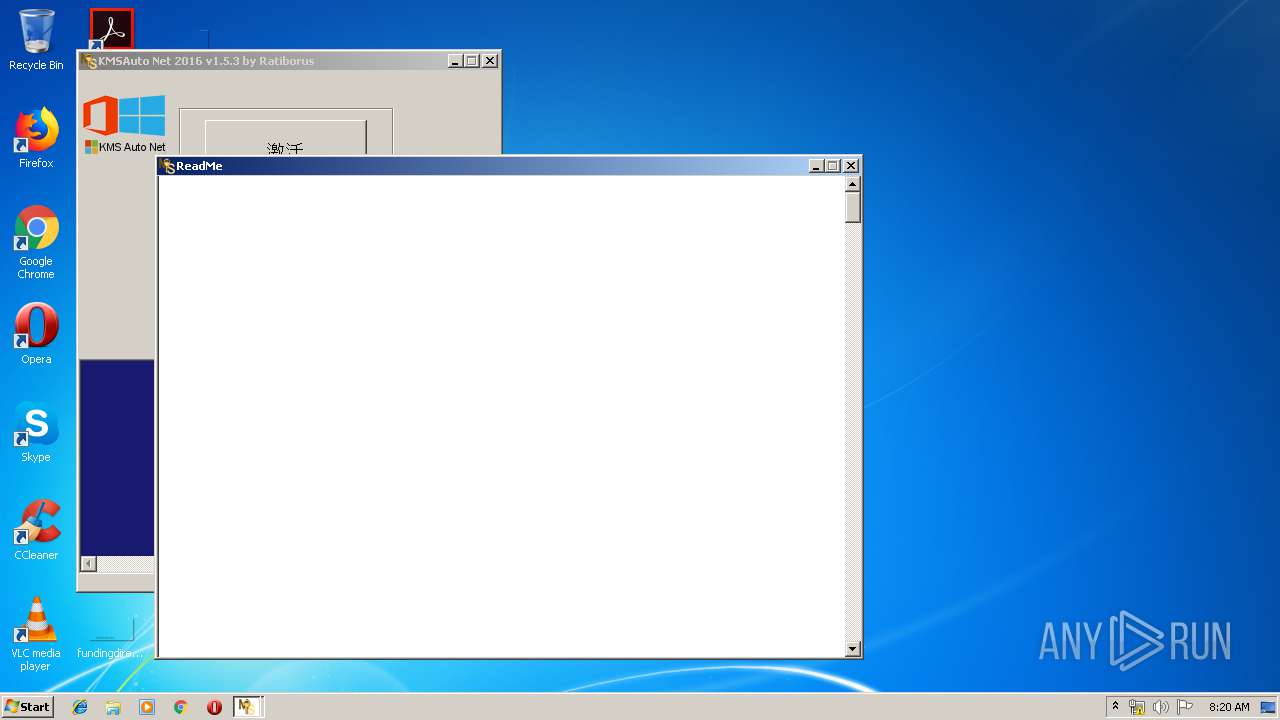
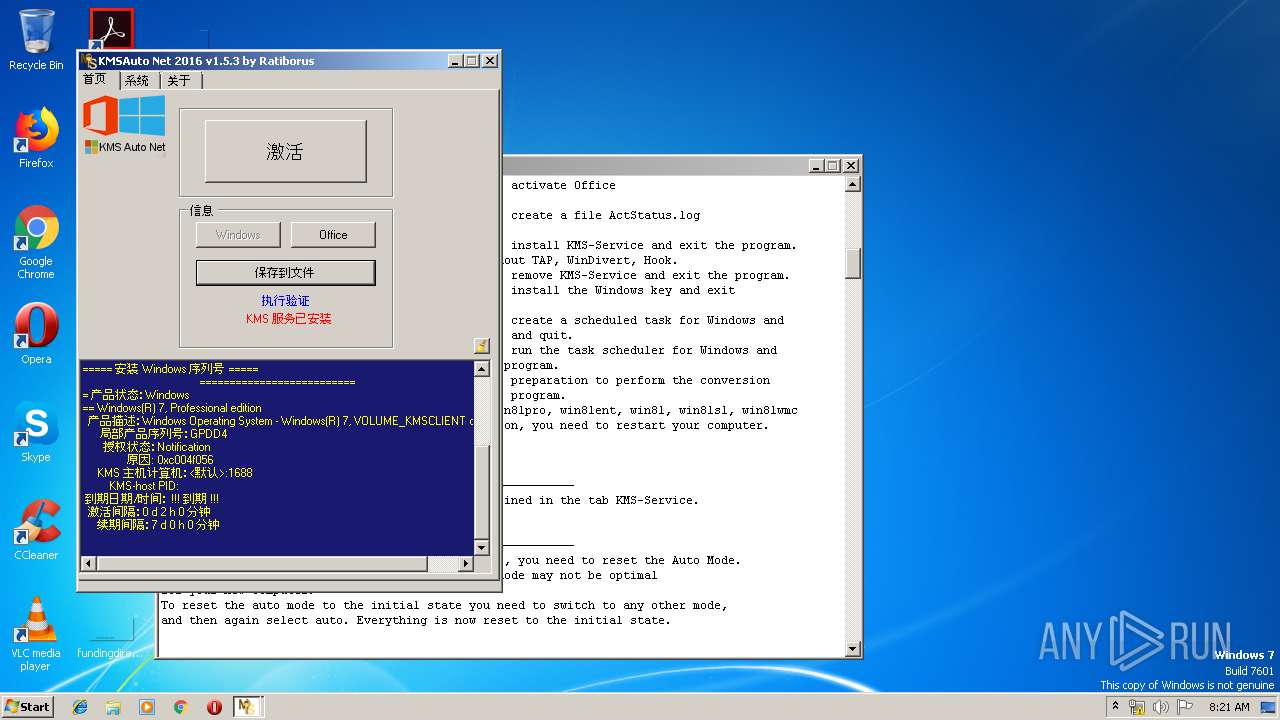
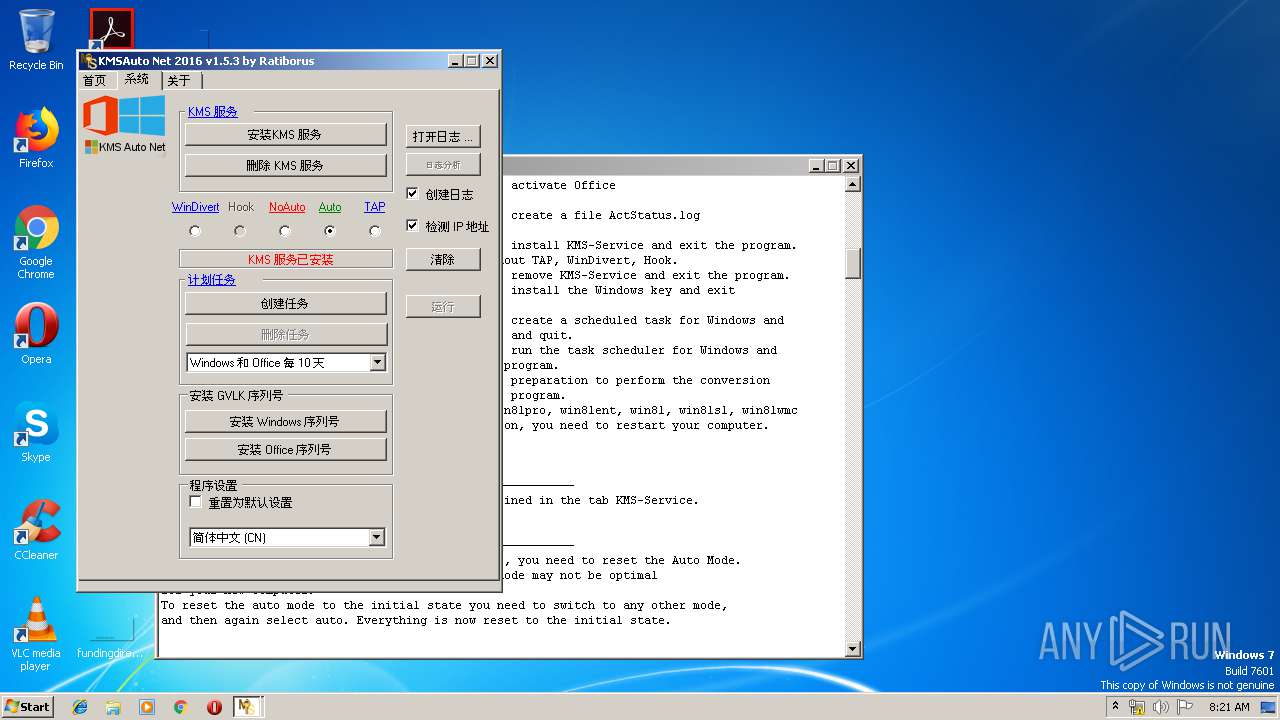
| File name: | KMSAuto Net.exe |
| Full analysis: | https://app.any.run/tasks/5a21e283-2c07-49af-9641-e9e663020410 |
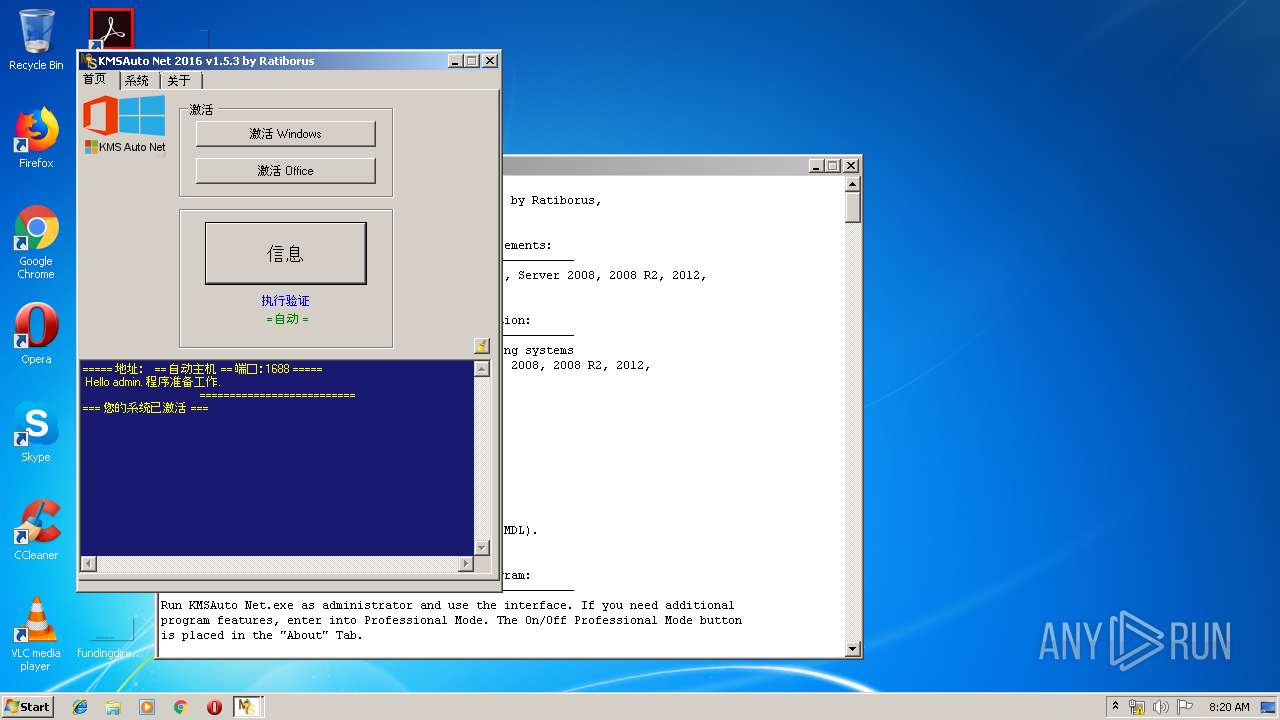
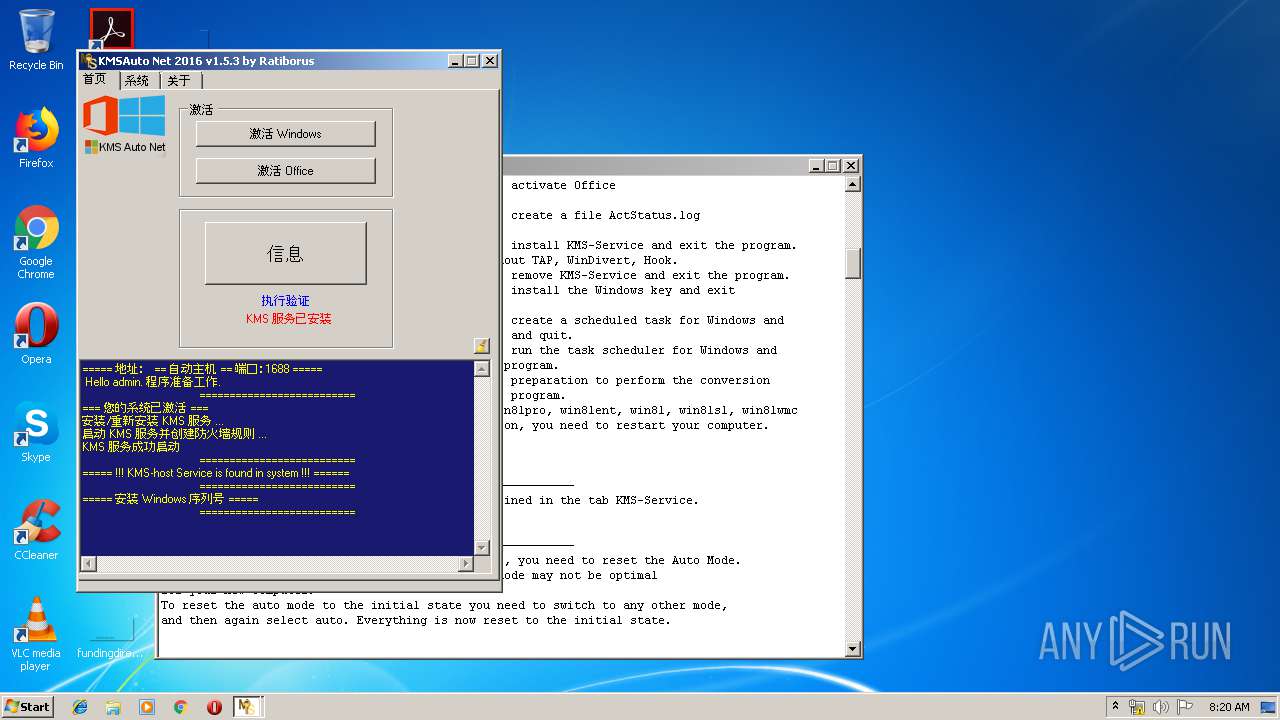
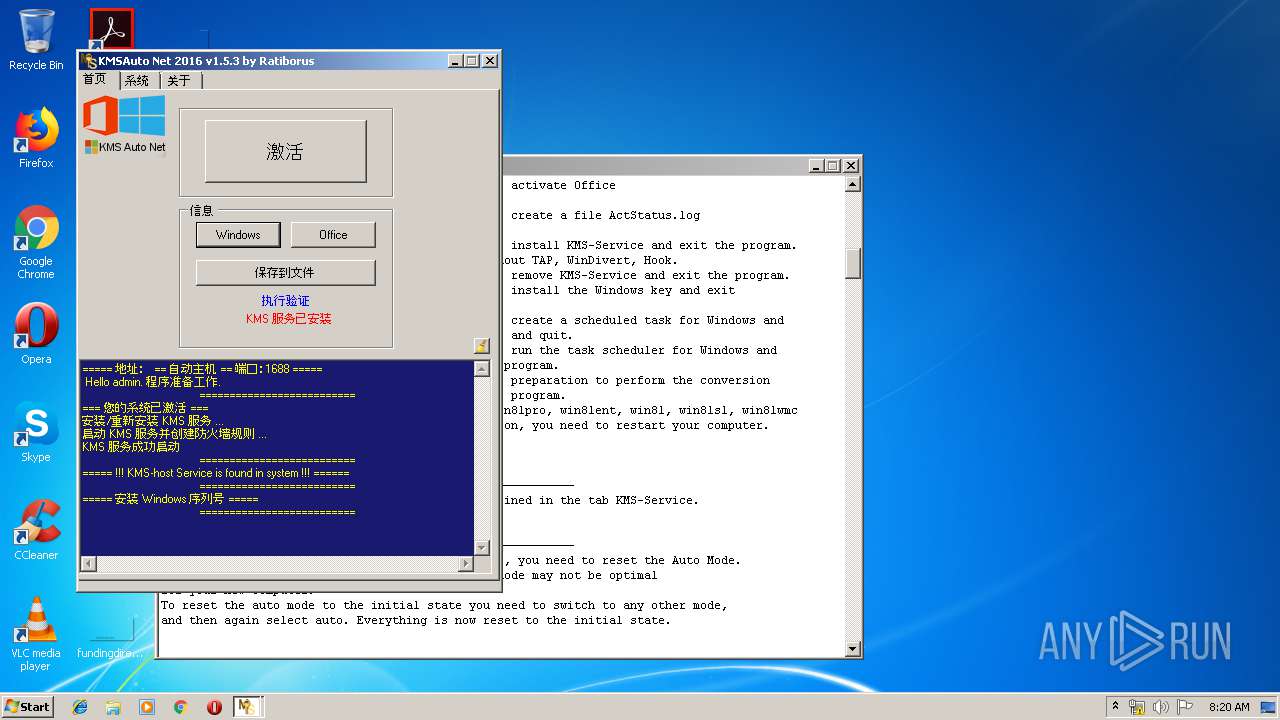
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2019, 07:19:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 0BB26F80AE0274DF1C06C30C4D1913CE |
| SHA1: | 6F91BD9500FF4D25A9DBC6C6058EC3E5068BA8ED |
| SHA256: | E4AE1C2B260450BDAA15CB6DC0BB3CC6047C388672ACF2F4CAA9F3A4F2C69D99 |
| SSDEEP: | 196608:+JaX7ywmI/yw+ywSyw/ywOweKywCAnywGywIywxywOyw3ywcywOywsyw/ZCHywH5:+e+wAwTwvwKwUHwCAywbwFwMwDwiwBw8 |
MALICIOUS
Application was dropped or rewritten from another process
- wzt.dat (PID: 3676)
- certmgr.exe (PID: 548)
- certmgr.exe (PID: 2228)
- bin.dat (PID: 2560)
- bin_x86.dat (PID: 2592)
- KMSSS.exe (PID: 2128)
Changes settings of System certificates
- certmgr.exe (PID: 548)
- certmgr.exe (PID: 2228)
SUSPICIOUS
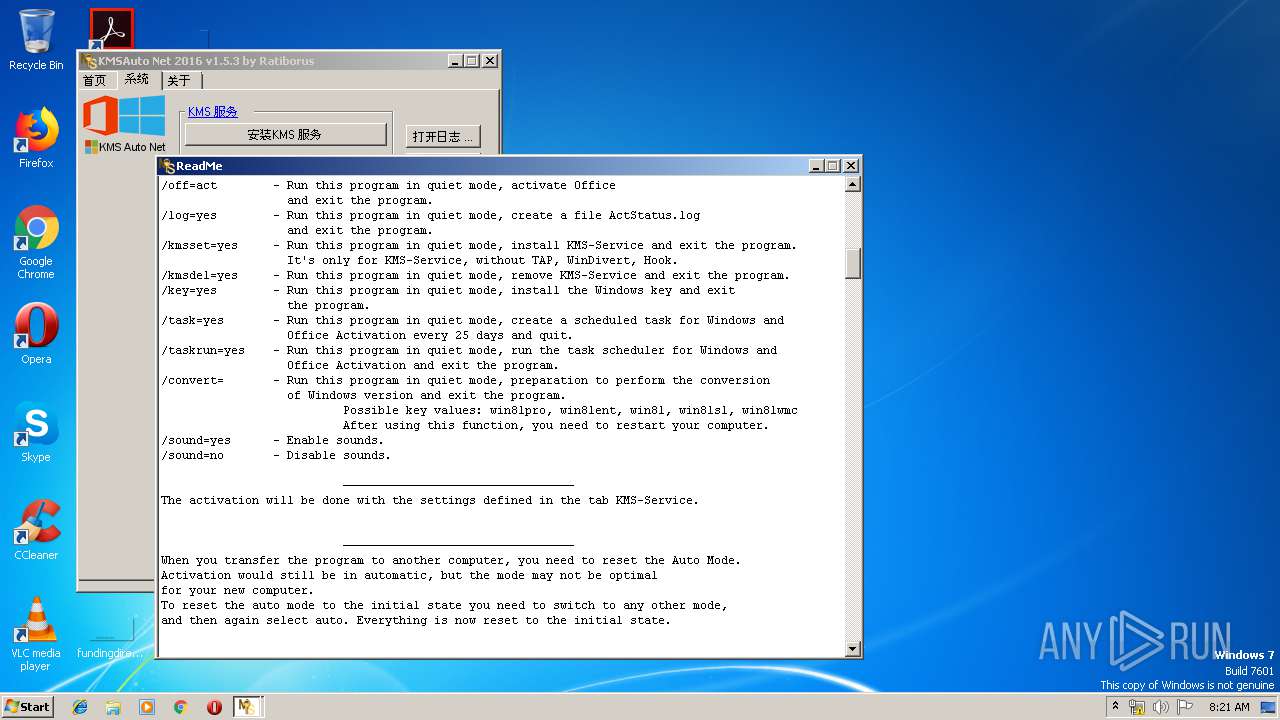
Starts CMD.EXE for self-deleting
- KMSAuto Net.exe (PID: 2700)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 2700)
- cmd.exe (PID: 2056)
Starts application with an unusual extension
- cmd.exe (PID: 3212)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 2200)
Executable content was dropped or overwritten
- KMSAuto Net.exe (PID: 2700)
- wzt.dat (PID: 3676)
- bin.dat (PID: 2560)
- AESDecoder.exe (PID: 2620)
- bin_x86.dat (PID: 2592)
Reads internet explorer settings
- KMSAuto Net.exe (PID: 2700)
Creates files in the program directory
- KMSAuto Net.exe (PID: 2700)
- wzt.dat (PID: 3676)
- bin.dat (PID: 2560)
- AESDecoder.exe (PID: 2620)
- bin_x86.dat (PID: 2592)
- KMSSS.exe (PID: 2128)
Reads Environment values
- KMSAuto Net.exe (PID: 2700)
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 3284)
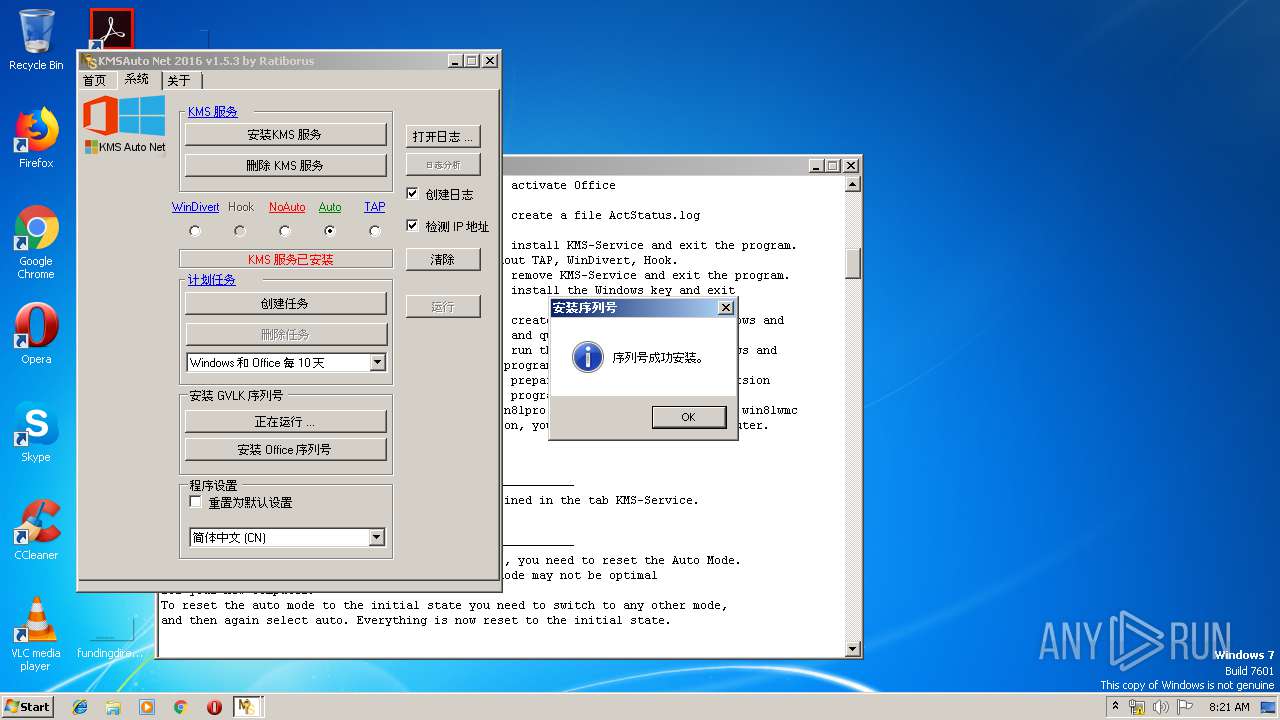
Creates or modifies windows services
- KMSAuto Net.exe (PID: 2700)
Uses NETSH.EXE for network configuration
- KMSAuto Net.exe (PID: 2700)
Starts SC.EXE for service management
- KMSAuto Net.exe (PID: 2700)
Executed as Windows Service
- KMSSS.exe (PID: 2128)
Executes scripts
- KMSAuto Net.exe (PID: 2700)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (45.1) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (19.2) |
| .exe | | | Win64 Executable (generic) (17) |
| .scr | | | Windows screen saver (8) |
| .dll | | | Win32 Dynamic Link Library (generic) (4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:10:31 14:33:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 9127936 |
| InitializedDataSize: | 49664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8b670e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.3.0 |
| ProductVersionNumber: | 1.5.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0004) |
| CharacterSet: | Windows, Chinese (Simplified) |
| Comments: | - |
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.5.3 |
| InternalName: | KMSAuto Net_zh-CHS.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | KMSAuto Net_zh-CHS.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.5.3 |
| AssemblyVersion: | 1.5.3.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Oct-2017 13:33:32 |
| Comments: | - |
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.5.3 |
| InternalName: | KMSAuto Net_zh-CHS.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | KMSAuto Net_zh-CHS.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.5.3 |
| Assembly Version: | 1.5.3.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 31-Oct-2017 13:33:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x008B4714 | 0x008B4800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.13769 |
.sdata | 0x008B8000 | 0x000001E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.61899 |
.rsrc | 0x008BA000 | 0x0000BC4C | 0x0000BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.62863 |
.reloc | 0x008C6000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.41186 | 3073 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.29604 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.35071 | 1736 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.03007 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.79019 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.1678 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.32586 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.672 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 5.05539 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.96193 | 132 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
100
Monitored processes
34
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Users\admin\AppData\Local\Temp\KMSAuto Net.exe" | C:\Users\admin\AppData\Local\Temp\KMSAuto Net.exe | — | explorer.exe | |||||||||||
User: admin Company: MSFree Inc. Integrity Level: MEDIUM Description: KMSAuto Net Exit code: 3221226540 Version: 1.5.3 Modules
| |||||||||||||||
| 476 | C:\Windows\System32\cmd.exe /D /c del /F /Q "test.test" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 476 | netstat -ano | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 548 | certmgr.exe -add wzteam.cer -n wzteam -s -r localMachine ROOT | C:\ProgramData\KMSAuto\wzt\certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 6.3.9600.17298 (winblue.141024-1500) Modules
| |||||||||||||||
| 680 | C:\Windows\System32\Netsh Advfirewall Firewall delete rule name="0pen Port KMS" protocol=TCP | C:\Windows\System32\Netsh.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2056 | C:\Windows\System32\cmd.exe /D /c for /f "tokens=5 delims=, " %i in ('netstat -ano ^| find ":1688 "') do taskkill /pid %i /f | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2088 | C:\Windows\System32\Netsh Advfirewall Firewall add rule name="0pen Port KMS" dir=in action=allow protocol=TCP localport=1688 | C:\Windows\System32\Netsh.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2128 | "C:\ProgramData\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -PO16 RandomKMSPID -AI 43200 -RI 43200 -Log -IP | C:\ProgramData\KMSAuto\bin\KMSSS.exe | — | services.exe | |||||||||||
User: SYSTEM Company: MSFree Inc. Integrity Level: SYSTEM Description: KMS emulator by Ratiborus, thanks to Hotbird64. Exit code: 0 Version: 2.0.4.0 Modules
| |||||||||||||||
| 2156 | C:\Windows\System32\cmd.exe /D /c del /F /Q "wzt.dat" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2184 | C:\Windows\System32\cmd.exe /D /c md "C:\ProgramData\KMSAuto" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
280
Read events
174
Write events
106
Delete events
0
Modification events
| (PID) Process: | (2228) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\648384A4DEE53D4C1C87E10D67CC99307CCC9C98 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000648384A4DEE53D4C1C87E10D67CC99307CCC9C982000000001000000FE010000308201FA30820167A00302010202108AC1A3101349C28A4D33947CFCD07662300906052B0E03021D05003011310F300D06035504031306575A5465616D301E170D3136313130323138343730365A170D3339313233313233353935395A3011310F300D06035504031306575A5465616D30819F300D06092A864886F70D010101050003818D0030818902818100AD2F8AA939C3EB40D1D6DE0509B9F4E7EBF8475B98C49E9FB4AD556D408E9B84E80D014078D65BE351E8A5D84CE2E92E84504F82E09DFA6C8310B58955527CEC2843039328B51891F2A09F70FD7E1348668A0AF780F741A30254397E9135220D442704C2395810A0A65B6B4EC54558E26C468C6087FD3BB1A1DE8414ADE68AAF0203010001A35B305930130603551D25040C300A06082B0601050507030330420603551D01043B30398010106AC14D8CB580F787E68A2938AB9BF3A1133011310F300D06035504031306575A5465616D82108AC1A3101349C28A4D33947CFCD07662300906052B0E03021D050003818100601D9E4107BECC4352D02281EC0764B2865E4ED60EE58228B7375D707730DEDE148E9ED41CE051C44D4E15D041CF8C601A054CA14B4A484F7DBAAB409E1D75CEBE6F8FA171E97E16EAE94B6757DA5C61B0B6F85CE2FEA31F50D664CC5BC1A40476A44EDDD5390357BC0D44C37B4969B5E4E923FEE772AFD4643B21BA918D40A8 | |||
| (PID) Process: | (548) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\648384A4DEE53D4C1C87E10D67CC99307CCC9C98 |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000648384A4DEE53D4C1C87E10D67CC99307CCC9C982000000001000000FE010000308201FA30820167A00302010202108AC1A3101349C28A4D33947CFCD07662300906052B0E03021D05003011310F300D06035504031306575A5465616D301E170D3136313130323138343730365A170D3339313233313233353935395A3011310F300D06035504031306575A5465616D30819F300D06092A864886F70D010101050003818D0030818902818100AD2F8AA939C3EB40D1D6DE0509B9F4E7EBF8475B98C49E9FB4AD556D408E9B84E80D014078D65BE351E8A5D84CE2E92E84504F82E09DFA6C8310B58955527CEC2843039328B51891F2A09F70FD7E1348668A0AF780F741A30254397E9135220D442704C2395810A0A65B6B4EC54558E26C468C6087FD3BB1A1DE8414ADE68AAF0203010001A35B305930130603551D25040C300A06082B0601050507030330420603551D01043B30398010106AC14D8CB580F787E68A2938AB9BF3A1133011310F300D06035504031306575A5465616D82108AC1A3101349C28A4D33947CFCD07662300906052B0E03021D050003818100601D9E4107BECC4352D02281EC0764B2865E4ED60EE58228B7375D707730DEDE148E9ED41CE051C44D4E15D041CF8C601A054CA14B4A484F7DBAAB409E1D75CEBE6F8FA171E97E16EAE94B6757DA5C61B0B6F85CE2FEA31F50D664CC5BC1A40476A44EDDD5390357BC0D44C37B4969B5E4E923FEE772AFD4643B21BA918D40A8 | |||
| (PID) Process: | (476) NETSTAT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
| (PID) Process: | (680) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (680) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (680) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (680) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (680) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (680) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (680) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
Executable files
16
Suspicious files
2
Text files
35
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4084 | cmd.exe | C:\Users\admin\AppData\Local\Temp\test.test | — | |
MD5:— | SHA256:— | |||
| 2560 | bin.dat | C:\ProgramData\KMSAuto\bin\KMSSS.exe.aes | — | |
MD5:— | SHA256:— | |||
| 2560 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror2.exe.aes | — | |
MD5:— | SHA256:— | |||
| 2560 | bin.dat | C:\ProgramData\KMSAuto\bin\AESDecoder.exe | — | |
MD5:— | SHA256:— | |||
| 2700 | KMSAuto Net.exe | C:\Users\admin\AppData\Local\MSfree Inc\kmsauto.ini | text | |
MD5:AF6A20FD7DFADCD582CCF2B1BFAAF82B | SHA256:0BEE97833A70AA9BA271E93226DACE849836C64919FBFE15543D694E219D4AF2 | |||
| 2700 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\bin.dat | executable | |
MD5:4C3E59E7EE273173E9413531647C3881 | SHA256:29D3EEF47A628754C99C65C789FC42331FA18AADF49E4D4AB4EDD0D0C76163BA | |||
| 2620 | AESDecoder.exe | C:\ProgramData\KMSAuto\bin\KMSSS.exe | executable | |
MD5:577D9CD8FDD91CF70CDF05BDCEA912F4 | SHA256:00FDBAF8624F4E124B22D46A7F3291870DC01FDE0D60305154EE515AFF73CB5F | |||
| 2560 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror.exe | executable | |
MD5:2ED9C12A91E795804B1B770958C647AC | SHA256:CB56C248A38292C234D1AABE5E33A671FE8AE8AED28E0C8C4FBE767E4E7B82F5 | |||
| 2700 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\wzt.dat | executable | |
MD5:822DA2319294F2B768BFE9ED4EEBAC15 | SHA256:17B74D4EA905FAC0BA6857F78F47EE1E940675AF1BC27DED69FE2941318106EF | |||
| 2620 | AESDecoder.exe | C:\ProgramData\KMSAuto\bin\TunMirror2.exe | executable | |
MD5:3B33E3AB6E91806DF4CAE19405AB8846 | SHA256:D9CD47831FABA4053225DAC181709FD7AB9D066C3DE6F541968FFFEEEE4A9BF9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report