| File name: | gs-auto-clicker-4-0.exe |
| Full analysis: | https://app.any.run/tasks/17bb60dc-12a8-4cdc-94ec-656963ff94fb |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2025, 06:43:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | E42D679A626463742B553794DEA6F62B |
| SHA1: | 789C25A360342FD431DCCBF01B831C36AA229317 |
| SHA256: | E4A3B0CE536C0996082311077AC65A096D9E6BBF404C6E6A155ECEFB32E864C5 |
| SSDEEP: | 12288:0aWzgMg7v3qnCi0ErQohh0F42CJ8lnypQDaGEohvRyPJ1+Fxe:raHMv6CorjSnypQDaG9u1We |
MALICIOUS
No malicious indicators.SUSPICIOUS
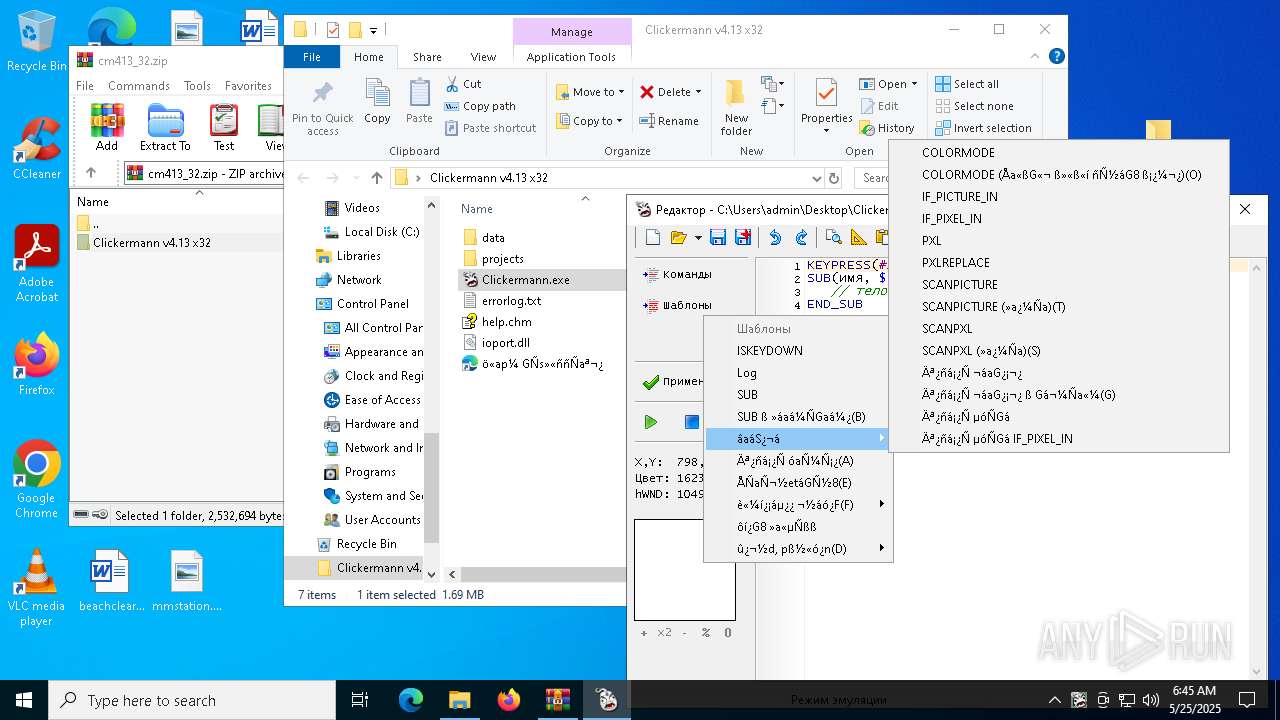
There is functionality for taking screenshot (YARA)
- gs-auto-clicker-4-0.exe (PID: 6048)
- Clickermann.exe (PID: 6632)
Reads the BIOS version
- Clickermann.exe (PID: 6112)
- Clickermann.exe (PID: 6632)
Creates/Modifies COM task schedule object
- Clickermann.exe (PID: 6632)
INFO
The sample compiled with english language support
- gs-auto-clicker-4-0.exe (PID: 6048)
- WinRAR.exe (PID: 1568)
Reads the computer name
- gs-auto-clicker-4-0.exe (PID: 6048)
- Clickermann.exe (PID: 6112)
- Clickermann.exe (PID: 6632)
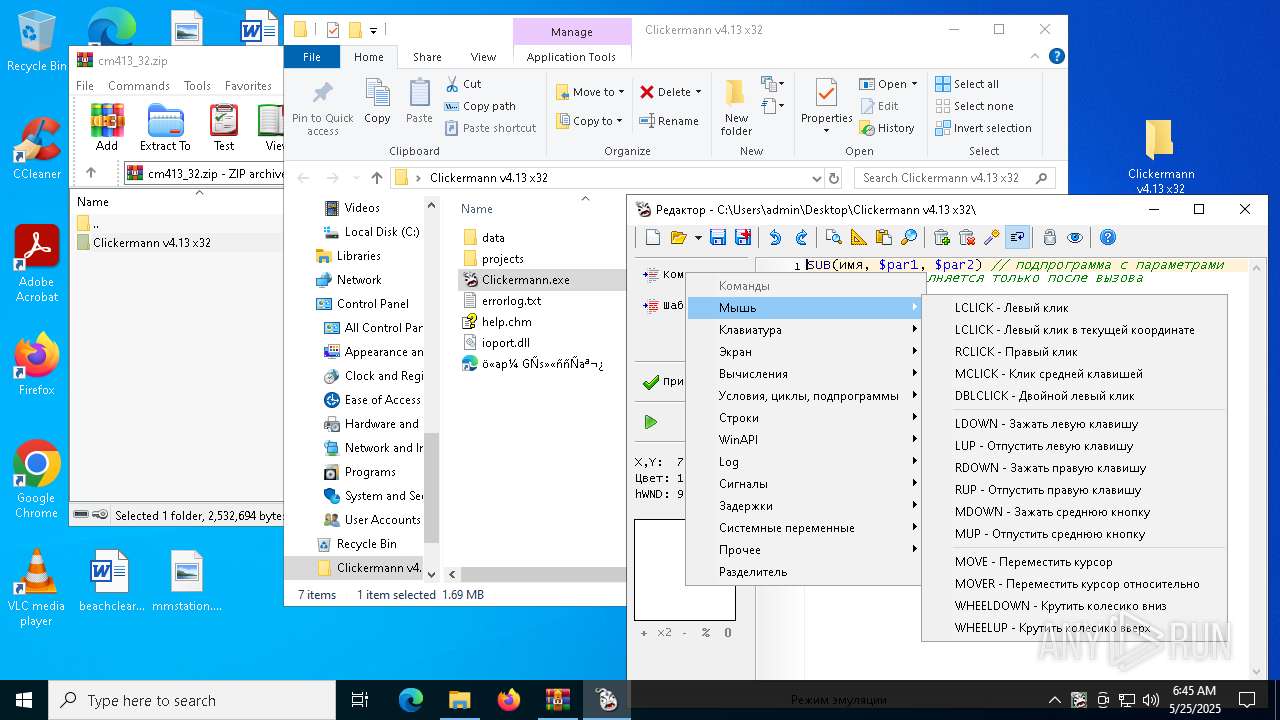
Reads mouse settings
- gs-auto-clicker-4-0.exe (PID: 6048)
Checks supported languages
- gs-auto-clicker-4-0.exe (PID: 6048)
- Clickermann.exe (PID: 6112)
- Clickermann.exe (PID: 6632)
The process uses AutoIt
- gs-auto-clicker-4-0.exe (PID: 6048)
Create files in a temporary directory
- gs-auto-clicker-4-0.exe (PID: 6048)
- Clickermann.exe (PID: 6112)
- Clickermann.exe (PID: 6632)
Reads the software policy settings
- slui.exe (PID: 7052)
- slui.exe (PID: 4008)
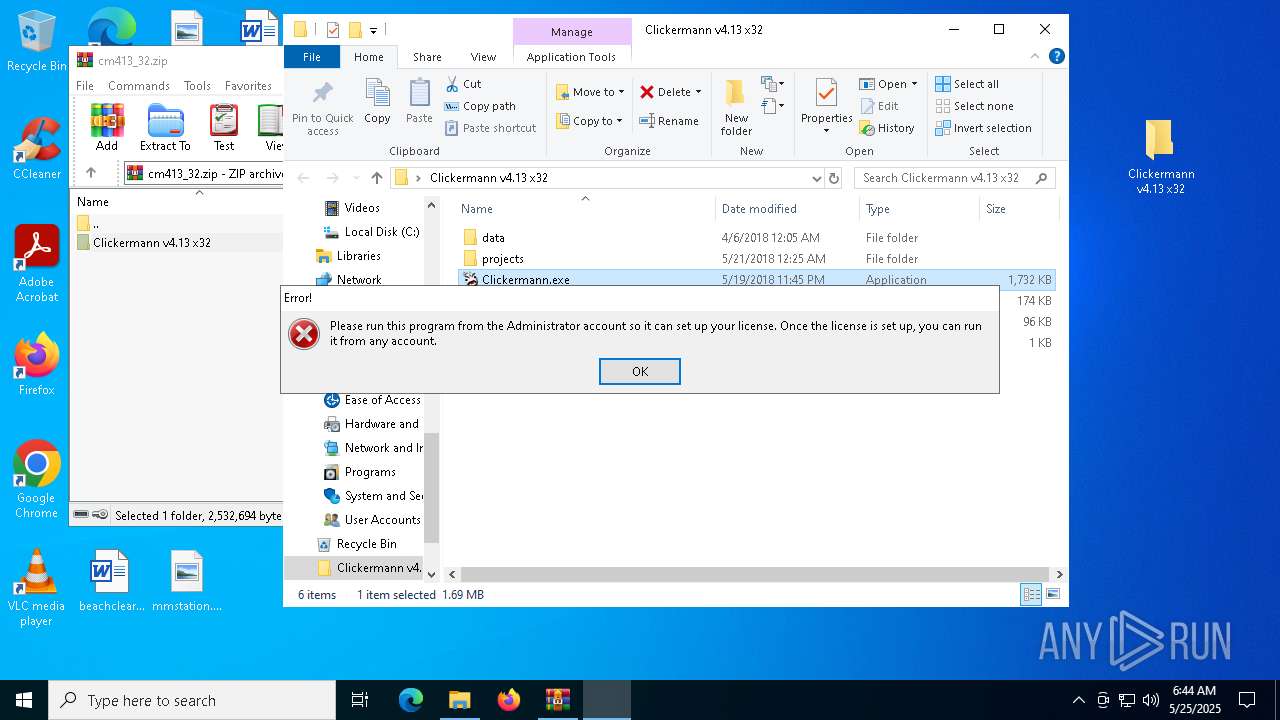
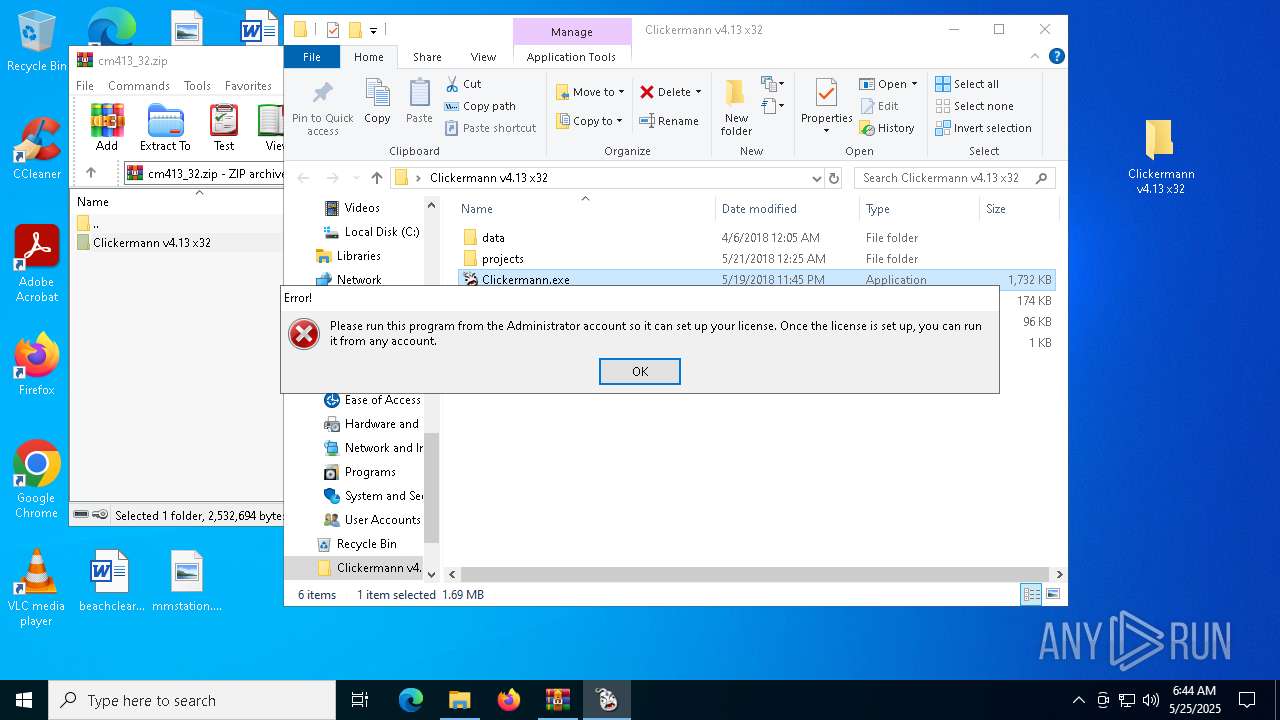
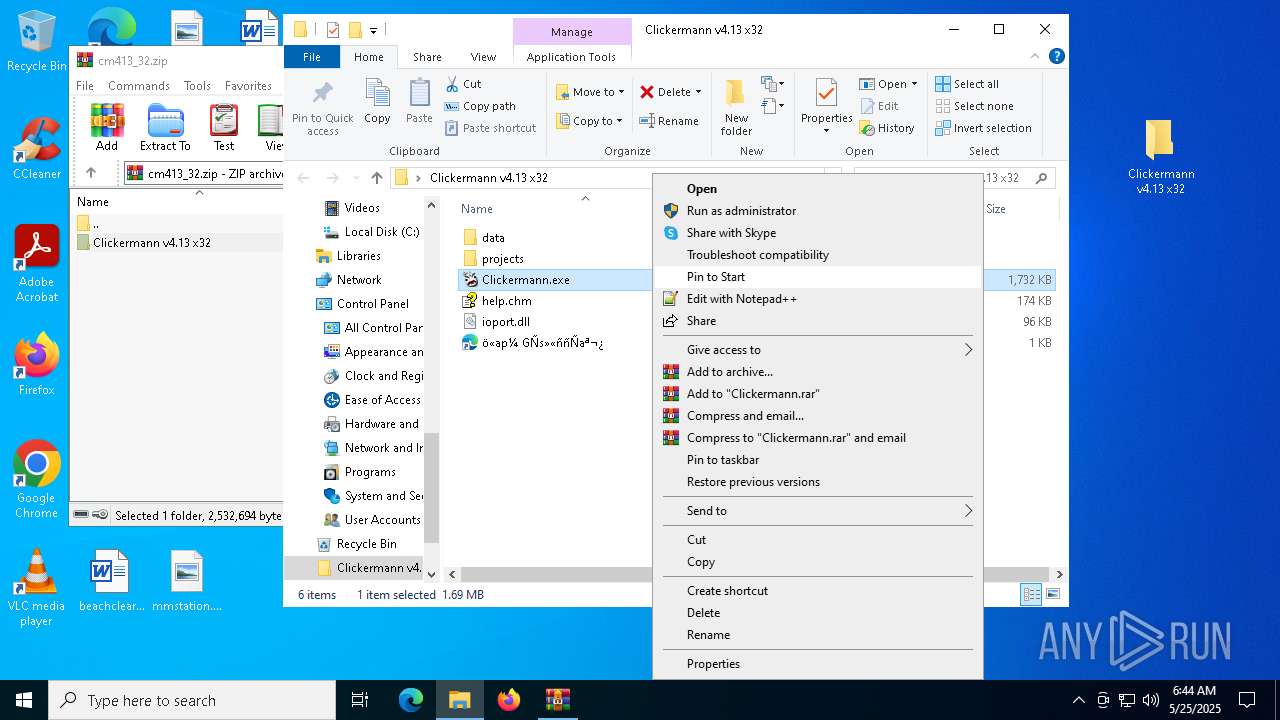
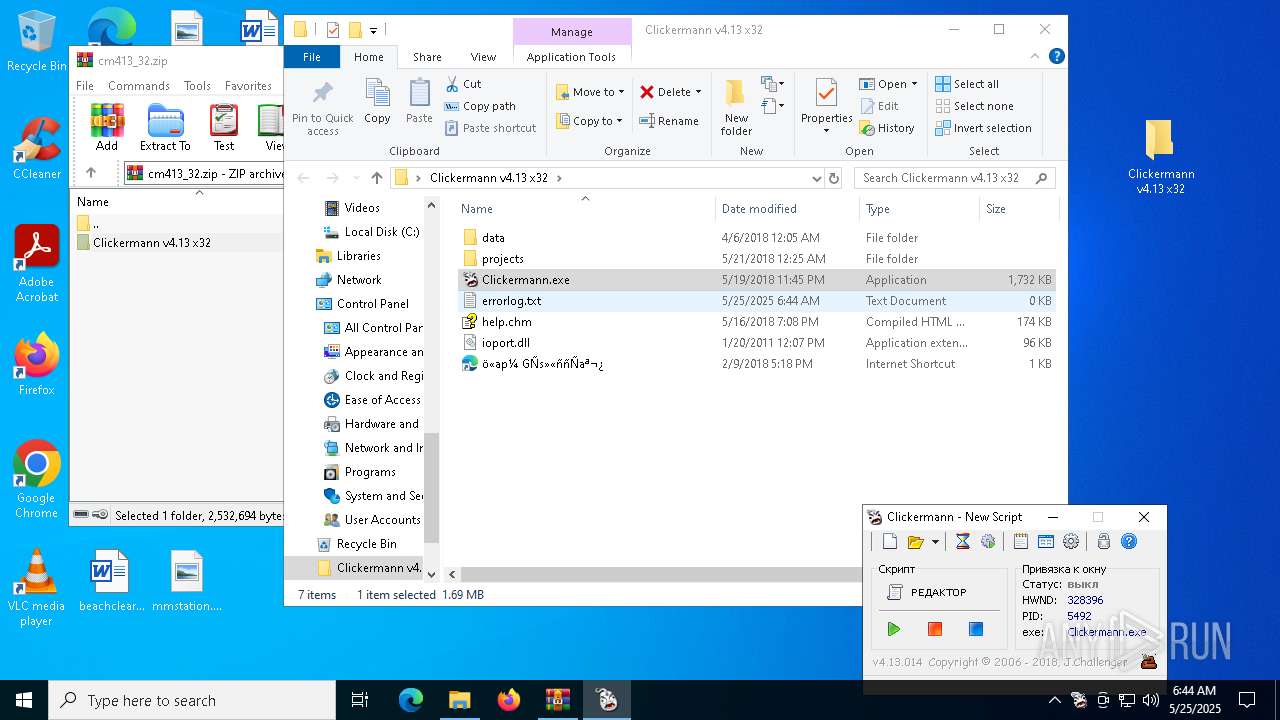
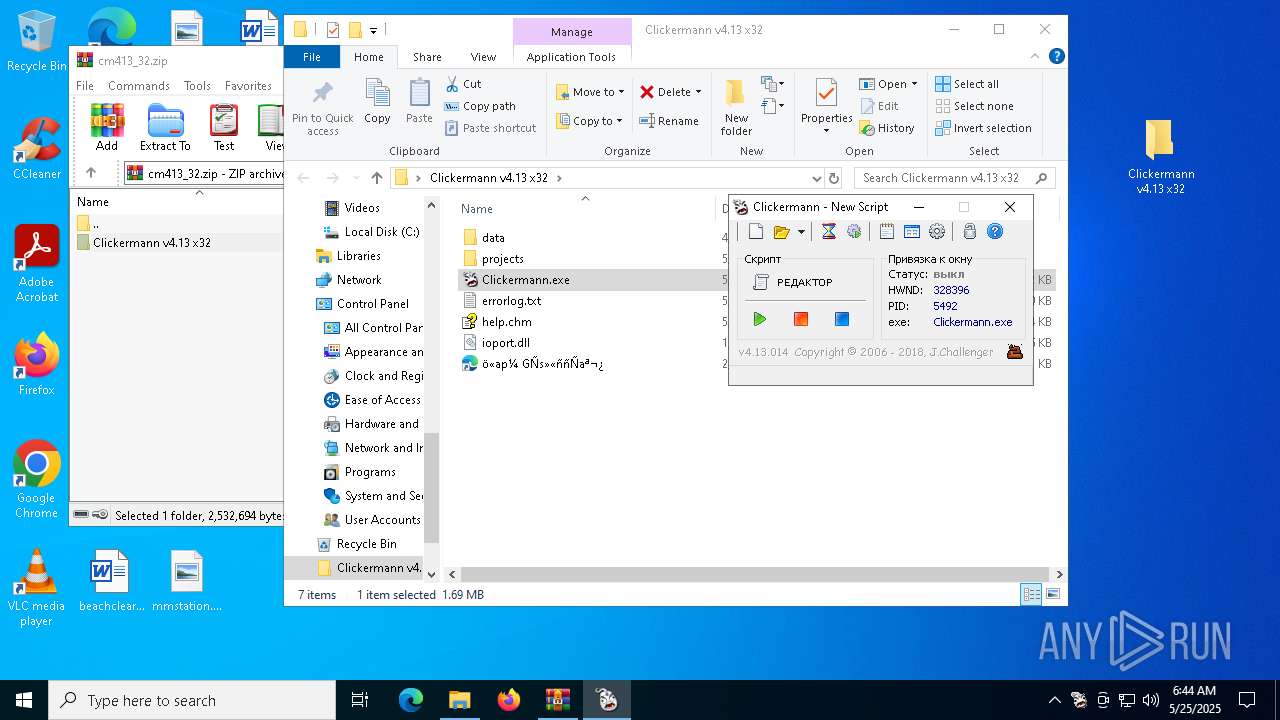
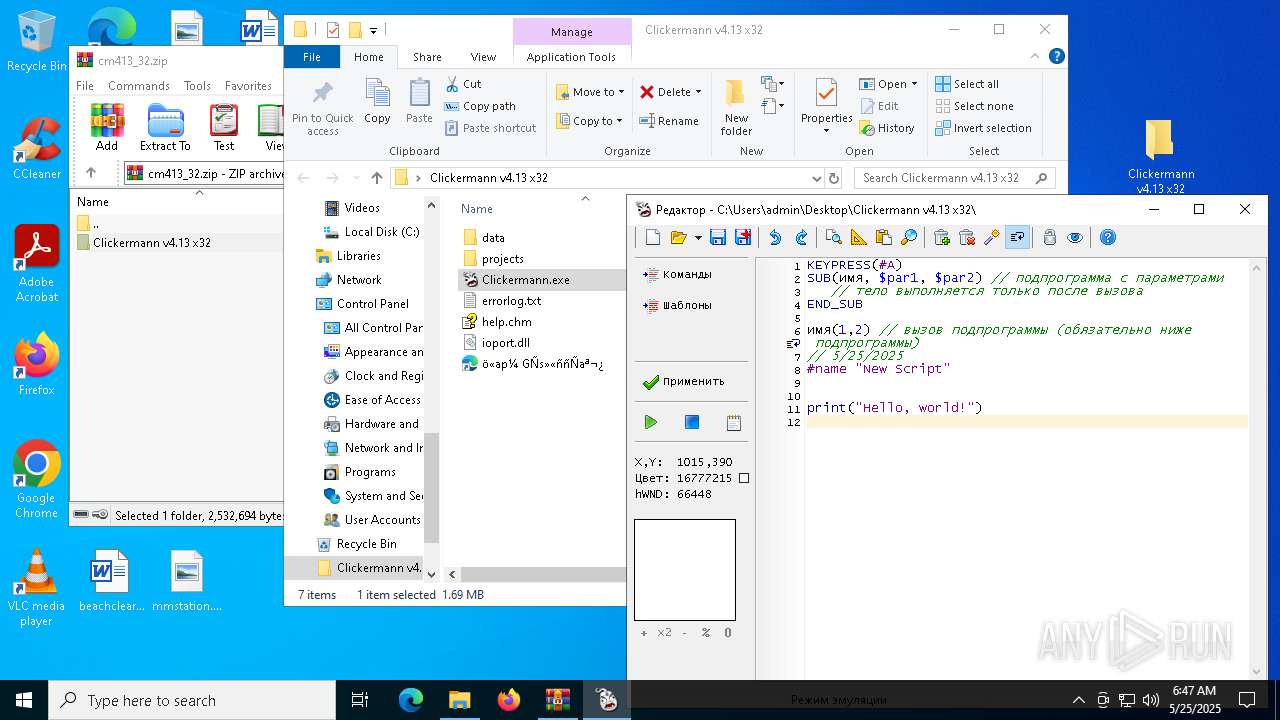
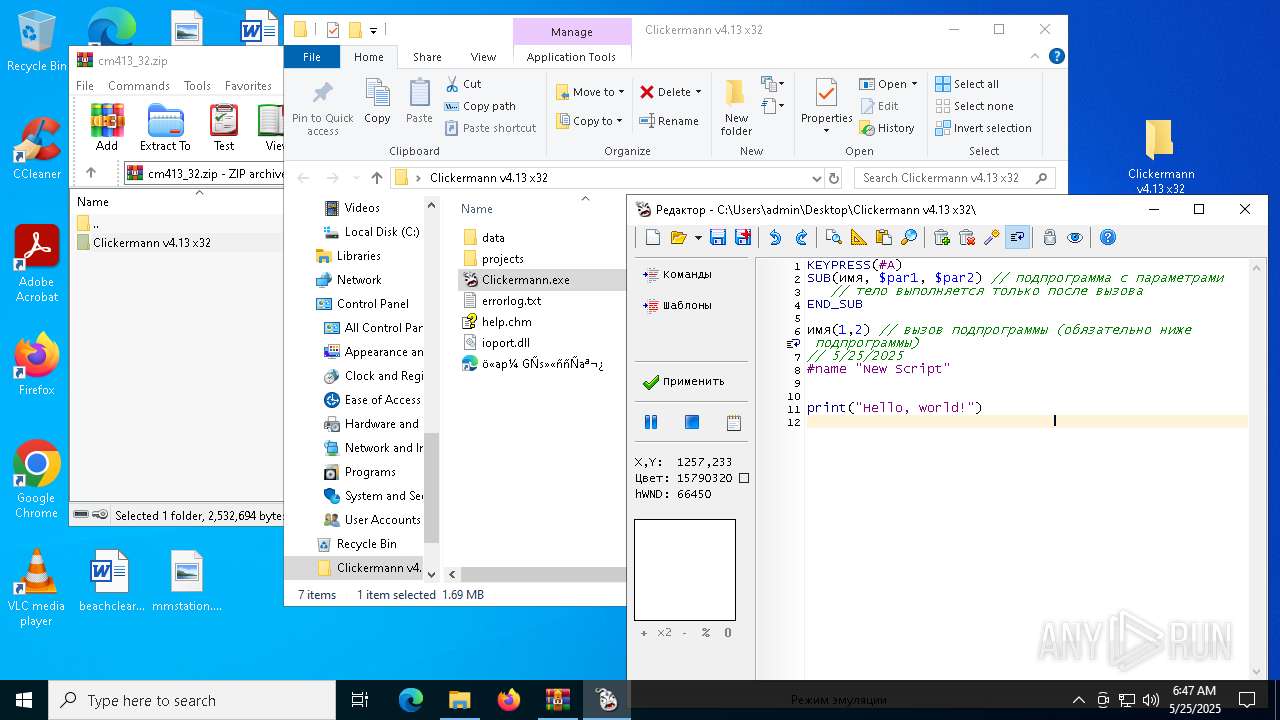
Manual execution by a user
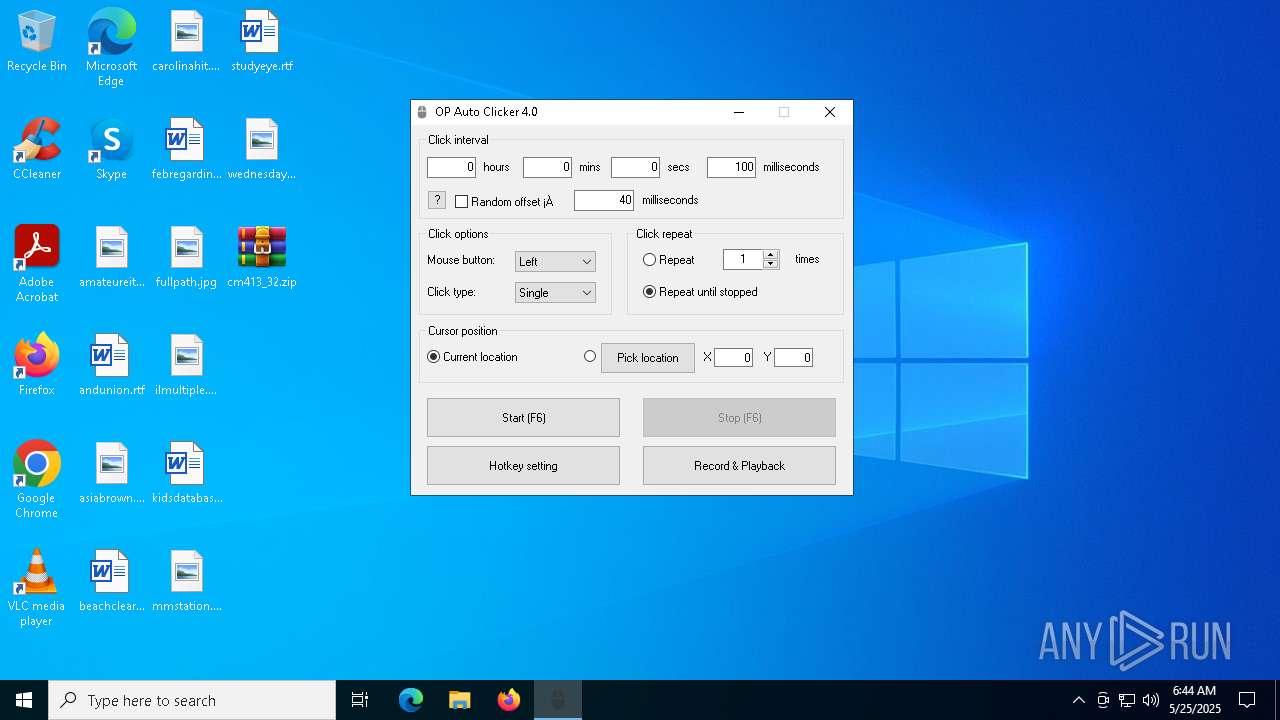
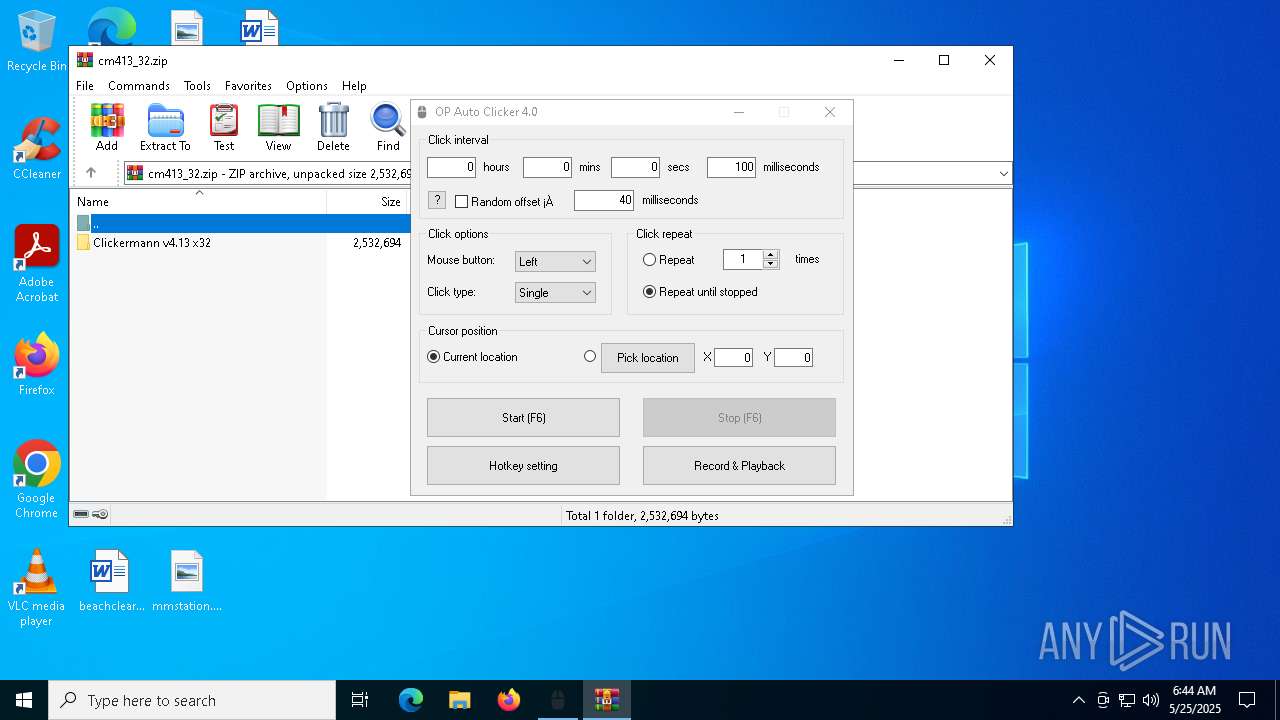
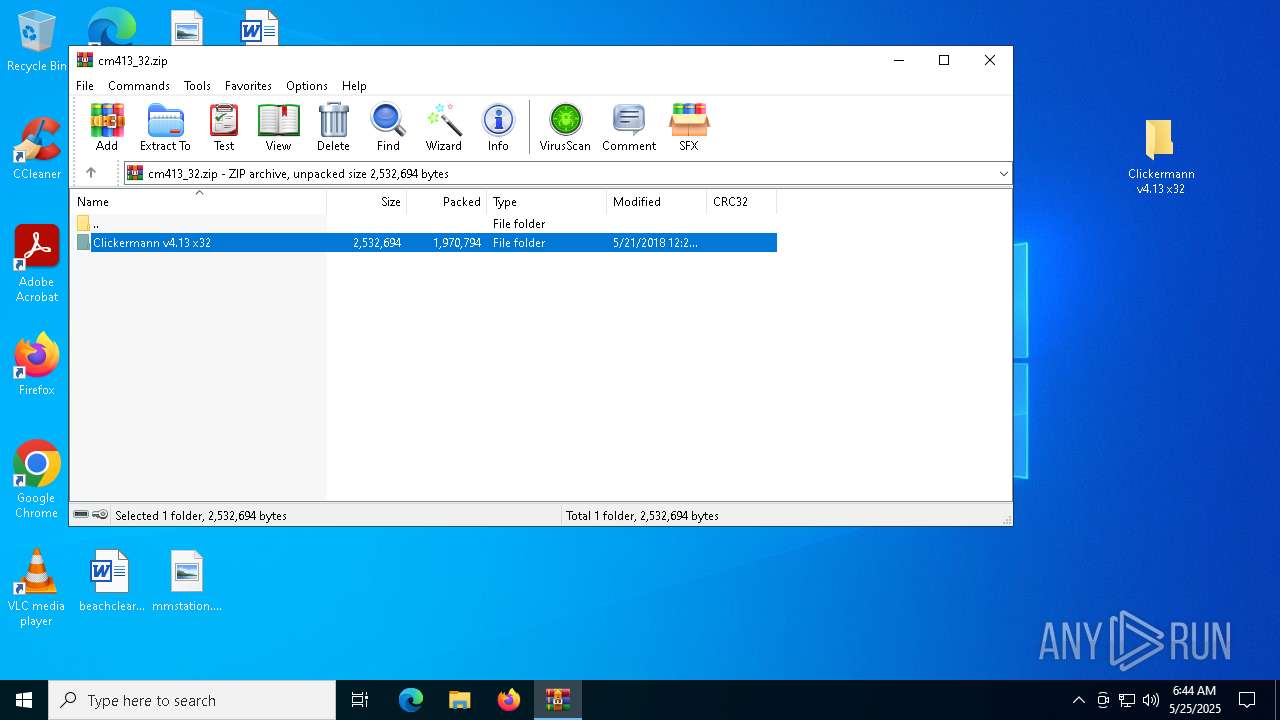
- WinRAR.exe (PID: 1568)
- Clickermann.exe (PID: 6112)
- Clickermann.exe (PID: 6632)
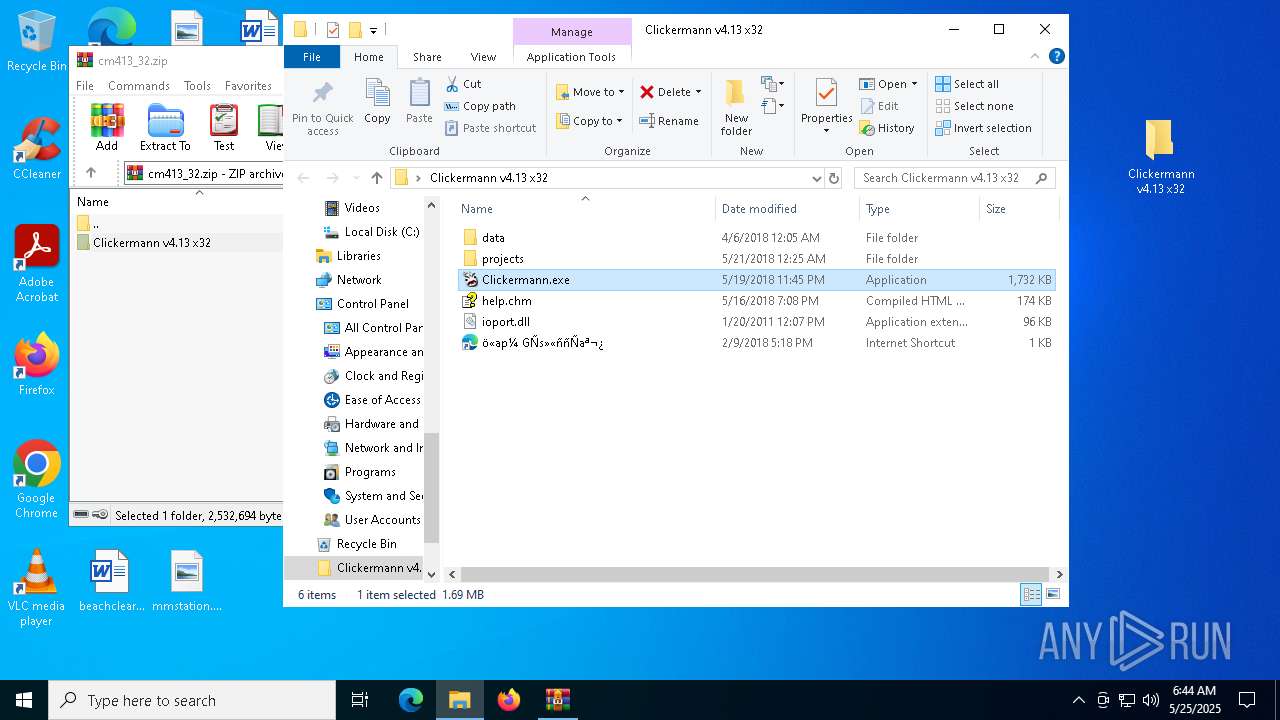
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1568)
The sample compiled with russian language support
- WinRAR.exe (PID: 1568)
Compiled with Borland Delphi (YARA)
- Clickermann.exe (PID: 6632)
Checks proxy server information
- slui.exe (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:06:30 11:20:36+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 524800 |
| InitializedDataSize: | 126976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16310 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.0 |
| ProductVersionNumber: | 4.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | www.opautoclicker.com |
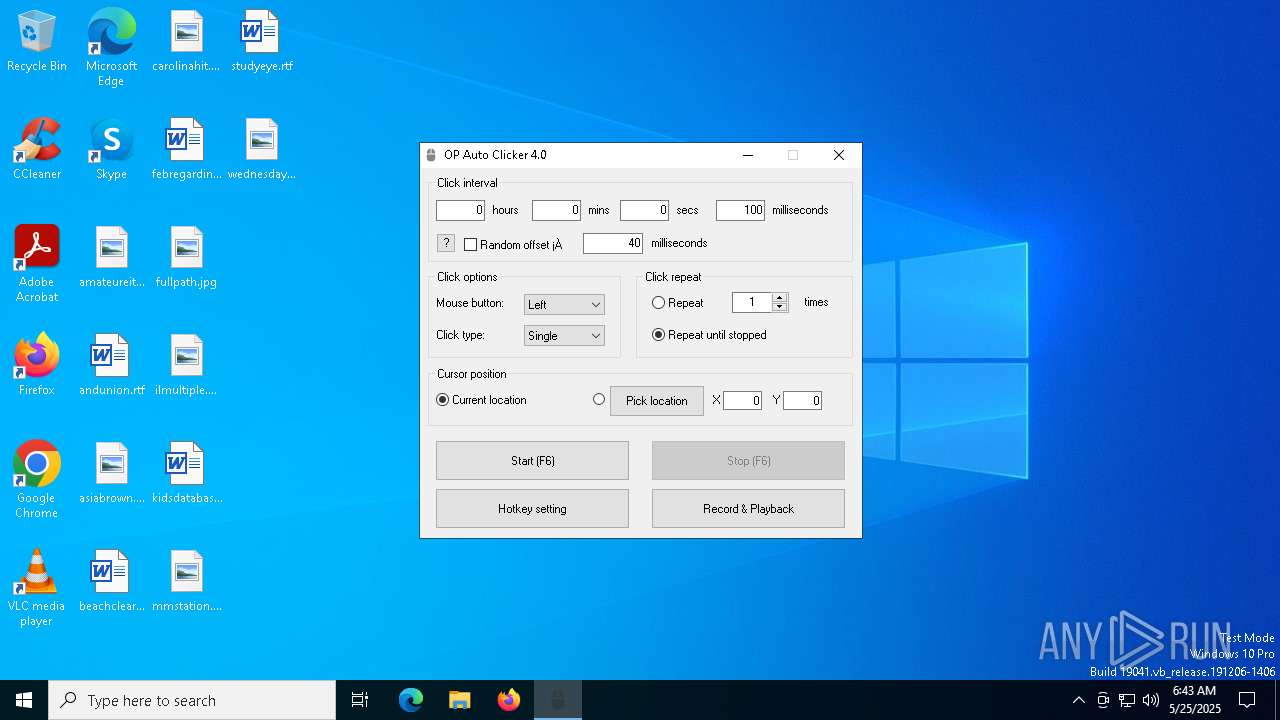
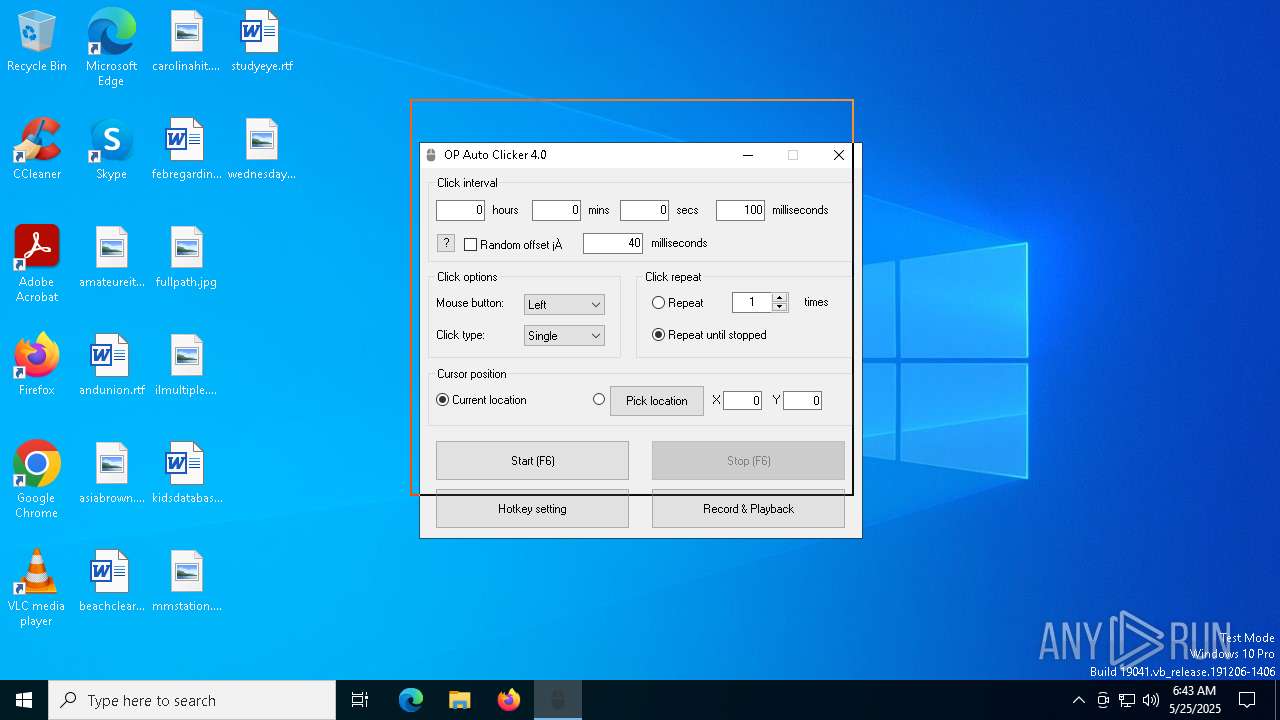
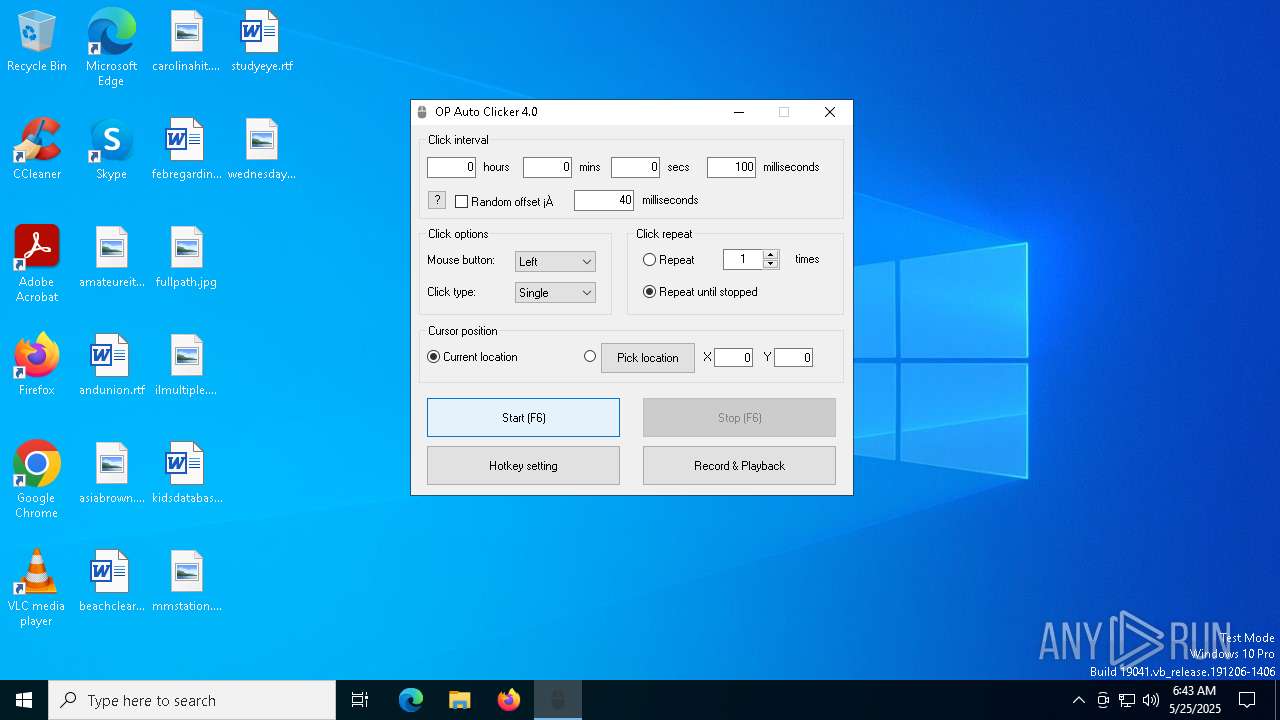
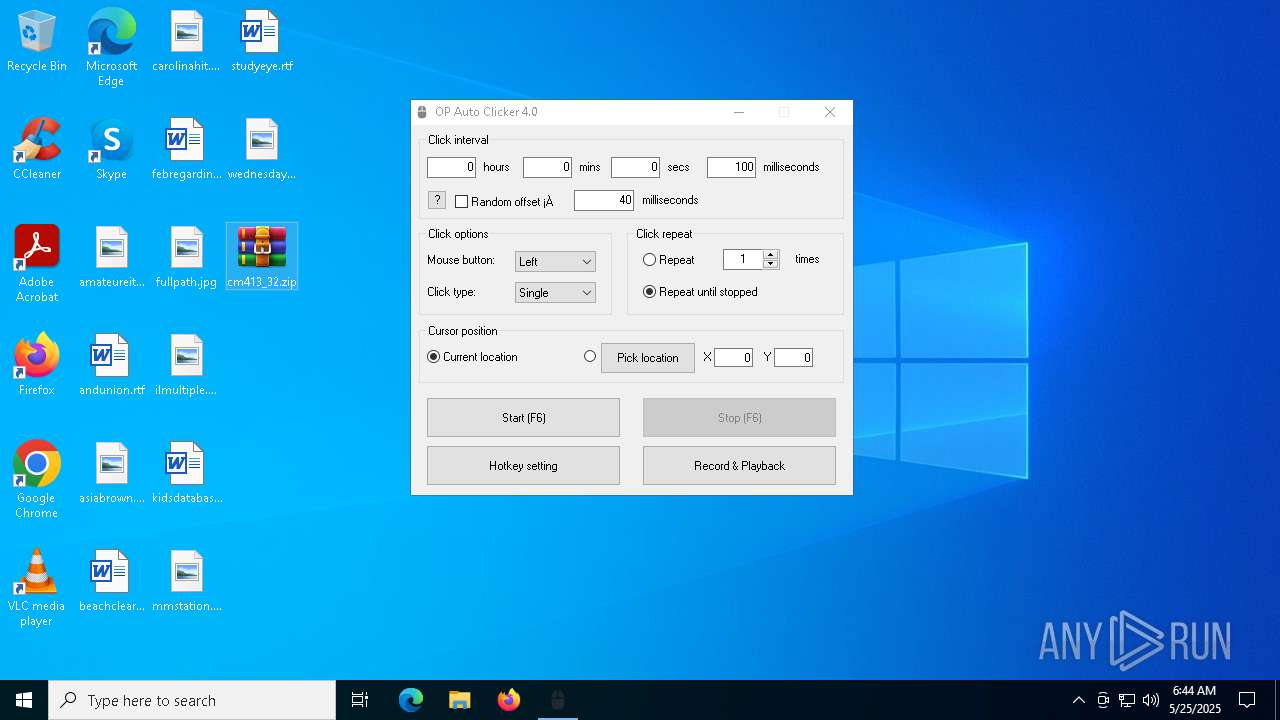
| FileDescription: | OP Auto Clicker |
| FileVersion: | 4 |
| LegalCopyright: | www.opautoclicker.com |
| ProductName: | OP Auto Clicker |
| ProductVersion: | 4 |
Total processes
138
Monitored processes
8
Malicious processes
3
Suspicious processes
0
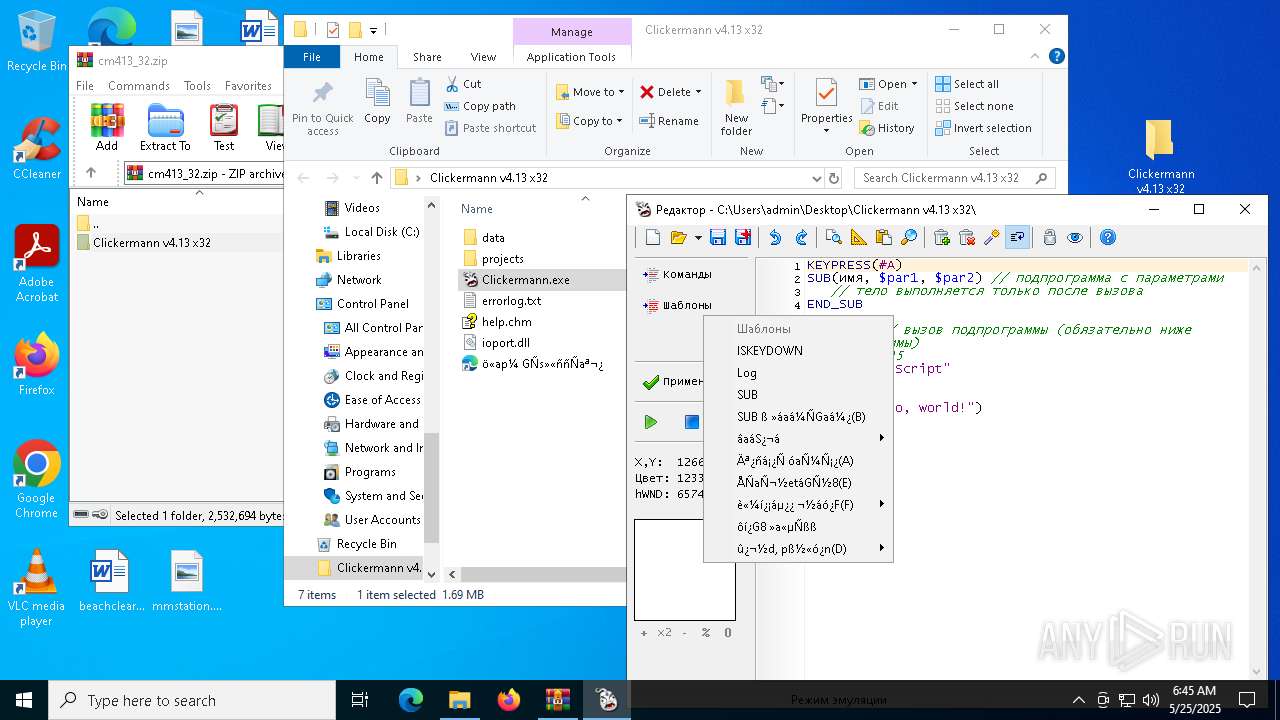
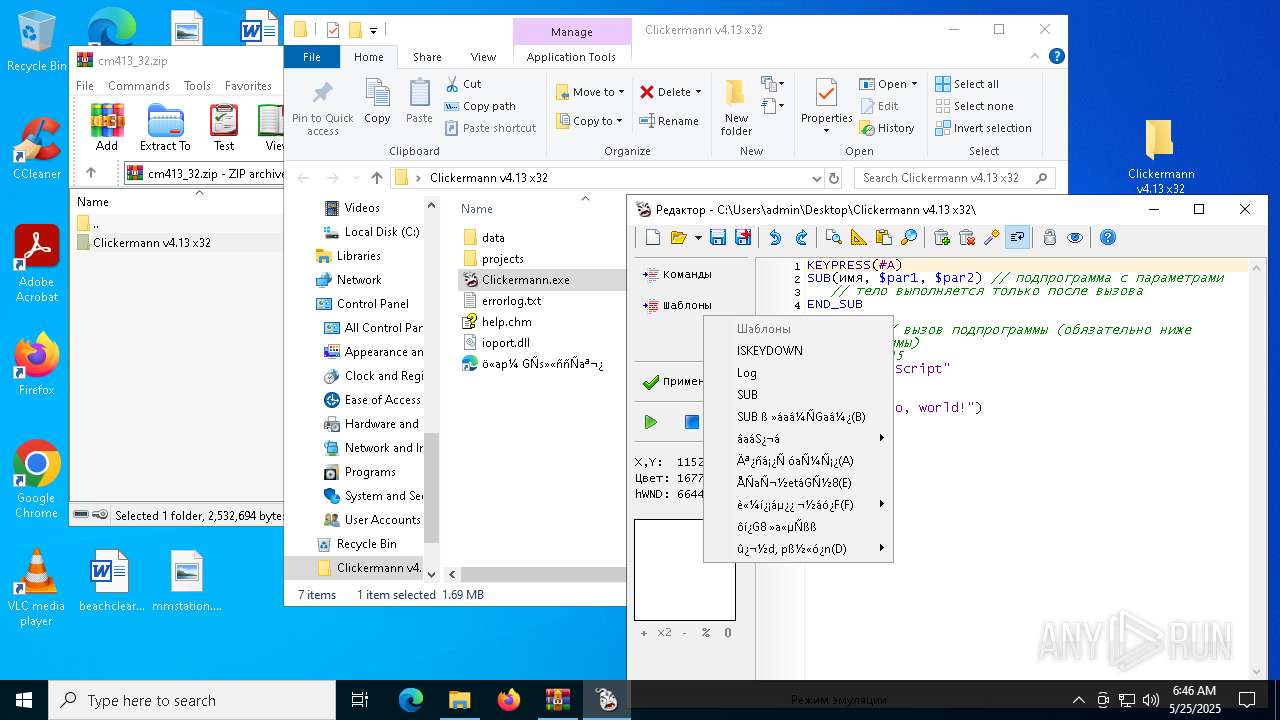
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
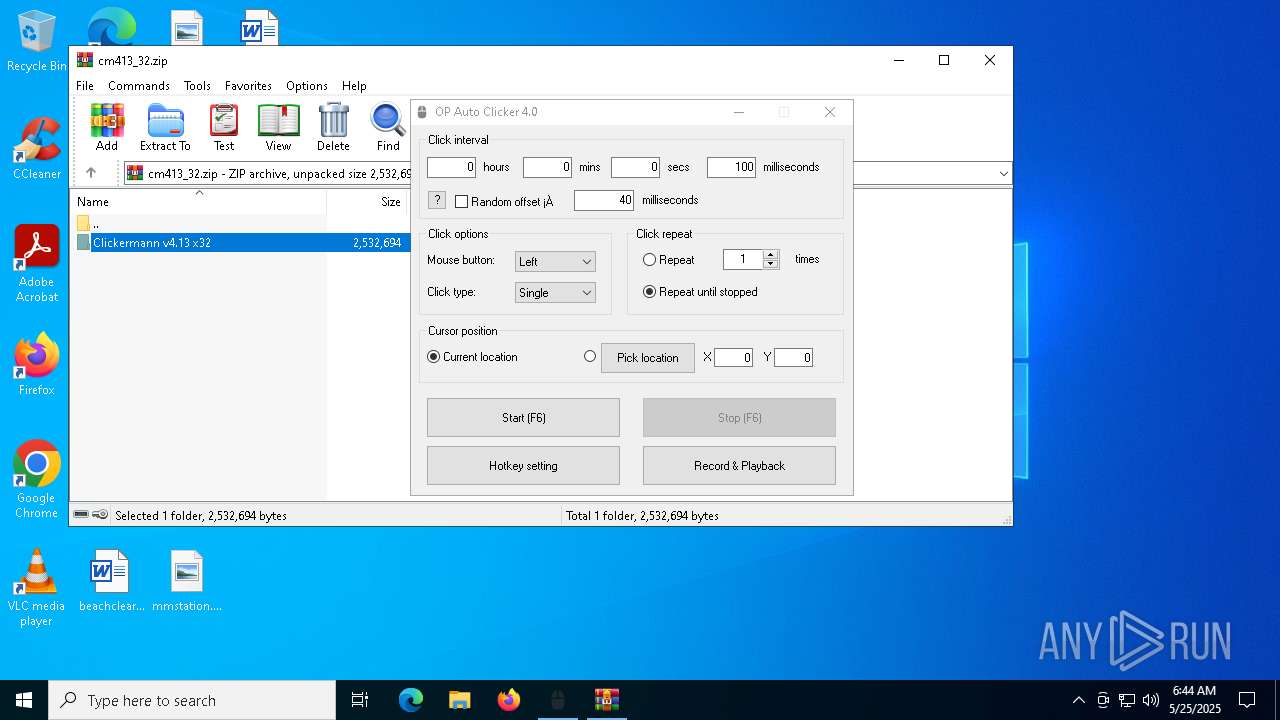
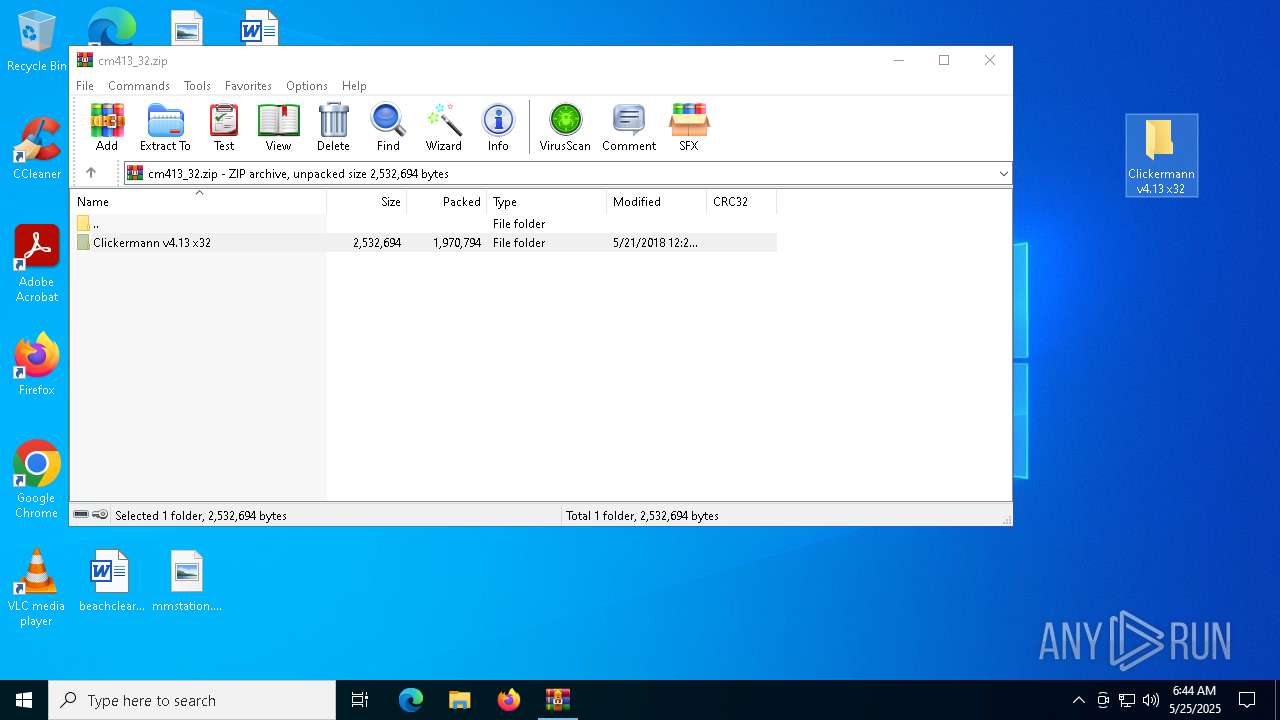
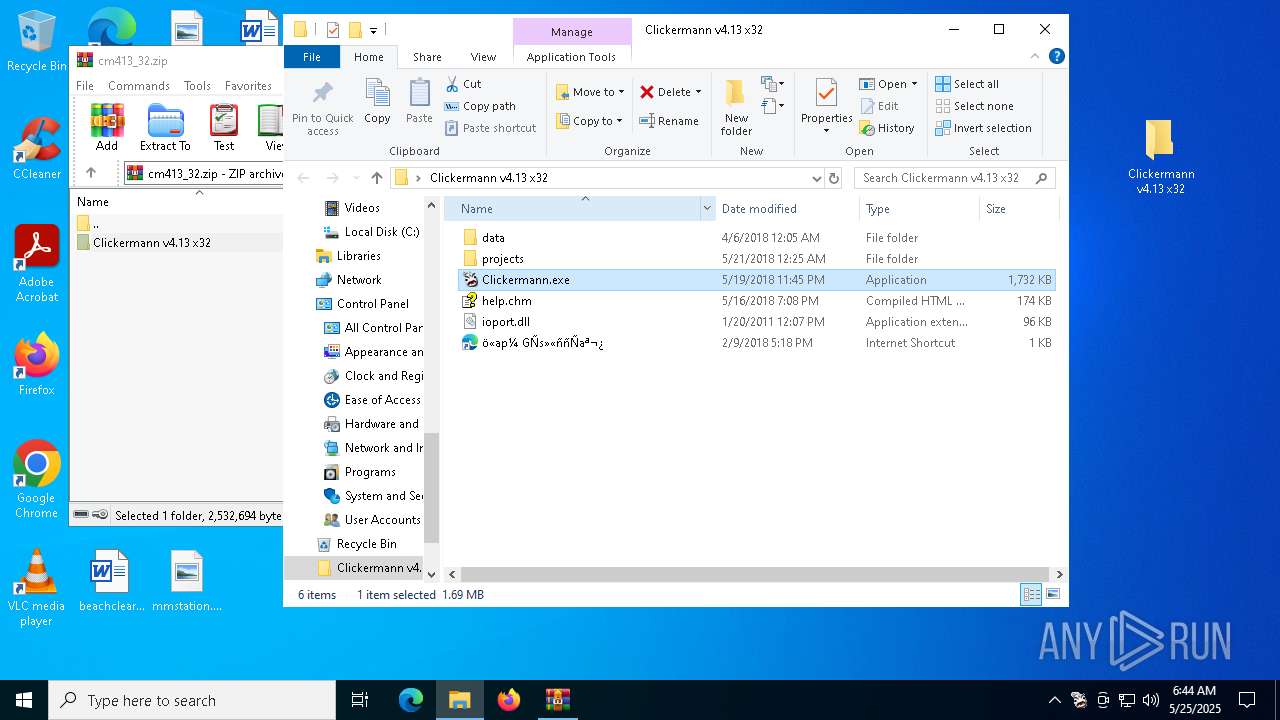
| 1568 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\cm413_32.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 | ||||
| 4008 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 4120 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe |
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | ||||
| 5228 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 6048 | "C:\Users\admin\AppData\Local\Temp\gs-auto-clicker-4-0.exe" | C:\Users\admin\AppData\Local\Temp\gs-auto-clicker-4-0.exe | — | explorer.exe |
User: admin Integrity Level: MEDIUM Description: OP Auto Clicker Exit code: 0 Version: 4.0 | ||||
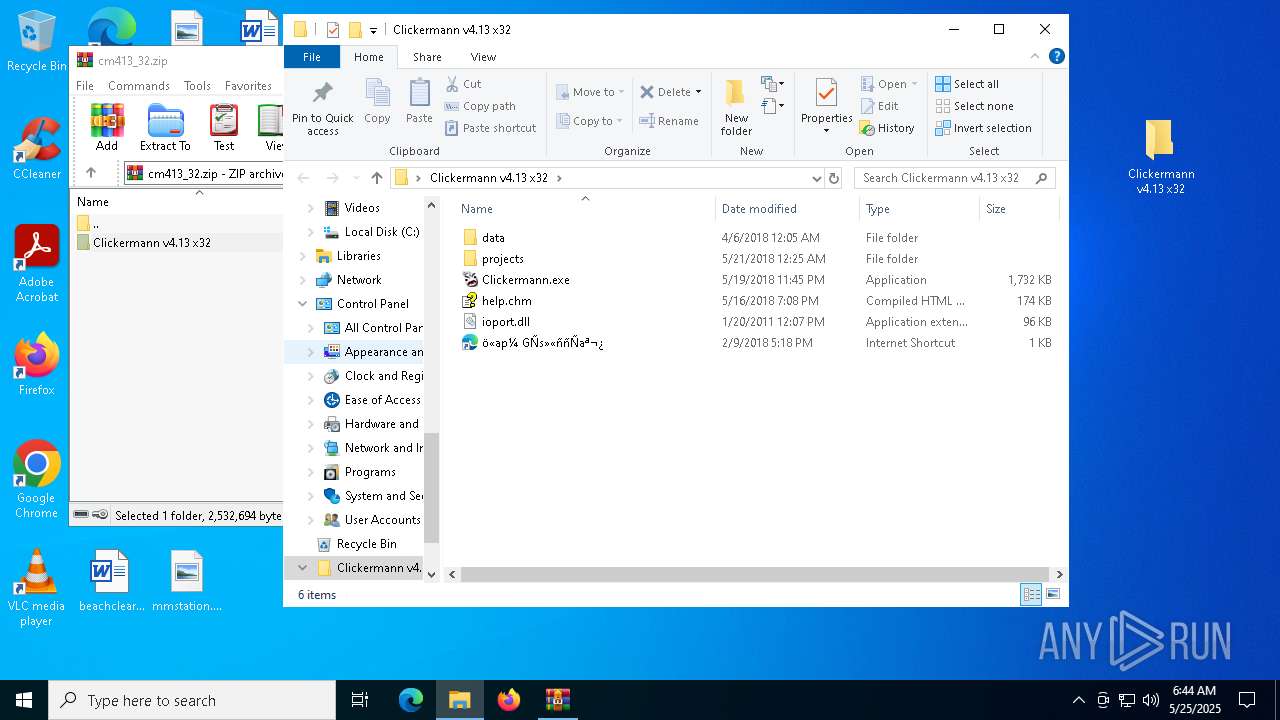
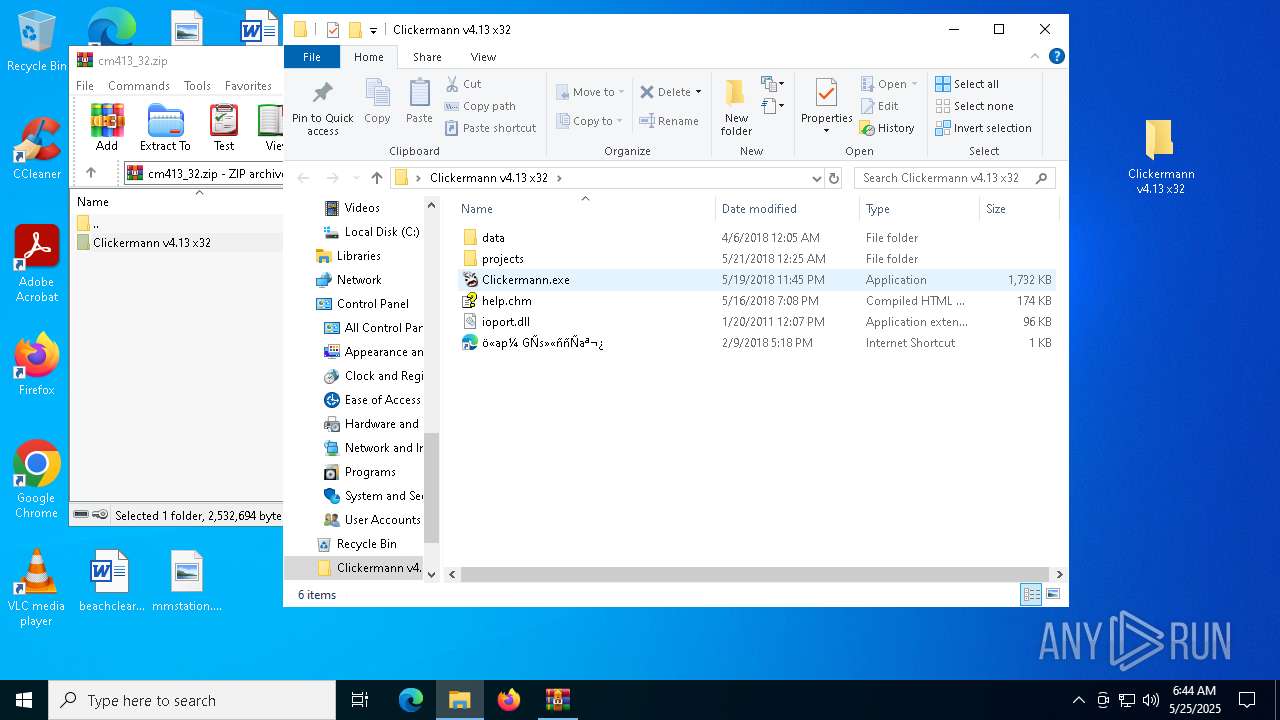
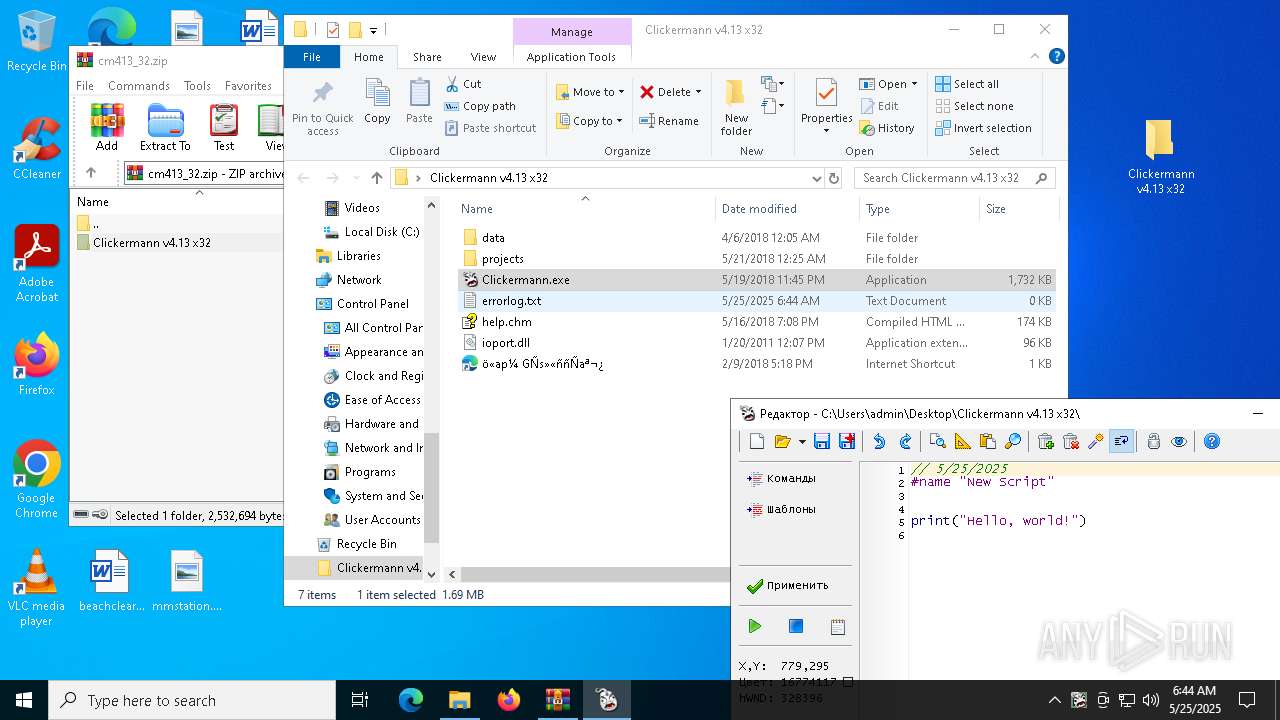
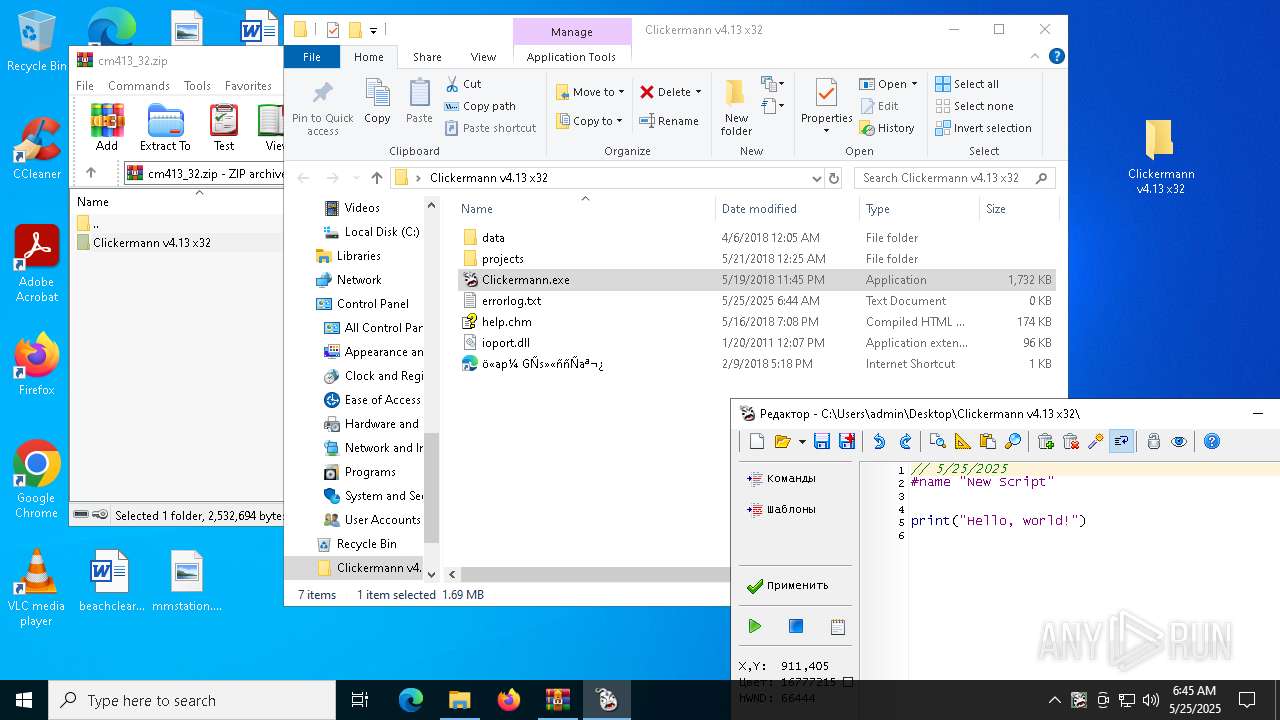
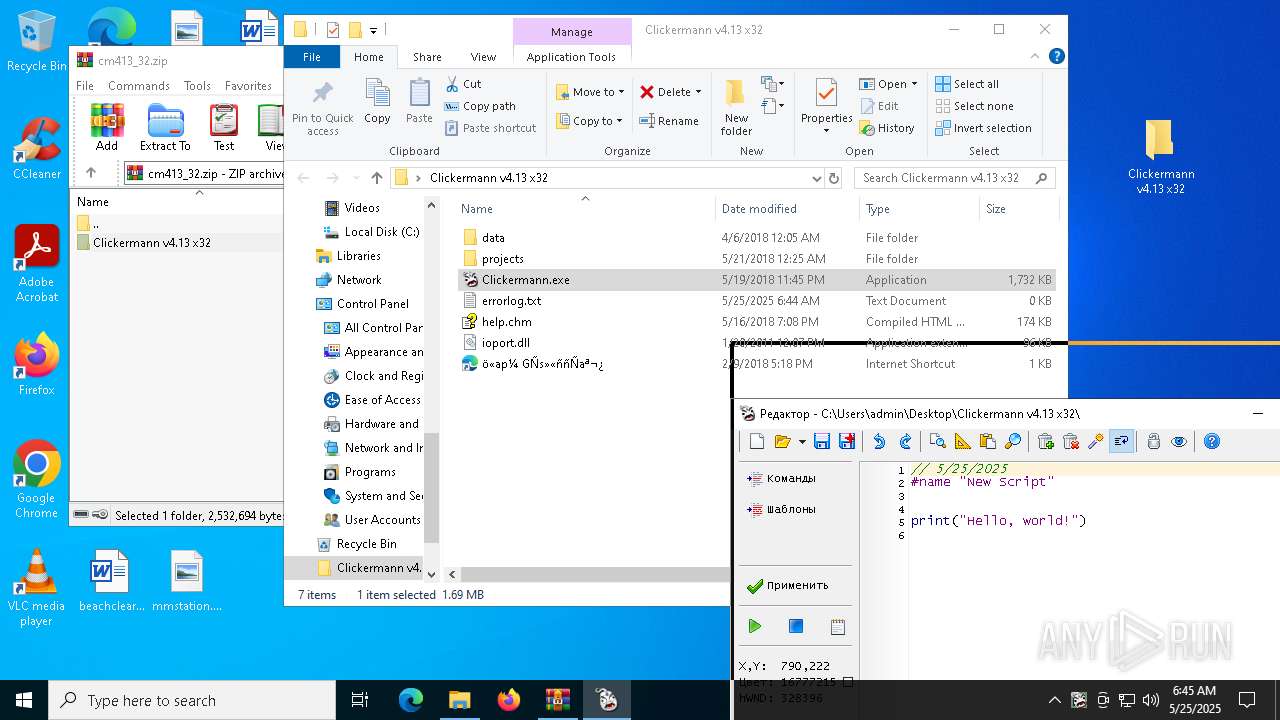
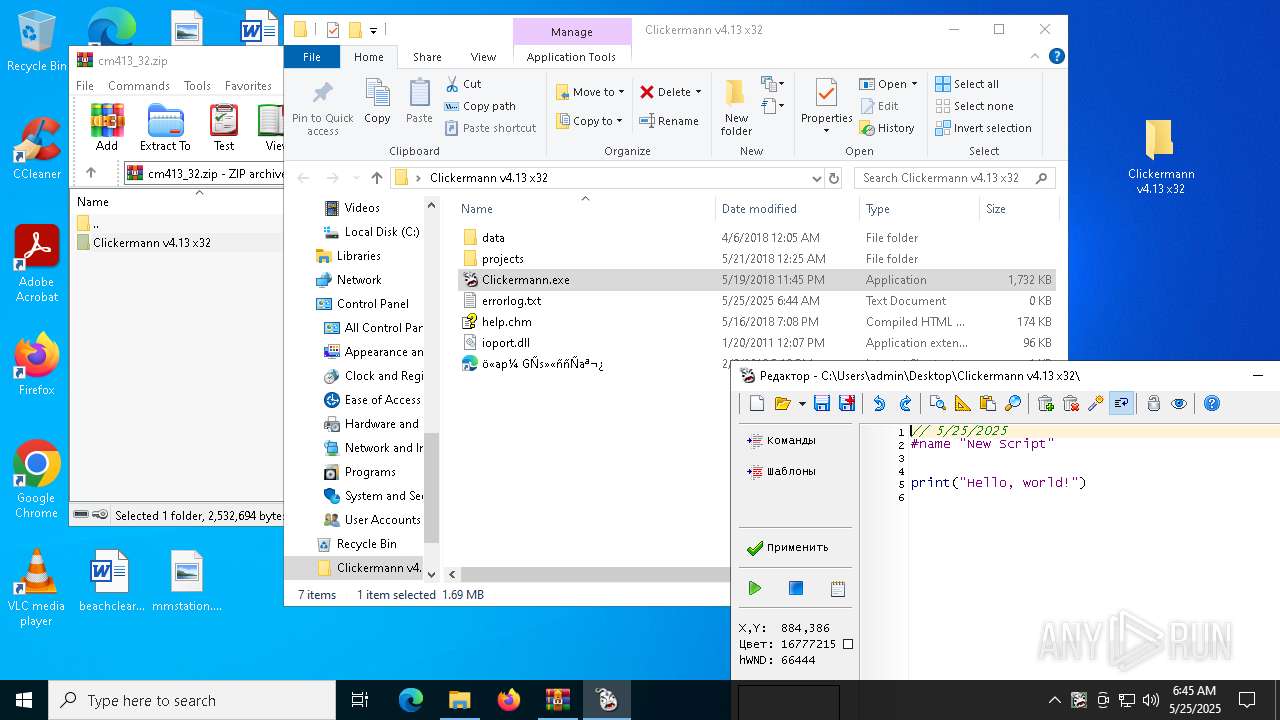
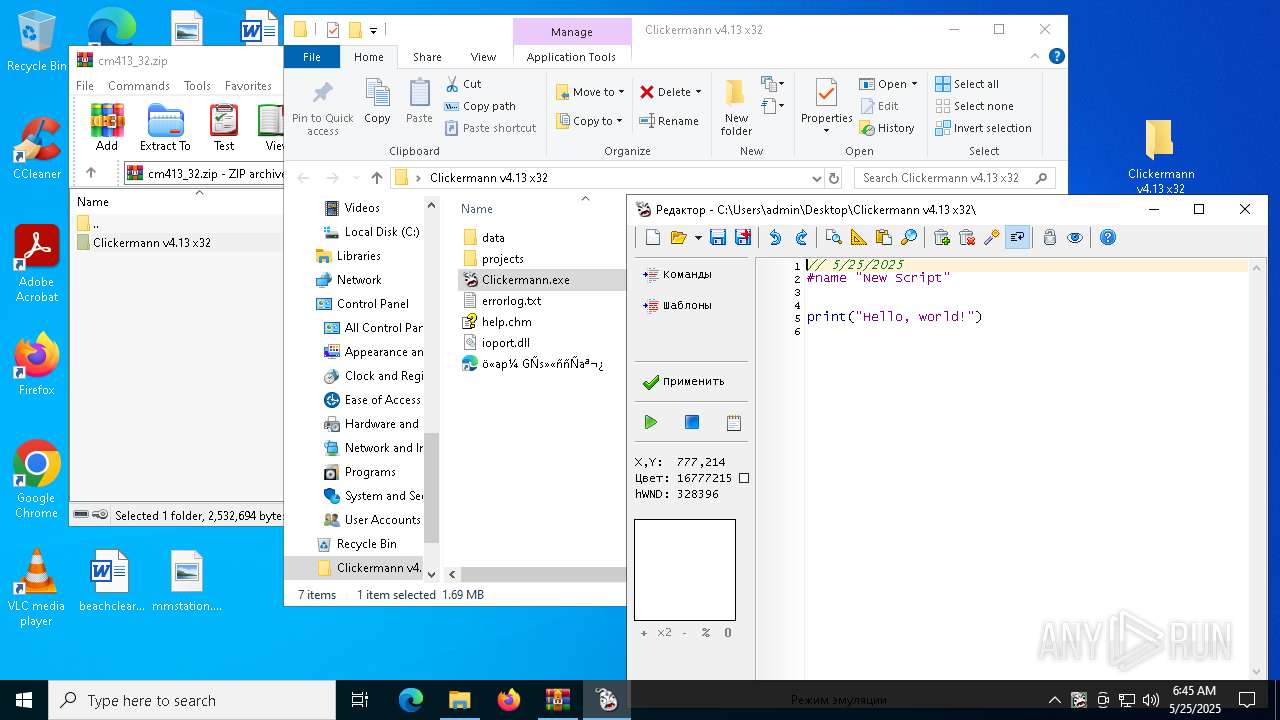
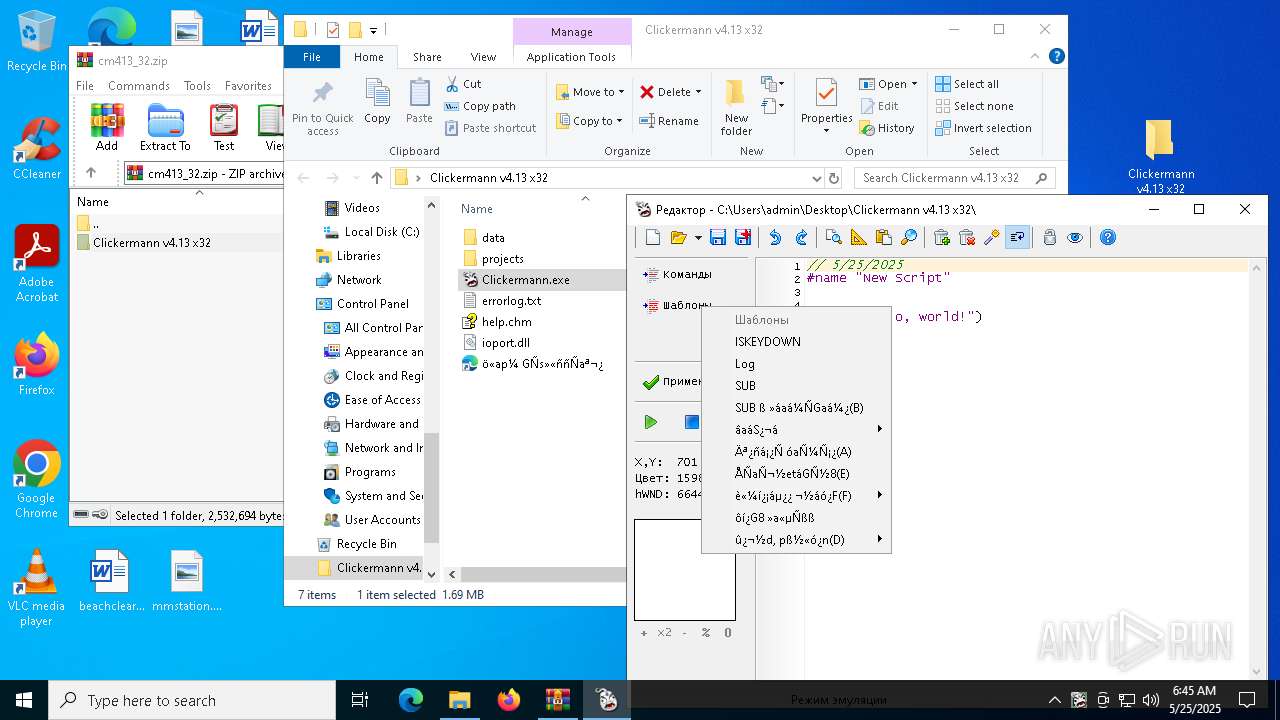
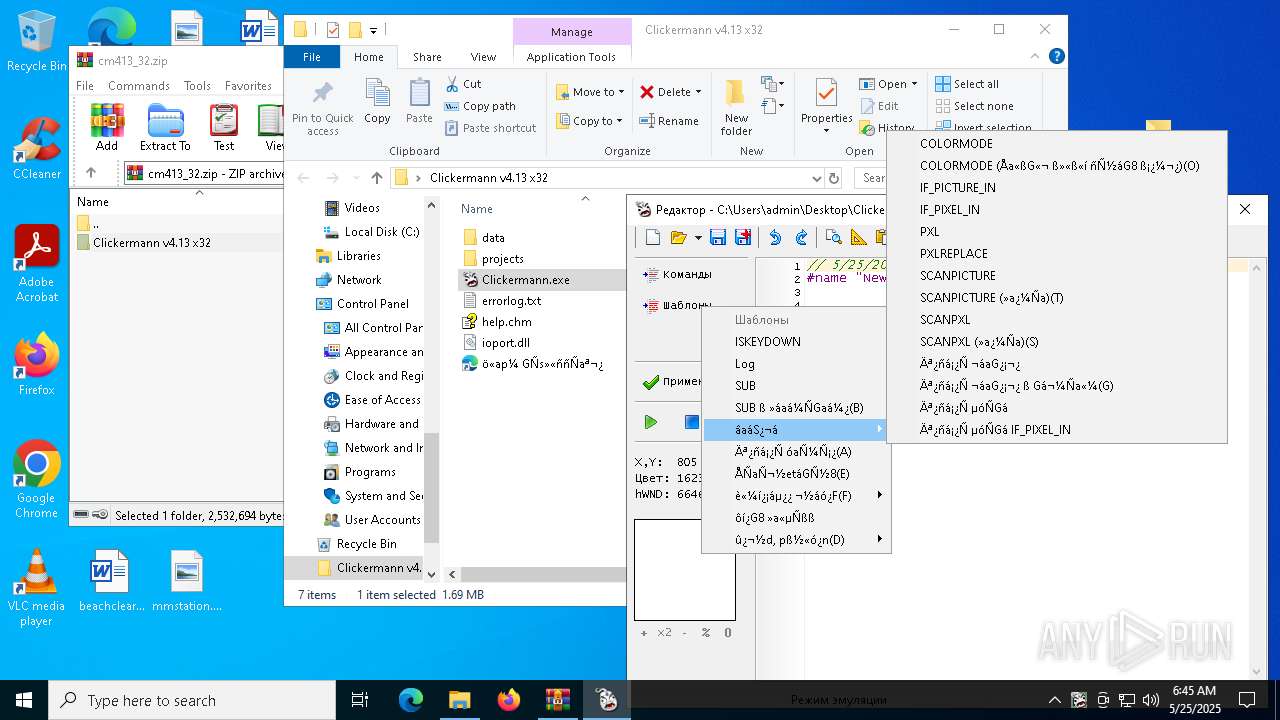
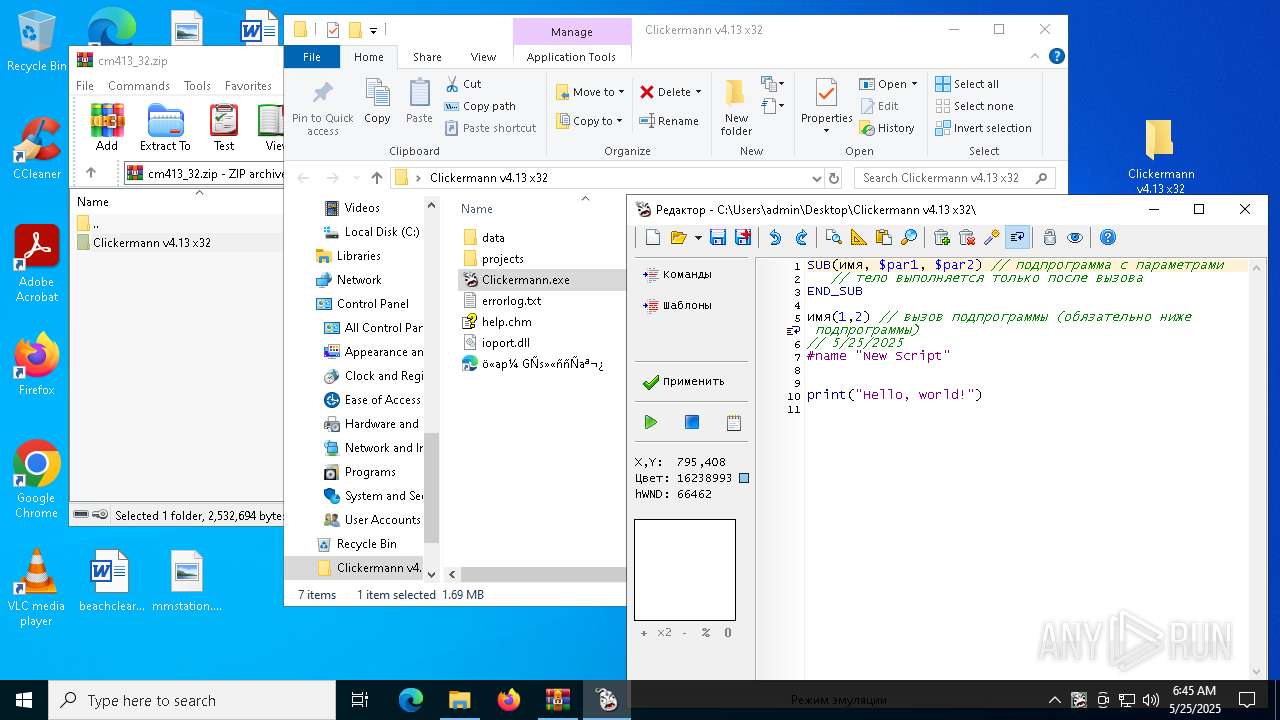
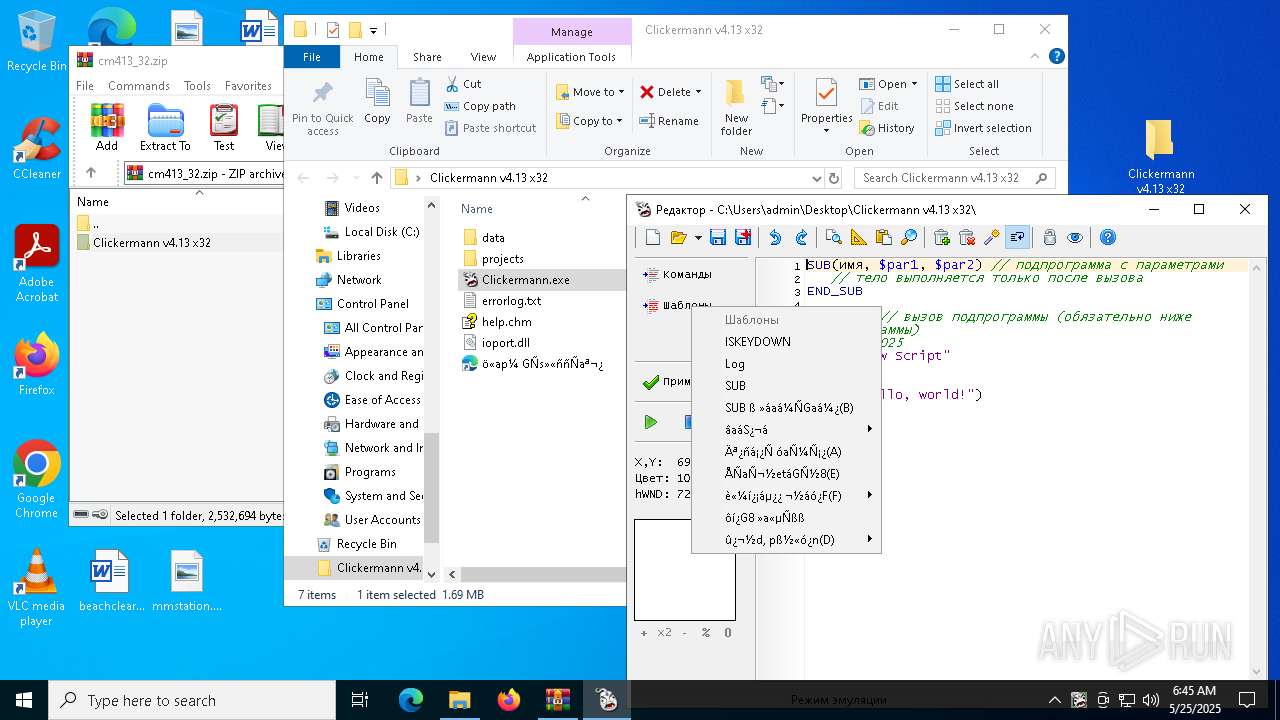
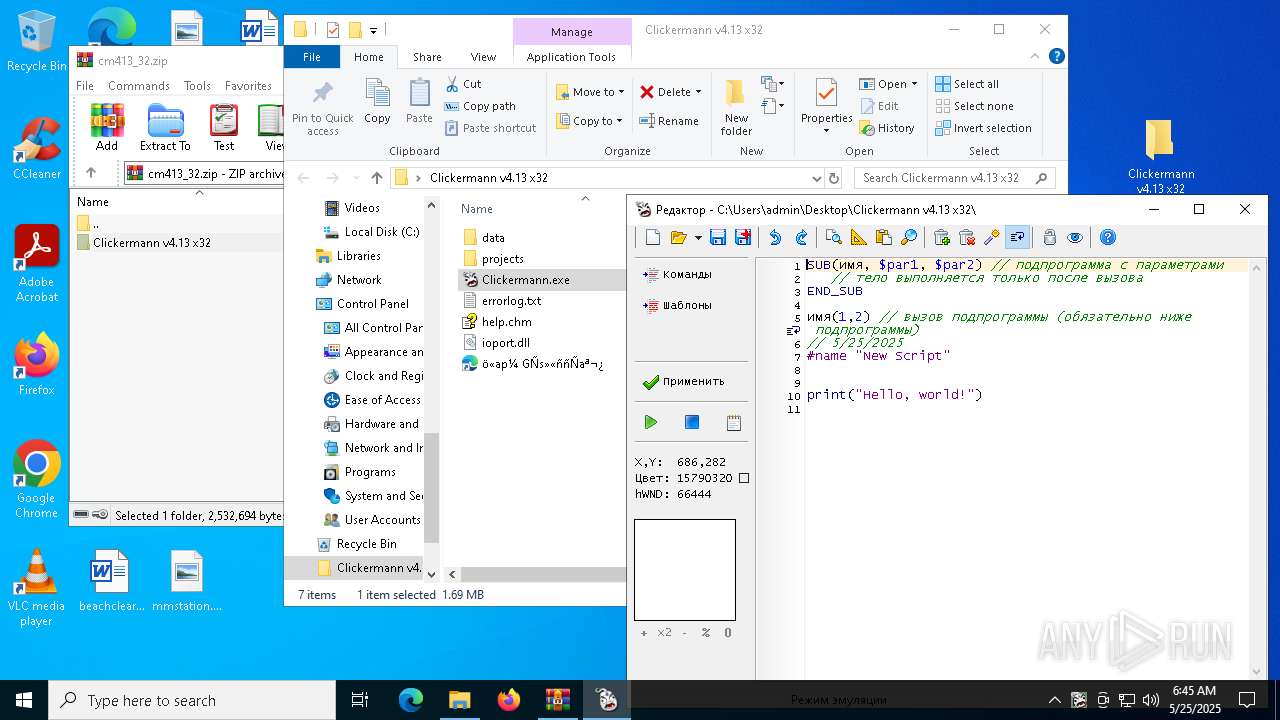
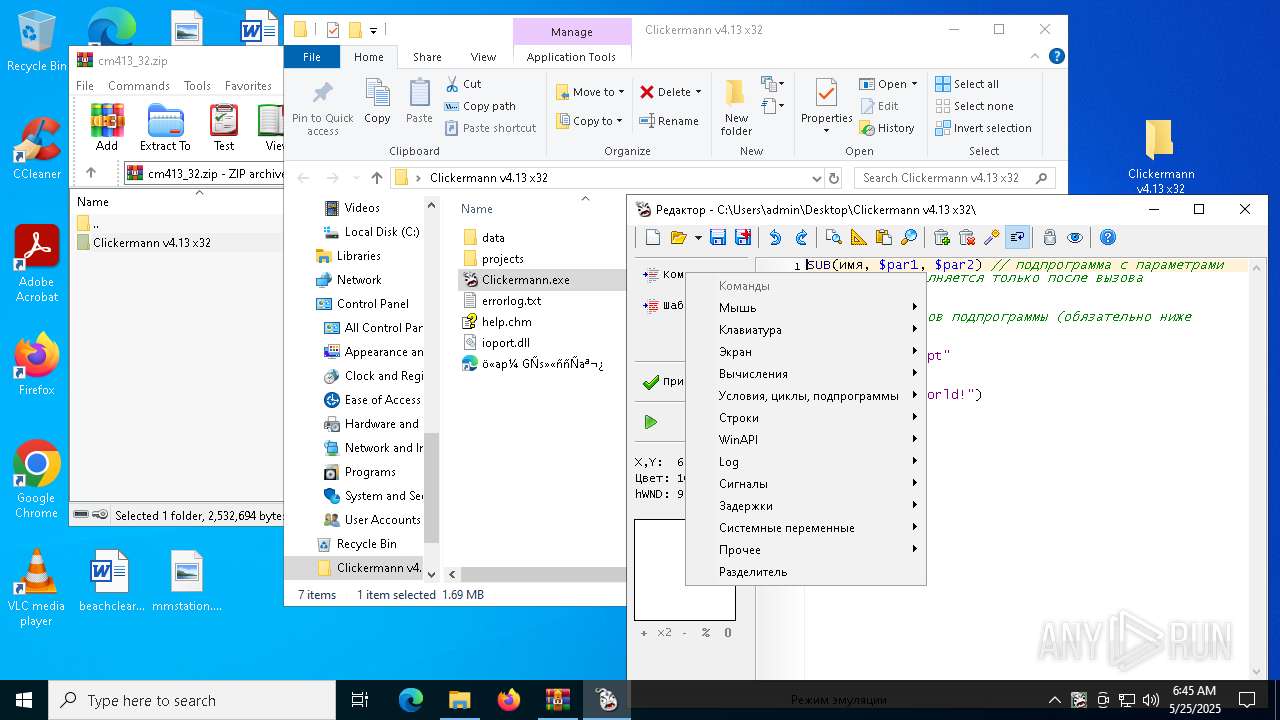
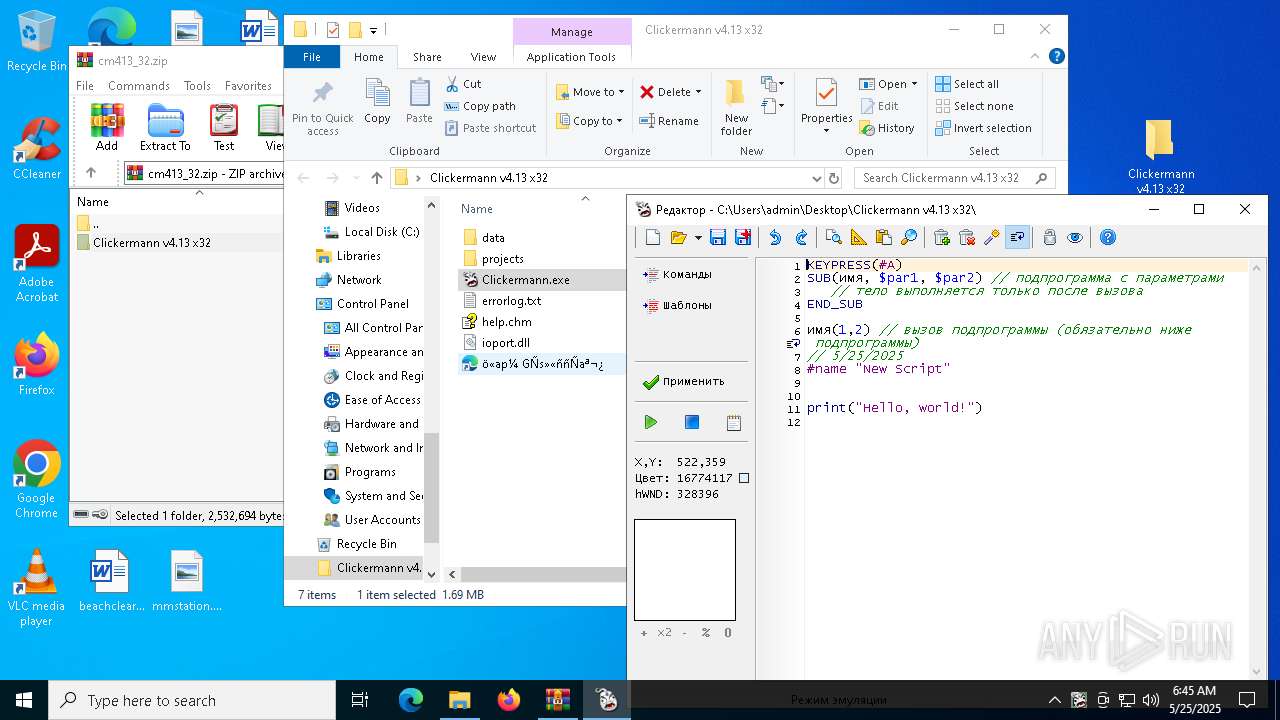
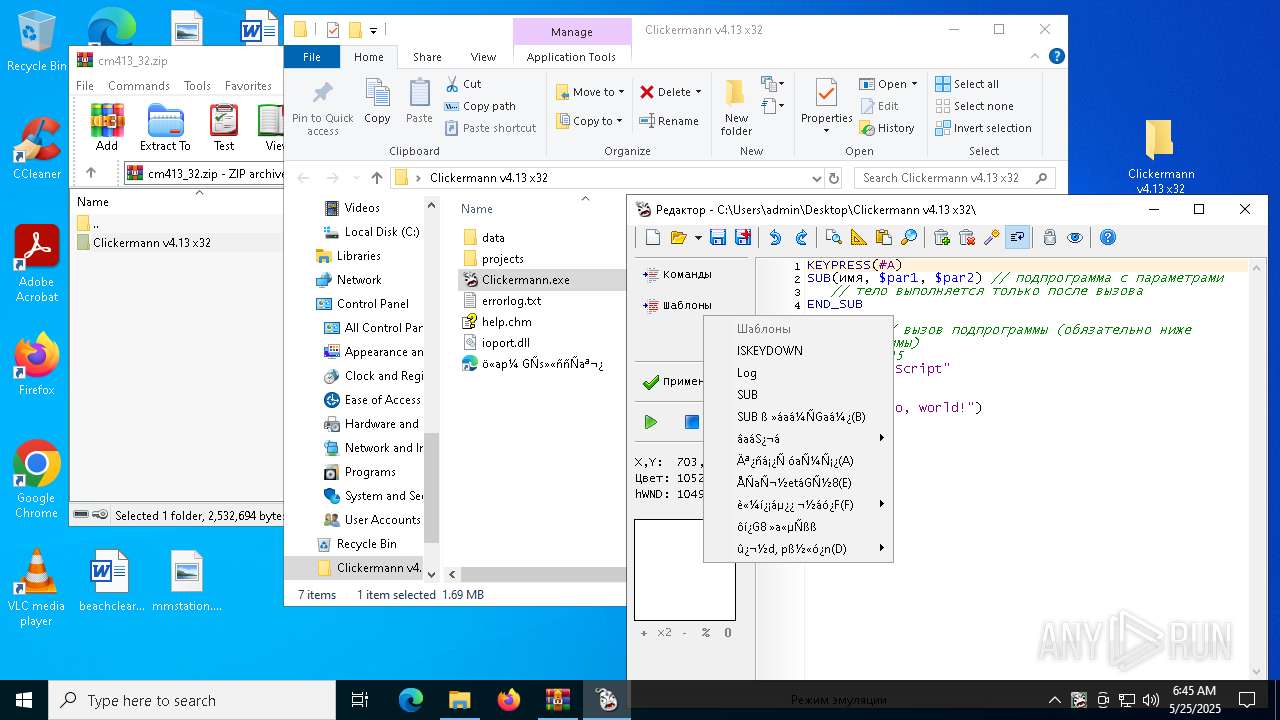
| 6112 | "C:\Users\admin\Desktop\Clickermann v4.13 x32\Clickermann.exe" | C:\Users\admin\Desktop\Clickermann v4.13 x32\Clickermann.exe | — | explorer.exe |
User: admin Integrity Level: MEDIUM Exit code: 1 Version: 4.13.0.0 | ||||
| 6632 | "C:\Users\admin\Desktop\Clickermann v4.13 x32\Clickermann.exe" | C:\Users\admin\Desktop\Clickermann v4.13 x32\Clickermann.exe | explorer.exe | |
User: admin Integrity Level: HIGH Version: 4.13.0.0 | ||||
| 7052 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | |
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
12
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6048 | gs-auto-clicker-4-0.exe | C:\Users\admin\AppData\Local\Temp\ACLib\stop.ico | image | |
MD5:7824CEFAD2522BE614AE5B7BDBF88339 | SHA256:9E869F60EA0A0DE06C7D562FF56D1AC53C534849C919E4B12344E73513649483 | |||
| 6048 | gs-auto-clicker-4-0.exe | C:\Users\admin\AppData\Local\Temp\ACLib\playback.ico | image | |
MD5:A20254EA7F9EF810C1681FA314EDAA28 | SHA256:5375290E66A20BFF81FB4D80346756F2D442184789681297CD1B84446A3FE80D | |||
| 6048 | gs-auto-clicker-4-0.exe | C:\Users\admin\AppData\Local\Temp\hakpean | text | |
MD5:8C4B5FAC3B12AD13E28FBDF7F9C71973 | SHA256:5DD93A460932E01E66E25D3BF38589392403CEE807526EAEF1DA58E175BD9E08 | |||
| 6048 | gs-auto-clicker-4-0.exe | C:\Users\admin\AppData\Local\Temp\ACLib\record.ico | image | |
MD5:1111E06679F96FF28C1E229B06CE7B41 | SHA256:59D5E9106E907FA61A560294A51C14ABCDE024FDD690E41A7F4D6C88DB7287A6 | |||
| 1568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1568.28090\Clickermann v4.13 x32\data\lang\en\gui.txt | text | |
MD5:44CE0B5DE1B8A6E45675682802C52EAC | SHA256:621C08DAD3EAE99ED955214059CEA28CDDF90BF49BA69004D9CF4B2DE4268DC4 | |||
| 1568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1568.28090\Clickermann v4.13 x32\data\const.txt | text | |
MD5:7CE5AECC10CE04264638117E9624007F | SHA256:8547D277D84DF62CF12F17BC5DF6098C9BA08ACC0CE4572FBA1312ACBF8B0A40 | |||
| 1568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1568.28090\Clickermann v4.13 x32\data\lang\en\qinsert_menu.txt | text | |
MD5:DD14046C09B76E35CF4004883EBBA367 | SHA256:7804D67B7DD8D44186B5DA3A142EE8C6F1880F4FAA3D2B575B3A10FF43131316 | |||
| 1568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1568.28090\Clickermann v4.13 x32\Clickermann.exe | executable | |
MD5:07FF8B7F7DCF4A787803CB5F52478418 | SHA256:90B6FBC25511D3CA7665B0E5C43E4B0EA9498967B6F2D19B94084B33A0A19779 | |||
| 1568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1568.28090\Clickermann v4.13 x32\data\config.ini | binary | |
MD5:9A036DEEBAAEDB6DEA4141B6DEB291FC | SHA256:5B2AF7BB2CD2B0EACBBF9D6934F35A4A2DD8C531A8D1F8E06678C1DC3D8F0E6C | |||
| 1568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1568.28090\Clickermann v4.13 x32\data\config_editor.ini | binary | |
MD5:F13AD46675DA46F947389B348EF33D67 | SHA256:6FB6F19203CA198169DD160A19D61BA8ACA94BEA046BFF4CA8133F4D22911DFA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
21
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 868 b | whitelisted |
6800 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 419 b | whitelisted |
6800 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | QA | binary | 407 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5592 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5796 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6800 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6800 | SIHClient.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
login.live.com |
| whitelisted |